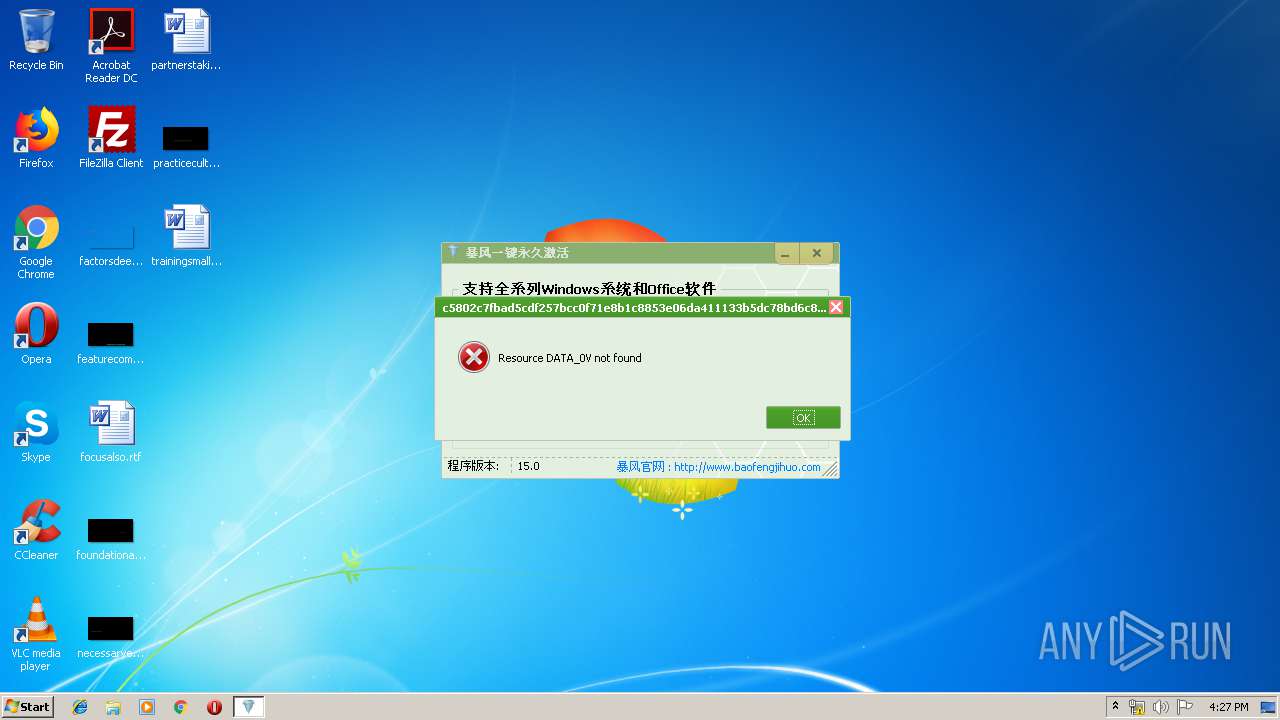
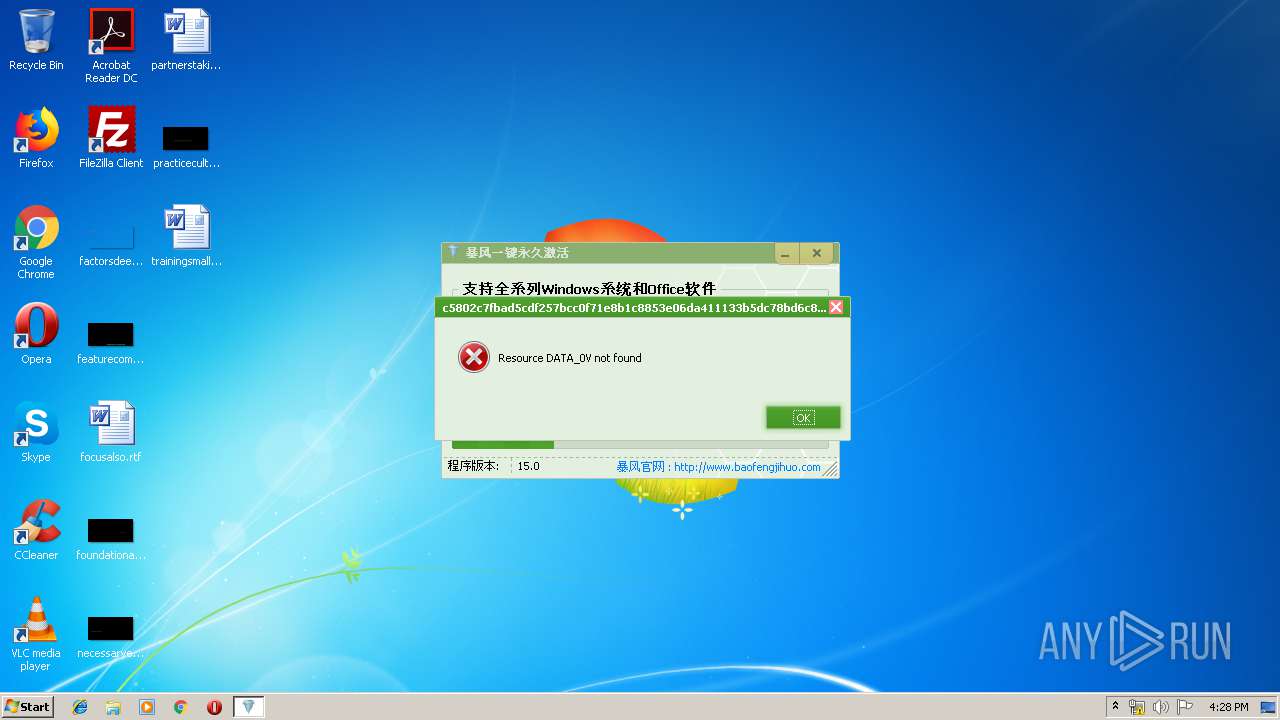
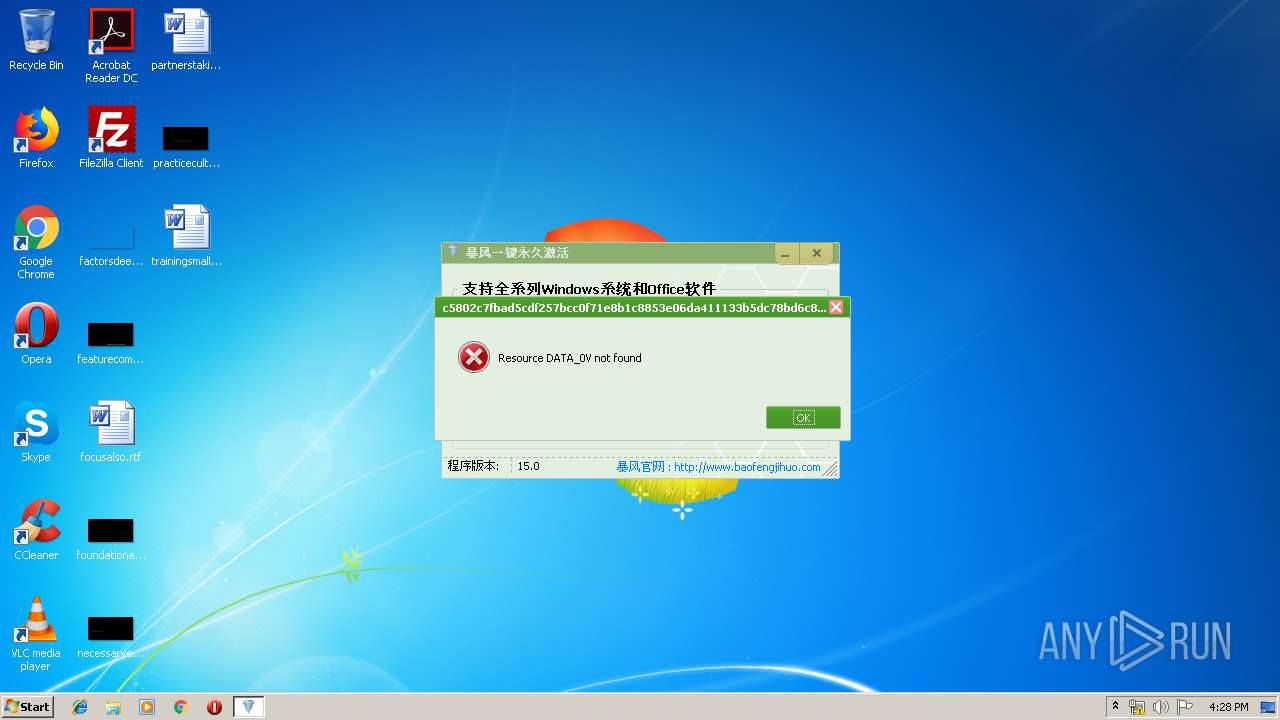
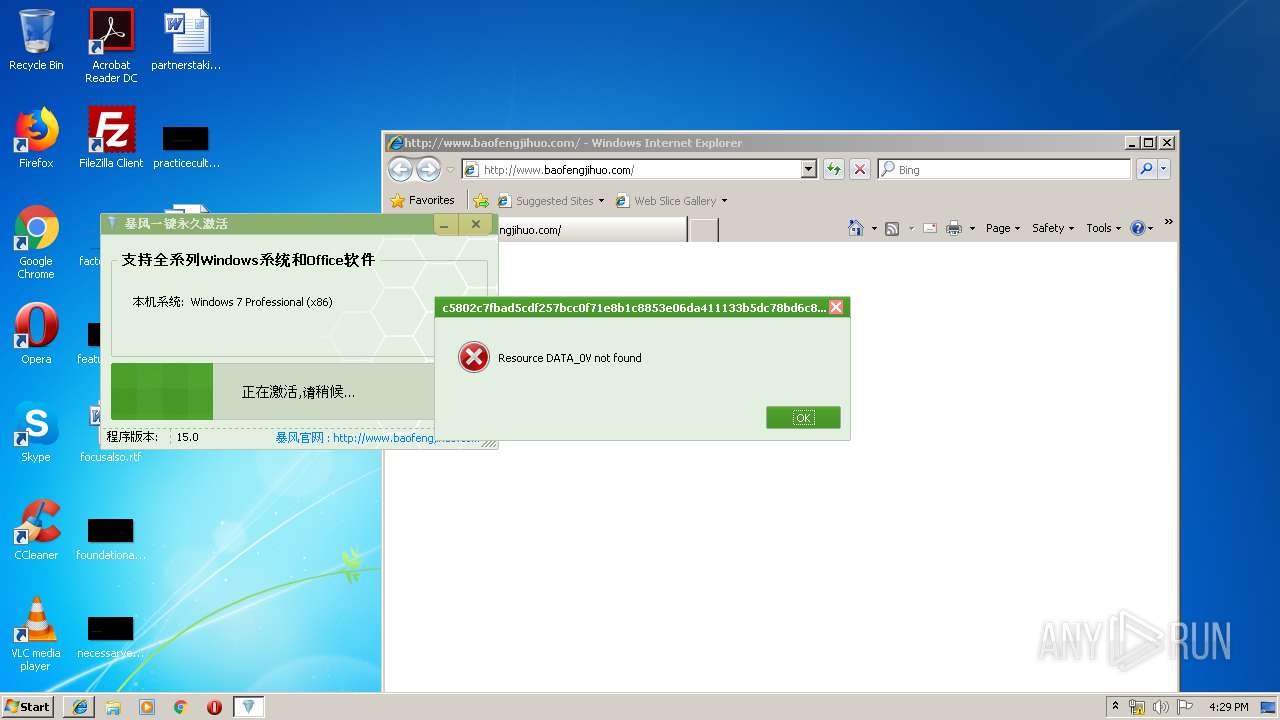
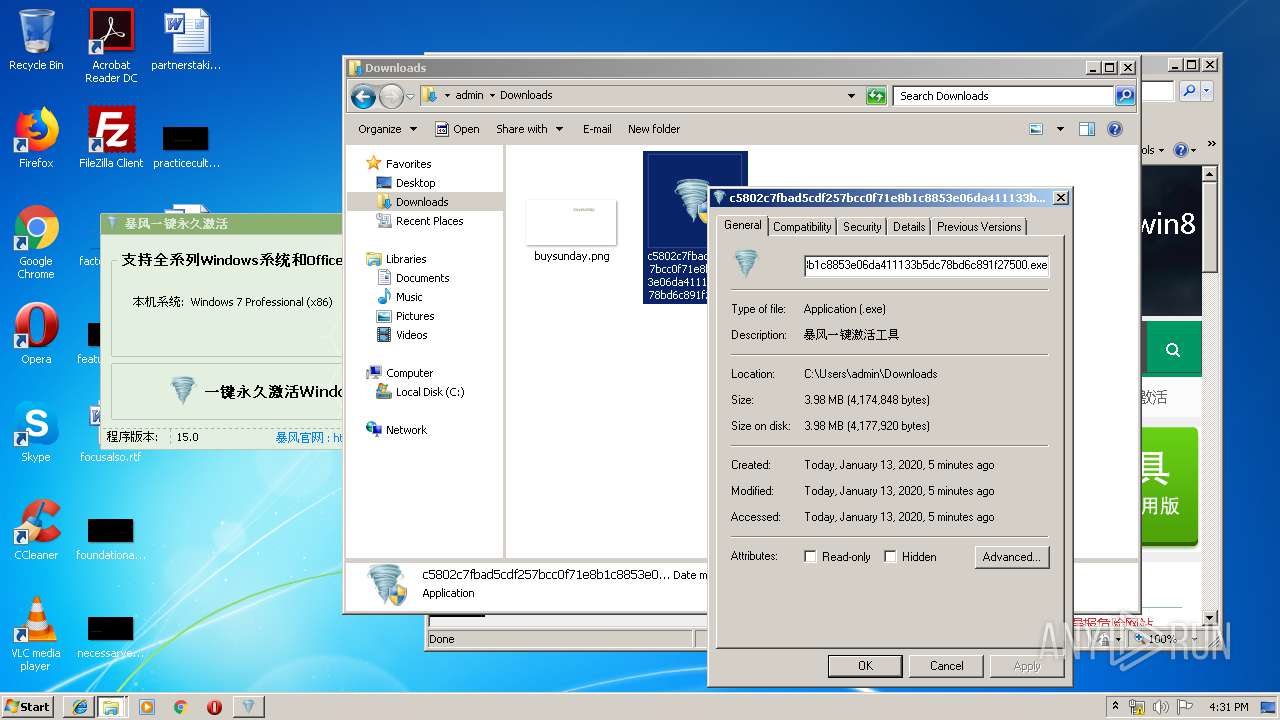
| File name: | c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500 |
| Full analysis: | https://app.any.run/tasks/6cd8df91-f293-49cc-a678-25f001041885 |
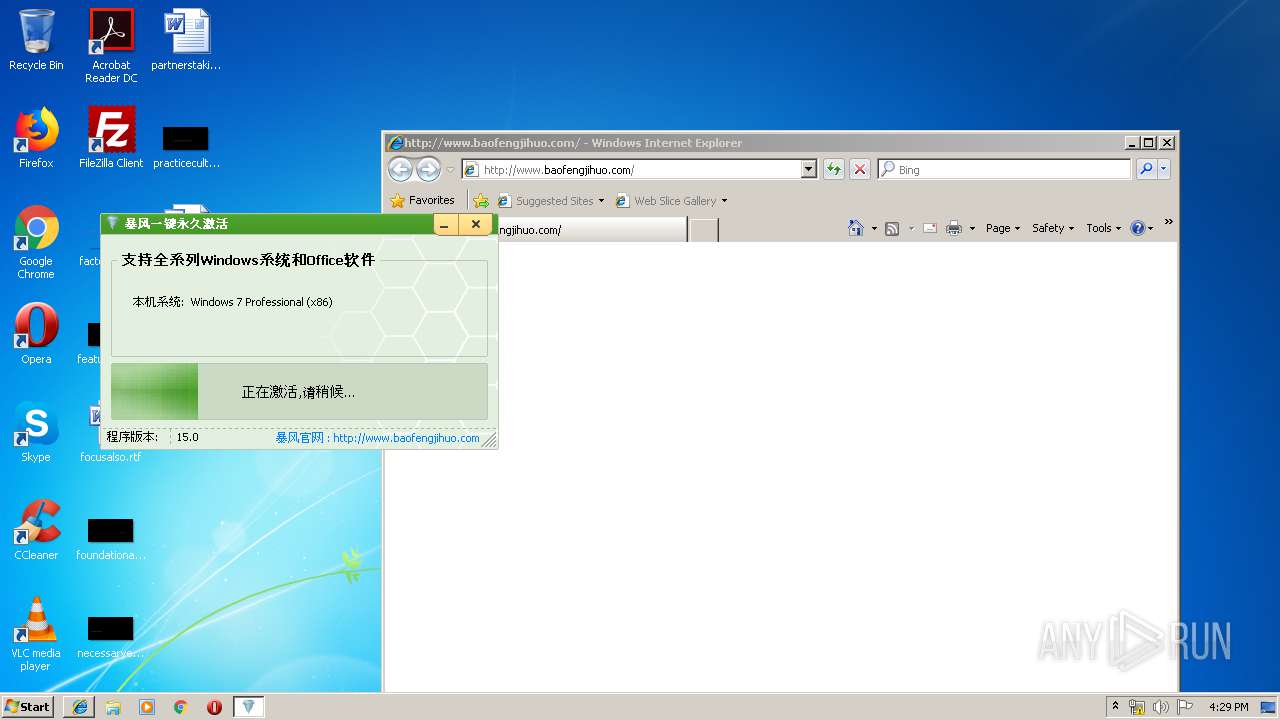
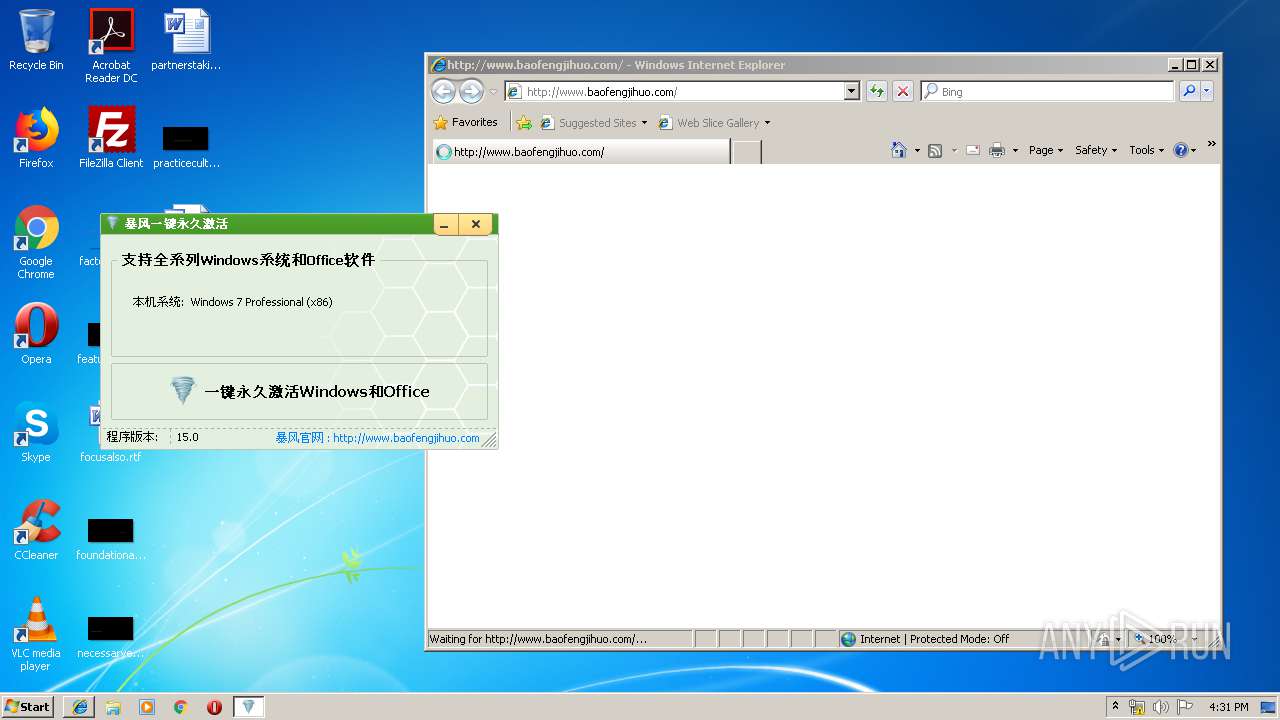
| Verdict: | Malicious activity |
| Analysis date: | January 13, 2020, 16:26:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 173B6225D42BE7ED01922F472A4BEA18 |
| SHA1: | E4449E49B8C9CB1196187F5BD12EF9322472647E |
| SHA256: | C5802C7FBAD5CDF257BCC0F71E8B1C8853E06DA411133B5DC78BD6C891F27500 |
| SSDEEP: | 98304:vJa7rV2cdCMgB3/H9DS9Jg+51ZueZwQHf4R9p82nrMgV:vJGQMgBPH9m9Xux2f+vP |
MALICIOUS
Application was dropped or rewritten from another process
- KMSService.exe (PID: 4000)
- SppExtComObjPatcher.exe (PID: 3924)
- KMSService.exe (PID: 1296)
- SppExtComObjPatcher.exe (PID: 1328)
- SppExtComObjPatcher.exe (PID: 3948)
- KMSService.exe (PID: 3352)
- SppExtComObjPatcher.exe (PID: 2572)
- KMSService.exe (PID: 1952)
Loads the Task Scheduler COM API
- OSPPSVC.EXE (PID: 236)
- OSPPSVC.EXE (PID: 1884)
- OSPPSVC.EXE (PID: 784)
- OSPPSVC.EXE (PID: 2168)
Loads dropped or rewritten executable
- OSPPSVC.EXE (PID: 236)
- OSPPSVC.EXE (PID: 1884)
- OSPPSVC.EXE (PID: 784)
- OSPPSVC.EXE (PID: 2168)
Changes Image File Execution Options
- c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe (PID: 272)
SUSPICIOUS
Uses WMIC.EXE to obtain a system information
- c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe (PID: 272)
Executable content was dropped or overwritten
- c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe (PID: 272)
Uses NETSH.EXE for network configuration
- c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe (PID: 272)
Creates files in the Windows directory
- c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe (PID: 272)
Executed as Windows Service
- KMSService.exe (PID: 4000)
- KMSService.exe (PID: 1296)
- SppExtComObjPatcher.exe (PID: 1328)
- SppExtComObjPatcher.exe (PID: 3924)
- KMSService.exe (PID: 3352)
- KMSService.exe (PID: 1952)
- SppExtComObjPatcher.exe (PID: 2572)
- SppExtComObjPatcher.exe (PID: 3948)
Executes scripts
- c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe (PID: 272)
Removes files from Windows directory
- c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe (PID: 272)
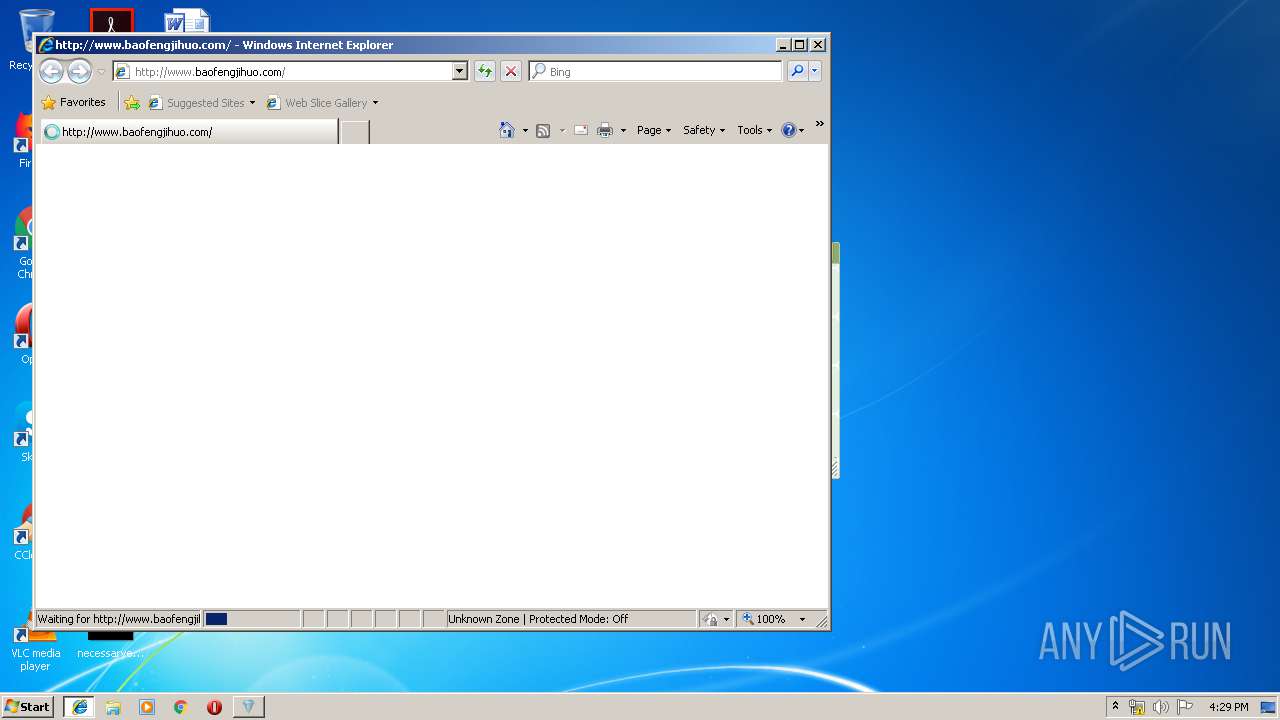
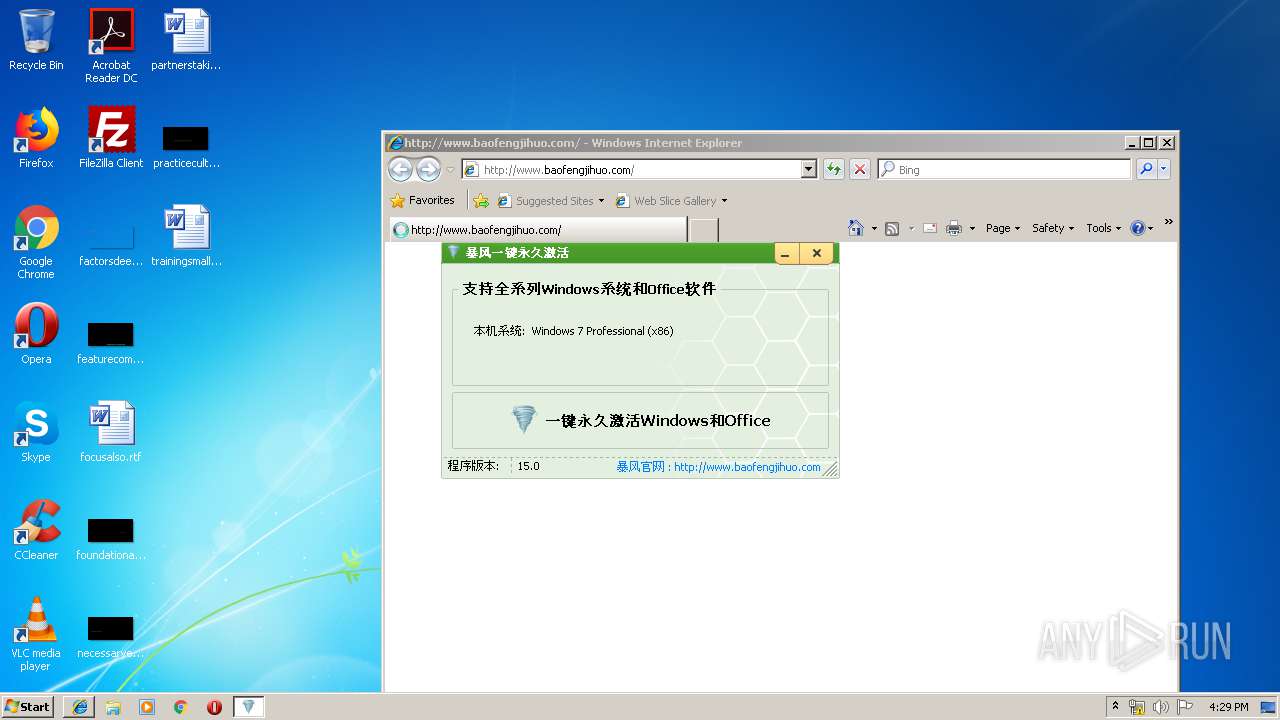
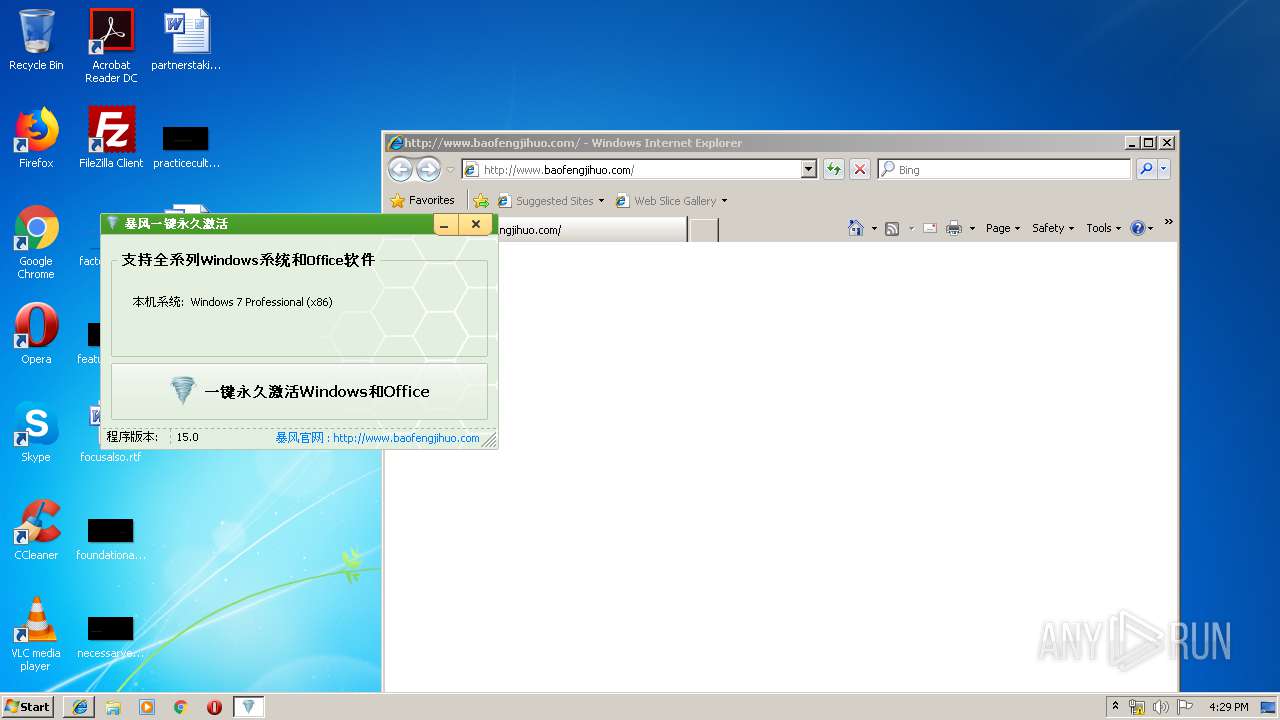
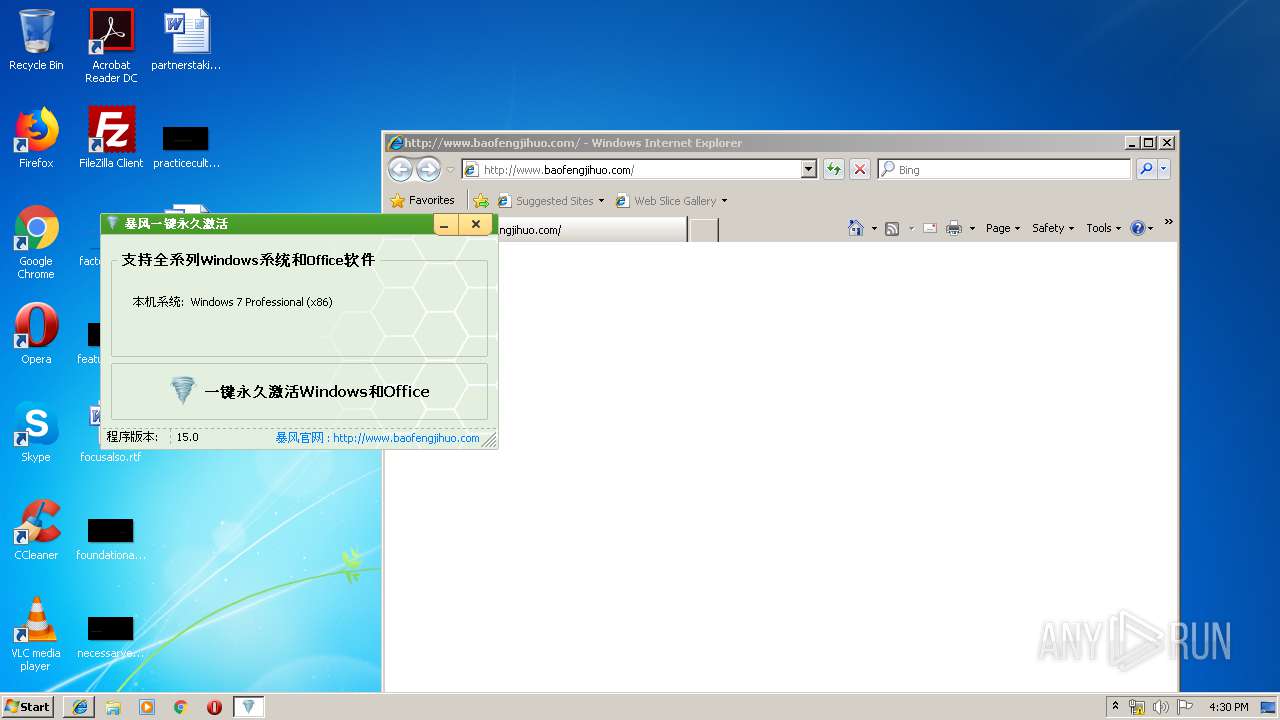
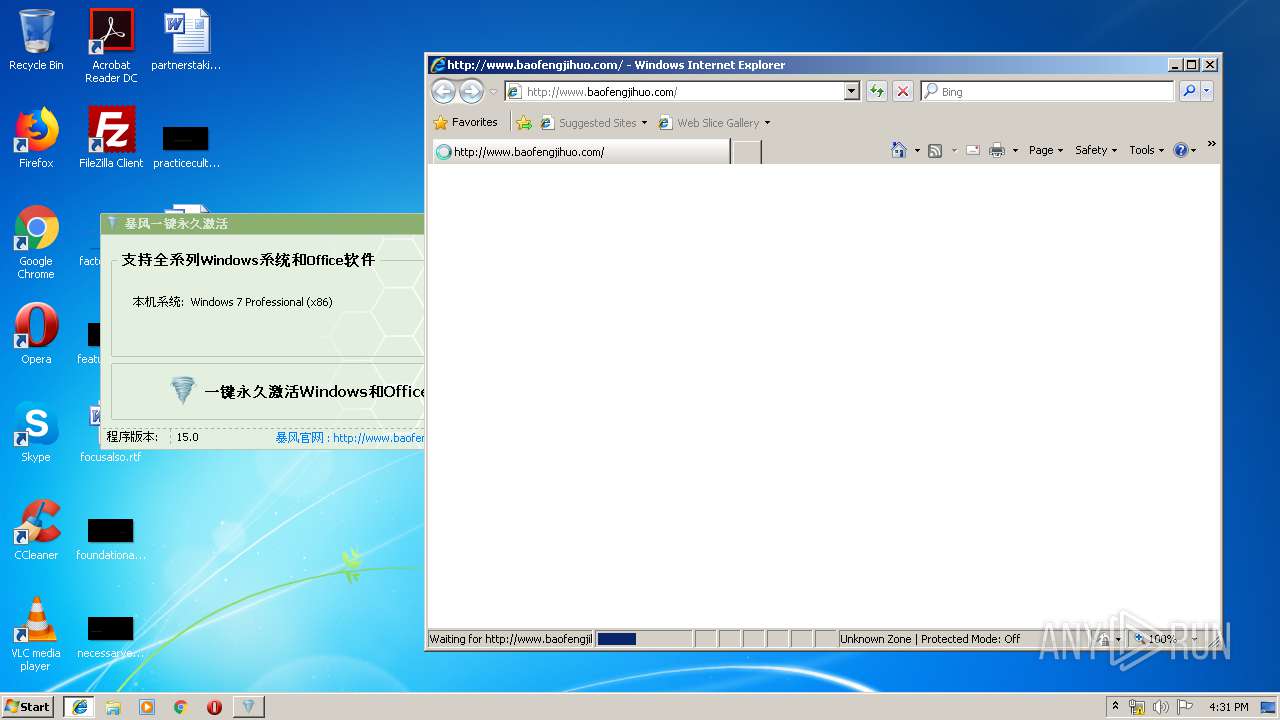
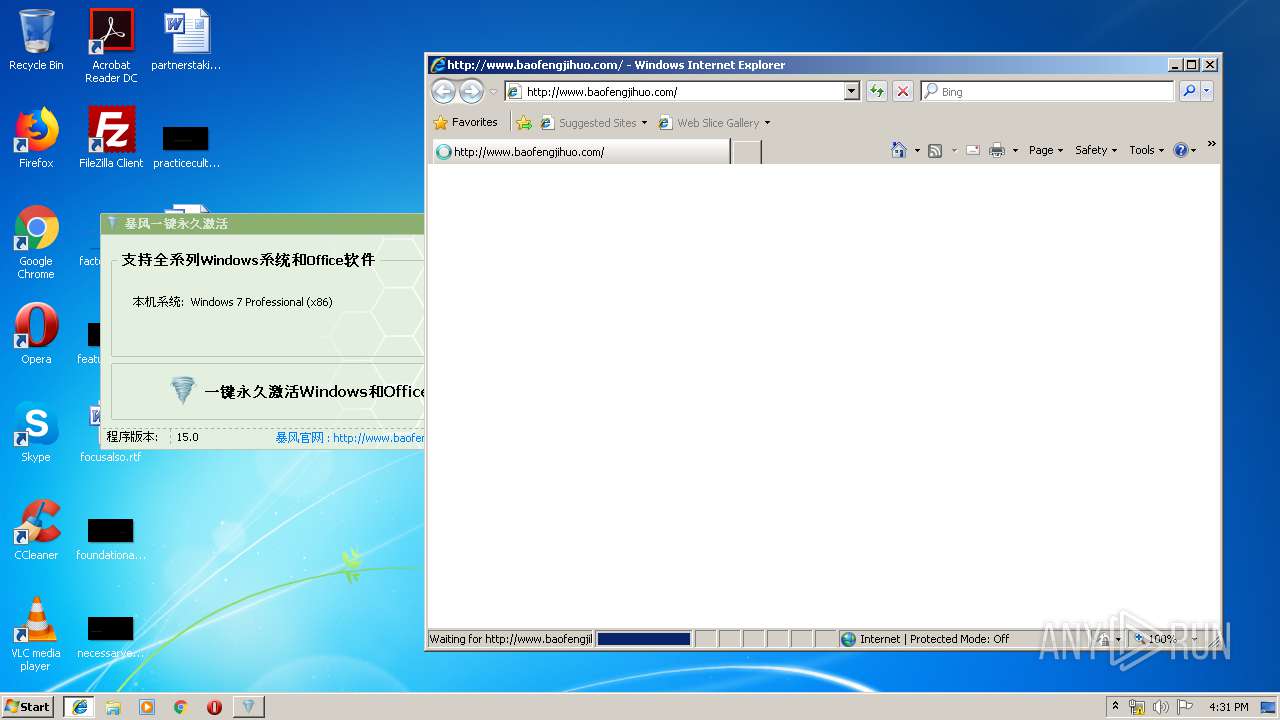
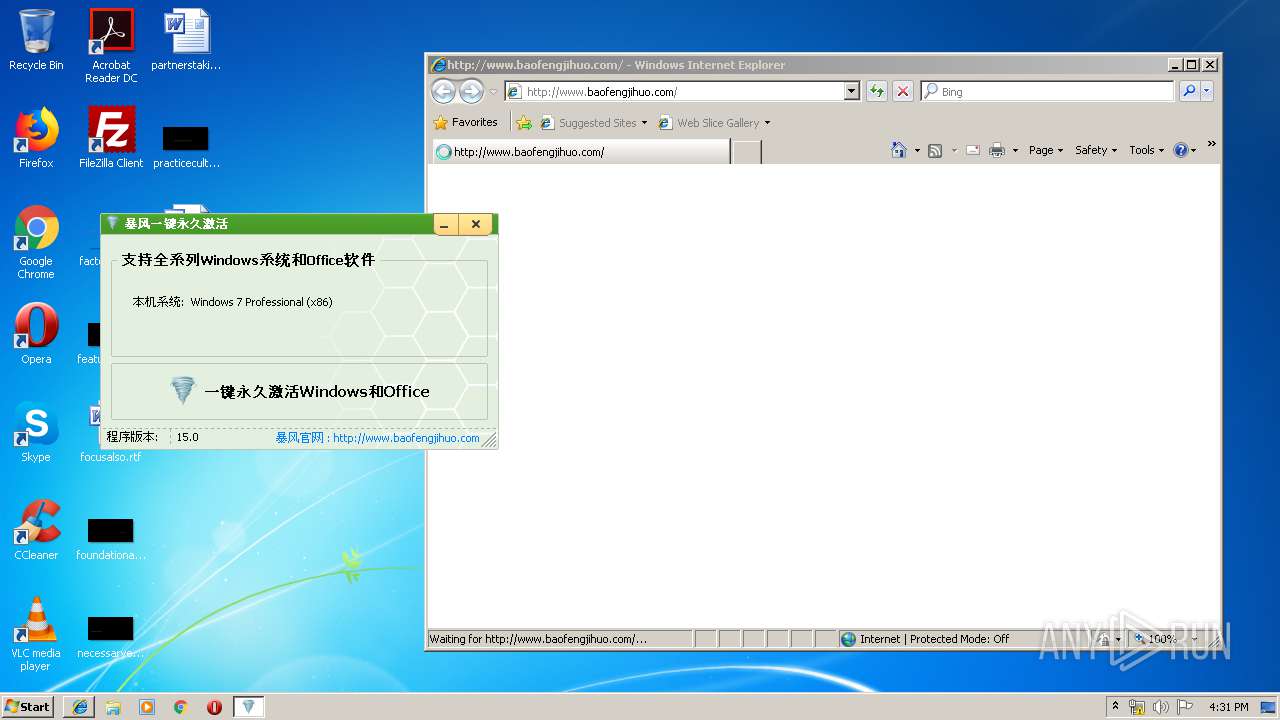
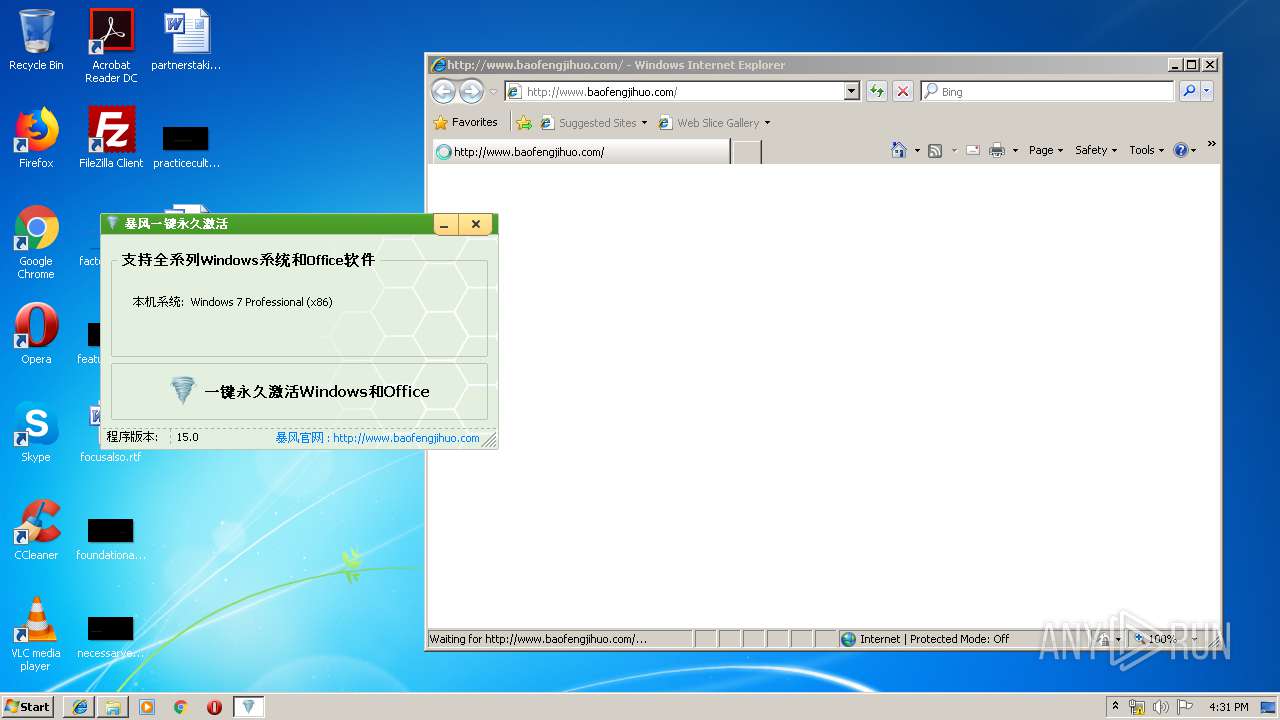
Starts Internet Explorer
- c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe (PID: 272)
INFO
Dropped object may contain Bitcoin addresses
- OSPPSVC.EXE (PID: 236)
Changes internet zones settings
- iexplore.exe (PID: 2620)
Creates files in the user directory
- iexplore.exe (PID: 3140)
Reads internet explorer settings
- iexplore.exe (PID: 3140)
Reads Internet Cache Settings
- iexplore.exe (PID: 3140)
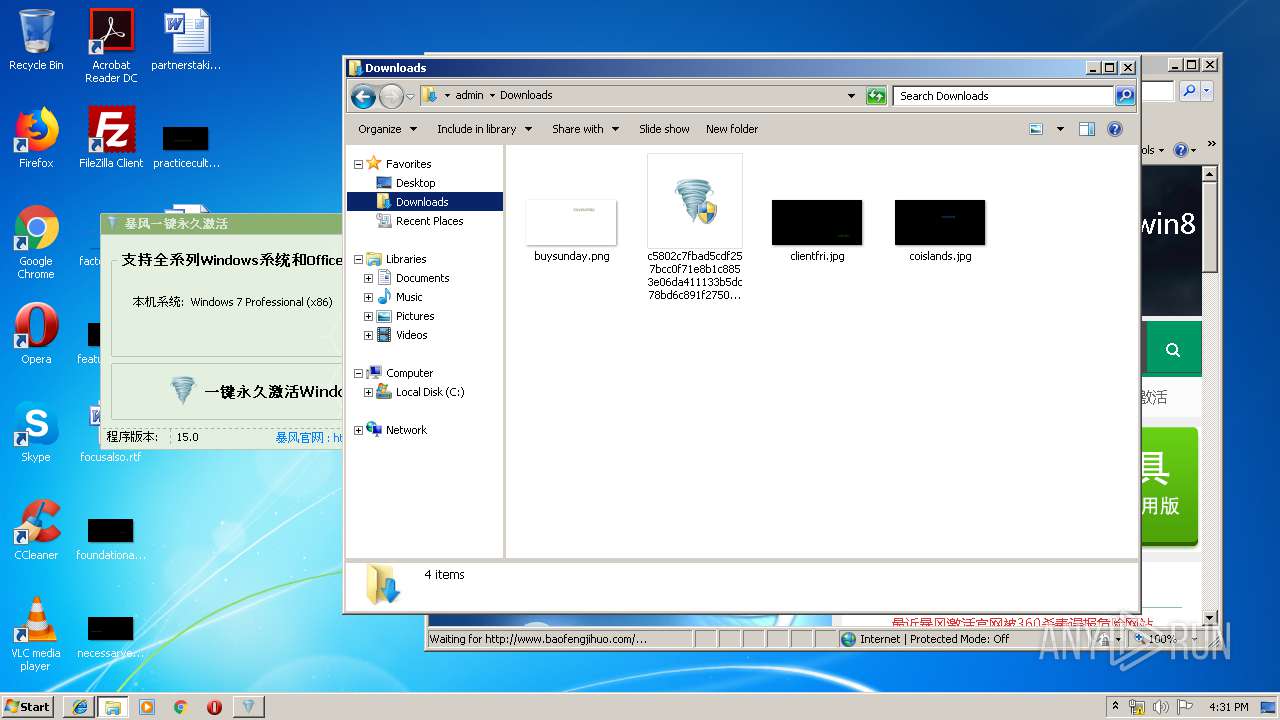
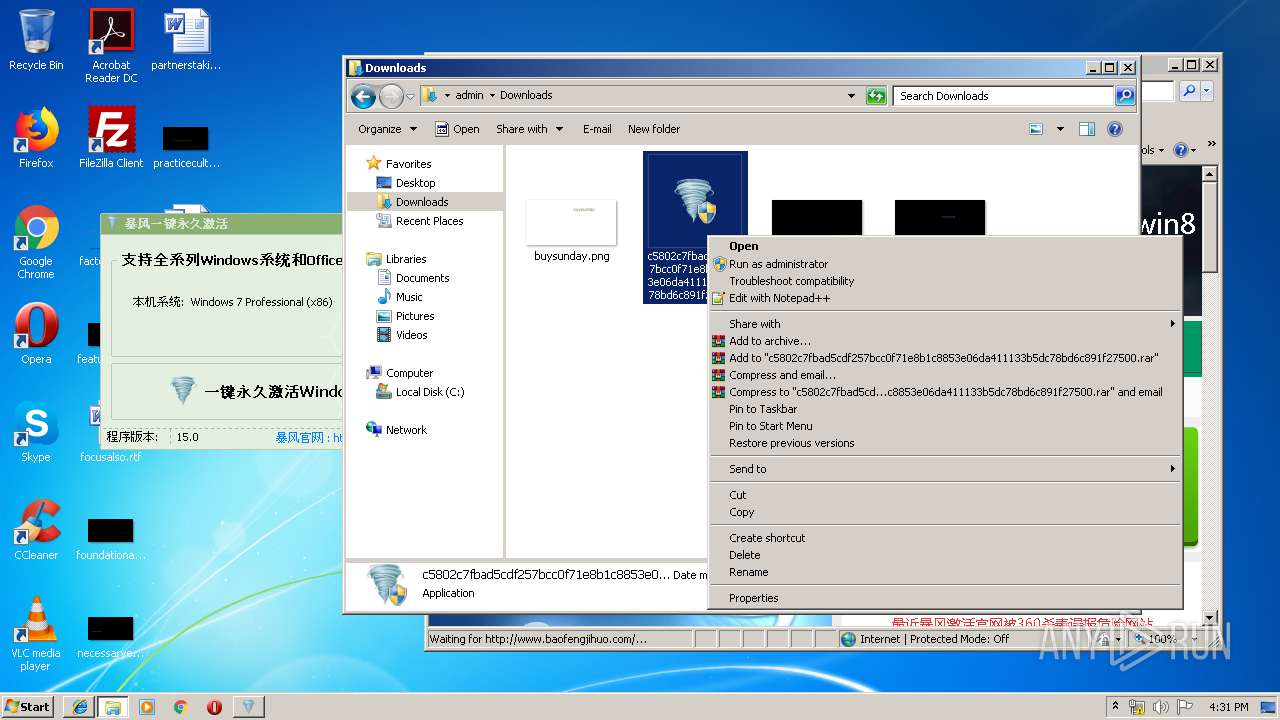
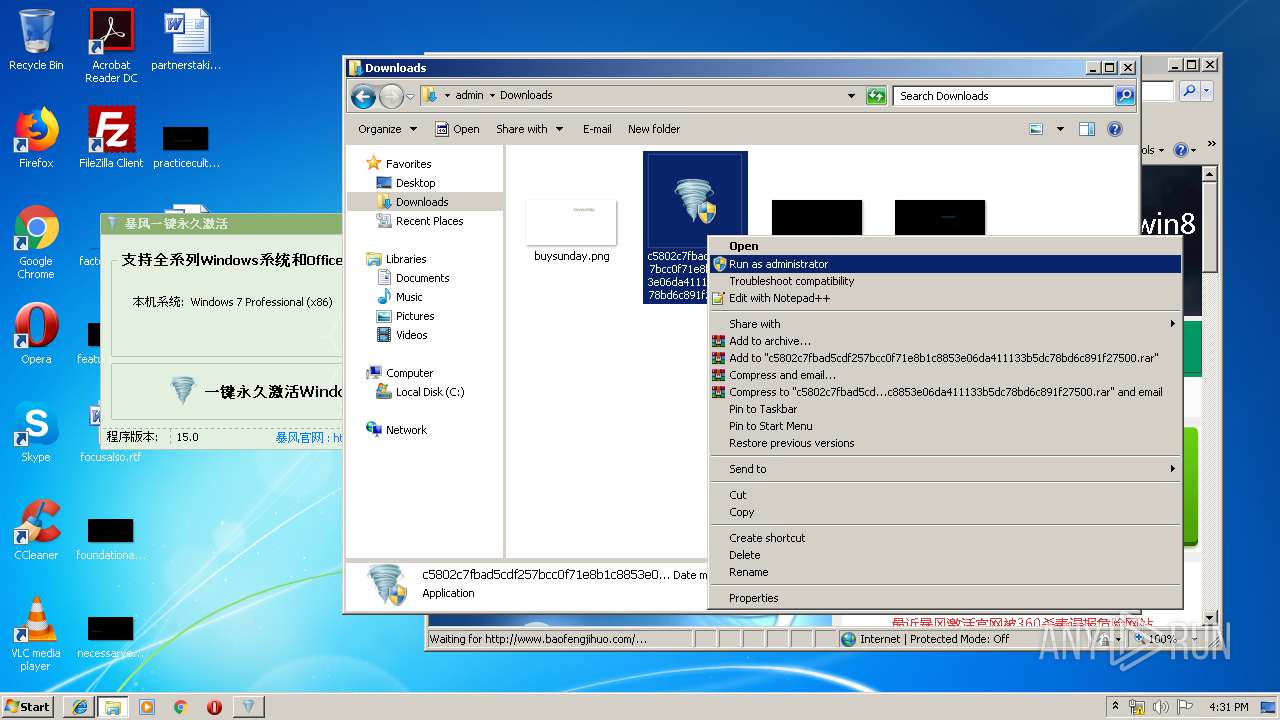
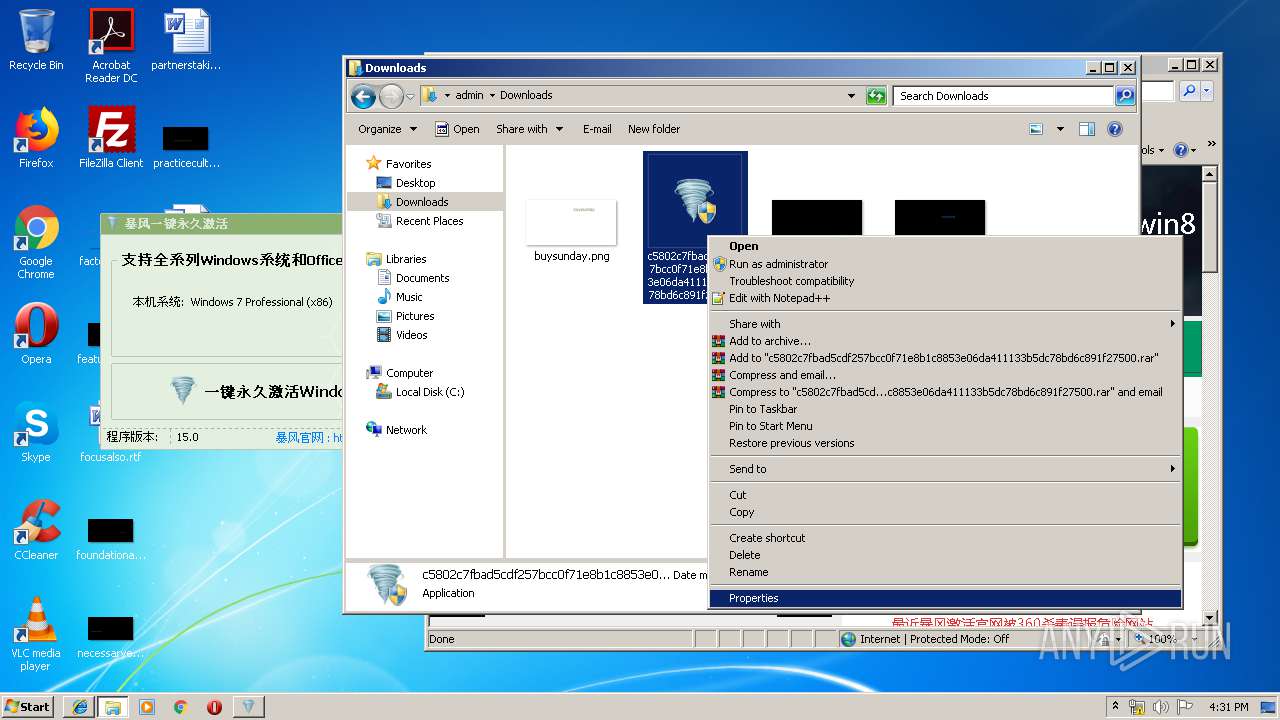
Manual execution by user
- explorer.exe (PID: 2124)
Reads settings of System Certificates
- iexplore.exe (PID: 3140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:01:13 14:19:34+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 3535360 |
| InitializedDataSize: | 1396224 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6c17ad |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
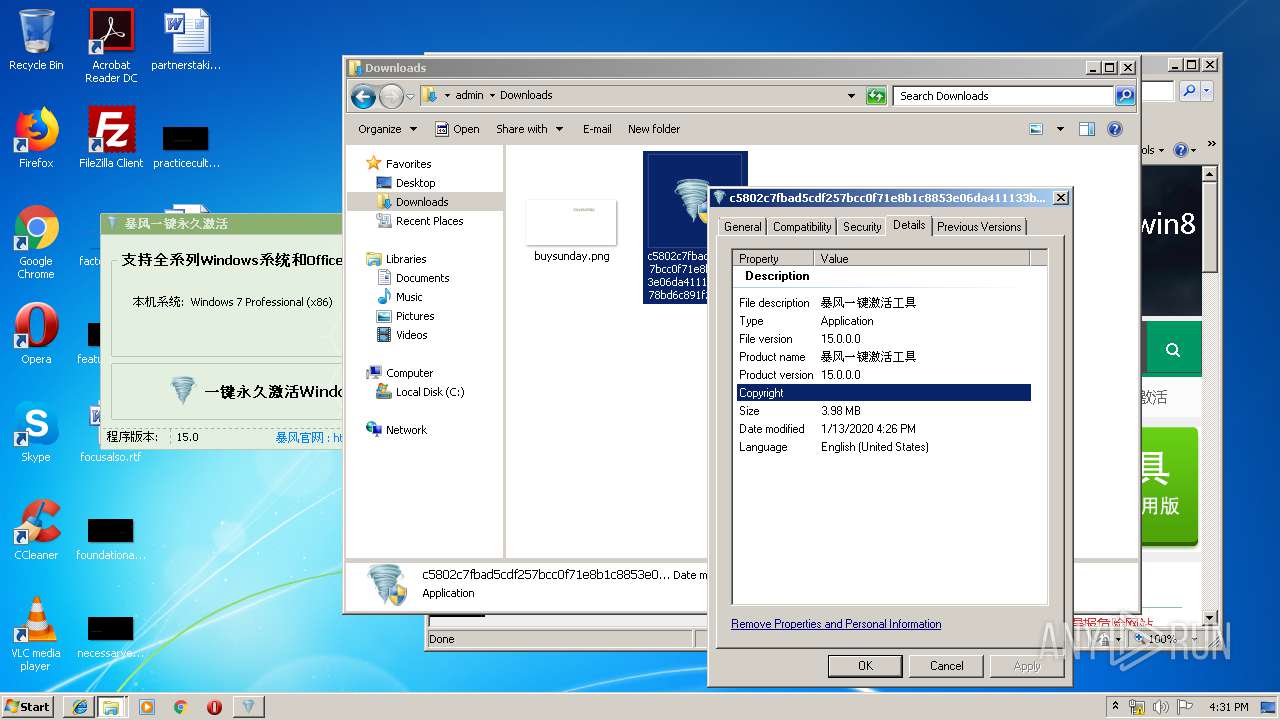
| FileVersionNumber: | 15.0.0.0 |
| ProductVersionNumber: | 15.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Pre-release |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
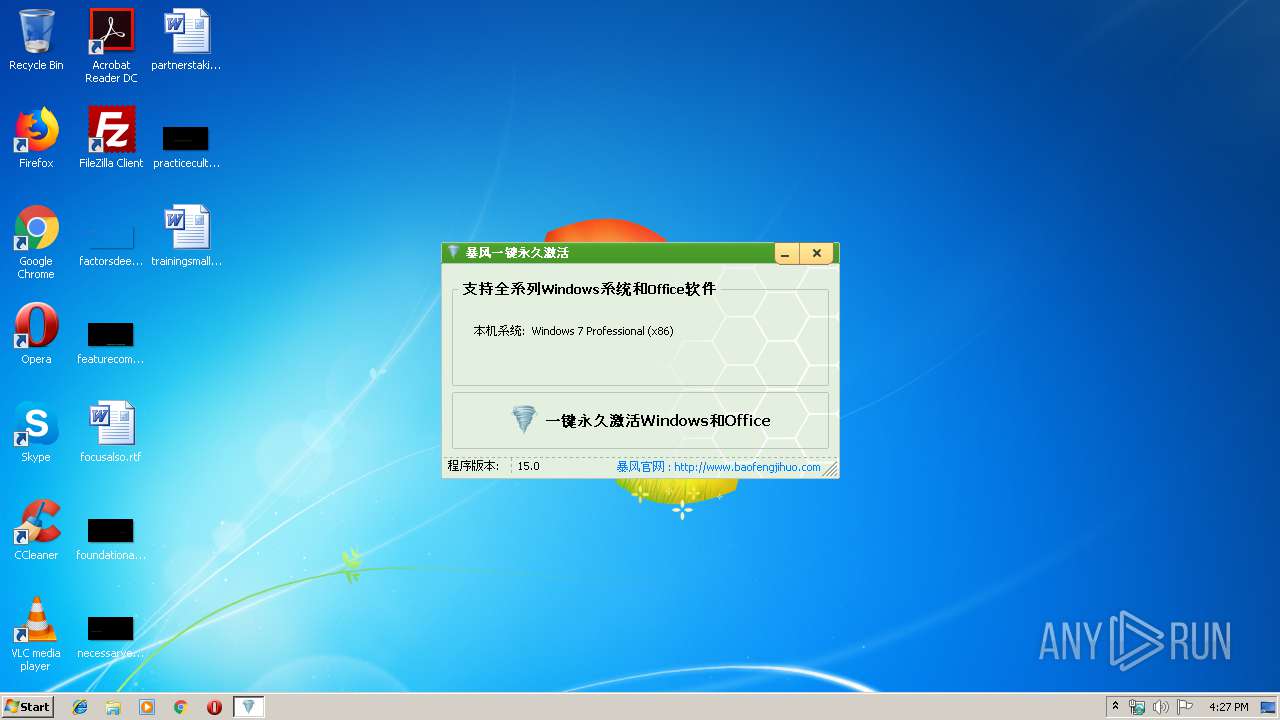
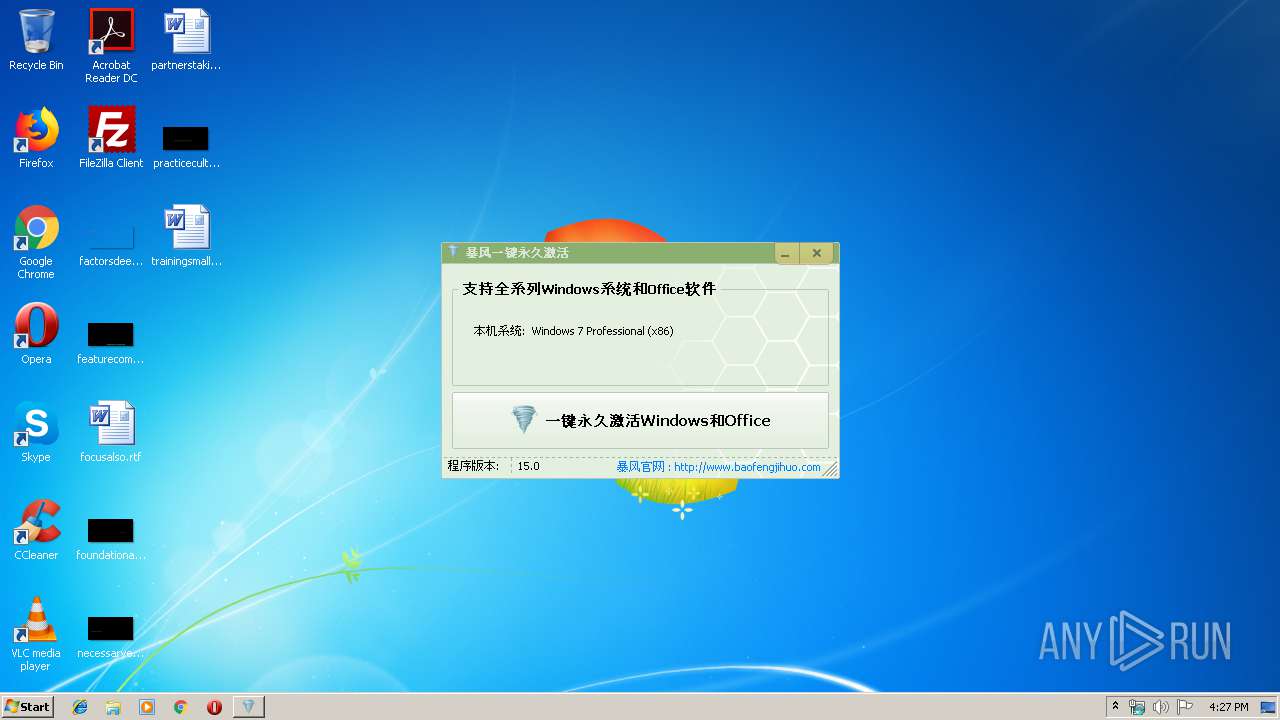
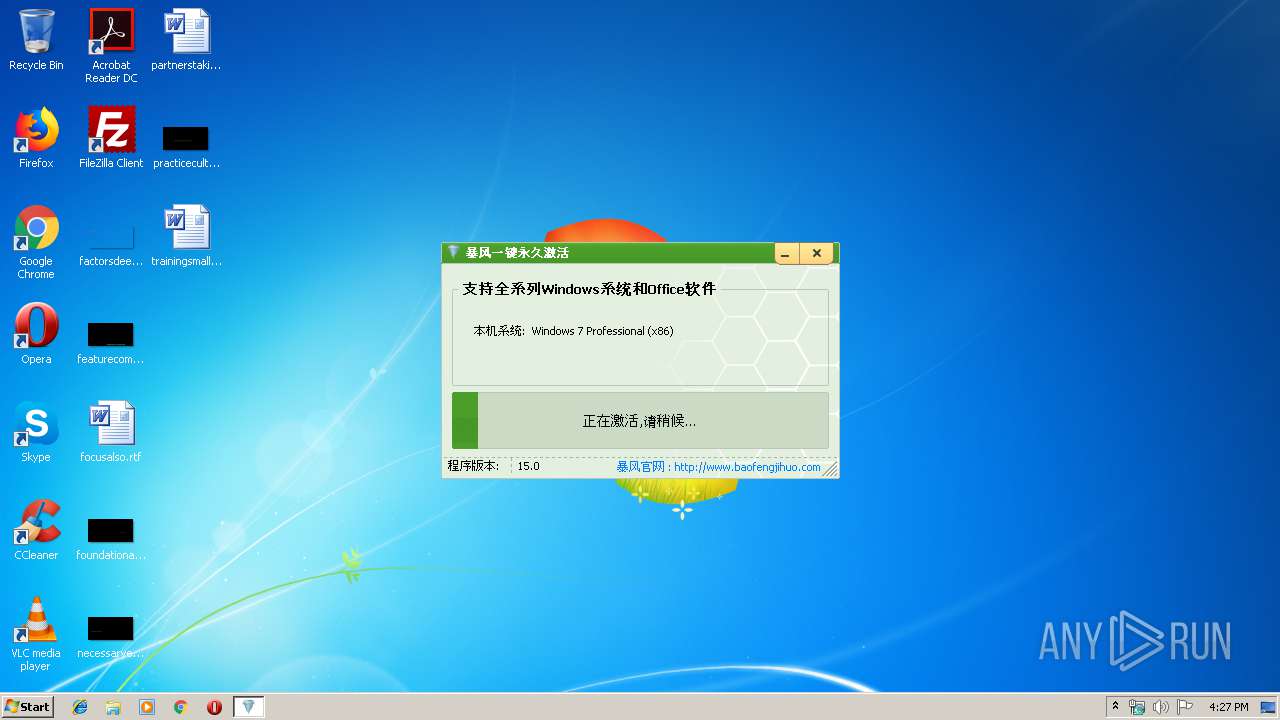
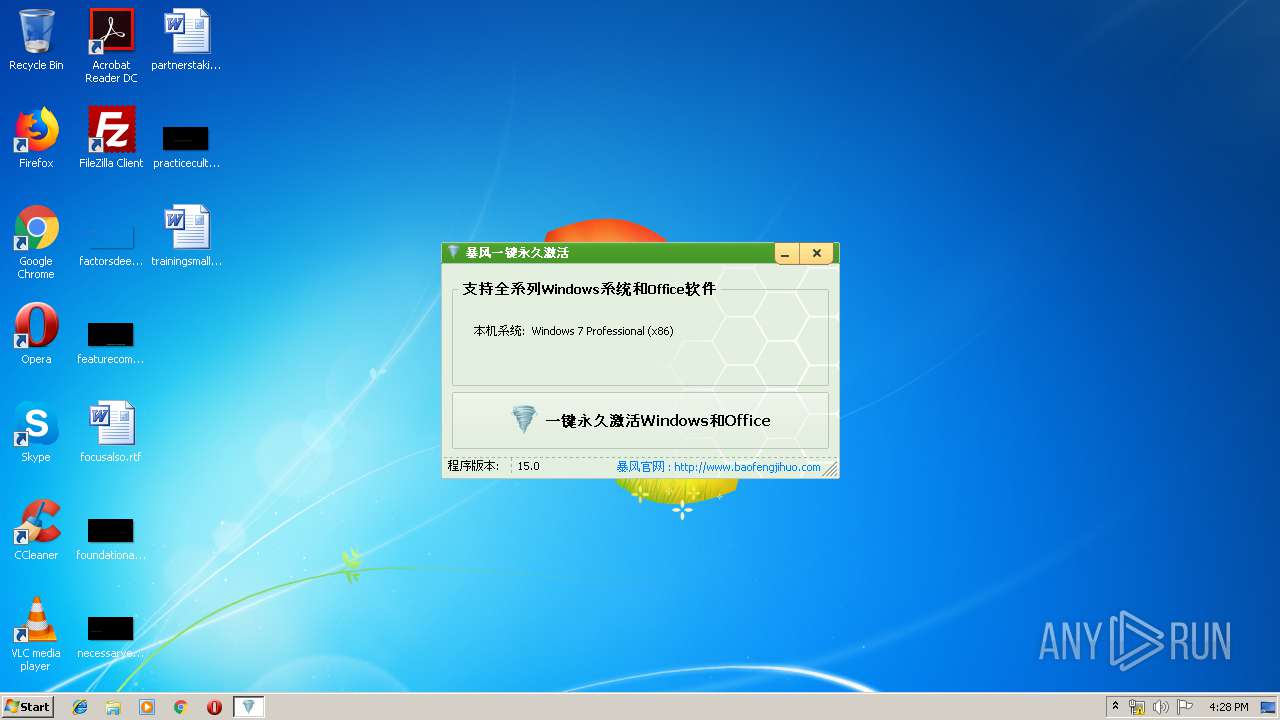
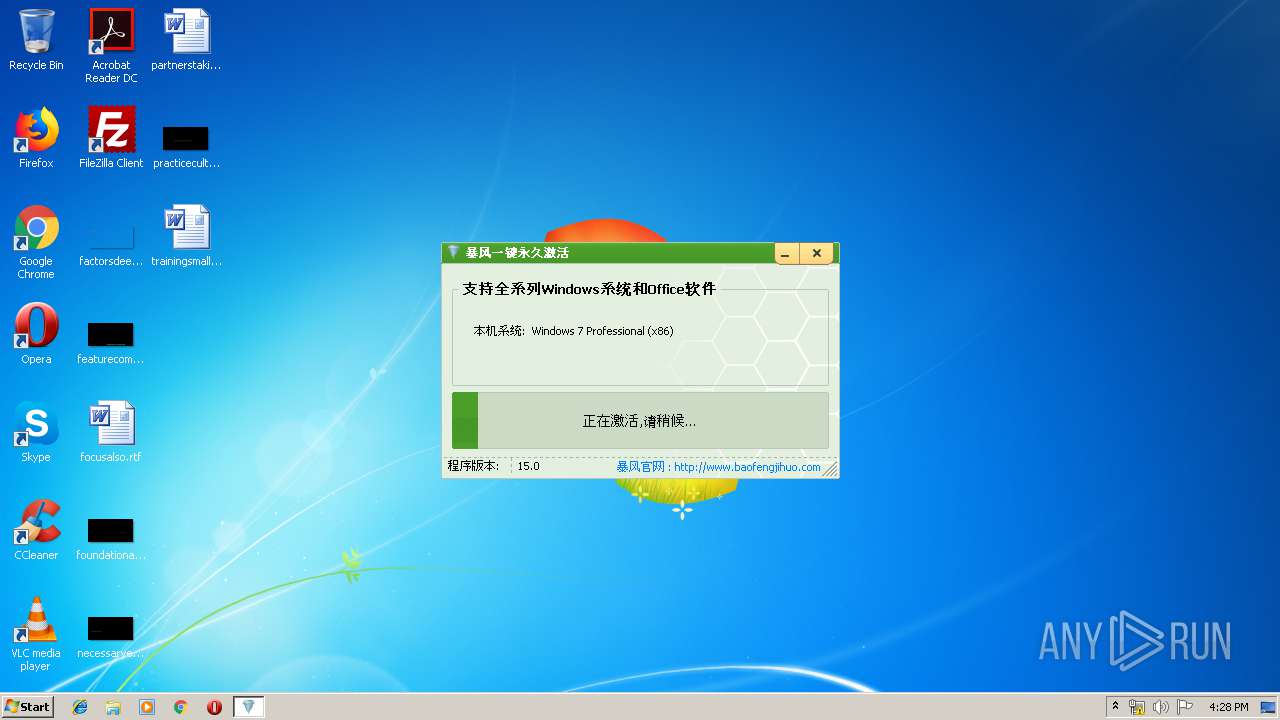
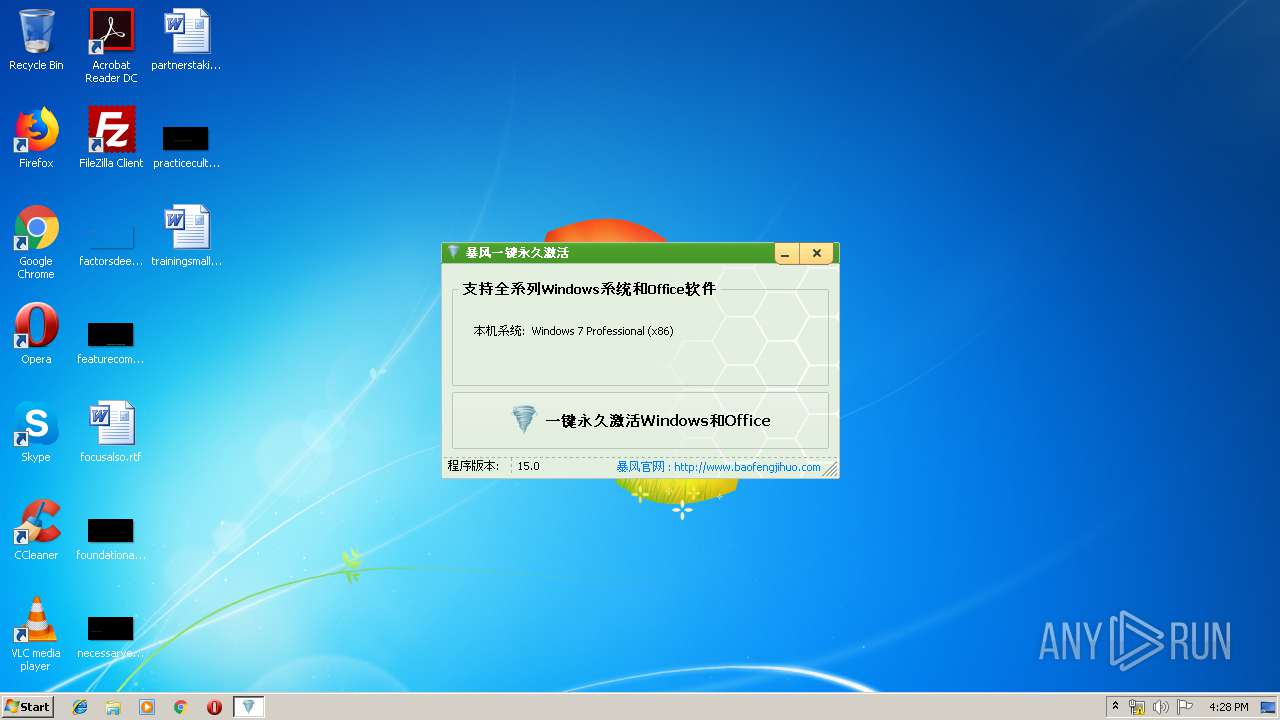
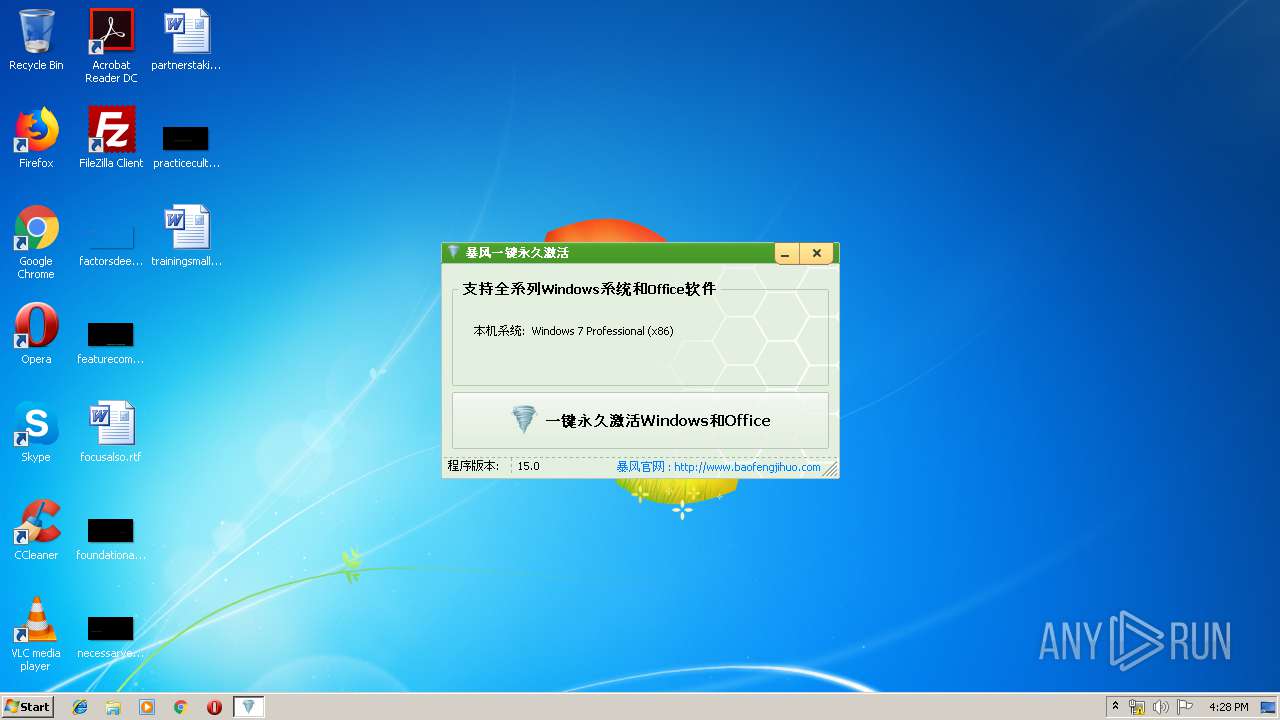
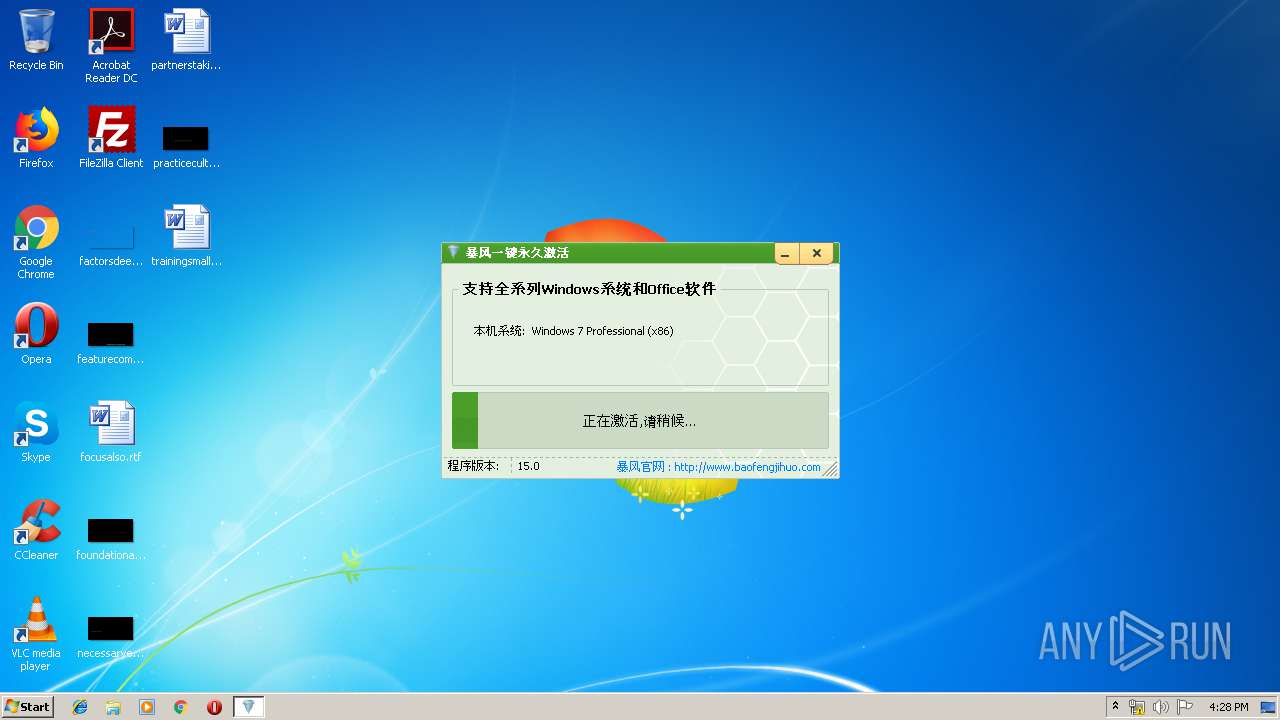
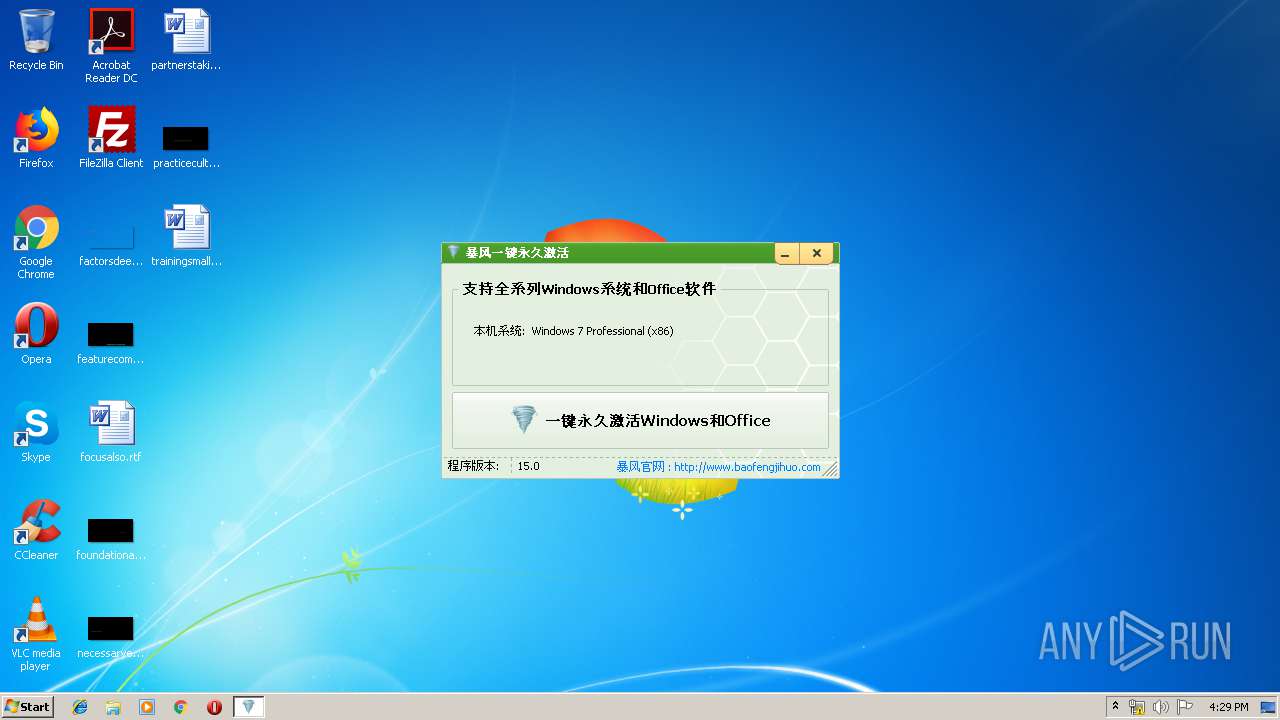
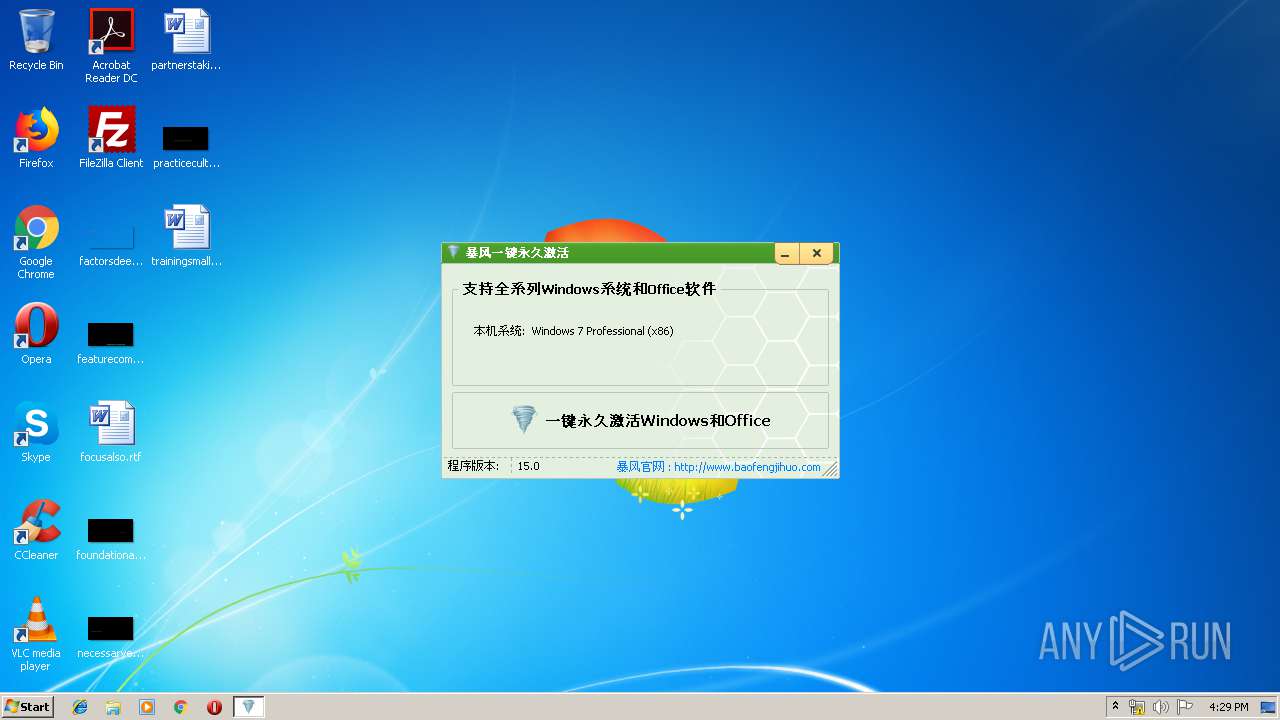
| FileDescription: | 暴风一键激活工具 |
| FileVersion: | 15.0.0.0 |
| ProductName: | 暴风一键激活工具 |
| ProductVersion: | 15.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Jan-2016 13:19:34 |
| Detected languages: |
|
| FileDescription: | 暴风一键激活工具 |
| FileVersion: | 15.0.0.0 |
| ProductName: | 暴风一键激活工具 |
| ProductVersion: | 15.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 13 |
| Time date stamp: | 13-Jan-2016 13:19:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0035C39C | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.itext | 0x0035E000 | 0x00002D8C | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.data | 0x00361000 | 0x0000D324 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.bss | 0x0036F000 | 0x00006068 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00376000 | 0x000042E4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.didata | 0x0037B000 | 0x00000A02 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.edata | 0x0037C000 | 0x00000060 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.tls | 0x0037D000 | 0x0000004C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0037E000 | 0x0000005D | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.vmp0 | 0x0037F000 | 0x00324882 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.17016 | 1679 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.89927 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 2.6295 | 296 | UNKNOWN | English - United States | RT_ICON |
4 | 3.9402 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 3.73503 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 2.19544 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 3.82119 | 16936 | UNKNOWN | English - United States | RT_ICON |
8 | 3.92603 | 9640 | UNKNOWN | English - United States | RT_ICON |
9 | 4.04992 | 4264 | UNKNOWN | English - United States | RT_ICON |
10 | 4.37912 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
msvcrt.dll |
ntdll.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
TMethodImplementationIntercept | 1 | 0x00060940 |
Total processes
127
Monitored processes
49
Malicious processes
4
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Common Files\Microsoft Shared\OfficeSoftwareProtectionPlatform\OSPPSVC.EXE" | C:\Program Files\Common Files\Microsoft Shared\OfficeSoftwareProtectionPlatform\OSPPSVC.EXE | — | SppExtComObjPatcher.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Office Software Protection Platform Service Exit code: 0 Version: 14.0.0370.400 (longhorn(wmbla).090811-1833) Modules
| |||||||||||||||
| 272 | "C:\Users\admin\Downloads\c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe" | C:\Users\admin\Downloads\c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 暴风一键激活工具 Exit code: 0 Version: 15.0.0.0 Modules
| |||||||||||||||
| 324 | cscript "C:\Program Files\Microsoft Office\Office14\\ospp.vbs" /dstatus | C:\Windows\system32\cscript.exe | — | c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 496 | wmic path SoftwareLicensingProduct where (Description like '%%KMSCLIENT%%') get Name /value | C:\Windows\System32\Wbem\wmic.exe | — | c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 516 | netsh firewall add allowedprogram "C:\Windows\KMSService.exe" "vlmcsd" | C:\Windows\system32\netsh.exe | — | c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 592 | wmic path SoftwareLicensingService where version='6.1.7601.17514' call SetKeyManagementServiceMachine MachineName="127.0.0.2" | C:\Windows\System32\Wbem\wmic.exe | — | c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 600 | netsh firewall delete allowedprogram "C:\Windows\KMSService.exe" | C:\Windows\system32\netsh.exe | — | c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 784 | "C:\Program Files\Common Files\Microsoft Shared\OfficeSoftwareProtectionPlatform\OSPPSVC.EXE" | C:\Program Files\Common Files\Microsoft Shared\OfficeSoftwareProtectionPlatform\OSPPSVC.EXE | — | SppExtComObjPatcher.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Office Software Protection Platform Service Exit code: 0 Version: 14.0.0370.400 (longhorn(wmbla).090811-1833) Modules
| |||||||||||||||
| 892 | wmic path SoftwareLicensingService where version='6.1.7601.17514' call SetKeyManagementServiceMachine MachineName="127.0.0.2" | C:\Windows\System32\Wbem\wmic.exe | — | c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 996 | netsh firewall add allowedprogram "C:\Windows\KMSService.exe" "vlmcsd" | C:\Windows\system32\netsh.exe | — | c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 872
Read events
1 391
Write events
480
Delete events
1
Modification events
| (PID) Process: | (3364) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3364) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (3364) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (3364) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (3364) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (3364) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (3364) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (3364) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
| (PID) Process: | (3364) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-3 |
Value: Microsoft Corporation | |||
| (PID) Process: | (3364) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\tsgqec.dll,-100 |
Value: RD Gateway Quarantine Enforcement Client | |||
Executable files
3
Suspicious files
1
Text files
55
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2620 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 272 | c5802c7fbad5cdf257bcc0f71e8b1c8853e06da411133b5dc78bd6c891f27500.exe | C:\Windows\system32\SppExtComObjPatcher.exe | executable | |
MD5:1DDFC527908F15ADA9081E5C18A5FA7E | SHA256:E932C1E22511B73365C45C9E05993344378025B5555477314E530CD8172FAA1B | |||
| 3140 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\jquery.min[1].js | text | |
MD5:3576A6E73C9DCCDBBC4A2CF8FF544AD7 | SHA256:61C6CAEBD23921741FB5FFE6603F16634FCA9840C2BF56AC8201E9264D6DACCF | |||
| 3140 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\style.min[1].css | text | |
MD5:375BD65D60FF3C8723FCCC343AFB1B9B | SHA256:4B8FE5C3D0E5EF7A6582185CBF5C535B5D369C8DF1DA98C03ED69833E55F474D | |||
| 3140 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\baofengjihuo_com[1].htm | html | |
MD5:— | SHA256:— | |||
| 3140 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3140 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\logo[1].png | image | |
MD5:— | SHA256:— | |||
| 3140 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\timthumb[1].jpg | image | |
MD5:— | SHA256:— | |||
| 3140 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\fontawesome-webfont[1].eot | eot | |
MD5:90186830C9C50A0FED932494581761D9 | SHA256:9F8288933D2C87AB3CDBDBDA5C9FA1E1E139B01C7C1D1983F91A13BE85173975 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
21
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3140 | iexplore.exe | GET | — | 103.122.94.235:80 | http://www.baofengjihuo.com/wp-content/themes/Git/style.css?ver=1.0 | unknown | — | — | malicious |
3140 | iexplore.exe | GET | 206 | 103.122.94.235:80 | http://www.baofengjihuo.com/wp-content/themes/Git/style.css?ver=1.0 | unknown | text | 120 Kb | malicious |
3140 | iexplore.exe | GET | 200 | 103.122.94.235:80 | http://www.baofengjihuo.com/ | unknown | html | 8.60 Kb | malicious |
3140 | iexplore.exe | GET | 200 | 103.122.94.235:80 | http://www.baofengjihuo.com/wp-content/themes/Git/timthumb.php?src=http://www.baofengjihuo.com/wp-content/uploads/2015/12/2016071815532736.png&h=110&w=185&q=90&zc=1&ct=1 | unknown | image | 25.1 Kb | malicious |
3140 | iexplore.exe | GET | 200 | 103.122.94.235:80 | http://www.baofengjihuo.com/wp-content/themes/Git/timthumb.php?src=http://www.baofengjihuo.com/wp-content/uploads/2016/08/201608071525176.jpg&h=110&w=185&q=90&zc=1&ct=1 | unknown | image | 8.69 Kb | malicious |
3140 | iexplore.exe | GET | 200 | 220.181.38.193:80 | http://znsv.baidu.com/customer_search/api/js?sid=1744800458304071801&plate_url=http%3A%2F%2Fwww.baofengjihuo.com%2F&t=438593 | CN | text | 36.6 Kb | whitelisted |
3140 | iexplore.exe | GET | 200 | 103.122.94.235:80 | http://www.baofengjihuo.com/wp-content/themes/Git/timthumb.php?src=http://www.baofengjihuo.com/wp-content/uploads/2016/12/201612021107111.jpg&h=110&w=185&q=90&zc=1&ct=1 | unknown | image | 5.56 Kb | malicious |
3140 | iexplore.exe | GET | 200 | 103.122.94.20:80 | http://www.win10dashi.com/d/file/p/2019/05-13/842a1bede855a850ec6c420d91b4ad07.jpg | unknown | image | 82.8 Kb | suspicious |
3140 | iexplore.exe | GET | 200 | 103.122.94.20:80 | http://www.win10dashi.com/d/file/p/2019/05-13/74fe93ff68af52d1bc29bb411c97b409.jpg | unknown | image | 58.9 Kb | suspicious |
3140 | iexplore.exe | GET | 200 | 103.122.94.235:80 | http://www.baofengjihuo.com/wp-includes/css/dist/block-library/style.min.css?ver=5.2.5 | unknown | text | 28.6 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2620 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3140 | iexplore.exe | 220.181.38.193:80 | znsv.baidu.com | IDC, China Telecommunications Corporation | CN | unknown |
— | — | 103.122.94.235:80 | www.baofengjihuo.com | — | — | unknown |
3140 | iexplore.exe | 103.122.94.20:80 | www.win10dashi.com | — | — | suspicious |
3140 | iexplore.exe | 119.96.207.121:80 | s4.cnzz.com | No.31,Jin-rong Street | CN | unknown |
3140 | iexplore.exe | 203.119.213.181:80 | z11.cnzz.com | — | CN | unknown |
— | — | 119.96.207.121:80 | s4.cnzz.com | No.31,Jin-rong Street | CN | unknown |
3140 | iexplore.exe | 103.235.46.191:443 | hm.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | suspicious |
3140 | iexplore.exe | 103.122.94.235:80 | www.baofengjihuo.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.baofengjihuo.com |
| malicious |
www.bing.com |
| whitelisted |
www.win10dashi.com |
| suspicious |
znsv.baidu.com |
| whitelisted |
hm.baidu.com |
| whitelisted |
s4.cnzz.com |
| whitelisted |
z11.cnzz.com |
| whitelisted |
c.cnzz.com |
| whitelisted |