| File name: | word.exe |
| Full analysis: | https://app.any.run/tasks/58875dd8-235b-46e7-b770-9b3fa132949e |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | March 14, 2019, 18:42:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 25DC3086DE8BDD780B89B0A7CD9D51BB |
| SHA1: | 9D12A67507E8F7DF1E060ECBAB142205DB18DC2E |
| SHA256: | C50167D9A899572E7DBA0DA1D80E3B9A94B2D3803A8F125119097ED5F92ADD6D |
| SSDEEP: | 12288:fYehPy/HhWunPurNYJ3rwcSARLgBNh8vGI8o6w6GqVIABosrLt:NPwnPcNYJ3rwcLRLgBNh/I8o6hVITsrx |
MALICIOUS
Deletes shadow copies
- word.exe (PID: 3464)
Renames files like Ransomware
- word.exe (PID: 3464)
Dropped file may contain instructions of ransomware
- word.exe (PID: 3464)
Actions looks like stealing of personal data
- word.exe (PID: 3464)
GANDCRAB detected
- word.exe (PID: 3464)
Writes file to Word startup folder
- word.exe (PID: 3464)
SUSPICIOUS
Creates files in the program directory
- word.exe (PID: 3464)
Reads the cookies of Mozilla Firefox
- word.exe (PID: 3464)
Creates files in the user directory
- word.exe (PID: 3464)
INFO
Dropped object may contain TOR URL's
- word.exe (PID: 3464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:13 14:26:40+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 316416 |
| InitializedDataSize: | 373248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x35342 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.5.5 |
| ProductVersionNumber: | 1.3.5.5 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| LegalTrademarks: | (c). All rights reserved. djsoft.net (c) 2003-2015 |
| Comments: | Nullable Arsenals Identifier Addpackage |
| ProductName: | Custody |
| CompanyName: | djsoft.net (c) 2003-2015 |
| LegalCopyright: | (c). All rights reserved. djsoft.net (c) 2003-2015 |
| FileDescription: | Nullable Arsenals Identifier Addpackage |
| ProductVersion: | 1.3.5.5 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Mar-2019 13:26:40 |
| Detected languages: |
|
| Debug artifacts: |
|
| LegalTrademarks: | (c). All rights reserved. djsoft.net (c) 2003-2015 |
| Comments: | Nullable Arsenals Identifier Addpackage |
| ProductName: | Custody |
| CompanyName: | djsoft.net (c) 2003-2015 |
| LegalCopyright: | (c). All rights reserved. djsoft.net (c) 2003-2015 |
| FileDescription: | Nullable Arsenals Identifier Addpackage |
| ProductVersion: | 1.3.5.5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 13-Mar-2019 13:26:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004D2E6 | 0x0004D400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63879 |
.rdata | 0x0004F000 | 0x0001D1B8 | 0x0001D200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.39939 |
.data | 0x0006D000 | 0x00005338 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.72215 |
.rsrc | 0x00073000 | 0x0003BC54 | 0x0003BE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.152 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.9549 | 624 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.22214 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.39111 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.77355 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.29433 | 10344 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.10799 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.80883 | 90 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
201 | 4 | 16 | Latin 1 / Western European | English - United States | RT_RCDATA |
202 | 6.05831 | 1462 | Latin 1 / Western European | English - United States | RT_RCDATA |
203 | 7.59911 | 3724 | Latin 1 / Western European | English - United States | RT_RCDATA |
Imports
ADVAPI32.dll |
AVIFIL32.dll |
COMCTL32.dll |
GDI32.dll |
GLU32.dll |
KERNEL32.dll |
MSVFW32.dll |
OLEAUT32.dll |
OPENGL32.dll |
SETUPAPI.dll |
Total processes
34
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2340 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2860 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3464 | "C:\Users\admin\AppData\Local\Temp\word.exe" | C:\Users\admin\AppData\Local\Temp\word.exe | explorer.exe | ||||||||||||
User: admin Company: djsoft.net (c) 2003-2015 Integrity Level: MEDIUM Description: Nullable Arsenals Identifier Addpackage Exit code: 0 Modules
| |||||||||||||||
| 3836 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | word.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
Total events
107
Read events
103
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3464) word.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3464) word.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
414
Text files
314
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3464 | word.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 3464 | word.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 3464 | word.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.orgxtg | — | |
MD5:— | SHA256:— | |||
| 3464 | word.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3464 | word.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3464 | word.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{38e8535f-27d0-4352-aa3a-ce4178930102}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3464 | word.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{3cc0f82b-873a-4e59-b89f-689fbdf88af9}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
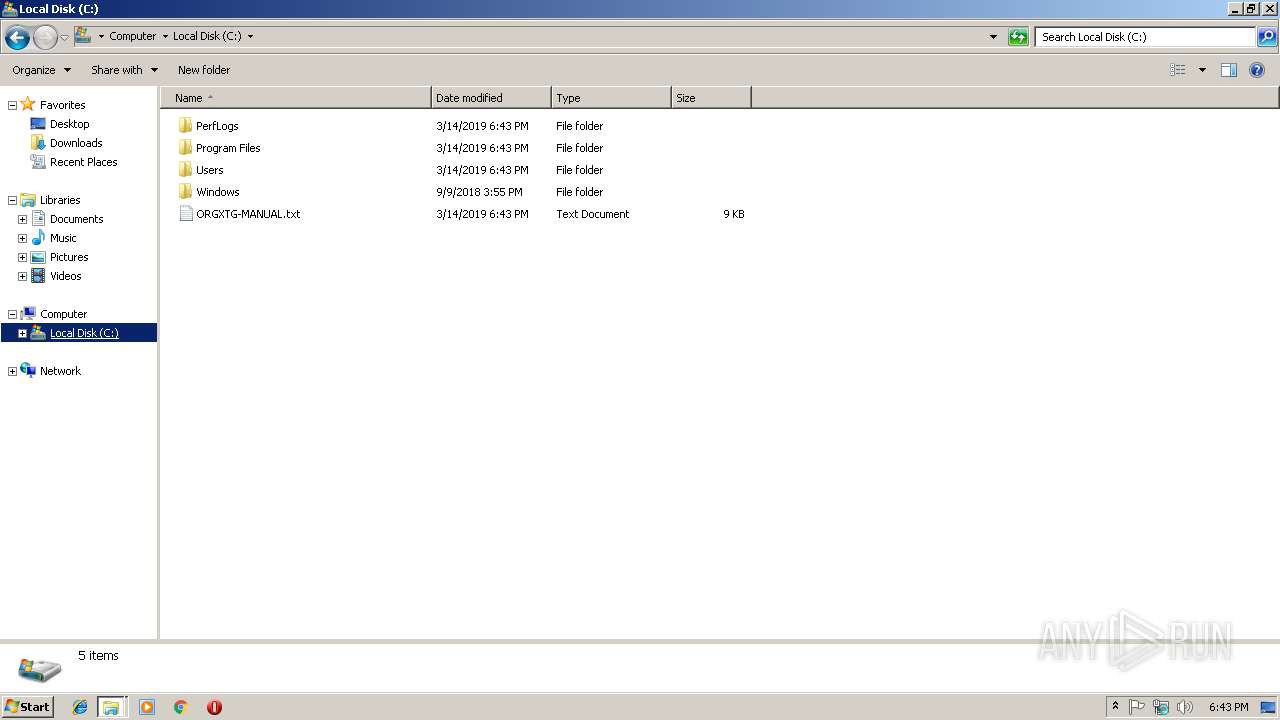
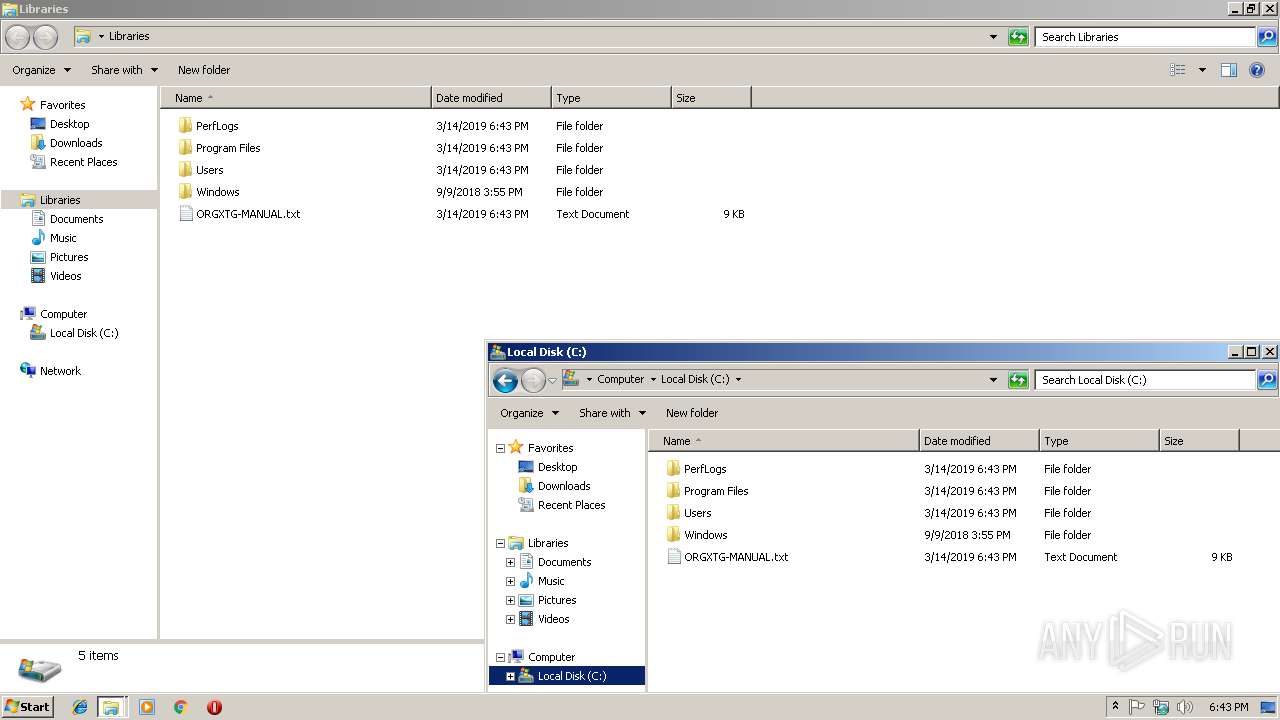
| 3464 | word.exe | C:\ORGXTG-MANUAL.txt | text | |
MD5:— | SHA256:— | |||
| 3464 | word.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{5c4beaff-a038-4df7-9b35-072a18f8e3d6}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 3464 | word.exe | C:\Users\ORGXTG-MANUAL.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report