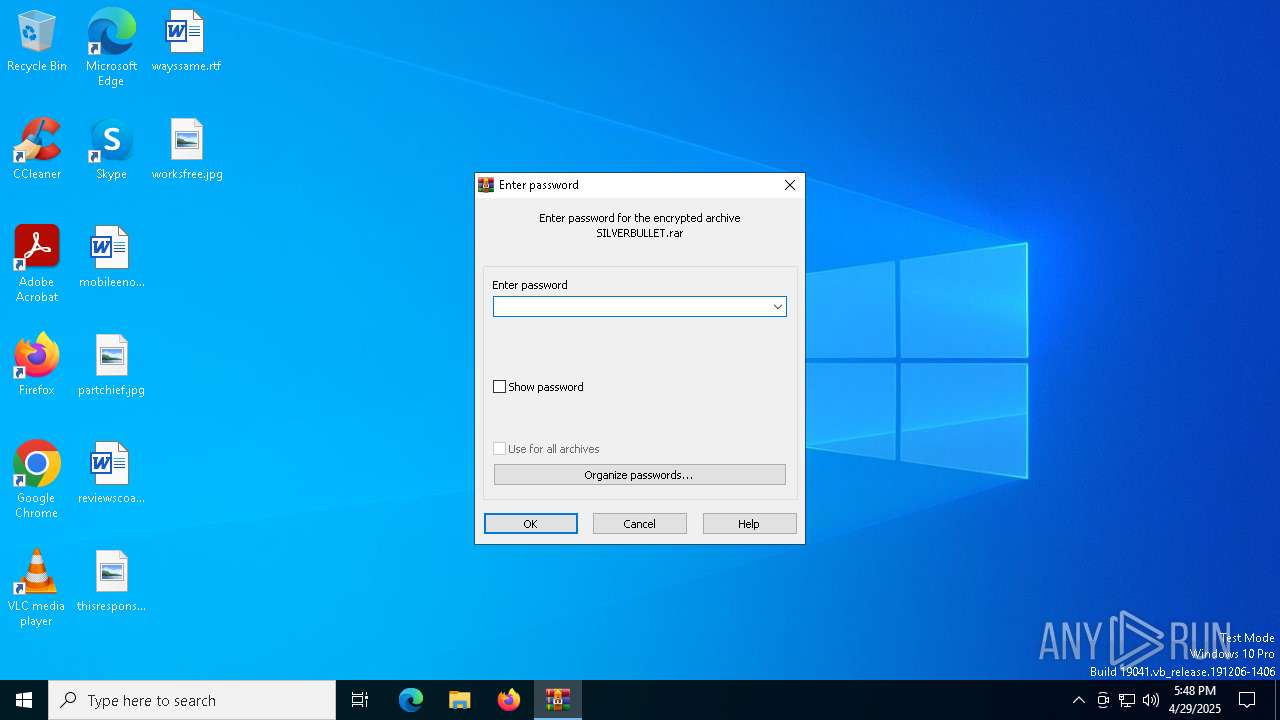
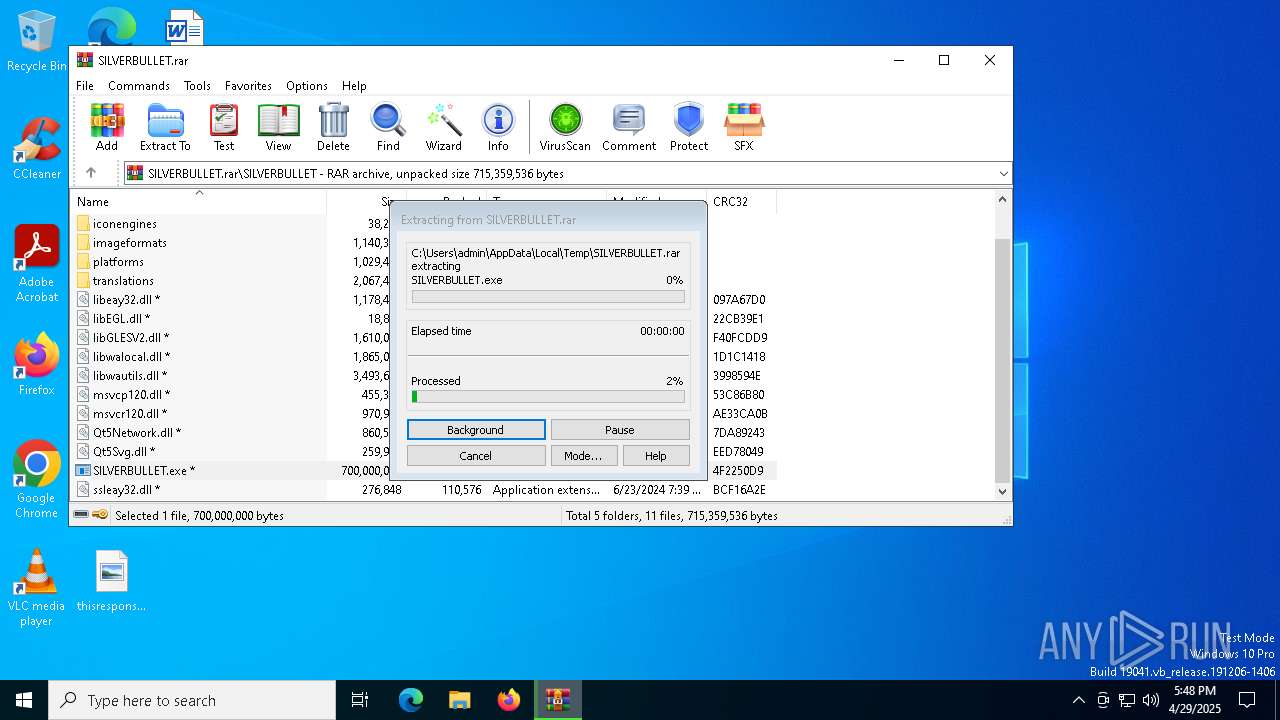
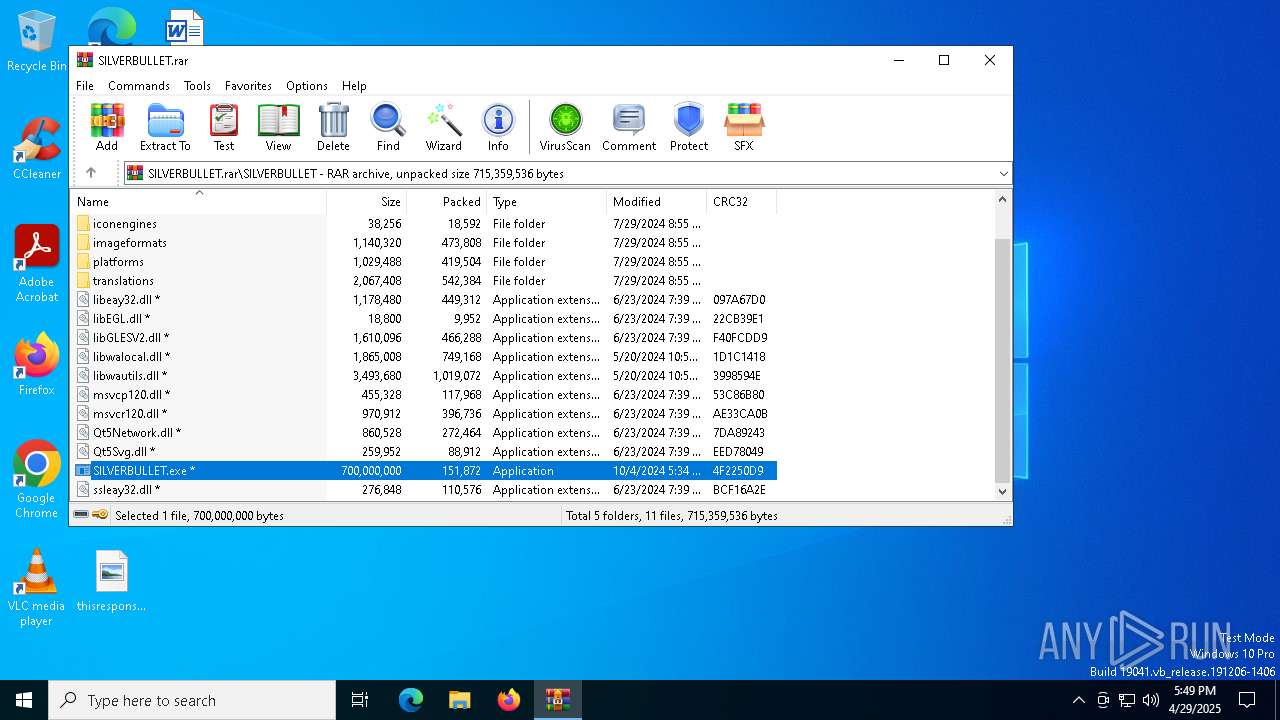
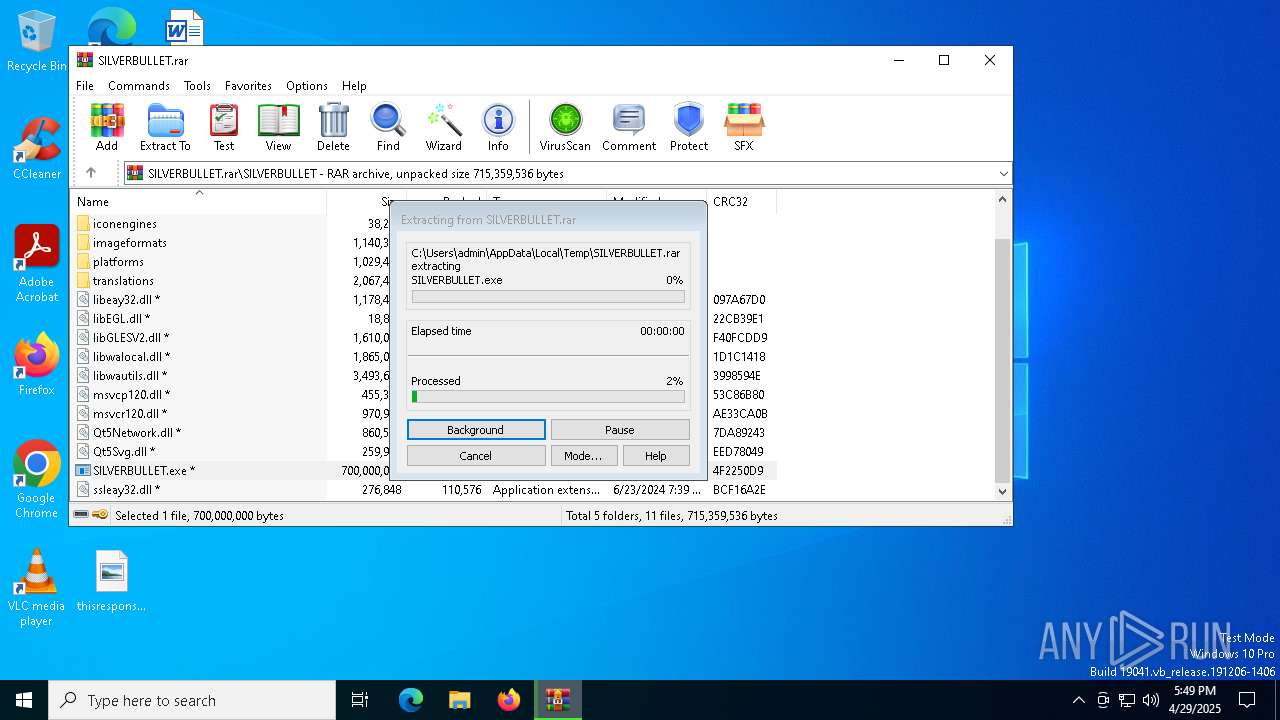
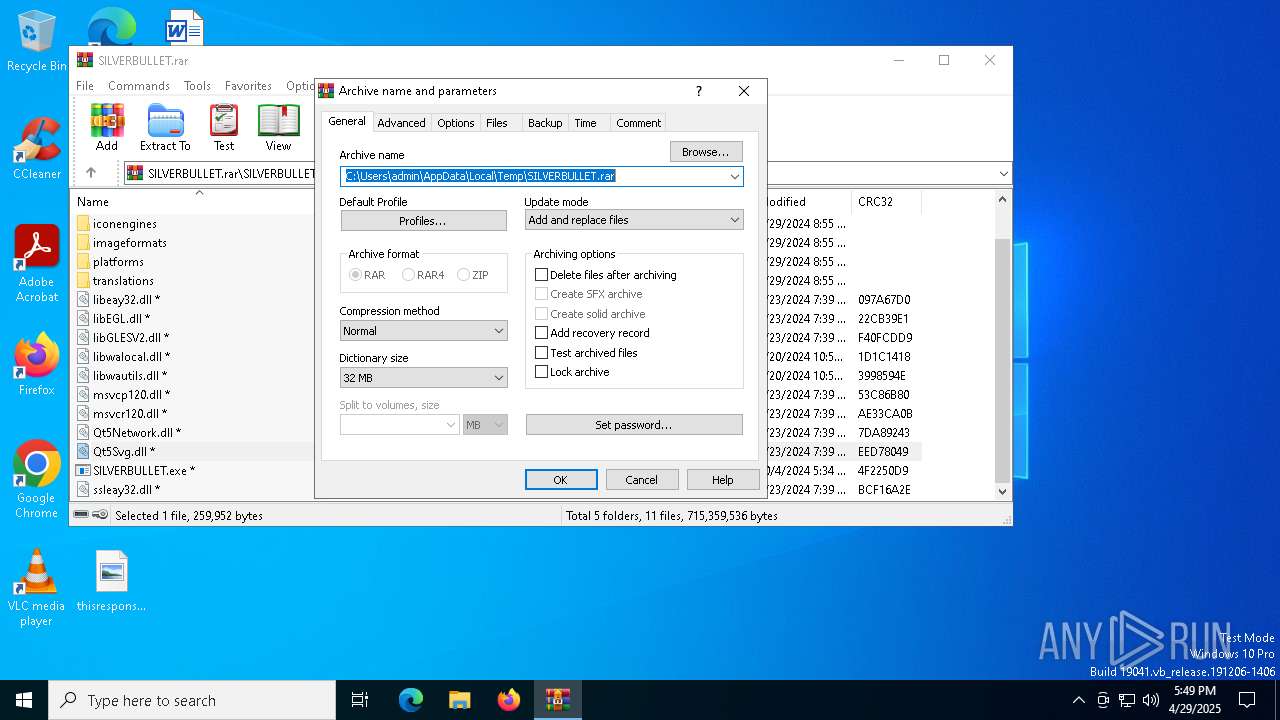
| File name: | SILVERBULLET.rar |
| Full analysis: | https://app.any.run/tasks/62209385-ee8b-49c4-a8b6-422730b22c4c |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 17:48:32 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 6A3C1F83B07FABB38DD766C63807F89D |
| SHA1: | 26095681F6BF4D548F99B40CACC4BC28D388F200 |
| SHA256: | C5B6B9BFD3C87CA972117B696D370B5FB846ACCDAE657D18E8474AD163E245A8 |
| SSDEEP: | 98304:4FEpqJSt2N/pQ62Uiv4LnUUWQT4uJwDR07+bdiM+HMw9iiHSjPHy+9nZsu/JZ9KU:pHujRI9A3xy |
MALICIOUS
Changes Windows Defender settings
- SILVERBULLET.exe (PID: 4188)
- GMCPJO.exe (PID: 5352)
Adds path to the Windows Defender exclusion list
- SILVERBULLET.exe (PID: 4188)
- GMCPJO.exe (PID: 5352)
Uses Task Scheduler to run other applications
- GMCPJO.exe (PID: 5352)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 2384)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2384)
- SILVERBULLET.exe (PID: 668)
- SILVERBULLET.exe (PID: 4188)
- GMCPJO.exe (PID: 5352)
Starts a Microsoft application from unusual location
- SILVERBULLET.exe (PID: 668)
- SILVERBULLET.exe (PID: 4188)
Application launched itself
- SILVERBULLET.exe (PID: 668)
Starts POWERSHELL.EXE for commands execution
- SILVERBULLET.exe (PID: 4188)
- GMCPJO.exe (PID: 5352)
Executing commands from a ".bat" file
- SILVERBULLET.exe (PID: 4188)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7012)
Script adds exclusion path to Windows Defender
- GMCPJO.exe (PID: 5352)
- SILVERBULLET.exe (PID: 4188)
Starts CMD.EXE for commands execution
- SILVERBULLET.exe (PID: 4188)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 2384)
Checks supported languages
- SILVERBULLET.exe (PID: 668)
- SILVERBULLET.exe (PID: 4188)
- GMCPJO.exe (PID: 5352)
Reads the computer name
- SILVERBULLET.exe (PID: 668)
- SILVERBULLET.exe (PID: 4188)
- GMCPJO.exe (PID: 5352)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2384)
Process checks computer location settings
- SILVERBULLET.exe (PID: 668)
- SILVERBULLET.exe (PID: 4188)
- GMCPJO.exe (PID: 5352)
Creates files in the program directory
- SILVERBULLET.exe (PID: 4188)
Create files in a temporary directory
- SILVERBULLET.exe (PID: 4188)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4212)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 1532)
- powershell.exe (PID: 2564)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 4212)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 1532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|
Total processes
148
Monitored processes
19
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2384.23905\SILVERBULLET\SILVERBULLET.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2384.23905\SILVERBULLET\SILVERBULLET.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Logon Application Exit code: 1 Version: 10.0.17134.1 Modules
| |||||||||||||||
| 1040 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath 'C:\ProgramData' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | GMCPJO.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | "C:\Windows\System32\schtasks.exe" /create /sc MINUTE /mo 1 /RL HIGHEST /tn "GMCPJO" /tr C:\ProgramData\trgrttre\GMCPJO.exe /f | C:\Windows\SysWOW64\schtasks.exe | — | GMCPJO.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
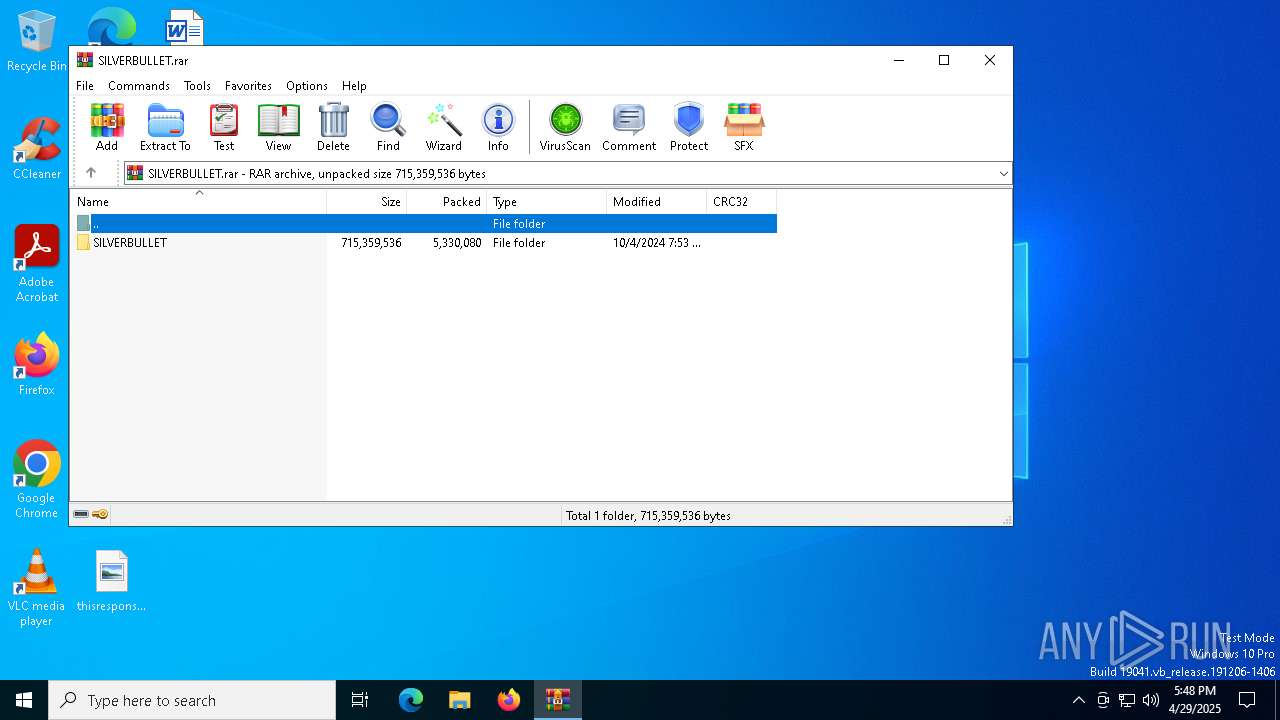
| 2384 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\SILVERBULLET.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2564 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Roaming' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | GMCPJO.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3768 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4152 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4188 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2384.23905\SILVERBULLET\SILVERBULLET.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2384.23905\SILVERBULLET\SILVERBULLET.exe | SILVERBULLET.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Logon Application Exit code: 0 Version: 10.0.17134.1 Modules
| |||||||||||||||
| 4212 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath 'C:\ProgramData' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | SILVERBULLET.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
24 323
Read events
24 314
Write events
9
Delete events
0
Modification events
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\SILVERBULLET.rar | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
25
Suspicious files
16
Text files
17
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
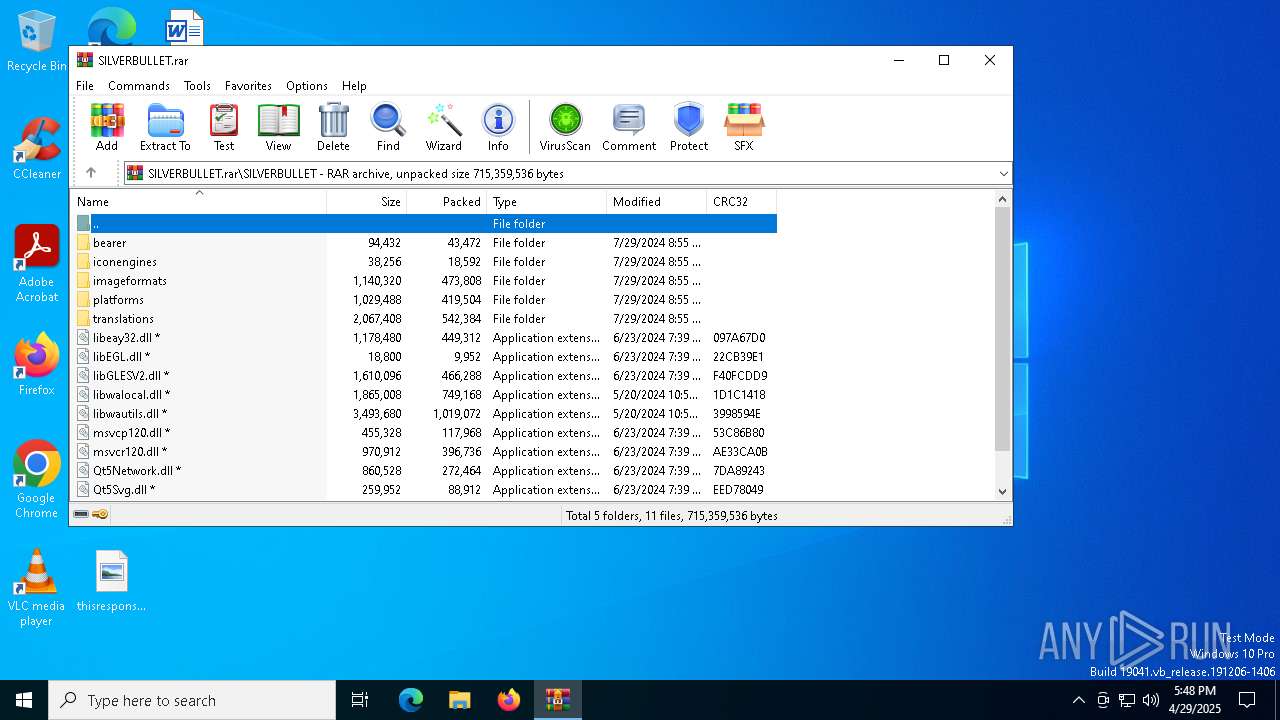
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2384.23905\SILVERBULLET\SILVERBULLET.exe | — | |
MD5:— | SHA256:— | |||
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2384.23905\SILVERBULLET\bearer\qnativewifibearer.dll | executable | |
MD5:A8BCA50F7966F578B127D1E24FC2430F | SHA256:C209D080A62F5E67DDC01A3AE6B4F9B103FAF4104C93B7DBB5FFA8D548BF0CD5 | |||
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2384.23905\SILVERBULLET\imageformats\qjpeg.dll | executable | |
MD5:3232706A63E7CDF217B8ED674179706C | SHA256:45C1F50C922AC1D9D4108E37F49981FD94F997667E23085CB2EA226D406C5602 | |||
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2384.23905\SILVERBULLET\imageformats\qgif.dll | executable | |
MD5:C108D79D7C85786F33F85041445F519F | SHA256:D5459A707922DD2BF50114CC6718965173EE5B0F67DEB05E933556150CFDD9D1 | |||
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2384.23905\SILVERBULLET\imageformats\qdds.dll | executable | |
MD5:3FDB8D8407CCCFAA0290036CC0107906 | SHA256:3A71A119EEABCE867B57636070ADEB057443A6EC262BE1360F344CB3905545DB | |||
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2384.23905\SILVERBULLET\imageformats\qsvg.dll | executable | |
MD5:2831B334B8EDF842CE273B3DD0ACE1F8 | SHA256:6BAE9AF6A7790FBDEE87B7EFA53D31D8AFF0AB49BDAAEFD3FB87A8CC7D4E8A90 | |||
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2384.23905\SILVERBULLET\imageformats\qtiff.dll | executable | |
MD5:756D047A93D72771578286E621585ED2 | SHA256:F9EBF4C98C1E0179CD76A1985386928FDB9E6F459E2238ED5530D160DF4F0923 | |||
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2384.23905\SILVERBULLET\imageformats\qico.dll | executable | |
MD5:EDDF7FB99F2FCAEA6FE4FD34B8FD5D39 | SHA256:9D942215A80A25E10EE1A2BB3D7C76003642D3A2D704C38C822E6A2CA82227BF | |||
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2384.23905\SILVERBULLET\bearer\qgenericbearer.dll | executable | |
MD5:DBA35D31C2B6797C8A4D38AE27D68E6E | SHA256:086D6BA24F34A269856C4E0159A860657590D05AABB2530247E685543B34C52F | |||
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2384.23905\SILVERBULLET\imageformats\qwebp.dll | executable | |
MD5:F859ECC883476FE2C649CEFBBD7E6F94 | SHA256:B057C49C23C6EBE92E377B573723D9B349A6EDE50CFD3B86573B565BF4A2AE0B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.21:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5380 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
5380 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.21:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |