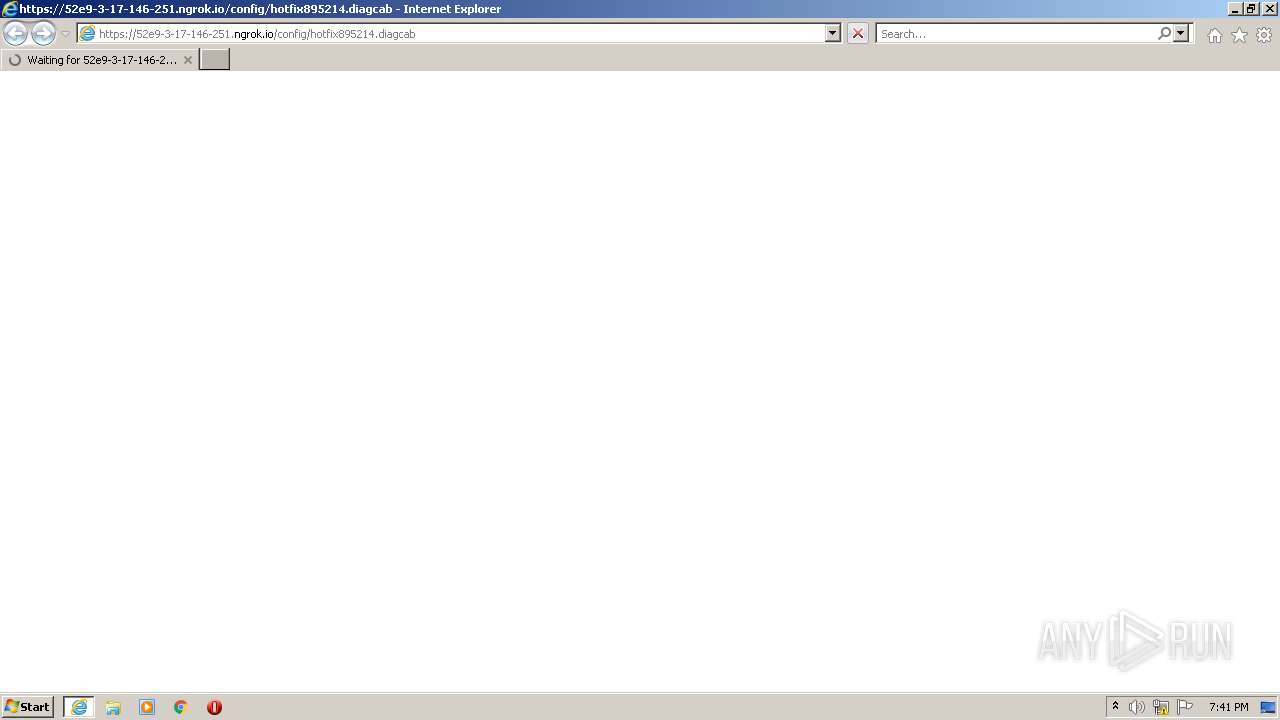
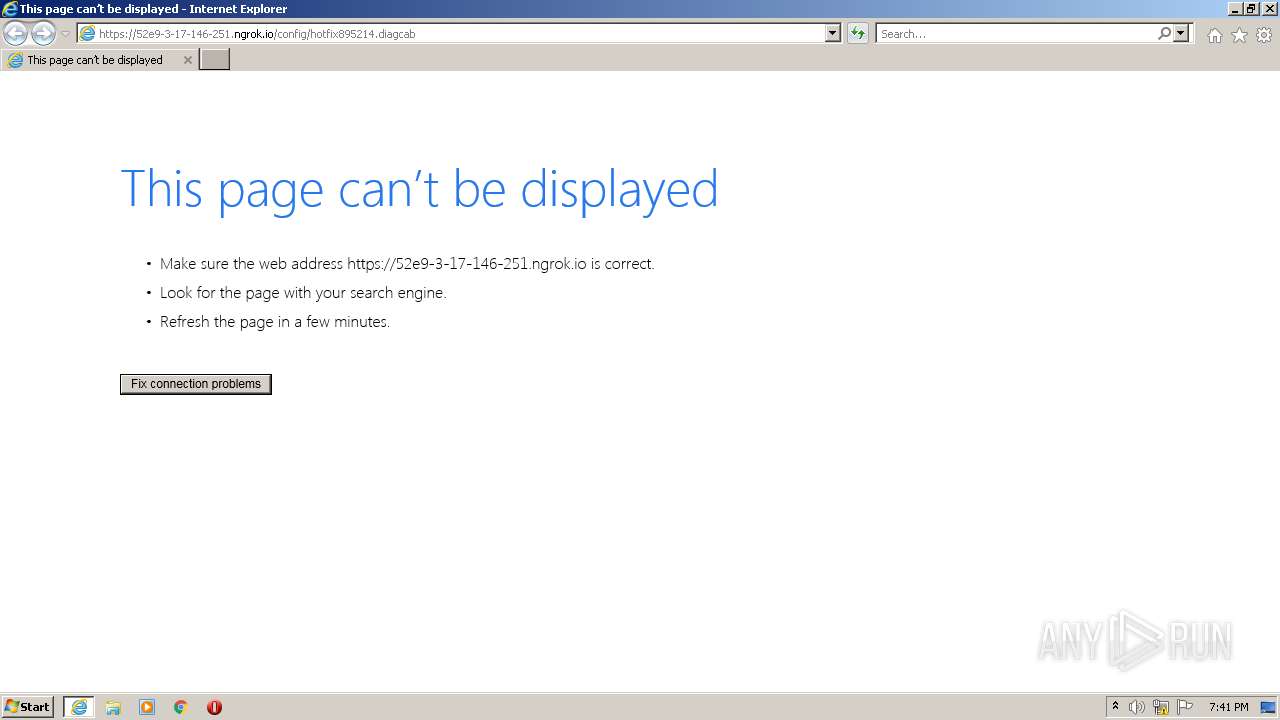
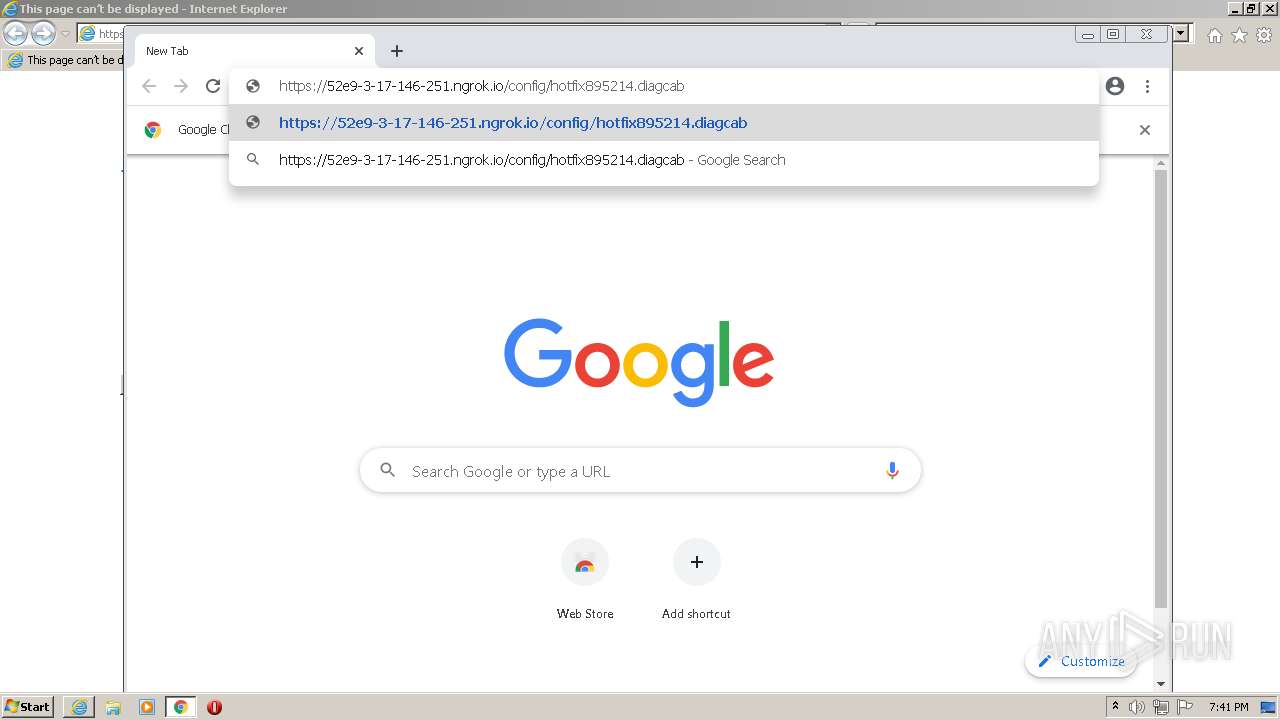
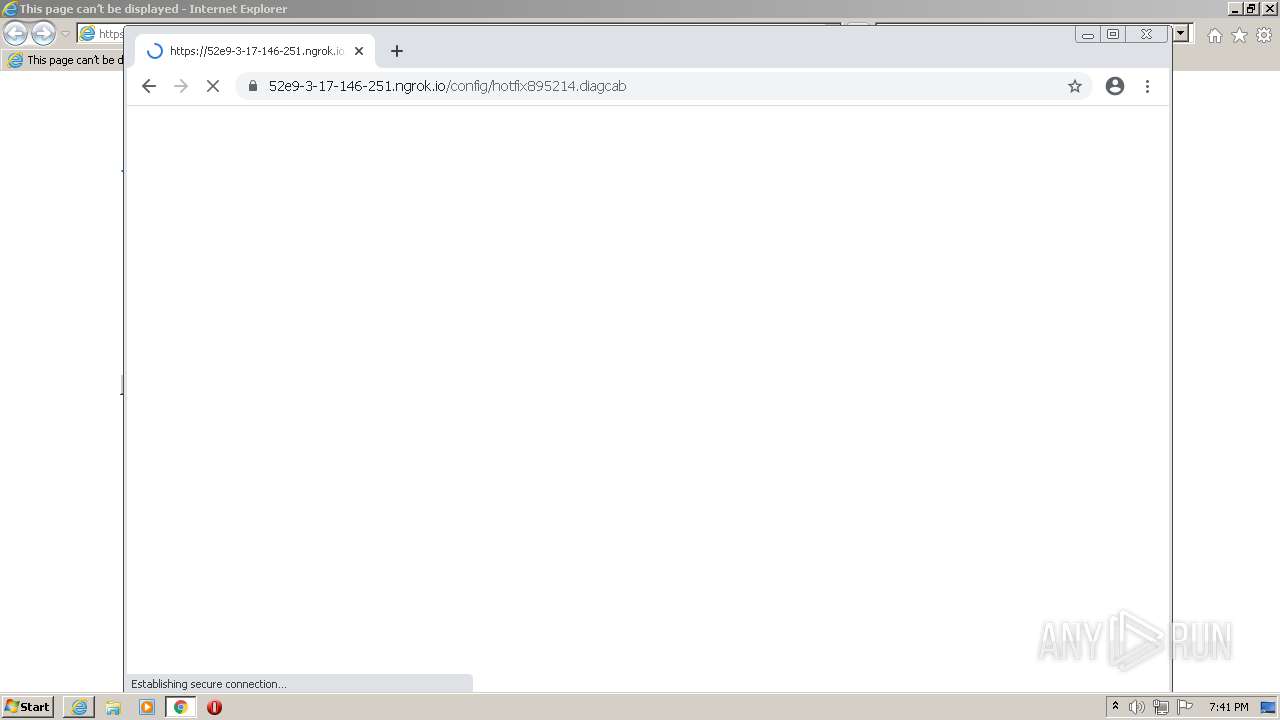
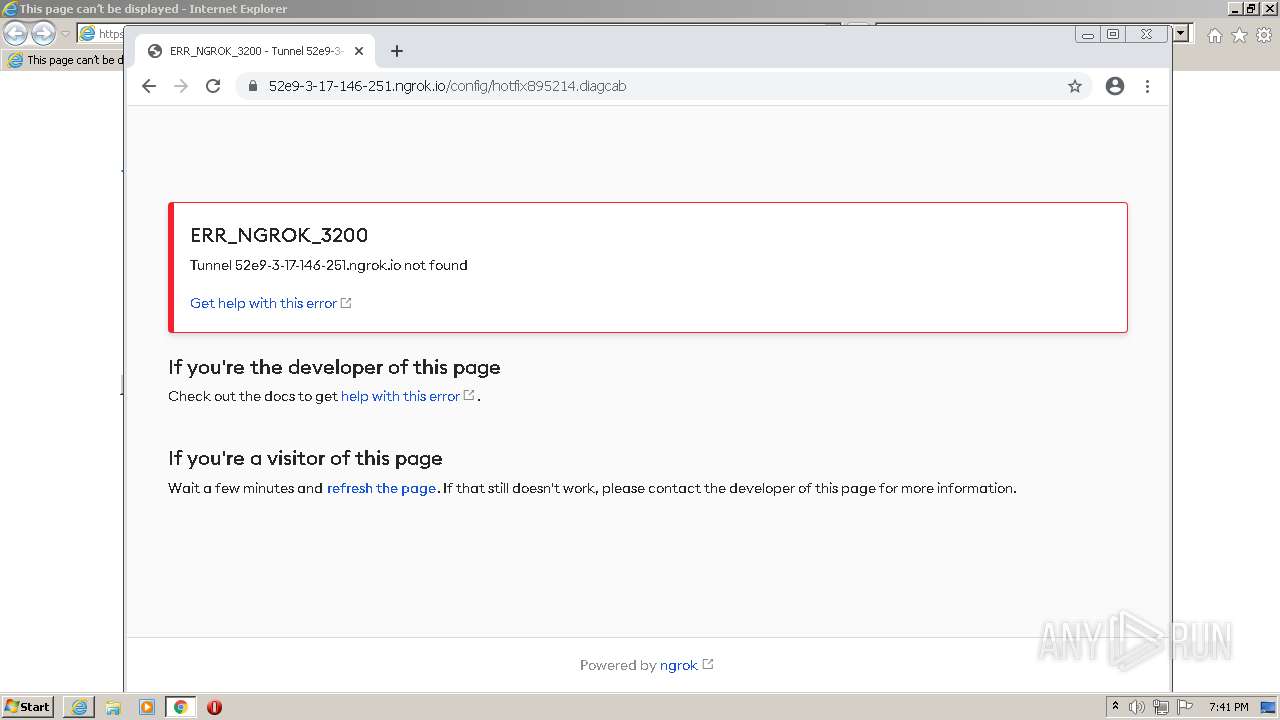
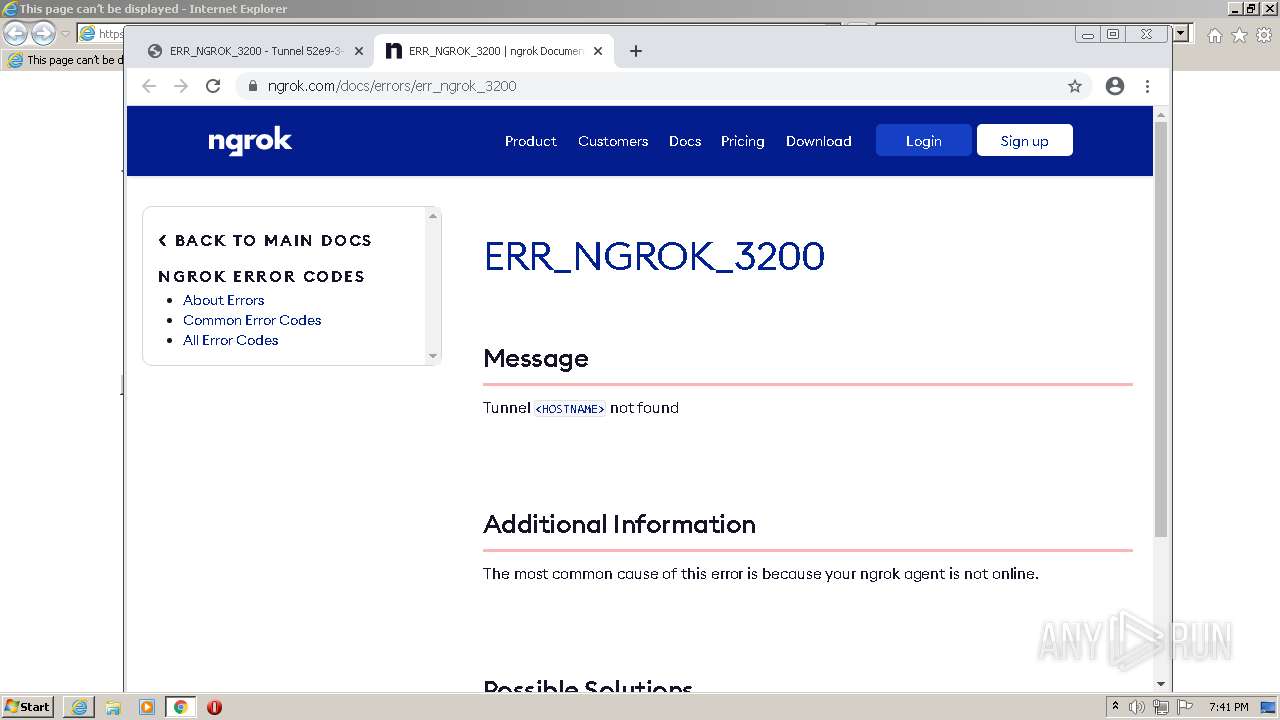
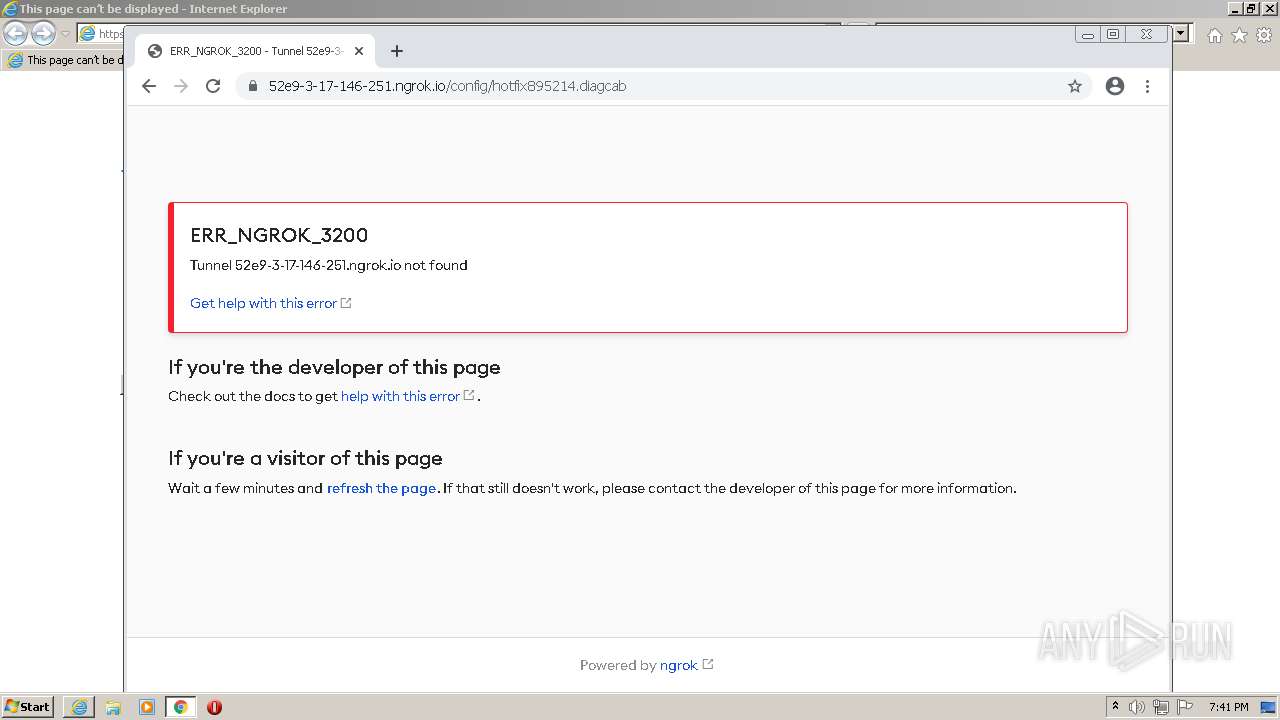
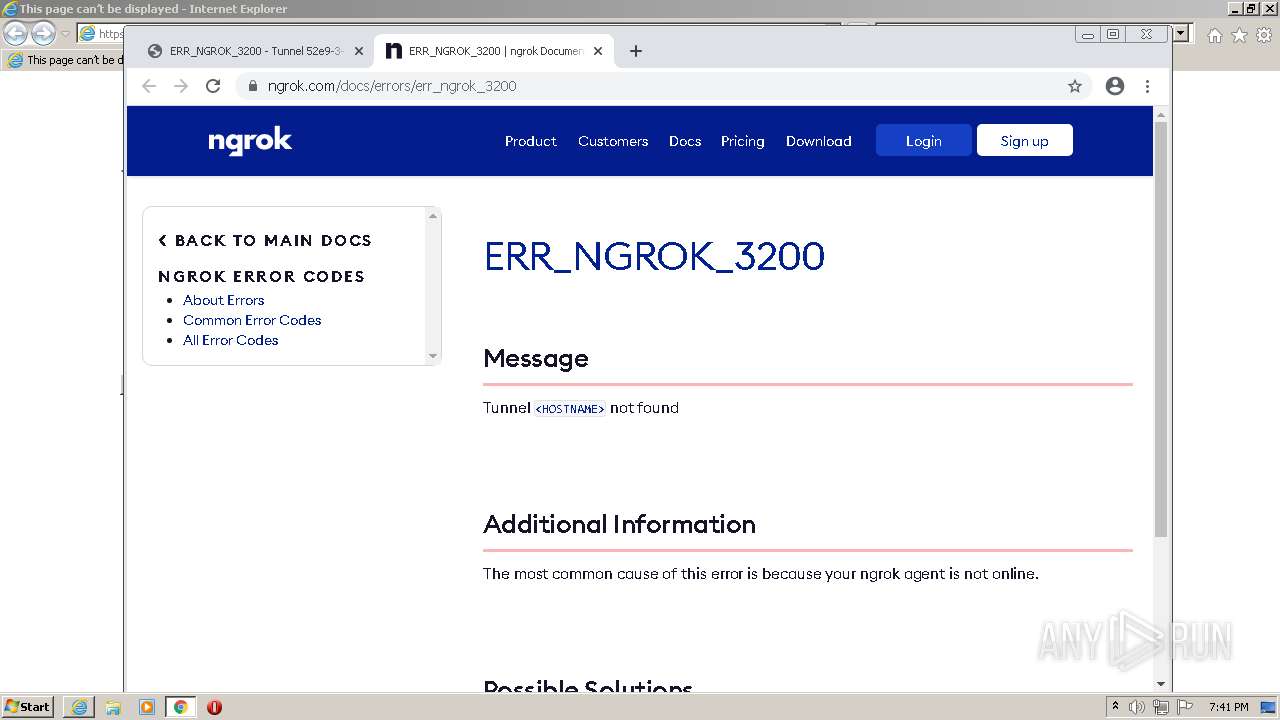
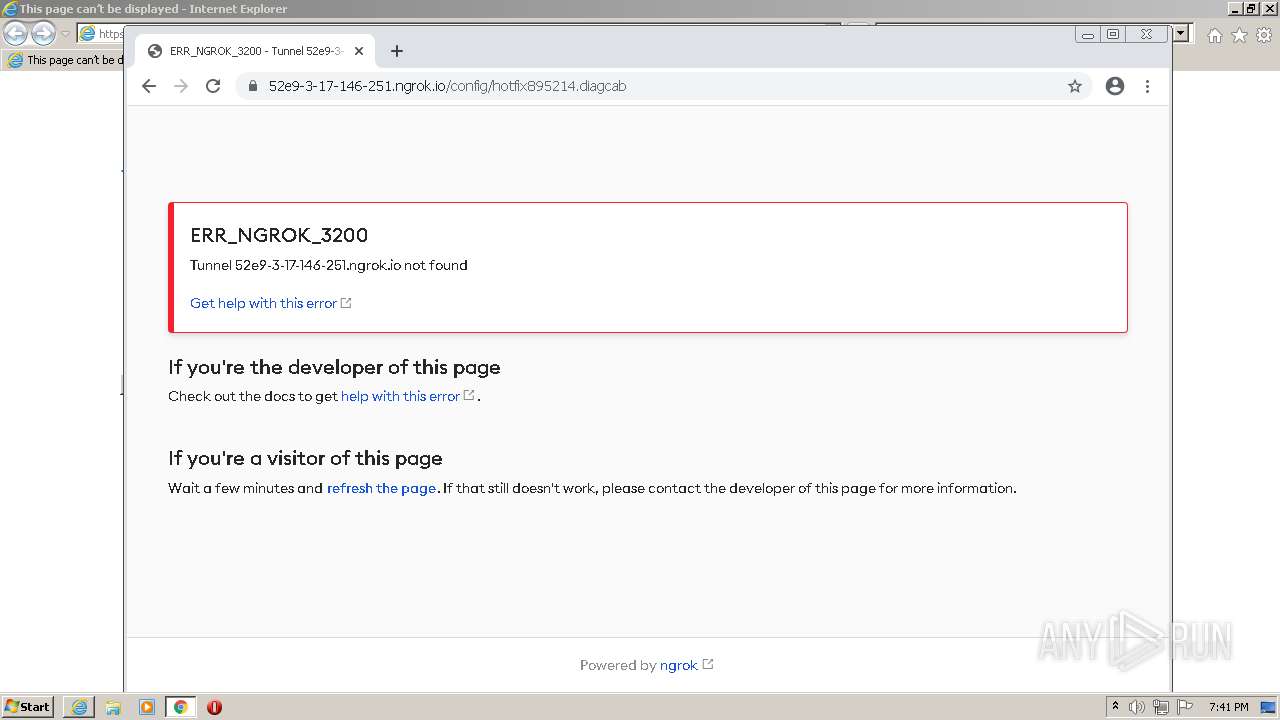
| URL: | https://52e9-3-17-146-251.ngrok.io/config/hotfix895214.diagcab |
| Full analysis: | https://app.any.run/tasks/77f18536-f527-439d-b10a-bea44ceb0ec6 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 18:40:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B2CBFBFB9768D60A5DEE39500C882AA0 |
| SHA1: | 5221932B323AF401A8A1245E79962FF34928CF90 |
| SHA256: | C5D28FB0DD91450EFA5127645D6DE638E94A8852E4FCA1E1024A91ECC1F45A64 |
| SSDEEP: | 3:N8obSI3xJXWhdeCUzMECGu:2oJJXkdTEFu |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3656)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3040)
INFO
Reads the computer name
- iexplore.exe (PID: 3136)
- iexplore.exe (PID: 3040)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 3924)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 2824)
- chrome.exe (PID: 384)
- chrome.exe (PID: 2520)
Checks supported languages
- chrome.exe (PID: 3924)
- iexplore.exe (PID: 3136)
- iexplore.exe (PID: 3040)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 2772)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 2824)
- chrome.exe (PID: 1620)
- chrome.exe (PID: 2476)
- chrome.exe (PID: 384)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 1732)
- chrome.exe (PID: 2580)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 3864)
- chrome.exe (PID: 3588)
- chrome.exe (PID: 3212)
- chrome.exe (PID: 2520)
Changes internet zones settings
- iexplore.exe (PID: 3136)
Application launched itself
- iexplore.exe (PID: 3136)
- chrome.exe (PID: 3656)
Checks Windows Trust Settings
- iexplore.exe (PID: 3040)
- iexplore.exe (PID: 3136)
Reads internet explorer settings
- iexplore.exe (PID: 3040)
Reads settings of System Certificates
- chrome.exe (PID: 2608)
- iexplore.exe (PID: 3040)
- iexplore.exe (PID: 3136)
Manual execution by user
- chrome.exe (PID: 3656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
18
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,8979277605227876193,12116138584574832300,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3424 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,8979277605227876193,12116138584574832300,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,8979277605227876193,12116138584574832300,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2368 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,8979277605227876193,12116138584574832300,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1324 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,8979277605227876193,12116138584574832300,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,8979277605227876193,12116138584574832300,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2468 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,8979277605227876193,12116138584574832300,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3416 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1028,8979277605227876193,12116138584574832300,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3224 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1028,8979277605227876193,12116138584574832300,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1332 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,8979277605227876193,12116138584574832300,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1924 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
30 621
Read events
30 449
Write events
171
Delete events
1
Modification events
| (PID) Process: | (3136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 318889936 | |||
| (PID) Process: | (3136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30977659 | |||
| (PID) Process: | (3136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 619054936 | |||
| (PID) Process: | (3136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30977659 | |||
| (PID) Process: | (3136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3136) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
142
Text files
102
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3656 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62F69ECC-E48.pma | — | |
MD5:— | SHA256:— | |||
| 3040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 3040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3040 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab523F.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3040 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar5240.tmp | cat | |
MD5:— | SHA256:— | |||
| 3040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\092777060E27A68FB6AF81F1E73F8D75 | der | |
MD5:— | SHA256:— | |||
| 3040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3040 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar5242.tmp | cat | |
MD5:— | SHA256:— | |||
| 3040 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab5241.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
70
DNS requests
36
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3136 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2608 | chrome.exe | GET | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 555 b | whitelisted |
3040 | iexplore.exe | GET | 200 | 2.16.186.27:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgTc5ZEkl965TtOX%2FLNW%2BcqOeA%3D%3D | unknown | der | 503 b | shared |
3040 | iexplore.exe | GET | 200 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b69629de045079c7 | US | compressed | 60.2 Kb | whitelisted |
3136 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
3040 | iexplore.exe | GET | 200 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?67709163b41400a0 | US | compressed | 4.70 Kb | whitelisted |
2608 | chrome.exe | GET | 200 | 74.125.111.106:80 | http://r5---sn-hpa7znz6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=45.134.22.248&mm=28&mn=sn-hpa7znz6&ms=nvh&mt=1660329001&mv=u&mvi=5&pl=24&rmhost=r2---sn-hpa7znz6.gvt1.com&shardbypass=sd | US | crx | 242 Kb | whitelisted |
3040 | iexplore.exe | GET | 200 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?665f022b31d5f029 | US | compressed | 4.70 Kb | whitelisted |
3040 | iexplore.exe | GET | 200 | 96.16.145.230:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
3040 | iexplore.exe | GET | 200 | 67.27.233.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0cd4c6d2bf5f1b52 | US | compressed | 60.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3040 | iexplore.exe | 3.134.39.220:443 | 52e9-3-17-146-251.ngrok.io | — | US | shared |
3040 | iexplore.exe | 67.27.233.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3136 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3040 | iexplore.exe | 96.16.145.230:80 | x1.c.lencr.org | Akamai Technologies, Inc. | US | suspicious |
3040 | iexplore.exe | 2.16.186.27:80 | r3.o.lencr.org | Akamai International B.V. | — | whitelisted |
2608 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3136 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2608 | chrome.exe | 142.250.186.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2608 | chrome.exe | 142.250.186.36:443 | www.google.com | Google Inc. | US | whitelisted |
2608 | chrome.exe | 142.250.186.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
52e9-3-17-146-251.ngrok.io |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r3.o.lencr.org |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
— | — | Potential Corporate Privacy Violation | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query to a *.ngrok domain (ngrok.com) |