| File name: | RobloxPlayerLauncher.exe |
| Full analysis: | https://app.any.run/tasks/afbb911c-4458-4adb-bb01-9c5bf1c40b66 |
| Verdict: | Malicious activity |
| Analysis date: | June 22, 2024, 04:50:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D0C604B76026481B5A58F7A23588EBAD |
| SHA1: | 72F025CDD20B9E4B3111CBDDE1F8184BBFB953E3 |
| SHA256: | C5AE8972803D2B25A92E2DC512C70F89C49CF6708D7A5F6ADEDD152A03344F50 |
| SSDEEP: | 12288:cGXacSiPZ3/rMXuaqi00/C+2ZrzcKlOcduc4lPNLmatnSv98orKR:LVPVYXuaqi0CparQ7LmatnBo+R |
MALICIOUS
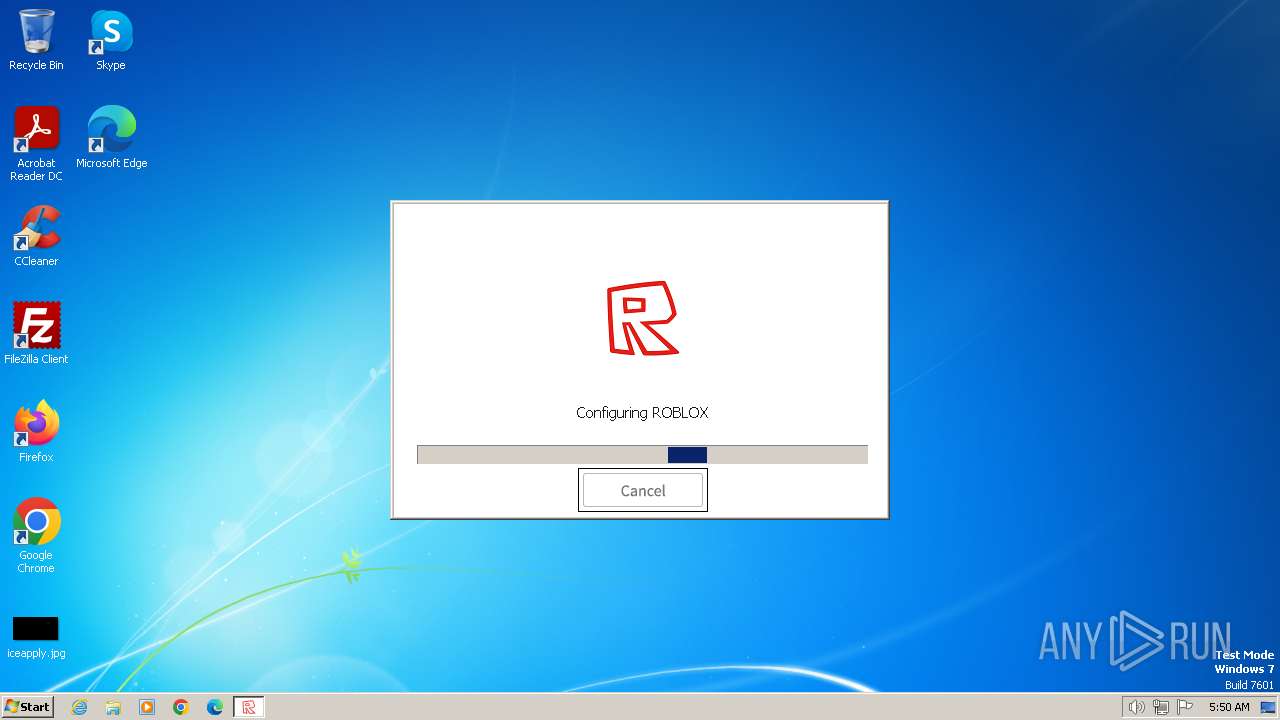
Drops the executable file immediately after the start
- RobloxPlayerLauncher.exe (PID: 3392)
Actions looks like stealing of personal data
- RobloxPlayerLauncher.exe (PID: 3392)
SUSPICIOUS
Reads security settings of Internet Explorer
- RobloxPlayerLauncher.exe (PID: 3392)
Reads the Internet Settings
- RobloxPlayerLauncher.exe (PID: 3392)
Executable content was dropped or overwritten
- RobloxPlayerLauncher.exe (PID: 3392)
Potential Corporate Privacy Violation
- RobloxPlayerLauncher.exe (PID: 3392)
INFO
Create files in a temporary directory
- RobloxPlayerLauncher.exe (PID: 3392)
Checks supported languages
- RobloxPlayerLauncher.exe (PID: 3392)
Reads the computer name
- RobloxPlayerLauncher.exe (PID: 3392)
Checks proxy server information
- RobloxPlayerLauncher.exe (PID: 3392)
Reads the machine GUID from the registry
- RobloxPlayerLauncher.exe (PID: 3392)
Process checks computer location settings
- RobloxPlayerLauncher.exe (PID: 3392)
Creates files or folders in the user directory
- RobloxPlayerLauncher.exe (PID: 3392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:09 05:33:37+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 444416 |
| InitializedDataSize: | 668160 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4b19d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.6.3.32426 |
| ProductVersionNumber: | 1.6.3.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | ROBLOX Corporation |
| FileDescription: | Roblox |
| FileVersion: | 1, 6, 3, 97962 |
| LegalCopyright: | (C) 2012 ROBLOX Corporation. All rights reserved. |
| OriginalFileName: | Roblox.exe |
| ProductName: | Roblox Bootstrapper |
| ProductVersion: | 1, 6, 3, 0 |
Total processes
39
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3392 | "C:\Users\admin\AppData\Local\Temp\RobloxPlayerLauncher.exe" | C:\Users\admin\AppData\Local\Temp\RobloxPlayerLauncher.exe | explorer.exe | ||||||||||||
User: admin Company: ROBLOX Corporation Integrity Level: MEDIUM Description: Roblox Version: 1, 6, 3, 97962 Modules
| |||||||||||||||
Total events
728
Read events
694
Write events
26
Delete events
8
Modification events
| (PID) Process: | (3392) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\ROBLOX Corporation\Roblox |
| Operation: | write | Name: | CPath |
Value: C:\Users\admin\AppData\LocalLow\rbxcsettings.rbx | |||
| (PID) Process: | (3392) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\ROBLOX Corporation\Roblox |
| Operation: | delete value | Name: | curStudioVer |
Value: | |||
| (PID) Process: | (3392) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\ROBLOX Corporation\Roblox |
| Operation: | delete value | Name: | curStudioUrl |
Value: | |||
| (PID) Process: | (3392) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3392) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3392) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3392) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3392) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (3392) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (3392) RobloxPlayerLauncher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
Executable files
1
Suspicious files
189
Text files
545
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Temp\RBX-48AA34DC.tmp | — | |
MD5:— | SHA256:— | |||
| 3392 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Roblox\Downloads\e78123c5772f6b7f7291e68bdabc02d9 | — | |
MD5:— | SHA256:— | |||
| 3392 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\LocalLow\rbxcsettings.rbx | text | |
MD5:818B469A34FD6BF9FF2C4FA463410A55 | SHA256:2E81AD6E973D1B9C66E30393EFFCBE0302E15B54F183E149C1047799E88E0B1E | |||
| 3392 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Roblox\Versions\version-stratusv1\AppSettings.xml | xml | |
MD5:3EE4BE8DCED628F466B45674C11EF478 | SHA256:29F5EF16526E917849F1A133D7FE97A10C2AAB59D1CF40C87FB0BC8180064158 | |||
| 3392 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Roblox\Versions\version-stratusv1\RobloxPlayerLauncher.exe | executable | |
MD5:D0C604B76026481B5A58F7A23588EBAD | SHA256:C5AE8972803D2B25A92E2DC512C70F89C49CF6708D7A5F6ADEDD152A03344F50 | |||
| 3392 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\WindowsBootstrapperSettings[1].json | binary | |
MD5:99914B932BD37A50B983C5E7C90AE93B | SHA256:44136FA355B3678A1146AD16F7E8649E94FB4FC21FE77E8310C060F61CAAFF8A | |||
| 3392 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Roblox\Versions\version-stratusv1\content\fonts\ArialBold.font | binary | |
MD5:A3E1D5586C5E6577EF4912C456953D7D | SHA256:DD57FEEC194BF8F29AA5CFF8AD4AC139AD015AEC45C8CE4C3D6B8856B43034E1 | |||
| 3392 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Roblox\Versions\version-stratusv1\content\fonts\arial.ttf | binary | |
MD5:096B6677FC4A0A2AB430CD3D28B6FD52 | SHA256:97DCF78FE226789FD413EABCE2BDA89A2F8A9182DA216EA43B1FE0BACBBE9F0A | |||
| 3392 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Roblox\Versions\version-stratusv1\content\fonts\Arial.font | binary | |
MD5:306659A54D4F2FBC78CBF0A1F271C739 | SHA256:98316CB0F6D52917DF5A1DE4D26EDB9BEEC8479CFAE166F9CFD76C40CC928762 | |||
| 3392 | RobloxPlayerLauncher.exe | C:\Users\admin\AppData\Local\Roblox\Versions\version-stratusv1\content\fonts\arialbd.ttf | binary | |
MD5:E66C59A1533739573CF63A21952771F5 | SHA256:8CA5DCAF6589267DC6F842E614AD0FE2E42374B23EFE87D89B991BD860F671E2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
20
DNS requests
8
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3392 | RobloxPlayerLauncher.exe | GET | 200 | 188.114.97.3:80 | http://setup.stratus.pw/version?guid30643 | unknown | — | — | unknown |
3392 | RobloxPlayerLauncher.exe | GET | 200 | 188.114.97.3:80 | http://clientsettings.api.stratus.pw/Setting/QuietGet/WindowsBootstrapperSettings/?apiKey=76E5A40C-3AE1-4028-9F10-7C62520BD94F | unknown | — | — | unknown |
3392 | RobloxPlayerLauncher.exe | GET | 404 | 188.114.97.3:80 | http://setup.stratus.pw/versionQTStudio?guid30643 | unknown | — | — | unknown |
3392 | RobloxPlayerLauncher.exe | GET | 404 | 188.114.97.3:80 | http://setup.stratus.pw/versionQTStudio?guid30643 | unknown | — | — | unknown |
3392 | RobloxPlayerLauncher.exe | GET | — | 188.114.97.3:80 | http://www.stratus.pw/install/GetInstallerCdns.ashx | unknown | — | — | unknown |
3392 | RobloxPlayerLauncher.exe | GET | — | 188.114.97.3:80 | http://www.stratus.pw/install/GetInstallerCdns.ashx | unknown | — | — | unknown |
3392 | RobloxPlayerLauncher.exe | GET | — | 13.32.27.22:80 | http://setup.rbxcdn.com/version-stratusv1-RobloxProxy.zip | unknown | — | — | unknown |
3392 | RobloxPlayerLauncher.exe | GET | — | 13.32.27.22:80 | http://setup.rbxcdn.com/version-stratusv1-RobloxProxy.zip | unknown | — | — | unknown |
3392 | RobloxPlayerLauncher.exe | GET | 200 | 188.114.97.3:80 | http://setup.stratus.pw/version-stratusv1-RobloxProxy.zip | unknown | — | — | unknown |
1372 | svchost.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1372 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3392 | RobloxPlayerLauncher.exe | 188.114.97.3:80 | clientsettings.api.stratus.pw | CLOUDFLARENET | NL | unknown |
3392 | RobloxPlayerLauncher.exe | 13.32.27.22:80 | setup.rbxcdn.com | AMAZON-02 | US | unknown |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1372 | svchost.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
1372 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
1060 | svchost.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientsettings.api.stratus.pw |
| unknown |
setup.stratus.pw |
| unknown |
www.stratus.pw |
| unknown |
setup.rbxcdn.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
3392 | RobloxPlayerLauncher.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
3392 | RobloxPlayerLauncher.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
3392 | RobloxPlayerLauncher.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
1060 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
3392 | RobloxPlayerLauncher.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
3392 | RobloxPlayerLauncher.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
3392 | RobloxPlayerLauncher.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
3392 | RobloxPlayerLauncher.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
1 ETPRO signatures available at the full report