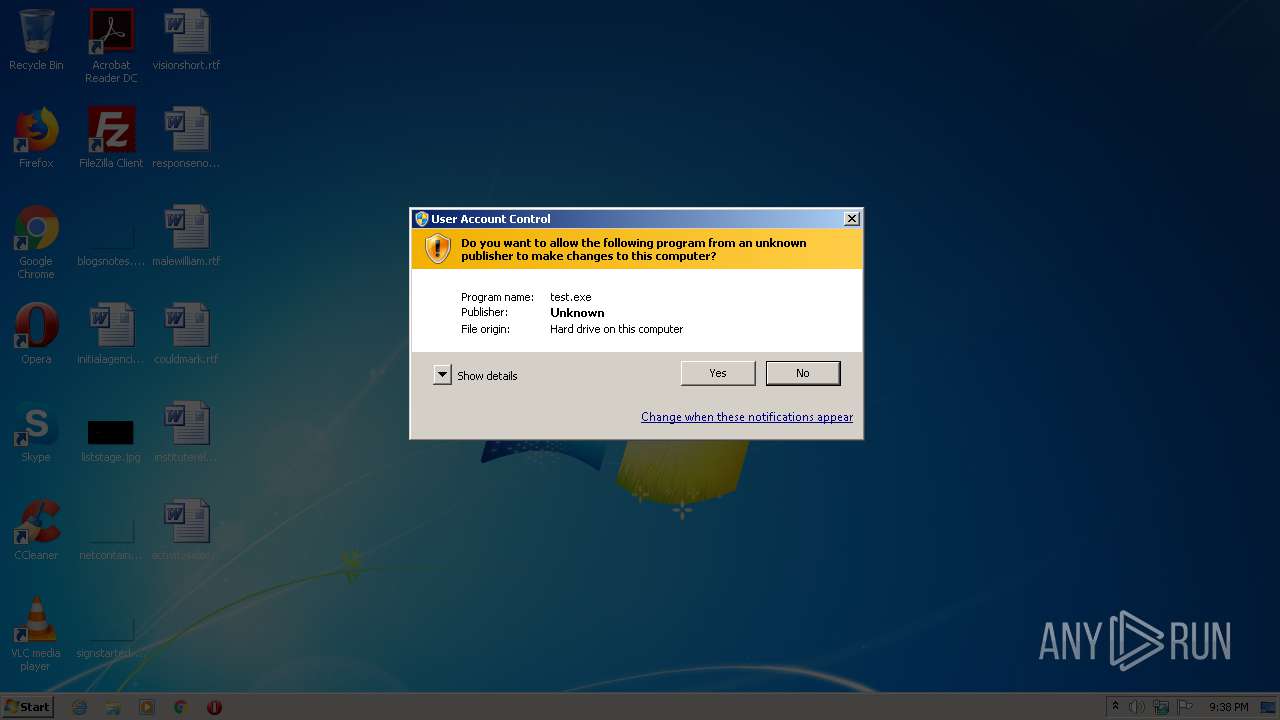
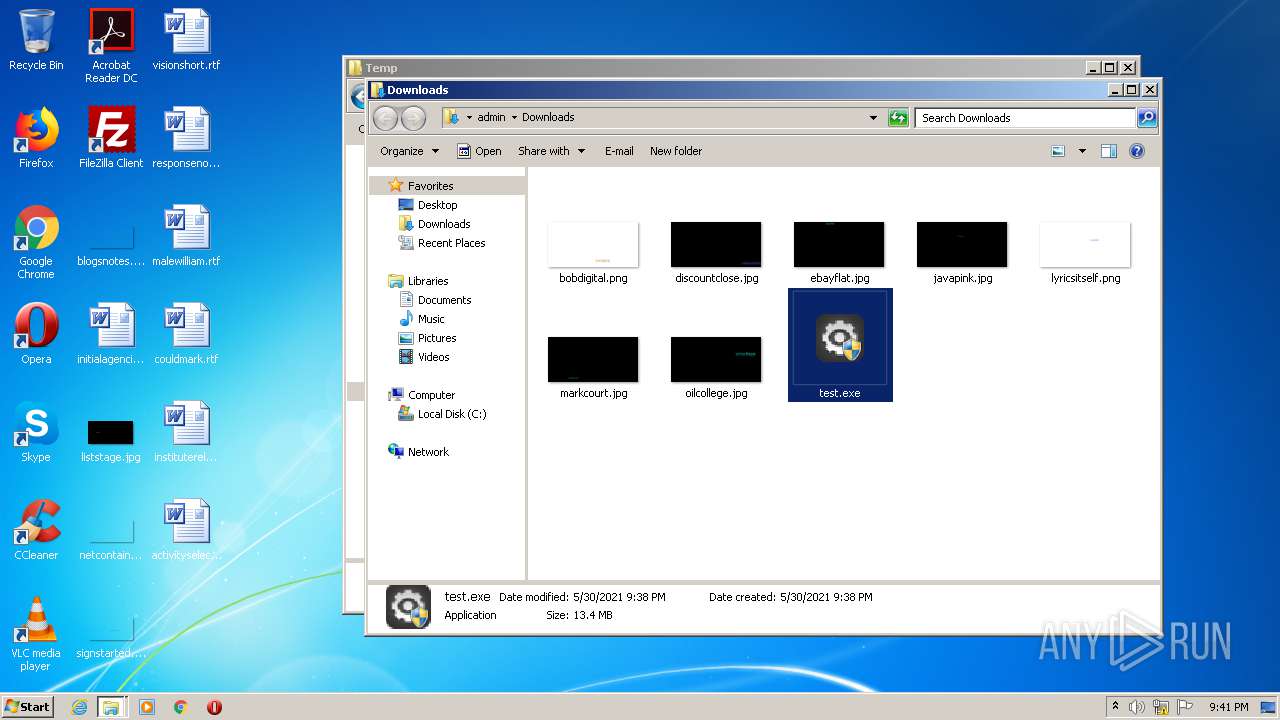
| File name: | test.exe |
| Full analysis: | https://app.any.run/tasks/0ab79c60-729d-4144-9b9d-255806ba5d4f |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2021, 20:38:31 |
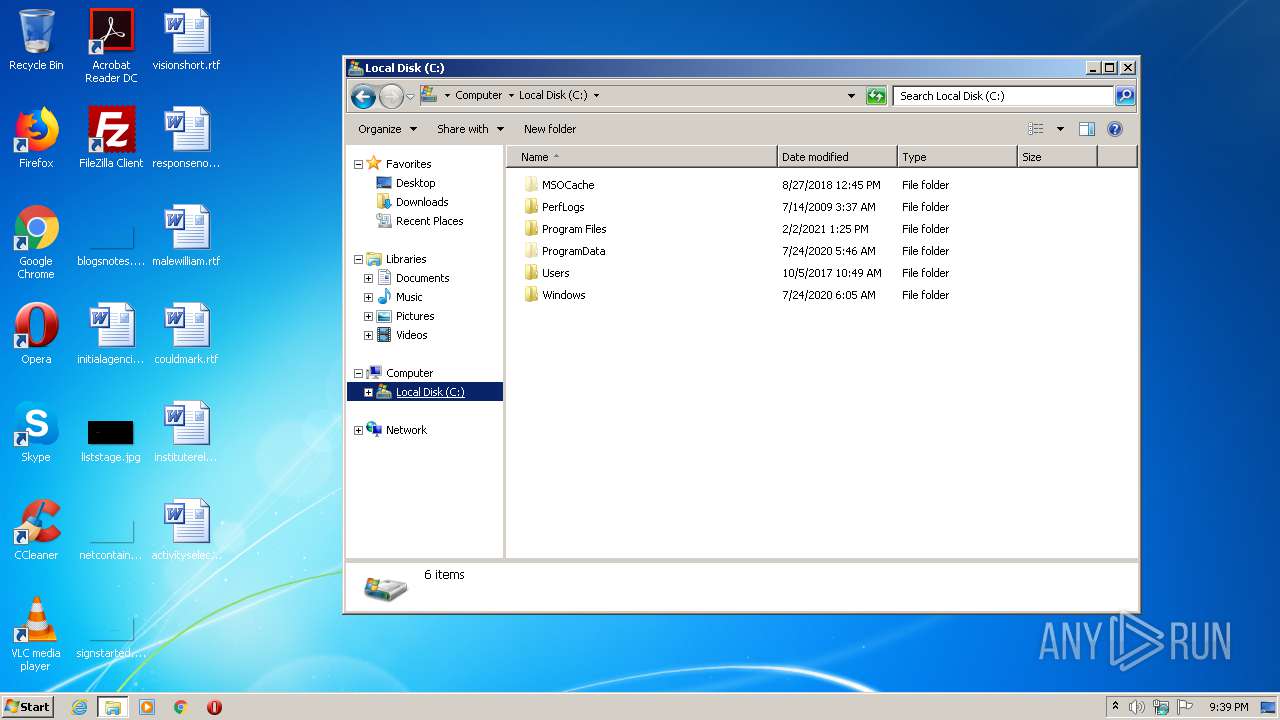
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E53DB7C1DFC7E3D3C463AF1EC7A926A1 |
| SHA1: | 3177897B1294D5B4EAF35FDBC63C93309B501086 |
| SHA256: | C5DF7DAAE8851B39FB57391D18C0A4C4F01ED4F82271E7EAD963158CF358BF73 |
| SSDEEP: | 393216:Jf6fUjUHTV1i1hP6dfQOS3HugyJkE8eyCdaj0:F6soMPoLSXtyeE8TC0j0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
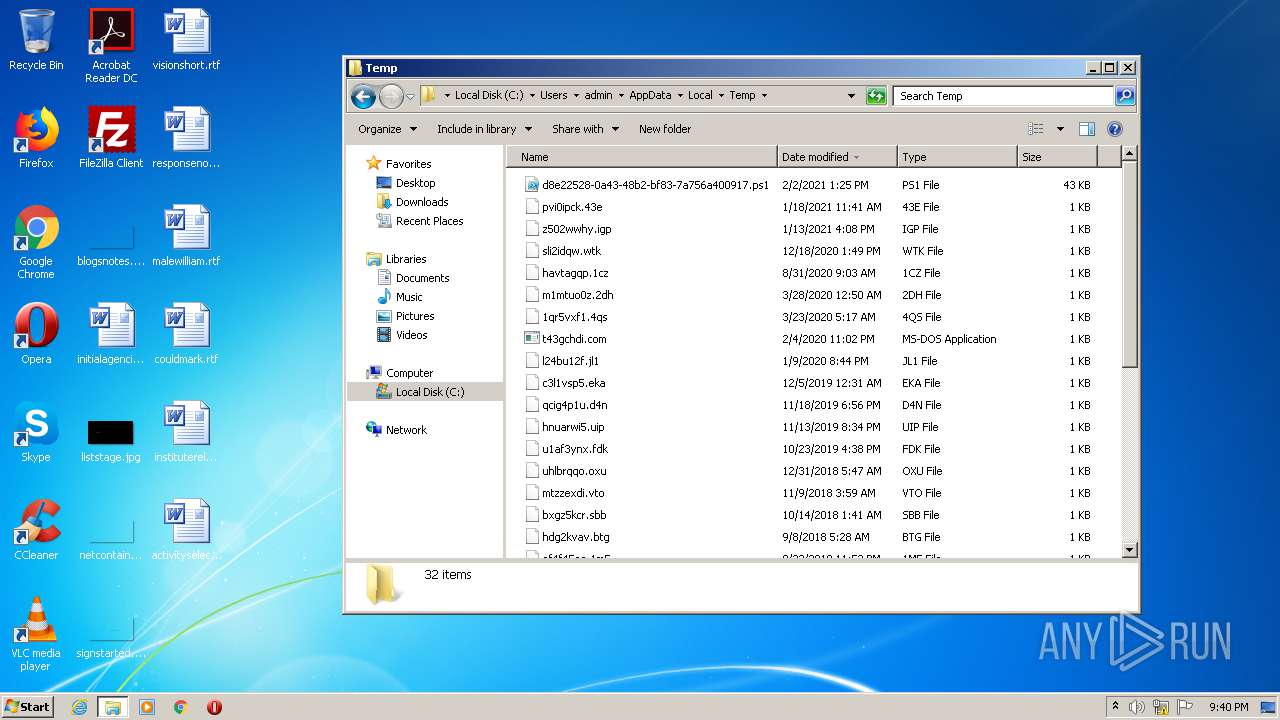
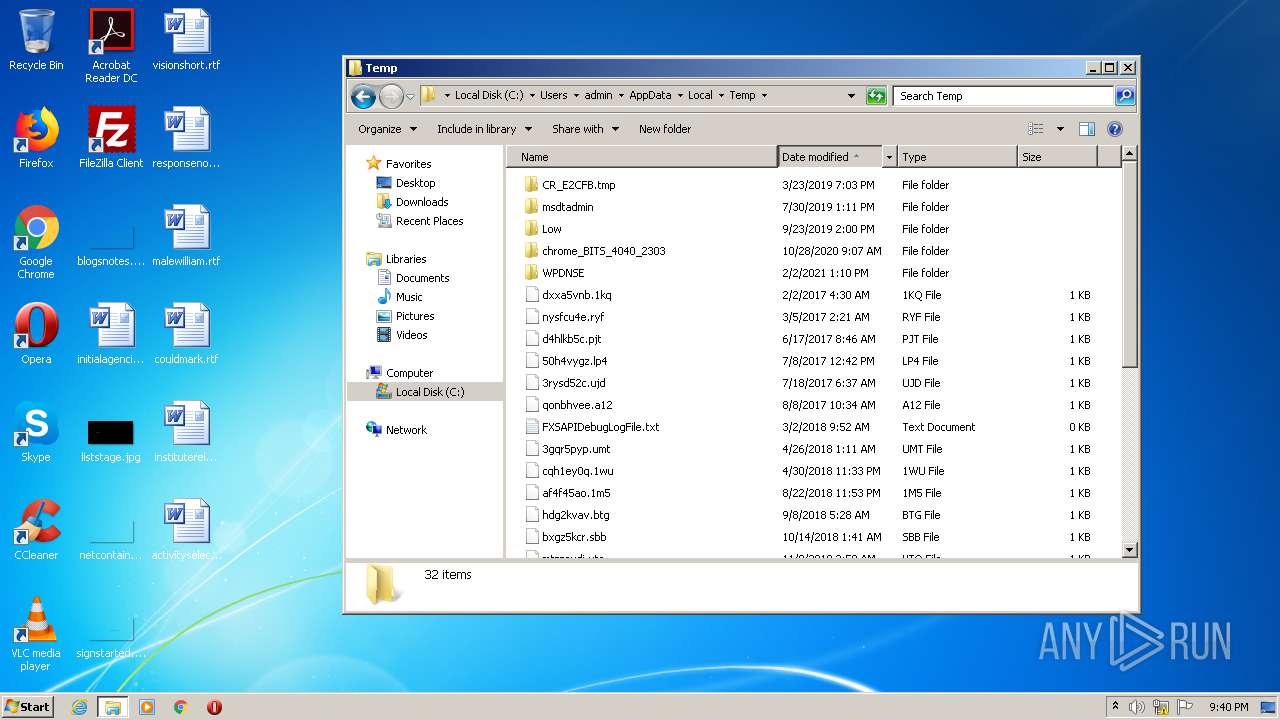
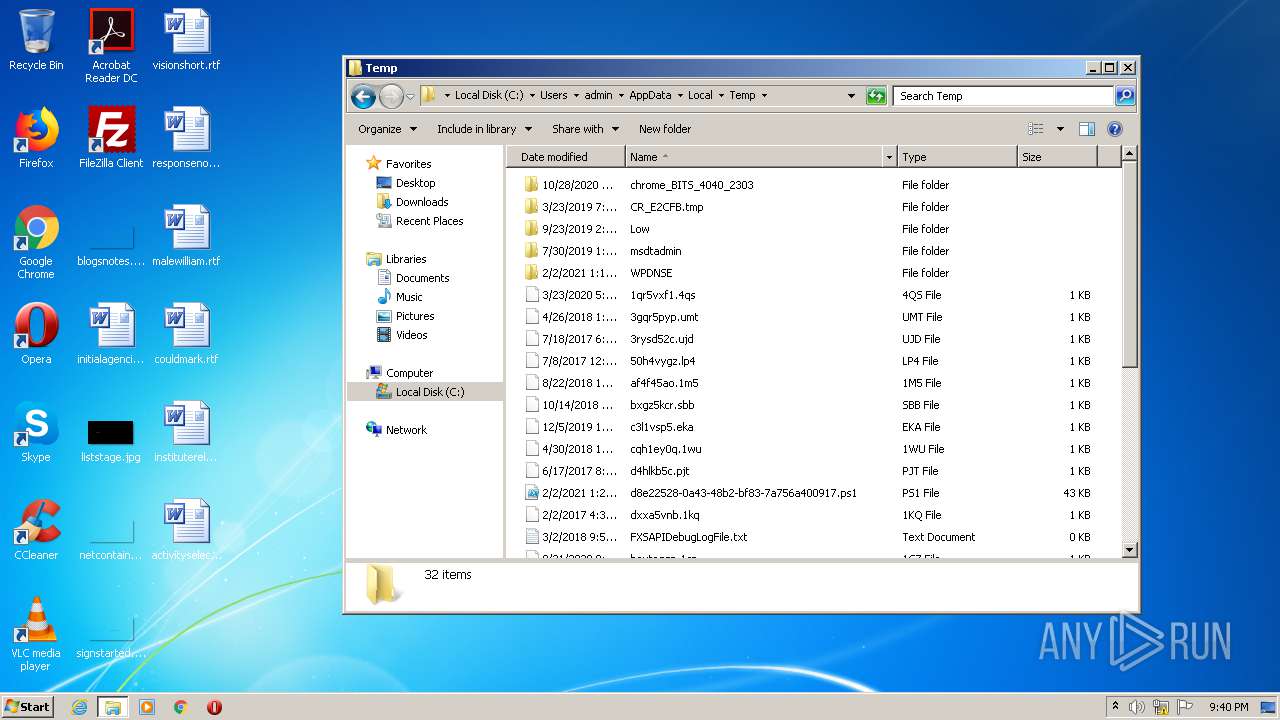
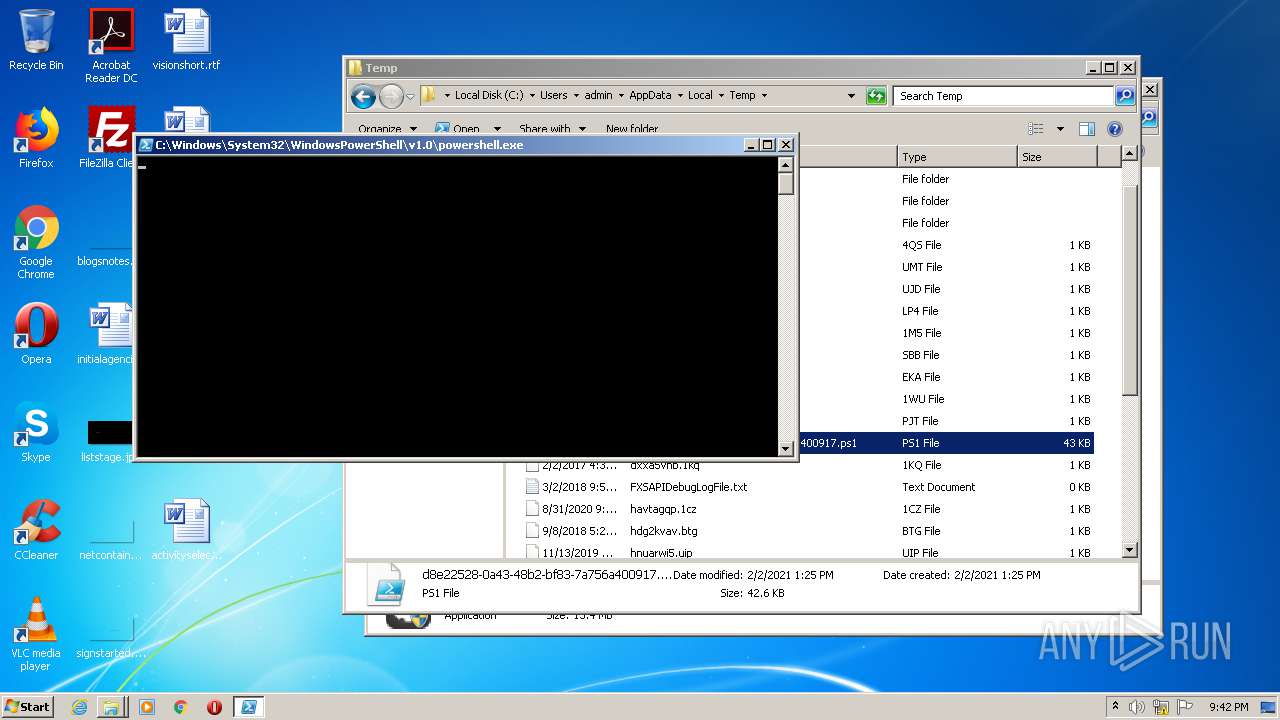
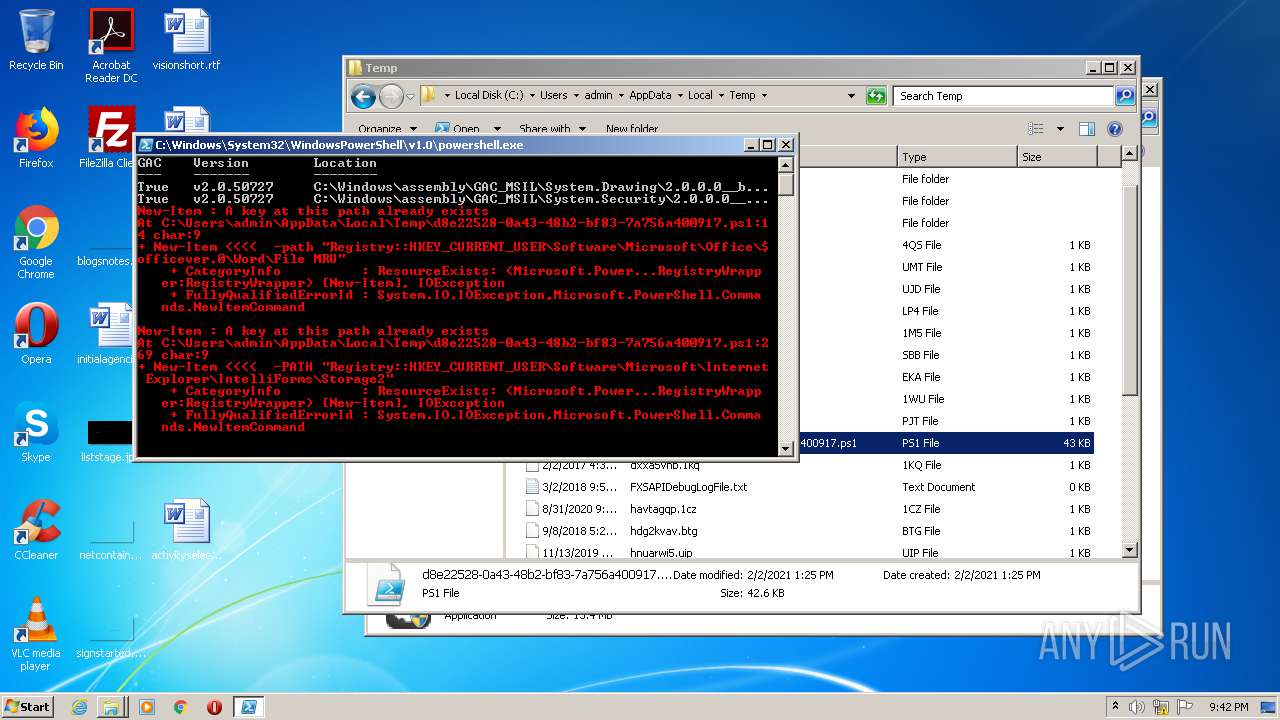
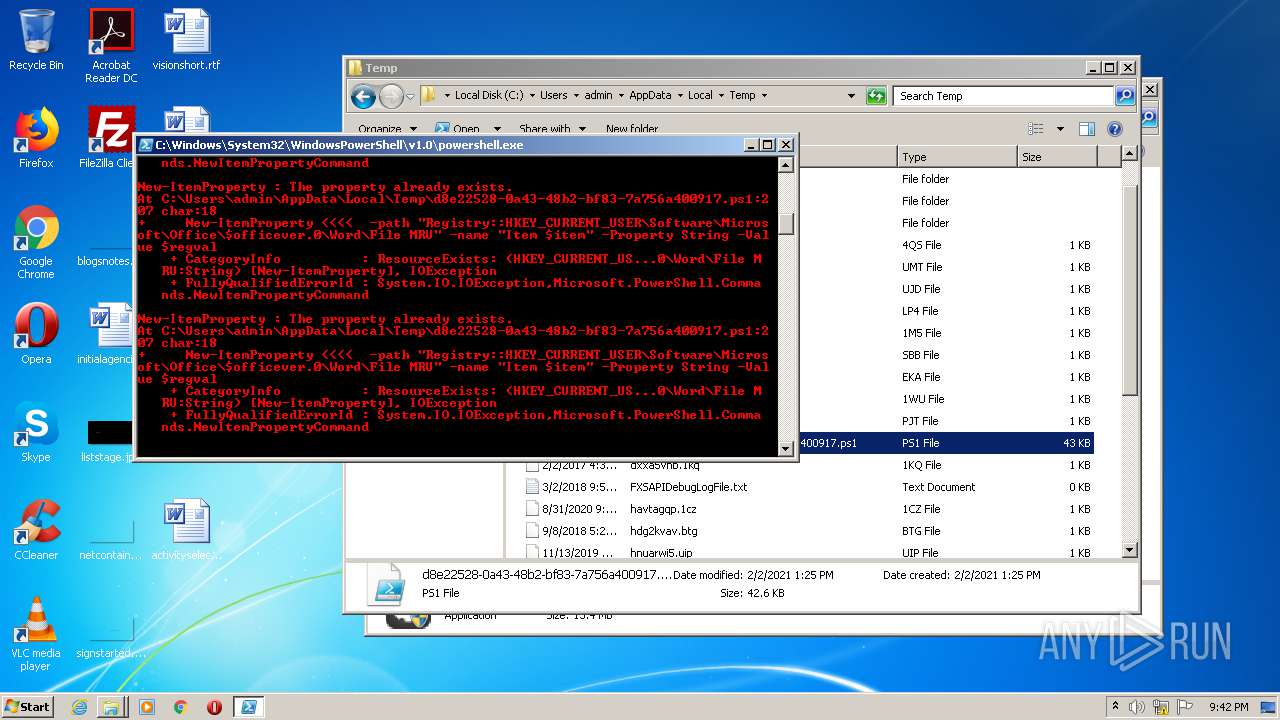
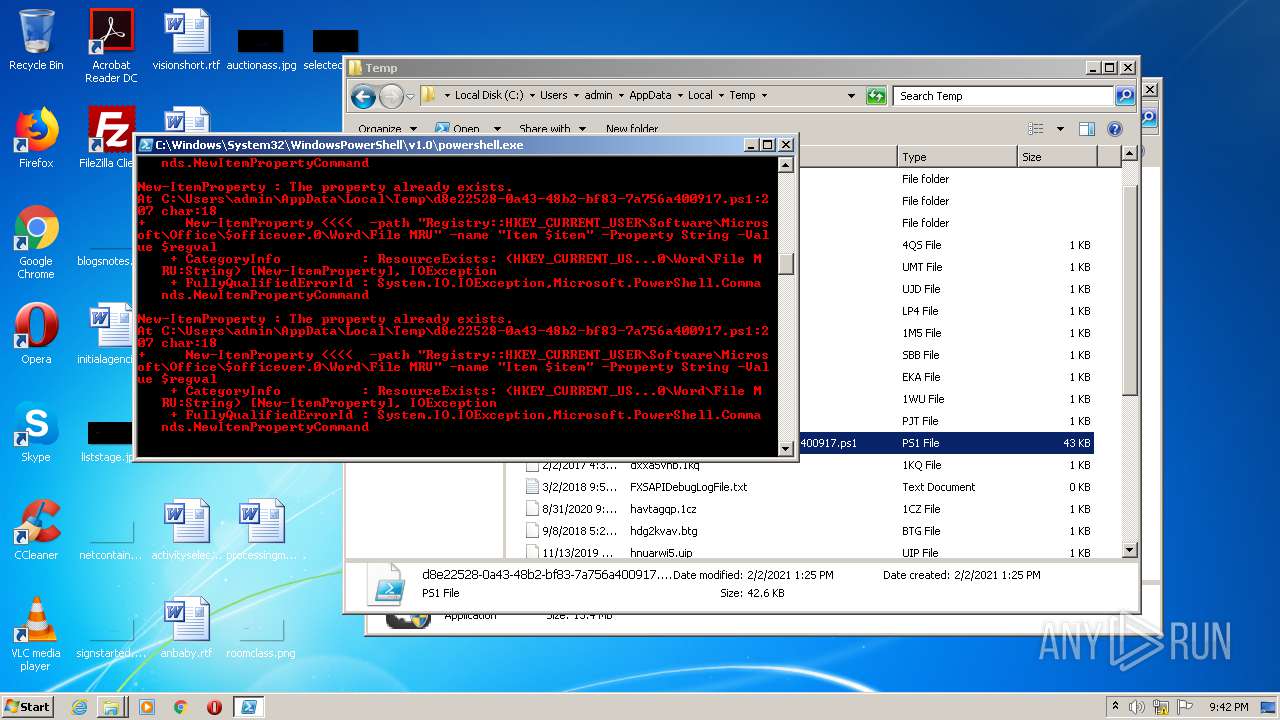
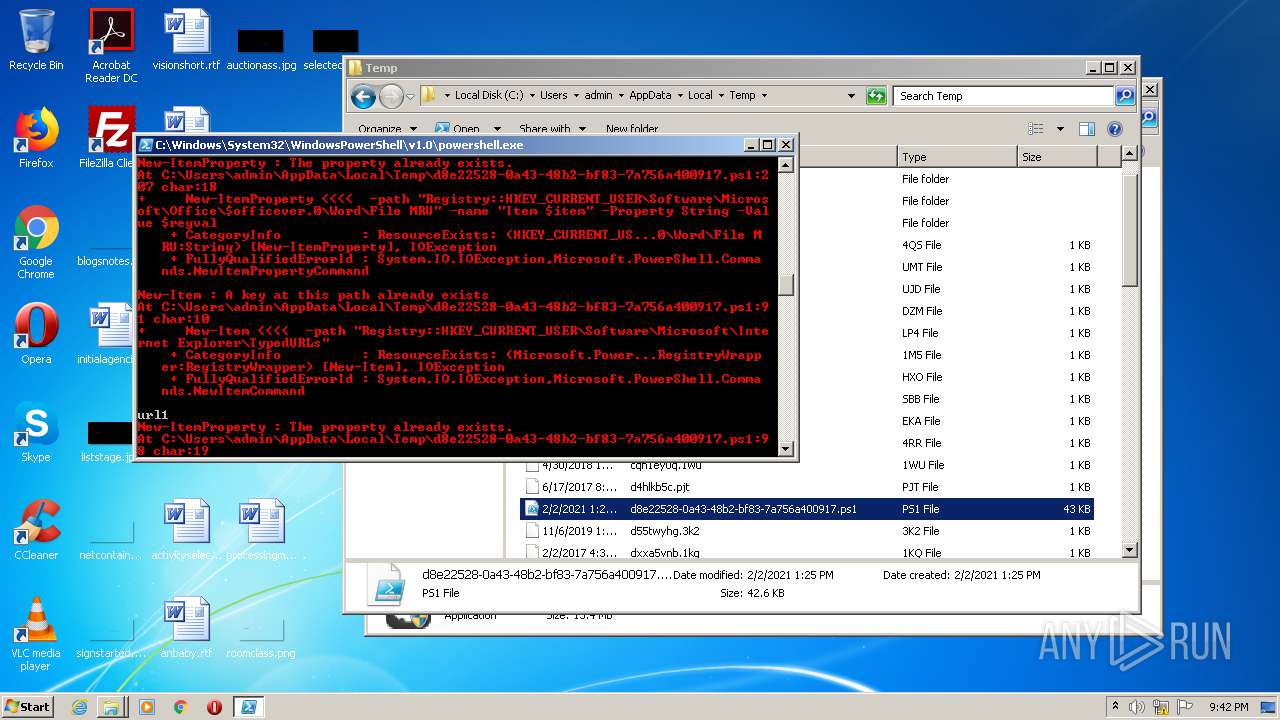
PowerShell script executed
- powershell.exe (PID: 2196)
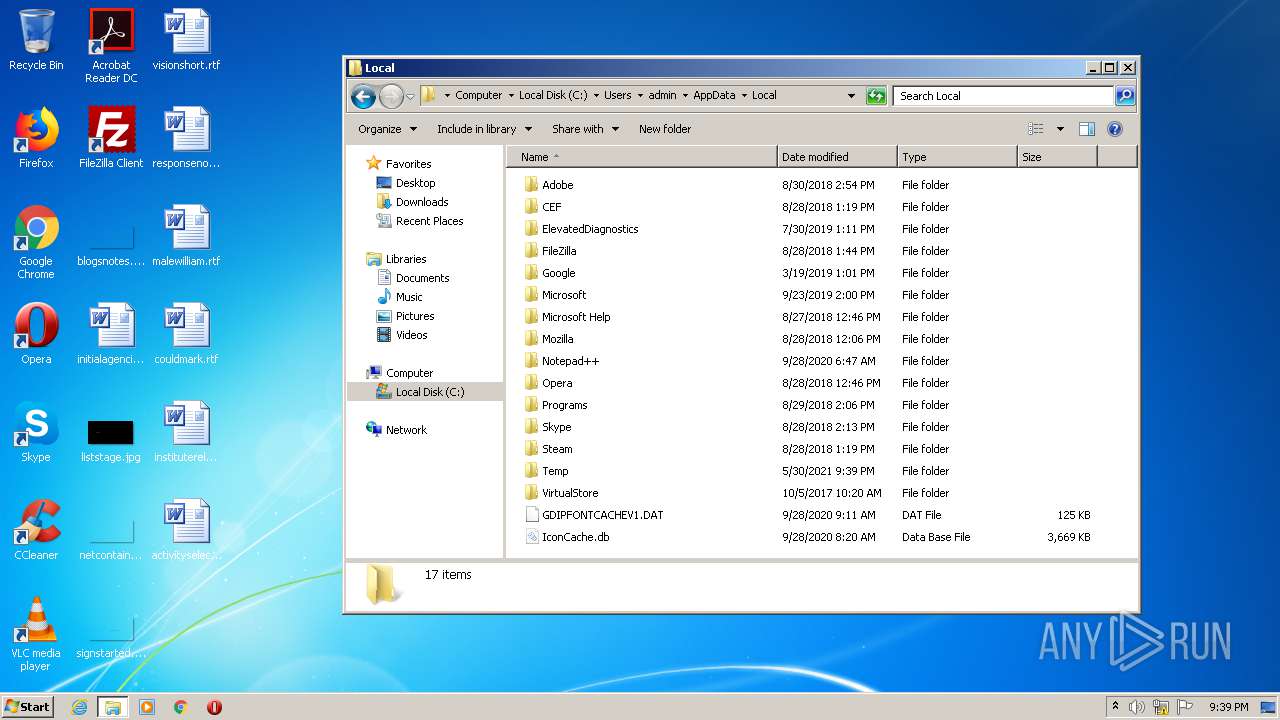
Creates files in the user directory
- powershell.exe (PID: 2196)
INFO
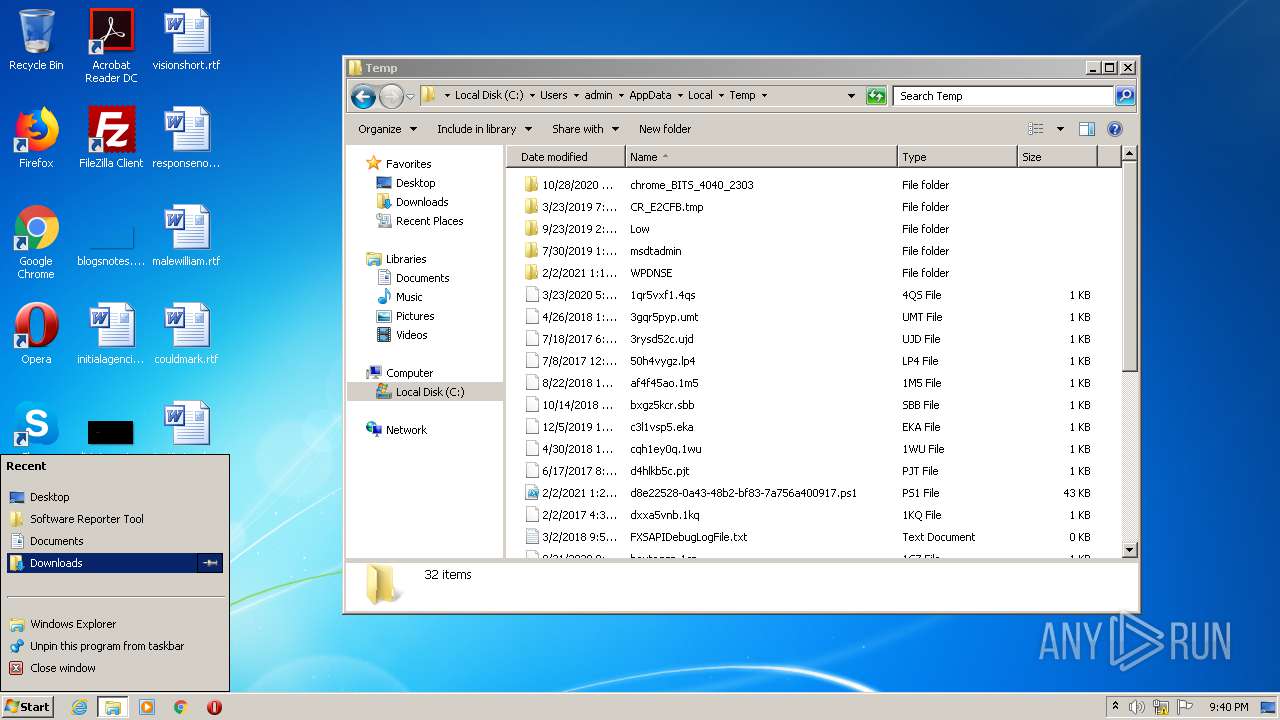
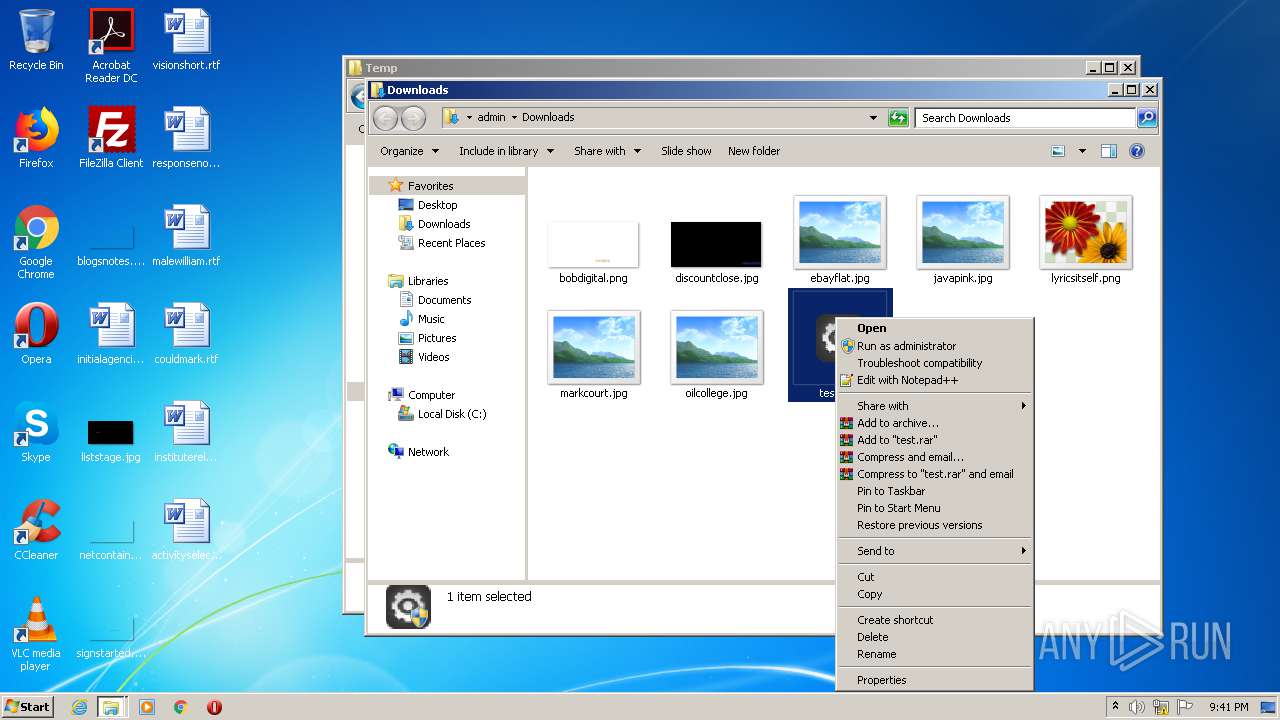
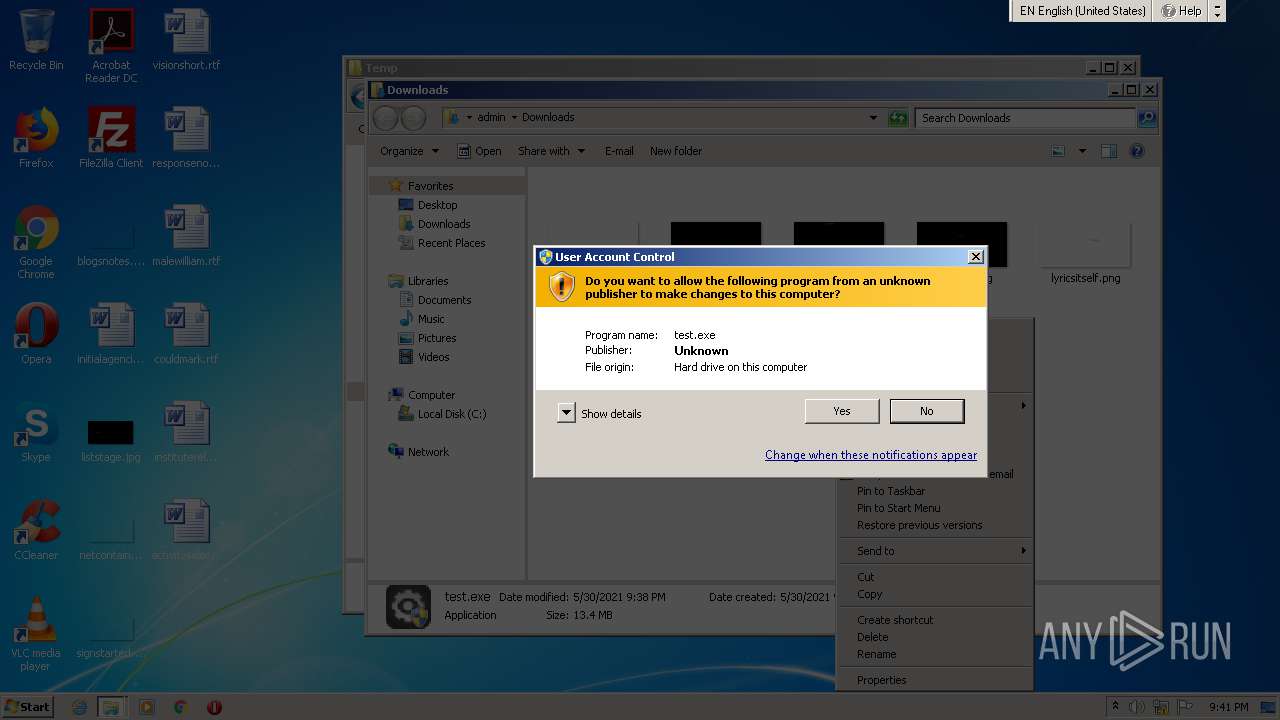
Manual execution by user
- explorer.exe (PID: 2396)
- test.exe (PID: 2760)
- powershell.exe (PID: 2196)
- test.exe (PID: 3312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| FileVersion: | 1.0.2.2 |
|---|---|
| FileDescription: | YDArk |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | Chinese (Simplified) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.0.2.2 |
| FileVersionNumber: | 1.0.2.2 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x3384 |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 118784 |
| CodeSize: | 25088 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2019:12:16 01:50:50+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Dec-2019 00:50:50 |
| Detected languages: |
|
| FileDescription: | YDArk |
| FileVersion: | 1.0.2.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 16-Dec-2019 00:50:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000060E4 | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41884 |
.rdata | 0x00008000 | 0x0000123E | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.03406 |
.data | 0x0000A000 | 0x0001A838 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.21839 |
.ndata | 0x00025000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002D000 | 0x00001610 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18546 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.01448 | 320 | UNKNOWN | Chinese - PRC | RT_VERSION |
103 | 1.5789 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
54
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
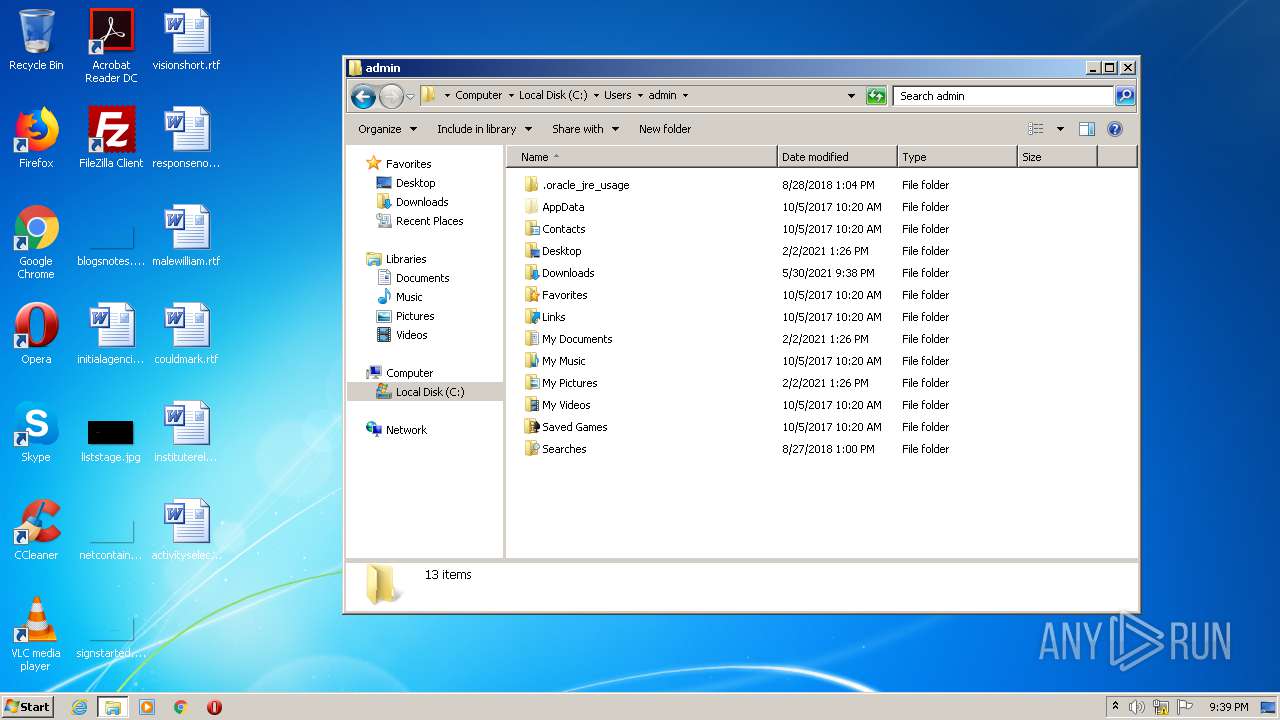
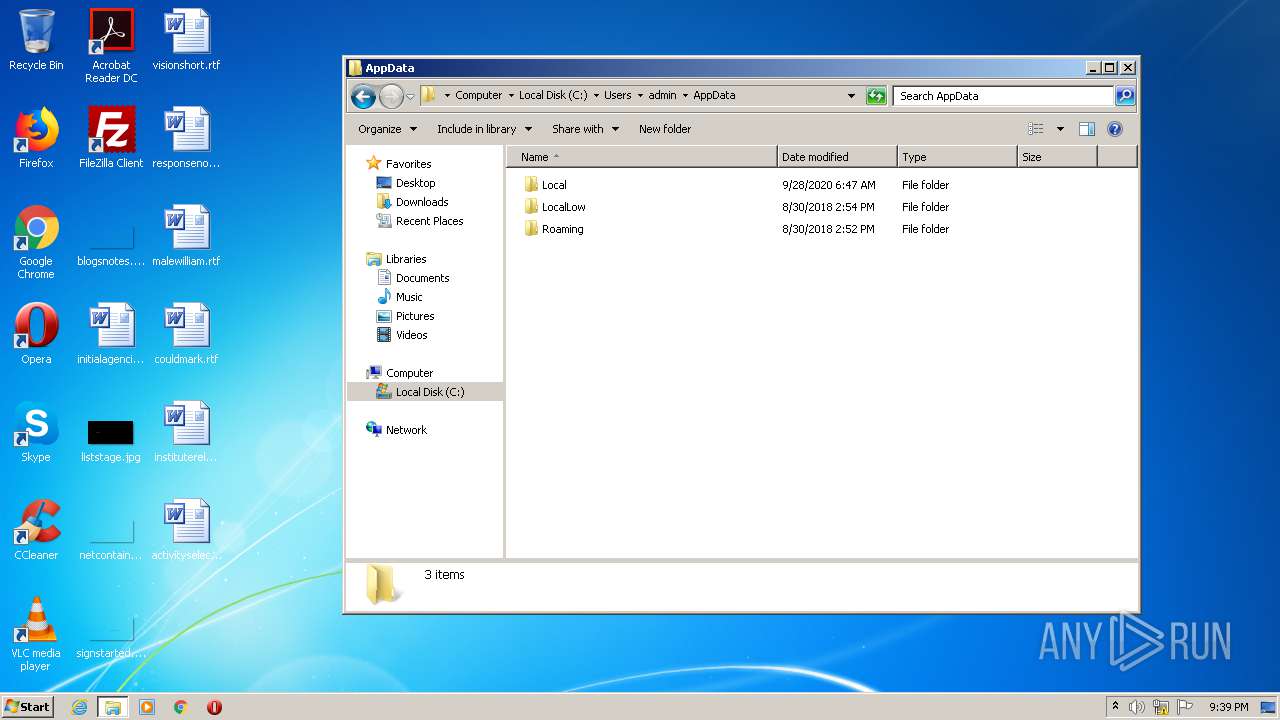
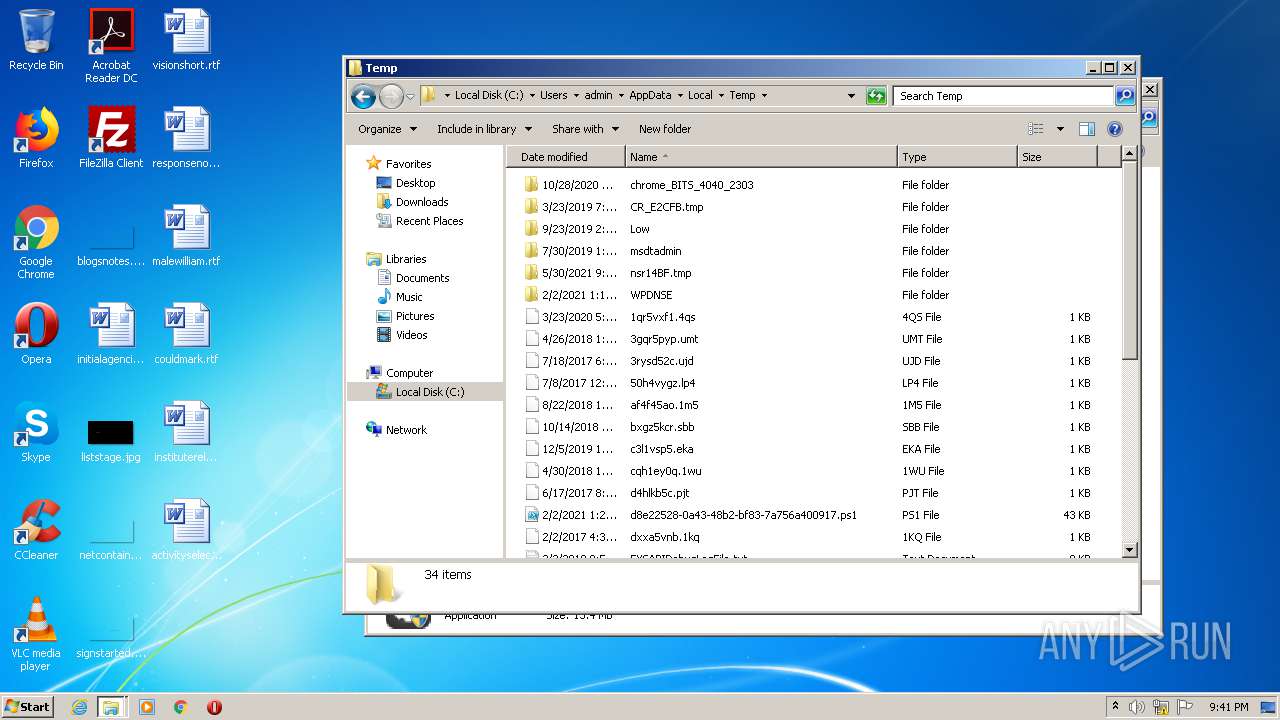
| 2196 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\AppData\Local\Temp\d8e22528-0a43-48b2-bf83-7a756a400917.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
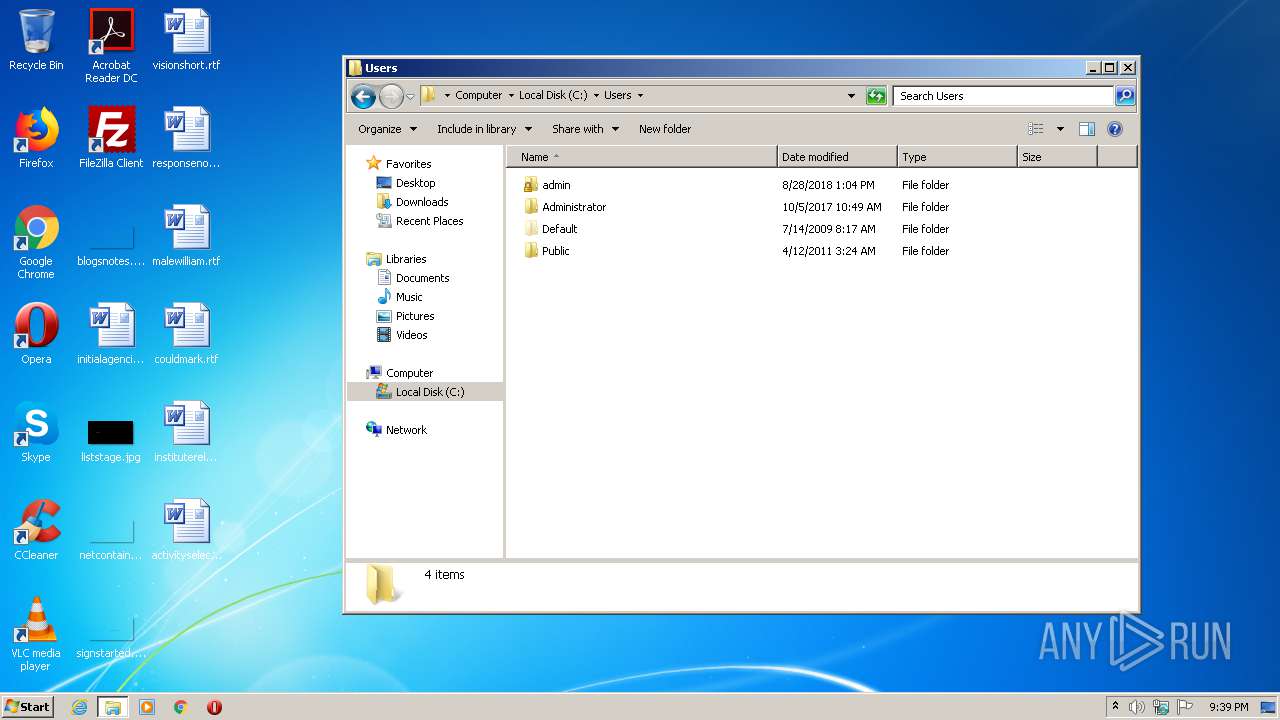
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
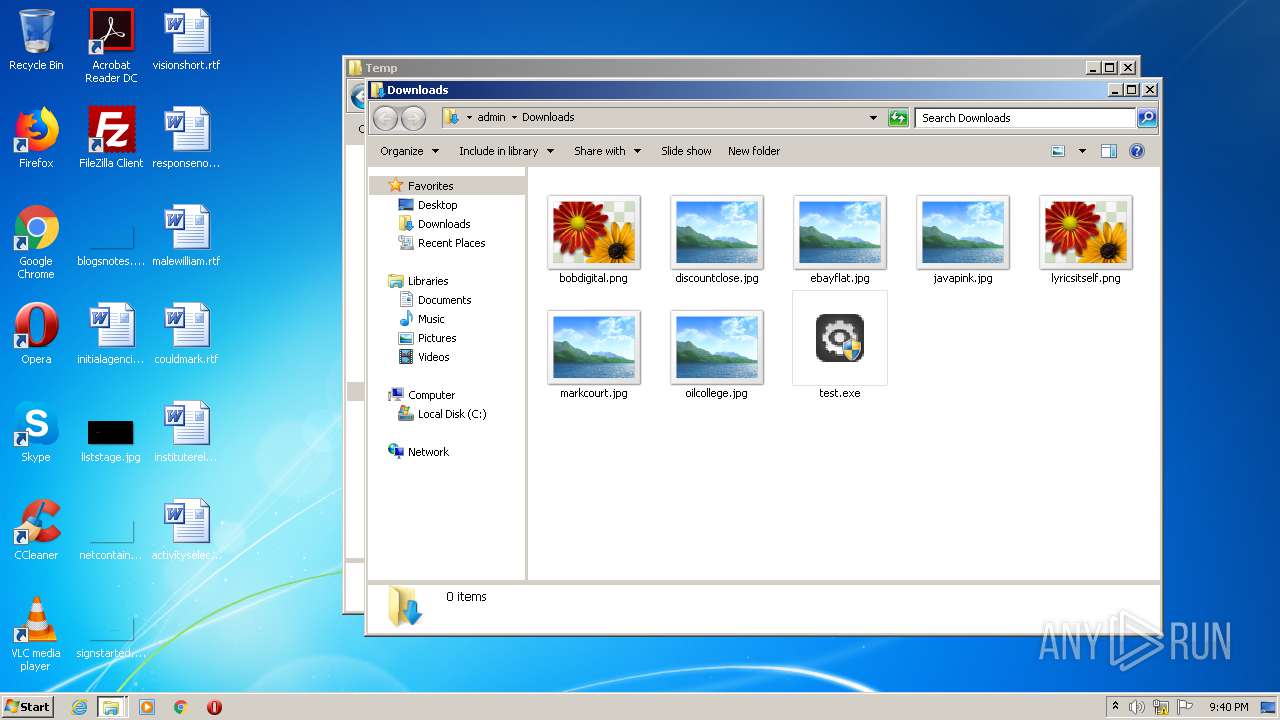
| 2608 | "C:\Users\admin\Downloads\test.exe" | C:\Users\admin\Downloads\test.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: YDArk Exit code: 0 Version: 1.0.2.2 Modules
| |||||||||||||||
| 2760 | "C:\Users\admin\Downloads\test.exe" | C:\Users\admin\Downloads\test.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: YDArk Exit code: 3221226540 Version: 1.0.2.2 Modules
| |||||||||||||||
| 2840 | "C:\Users\admin\Downloads\test.exe" | C:\Users\admin\Downloads\test.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: YDArk Exit code: 3221226540 Version: 1.0.2.2 Modules
| |||||||||||||||
| 3312 | "C:\Users\admin\Downloads\test.exe" | C:\Users\admin\Downloads\test.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: YDArk Exit code: 0 Version: 1.0.2.2 Modules
| |||||||||||||||
Total events
1 259
Read events
1 187
Write events
72
Delete events
0
Modification events
| (PID) Process: | (2196) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2196) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2196) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2196) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\IntelliForms\Storage2 |
| Operation: | write | Name: | BB79D934C1DF2D6A53F2778B62DDF005324A0EE663 |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000B8A2C0D43F2A184D9ADCECA5EC47F315000000000200000000001066000000010000200000004FE99824276CC2CAF26802C1DA8479CF1356A4E2D7349257F3DDF294EBCC4F6F000000000E8000000002000020000000E4204B441DFDDF9CF4CD6E84DDE8AA9CE7804F6B8A928A9BB15597B1C1A95C0190000000DF3EE66BDD02A213910710762D8AAE20B6D2EDF533137A9DF42F6F7E3BF7B9CF4B10AB75C01CE801E27DBBD5960A5406A63A2763107F3044844E470ED7F8ADEF45E4B4AAD0408EA1A930161F1485E3338850F2EF57CC597DFC44DC145BDF5D53EE80B6288E0C9B3213FBE3AD884D8C81C8DFF5C95371210C36425514C2A894ACAF39E8365F2ABB28B6522C92B14CE7E340000000E2473F8D3D5A495AC9EEC6DDFB25A1BE1651DB8425DECC539BACC6EE45DE7CAE04EB39B24574FCA850201604E32899DB394A0A1DD5A2C2207AAD4818143FEE39 | |||
| (PID) Process: | (2196) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\IntelliForms\Storage2 |
| Operation: | write | Name: | 9F4C19CE378F430520331C3037B0BD92EC24A790FC |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000B8A2C0D43F2A184D9ADCECA5EC47F315000000000200000000001066000000010000200000001D4940FD7710BE3C8F89E72CE10A586BA223A67E1170B5EFB94F8BE5B299A868000000000E80000000020000200000002AE3F2AB5F8B7CB91A135C8CE6F93DCA712BB8BA7943D1DF1F4EA6ADE9EF450F900000005CD3A37FF6221B51F780B37292505640E3C64E0CBA98614F1687FFD0697567D3B0E329C1E73962F4FE119127AF65944CB06F6E844A8872E38D6C6AB182D3D937E5DE3775B3F5F11B2BDE8D3A2453FF73C70259DF7FE9506A43F6E0585D25C1BA9F52AD178F60A3ECE4FF68FD3A8DEF6FDCE85C4DEE1F17D59FC7B17BBB429A571DAF94718742E05FB4B547EB764D4FEF40000000122E3840EFC7E537B5AC93D41AA32F52C576101CC2E2EB36CB9F2DF7E9E0E42D291EE969F0ECB8513BB7CEA2CBDE952871244C7BE689C1A1EE52E91C1263C29F | |||
| (PID) Process: | (2196) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\IntelliForms\Storage2 |
| Operation: | write | Name: | 0E03DB487D20CFE0EB6801C91AC7177F00F0696FDC |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000B8A2C0D43F2A184D9ADCECA5EC47F31500000000020000000000106600000001000020000000F99760F753784AAB5EB46AB4116AB3D1971B67B327D0D09F797D6189EDEE8AA2000000000E80000000020000200000009E0DD0EB59E3FFF49F4CFD82EBE973B1D2274032D1B71CC8AFA3A0C21DE580B190000000A84D9898405B08BC17BD0FC4A76159CE758898420BB3E3BB1FE4E2C6463CC9FDF77B814950B38C01519EC49AC5AD209DF959CBEA7020F6B81ECDB159A50F25453F51E840152B1FE67093A65F2C99FE32070638AFA466904DBA5DA0ABF1FBCE24323B83C730653D5EEE904A8E6C7BBC43B4F84D46857BF5186793519A42008AAD95438A77DFA89AE7B7D23CA19932E2A240000000CD3A804DE3858AE1EA8331942403FFA473AF3CD788267050CE7B85489BC7883480153183A4111A2459724A81E67BDE72340E62604427F7C60A76B5112E482064 | |||
| (PID) Process: | (2196) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\IntelliForms\Storage2 |
| Operation: | write | Name: | 7B0E8EC4799667FFCC54BA11B9206BB8E558854E47 |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000B8A2C0D43F2A184D9ADCECA5EC47F315000000000200000000001066000000010000200000006DF2502FD22B6836E5B490F54F0EE1CB3F3B4B2793CB9859BC309882B3E56F3B000000000E8000000002000020000000BA5B3EC1DAD7F9F80E1D503DACBD6F8EE6CC72E15EAC34CEC17288BE2F45C0F690000000E20836125BCF53B7DE91B5EA24D4F8DDE51A8500299E7ACB705B9E836A9DCFE6D9C431069383F9881E9F13C411C7D0CC5E28722A966202B06B59161EF0C30A9611750A903207ED660C833CB9A05D4A50DDDE48D1A5D725CA4B5F2AD6D07B3F867B8FA755CC9B035008AD56242D9BF896732CB2099F7E24431E20F8D499DF6F6752AA6CF237B333BB7C8F4332AB155E2140000000B7B465A563EF60F97DD8E18C7CD6EF3D51373A57ACFBACF6140B1187D8D5FB168499A13A4EA4EDD17D5B567E2733E14F6D559C5A90DFAD269B28D4CA909CFDDF | |||
| (PID) Process: | (2196) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\IntelliForms\Storage2 |
| Operation: | write | Name: | ECC42716A9327BCA481BB60450D55AB8854B0BFA36 |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000B8A2C0D43F2A184D9ADCECA5EC47F315000000000200000000001066000000010000200000003406B0D6E0287FD45E6AE1B4592BEF7341100CE3FA4ECCAA8E338AC611A43EF3000000000E8000000002000020000000FA2984B977270C2319D866C9DCA5222007B368DF31C5958390E4A99B709CFFFC90000000C7AF620F7B8AAF6F9A125D8105D8CEB524506A539333F9A1850AAA11F71D5250366EF6049DF4507FC69541DF5347E9B680324A2B3999BB529CA8F868292996A50DF28E54209F94BDB4A7D2B26D217D8357DE2C4CD2DB6FF1C874213CEE408AD40AE6EED2AC620CAC5E8E529494C5BB9BB3068A79488657F14EACD4AFC5F0EA1D985C99CEB61E13330D3981873DE649CF40000000DEF3AEA0FA834181FDFB19A6F111E05AE0AF56965A3AFFCCB44384082523A92225BC68474F017A8ED2B6C50135C5F2BFCF4EDEF3DDD70A6E40D8EA96B019B174 | |||
| (PID) Process: | (2196) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\IntelliForms\Storage2 |
| Operation: | write | Name: | 1489F923C4DCA729178B3E3233458550D8DDDF2945 |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000B8A2C0D43F2A184D9ADCECA5EC47F31500000000020000000000106600000001000020000000DDF5D32F9F1D70AD8F86B240F2634EDA25A41E2CFD49A1ED537DF5605446A09B000000000E8000000002000020000000C11C888BA65532B6DCDC5095551B9D3E3BA80BE6E40D2D5AF93A7CD50AA07DC99000000023A380952300625624F91FAF09A1C579482D2F0D36127C1E6BB0D4A15F542A23AEFF5B6BA92F35753CA4156260D2ABDA59A7DB2AEB9862E2B5147082E97CBB531F4319F501651A06540662AD2DD1C2D096ECBEEDB93268C42E43C7CD6BCA9BD081890B07D1101DA67C650402FA327EE0A44AE63B8A45B8348E9F6D626833F712BB331830572955D9C102800ABE190B074000000044A7603FCC5F5056FAA109DF05C11CA9D5F72AAAE6166EA668BF2639BCD94D15DDFFCA5A4F9B533E6D24A1E1789B512A5428756E5E4EA7544CD518887CD51374 | |||
| (PID) Process: | (2196) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\IntelliForms\Storage2 |
| Operation: | write | Name: | AAEE3588435992F2F2A56F9215B3A9487A33876A64 |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000B8A2C0D43F2A184D9ADCECA5EC47F315000000000200000000001066000000010000200000002546A052A387BBE16EC840276DE5BACBF1862AF15782DB70E528906A5C2C59CC000000000E8000000002000020000000161DDE7FB26BCFA1A1C016EAB7F1B79128C226A67651D364D619FFA421BE55719000000034B0EED6FD851C0F6FFF03121DE1C50C819BE2B1FC8CFADCF9FBC5424E12CAE44280A1C411BAB979AEB9B1CA3FE07727ECD19D8E1D41B8AB9534E80F118C1580435BC5A9855EEBD80EA152DA3BAF8CE8E7B0AAA919FF57FA7A0862D7DA28B704D0E53F00E804FD38AA9D1477371E8E857622F5D5BAECF33C3935735AEBA7CEAEE96B9A879A218A14798F22818AD6516740000000BC75D4EA23D571156644B309C05A0566CE10502026EA4480297C6A195CAC54461C15603131EE549ECDCF99662F33EF635D67F650E22EE2C0E401429E3B0AE9E8 | |||
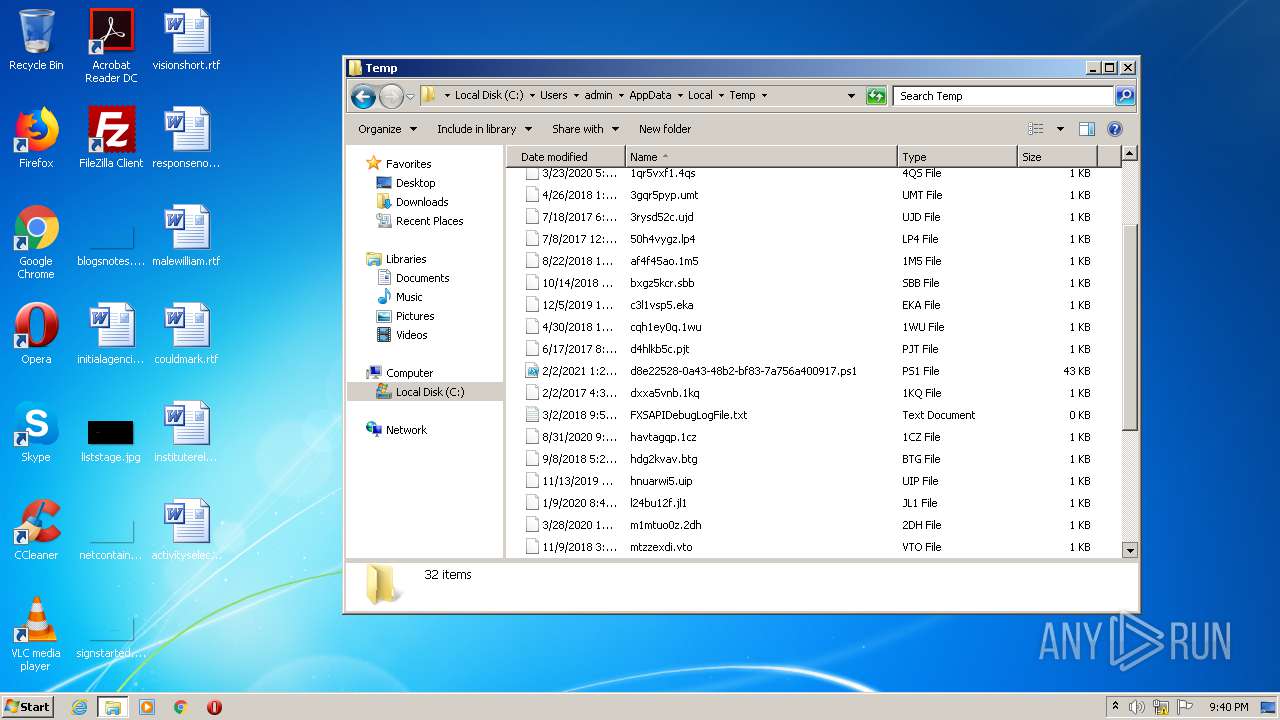
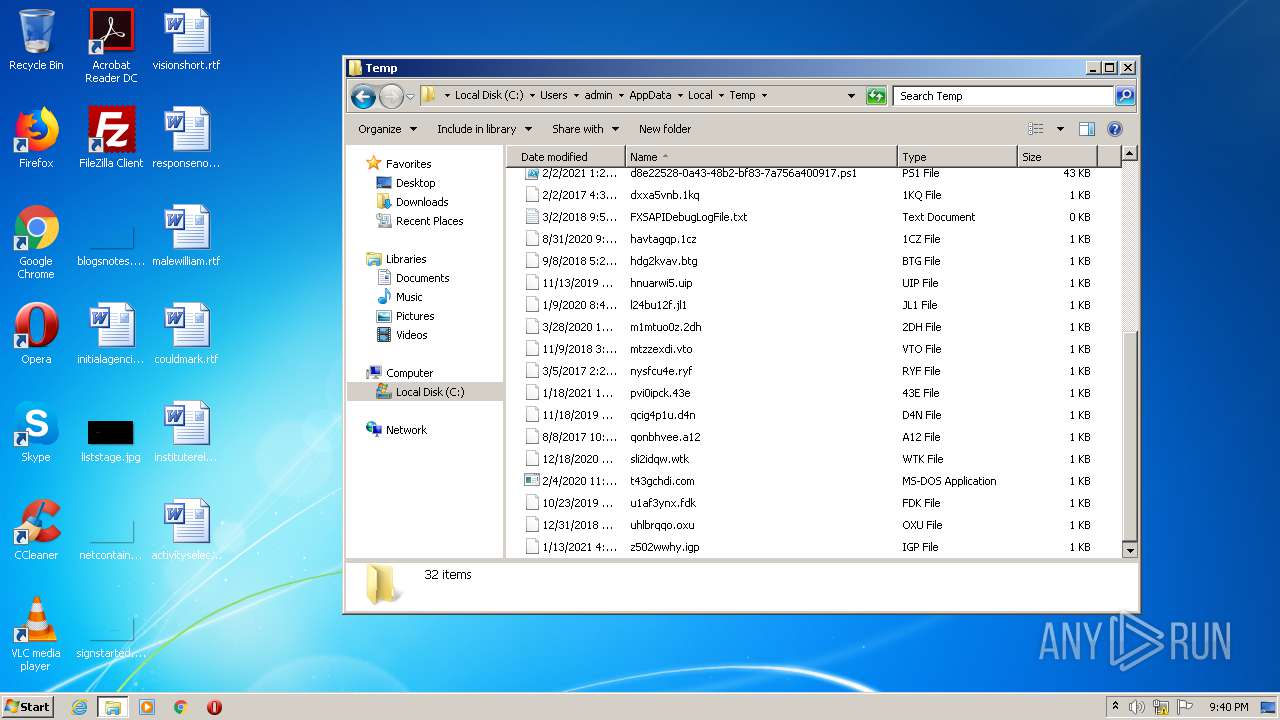
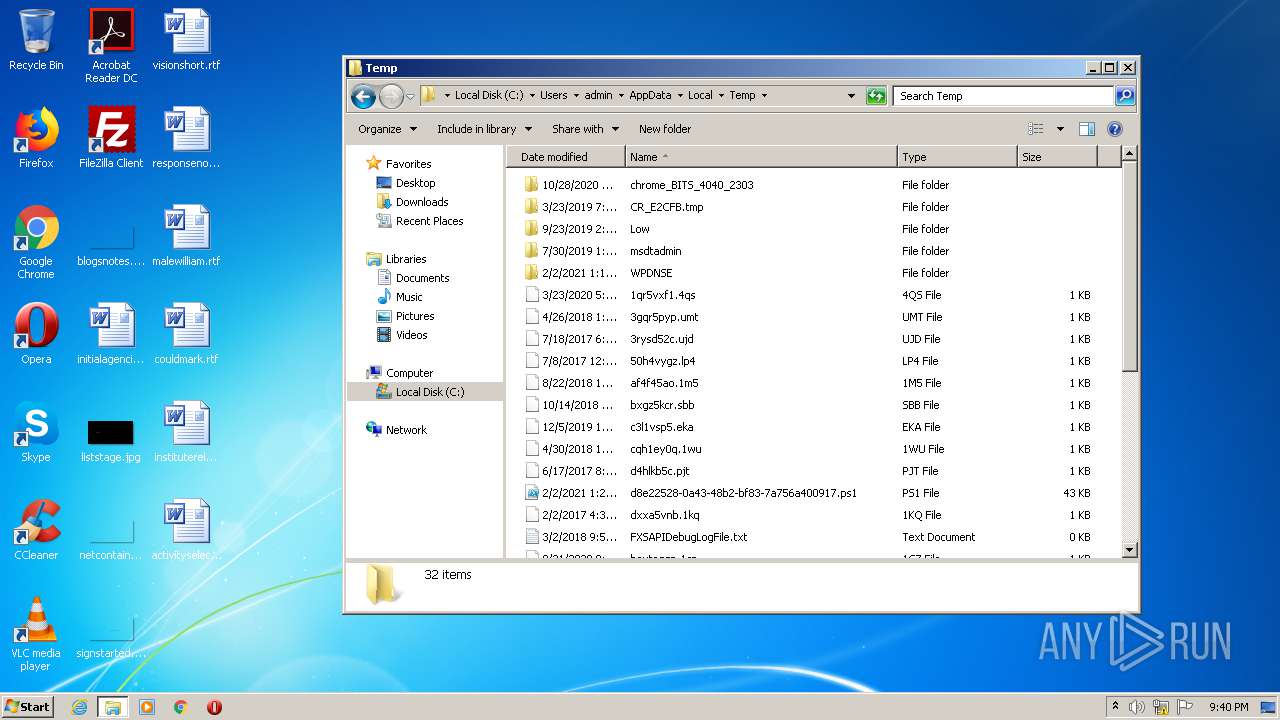
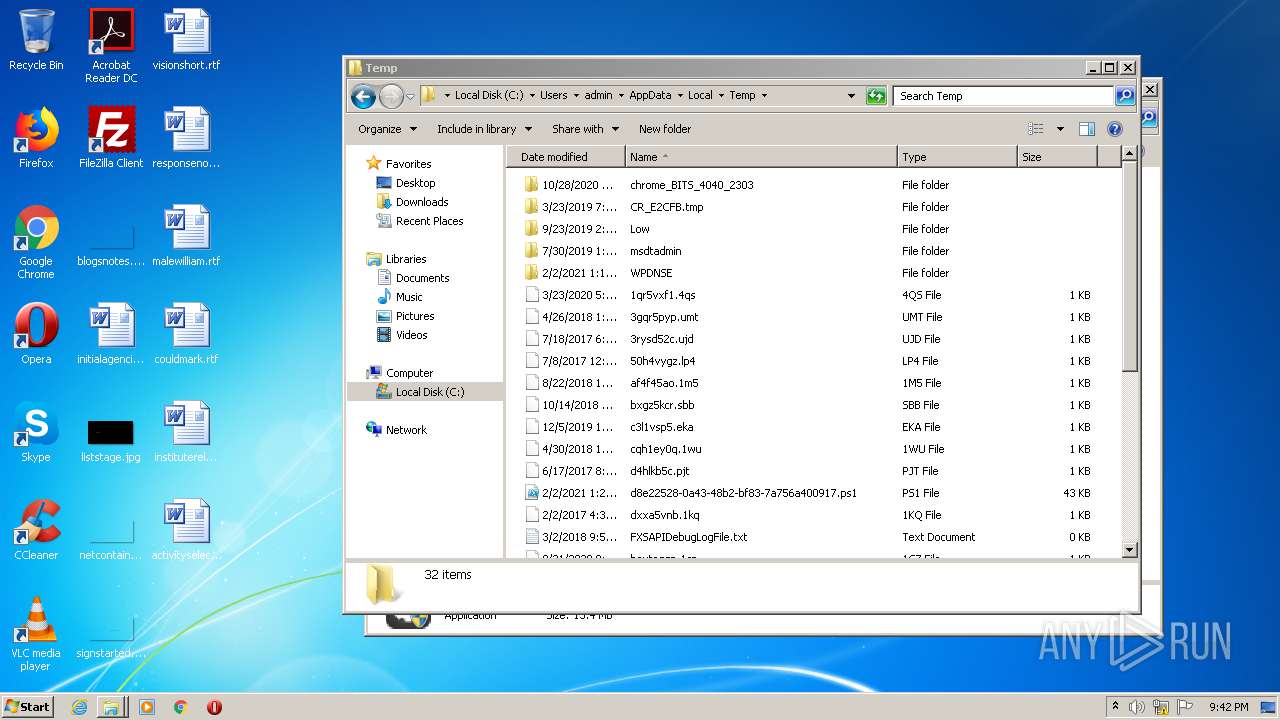
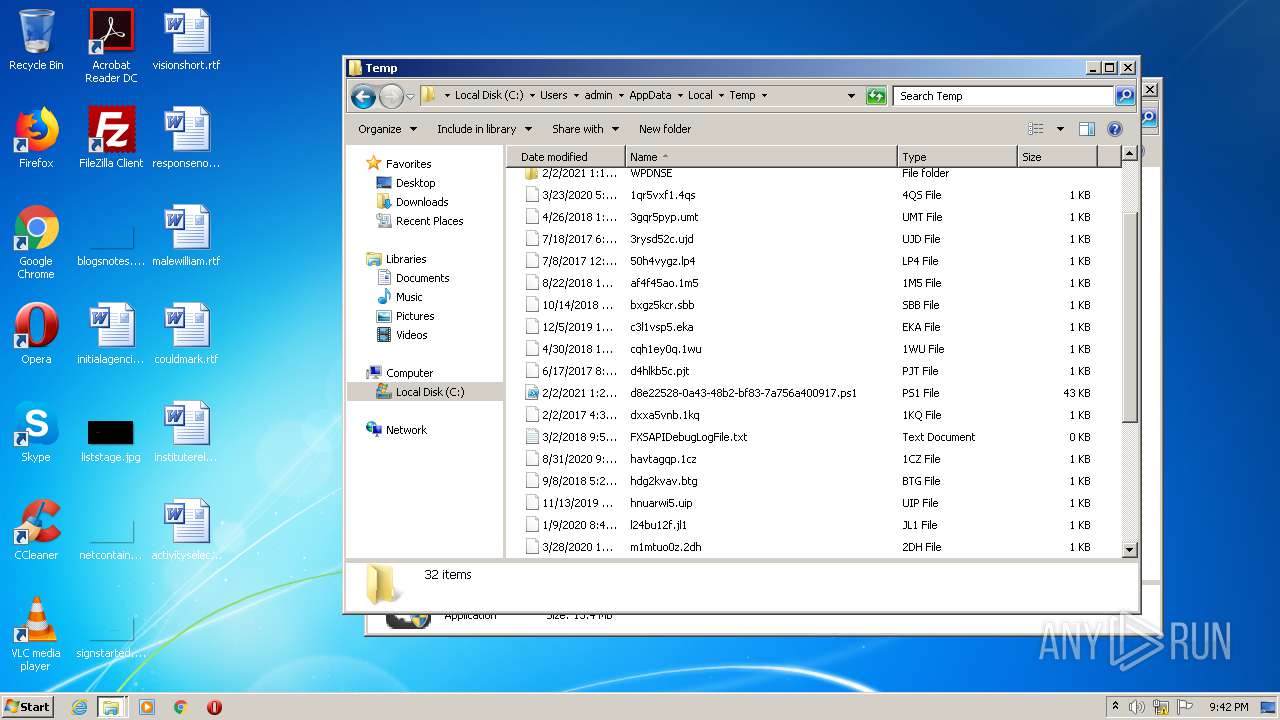
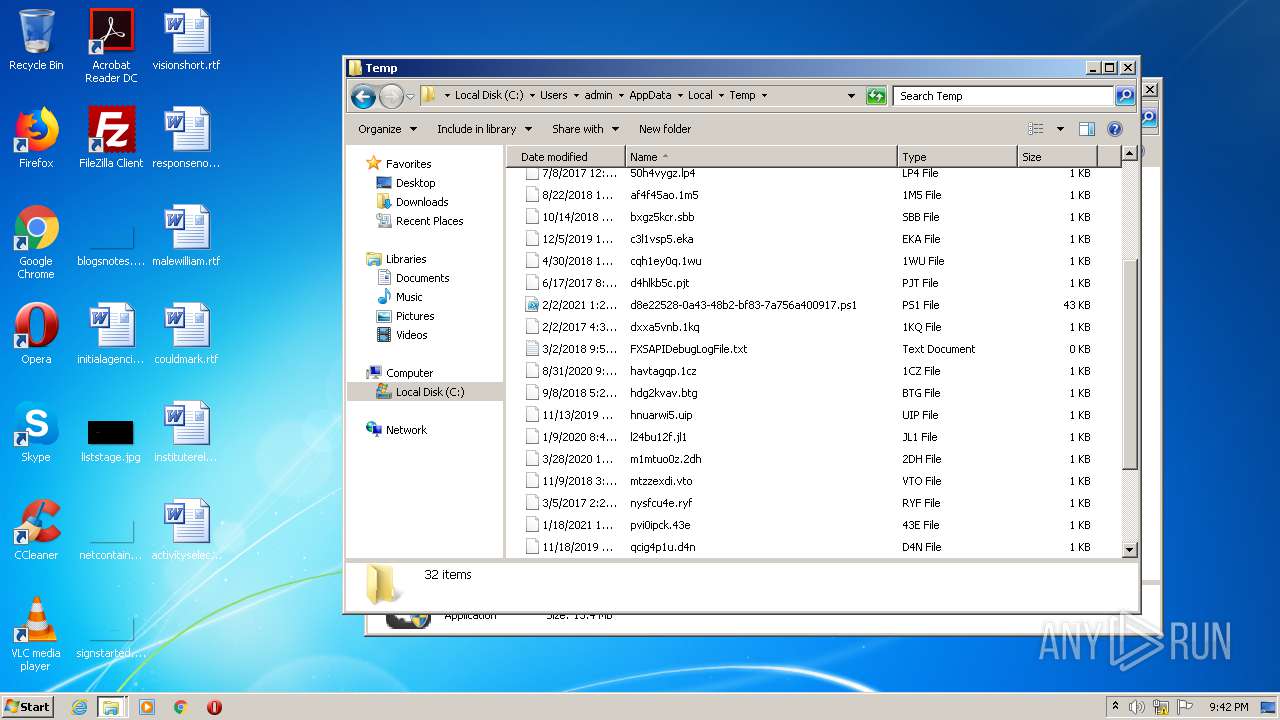
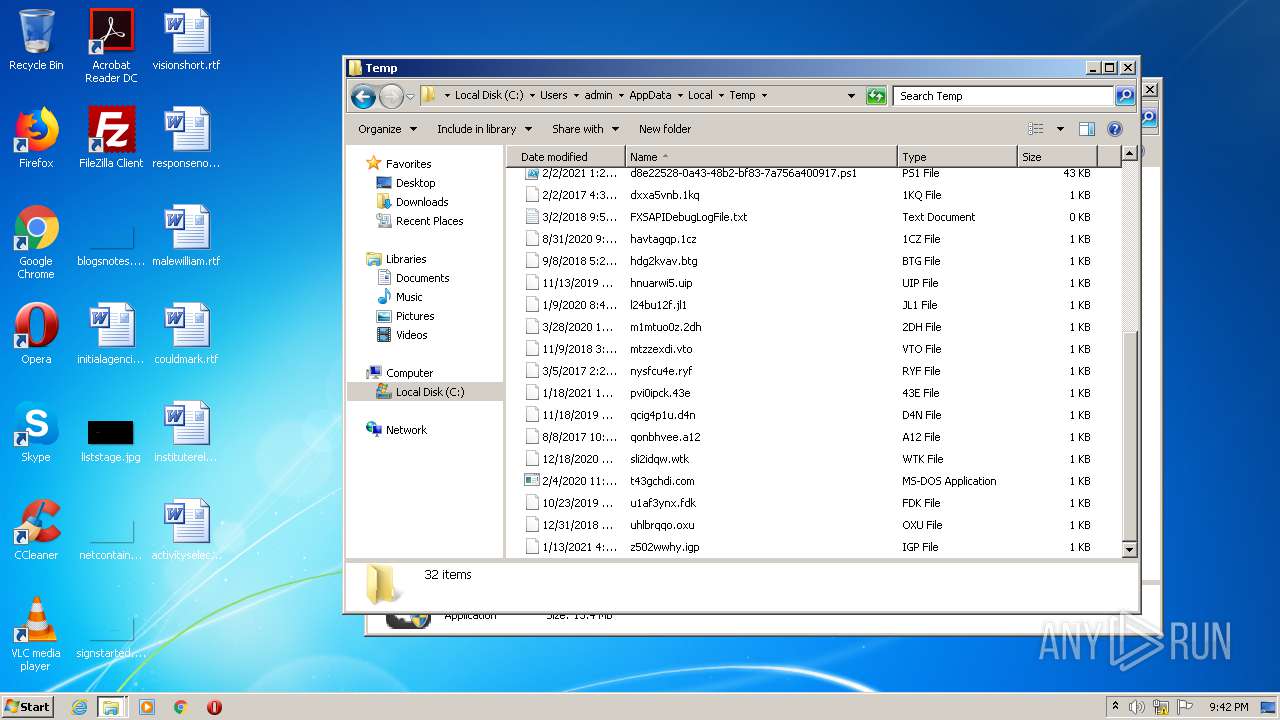
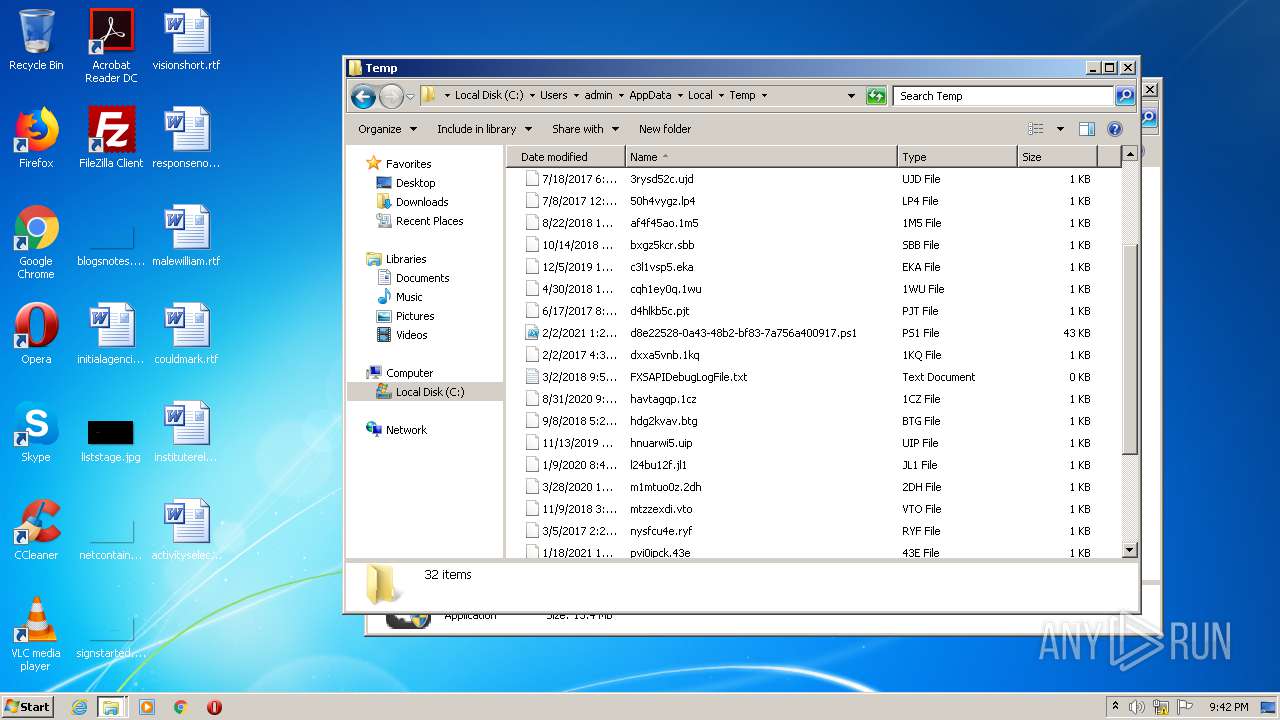
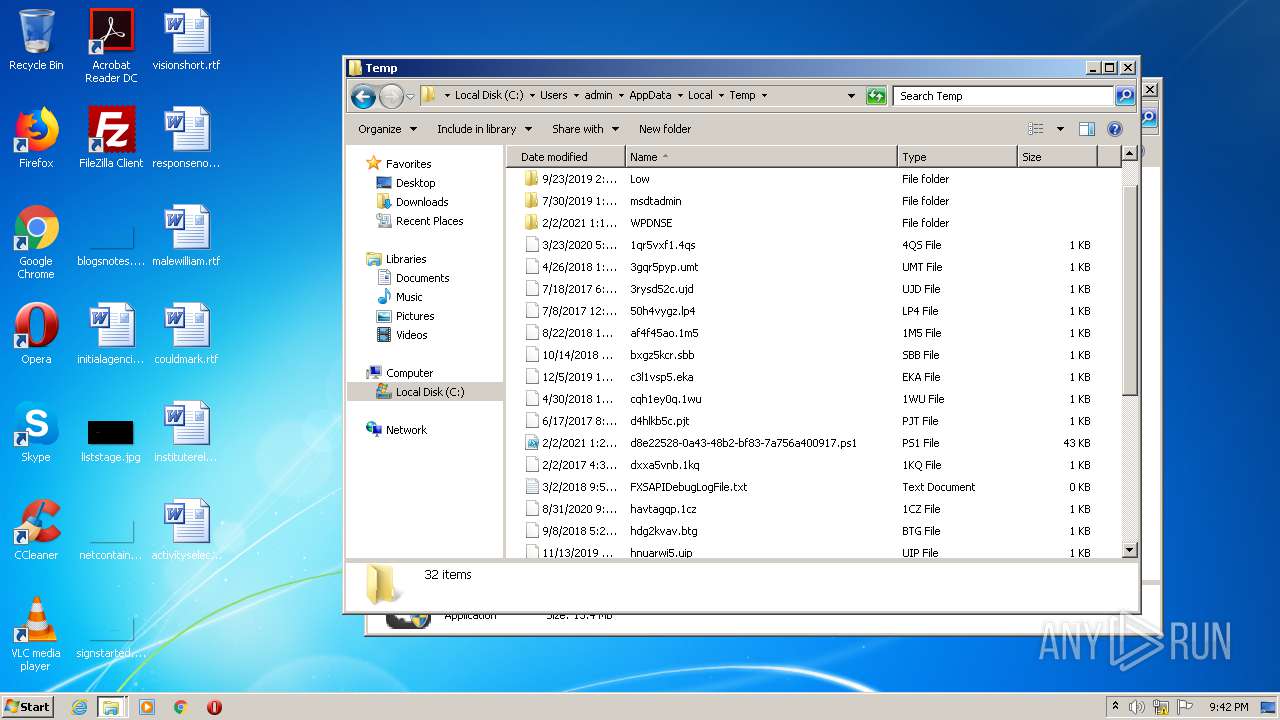
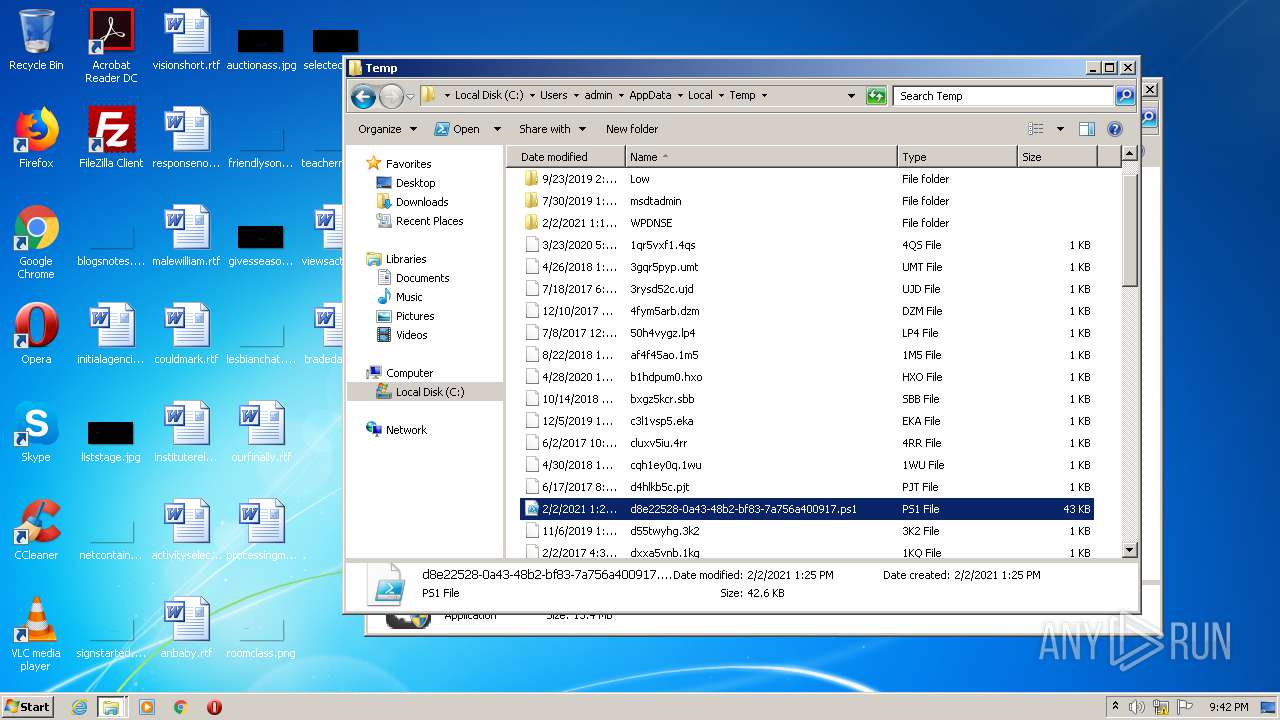
Executable files
0
Suspicious files
30
Text files
27
Unknown types
16
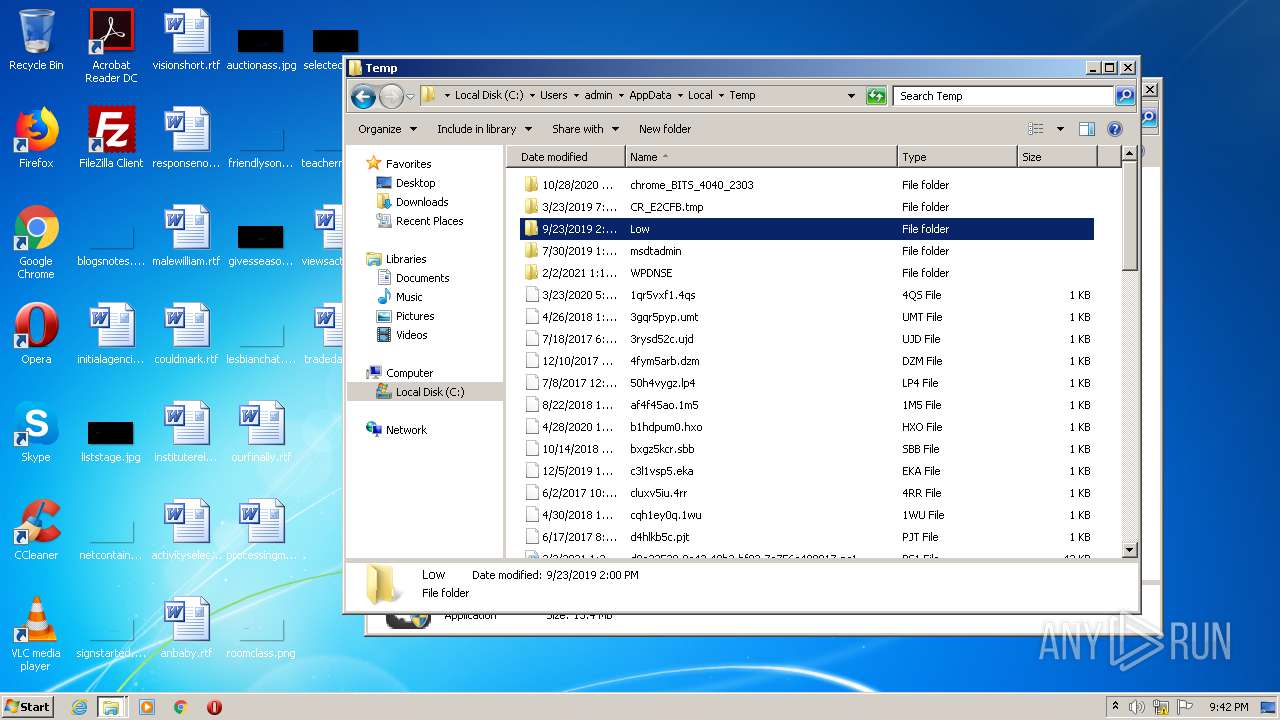
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2608 | test.exe | C:\Users\admin\AppData\Local\Temp\nsz454F.tmp\System.dll | — | |
MD5:— | SHA256:— | |||
| 2608 | test.exe | C:\Users\admin\AppData\Local\Temp\YDArk\423Down.url.url | — | |
MD5:— | SHA256:— | |||
| 2608 | test.exe | C:\Users\admin\AppData\Local\Temp\YDArk\YDArk.exe | — | |
MD5:— | SHA256:— | |||
| 2608 | test.exe | C:\Users\admin\AppData\Local\Temp\YDArk\YDArkDrv.sys | — | |
MD5:— | SHA256:— | |||
| 2608 | test.exe | C:\Users\admin\AppData\Local\Temp\YDArk\dbghelp.dll | — | |
MD5:— | SHA256:— | |||
| 2608 | test.exe | C:\Users\admin\AppData\Local\Temp\YDArk\symsrv.dll | — | |
MD5:— | SHA256:— | |||
| 2608 | test.exe | C:\Users\admin\AppData\Local\Temp\nsz453E.tmp | — | |
MD5:— | SHA256:— | |||
| 3312 | test.exe | C:\Users\admin\AppData\Local\Temp\nsr14BF.tmp\System.dll | — | |
MD5:— | SHA256:— | |||
| 3312 | test.exe | C:\Users\admin\AppData\Local\Temp\YDArk\423Down.url.url | — | |
MD5:— | SHA256:— | |||
| 3312 | test.exe | C:\Users\admin\AppData\Local\Temp\YDArk\YDArk.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report