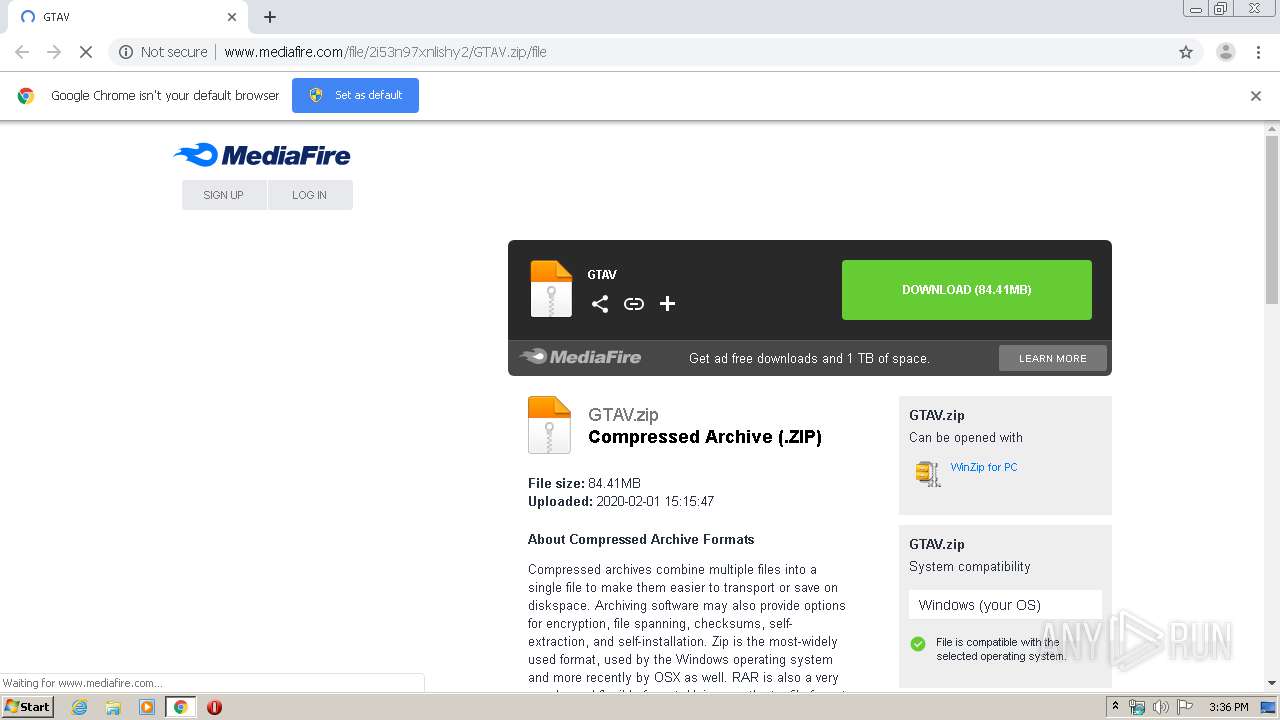
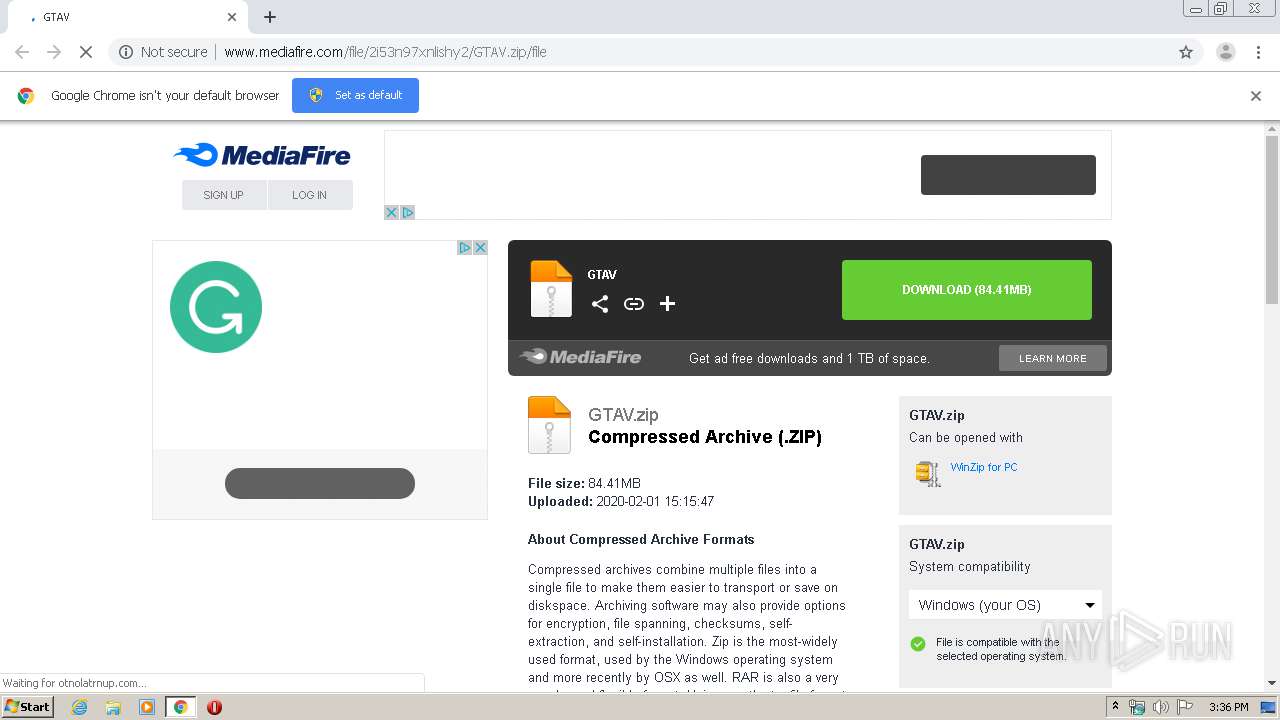
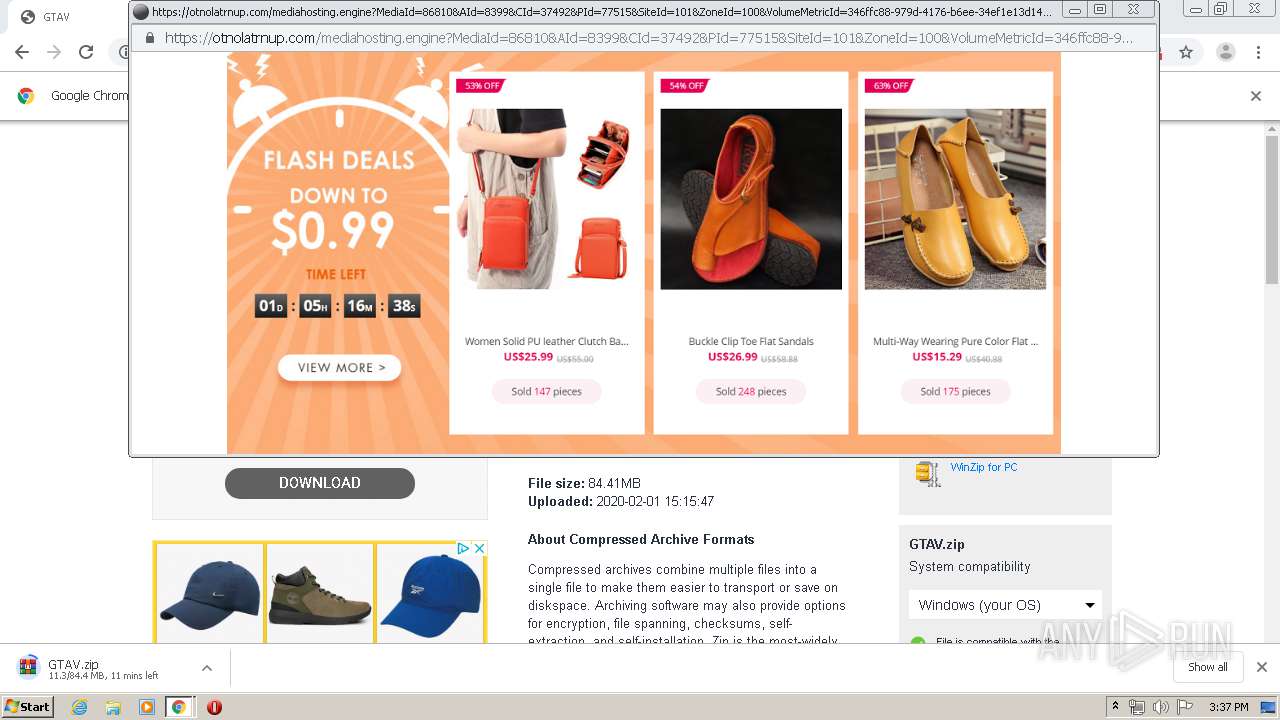
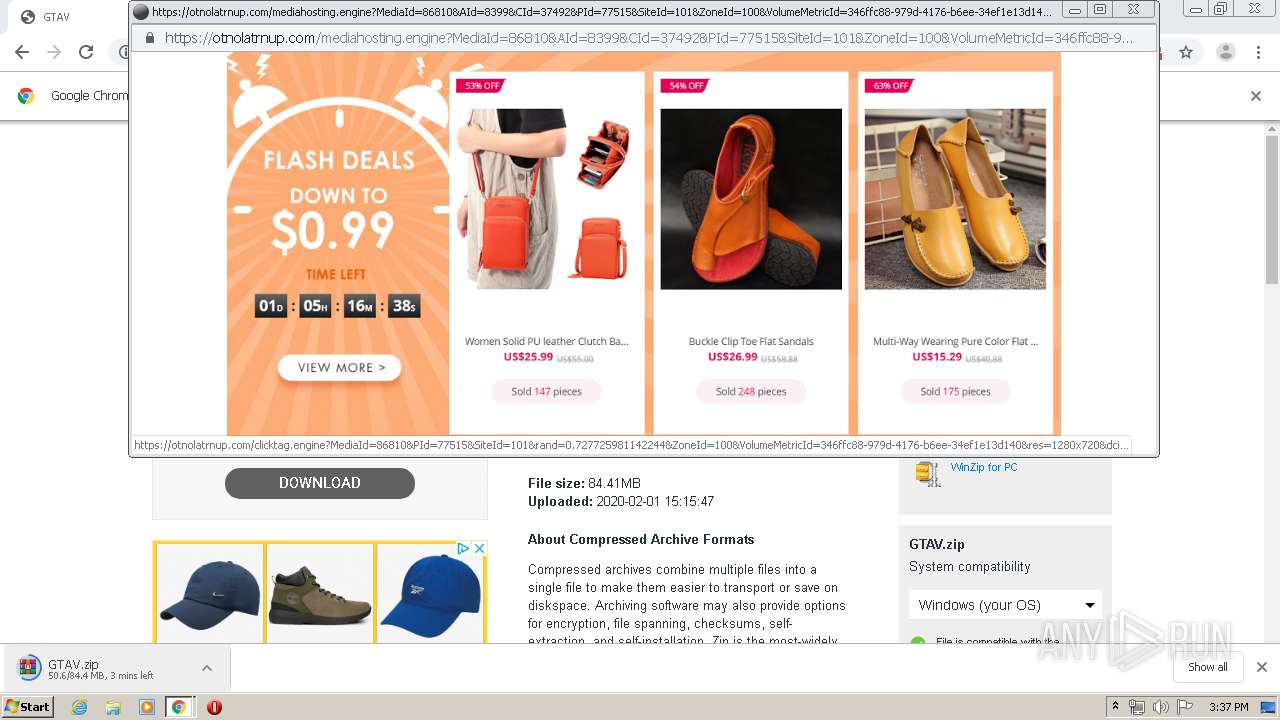
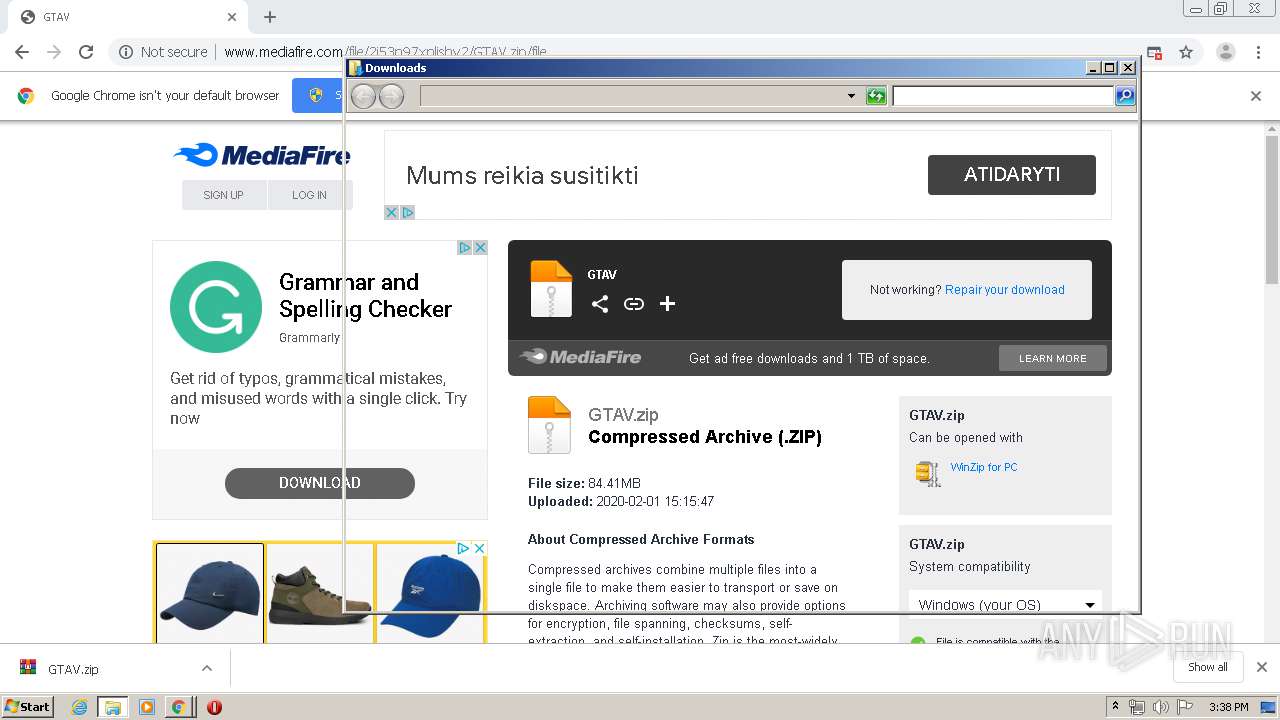
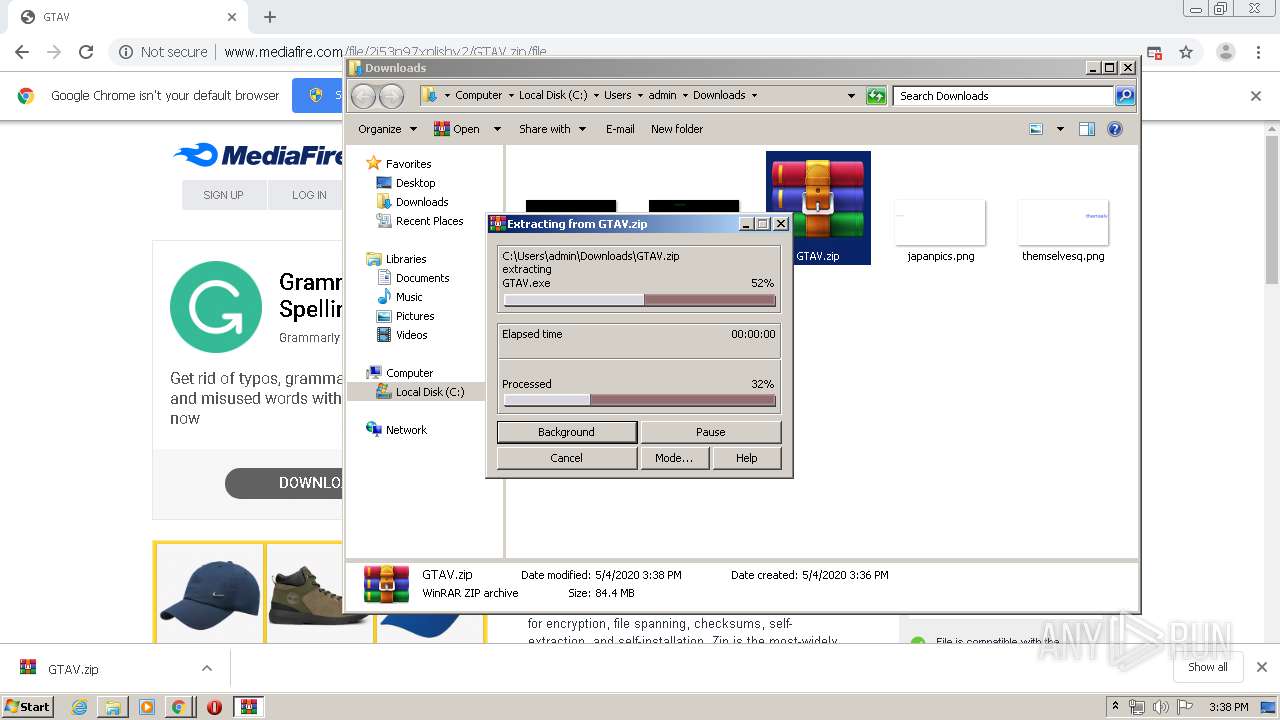
| URL: | http://www.mediafire.com/file/2i53n97xnlishy2/GTAV.zip/file |
| Full analysis: | https://app.any.run/tasks/bfa0c625-6d8b-4d1d-a5a6-489260b1a3c1 |
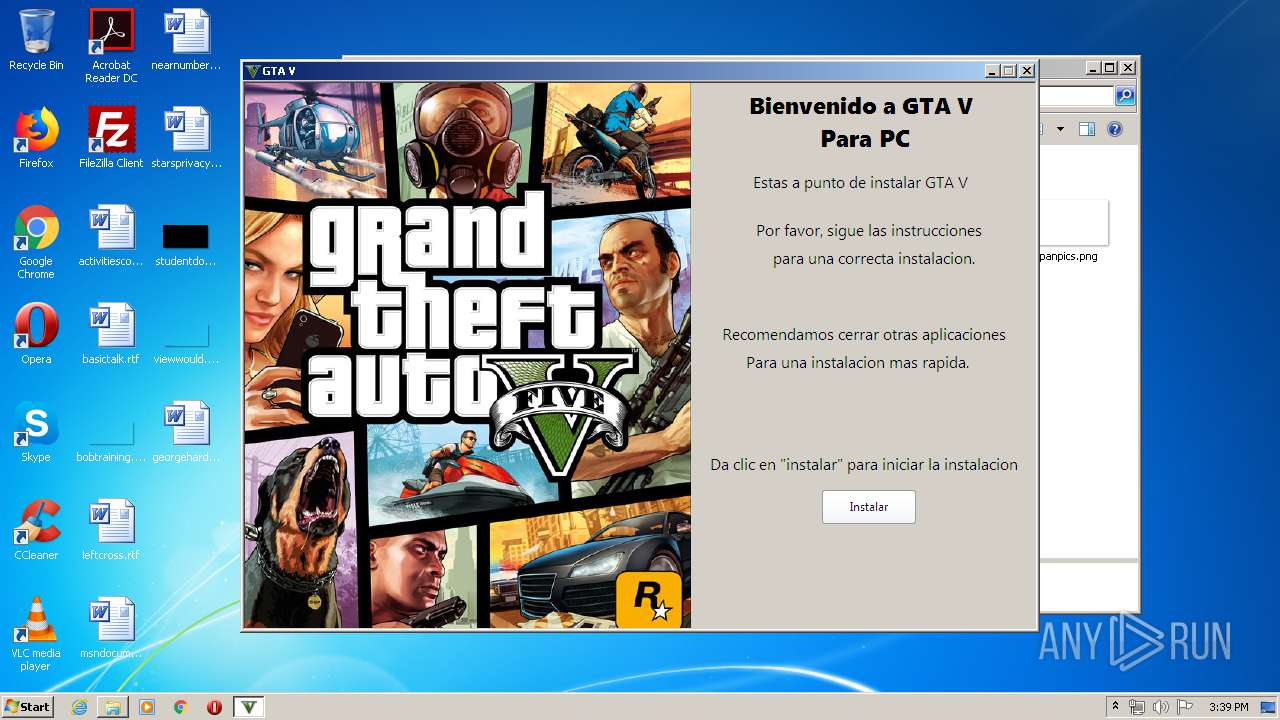
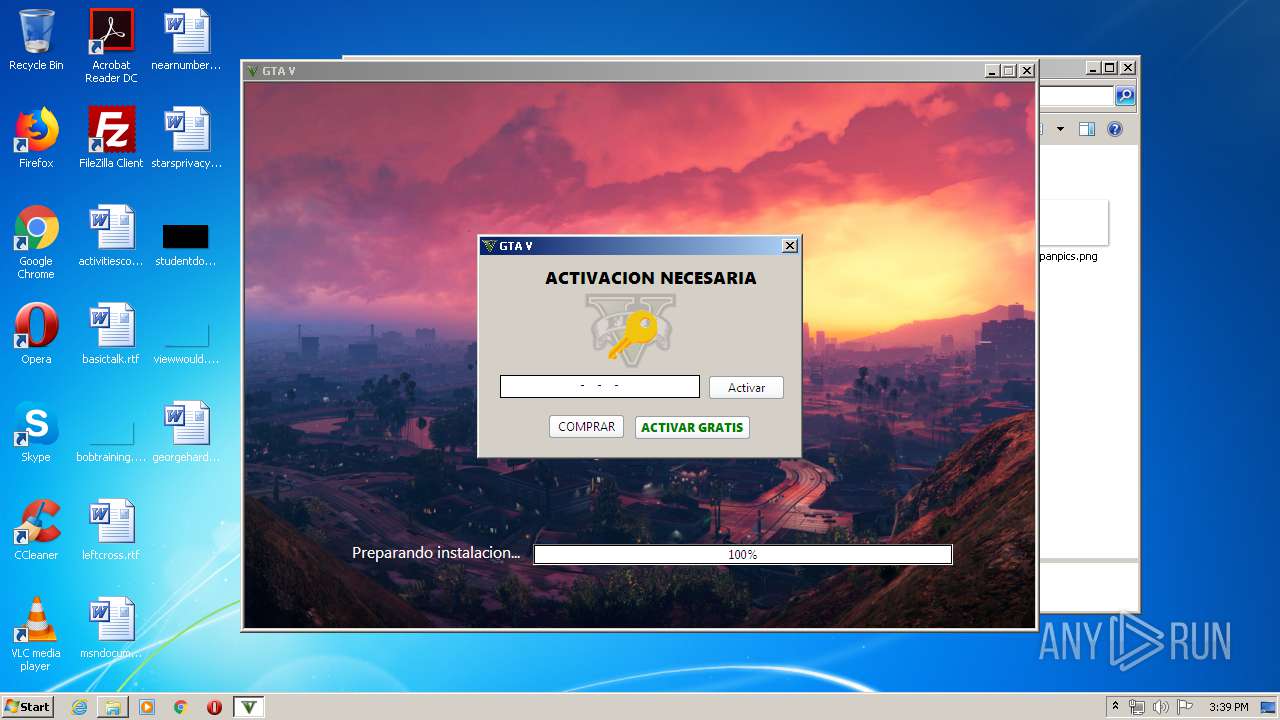
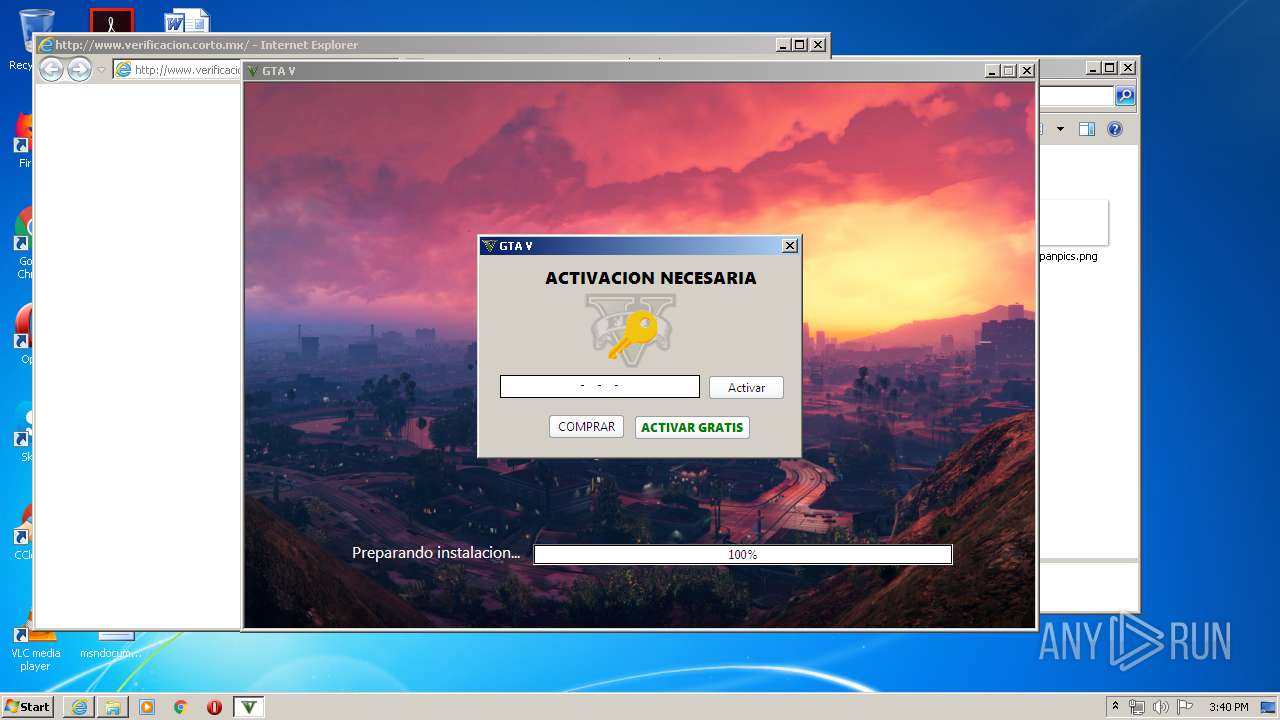
| Verdict: | Malicious activity |
| Analysis date: | May 04, 2020, 14:35:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 83F0BB19500EB49D43CFEFEFD39E2EE4 |
| SHA1: | 32DD2F8D9DC0654B19F5AFC1F88D6BA5DF99ABFA |
| SHA256: | C545A105C297A82F950EF03FC956FE0202F326E6B08A131E87318A8A55C98E1A |
| SSDEEP: | 3:N1KJS4w3eGUoXMQWLhuHXKiQHx:Cc4w3eGzMQWLHx |
MALICIOUS
Loads dropped or rewritten executable
- autorun.exe (PID: 3360)
Application was dropped or rewritten from another process
- autorun.exe (PID: 3360)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2344)
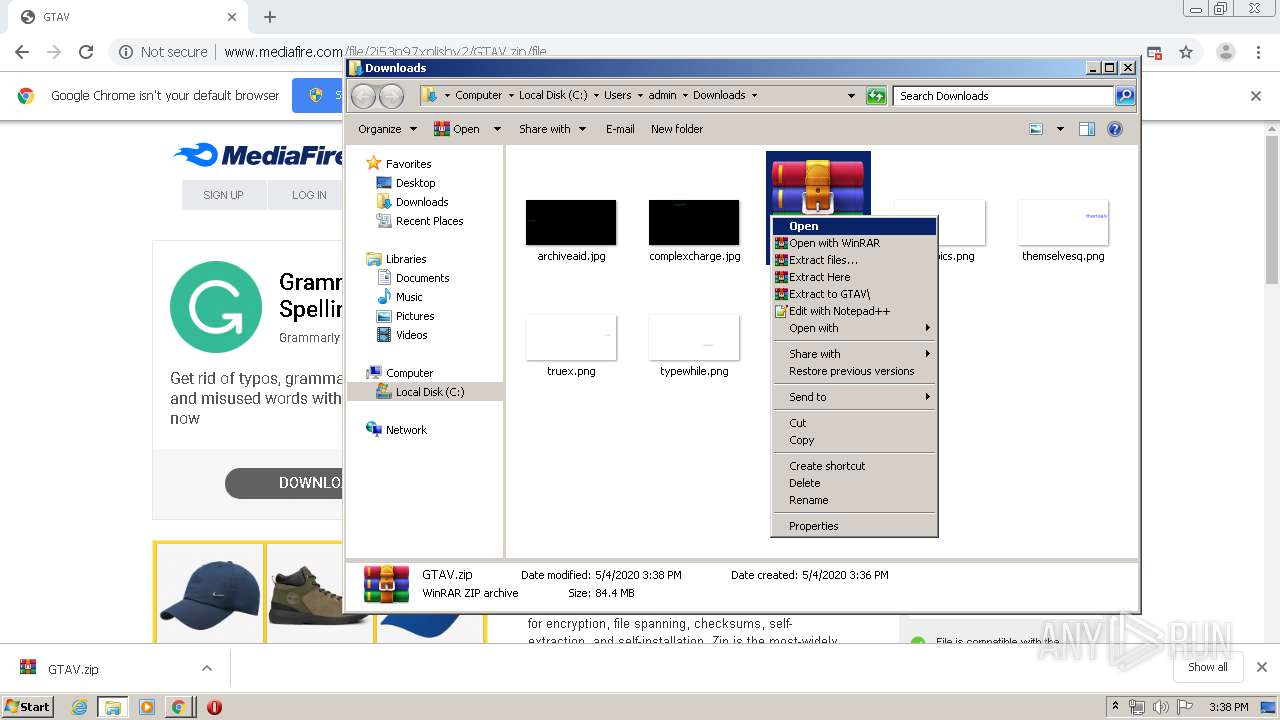
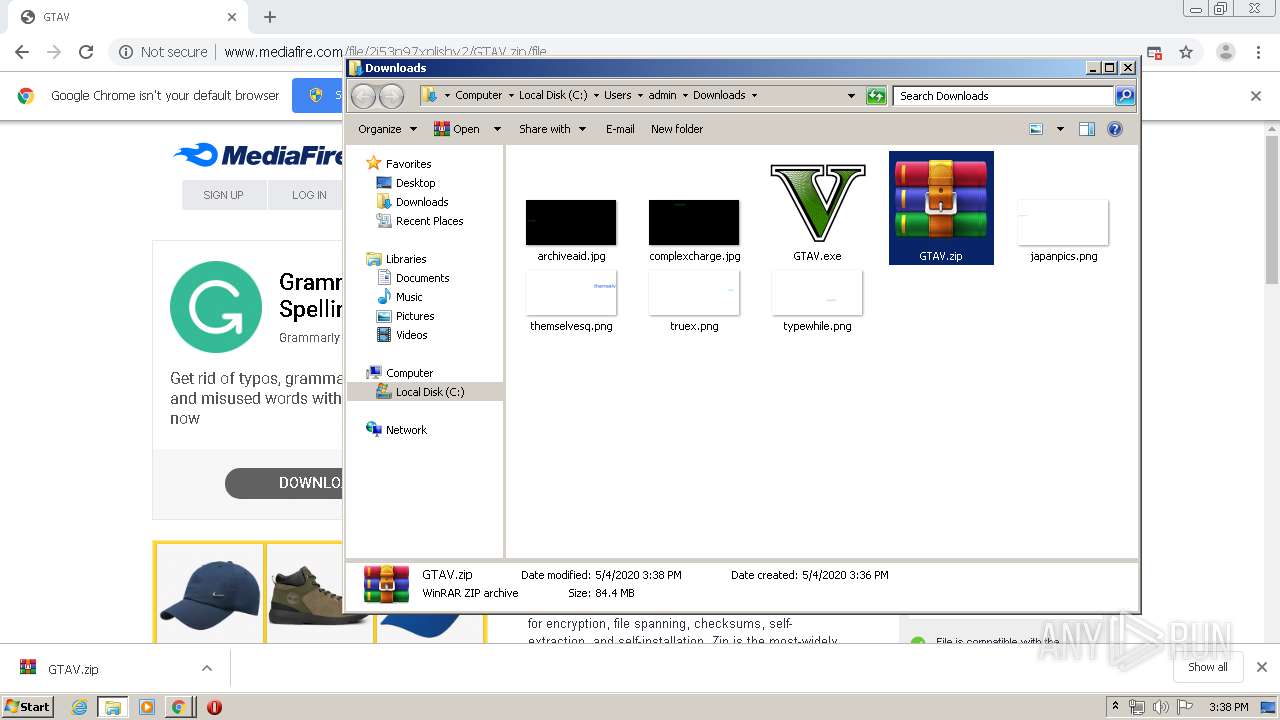
Executable content was dropped or overwritten
- GTAV.exe (PID: 1784)
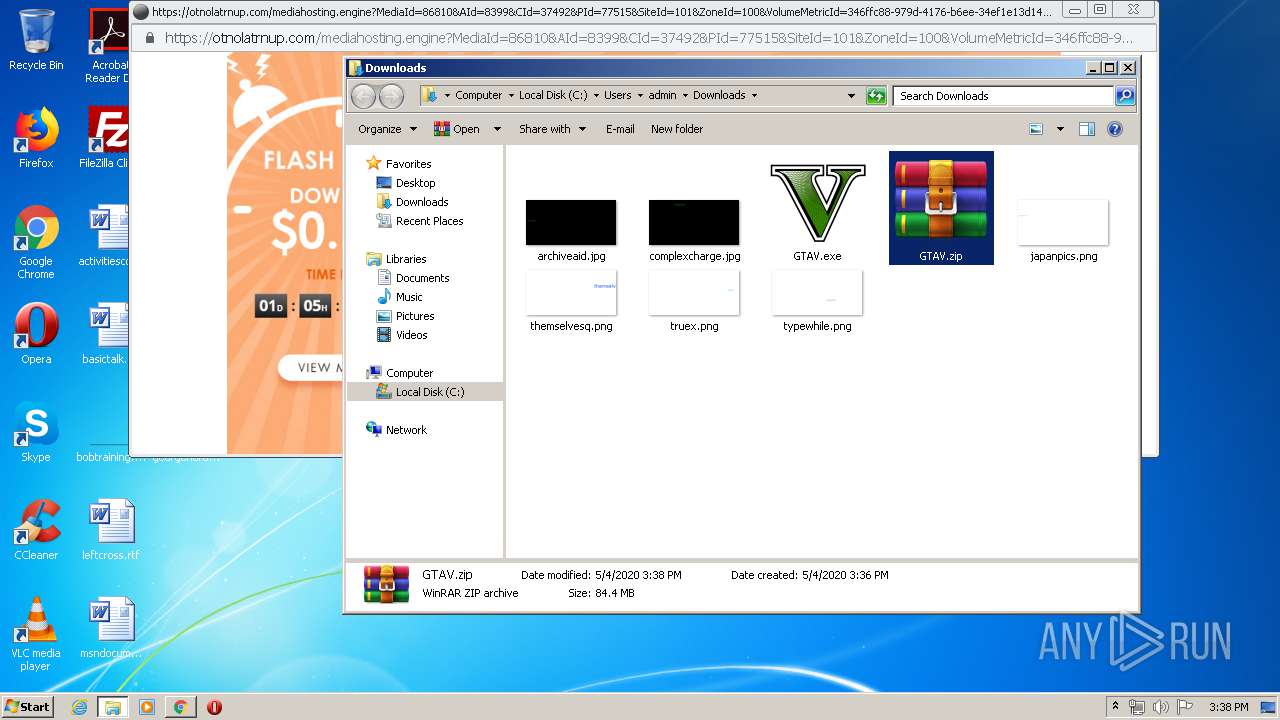
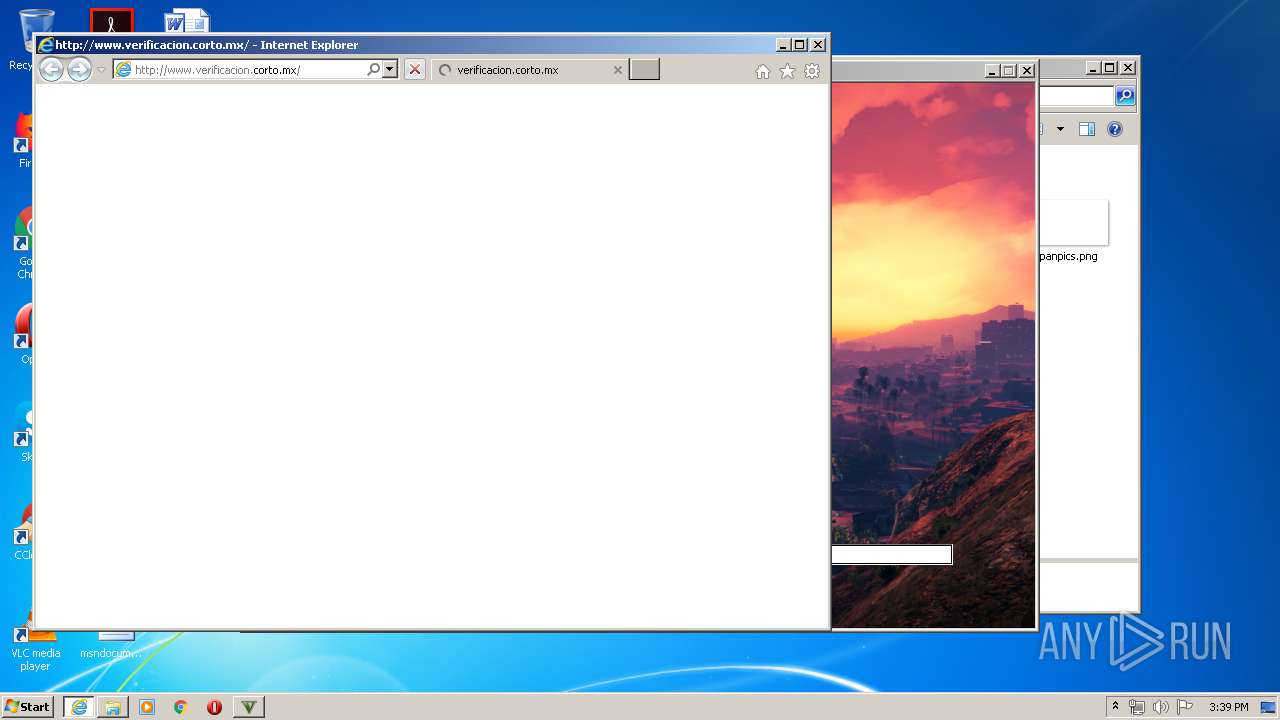
Starts Internet Explorer
- autorun.exe (PID: 3360)
INFO
Reads the hosts file
- chrome.exe (PID: 3968)
- chrome.exe (PID: 2344)
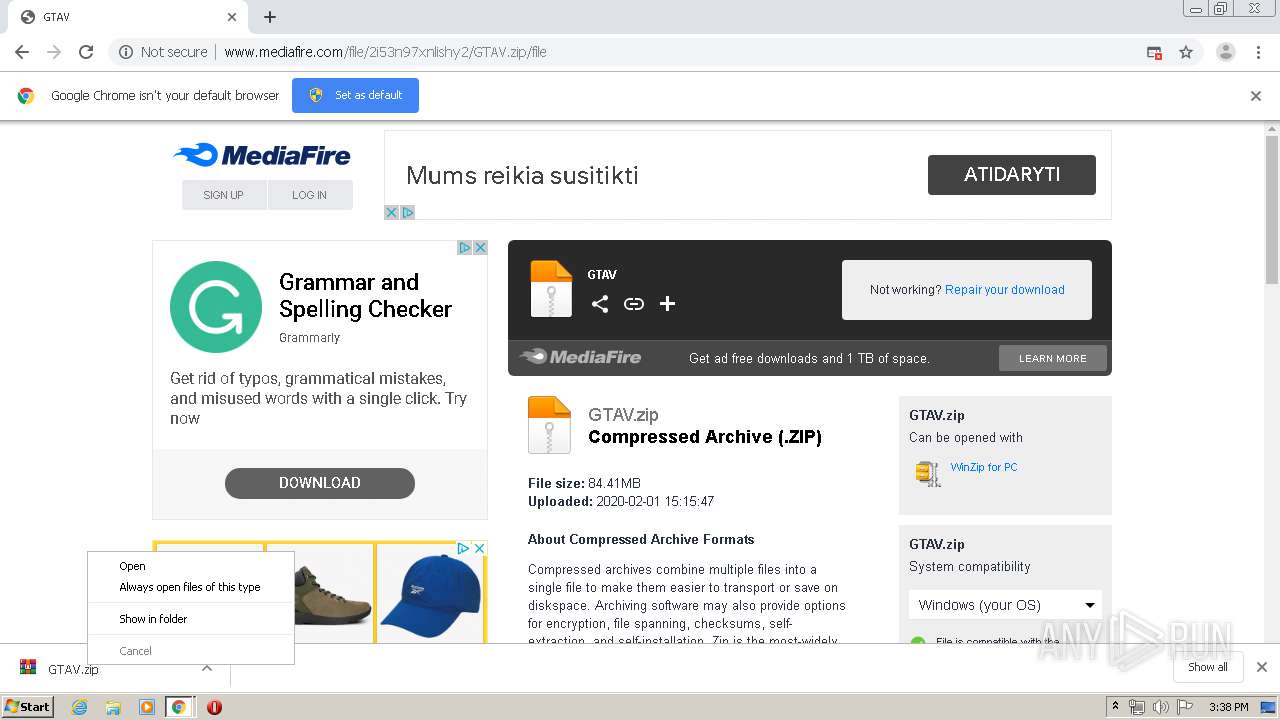
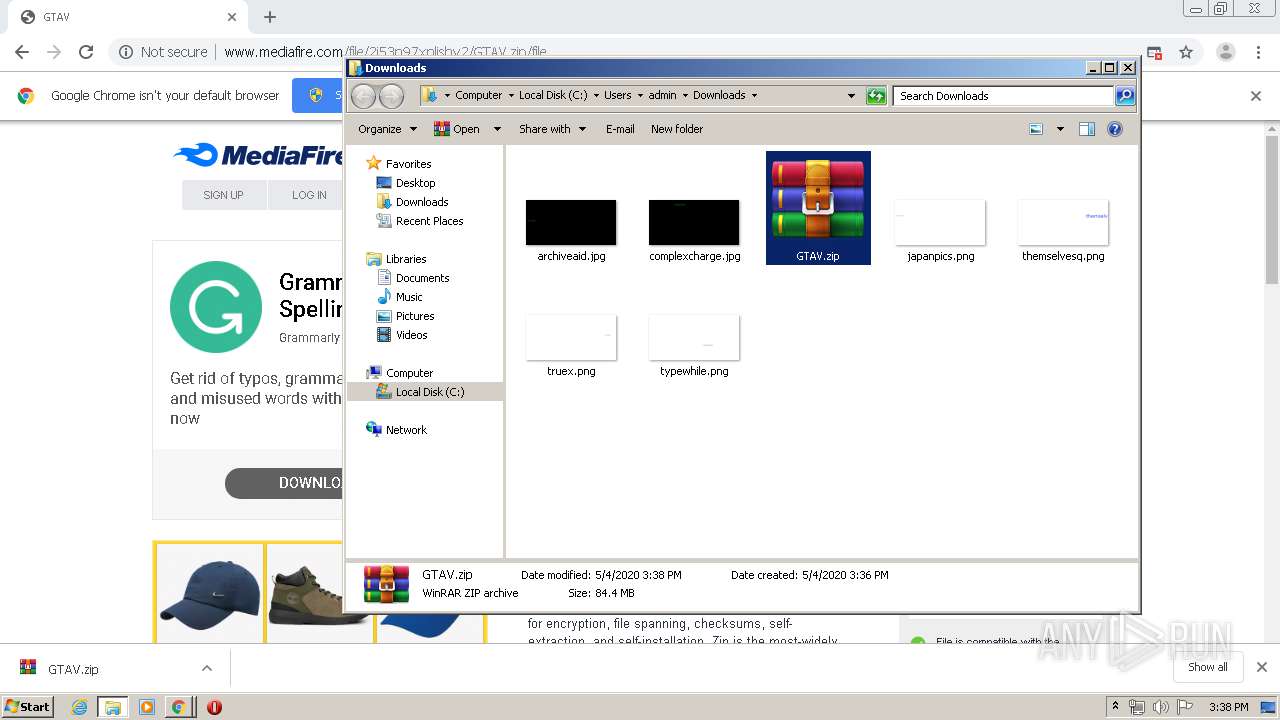
Manual execution by user
- WinRAR.exe (PID: 5944)
- GTAV.exe (PID: 1784)
Changes internet zones settings
- iexplore.exe (PID: 3908)
Reads internet explorer settings
- iexplore.exe (PID: 3220)
Application launched itself
- chrome.exe (PID: 2344)
- iexplore.exe (PID: 3908)
Reads Internet Cache Settings
- iexplore.exe (PID: 3220)
- chrome.exe (PID: 2344)
- iexplore.exe (PID: 3908)
Changes settings of System certificates
- chrome.exe (PID: 3968)
Reads settings of System Certificates
- iexplore.exe (PID: 3908)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
109
Monitored processes
65
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4758027037062213039 --mojo-platform-channel-handle=5892 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14510289439327562206 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5325374610718851917 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4604 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1842029688178464287 --mojo-platform-channel-handle=5728 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1690447475720778633 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2520 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5094751561951018983 --renderer-client-id=43 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1356422661851775889 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3644 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11014353722762618156 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3680 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10551043509255784874 --mojo-platform-channel-handle=1952 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,4699929076933261588,8658156528357005958,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9424339477398235194 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4420 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 507
Read events
1 315
Write events
187
Delete events
5
Modification events
| (PID) Process: | (3232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2344-13233076575079750 |
Value: 259 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
3
Suspicious files
80
Text files
430
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EB0285F-928.pma | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8d980fed-77c3-4501-bbbe-c565710c35cf.tmp | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFa8753e.TMP | text | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa87638.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
157
DNS requests
110
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3968 | chrome.exe | GET | 200 | 104.17.166.186:80 | http://6.adsco.re/ | US | — | — | whitelisted |
3968 | chrome.exe | GET | — | 162.252.214.5:80 | http://adsco.re/p | US | — | — | whitelisted |
3968 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/file/2i53n97xnlishy2/GTAV.zip/file | US | html | 82.3 Kb | shared |
3968 | chrome.exe | GET | 200 | 104.16.202.237:80 | http://www.mediafire.com/js/prebid2.44.1.js | US | text | 52.9 Kb | shared |
3968 | chrome.exe | GET | 200 | 104.17.166.186:80 | http://c.adsco.re/ | US | html | 34.3 Kb | whitelisted |
3968 | chrome.exe | GET | 304 | 104.17.166.186:80 | http://c.adsco.re/ | US | html | 34.3 Kb | whitelisted |
3968 | chrome.exe | POST | 200 | 37.252.172.36:80 | http://ib.adnxs.com/ut/v3/prebid | unknown | text | 235 b | whitelisted |
3968 | chrome.exe | POST | 200 | 162.252.214.5:80 | http://adsco.re/p | US | text | 134 b | whitelisted |
3968 | chrome.exe | GET | 200 | 172.217.21.206:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | text | 796 b | whitelisted |
3968 | chrome.exe | GET | 200 | 104.16.203.237:80 | http://static.mediafire.com/images/backgrounds/download/dl_promo_logo.png | US | image | 2.19 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3968 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3968 | chrome.exe | 104.16.203.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
3968 | chrome.exe | 172.217.23.100:443 | www.google.com | Google Inc. | US | whitelisted |
3968 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3968 | chrome.exe | 104.16.202.237:80 | www.mediafire.com | Cloudflare Inc | US | unknown |
3968 | chrome.exe | 172.217.23.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3968 | chrome.exe | 172.217.21.206:80 | translate.google.com | Google Inc. | US | whitelisted |
3968 | chrome.exe | 2.20.168.110:443 | c.aaxads.com | Akamai Technologies, Inc. | — | unknown |
3968 | chrome.exe | 172.217.23.98:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
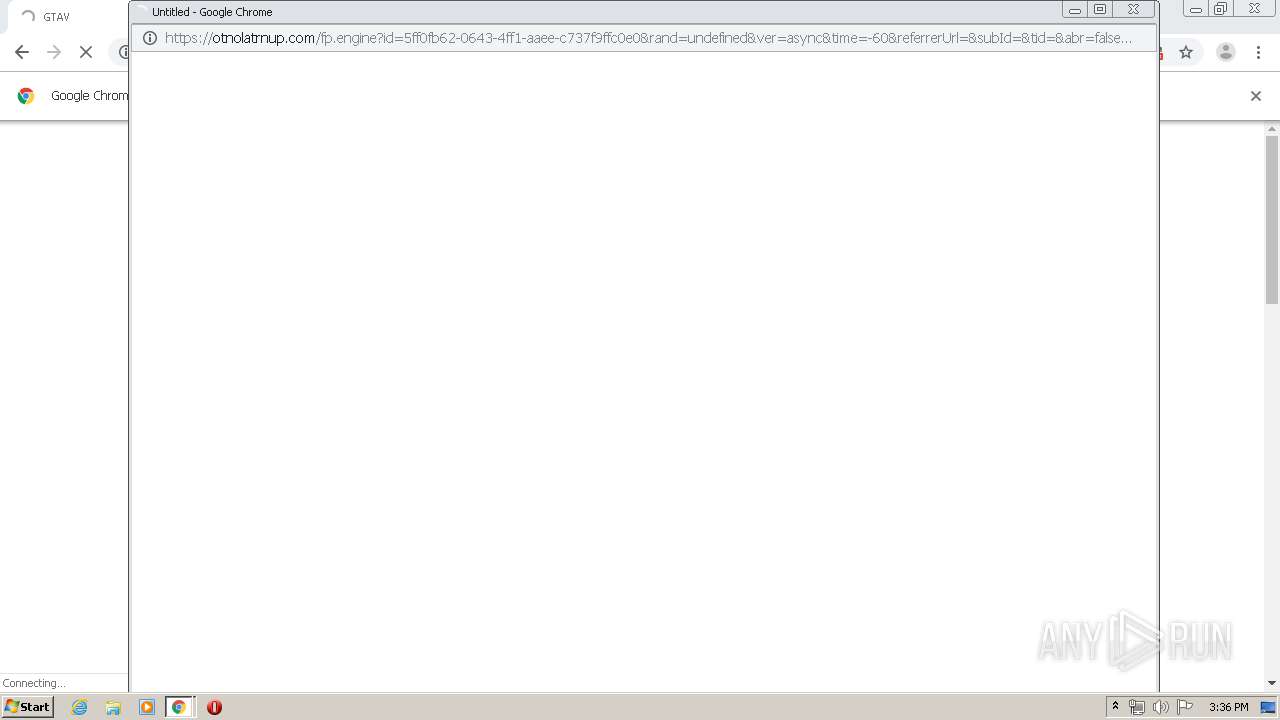
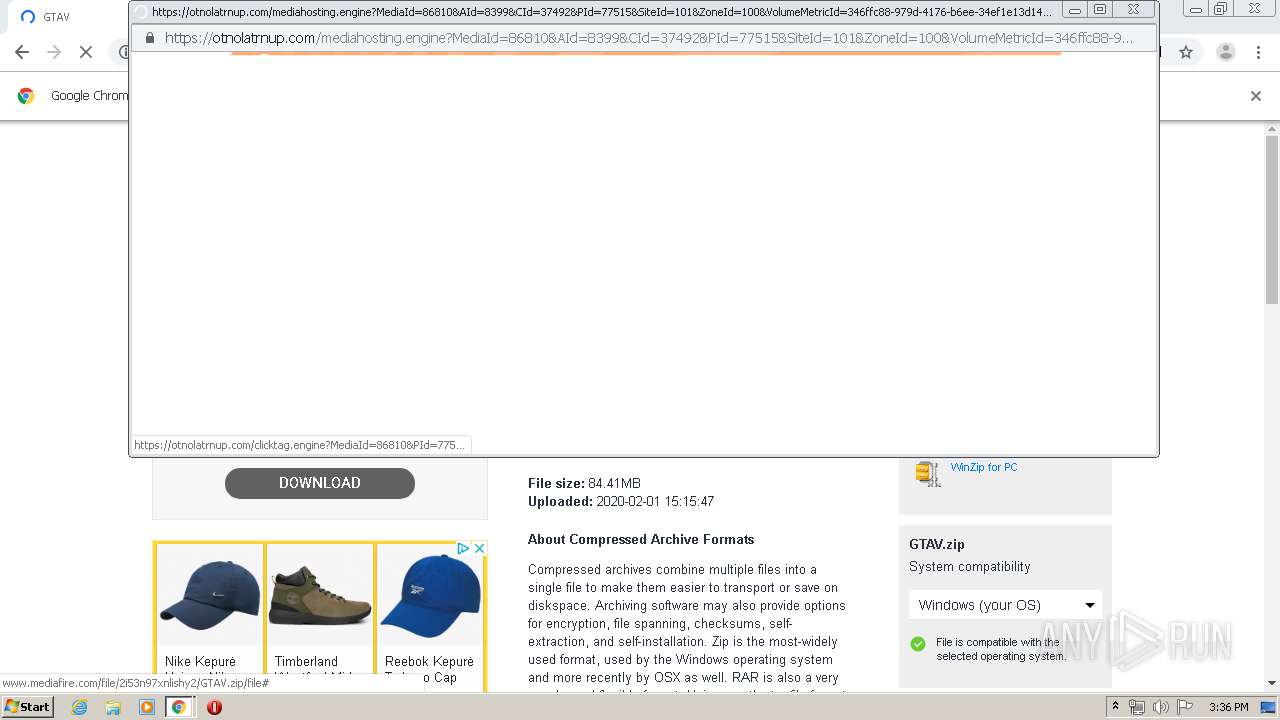
3968 | chrome.exe | 104.19.214.37:443 | cdn.otnolatrnup.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.mediafire.com |
| shared |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
translate.google.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
c.aaxads.com |
| whitelisted |
static.mediafire.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3968 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3968 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |