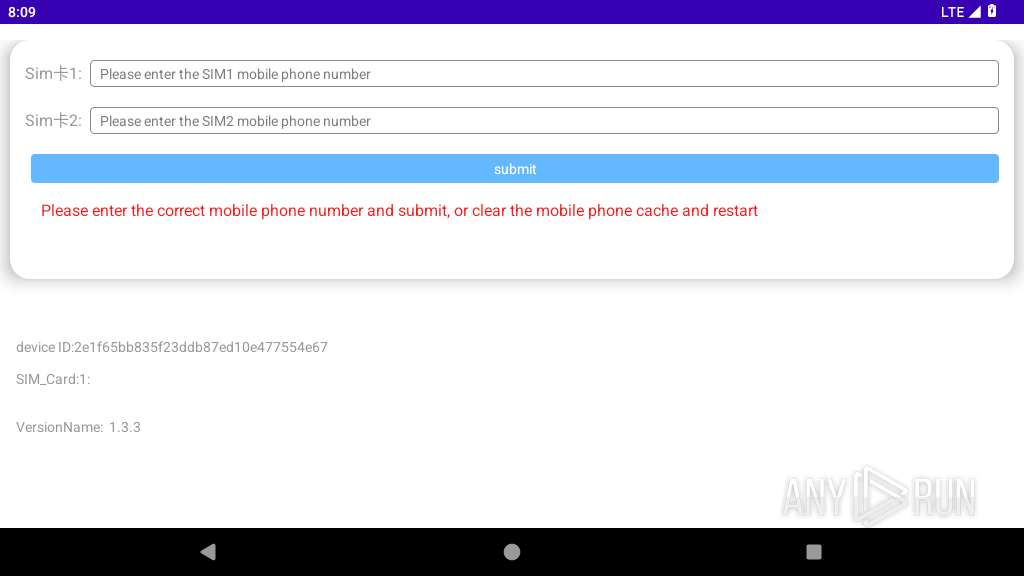
| File name: | util.apk |
| Full analysis: | https://app.any.run/tasks/e7b72552-98c2-4302-8b3e-e6b4086c10ec |
| Verdict: | Malicious activity |
| Analysis date: | September 17, 2025, 20:09:33 |
| OS: | Android 14 |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with zipflinger virtual entry |
| MD5: | D79DE26932A230A00C852CAFE079B4CC |
| SHA1: | 46AFD7DA7F5B40E3A45DA7D2B55E41C4F2E0526A |
| SHA256: | C5B66D381050D0122171BE80D52A64D2EAFB9BA7108C73821CA0E7D9E4D150CF |
| SSDEEP: | 98304:P2+vmSQP1zwnmj7IX/Fc7h5gU9hDsD5bSJott5YK83/yr6it8Hldz8J6imnUXhHd:4zpLuAQ95+b8onhhbR4 |
MALICIOUS
Checks whether the screen is currently on
- app_process64 (PID: 2798)
SUSPICIOUS
Accesses external device storage files
- app_process64 (PID: 2798)
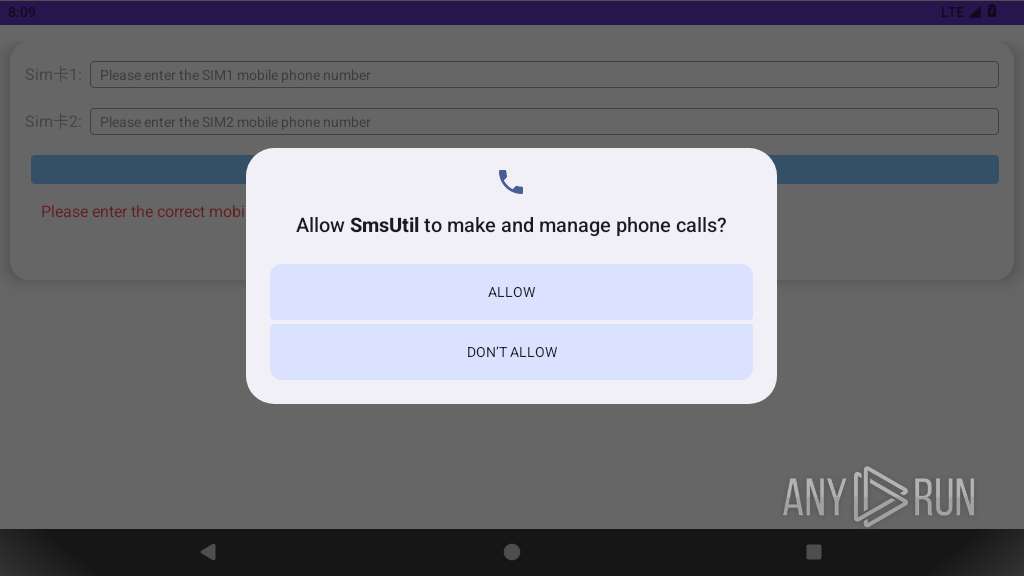
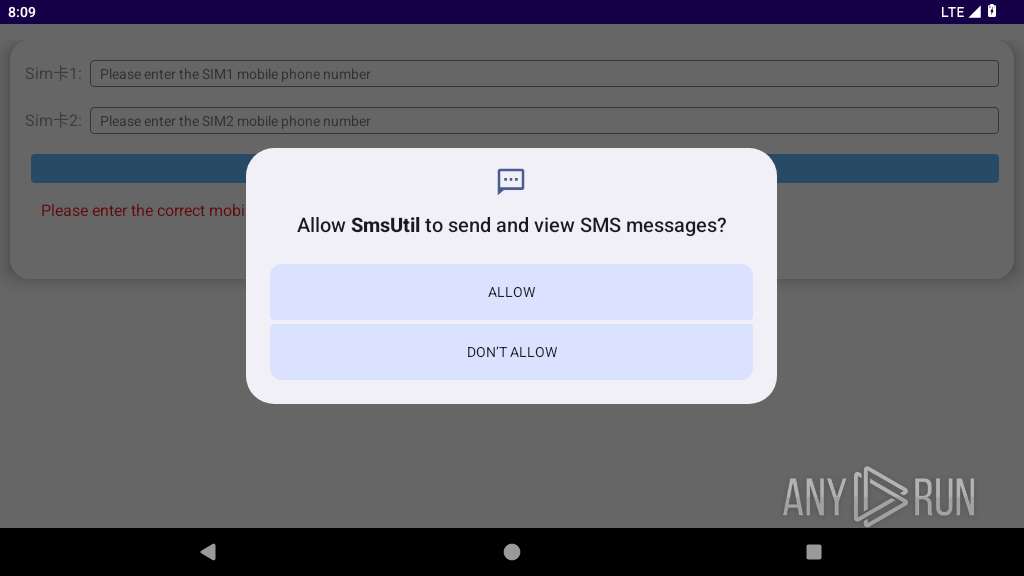
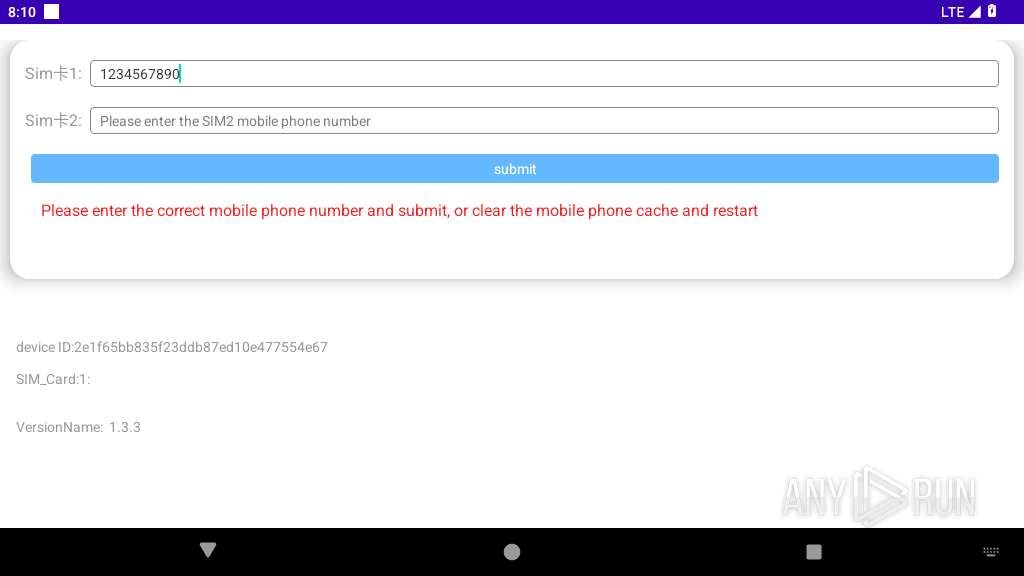
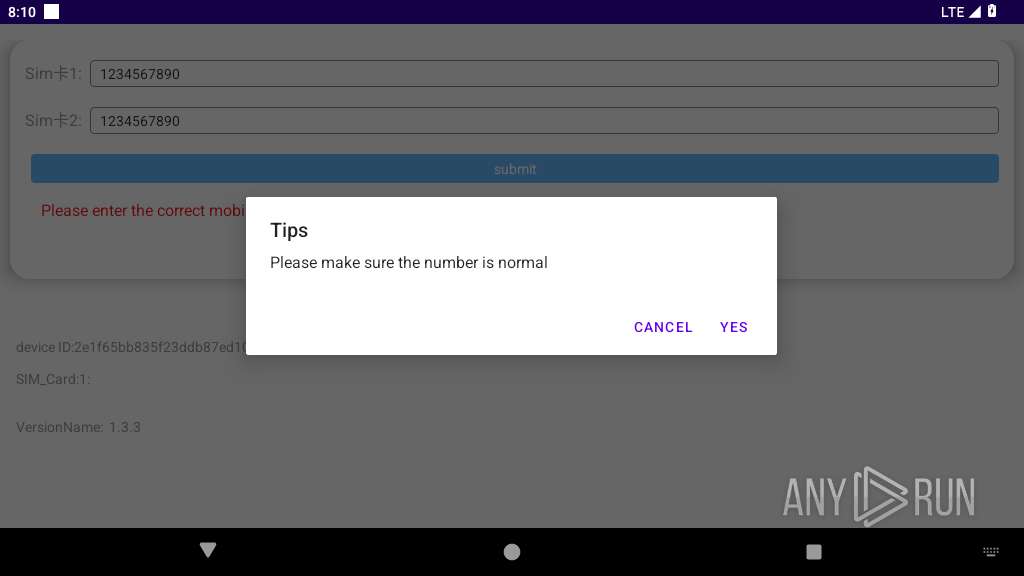
Monitors and intercepts incoming messages
- app_process64 (PID: 2798)
Accesses system-level resources
- app_process64 (PID: 2798)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 2798)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2798)
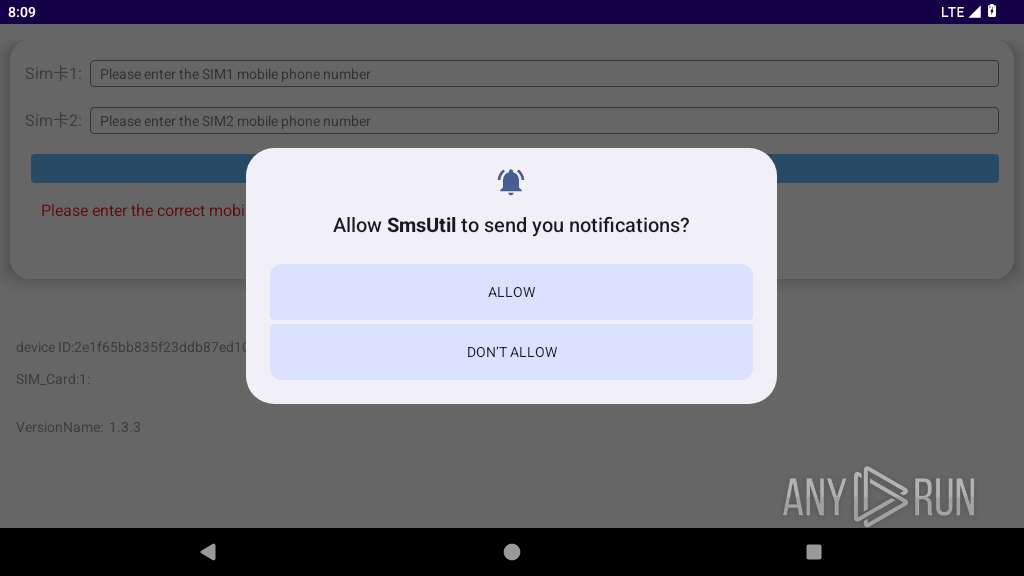
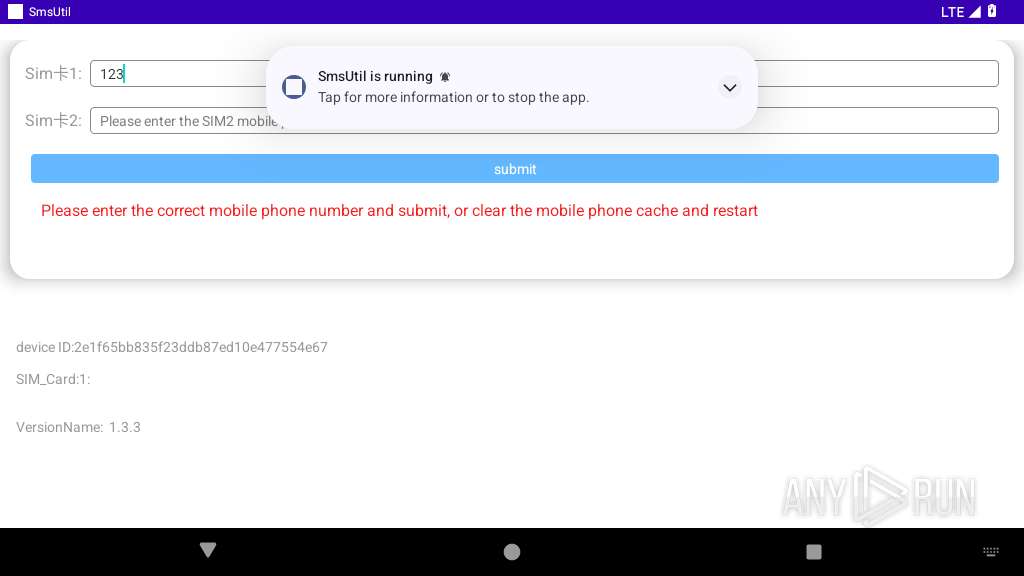
Abuses foreground service for persistence
- app_process64 (PID: 2798)
Collects nearby Wi-Fi network information
- app_process64 (PID: 2798)
INFO
Dynamically registers broadcast event listeners
- app_process64 (PID: 2798)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2798)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 2798)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2798)
Creates and writes local files
- app_process64 (PID: 2798)
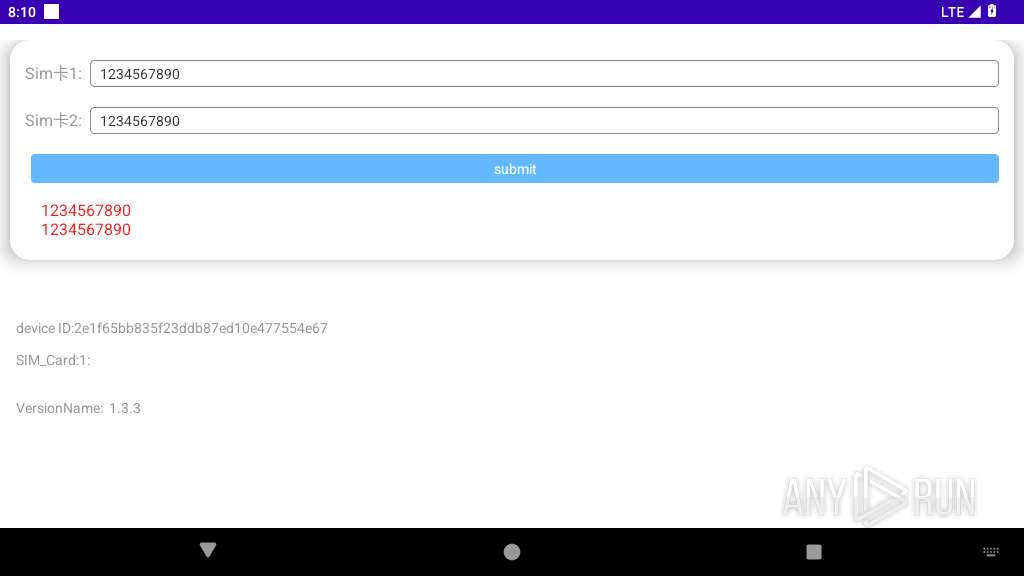
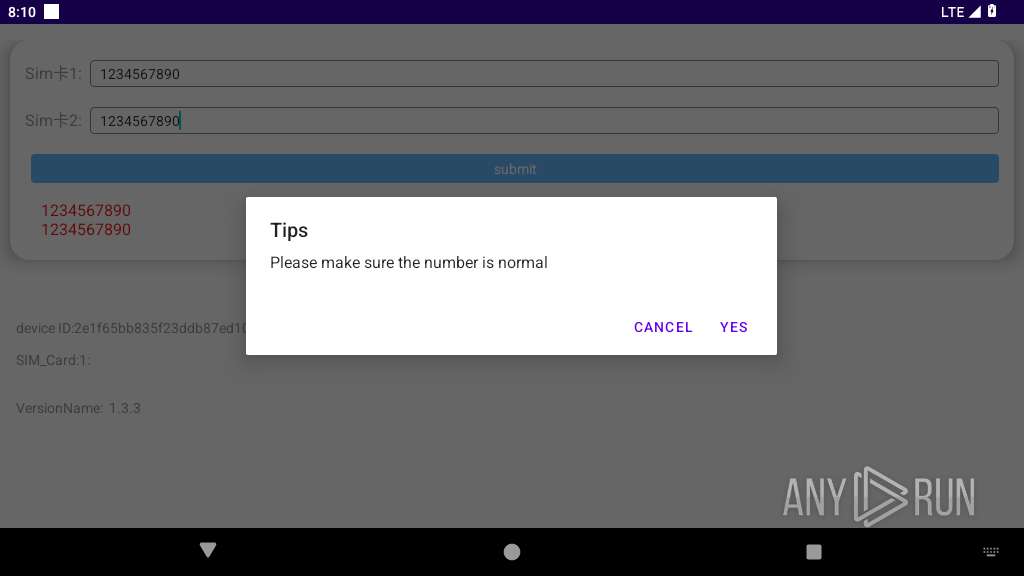
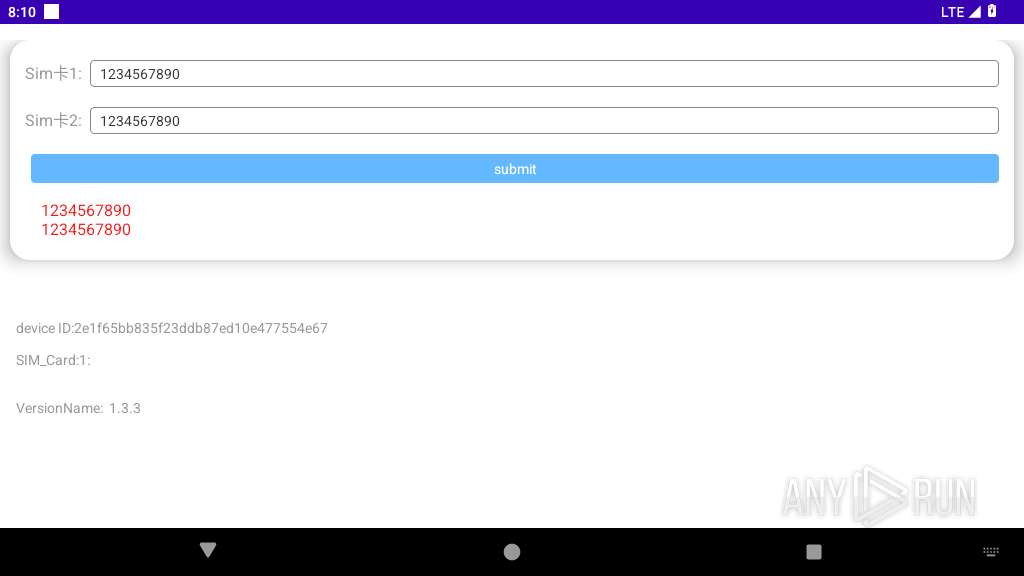
Verifies presence of SIM card
- app_process64 (PID: 2798)
Retrieves the value of a secure system setting
- app_process64 (PID: 2798)
Dynamically loads a class in Java
- app_process64 (PID: 2798)
Detects device power status
- app_process64 (PID: 2798)
Verifies whether the device is connected to the internet
- app_process64 (PID: 2798)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (73.9) |
|---|---|---|
| .jar | | | Java Archive (20.4) |
| .zip | | | ZIP compressed archive (5.6) |
EXIF
ZIP
| ZipRequiredVersion: | - |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1981:01:01 01:01:02 |
| ZipCRC: | 0xe91e1b7c |
| ZipCompressedSize: | 900 |
| ZipUncompressedSize: | 1532 |
| ZipFileName: | classes9.dex |
Total processes
130
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2798 | com.gyh.er.util | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2878 | crash_dump64 2863 2877 4 | /apex/com.android.runtime/bin/crash_dump64 | — | app_process64 |
User: u0_a104 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2879 | crash_dump64 2863 2877 4 | /apex/com.android.runtime/bin/crash_dump64 | — | crash_dump64 |
User: u0_a104 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2882 | com.android.rkpdapp | /system/bin/app_process64 | — | app_process64 |
User: u0_a104 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2884 | com.android.rkpdapp | /system/bin/app_process64 | — | app_process64 |
User: u0_a104 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2908 | <pre-initialized> | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
3
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2798 | app_process64 | /data/data/com.gyh.er.util/shared_prefs/crashrecord.xml | xml | |
MD5:— | SHA256:— | |||
| 2798 | app_process64 | /data/data/com.gyh.er.util/app_crashrecord/1004 | binary | |
MD5:— | SHA256:— | |||
| 2798 | app_process64 | /data/data/com.gyh.er.util/files/bugly_last_us_up_tm | text | |
MD5:— | SHA256:— | |||
| 2798 | app_process64 | /data/data/com.gyh.er.util/shared_prefs/BUGLY_COMMON_VALUES.xml | xml | |
MD5:— | SHA256:— | |||
| 2798 | app_process64 | /storage/emulated/0/Android/data/com.gyh.er.util/files/log/util_2025_09_17_com.gyh.er.util.txt | text | |
MD5:— | SHA256:— | |||
| 2798 | app_process64 | /data/data/com.gyh.er.util/shared_prefs/Utils.xml | xml | |
MD5:— | SHA256:— | |||
| 2798 | app_process64 | /data/data/com.gyh.er.util/shared_prefs/spUtils.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
13
DNS requests
7
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
831 | app_process64 | GET | 204 | 142.250.184.227:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
— | — | GET | 204 | 142.250.186.36:80 | http://www.google.com/gen_204 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
446 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 142.250.186.36:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.184.227:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 142.250.186.36:443 | www.google.com | GOOGLE | US | whitelisted |
574 | app_process64 | 216.239.35.4:123 | time.android.com | — | — | unknown |
831 | app_process64 | 142.250.184.227:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
831 | app_process64 | 142.250.186.36:443 | www.google.com | GOOGLE | US | whitelisted |
1711 | app_process64 | 64.233.167.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
2798 | app_process64 | 14.22.7.199:443 | android.bugly.qq.com | Chinanet | CN | unknown |
2908 | app_process64 | 64.233.167.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
google.com |
| whitelisted |
time.android.com |
| unknown |
connectivitycheck.gstatic.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
android.bugly.qq.com |
| unknown |
app.kainder.xyz |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
831 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |