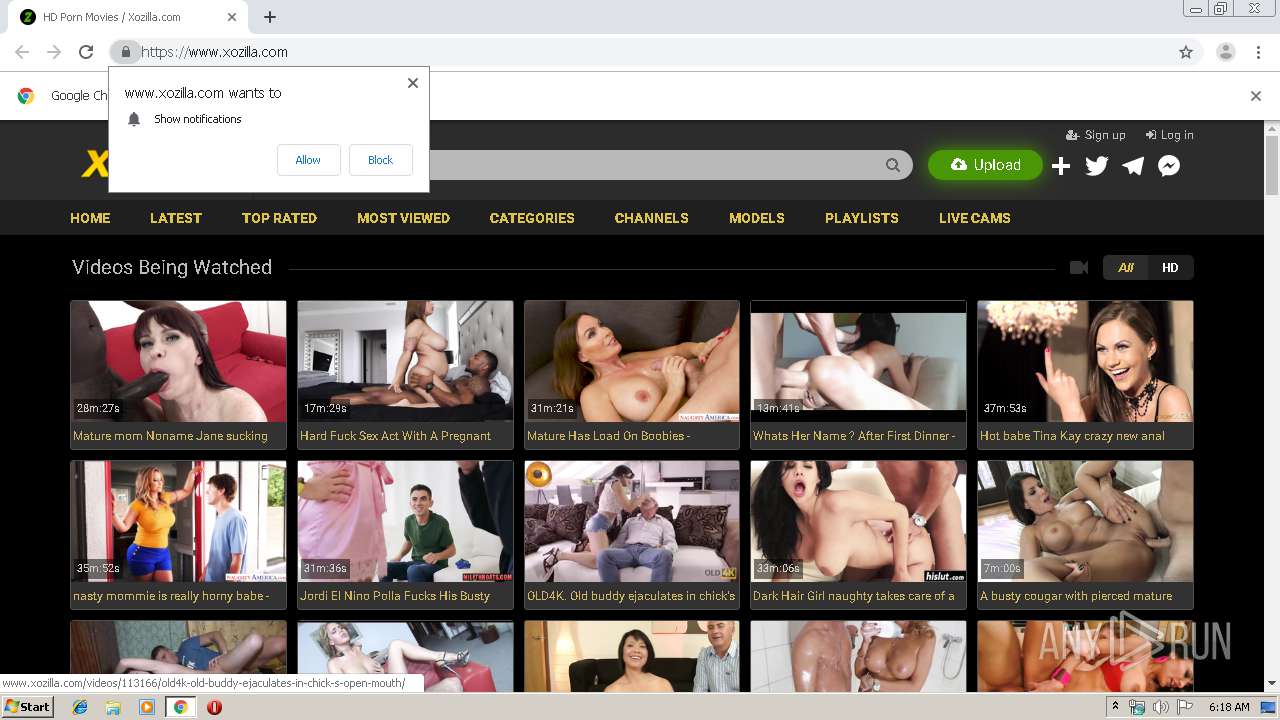
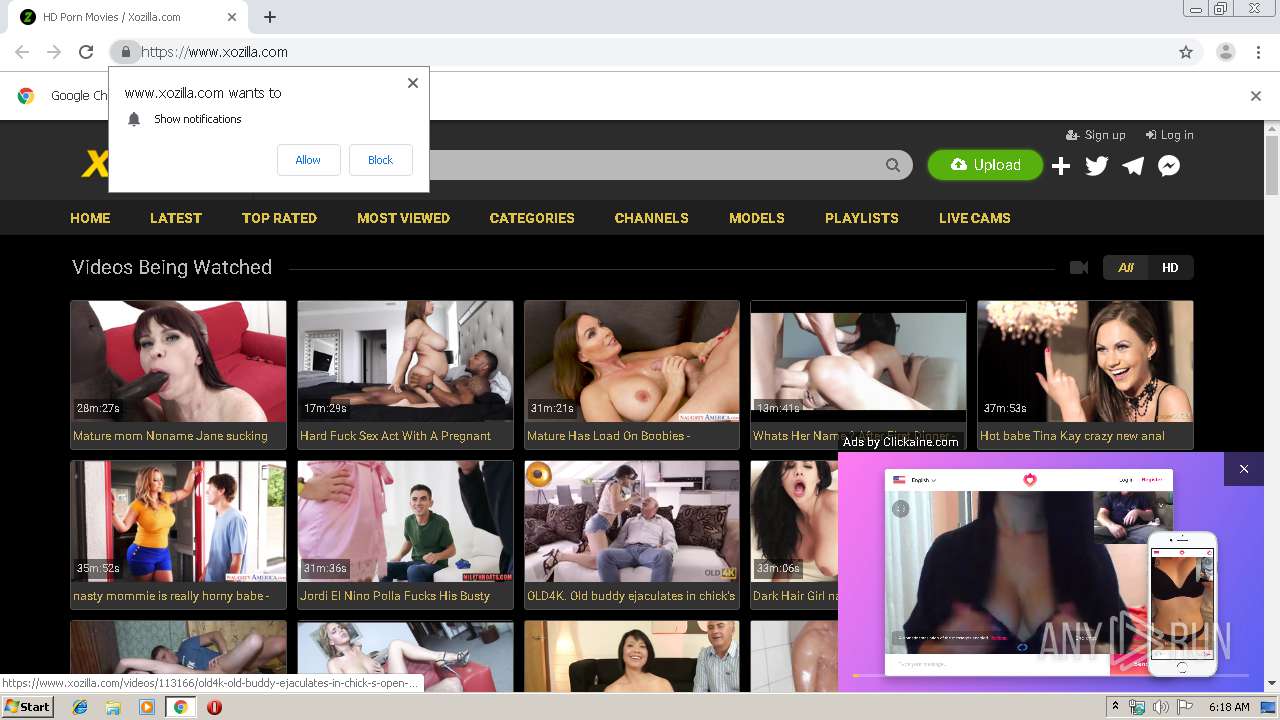
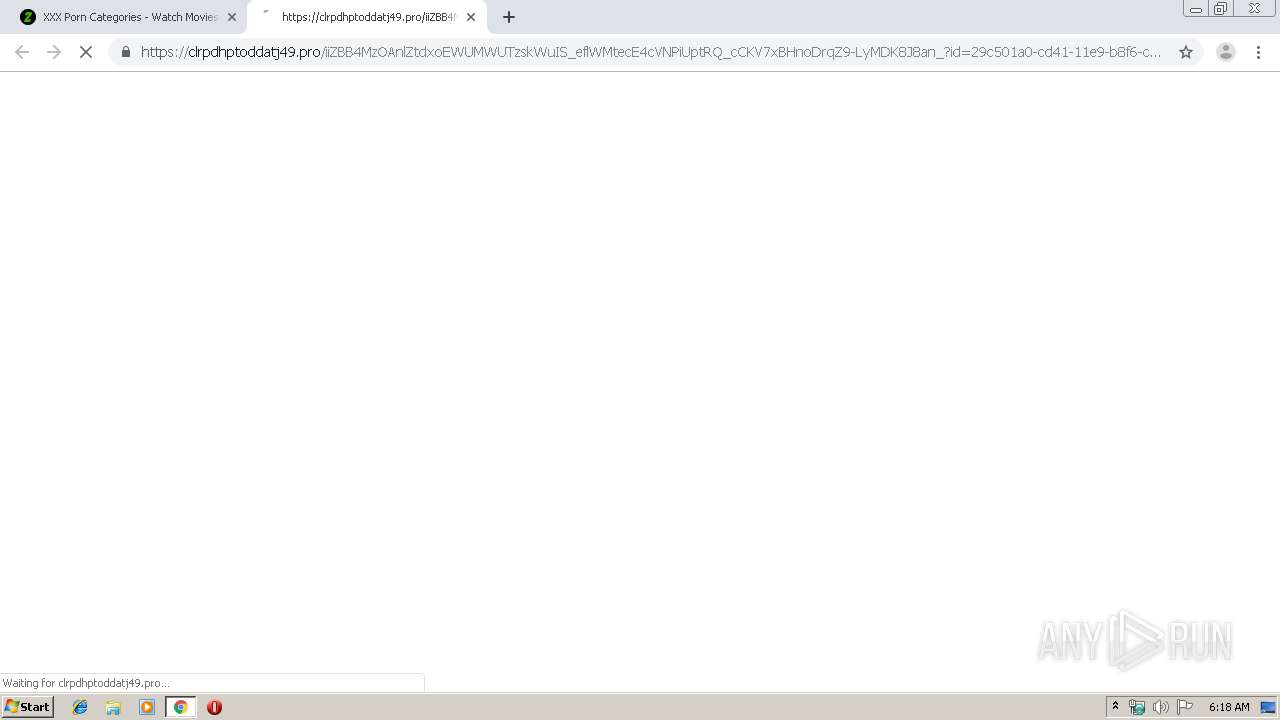
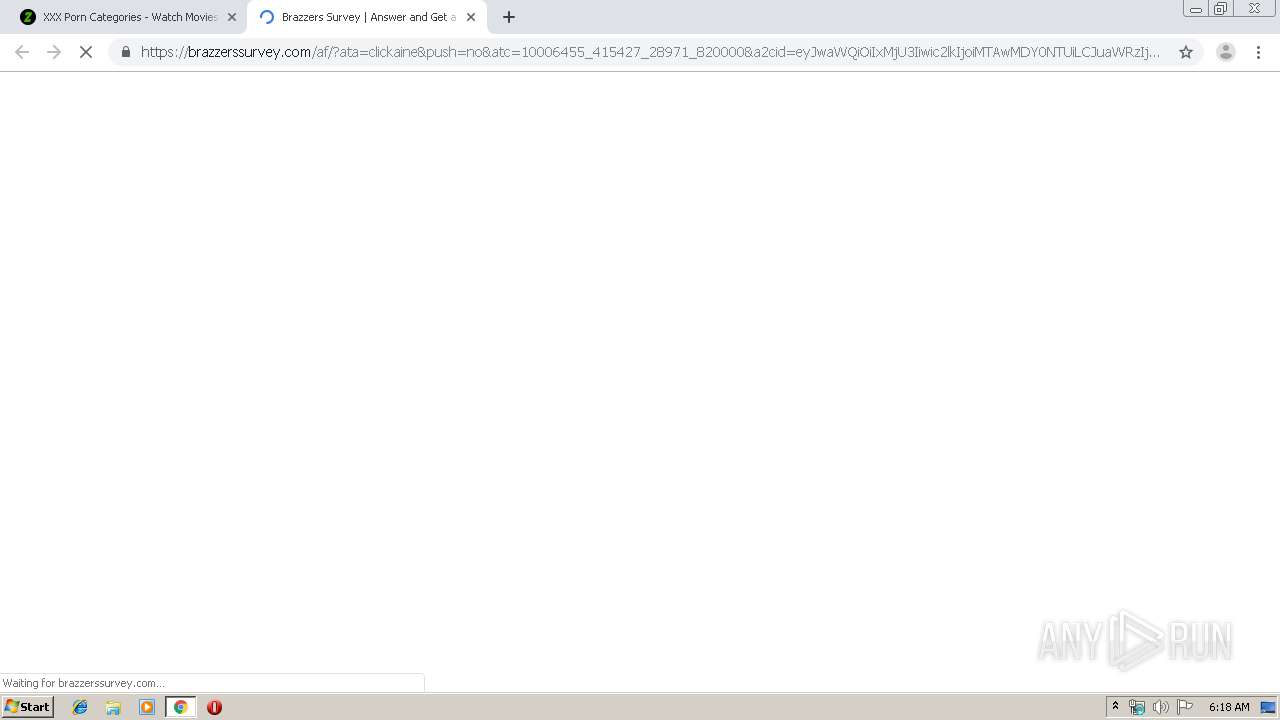
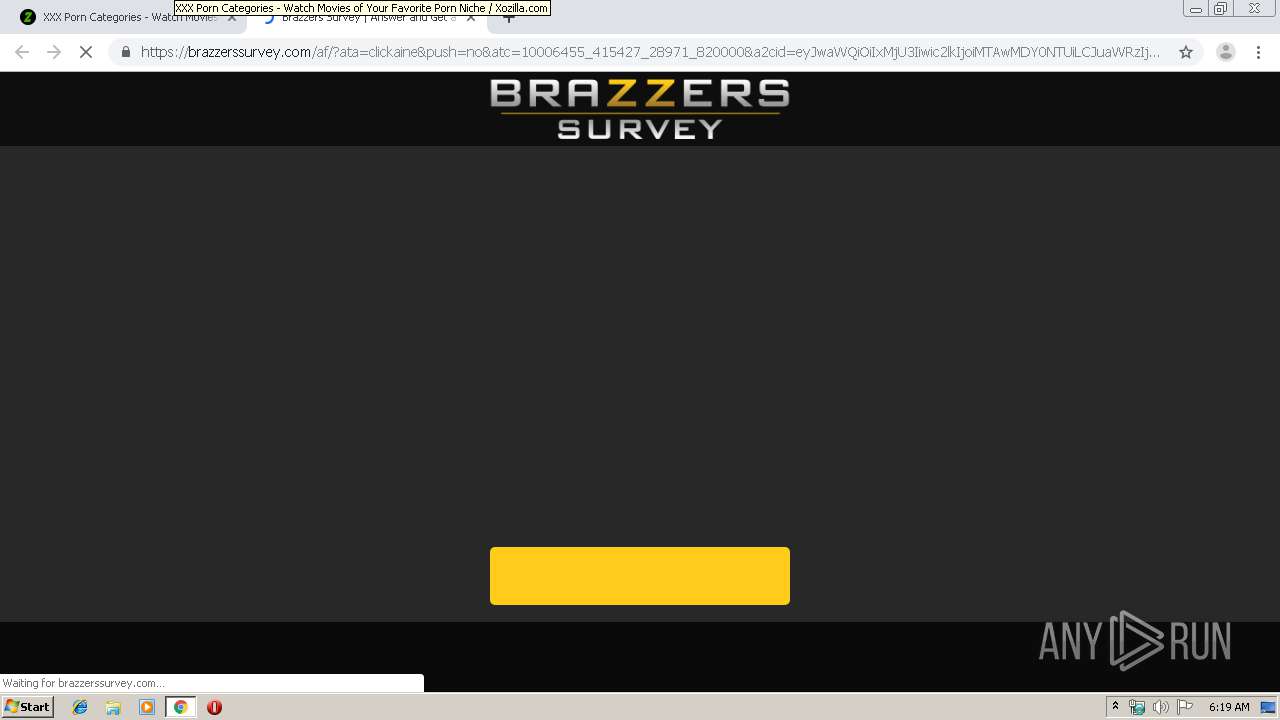
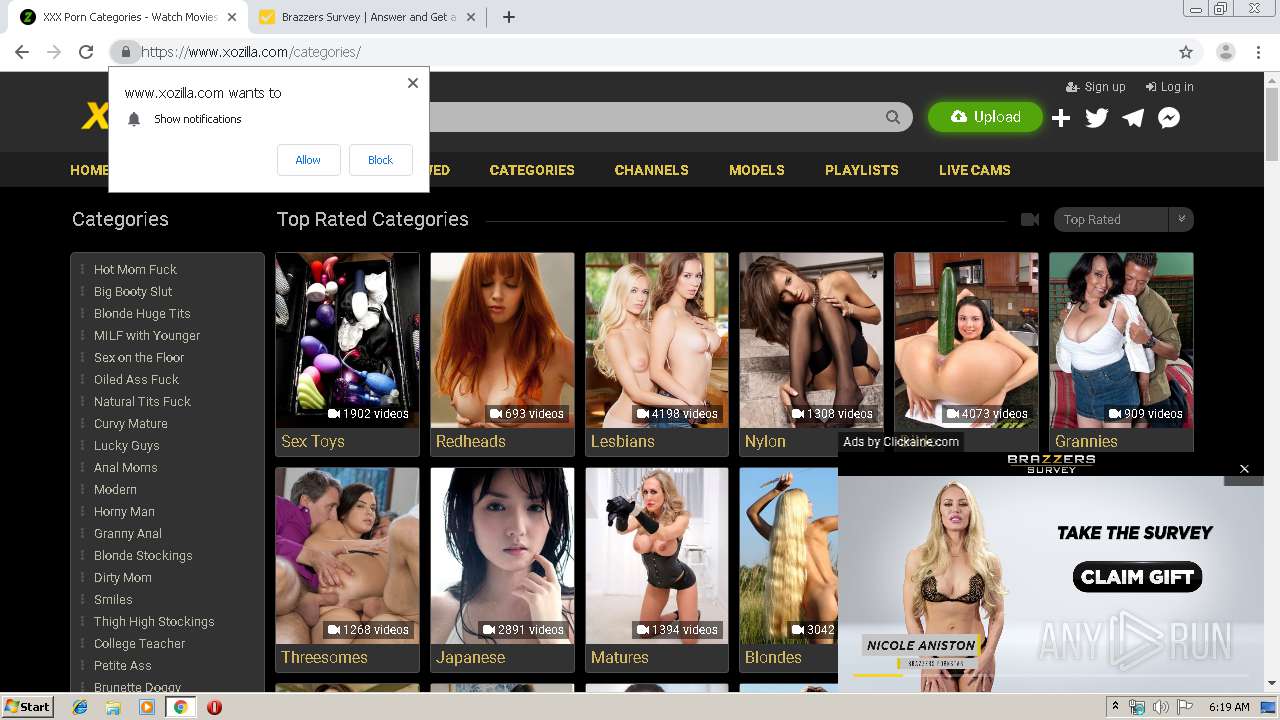
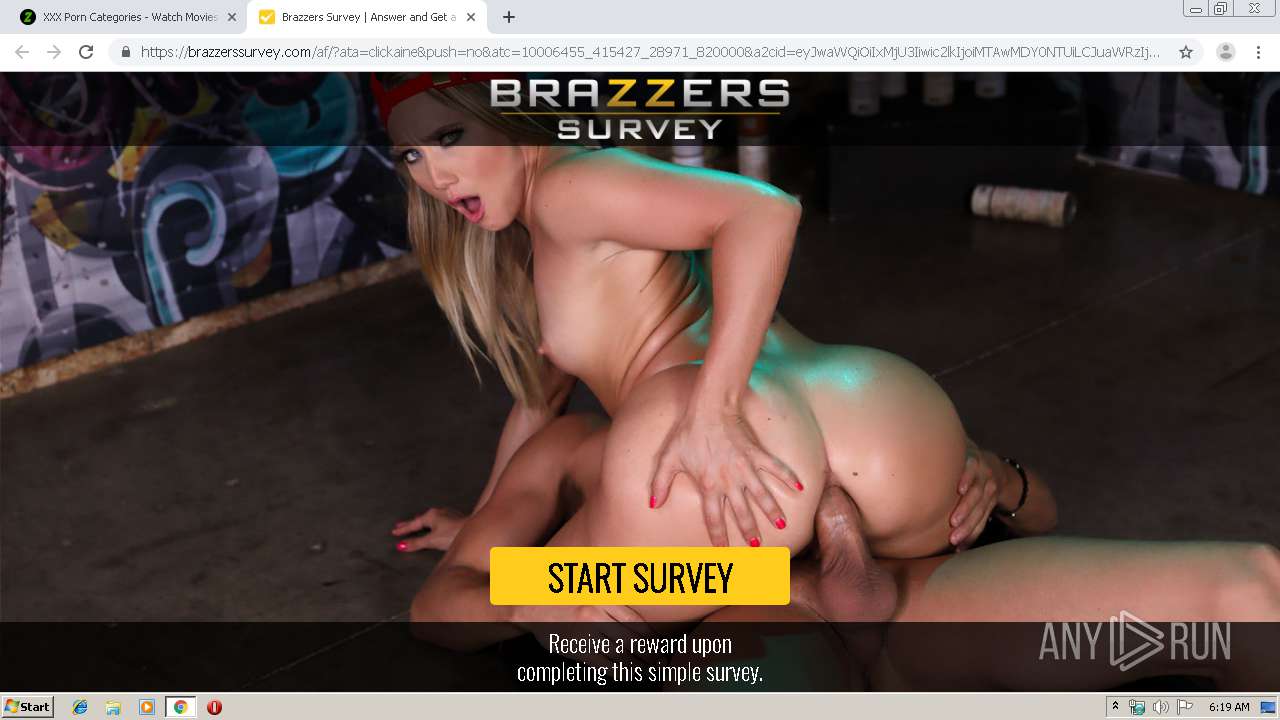
| URL: | https://www.xozilla.com |
| Full analysis: | https://app.any.run/tasks/9d677506-b100-4281-b16a-bb81f86cb2e6 |
| Verdict: | No threats detected |
| Analysis date: | September 02, 2019, 05:18:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 476FAB4DF965116BE9D3FFAC14854745 |
| SHA1: | 0101A02E76D115EF6800A18423EED712EE9556D3 |
| SHA256: | C544925A84B3E149B5CE0FA5C65C7219247B1D8BE0DC5D5EA793C5A5CAD1FC3E |
| SSDEEP: | 3:N8DSLRKLdIn:2OLcLdI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3652)
INFO
Application launched itself
- chrome.exe (PID: 3652)
Reads settings of System Certificates
- chrome.exe (PID: 2972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
42
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16434998672566931844 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3780 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13294908254614431506 --mojo-platform-channel-handle=4640 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3520687408803545787 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4536 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16844073667895477449 --mojo-platform-channel-handle=2076 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8569708857603085531 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6466411332563481238 --mojo-platform-channel-handle=4588 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16467683931821345676 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14130109706146118575 --mojo-platform-channel-handle=4592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3278303673569965629 --mojo-platform-channel-handle=4656 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11447175671936770699 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3816 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
680
Read events
571
Write events
104
Delete events
5
Modification events
| (PID) Process: | (3536) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3652-13211875111846625 |
Value: 259 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3652) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
209
Text files
332
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a257d8c7-1171-40ab-af8b-c935eff9513f.tmp | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169ba8.TMP | text | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF169bf6.TMP | text | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169ba8.TMP | text | |
MD5:— | SHA256:— | |||
| 3652 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
167
DNS requests
82
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2972 | chrome.exe | GET | — | 216.18.168.122:80 | http://afcpatrk.com/redirect/atlas?cep=rocPBmmBFMTQXUhtJrC3SzgAcOIsrZf3UmcdOYYa6zMLr09ERgbgDrYPKacHswZh7jL1sq6CcT3bOBXCtrn-8aIfG7aEy8j9zv2erhVRKlOB9d2582V4kBu8eVv68G1WTzMcnflrVO5RxKvFycBvULkTf4vR-ynP7Wc0952PNaq9v21Ipi3Y-6AjIzLyvrC0k3r-runn6uSfOUb_WRE4rDFBcqMEEbZ9gLDPOIc4ugODyz7GIqTa4ff7UmO2Nk7szRwEj4DnFEoOQETkRLQCkLCsGXCM11qswY4yZQjxh-inR5UGxB7pbeat6pwf0DKL6ms5CD7Z1RQETrG1IXcSQR1cOC5T2PK7fI9mkMkh19bjNvLDZIemlQ7lTR-JxzizqCaGeaQHAF1ksHYlWTFUvh_bMy51gvCqQkHAgtpL3nr3-A7k4v1s19jWcGkfSZ_lc4gRt44gOPzj1oyfHW_84z4XnnntcD0mf1IzcRjgsl4L9lqoD_SpI0H7_PeP5SVsElSLmdX50vBu89mYTLQ7ug4zNWNaHTMRfei3HZC7cMb-1AnmJ2QSWDFXfMe16dLA8ZdwR7fcbI8JS9WL4ACE5n9sDcpE9AEBVBc_lcG5ilE&lptoken=1590672f40aa33174899&ata=clickaine&atc=10006455_415427_28971_820000&apb=Al5DK0ILqFLjuXq6N8kaeTtKgAF7a4Wc71MeAlne6IgxVl_MGa7bFgNO_LZZDH_s4HZtlfHY6MfBJoFU3jgT2eBjMUJVnSoj6ln8Ob71AfnrjDCyTEM_9NDtloPeRLpEiSzo12mNkdAgmw8kzt9Lvhp_OWZ-4x09077L7g | US | — | — | suspicious |
2972 | chrome.exe | GET | — | 35.157.133.117:80 | http://track.afcpatrk.com/click?ats=undefined&apb=Al5DK0ILqFLjuXq6N8kaeTtKgAF7a4Wc71MeAlne6IgxVl_MGa7bFgNO_LZZDH_s4HZtlfHY6MfBJoFU3jgT2eBjMUJVnSoj6ln8Ob71AfnrjDCyTEM_9NDtloPeRLpEiSzo12mNkdAgmw8kzt9Lvhp_OWZ-4x09077L7g&atc=10006455_415427_28971_820000&ata=clickaine&cep=rocPBmmBFMTQXUhtJrC3SzgAcOIsrZf3UmcdOYYa6zMLr09ERgbgDrYPKacHswZh7jL1sq6CcT3bOBXCtrn-8aIfG7aEy8j9zv2erhVRKlOB9d2582V4kBu8eVv68G1WTzMcnflrVO5RxKvFycBvULkTf4vR-ynP7Wc0952PNaq9v21Ipi3Y-6AjIzLyvrC0k3r-runn6uSfOUb_WRE4rDFBcqMEEbZ9gLDPOIc4ugODyz7GIqTa4ff7UmO2Nk7szRwEj4DnFEoOQETkRLQCkLCsGXCM11qswY4yZQjxh-inR5UGxB7pbeat6pwf0DKL6ms5CD7Z1RQETrG1IXcSQR1cOC5T2PK7fI9mkMkh19bjNvLDZIemlQ7lTR-JxzizqCaGeaQHAF1ksHYlWTFUvh_bMy51gvCqQkHAgtpL3nr3-A7k4v1s19jWcGkfSZ_lc4gRt44gOPzj1oyfHW_84z4XnnntcD0mf1IzcRjgsl4L9lqoD_SpI0H7_PeP5SVsElSLmdX50vBu89mYTLQ7ug4zNWNaHTMRfei3HZC7cMb-1AnmJ2QSWDFXfMe16dLA8ZdwR7fcbI8JS9WL4ACE5n9sDcpE9AEBVBc_lcG5ilE | DE | — | — | shared |
2972 | chrome.exe | GET | — | 216.18.168.122:80 | http://afcpatrk.com/libs/js/vortex.modern.min.js | US | — | — | suspicious |
2972 | chrome.exe | GET | — | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | — | — | whitelisted |
2972 | chrome.exe | GET | — | 173.194.129.233:80 | http://r4---sn-q0c7rn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=78.153.204.5&mm=28&mn=sn-q0c7rn76&ms=nvh&mt=1567401497&mv=m&mvi=3&pl=19&shardbypass=yes | US | — | — | whitelisted |
2972 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
2972 | chrome.exe | GET | — | 66.254.114.63:80 | http://atlas.etahub.com/guid?app_id=&eventName=& | US | — | — | whitelisted |
2972 | chrome.exe | GET | — | 216.18.168.122:80 | http://afcpatrk.com/libs/js/jquery.min.js | US | — | — | suspicious |
2972 | chrome.exe | GET | — | 216.18.168.122:80 | http://afcpatrk.com/libs/js/atlaslib.min.js | US | — | — | suspicious |
2972 | chrome.exe | GET | — | 216.18.168.122:80 | http://afcpatrk.com/redirect/atlas/?cep=rocPBmmBFMTQXUhtJrC3SzgAcOIsrZf3UmcdOYYa6zMLr09ERgbgDrYPKacHswZh7jL1sq6CcT3bOBXCtrn-8aIfG7aEy8j9zv2erhVRKlOB9d2582V4kBu8eVv68G1WTzMcnflrVO5RxKvFycBvULkTf4vR-ynP7Wc0952PNaq9v21Ipi3Y-6AjIzLyvrC0k3r-runn6uSfOUb_WRE4rDFBcqMEEbZ9gLDPOIc4ugODyz7GIqTa4ff7UmO2Nk7szRwEj4DnFEoOQETkRLQCkLCsGXCM11qswY4yZQjxh-inR5UGxB7pbeat6pwf0DKL6ms5CD7Z1RQETrG1IXcSQR1cOC5T2PK7fI9mkMkh19bjNvLDZIemlQ7lTR-JxzizqCaGeaQHAF1ksHYlWTFUvh_bMy51gvCqQkHAgtpL3nr3-A7k4v1s19jWcGkfSZ_lc4gRt44gOPzj1oyfHW_84z4XnnntcD0mf1IzcRjgsl4L9lqoD_SpI0H7_PeP5SVsElSLmdX50vBu89mYTLQ7ug4zNWNaHTMRfei3HZC7cMb-1AnmJ2QSWDFXfMe16dLA8ZdwR7fcbI8JS9WL4ACE5n9sDcpE9AEBVBc_lcG5ilE&lptoken=1590672f40aa33174899&ata=clickaine&atc=10006455_415427_28971_820000&apb=Al5DK0ILqFLjuXq6N8kaeTtKgAF7a4Wc71MeAlne6IgxVl_MGa7bFgNO_LZZDH_s4HZtlfHY6MfBJoFU3jgT2eBjMUJVnSoj6ln8Ob71AfnrjDCyTEM_9NDtloPeRLpEiSzo12mNkdAgmw8kzt9Lvhp_OWZ-4x09077L7g | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2972 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2972 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2972 | chrome.exe | 31.220.24.101:443 | www.xozilla.com | — | NL | unknown |
2972 | chrome.exe | 104.20.110.39:443 | static.addtoany.com | Cloudflare Inc | US | shared |
2972 | chrome.exe | 104.31.79.233:443 | pub.nakedreel.com | Cloudflare Inc | US | shared |
2972 | chrome.exe | 213.174.135.2:443 | i.xozilla.com | DataWeb Global Group B.V. | US | suspicious |
2972 | chrome.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2972 | chrome.exe | 18.197.128.209:443 | jeeves.excited.me | Amazon.com, Inc. | DE | unknown |
2972 | chrome.exe | 172.217.18.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
2972 | chrome.exe | 104.17.172.56:443 | jsc.adskeeper.co.uk | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.xozilla.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
i.xozilla.com |
| suspicious |
static.addtoany.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |