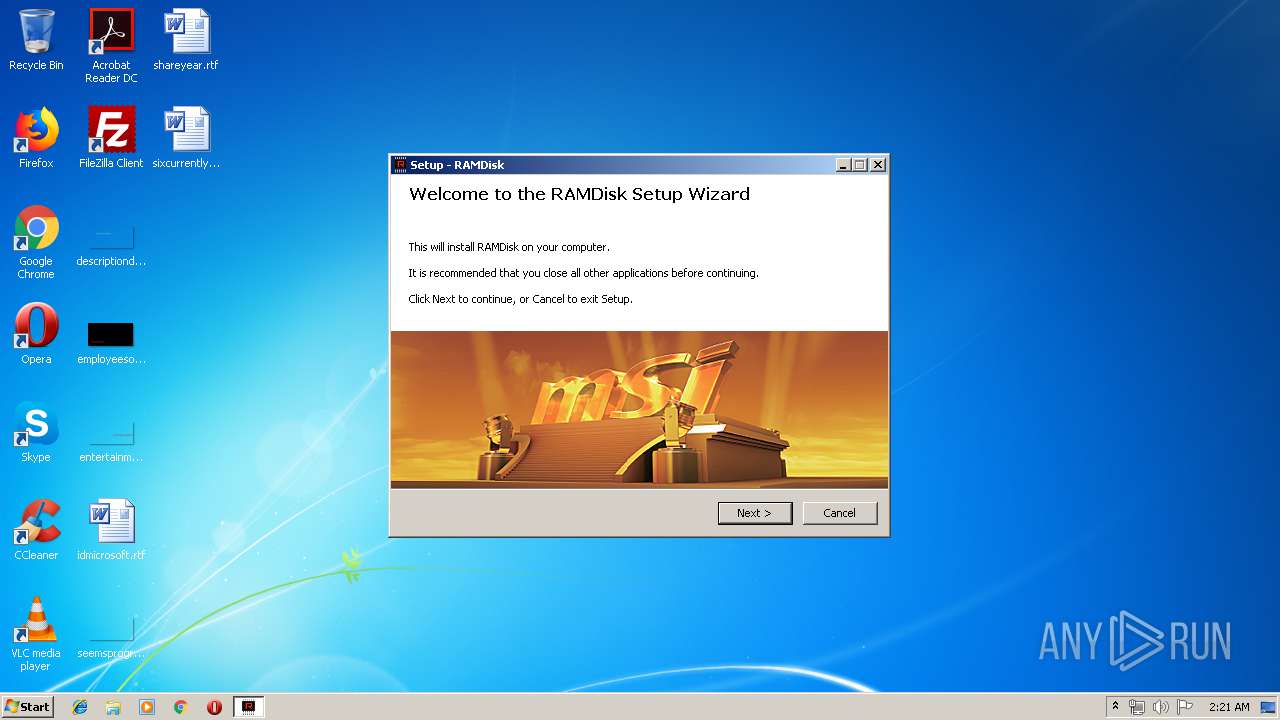
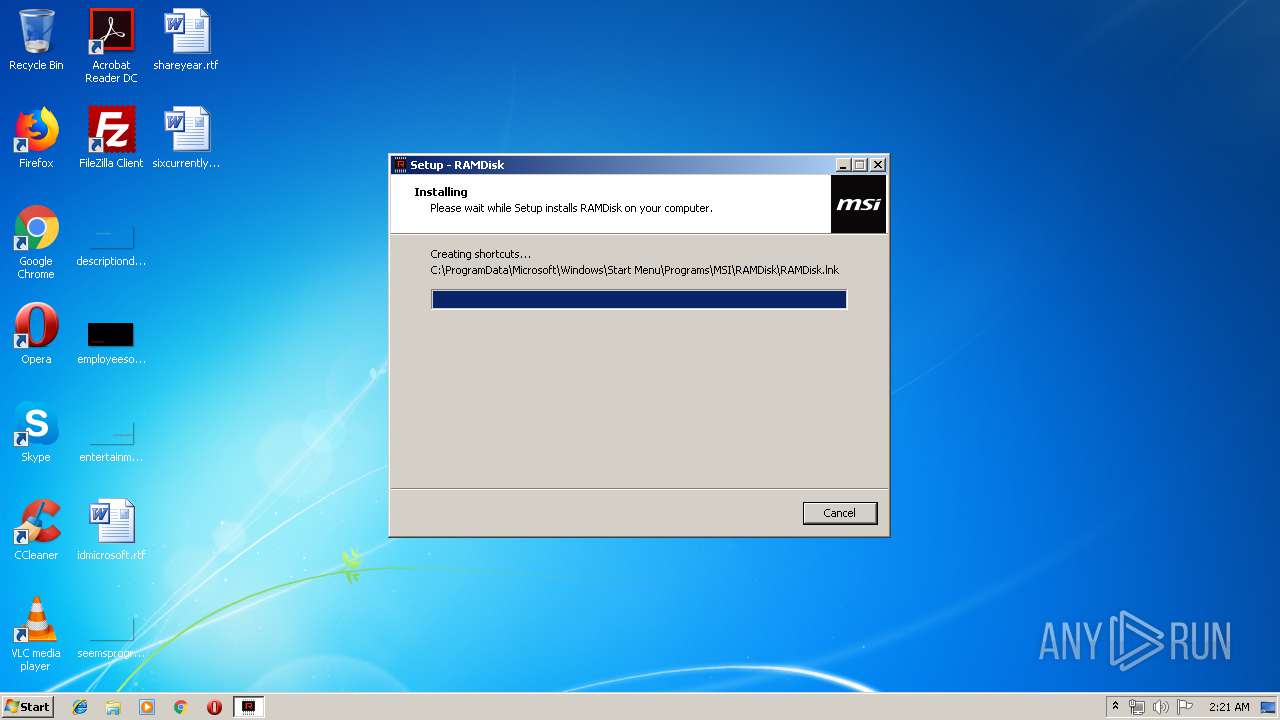
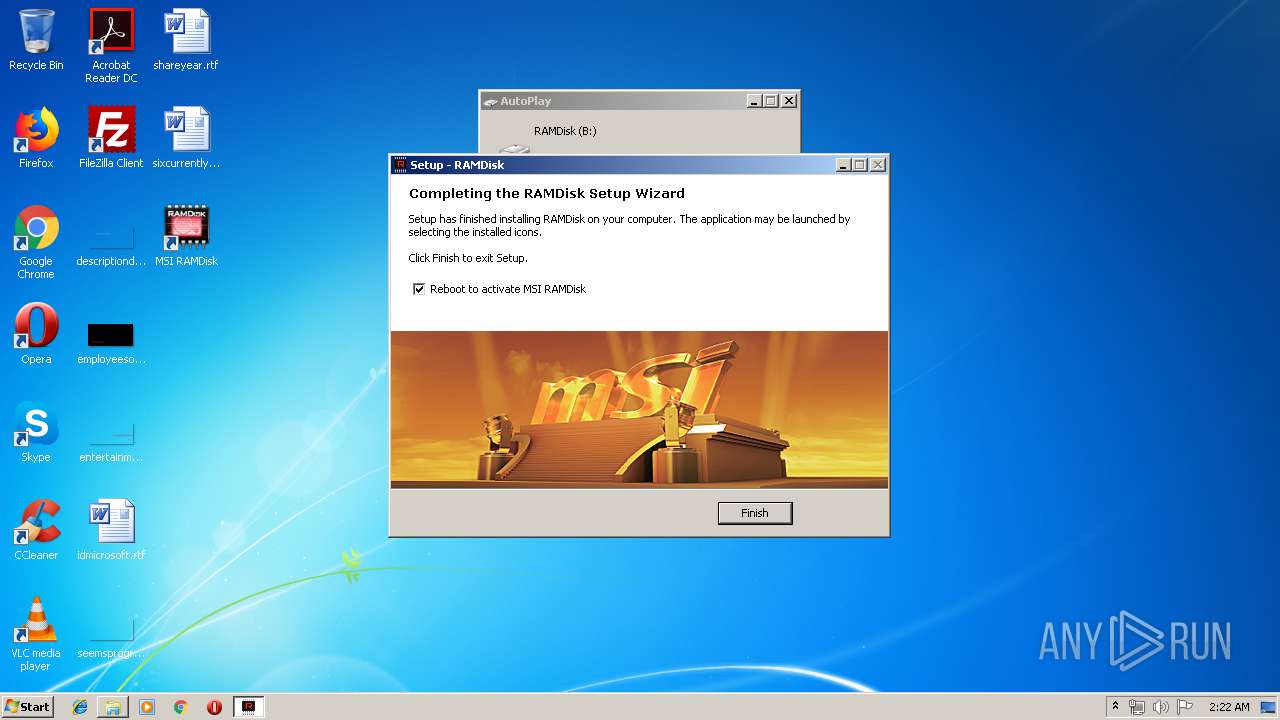
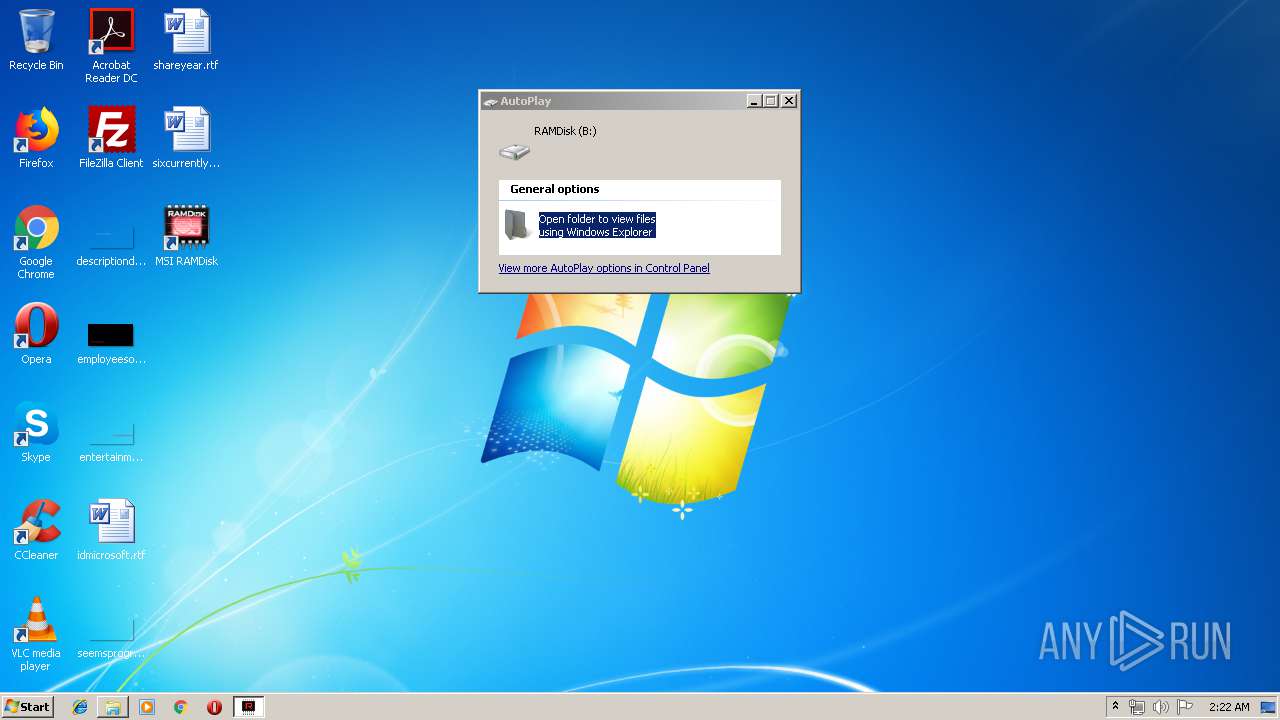
| File name: | RAMDisk_1.0.0.27.exe |
| Full analysis: | https://app.any.run/tasks/67f4c418-fcc1-4831-9d2a-4fb1d38cd220 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 01:21:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FC2B16975648A08C895806452C285DE7 |
| SHA1: | 00523081B022E29256CAD62E13865C0643C52436 |
| SHA256: | C5A8BCB6C0DAEA9BEAC3BCF47203A1CEAF94A135D222238DCC15E04DE4E552C6 |
| SSDEEP: | 98304:JmELwwB6lsyX9Qs1ZUscyf6I/Aulk+F/C07n/T0BW:JmELJQH9xZU7yf6I/VZC0LL0BW |
MALICIOUS
Application was dropped or rewritten from another process
- RAMDisk.exe (PID: 2976)
- certmgr.exe (PID: 676)
- RAMDisk.exe (PID: 2176)
- certmgr.exe (PID: 2668)
- certmgr.exe (PID: 2848)
- MSI_RAMDrive_Installer.exe (PID: 296)
- ServiceControl.exe (PID: 4068)
- MSI_RAMDisk_Service.exe (PID: 1360)
- ISWIN2K.exe (PID: 3480)
- PROCTYPE.exe (PID: 640)
- x86.exe (PID: 3800)
- devcon86.exe (PID: 3436)
- devcon86.exe (PID: 3012)
- ISWIN2K.exe (PID: 3556)
- kill.exe (PID: 3260)
Changes settings of System certificates
- certmgr.exe (PID: 676)
- certmgr.exe (PID: 2848)
- ServiceControl.exe (PID: 4068)
- certmgr.exe (PID: 2668)
- devcon86.exe (PID: 3436)
Loads dropped or rewritten executable
- DrvInst.exe (PID: 2332)
SUSPICIOUS
Executable content was dropped or overwritten
- RAMDisk.exe (PID: 2176)
- RAMDisk.tmp (PID: 2472)
- MSI_RAMDrive_Installer.exe (PID: 296)
- x86.exe (PID: 3800)
- cmd.exe (PID: 3184)
- DrvInst.exe (PID: 2556)
- devcon86.exe (PID: 3436)
- RAMDisk_1.0.0.27.exe (PID: 3000)
- DrvInst.exe (PID: 2332)
Starts CMD.EXE for commands execution
- RAMDisk.tmp (PID: 2472)
- MSI_RAMDrive_Installer.exe (PID: 296)
Adds / modifies Windows certificates
- certmgr.exe (PID: 2668)
- ServiceControl.exe (PID: 4068)
Reads Windows owner or organization settings
- RAMDisk.tmp (PID: 2472)
Reads the Windows organization settings
- RAMDisk.tmp (PID: 2472)
Creates files in the program directory
- ServiceControl.exe (PID: 4068)
- MSI_RAMDrive_Installer.exe (PID: 296)
- x86.exe (PID: 3800)
Creates files in the driver directory
- cmd.exe (PID: 3184)
- DrvInst.exe (PID: 2556)
Creates files in the Windows directory
- cmd.exe (PID: 3184)
- devcon86.exe (PID: 3436)
- DrvInst.exe (PID: 2556)
- DrvInst.exe (PID: 2332)
Searches for installed software
- DrvInst.exe (PID: 2556)
Removes files from Windows directory
- DrvInst.exe (PID: 2556)
- DrvInst.exe (PID: 2332)
INFO
Application was dropped or rewritten from another process
- RAMDisk.tmp (PID: 2472)
Loads dropped or rewritten executable
- RAMDisk.tmp (PID: 2472)
Creates files in the program directory
- RAMDisk.tmp (PID: 2472)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3224)
Creates a software uninstall entry
- RAMDisk.tmp (PID: 2472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:08:14 21:15:49+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 188416 |
| InitializedDataSize: | 196096 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1cab5 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2016 19:15:49 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 14-Aug-2016 19:15:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002DFE8 | 0x0002E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71025 |
.rdata | 0x0002F000 | 0x000099D0 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15287 |
.data | 0x00039000 | 0x0001F8B8 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29547 |
.gfids | 0x00059000 | 0x000000F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.12367 |
.rsrc | 0x0005A000 | 0x00004680 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.63811 |
.reloc | 0x0005F000 | 0x00001F8C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62986 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.88998 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 4.12176 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 4.68705 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.15447 | 494 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
11 | 3.2036 | 1094 | UNKNOWN | English - United States | RT_STRING |
12 | 3.12889 | 358 | UNKNOWN | English - United States | RT_STRING |
Imports
COMCTL32.dll (delay-loaded) |
KERNEL32.dll |
Total processes
64
Monitored processes
24
Malicious processes
8
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
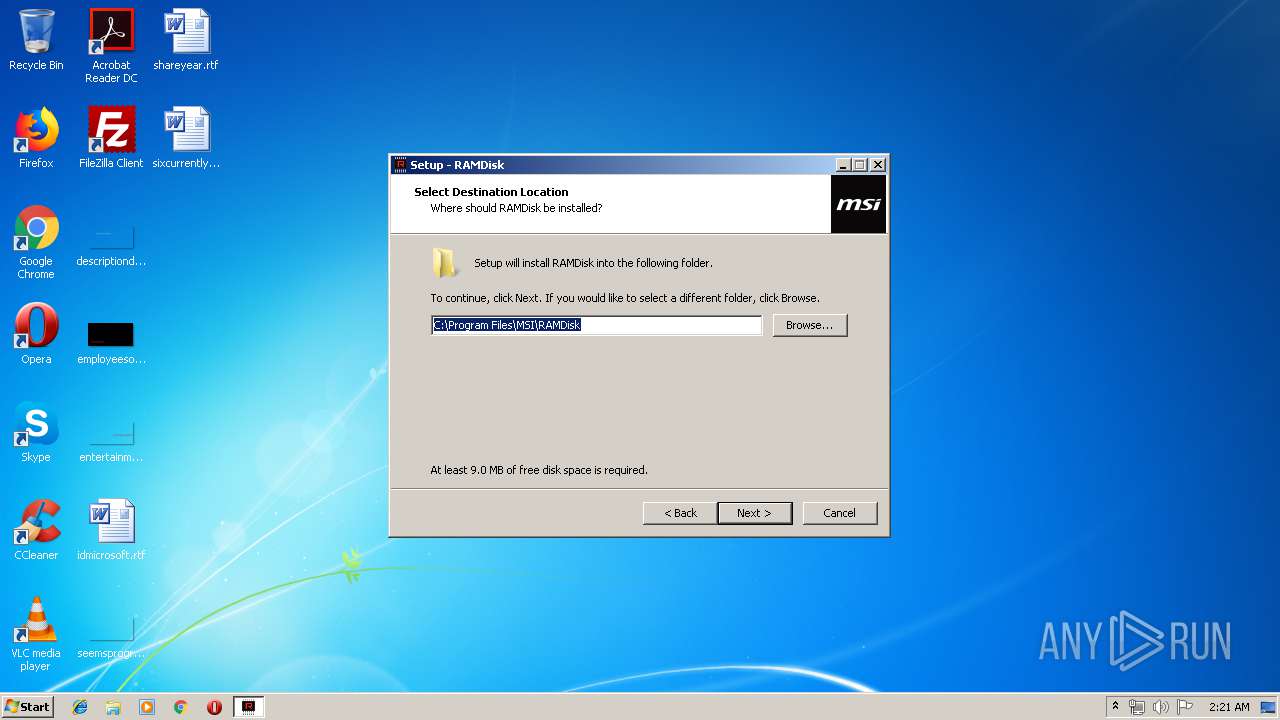
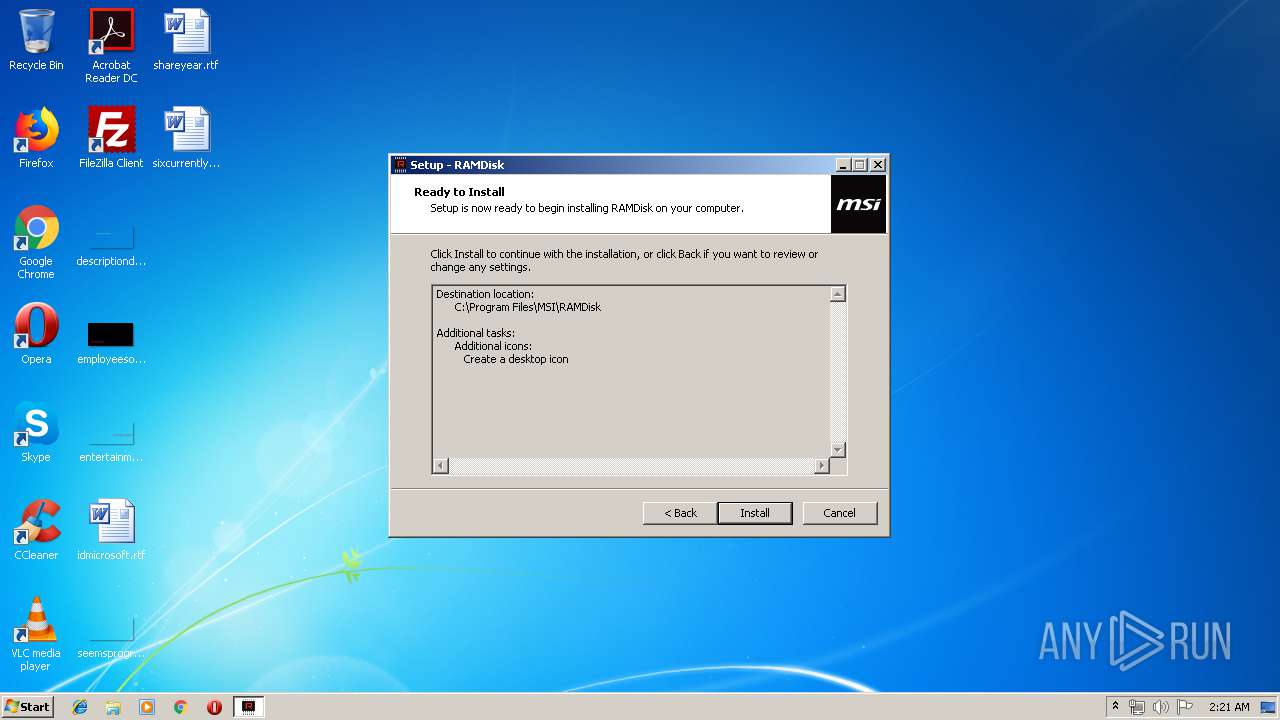
| 296 | "C:\Program Files\MSI\RAMDisk\MSI_RAMDrive_Installer.exe" /quiet /hidden | C:\Program Files\MSI\RAMDisk\MSI_RAMDrive_Installer.exe | RAMDisk.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 540 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\MSI\RAMDisk\Run.bat"" | C:\Windows\system32\cmd.exe | — | RAMDisk.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 640 | PROCTYPE.exe | C:\Program Files\MSI\RAMDisk\PROCTYPE.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 676 | certmgr.exe -add WinramtechCert.cer -c -s -r localMachine TrustedPublisher | C:\Program Files\MSI\RAMDisk\certmgr.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\MSI\RAMDisk\MSI_RAMDisk_Service.exe" | C:\Program Files\MSI\RAMDisk\MSI_RAMDisk_Service.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Micro-Star Int'l Co., Ltd. Integrity Level: SYSTEM Description: MSI RAMDisk Service Exit code: 0 Version: 1.0.0.32 Modules
| |||||||||||||||
| 1500 | "C:\Windows\system32\shutdown.exe" -r -f -t 0 | C:\Windows\system32\shutdown.exe | — | RAMDisk.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\AppData\Local\Temp\RAMDisk.exe" | C:\Users\admin\AppData\Local\Temp\RAMDisk.exe | RAMDisk_1.0.0.27.exe | ||||||||||||
User: admin Company: MSI Integrity Level: HIGH Description: RAMDisk Setup Exit code: 0 Version: 1.0.0.32 Modules
| |||||||||||||||
| 2332 | DrvInst.exe "2" "211" "ROOT\RAMDRIV\0000" "C:\Windows\INF\oem4.inf" "ramdriv.inf:DiskDevice:DiskInstall:5.3.2.15:ramdriv" "68794a143" "000005B8" "000005E4" "000005F8" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | "C:\Users\admin\AppData\Local\Temp\is-U6BJ3.tmp\RAMDisk.tmp" /SL5="$40112,2824986,699392,C:\Users\admin\AppData\Local\Temp\RAMDisk.exe" | C:\Users\admin\AppData\Local\Temp\is-U6BJ3.tmp\RAMDisk.tmp | RAMDisk.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2556 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{3af4b3b4-613b-674b-1921-9674421aa044}\ramdriv.inf" "0" "68794a143" "000005B8" "WinSta0\Default" "000005C8" "208" "c:\program files\msi\ramdisk" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 412
Read events
1 092
Write events
319
Delete events
1
Modification events
| (PID) Process: | (3000) RAMDisk_1.0.0.27.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3000) RAMDisk_1.0.0.27.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2472) RAMDisk.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MSI\RAMDisk |
| Operation: | write | Name: | AppVersion |
Value: 1.0.0.32 | |||
| (PID) Process: | (2472) RAMDisk.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MSI\RAMDisk |
| Operation: | write | Name: | WorkDir |
Value: C:\Program Files\MSI\RAMDisk | |||
| (PID) Process: | (2472) RAMDisk.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F29CF050-7278-4CDB-9EF8-2DC6DAA87453}}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.4.2.ee2 (u) | |||
| (PID) Process: | (2472) RAMDisk.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F29CF050-7278-4CDB-9EF8-2DC6DAA87453}}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\MSI\RAMDisk | |||
| (PID) Process: | (2472) RAMDisk.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F29CF050-7278-4CDB-9EF8-2DC6DAA87453}}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\MSI\RAMDisk\ | |||
| (PID) Process: | (2472) RAMDisk.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F29CF050-7278-4CDB-9EF8-2DC6DAA87453}}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: MSI\RAMDisk | |||
| (PID) Process: | (2472) RAMDisk.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F29CF050-7278-4CDB-9EF8-2DC6DAA87453}}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (2472) RAMDisk.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{F29CF050-7278-4CDB-9EF8-2DC6DAA87453}}_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon | |||
Executable files
40
Suspicious files
22
Text files
396
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2472 | RAMDisk.tmp | C:\Program Files\MSI\RAMDisk\is-VLRQ2.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | RAMDisk.tmp | C:\Program Files\MSI\RAMDisk\is-MSSQN.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | RAMDisk.tmp | C:\Program Files\MSI\RAMDisk\is-06T88.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | RAMDisk.tmp | C:\Program Files\MSI\RAMDisk\is-2DFV7.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | RAMDisk.tmp | C:\Program Files\MSI\RAMDisk\is-7G8I9.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | RAMDisk.tmp | C:\Program Files\MSI\RAMDisk\is-2FIIQ.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | RAMDisk.tmp | C:\Program Files\MSI\RAMDisk\is-LCNRM.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | RAMDisk.tmp | C:\Program Files\MSI\RAMDisk\is-DFQ7E.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | RAMDisk.tmp | C:\Program Files\MSI\RAMDisk\is-0SLUC.tmp | — | |
MD5:— | SHA256:— | |||
| 2472 | RAMDisk.tmp | C:\Program Files\MSI\RAMDisk\is-OKNUB.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4068 | ServiceControl.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4068 | ServiceControl.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |