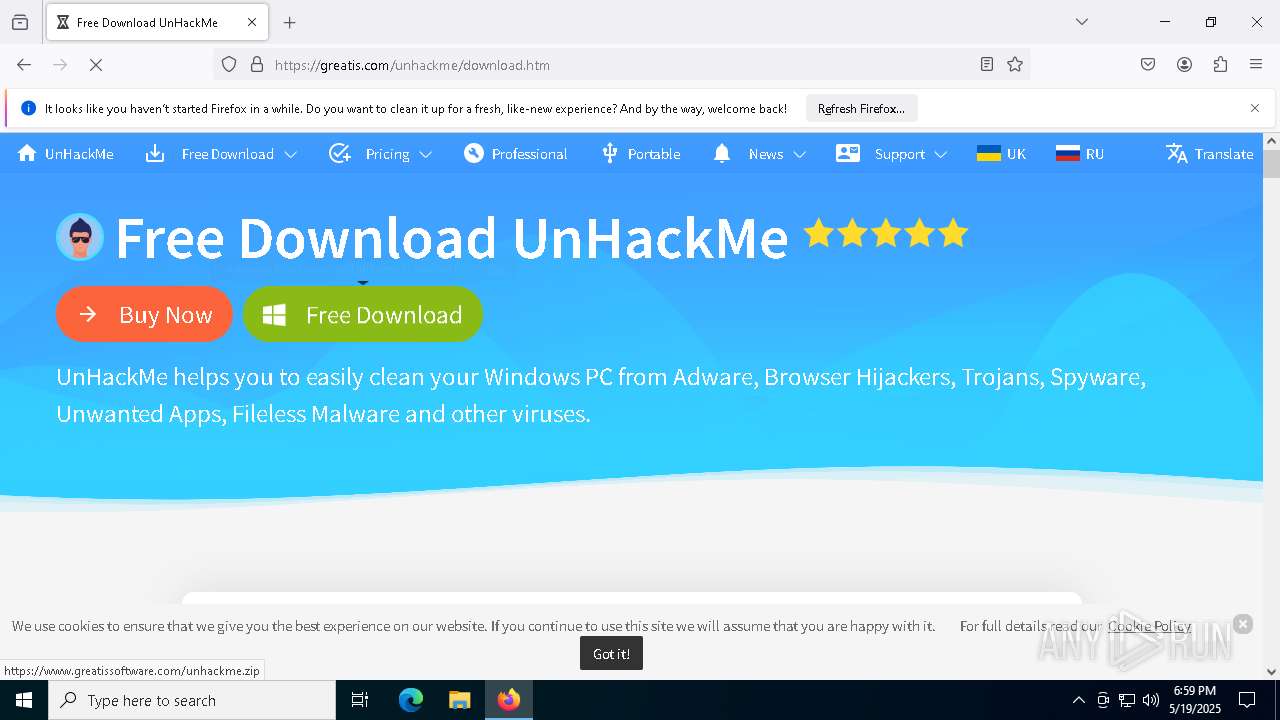
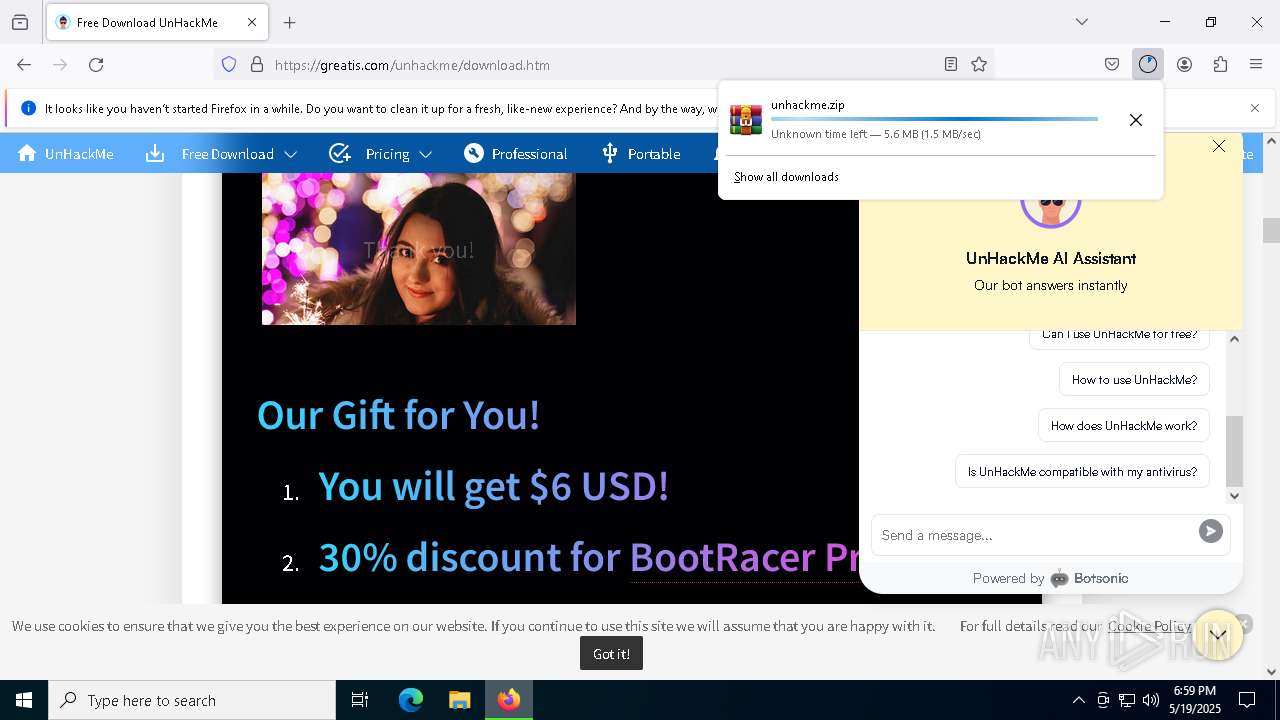
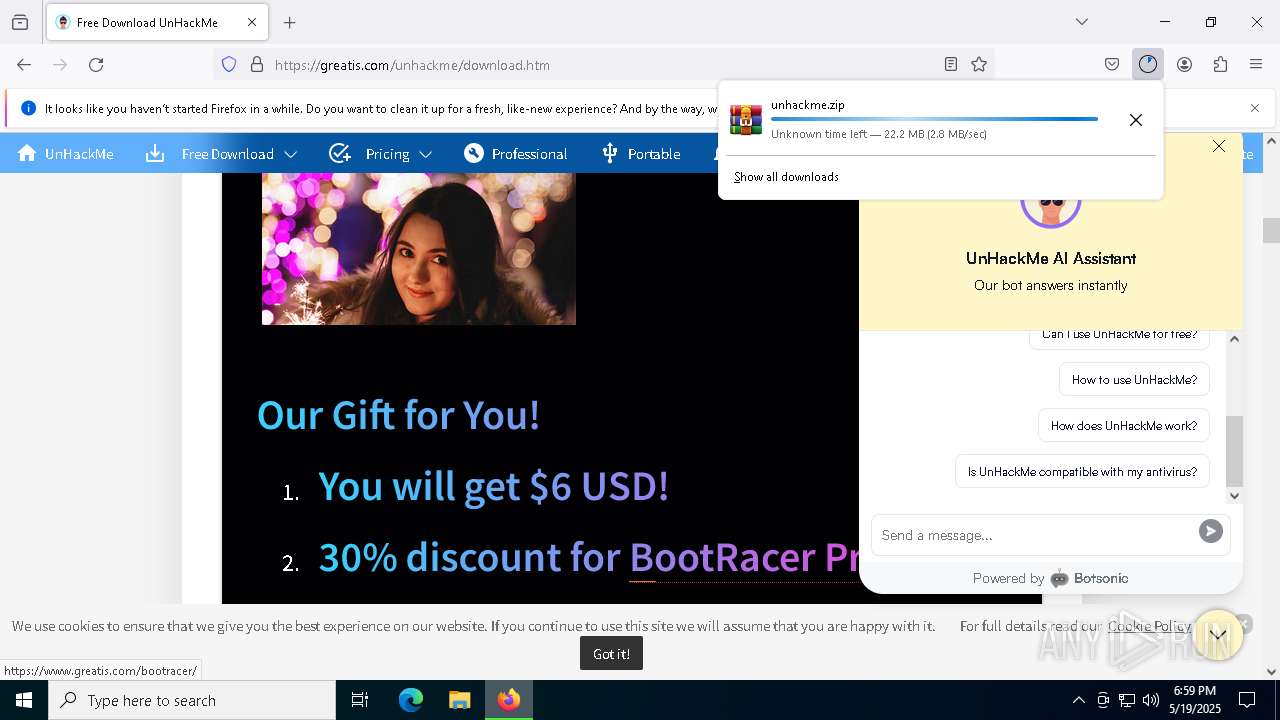
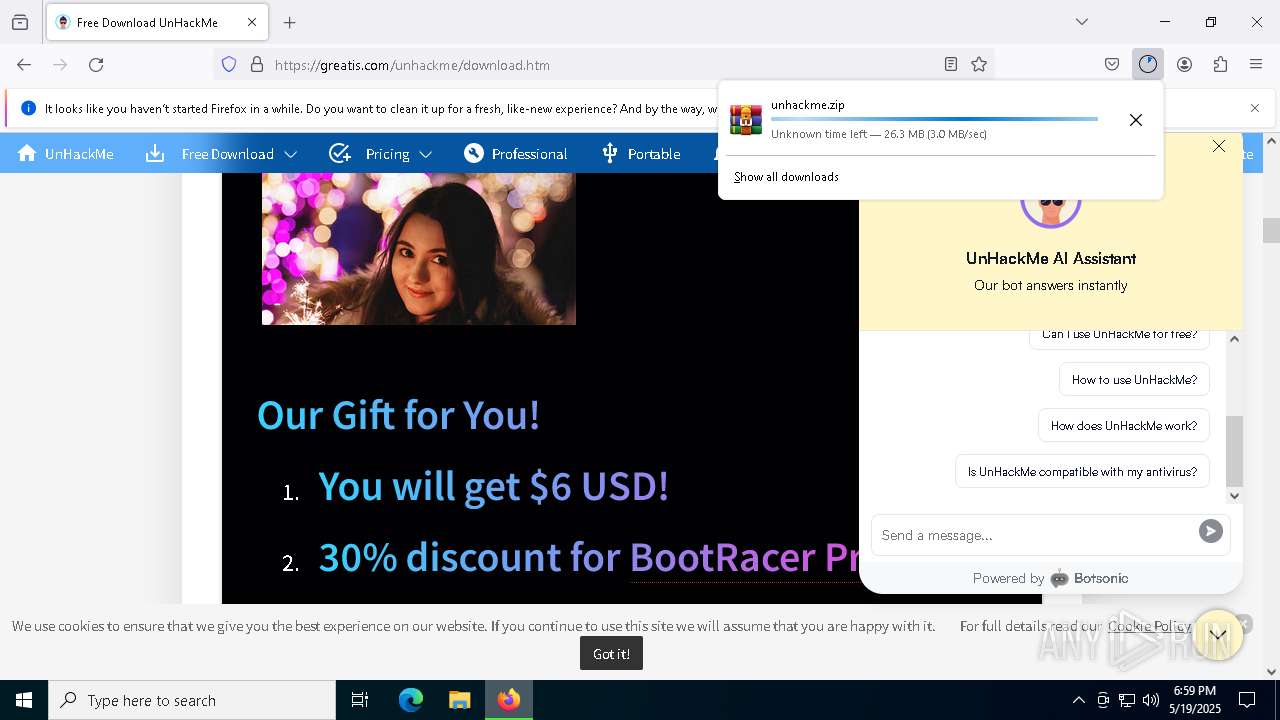
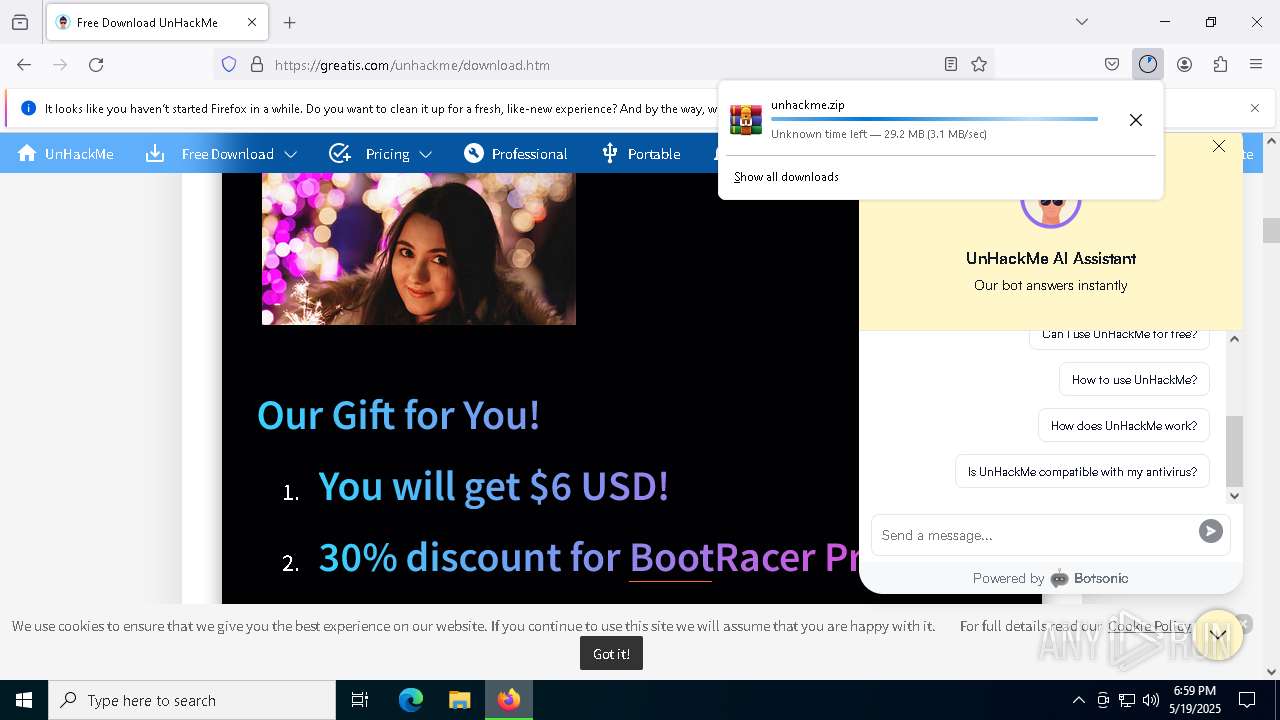
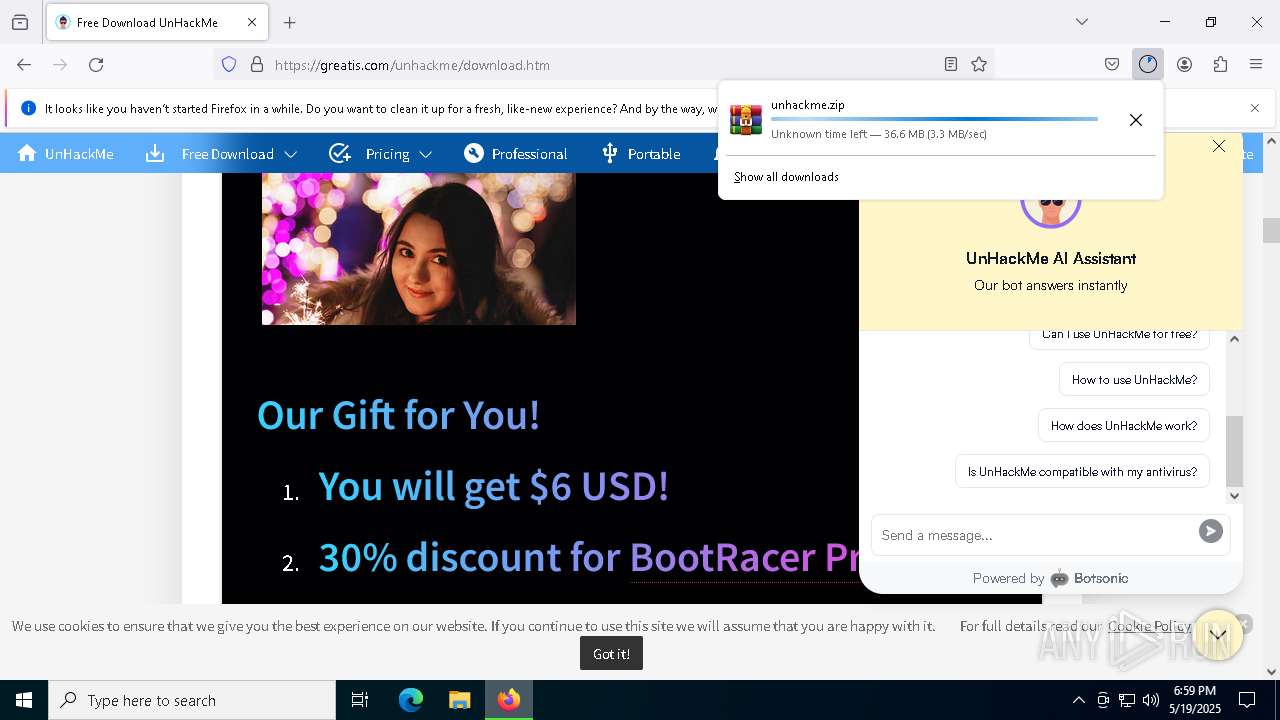
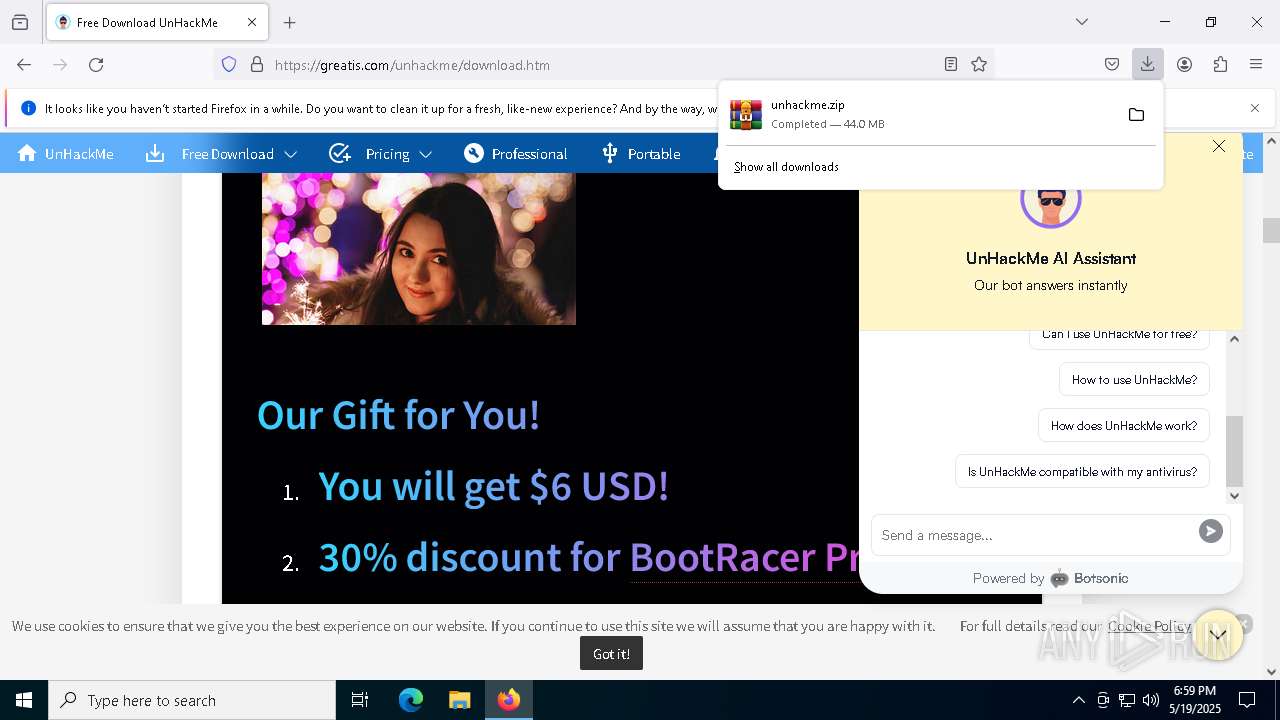
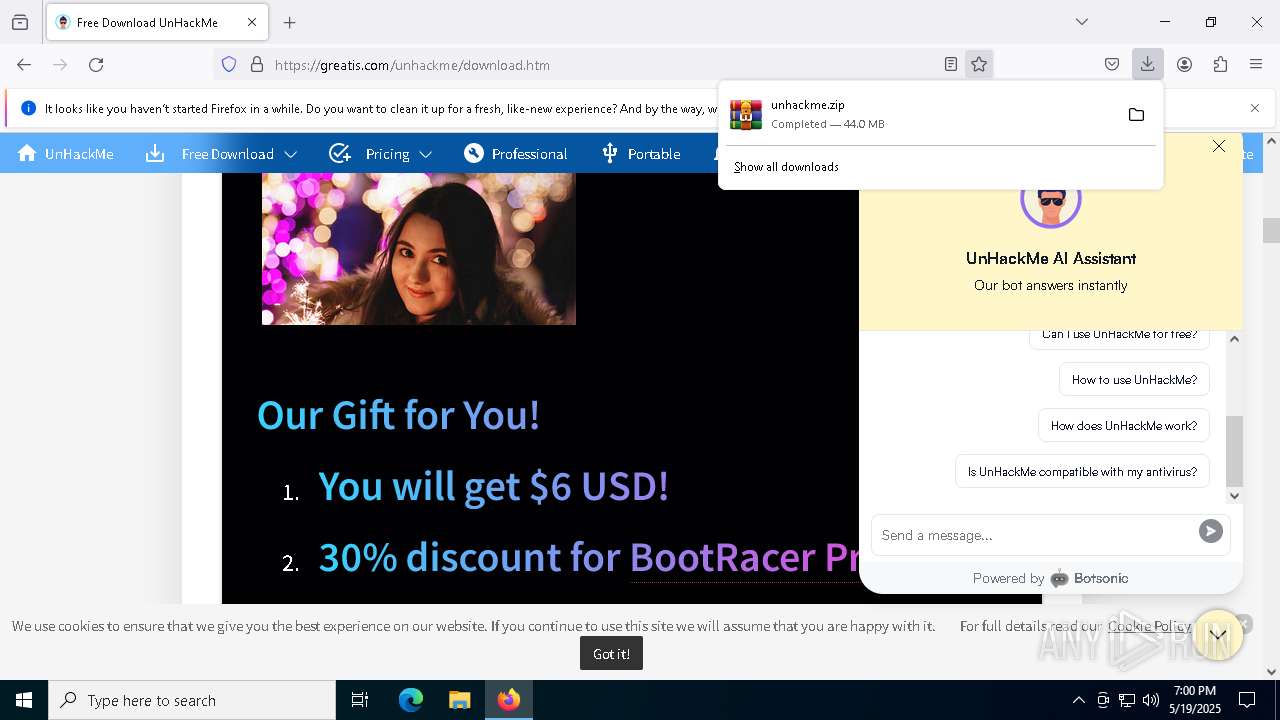
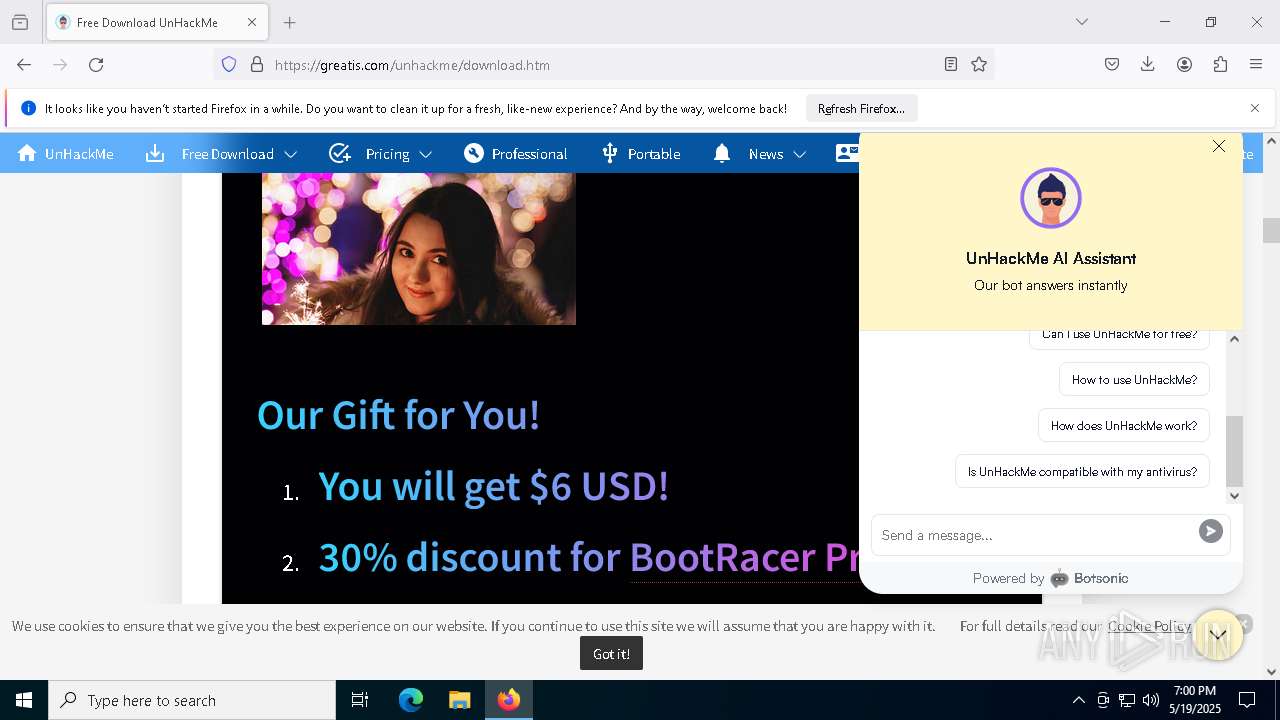
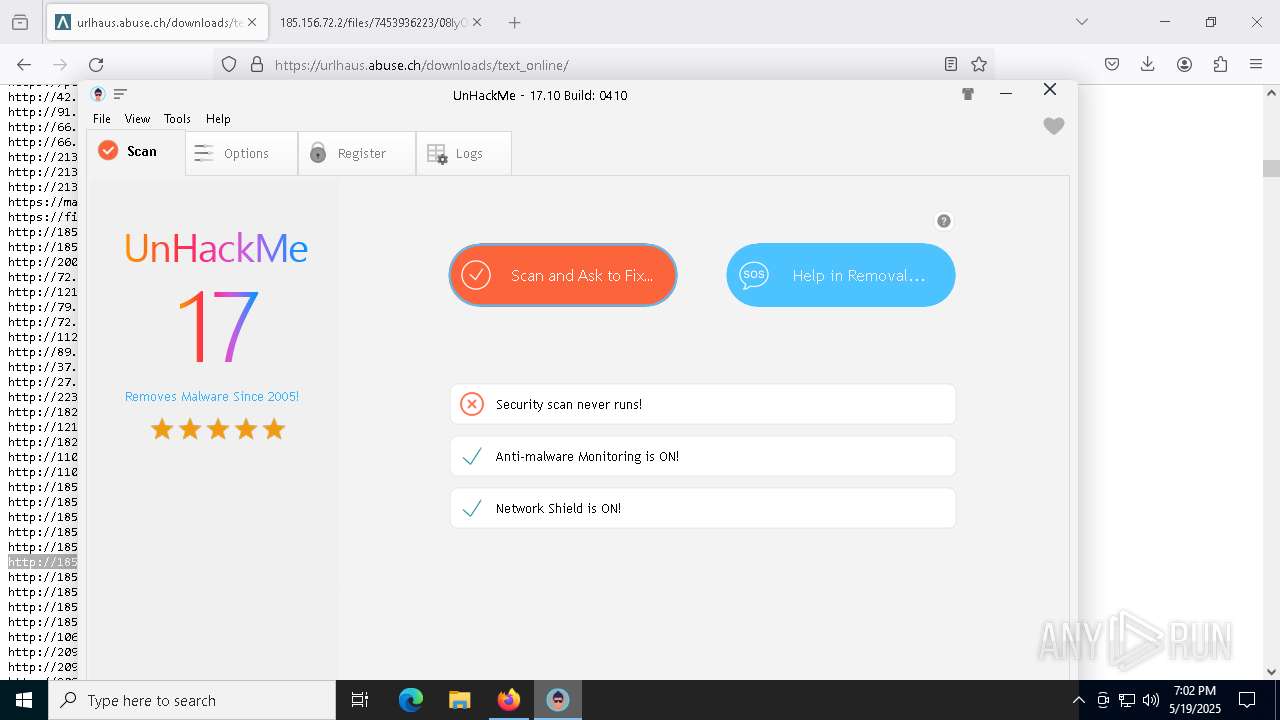
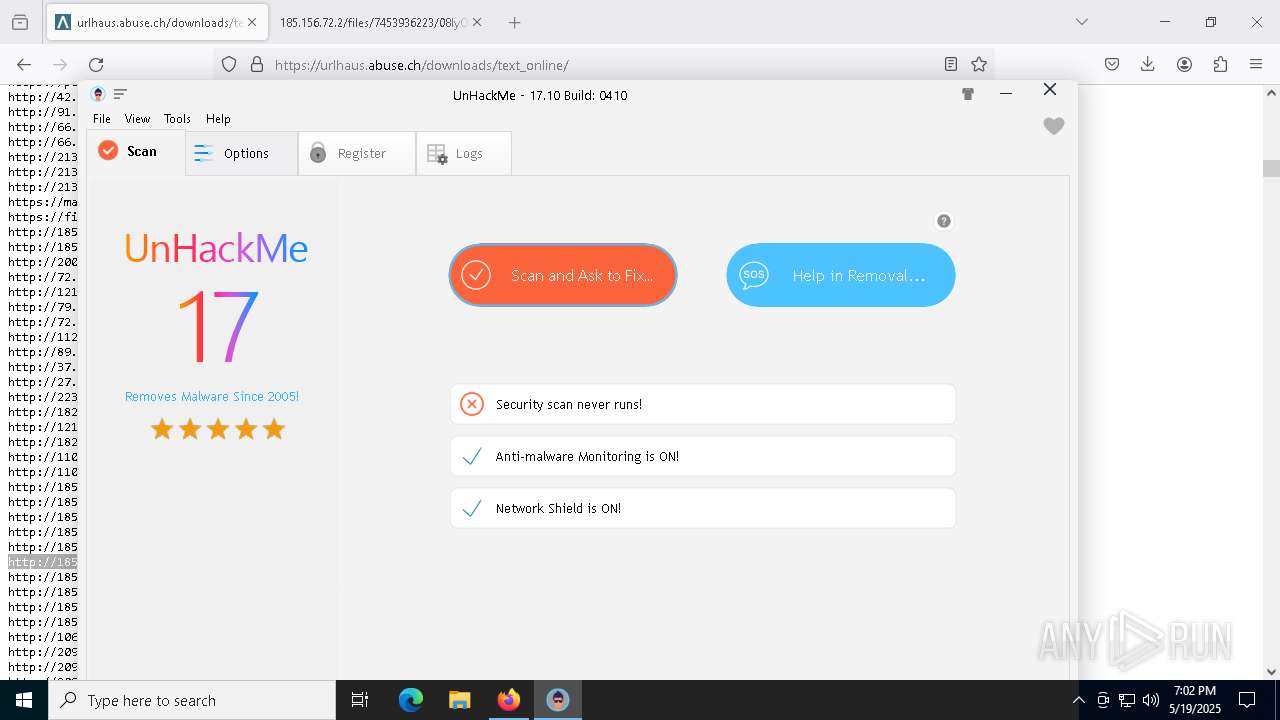
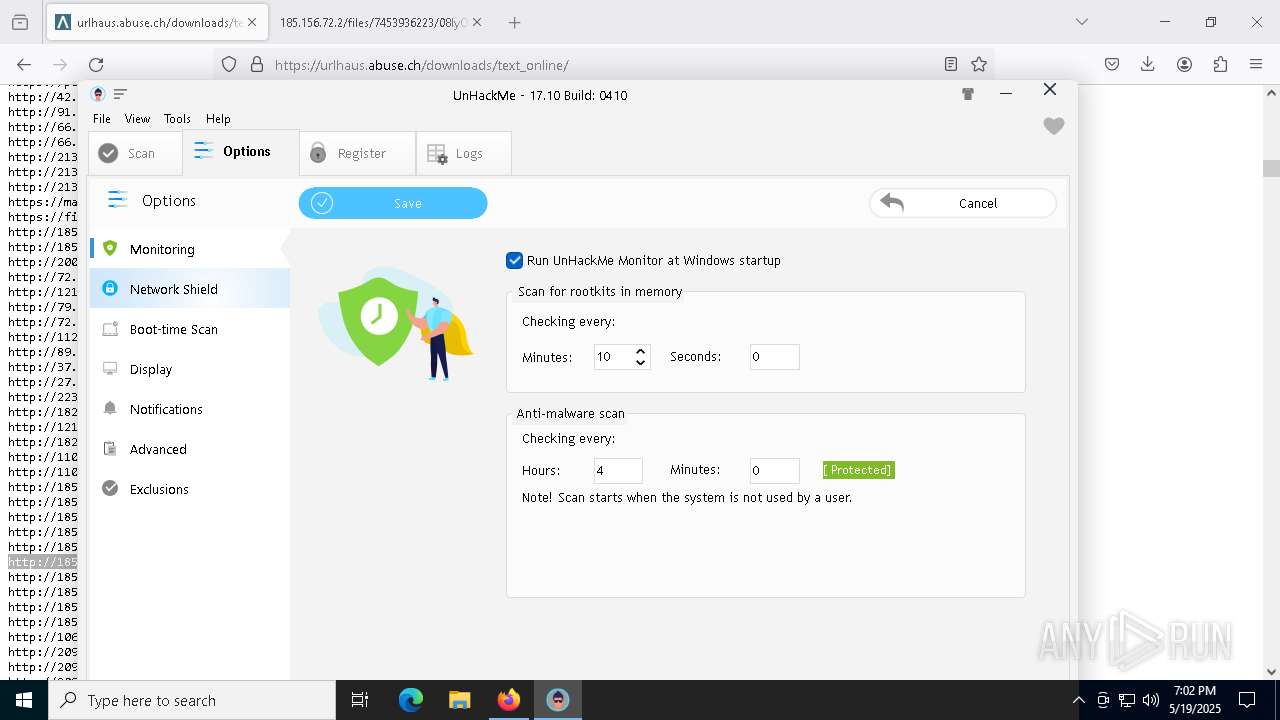
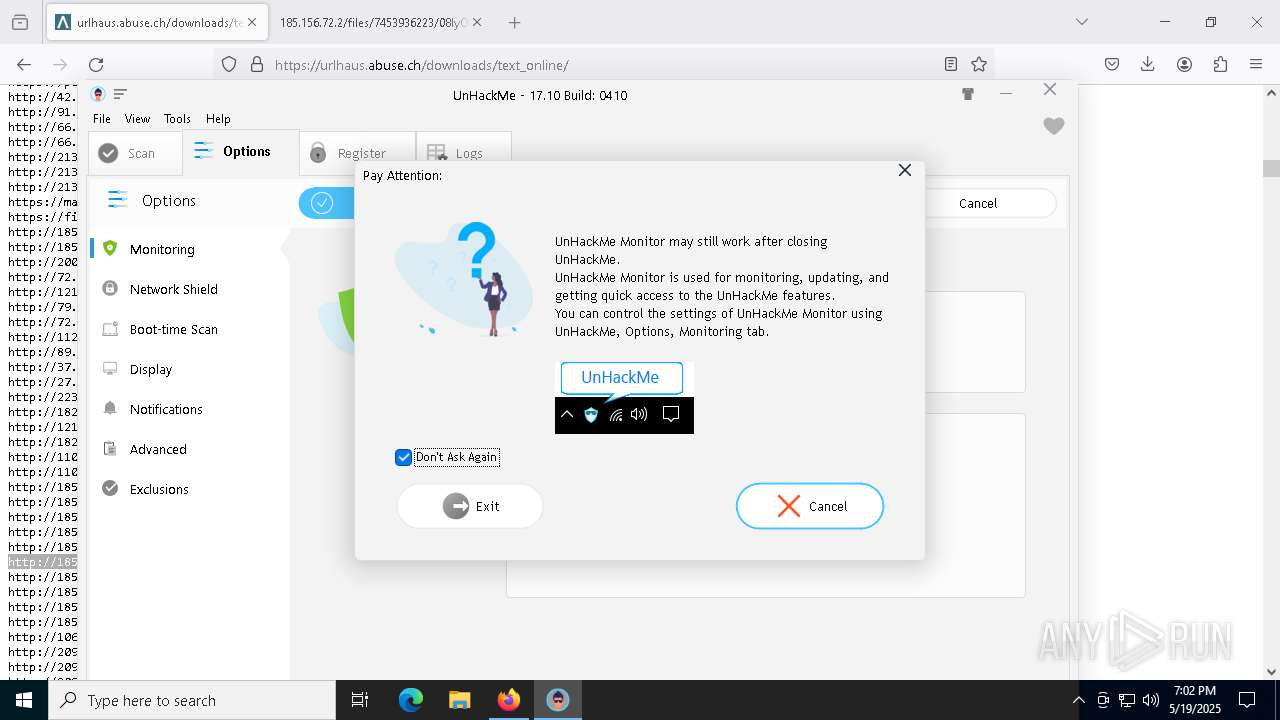
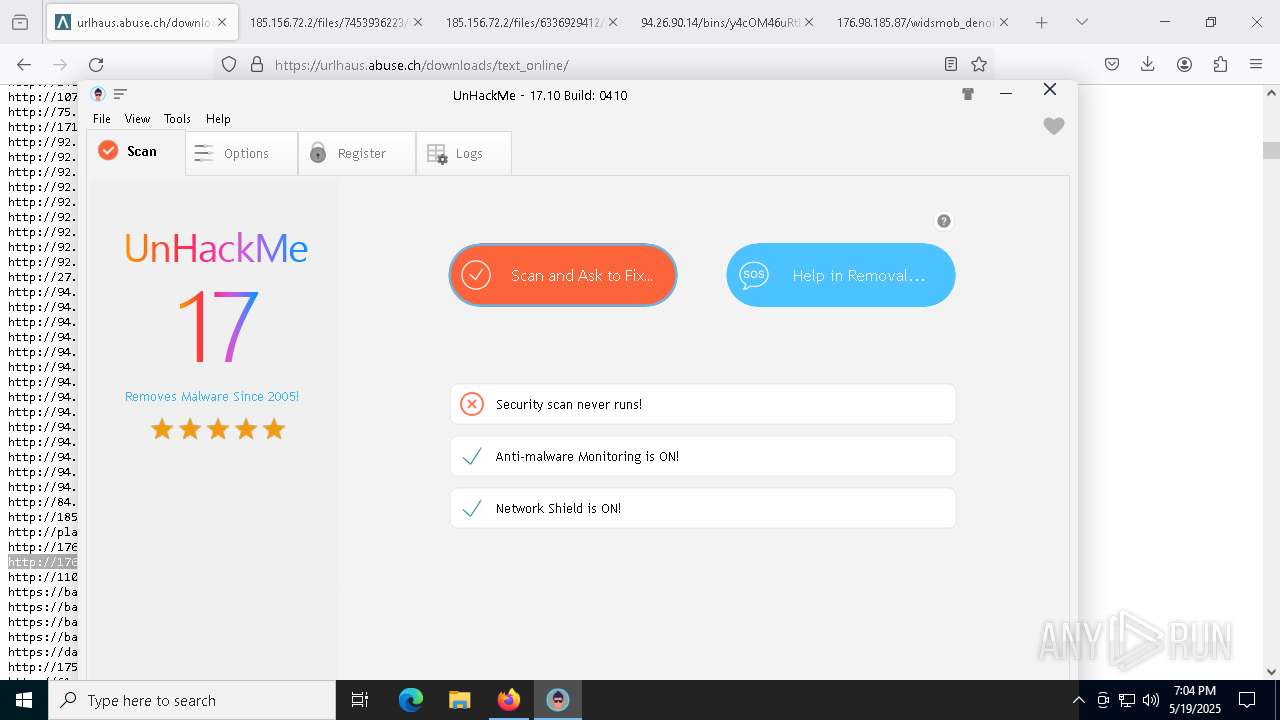
| URL: | https://greatis.com/unhackme/index.html |
| Full analysis: | https://app.any.run/tasks/41e71676-adae-40f3-a2bf-ebb6d8138cd0 |
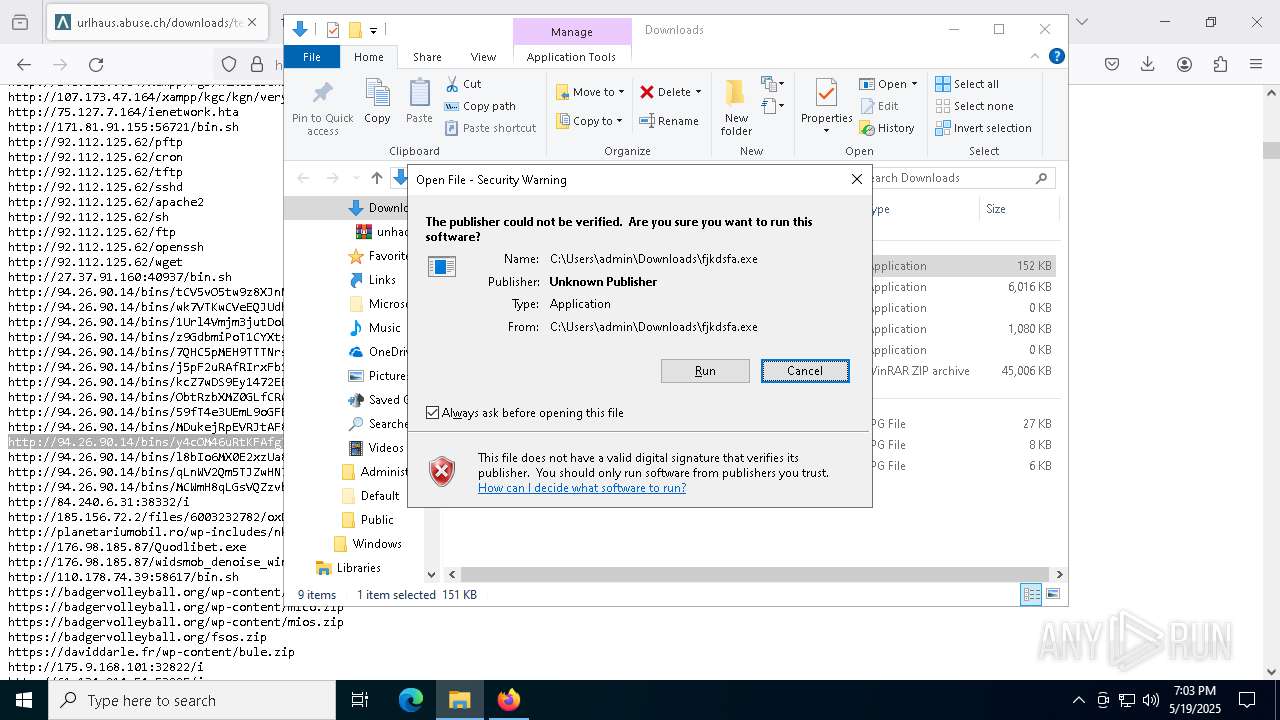
| Verdict: | Malicious activity |
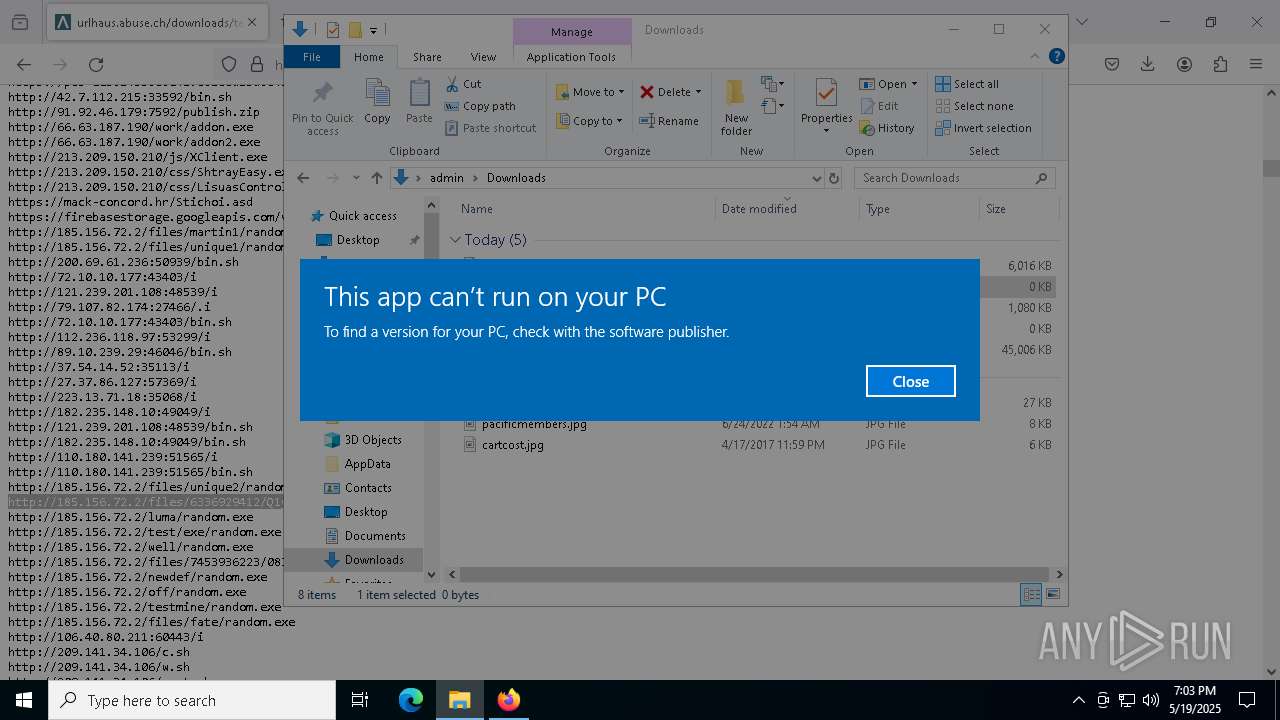
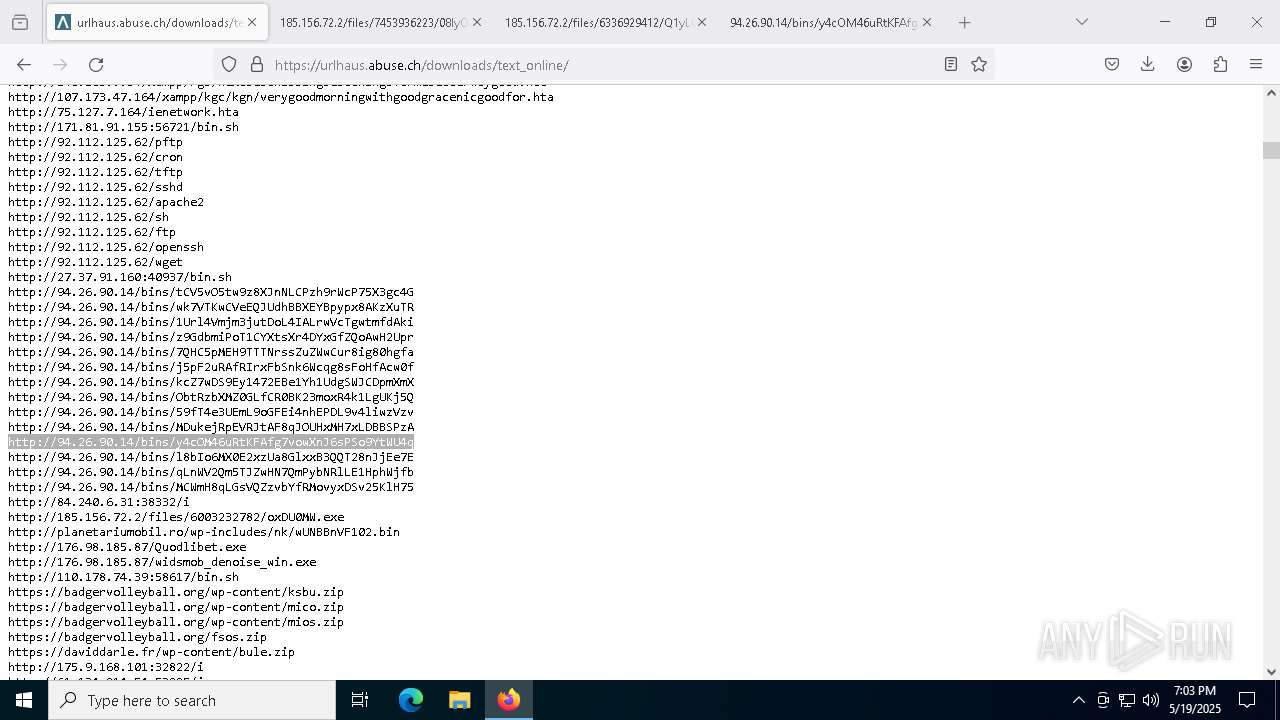
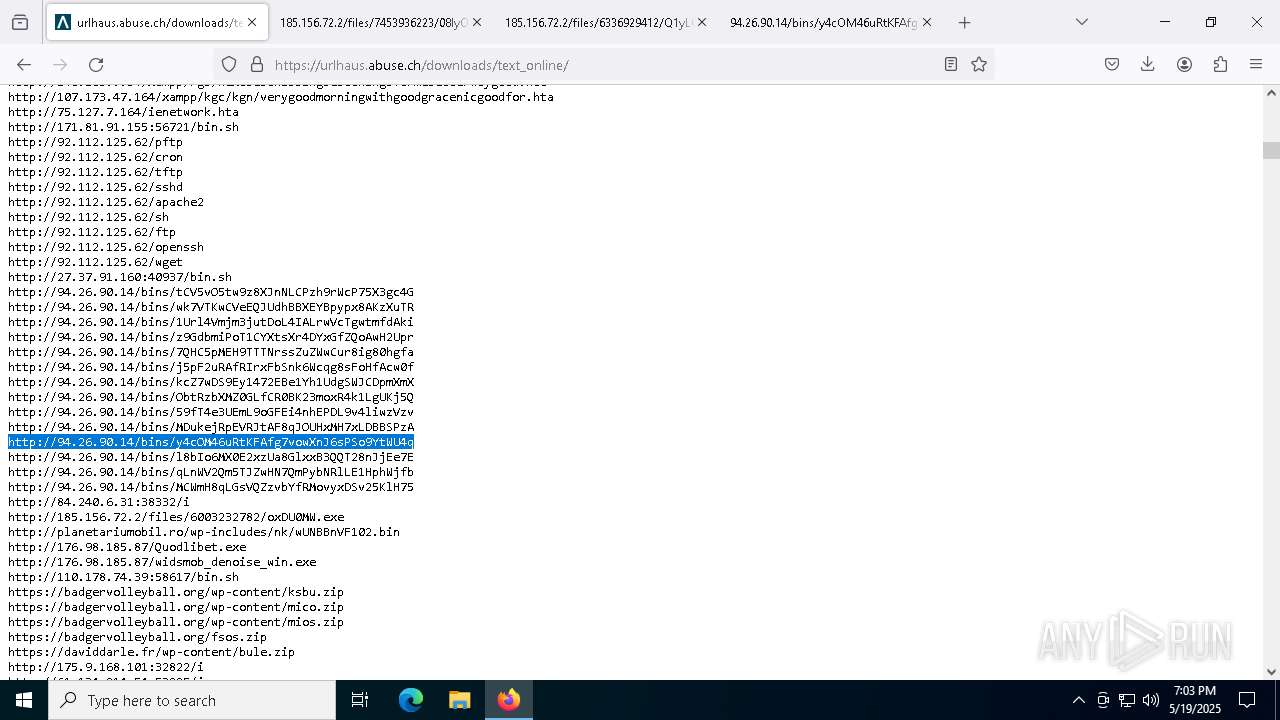
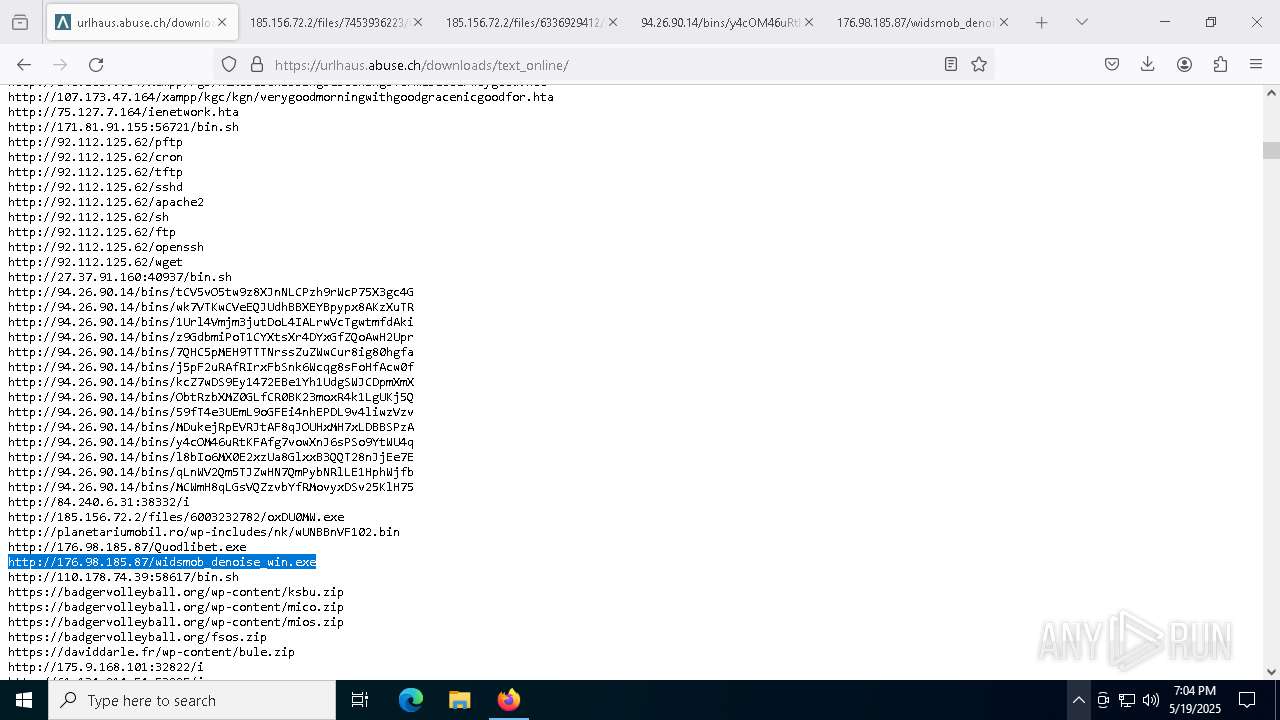
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
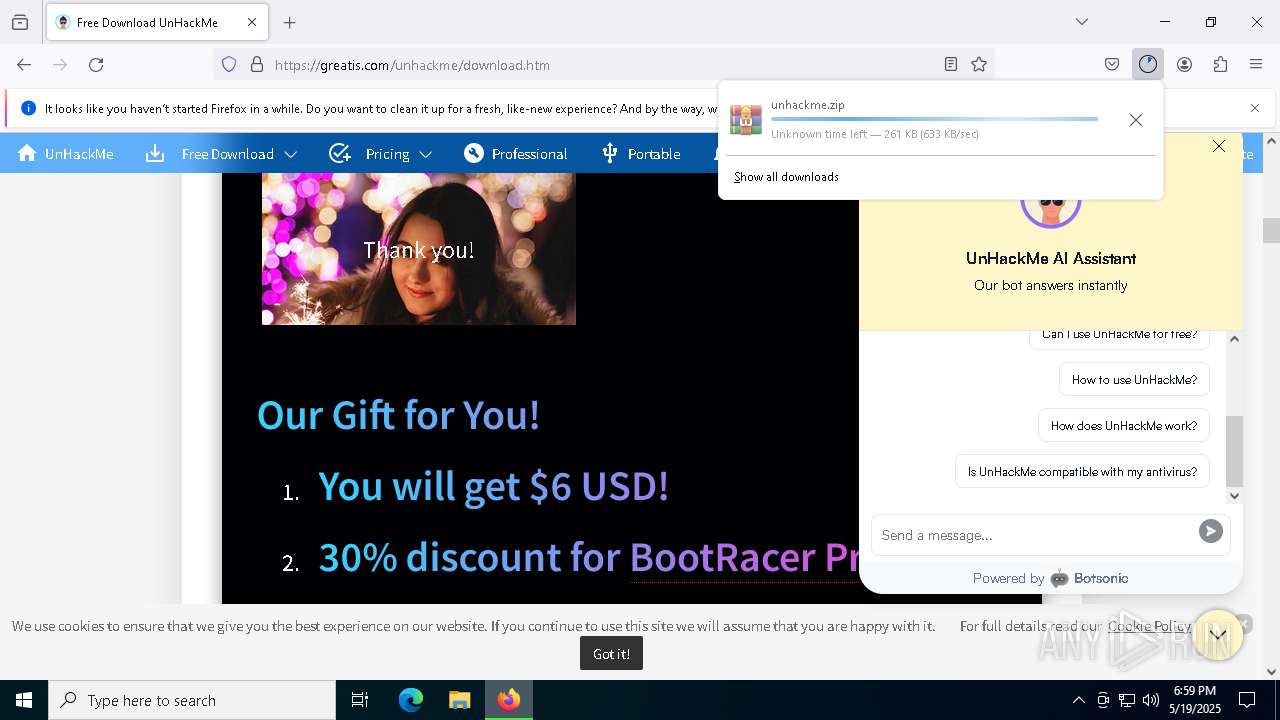
| Analysis date: | May 19, 2025, 18:59:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9442AB9B43DD1A787E51A1A458816643 |
| SHA1: | E37B920916BD340387C3DA32B958B199D23CE854 |
| SHA256: | C59A149D847D15B1D04D9FB8F8ACD487B6CAE980929C31F521421931FB75D569 |
| SSDEEP: | 3:N82A4MzLa2vM1Ad5G:22szLa2TDG |
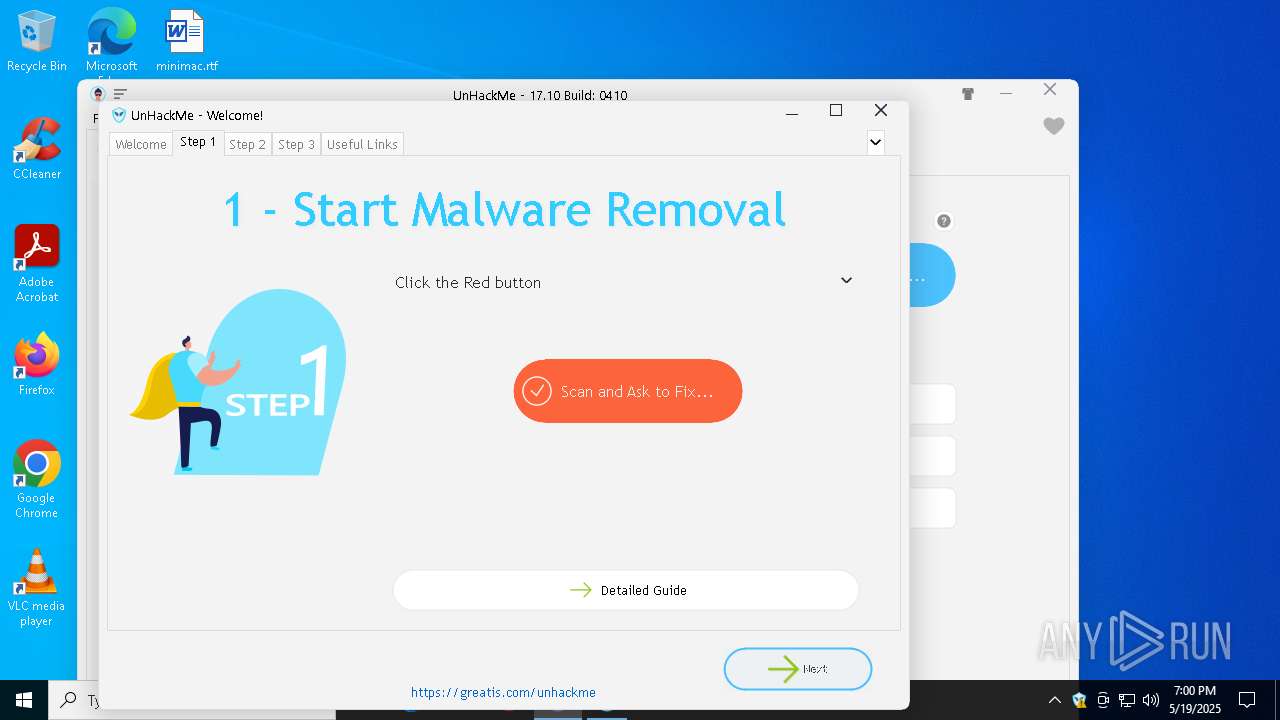
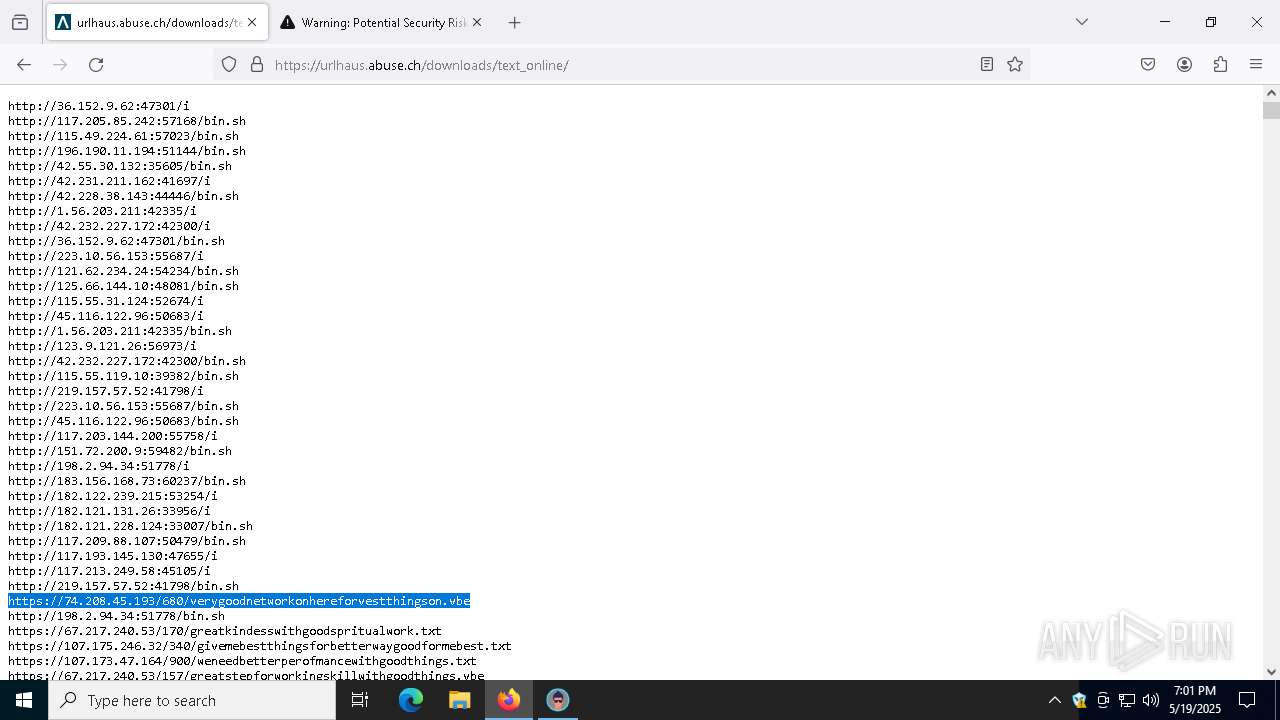
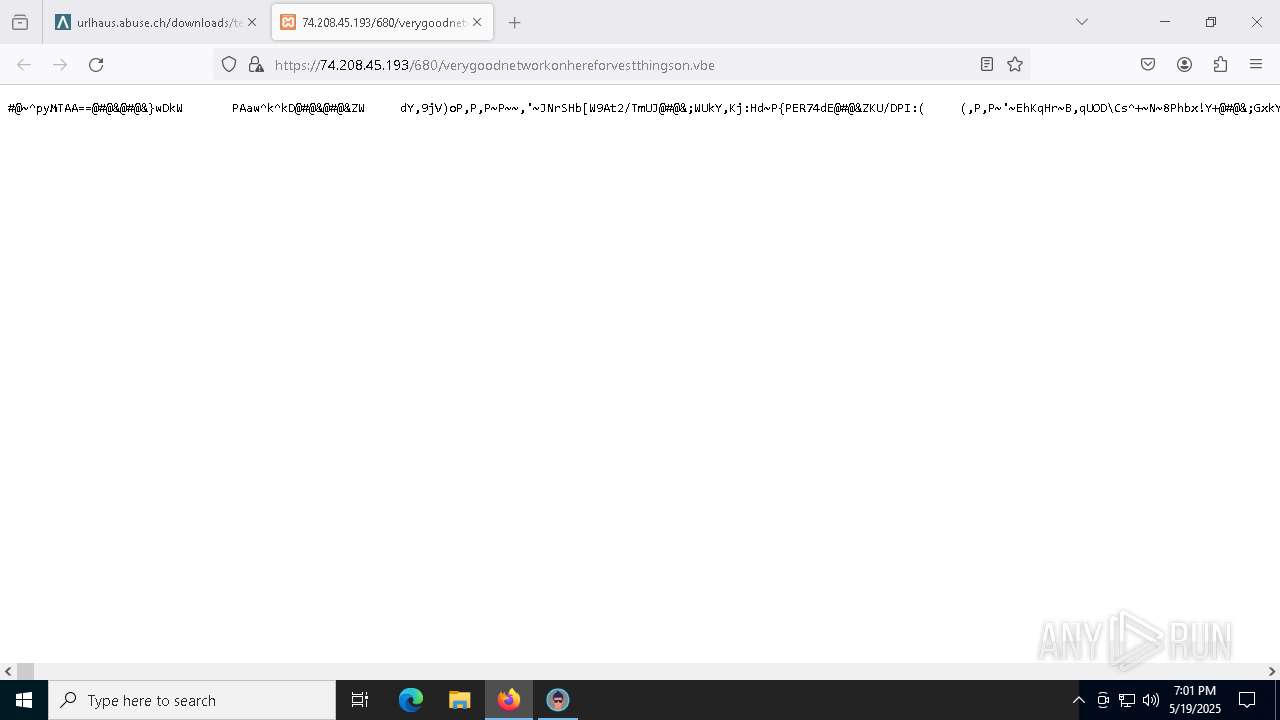
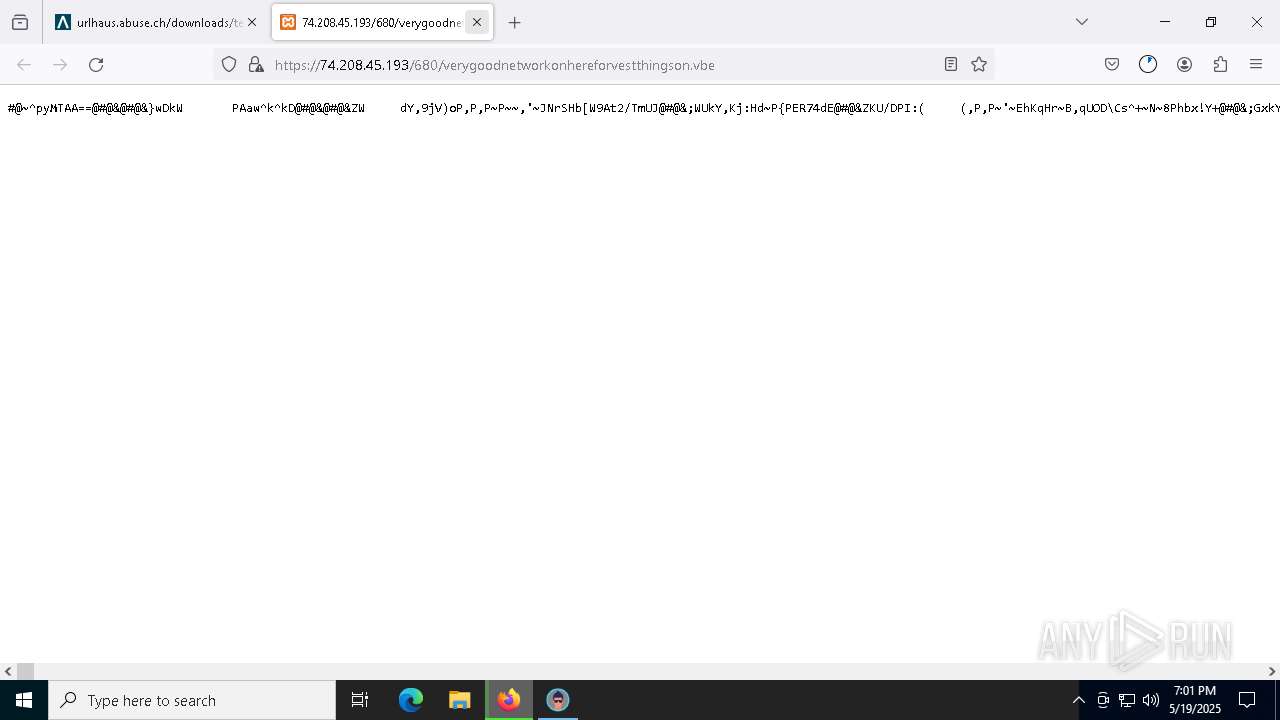
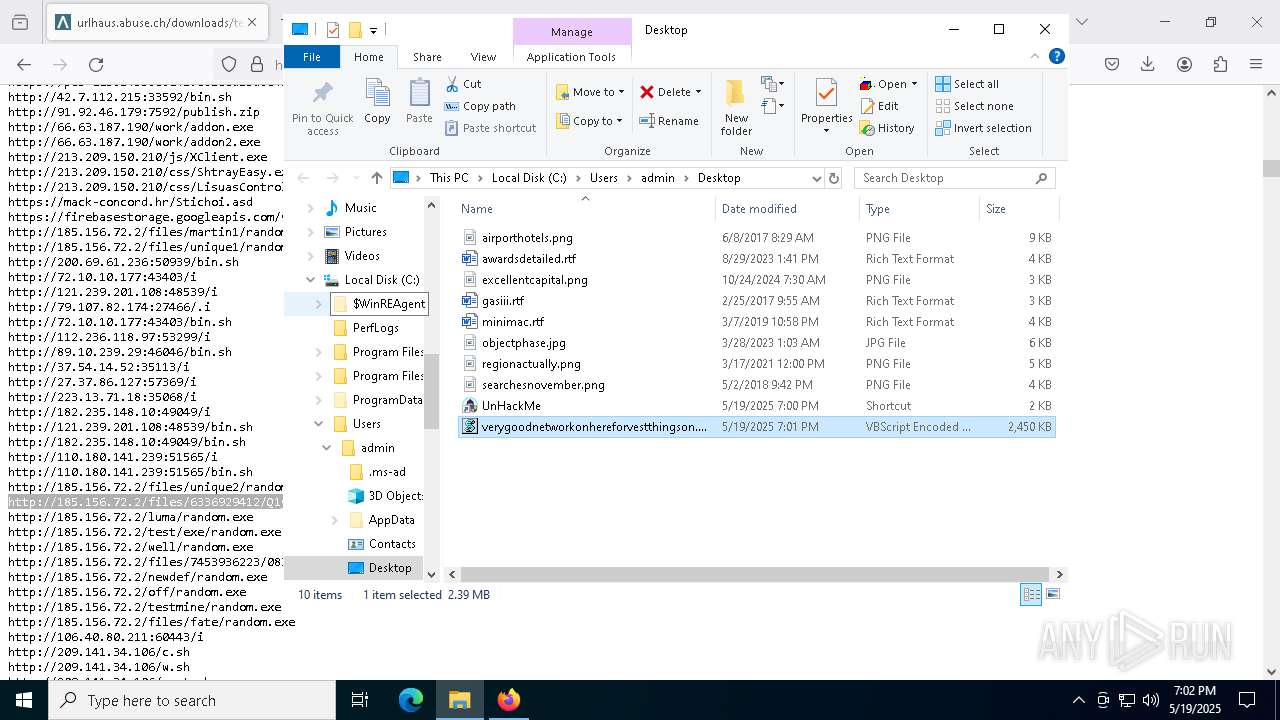
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7144)
Run PowerShell with an invisible window
- powershell.exe (PID: 7144)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 7352)
REMCOS has been detected (YARA)
- MSBuild.exe (PID: 2552)
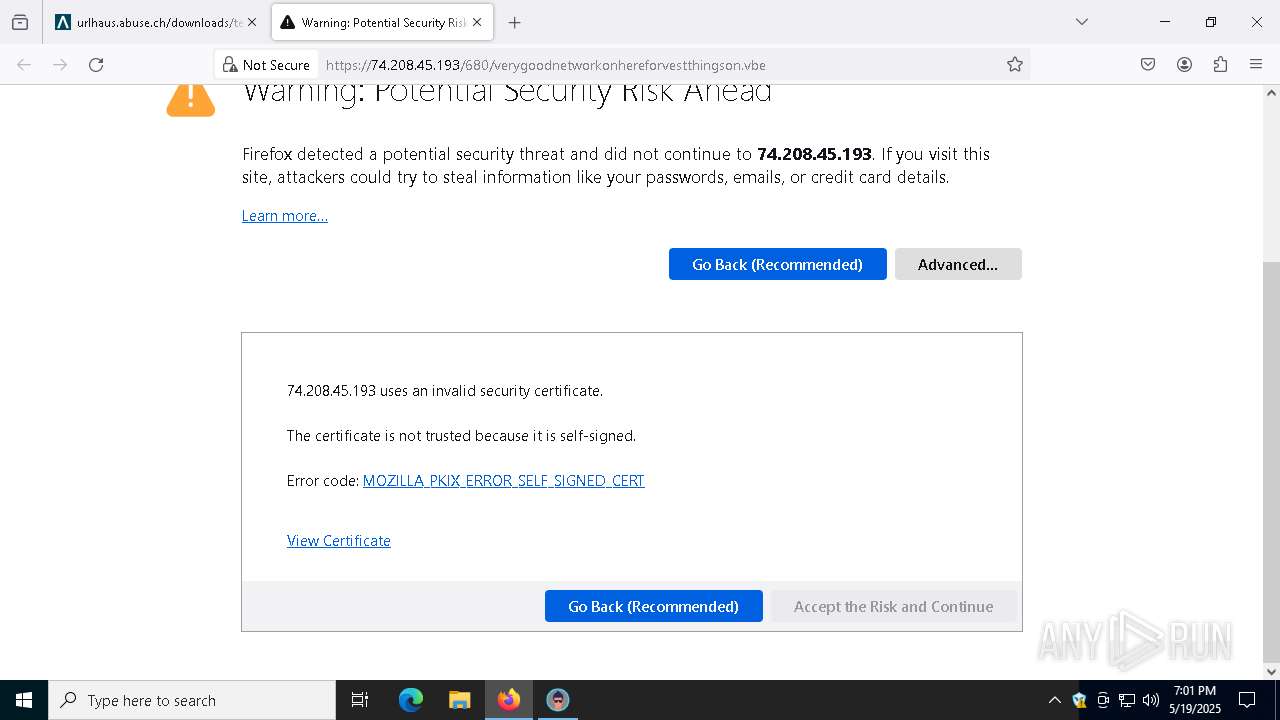
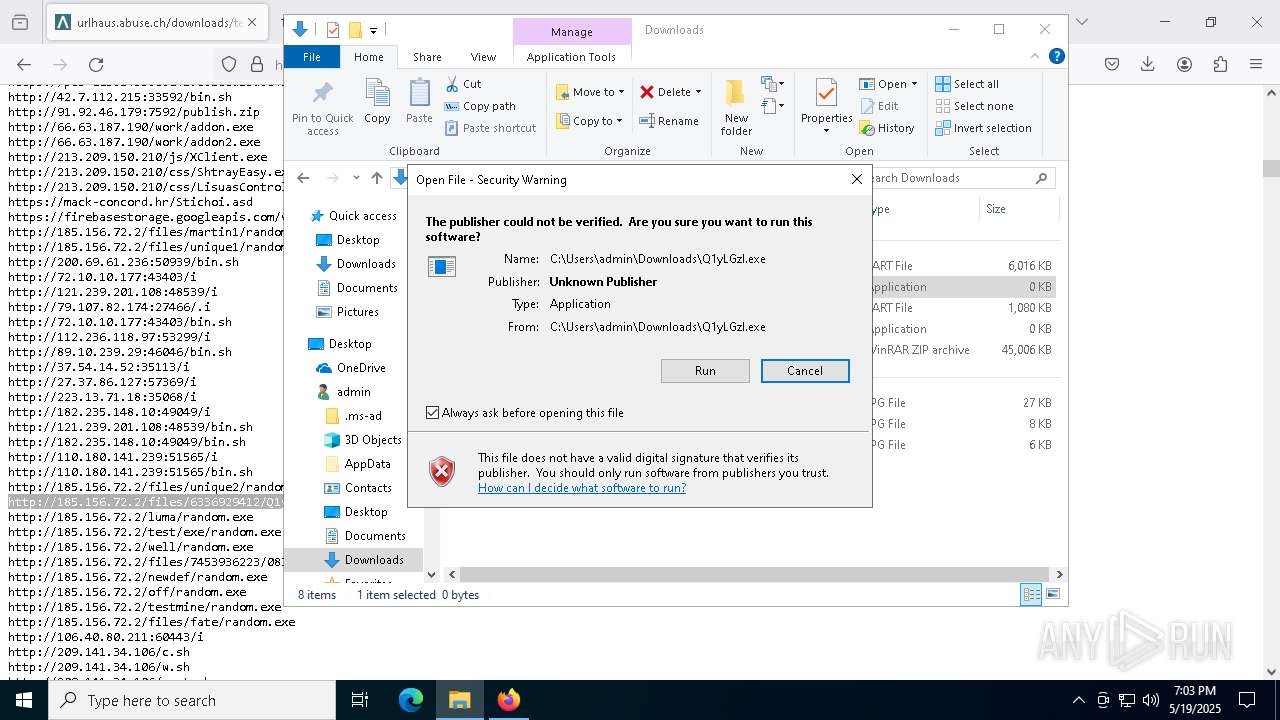
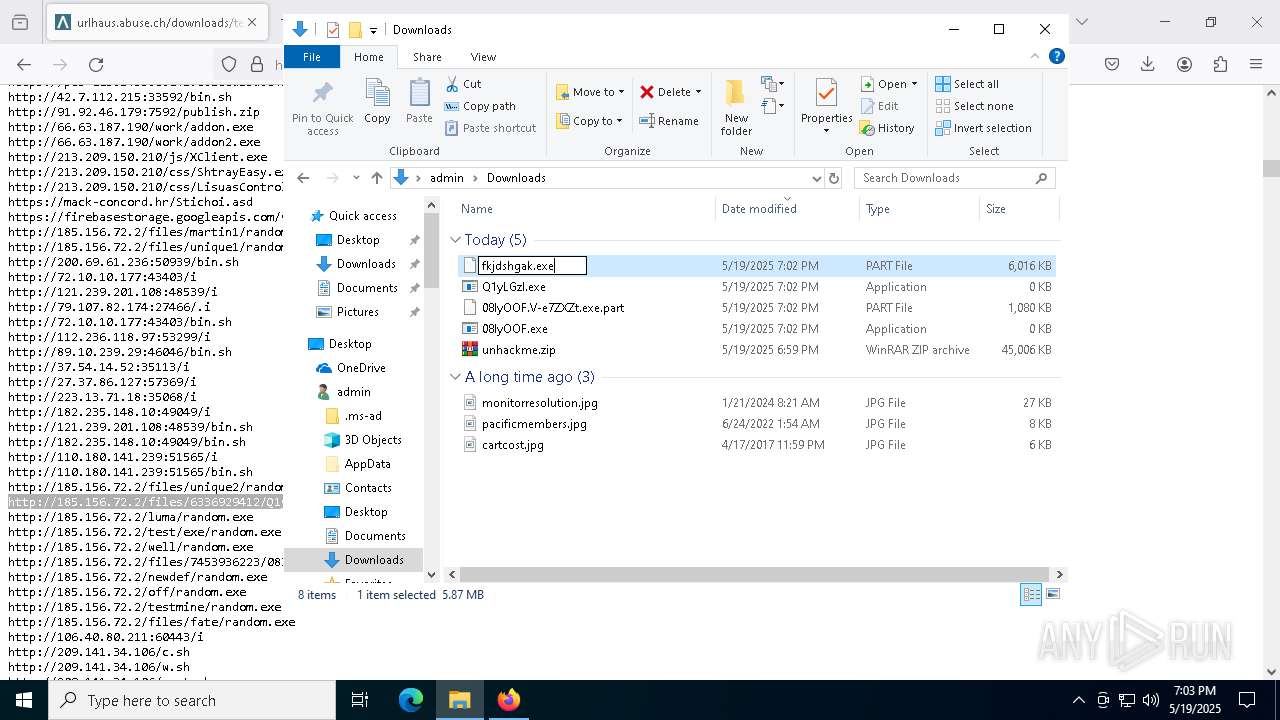
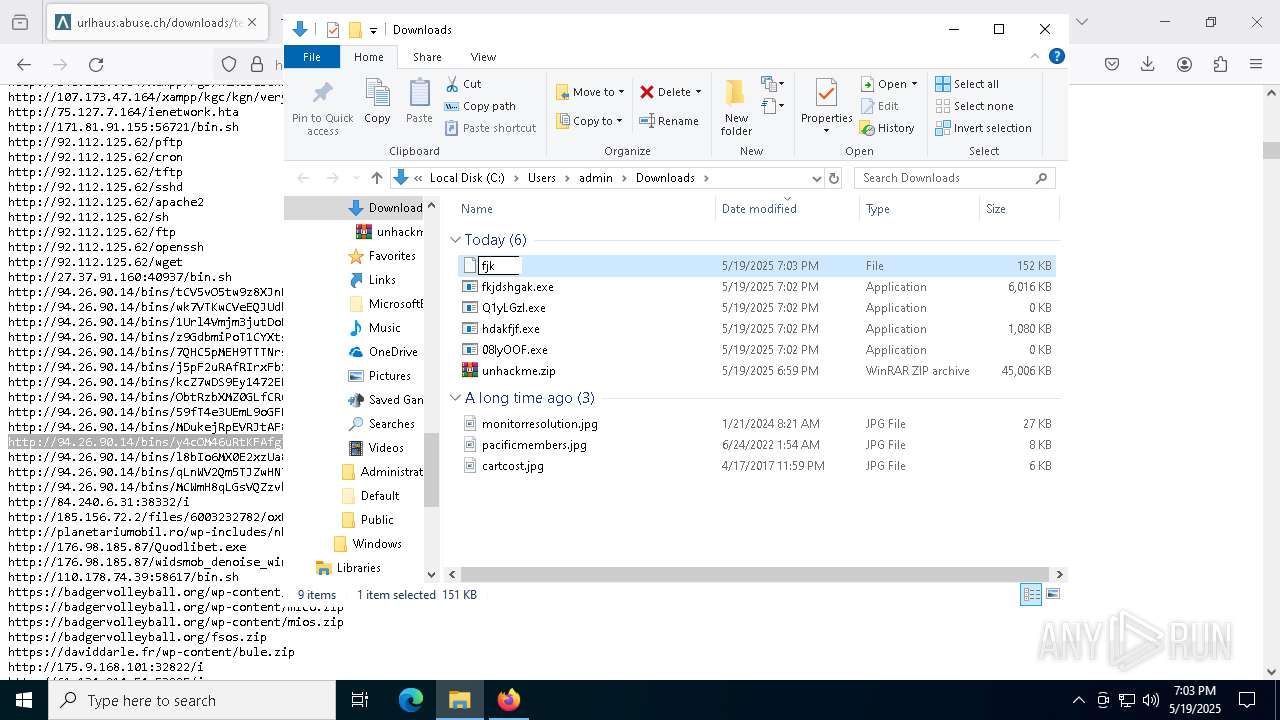
Executing a file with an untrusted certificate
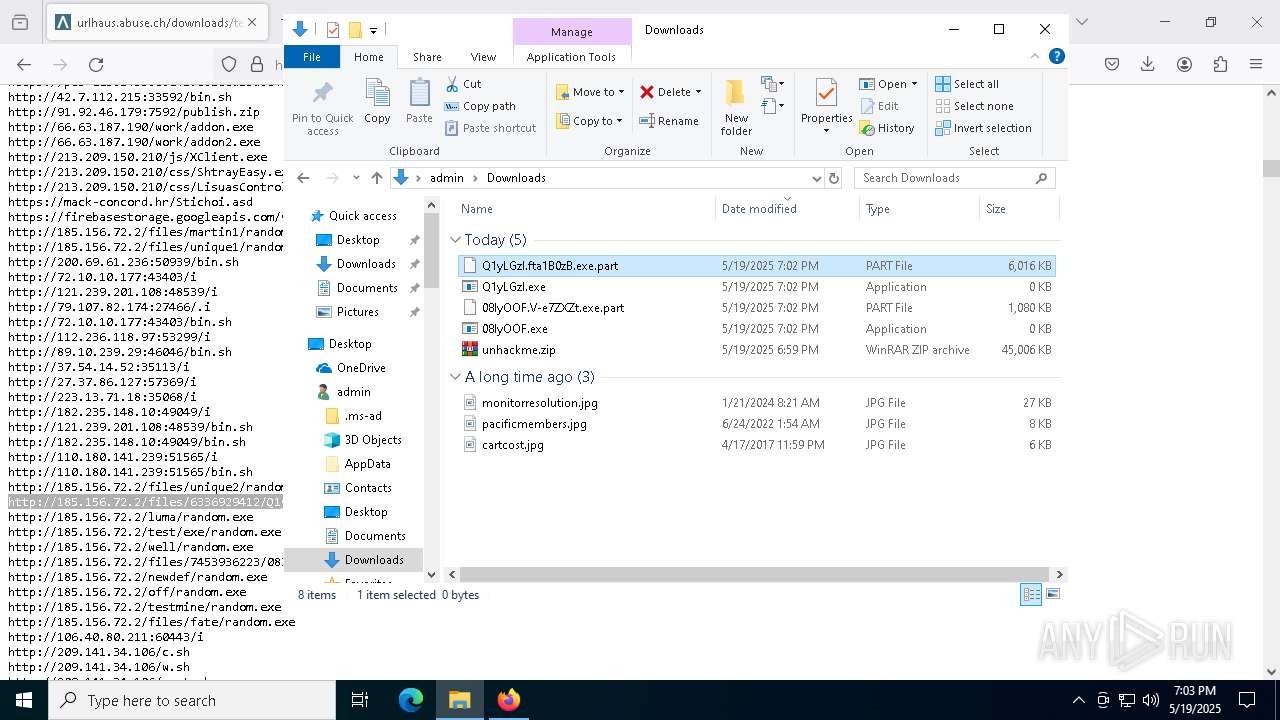
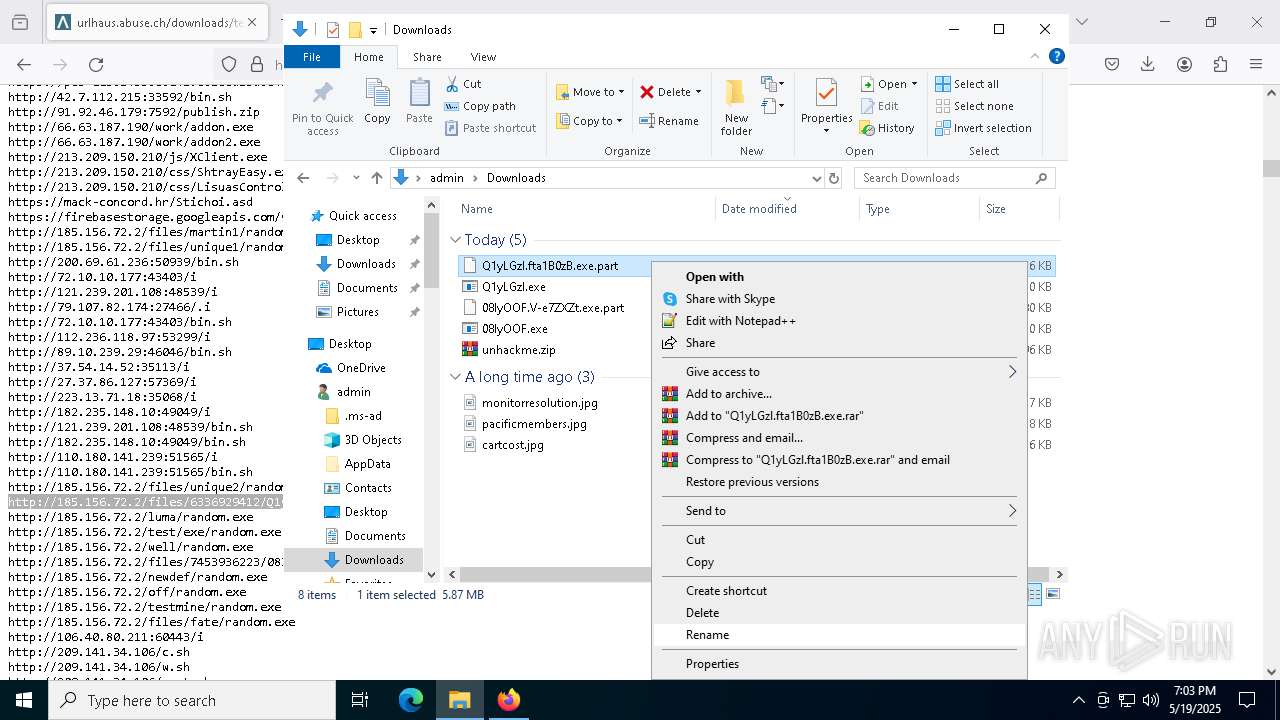
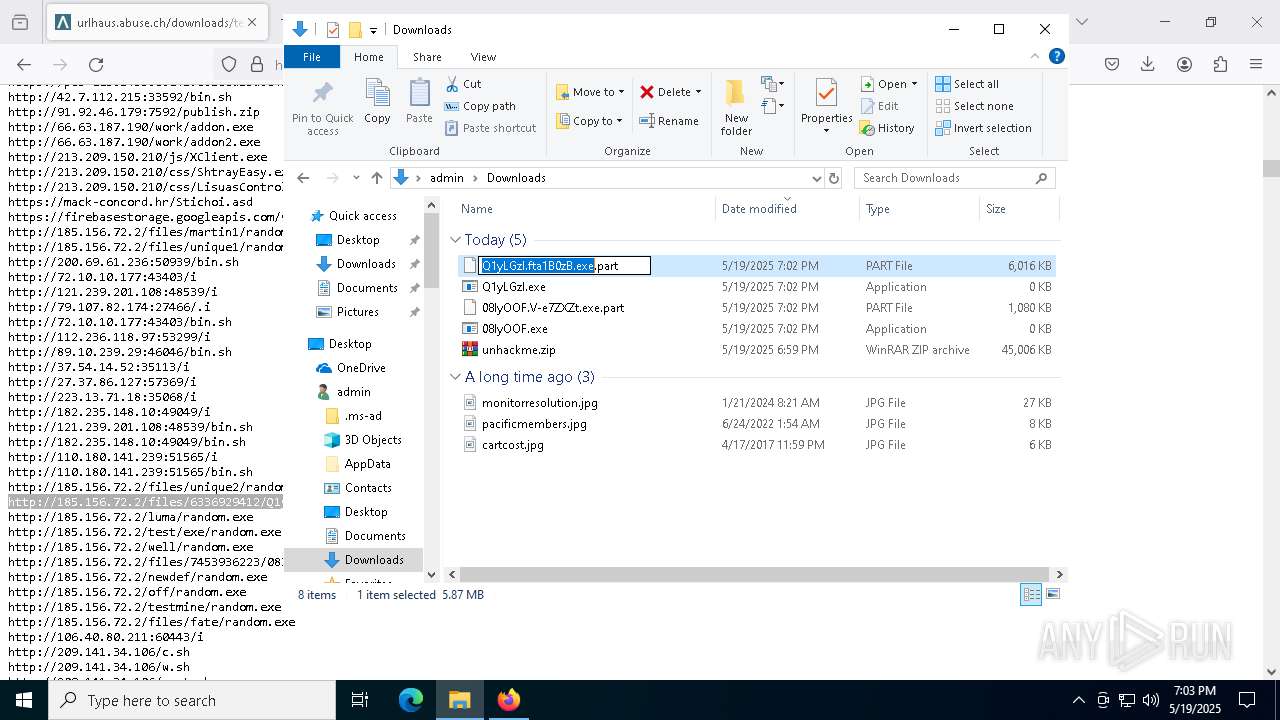
- fkjdshgak.exe (PID: 5280)
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- fkjdshgak.exe (PID: 5280)
GHOSTSOCKS has been found (auto)
- firefox.exe (PID: 8764)
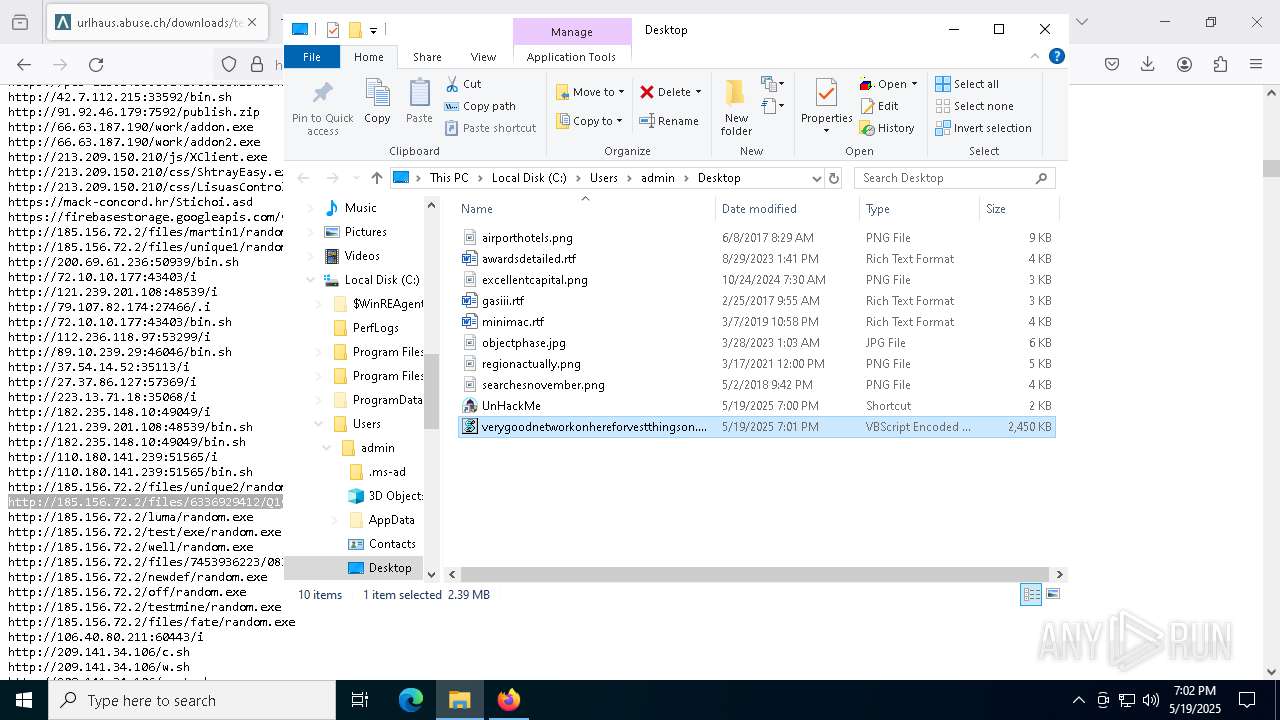
SUSPICIOUS
Reads security settings of Internet Explorer
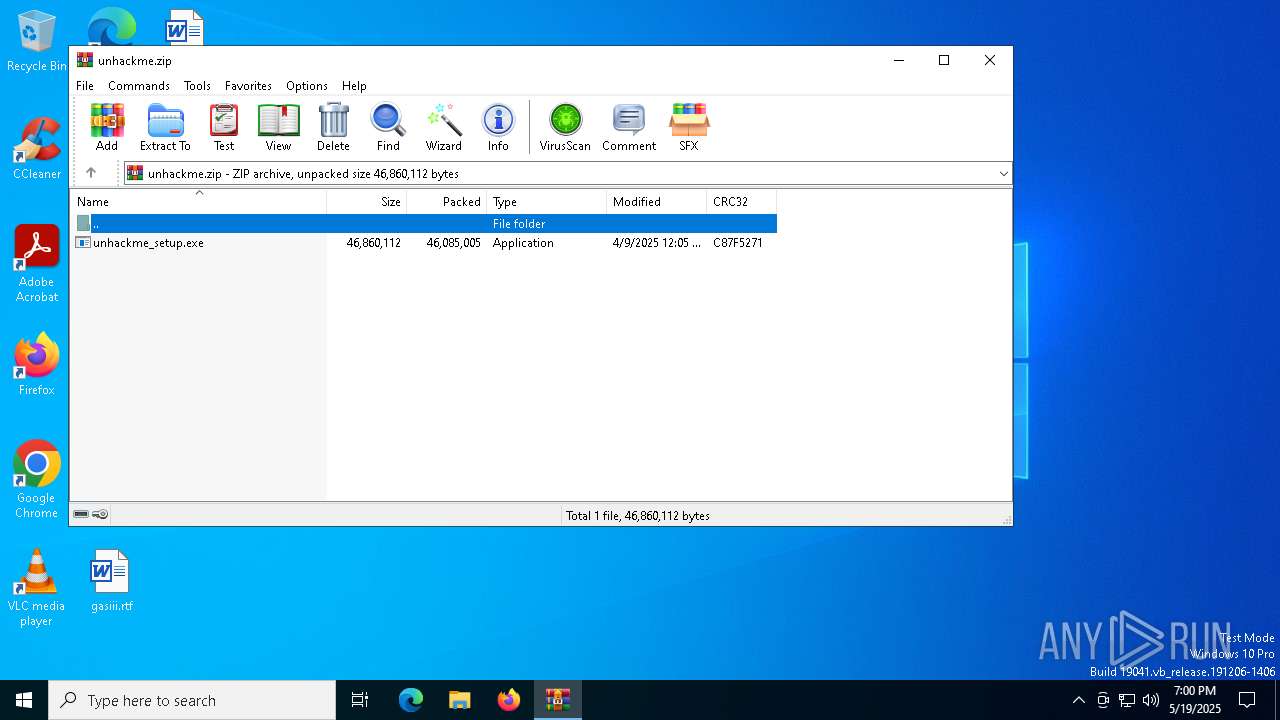
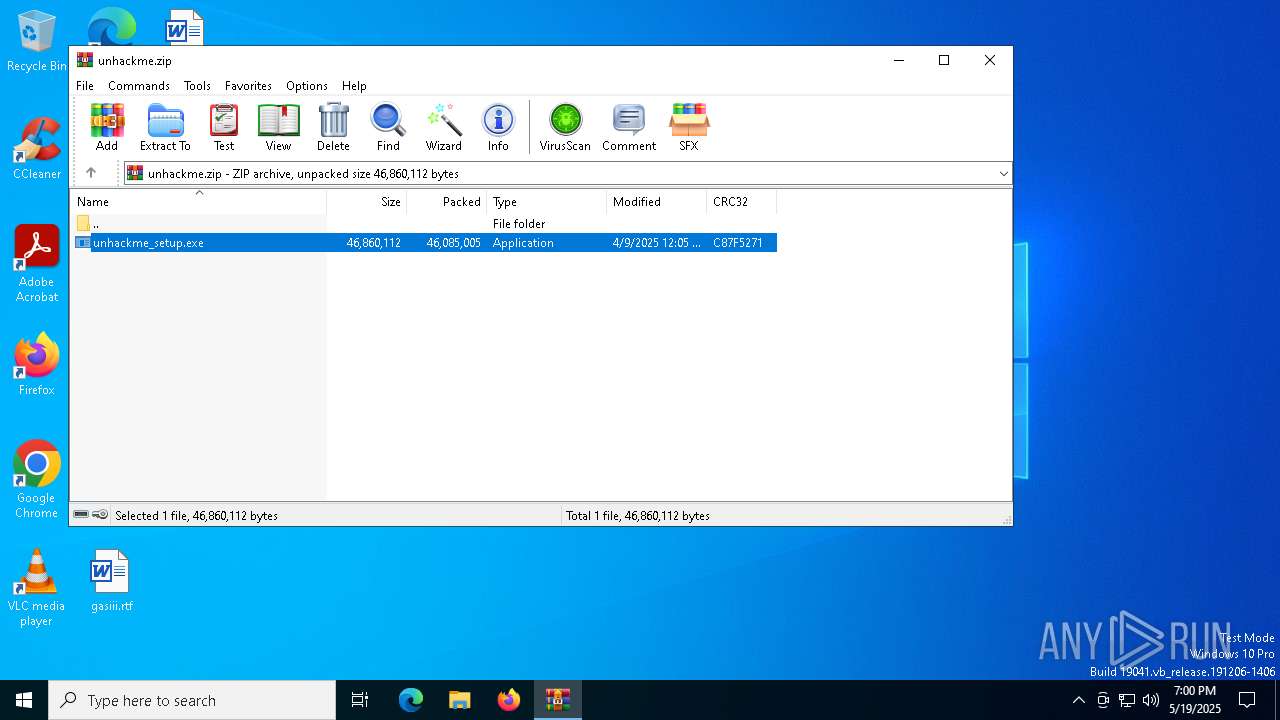
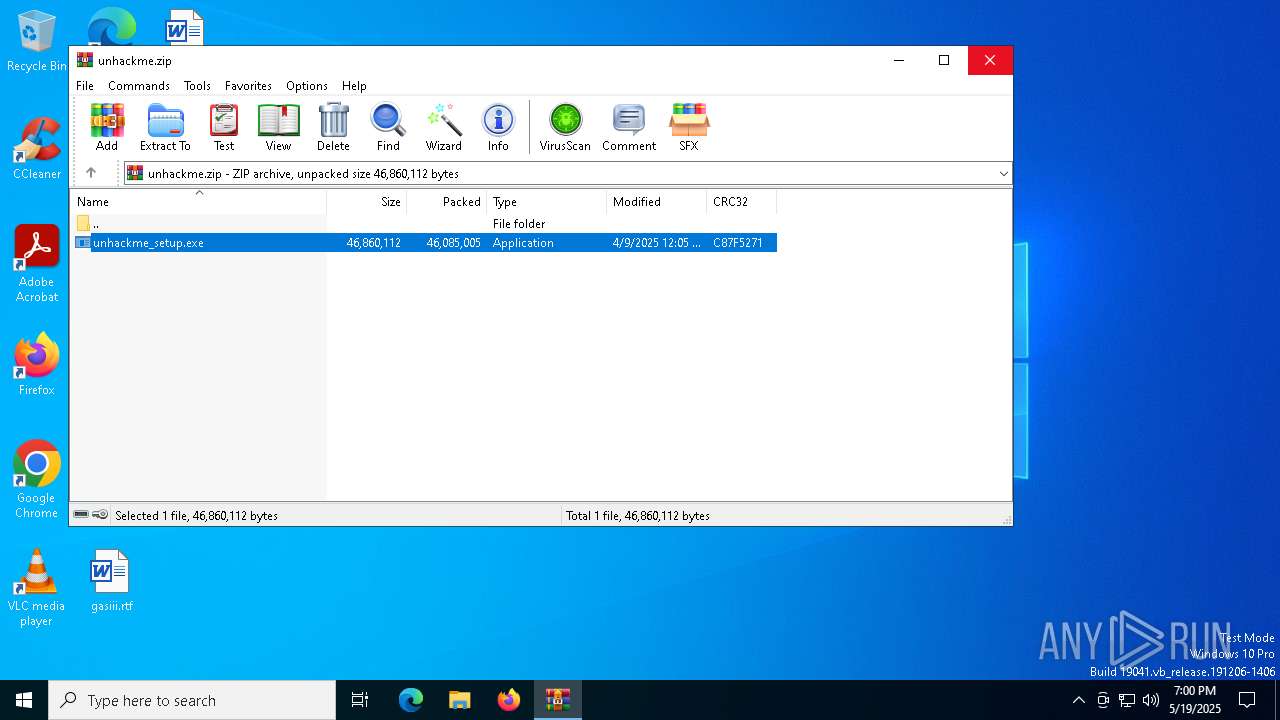
- WinRAR.exe (PID: 8908)
- unhackme_setup.tmp (PID: 9084)
- RegRunInfo.exe (PID: 8460)
Checks for external IP
- svchost.exe (PID: 2196)
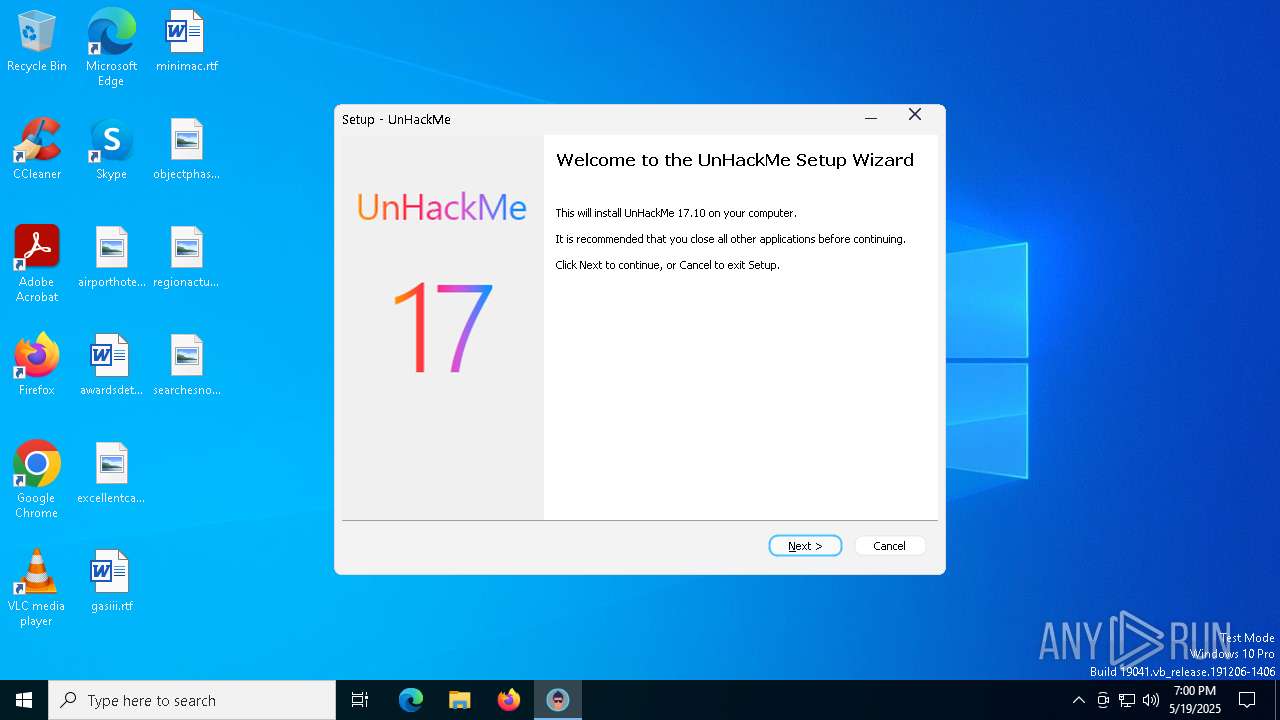
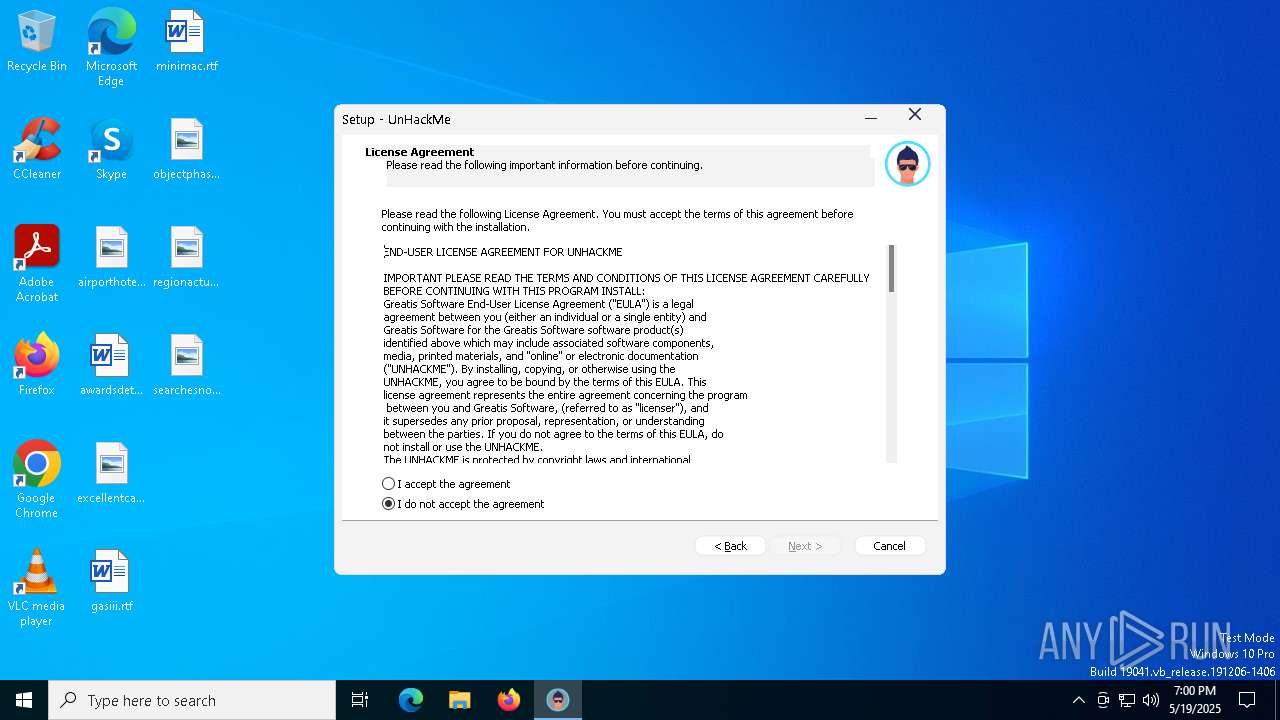
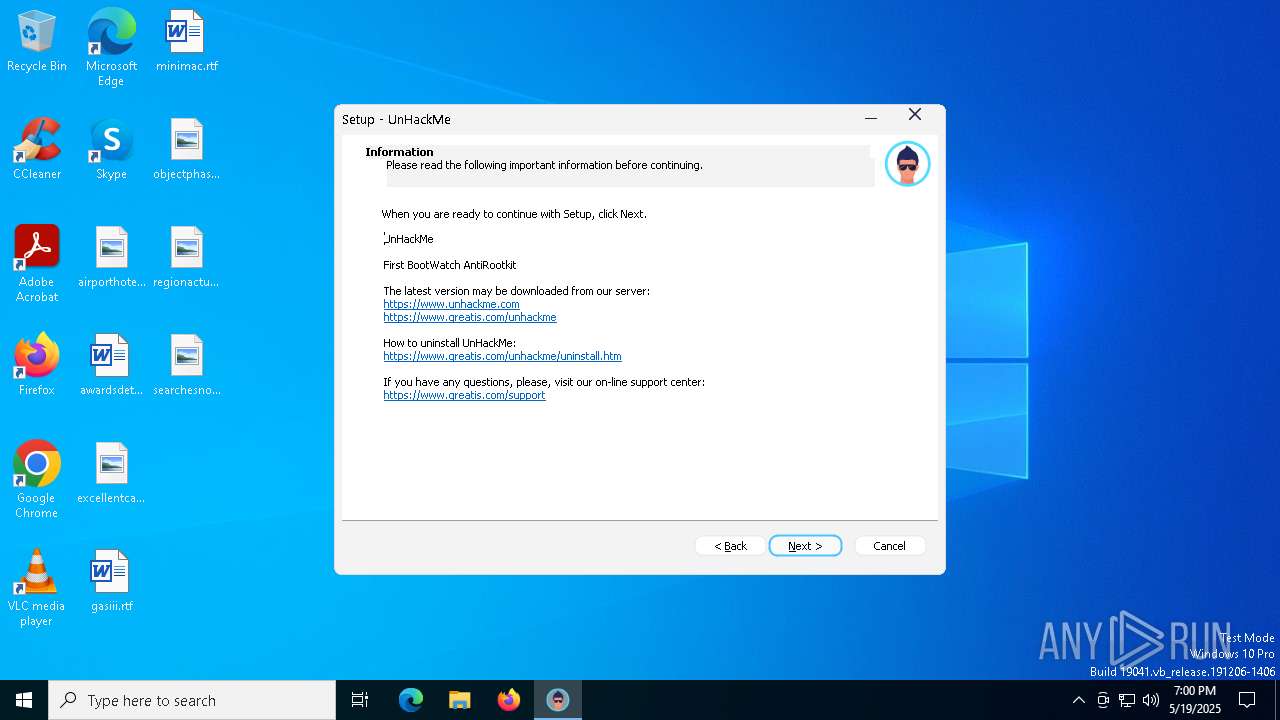
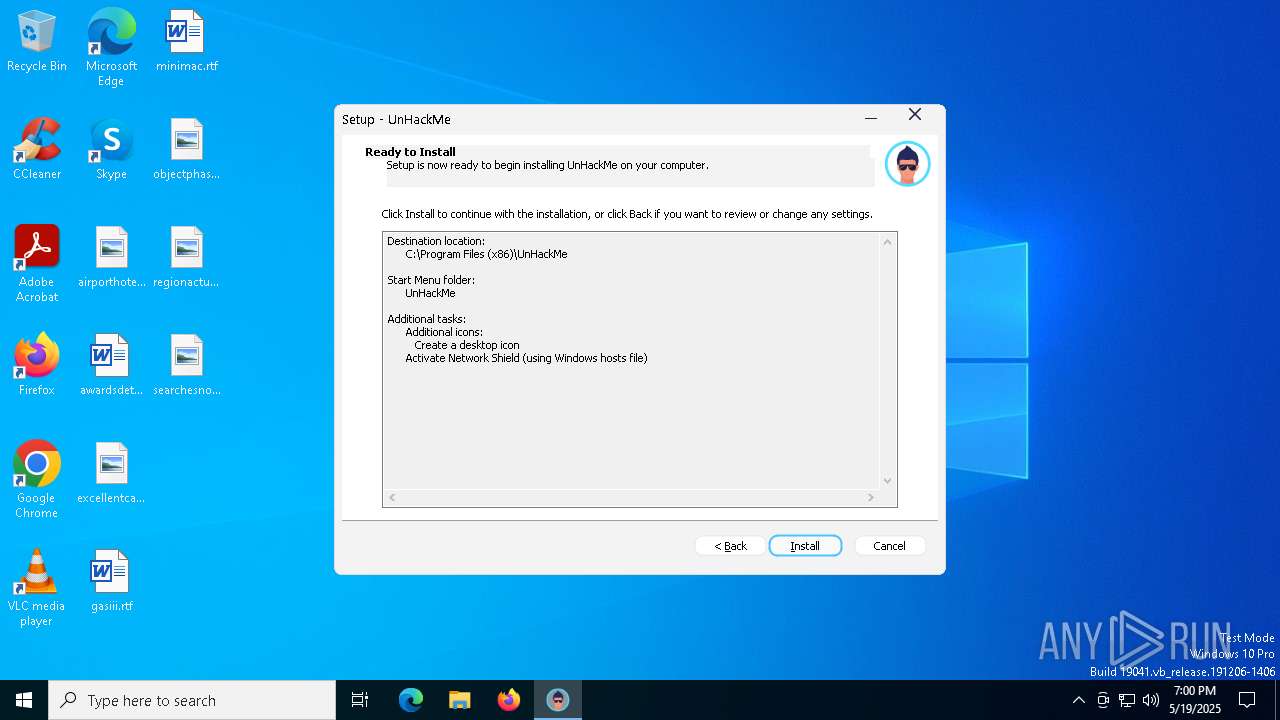
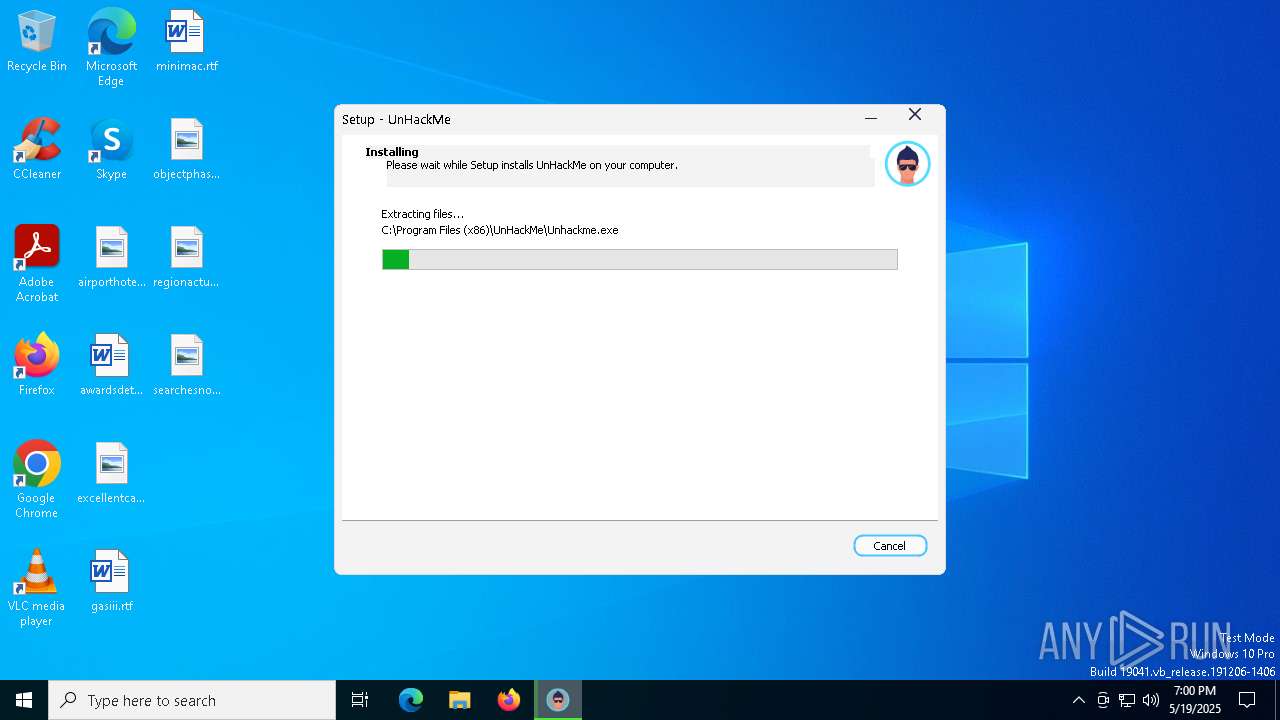
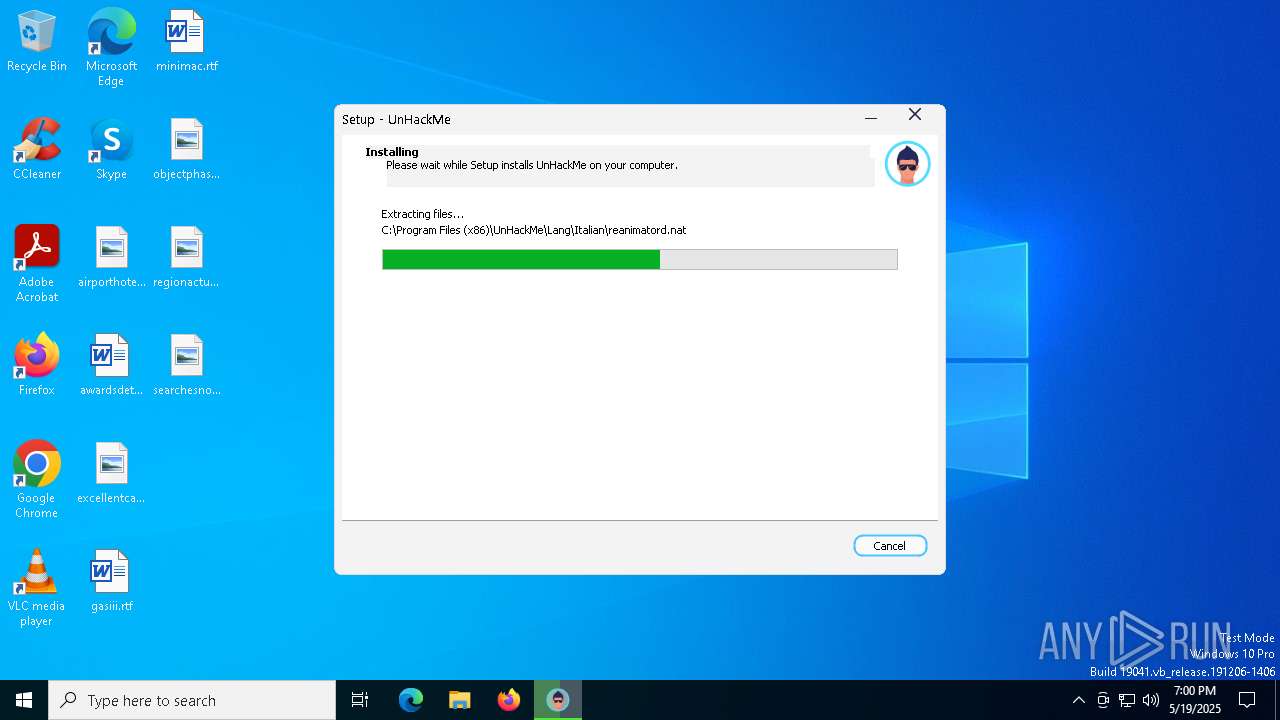
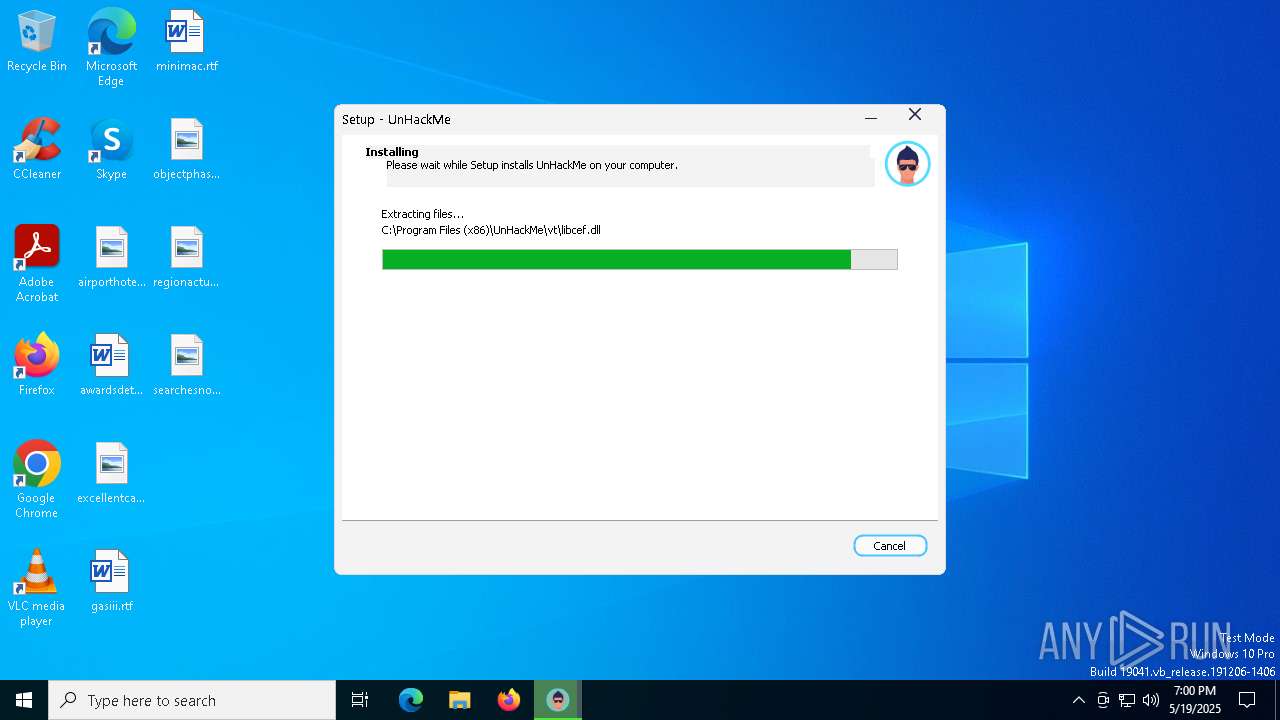
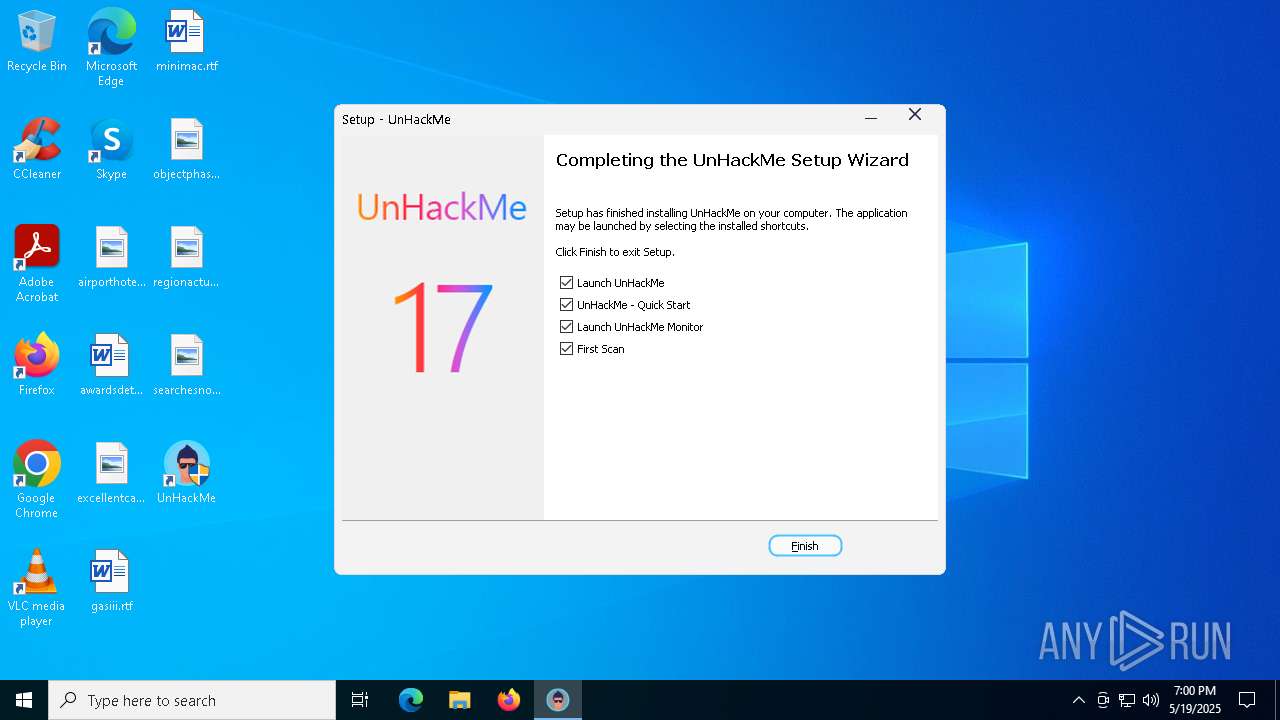
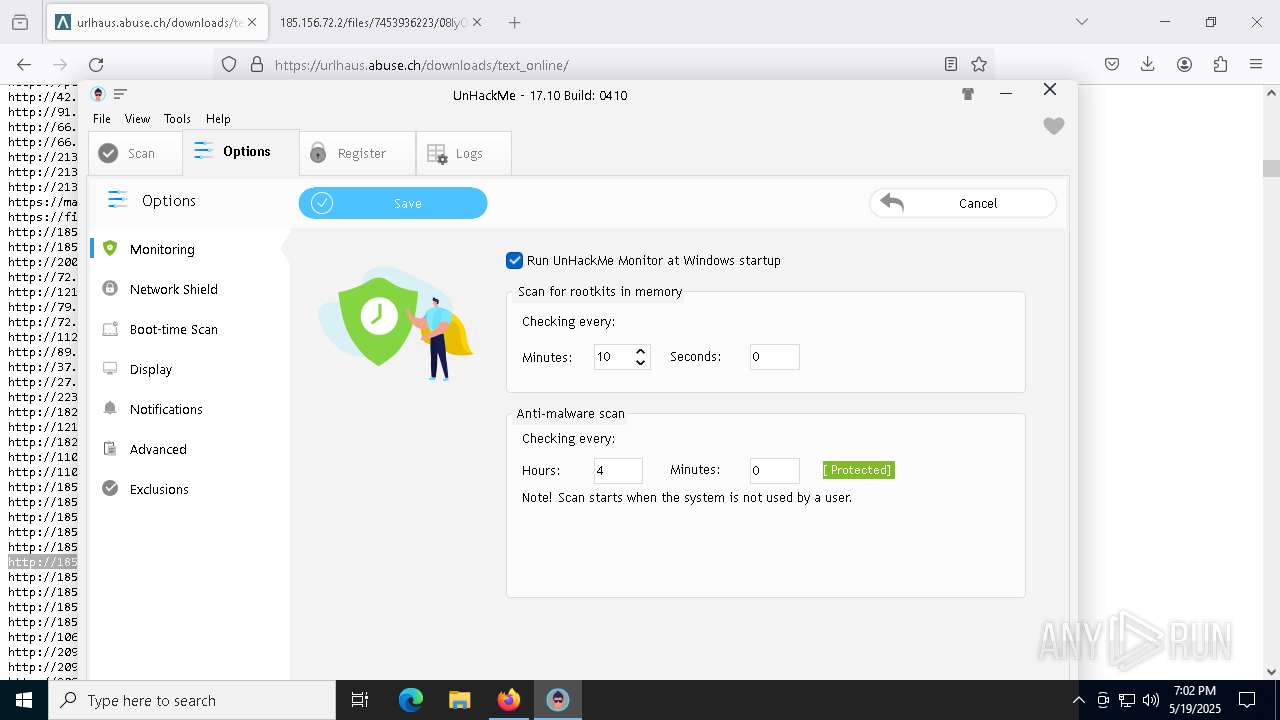
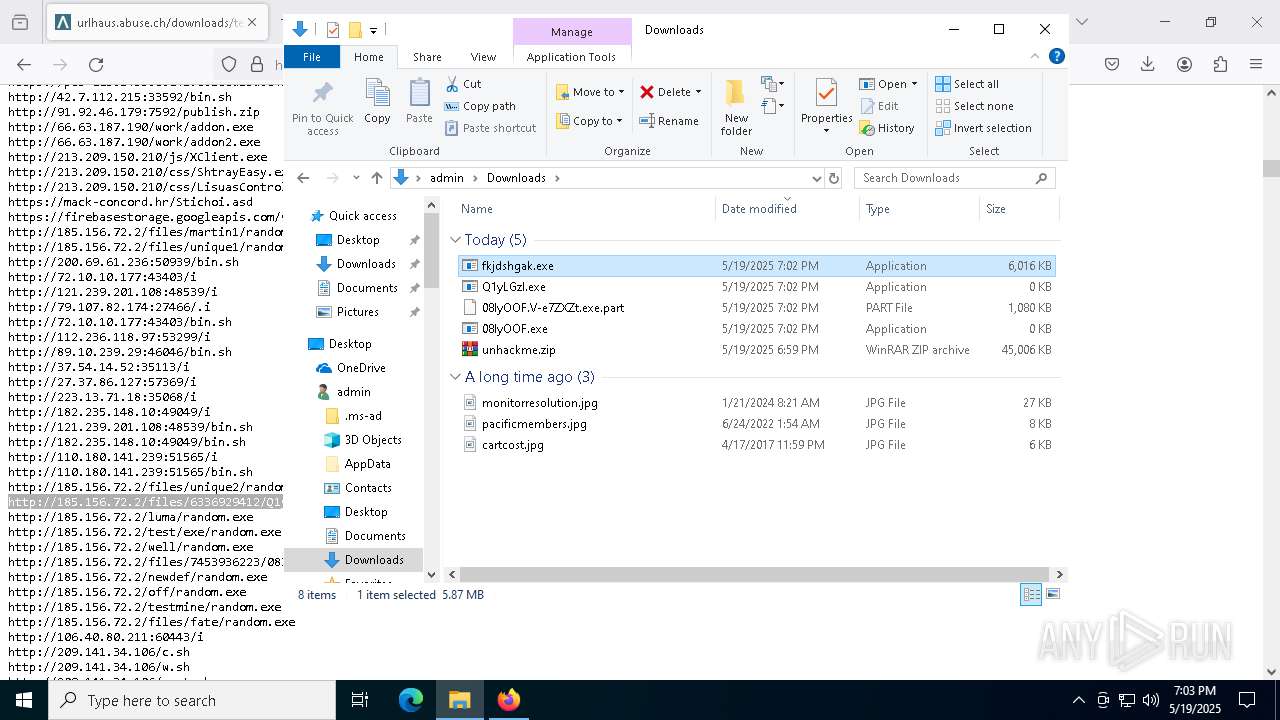
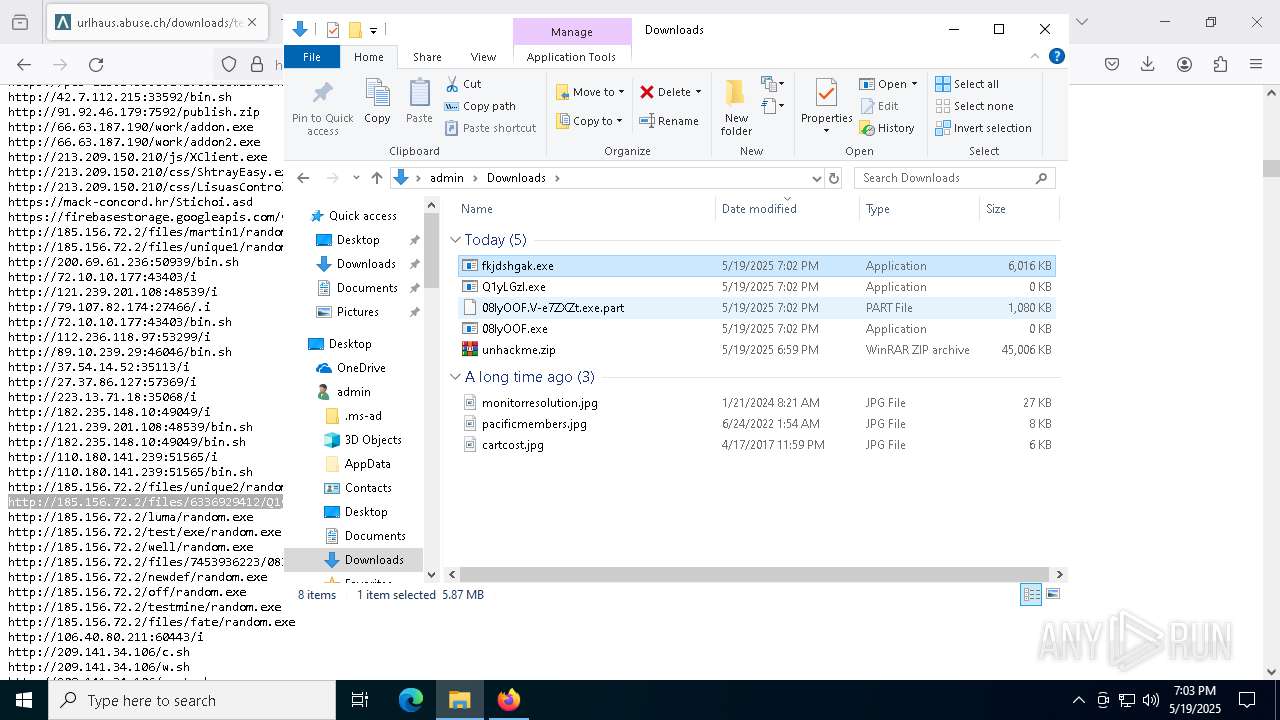
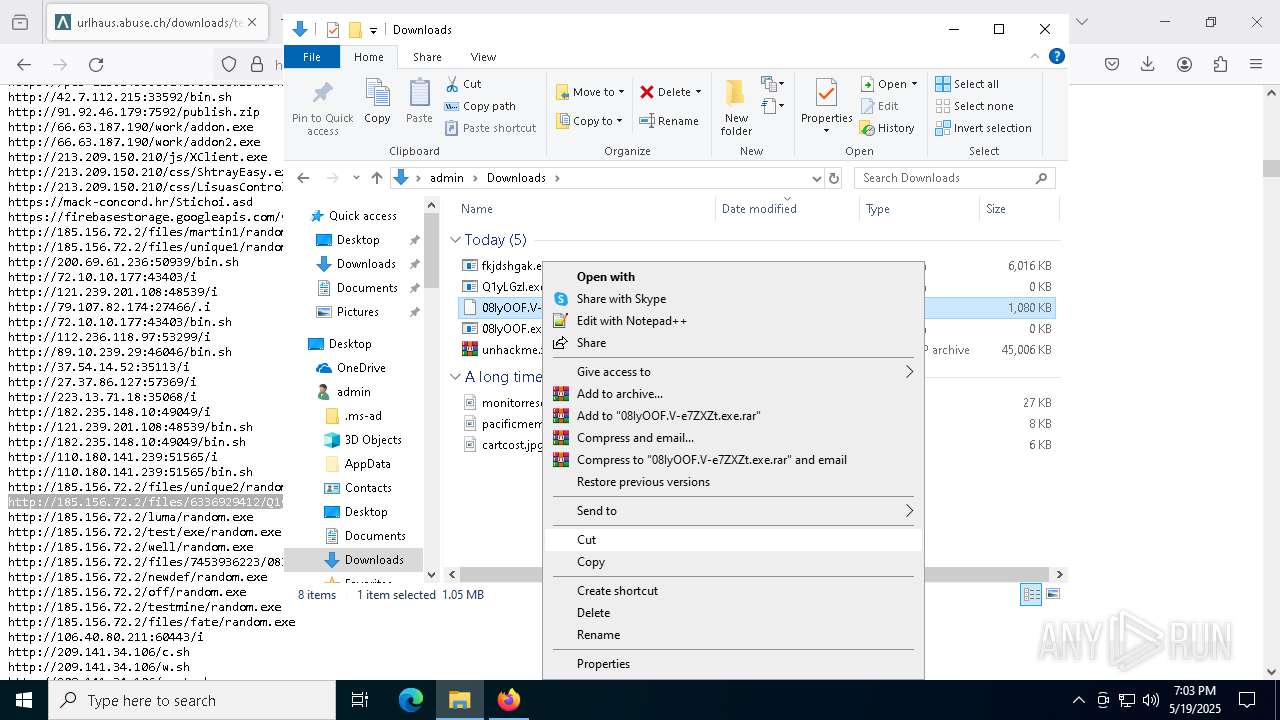
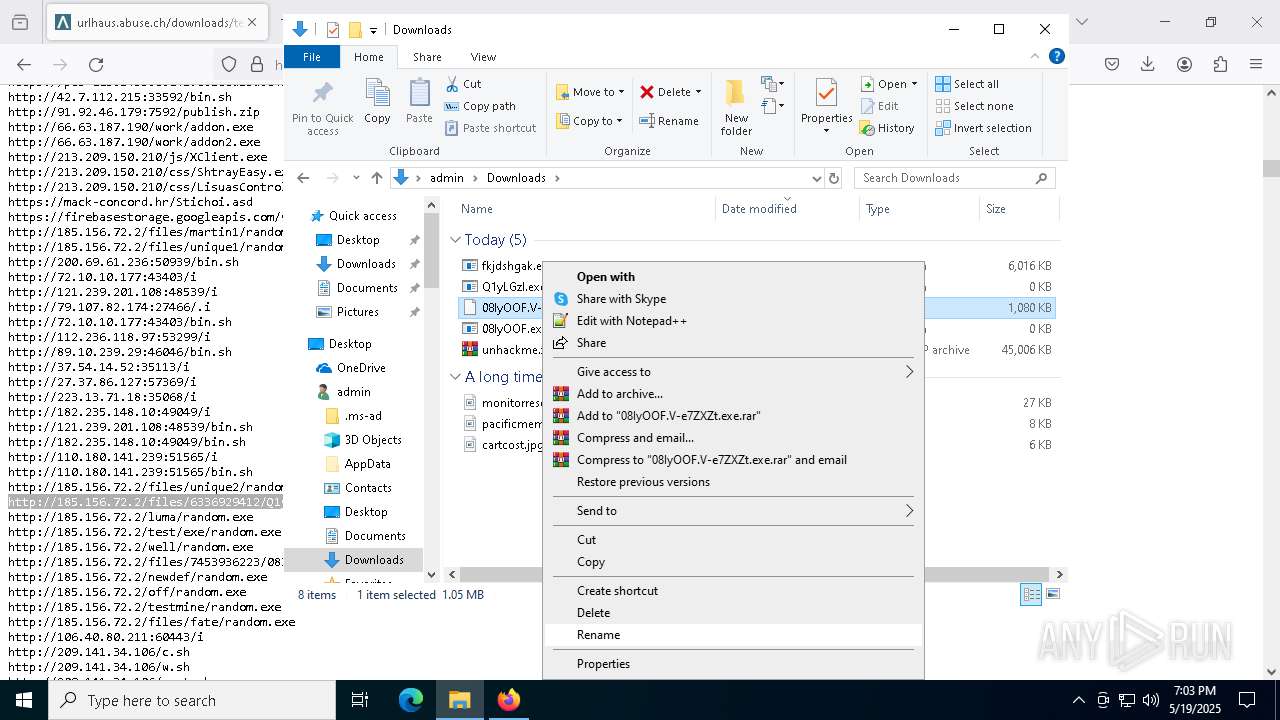
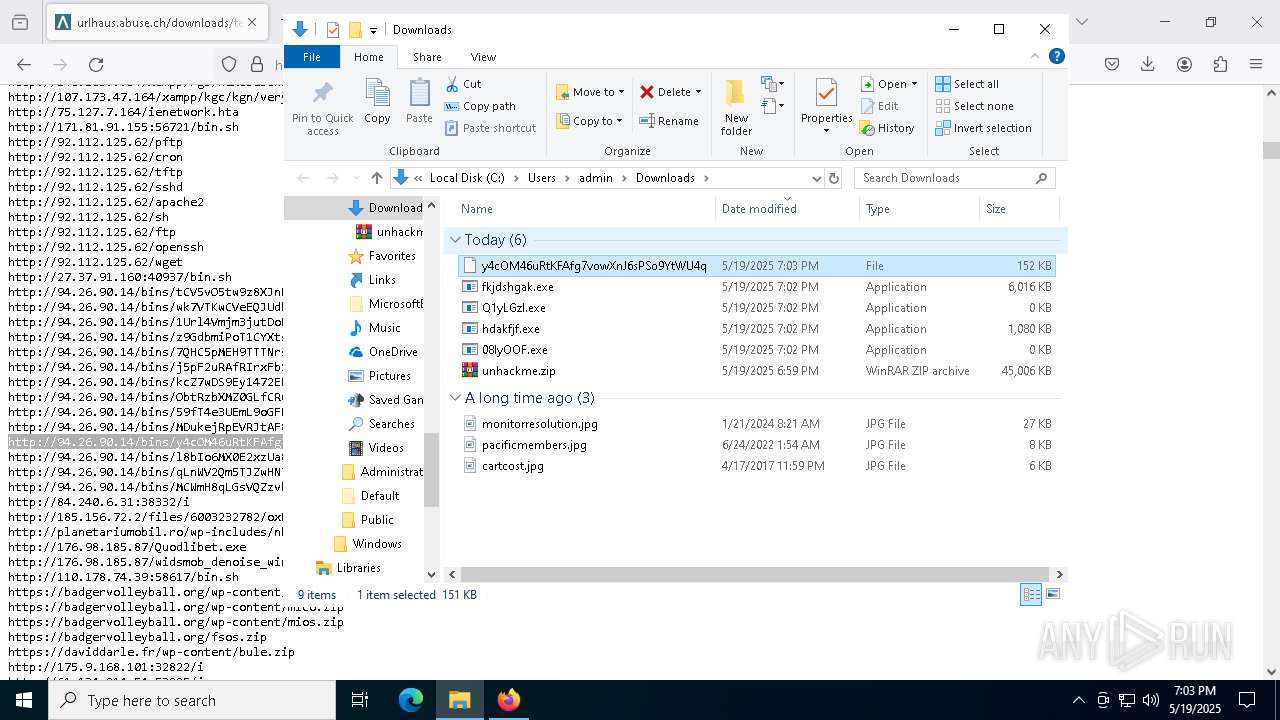
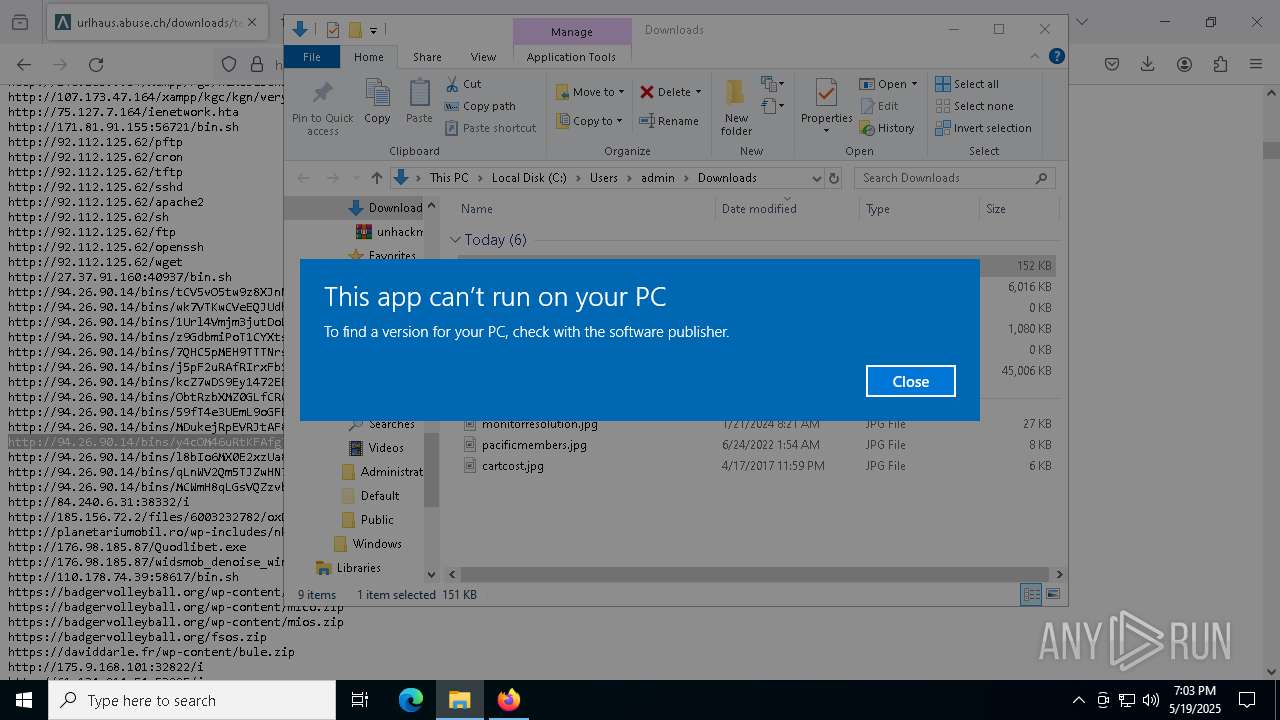
Executable content was dropped or overwritten
- unhackme_setup.exe (PID: 9060)
- unhackme_setup.exe (PID: 9168)
- unhackme_setup.tmp (PID: 9192)
Uses TASKKILL.EXE to kill process
- unhackme_setup.tmp (PID: 9192)
Drops 7-zip archiver for unpacking
- unhackme_setup.tmp (PID: 9192)
Reads the Windows owner or organization settings
- unhackme_setup.tmp (PID: 9192)
Process drops legitimate windows executable
- unhackme_setup.tmp (PID: 9192)
Creates files in the driver directory
- unhackme_setup.tmp (PID: 9192)
Drops a system driver (possible attempt to evade defenses)
- unhackme_setup.tmp (PID: 9192)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7352)
The process executes via Task Scheduler
- wscript.exe (PID: 7476)
There is functionality for taking screenshot (YARA)
- MSBuild.exe (PID: 2552)
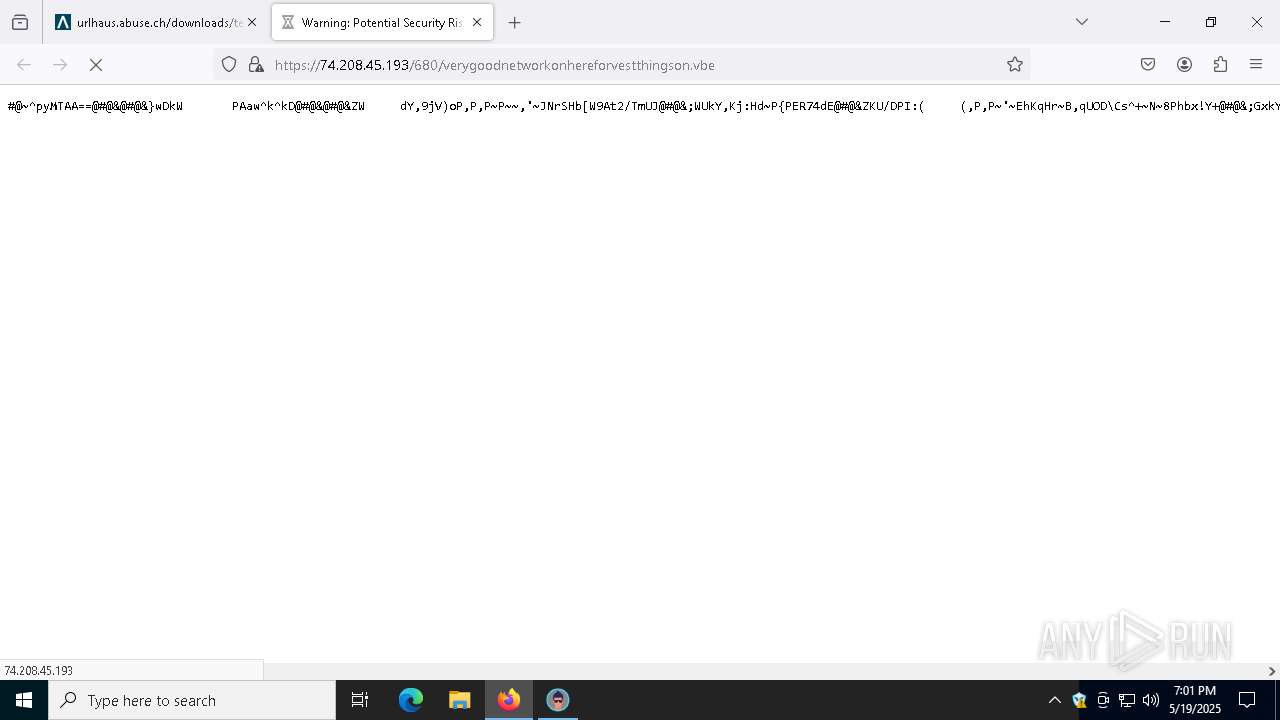
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 7352)
Connects to unusual port
- MSBuild.exe (PID: 2552)
Potential Corporate Privacy Violation
- firefox.exe (PID: 8764)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- fkjdshgak.exe (PID: 5280)
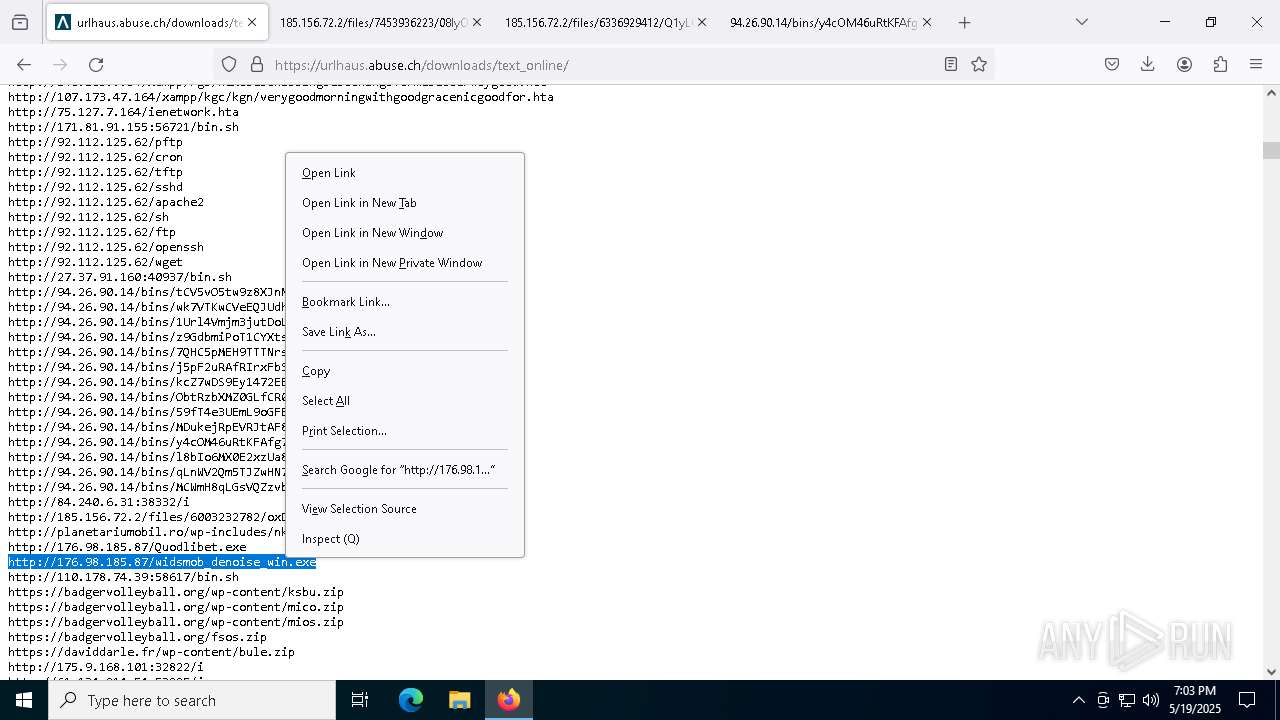
There is functionality for communication over UDP network (YARA)
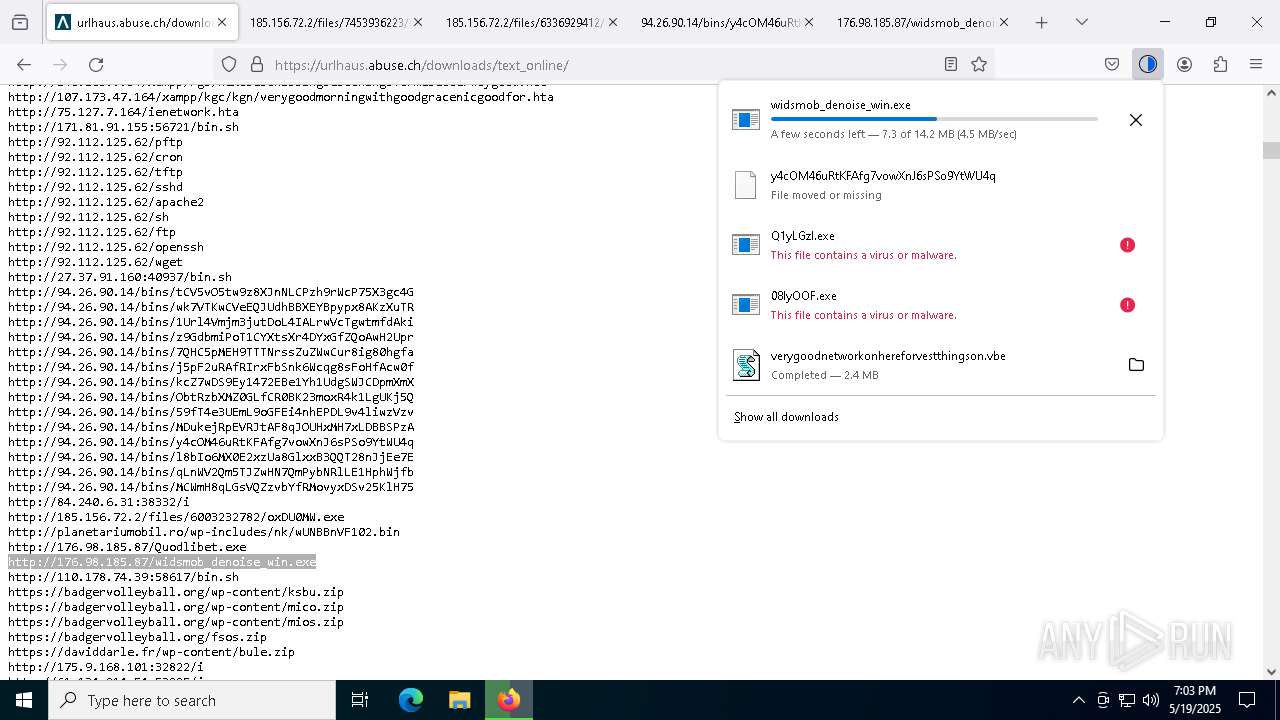
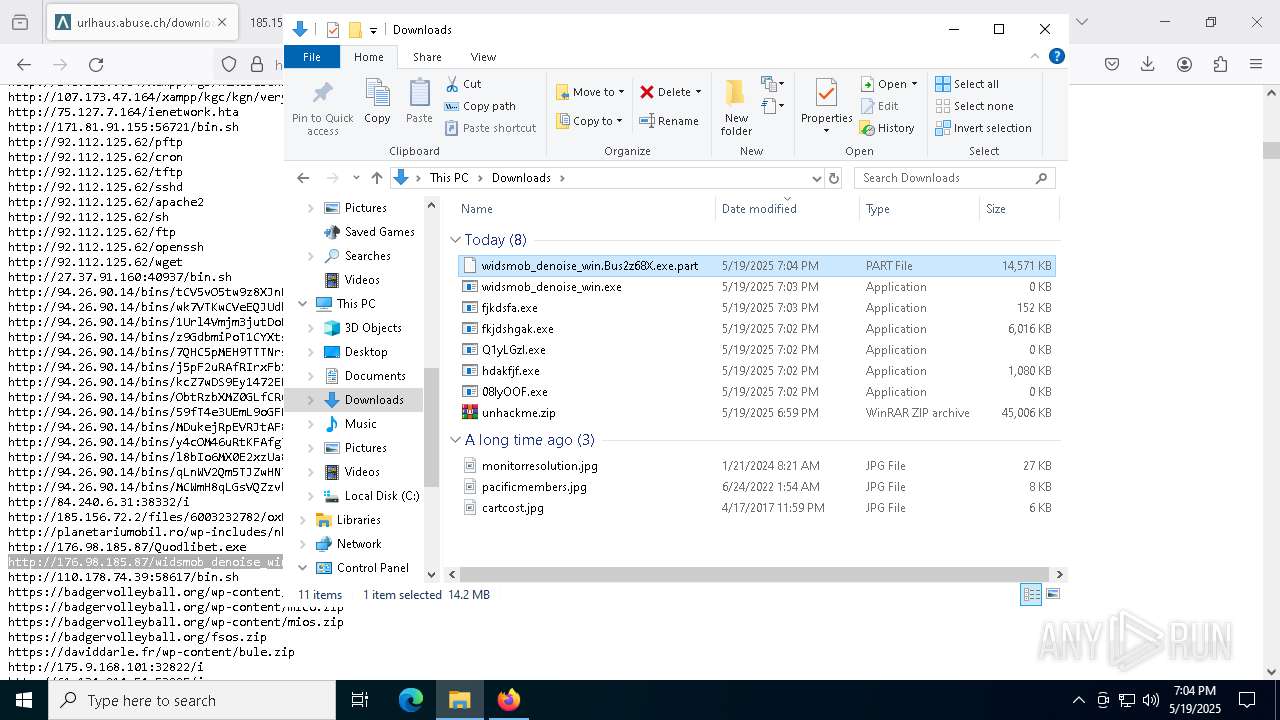
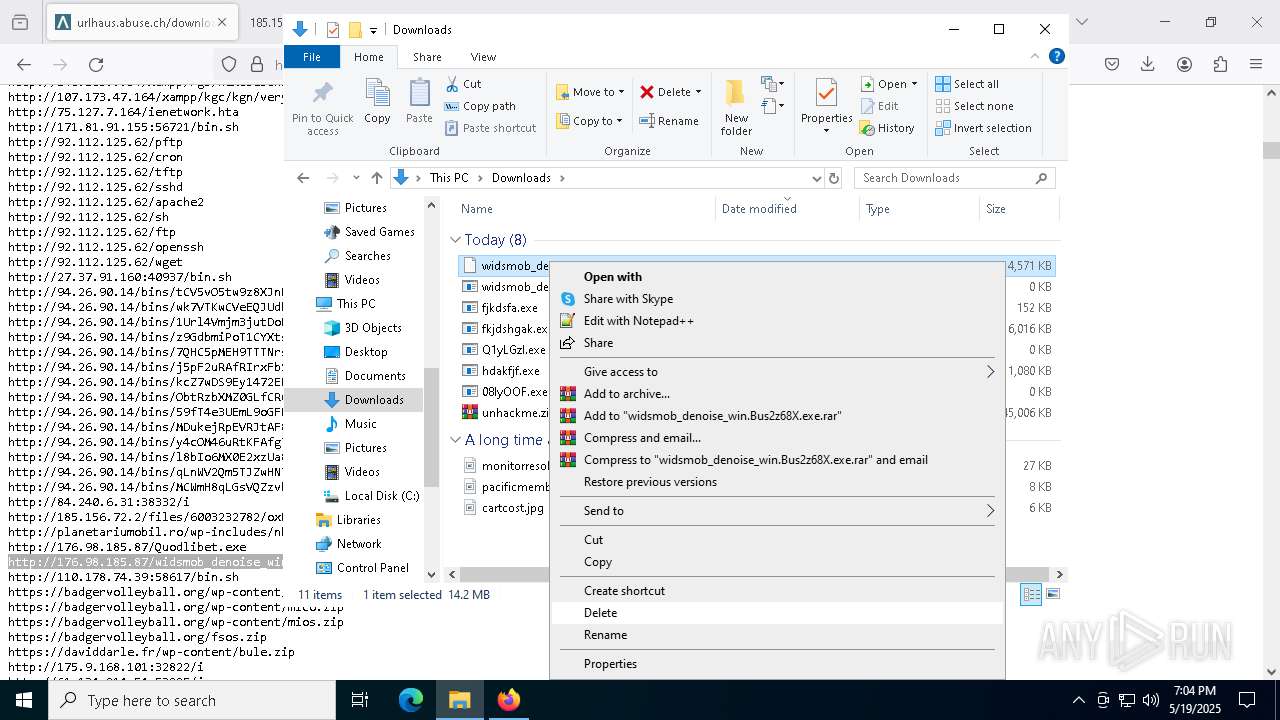
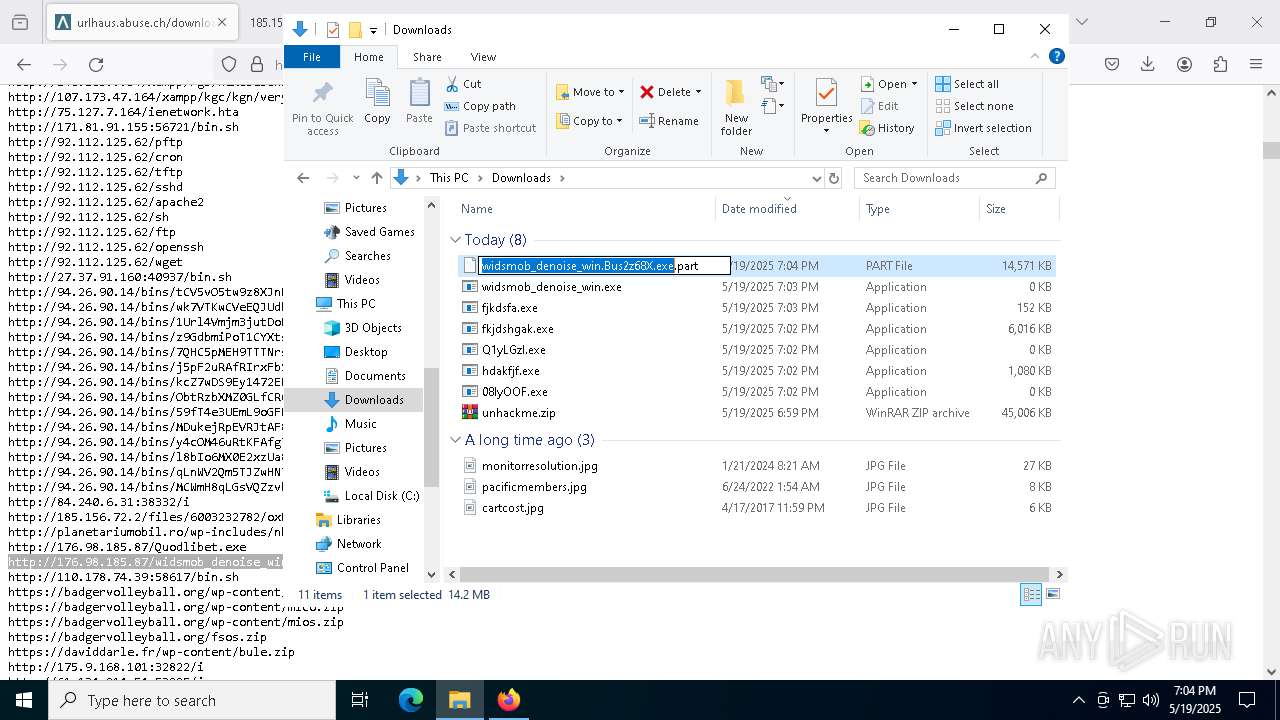
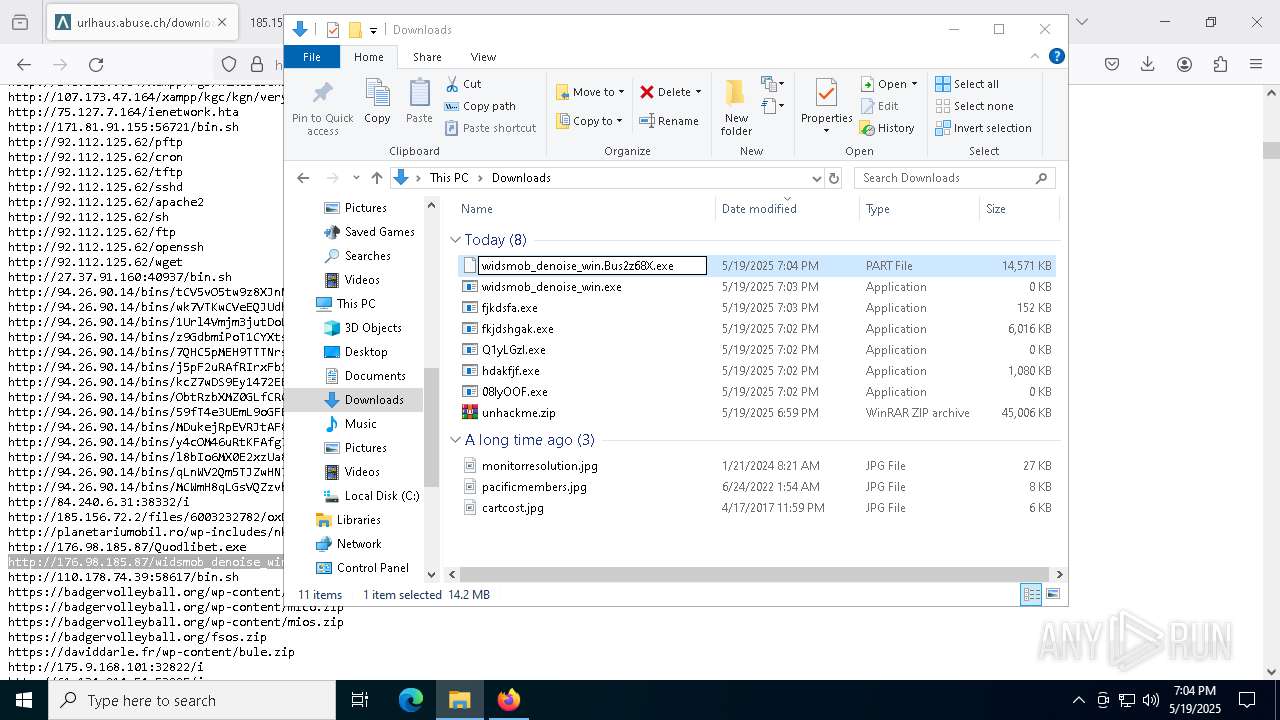
- widsmob_denoise_win.Bus2z68X.exe (PID: 7000)
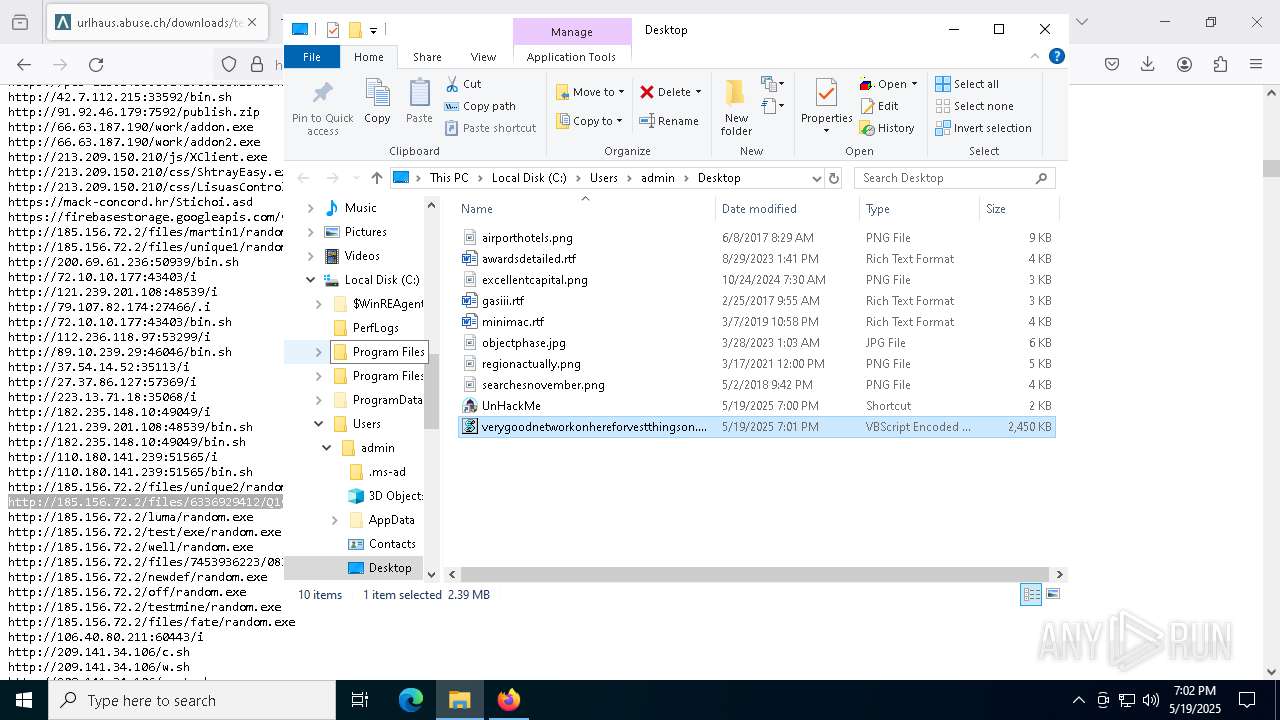
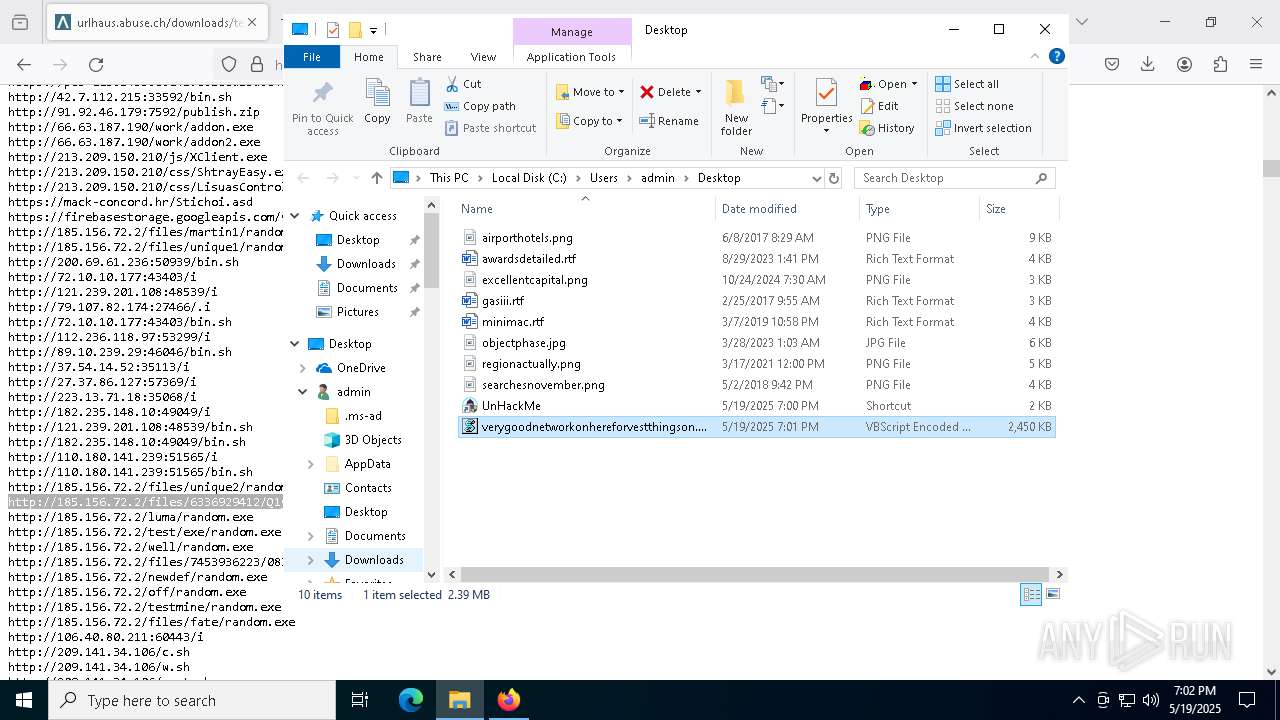
INFO
Application launched itself
- firefox.exe (PID: 7364)
- firefox.exe (PID: 7444)
- firefox.exe (PID: 2516)
- firefox.exe (PID: 8764)
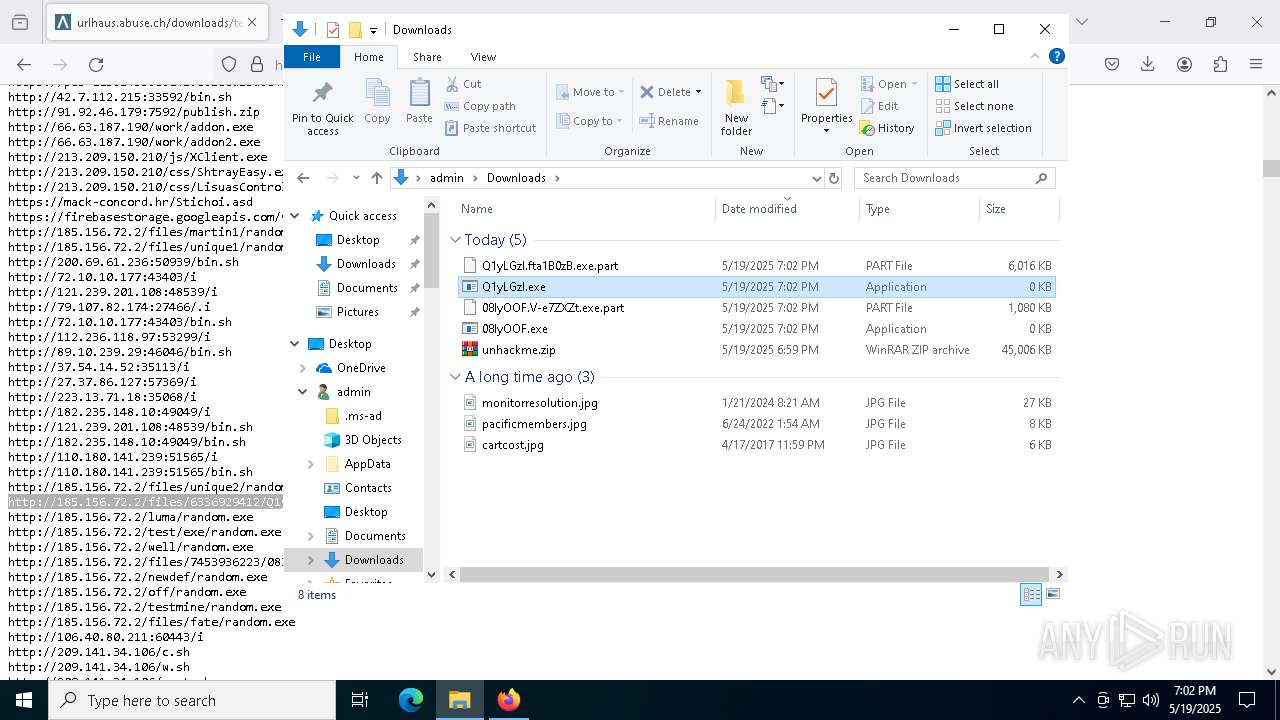
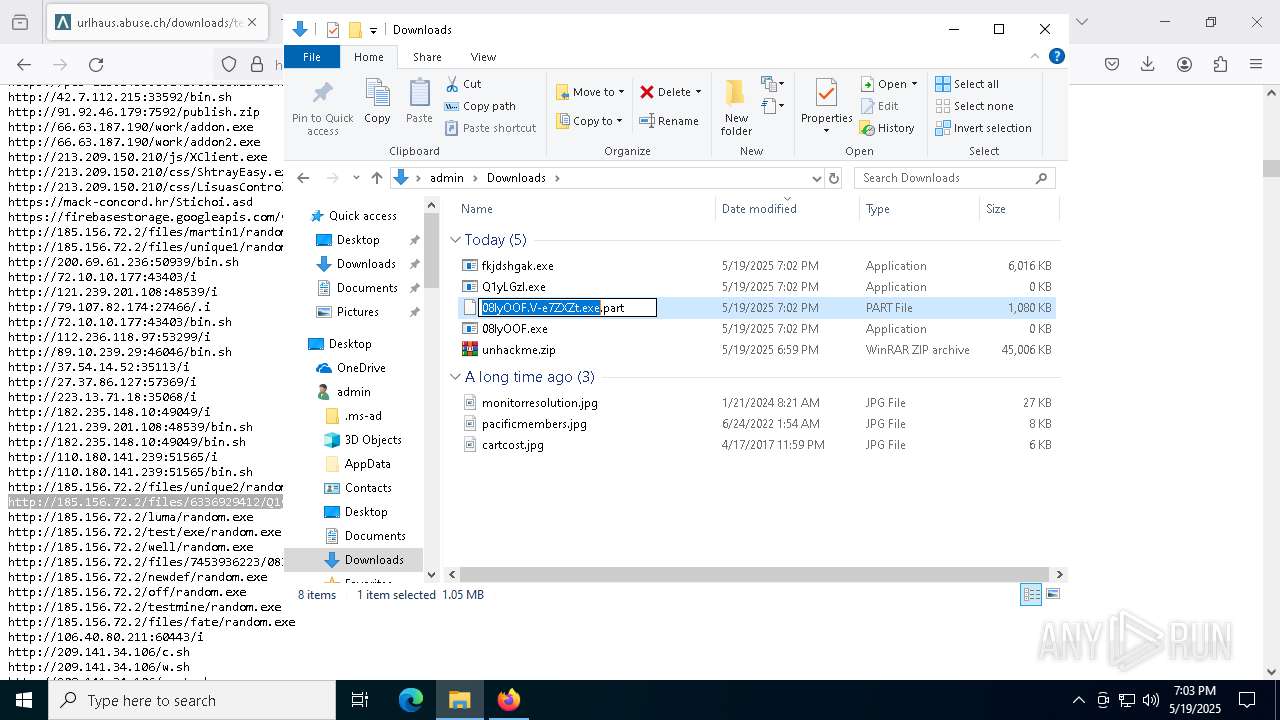
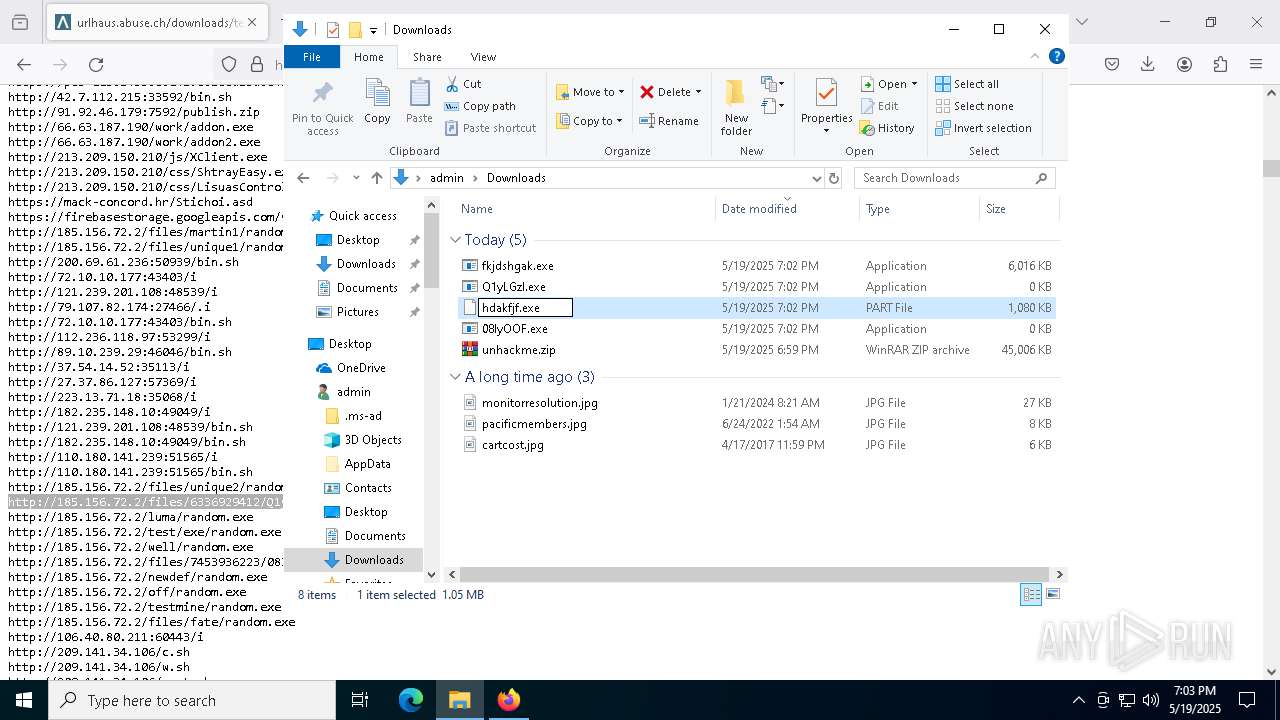
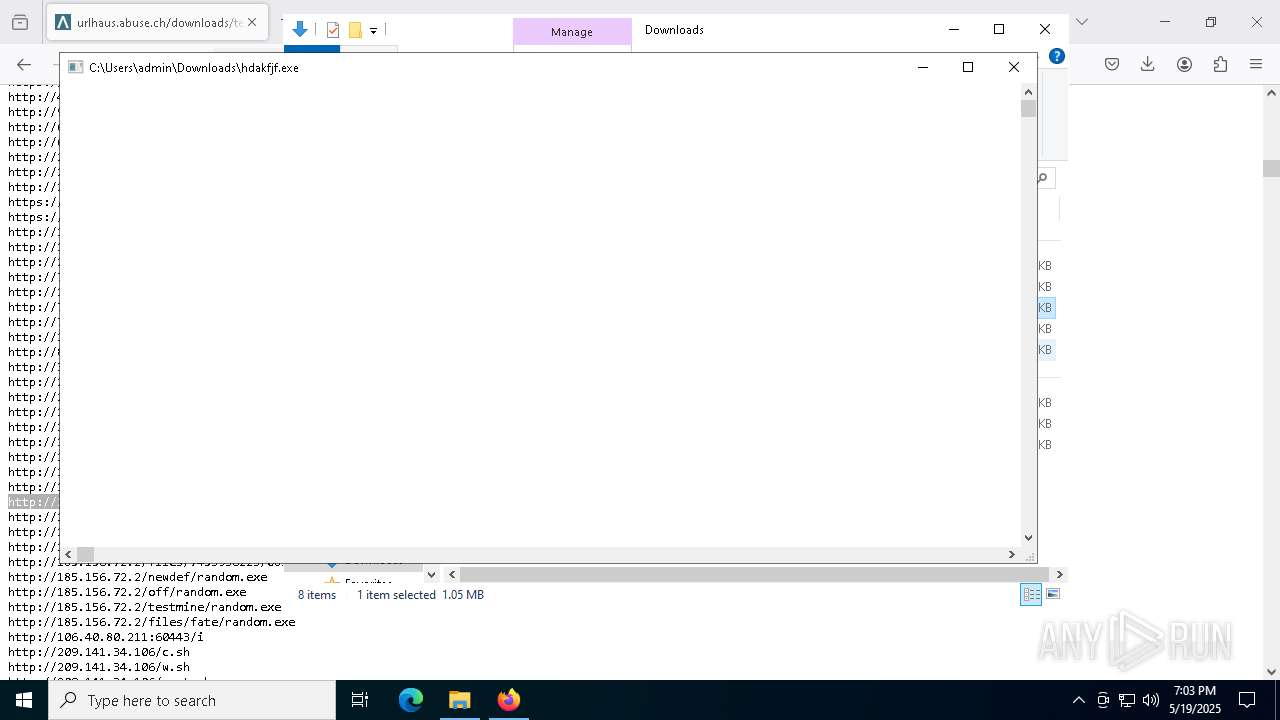
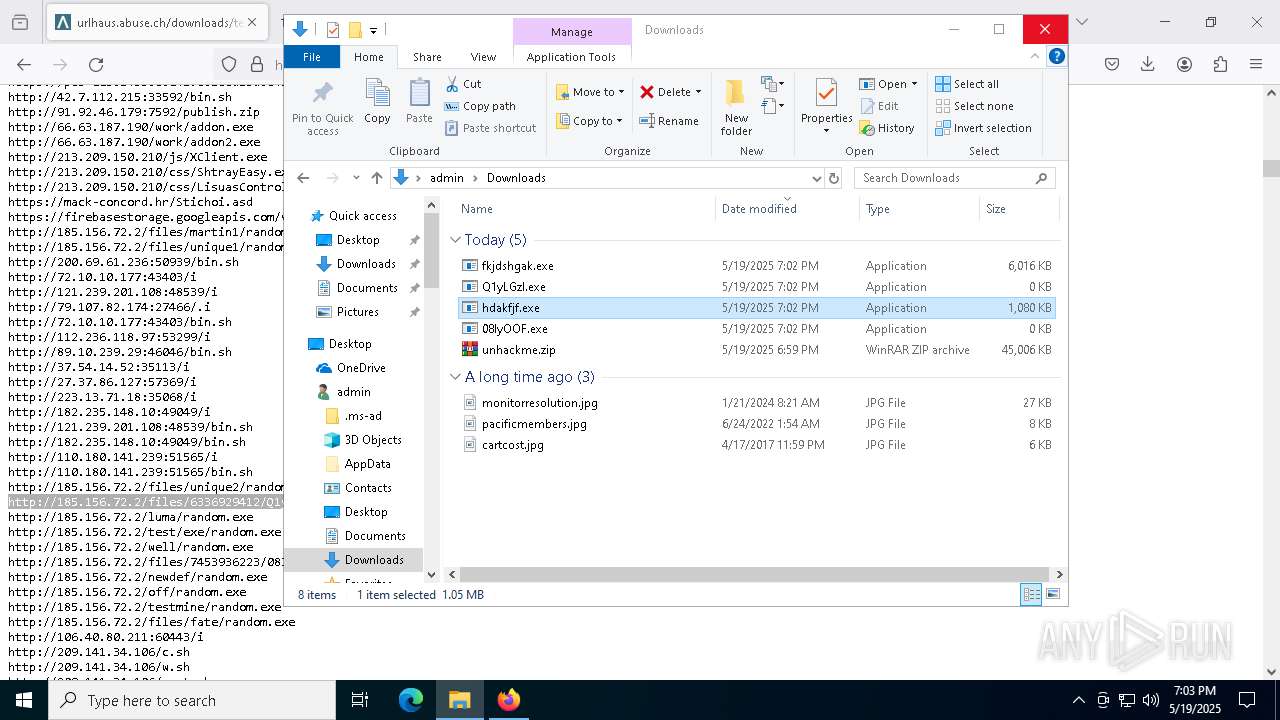
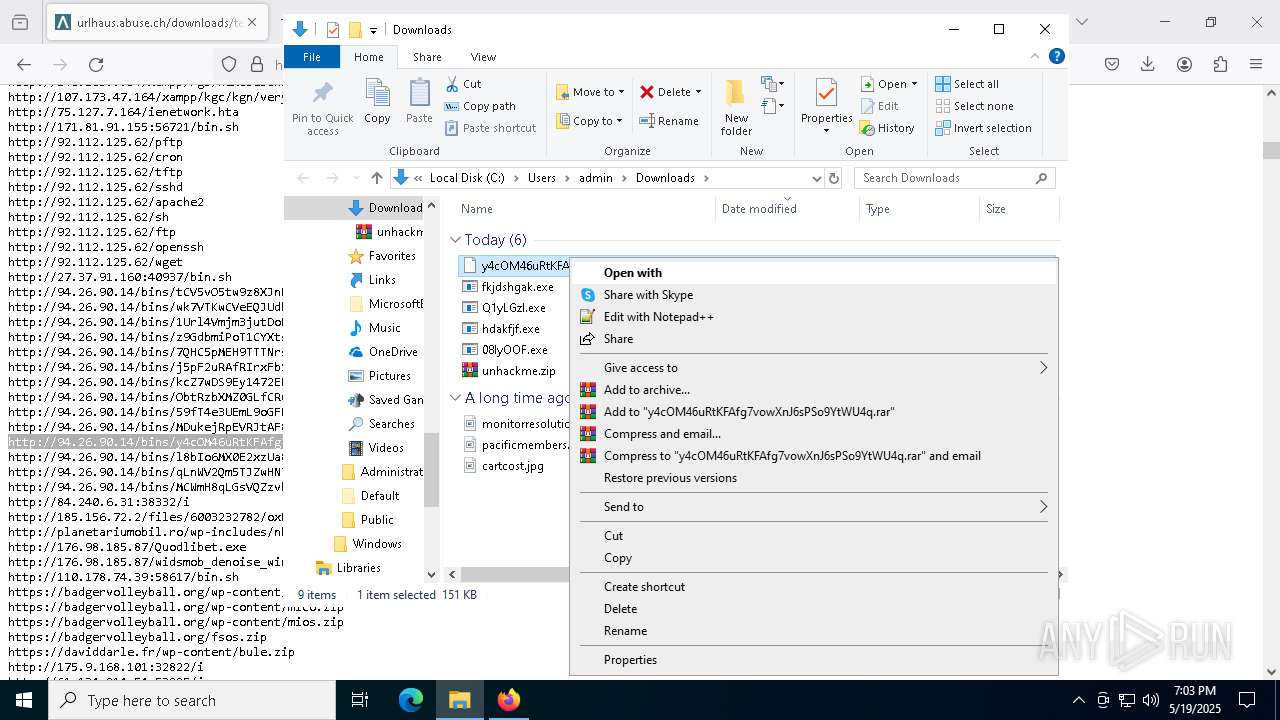
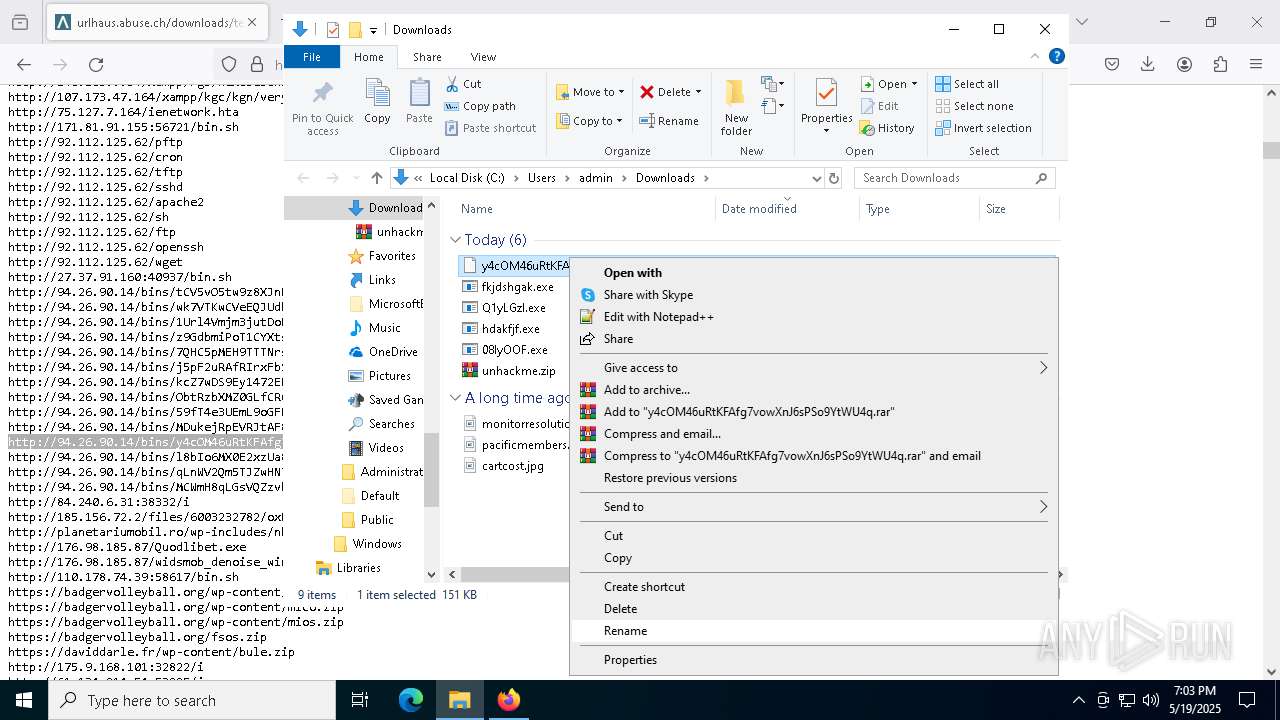
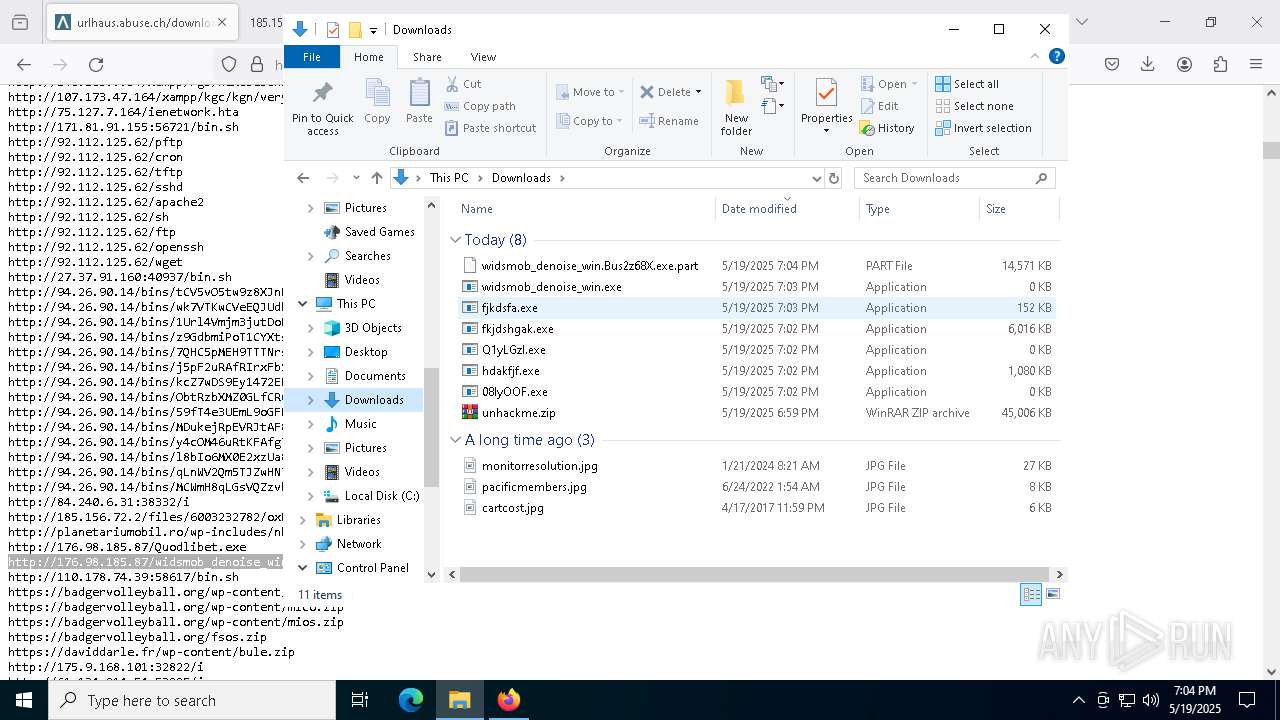
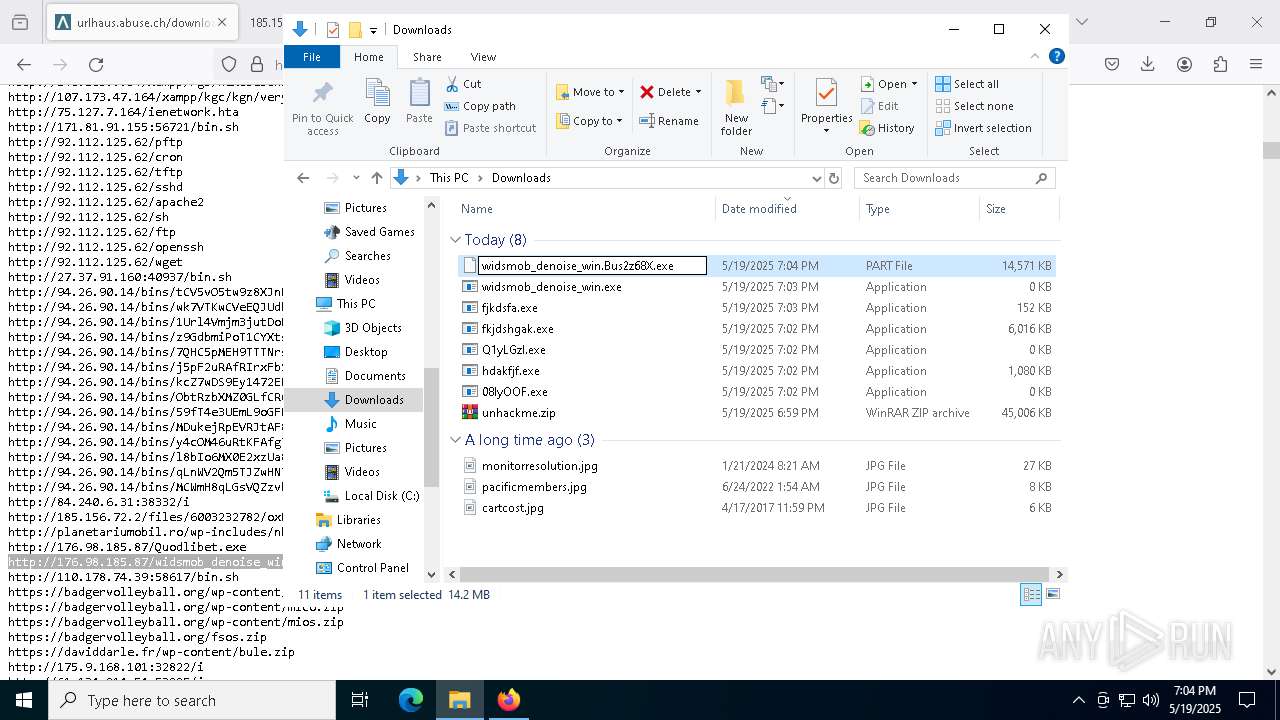
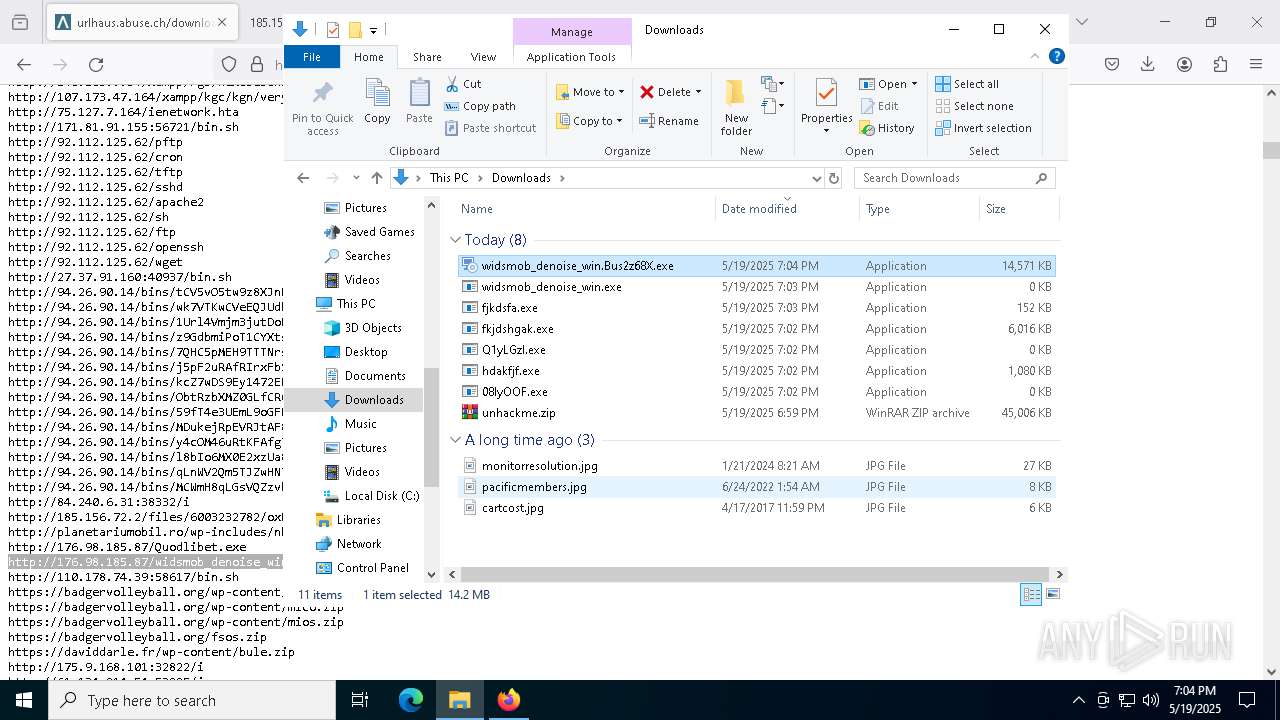
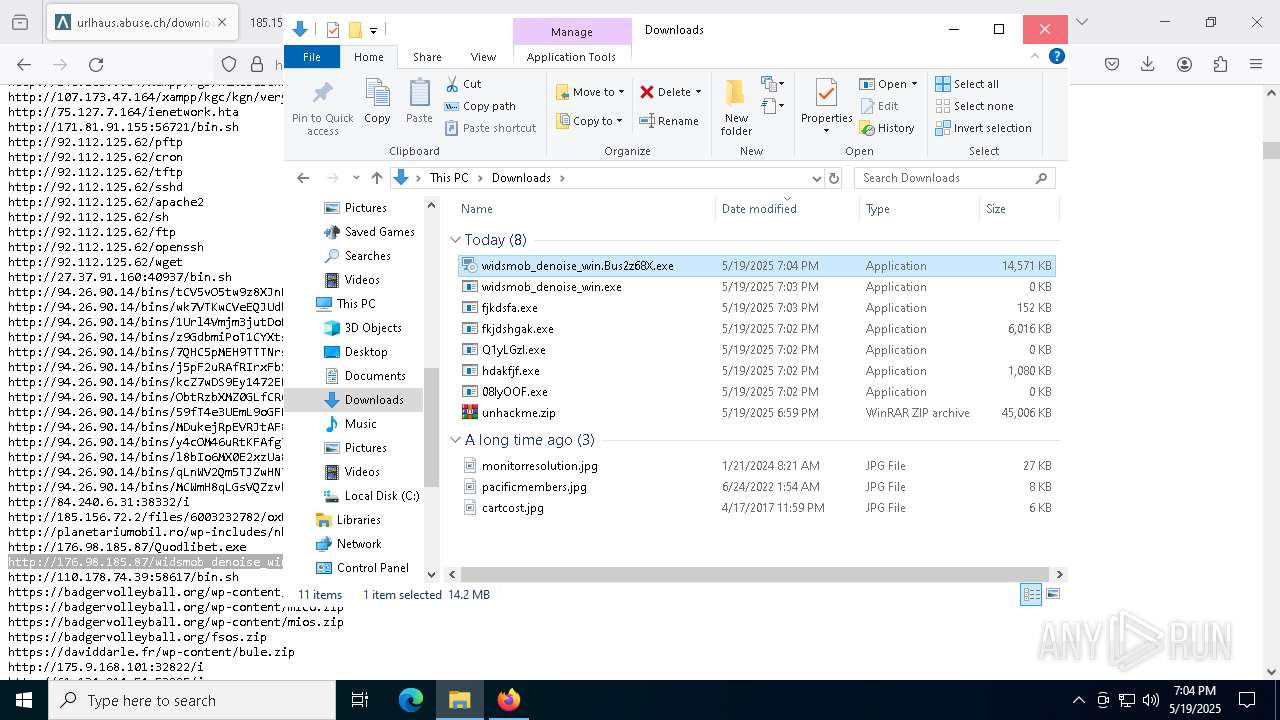
Manual execution by a user
- WinRAR.exe (PID: 8908)
- wscript.exe (PID: 7352)
- firefox.exe (PID: 2516)
- fkjdshgak.exe (PID: 5280)
- widsmob_denoise_win.Bus2z68X.exe (PID: 7000)
- hdakfjf.exe (PID: 6068)
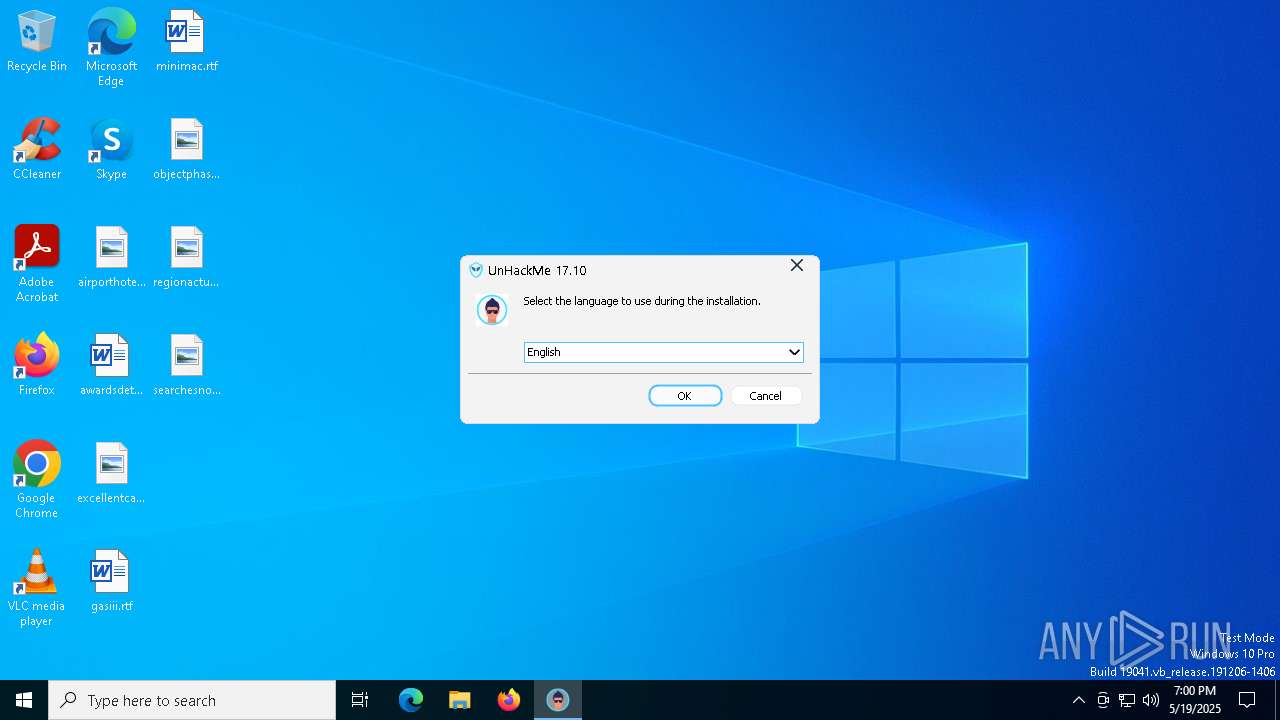
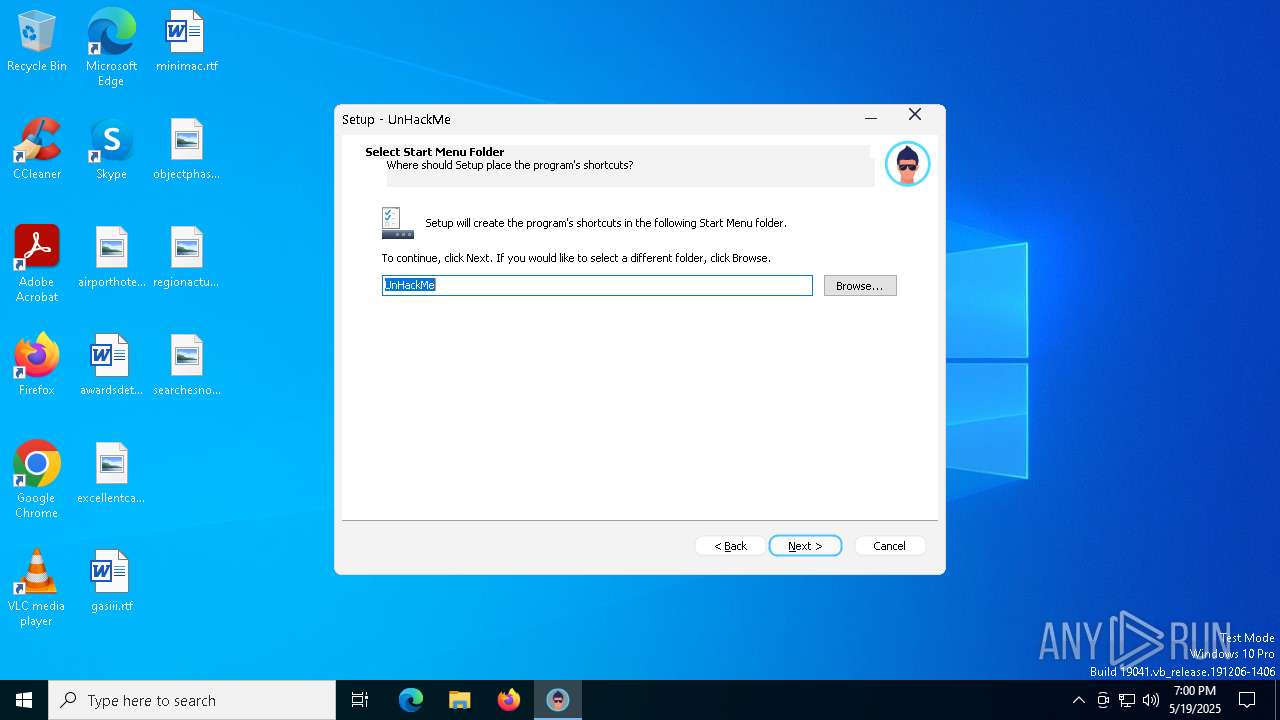
Checks supported languages
- unhackme_setup.exe (PID: 9060)
- unhackme_setup.tmp (PID: 9084)
- unhackme_setup.exe (PID: 9168)
- unhackme_setup.tmp (PID: 9192)
- unhackmeschedule.exe (PID: 8464)
- RegRunInfo.exe (PID: 8460)
- UnHackMe.exe (PID: 4560)
- WelcomeUnHackMe.exe (PID: 5064)
- hackmon.exe (PID: 5344)
Create files in a temporary directory
- unhackme_setup.exe (PID: 9060)
- unhackme_setup.exe (PID: 9168)
- unhackme_setup.tmp (PID: 9192)
- RegRunInfo.exe (PID: 8460)
Process checks computer location settings
- unhackme_setup.tmp (PID: 9084)
Compiled with Borland Delphi (YARA)
- unhackme_setup.tmp (PID: 9084)
- unhackme_setup.exe (PID: 9060)
- unhackme_setup.exe (PID: 9168)
- unhackme_setup.tmp (PID: 9192)
- hackmon.exe (PID: 5344)
- UnHackMe.exe (PID: 4560)
Creates files in the program directory
- unhackme_setup.tmp (PID: 9192)
Reads the computer name
- unhackme_setup.tmp (PID: 9084)
- unhackme_setup.tmp (PID: 9192)
- unhackmeschedule.exe (PID: 8464)
- RegRunInfo.exe (PID: 8460)
- WelcomeUnHackMe.exe (PID: 5064)
- UnHackMe.exe (PID: 4560)
- hackmon.exe (PID: 5344)
Detects InnoSetup installer (YARA)
- unhackme_setup.exe (PID: 9060)
- unhackme_setup.exe (PID: 9168)
Creates a software uninstall entry
- unhackme_setup.tmp (PID: 9192)
Reads the machine GUID from the registry
- RegRunInfo.exe (PID: 8460)
Creates files or folders in the user directory
- RegRunInfo.exe (PID: 8460)
Reads the software policy settings
- slui.exe (PID: 7532)
- RegRunInfo.exe (PID: 8460)
The sample compiled with russian language support
- unhackme_setup.tmp (PID: 9192)
The sample compiled with english language support
- unhackme_setup.tmp (PID: 9192)
- firefox.exe (PID: 8764)
Checks proxy server information
- RegRunInfo.exe (PID: 8460)
Executable content was dropped or overwritten
- firefox.exe (PID: 8764)
Detects GO elliptic curve encryption (YARA)
- widsmob_denoise_win.Bus2z68X.exe (PID: 7000)
Application based on Golang
- widsmob_denoise_win.Bus2z68X.exe (PID: 7000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Remcos
(PID) Process(2552) MSBuild.exe
C2 (1)216.9.225.163:13030
BotnetRemoteHost
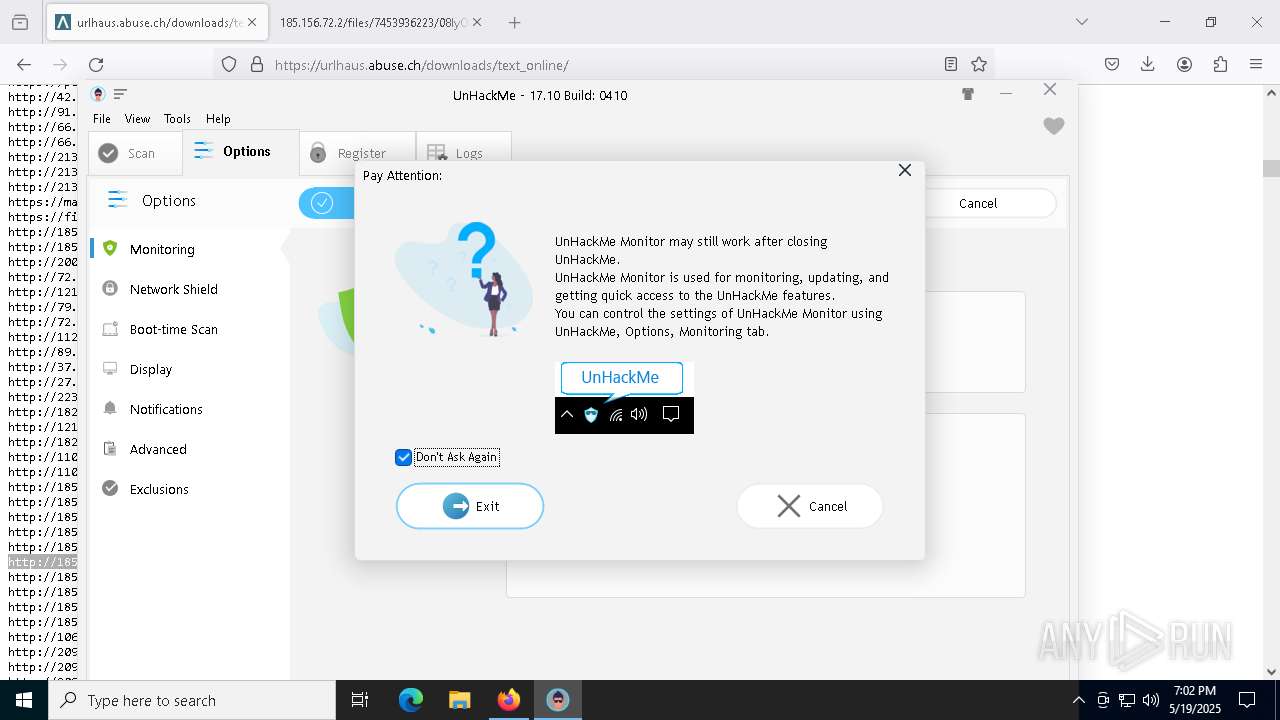
Options
Connect_interval1
Install_flagFalse
Install_HKCU\RunTrue
Install_HKLM\RunTrue
Install_HKLM\Explorer\Run1
Install_HKLM\Winlogon\Shell100000
Setup_path%LOCALAPPDATA%
Copy_fileremcos.exe
Startup_valueFalse
Hide_fileFalse
Mutex_nameRmc-9I6IG8
Keylog_flag0
Keylog_path%LOCALAPPDATA%
Keylog_filelogs.dat
Keylog_cryptFalse
Hide_keylogFalse
Screenshot_flagFalse
Screenshot_time5
Take_ScreenshotFalse
Screenshot_path%APPDATA%
Screenshot_fileScreenshots
Screenshot_cryptFalse
Mouse_optionFalse
Delete_fileFalse
Audio_record_time5
Audio_path1
Audio_dirMicRecords
Connect_delay0
Copy_dirRemcos
Keylog_dirremcos
Total processes
202
Monitored processes
66
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=7588 -childID 8 -isForBrowser -prefsHandle 2620 -prefMapHandle 2680 -prefsLen 31459 -prefMapSize 244583 -jsInitHandle 1348 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {b26fdef4-29a0-4f11-a139-cb270345cb2b} 8764 "\\.\pipe\gecko-crash-server-pipe.8764" 1dff31e4d90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 632 | "C:\WINDOWS\system32\taskkill.exe" /f /im "unhackme.exe" | C:\Windows\SysWOW64\taskkill.exe | — | unhackme_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5024 -childID 4 -isForBrowser -prefsHandle 5012 -prefMapHandle 4992 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1348 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {30697848-47ad-4904-97af-59c3d490ffae} 8764 "\\.\pipe\gecko-crash-server-pipe.8764" 1dff2872f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 668 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=7704 -childID 9 -isForBrowser -prefsHandle 4168 -prefMapHandle 3992 -prefsLen 31459 -prefMapSize 244583 -jsInitHandle 1348 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {62c4ced7-434a-466d-8fe3-4431749fb058} 8764 "\\.\pipe\gecko-crash-server-pipe.8764" 1dff53c8690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5056 -childID 5 -isForBrowser -prefsHandle 5024 -prefMapHandle 4912 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1352 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {aa8c4882-f7c1-4443-a674-0e65a638f1d6} 7444 "\\.\pipe\gecko-crash-server-pipe.7444" 1c59e00f690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 | |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2552 | "C:\WINDOWS\system32\taskkill.exe" /f /im "hackmon.exe" | C:\Windows\SysWOW64\taskkill.exe | — | unhackme_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | "C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
Remcos(PID) Process(2552) MSBuild.exe C2 (1)216.9.225.163:13030 BotnetRemoteHost Options Connect_interval1 Install_flagFalse Install_HKCU\RunTrue Install_HKLM\RunTrue Install_HKLM\Explorer\Run1 Install_HKLM\Winlogon\Shell100000 Setup_path%LOCALAPPDATA% Copy_fileremcos.exe Startup_valueFalse Hide_fileFalse Mutex_nameRmc-9I6IG8 Keylog_flag0 Keylog_path%LOCALAPPDATA% Keylog_filelogs.dat Keylog_cryptFalse Hide_keylogFalse Screenshot_flagFalse Screenshot_time5 Take_ScreenshotFalse Screenshot_path%APPDATA% Screenshot_fileScreenshots Screenshot_cryptFalse Mouse_optionFalse Delete_fileFalse Audio_record_time5 Audio_path1 Audio_dirMicRecords Connect_delay0 Copy_dirRemcos Keylog_dirremcos | |||||||||||||||
Total events
45 205
Read events
44 972
Write events
230
Delete events
3
Modification events
| (PID) Process: | (7444) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (8908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\unhackme.zip | |||
| (PID) Process: | (8908) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
69
Suspicious files
322
Text files
381
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7444 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7444 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 7444 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7444 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7444 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 7444 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7444 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 7444 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db-journal | binary | |
MD5:B61F7CE8BBB50A1A1F73C0D61002579D | SHA256:8ADB2C41F659A88393C1D3493E3727DE5B2E1D05FBA36FE711BFB21C155E51EB | |||
| 7444 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 7444 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
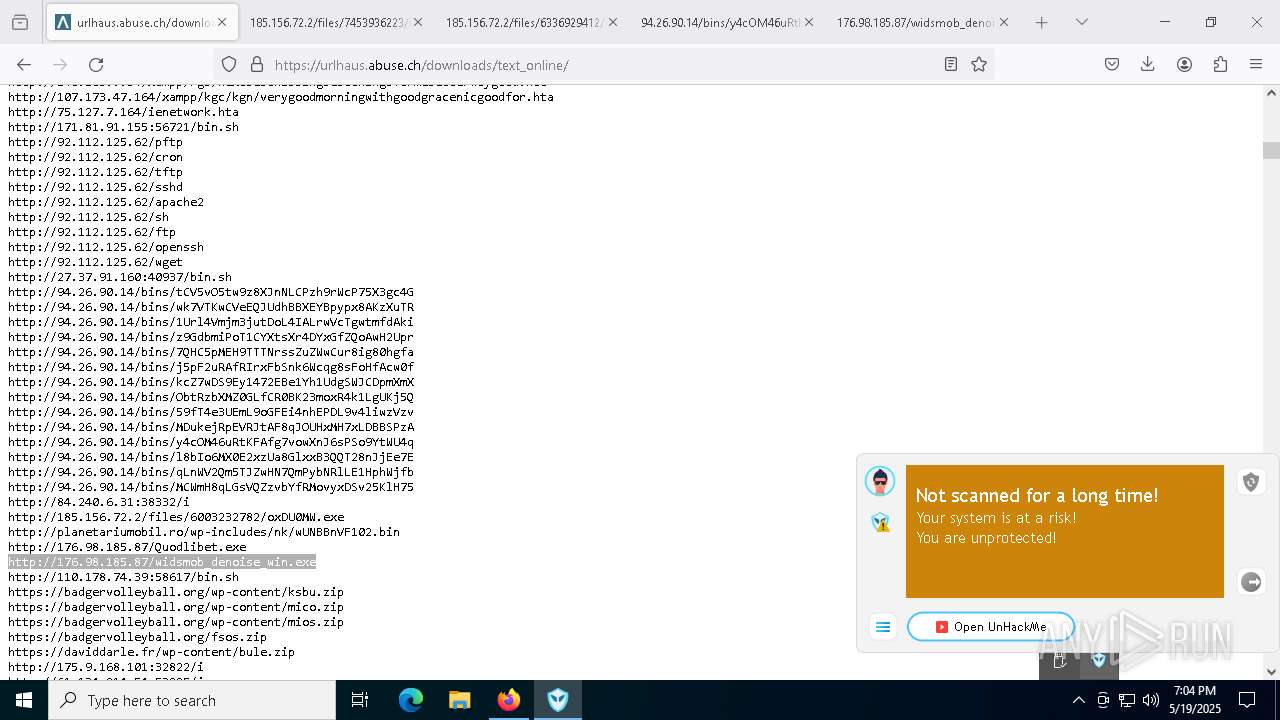
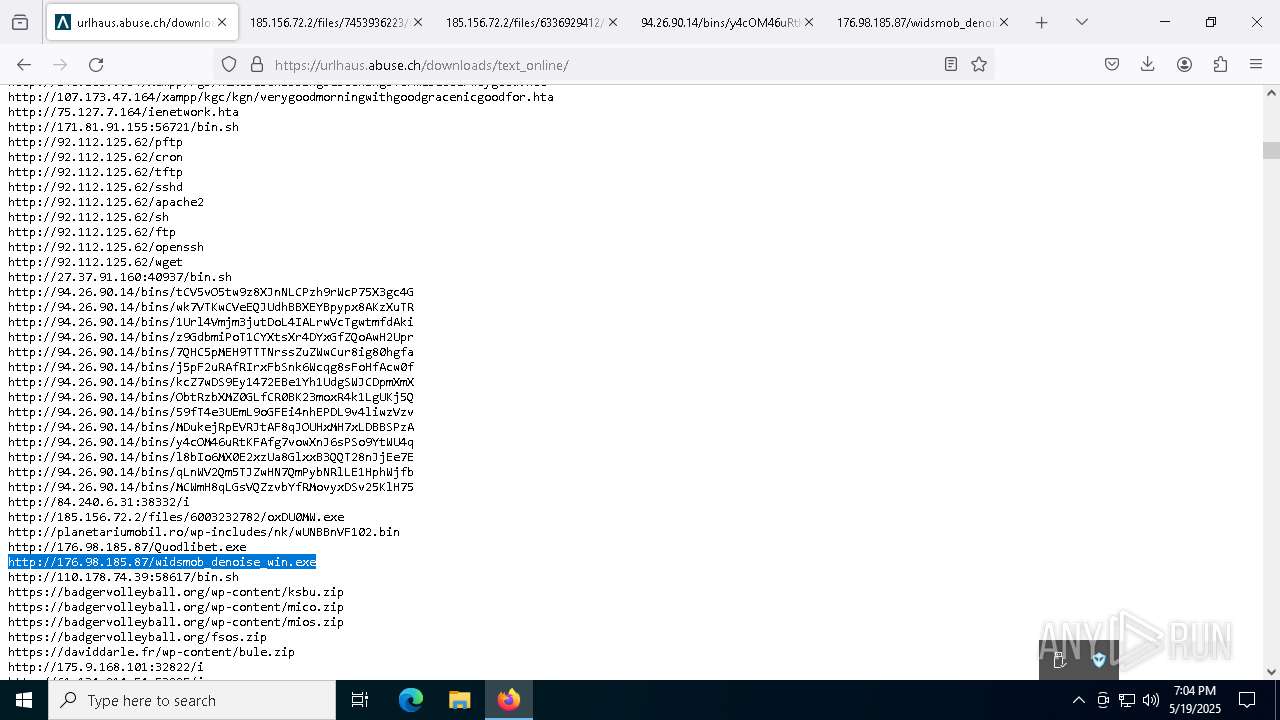
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
67
TCP/UDP connections
201
DNS requests
215
Threats
30
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7444 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7444 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7444 | firefox.exe | POST | 200 | 184.24.77.75:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7444 | firefox.exe | POST | 200 | 184.24.77.75:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7444 | firefox.exe | POST | 200 | 184.24.77.58:80 | http://e6.o.lencr.org/ | unknown | — | — | whitelisted |
7444 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
— | — | POST | 200 | 142.250.186.35:80 | http://o.pki.goog/s/wr3/3H4 | unknown | — | — | whitelisted |
— | — | POST | 200 | 142.250.186.35:80 | http://o.pki.goog/s/wr3/3H4 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7444 | firefox.exe | 142.250.185.74:443 | safebrowsing.googleapis.com | — | — | whitelisted |
7444 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
— | — | 34.107.243.93:443 | push.services.mozilla.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
greatis.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain in DNS Lookup (geolocation-db .com) |
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain in DNS Lookup (geolocation-db .com) |
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain in DNS Lookup (geolocation-db .com) |
7444 | firefox.exe | Misc activity | ET INFO External IP Lookup Domain (geolocation-db .com) in TLS SNI |
7444 | firefox.exe | Misc activity | ET INFO External IP Lookup Domain (geolocation-db .com) in TLS SNI |
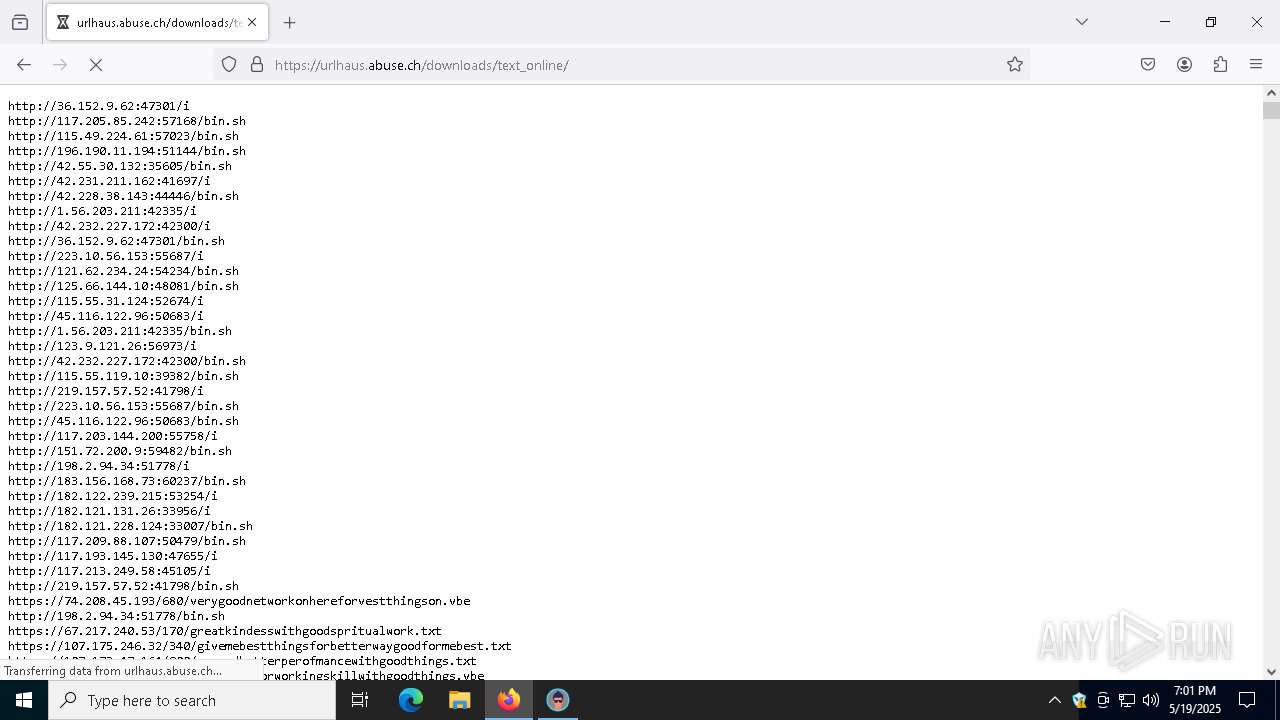
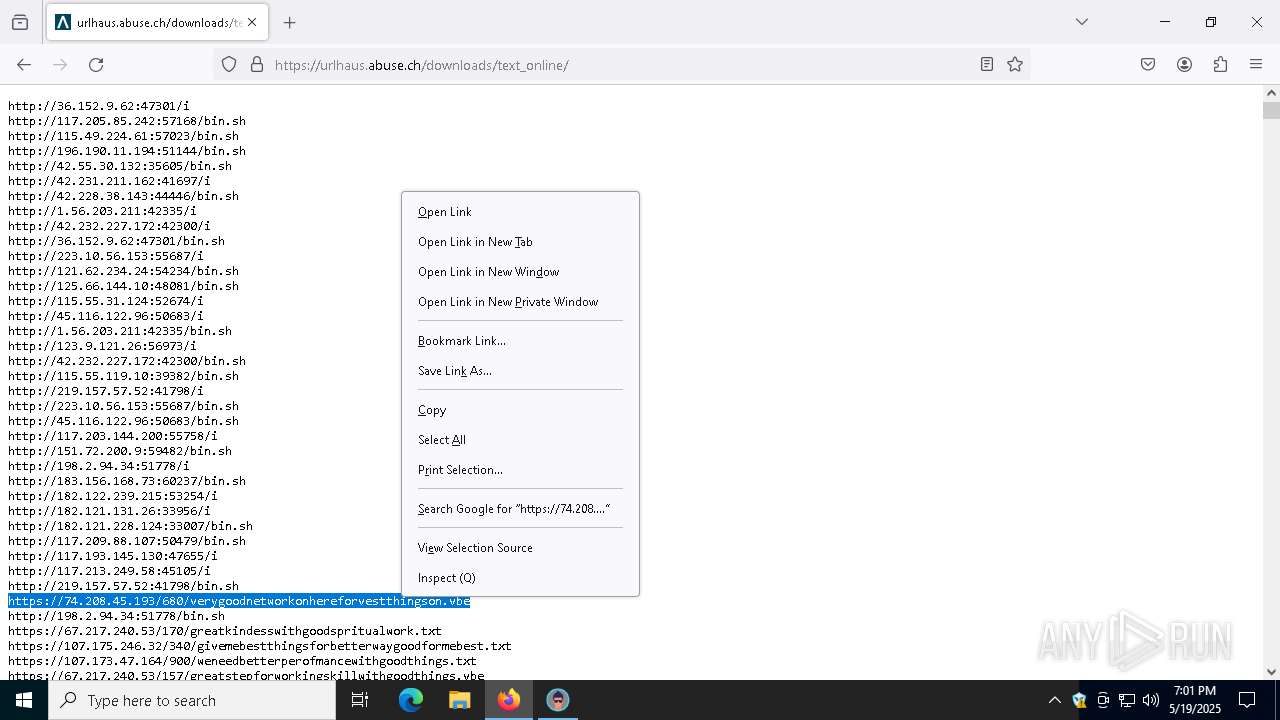
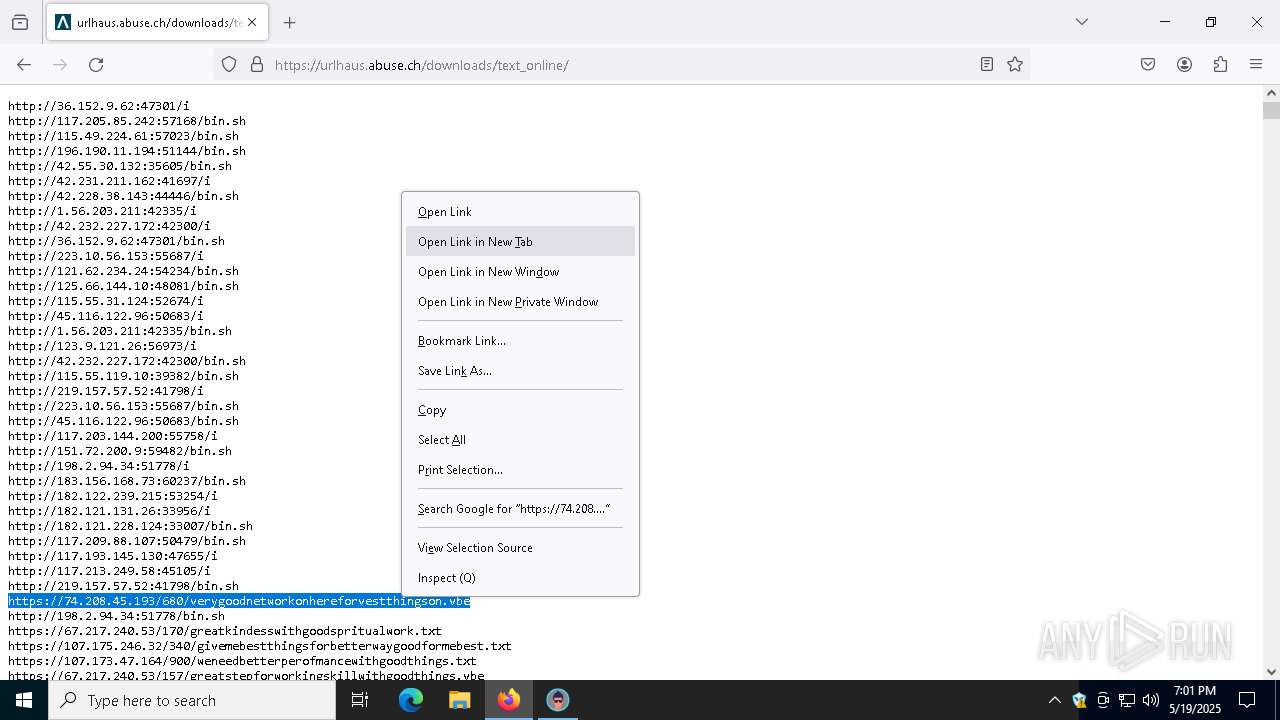
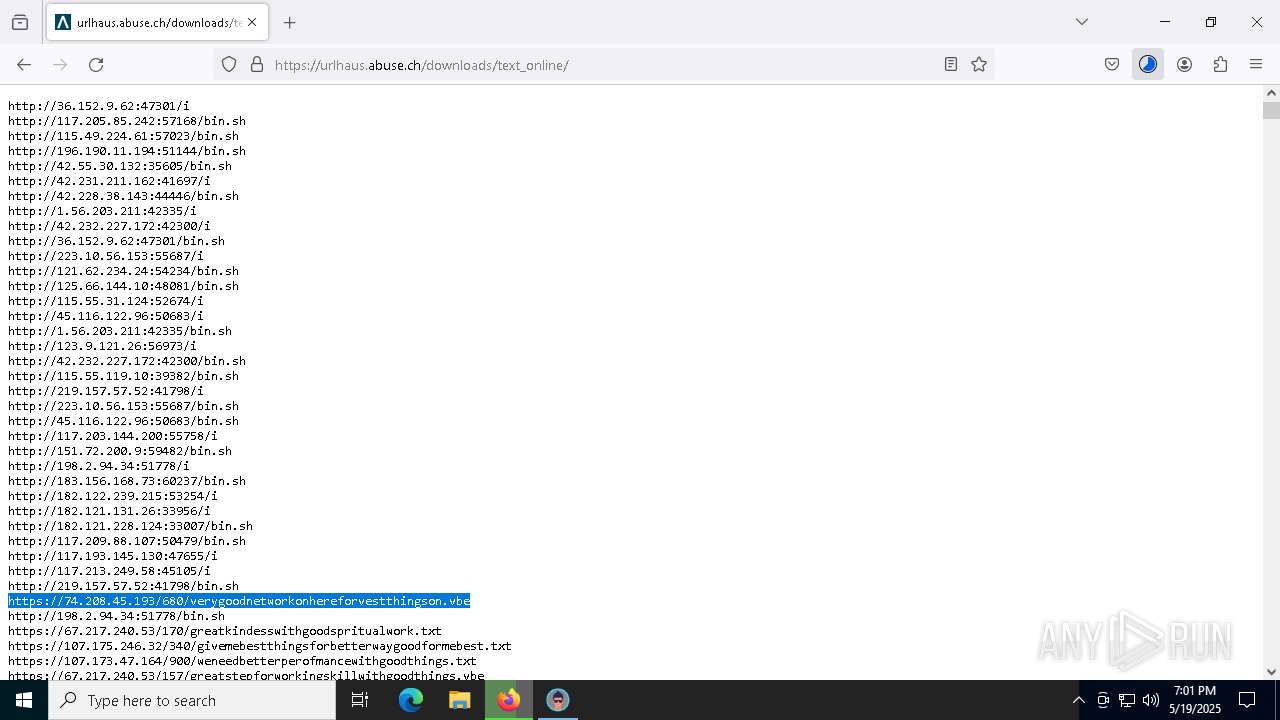
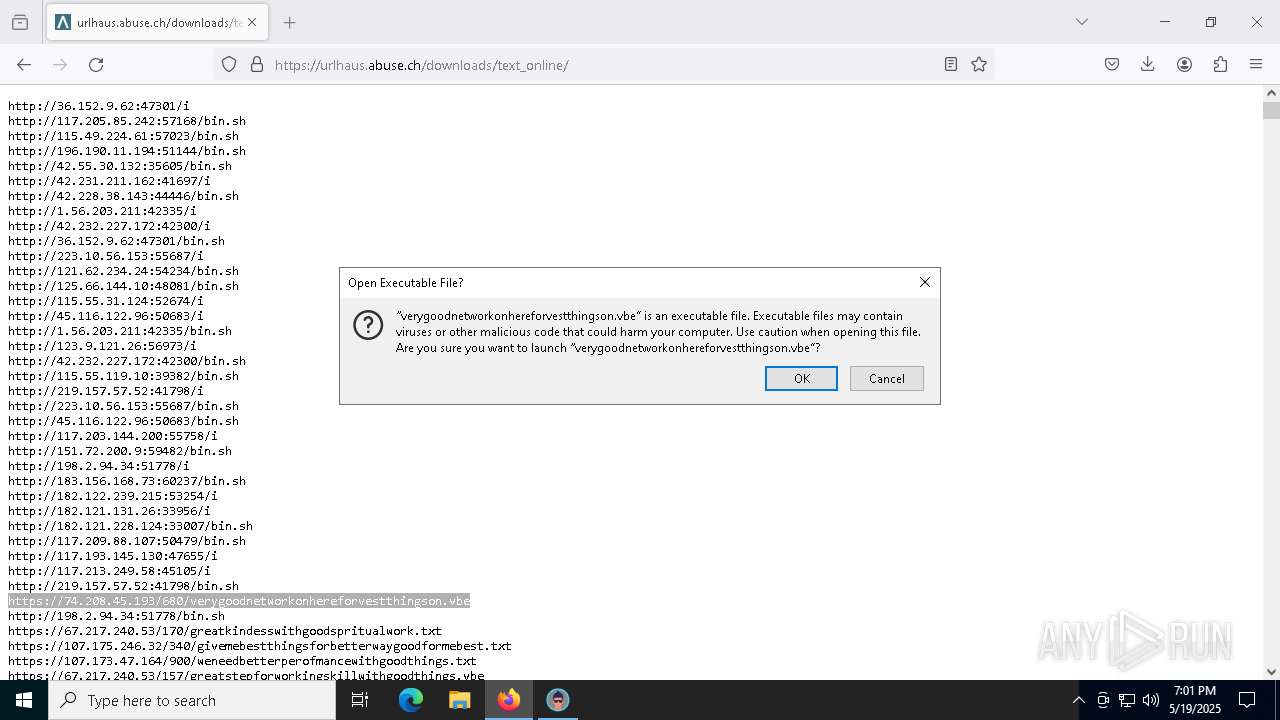
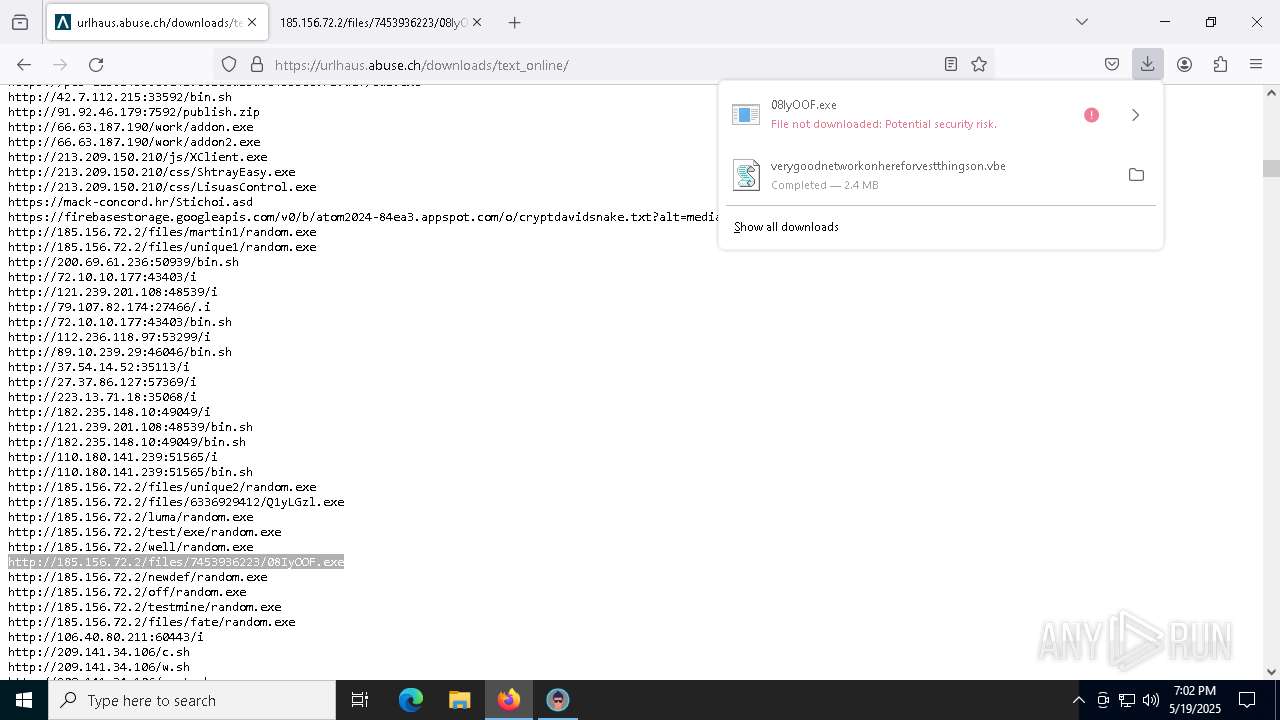
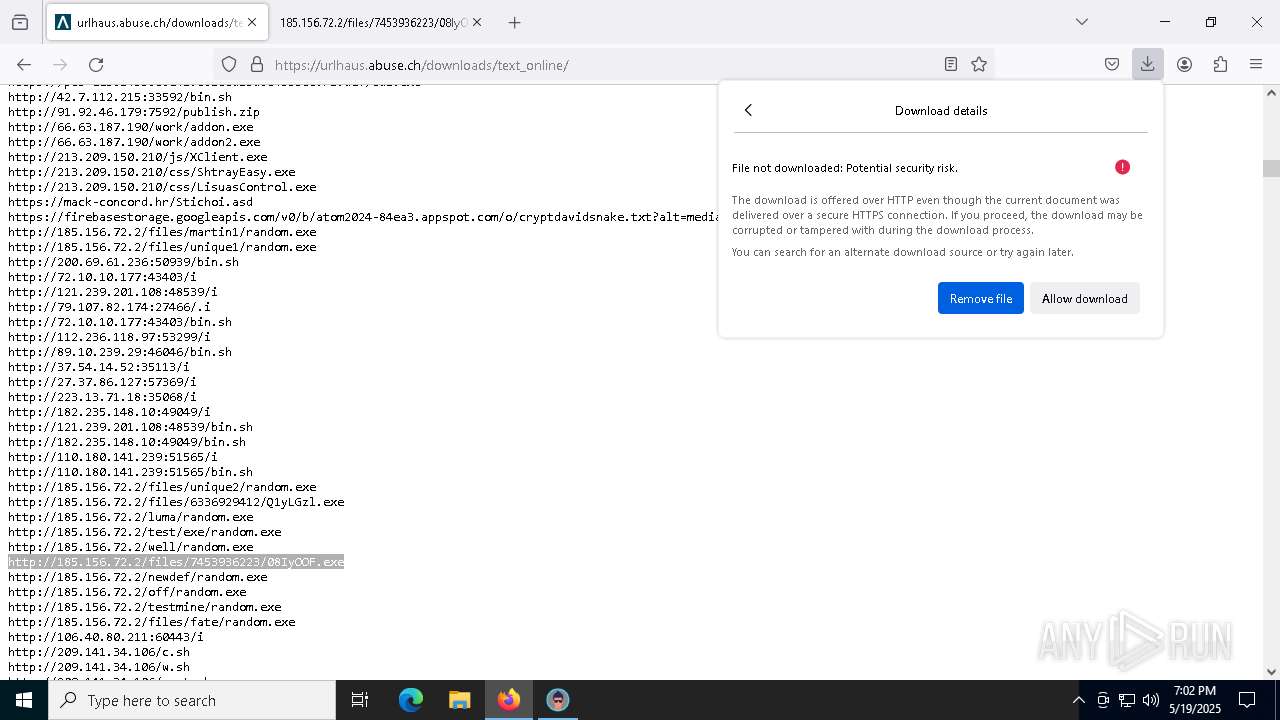
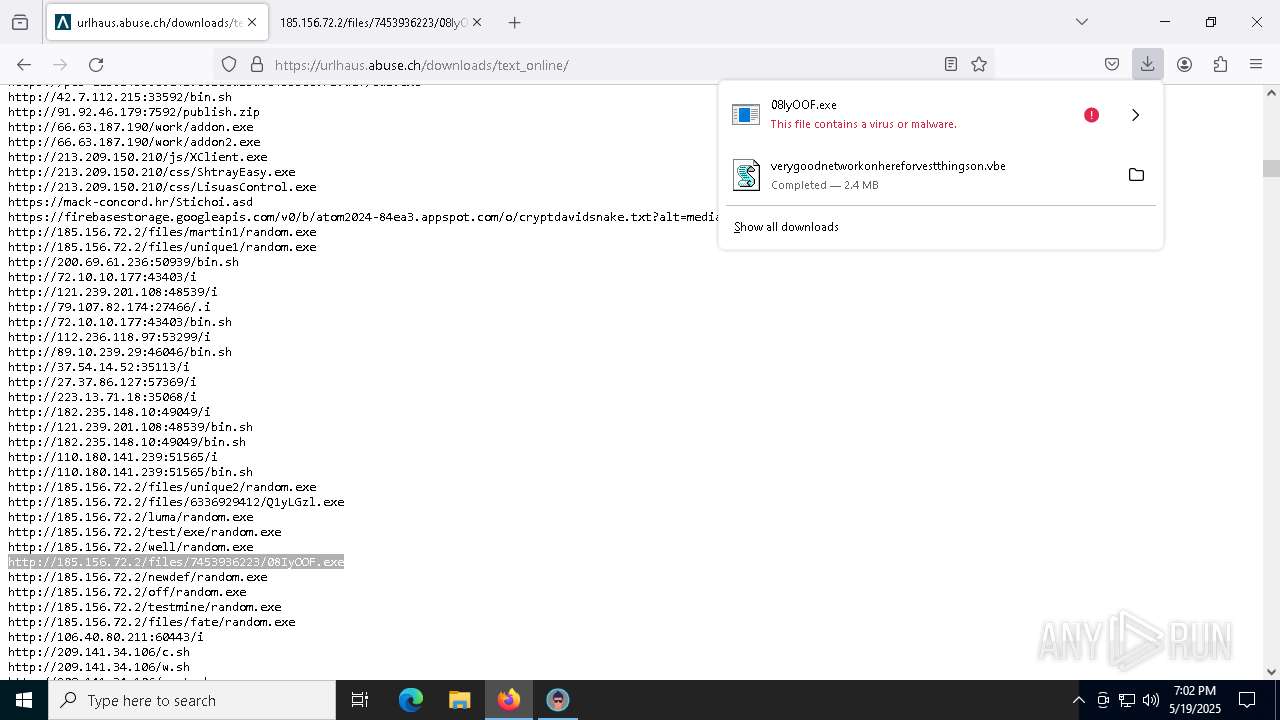
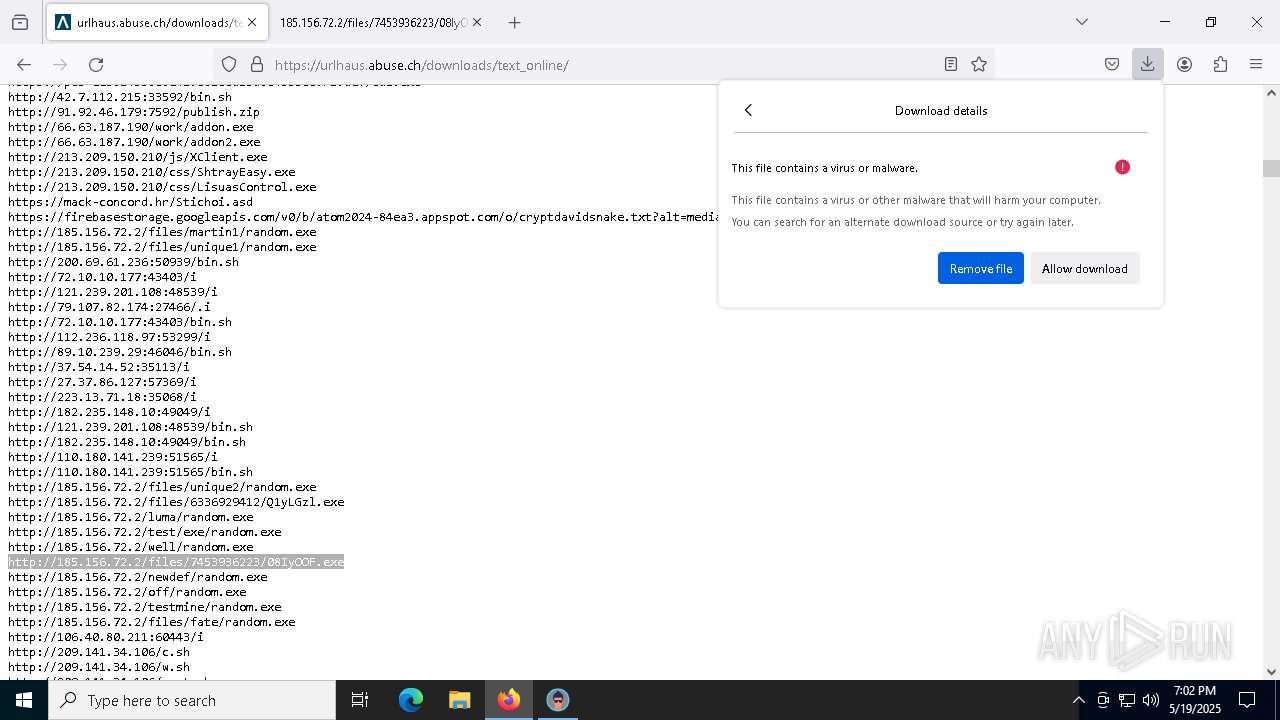
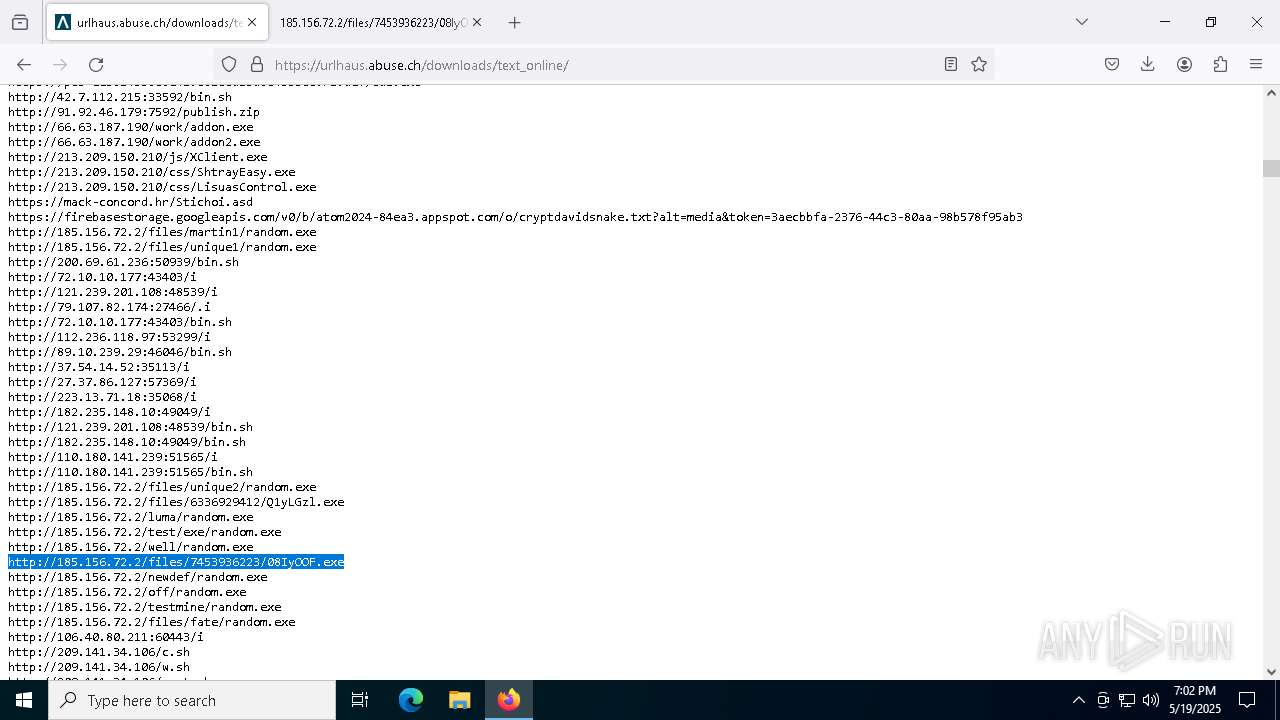
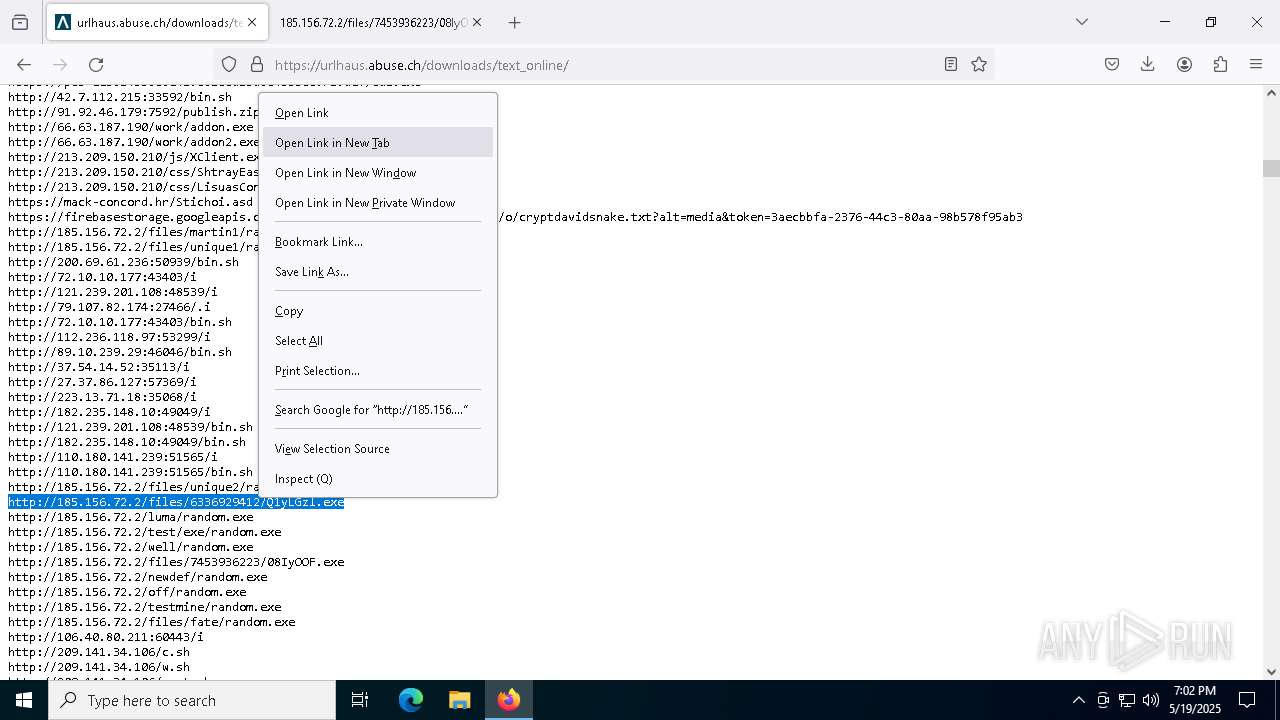
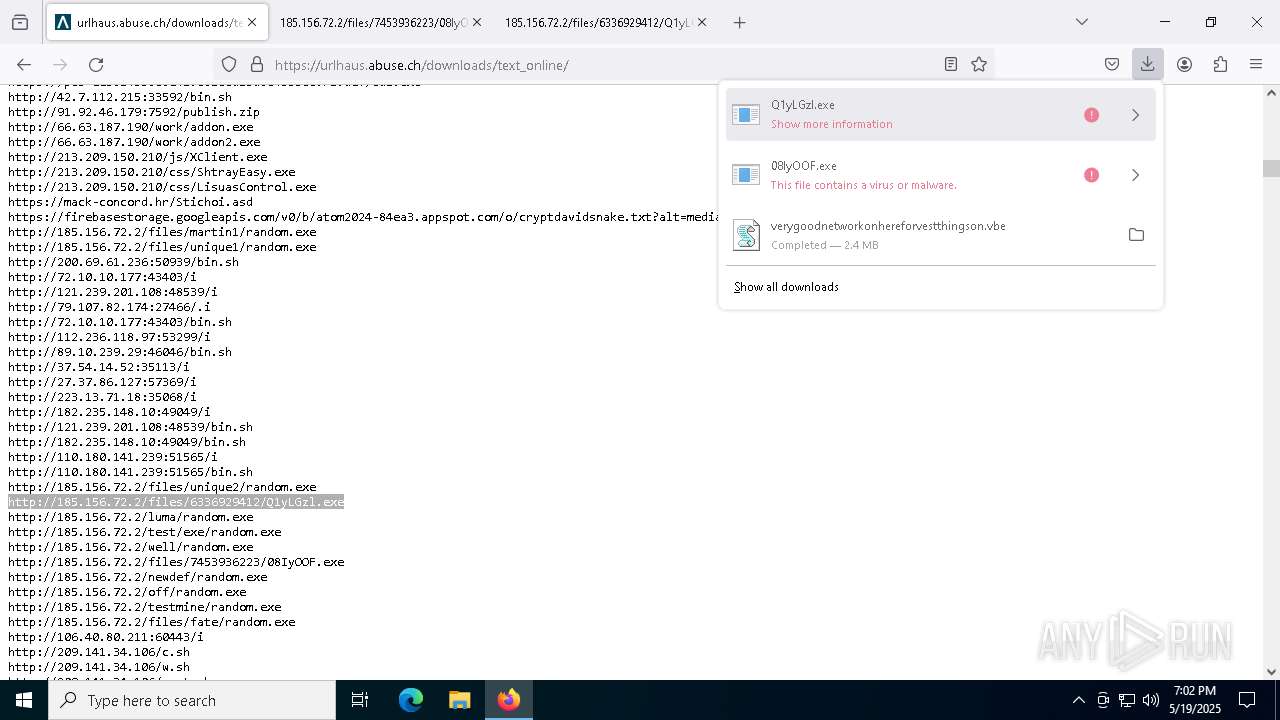
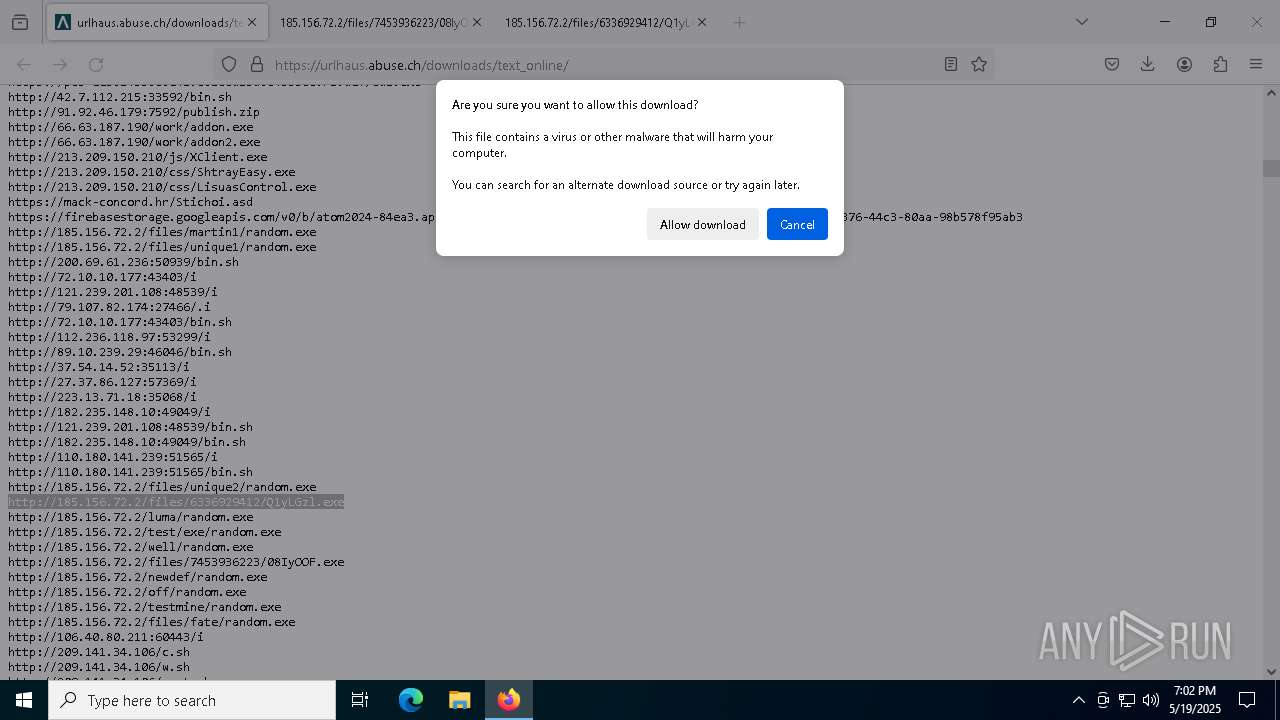
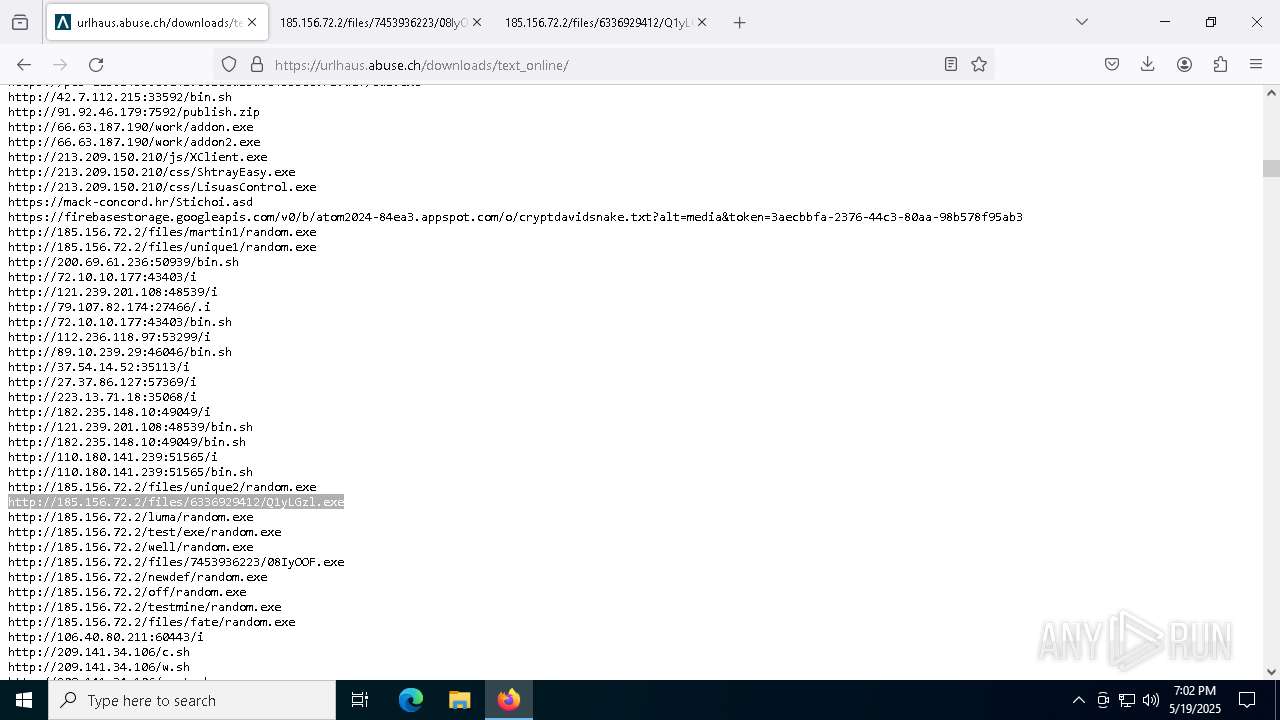
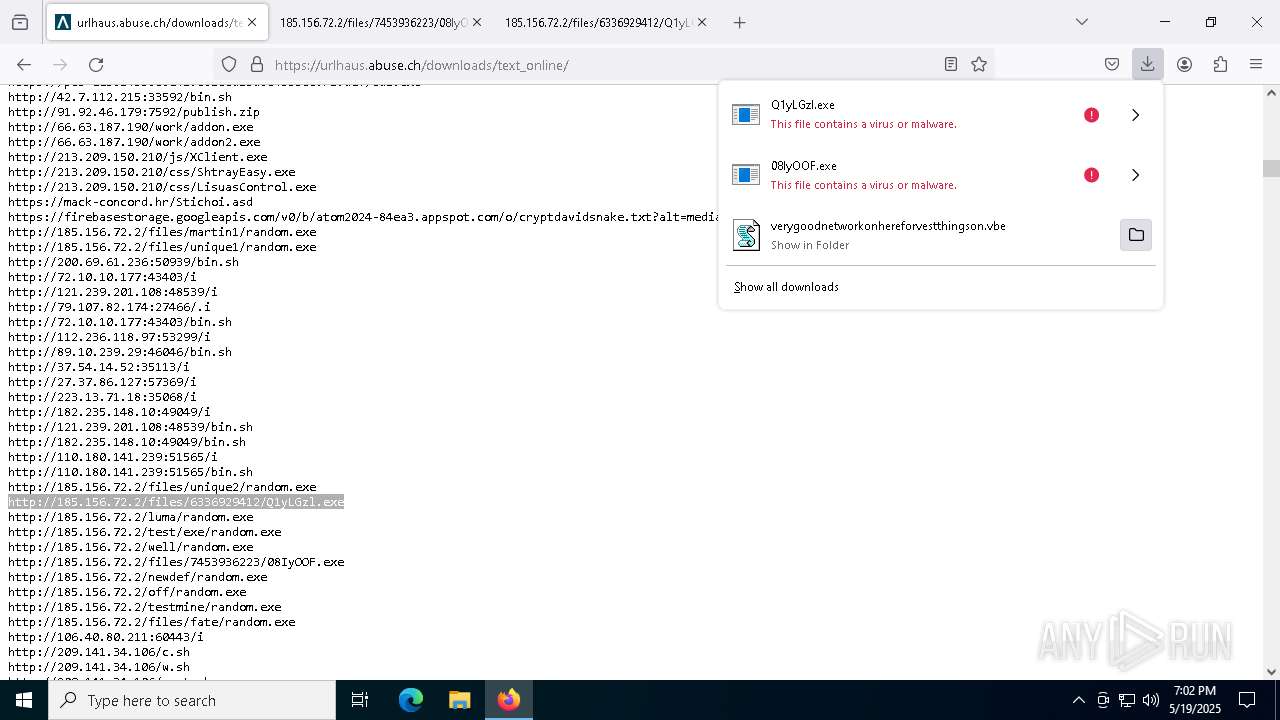
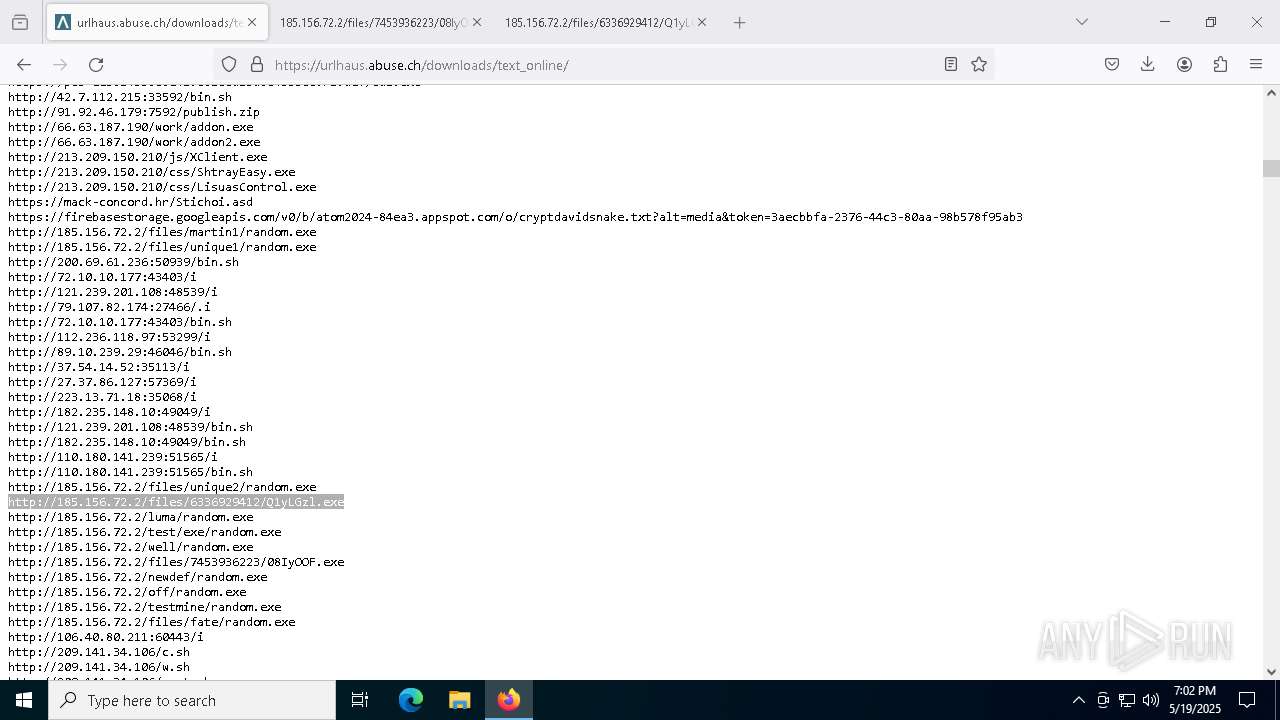
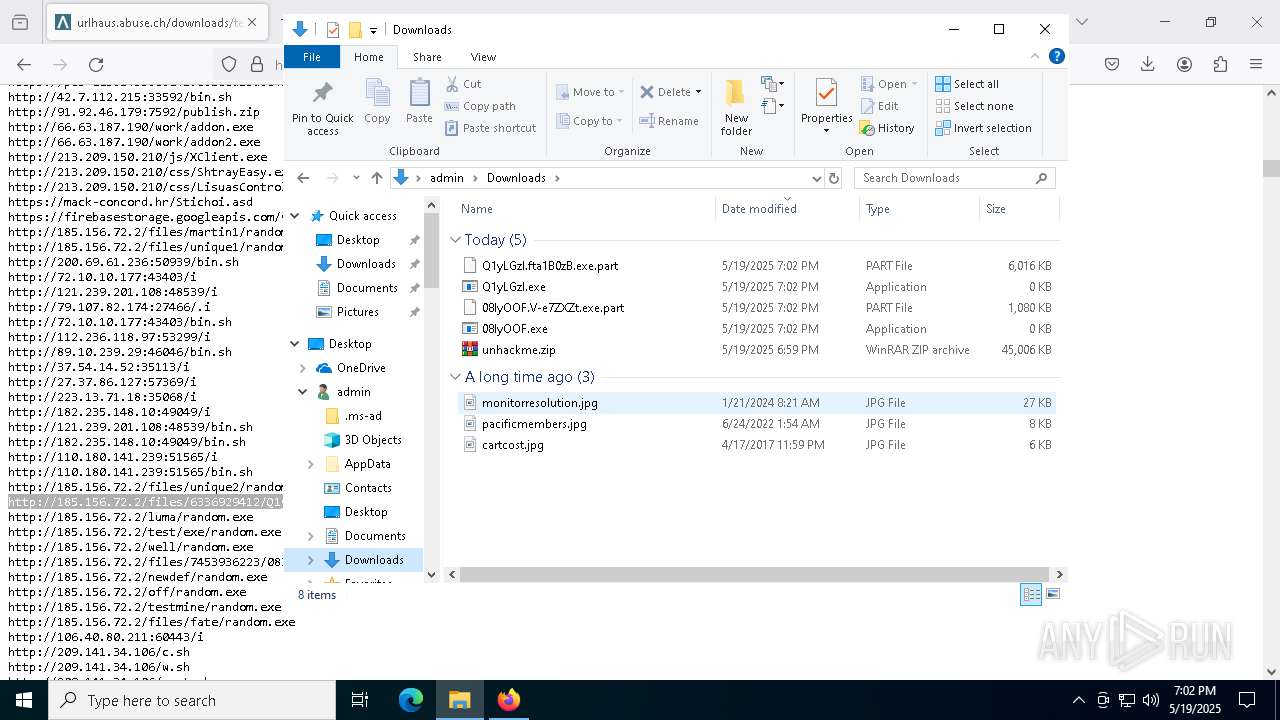
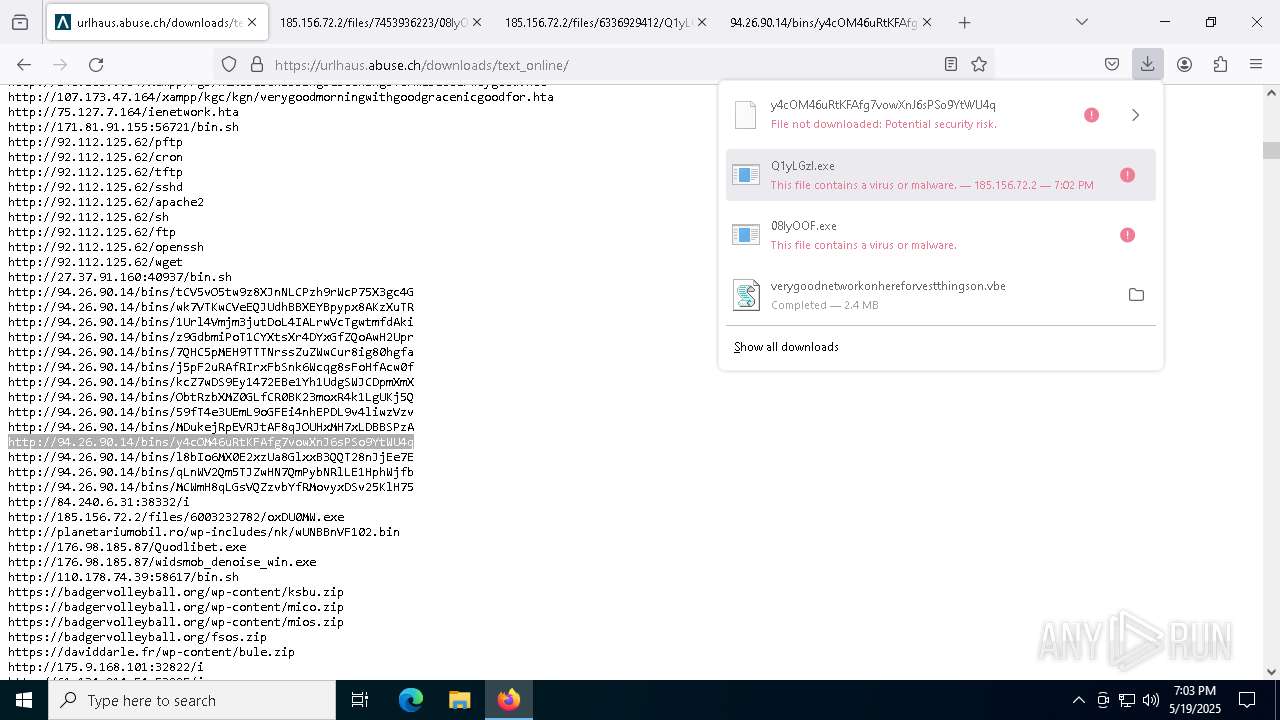
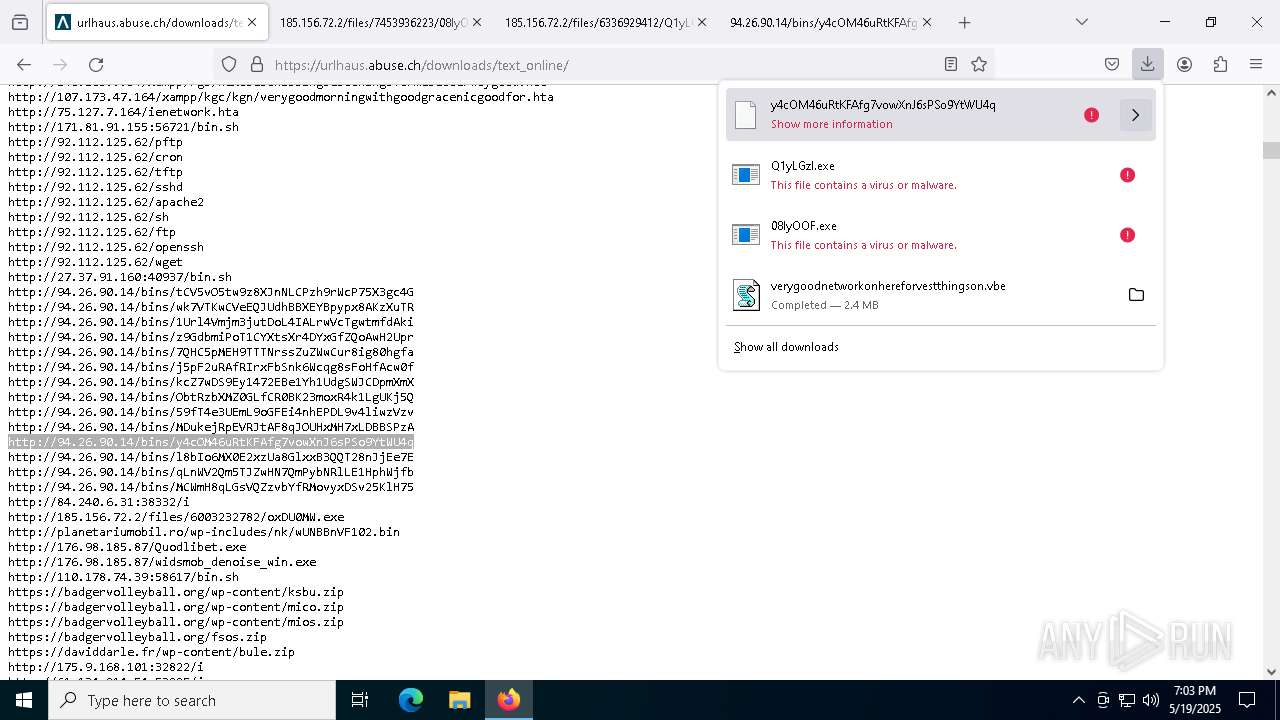
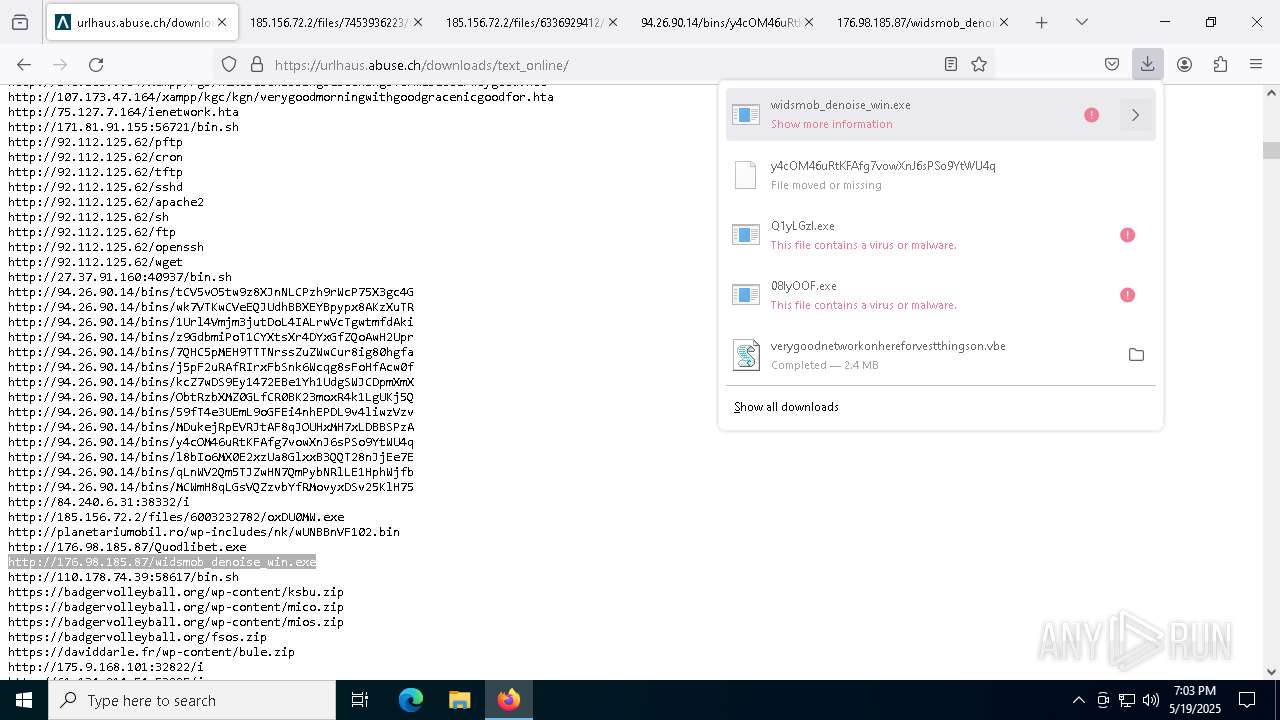
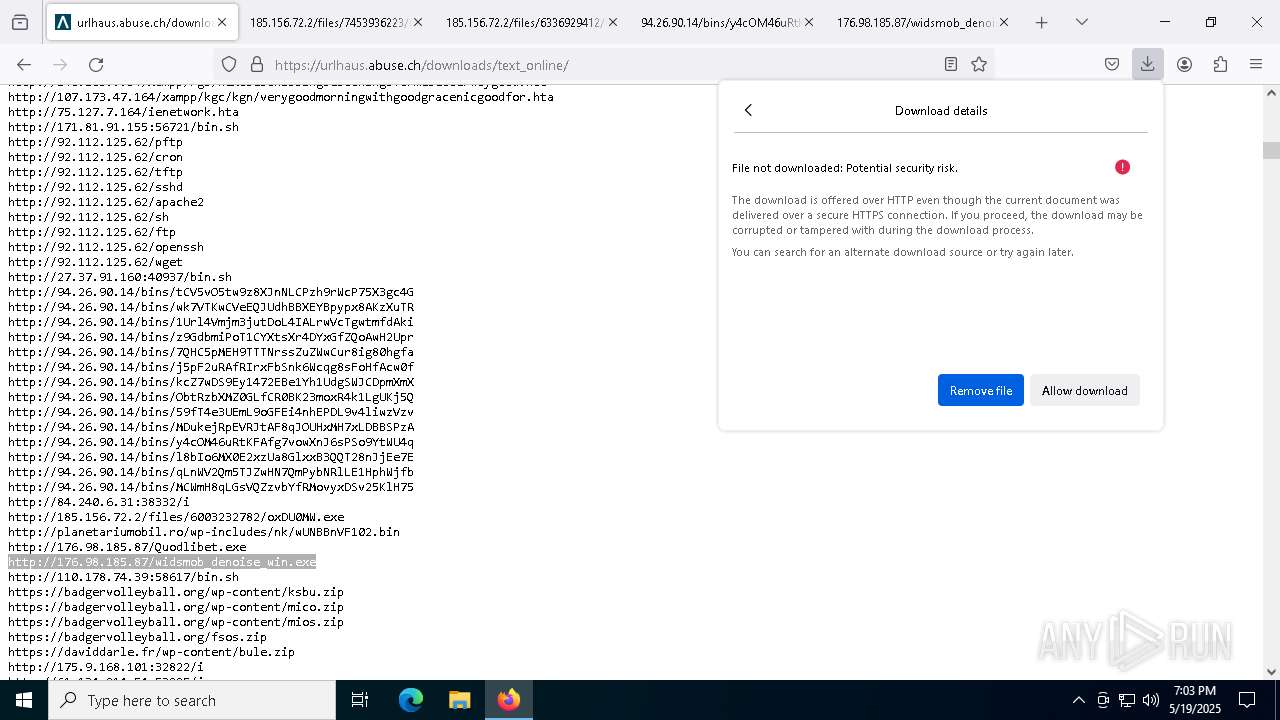
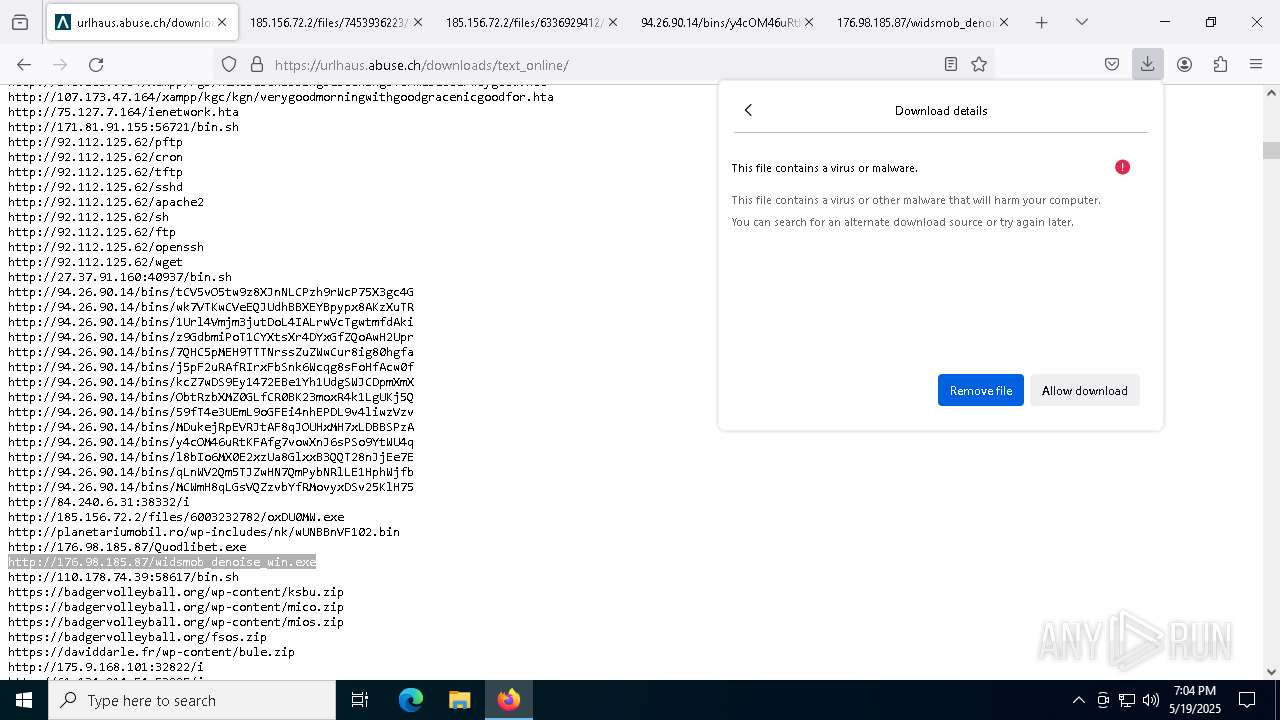
8764 | firefox.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
8764 | firefox.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
8764 | firefox.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
8764 | firefox.exe | Misc activity | ET INFO Packed Executable Download |