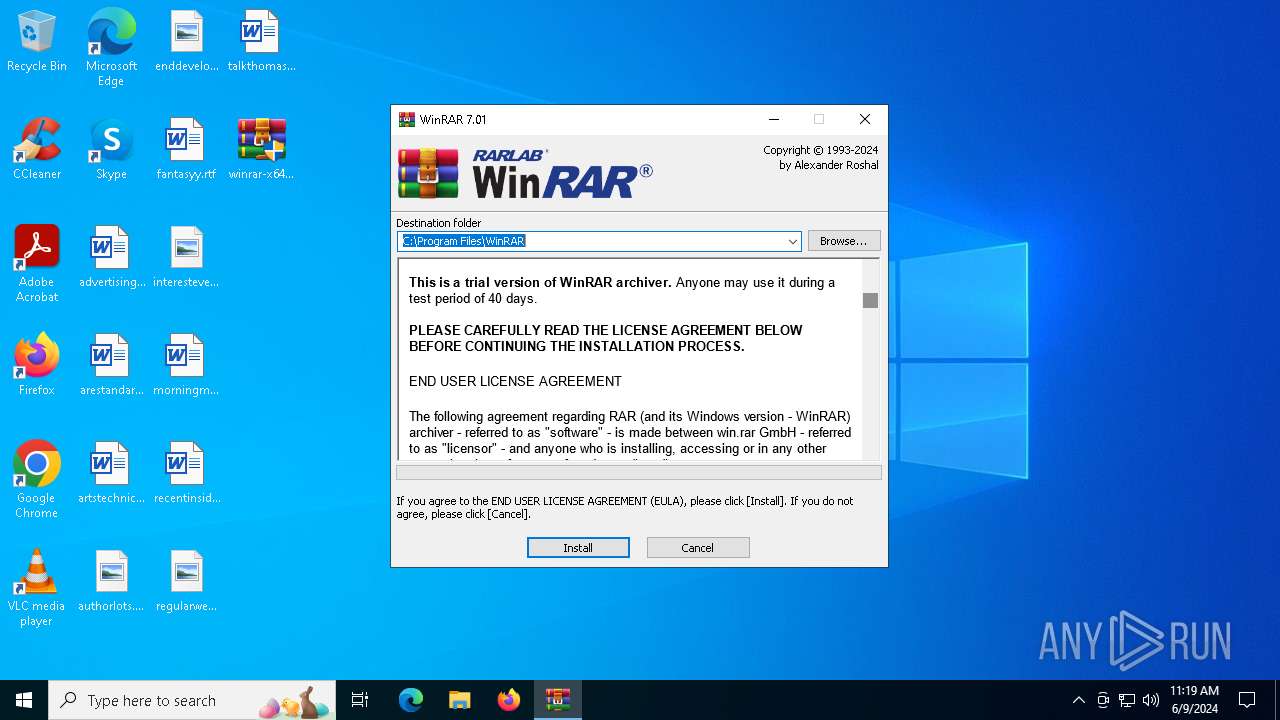
| File name: | winrar-x64-701.exe |
| Full analysis: | https://app.any.run/tasks/1be6c67d-7b21-41cd-a119-e7d53daf55ff |
| Verdict: | Malicious activity |
| Analysis date: | June 09, 2024, 11:18:47 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 46C17C999744470B689331F41EAB7DF1 |
| SHA1: | B8A63127DF6A87D333061C622220D6D70ED80F7C |
| SHA256: | C5B5DEF1C8882B702B6B25CBD94461C737BC151366D2D9EBA5006C04886BFC9A |
| SSDEEP: | 98304:Cq69dyxpSd9ptUgSFRbfr+8VpyJftDT6LoERRKlKJqGt0RNs8rJ6POMD2drS8J/q:tGsOwbH54Bg |
MALICIOUS
Drops the executable file immediately after the start
- winrar-x64-701.exe (PID: 6372)
SUSPICIOUS
Reads security settings of Internet Explorer
- winrar-x64-701.exe (PID: 6372)
- Uninstall.exe (PID: 6684)
Reads Microsoft Outlook installation path
- winrar-x64-701.exe (PID: 6372)
Reads Internet Explorer settings
- winrar-x64-701.exe (PID: 6372)
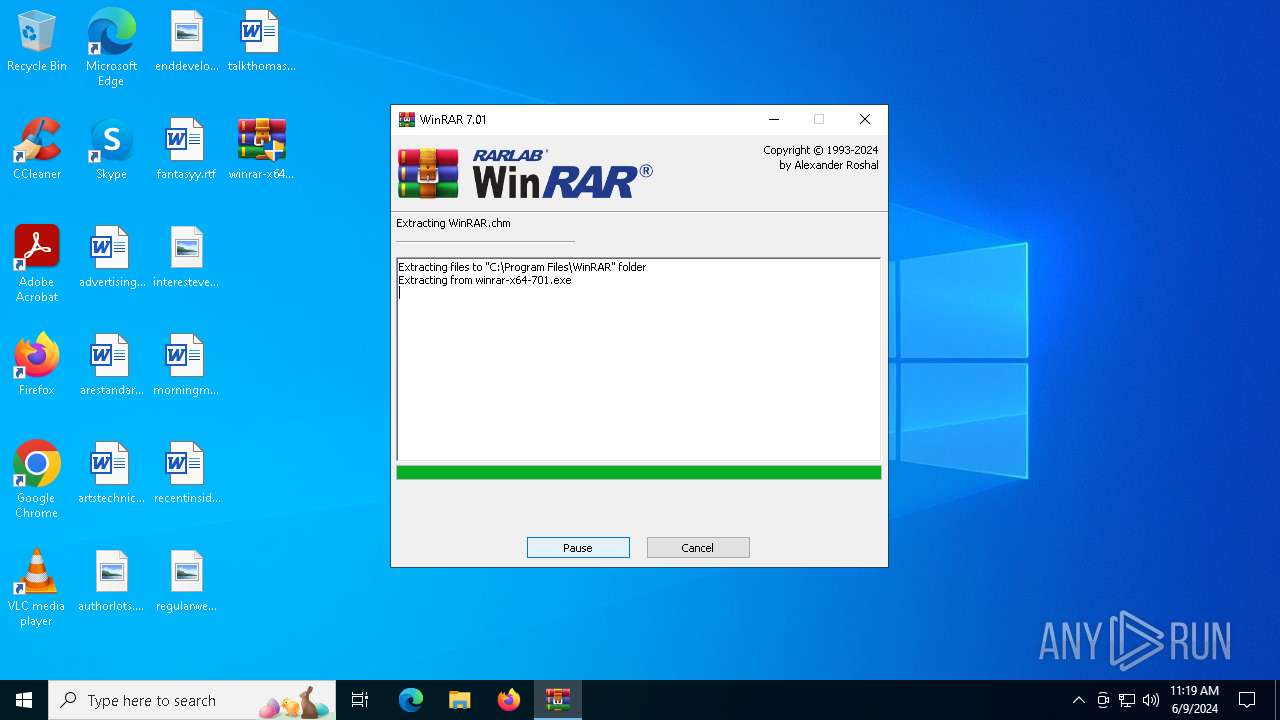
Executable content was dropped or overwritten
- winrar-x64-701.exe (PID: 6372)
Drops 7-zip archiver for unpacking
- winrar-x64-701.exe (PID: 6372)
Reads the date of Windows installation
- winrar-x64-701.exe (PID: 6372)
- Uninstall.exe (PID: 6684)
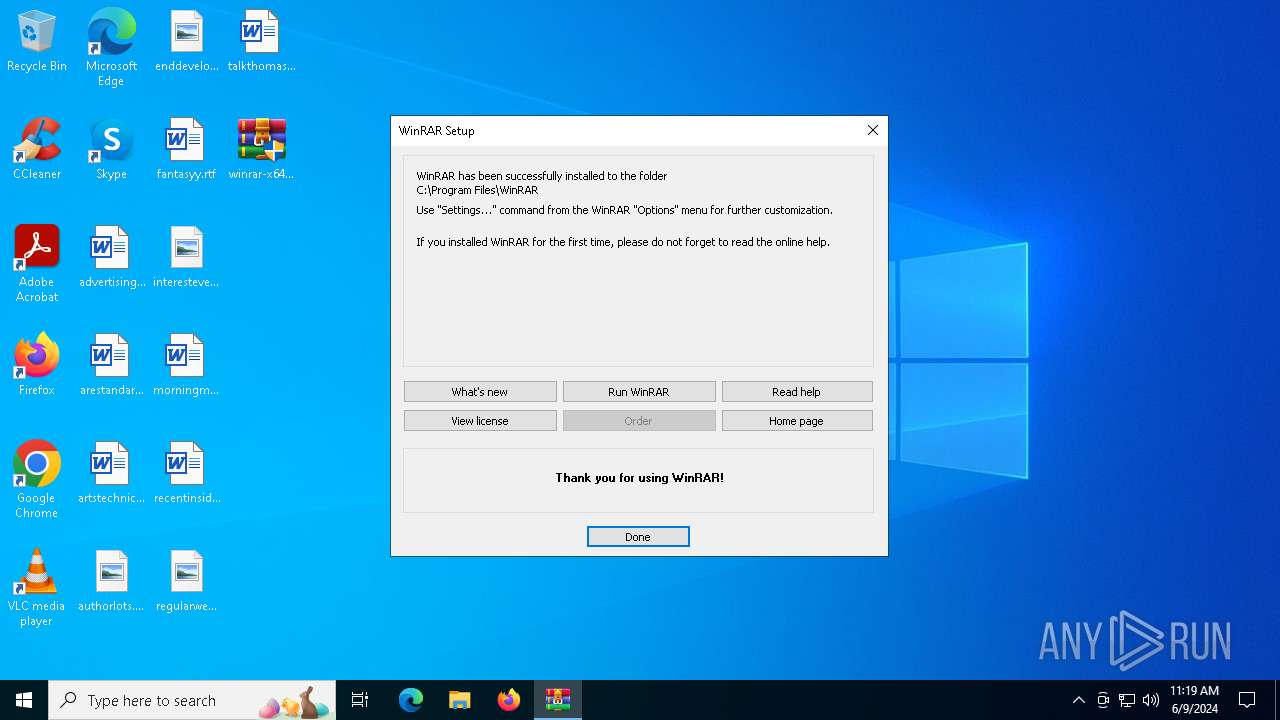
Creates/Modifies COM task schedule object
- Uninstall.exe (PID: 6684)
Searches for installed software
- Uninstall.exe (PID: 6684)
Creates a software uninstall entry
- Uninstall.exe (PID: 6684)
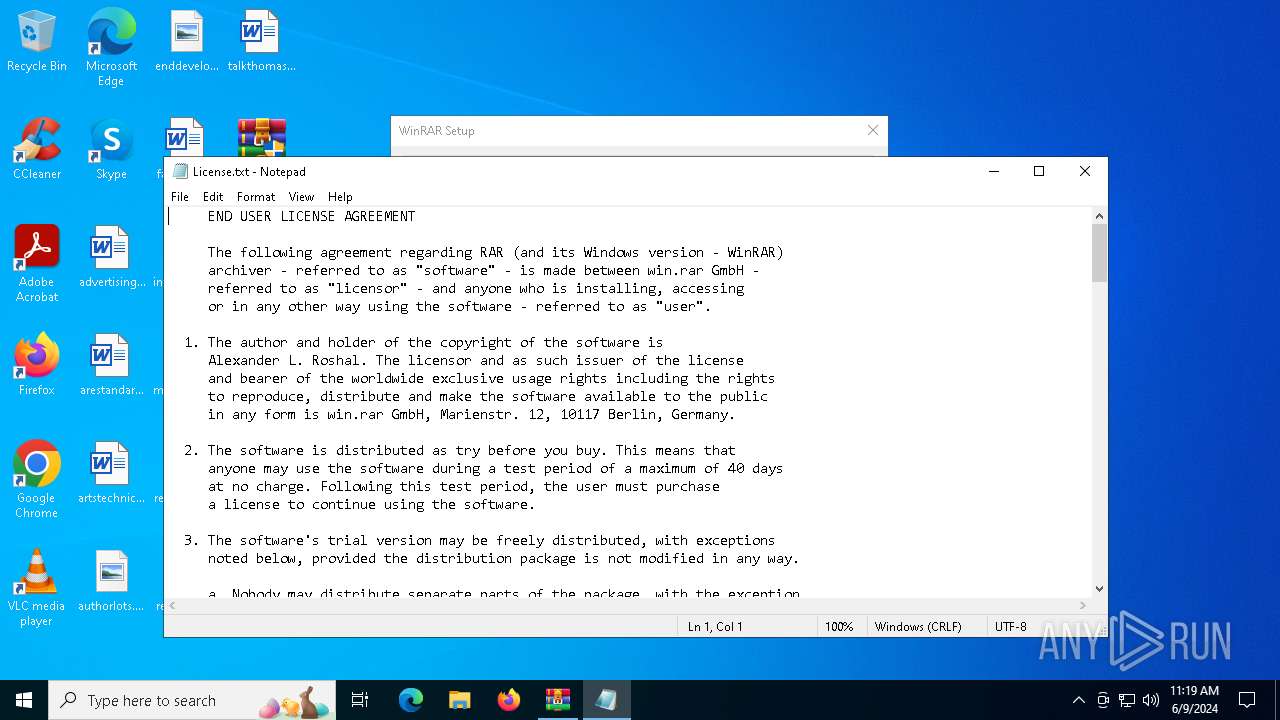
Start notepad (likely ransomware note)
- Uninstall.exe (PID: 6684)
INFO
Checks supported languages
- winrar-x64-701.exe (PID: 6372)
- Uninstall.exe (PID: 6684)
Reads the computer name
- winrar-x64-701.exe (PID: 6372)
- Uninstall.exe (PID: 6684)
Checks proxy server information
- winrar-x64-701.exe (PID: 6372)
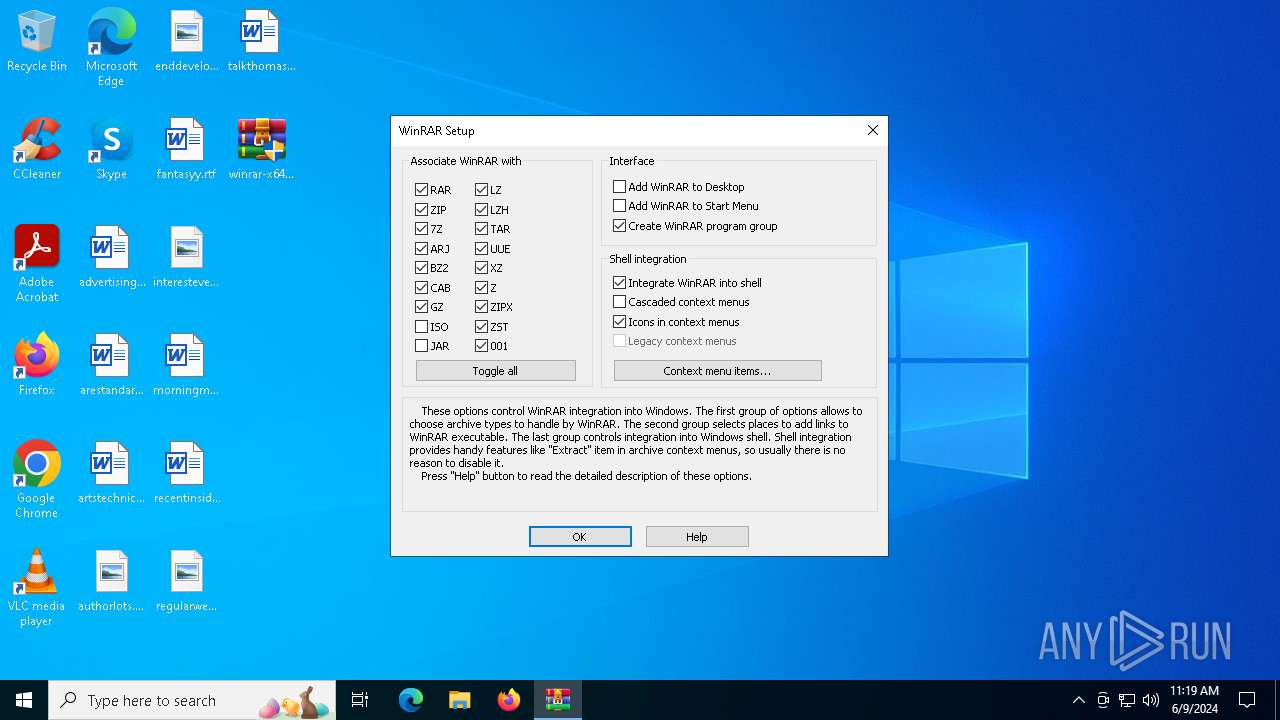
Creates files in the program directory
- winrar-x64-701.exe (PID: 6372)
- Uninstall.exe (PID: 6684)
Process checks Internet Explorer phishing filters
- winrar-x64-701.exe (PID: 6372)
Process checks computer location settings
- winrar-x64-701.exe (PID: 6372)
- Uninstall.exe (PID: 6684)
Creates files or folders in the user directory
- Uninstall.exe (PID: 6684)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6848)
Reads Microsoft Office registry keys
- Uninstall.exe (PID: 6684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:05:12 10:17:26+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.33 |
| CodeSize: | 270848 |
| InitializedDataSize: | 309760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x29e90 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.1.0.0 |
| ProductVersionNumber: | 7.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| ProductName: | WinRAR |
| CompanyName: | Alexander Roshal |
| FileDescription: | WinRAR |
| FileVersion: | 7.1.0 |
| ProductVersion: | 7.1.0 |
| InternalName: | WinRAR |
| LegalCopyright: | Copyright © Alexander Roshal 1993-2024 |
| OriginalFileName: | WinRAR.exe |
Total processes
120
Monitored processes
4
Malicious processes
2
Suspicious processes
0
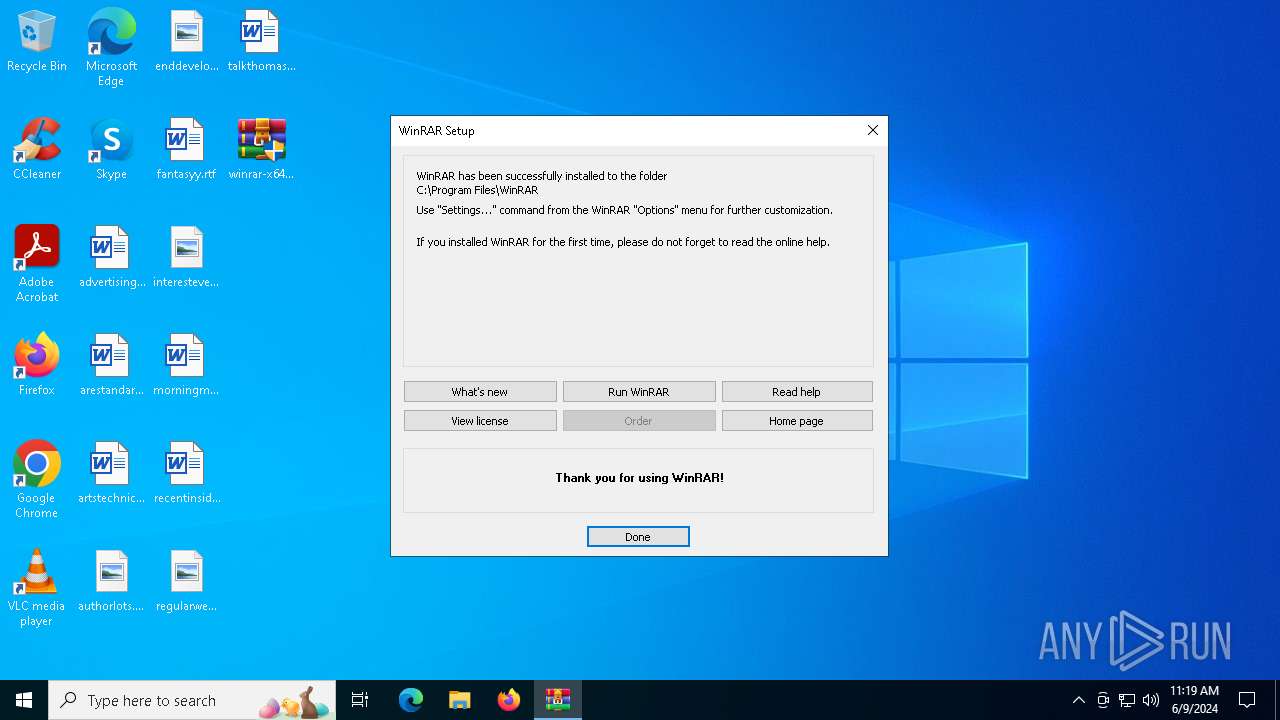
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6316 | "C:\Users\admin\Desktop\winrar-x64-701.exe" | C:\Users\admin\Desktop\winrar-x64-701.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR Exit code: 3221226540 Version: 7.1.0 Modules
| |||||||||||||||
| 6372 | "C:\Users\admin\Desktop\winrar-x64-701.exe" | C:\Users\admin\Desktop\winrar-x64-701.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR Exit code: 0 Version: 7.1.0 Modules
| |||||||||||||||
| 6684 | "C:\Program Files\WinRAR\uninstall.exe" /setup | C:\Program Files\WinRAR\Uninstall.exe | — | winrar-x64-701.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: Uninstall WinRAR Version: 7.1.0 Modules
| |||||||||||||||
| 6848 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Program Files\WinRAR\License.txt | C:\Windows\System32\notepad.exe | — | Uninstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 166
Read events
4 058
Write events
104
Delete events
4
Modification events
| (PID) Process: | (6372) winrar-x64-701.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6372) winrar-x64-701.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6372) winrar-x64-701.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6372) winrar-x64-701.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6372) winrar-x64-701.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6372) winrar-x64-701.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6372) winrar-x64-701.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6372) winrar-x64-701.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR SFX |
| Operation: | write | Name: | C%%Program Files%WinRAR |
Value: C:\Program Files\WinRAR | |||
| (PID) Process: | (6372) winrar-x64-701.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
| (PID) Process: | (6372) winrar-x64-701.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFeedsInitialSelection |
Value: | |||
Executable files
13
Suspicious files
10
Text files
11
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6372 | winrar-x64-701.exe | — | ||
MD5:— | SHA256:— | |||
| 6372 | winrar-x64-701.exe | C:\Program Files\WinRAR\Descript.ion | text | |
MD5:84846ABC52DC17020E4E934D3C94B4E6 | SHA256:3449FD40D054C96285FAB92011E732174C7CD000EDA67470376F26F0D431F1F2 | |||
| 6372 | winrar-x64-701.exe | C:\Program Files\WinRAR\Uninstall.exe | executable | |
MD5:4783F1A5F0BBA7A6A40CB74BC8C41217 | SHA256:F376AAA0D4444D0727DB5598E8377F9F1606400ADBBB4772D39D1E4937D5F28C | |||
| 6372 | winrar-x64-701.exe | C:\Program Files\WinRAR\ReadMe.txt | text | |
MD5:00D0A57A6D64EE3DE8F4D5529D6C6447 | SHA256:FCD13E1B97AF47B8B923BA97AE15E9731C66093609667C3171D5DD24A6F7F2E6 | |||
| 6372 | winrar-x64-701.exe | C:\Program Files\WinRAR\RarExt32.dll | executable | |
MD5:24F6FAA5D2E9C8FB15AE0C936BFA4545 | SHA256:BD3F01E7C100422A6FAAE60D76DA16158F6D8B3868D474E81FD657EC3C0127EF | |||
| 6372 | winrar-x64-701.exe | C:\Program Files\WinRAR\WhatsNew.txt | text | |
MD5:1C44C85FDAB8E9C663405CD8E4C3DBBD | SHA256:33108DD40B4E07D60E96E1BCFA4AD877EB4906DE2CC55844E40360E5D4DAFB5D | |||
| 6372 | winrar-x64-701.exe | C:\Program Files\WinRAR\Rar.txt | text | |
MD5:B954981A253F5E1EE25585037A0C5FEE | SHA256:59E40B34B09BE2654B793576035639C459AD6E962F9F9CD000D556FA21B1C7CD | |||
| 6372 | winrar-x64-701.exe | C:\Program Files\WinRAR\RarExtInstaller.exe | executable | |
MD5:F5B54D16610A819BBC6099BDC92ADD2C | SHA256:46F533007FB231D0B0AF058A0997AB5E6B44A1B02AE327621F04FDC4B2E18964 | |||
| 6372 | winrar-x64-701.exe | C:\Program Files\WinRAR\License.txt | text | |
MD5:672064CF19DB0B083B981CF0BE7662B0 | SHA256:9FC8AA33CCAFA04C1CE4C0A61047B341297D720ADAB1B77F67B5FE59F43BB59F | |||
| 6372 | winrar-x64-701.exe | C:\Program Files\WinRAR\Uninstall.lst | text | |
MD5:6EEEFCB85673C14201D024B6E6AC6258 | SHA256:B75FDEE208D2834AB147DACB51F4E7D70E44457C8B639048FE67B252B8D61F1F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
25
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5380 | RUXIMICS.exe | GET | 200 | 2.16.241.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5380 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
5632 | svchost.exe | GET | 200 | 2.16.241.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5632 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
— | — | POST | 204 | 104.115.83.114:443 | https://www.bing.com/threshold/xls.aspx | unknown | — | — | unknown |
— | — | GET | 200 | 104.115.83.114:443 | https://www.bing.com/rb/18/jnc,nj/6hU_LneafI_NFLeDvM367ebFaKQ.js?bu=DyIrb3t-gQF4cnWyAbUBK6UBK7gB&or=w | unknown | s | 21.3 Kb | unknown |
— | — | GET | 200 | 104.115.83.114:443 | https://www.bing.com/manifest/threshold.appcache | unknown | text | 3.36 Kb | unknown |
— | — | POST | 200 | 104.208.16.91:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5632 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5380 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5140 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5380 | RUXIMICS.exe | 2.16.241.6:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5140 | MoUsoCoreWorker.exe | 2.16.241.6:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5632 | svchost.exe | 2.16.241.6:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5380 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
5632 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
5140 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
5456 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP Request abnormal Content-Encoding header |