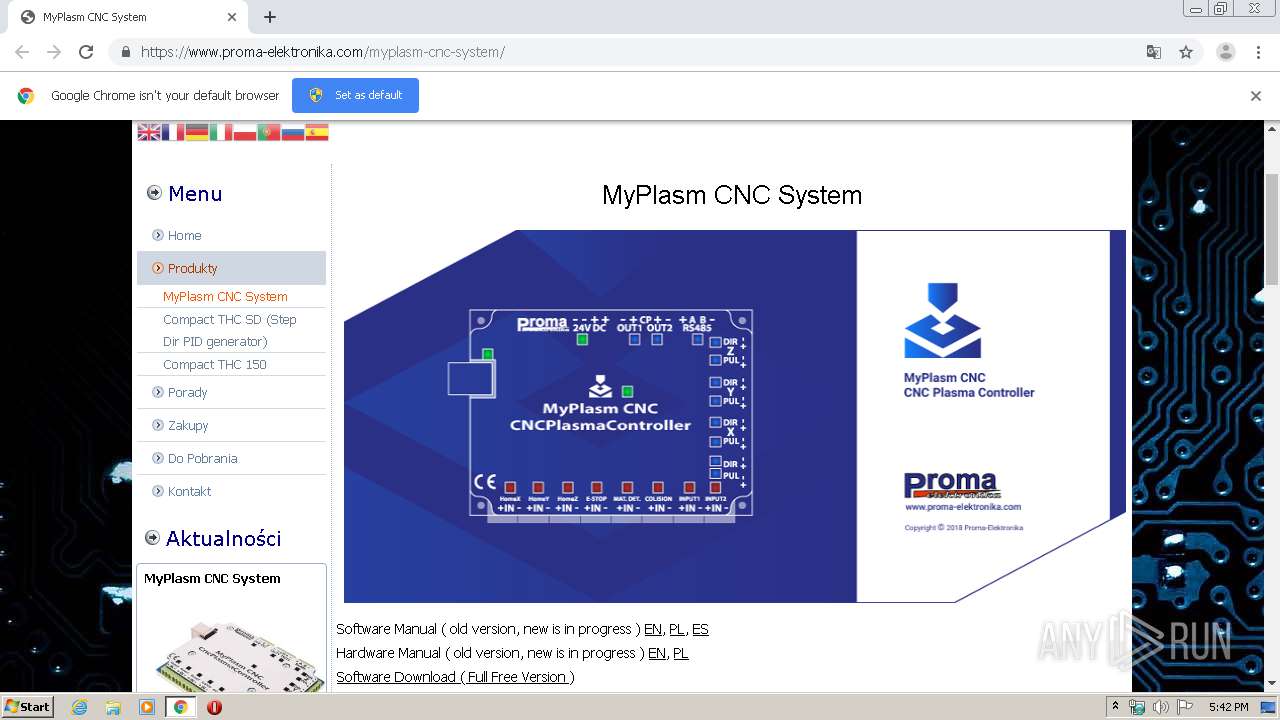
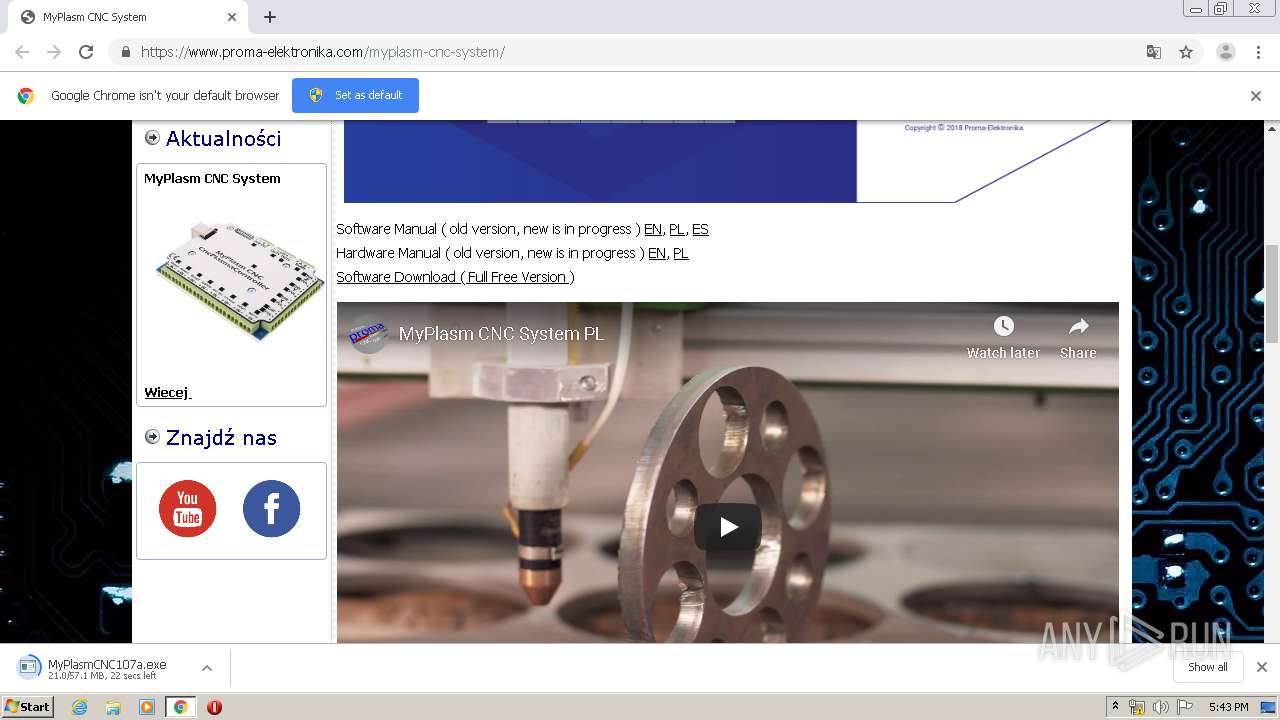
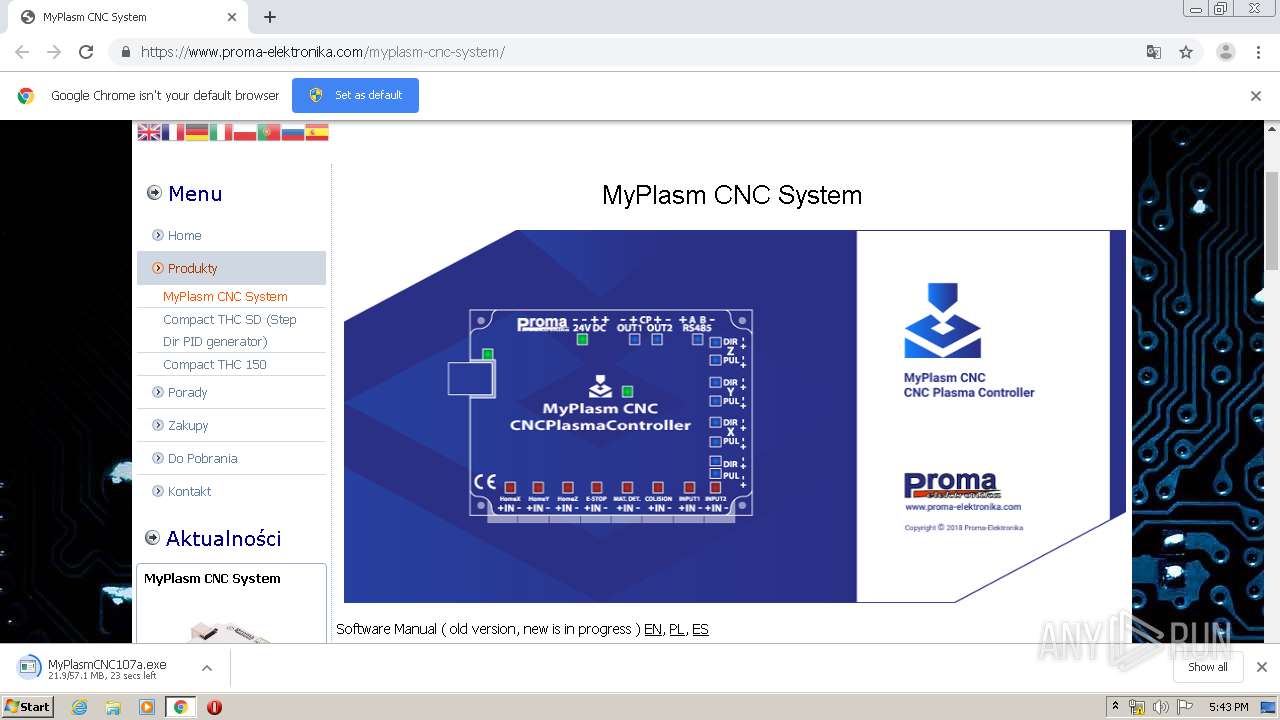
| URL: | https://www.proma-elektronika.com/myplasm-cnc-system/ |
| Full analysis: | https://app.any.run/tasks/4b2dffdf-0871-4c63-8954-40fb37044f43 |
| Verdict: | Malicious activity |
| Analysis date: | January 23, 2020, 17:42:09 |
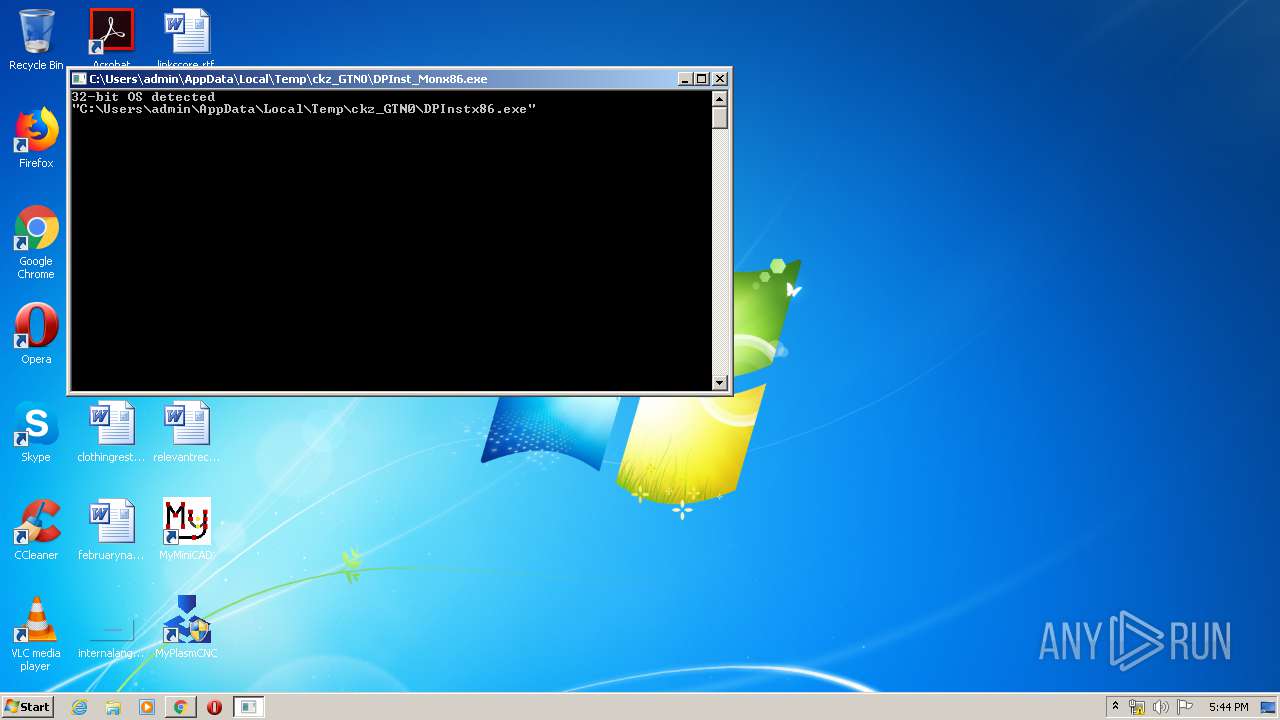
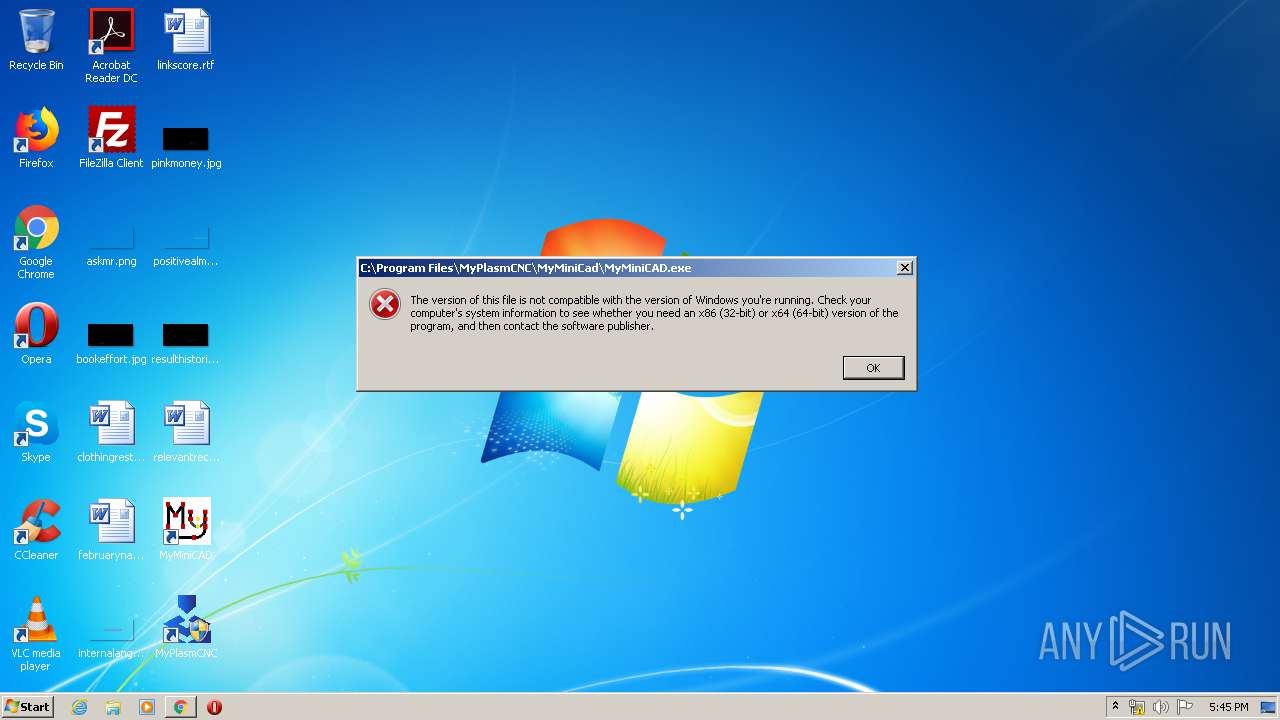
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0EA9DDAAF0B5567340AF73D900B37FA4 |
| SHA1: | 639D43856D44223D56C2154F77837FE011D9BB8C |
| SHA256: | C57CD8780CB1D68F768DE0EE185893CB21B1376403D12B3F75254238792FBCFD |
| SSDEEP: | 3:N8DSLoIh8XQNKIKZOWR4:2OLVhzM5R4 |
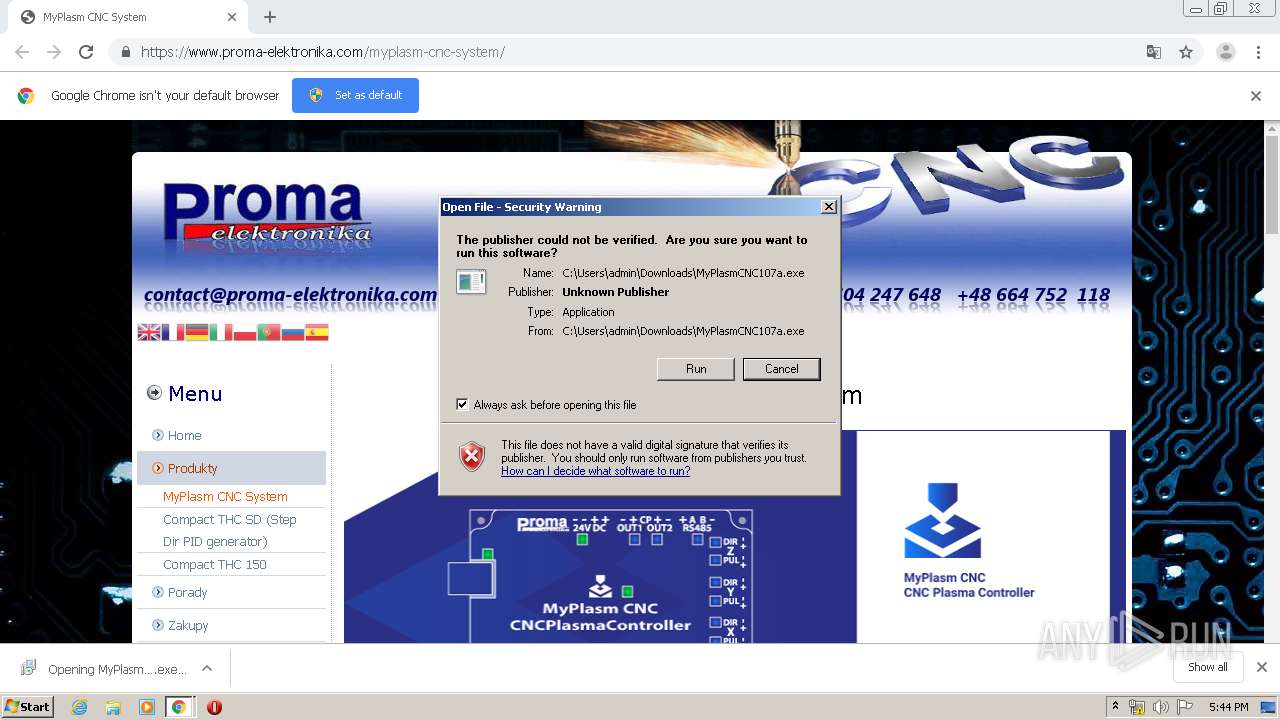
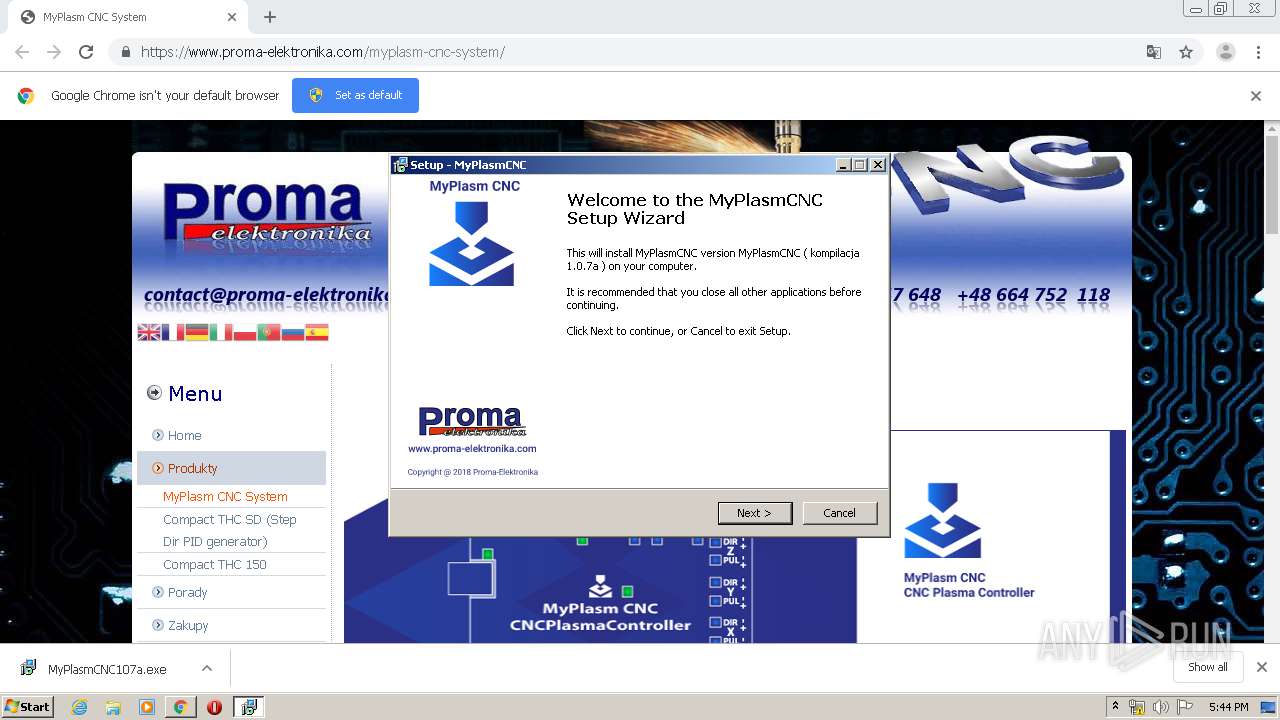
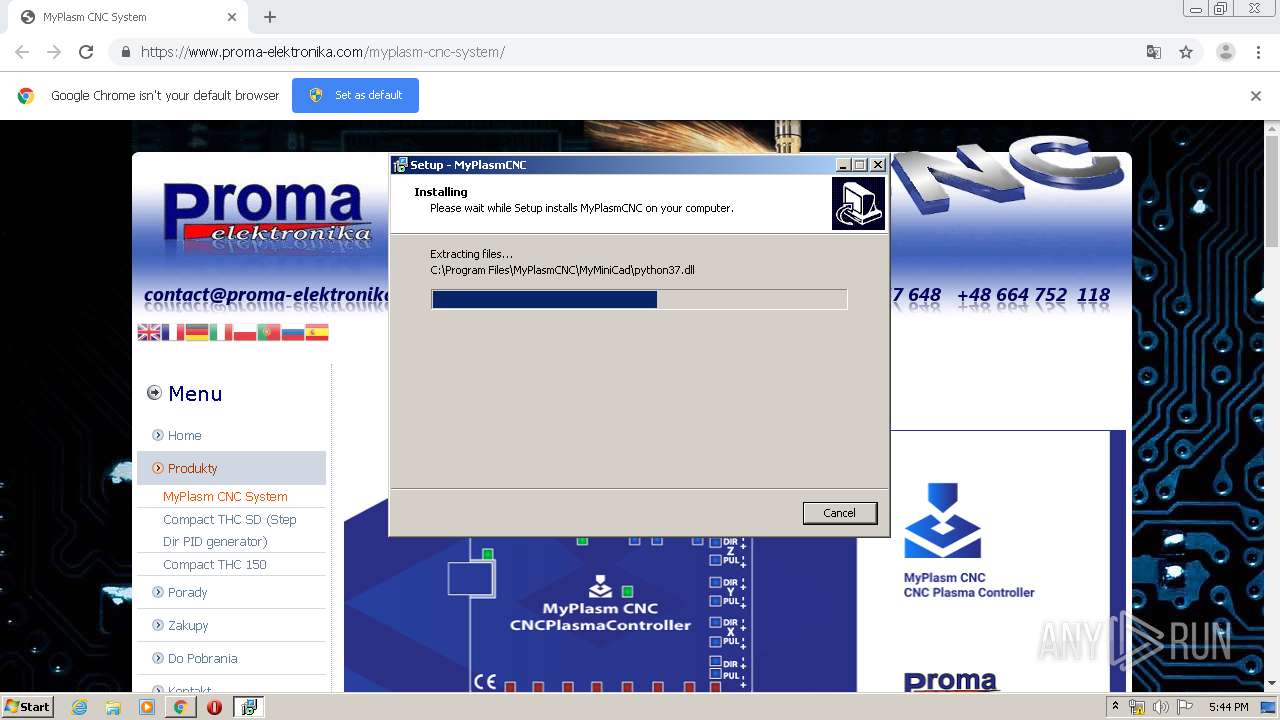
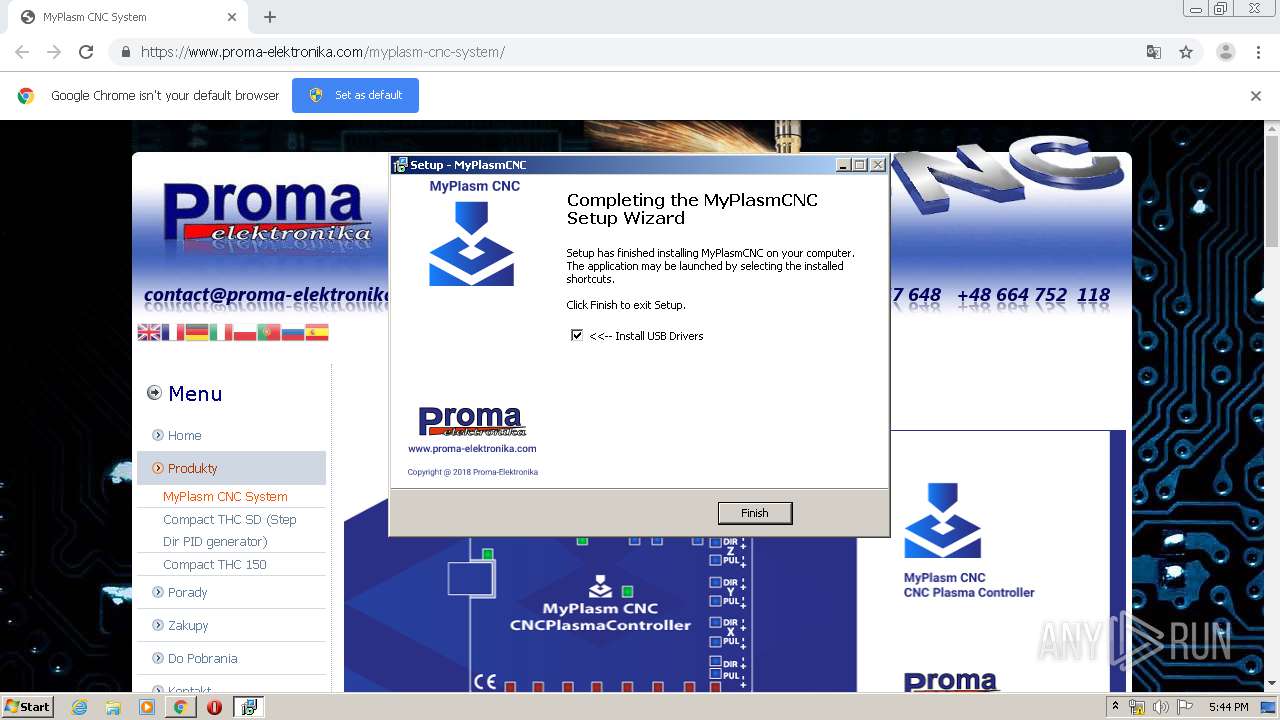
MALICIOUS
Application was dropped or rewritten from another process
- MyPlasmCNC107a.exe (PID: 2720)
- MyPlasmCNC107a.exe (PID: 3848)
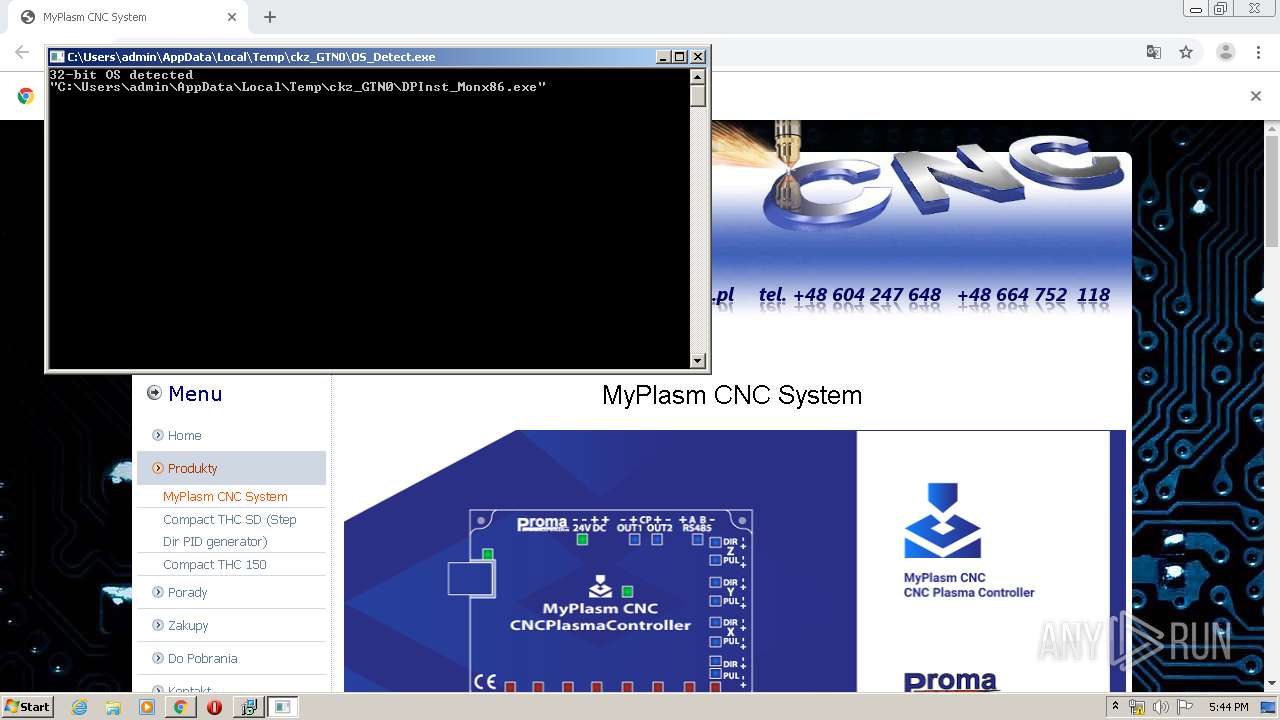
- OS_Detect.exe (PID: 2208)
- OS_Detect.exe (PID: 2348)
- DPInst_Monx86.exe (PID: 2500)
- DPInstx86.exe (PID: 2128)
- drivers.exe (PID: 2400)
- MyPlasmCNC.exe (PID: 2660)
- MyPlasmCNC.exe (PID: 1860)
Loads dropped or rewritten executable
- MyPlasmCNC.exe (PID: 1860)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2880)
Executable content was dropped or overwritten
- chrome.exe (PID: 2880)
- MyPlasmCNC107a.exe (PID: 2720)
- MyPlasmCNC107a.exe (PID: 3848)
- drivers.exe (PID: 2400)
- DPInstx86.exe (PID: 2128)
- DrvInst.exe (PID: 3016)
- DrvInst.exe (PID: 2312)
- MyPlasmCNC107a.tmp (PID: 3004)
Creates files in the Windows directory
- DPInstx86.exe (PID: 2128)
- DrvInst.exe (PID: 3016)
- DrvInst.exe (PID: 2312)
Executed via COM
- DrvInst.exe (PID: 3016)
- DrvInst.exe (PID: 2312)
Removes files from Windows directory
- DrvInst.exe (PID: 3016)
- DrvInst.exe (PID: 2312)
Creates files in the driver directory
- DrvInst.exe (PID: 3016)
- DrvInst.exe (PID: 2312)
Creates files in the program directory
- DPInstx86.exe (PID: 2128)
- MyPlasmCNC.exe (PID: 1860)
Creates a software uninstall entry
- DPInstx86.exe (PID: 2128)
INFO
Reads the hosts file
- chrome.exe (PID: 2880)
- chrome.exe (PID: 3112)
Application launched itself
- chrome.exe (PID: 2880)
Reads Internet Cache Settings
- chrome.exe (PID: 2880)
Application was dropped or rewritten from another process
- MyPlasmCNC107a.tmp (PID: 4000)
- MyPlasmCNC107a.tmp (PID: 3004)
Dropped object may contain Bitcoin addresses
- MyPlasmCNC107a.tmp (PID: 3004)
Creates a software uninstall entry
- MyPlasmCNC107a.tmp (PID: 3004)
Reads settings of System Certificates
- DrvInst.exe (PID: 3016)
- chrome.exe (PID: 3112)
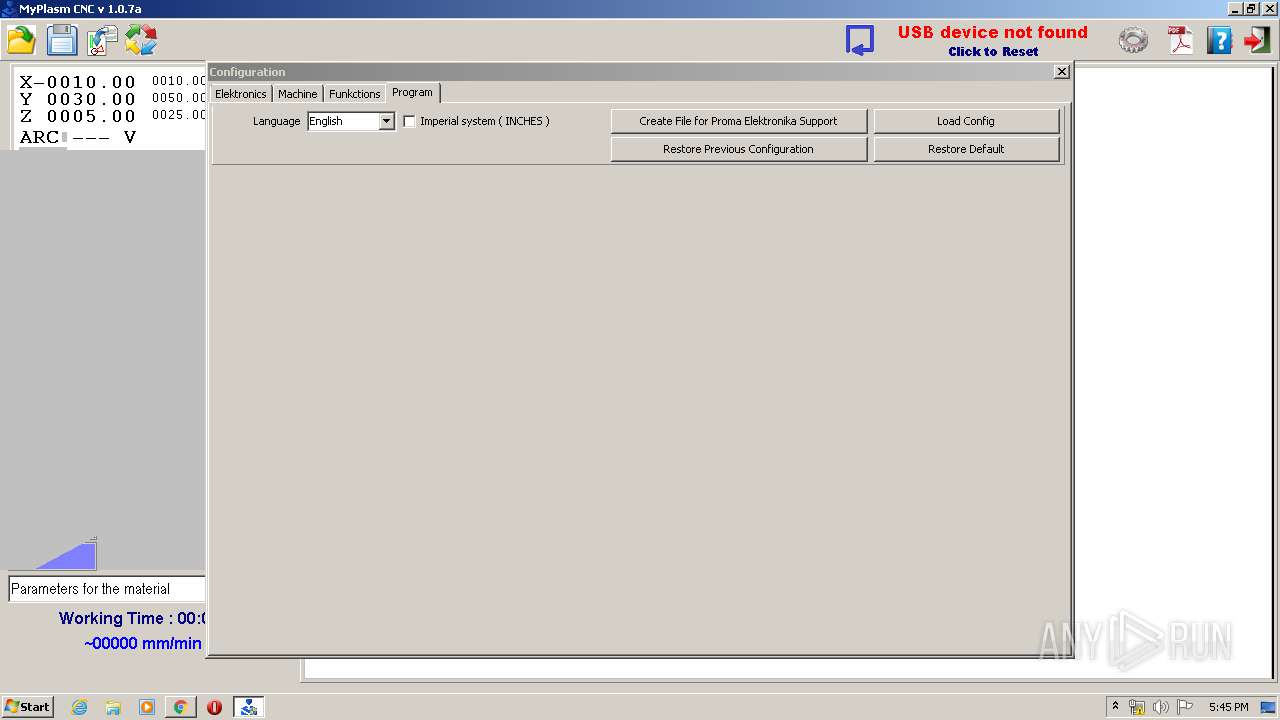
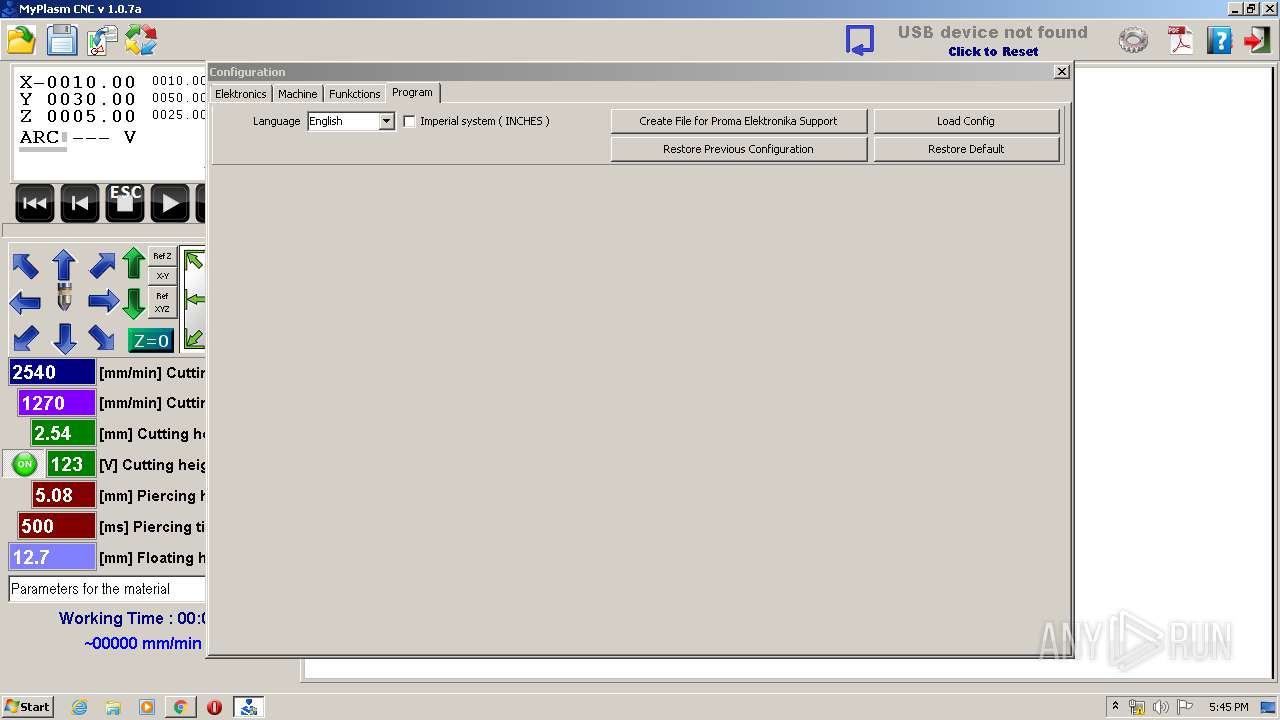
Manual execution by user
- MyPlasmCNC.exe (PID: 2660)
- MyPlasmCNC.exe (PID: 1860)
Creates files in the program directory
- MyPlasmCNC107a.tmp (PID: 3004)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3016)
Changes settings of System certificates
- DrvInst.exe (PID: 3016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
41
Malicious processes
6
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11941584559208497660 --mojo-platform-channel-handle=4492 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15126982701481013162 --mojo-platform-channel-handle=4372 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17268463328437709975 --mojo-platform-channel-handle=3604 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\MyPlasmCNC\MyPlasmCNC.exe" | C:\Program Files\MyPlasmCNC\MyPlasmCNC.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2128 | "C:\Users\admin\AppData\Local\Temp\ckz_GTN0\DPInstx86.exe" | C:\Users\admin\AppData\Local\Temp\ckz_GTN0\DPInstx86.exe | DPInst_Monx86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 512 Version: 2.1 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7885827245033645205 --mojo-platform-channel-handle=4360 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Users\admin\AppData\Local\Temp\ckz_GTN0\OS_Detect.exe" | C:\Users\admin\AppData\Local\Temp\ckz_GTN0\OS_Detect.exe | — | drivers.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2312 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{00dfcb2d-5570-609f-e460-303e513b7937}\ftdiport.inf" "0" "61721f653" "00000554" "WinSta0\Default" "0000033C" "208" "c:\users\admin\appdata\local\temp\ckz_gtn0" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11822558996234589729 --mojo-platform-channel-handle=4916 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2348 | "C:\Users\admin\AppData\Local\Temp\ckz_GTN0\OS_Detect.exe" | C:\Users\admin\AppData\Local\Temp\ckz_GTN0\OS_Detect.exe | drivers.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
4 222
Read events
2 870
Write events
1 342
Delete events
10
Modification events
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2880-13224274944678125 |
Value: 259 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
Executable files
193
Suspicious files
105
Text files
1 430
Unknown types
685
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E29DB01-B40.pma | — | |
MD5:— | SHA256:— | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cdfbef1f-8b9b-4139-bf49-752c991e5ffd.tmp | — | |
MD5:— | SHA256:— | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa66c20.TMP | text | |
MD5:— | SHA256:— | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66c01.TMP | text | |
MD5:— | SHA256:— | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66bf1.TMP | text | |
MD5:— | SHA256:— | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66dd5.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
29
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3112 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
3112 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
3112 | chrome.exe | GET | 200 | 209.85.230.203:80 | http://r5---sn-h5q7dnlk.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.253.99.100&mm=28&mn=sn-h5q7dnlk&ms=nvh&mt=1579801278&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
3112 | chrome.exe | GET | 200 | 173.194.139.134:80 | http://r1---sn-h5q7rn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.253.99.100&mm=28&mn=sn-h5q7rn7s&ms=nvh&mt=1579801278&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3112 | chrome.exe | 172.217.23.102:443 | static.doubleclick.net | Google Inc. | US | suspicious |
3112 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3112 | chrome.exe | 188.210.221.62:443 | www.proma-elektronika.com | Data Invest sp. z o.o. S.K.A | PL | unknown |
3112 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3112 | chrome.exe | 216.58.210.14:443 | translate.google.com | Google Inc. | US | whitelisted |
3112 | chrome.exe | 192.0.77.48:443 | s.w.org | Automattic, Inc | US | suspicious |
3112 | chrome.exe | 172.217.22.74:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3112 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3112 | chrome.exe | 172.217.23.97:443 | yt3.ggpht.com | Google Inc. | US | whitelisted |
3112 | chrome.exe | 216.58.205.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.proma-elektronika.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
s.w.org |
| whitelisted |
translate.google.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
www.youtube.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
www.google.com |
| malicious |