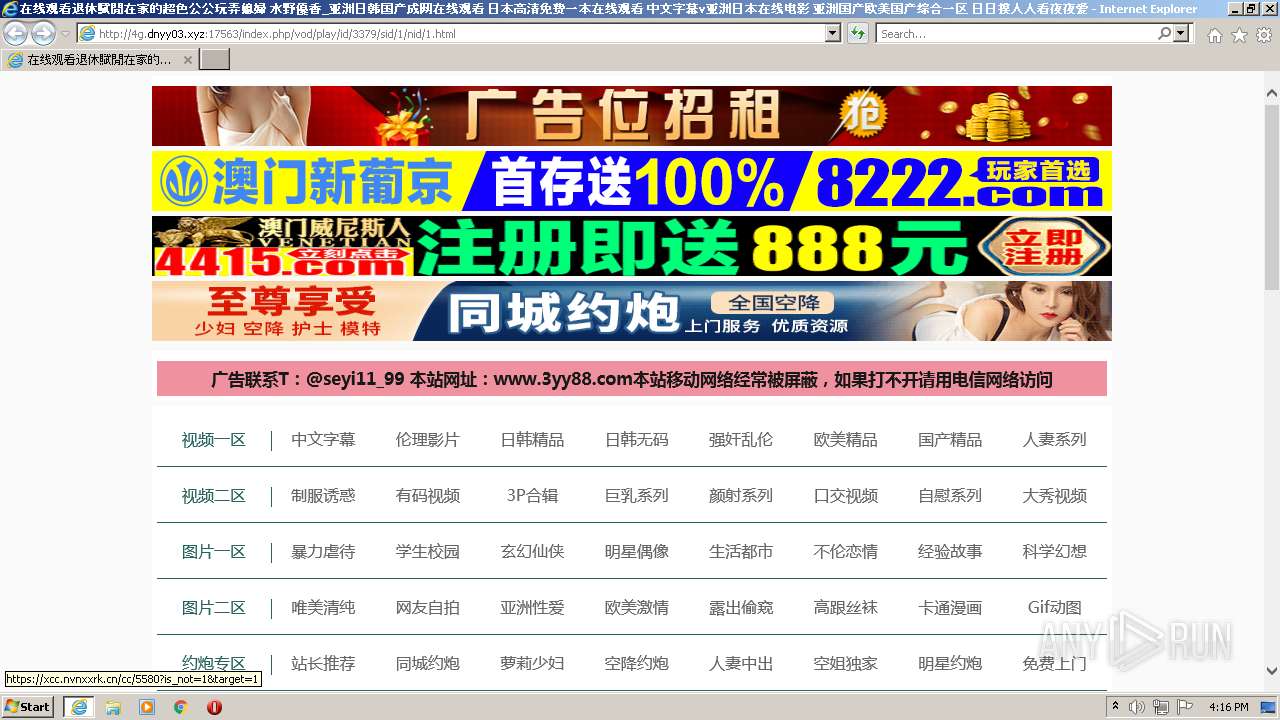
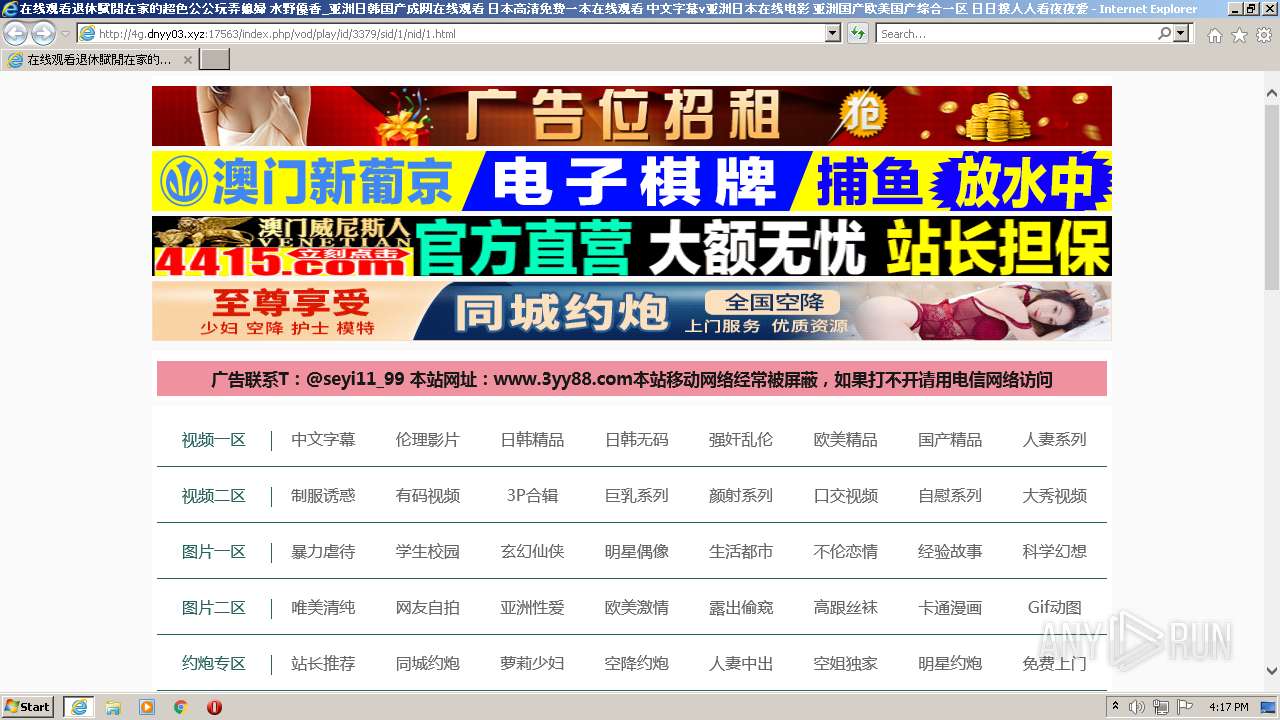
| URL: | http://4g.dnyy03.xyz:17563/index.php/vod/play/id/3379/sid/1/nid/1.html |
| Full analysis: | https://app.any.run/tasks/cf85e89f-5b56-4660-bd8b-fc00e45e030a |
| Verdict: | Malicious activity |
| Analysis date: | May 29, 2022, 15:16:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3664338AAB39D21A7D38C50E53703BA7 |
| SHA1: | B85A0379E4E4C183D942EC603672636FD40E28E1 |
| SHA256: | C5BDE291FF341740FBDB7EB032BB724E7C79C6C51536565C42E8D53EA67229AC |
| SSDEEP: | 3:N1KUcWQLGWKM1AbHIjKIH2eKPp:CUcWQx1AbHIjKIWeKR |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2340)
INFO
Checks supported languages
- iexplore.exe (PID: 3068)
- iexplore.exe (PID: 2340)
Reads the computer name
- iexplore.exe (PID: 3068)
- iexplore.exe (PID: 2340)
Application launched itself
- iexplore.exe (PID: 3068)
Changes internet zones settings
- iexplore.exe (PID: 3068)
Checks Windows Trust Settings
- iexplore.exe (PID: 3068)
- iexplore.exe (PID: 2340)
Reads settings of System Certificates
- iexplore.exe (PID: 2340)
- iexplore.exe (PID: 3068)
Reads internet explorer settings
- iexplore.exe (PID: 2340)
Creates files in the user directory
- iexplore.exe (PID: 2340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2340 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3068 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3068 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://4g.dnyy03.xyz:17563/index.php/vod/play/id/3379/sid/1/nid/1.html" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
15 365
Read events
15 246
Write events
119
Delete events
0
Modification events
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 146026272 | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30962543 | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 446030022 | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30962543 | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3068) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
23
Text files
52
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\xx1[1].js | text | |
MD5:6BF1EBF28BD8068D9B9A2E35BE461089 | SHA256:125AC17C233106EBBE659E35092154BFF48C36E76B5C7AACD90CA35015997CC4 | |||
| 2340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\1[1].htm | html | |
MD5:0E5146F6AA5E042FC309AF05F455B323 | SHA256:03FE00732F85B5514AFD2C725249393C014C90EA323B47EC0EC0D53B0F246D95 | |||
| 2340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\dh[1].js | html | |
MD5:7941D86FC21C5BA2B13FAD77D841B6F0 | SHA256:FC257DBC47DA8BCF68868E0CEF6A41EC11717627CA8206B7B1C317185B88A32C | |||
| 2340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\xx3[1].js | text | |
MD5:1DB74F518B0EE78F69C284CDF767F98B | SHA256:87C0D624BC25BB0FBE546D6F15CB855005FCBF5F74938917E28919E9B5005286 | |||
| 2340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\player[1].js | text | |
MD5:361D93DF6E2E28BE98966163BA21136A | SHA256:BF9A452C2BE87BA506D8138073C0395F712A5602789D36D5337948BF608198E5 | |||
| 2340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\playerconfig[1].js | text | |
MD5:42F7C4D7D741F1B25052DA9F6DE9D700 | SHA256:83FE9C081ECCE46929134ACA5857858C8F37968A661475272F80D8637B325EEA | |||
| 2340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\zui[1].css | text | |
MD5:1E84C8909C4BF95EBEF50CF8F6F01313 | SHA256:CA8B8CC6AAA054D6501F43A8C1E45851D6054262800F34692C86863608B3A225 | |||
| 2340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:308336E7F515478969B24C13DED11EDE | SHA256:889B832323726A9F10AD03F85562048FDCFE20C9FF6F9D37412CF477B4E92FF9 | |||
| 2340 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar6093.tmp | cat | |
MD5:2D8A5090656DE9FB55DD0F3BA20F9299 | SHA256:44AE1E61A4E6305C15AAA52FD1B29DDB060E69233703CBA611F5E781D766442E | |||
| 3068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:9F88B1B38FCBDADDA9F9F879036E9D0F | SHA256:795F640AB1DD3D26A3DE41F90EDD23F79066316A69748E933704CAE28C6B1D39 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
86
DNS requests
34
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2340 | iexplore.exe | GET | 200 | 172.247.112.2:80 | http://172.247.112.2/xx1.js | US | text | 525 b | unknown |
2340 | iexplore.exe | GET | 200 | 172.247.112.6:17563 | http://4g.dnyy03.xyz:17563/index.php/vod/play/id/3379/sid/1/nid/1.html | US | html | 12.6 Kb | suspicious |
2340 | iexplore.exe | GET | 200 | 172.247.112.6:17563 | http://4g.dnyy03.xyz:17563/template/m1938pc/css/ate.css | US | text | 7.98 Kb | suspicious |
2340 | iexplore.exe | GET | 200 | 172.247.112.6:17563 | http://4g.dnyy03.xyz:17563/template/m1938pc/css/zui.css | US | text | 21.3 Kb | suspicious |
2340 | iexplore.exe | GET | 200 | 172.247.112.2:80 | http://172.247.112.2/dh.js | US | html | 554 b | unknown |
2340 | iexplore.exe | GET | 200 | 172.247.112.6:17563 | http://4g.dnyy03.xyz:17563/static/css/home.css | US | text | 6.37 Kb | suspicious |
2340 | iexplore.exe | GET | 200 | 172.247.112.2:80 | http://172.247.112.2/xx2.js | US | text | 282 b | unknown |
2340 | iexplore.exe | GET | 200 | 172.247.112.6:17563 | http://4g.dnyy03.xyz:17563/static/js/jquery.js | US | text | 40.5 Kb | suspicious |
2340 | iexplore.exe | GET | 200 | 172.247.112.6:17563 | http://4g.dnyy03.xyz:17563/static/js/jquery.lazyload.js | US | text | 918 b | suspicious |
2340 | iexplore.exe | GET | 200 | 172.247.112.6:17563 | http://4g.dnyy03.xyz:17563/static/js/home.js | US | text | 11.7 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2340 | iexplore.exe | 172.247.112.6:17563 | 4g.dnyy03.xyz | CloudRadium L.L.C | US | suspicious |
2340 | iexplore.exe | 104.89.32.83:80 | x2.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
2340 | iexplore.exe | 104.90.178.254:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | unknown |
2340 | iexplore.exe | 220.128.218.220:443 | taiwtp1.com | Data Communication Business Group | TW | unknown |
2340 | iexplore.exe | 92.123.195.28:80 | e1.o.lencr.org | Akamai International B.V. | — | suspicious |
2340 | iexplore.exe | 23.224.224.130:443 | vip5.ddyunbo.com | CloudRadium L.L.C | US | unknown |
2340 | iexplore.exe | 20.24.93.66:80 | union.maccms.com | — | US | unknown |
2340 | iexplore.exe | 154.23.245.118:4034 | 1653837395315.dspxxy.com | — | US | unknown |
2340 | iexplore.exe | 154.23.245.118:4011 | 1653837395315.dspxxy.com | — | US | unknown |
2340 | iexplore.exe | 103.235.46.191:443 | hm.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
4g.dnyy03.xyz |
| suspicious |
ddcdn.comtucdncom.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
e1.o.lencr.org |
| whitelisted |
www.3yy88.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2340 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2340 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2340 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2340 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2340 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2340 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2340 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2340 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2340 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2340 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |