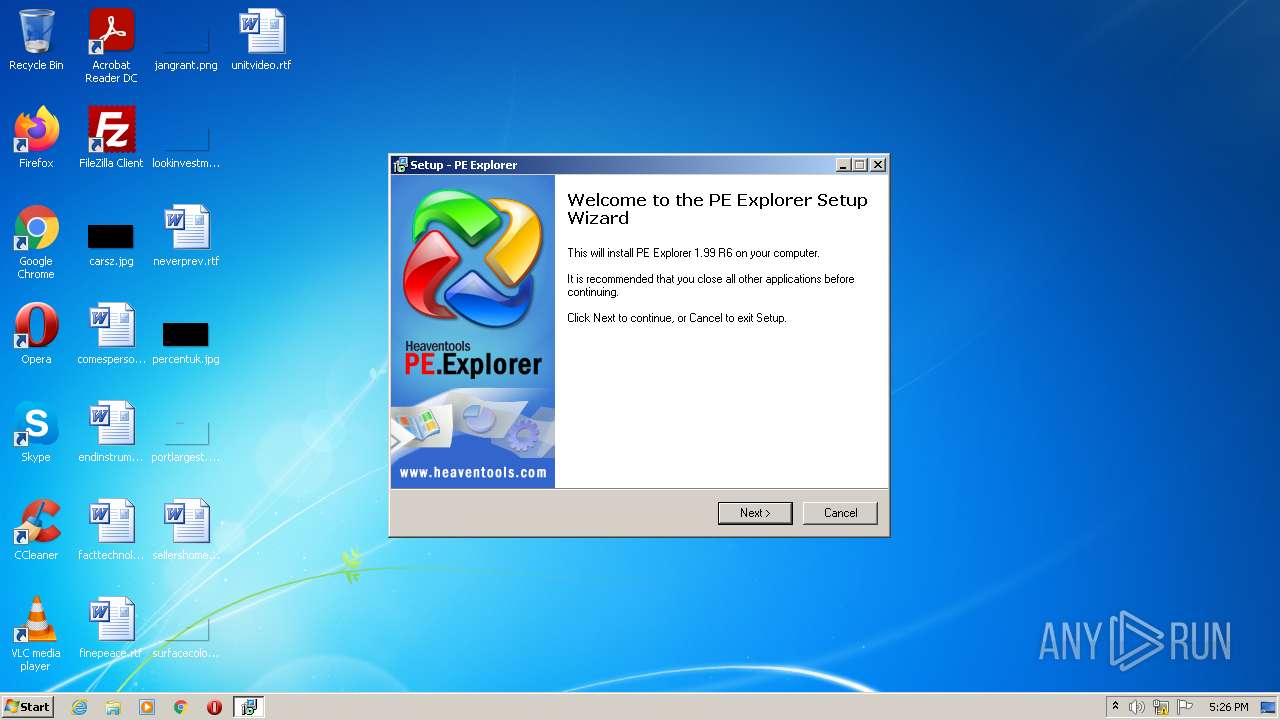
| File name: | PE.Explorer_setup.exe |
| Full analysis: | https://app.any.run/tasks/6e67e64b-0dd3-4571-bc86-a5e2264326ee |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 16:25:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EFC2E46440A5F3E142C11353386DB65D |
| SHA1: | FD72D9FBA765156012F45496E34FA2E2A9ABCC51 |
| SHA256: | C51952CA192EF5CDEA99F1E70EF2981761C882D0DCD65AEA2134F3C7C5DA1972 |
| SSDEEP: | 98304:0SK4LSJWSRKvges0BNQj62cX3K8rhetRv30lByhYVC5ota:nFLlaeJOcX3z0tR3AM |
MALICIOUS
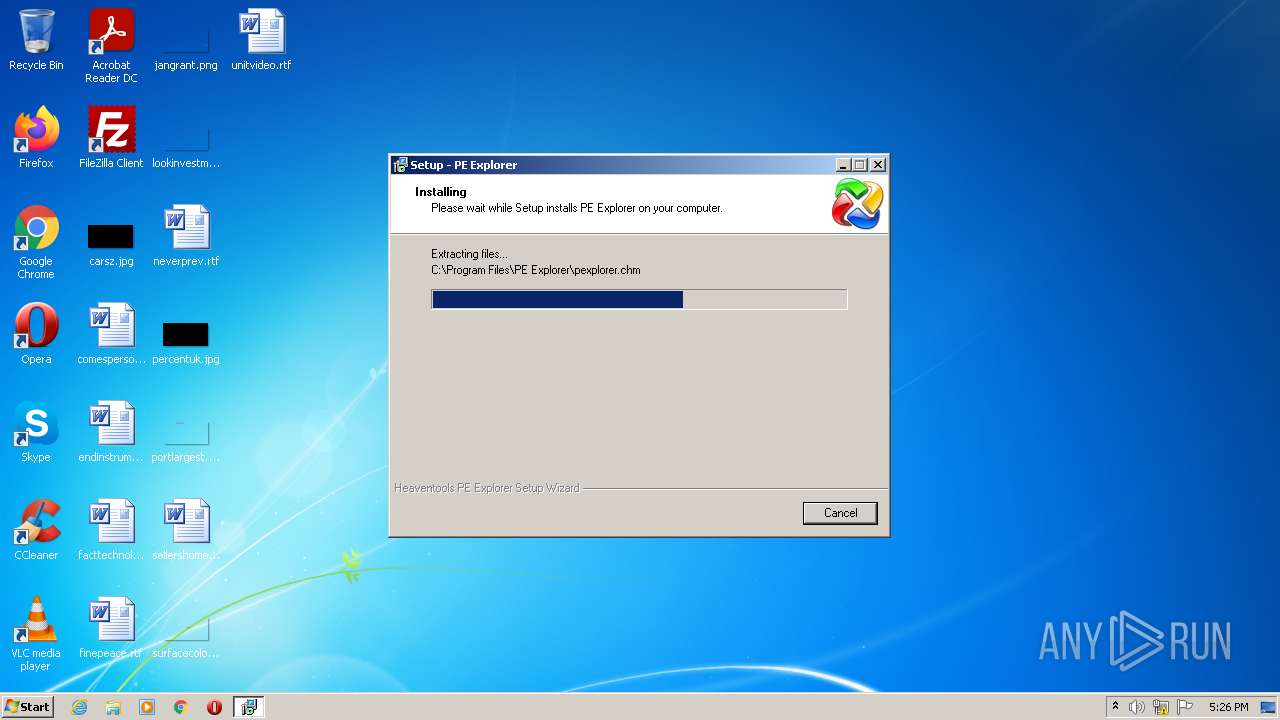
Drops executable file immediately after starts
- PE.Explorer_setup.exe (PID: 1760)
- PE.Explorer_setup.tmp (PID: 1540)
Application was dropped or rewritten from another process
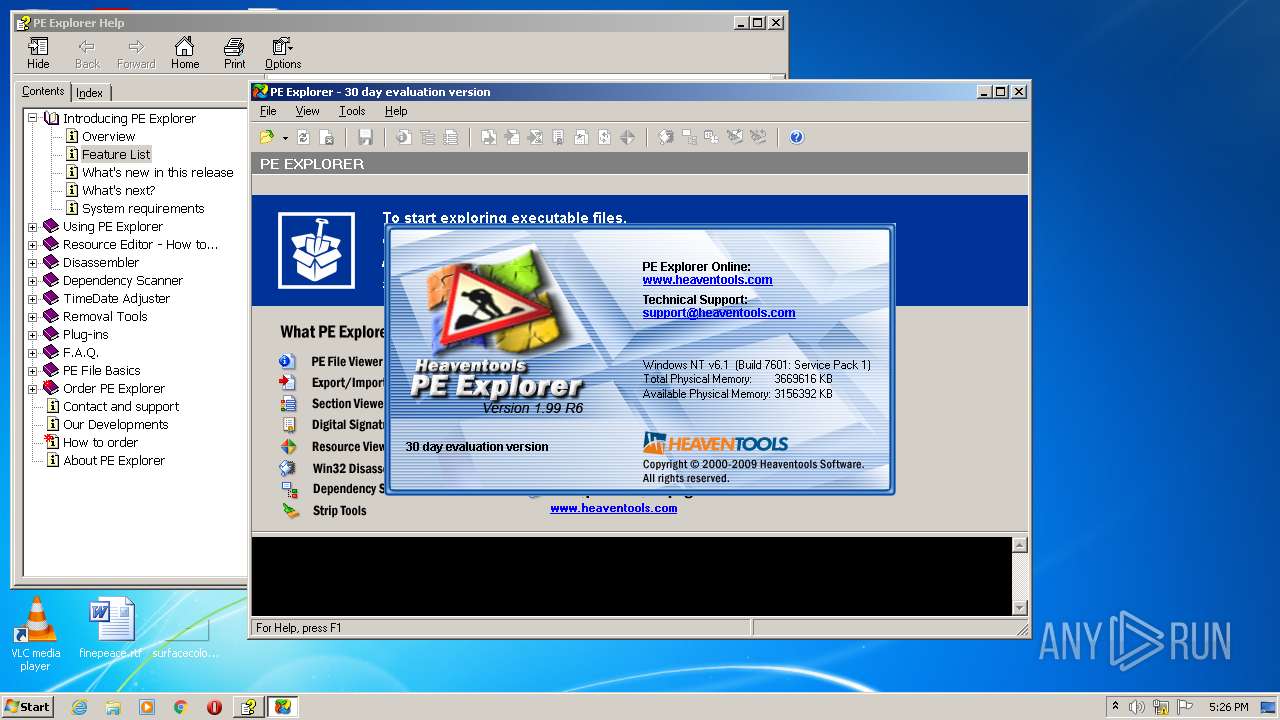
- pexplorer.exe (PID: 3516)
Loads dropped or rewritten executable
- pexplorer.exe (PID: 3516)
SUSPICIOUS
Checks supported languages
- PE.Explorer_setup.exe (PID: 1760)
- PE.Explorer_setup.tmp (PID: 1540)
- pexplorer.exe (PID: 3516)
Reads Windows owner or organization settings
- PE.Explorer_setup.tmp (PID: 1540)
Reads the Windows organization settings
- PE.Explorer_setup.tmp (PID: 1540)
Reads the computer name
- PE.Explorer_setup.tmp (PID: 1540)
- pexplorer.exe (PID: 3516)
Executable content was dropped or overwritten
- PE.Explorer_setup.exe (PID: 1760)
- PE.Explorer_setup.tmp (PID: 1540)
Creates files in the user directory
- PE.Explorer_setup.tmp (PID: 1540)
Drops a file with a compile date too recent
- PE.Explorer_setup.exe (PID: 1760)
- PE.Explorer_setup.tmp (PID: 1540)
Changes default file association
- PE.Explorer_setup.tmp (PID: 1540)
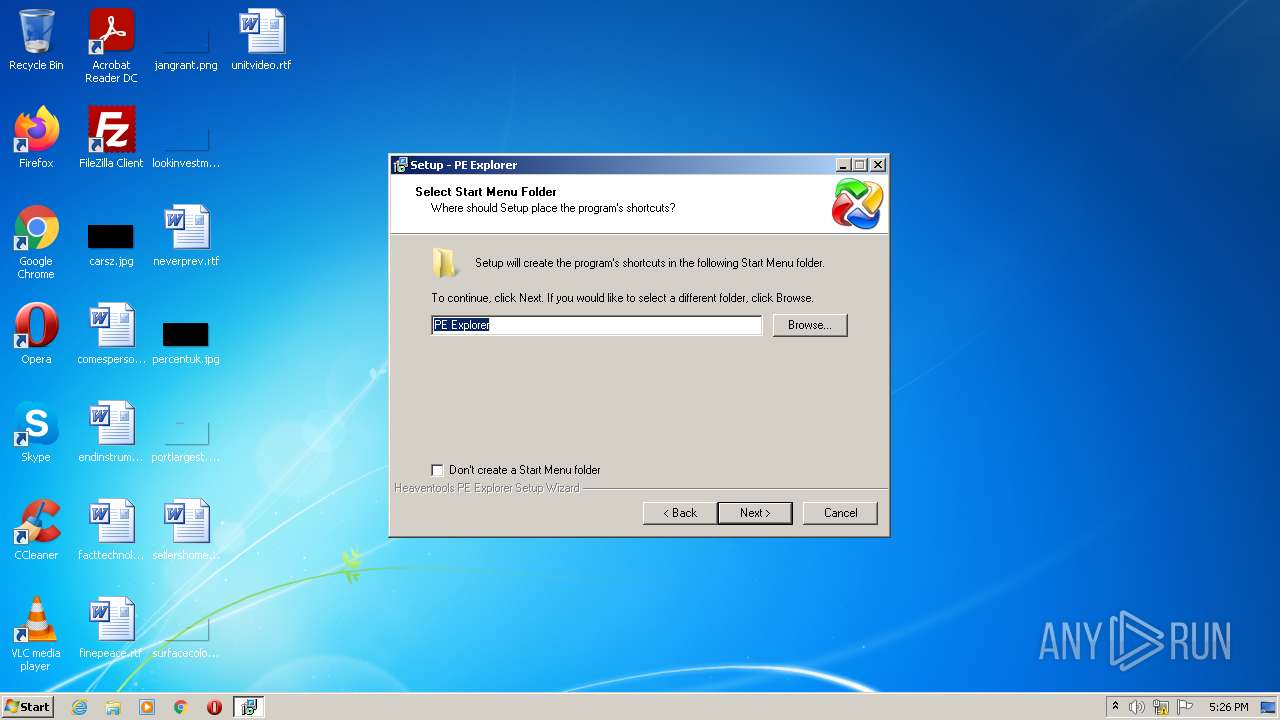
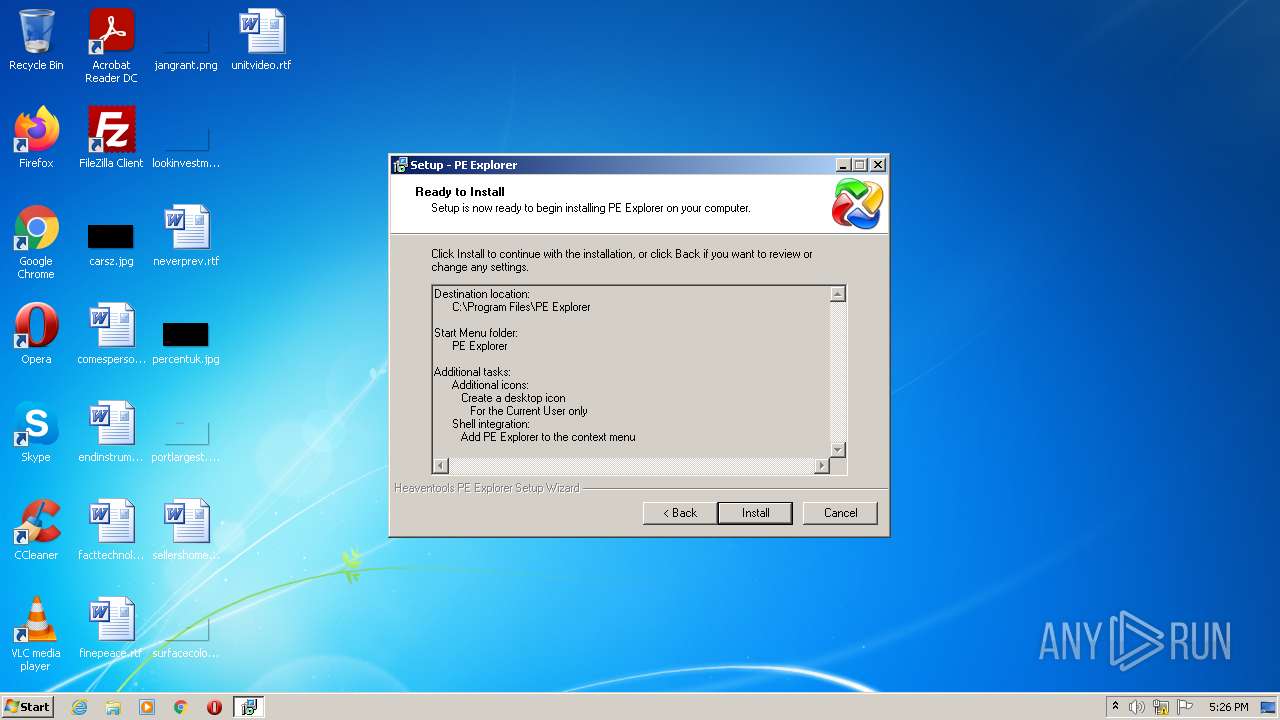
Creates a directory in Program Files
- PE.Explorer_setup.tmp (PID: 1540)
Reads internet explorer settings
- hh.exe (PID: 3584)
Reads Microsoft Outlook installation path
- hh.exe (PID: 3584)
INFO
Loads dropped or rewritten executable
- PE.Explorer_setup.tmp (PID: 1540)
Application was dropped or rewritten from another process
- PE.Explorer_setup.tmp (PID: 1540)
Reads the computer name
- hh.exe (PID: 3584)
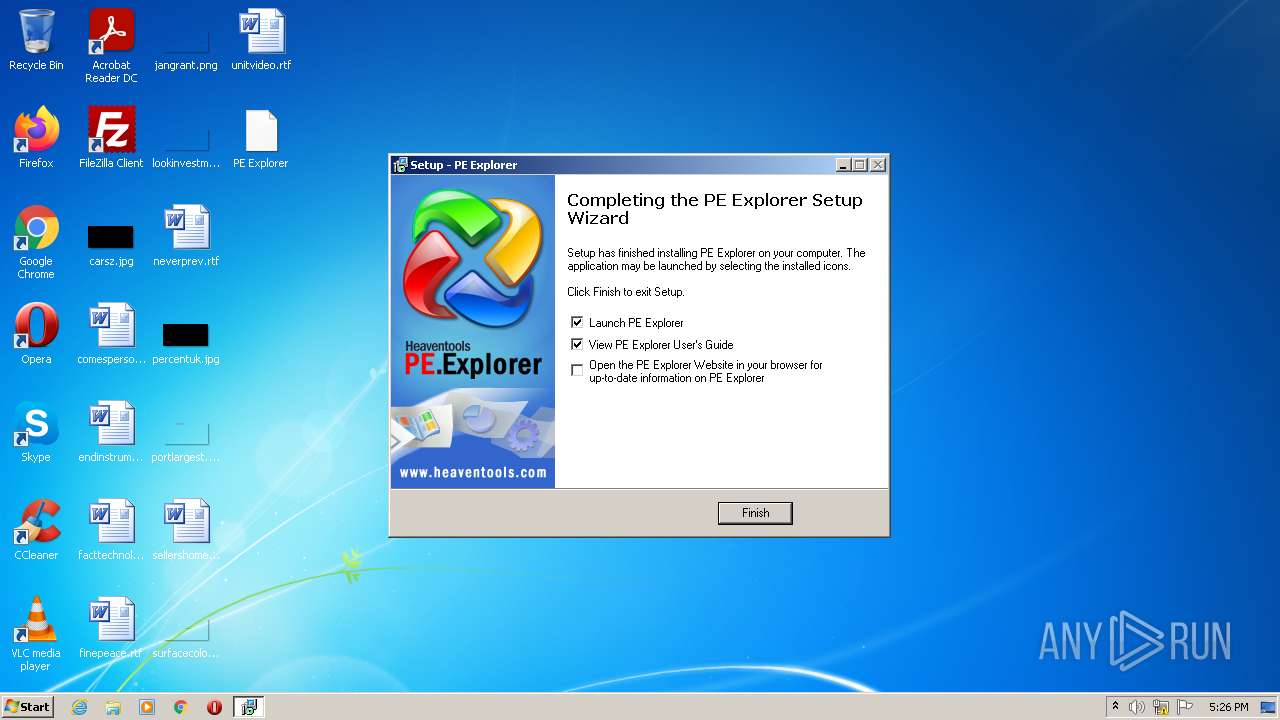
Creates a software uninstall entry
- PE.Explorer_setup.tmp (PID: 1540)
Creates files in the program directory
- PE.Explorer_setup.tmp (PID: 1540)
Checks supported languages
- hh.exe (PID: 3584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| OriginalFileName: | PE.Explorer_setup.exe |
|---|---|
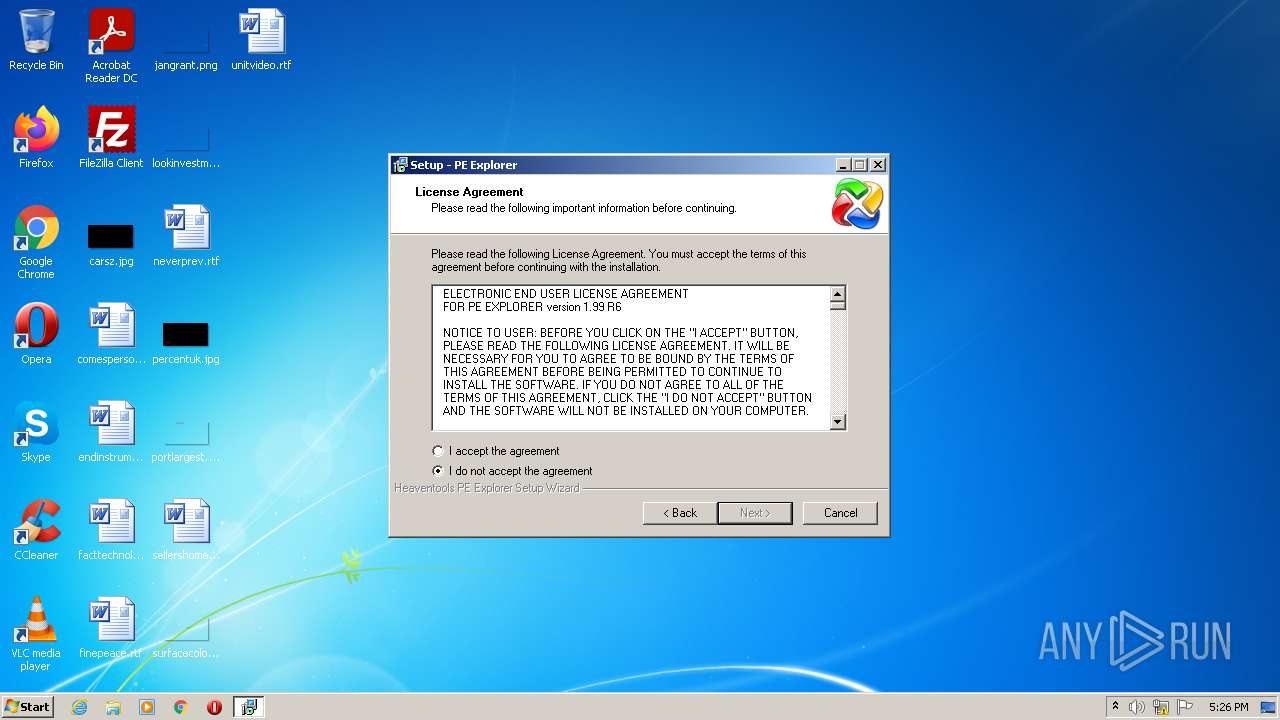
| InternalName: | PE Explorer Setup |
| LegalTrademarks: | PE Explorer is a trademark of Heaventools Software |
| ProductVersion: | 1.0.0.0 |
| ProductName: | PE Explorer |
| LegalCopyright: | Copyright © 2000-2008 Heaventools Software |
| FileVersion: | 1.99.6.1400 |
| FileDescription: | PE Explorer Setup |
| CompanyName: | Heaventools Software |
| Comments: | - |
| CharacterSet: | Windows, Cyrillic |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.99.6.1400 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 1 |
| EntryPoint: | 0x9b24 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 34304 |
| CodeSize: | 37888 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2009:10:14 13:00:00+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Oct-2009 11:00:00 |
| Comments: | - |
| CompanyName: | Heaventools Software |
| FileDescription: | PE Explorer Setup |
| FileVersion: | 1.99.6.1400 |
| LegalCopyright: | Copyright © 2000-2008 Heaventools Software |
| ProductName: | PE Explorer |
| ProductVersion: | 1.0.0.0 |
| LegalTrademarks: | PE Explorer is a trademark of Heaventools Software |
| InternalName: | PE Explorer Setup |
| OriginalFilename: | PE.Explorer_setup.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 14-Oct-2009 11:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009244 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52973 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.7347 |
BSS | 0x0000C000 | 0x00000E48 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00007440 | 0x00007600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.47115 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07297 | 1403 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.25755 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.65547 | 3752 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
4 | 6.04945 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 6.14281 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.06468 | 9640 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
7 | 5.21427 | 4264 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
8 | 5.21644 | 1128 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
41
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1540 | "C:\Users\admin\AppData\Local\Temp\is-6JEGO.tmp\PE.Explorer_setup.tmp" /SL5="$30138,3431473,73216,C:\Users\admin\AppData\Local\Temp\PE.Explorer_setup.exe" | C:\Users\admin\AppData\Local\Temp\is-6JEGO.tmp\PE.Explorer_setup.tmp | PE.Explorer_setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
| 1760 | "C:\Users\admin\AppData\Local\Temp\PE.Explorer_setup.exe" | C:\Users\admin\AppData\Local\Temp\PE.Explorer_setup.exe | Explorer.EXE | ||||||||||||
User: admin Company: Heaventools Software Integrity Level: HIGH Description: PE Explorer Setup Exit code: 0 Version: 1.99.6.1400 Modules
| |||||||||||||||
| 2852 | "C:\Users\admin\AppData\Local\Temp\PE.Explorer_setup.exe" | C:\Users\admin\AppData\Local\Temp\PE.Explorer_setup.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Heaventools Software Integrity Level: MEDIUM Description: PE Explorer Setup Exit code: 3221226540 Version: 1.99.6.1400 Modules
| |||||||||||||||
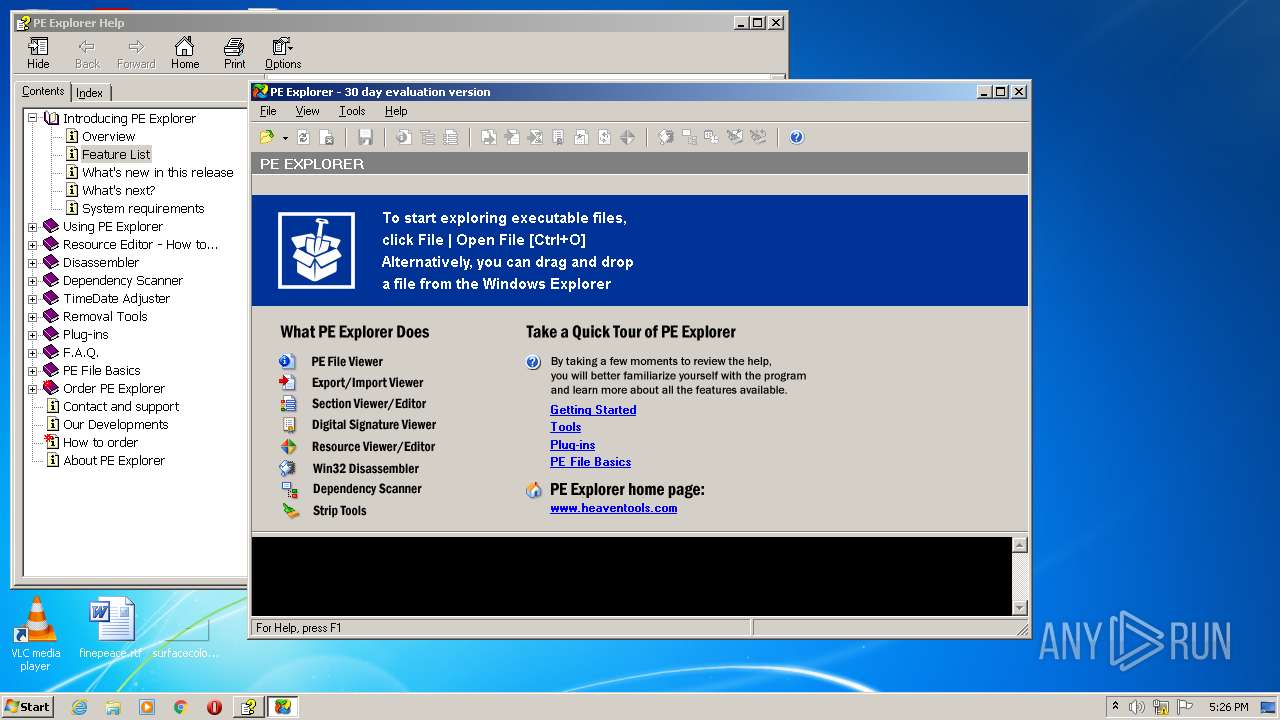
| 3516 | "C:\Program Files\PE Explorer\pexplorer.exe" | C:\Program Files\PE Explorer\pexplorer.exe | — | PE.Explorer_setup.tmp | |||||||||||
User: admin Company: Heaventools Software Integrity Level: HIGH Description: PE Explorer Exit code: 0 Version: 1.99.6.1400 Modules
| |||||||||||||||
| 3584 | "hh.exe" "C:\Program Files\PE Explorer\pexplorer.chm::Intro - features.htm" | C:\Windows\hh.exe | — | PE.Explorer_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® HTML Help Executable Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 542
Read events
2 388
Write events
154
Delete events
0
Modification events
| (PID) Process: | (1540) PE.Explorer_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\dllfile\shell\Open_with_PE_Explorer |
| Operation: | write | Name: | (default) |
Value: Open with PE Explorer | |||
| (PID) Process: | (1540) PE.Explorer_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\dllfile\shell\Open_with_PE_Explorer\command |
| Operation: | write | Name: | (default) |
Value: "C:\Program Files\PE Explorer\pexplorer.exe" "%1" | |||
| (PID) Process: | (1540) PE.Explorer_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile\shell\Open_with_PE_Explorer |
| Operation: | write | Name: | (default) |
Value: Open with PE Explorer | |||
| (PID) Process: | (1540) PE.Explorer_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile\shell\Open_with_PE_Explorer\command |
| Operation: | write | Name: | (default) |
Value: "C:\Program Files\PE Explorer\pexplorer.exe" "%1" | |||
| (PID) Process: | (1540) PE.Explorer_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ocxfile\shell\Open_with_PE_Explorer |
| Operation: | write | Name: | (default) |
Value: Open with PE Explorer | |||
| (PID) Process: | (1540) PE.Explorer_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\ocxfile\shell\Open_with_PE_Explorer\command |
| Operation: | write | Name: | (default) |
Value: "C:\Program Files\PE Explorer\pexplorer.exe" "%1" | |||
| (PID) Process: | (1540) PE.Explorer_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\sysfile\shell\Open_with_PE_Explorer |
| Operation: | write | Name: | (default) |
Value: Open with PE Explorer | |||
| (PID) Process: | (1540) PE.Explorer_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\sysfile\shell\Open_with_PE_Explorer\command |
| Operation: | write | Name: | (default) |
Value: "C:\Program Files\PE Explorer\pexplorer.exe" "%1" | |||
| (PID) Process: | (1540) PE.Explorer_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\scrfile\shell\Open_with_PE_Explorer |
| Operation: | write | Name: | (default) |
Value: Open with PE Explorer | |||
| (PID) Process: | (1540) PE.Explorer_setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\scrfile\shell\Open_with_PE_Explorer\command |
| Operation: | write | Name: | (default) |
Value: "C:\Program Files\PE Explorer\pexplorer.exe" "%1" | |||
Executable files
23
Suspicious files
84
Text files
74
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1540 | PE.Explorer_setup.tmp | C:\Program Files\PE Explorer\is-8NRUF.tmp | executable | |
MD5:97A39F059A82F77FD3E024D9D2D21857 | SHA256:81EF9C56C9A8E4401FB868A036E33E3A6EDE86FEB7046C8059DEF40BC17DD260 | |||
| 1540 | PE.Explorer_setup.tmp | C:\Program Files\PE Explorer\is-AGUJA.tmp | chm | |
MD5:F3B3F62C4E7F6A59605A15CA045EB3C7 | SHA256:31656FE1F92FACAF49DE5F712CD4681AA6E598A3BA8F5AD979A8FE10A8E10041 | |||
| 1760 | PE.Explorer_setup.exe | C:\Users\admin\AppData\Local\Temp\is-6JEGO.tmp\PE.Explorer_setup.tmp | executable | |
MD5:C04AF2E8479E97B7734A912456464CA8 | SHA256:9E18F7E9753F2951BF13F8CD2E972202AF5D87B21B54A5E2B2BC53E1285EAD48 | |||
| 1540 | PE.Explorer_setup.tmp | C:\Program Files\PE Explorer\unins000.exe | executable | |
MD5:97A39F059A82F77FD3E024D9D2D21857 | SHA256:81EF9C56C9A8E4401FB868A036E33E3A6EDE86FEB7046C8059DEF40BC17DD260 | |||
| 1540 | PE.Explorer_setup.tmp | C:\Users\admin\AppData\Local\Temp\is-442O5.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 1540 | PE.Explorer_setup.tmp | C:\Program Files\PE Explorer\pexplorer.chm | chm | |
MD5:F3B3F62C4E7F6A59605A15CA045EB3C7 | SHA256:31656FE1F92FACAF49DE5F712CD4681AA6E598A3BA8F5AD979A8FE10A8E10041 | |||
| 1540 | PE.Explorer_setup.tmp | C:\Program Files\PE Explorer\pexplorer.exe | executable | |
MD5:133CDA68C8E5F2E3794E794AFB3FC65F | SHA256:0E28175665F3A913D9BF465B66766780DE52753B4B89F5CE0D15298A66E79F8B | |||
| 1540 | PE.Explorer_setup.tmp | C:\Users\admin\AppData\Local\Temp\is-442O5.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:0EE914C6F0BB93996C75941E1AD629C6 | SHA256:4DC09BAC0613590F1FAC8771D18AF5BE25A1E1CB8FDBF4031AA364F3057E74A2 | |||
| 1540 | PE.Explorer_setup.tmp | C:\Program Files\PE Explorer\is-QTA85.tmp | executable | |
MD5:BF9ACDE13D8223576FFB01054A92AF5D | SHA256:AD10D7DC4FB45B8B74EAB93FC9F901BF27F8C21D1CF762744C5A1579879FAFF0 | |||
| 1540 | PE.Explorer_setup.tmp | C:\Program Files\PE Explorer\is-C57SU.tmp | text | |
MD5:6A952C10C56DE70DDA10F8934F0C916F | SHA256:6124508A393C392408E6E931090545918E9D9A68499A64AA46AC616F8E0FC618 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report