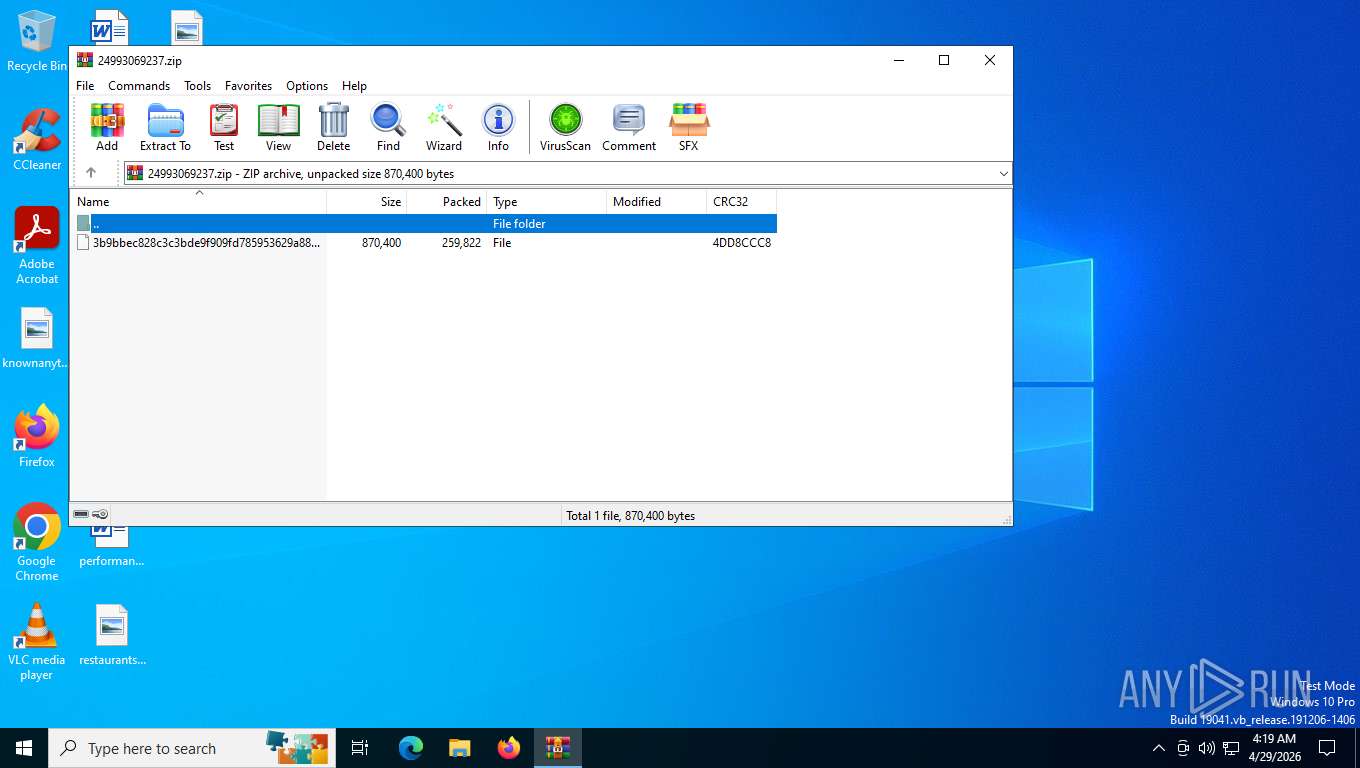
| File name: | 24993069237.zip |
| Full analysis: | https://app.any.run/tasks/7b8c8b26-9a88-415a-ae37-1cc5a45ee935 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2026, 08:19:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 5F947185BB9B72F14CA55C78D249A9E9 |
| SHA1: | A07EF94F3C2FCB99D33B85175F0BAFEC2A5334ED |
| SHA256: | C5E127E32D498E12F5DB4CEB81F28E927F4DC4D5081C30658DE23CDC9438DDEA |
| SSDEEP: | 12288:PHcuStqw6w5Tu8raYECHemKDUk5w3xSHOC3I:/cuSww6H8eYEC+mKDI3xiOC3I |
MALICIOUS
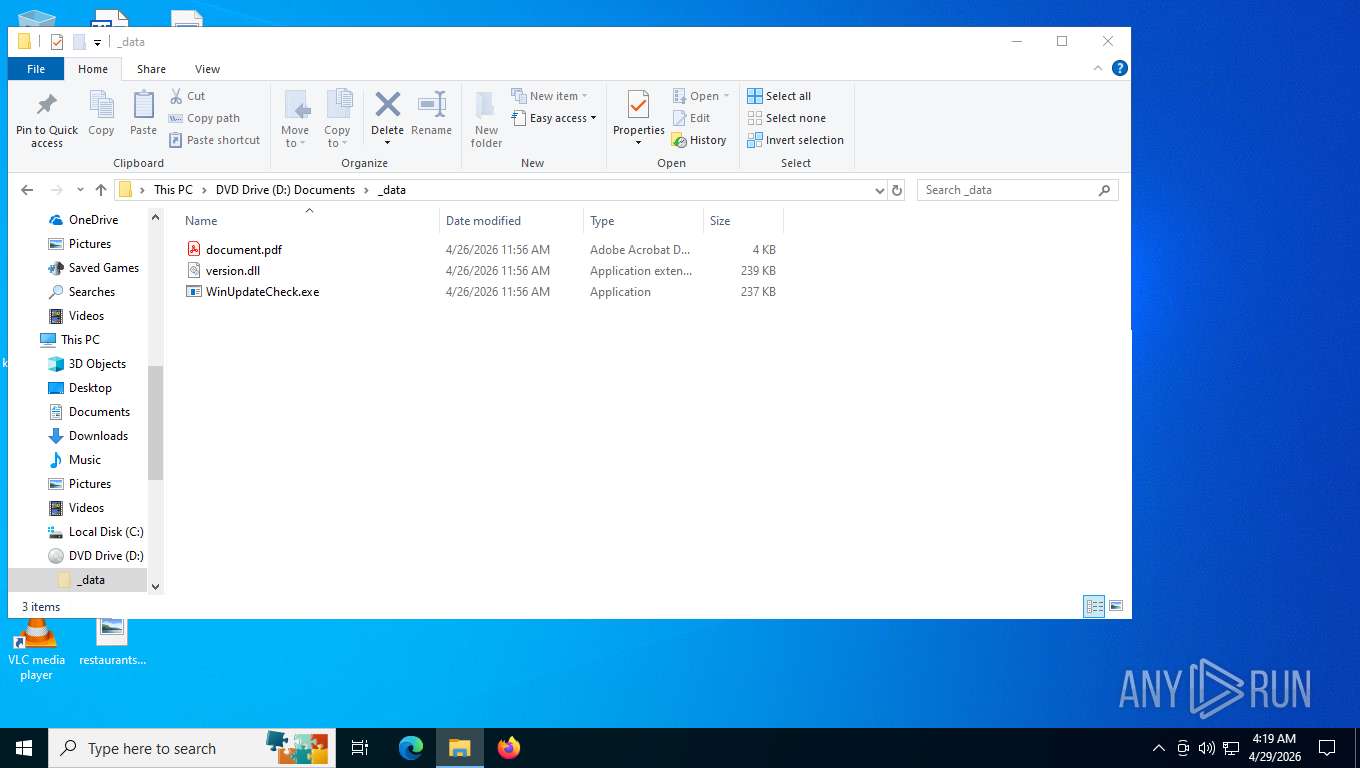
Executing a file with an untrusted certificate
- WinUpdateCheck.exe (PID: 8176)
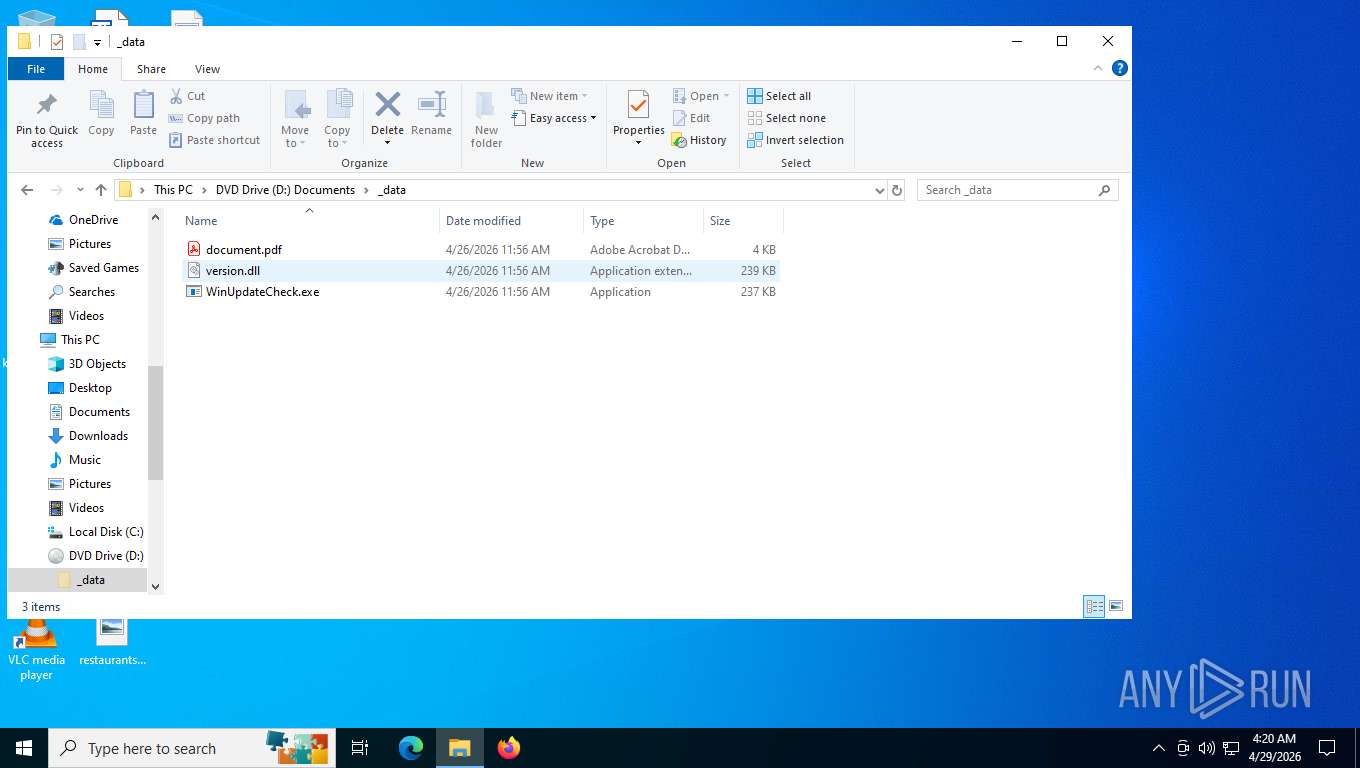
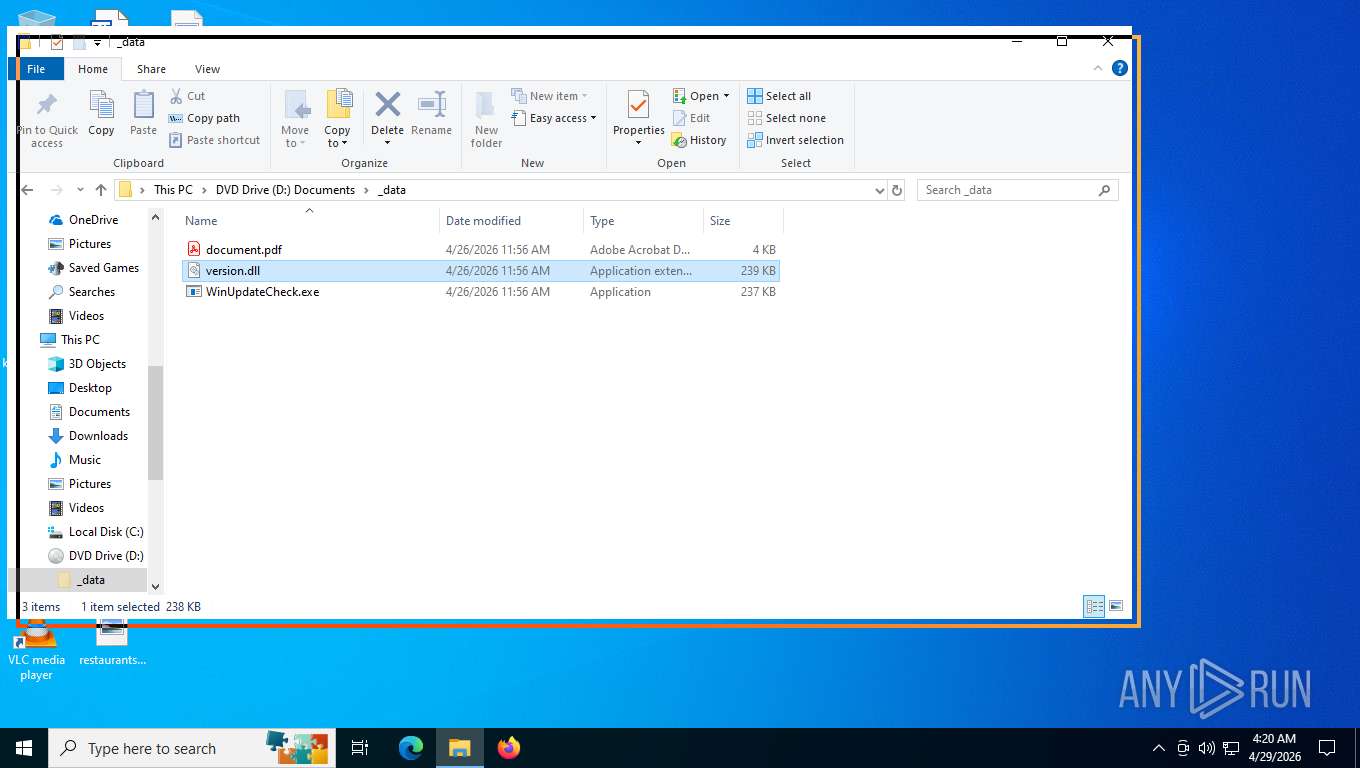
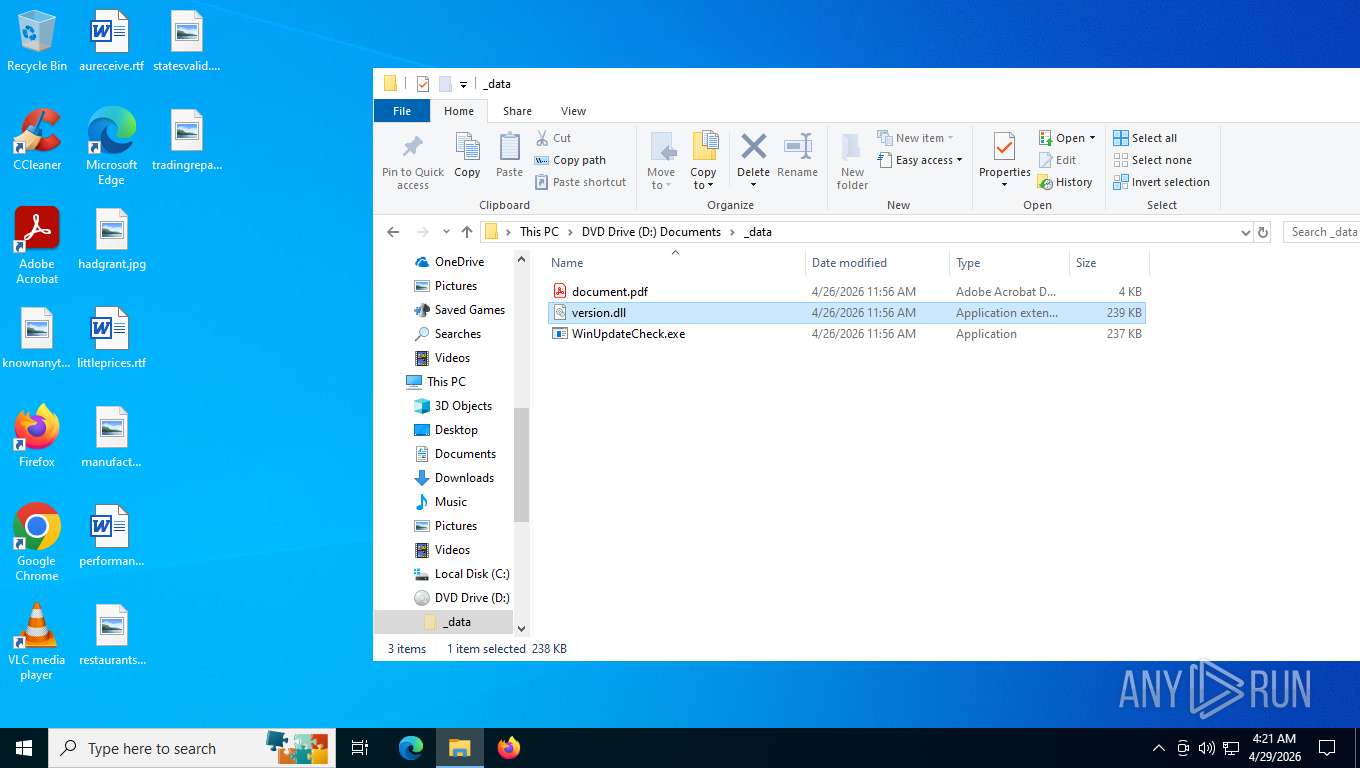
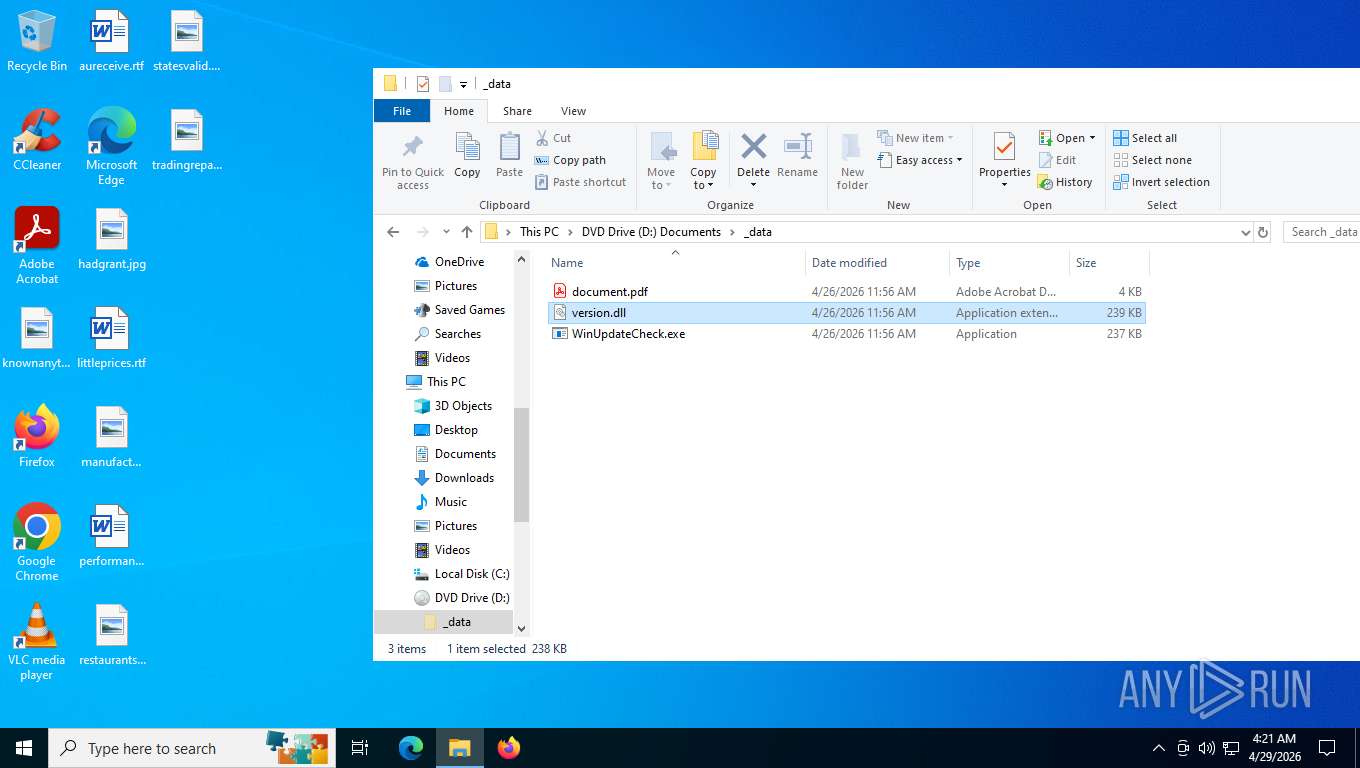
Potential DLL hijacking behavior detected
- WinUpdateCheck.exe (PID: 8176)
Changes the autorun value in the registry
- WinUpdateCheck.exe (PID: 8176)
Uses Task Scheduler to autorun other applications
- WinUpdateCheck.exe (PID: 8176)
Create files in the Startup directory
- WinUpdateCheck.exe (PID: 8176)
Uses Task Scheduler to run other applications
- WinUpdateCheck.exe (PID: 8176)
SUSPICIOUS
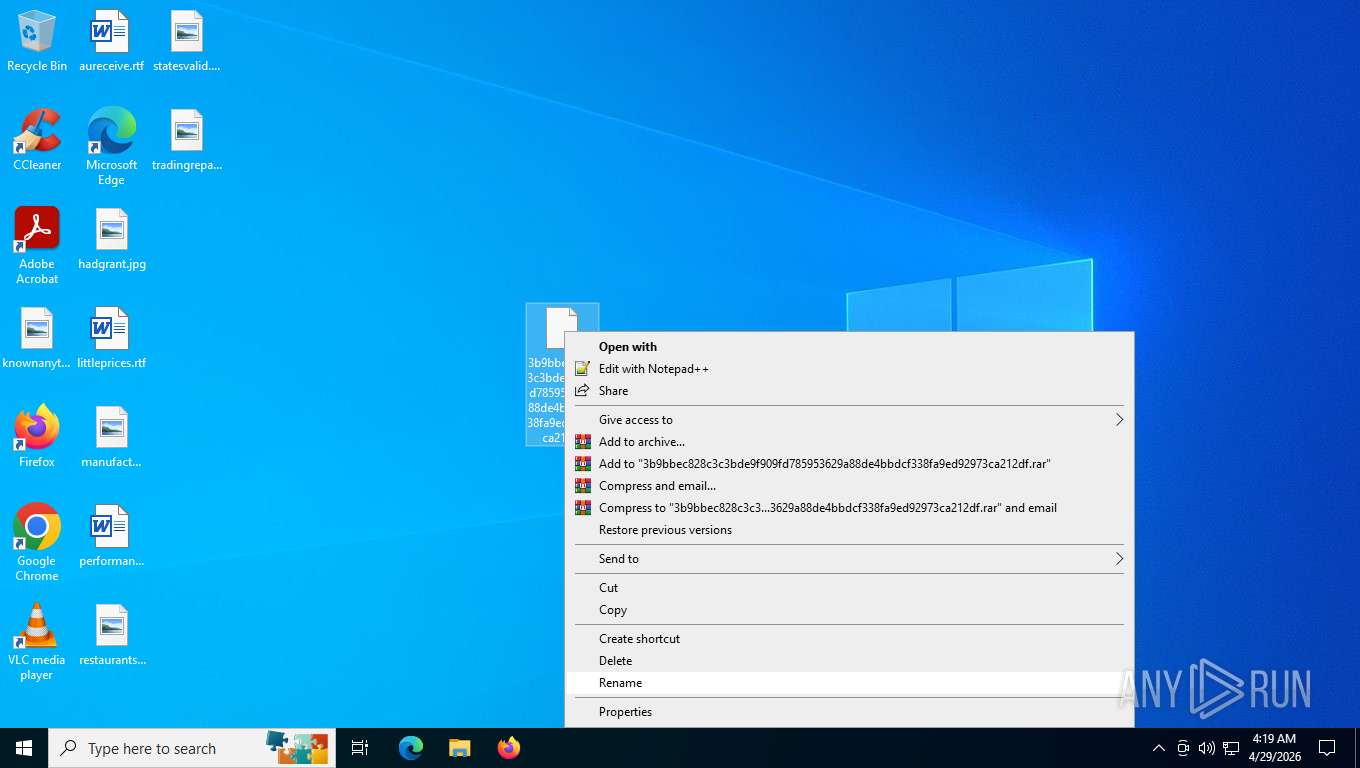
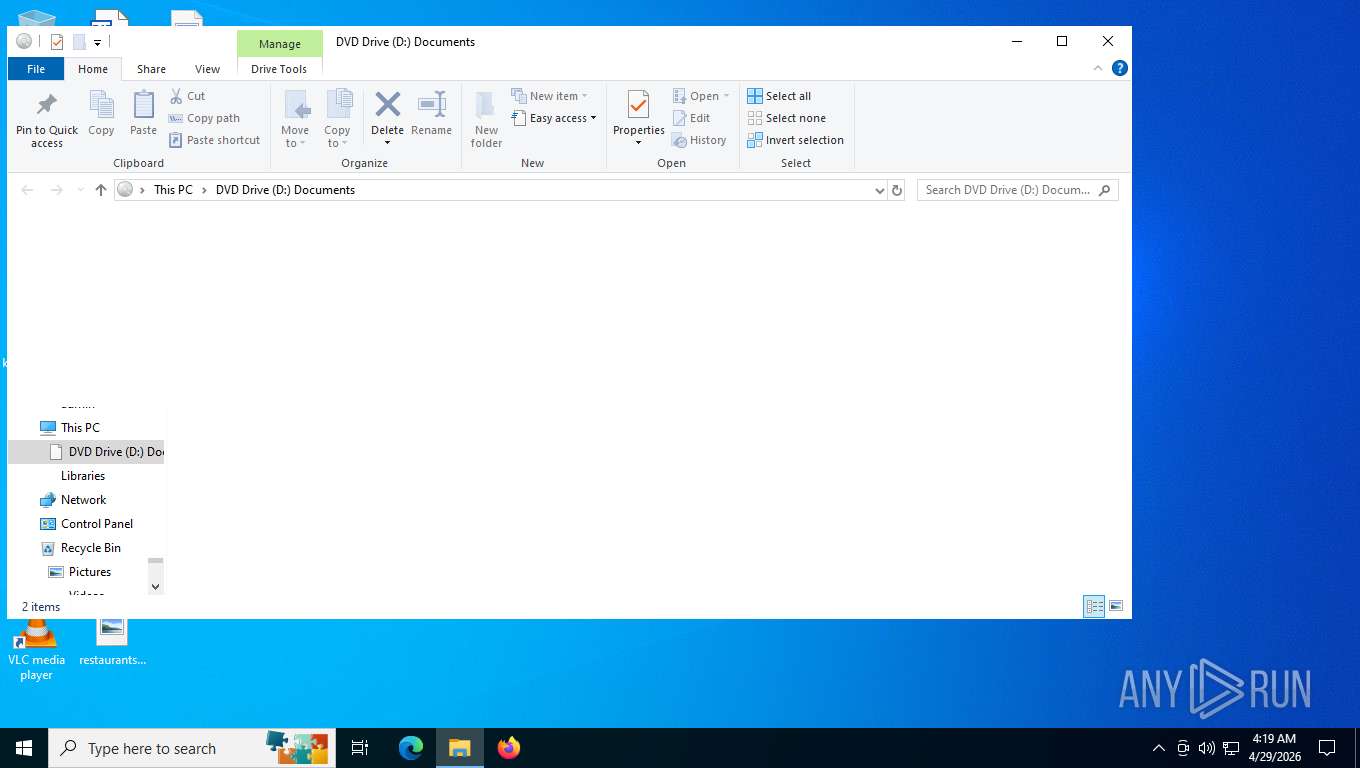
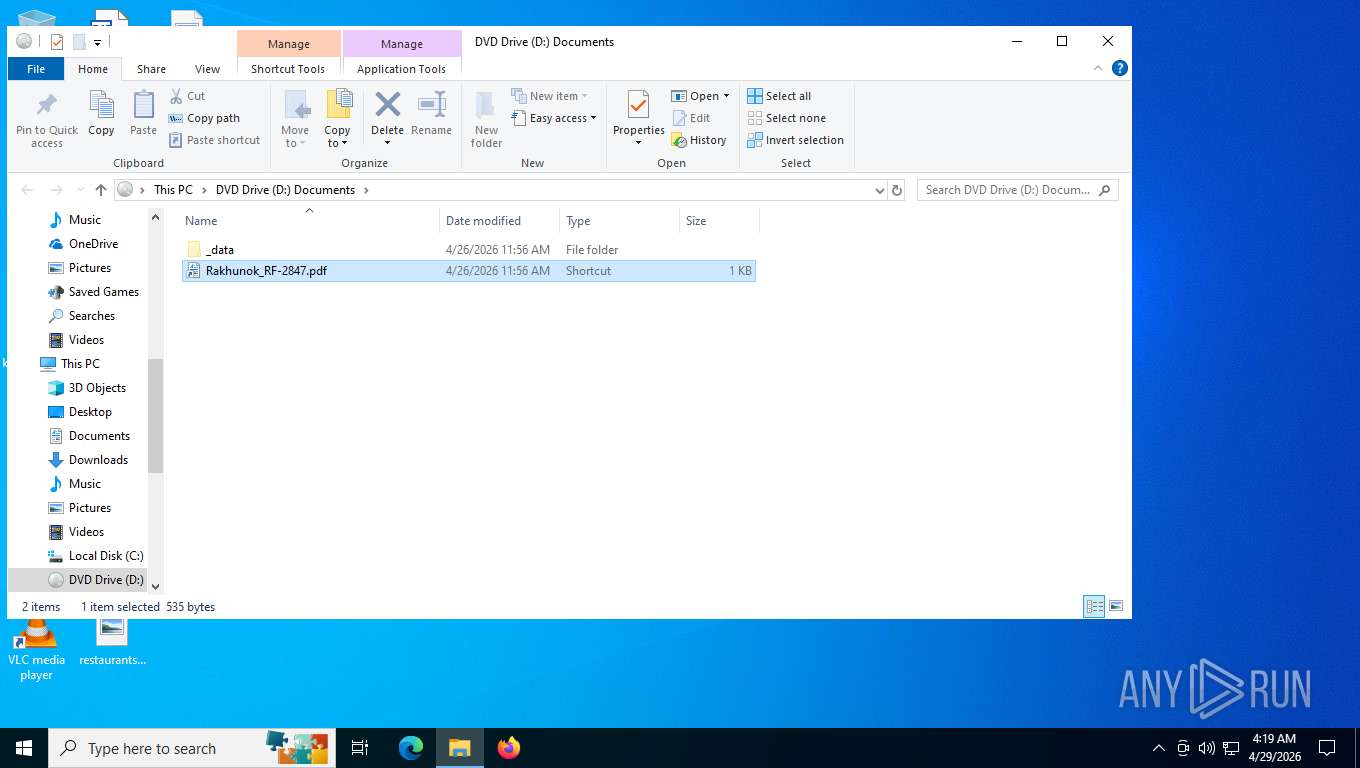
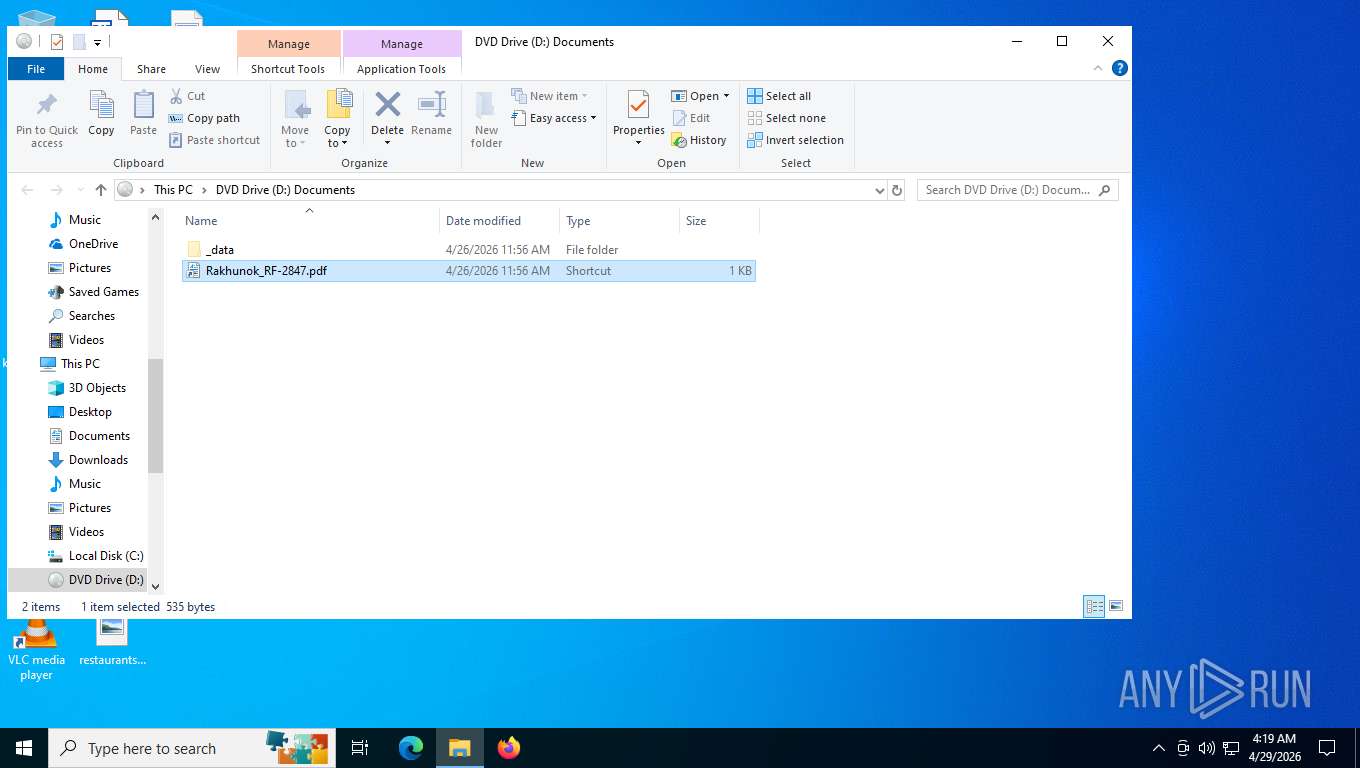
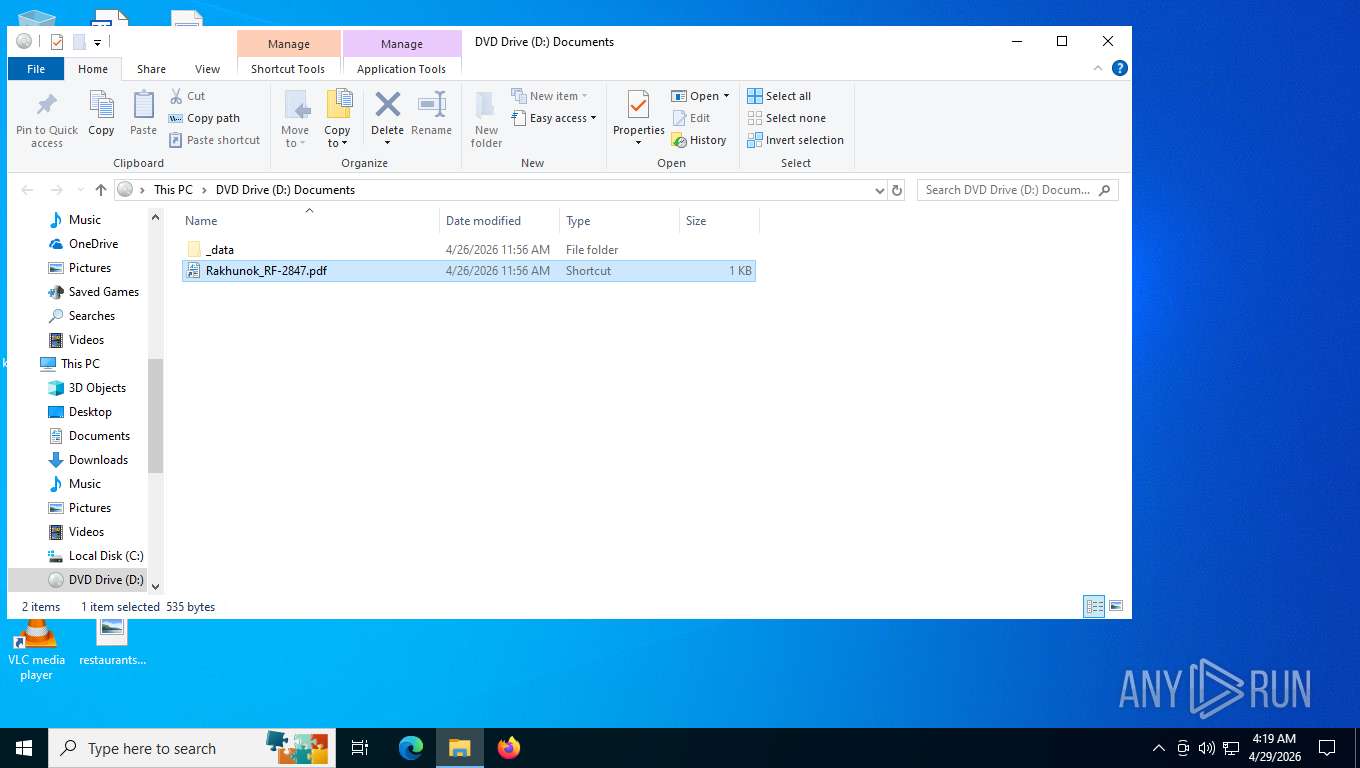
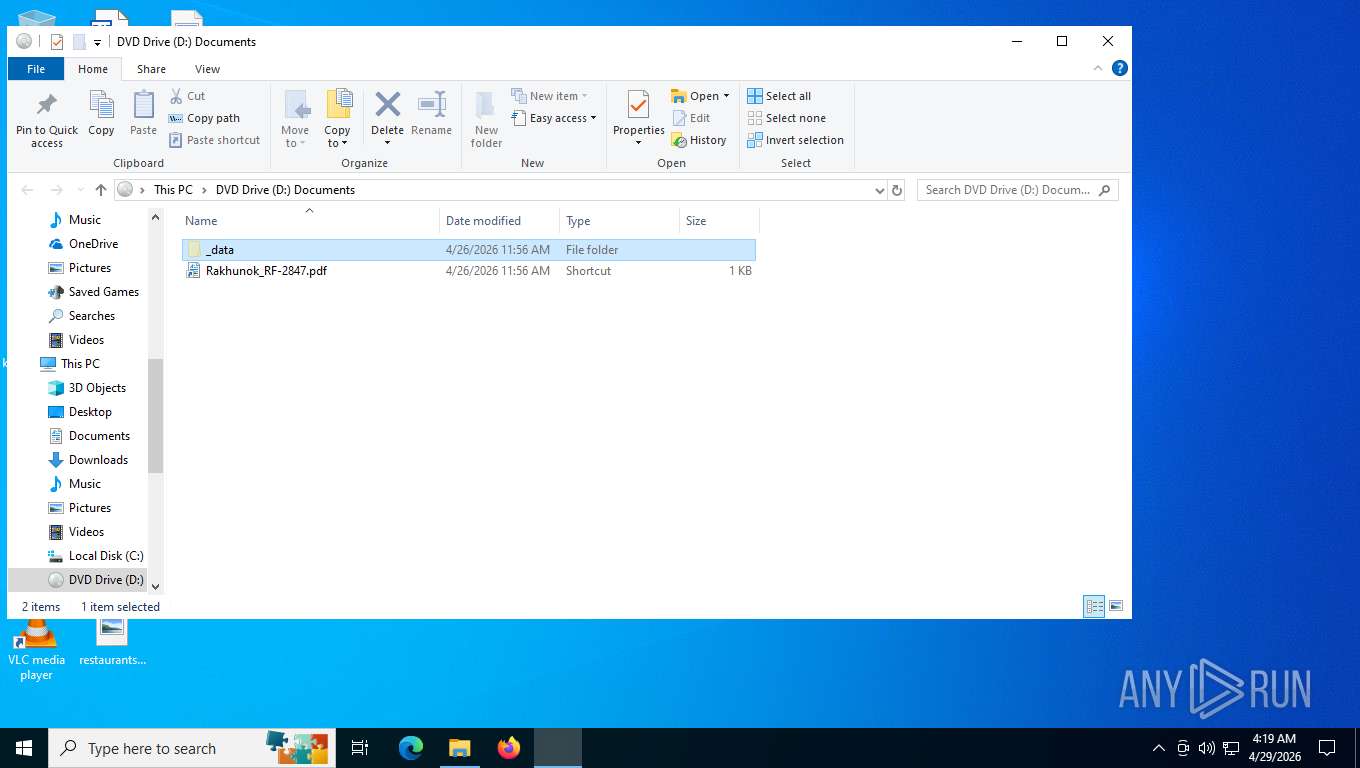
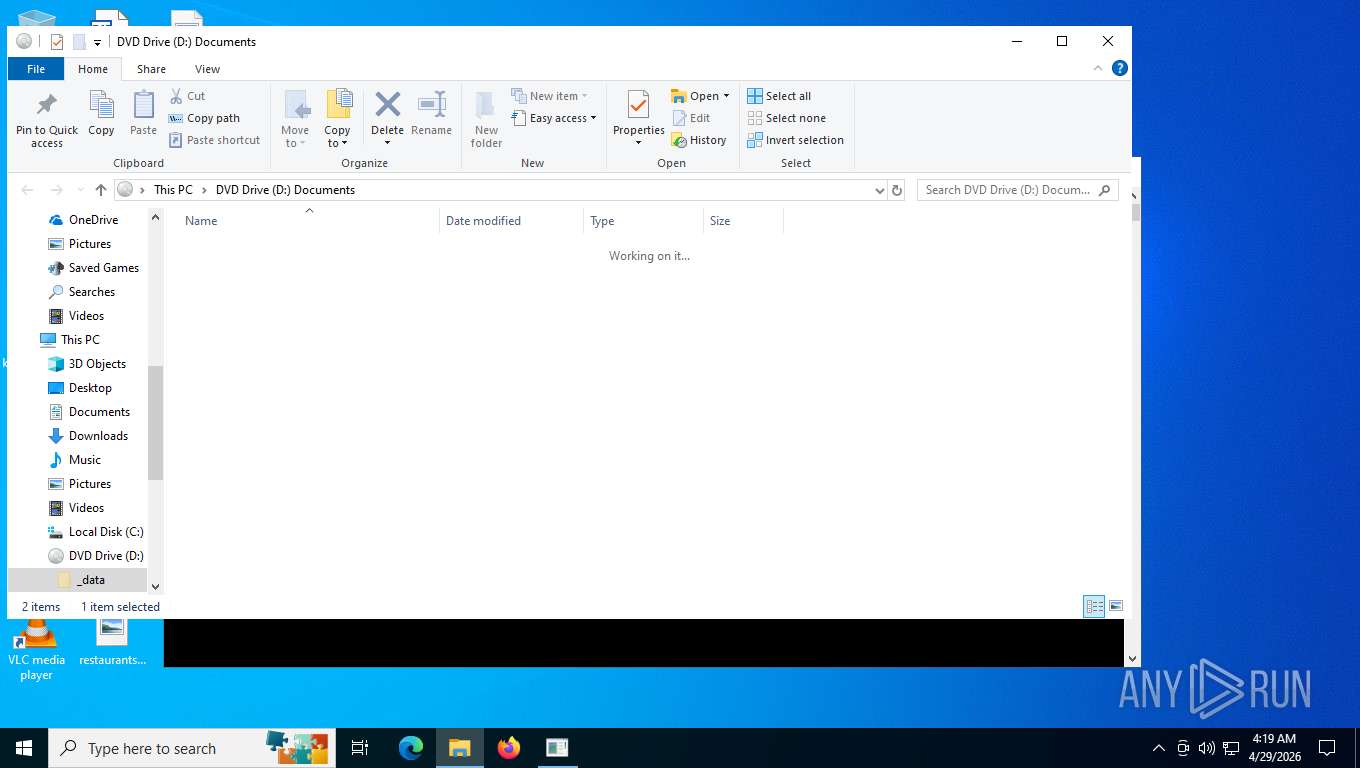
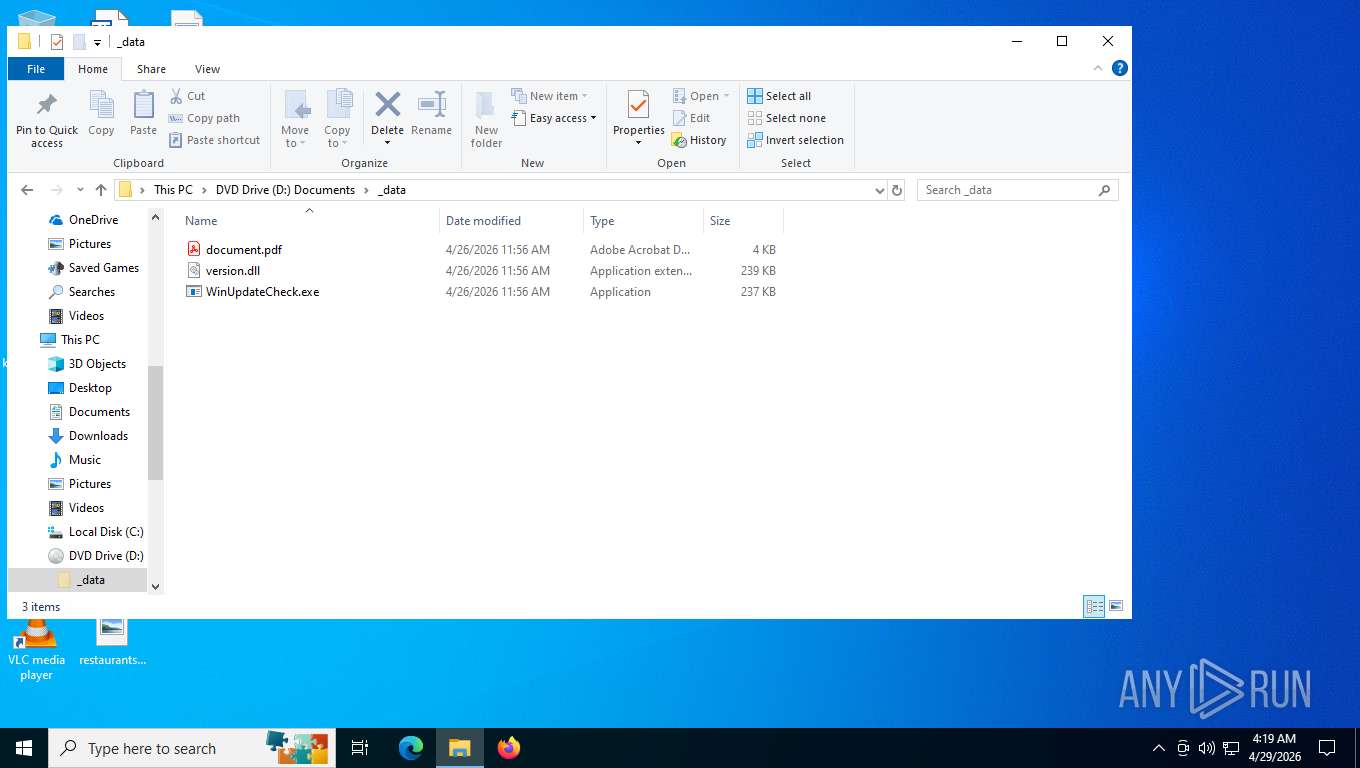
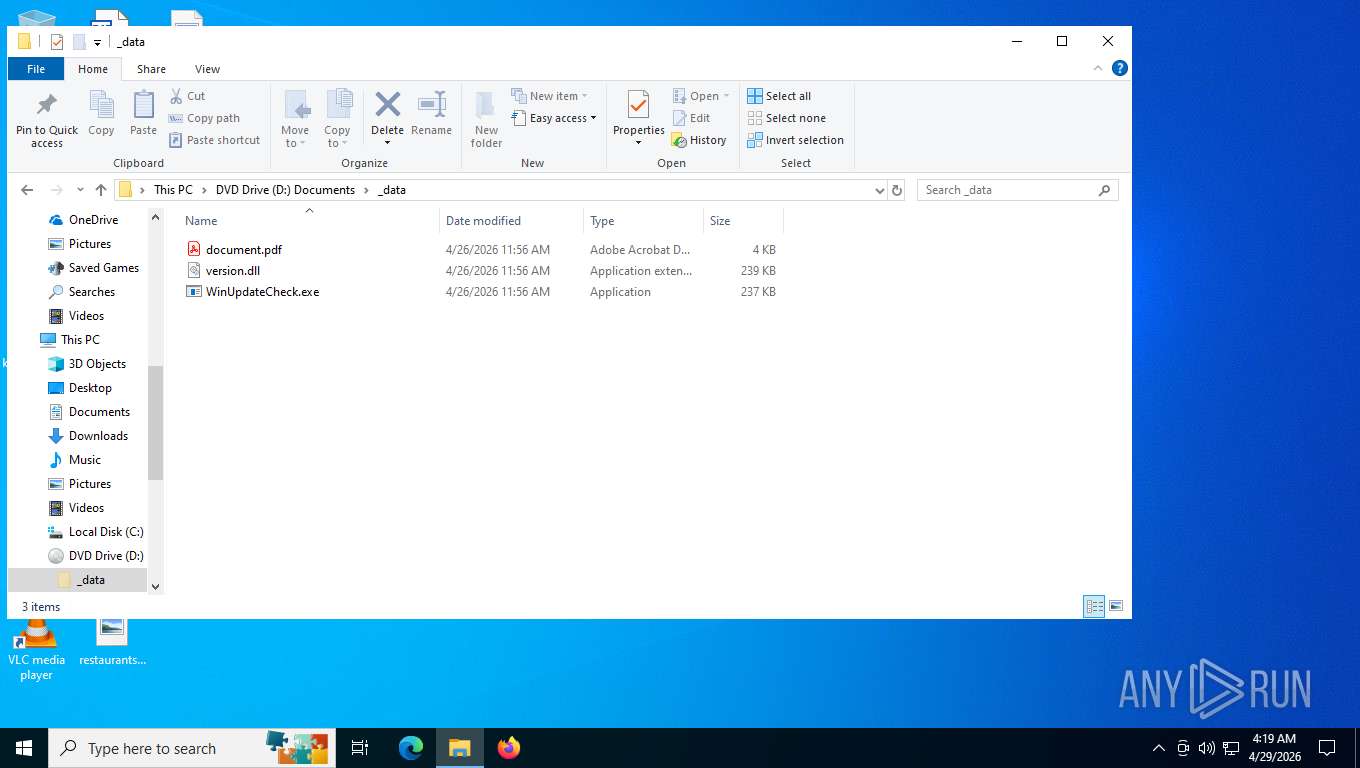
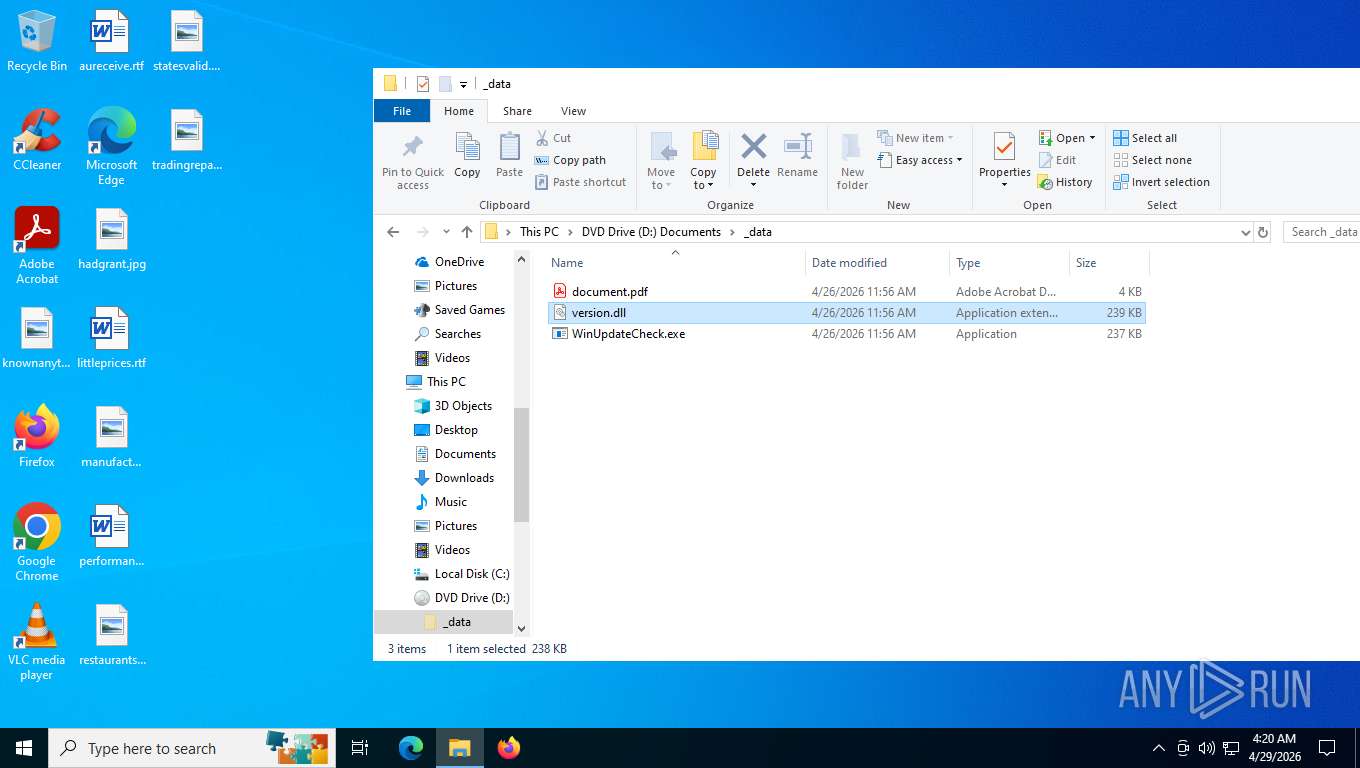
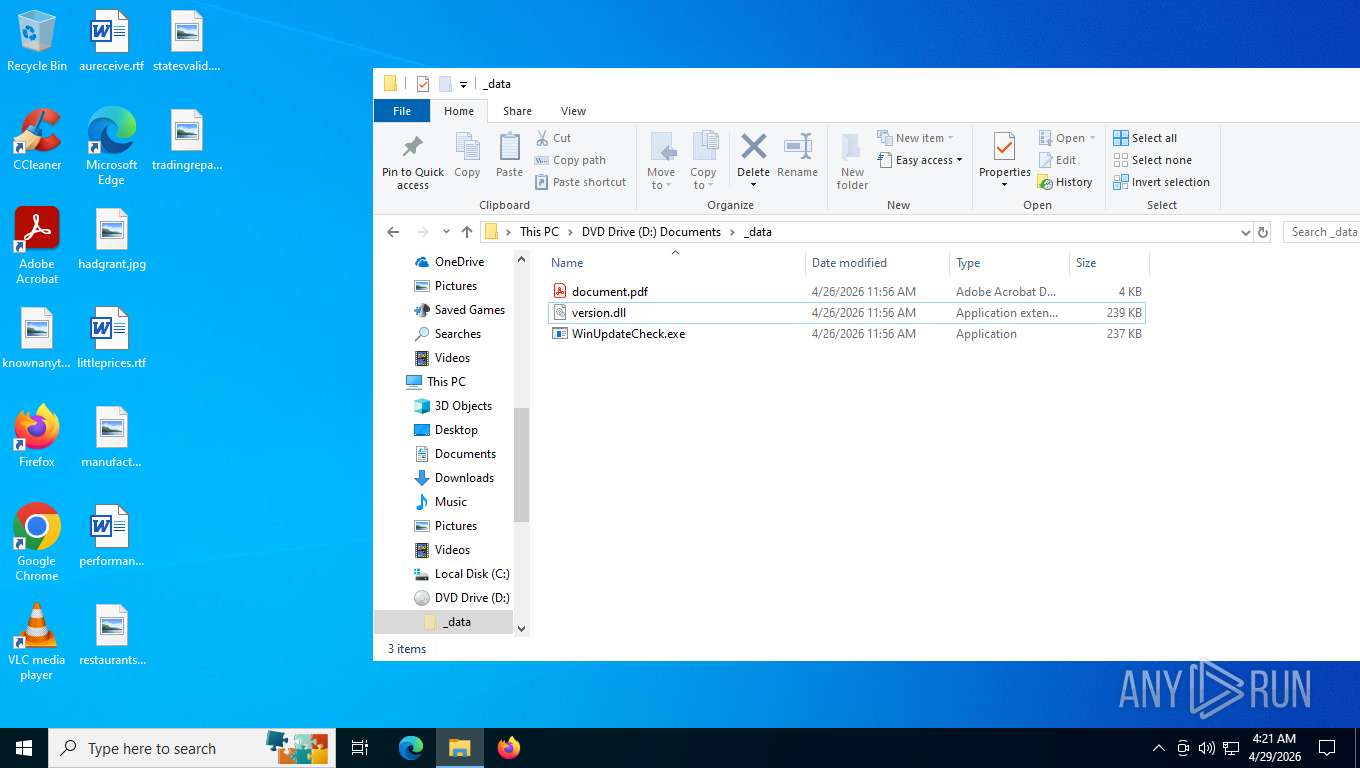
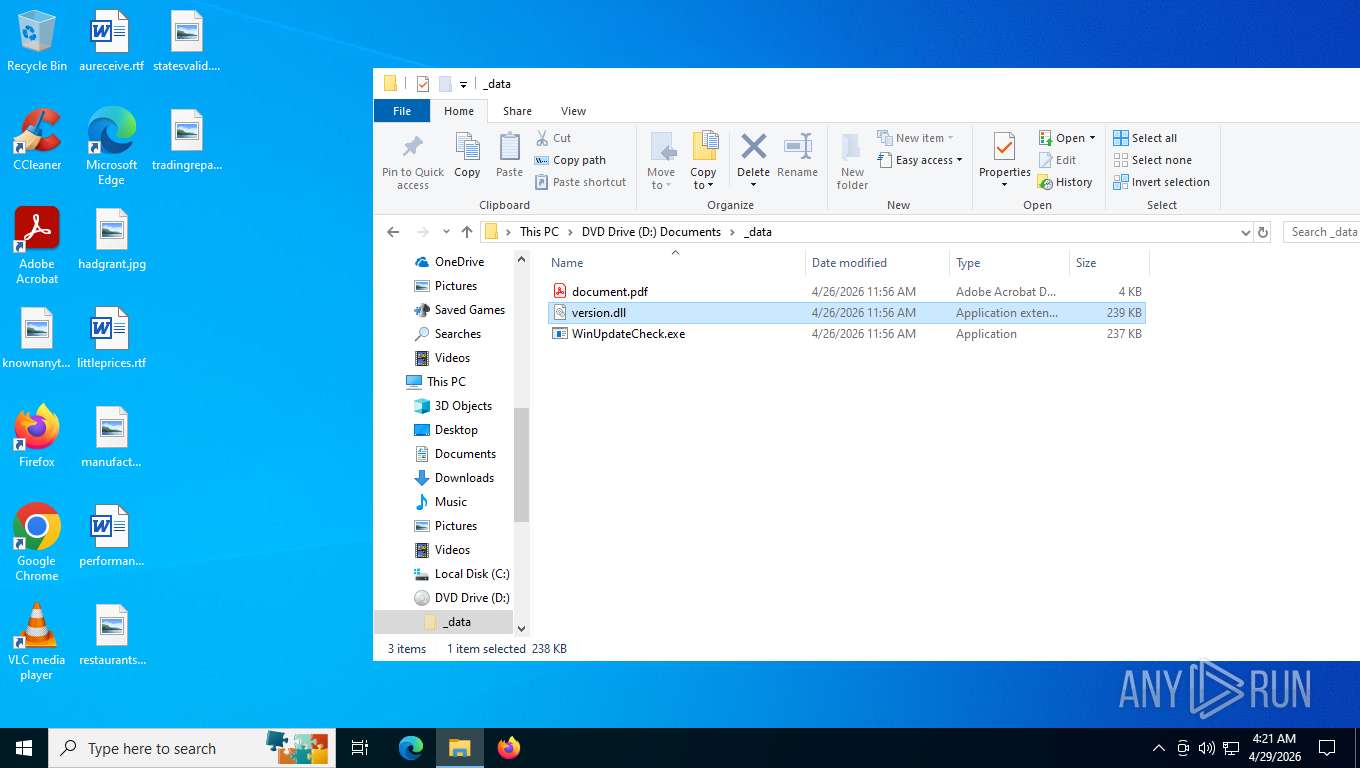
Image mount has been detect
- explorer.exe (PID: 4696)
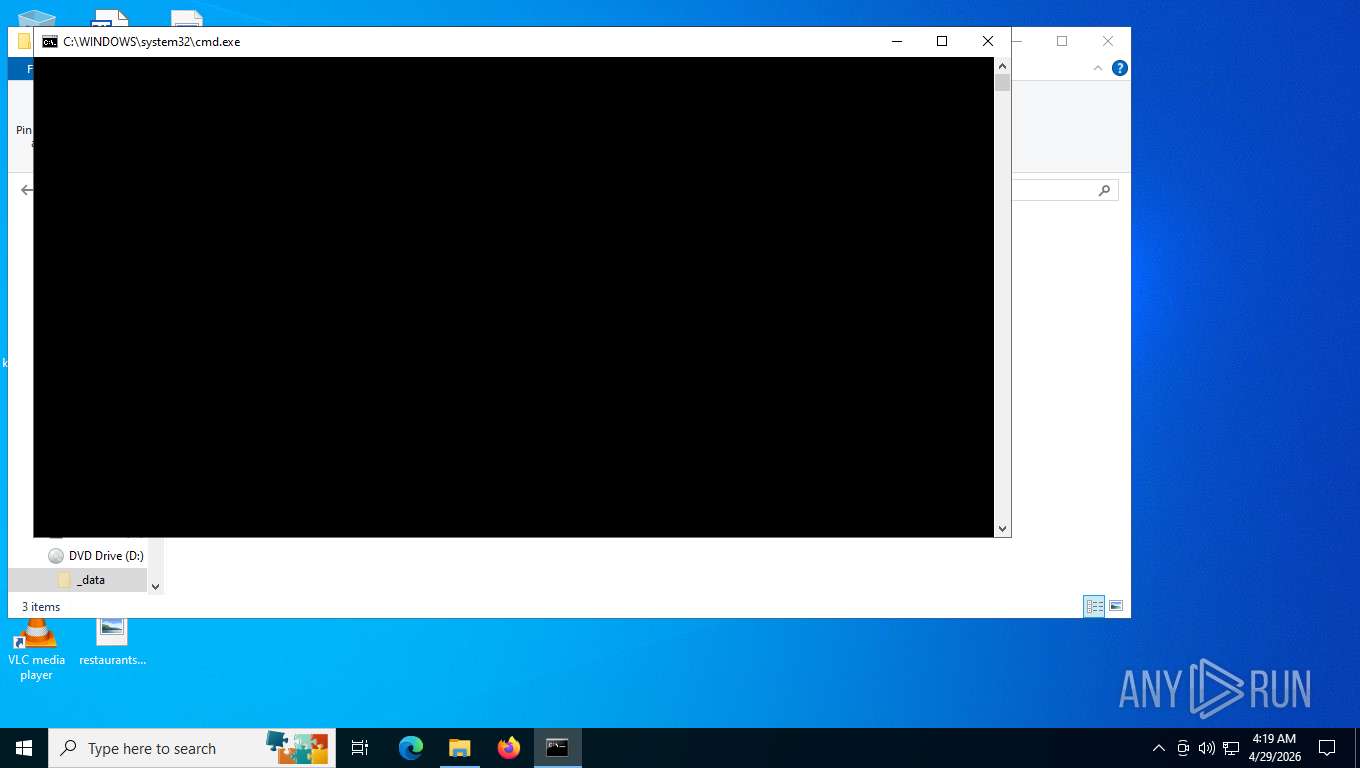
Starts CMD.EXE with AutoRun commands disabled
- cmd.exe (PID: 6672)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6672)
- cmd.exe (PID: 2876)
Loading modules from mounted disk drive
- WinUpdateCheck.exe (PID: 8176)
Uses REG/REGEDIT.EXE to modify or delete registry entries
- WinUpdateCheck.exe (PID: 8176)
There is functionality for VM detection VirtualBox (YARA)
- WinUpdateCheck.exe (PID: 8176)
Uses WMIC.EXE to obtain CPU information
- WinUpdateCheck.exe (PID: 8176)
Uses WMIC.EXE to obtain operating system information
- WinUpdateCheck.exe (PID: 8176)
The process hide an interactive prompt from the user
- WinUpdateCheck.exe (PID: 8176)
Get information on the list of running processes
- WinUpdateCheck.exe (PID: 8176)
Uses WMIC.EXE to obtain physical disk drive information
- WinUpdateCheck.exe (PID: 8176)
Starts POWERSHELL.EXE for commands execution
- WinUpdateCheck.exe (PID: 8176)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 2956)
- schtasks.exe (PID: 1728)
- schtasks.exe (PID: 3508)
- schtasks.exe (PID: 2456)
Executable content was dropped or overwritten
- WinUpdateCheck.exe (PID: 8176)
The process bypasses the loading of PowerShell profile settings
- WinUpdateCheck.exe (PID: 8176)
Checks for external IP
- svchost.exe (PID: 2232)
Lists all scheduled tasks
- schtasks.exe (PID: 996)
- schtasks.exe (PID: 2828)
Uses DRIVERQUERY.EXE to obtain a list of installed device drivers
- cmd.exe (PID: 2876)
Creates scheduled task with ONLOGON parameter
- WinUpdateCheck.exe (PID: 8176)
Creates scheduled task with highest privileges
- schtasks.exe (PID: 7560)
- schtasks.exe (PID: 8060)
- schtasks.exe (PID: 2136)
- schtasks.exe (PID: 7880)
INFO
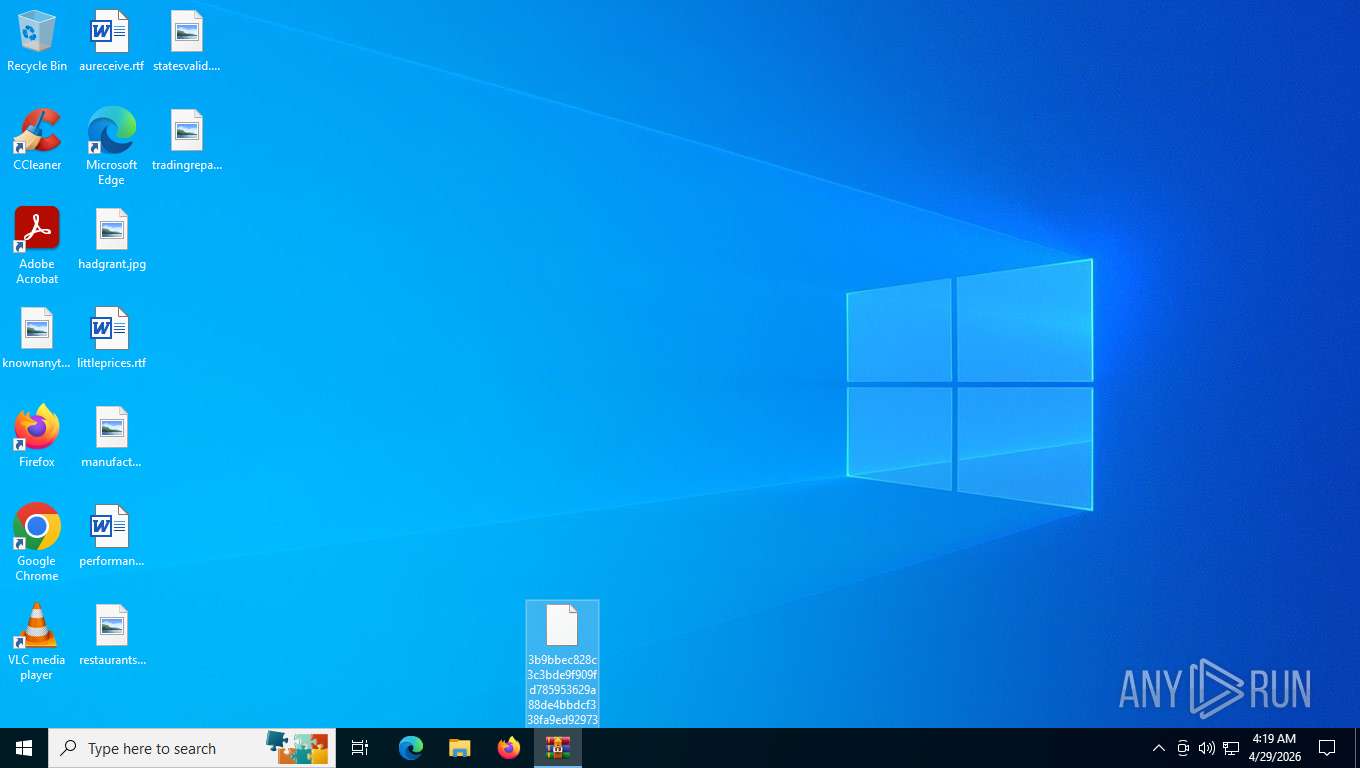
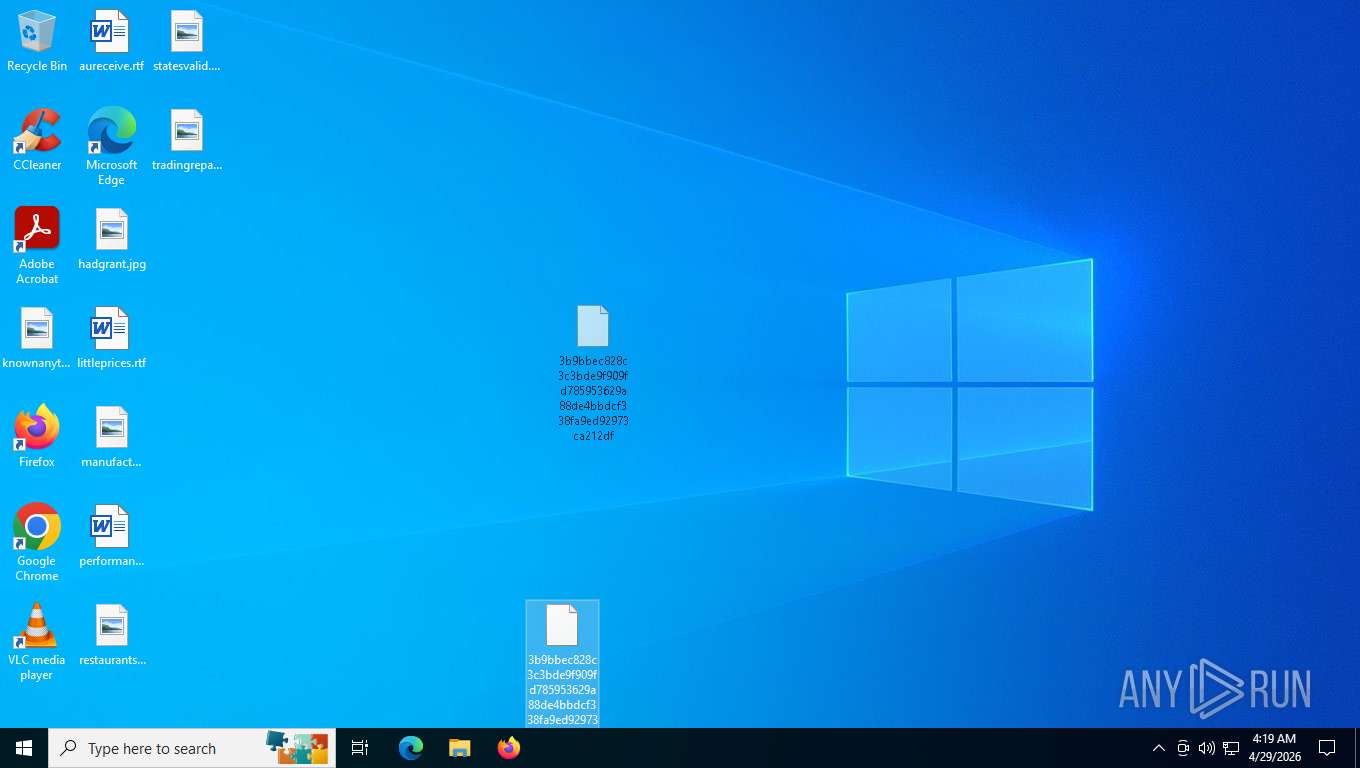
Manual execution by a user
- cmd.exe (PID: 6672)
Reads security settings of Internet Explorer
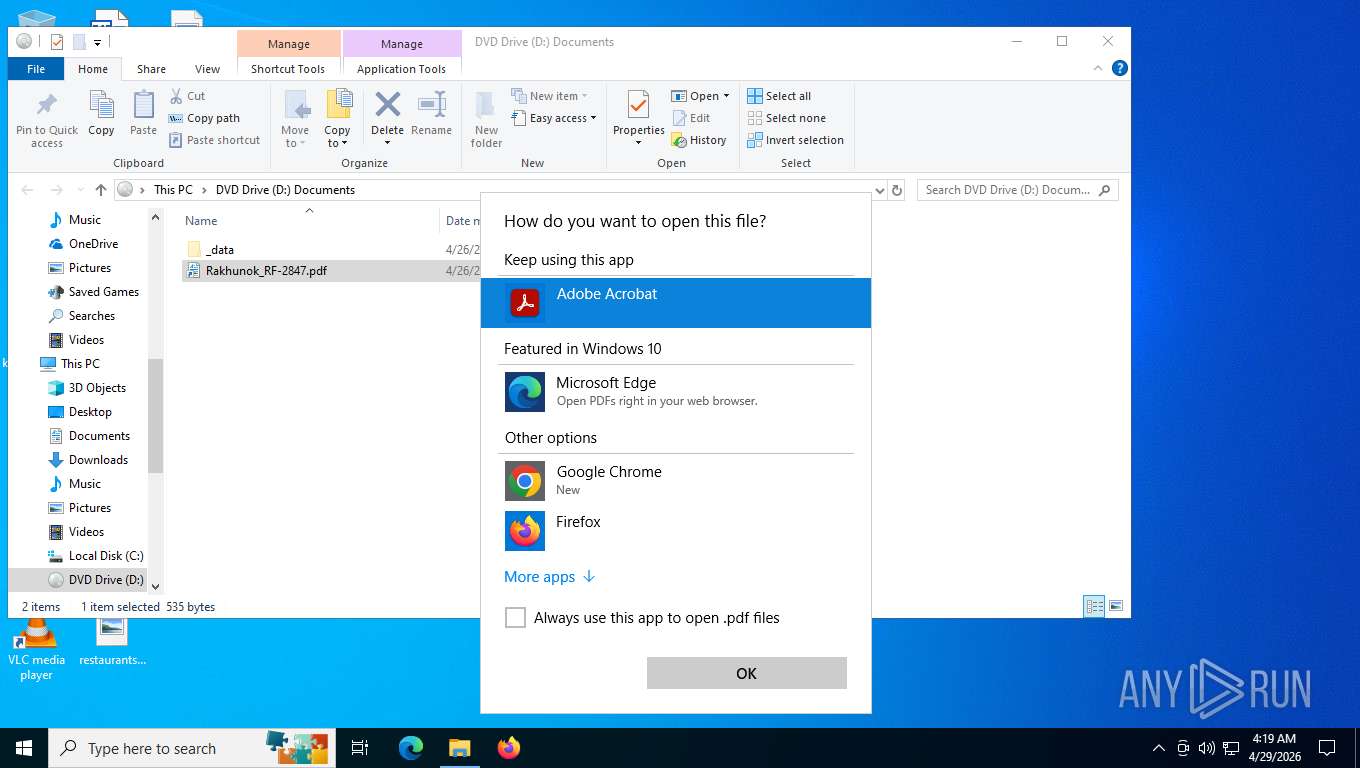
- explorer.exe (PID: 4696)
- OpenWith.exe (PID: 2812)
- WinUpdateCheck.exe (PID: 8176)
- WMIC.exe (PID: 6236)
- WMIC.exe (PID: 6212)
- WMIC.exe (PID: 5704)
Reads Microsoft Office registry keys
- explorer.exe (PID: 4696)
- OpenWith.exe (PID: 2812)
Checks supported languages
- WinUpdateCheck.exe (PID: 8176)
Application launched itself
- Acrobat.exe (PID: 6104)
- AcroCEF.exe (PID: 2420)
Reads the computer name
- WinUpdateCheck.exe (PID: 8176)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 7216)
Creates files or folders in the user directory
- WinUpdateCheck.exe (PID: 8176)
Launching a file from a Registry key
- WinUpdateCheck.exe (PID: 8176)
The sample compiled with english language support
- WinUpdateCheck.exe (PID: 8176)
Attempting to connect via WebSocket
- WinUpdateCheck.exe (PID: 8176)
Launching a file from Task Scheduler
- WinUpdateCheck.exe (PID: 8176)
Launching a file from the Startup directory
- WinUpdateCheck.exe (PID: 8176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x4dd8ccc8 |
| ZipCompressedSize: | 259822 |
| ZipUncompressedSize: | 870400 |
| ZipFileName: | 3b9bbec828c3c3bde9f909fd785953629a88de4bbdcf338fa9ed92973ca212df |
Total processes
199
Monitored processes
61
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 996 | "schtasks" /query /tn MicrosoftEdgeUpdateService | C:\Windows\System32\schtasks.exe | — | WinUpdateCheck.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1728 | "schtasks" /delete /tn MicrosoftEdgeUpdateService /f | C:\Windows\System32\schtasks.exe | — | WinUpdateCheck.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2016 | "reg" query HKLM\HARDWARE\ACPI\DSDT\VBOX__ | C:\Windows\System32\reg.exe | — | WinUpdateCheck.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | "schtasks" /create /tn MicrosoftEdgeUpdateService /tr "wscript.exe \"C:\Users\admin\AppData\Roaming\Microsoft\Windows\SystemUpdate\svc.vbs\"" /sc ONLOGON /ru SYSTEM /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WinUpdateCheck.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2220 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2232 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --backgroundcolor=16514043 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | Acrobat.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=gpu-process --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=1552 --field-trial-handle=1612,i,15353555865168877141,8960233346987097472,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:2 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 2456 | "schtasks" /delete /tn MicrosoftEdgeUpdateService /f | C:\Windows\System32\schtasks.exe | — | WinUpdateCheck.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
32 017
Read events
31 676
Write events
309
Delete events
32
Modification events
| (PID) Process: | (4696) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000000000000000000000 | |||
| (PID) Process: | (4696) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:000000000006041C |
| Operation: | write | Name: | VirtualDesktop |
Value: 100000003030445602603FA5B72DE44882A417B3949BF781 | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\24993069237.zip | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4692) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
55
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8176 | WinUpdateCheck.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\stage[1] | — | |
MD5:— | SHA256:— | |||
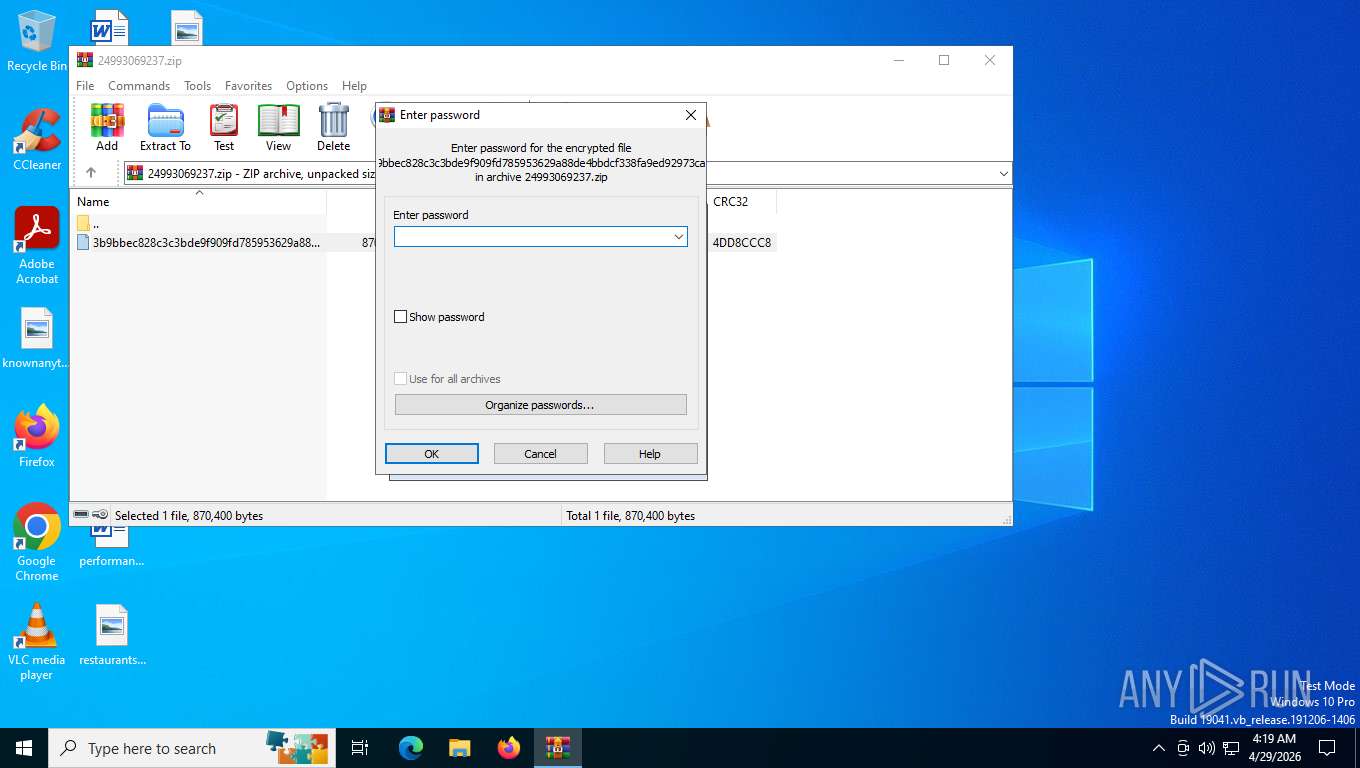
| 4692 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb4692.39583\3b9bbec828c3c3bde9f909fd785953629a88de4bbdcf338fa9ed92973ca212df | compressed | |
MD5:B1A512ED7EEEDE9EB4A6B71F39BC82AB | SHA256:3B9BBEC828C3C3BDE9F909FD785953629A88DE4BBDCF338FA9ED92973CA212DF | |||
| 4696 | explorer.exe | C:\Users\admin\Desktop\3b9bbec828c3c3bde9f909fd785953629a88de4bbdcf338fa9ed92973ca212df | compressed | |
MD5:B1A512ED7EEEDE9EB4A6B71F39BC82AB | SHA256:3B9BBEC828C3C3BDE9F909FD785953629A88DE4BBDCF338FA9ED92973CA212DF | |||
| 4696 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | text | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 4696 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\f01b4d95cf55d32a.automaticDestinations-ms | binary | |
MD5:6C760093E1F98AAFAE6648A3A374234E | SHA256:87D255355BADD1300391A635D26911DF985E7D07B1D52B1465D6A8555E6CAC51 | |||
| 7508 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\Cache\AdobeFnt23.lst.7508 | binary | |
MD5:B7BB33BA2D063FE57B6C3EAA7E7ADF70 | SHA256:298999CAAA697082B5FD80903B1966482F211C921AB1FF74BB239C0DB3337022 | |||
| 7508 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeFnt23.lst.7508 | binary | |
MD5:366B140BAFC863B7E366AA1E51604759 | SHA256:CBC8B288DBD2C72432081CF33CEF431572A94C7FB89DBCD59973B99E3871814E | |||
| 7508 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SharedDataEvents-journal | binary | |
MD5:F9B012E8C0C07A29A5923915E1511D8F | SHA256:DCBAD8791FC46F7D003C91665FF1D3AA0A3B2CD8615A654074C9E225F9057573 | |||
| 2420 | AcroCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Session Storage\LOG.old | text | |
MD5:EB1590F2607E1CE46DBF6A521F772EA0 | SHA256:4355D9A8A115BA4E41178B456A8A5578846EB1F7EC9509249C2405F758F31731 | |||
| 7508 | Acrobat.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Acrobat\SOPHIA.json | text | |
MD5:837C1211E392A24D64C670DC10E8DA1B | SHA256:8013AC030684B86D754BBFBAB8A9CEC20CAA4DD9C03022715FF353DC10E14031 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
39
DNS requests
26
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.160.64:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.160.64:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.160.64:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.160.64:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
5316 | svchost.exe | GET | 200 | 23.11.40.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | NL | binary | 471 b | whitelisted |
1132 | SIHClient.exe | GET | 304 | 135.233.95.144:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
1132 | SIHClient.exe | GET | 200 | 20.165.94.54:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
5316 | svchost.exe | POST | 400 | 20.190.160.64:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 204 b | whitelisted |
7268 | svchost.exe | POST | 403 | 88.221.169.205:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | US | html | 386 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6260 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6260 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6260 | svchost.exe | 2.16.164.72:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6260 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8176 | WinUpdateCheck.exe | 185.102.115.84:4000 | — | NEONCORENETWORKS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6260 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
8176 | WinUpdateCheck.exe | Misc activity | INFO [ANY.RUN] USER_AGENTS Suspicious User-Agent (Mozilla/5.0) |
8176 | WinUpdateCheck.exe | Misc activity | HUNTING [ANY.RUN] TCP binary protocol 16-BE data-len prefix on non-standard port inbound |
2232 | svchost.exe | Misc activity | INFO [ANY.RUN] External IP Check (ip-api .com) |
8168 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
2232 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
8176 | WinUpdateCheck.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |