| File name: | Yandex.exe |
| Full analysis: | https://app.any.run/tasks/65b2a910-8551-412d-b271-7fa4b550efab |
| Verdict: | No threats detected |
| Analysis date: | June 01, 2018, 11:47:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F4A2D0AA8C8F2299F3AFBD85C7449F78 |
| SHA1: | FFE38436DF97DE56F9690A1D2CE80E440D1D7885 |
| SHA256: | C4FFDCE99CE41D9A5EEF2F0995A25BB5C560D32A7FE853C162C82B593C1CCF34 |
| SSDEEP: | 3072:szsEk2Aow7vBqVrdlv/I+izNVgkWde8WA7H7dmr+ta+ictxGtg6S9xy3+v2qJ:sz023gvBqVhlvnHPWAlmrI6SfY+v2qJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
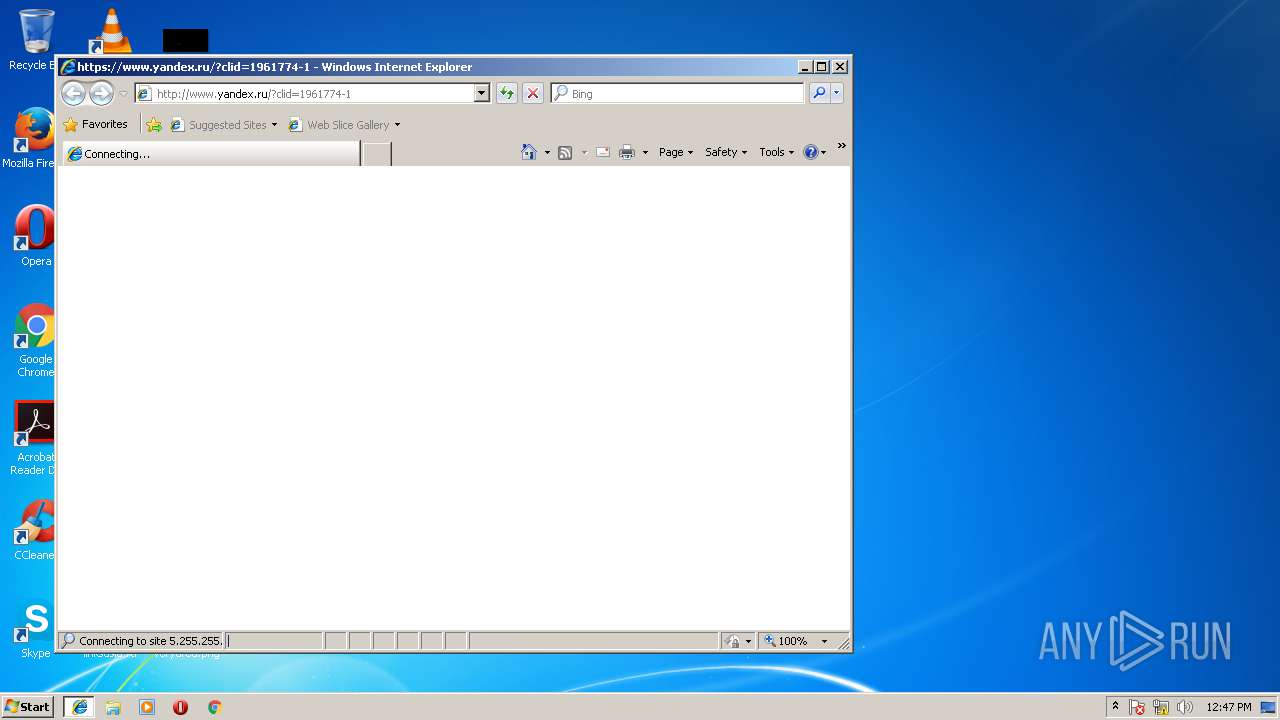
Starts Internet Explorer
- Yandex.exe (PID: 3112)
INFO
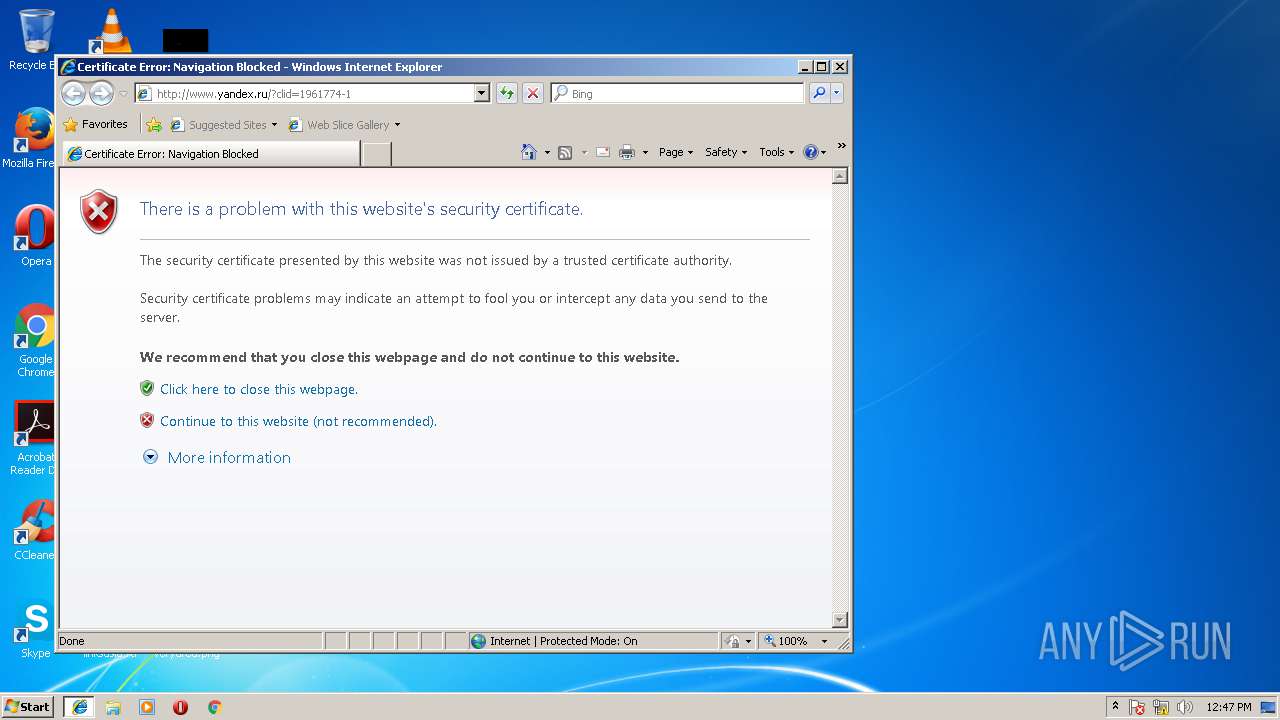
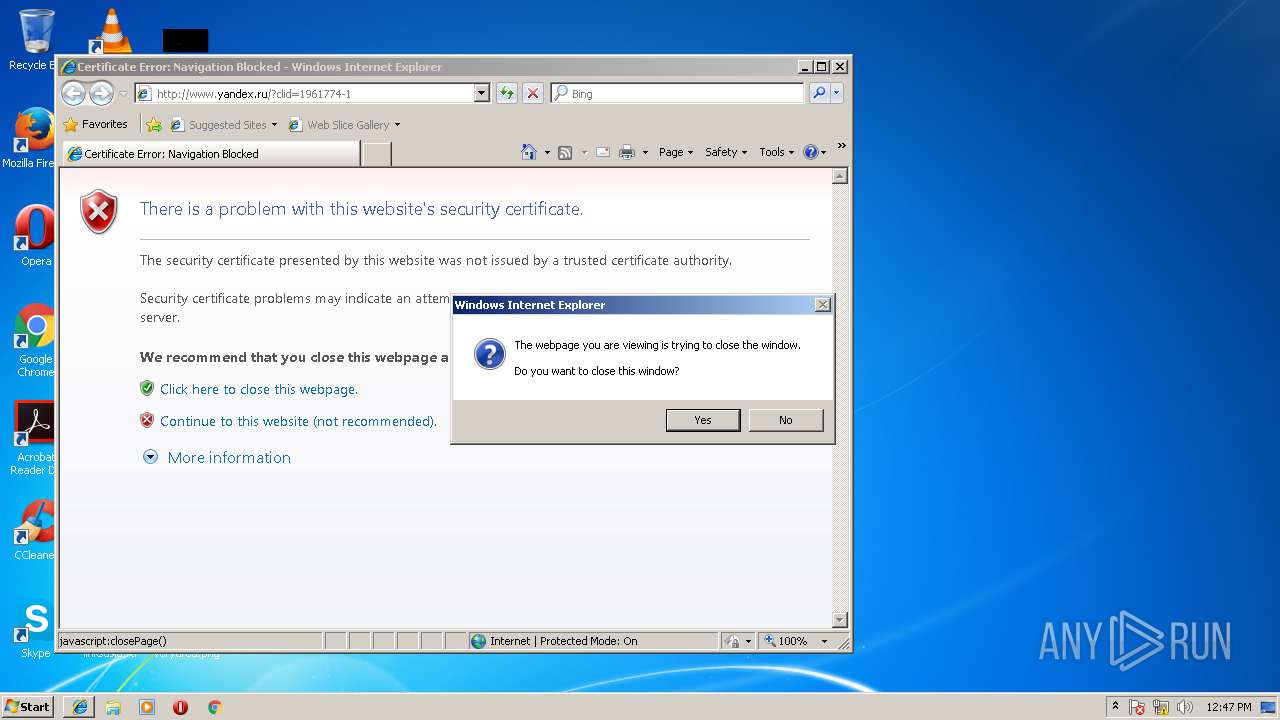
Changes internet zones settings
- IEXPLORE.EXE (PID: 3976)
Creates files in the user directory
- IEXPLORE.EXE (PID: 3976)
- IEXPLORE.EXE (PID: 620)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 620)
Reads Internet Cache Settings
- IEXPLORE.EXE (PID: 620)
Dropped object may contain URL's
- IEXPLORE.EXE (PID: 620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:05:07 19:01:09+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 142336 |
| InitializedDataSize: | 84992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12d68 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.2116 |
| ProductVersionNumber: | 2.0.0.2116 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | YandexPin |
| FileVersion: | 2.0.0.2116 |
| InternalName: | YandexPin |
| LegalCopyright: | Copyright (C) Yandex 2014 |
| OriginalFileName: | YandexPin.exe |
| ProductName: | YandexPin |
| ProductVersion: | 2.0.0.2116 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-May-2015 17:01:09 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileDescription: | YandexPin |
| FileVersion: | 2.0.0.2116 |
| InternalName: | YandexPin |
| LegalCopyright: | Copyright (C) Yandex 2014 |
| OriginalFilename: | YandexPin.exe |
| ProductName: | YandexPin |
| ProductVersion: | 2.0.0.2116 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 07-May-2015 17:01:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00022A45 | 0x00022C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60143 |
.rdata | 0x00024000 | 0x0000A8EE | 0x0000AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.77024 |
.data | 0x0002F000 | 0x00003540 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.49697 |
.rsrc | 0x00033000 | 0x00004FB0 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.45011 |
.reloc | 0x00038000 | 0x00001B88 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.58844 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.30841 | 904 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.18993 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.9003 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.68237 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 3.1893 | 136 | UNKNOWN | Belarusian - Belarus | RT_STRING |
129 | 2.62308 | 62 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
Secur32.dll |
VERSION.dll |
WININET.dll |
WTSAPI32.dll |
ole32.dll |
Total processes
33
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" SCODEF:3976 CREDAT:71937 | C:\Program Files\Internet Explorer\IEXPLORE.EXE | IEXPLORE.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3112 | "C:\Users\admin\AppData\Local\Temp\Yandex.exe" | C:\Users\admin\AppData\Local\Temp\Yandex.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: YandexPin Exit code: 1 Version: 2.0.0.2116 Modules
| |||||||||||||||
| 3976 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" www.yandex.ru?clid=1961774-1 | C:\Program Files\Internet Explorer\IEXPLORE.EXE | Yandex.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
397
Read events
348
Write events
48
Delete events
1
Modification events
| (PID) Process: | (3112) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YaPinLancher |
| Operation: | write | Name: | Counter |
Value: 0 | |||
| (PID) Process: | (3976) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3976) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3976) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3976) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3976) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3976) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006B000000010000000000000000000000000000000000000000000000400C35B347C7D301000000000000000000000000020000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001C00000000000000000000000000000000000000000000000000000000000000170000000000000000000000000000000000FFFFC0A8640B000000000000000002000000C0A801640000000000000000000000000000000000000000000000000C00000C37D0000010A73800D8703600000000000000000000000000000000000000000000000000000000000000000000000000000000000000000081F800009000230090002300380023000000000000702C000A00000000000000F8412C00 | |||
| (PID) Process: | (3976) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {93118F6B-6591-11E8-B27F-5254004AAD21} |
Value: 0 | |||
| (PID) Process: | (3976) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3976) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 5 | |||
Executable files
0
Suspicious files
7
Text files
13
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3976 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\2LKO8ICX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3976 | IEXPLORE.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 620 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\CabF8EA.tmp | — | |
MD5:— | SHA256:— | |||
| 620 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\TarF8EB.tmp | — | |
MD5:— | SHA256:— | |||
| 620 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\CabF8FB.tmp | — | |
MD5:— | SHA256:— | |||
| 620 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\TarF8FC.tmp | — | |
MD5:— | SHA256:— | |||
| 620 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\CabF95B.tmp | — | |
MD5:— | SHA256:— | |||
| 620 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\TarF95C.tmp | — | |
MD5:— | SHA256:— | |||
| 620 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\CabF97C.tmp | — | |
MD5:— | SHA256:— | |||
| 620 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\TarF97D.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
5
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
620 | IEXPLORE.EXE | GET | 302 | 5.255.255.55:80 | http://www.yandex.ru/?clid=1961774-1 | RU | — | — | whitelisted |
620 | IEXPLORE.EXE | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
620 | IEXPLORE.EXE | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
620 | IEXPLORE.EXE | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
620 | IEXPLORE.EXE | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
620 | IEXPLORE.EXE | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
620 | IEXPLORE.EXE | GET | 200 | 23.111.11.204:80 | http://repository.certum.pl/ctnca.cer | US | der | 959 b | whitelisted |
3976 | IEXPLORE.EXE | GET | 200 | 204.79.197.229:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
620 | IEXPLORE.EXE | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
620 | IEXPLORE.EXE | 5.255.255.55:80 | www.yandex.ru | YANDEX LLC | RU | whitelisted |
3976 | IEXPLORE.EXE | 204.79.197.229:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
620 | IEXPLORE.EXE | 5.255.255.55:443 | www.yandex.ru | YANDEX LLC | RU | whitelisted |
620 | IEXPLORE.EXE | 23.111.11.204:80 | repository.certum.pl | netDNA | US | unknown |
620 | IEXPLORE.EXE | 2.16.186.81:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.yandex.ru |
| whitelisted |
www.bing.com |
| whitelisted |
repository.certum.pl |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Yandex.exe | GetLoggedUserSid(): szUserName = admin, szDomain = PC, dwSessionId = 1
|
Yandex.exe | GetLoggedUserSid(): user sid is found: S-1-5-21-1302019708-1500728564-335382590-1000
|
Yandex.exe | GetRunData() : run as user SID = S-1-5-21-1302019708-1500728564-335382590-1000
|
Yandex.exe | Process runs normally, i.e. under a logged user
|
Yandex.exe | SwitchRegistry() In |
Yandex.exe | SwitchRegistry() Out |
Yandex.exe | GetTaskBarDirPath() : Call GetUserSpecDirPath() |
Yandex.exe | GetUserSpecDirPath(1, bTakeAsIs = 0) res = C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\User Pinned\TaskBar.
|
Yandex.exe | GetPinnedSiteFiles(): no website files found in C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\User Pinned\TaskBar.
|
Yandex.exe | GetPinnedSiteFiles(): no website files found in C:\Users\admin\AppData\Local\Temp.
|