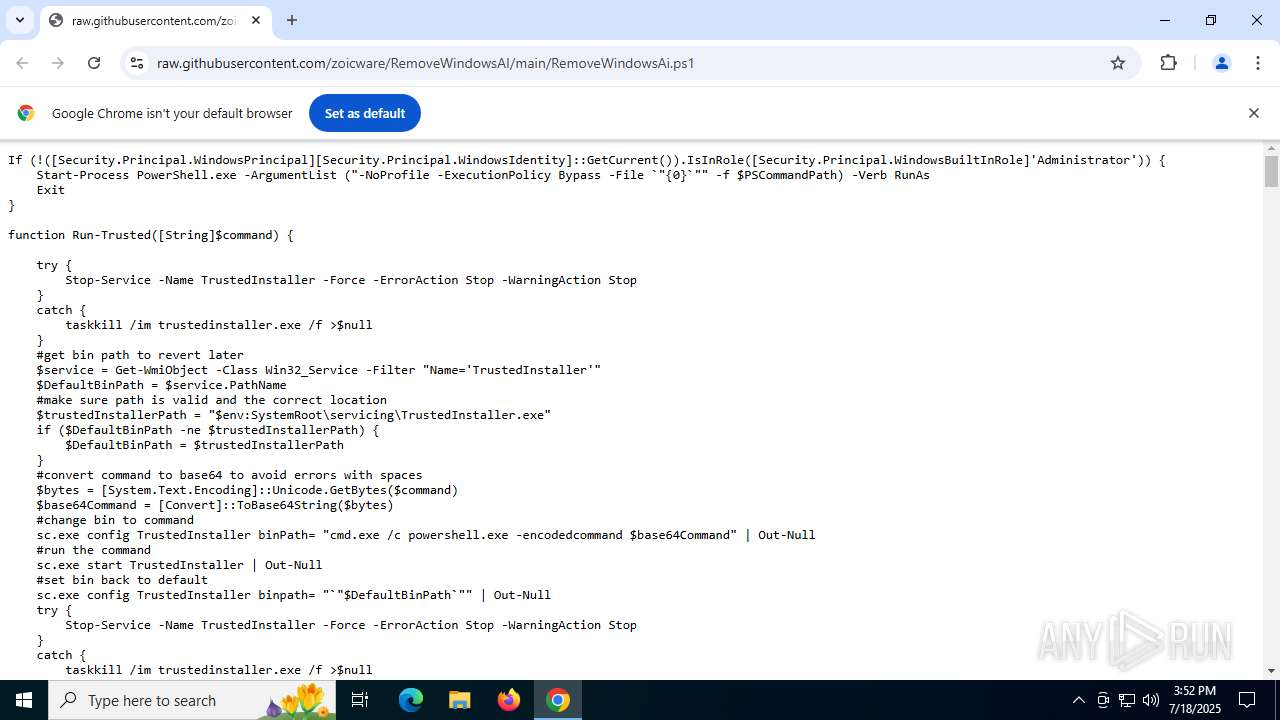
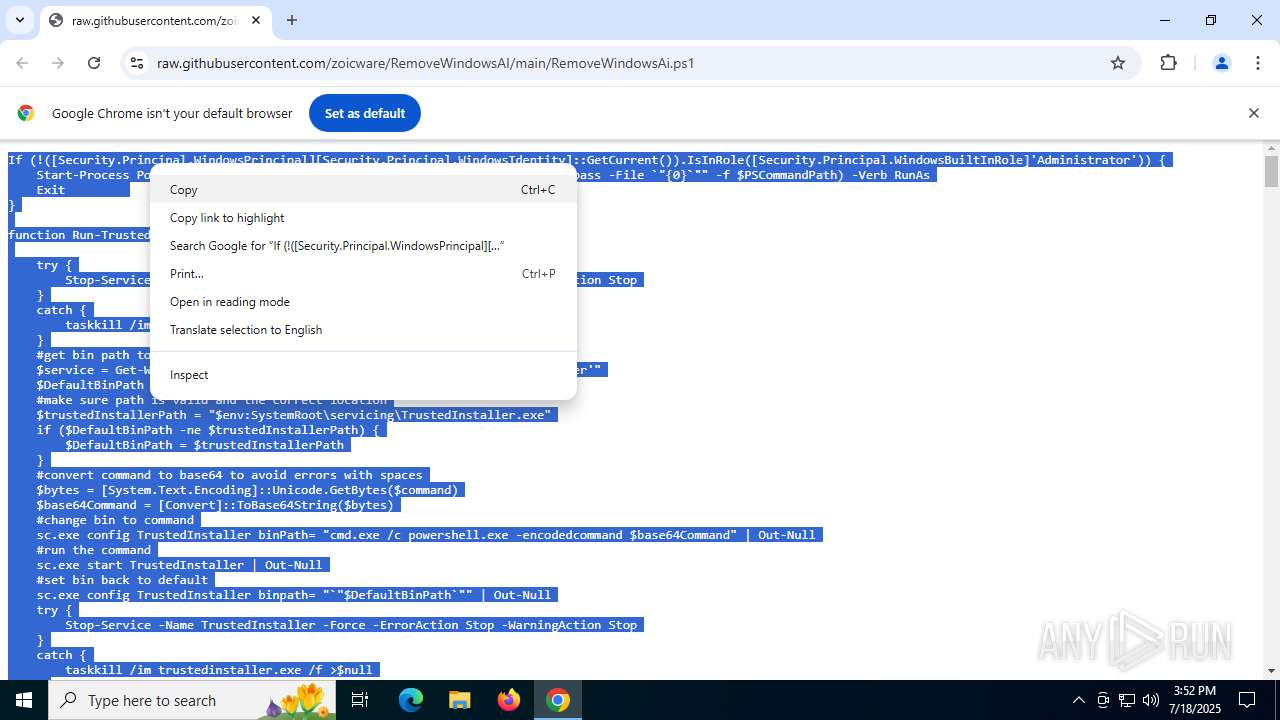
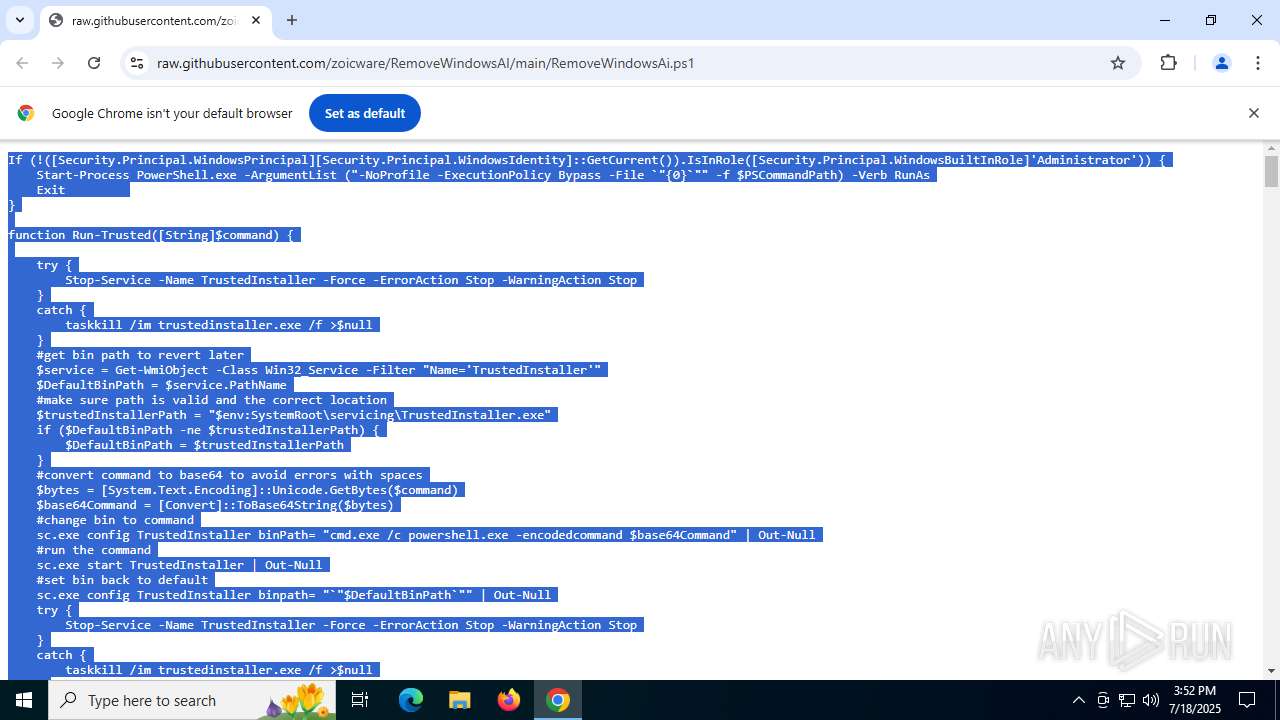
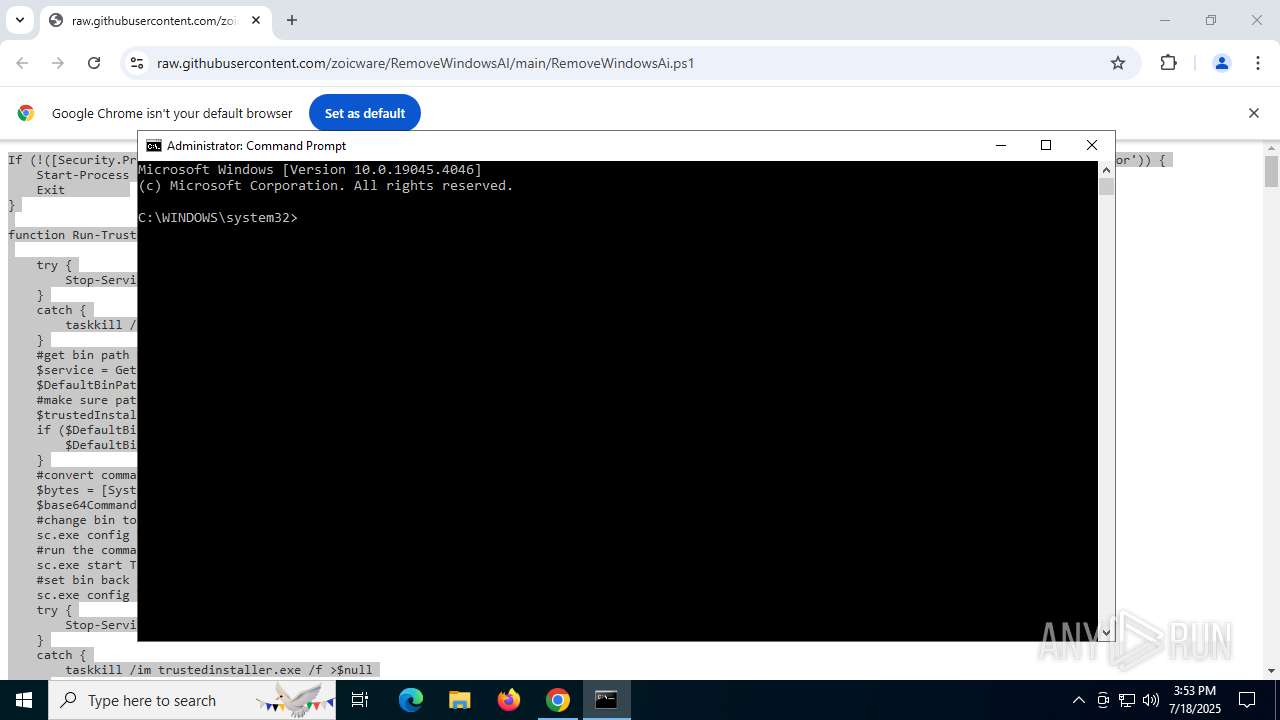
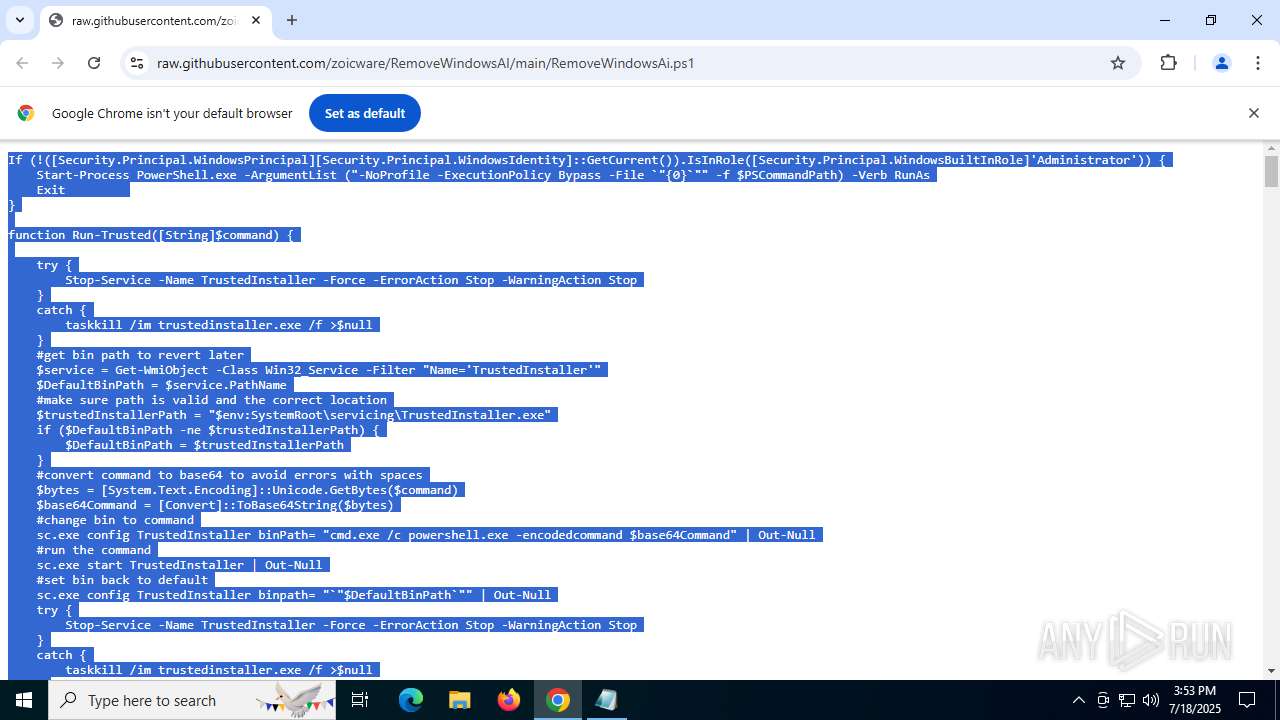
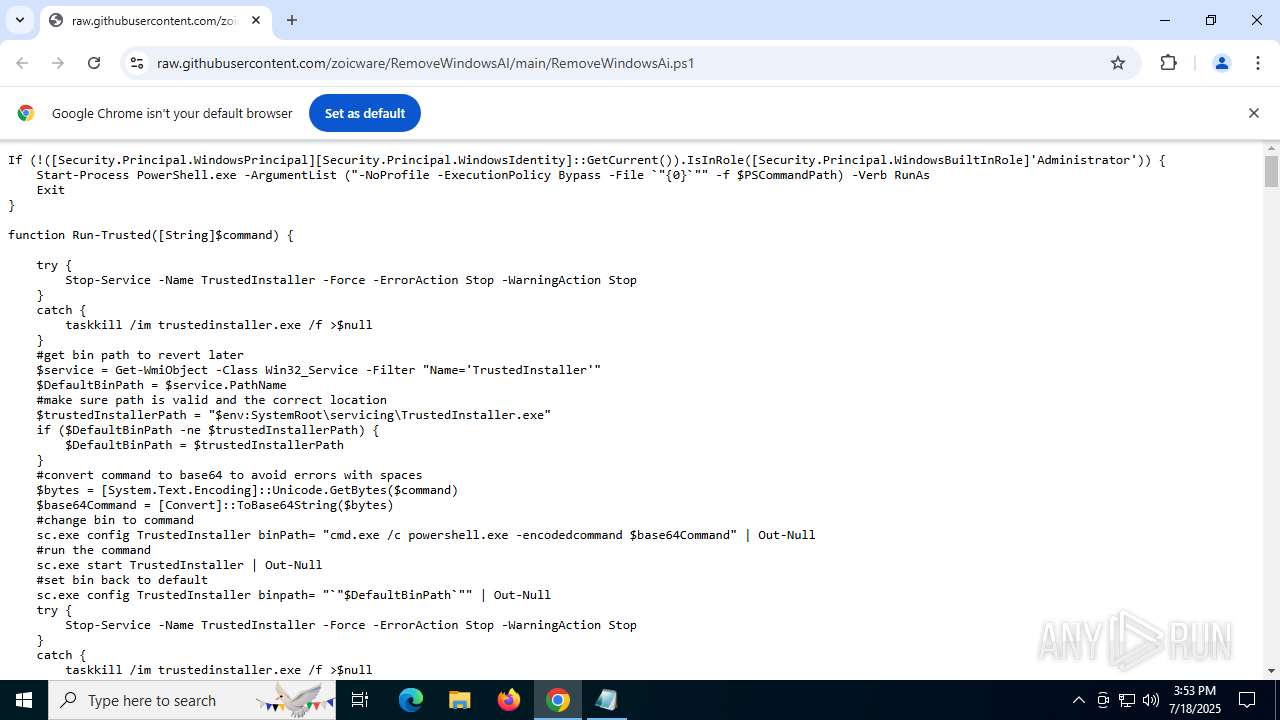
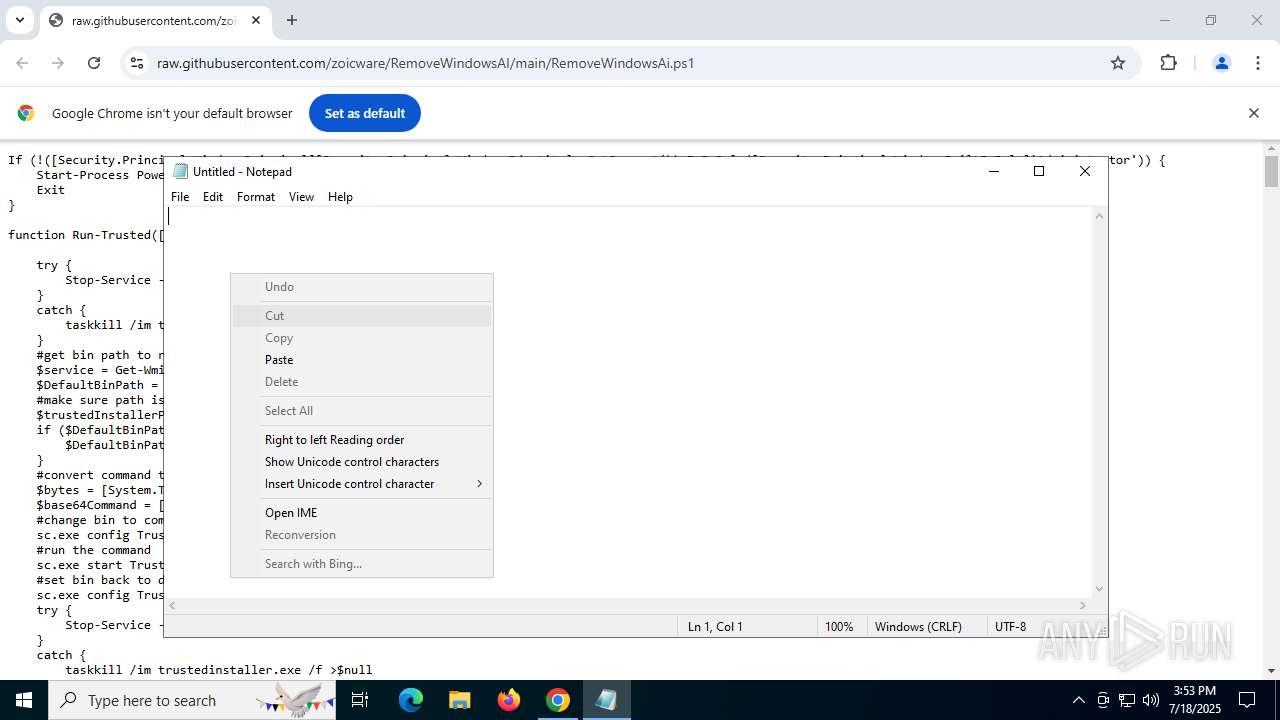
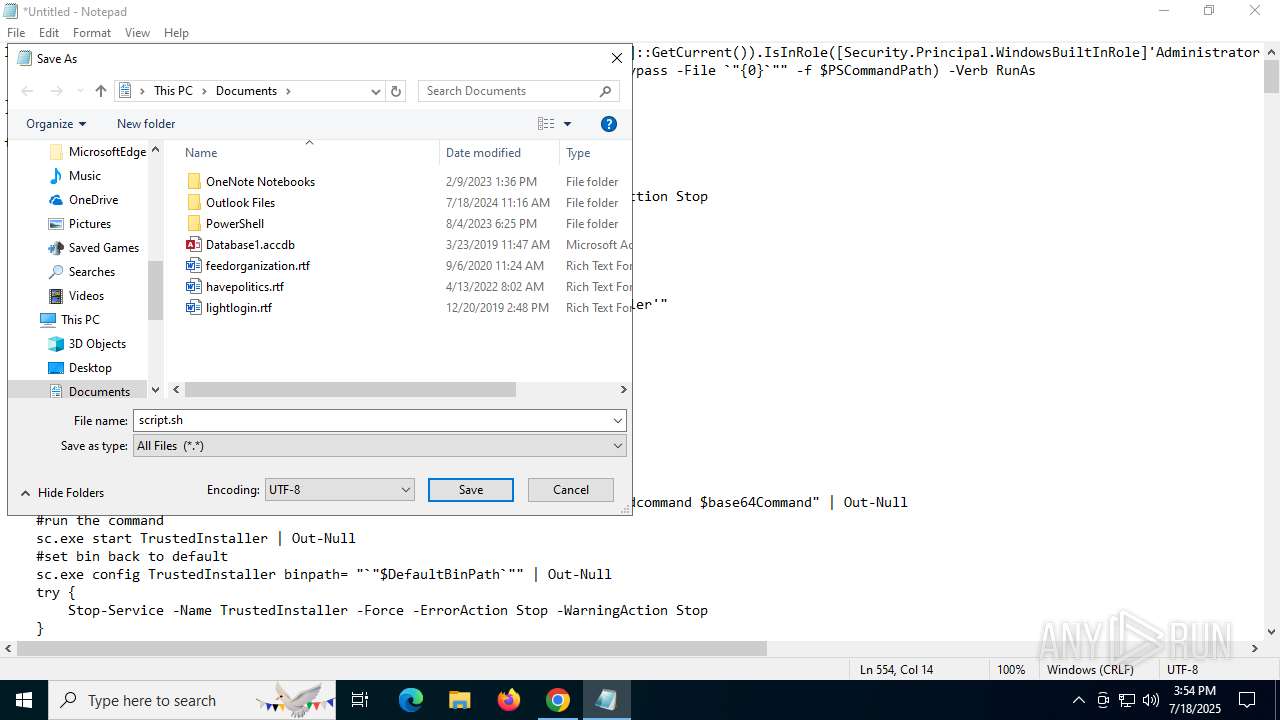
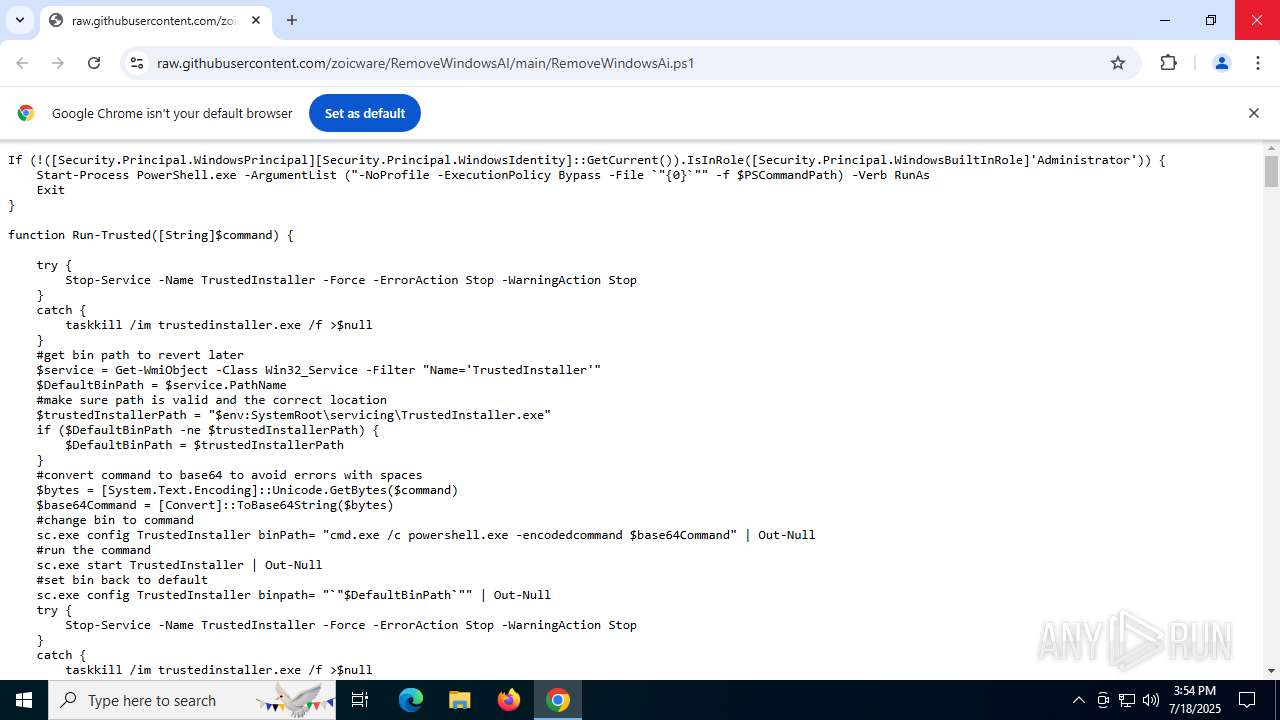
| URL: | https://raw.githubusercontent.com/zoicware/RemoveWindowsAI/main/RemoveWindowsAi.ps1 |
| Full analysis: | https://app.any.run/tasks/25b2a569-eda1-40ce-bf64-ab7eaf0b4e72 |
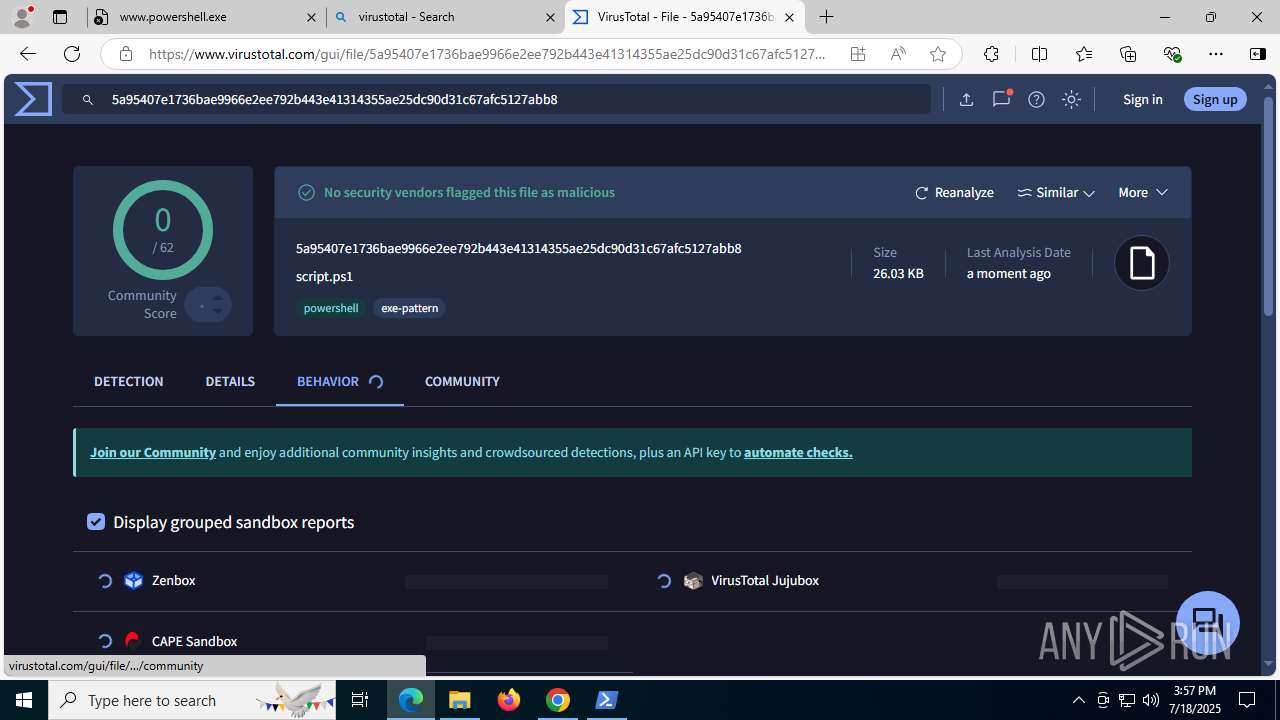
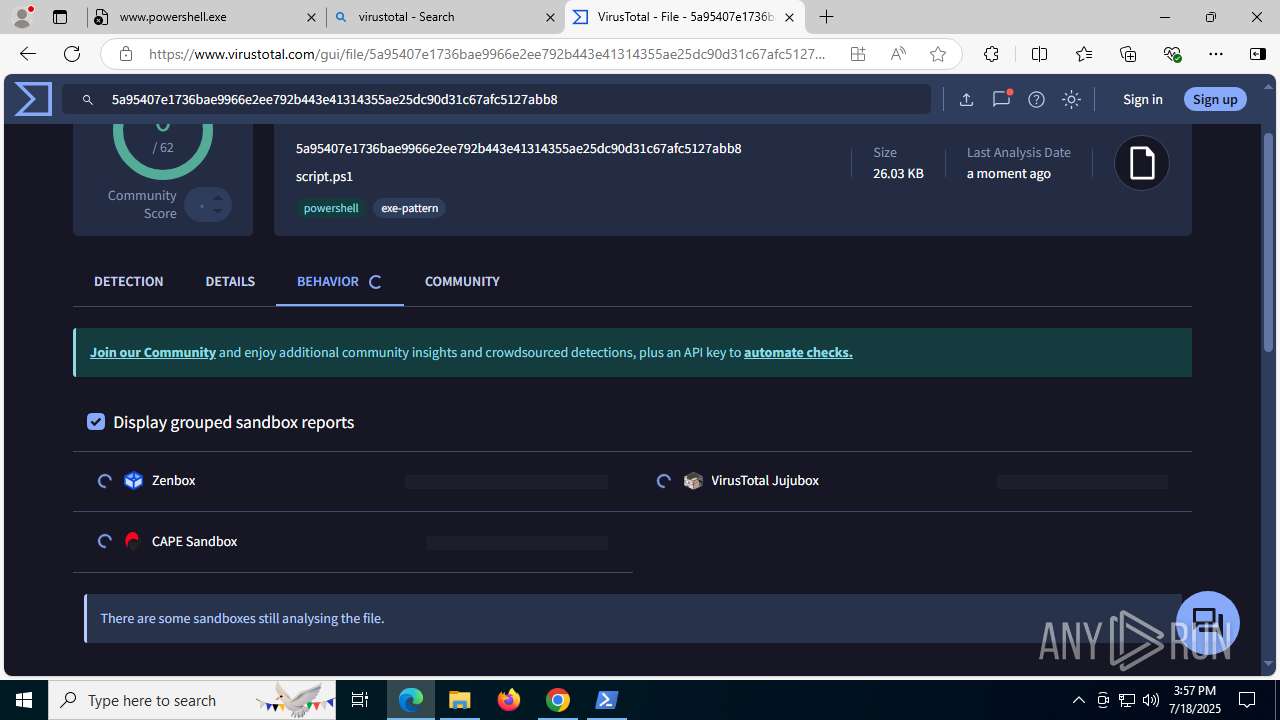
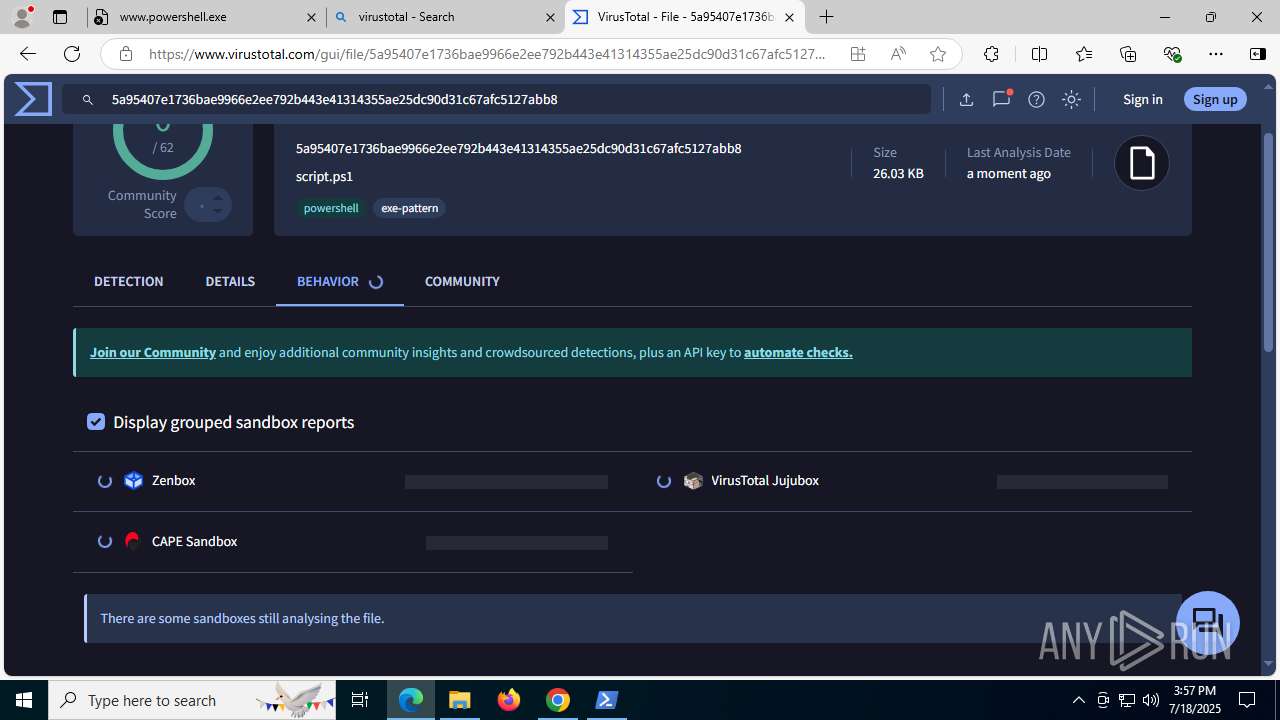
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2025, 15:52:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
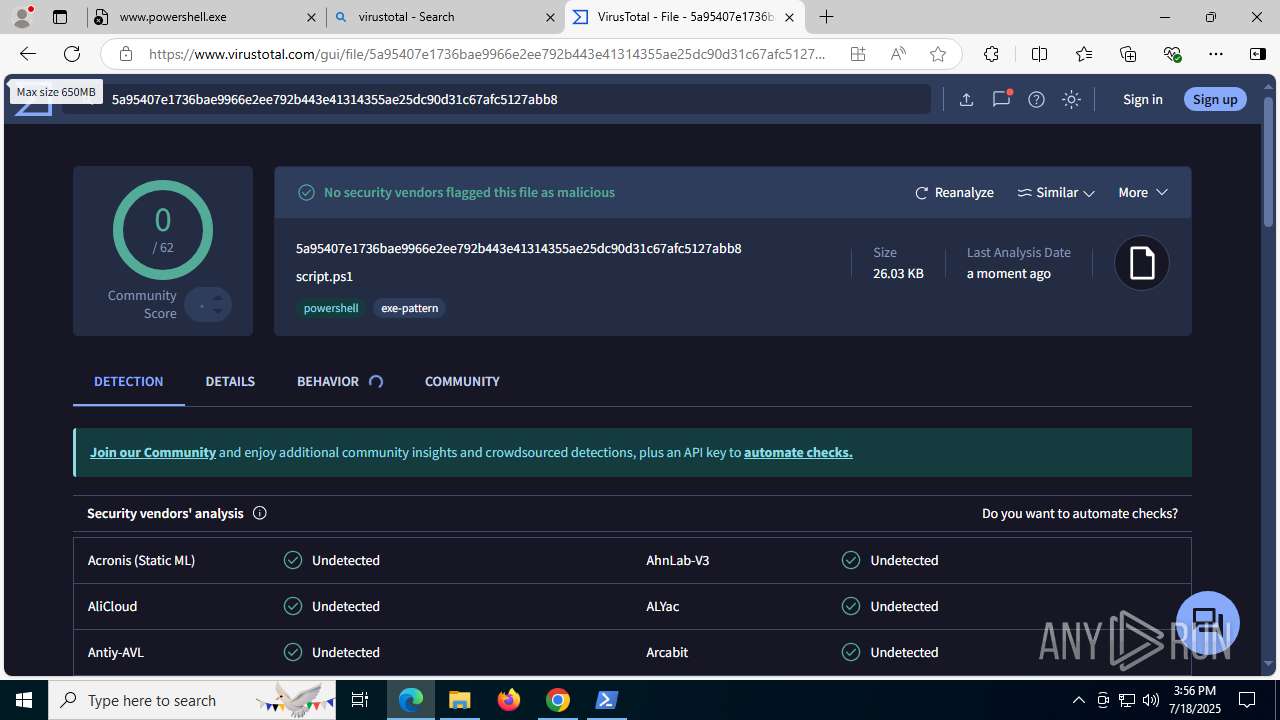
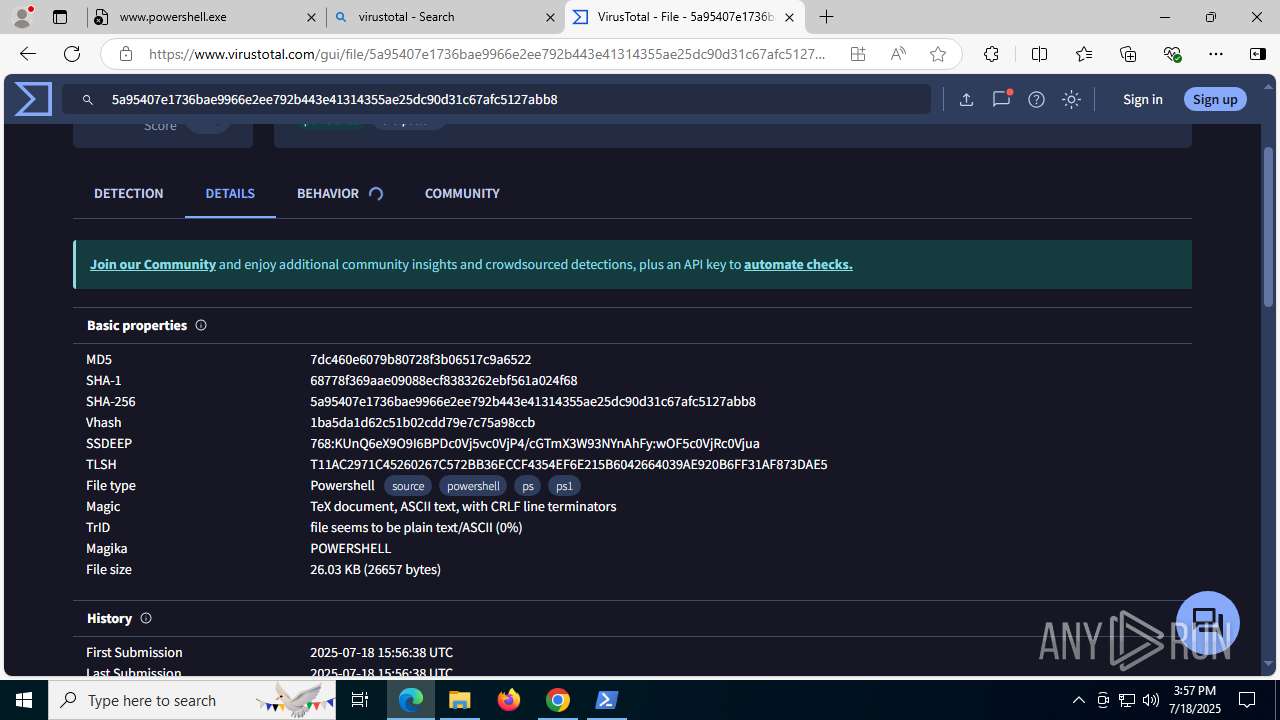
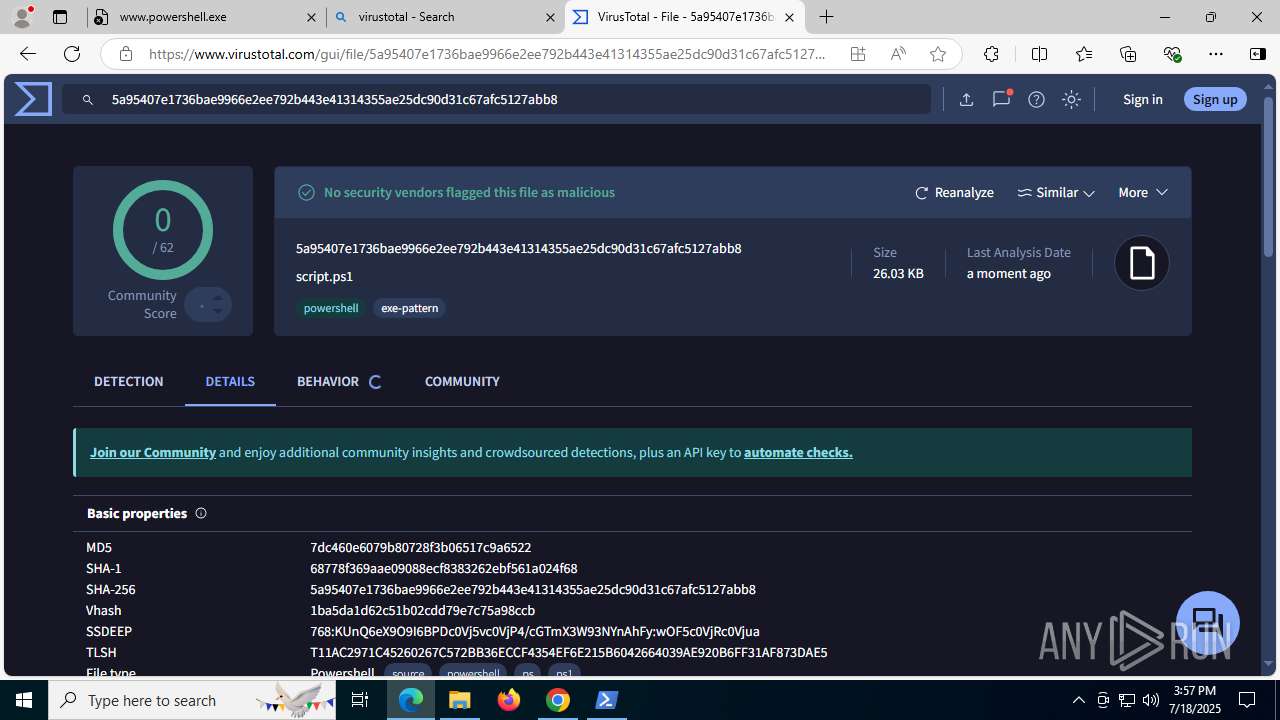
| MD5: | D74439B229F3351BDEC89302B55D11D6 |
| SHA1: | 72F53938056C6522C718432D481A49BC1C25F162 |
| SHA256: | C5B3E2B0C185A4FB5D2922BAB74EAFB011B54385702223BAFFF70F9BBA20FB10 |
| SSDEEP: | 3:N8SGfALtGT7ggKL+AhWU:2FMGHggQ+AAU |
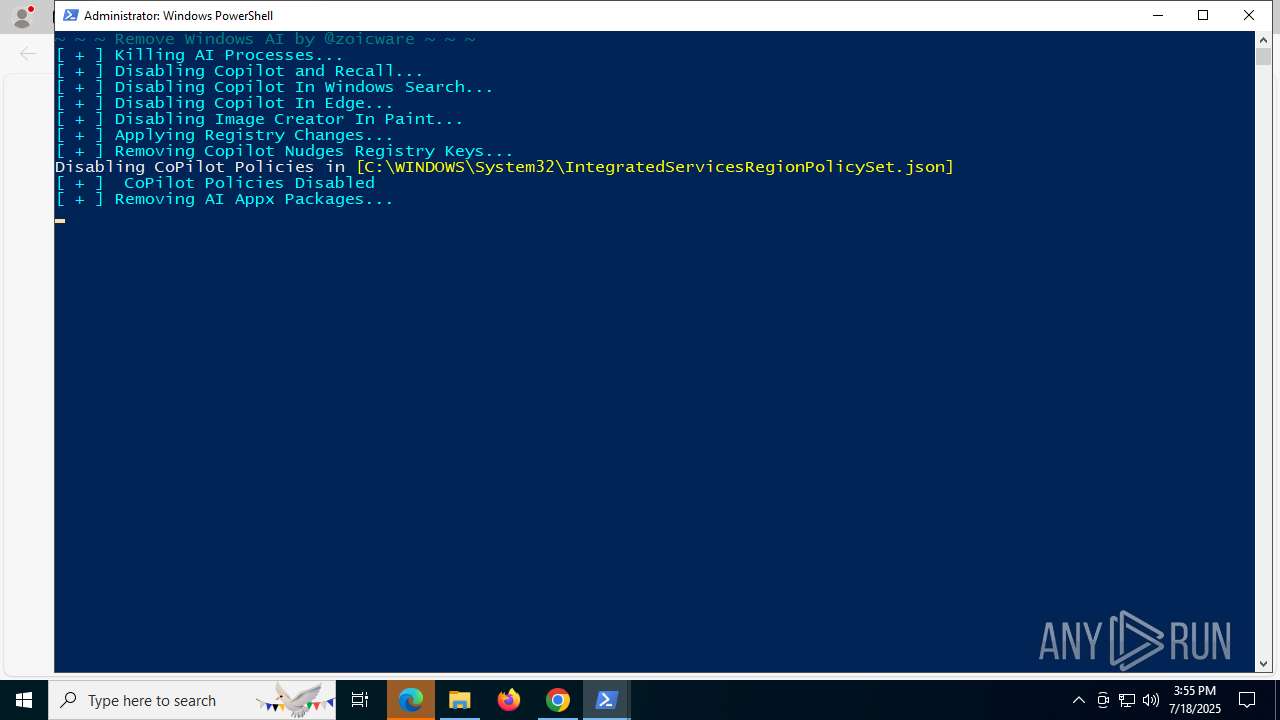
MALICIOUS
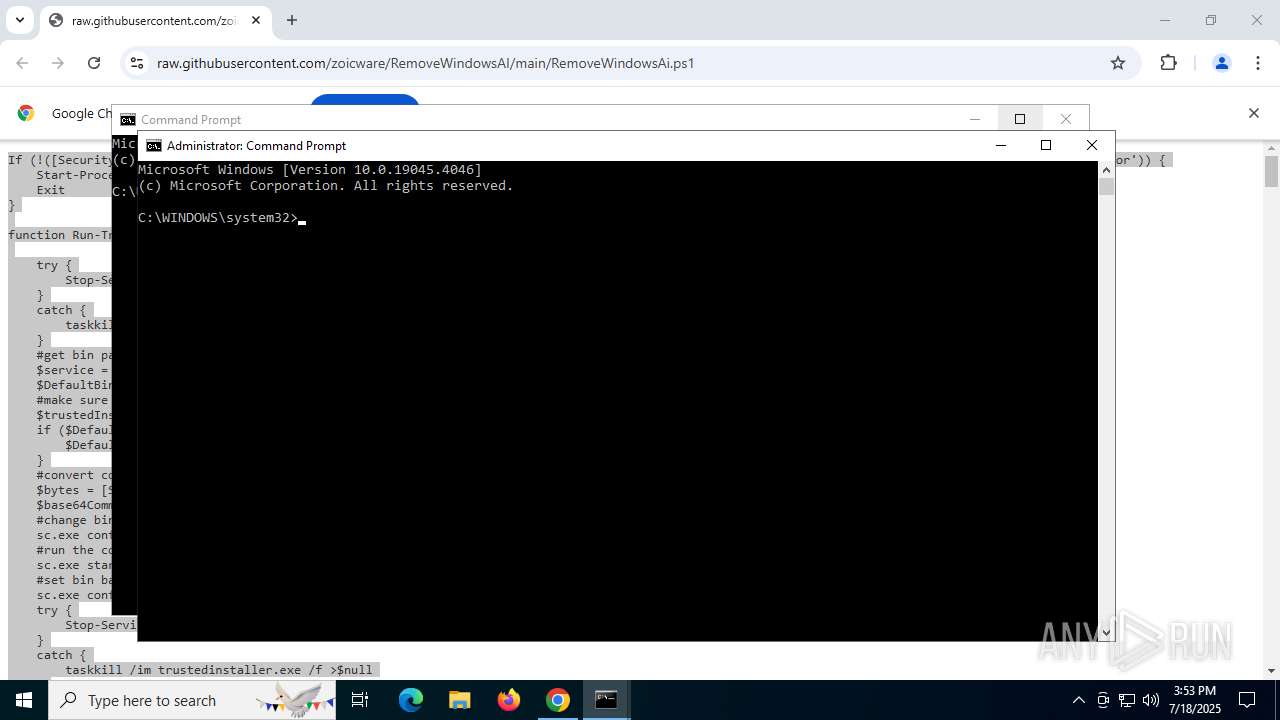
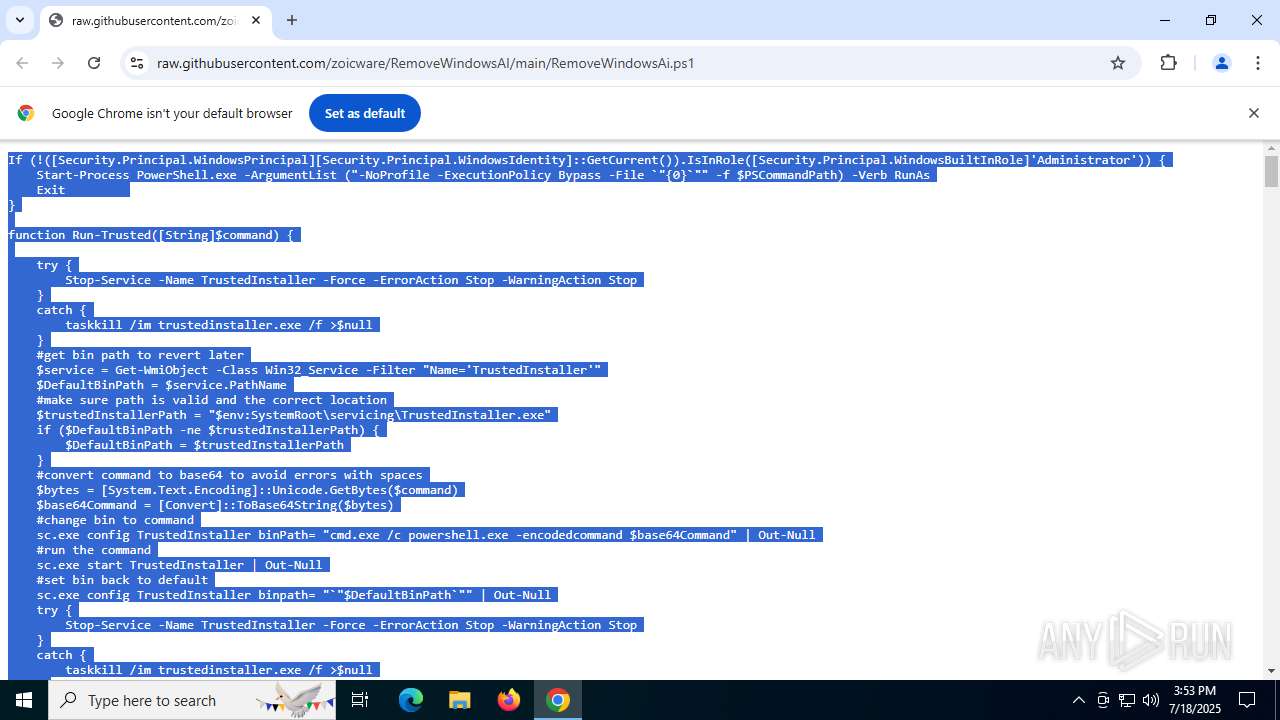
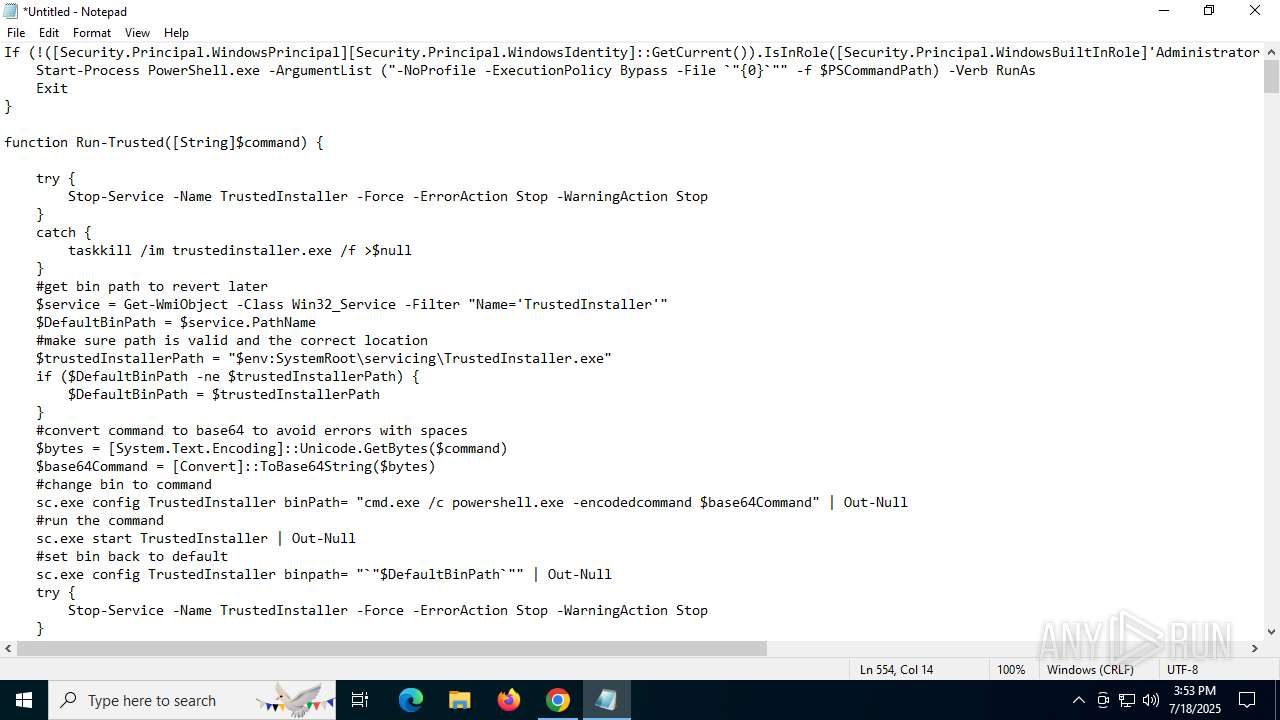
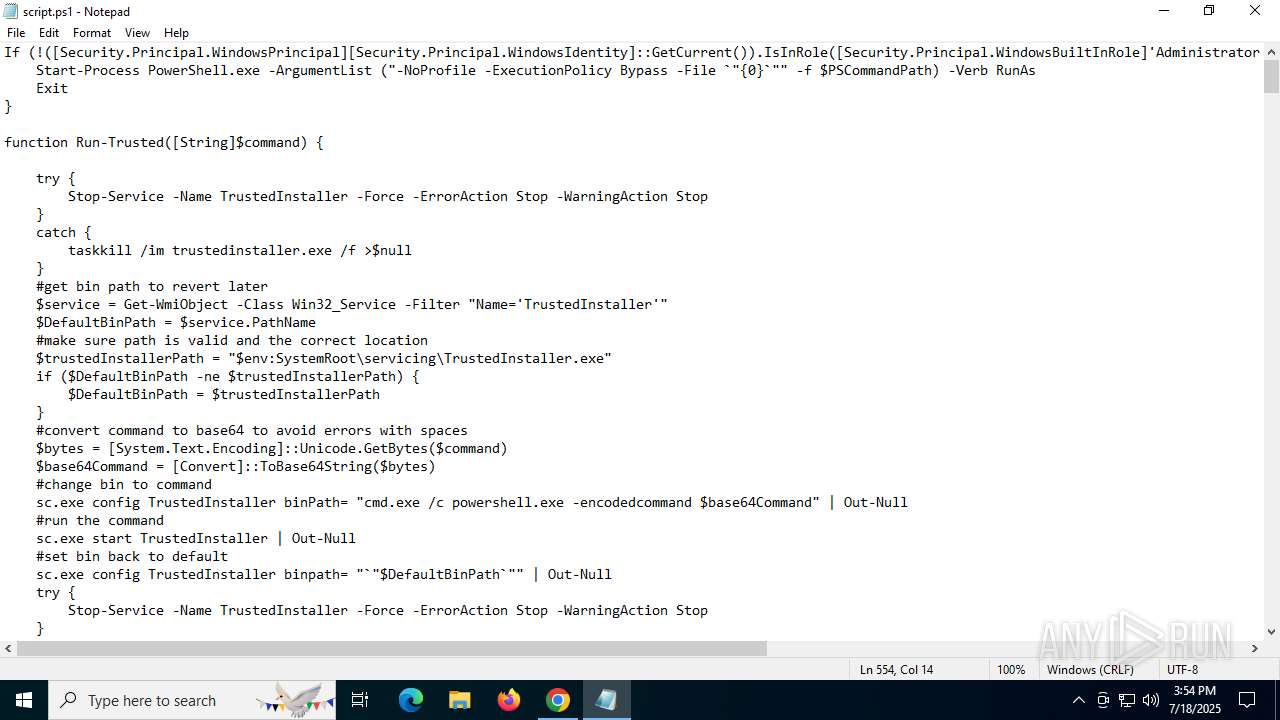
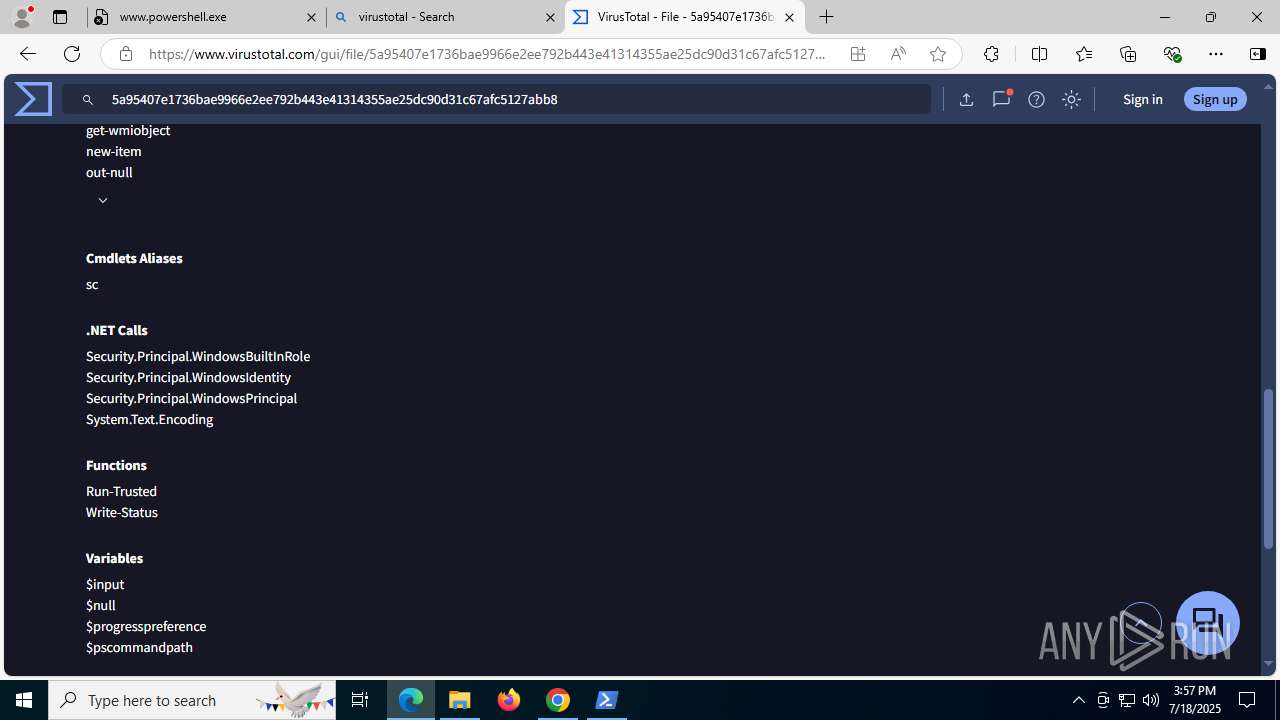
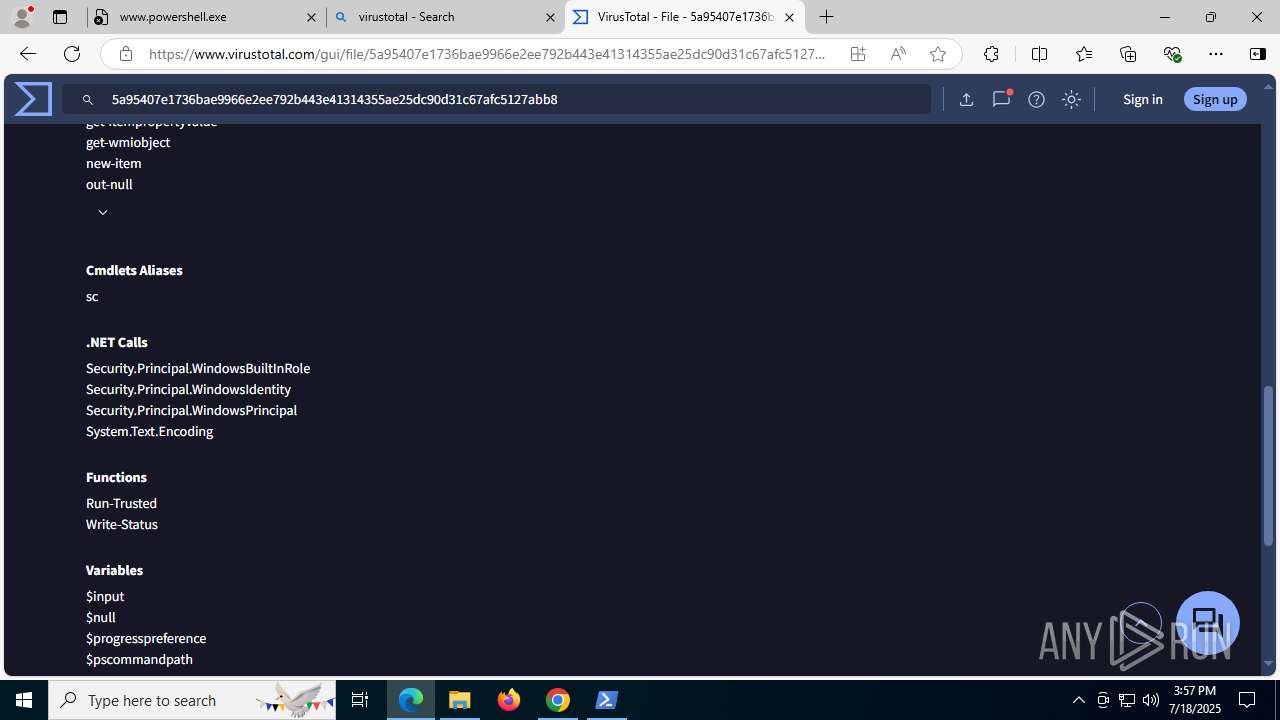
Bypass execution policy to execute commands
- powershell.exe (PID: 6140)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 2076)
SUSPICIOUS
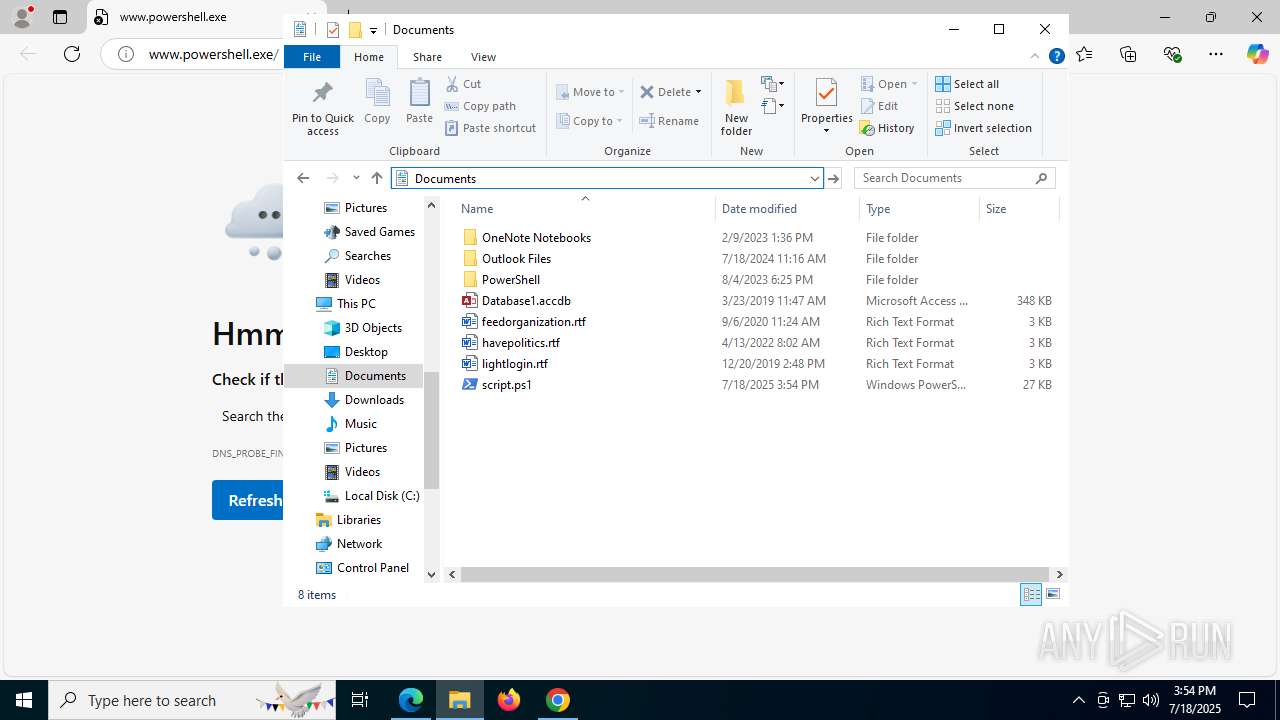
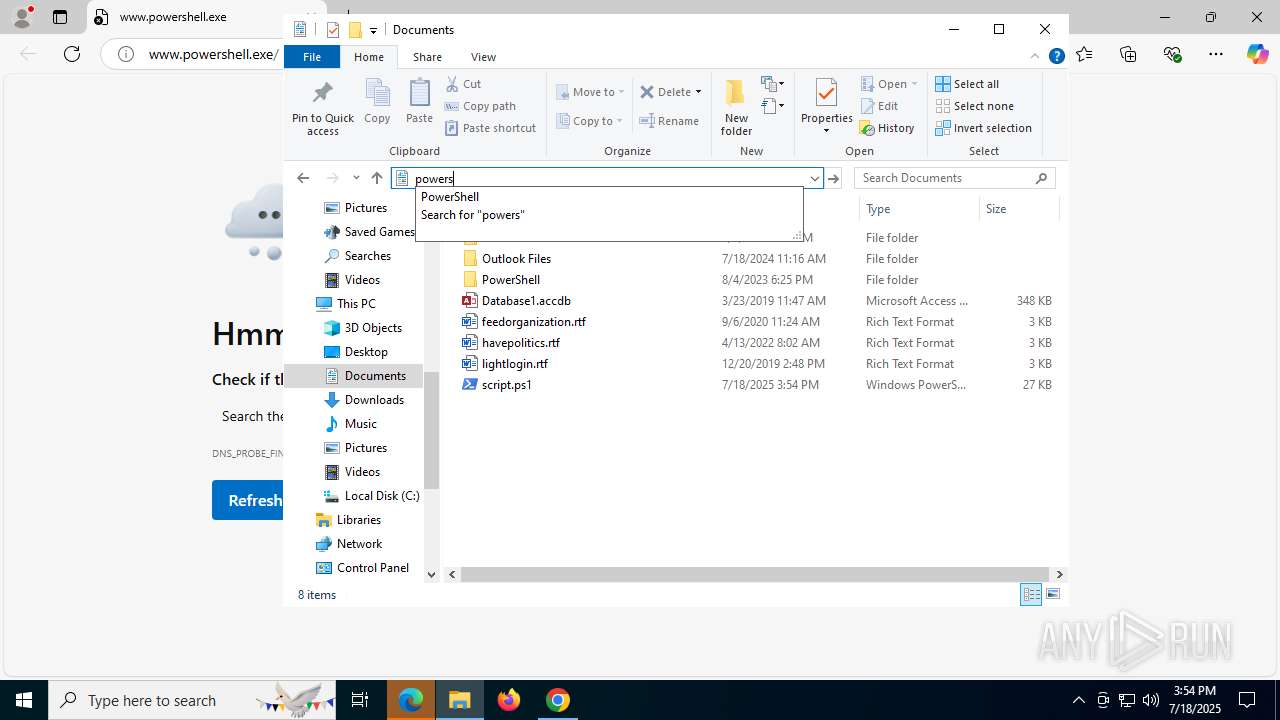
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 2076)
The process executes Powershell scripts
- powershell.exe (PID: 2076)
Application launched itself
- powershell.exe (PID: 2076)
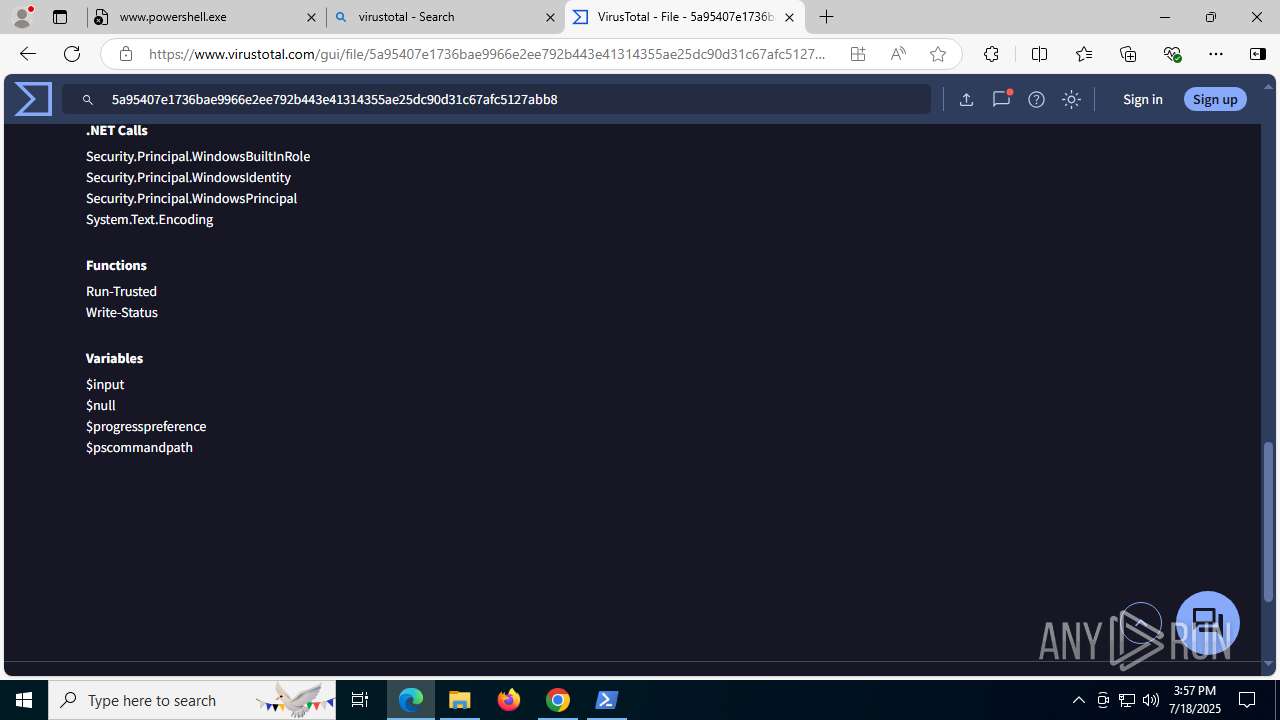
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 2076)
- powershell.exe (PID: 6140)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 2076)
- cmd.exe (PID: 8960)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 5476)
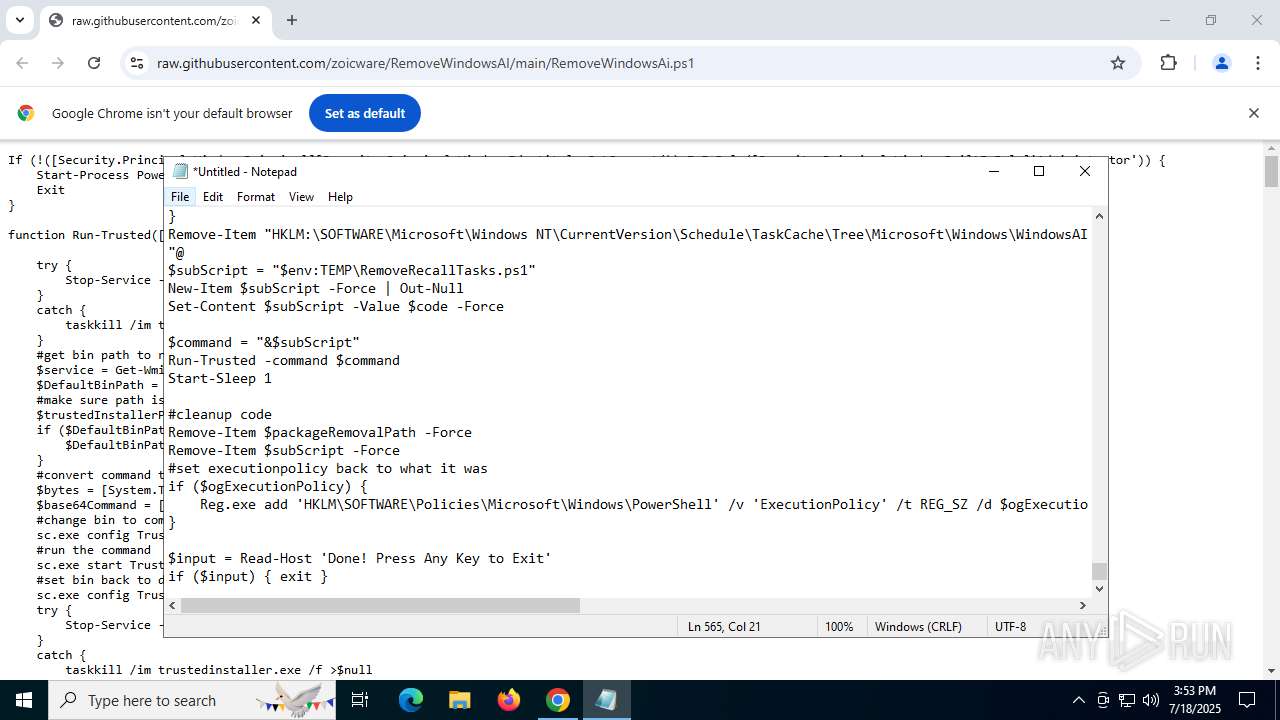
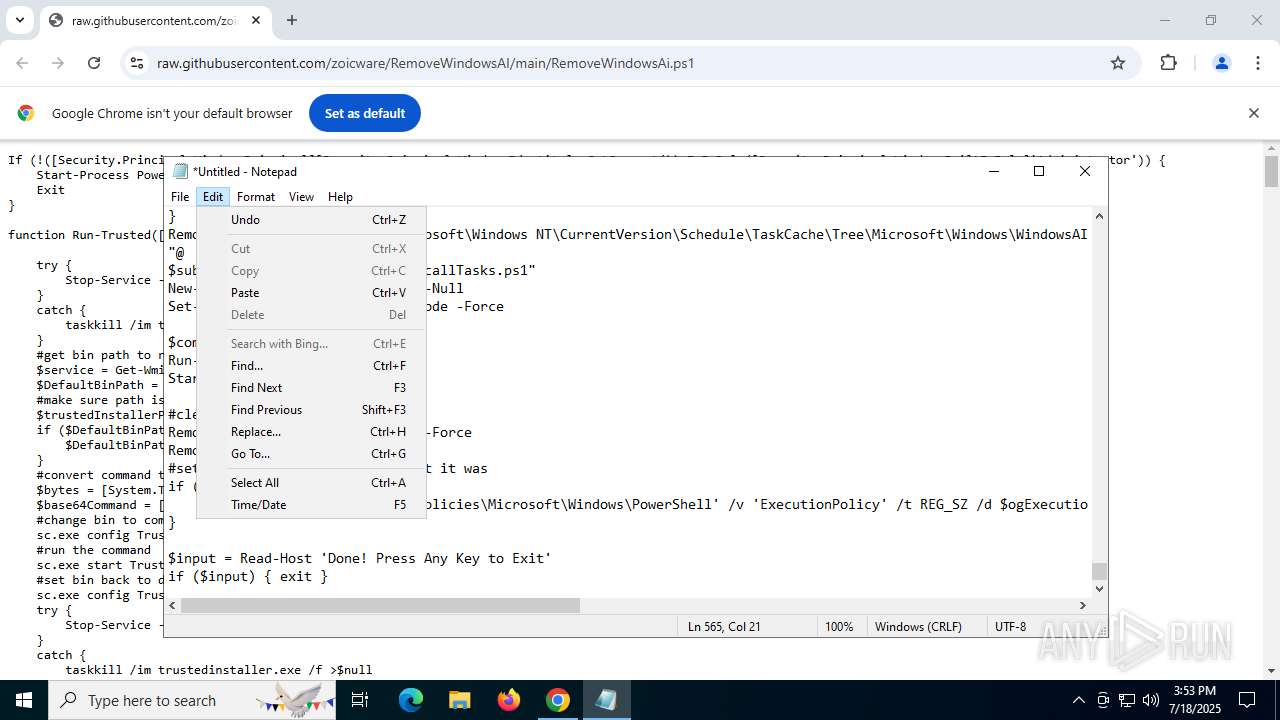
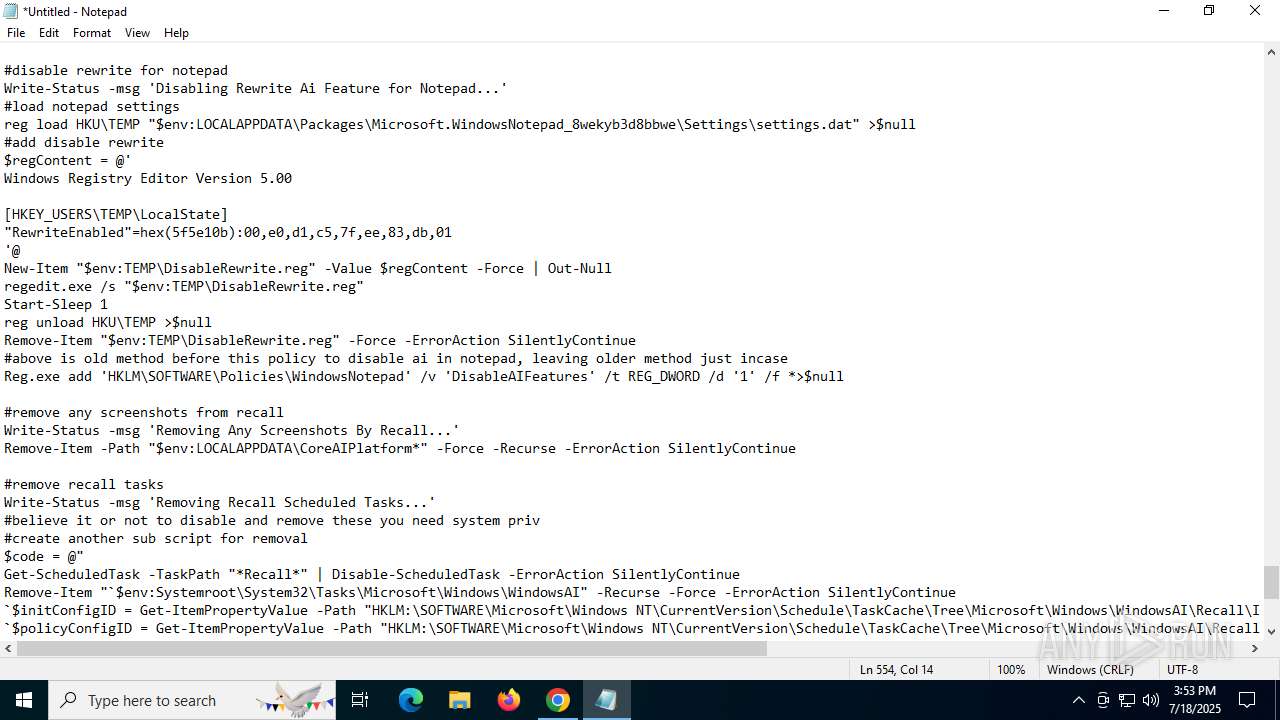
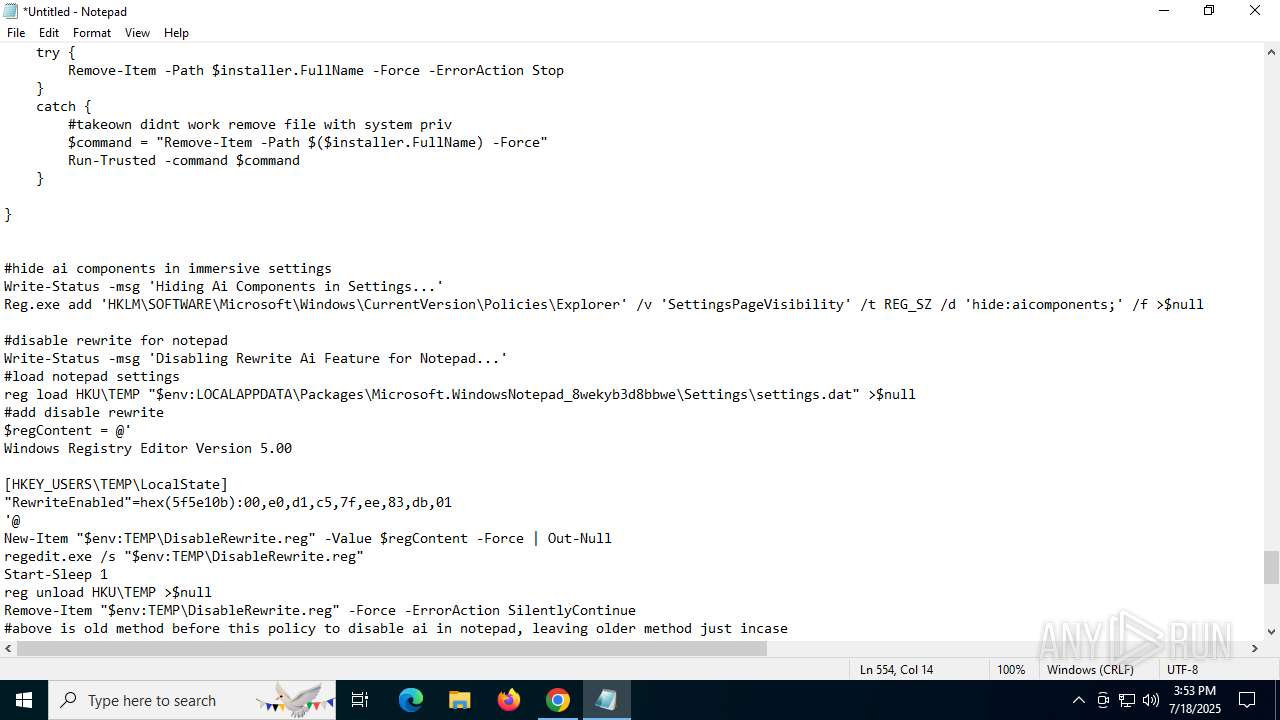
Uses REG/REGEDIT.EXE to modify registry
- powershell.exe (PID: 6140)
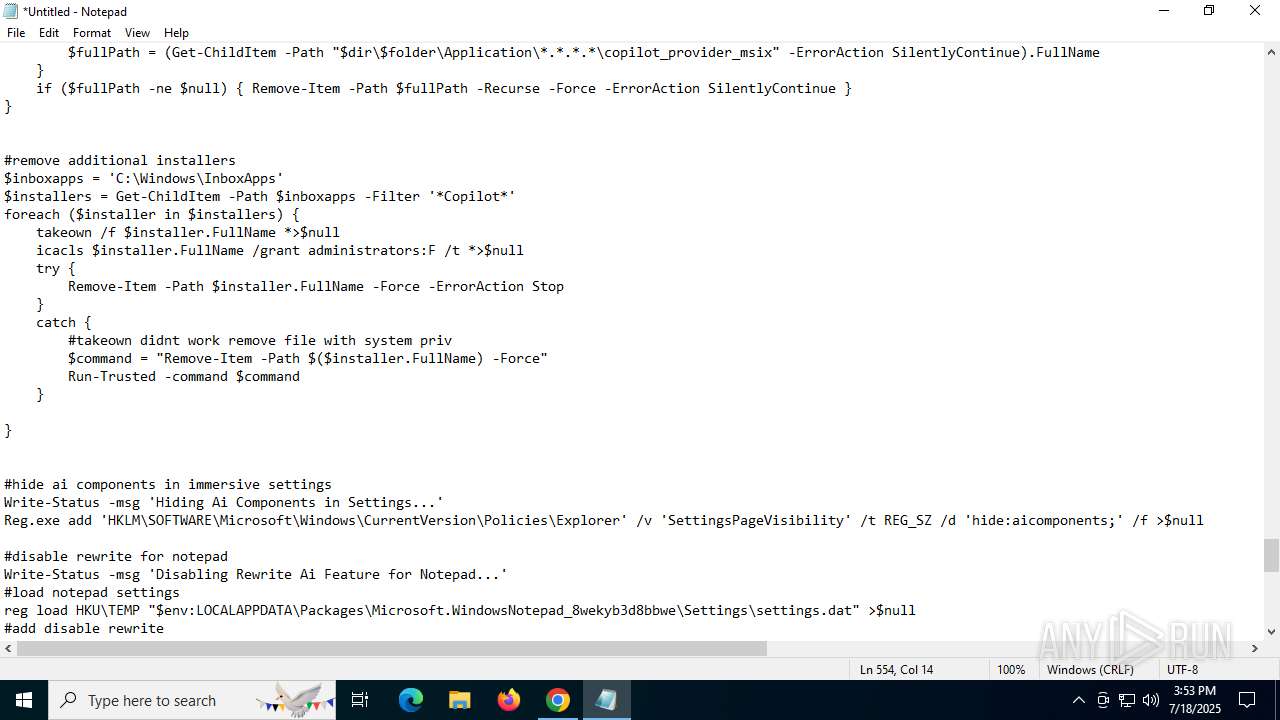
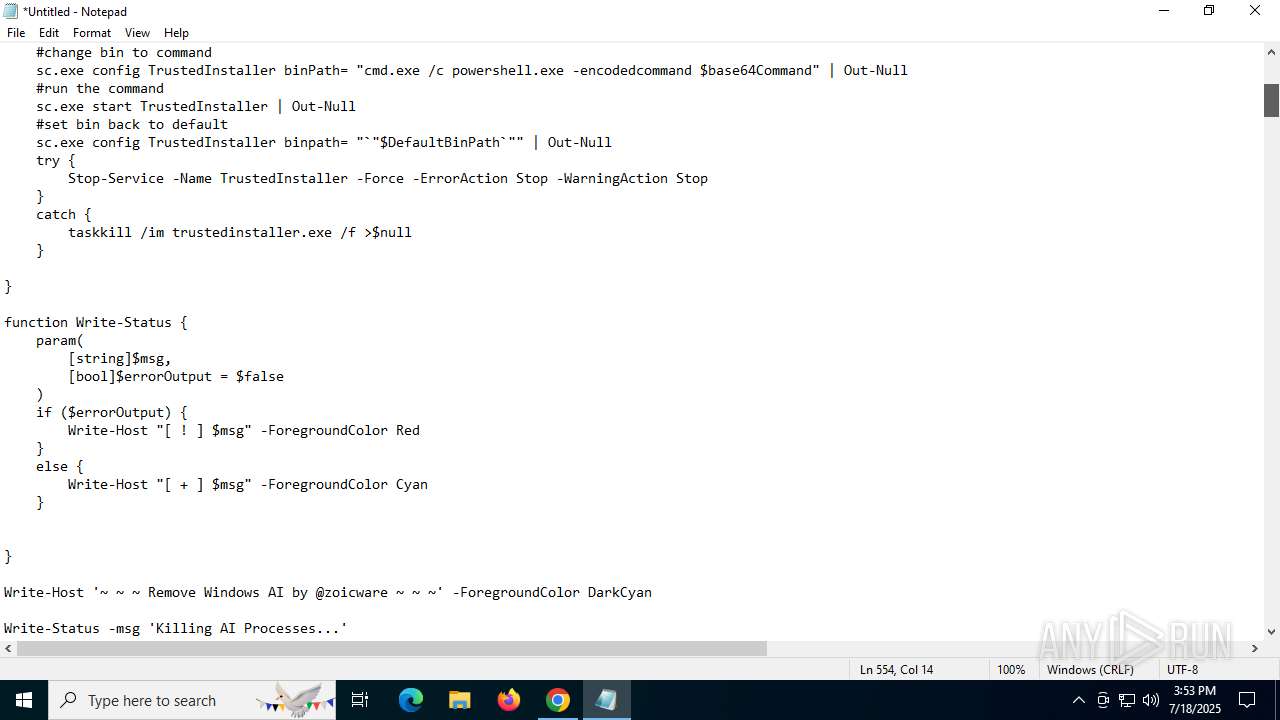
Takes ownership (TAKEOWN.EXE)
- powershell.exe (PID: 6140)
Starts SC.EXE for service management
- powershell.exe (PID: 6140)
Windows service management via SC.EXE
- sc.exe (PID: 6508)
- sc.exe (PID: 8916)
- sc.exe (PID: 8940)
- sc.exe (PID: 6664)
- sc.exe (PID: 6680)
- sc.exe (PID: 8056)
- sc.exe (PID: 620)
- sc.exe (PID: 4024)
- sc.exe (PID: 7140)
- sc.exe (PID: 8916)
- sc.exe (PID: 6092)
- sc.exe (PID: 9132)
- sc.exe (PID: 8924)
Executes as Windows Service
- cmd.exe (PID: 8960)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 5476)
Base64-obfuscated command line is found
- cmd.exe (PID: 8960)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 5476)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 8960)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 5476)
Uses TASKKILL.EXE to kill process
- powershell.exe (PID: 6140)
Creates or modifies Windows services
- reg.exe (PID: 4024)
Uses ICACLS.EXE to modify access control lists
- powershell.exe (PID: 6140)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6140)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 8368)
- DismHost.exe (PID: 9188)
- DismHost.exe (PID: 7428)
Executable content was dropped or overwritten
- powershell.exe (PID: 6140)
- powershell.exe (PID: 8976)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 6140)
- powershell.exe (PID: 8976)
The process creates files with name similar to system file names
- powershell.exe (PID: 6140)
- powershell.exe (PID: 8976)
Process drops legitimate windows executable
- powershell.exe (PID: 8976)
- powershell.exe (PID: 6140)
INFO
Application launched itself
- chrome.exe (PID: 6460)
- msedge.exe (PID: 7296)
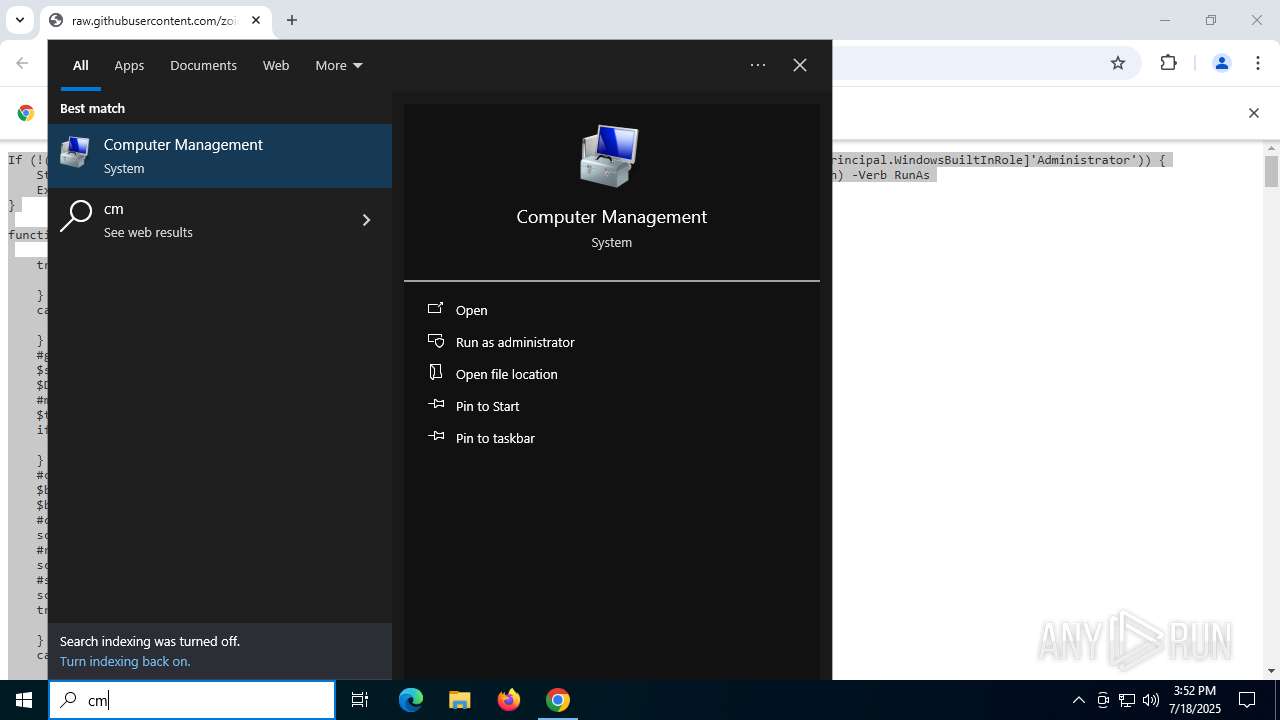
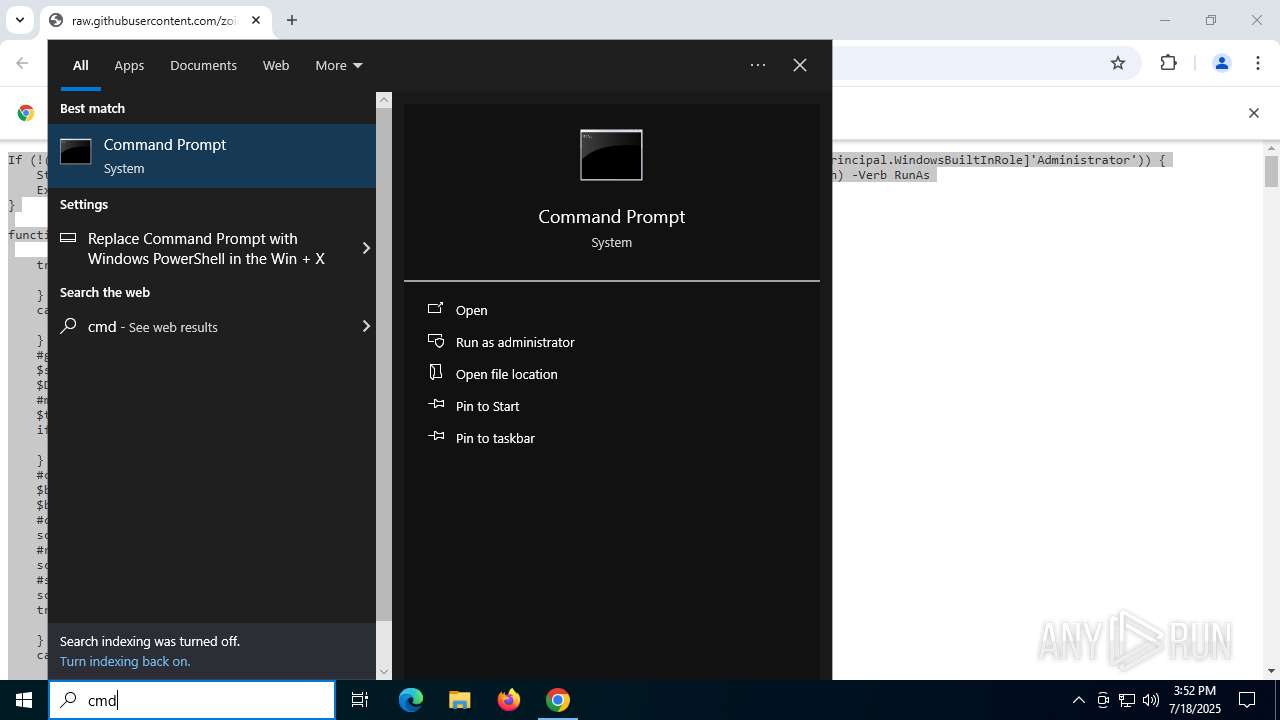
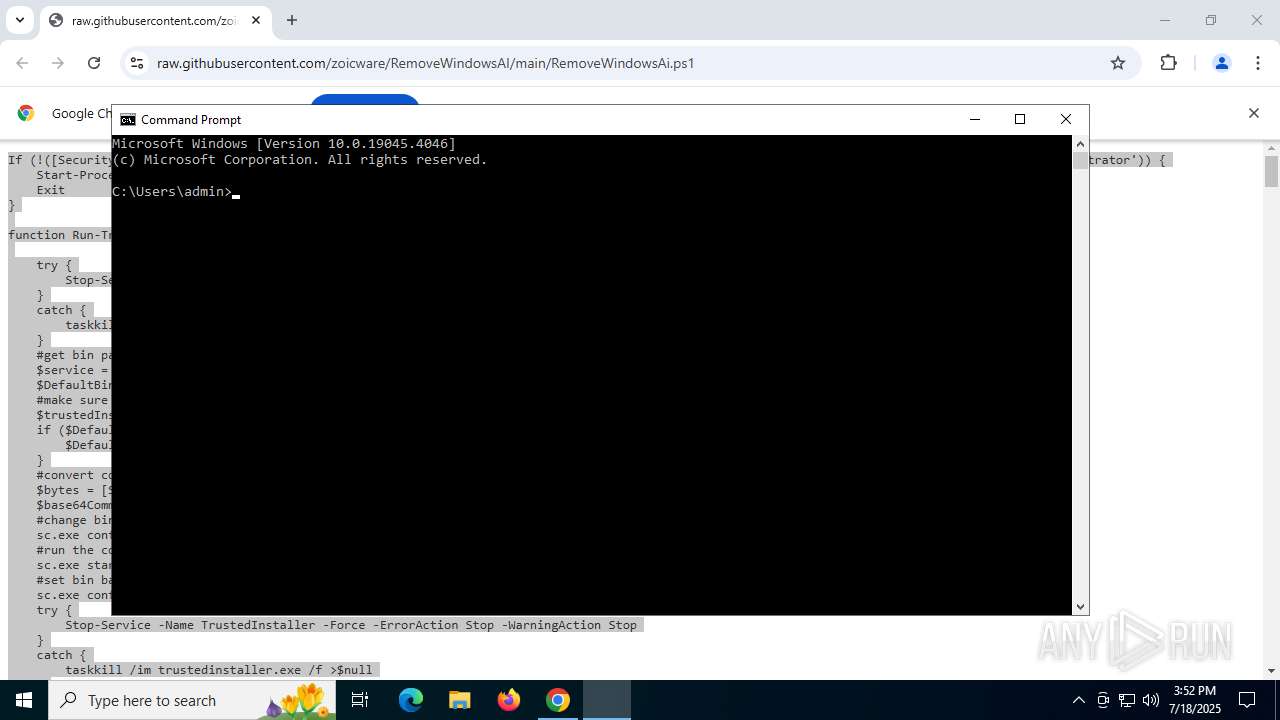
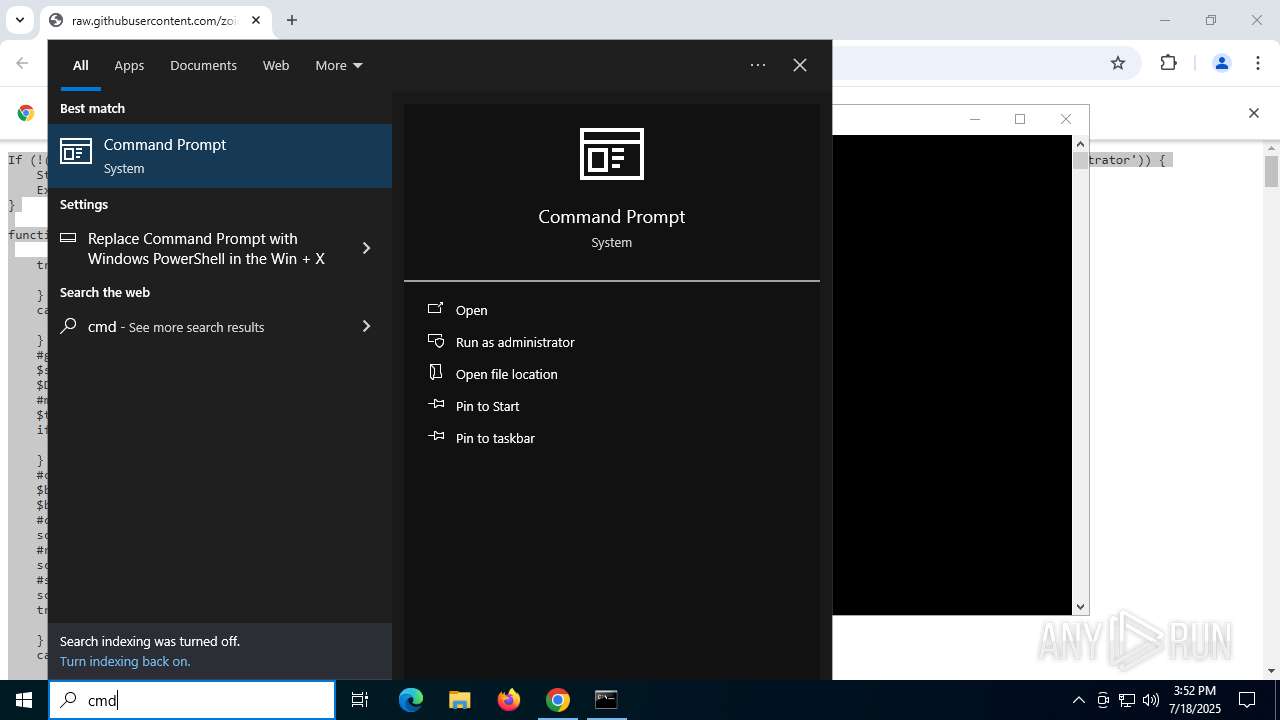
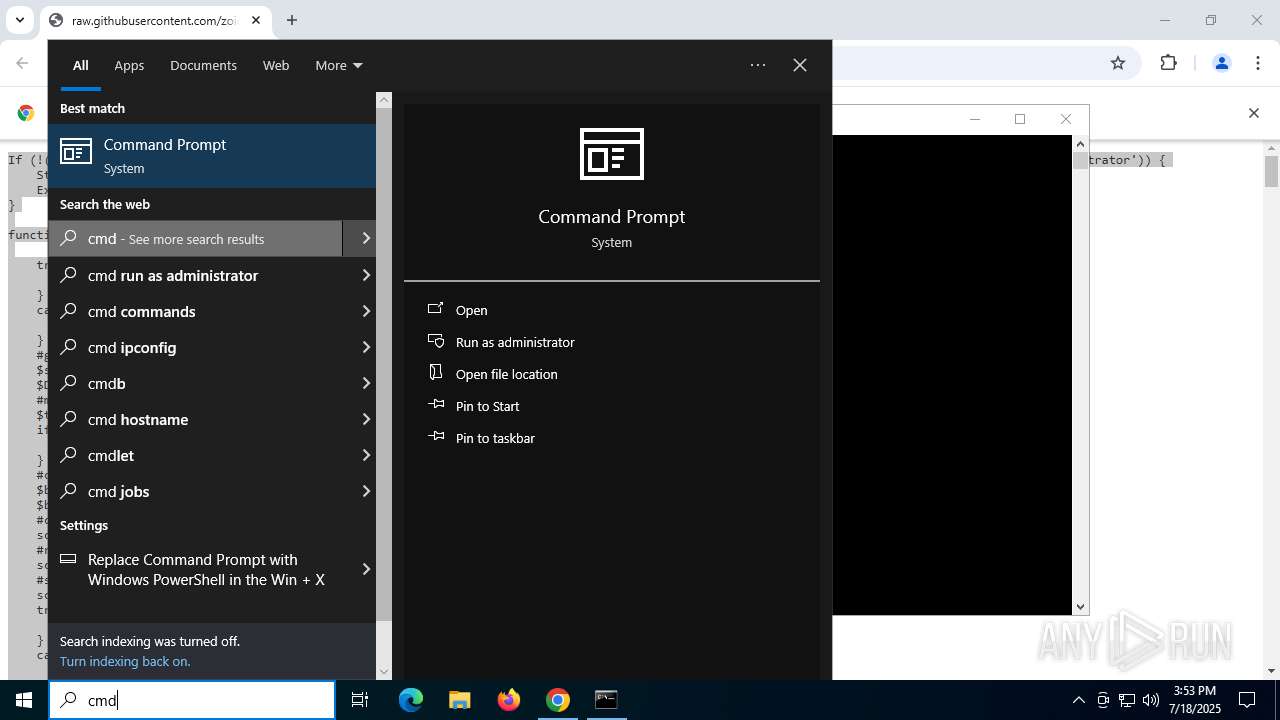
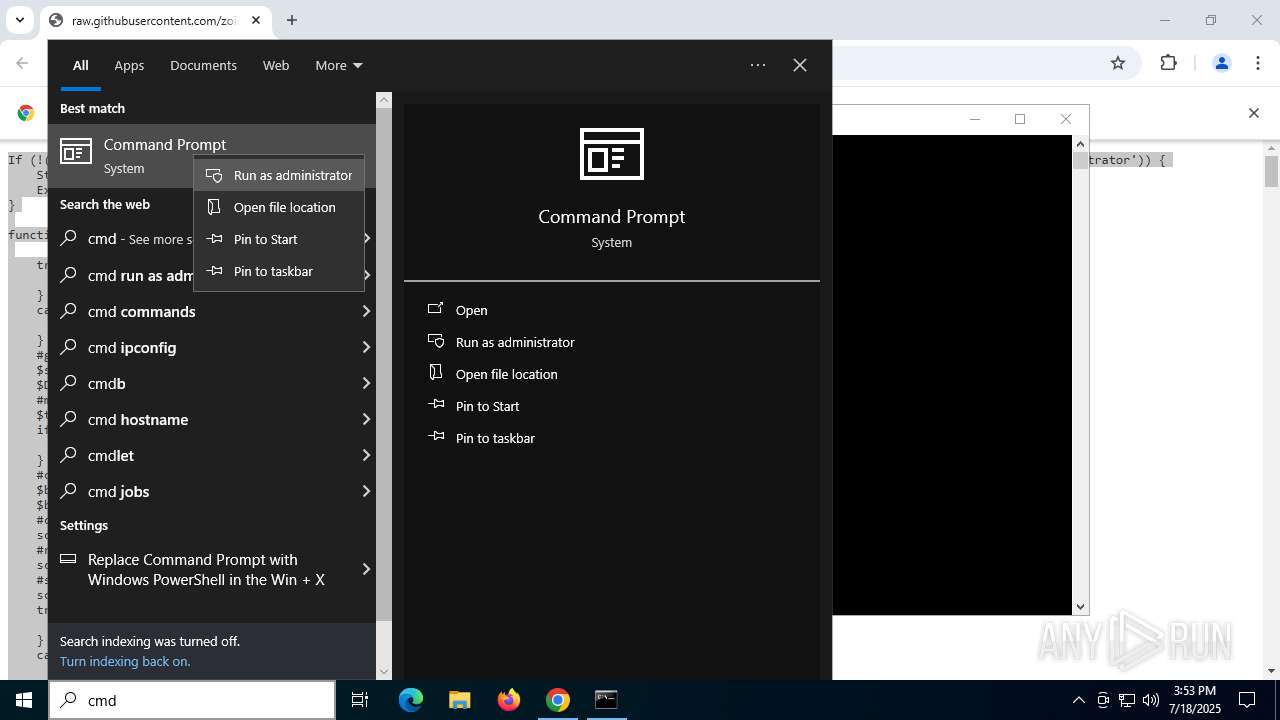
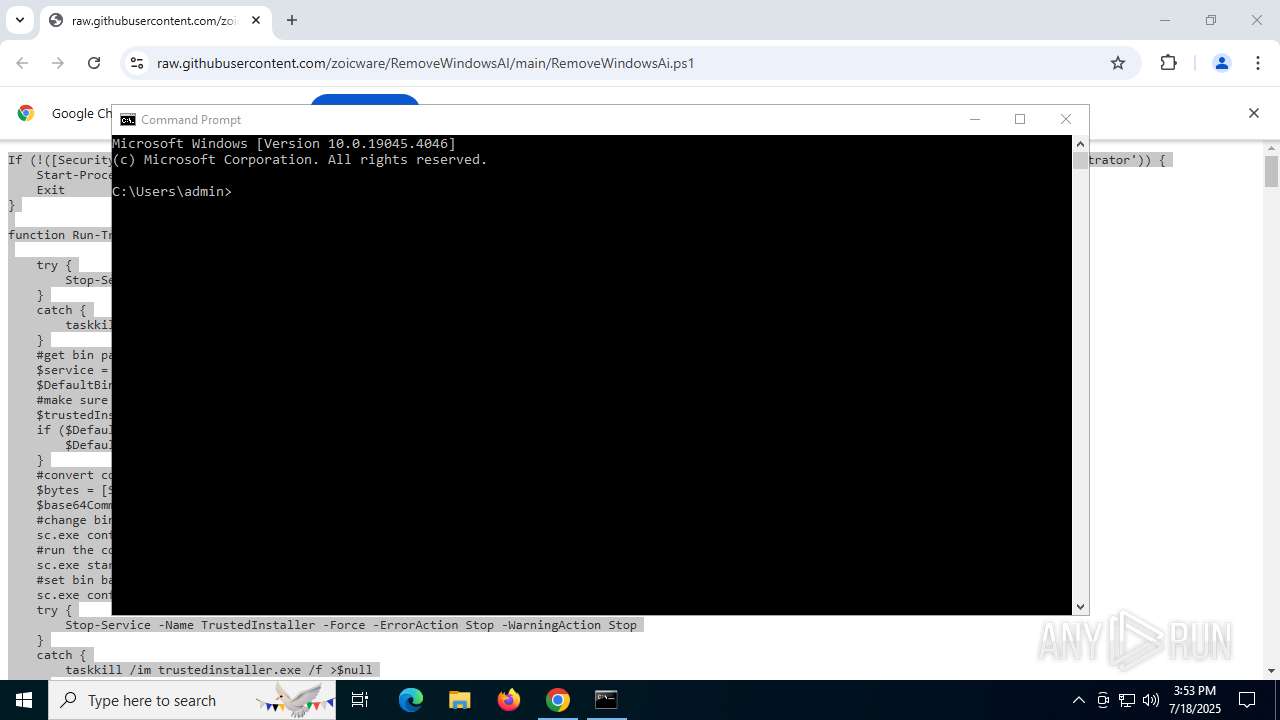
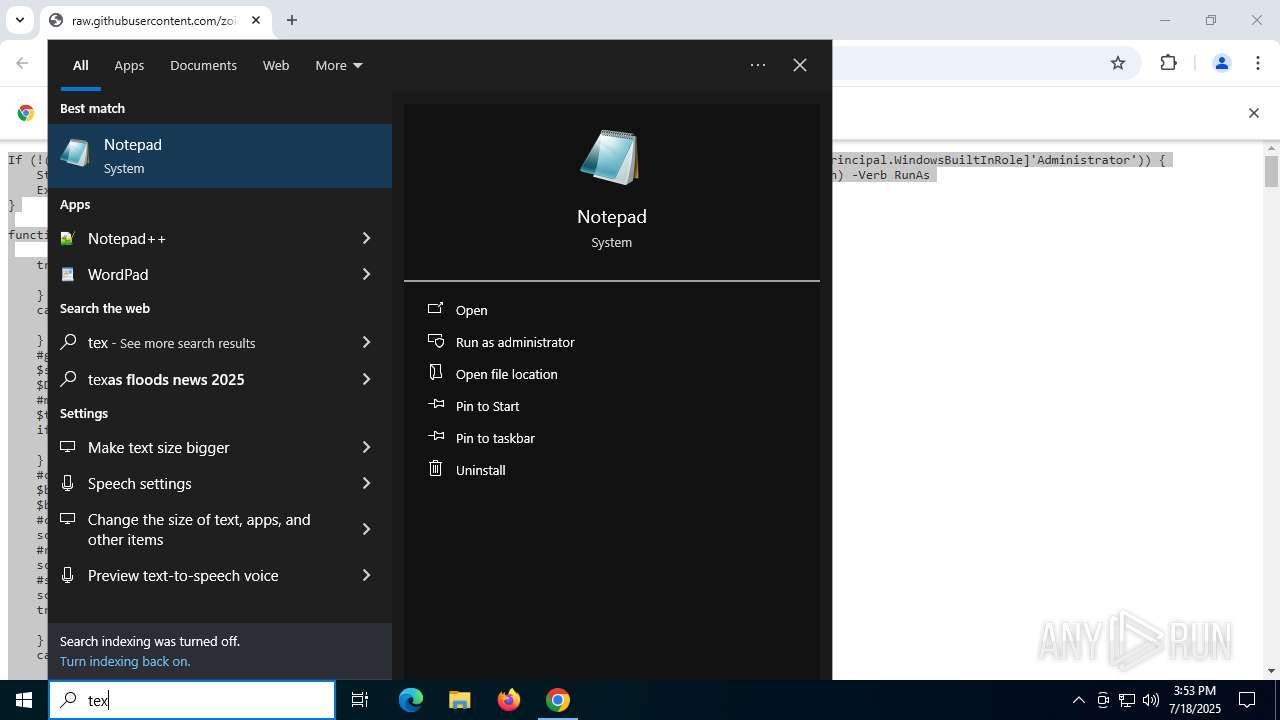
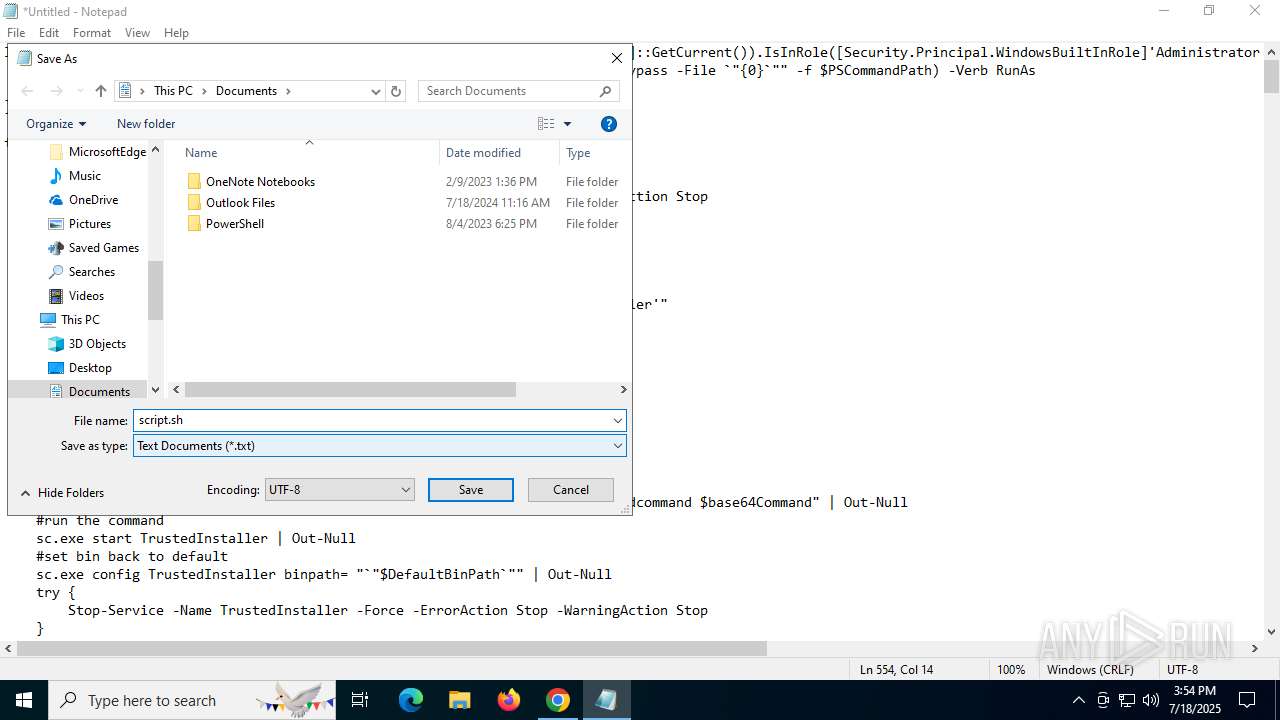
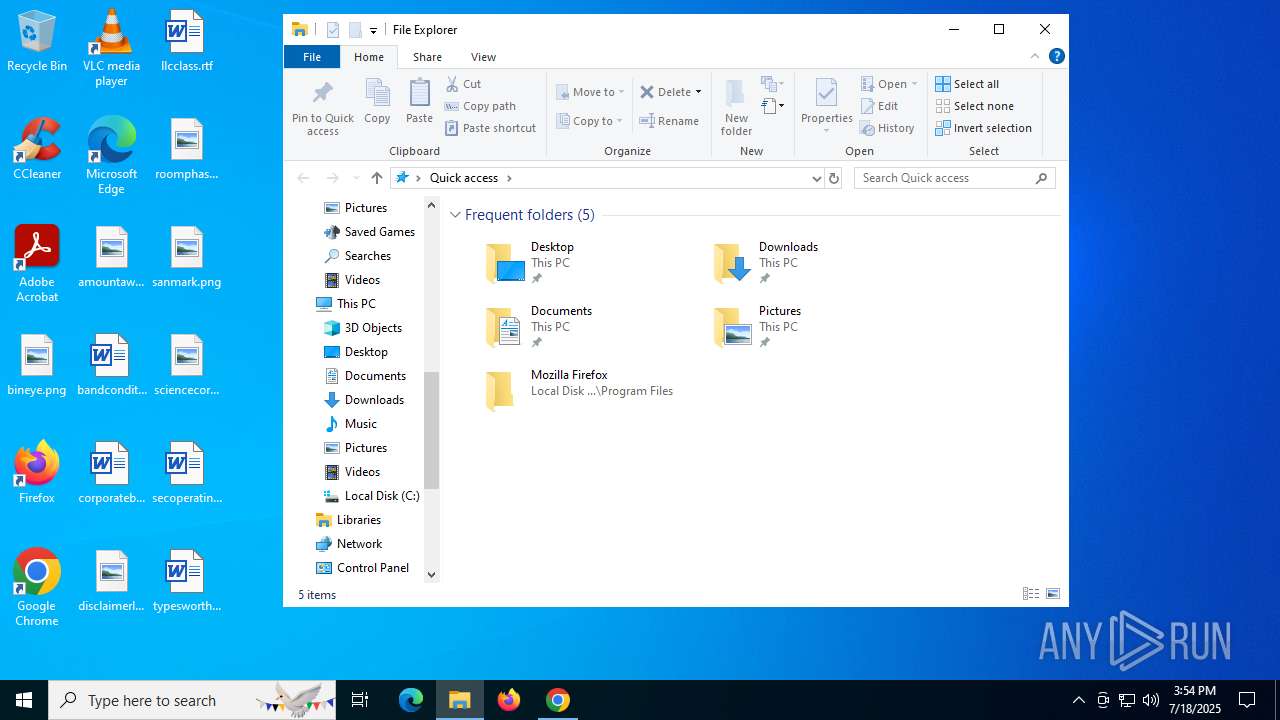
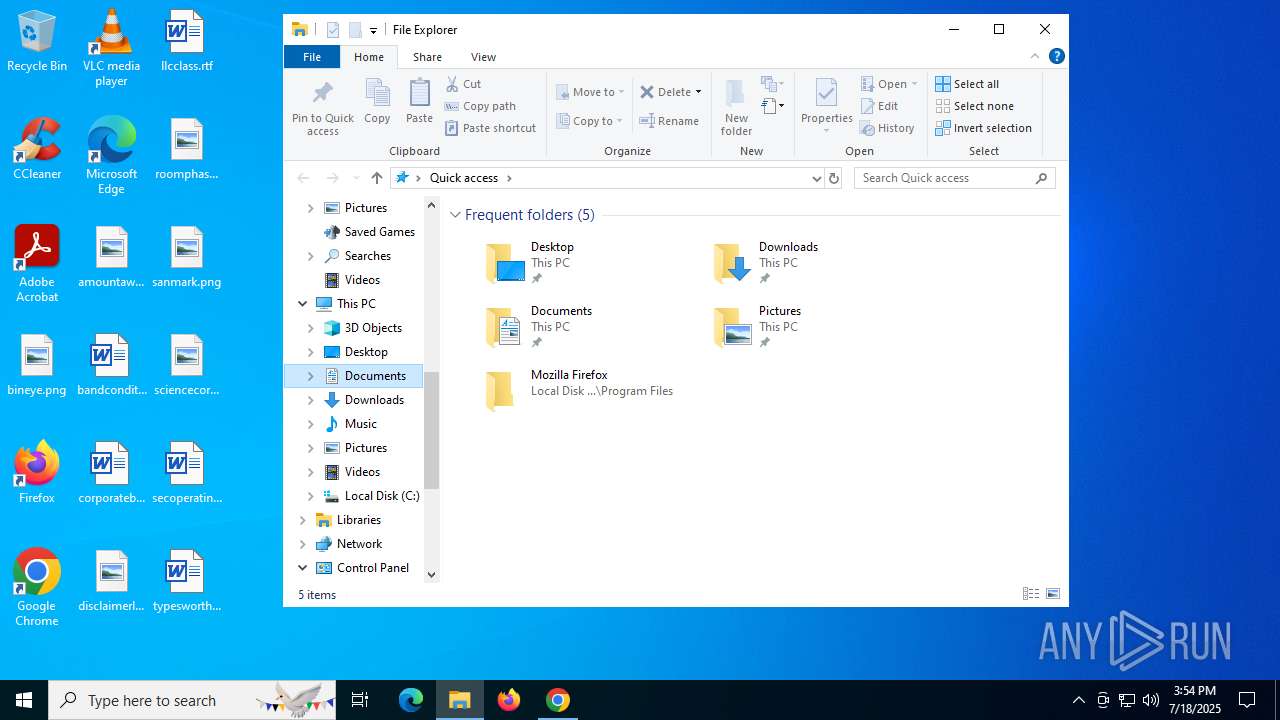
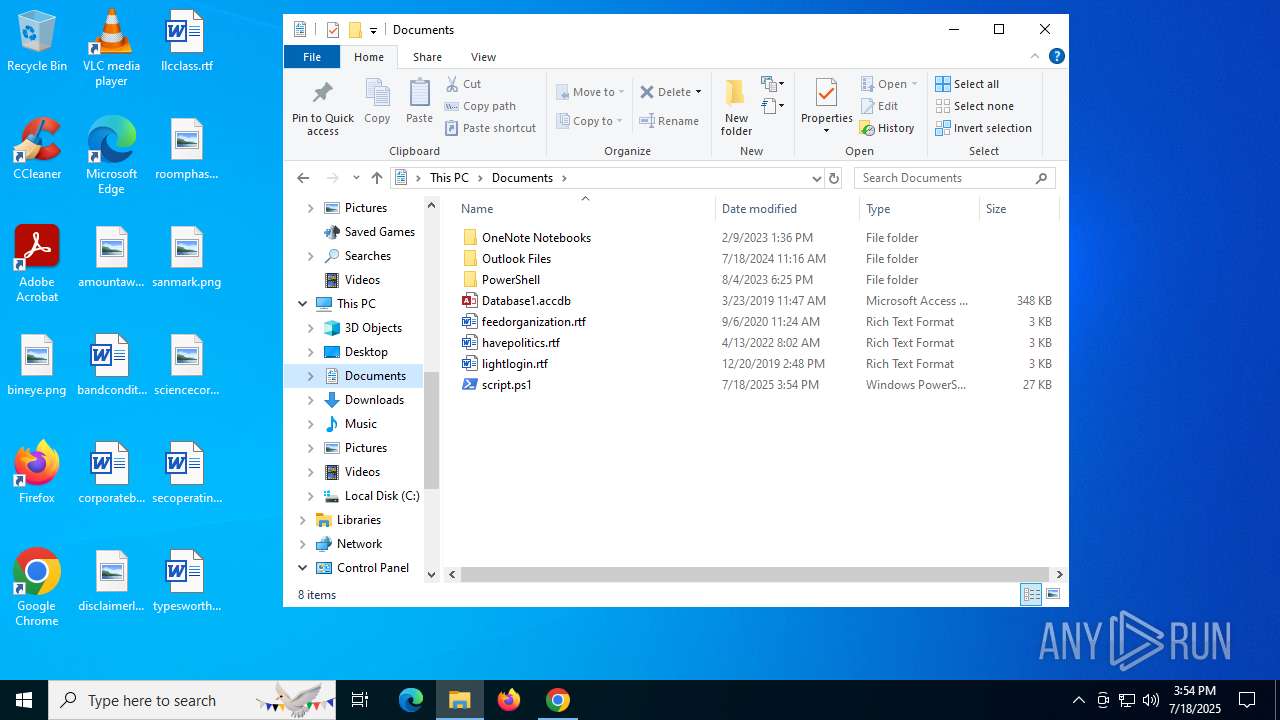
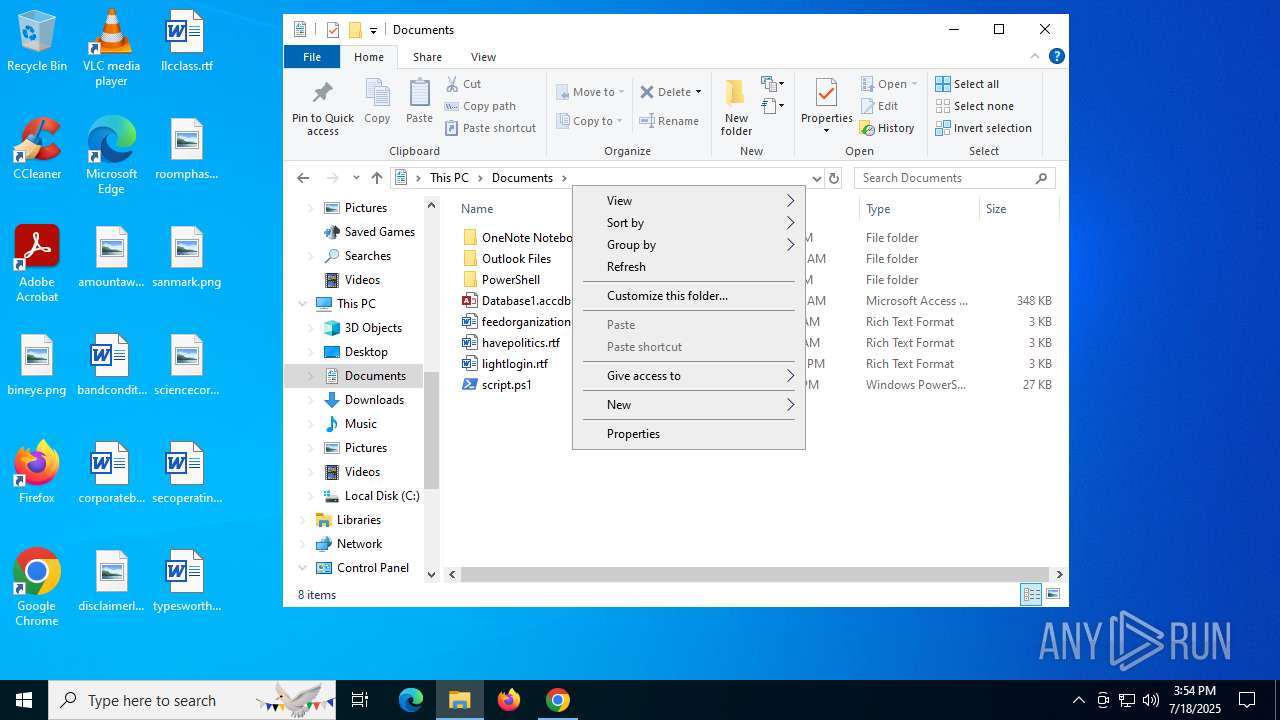
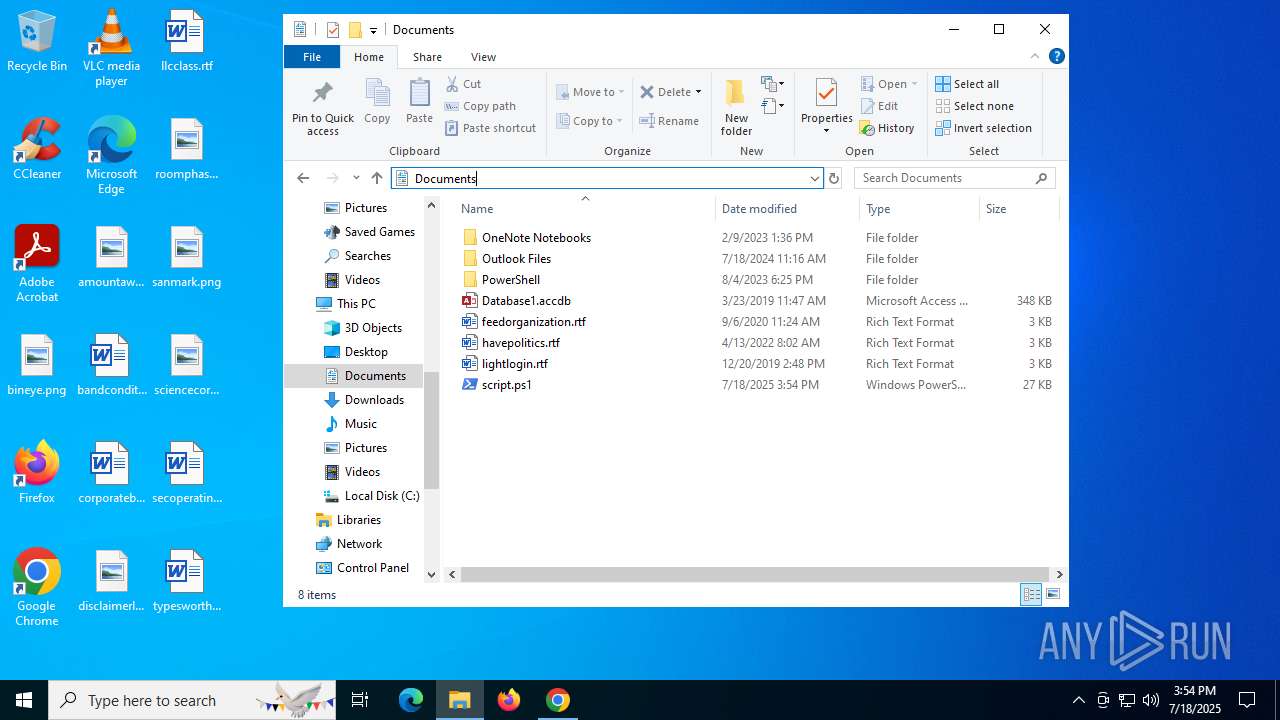
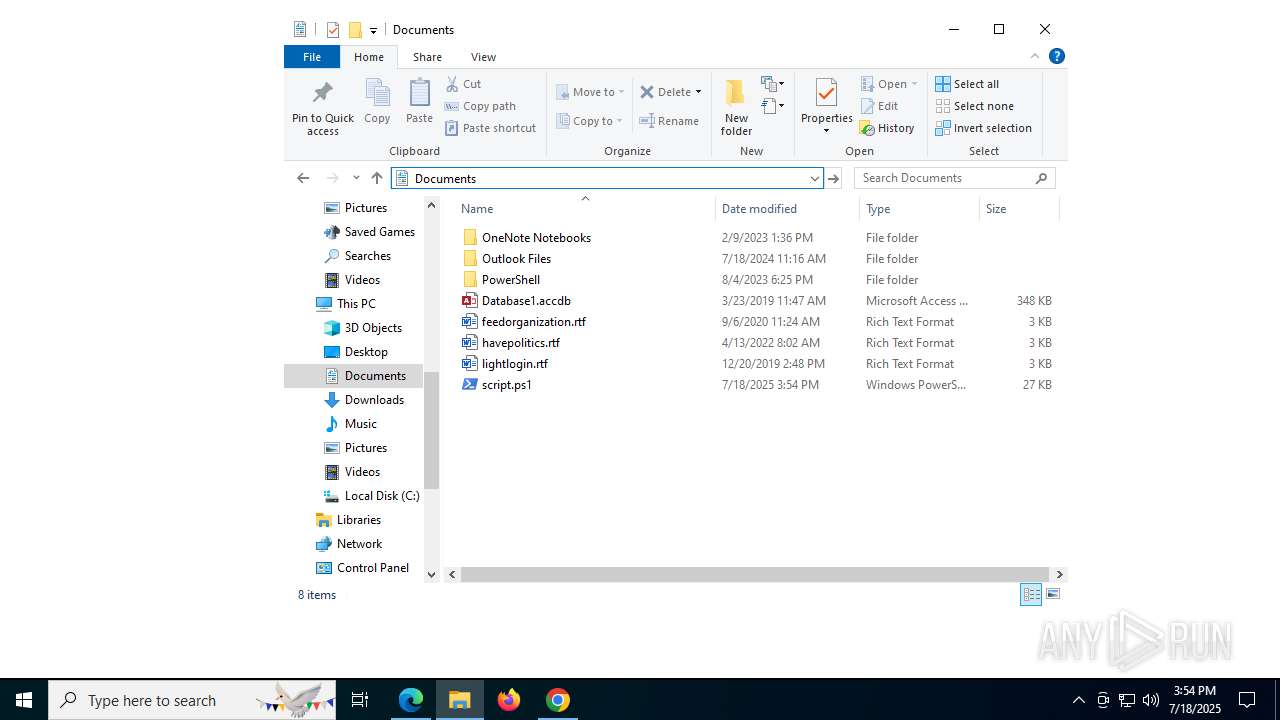
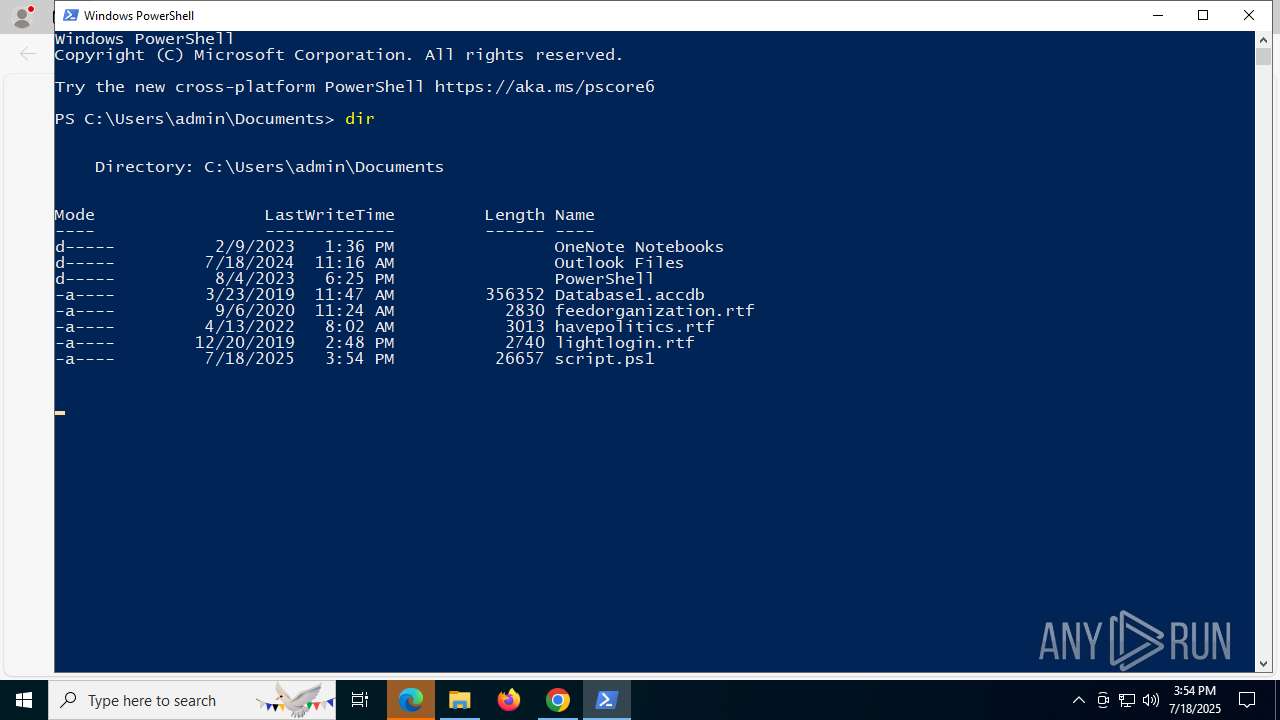
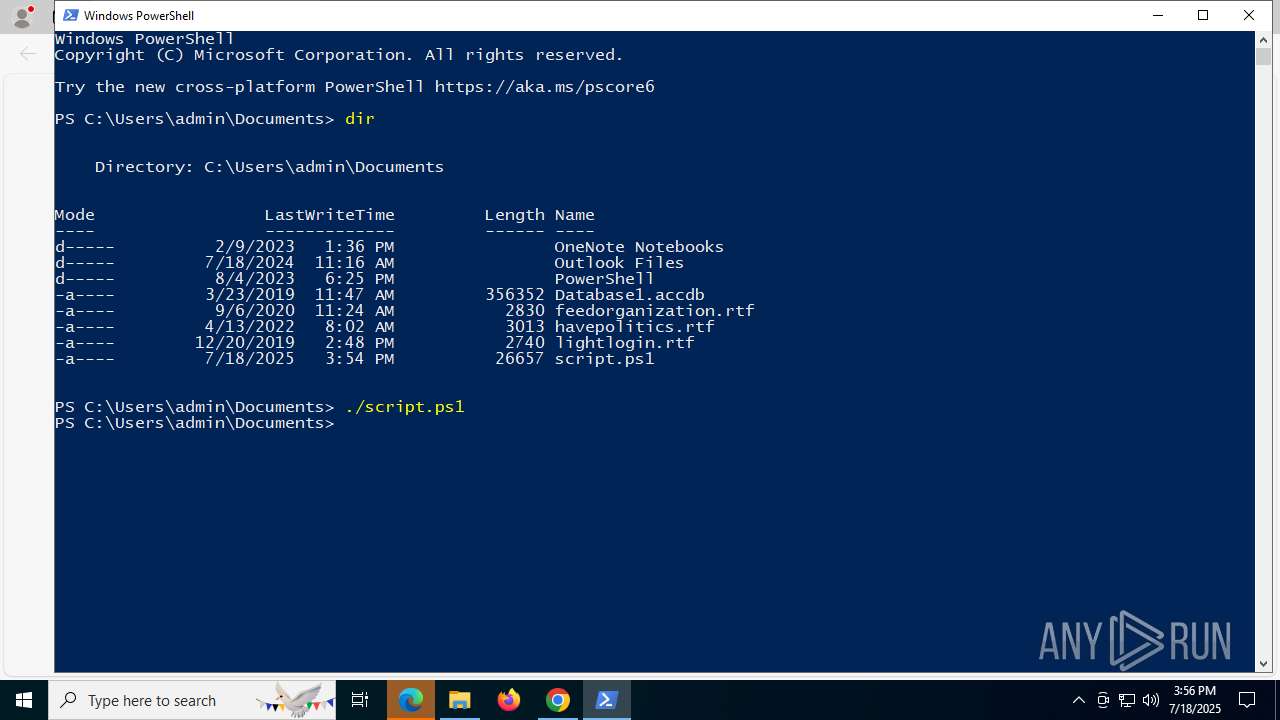
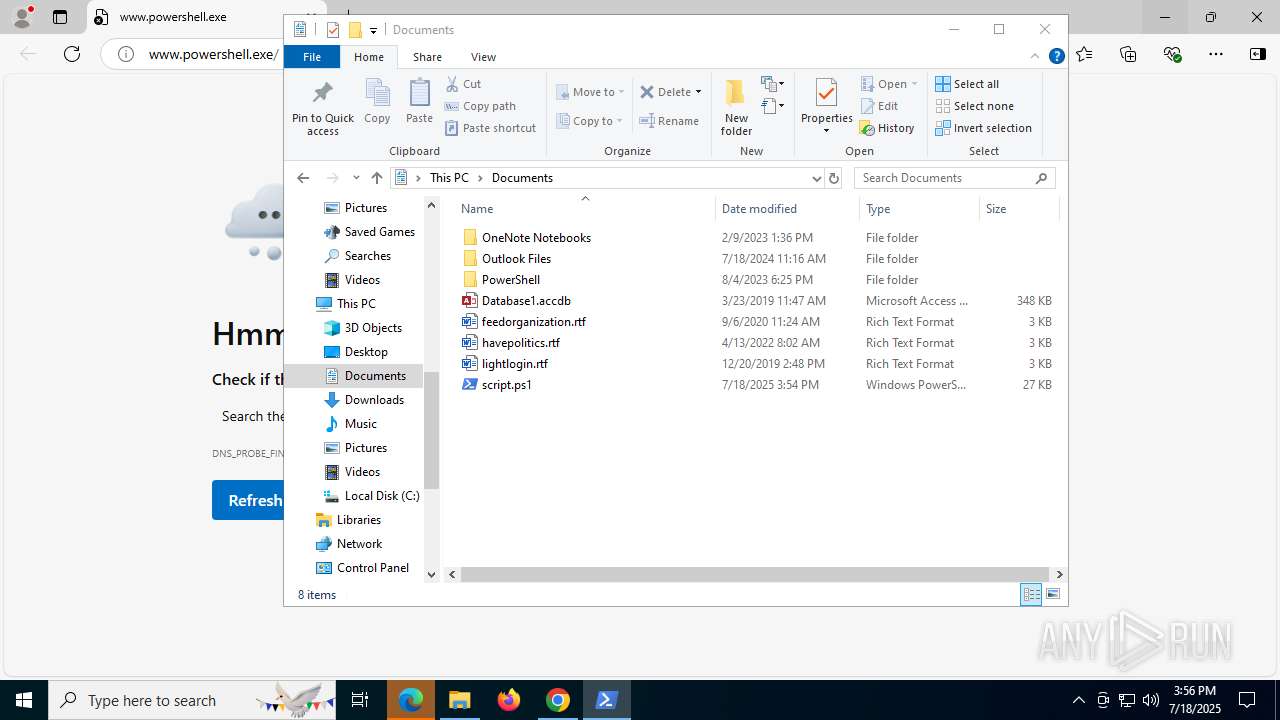
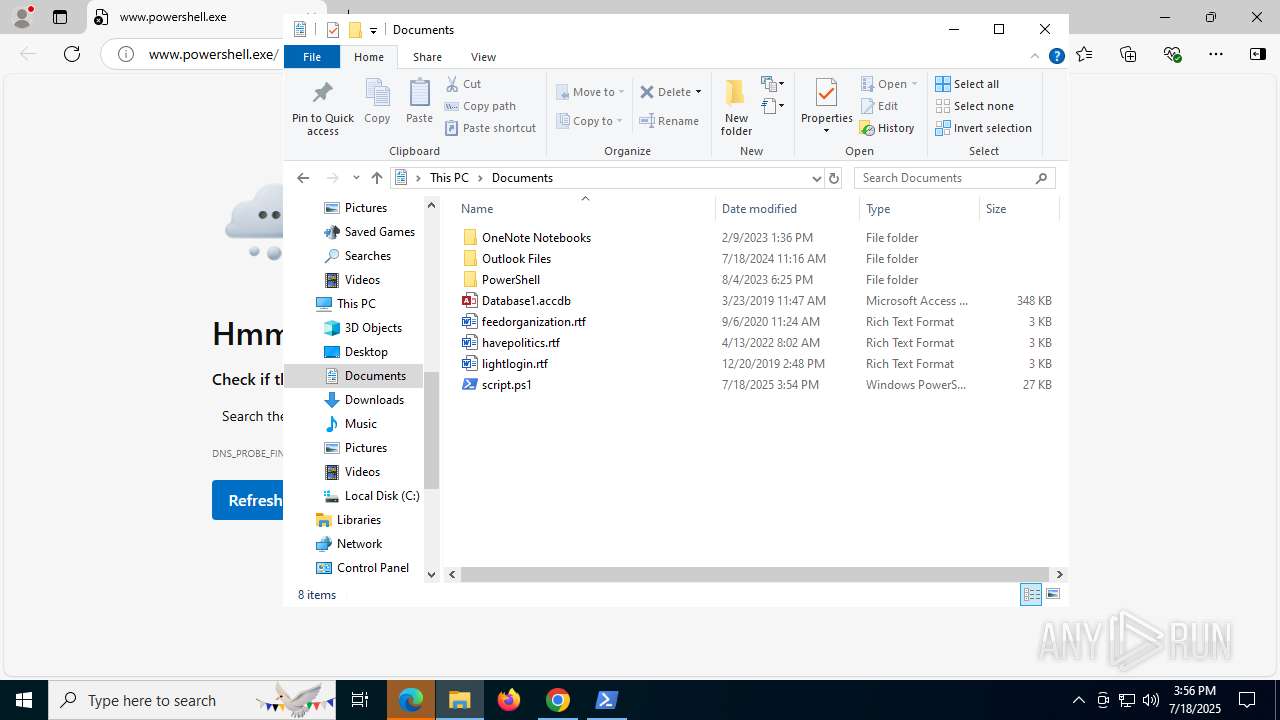
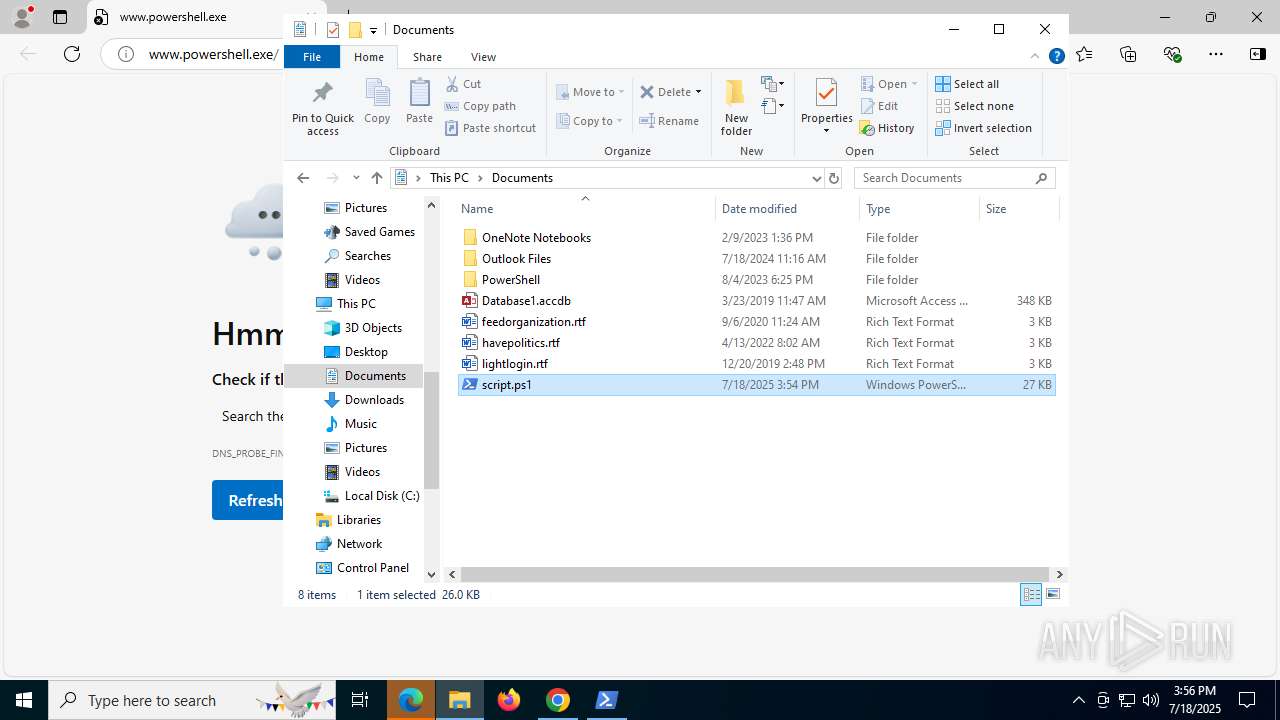
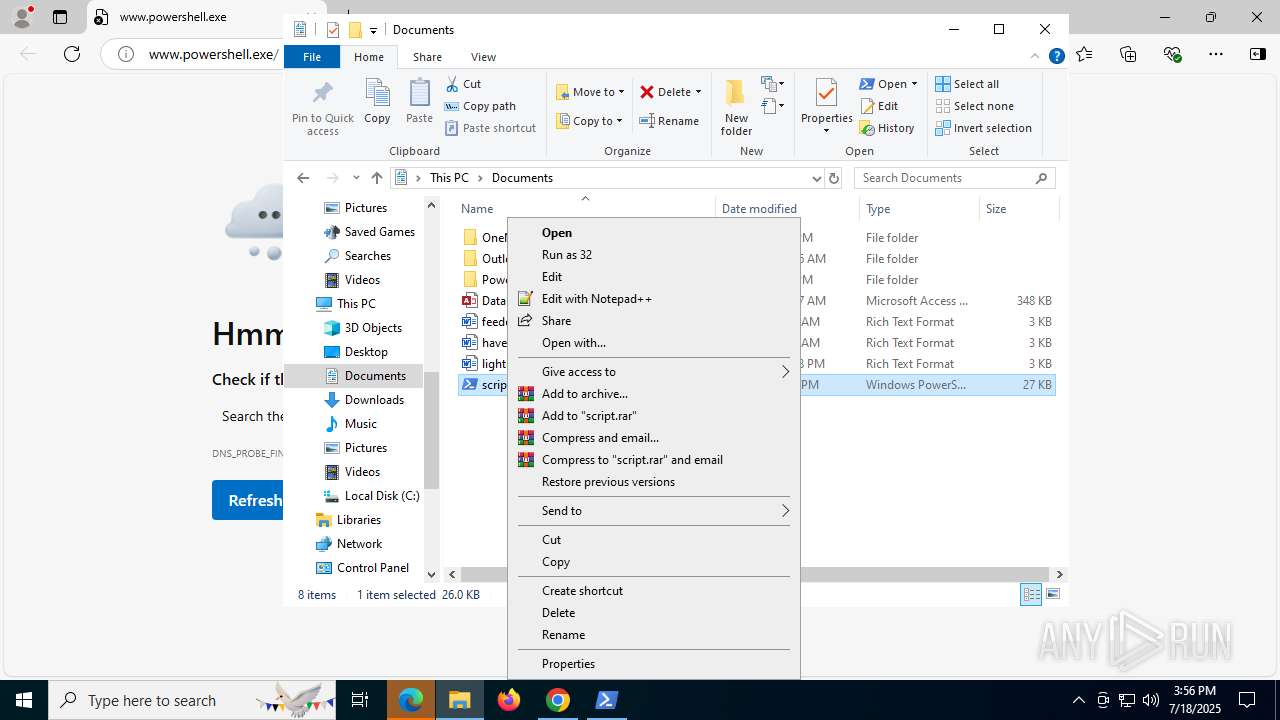
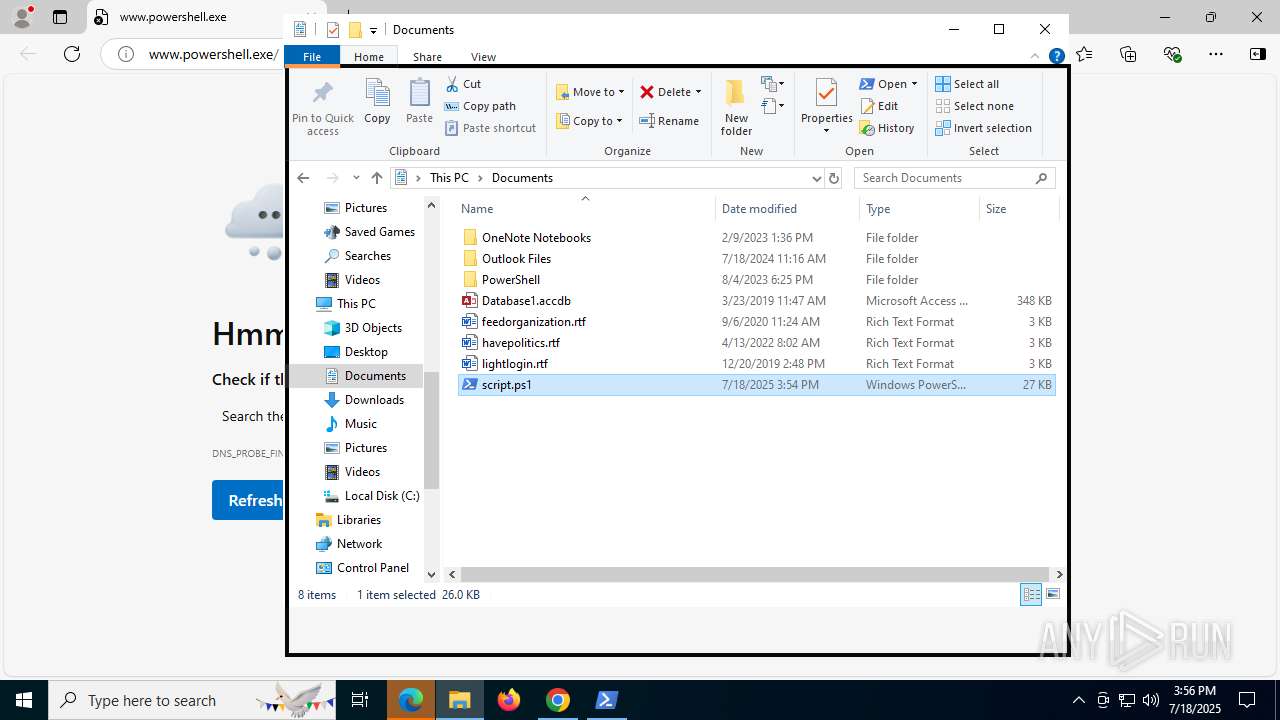
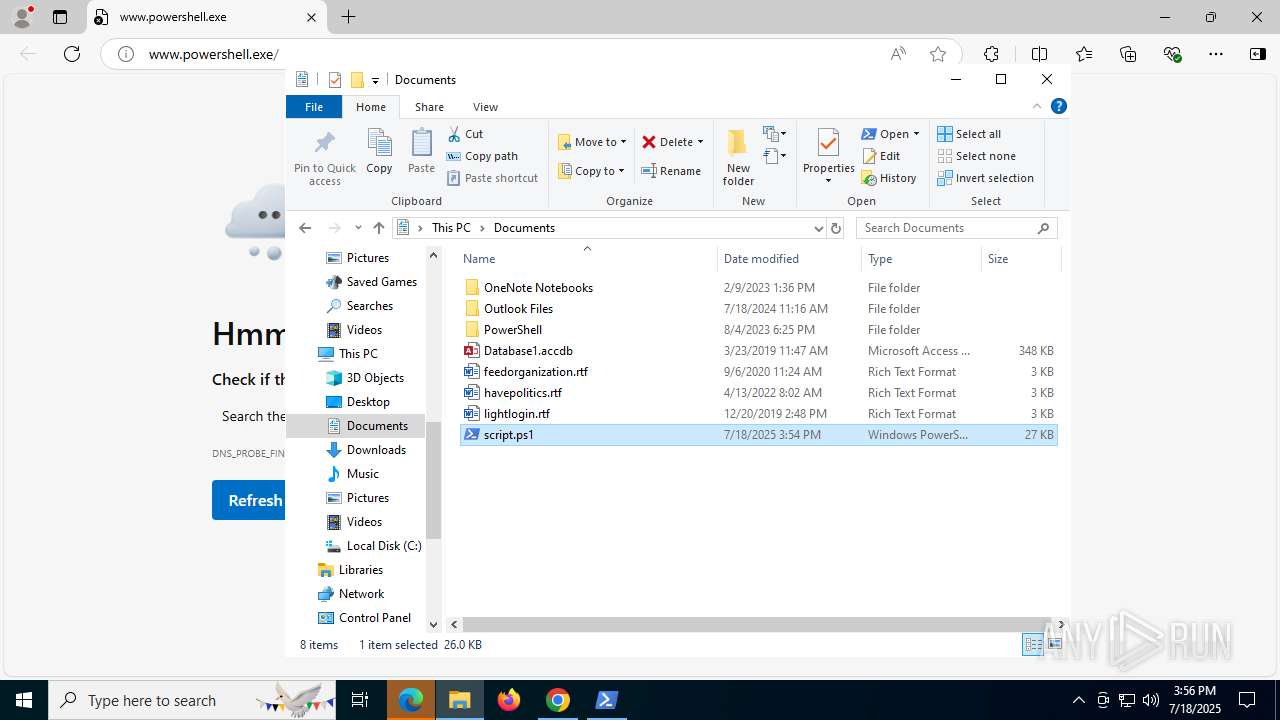
Manual execution by a user
- cmd.exe (PID: 1964)
- cmd.exe (PID: 8004)
- notepad.exe (PID: 7356)
- msedge.exe (PID: 7296)
- powershell.exe (PID: 2076)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7356)
Checks proxy server information
- slui.exe (PID: 7052)
Reads the computer name
- identity_helper.exe (PID: 7900)
- DismHost.exe (PID: 8368)
- DismHost.exe (PID: 9188)
- DismHost.exe (PID: 7428)
Reads Environment values
- identity_helper.exe (PID: 7900)
- DismHost.exe (PID: 9188)
- DismHost.exe (PID: 8368)
- DismHost.exe (PID: 7428)
Reads the software policy settings
- slui.exe (PID: 7052)
Checks supported languages
- identity_helper.exe (PID: 7900)
- DismHost.exe (PID: 9188)
- DismHost.exe (PID: 8368)
- DismHost.exe (PID: 7428)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 2076)
- powershell.exe (PID: 8976)
Checks current location (POWERSHELL)
- powershell.exe (PID: 2076)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 2076)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2076)
- powershell.exe (PID: 8976)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8976)
- powershell.exe (PID: 1980)
The sample compiled with english language support
- powershell.exe (PID: 8976)
- powershell.exe (PID: 6140)
The executable file from the user directory is run by the Powershell process
- DismHost.exe (PID: 7428)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
341
Monitored processes
170
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 72 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=3268,i,8638790831298445394,5882354134279148968,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3148 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 304 | "C:\WINDOWS\system32\reg.exe" add HKLM\SOFTWARE\Policies\Microsoft\Windows\WindowsAI /v DisableClickToDo /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | "C:\WINDOWS\system32\sc.exe" config TrustedInstaller binpath= "C:\WINDOWS\servicing\TrustedInstaller.exe" | C:\Windows\System32\sc.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --always-read-main-dll --field-trial-handle=5532,i,10628142172874302084,259619577873161219,262144 --variations-seed-version --mojo-platform-channel-handle=7308 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 700 | "C:\WINDOWS\system32\reg.exe" add HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Notifications\Settings /v AutoOpenCopilotLargeScreens /t REG_DWORD /d 0 /f | C:\Windows\System32\reg.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 888 | "C:\WINDOWS\system32\reg.exe" add HKCU\SOFTWARE\Policies\Microsoft\Windows\WindowsCopilot /v TurnOffWindowsCopilot /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 892 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=904,i,10628142172874302084,259619577873161219,262144 --variations-seed-version --mojo-platform-channel-handle=7860 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1040 | "C:\WINDOWS\system32\reg.exe" add HKCU\SOFTWARE\Microsoft\Windows\Shell\Copilot\BingChat /v IsUserEligible /t REG_DWORD /d 0 /f | C:\Windows\System32\reg.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | "C:\WINDOWS\system32\reg.exe" add HKLM\SOFTWARE\Policies\Microsoft\Edge /v CopilotPageContext /t REG_DWORD /d 0 /f | C:\Windows\System32\reg.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=3932,i,8638790831298445394,5882354134279148968,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
58 646
Read events
58 388
Write events
221
Delete events
37
Modification events
| (PID) Process: | (6460) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6460) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6460) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6460) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6460) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7356) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (7356) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000003000000110000000E000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (7356) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000003000000050000000200000001000000FFFFFFFF | |||
| (PID) Process: | (7356) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
| (PID) Process: | (7356) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 121 | |||
Executable files
150
Suspicious files
795
Text files
224
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF18d3b6.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF18d3b6.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF18d3b6.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF18d3c6.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old~RF18d3c6.TMP | — | |
MD5:— | SHA256:— | |||
| 6460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SignalDB\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
63
TCP/UDP connections
176
DNS requests
198
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5372 | chrome.exe | GET | 200 | 142.250.185.142:80 | http://clients2.google.com/time/1/current?cup2key=8:pOlKubj6QpnIfLdbgGgqXWC6p6eXgbYLtYhzt0LPbK4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3872 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8080 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8080 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4520 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1636 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5328 | SearchApp.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
5328 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5372 | chrome.exe | 185.199.111.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
5372 | chrome.exe | 142.250.185.142:80 | clients2.google.com | GOOGLE | US | whitelisted |
5372 | chrome.exe | 142.250.186.138:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
accounts.google.com |
| whitelisted |
login.live.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5372 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
5372 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7320 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7320 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7320 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7320 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
powershell.exe | PID=8976 TID=9104 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=8976 TID=9104 DismApi.dll: <----- Starting DismApi.dll session -----> - DismInitializeInternal
|
powershell.exe | PID=8976 TID=9104 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=8976 TID=9104 DismApi.dll: Host machine information: OS Version=10.0.19045, Running architecture=amd64, Number of processors=4 - DismInitializeInternal
|
powershell.exe | PID=8976 TID=9104 DismApi.dll: API Version 10.0.19041.3758 - DismInitializeInternal
|
powershell.exe | PID=8976 TID=9104 DismApi.dll: Parent process command line: powershell.exe -encodedcommand JgBDADoAXABVAHMAZQByAHMAXABhAGQAbQBpAG4AXABBAHAAcABEAGEAdABhAFwATABvAGMAYQBsAFwAVABlAG0AcABcAGEAaQBQAGEAYwBrAGEAZwBlAFIAZQBtAG8AdgBhAGwALgBwAHMAMQA= - DismInitializeInternal
|
powershell.exe | PID=8976 TID=9104 Enter DismInitializeInternal - DismInitializeInternal
|
powershell.exe | PID=8976 TID=9104 Input parameters: LogLevel: 2, LogFilePath: C:\WINDOWS\Logs\DISM\dism.log, ScratchDirectory: (null) - DismInitializeInternal
|
powershell.exe | PID=8976 TID=9104 Initialized GlobalConfig - DismInitializeInternal
|
powershell.exe | PID=8976 TID=9104 Initialized SessionTable - DismInitializeInternal
|