| URL: | https://www.google.com/url?sa=t&source=web&rct=j&opi=89978449&url=https://www.youtube.com/watch?v=ofzQGxaQI2c&ved=2ahUKEwjP8ZynhPOJAxXK2QIHHdwNAhk4HhAWegQIFRAB&usg=AOvVaw1sznPiS27DzMa0VfR-hRI8 |
| Full analysis: | https://app.any.run/tasks/2e1860d1-6765-4e7a-8b95-62e0dc85f107 |
| Verdict: | Suspicious activity |
| Analysis date: | November 23, 2024, 19:31:28 |
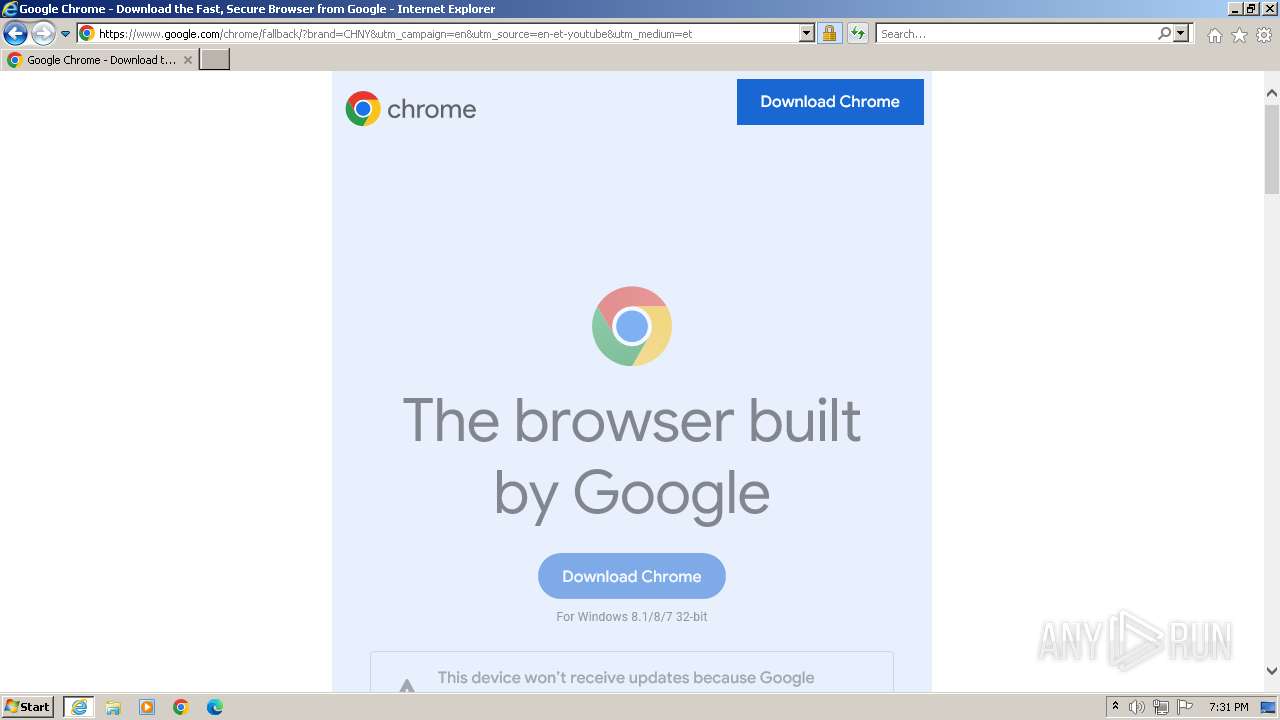
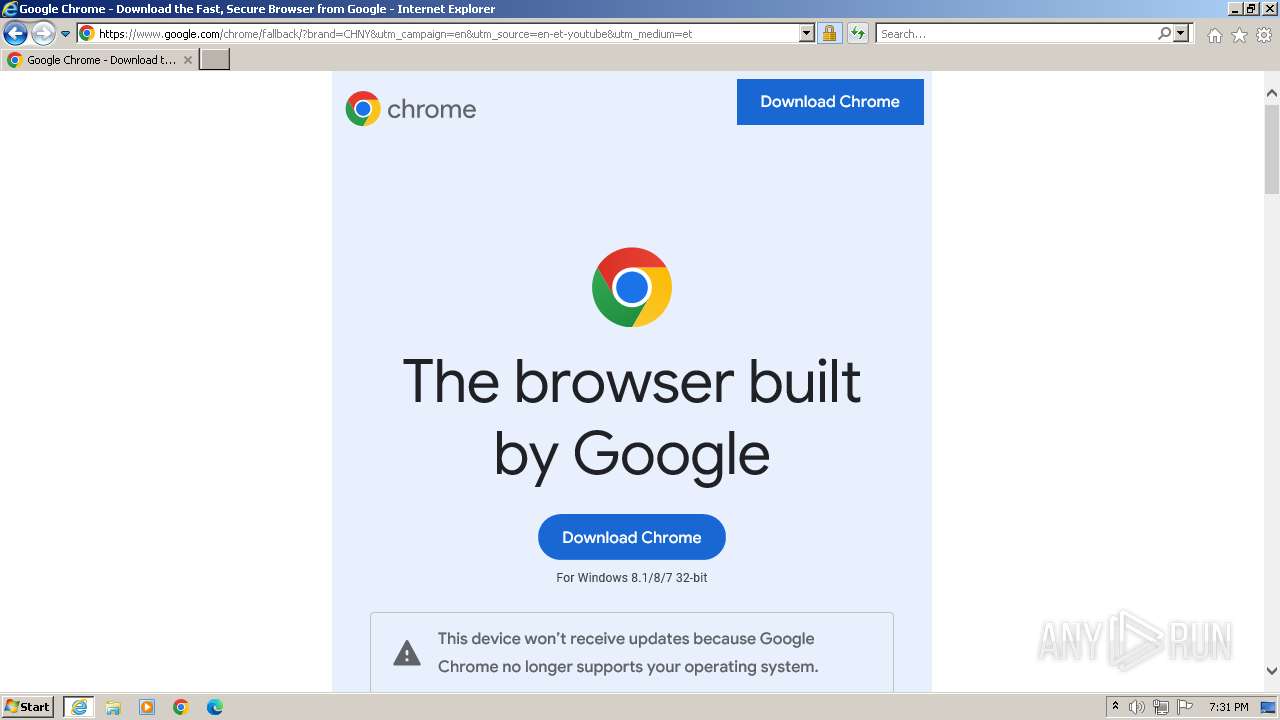
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A019D6646397E0E50418C389A0984E3B |
| SHA1: | CFCD005A92DACA343434CC4219BCFF1D944608A0 |
| SHA256: | C54DCE08C0A05766AE839DCF8DB8FF19B2BD81E966FFF66E30FEA96E190FBFC1 |
| SSDEEP: | 3:N8DSLI2sljXoW+PhIDNRRVYrSLUxGTKSEIYnow2UTxENbKnkX0sfiRtVANnDeJLf:2OLI2slQpUNRROGLUxGF5Y72UTCN2nk8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
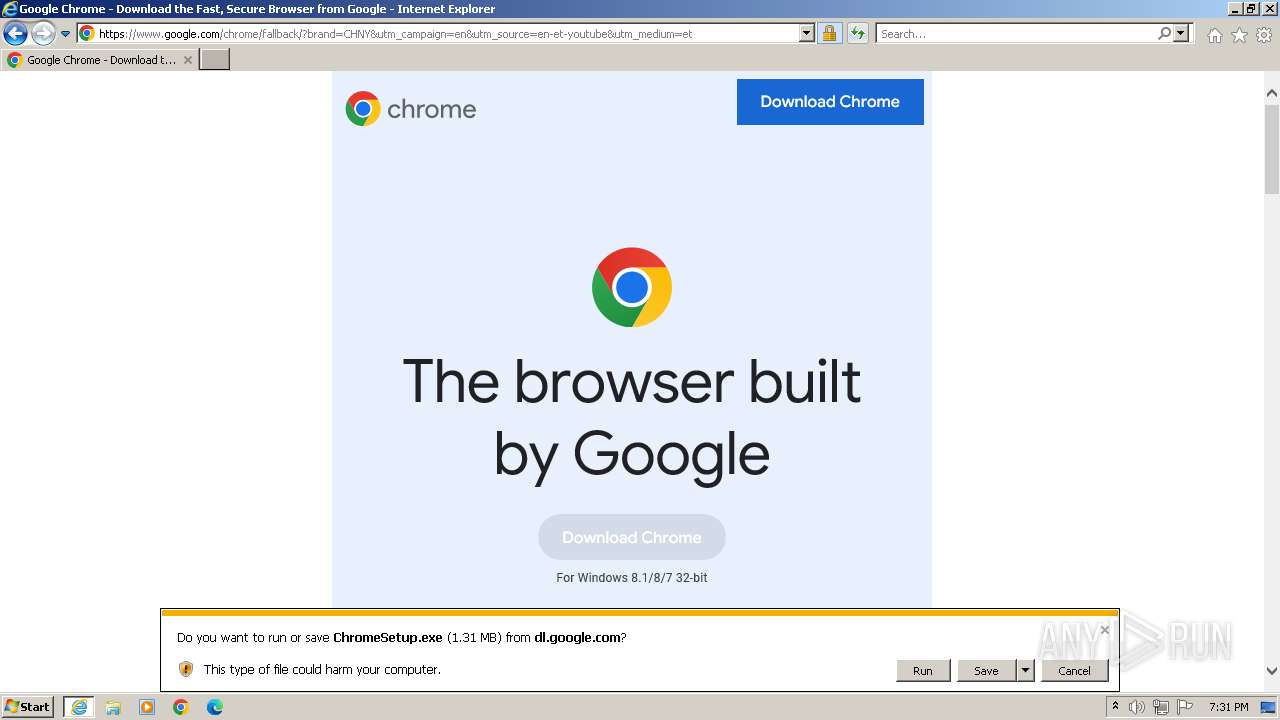
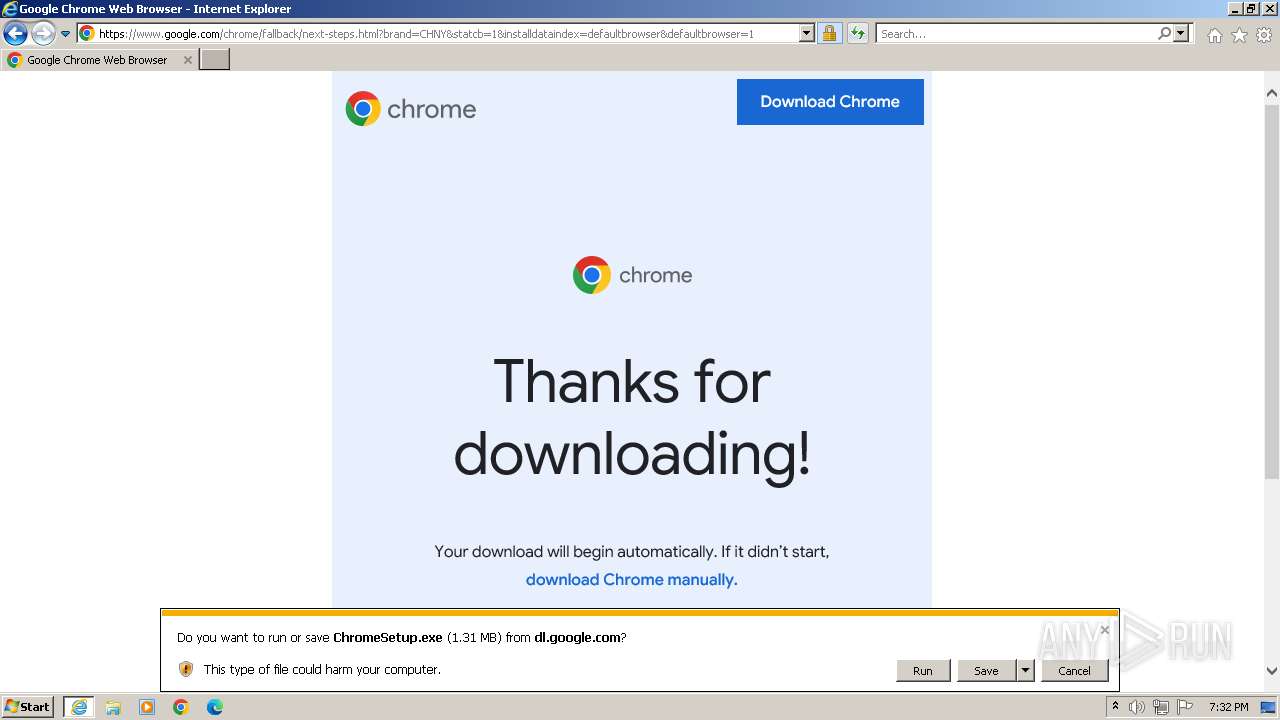
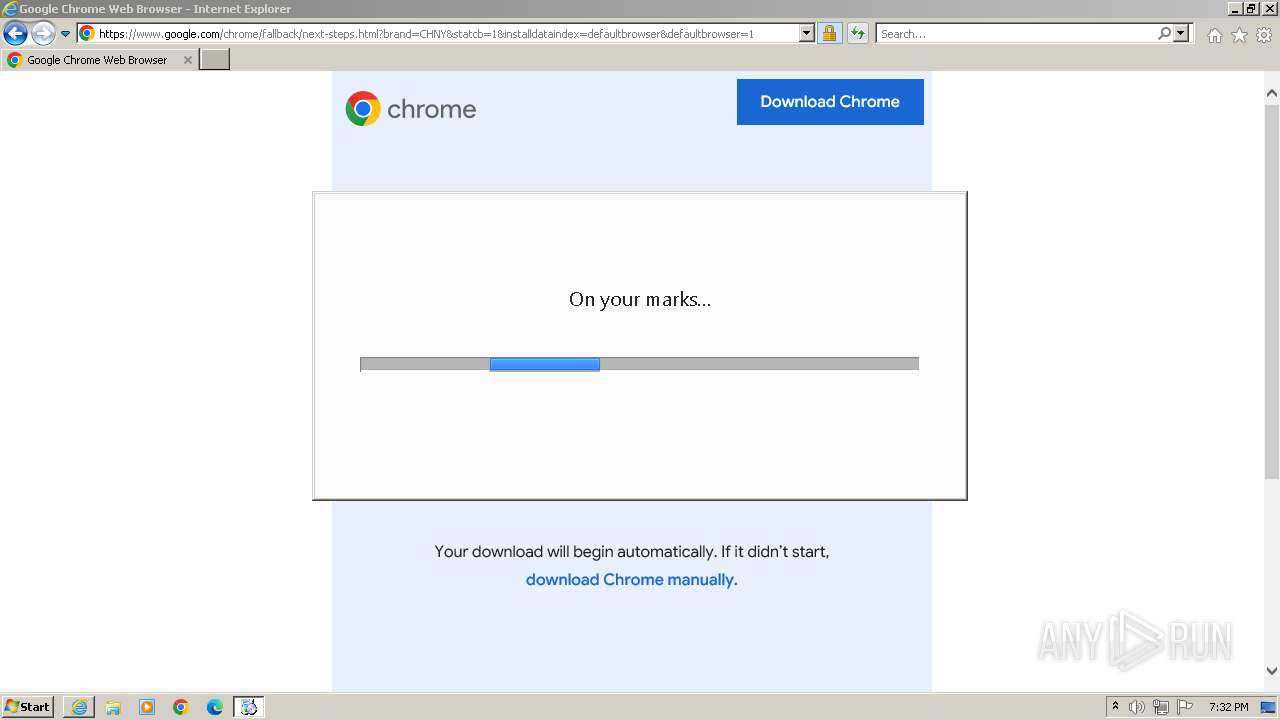
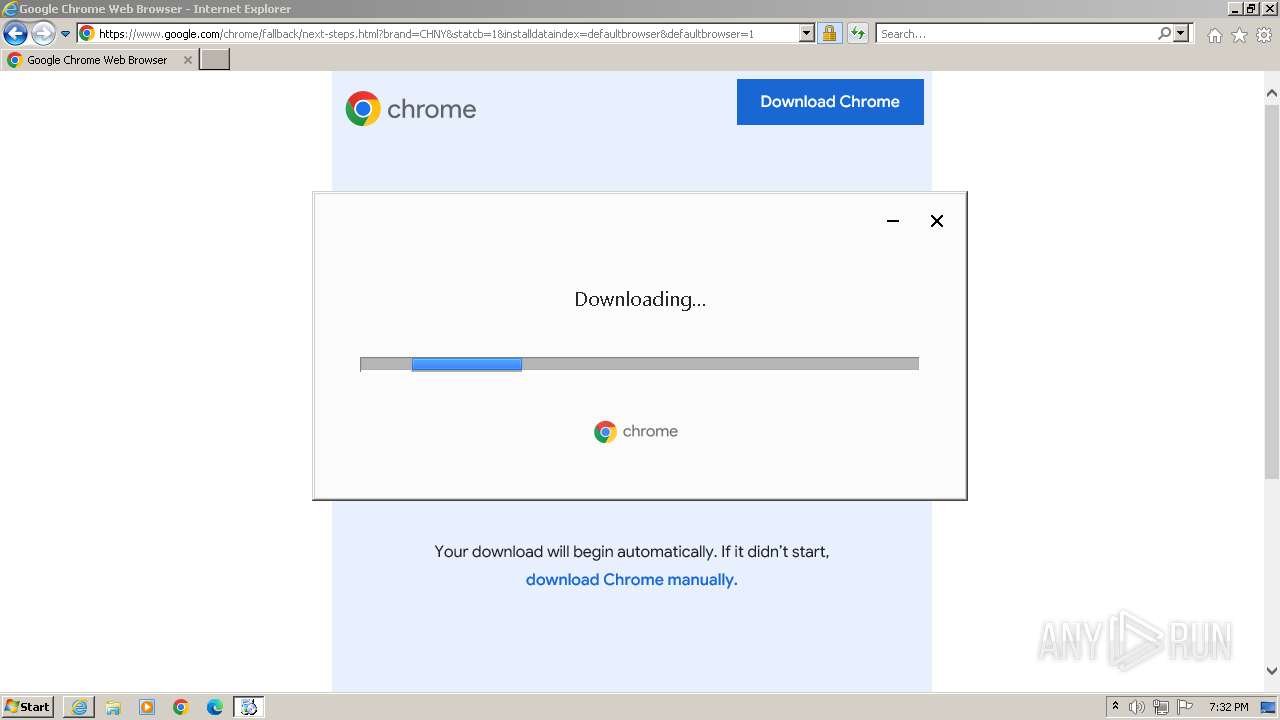
Executable content was dropped or overwritten
- ChromeSetup.exe (PID: 1288)
- GoogleUpdateSetup.exe (PID: 3292)
- GoogleUpdate.exe (PID: 3136)
Disables SEHOP
- GoogleUpdate.exe (PID: 3136)
Creates/Modifies COM task schedule object
- GoogleUpdate.exe (PID: 3260)
Reads the Internet Settings
- GoogleUpdate.exe (PID: 3324)
- GoogleUpdate.exe (PID: 3088)
Executes as Windows Service
- GoogleUpdate.exe (PID: 1236)
Reads settings of System Certificates
- GoogleUpdate.exe (PID: 3324)
Reads security settings of Internet Explorer
- GoogleUpdate.exe (PID: 3088)
INFO
Manual execution by a user
- wmpnscfg.exe (PID: 3116)
Reads the computer name
- wmpnscfg.exe (PID: 3116)
- GoogleUpdate.exe (PID: 1424)
- GoogleUpdate.exe (PID: 3136)
- GoogleUpdate.exe (PID: 3208)
- GoogleUpdate.exe (PID: 3260)
- GoogleUpdate.exe (PID: 3324)
- GoogleUpdate.exe (PID: 3088)
- GoogleUpdate.exe (PID: 1236)
Checks supported languages
- wmpnscfg.exe (PID: 3116)
- ChromeSetup.exe (PID: 1288)
- GoogleUpdate.exe (PID: 1424)
- GoogleUpdateSetup.exe (PID: 3292)
- GoogleUpdate.exe (PID: 3136)
- GoogleUpdate.exe (PID: 3208)
- GoogleUpdate.exe (PID: 3260)
- GoogleUpdate.exe (PID: 3324)
- GoogleUpdate.exe (PID: 3088)
- GoogleUpdate.exe (PID: 1236)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1568)
Executable content was dropped or overwritten
- iexplore.exe (PID: 1568)
- iexplore.exe (PID: 116)
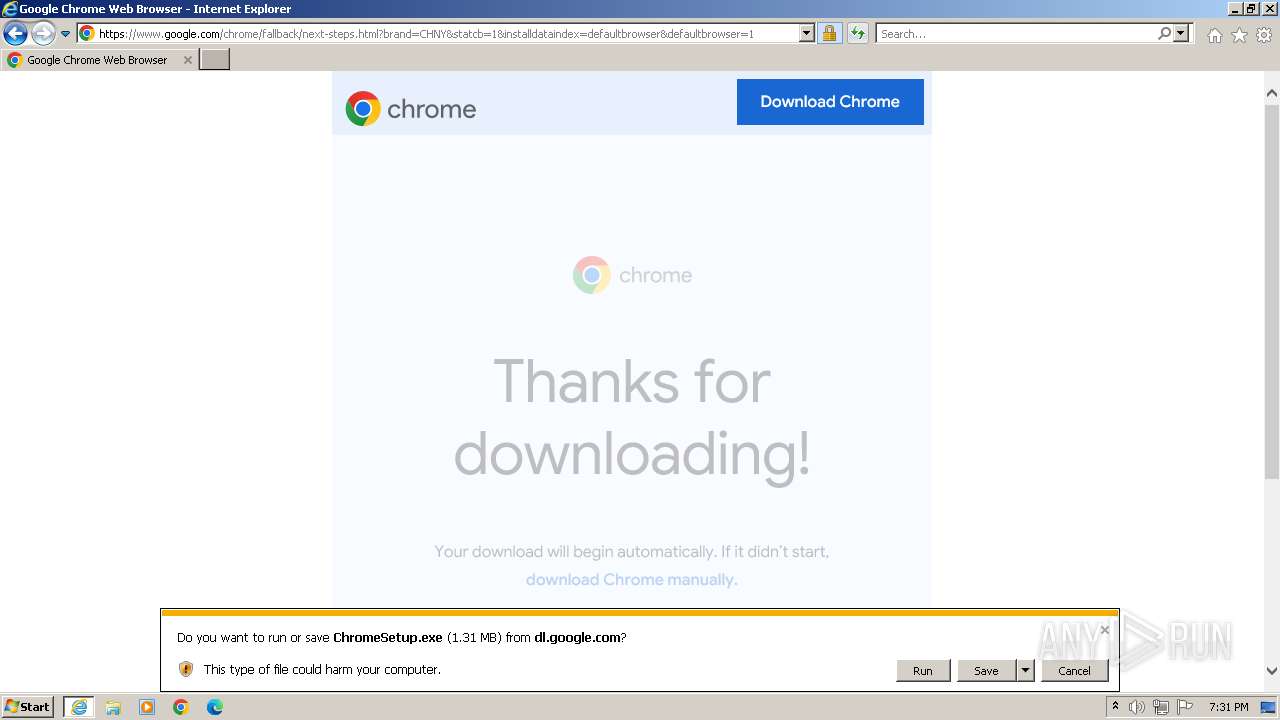
The process uses the downloaded file
- iexplore.exe (PID: 1568)
- ChromeSetup.exe (PID: 1288)
- GoogleUpdateSetup.exe (PID: 3292)
Application launched itself
- iexplore.exe (PID: 1568)
Create files in a temporary directory
- ChromeSetup.exe (PID: 1288)
Reads the machine GUID from the registry
- GoogleUpdate.exe (PID: 1424)
- GoogleUpdate.exe (PID: 3136)
- GoogleUpdate.exe (PID: 3088)
- GoogleUpdate.exe (PID: 1236)
Creates files in the program directory
- GoogleUpdateSetup.exe (PID: 3292)
- GoogleUpdate.exe (PID: 3136)
- GoogleUpdate.exe (PID: 3208)
- GoogleUpdate.exe (PID: 3260)
- GoogleUpdate.exe (PID: 3324)
- GoogleUpdate.exe (PID: 3088)
- GoogleUpdate.exe (PID: 1236)
Reads the software policy settings
- GoogleUpdate.exe (PID: 3324)
Checks proxy server information
- GoogleUpdate.exe (PID: 3088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
12
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1568 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /svc | C:\Program Files\Google\Update\GoogleUpdate.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Google Inc. Integrity Level: SYSTEM Description: Google Installer Version: 1.3.33.23 Modules
| |||||||||||||||
| 1288 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\ChromeSetup.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\ChromeSetup.exe | iexplore.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Update Setup Version: 1.3.36.372 Modules
| |||||||||||||||
| 1424 | C:\Users\admin\AppData\Local\Temp\GUM1C.tmp\GoogleUpdate.exe /installsource taggedmi /install "appguid={8A69D345-D564-463C-AFF1-A69D9E530F96}&iid={6E5DFD98-0595-3D82-94B1-1E143A6B223A}&lang=en&browser=2&usagestats=1&appname=Google%20Chrome&needsadmin=prefers&ap=x86-statsdef_1&brand=CHNY&installdataindex=defaultbrowser" | C:\Users\admin\AppData\Local\Temp\GUM1C.tmp\GoogleUpdate.exe | — | ChromeSetup.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Installer Version: 1.3.36.371 Modules
| |||||||||||||||
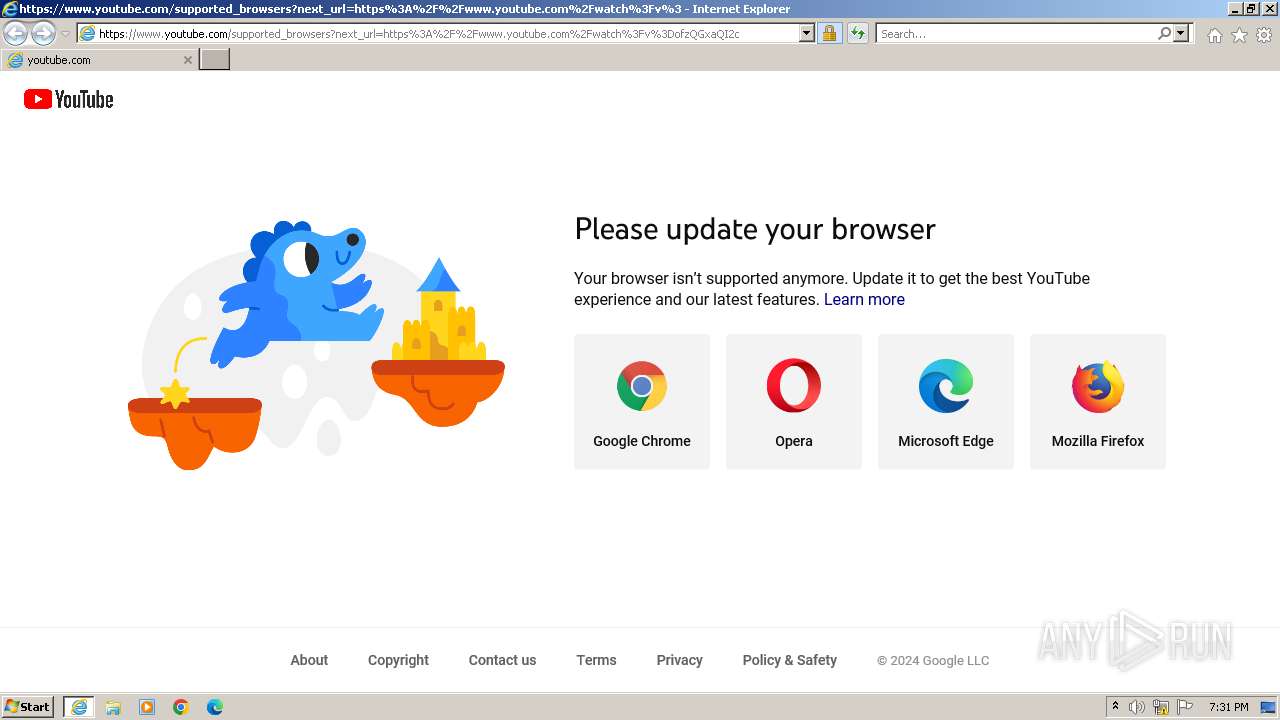
| 1568 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.google.com/url?sa=t&source=web&rct=j&opi=89978449&url=https://www.youtube.com/watch?v=ofzQGxaQI2c&ved=2ahUKEwjP8ZynhPOJAxXK2QIHHdwNAhk4HhAWegQIFRAB&usg=AOvVaw1sznPiS27DzMa0VfR-hRI8" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3088 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /handoff "appguid={8A69D345-D564-463C-AFF1-A69D9E530F96}&iid={6E5DFD98-0595-3D82-94B1-1E143A6B223A}&lang=en&browser=2&usagestats=1&appname=Google%20Chrome&needsadmin=prefers&ap=x86-statsdef_1&brand=CHNY&installdataindex=defaultbrowser" /installsource taggedmi /sessionid "{8362F42D-02FC-412F-A33A-84212D1D7258}" | C:\Program Files\Google\Update\GoogleUpdate.exe | GoogleUpdate.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Version: 1.3.33.23 Modules
| |||||||||||||||
| 3116 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3136 | "C:\Program Files\Google\Temp\GUM453.tmp\GoogleUpdate.exe" /installsource taggedmi /install "appguid={8A69D345-D564-463C-AFF1-A69D9E530F96}&iid={6E5DFD98-0595-3D82-94B1-1E143A6B223A}&lang=en&browser=2&usagestats=1&appname=Google%20Chrome&needsadmin=prefers&ap=x86-statsdef_1&brand=CHNY&installdataindex=defaultbrowser" /installelevated | C:\Program Files\Google\Temp\GUM453.tmp\GoogleUpdate.exe | GoogleUpdateSetup.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Installer Version: 1.3.36.371 Modules
| |||||||||||||||
| 3208 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /regsvc | C:\Program Files\Google\Update\GoogleUpdate.exe | — | GoogleUpdate.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 3260 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /regserver | C:\Program Files\Google\Update\GoogleUpdate.exe | — | GoogleUpdate.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
Total events
21 905
Read events
21 577
Write events
202
Delete events
126
Modification events
| (PID) Process: | (1568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31145438 | |||
| (PID) Process: | (1568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31145438 | |||
| (PID) Process: | (1568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
206
Suspicious files
35
Text files
47
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:306AFF357F51DE2FD0C763D3615C0443 | SHA256:C8D5E5F06D246B3B0FBFBE7058CACC1F2F25F291F63B4ECBE721DF97DA3312D7 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:9083B95564A12E0EDB0AC8812C0AC40A | SHA256:62B6EA7B8ADAE7E9DBA5BBDB2CF7B8422DCEA25DD0111D72F8145B39ABEF688B | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\4FA45AE1010E09657982D8D28B3BD38E_841DF67C840691A847835C0F760B4DC0 | binary | |
MD5:BE8B7C9C5CFB9D55FB5182DAE2EE412C | SHA256:7026E18AAB9F8C98ED2C0140403DCC8E96227D5E57EE35165EBDD1AA2ECC962A | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\supported_browsers[1].htm | html | |
MD5:053FE7D16CE01EA4AA311149BD5DF5C1 | SHA256:96F85625E55440AA91B0C41018B4B2A62931DCD6F82DF47966BBF47ACB171772 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\yt_logo_rgb_light[1].png | image | |
MD5:D654F892F287A28026CD4D4DF56C29C8 | SHA256:FC6F5D8F32F13D5855840234DC1BFF5C91C35318EE2192D99B13EB3572F0BCA8 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C02877841121CC45139CB51404116B25_16659210B029E2342348119FD8382C02 | binary | |
MD5:8CA104C0E1E82BDB88A70B53FF53D537 | SHA256:20D2D35B1013E3DB6413AB4F30AE542CBA780F20B8B7FAF0BFDE77DA1880D155 | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\url[1].htm | binary | |
MD5:A96D1CE9B8539E20B18598E2280C59F7 | SHA256:72CA3B05116E22FC6078A4500D0F469008C1218E4C4BCE5FB4073802324521CB | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:1F150D231A2C309EA8546606D81C1A77 | SHA256:6F77C2522291B5A1413F6F6B8E5061E028C5C5E733CD00017C9584ABCB6D6CFC | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\JOCTCOHJ.txt | text | |
MD5:ECF1F3CBF3F4C4374E6D414147403601 | SHA256:B46967D1583958CBEAD1824A81A1B27AD06DFF40C09B88C00F4A991F75BB419D | |||
| 116 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C02877841121CC45139CB51404116B25_16659210B029E2342348119FD8382C02 | binary | |
MD5:B93F79B722C81A9AD4F604B8BEBDD68C | SHA256:F8915DEDAEEFE287B569C5EAEFF92F506C55A4CF4FB9A562AFE67E58F1186BAA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
57
DNS requests
21
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
116 | iexplore.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5e22539541d96f8b | unknown | — | — | whitelisted |
116 | iexplore.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?22d741c4b27dee88 | unknown | — | — | whitelisted |
116 | iexplore.exe | GET | 200 | 216.58.212.163:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | whitelisted |
116 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
116 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://o.pki.goog/wr2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEQCdnAM1WJ6jQhB6sJGT2Dti | unknown | — | — | whitelisted |
116 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://o.pki.goog/wr2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEQCm0zxQ5KDvqwpdQsrzXj3H | unknown | — | — | whitelisted |
116 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://o.pki.goog/wr2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEEGoFYJ0C3qQCbRh5xcgwPQ%3D | unknown | — | — | whitelisted |
116 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://o.pki.goog/wr2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEQDEGAgOcBEqfBC%2B1yioLDZa | unknown | — | — | whitelisted |
1568 | iexplore.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?19bcfd70676951c9 | unknown | — | — | whitelisted |
1568 | iexplore.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e21f9209887329b2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
116 | iexplore.exe | 172.217.16.196:443 | www.google.com | GOOGLE | US | whitelisted |
116 | iexplore.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
1108 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
116 | iexplore.exe | 142.250.181.227:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
116 | iexplore.exe | 216.58.212.163:80 | c.pki.goog | GOOGLE | US | whitelisted |
116 | iexplore.exe | 142.250.185.238:443 | www.youtube.com | GOOGLE | US | whitelisted |
116 | iexplore.exe | 142.250.181.234:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
c.pki.goog |
| whitelisted |
o.pki.goog |
| whitelisted |
www.youtube.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |