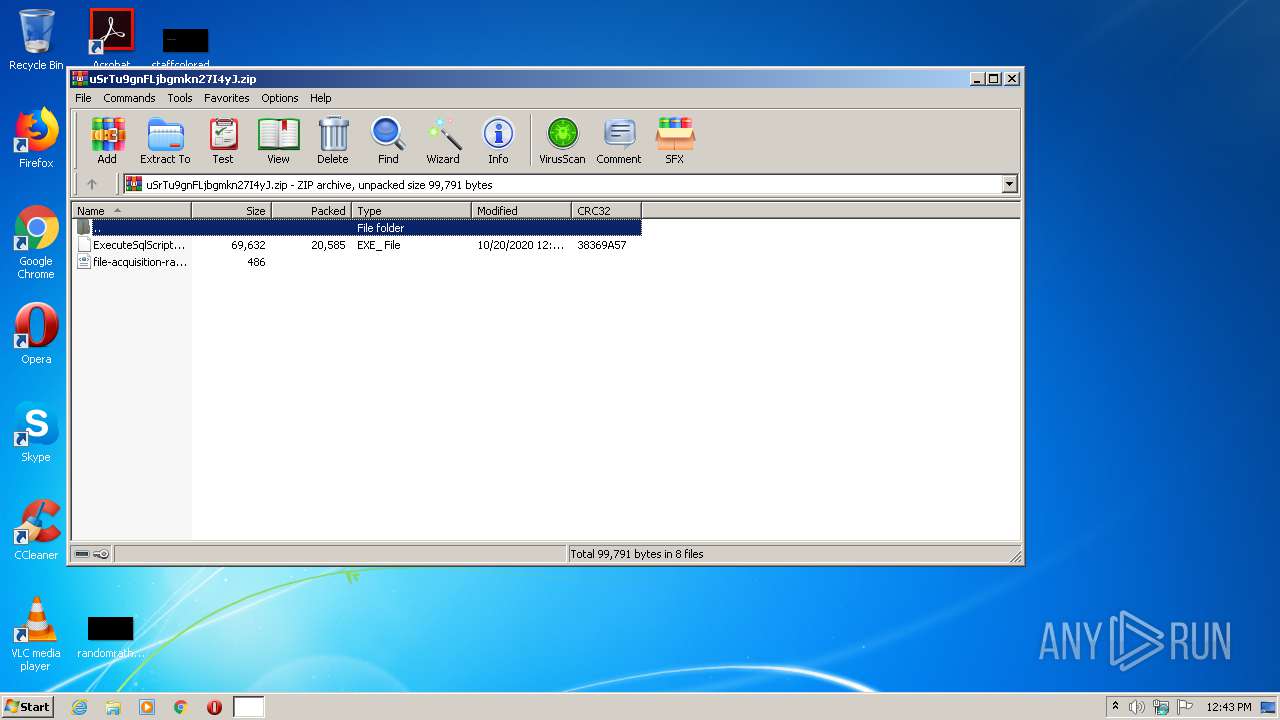
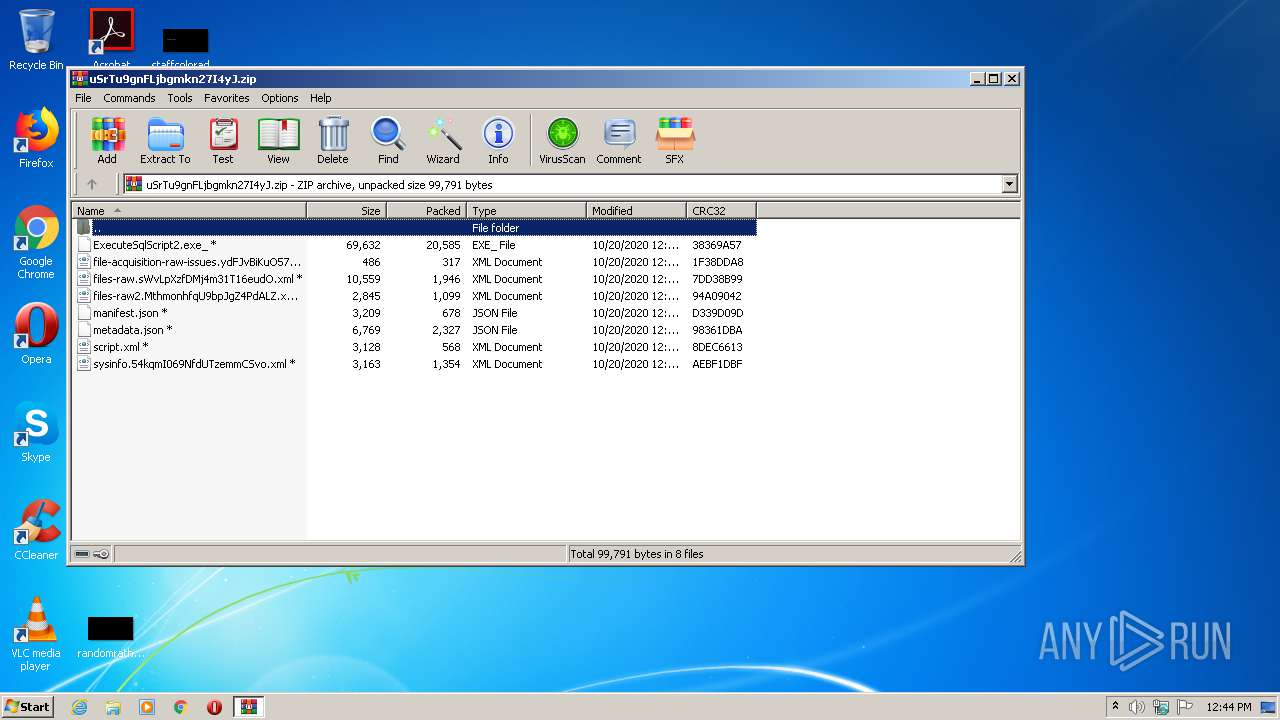
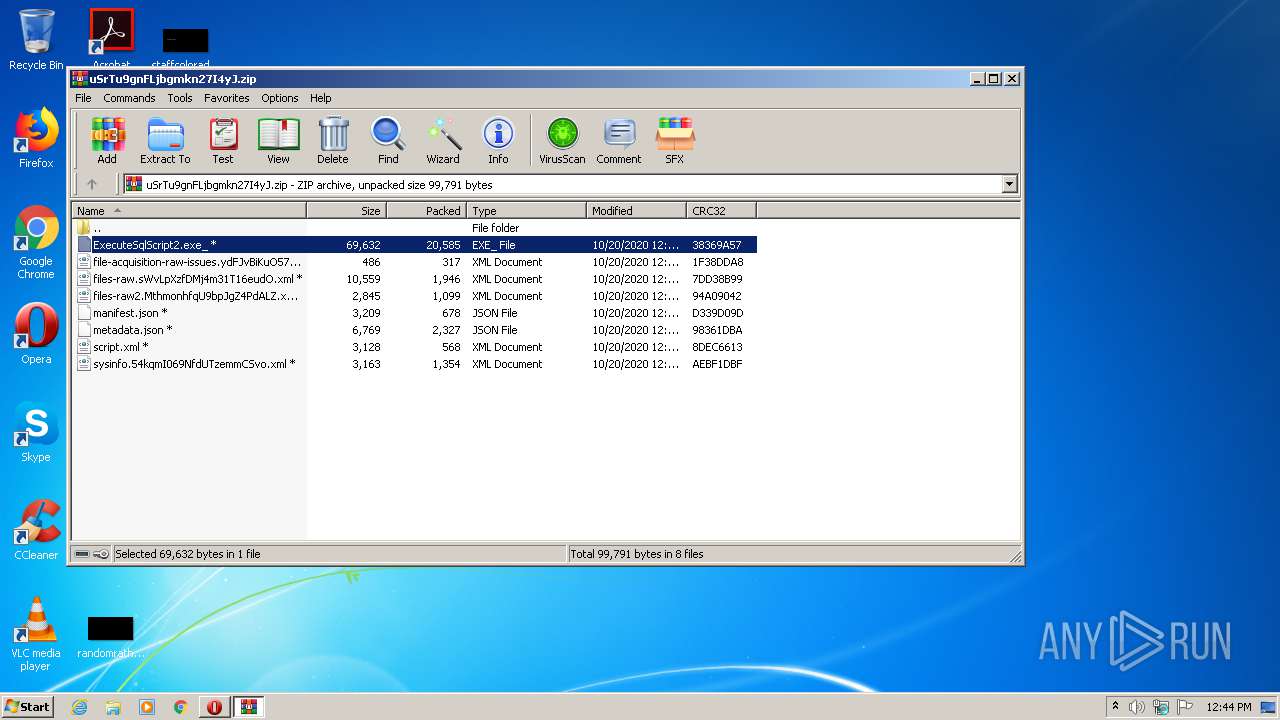
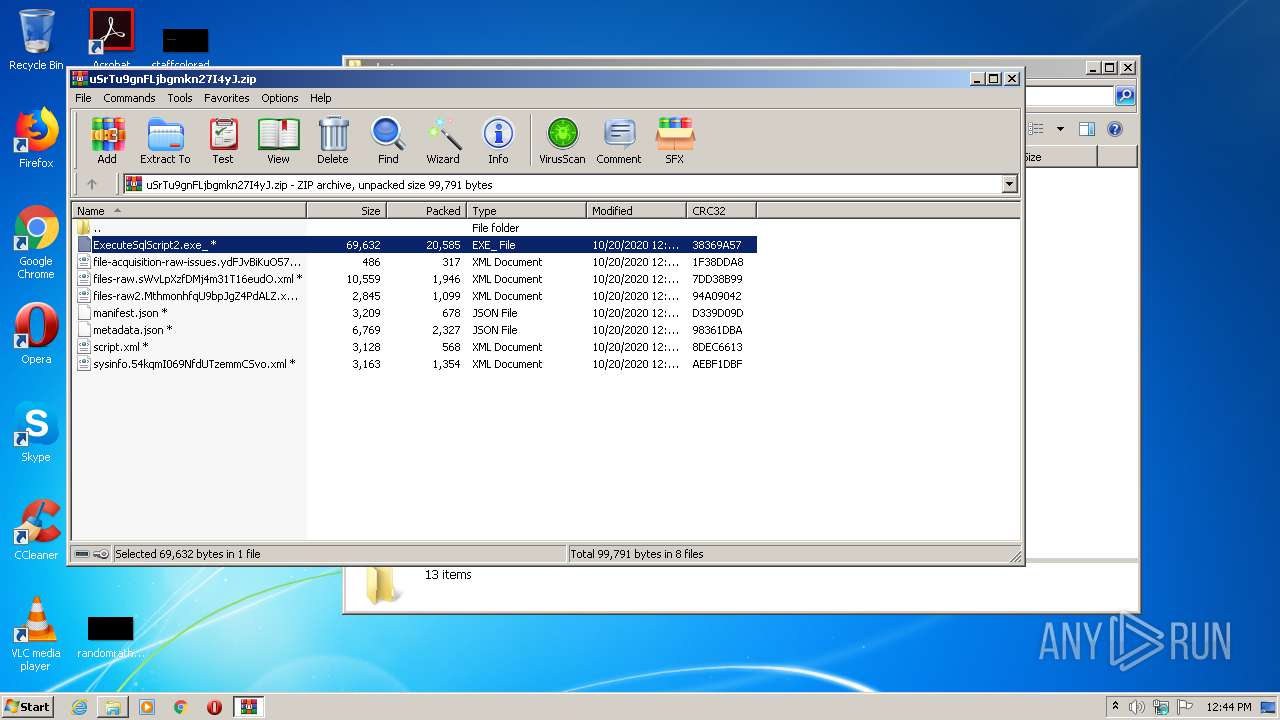
| File name: | uSrTu9gnFLjbgmkn27I4yJ.zip |
| Full analysis: | https://app.any.run/tasks/f030e761-156f-457c-a533-5d0e1f793a86 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 11:43:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 664D23EEE79770469489EF9E5FC72A27 |
| SHA1: | FB71533F848FDE260A85CDD3FFFD9F387A49B816 |
| SHA256: | C5796C5369CC973CB7CFDE6508AAAA96152D8E88E0D9BEB96D4EBFC70A8B4710 |
| SSDEEP: | 768:yTjDgr0GusGKni0M8S+FIJfOf0xmpJkPrg0a7dSLT:yj//hKC+Fq987dk |
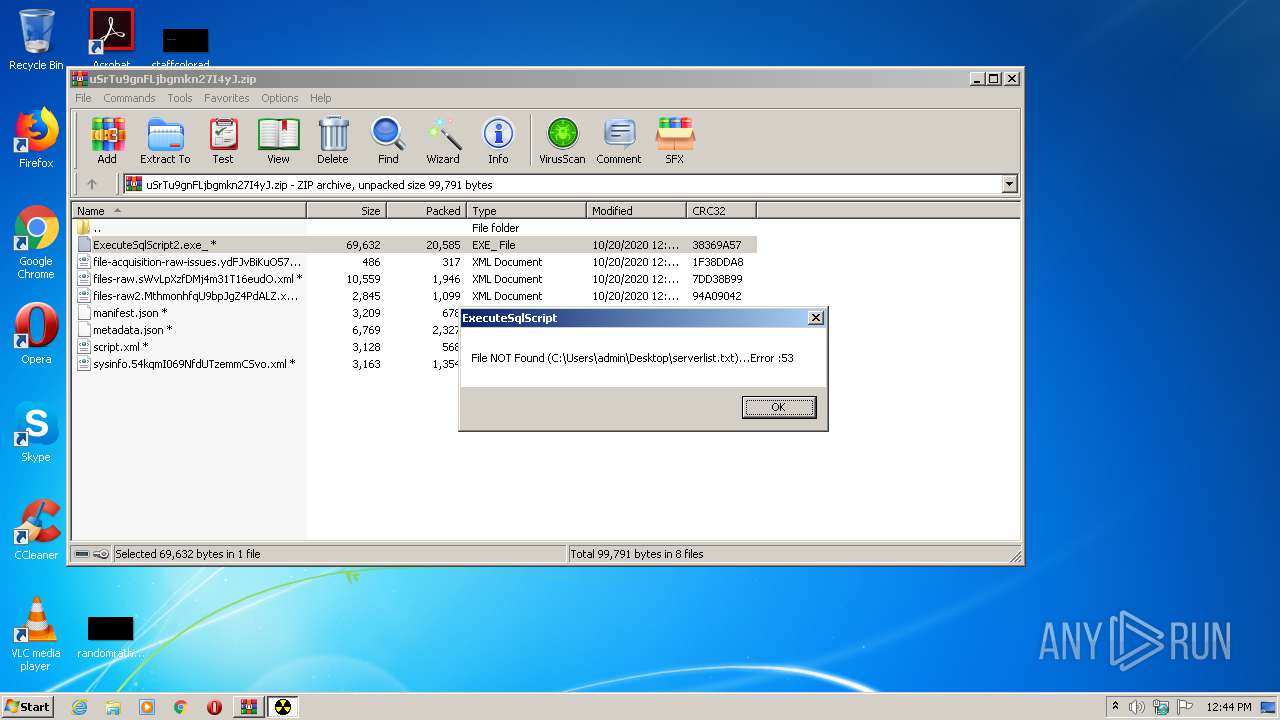
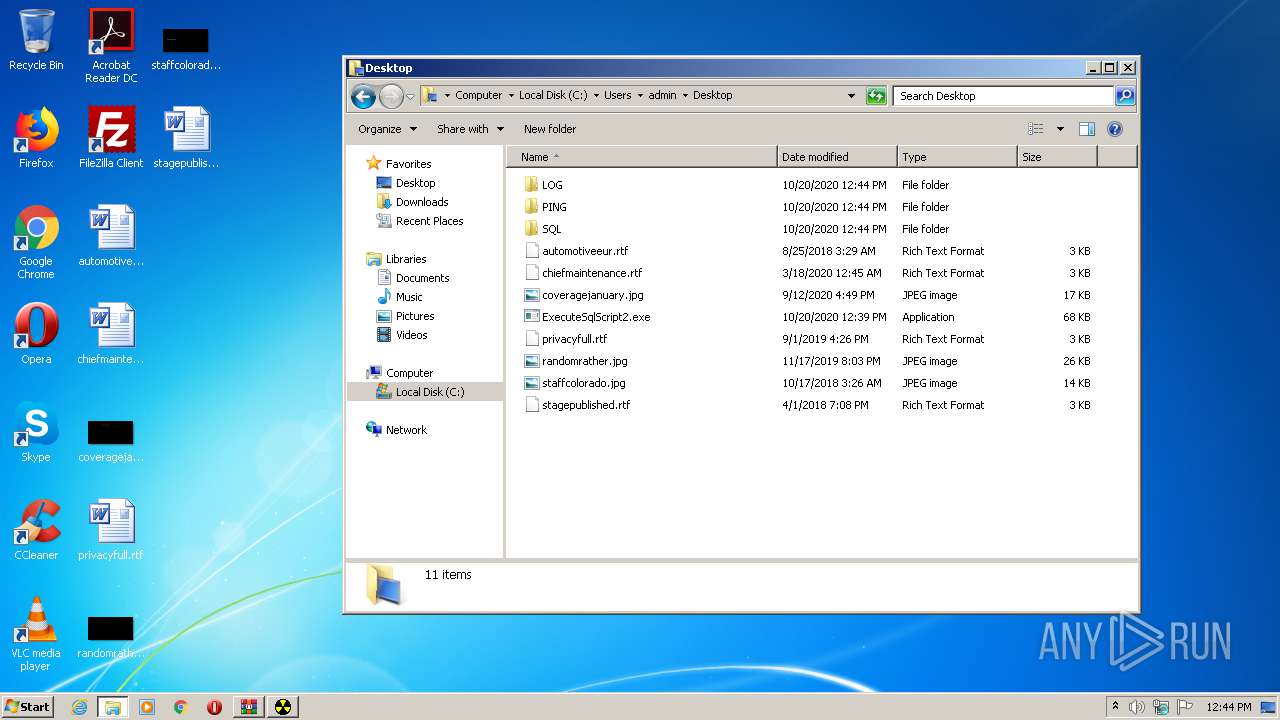
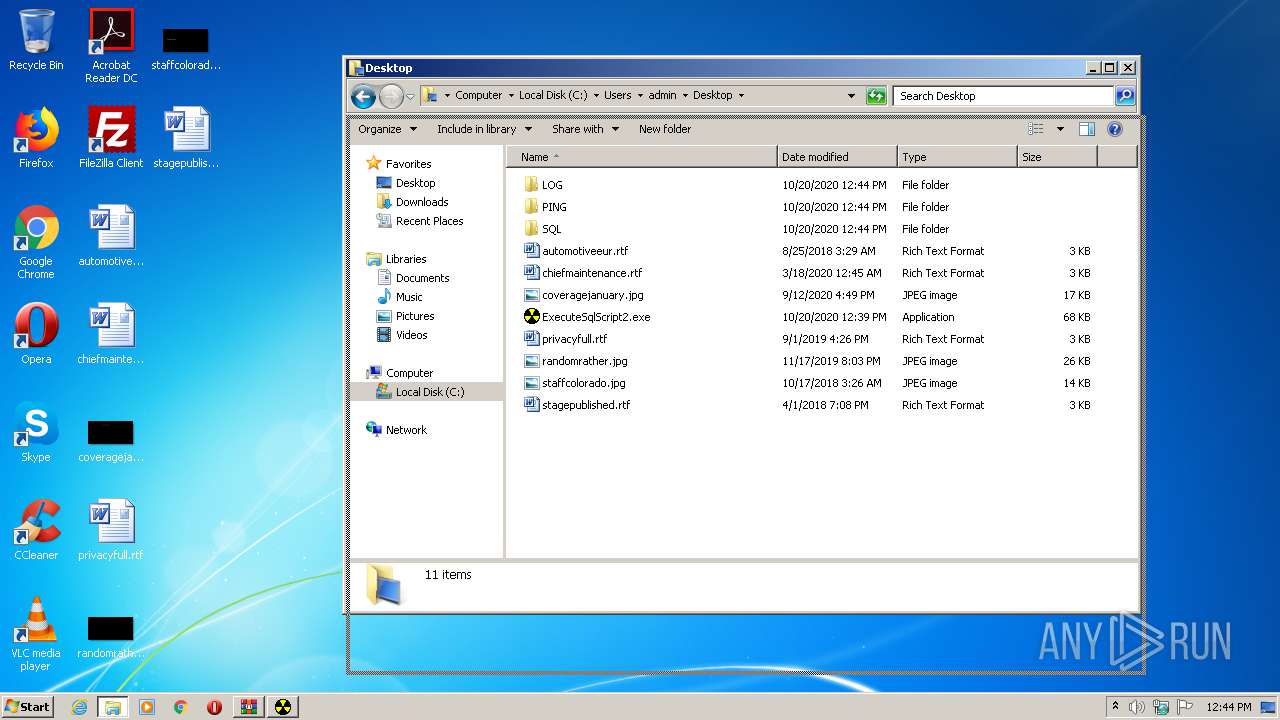
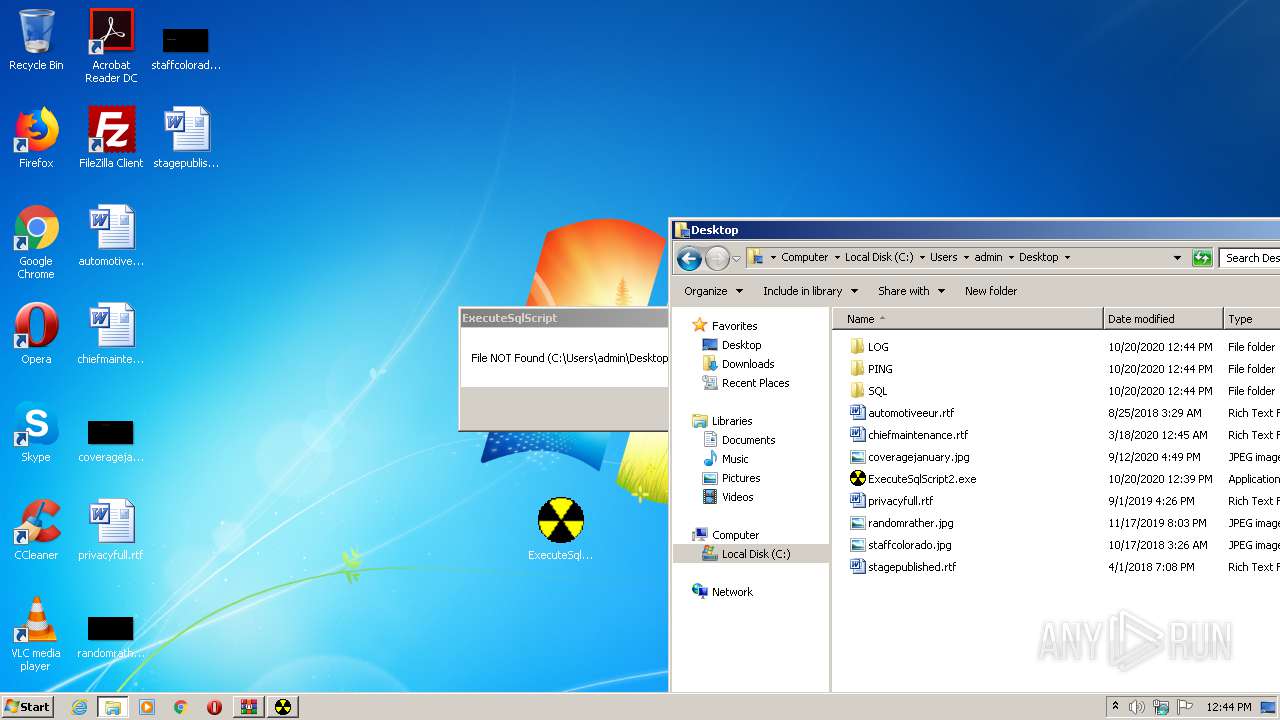
MALICIOUS
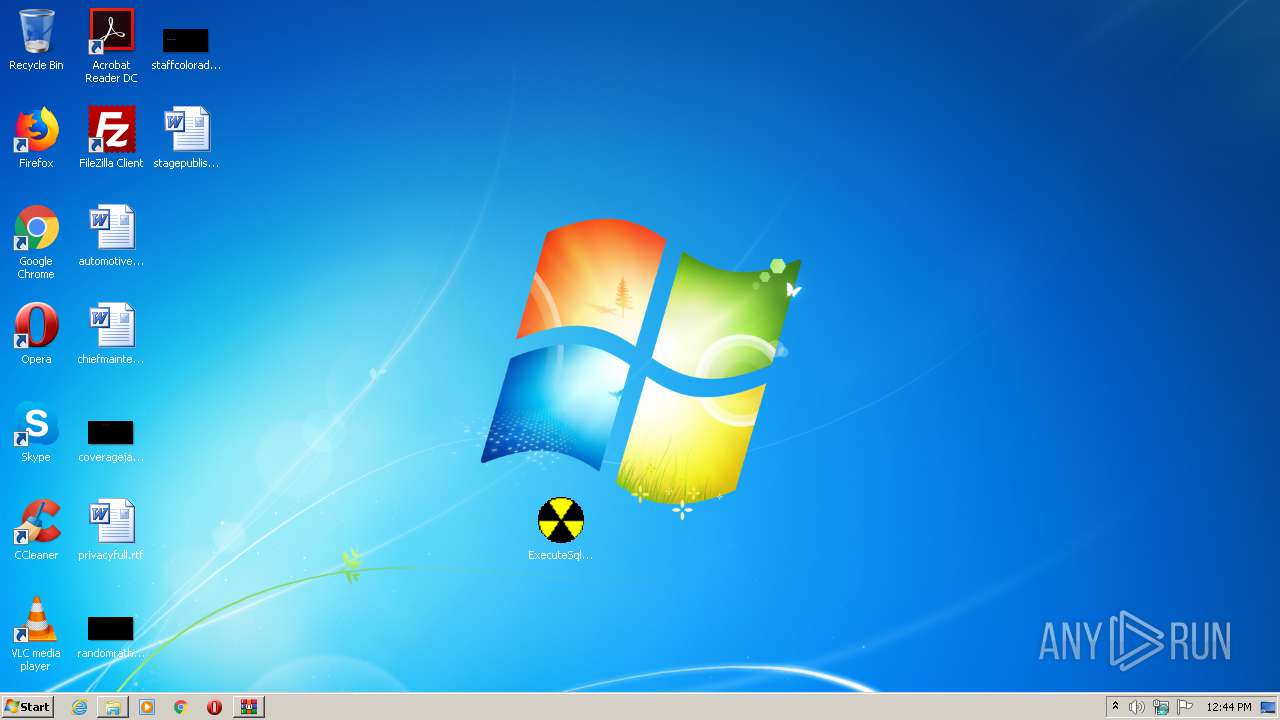
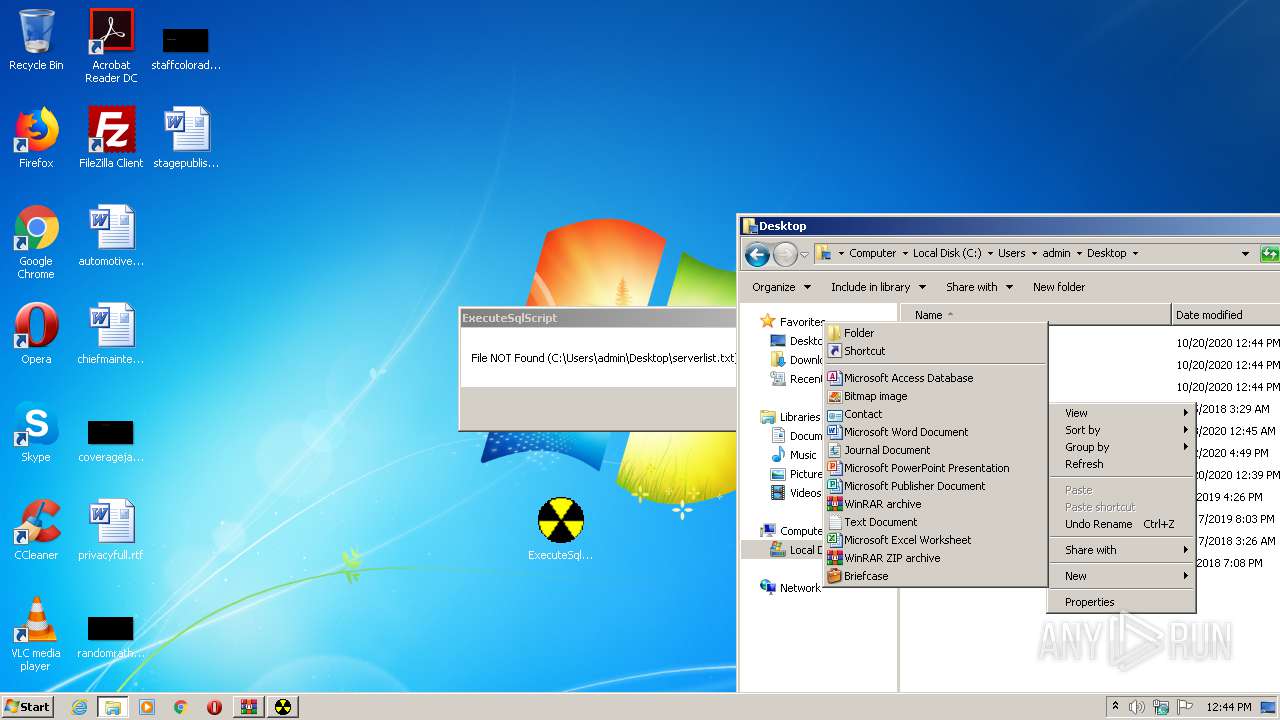
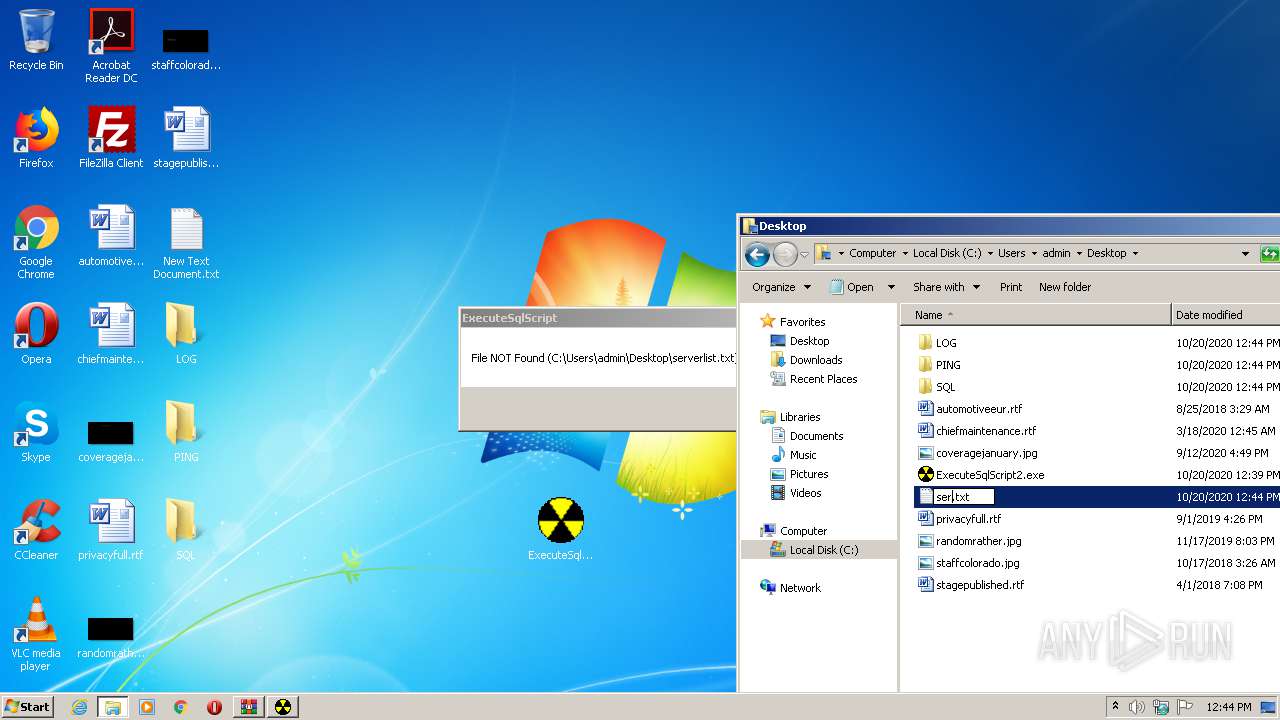
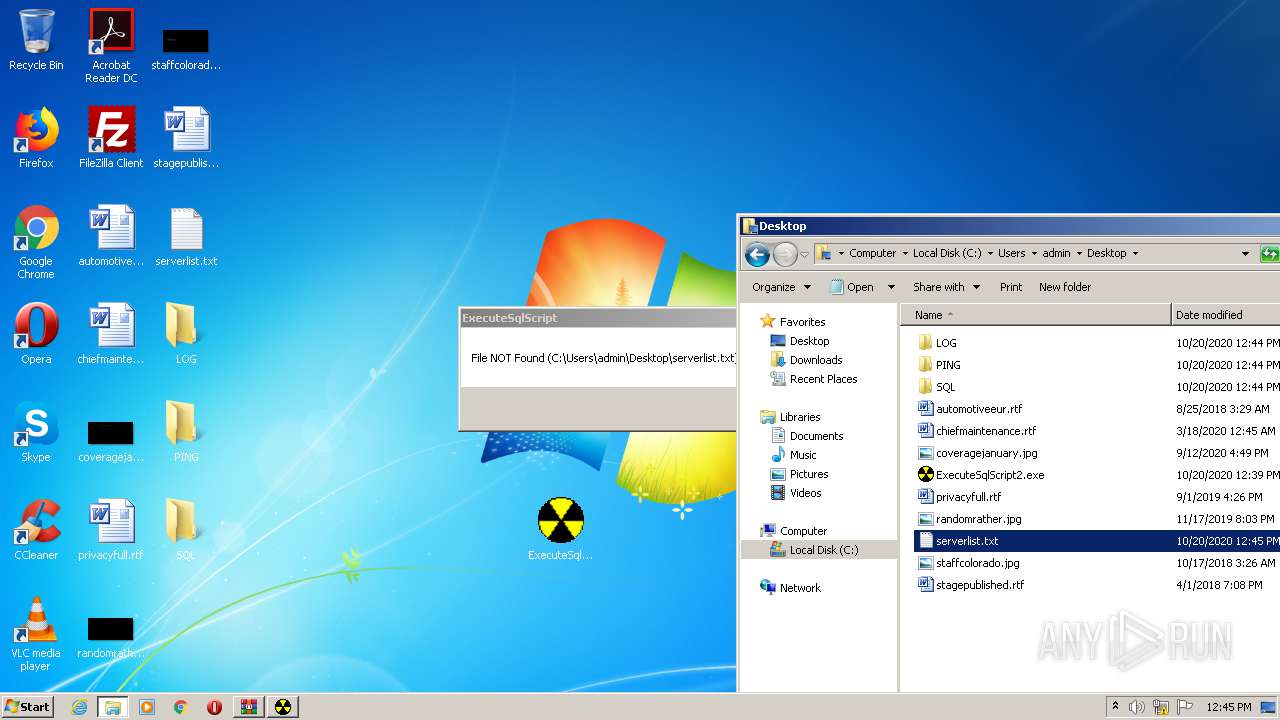
Application was dropped or rewritten from another process
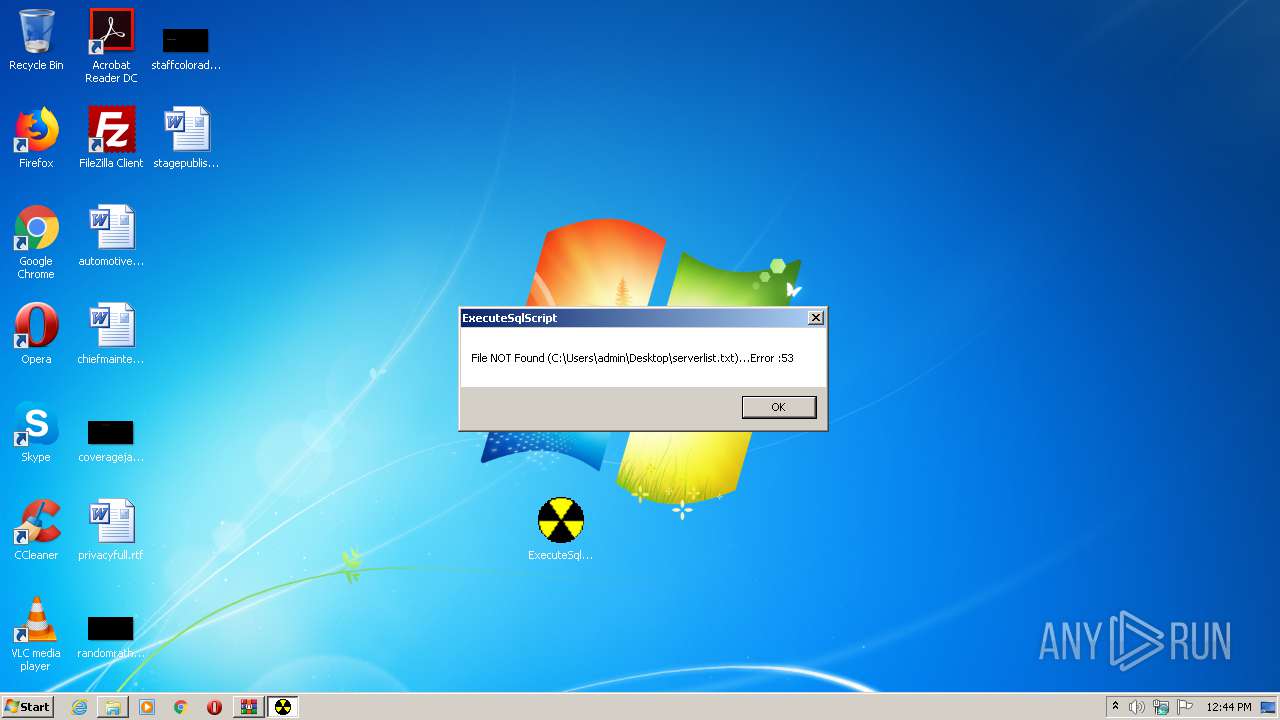
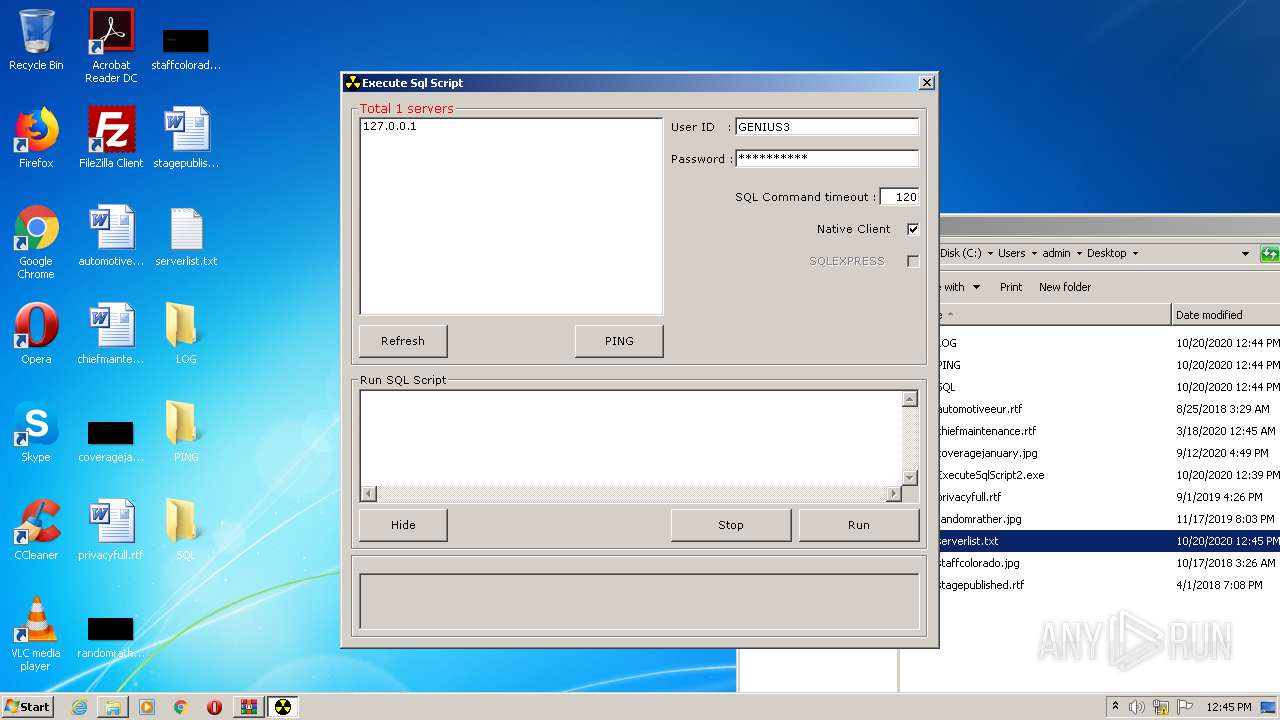
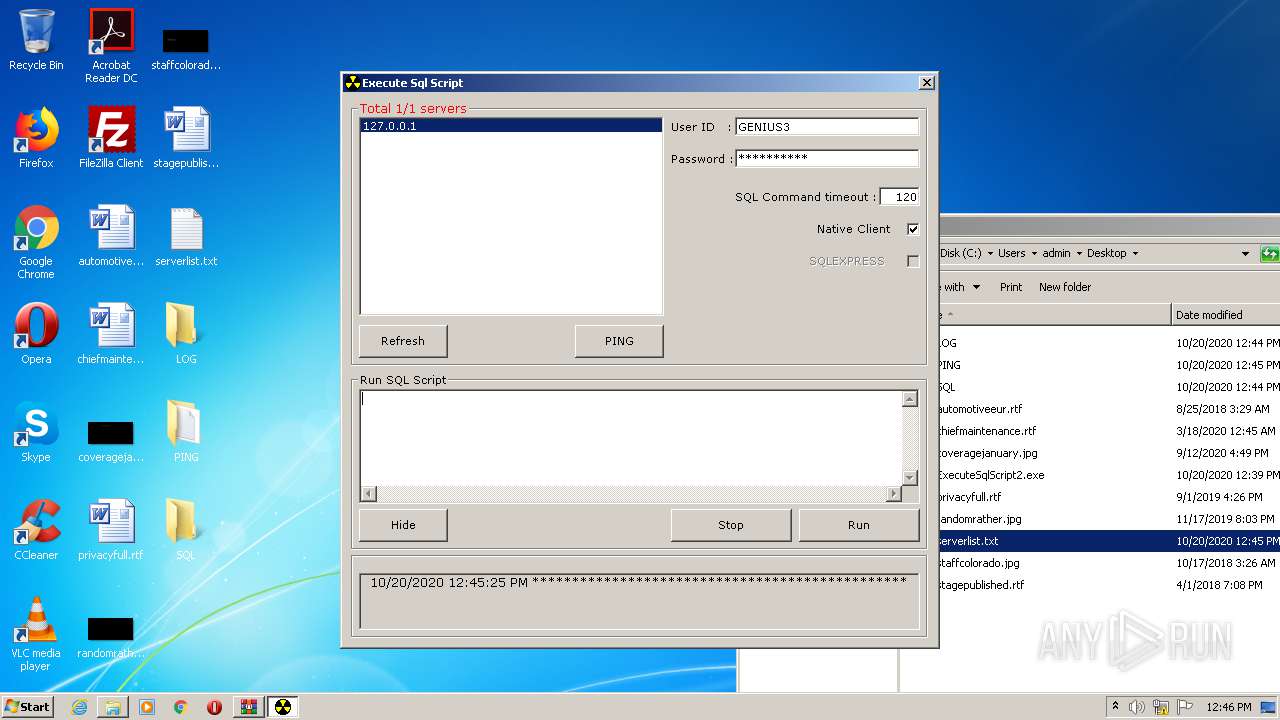
- ExecuteSqlScript2.exe (PID: 2884)
- ExecuteSqlScript2.exe (PID: 2388)
- ExecuteSqlScript2.exe (PID: 3652)
SUSPICIOUS
No suspicious indicators.INFO
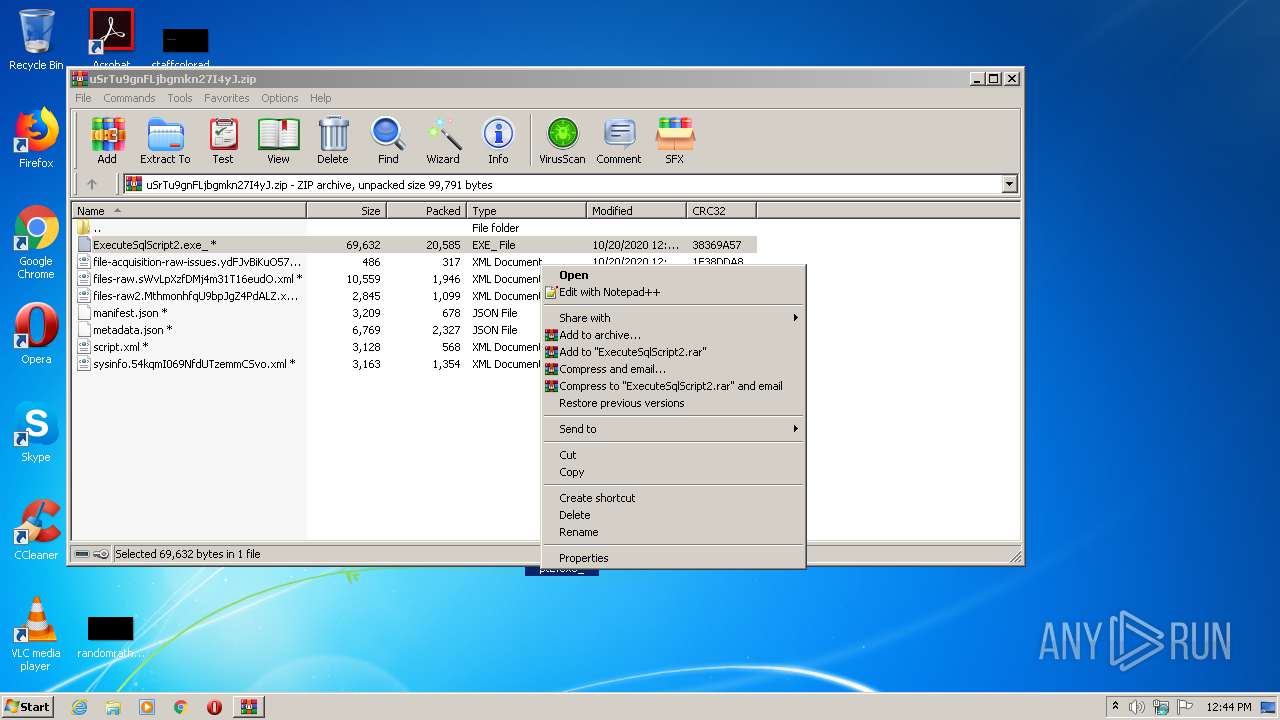
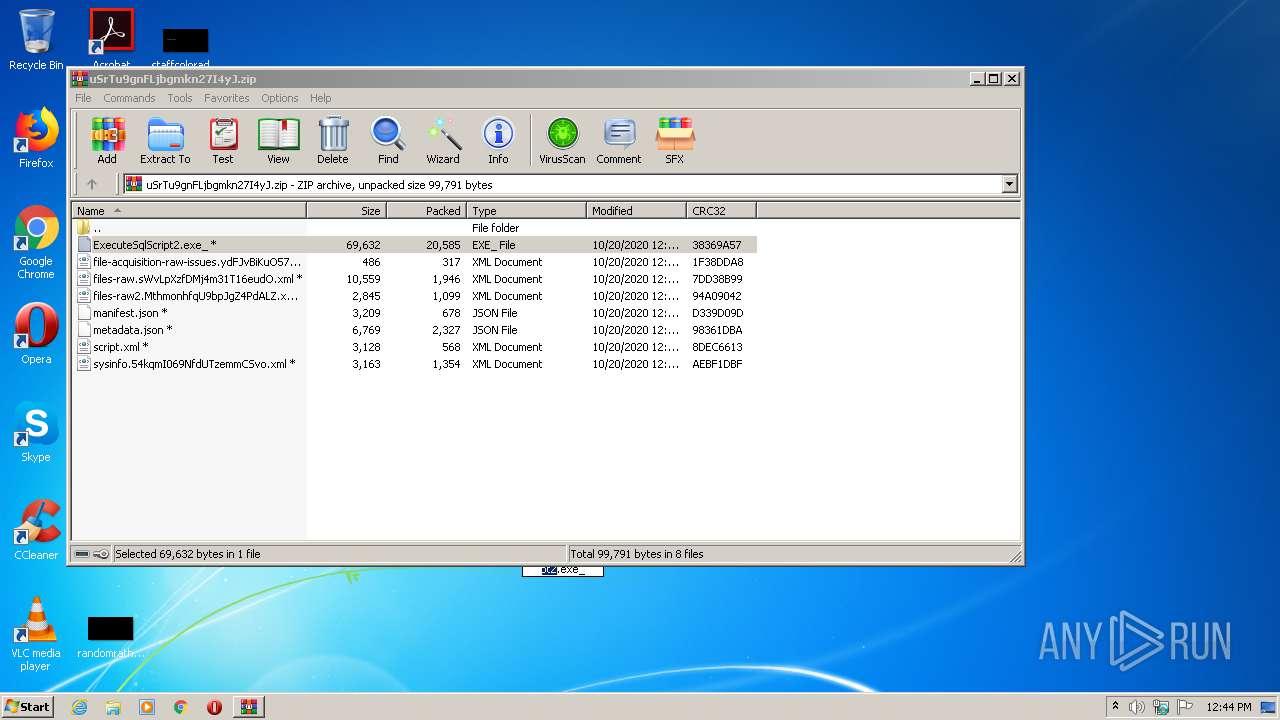
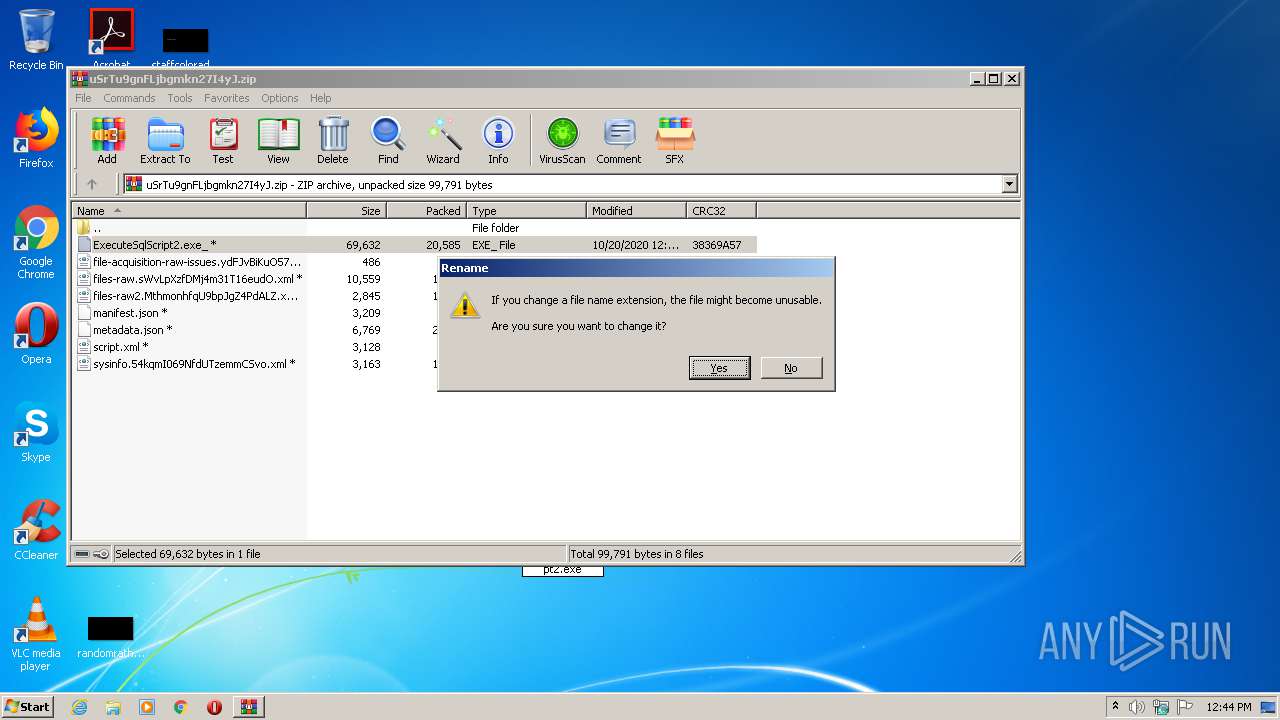
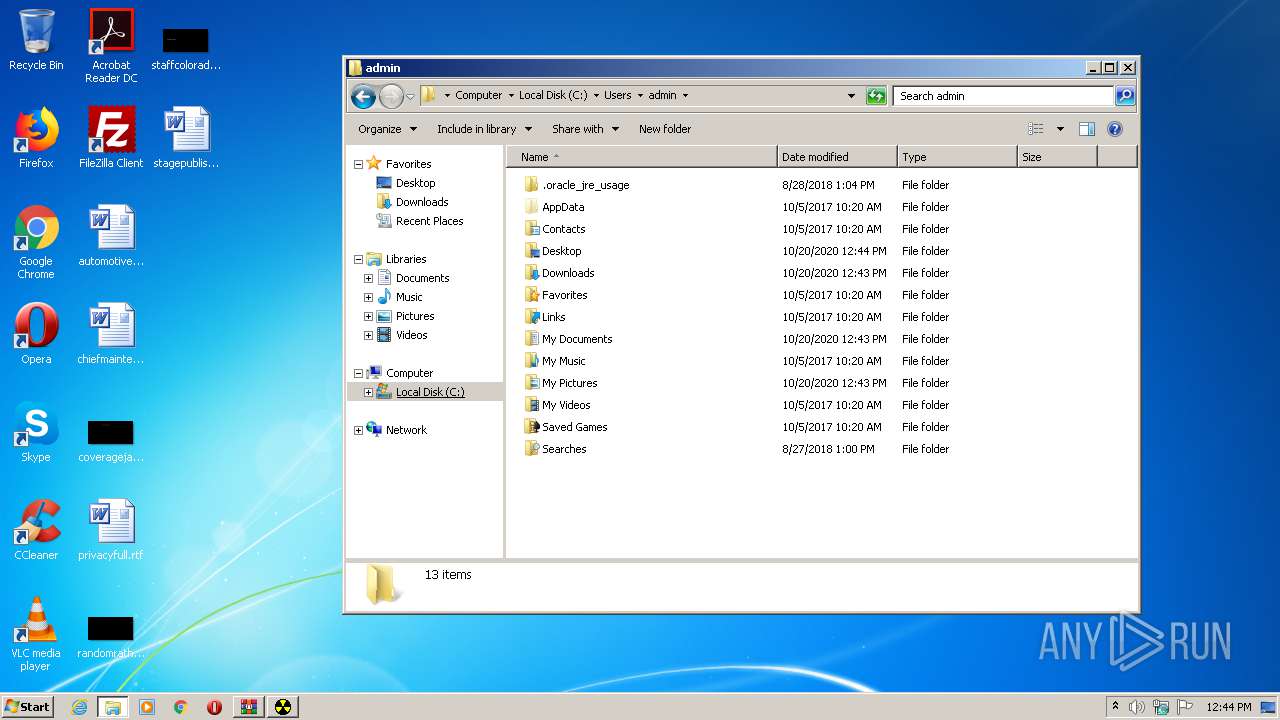
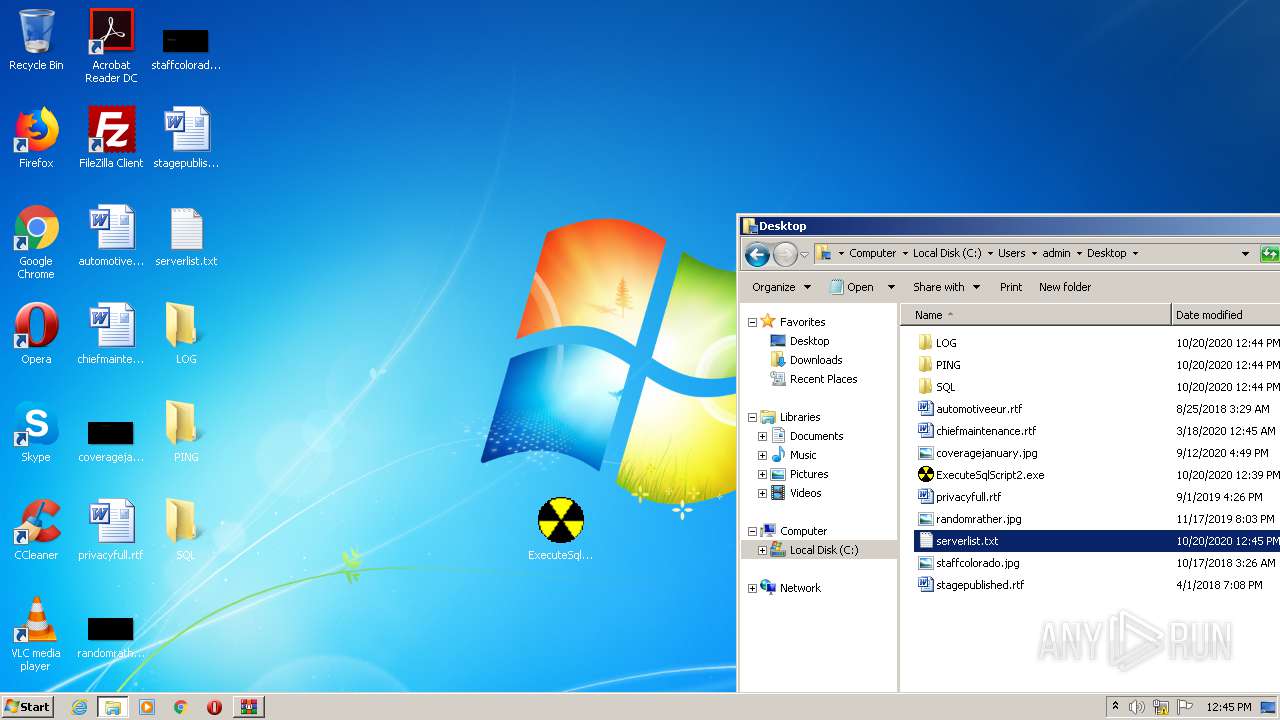
Manual execution by user
- ExecuteSqlScript2.exe (PID: 2884)
- explorer.exe (PID: 3024)
- ExecuteSqlScript2.exe (PID: 2388)
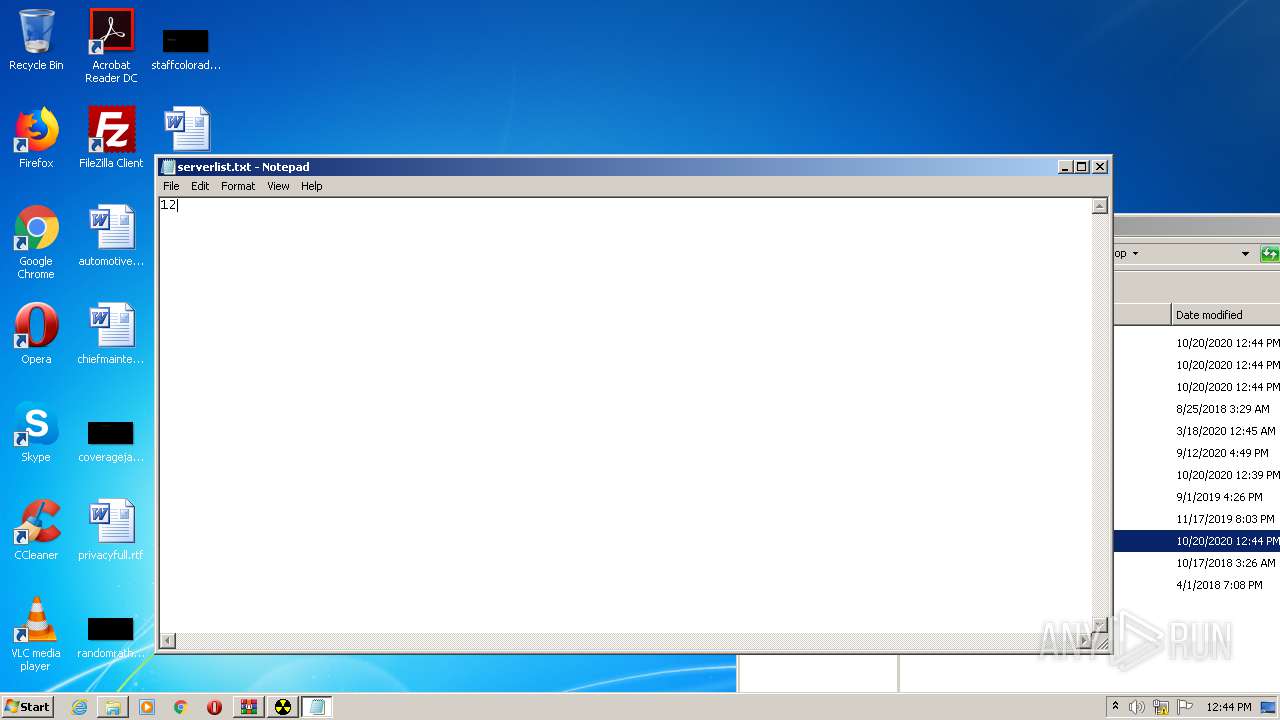
- NOTEPAD.EXE (PID: 2708)
- ExecuteSqlScript2.exe (PID: 3652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:10:20 11:39:18 |
| ZipCRC: | 0xaebf1dbf |
| ZipCompressedSize: | 1354 |
| ZipUncompressedSize: | 3163 |
| ZipFileName: | sysinfo.54kqmI069NfdUTzemmCSvo.xml |
Total processes
45
Monitored processes
6
Malicious processes
1
Suspicious processes
0
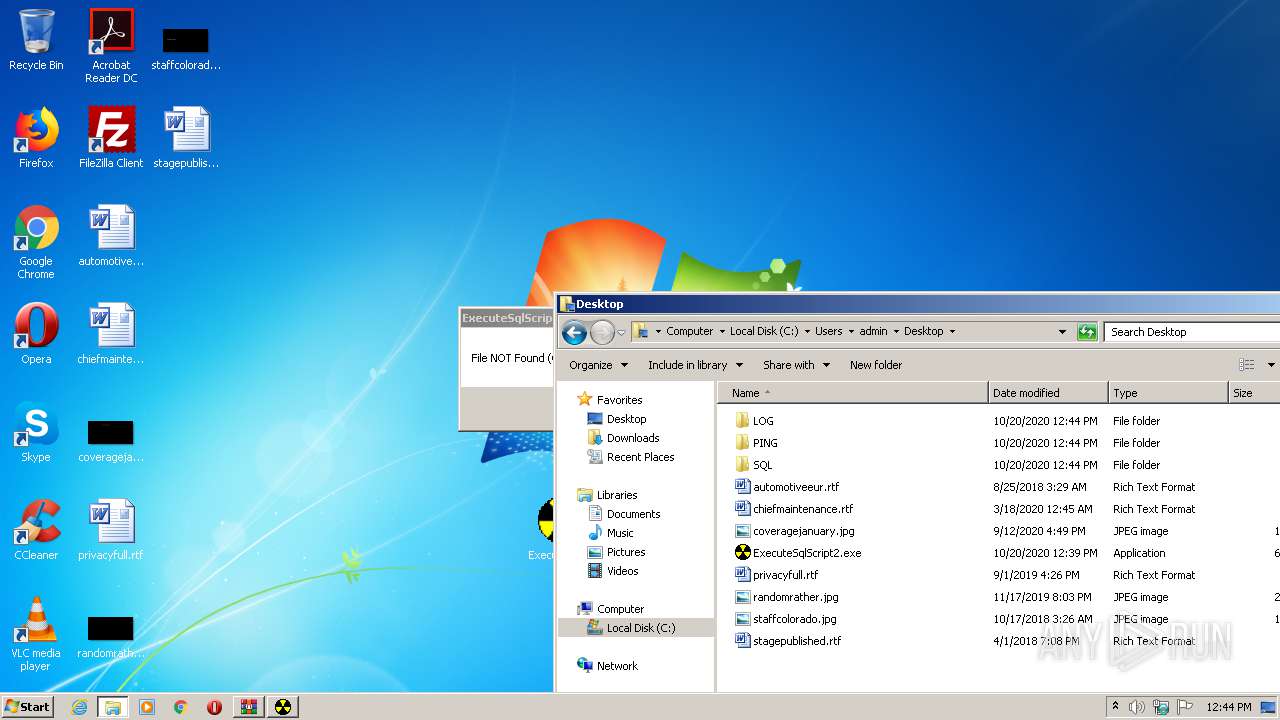
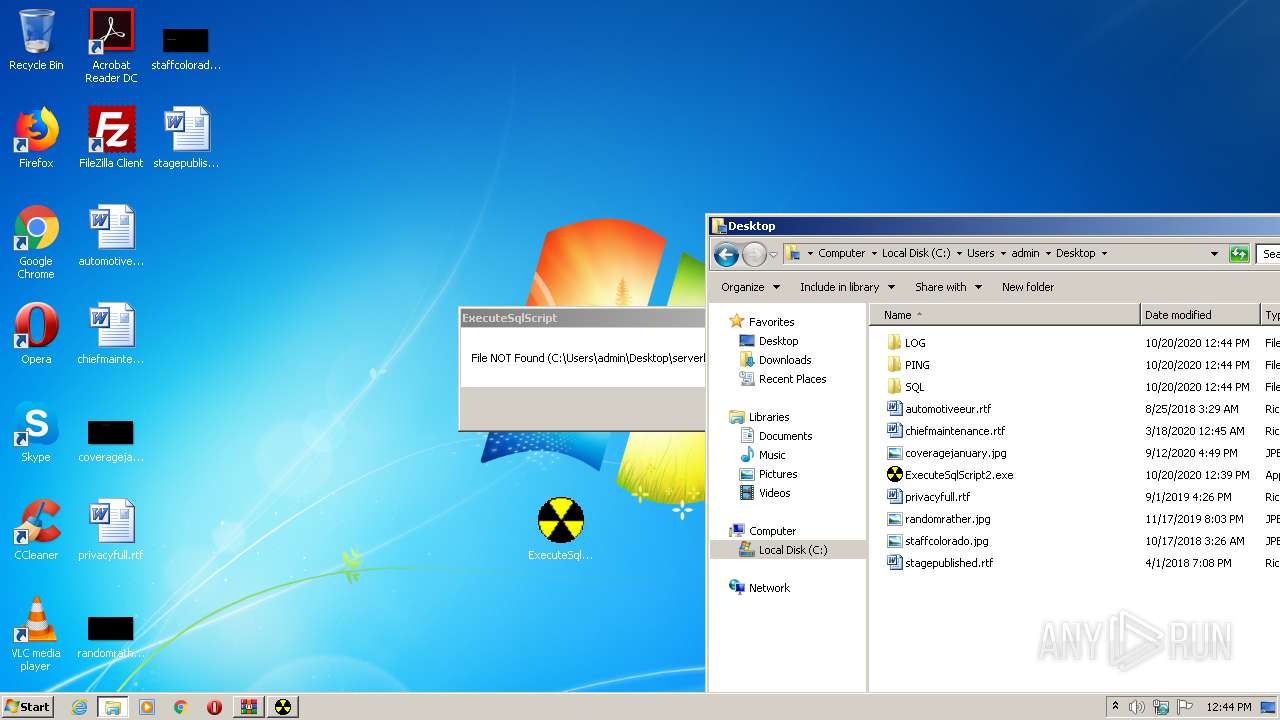
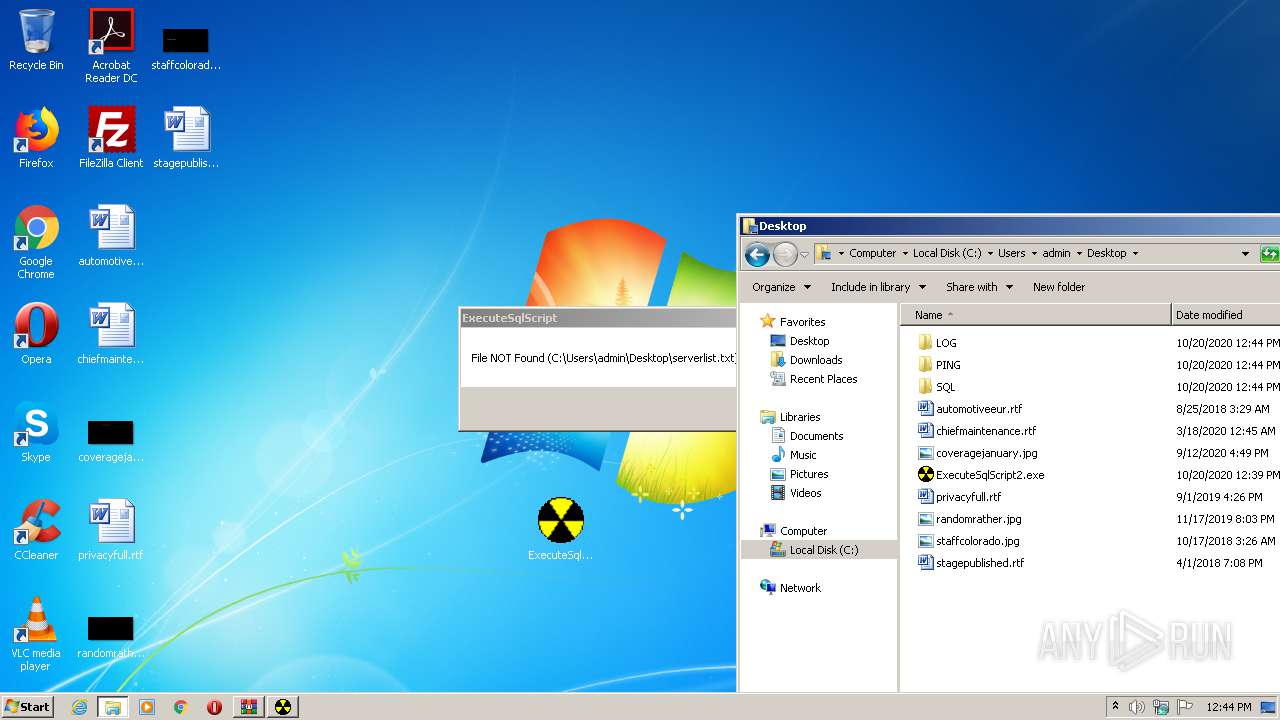
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
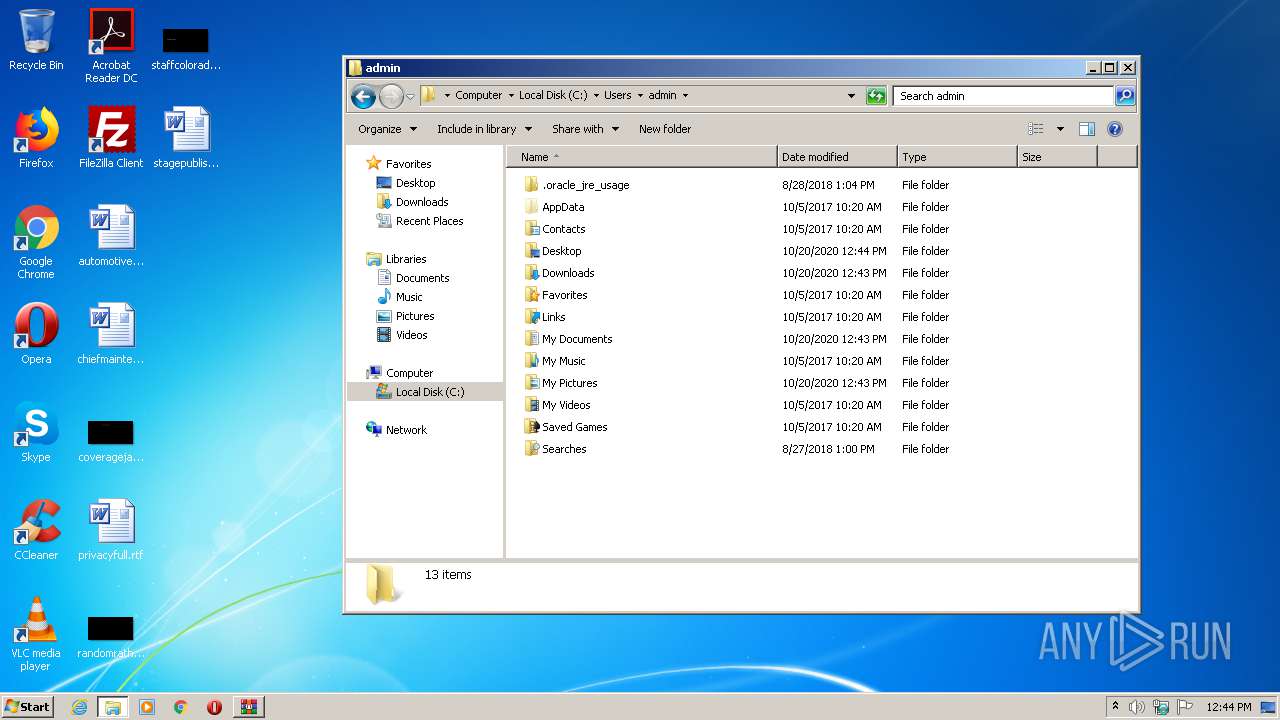
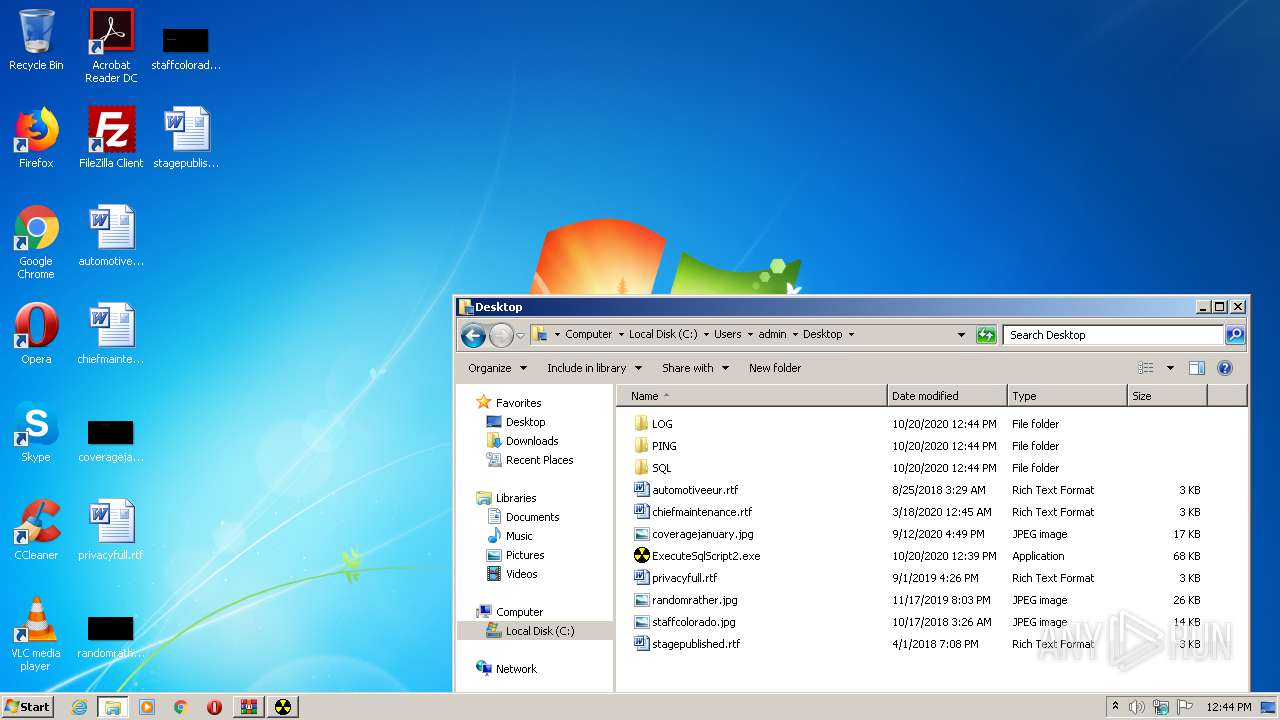
| 2388 | "C:\Users\admin\Desktop\ExecuteSqlScript2.exe" | C:\Users\admin\Desktop\ExecuteSqlScript2.exe | — | explorer.exe | |||||||||||
User: admin Company: IBM Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2708 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\serverlist.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2884 | "C:\Users\admin\Desktop\ExecuteSqlScript2.exe" | C:\Users\admin\Desktop\ExecuteSqlScript2.exe | — | explorer.exe | |||||||||||
User: admin Company: IBM Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
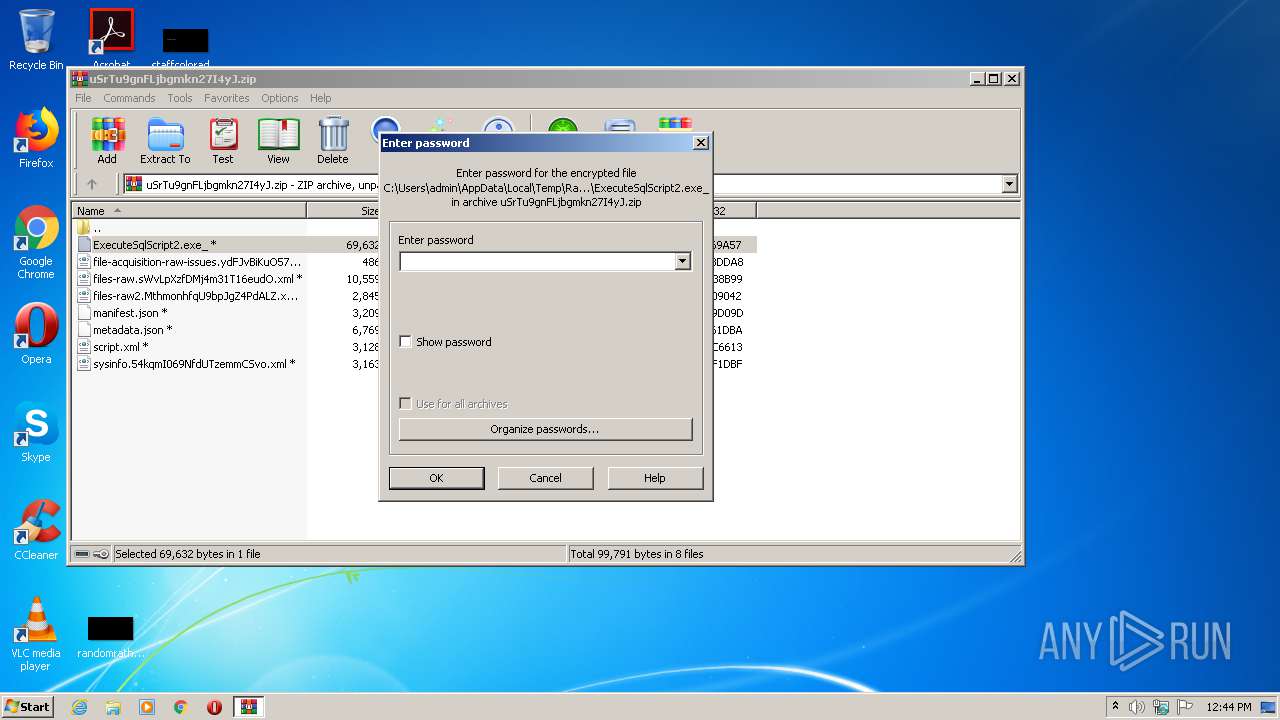
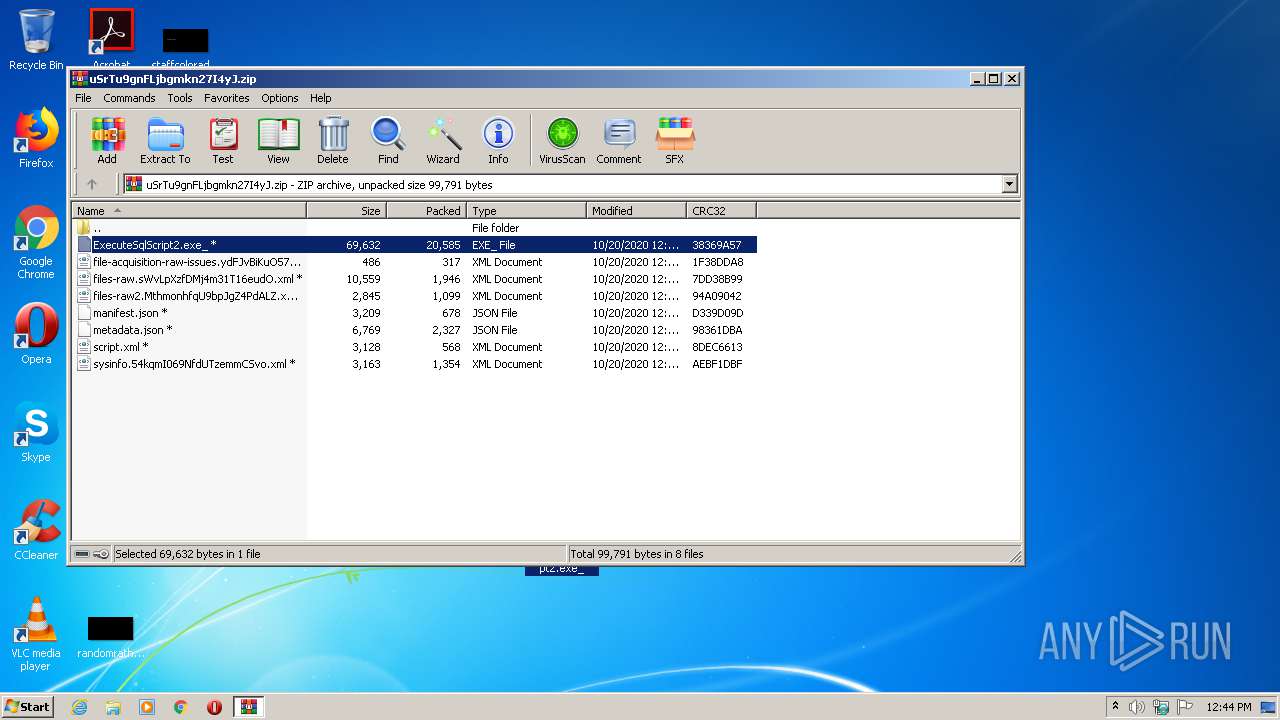
| 2940 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\uSrTu9gnFLjbgmkn27I4yJ.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3024 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\Desktop\ExecuteSqlScript2.exe" | C:\Users\admin\Desktop\ExecuteSqlScript2.exe | — | explorer.exe | |||||||||||
User: admin Company: IBM Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
482
Read events
467
Write events
15
Delete events
0
Modification events
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\uSrTu9gnFLjbgmkn27I4yJ.zip | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msxml3r.dll,-1 |
Value: XML Document | |||
| (PID) Process: | (2940) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2940.7144\ExecuteSqlScript2.exe_ | — | |
MD5:— | SHA256:— | |||
| 3652 | ExecuteSqlScript2.exe | C:\Users\admin\Desktop\PING\PING_20102020_124524.txt | text | |
MD5:— | SHA256:— | |||
| 2708 | NOTEPAD.EXE | C:\Users\admin\Desktop\serverlist.txt | text | |
MD5:F528764D624DB129B32C21FBCA0CB8D6 | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report