| download: | AeroAdmin.exe |
| Full analysis: | https://app.any.run/tasks/afaa764f-4bf7-4898-a172-3ecd6b318982 |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2019, 19:34:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 26387C4C6BB65C185A4FFC3CC1D11491 |
| SHA1: | A1963430147565B9278F1A08E3864BB50725E976 |
| SHA256: | C5D40EEB1EE8507B416AF21A0E021F7840DFCBB7EEFDD6B708CA4D05D1497BD2 |
| SSDEEP: | 49152:mxOwdCF66skrxYu6r0agDzuATQH6m29BtY5QSI1f:FOCwDoxkgXxmkBoQSI1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- AeroAdmin.exe (PID: 3148)
- AeroAdmin.exe (PID: 2452)
Low-level read access rights to disk partition
- AeroAdmin.exe (PID: 3404)
Creates files in the program directory
- AeroAdmin.exe (PID: 3404)
- AeroAdmin.exe (PID: 3148)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:09 20:00:28+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.15 |
| CodeSize: | 1368576 |
| InitializedDataSize: | 1078784 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x106a9c |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.0.5.5 |
| ProductVersionNumber: | 4.6.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | AeroAdmin LLC |
| FileDescription: | AeroAdmin |
| FileVersion: | 3.0.5.5 |
| InternalName: | AeroAdmin.exe |
| LegalCopyright: | AeroAdmin LLC |
| LegalTrademarks: | AeroAdmin |
| OriginalFileName: | AeroAdmin.exe |
| ProductName: | AeroAdmin |
| ProductVersion: | v4.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Nov-2018 19:00:28 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | AeroAdmin LLC |
| FileDescription: | AeroAdmin |
| FileVersion: | 3.0.5.5 |
| InternalName: | AeroAdmin.exe |
| LegalCopyright: | AeroAdmin LLC |
| LegalTrademarks: | AeroAdmin |
| OriginalFilename: | AeroAdmin.exe |
| ProductName: | AeroAdmin |
| ProductVersion: | v4.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Nov-2018 19:00:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0014E03C | 0x0014E200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.77166 |
.rdata | 0x00150000 | 0x00039256 | 0x00039400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.54143 |
.data | 0x0018A000 | 0x000BAD44 | 0x00085200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.5942 |
.rsrc | 0x00245000 | 0x00004C38 | 0x00004E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.56669 |
.reloc | 0x0024A000 | 0x0000E49C | 0x0000E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.70034 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.12787 | 825 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.23898 | 4264 | UNKNOWN | Russian - Russia | RT_ICON |
3 | 3.91639 | 1128 | UNKNOWN | Russian - Russia | RT_ICON |
123 | 2.45849 | 48 | UNKNOWN | Russian - Russia | RT_GROUP_ICON |
124 | 0.422766 | 2376 | UNKNOWN | Russian - Russia | RT_RCDATA |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
MSIMG32.dll |
OLEAUT32.dll |
SHELL32.dll |
Total processes
36
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2452 | "C:\Users\admin\AppData\Local\Temp\AeroAdmin.exe" s -sid 1 | C:\Users\admin\AppData\Local\Temp\AeroAdmin.exe | services.exe | ||||||||||||
User: SYSTEM Company: AeroAdmin LLC Integrity Level: SYSTEM Description: AeroAdmin Exit code: 1 Version: 3.0.5.5 Modules
| |||||||||||||||
| 3148 | "C:\Users\admin\AppData\Local\Temp\AeroAdmin.exe" | C:\Users\admin\AppData\Local\Temp\AeroAdmin.exe | explorer.exe | ||||||||||||
User: admin Company: AeroAdmin LLC Integrity Level: MEDIUM Description: AeroAdmin Exit code: 0 Version: 3.0.5.5 Modules
| |||||||||||||||
| 3380 | "C:\Users\admin\AppData\Local\Temp\AeroAdmin.exe" z z | C:\Users\admin\AppData\Local\Temp\AeroAdmin.exe | AeroAdmin.exe | ||||||||||||
User: admin Company: AeroAdmin LLC Integrity Level: HIGH Description: AeroAdmin Exit code: 0 Version: 3.0.5.5 Modules
| |||||||||||||||
| 3404 | C:\Users\admin\AppData\Local\Temp\AeroAdmin.exe a | C:\Users\admin\AppData\Local\Temp\AeroAdmin.exe | AeroAdmin.exe | ||||||||||||
User: SYSTEM Company: AeroAdmin LLC Integrity Level: SYSTEM Description: AeroAdmin Exit code: 0 Version: 3.0.5.5 Modules
| |||||||||||||||
Total events
395
Read events
387
Write events
6
Delete events
2
Modification events
| (PID) Process: | (3148) AeroAdmin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3148) AeroAdmin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3380) AeroAdmin.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\AeroadminService |
| Operation: | write | Name: | |
Value: Service | |||
| (PID) Process: | (3404) AeroAdmin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\AeroAdmin |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3404) AeroAdmin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\AeroAdmin |
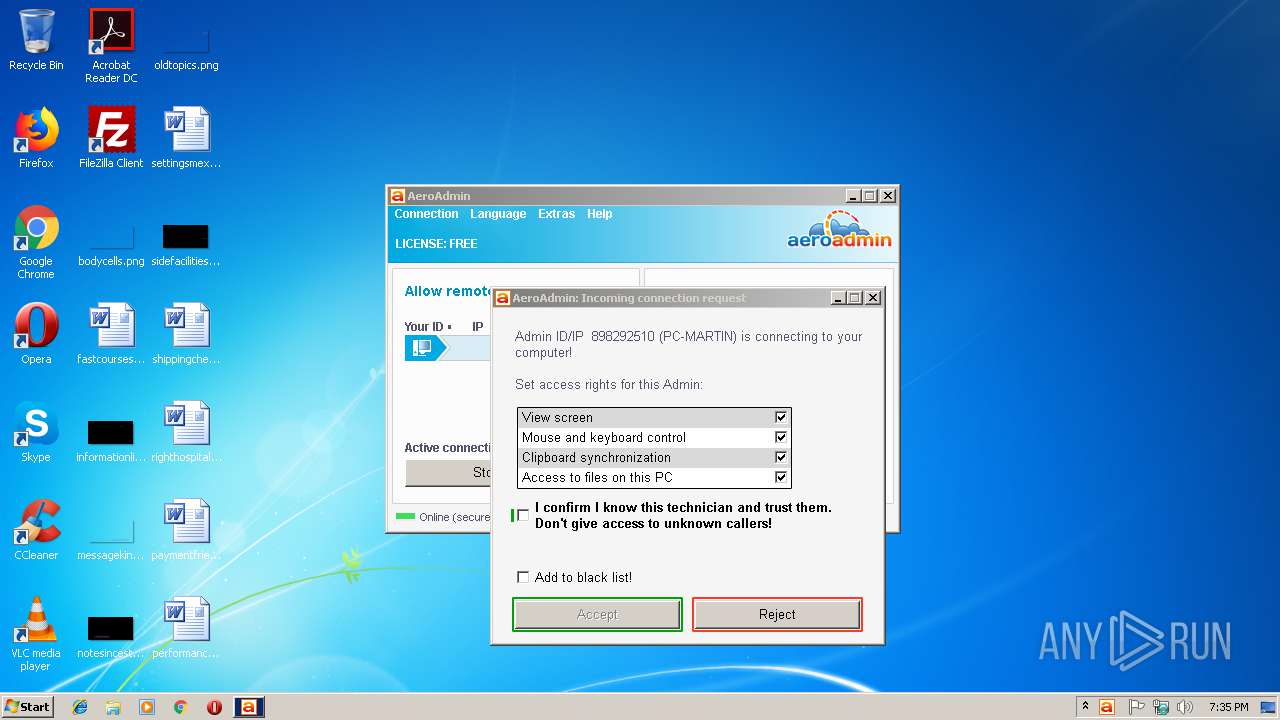
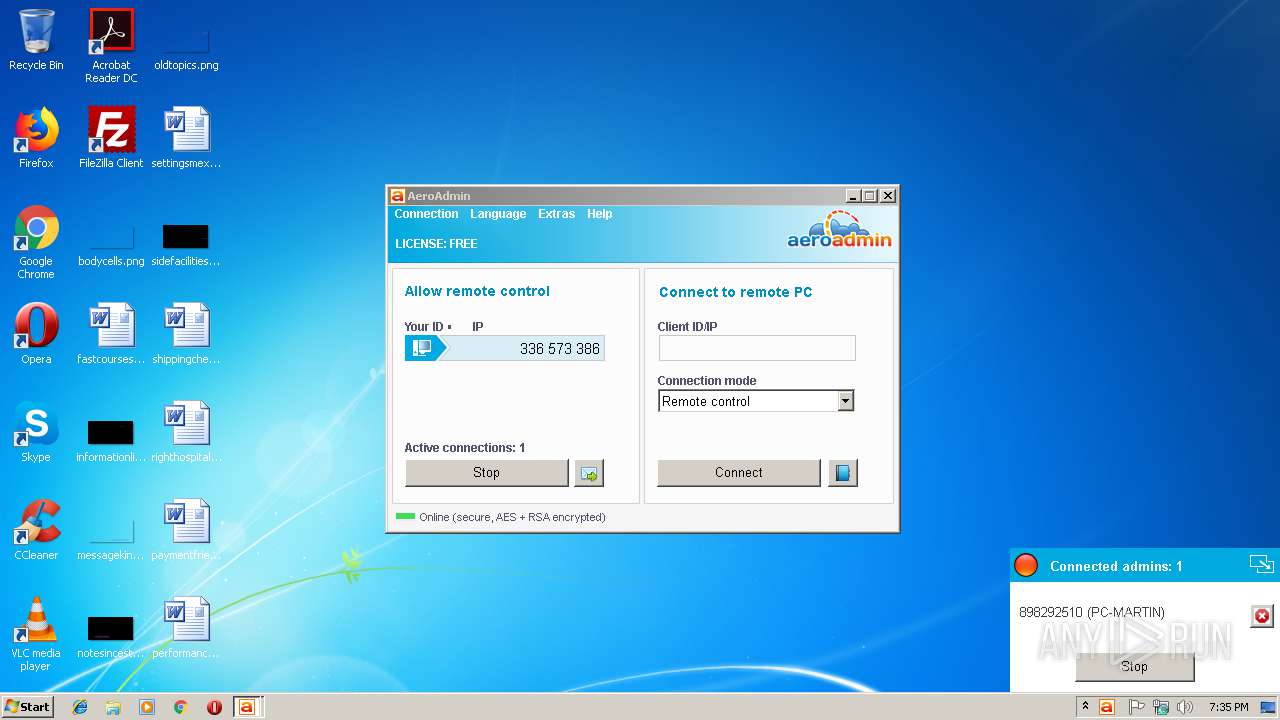
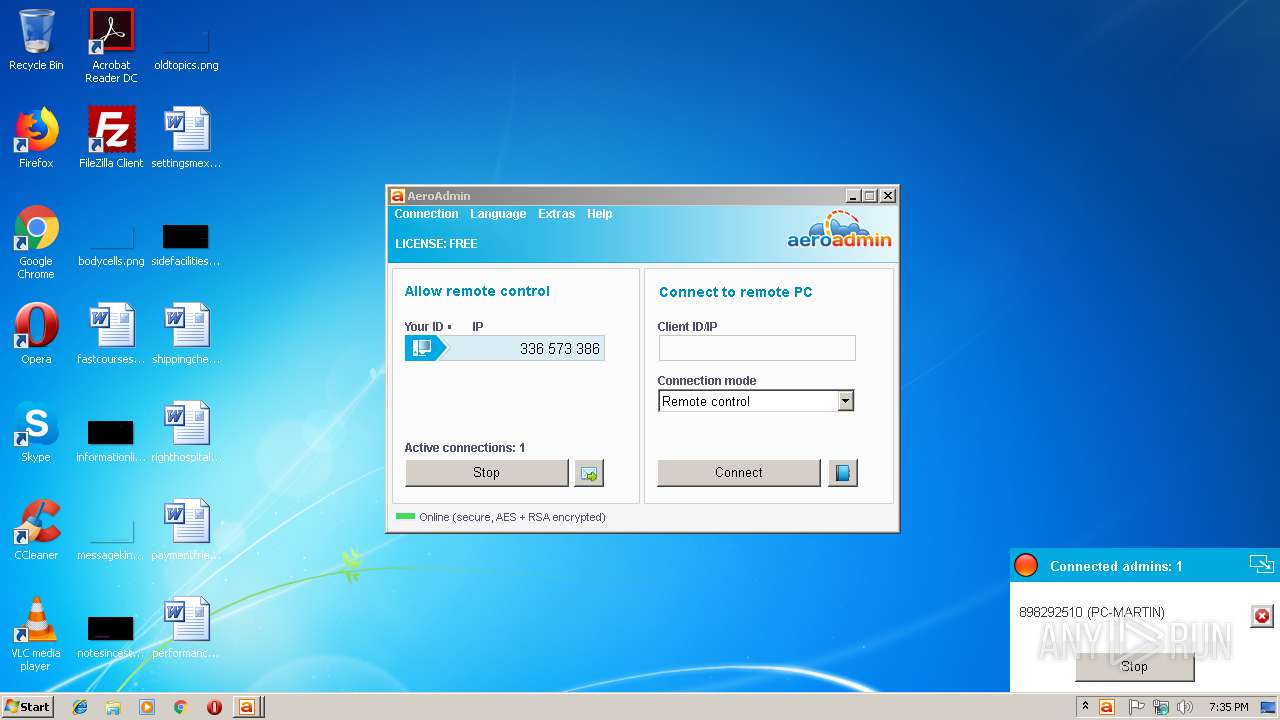
| Operation: | write | Name: | admins |
Value: 898292510 | |||
Executable files
0
Suspicious files
2
Text files
81
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3380 | AeroAdmin.exe | C:\ProgramData\Aeroadmin\log.txt | text | |
MD5:— | SHA256:— | |||
| 3148 | AeroAdmin.exe | C:\ProgramData\Aeroadmin\log.txt | text | |
MD5:— | SHA256:— | |||
| 3380 | AeroAdmin.exe | C:\ProgramData\Aeroadmin\config | text | |
MD5:F35EB91CDF228D96FF702D5035F49C5D | SHA256:0B3E8634607A8F154AD4C2072C818D9E8C9D2952F7389E6BE4B1CDC22A9B1B99 | |||
| 2452 | AeroAdmin.exe | C:\ProgramData\Aeroadmin\config | text | |
MD5:F35EB91CDF228D96FF702D5035F49C5D | SHA256:0B3E8634607A8F154AD4C2072C818D9E8C9D2952F7389E6BE4B1CDC22A9B1B99 | |||
| 2452 | AeroAdmin.exe | C:\ProgramData\Aeroadmin\log.txt | text | |
MD5:— | SHA256:— | |||
| 3404 | AeroAdmin.exe | C:\ProgramData\Aeroadmin\log.txt | text | |
MD5:— | SHA256:— | |||
| 3404 | AeroAdmin.exe | C:\ProgramData\Aeroadmin\guid.bin | binary | |
MD5:— | SHA256:— | |||
| 3404 | AeroAdmin.exe | C:\ProgramData\Aeroadmin\settings.bin | binary | |
MD5:— | SHA256:— | |||
| 3148 | AeroAdmin.exe | C:\ProgramData\Aeroadmin\config | text | |
MD5:F35EB91CDF228D96FF702D5035F49C5D | SHA256:0B3E8634607A8F154AD4C2072C818D9E8C9D2952F7389E6BE4B1CDC22A9B1B99 | |||
| 3404 | AeroAdmin.exe | C:\ProgramData\Aeroadmin\config | text | |
MD5:F35EB91CDF228D96FF702D5035F49C5D | SHA256:0B3E8634607A8F154AD4C2072C818D9E8C9D2952F7389E6BE4B1CDC22A9B1B99 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
174
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
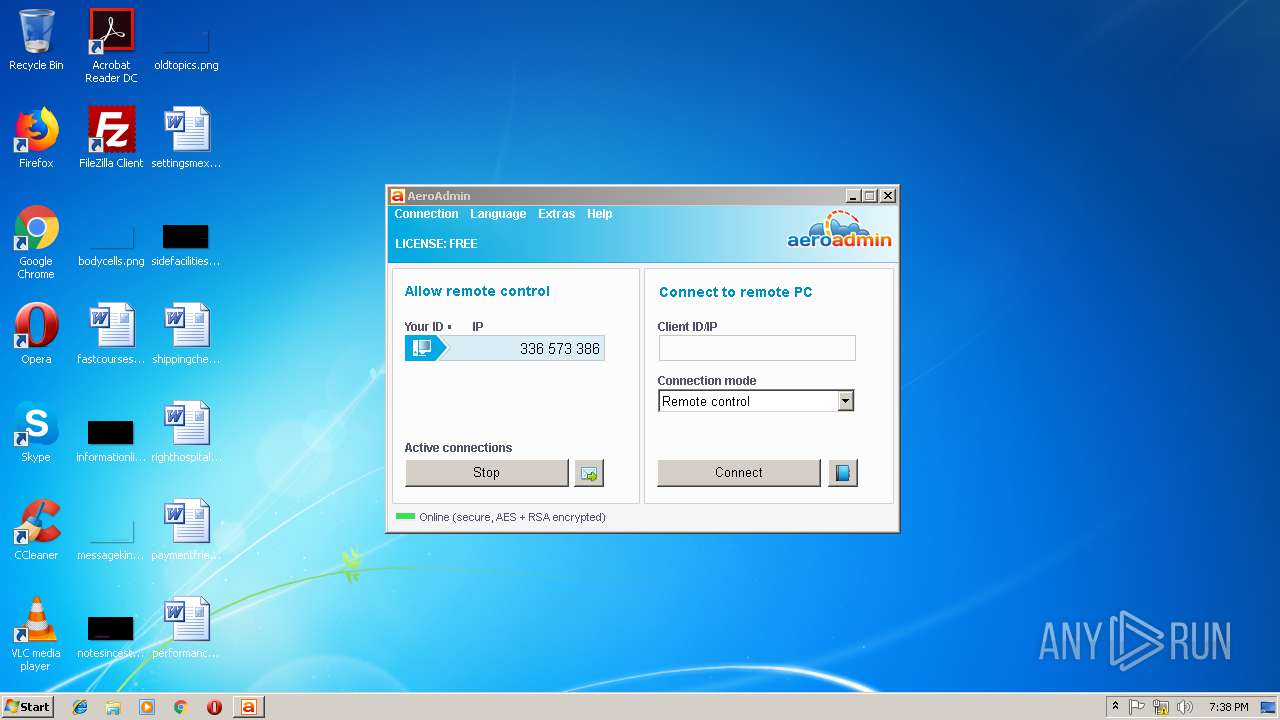
3404 | AeroAdmin.exe | 5.79.97.62:443 | auth11.aeroadmin.com | LeaseWeb Netherlands B.V. | NL | suspicious |
3404 | AeroAdmin.exe | 95.211.205.66:443 | — | LeaseWeb Netherlands B.V. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
auth11.aeroadmin.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
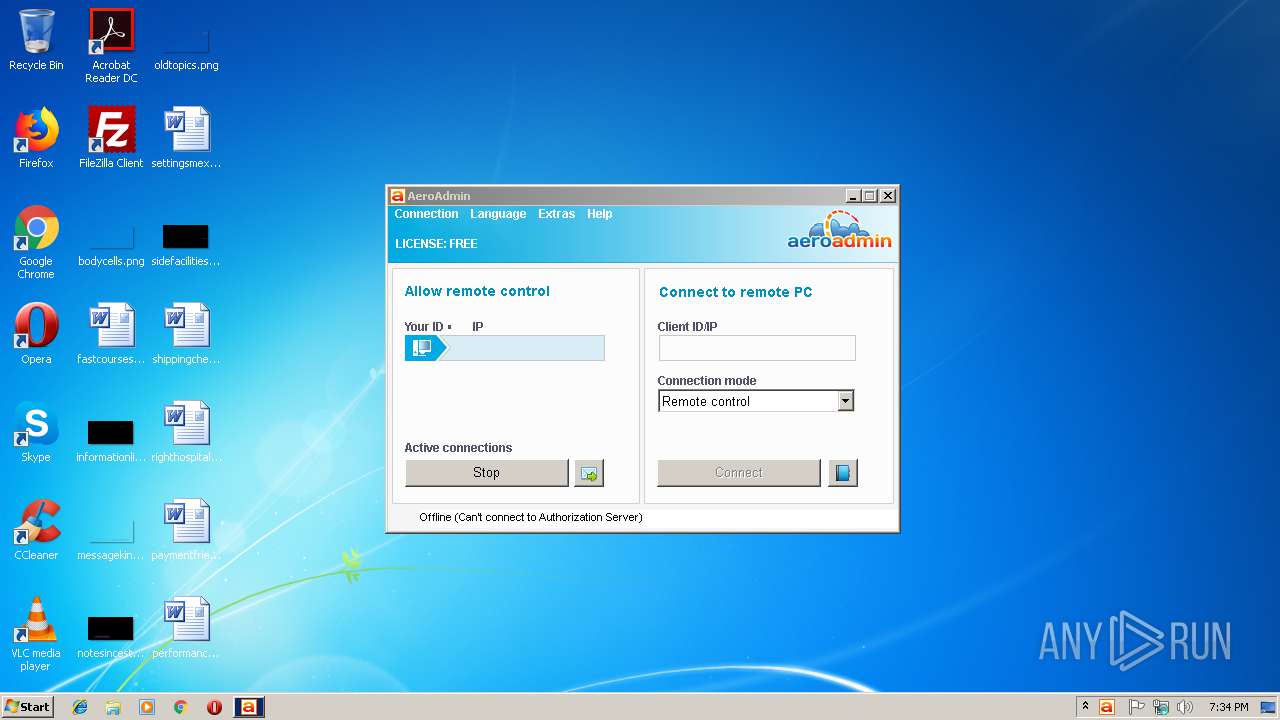
3404 | AeroAdmin.exe | Potential Corporate Privacy Violation | ET POLICY PTsecurity Remote Desktop AeroAdmin Server Hello |
3404 | AeroAdmin.exe | A Network Trojan was detected | MALWARE [PTsecurity] Remote Desktop AeroAdmin Server Hello |
3404 | AeroAdmin.exe | Generic Protocol Command Decode | SURICATA Applayer Wrong direction first Data |
3404 | AeroAdmin.exe | Potential Corporate Privacy Violation | ET POLICY PTsecurity Remote Desktop AeroAdmin handshake |
3404 | AeroAdmin.exe | A Network Trojan was detected | MALWARE [PTsecurity] Remote Desktop AeroAdmin handshake |
3404 | AeroAdmin.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore/NetWire.RAT |
3404 | AeroAdmin.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore/NetWire.RAT |
3404 | AeroAdmin.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore/NetWire.RAT |
3404 | AeroAdmin.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore/NetWire.RAT |
3404 | AeroAdmin.exe | A Network Trojan was detected | MALWARE [PTsecurity] NanoCore/NetWire.RAT |
Process | Message |
|---|---|
AeroAdmin.exe | 20190128 19:34:54 [3148 / aeroadmin\aeroadmin.cpp:1140] Build#: 3055, mode: , sessid: 1, ARGS: "C:\Users\admin\AppData\Local\Temp\AeroAdmin.exe" , selected
|
AeroAdmin.exe | 20190128 19:34:54 [3148 / aeroadmin\aeroadmin.cpp:1149] Windows ver. 6.1, build# 7601, SP: Service Pack 1, platform id: 2, suite: 256, type: 1
|
AeroAdmin.exe | 20190128 19:34:54 [3148 / aeroadmin\service.cpp:670] return fIsRunAsAdmin == TRUE0
|
AeroAdmin.exe | 20190128 19:34:55 [3148 / aeroadmin\service.cpp:692] RestartAsAdmin: z , res = 1
|
AeroAdmin.exe | 20190128 19:34:55 [3380 / aeroadmin\aeroadmin.cpp:1140] Build#: 3055, mode: z, sessid: 1, ARGS: "C:\Users\admin\AppData\Local\Temp\AeroAdmin.exe" z z , selected
|
AeroAdmin.exe | 20190128 19:34:55 [3380 / aeroadmin\aeroadmin.cpp:1149] Windows ver. 6.1, build# 7601, SP: Service Pack 1, platform id: 2, suite: 256, type: 1
|
AeroAdmin.exe | 20190128 19:34:55 [3380 / aeroadmin\service.cpp:670] return fIsRunAsAdmin == TRUE1
|
AeroAdmin.exe | 20190128 19:34:55 [3380 / aeroadmin\service.cpp:542] REMOVE SERVICE
|
AeroAdmin.exe | 20190128 19:34:55 [3380 / aeroadmin\service.cpp:556] !hService
|
AeroAdmin.exe | 20190128 19:34:55 [3380 / aeroadmin\aeroadmin.cpp:930] Elevate: start service as s -sid 1
|