| File name: | Nitro gen.exe |
| Full analysis: | https://app.any.run/tasks/59755c4d-ee25-4b90-82b9-d7831fbe4870 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 21:31:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9578BC4D3BDD4024CD4B4DF058E6DF6F |
| SHA1: | 9D65693CD453C4CF0894FE3996560A1C215A2624 |
| SHA256: | C5C520DDAB03218E12F862AE0F4E2D1DE9B497EF20BC0E48EACBC96B8CE79E0D |
| SSDEEP: | 196608:8uF1AMxAsmBXGYPtbYPvbJQlHmZu8CFCTv69Y/aY:lF1YNGYPkJQlGDTv6S/ |
MALICIOUS
Loads dropped or rewritten executable
- Nitro gen.exe (PID: 3468)
SUSPICIOUS
Application launched itself
- Nitro gen.exe (PID: 3764)
Loads Python modules
- Nitro gen.exe (PID: 3468)
Executable content was dropped or overwritten
- Nitro gen.exe (PID: 3764)
INFO
Dropped object may contain Bitcoin addresses
- Nitro gen.exe (PID: 3764)
Manual execution by user
- explorer.exe (PID: 3836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (50.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (32.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.6) |
| .exe | | | Win32 Executable (generic) (5.2) |
| .exe | | | Generic Win/DOS Executable (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:05 13:16:35+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 126976 |
| InitializedDataSize: | 173568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7cd3 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Jan-2020 12:16:35 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 05-Jan-2020 12:16:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001EE04 | 0x0001F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64212 |
.rdata | 0x00020000 | 0x0000B206 | 0x0000B400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.06574 |
.data | 0x0002C000 | 0x0000E688 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.92321 |
.gfids | 0x0003B000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.82374 |
.rsrc | 0x0003C000 | 0x0000EEC8 | 0x0000F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.51705 |
.reloc | 0x0004B000 | 0x000017B4 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65769 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 6.15653 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 6.44895 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.77742 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.95095 | 38188 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 6.0521 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 6.15081 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 6.39466 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
USER32.dll |
WS2_32.dll |
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3468 | "C:\Users\admin\AppData\Local\Temp\Nitro gen.exe" | C:\Users\admin\AppData\Local\Temp\Nitro gen.exe | Nitro gen.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3764 | "C:\Users\admin\AppData\Local\Temp\Nitro gen.exe" | C:\Users\admin\AppData\Local\Temp\Nitro gen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
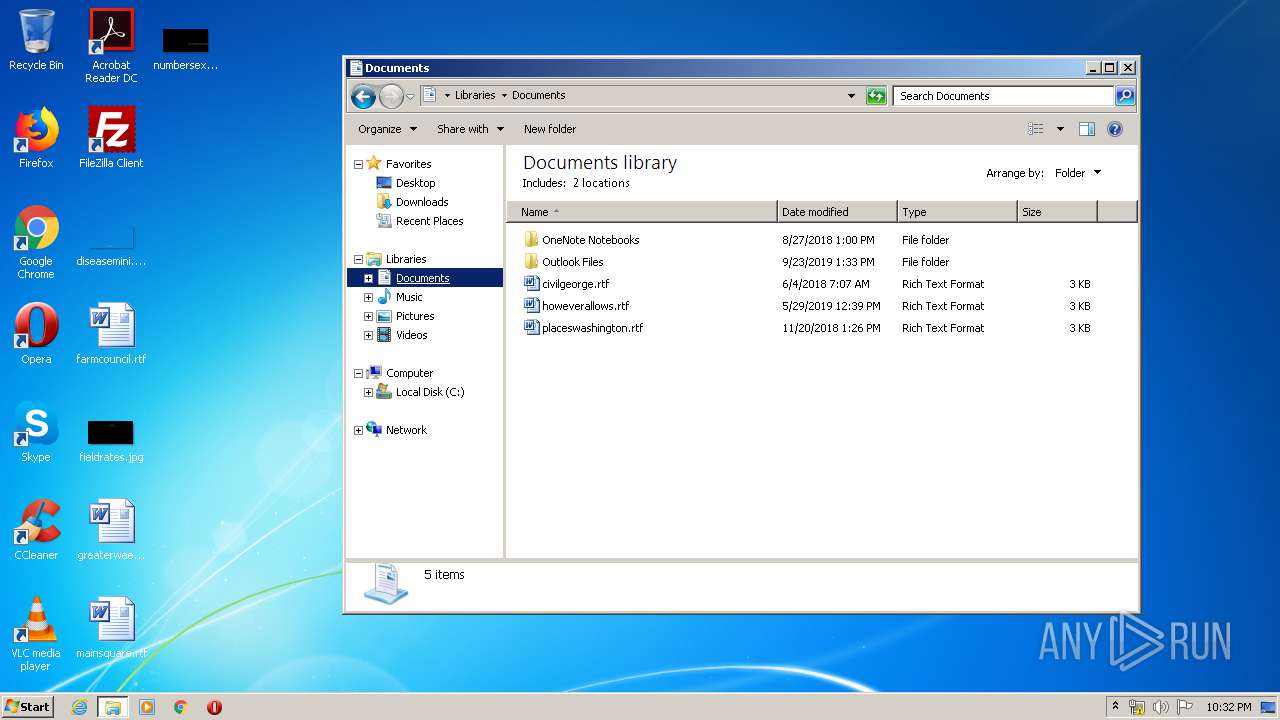
| 3836 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
35
Read events
35
Write events
0
Delete events
0
Modification events
Executable files
26
Suspicious files
3
Text files
916
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3764 | Nitro gen.exe | C:\Users\admin\AppData\Local\Temp\_MEI37642\Preimenuj.exe.manifest | xml | |
MD5:— | SHA256:— | |||
| 3764 | Nitro gen.exe | C:\Users\admin\AppData\Local\Temp\_MEI37642\_bz2.pyd | executable | |
MD5:1C7F3F37A067019B7926C0F92F3A3AA7 | SHA256:BBC7F102B547180EA8CA5FF496F1BD419BFEFD360BE15610AE6B08837076F5DC | |||
| 3764 | Nitro gen.exe | C:\Users\admin\AppData\Local\Temp\_MEI37642\_hashlib.pyd | executable | |
MD5:AAA99FFB90EC5985BE0FACE4F0A40892 | SHA256:B118B6EF5486A65C41FDF049EF3C30D90F39097B5EF4C0B9F61824ACFDE50B6A | |||
| 3764 | Nitro gen.exe | C:\Users\admin\AppData\Local\Temp\_MEI37642\_lzma.pyd | executable | |
MD5:280C3A7C8C5E5282EC8E746AE685FF54 | SHA256:C6E30F1139D4F2B1EC7A5ACA8563D6F946EE6FFA6A90A4EB066CD867D3384C39 | |||
| 3764 | Nitro gen.exe | C:\Users\admin\AppData\Local\Temp\_MEI37642\_ssl.pyd | executable | |
MD5:8A2EB91CBD839DA8813BB6DC5BD48178 | SHA256:5AD15DBC726D002D356BFD7E6A077F8568FEE463B7CE5F71C33A04B2E11558F1 | |||
| 3764 | Nitro gen.exe | C:\Users\admin\AppData\Local\Temp\_MEI37642\_multiprocessing.pyd | executable | |
MD5:F5BB0B71862C1011DE7660E5E5721846 | SHA256:BC2E196BFB21A3F57CA86E96127B1246D47CDAEEB99F6239AF38165BF42B5117 | |||
| 3764 | Nitro gen.exe | C:\Users\admin\AppData\Local\Temp\_MEI37642\_queue.pyd | executable | |
MD5:8A21A5CCB136E6C265975CE1E91CB870 | SHA256:7F43DFB5BA9F4AFA82630CD3E234EDE0596ABE3584F107B9855747EF1CDE9ACC | |||
| 3764 | Nitro gen.exe | C:\Users\admin\AppData\Local\Temp\_MEI37642\_asyncio.pyd | executable | |
MD5:4E406CBFBFB77D6155B814E9F344165C | SHA256:47998CDEC5D134DD351947D94AD5CA5A234130D22DFF7DAE1A12B8C06DAF2891 | |||
| 3764 | Nitro gen.exe | C:\Users\admin\AppData\Local\Temp\_MEI37642\_tkinter.pyd | executable | |
MD5:1B81683BE893967C0300BA93D65626F2 | SHA256:DF2C5E49D13DAA417CD599C0955AEEA0679543766E5F30F1814B1F8BF9C6435D | |||
| 3764 | Nitro gen.exe | C:\Users\admin\AppData\Local\Temp\_MEI37642\_decimal.pyd | executable | |
MD5:7BC3E402069CAA8AFB04F966E6F2B1CF | SHA256:14A59911E349064E4BE60DCBF3A0E60DC0F4C0EEE2A406B69C9A24DDEE3B60AB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
8
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3468 | Nitro gen.exe | 23.21.213.140:443 | api.ipify.org | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3468 | Nitro gen.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
3468 | Nitro gen.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
3468 | Nitro gen.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
3468 | Nitro gen.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
3468 | Nitro gen.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
3468 | Nitro gen.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
3468 | Nitro gen.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
3468 | Nitro gen.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |