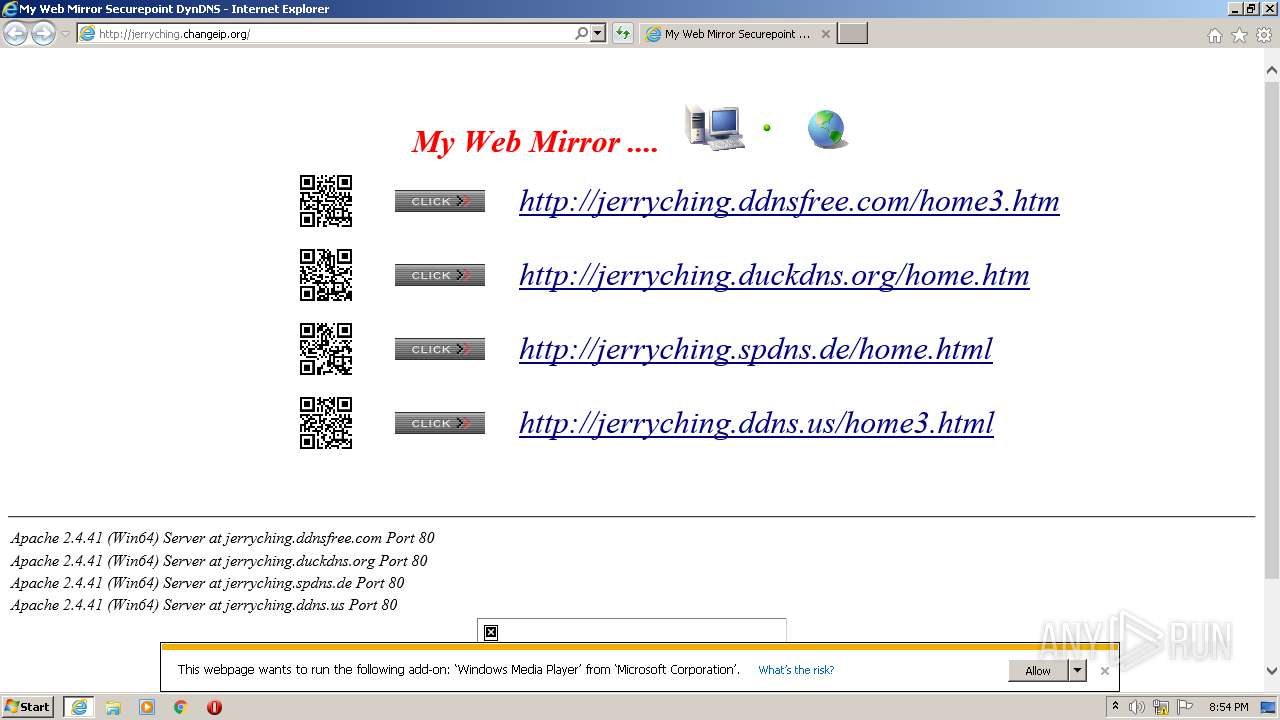
| URL: | http://jerryching.changeip.org/ |
| Full analysis: | https://app.any.run/tasks/60f6162f-707c-4e6d-b807-746e75fd8aa8 |
| Verdict: | Malicious activity |
| Analysis date: | September 23, 2020, 19:54:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 976F504540700BD0B6A8FCDA110BB580 |
| SHA1: | 2EBE44B73EFA9BEFFBC8846053F03DD4873F9775 |
| SHA256: | C5DF103A34043906E7F3A8C791D00D8D7A5EDEE5201810E6F761685EFE4F2DBF |
| SSDEEP: | 3:N1KUEcGNMMCAUi:CUEcHMC7i |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2672)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 1452)
- iexplore.exe (PID: 2244)
Application launched itself
- iexplore.exe (PID: 2244)
Changes internet zones settings
- iexplore.exe (PID: 2244)
Reads internet explorer settings
- iexplore.exe (PID: 1452)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1452 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2244 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Internet Explorer\iexplore.exe" http://jerryching.changeip.org/ | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2672 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
Total events
745
Read events
606
Write events
138
Delete events
1
Modification events
| (PID) Process: | (2244) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1734380468 | |||
| (PID) Process: | (2244) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30839267 | |||
| (PID) Process: | (2244) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2244) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2244) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2244) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2244) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2244) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2244) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2244) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
3
Text files
54
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2244 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1452 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Virtualized\C\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML.bak | — | |
MD5:— | SHA256:— | |||
| 1452 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Virtualized\C\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNSD.XML | — | |
MD5:— | SHA256:— | |||
| 2672 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2672 | FlashUtil32_26_0_0_131_ActiveX.exe | C:\Users\admin\AppData\Roaming\Macromedia\Flash Player\macromedia.com\support\flashplayer\sys\settings.sxx | — | |
MD5:— | SHA256:— | |||
| 1452 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\Click[1].gif | image | |
MD5:— | SHA256:— | |||
| 1452 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 1452 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\jerryching.duckdns.org[1].png | image | |
MD5:— | SHA256:— | |||
| 1452 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\jerryching.ddnsfree.com[1].png | image | |
MD5:— | SHA256:— | |||
| 1452 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\L13719DV.htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
61
TCP/UDP connections
34
DNS requests
10
Threats
56
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1452 | iexplore.exe | GET | 200 | 58.71.204.54:80 | http://jerryching.changeip.org/ | MY | html | 5.91 Kb | suspicious |
1452 | iexplore.exe | GET | 200 | 58.71.204.54:80 | http://jerryching.changeip.org/Web%20Photo/IE.jpg | MY | image | 1.41 Kb | suspicious |
1452 | iexplore.exe | GET | 200 | 58.71.204.54:80 | http://jerryching.changeip.org/Web%20Photo/My%20Web%20QR%20Code/jerryching.ddnsfree.com.png | MY | image | 6.28 Kb | suspicious |
1452 | iexplore.exe | GET | 200 | 58.71.204.54:80 | http://jerryching.changeip.org/Web%20Photo/Microsoft%20Expression%20Web.jpg | MY | image | 2.18 Kb | suspicious |
1452 | iexplore.exe | GET | 200 | 58.71.204.54:80 | http://jerryching.changeip.org/Web%20Photo/Click.gif | MY | image | 962 b | suspicious |
1452 | iexplore.exe | GET | 200 | 58.71.204.54:80 | http://jerryching.changeip.org/Web%20Photo/Firefox.jpg | MY | image | 1.36 Kb | suspicious |
1452 | iexplore.exe | GET | 200 | 58.71.204.54:80 | http://jerryching.changeip.org/Web%20Photo/My%20Web%20QR%20Code/jerryching.ddns.us.png | MY | image | 6.26 Kb | suspicious |
1452 | iexplore.exe | GET | 200 | 58.71.204.54:80 | http://jerryching.changeip.org/Web%20Photo/My%20Web%20QR%20Code/jerryching.spdns.de.png | MY | image | 6.28 Kb | suspicious |
1452 | iexplore.exe | GET | 200 | 58.71.204.54:80 | http://jerryching.changeip.org/Web%20Photo/My%20Web%20QR%20Code/jerryching.duckdns.org.png | MY | image | 6.25 Kb | suspicious |
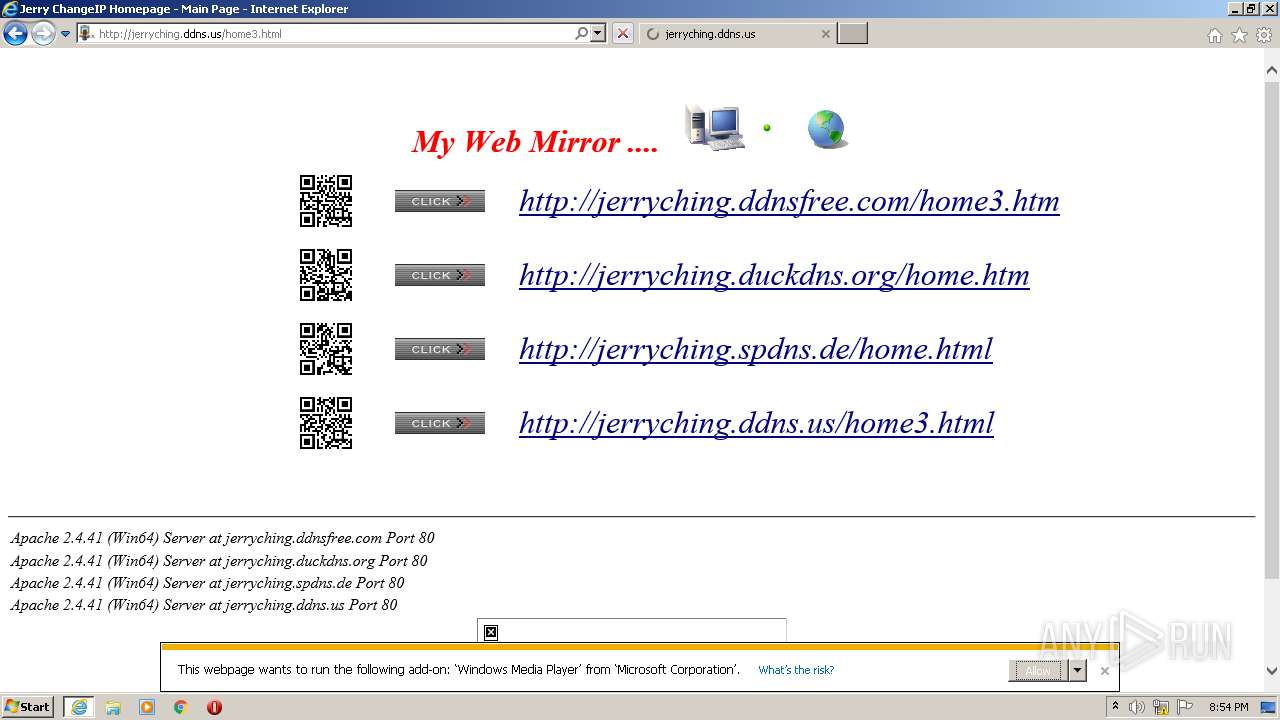
1452 | iexplore.exe | GET | 200 | 58.71.204.54:80 | http://jerryching.ddns.us/home3.html | MY | html | 20.2 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2244 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 58.71.204.54:80 | jerryching.changeip.org | Binariang Berhad | MY | suspicious |
1452 | iexplore.exe | 58.71.204.54:80 | jerryching.changeip.org | Binariang Berhad | MY | suspicious |
2244 | iexplore.exe | 58.71.204.54:80 | jerryching.changeip.org | Binariang Berhad | MY | suspicious |
1452 | iexplore.exe | 34.214.179.92:80 | www.hit-counts.com | Amazon.com, Inc. | US | unknown |
1452 | iexplore.exe | 34.214.179.92:443 | www.hit-counts.com | Amazon.com, Inc. | US | unknown |
1452 | iexplore.exe | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
1452 | iexplore.exe | 54.39.158.232:80 | www.worldtimeserver.com | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jerryching.changeip.org |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
jerryching.ddns.us |
| suspicious |
www.hit-counts.com |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
www.worldtimeserver.com |
| suspicious |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1452 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |
55 ETPRO signatures available at the full report