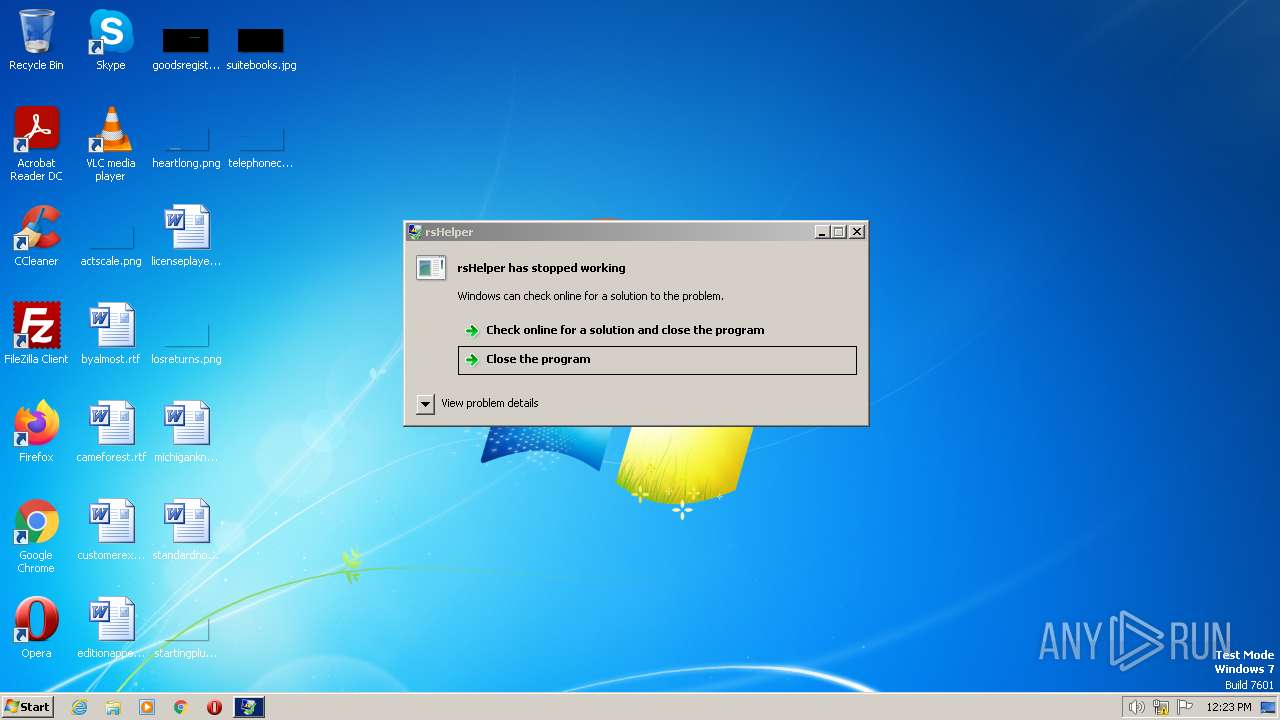
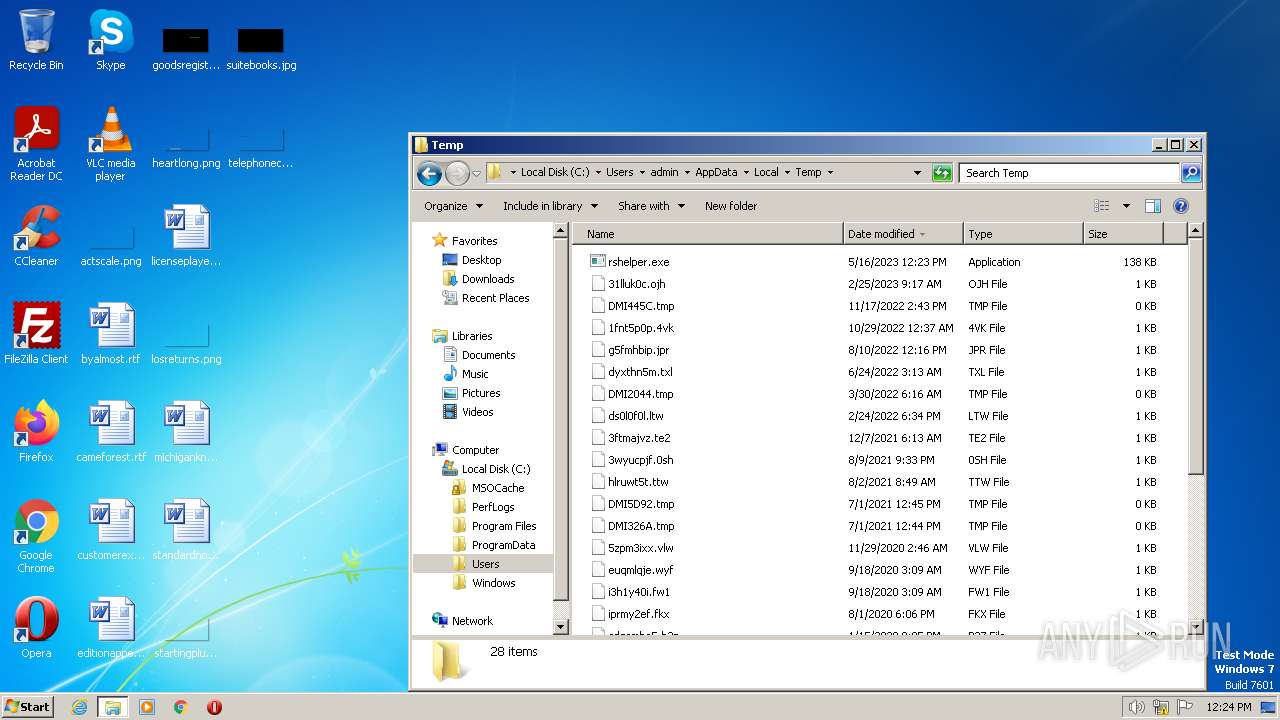
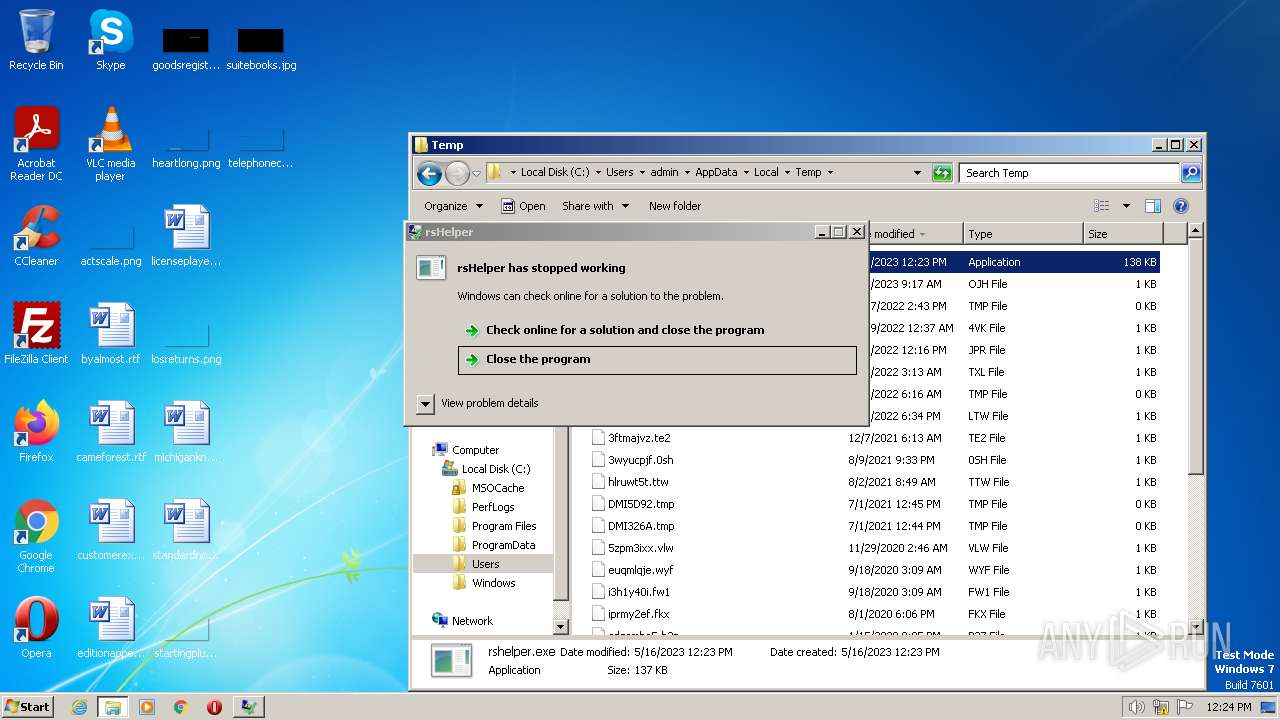
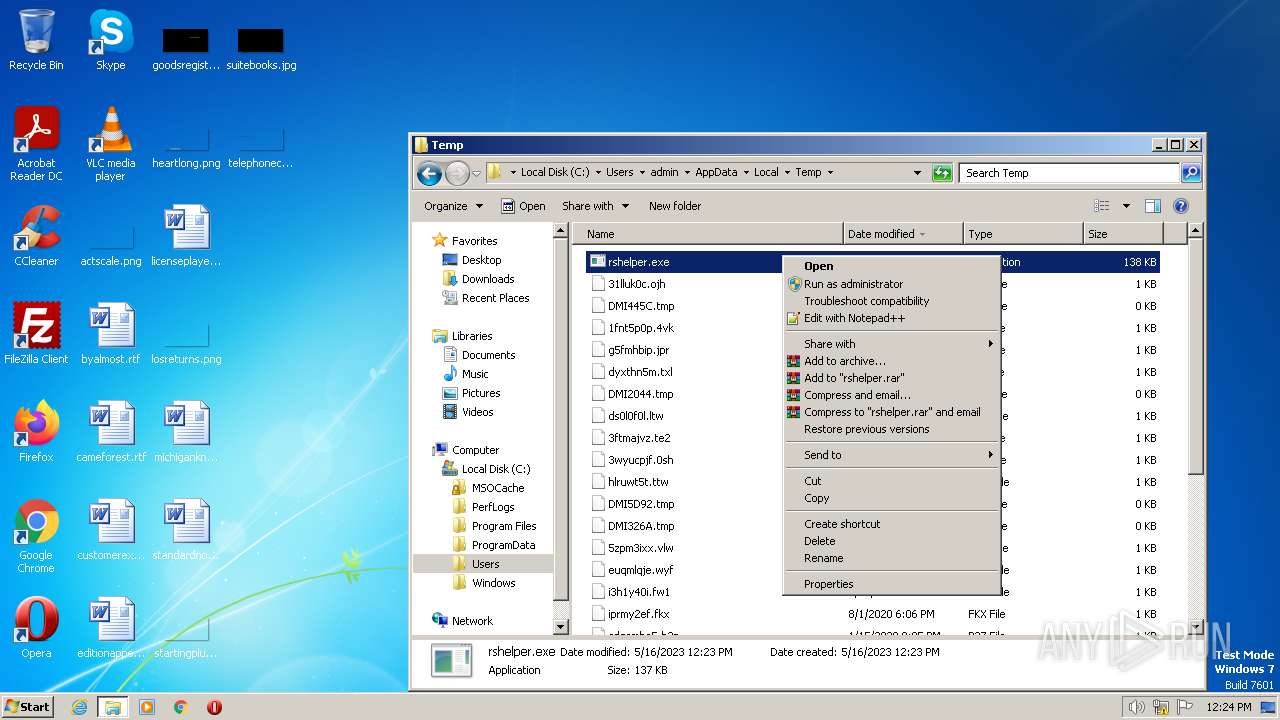
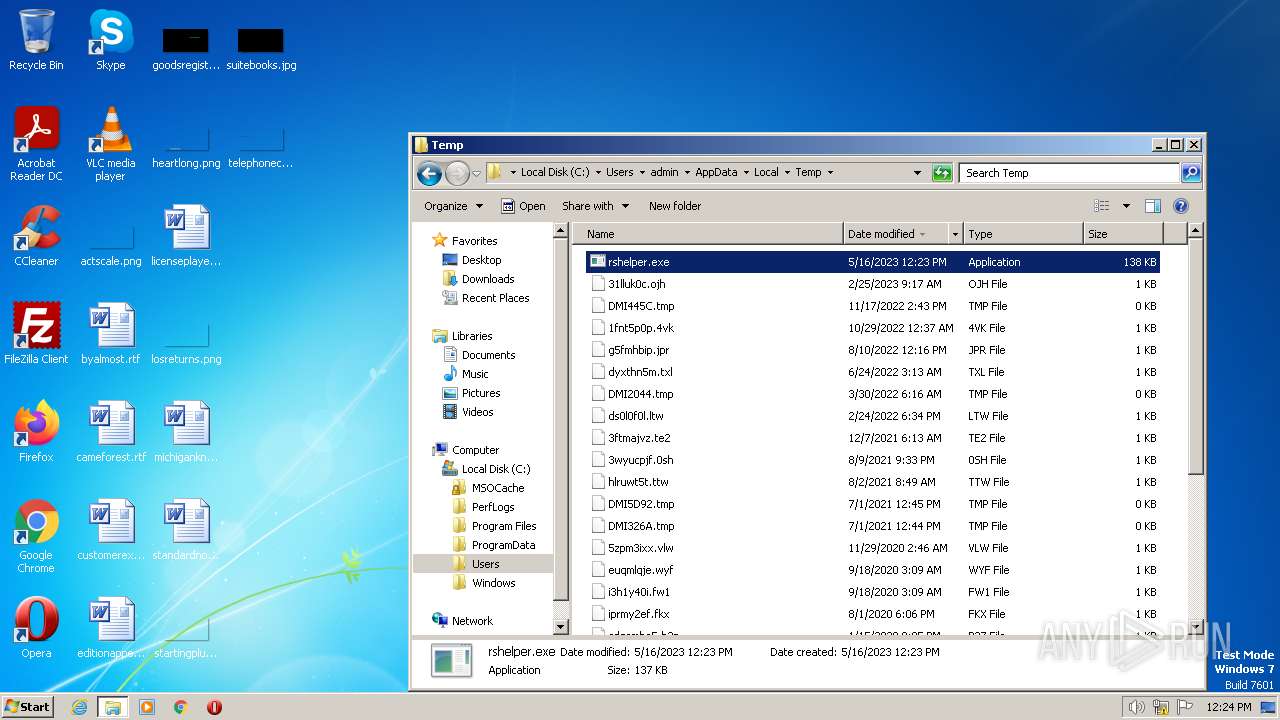
| File name: | rshelper.exe |
| Full analysis: | https://app.any.run/tasks/df48f892-5d25-4363-8c4e-d33de45aad16 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2023, 11:23:22 |
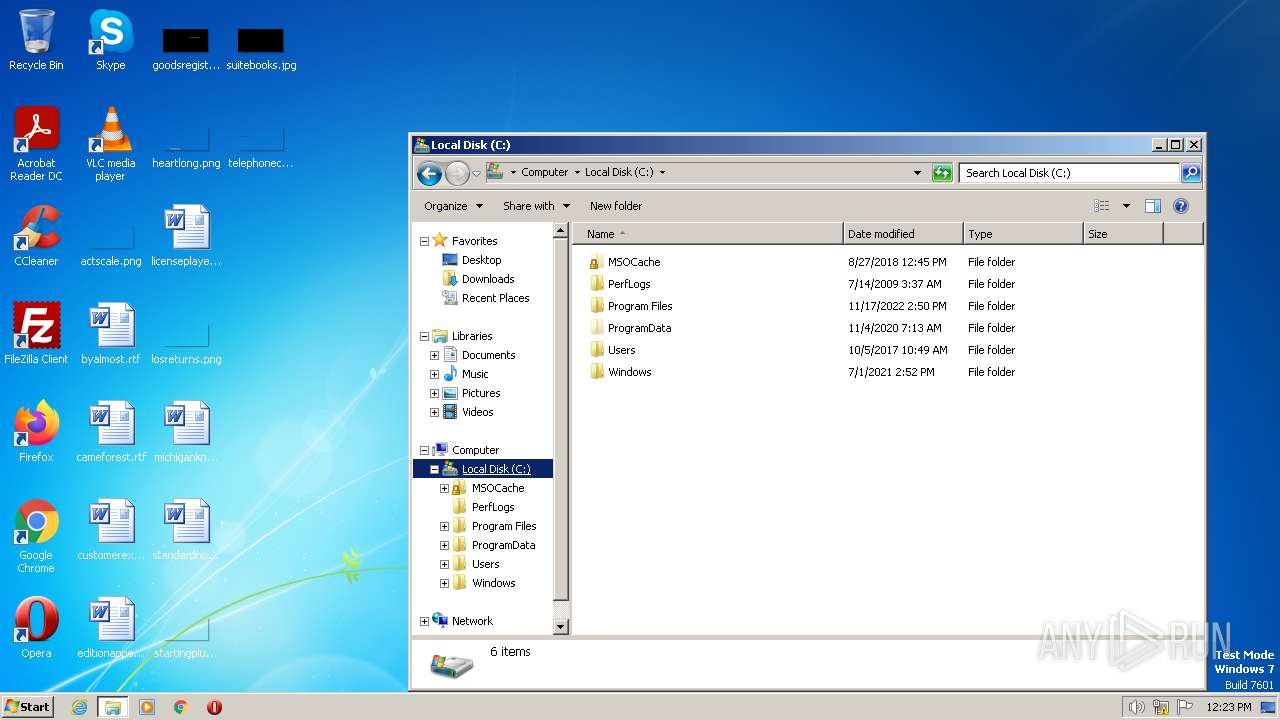
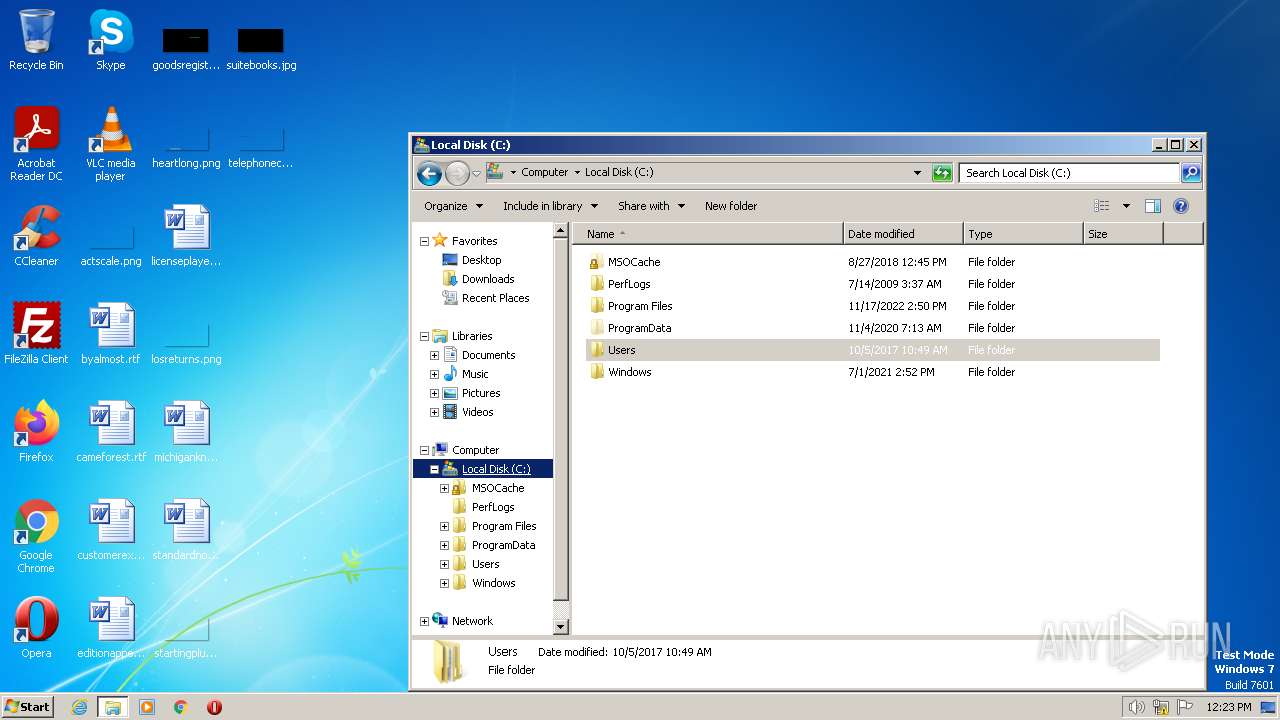
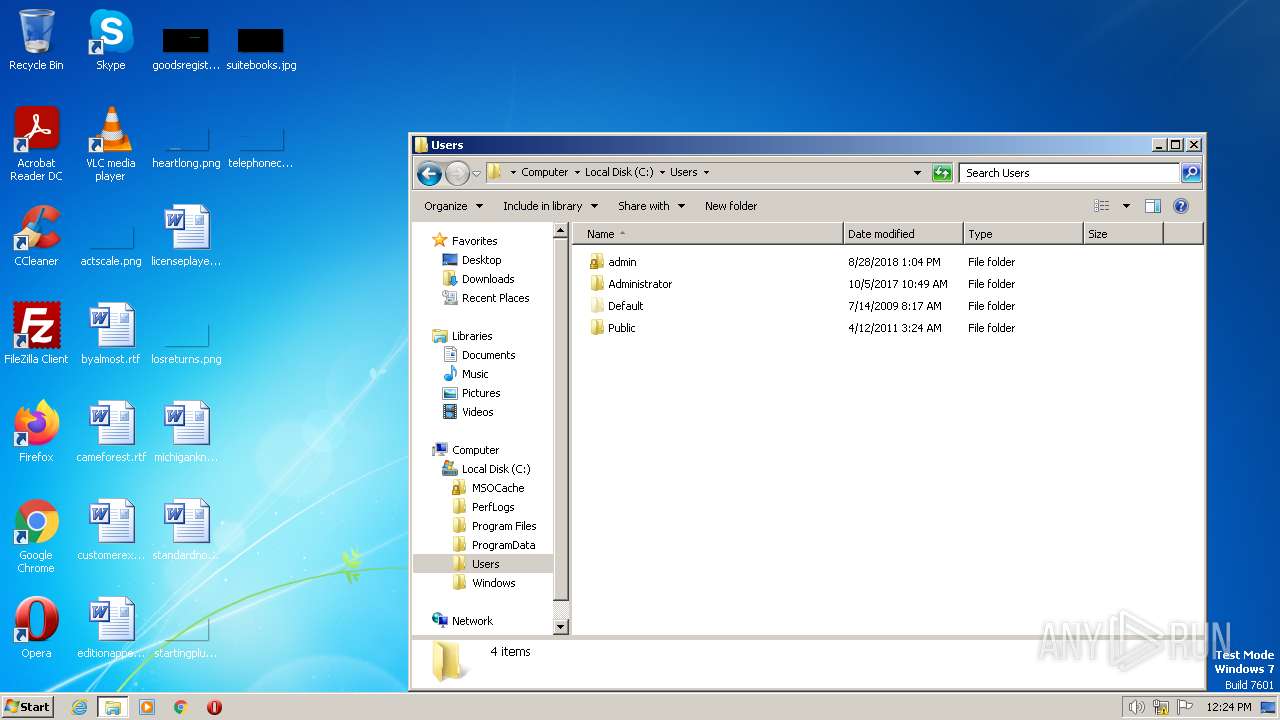
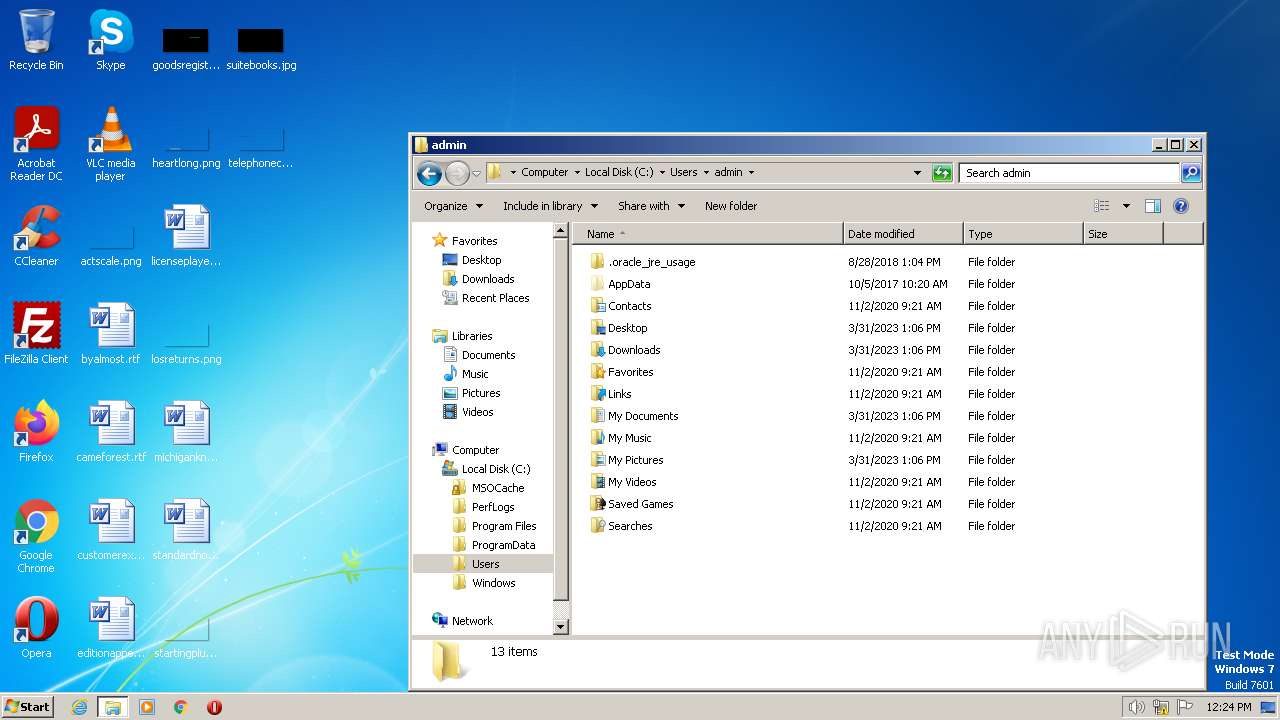
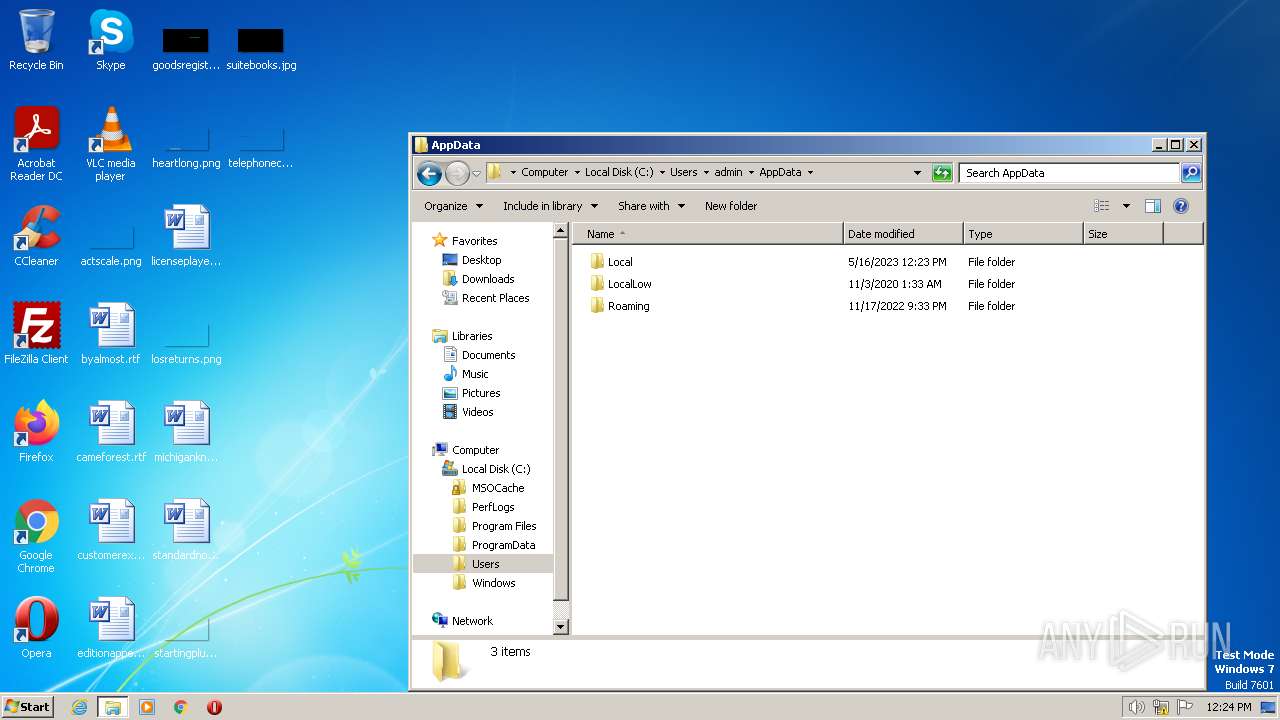
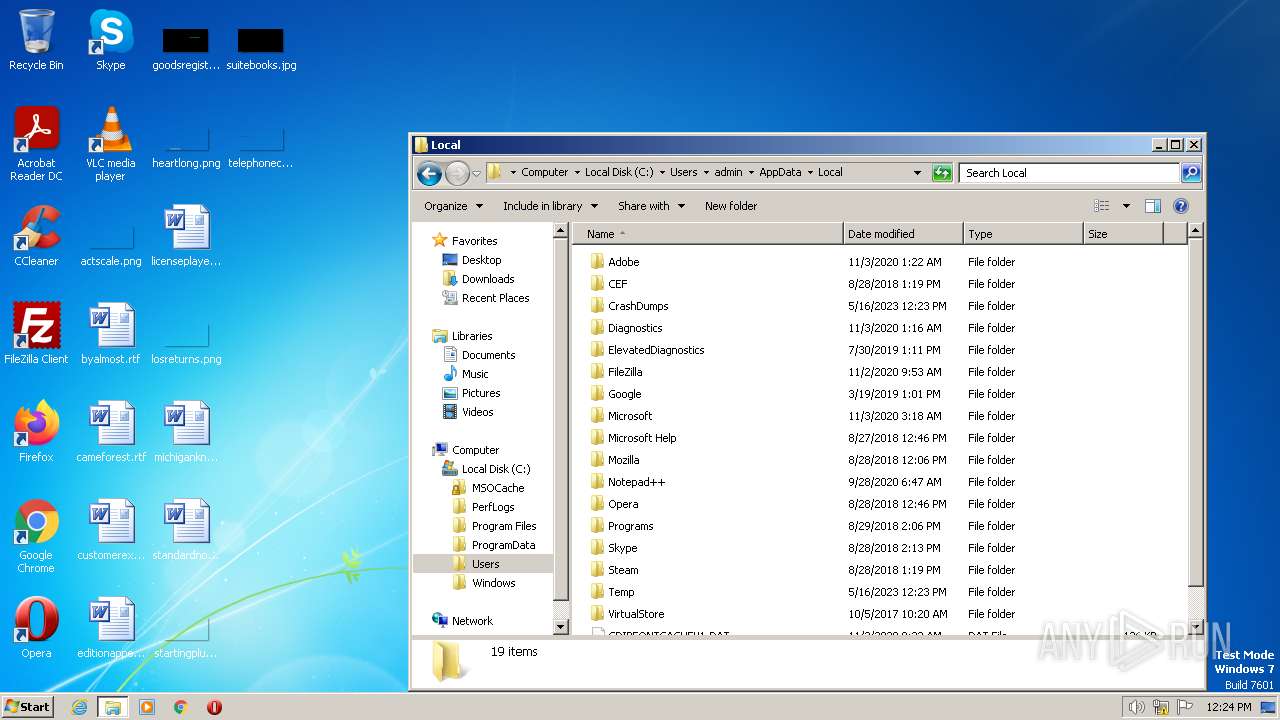
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 3A99CA98EF21BD533DF2B92D83368112 |
| SHA1: | 877923DA74C6151CDE489C34F45D973602C0A605 |
| SHA256: | C59A2ED3919FD9380C4FC339C1F5B727629B391ADBC9211B254BBB740852E588 |
| SSDEEP: | 3072:hXsnkPxkDkeoSCXJpq3ZDcsoUazBXovOtESTdDDOIVN7PxaE:inkCY5SJwsoUEBtBaoR |
MALICIOUS
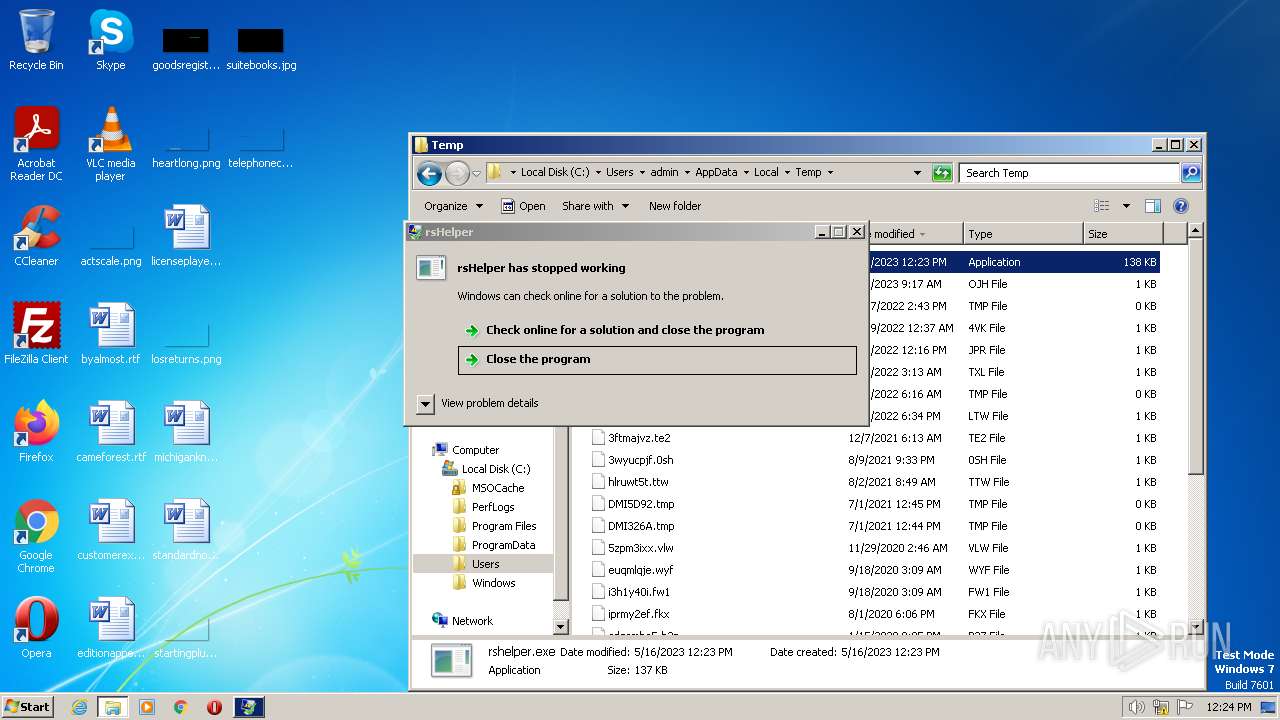
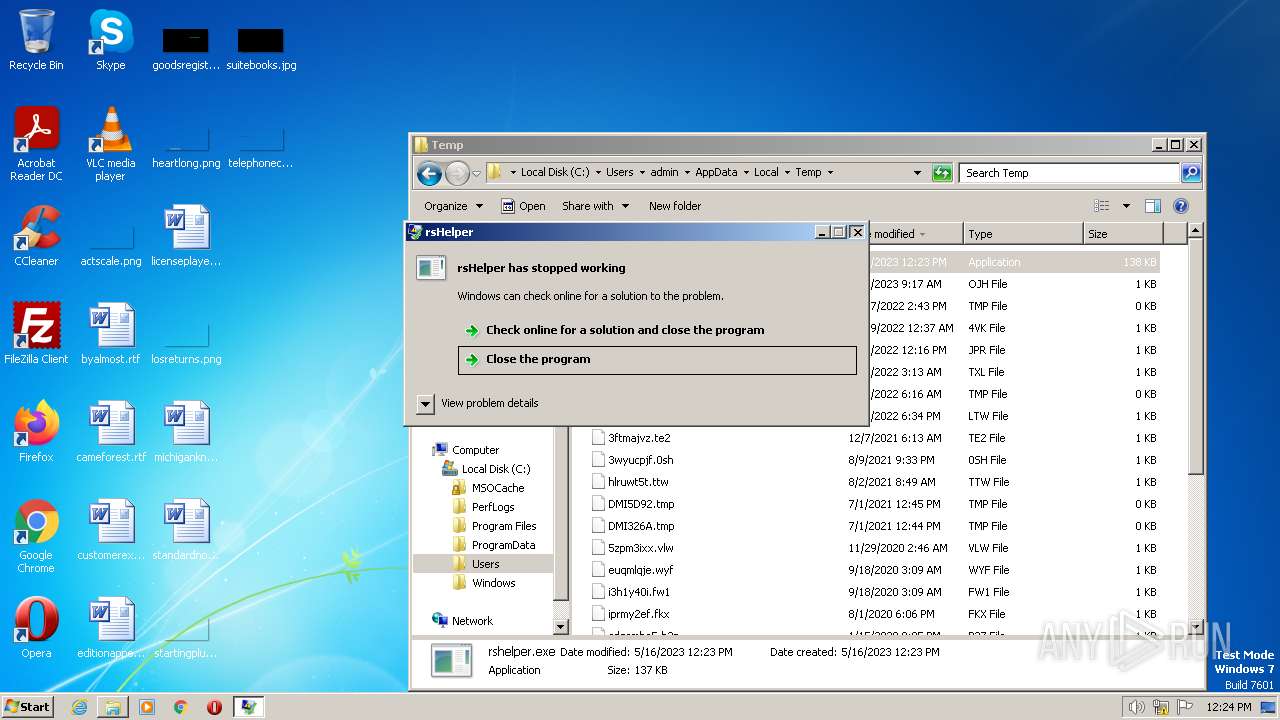
Starts Visual C# compiler
- sdiagnhost.exe (PID: 3556)
SUSPICIOUS
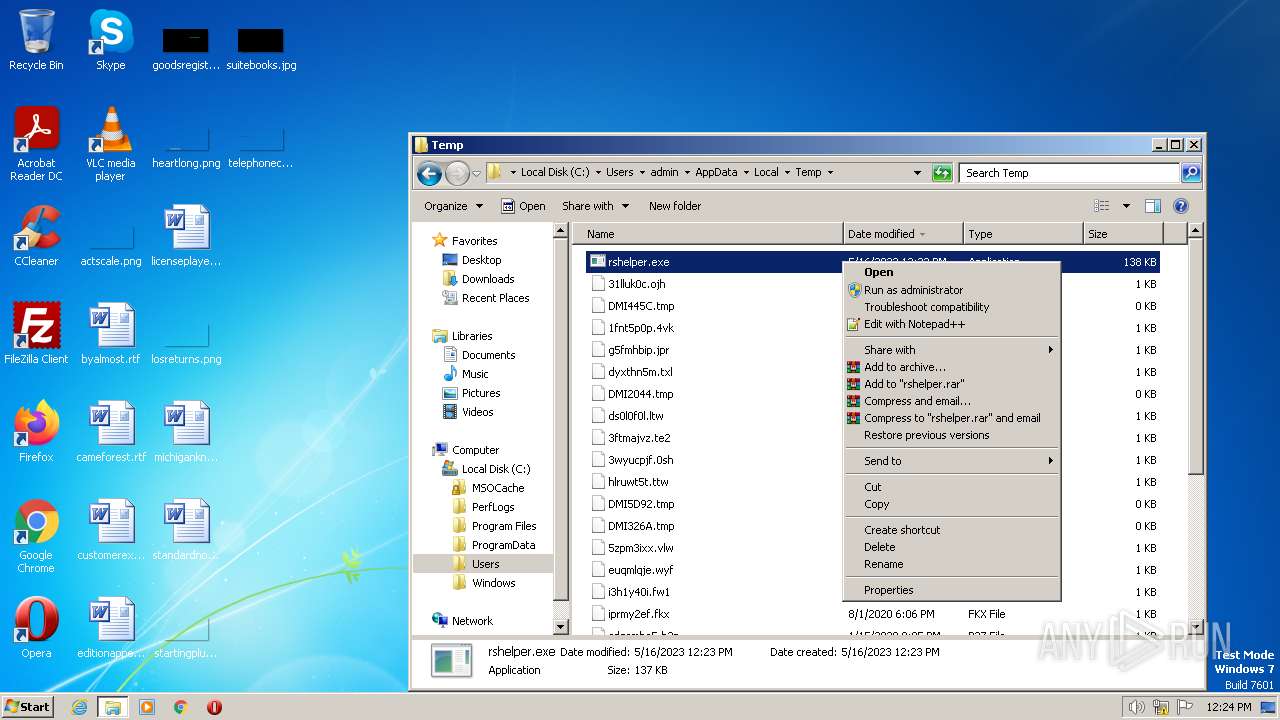
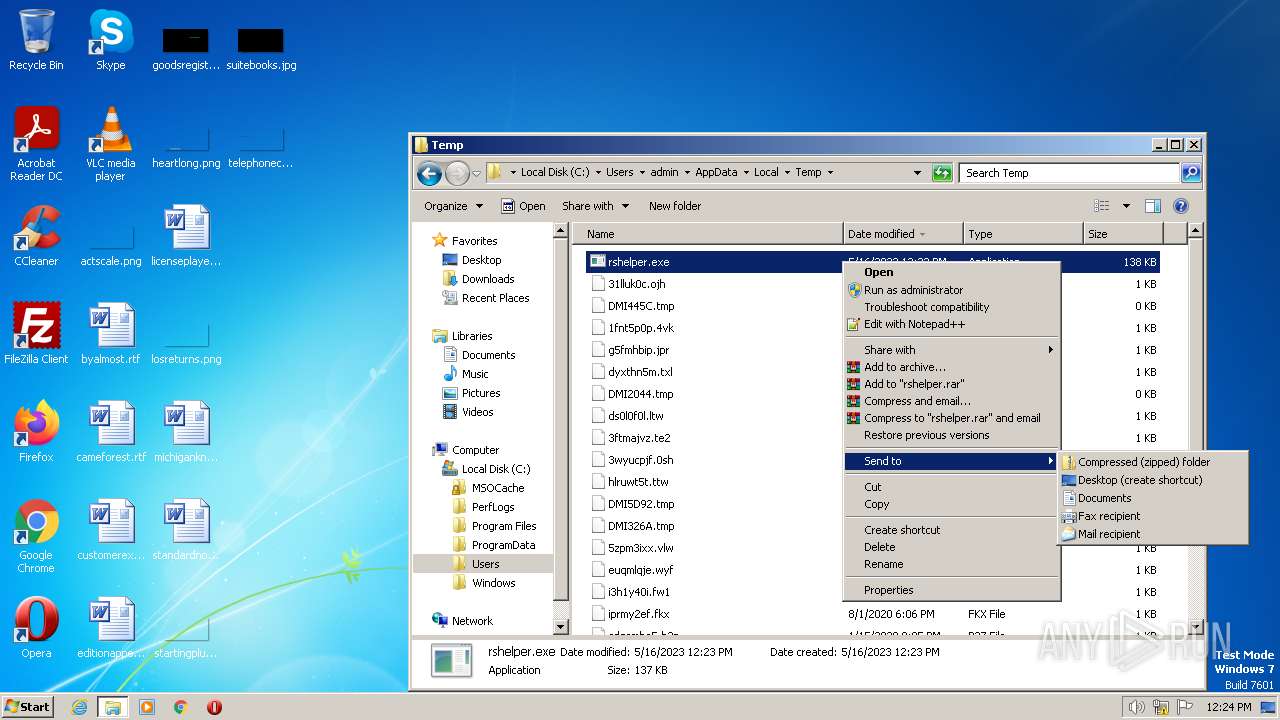
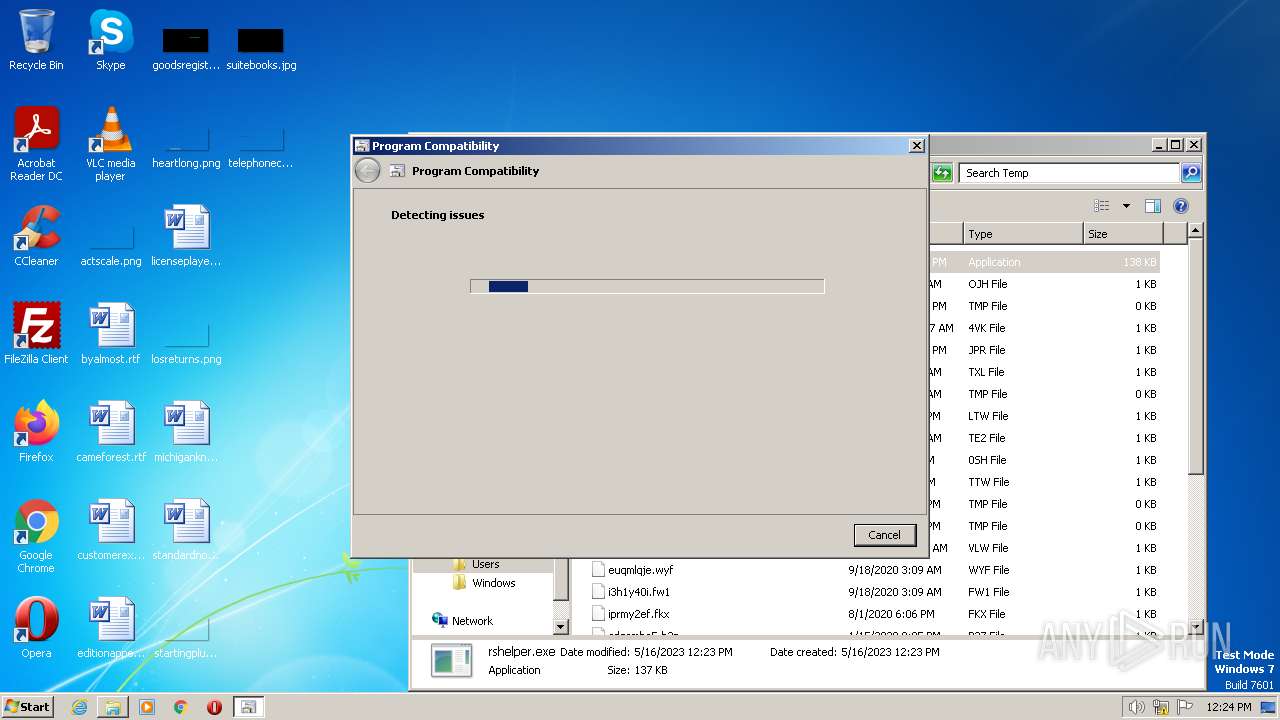
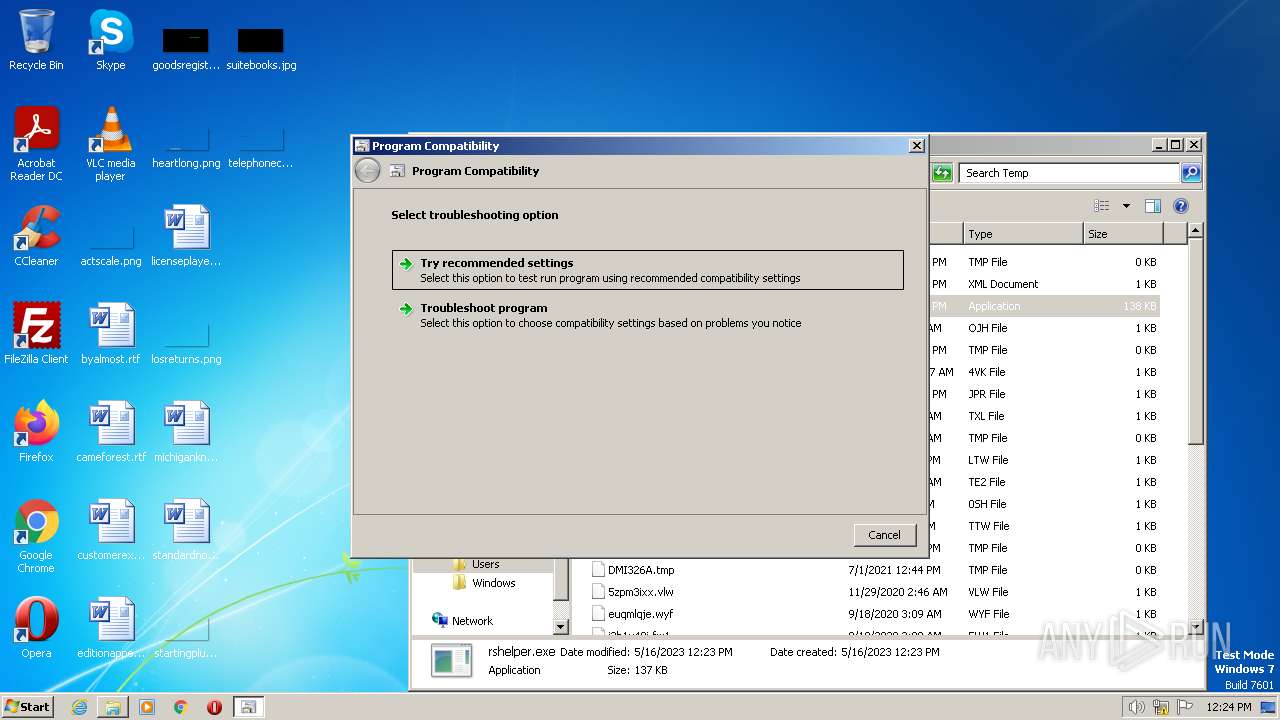
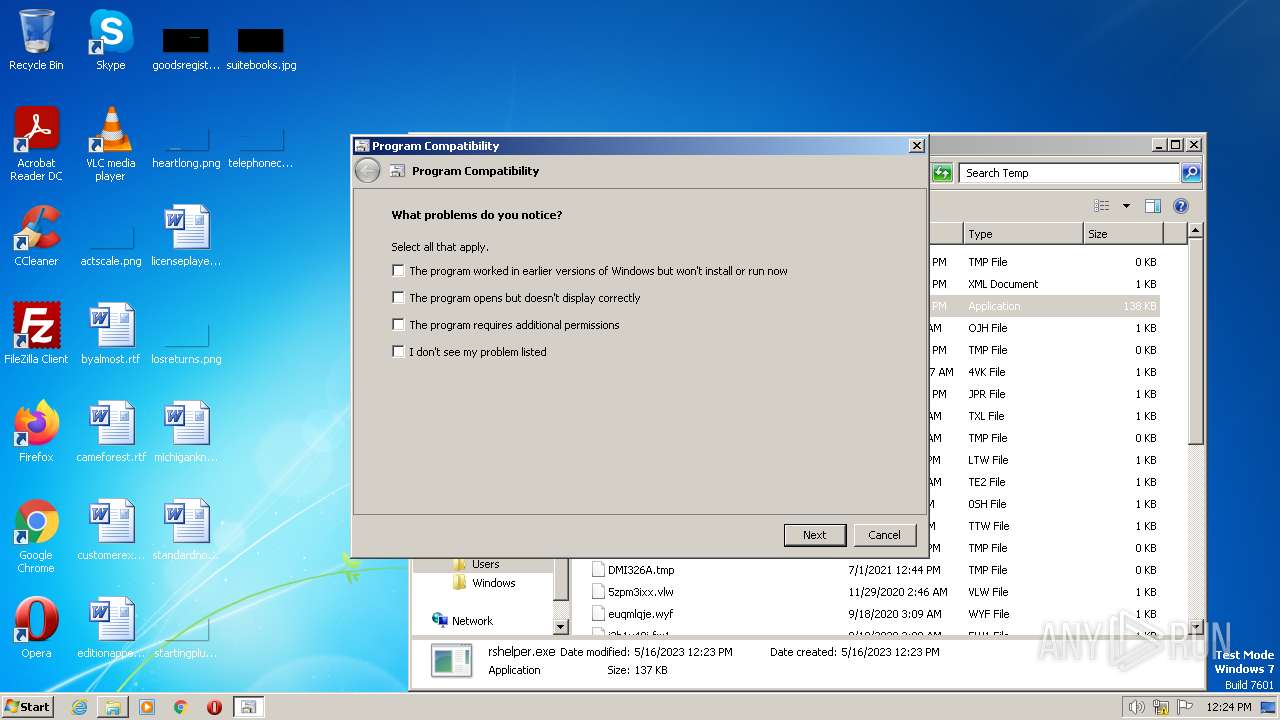
Probably uses Microsoft diagnostics tool to execute malicious payload
- pcwrun.exe (PID: 2608)
Executable content was dropped or overwritten
- msdt.exe (PID: 844)
- csc.exe (PID: 2120)
- csc.exe (PID: 956)
- csc.exe (PID: 3088)
Reads settings of System Certificates
- msdt.exe (PID: 844)
Reads security settings of Internet Explorer
- msdt.exe (PID: 844)
Uses .NET C# to load dll
- sdiagnhost.exe (PID: 3556)
INFO
Reads the computer name
- rshelper.exe (PID: 3952)
- rshelper.exe (PID: 3036)
- rshelper.exe (PID: 2888)
Checks supported languages
- rshelper.exe (PID: 3952)
- rshelper.exe (PID: 3036)
- rshelper.exe (PID: 2888)
The process checks LSA protection
- rshelper.exe (PID: 3952)
- explorer.exe (PID: 2624)
- rshelper.exe (PID: 3036)
- rshelper.exe (PID: 2888)
- msdt.exe (PID: 844)
Reads the machine GUID from the registry
- rshelper.exe (PID: 3952)
- rshelper.exe (PID: 3036)
- rshelper.exe (PID: 2888)
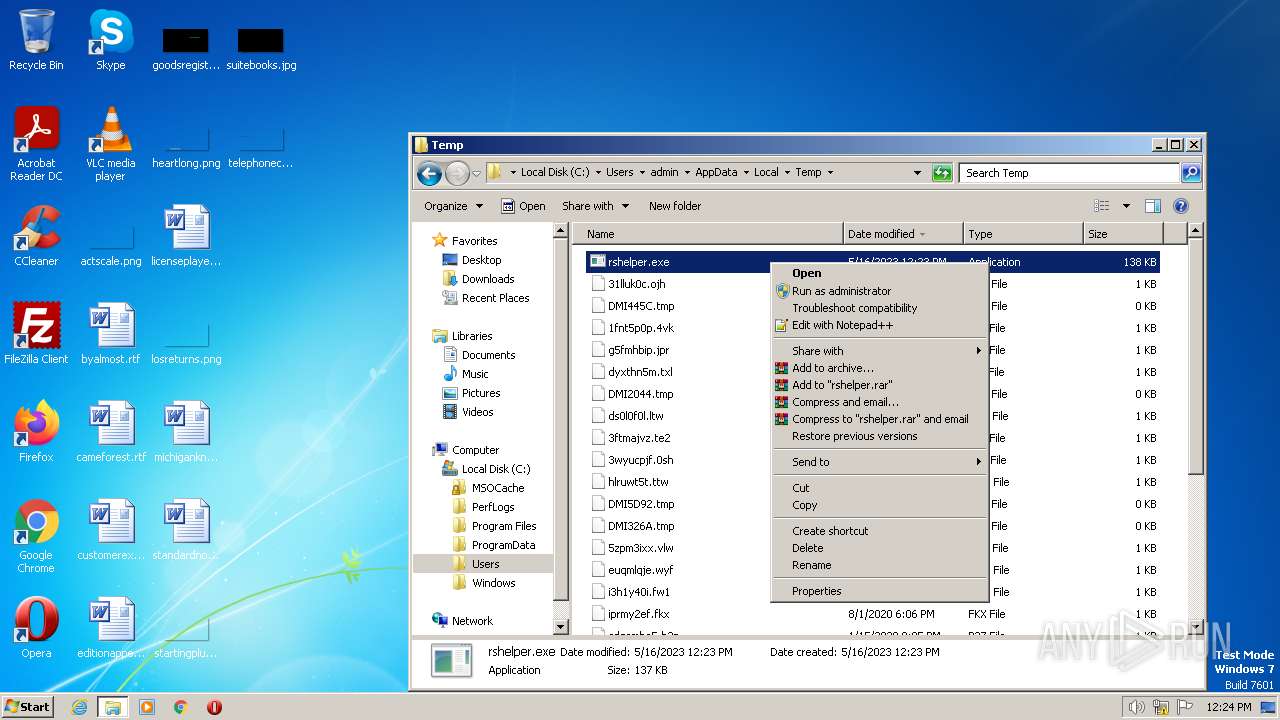
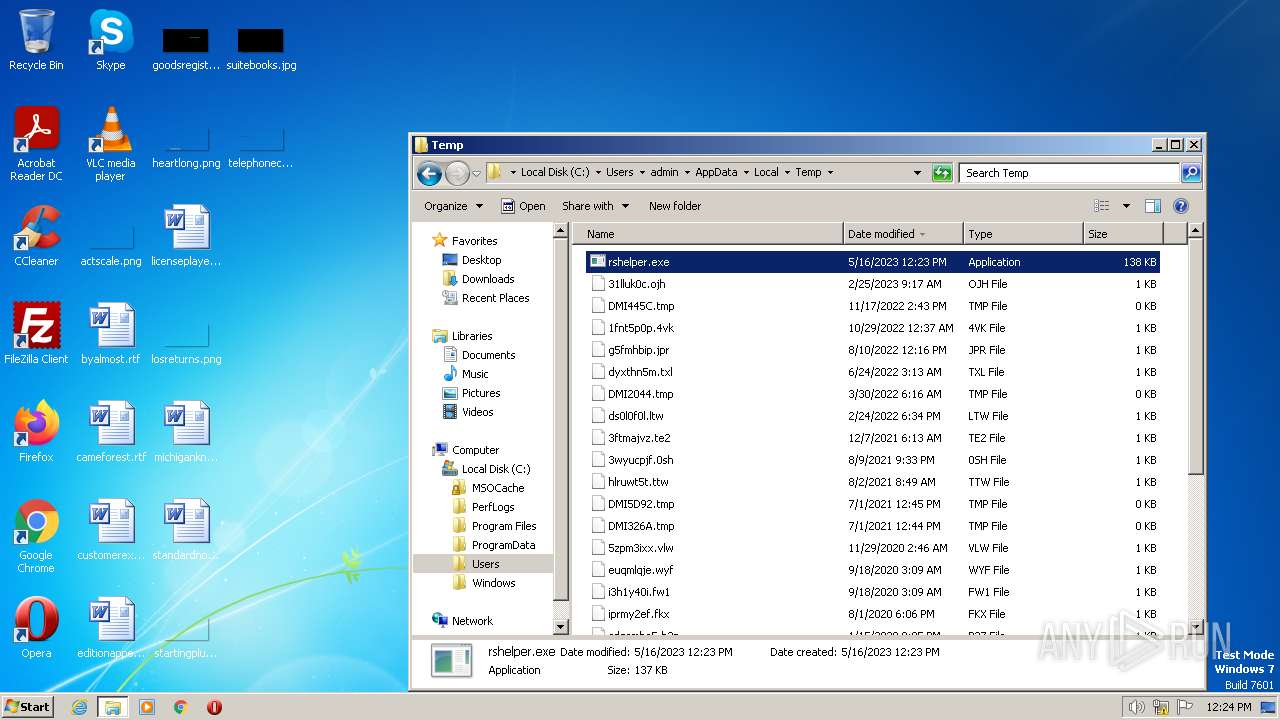
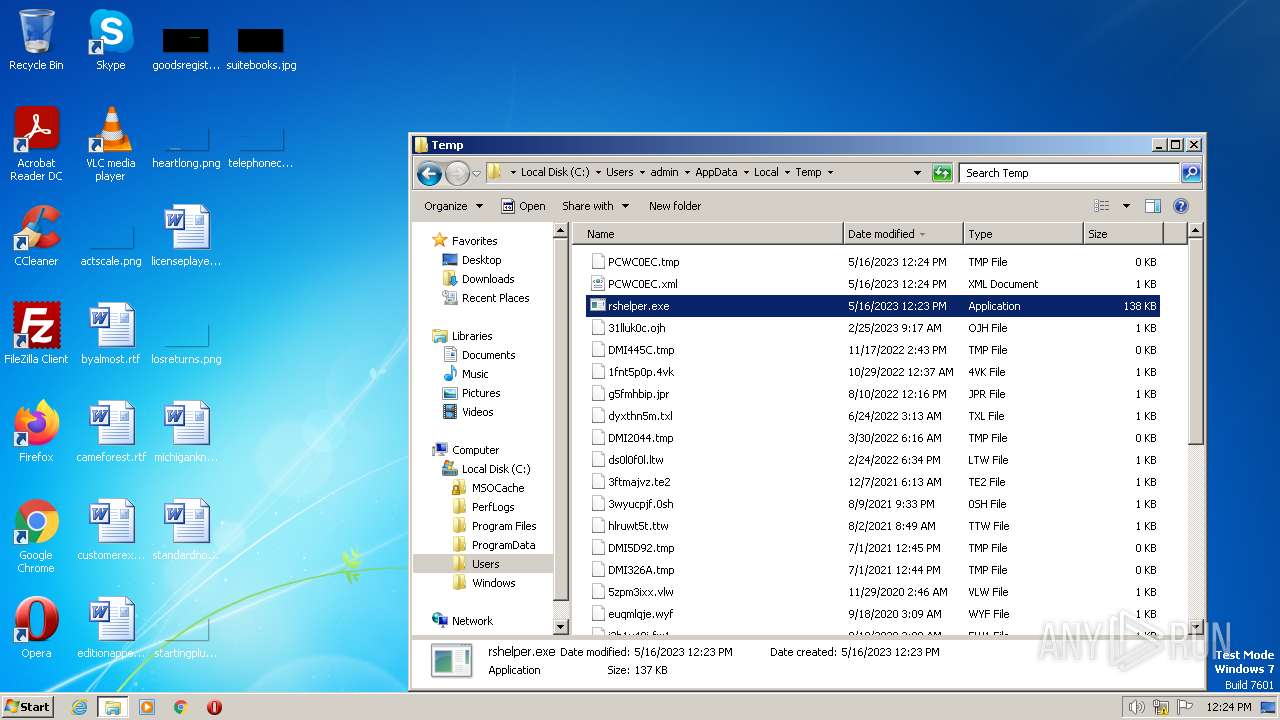
Manual execution by a user
- explorer.exe (PID: 2624)
- rshelper.exe (PID: 2888)
- rshelper.exe (PID: 3036)
- pcwrun.exe (PID: 2608)
Create files in a temporary directory
- pcwrun.exe (PID: 2608)
- msdt.exe (PID: 844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| AssemblyVersion: | 3.2.0.0 |
|---|---|
| ProductVersion: | 3.2.0.0 |
| ProductName: | Reason Security |
| OriginalFileName: | rsHelper.exe |
| LegalTrademarks: | Reason Security is a trademark of Reason Software Company Inc. |
| LegalCopyright: | Copyright © 2022 Reason Software Company Inc. |
| InternalName: | rsHelper.exe |
| FileVersion: | 3.2.0.0 |
| FileDescription: | rsHelper |
| CompanyName: | Reason Software Company Inc. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 3.2.0.0 |
| FileVersionNumber: | 3.2.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1fb6e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2560 |
| CodeSize: | 121856 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2045:07:07 07:05:17+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Jul-2045 07:05:17 |
| Debug artifacts: |
|
| CompanyName: | Reason Software Company Inc. |
| FileDescription: | rsHelper |
| FileVersion: | 3.2.0.0 |
| InternalName: | rsHelper.exe |
| LegalCopyright: | Copyright © 2022 Reason Software Company Inc. |
| LegalTrademarks: | Reason Security is a trademark of Reason Software Company Inc. |
| OriginalFilename: | rsHelper.exe |
| ProductName: | Reason Security |
| ProductVersion: | 3.2.0.0 |
| Assembly Version: | 3.2.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 07-Jul-2045 07:05:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0001DB74 | 0x0001DC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.95796 |
.rsrc | 0x00020000 | 0x00000684 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.59479 |
.reloc | 0x00022000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
59
Monitored processes
13
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
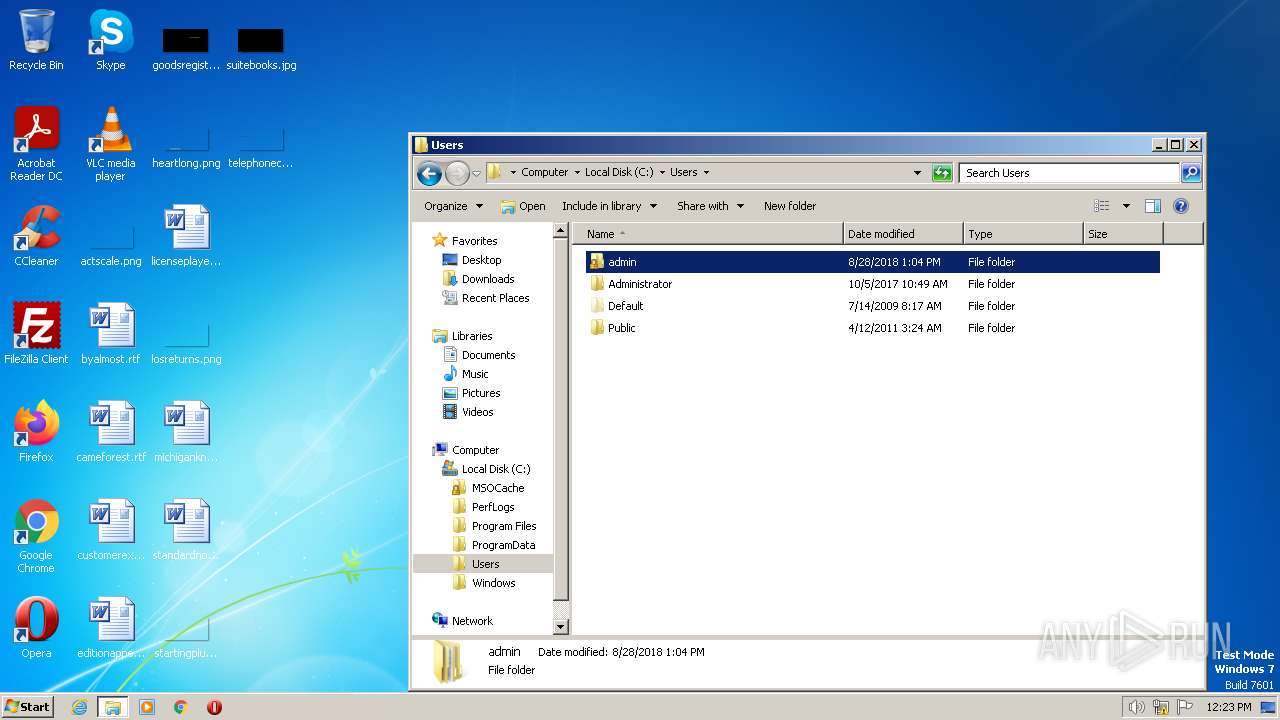
| 784 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESC532.tmp" "c:\Users\admin\AppData\Local\Temp\CSCC531.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 844 | C:\Windows\System32\msdt.exe -path C:\Windows\diagnostics\index\PCWDiagnostic.xml -af C:\Users\admin\AppData\Local\Temp\PCWC0EC.xml /skip TRUE | C:\Windows\System32\msdt.exe | pcwrun.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 956 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\ros6qwcs.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1356 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESC590.tmp" "c:\Users\admin\AppData\Local\Temp\CSCC58F.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2120 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\kdip-xcm.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2376 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESC61D.tmp" "c:\Users\admin\AppData\Local\Temp\CSCC61C.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2608 | C:\Windows\system32\pcwrun.exe "C:\Users\admin\AppData\Local\Temp\rshelper.exe" | C:\Windows\System32\pcwrun.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Program Compatibility Troubleshooter Invoker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2624 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2888 | "C:\Users\admin\AppData\Local\Temp\rshelper.exe" | C:\Users\admin\AppData\Local\Temp\rshelper.exe | explorer.exe | ||||||||||||
User: admin Company: Reason Software Company Inc. Integrity Level: HIGH Description: rsHelper Exit code: 3762504530 Version: 3.2.0.0 Modules
| |||||||||||||||
| 3036 | "C:\Users\admin\AppData\Local\Temp\rshelper.exe" | C:\Users\admin\AppData\Local\Temp\rshelper.exe | explorer.exe | ||||||||||||
User: admin Company: Reason Software Company Inc. Integrity Level: MEDIUM Description: rsHelper Exit code: 3762504530 Version: 3.2.0.0 Modules
| |||||||||||||||
Total events
5 846
Read events
5 782
Write events
64
Delete events
0
Modification events
| (PID) Process: | (3952) rshelper.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3036) rshelper.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2888) rshelper.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (844) msdt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3556) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3556) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3556) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3556) sdiagnhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
5
Suspicious files
15
Text files
23
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 844 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_da19df26-83ef-4946-89d6-5011cb50c3dd\RS_ProgramCompatibilityWizard.ps1 | text | |
MD5:367FE5F4C6DB87E1600F46687E5AAC54 | SHA256:177625AC9B07BBFFCBBB47101C2D1121F47B03B42226861BFD7974B9CEBC0C98 | |||
| 844 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_da19df26-83ef-4946-89d6-5011cb50c3dd\DiagPackage.diagpkg | html | |
MD5:18A906A43C1C3E27064DB30C81505234 | SHA256:041430D1F0AE14300C46BDCD917C882F4850DA3D6010E3FBF692023655BC406E | |||
| 844 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_da19df26-83ef-4946-89d6-5011cb50c3dd\result\results.xsl | xml | |
MD5:310E1DA2344BA6CA96666FB639840EA9 | SHA256:67401342192BABC27E62D4C1E0940409CC3F2BD28F77399E71D245EAE8D3F63C | |||
| 3556 | sdiagnhost.exe | C:\Users\admin\AppData\Local\Temp\kdip-xcm.cmdline | text | |
MD5:13CA97668874B802D9FEBFE3F0463371 | SHA256:020659383CBF7E8B2A1D2489A8BD231ED42E7530D46F6BB1FF7BBA65D4979C53 | |||
| 844 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_da19df26-83ef-4946-89d6-5011cb50c3dd\en-US\DiagPackage.dll.mui | executable | |
MD5:C31BD28AB34E75BC65A5458AC8D37539 | SHA256:5FB9E280013D58043C5689478F9DCFAD3212F4681534627EB33998DDD6F63308 | |||
| 2120 | csc.exe | C:\Users\admin\AppData\Local\Temp\kdip-xcm.out | text | |
MD5:922A79DC8D30F916519EF532591CB543 | SHA256:315C6FC085D159B0423493F9FCC45670D0AAF58C4A55F1E114BCA3BB50D9A3DC | |||
| 2120 | csc.exe | C:\Users\admin\AppData\Local\Temp\kdip-xcm.pdb | binary | |
MD5:5F5EAD37FA9E978957FFC2447D20813B | SHA256:4CAD940EDC16D164238DD7CFCDE89465232D01053609AD0152CF9E5D50B69EFF | |||
| 956 | csc.exe | C:\Users\admin\AppData\Local\Temp\ros6qwcs.pdb | binary | |
MD5:77050D3DB03247B44F0AFDBF89B94005 | SHA256:D034BB3C8618033229121140ECD10DF204A4DC385927FD1C3CB991D36A793963 | |||
| 844 | msdt.exe | C:\Users\admin\AppData\Local\Temp\SDIAG_da19df26-83ef-4946-89d6-5011cb50c3dd\TS_ProgramCompatibilityWizard.ps1 | text | |
MD5:46E22C2582B54BE56D80D7A79FEC9BB5 | SHA256:459AF2960B08E848573D45A7350223657ADB2115F24A3C37E69FFE61DEA647F9 | |||
| 2120 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCC531.tmp | binary | |
MD5:7B6F5D85C3AB79EF89C890A309EFAF8C | SHA256:E61249D85DD014C298DB41E688C4E456D94A9FA7B475532C10F65FA1A5715232 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3396 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|