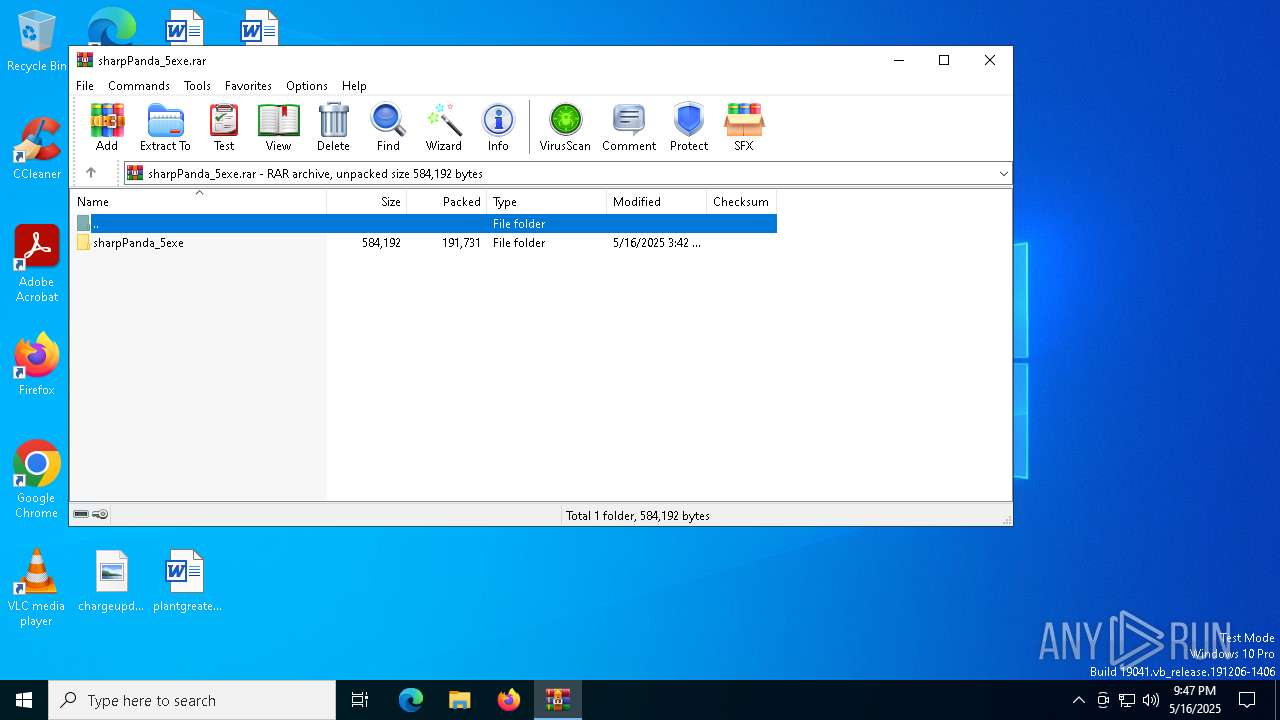
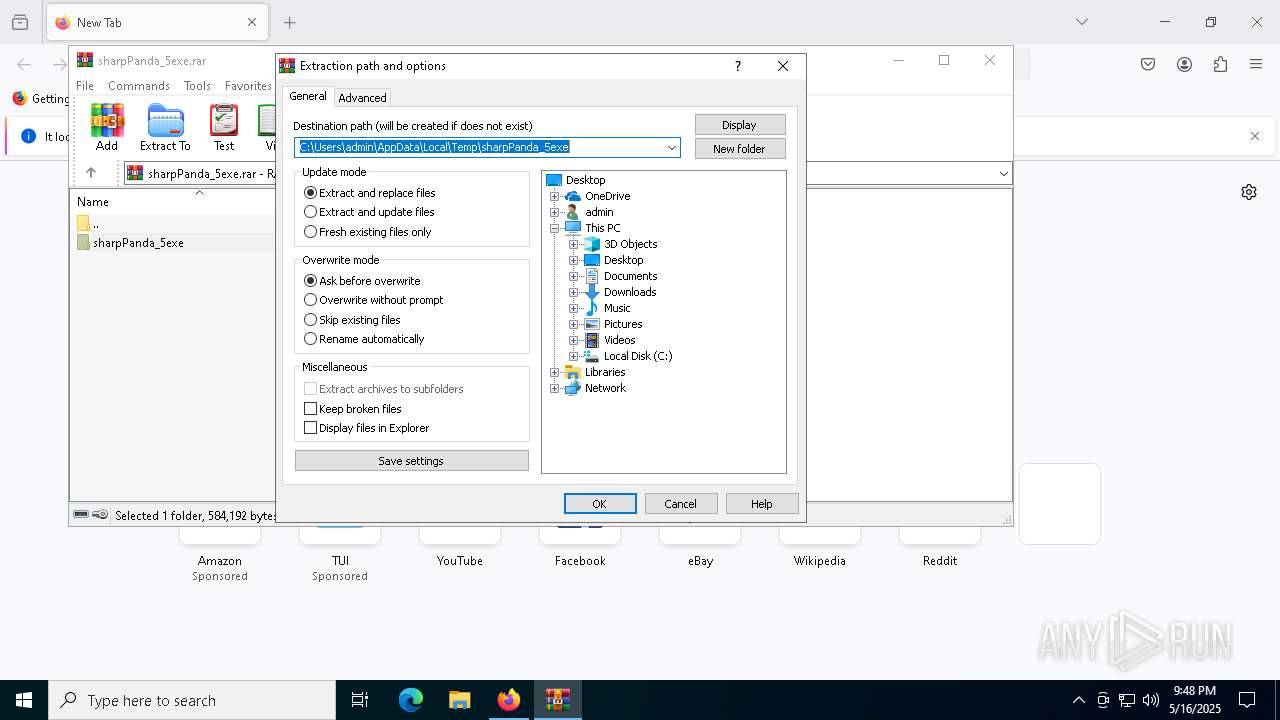
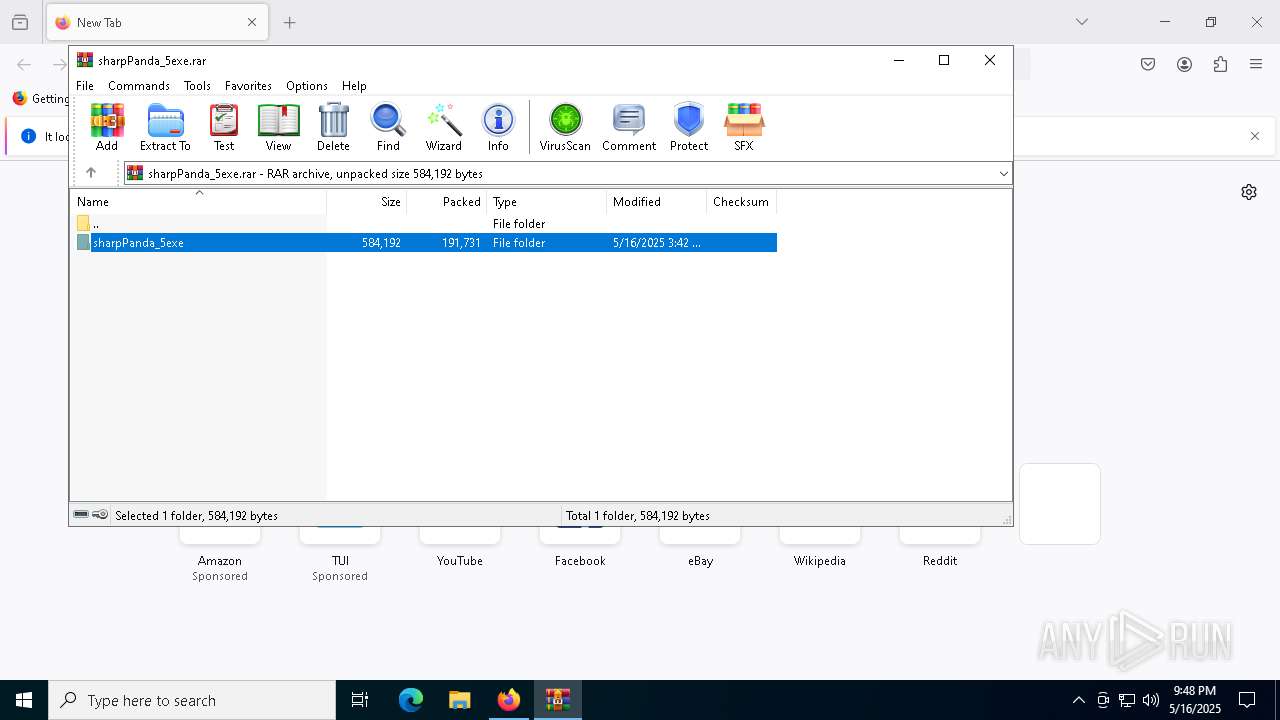
| File name: | sharpPanda_5exe.rar |
| Full analysis: | https://app.any.run/tasks/43f1f40d-084c-488c-bb1a-1f97fd15cbf8 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 21:47:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | CD2786A7702D4B4F604789C9527D90D6 |
| SHA1: | 78AC57FB353FB23181858B122622063F826AB98D |
| SHA256: | C4F34075F301985F4CA1DD4D9C1B4DEBDE679D33F7DBE7F6963655C35E382550 |
| SSDEEP: | 6144:dSSFkuQN4AIk2r+rfOLazTY4Ert6ARqVC5yT1lRi5QxO:dSmkuQXtBfh3Gt6ARo8yfRhxO |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 5680)
- powershell.exe (PID: 7224)
- powershell.exe (PID: 7644)
- powershell.exe (PID: 968)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 1040)
SUSPICIOUS
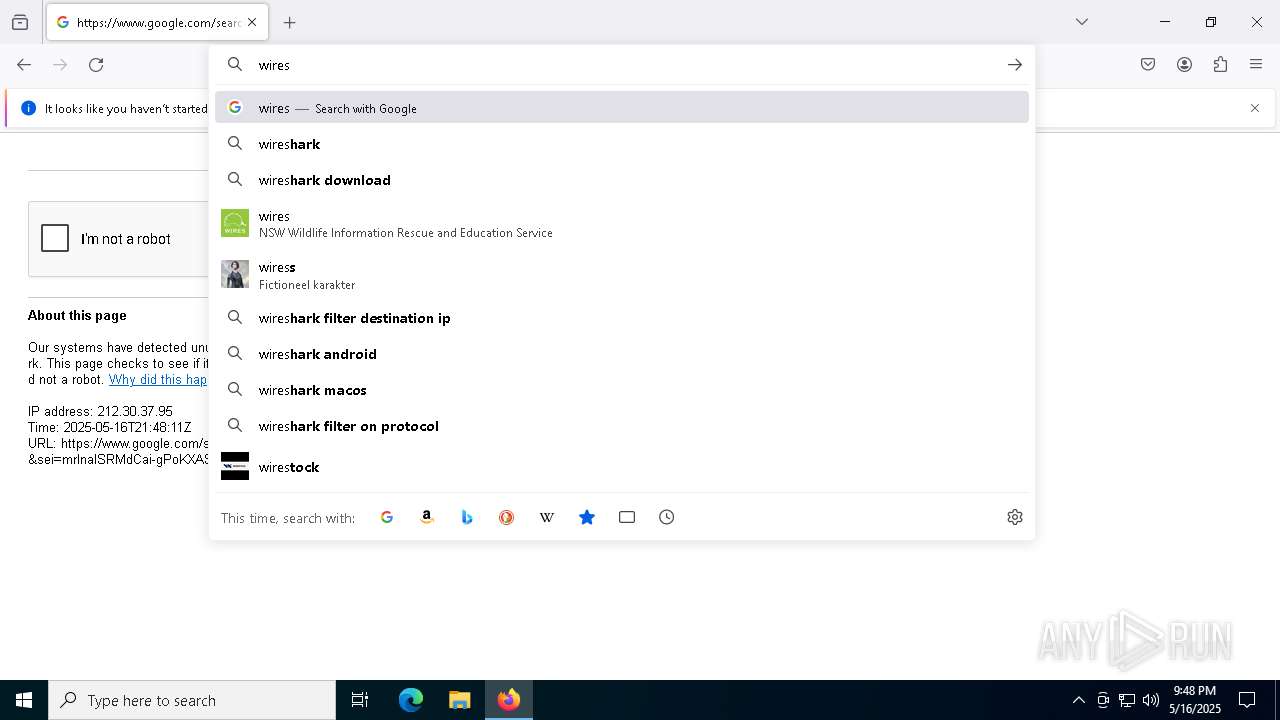
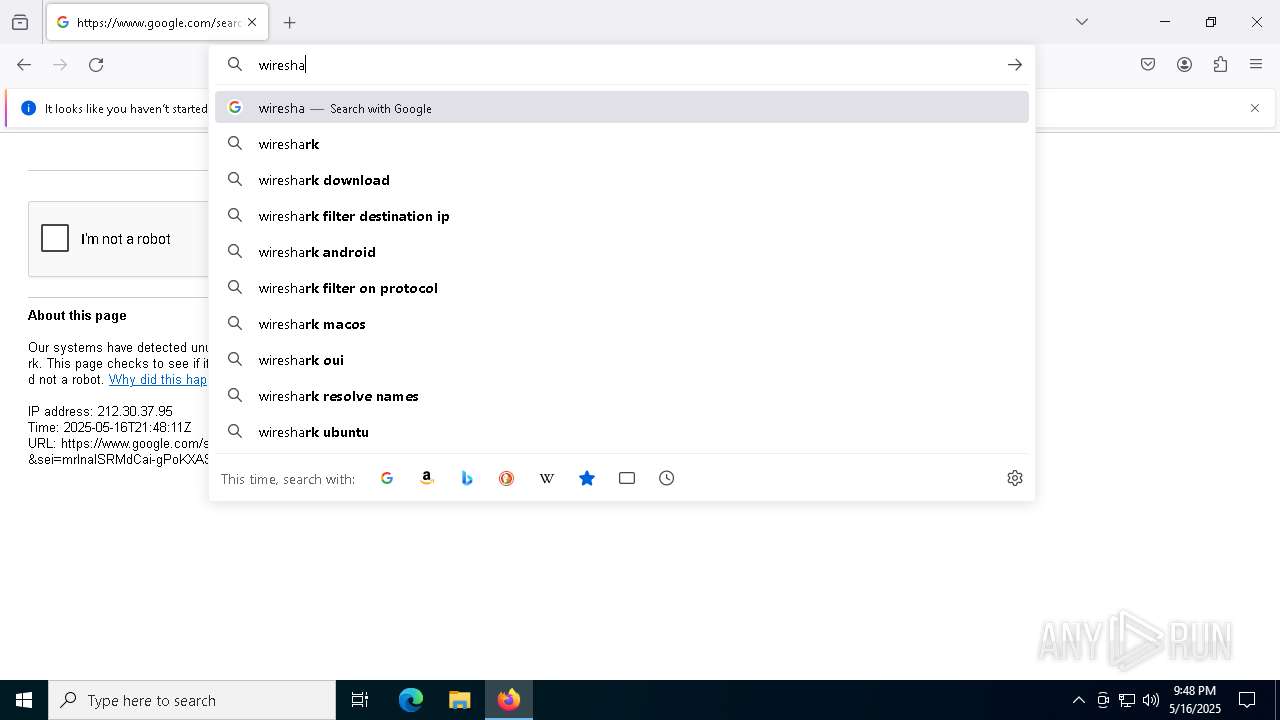
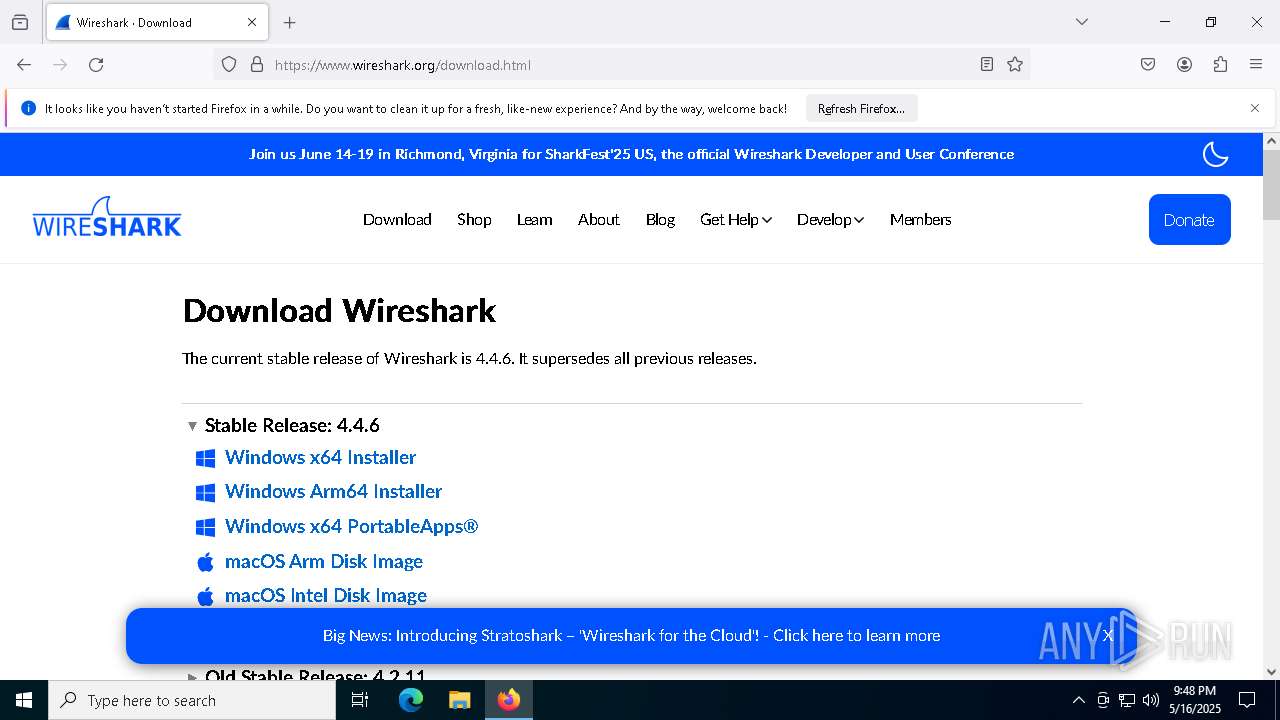
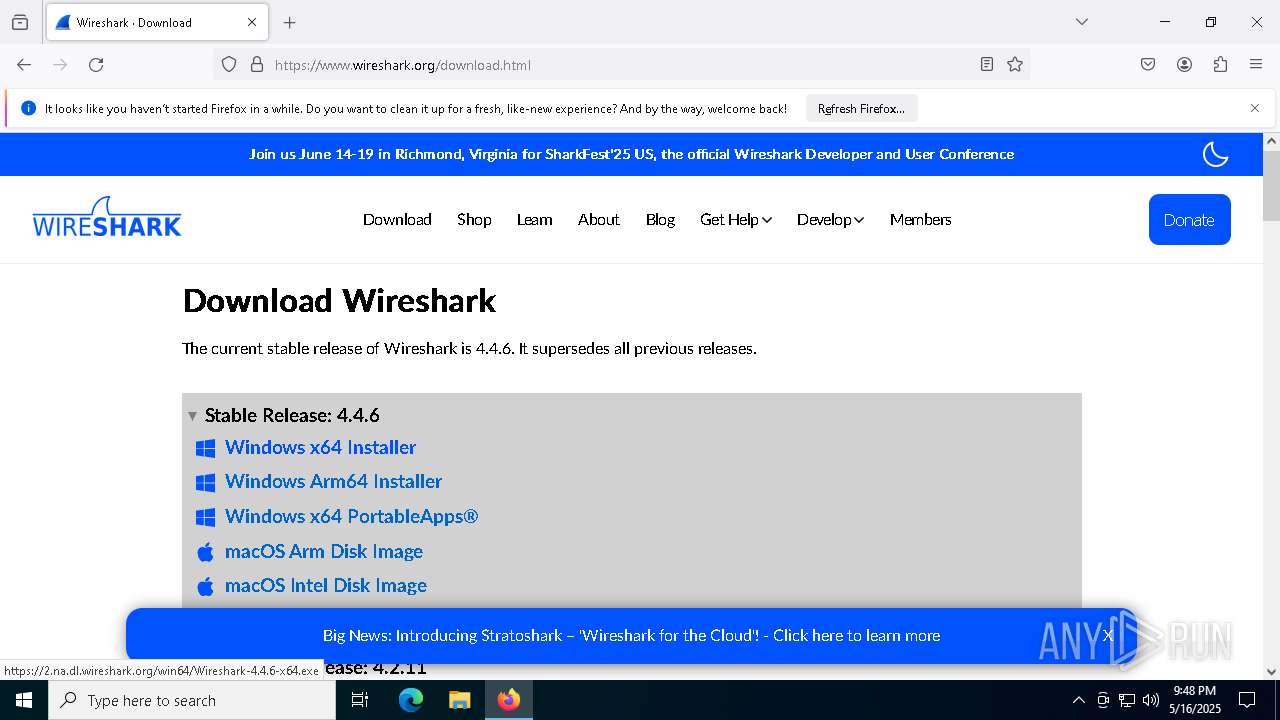
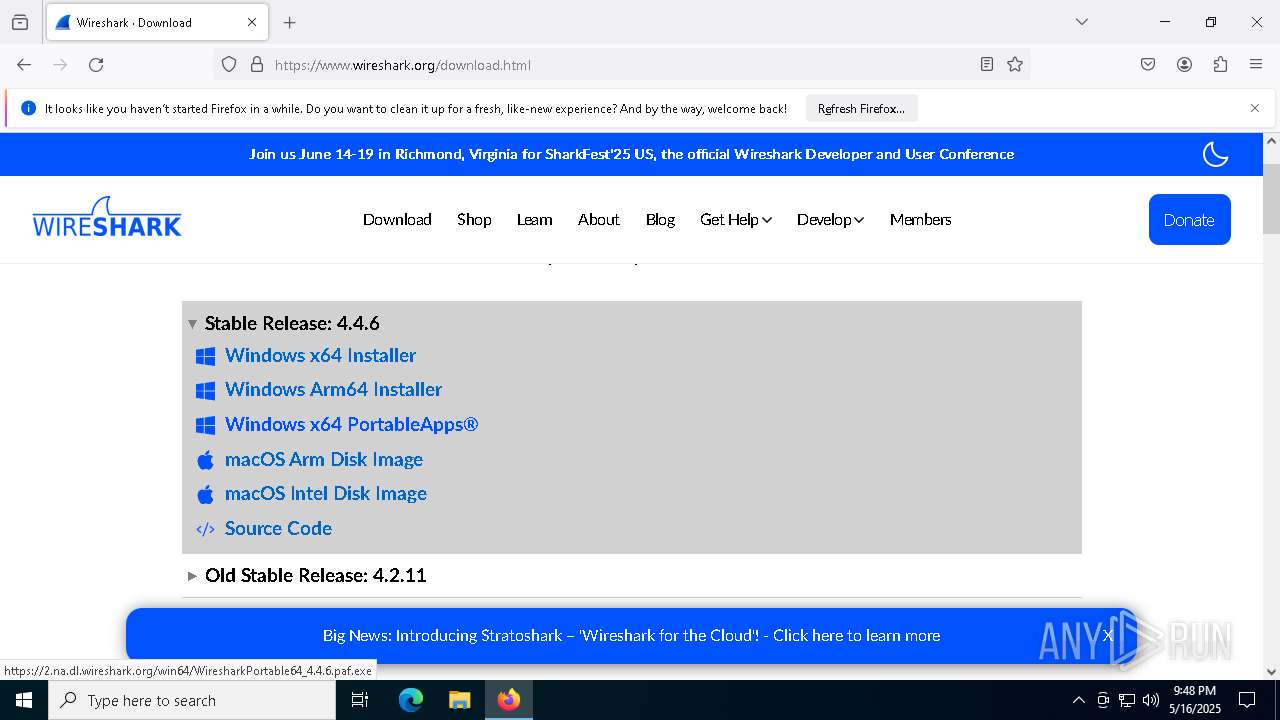
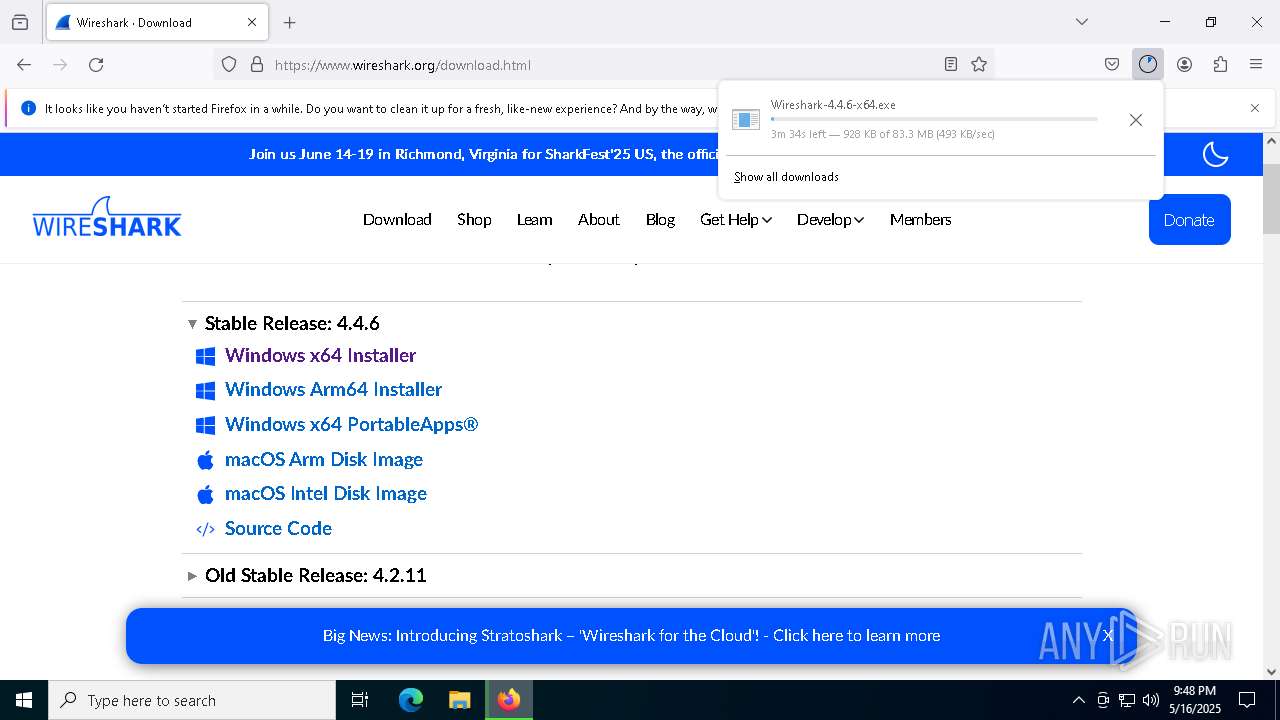
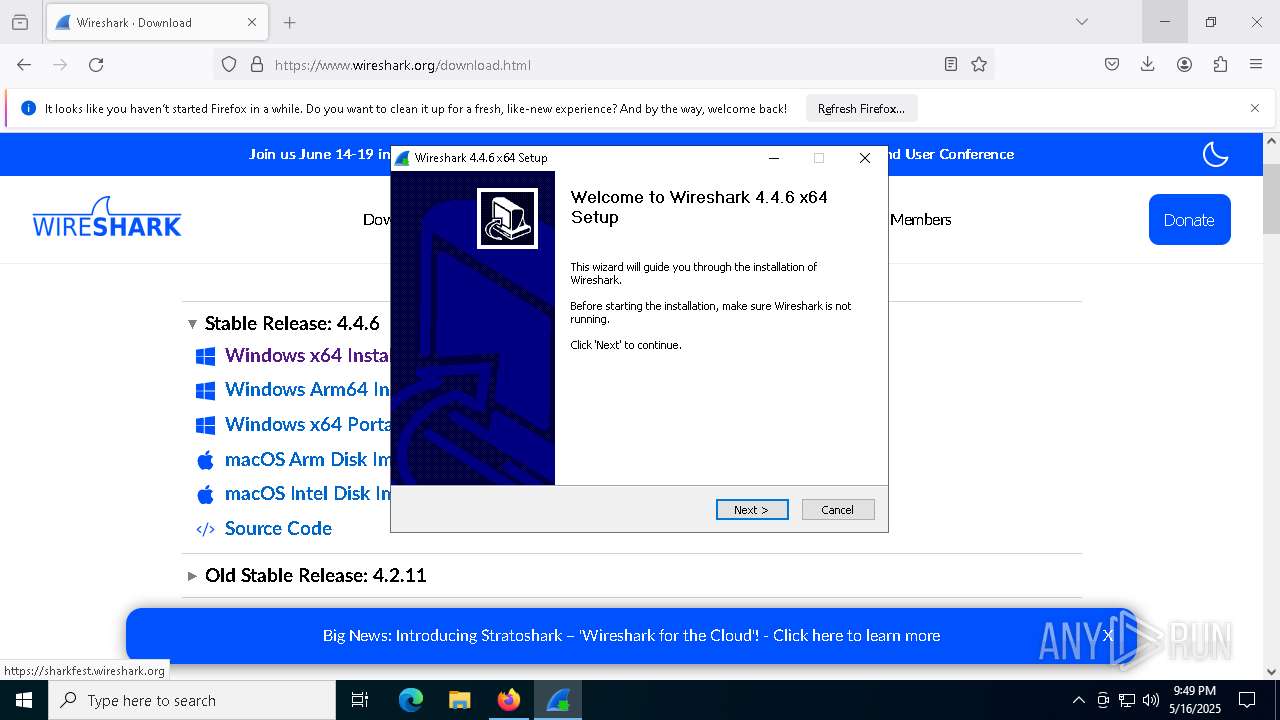
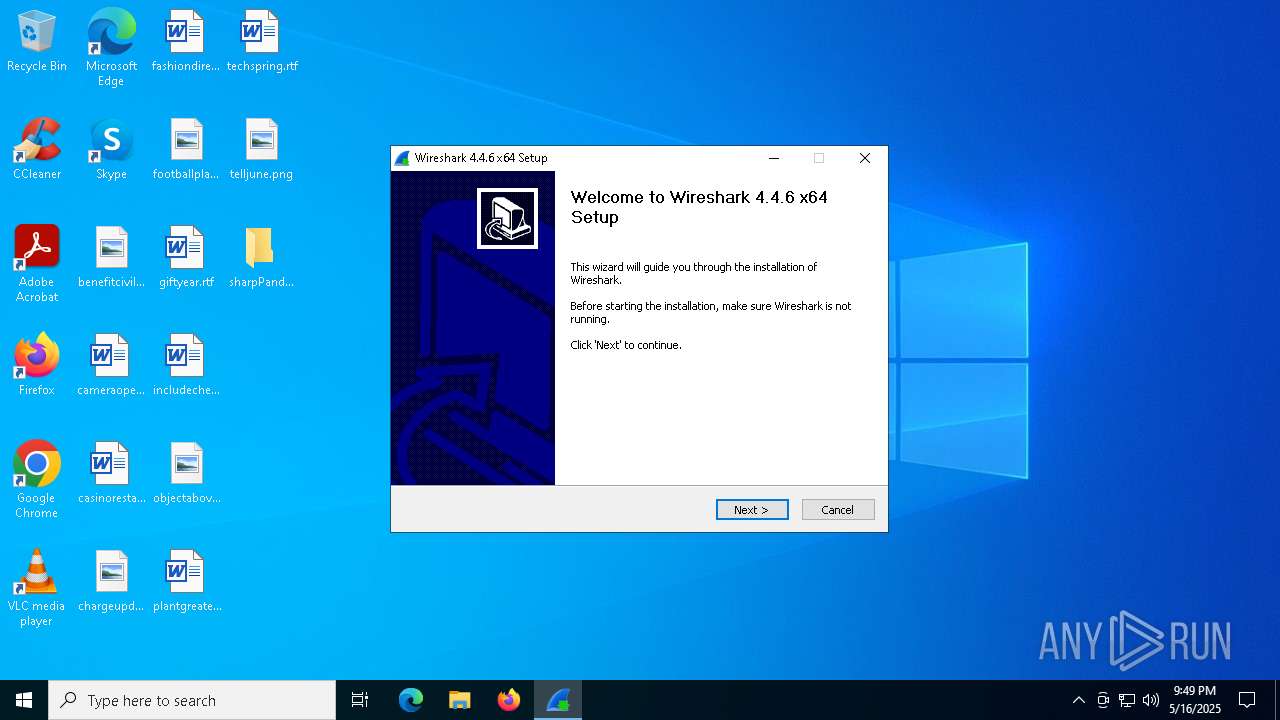
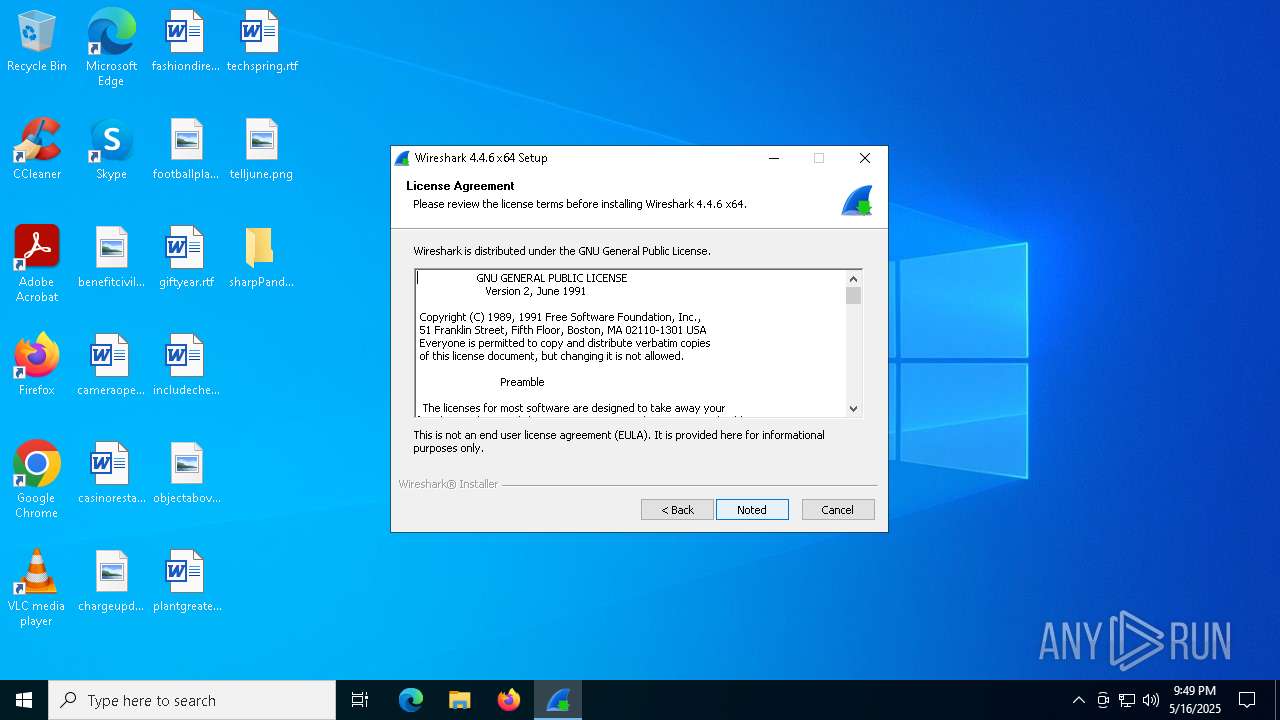
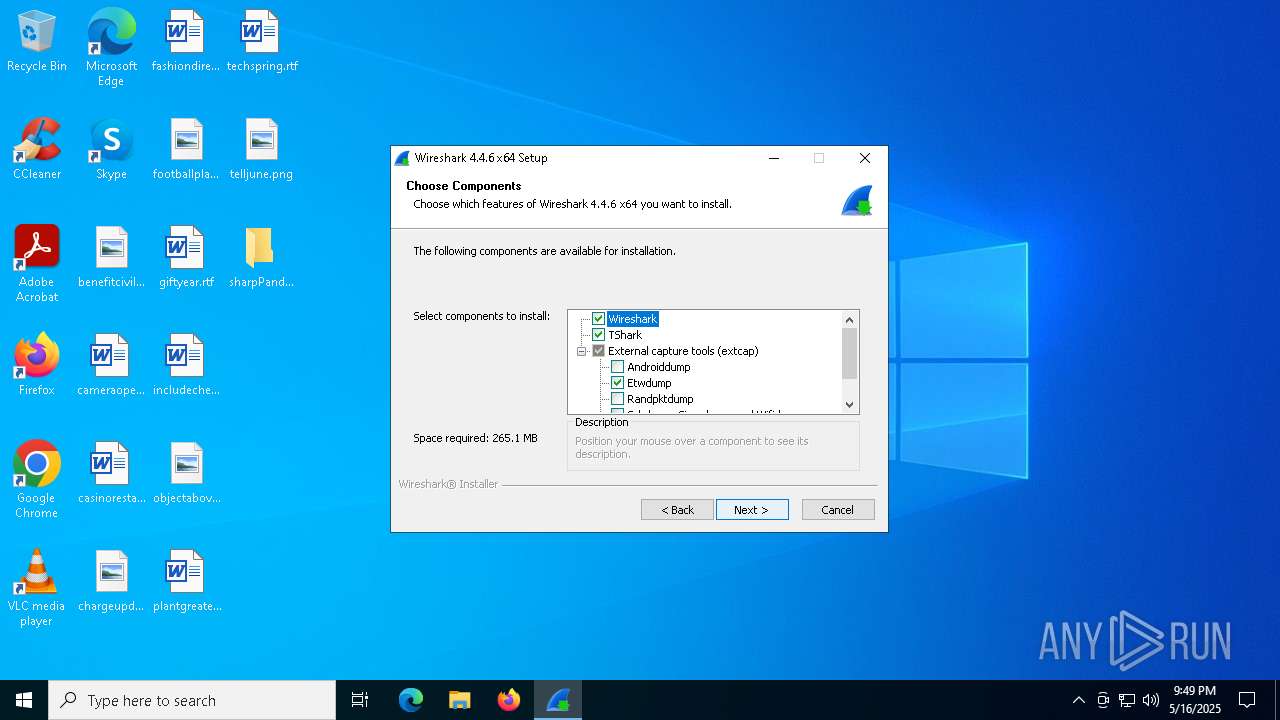
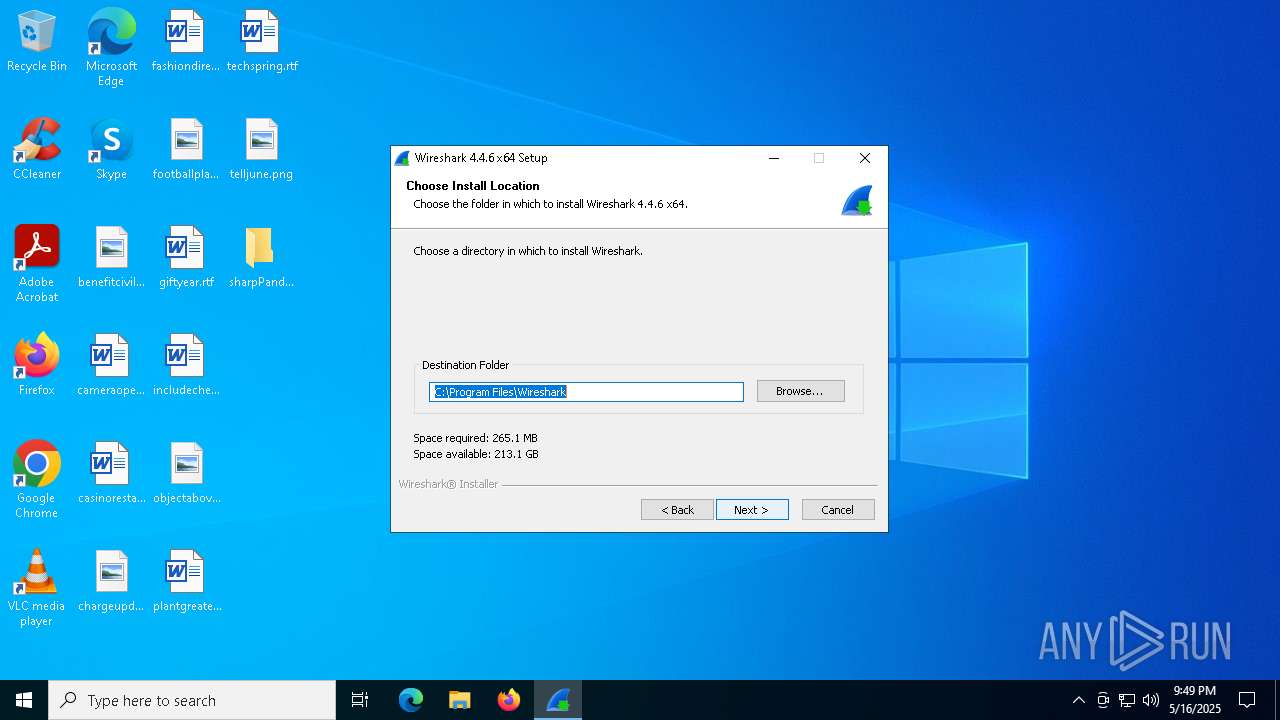
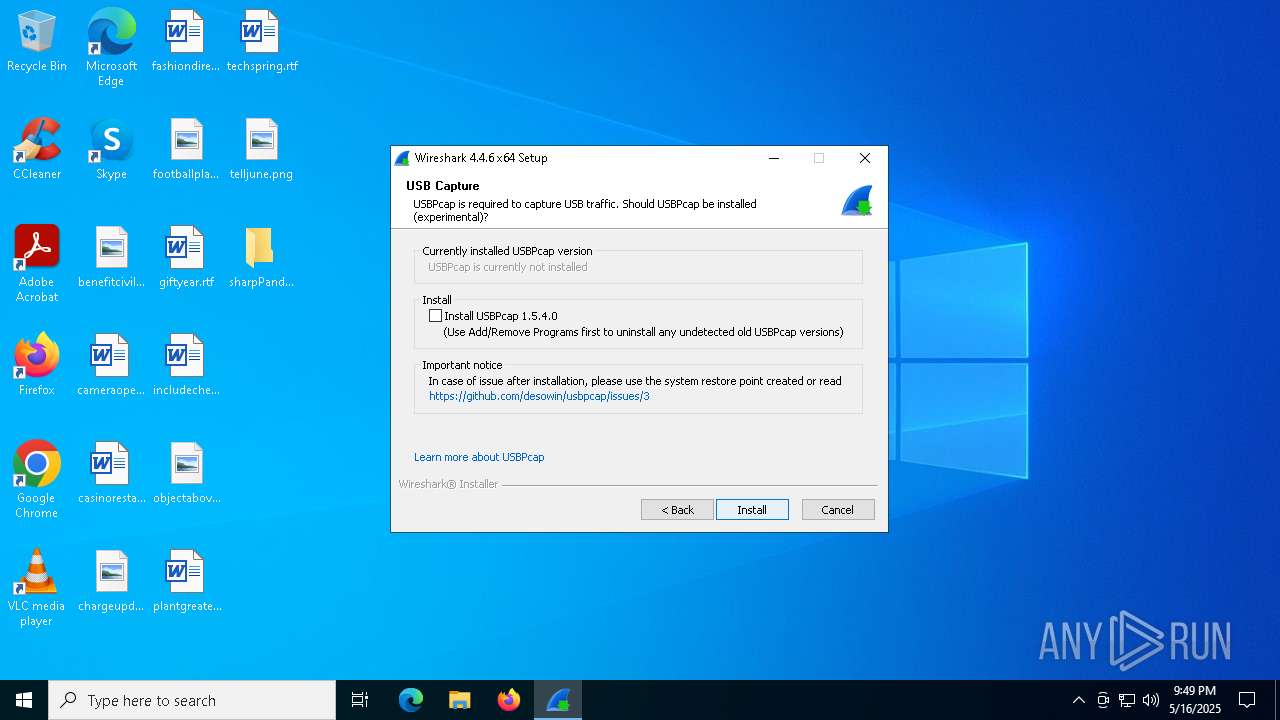
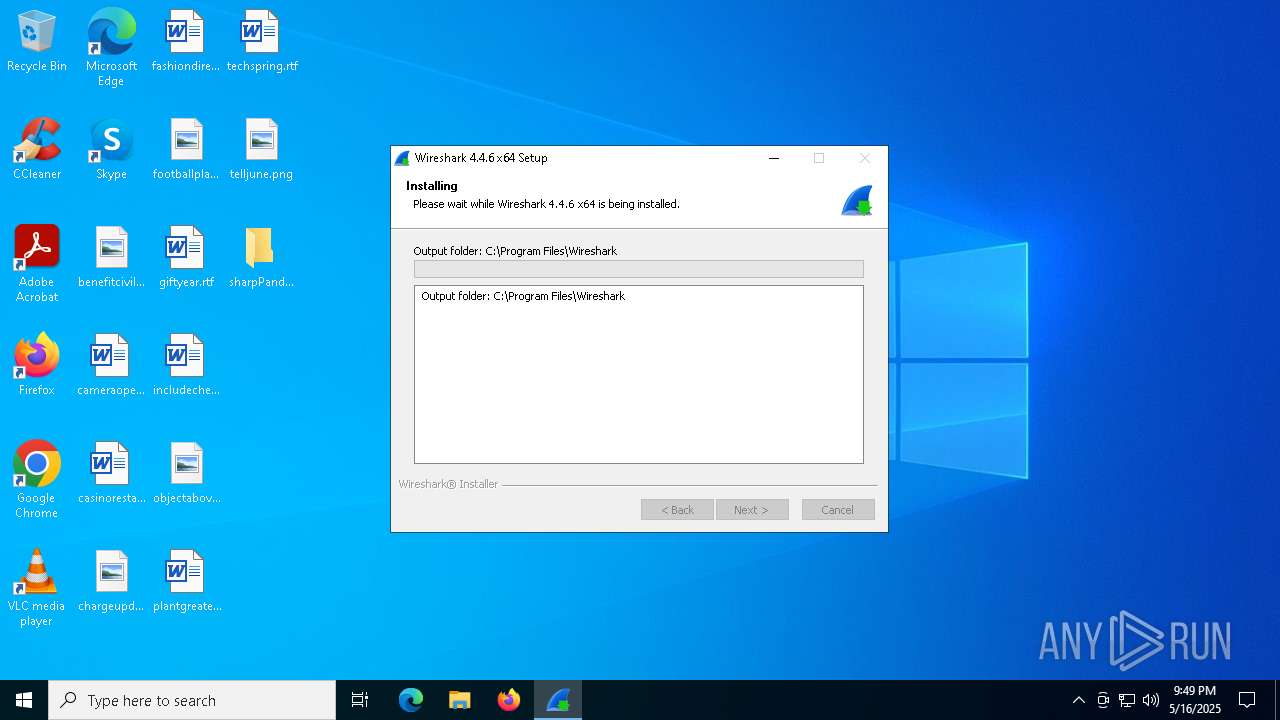
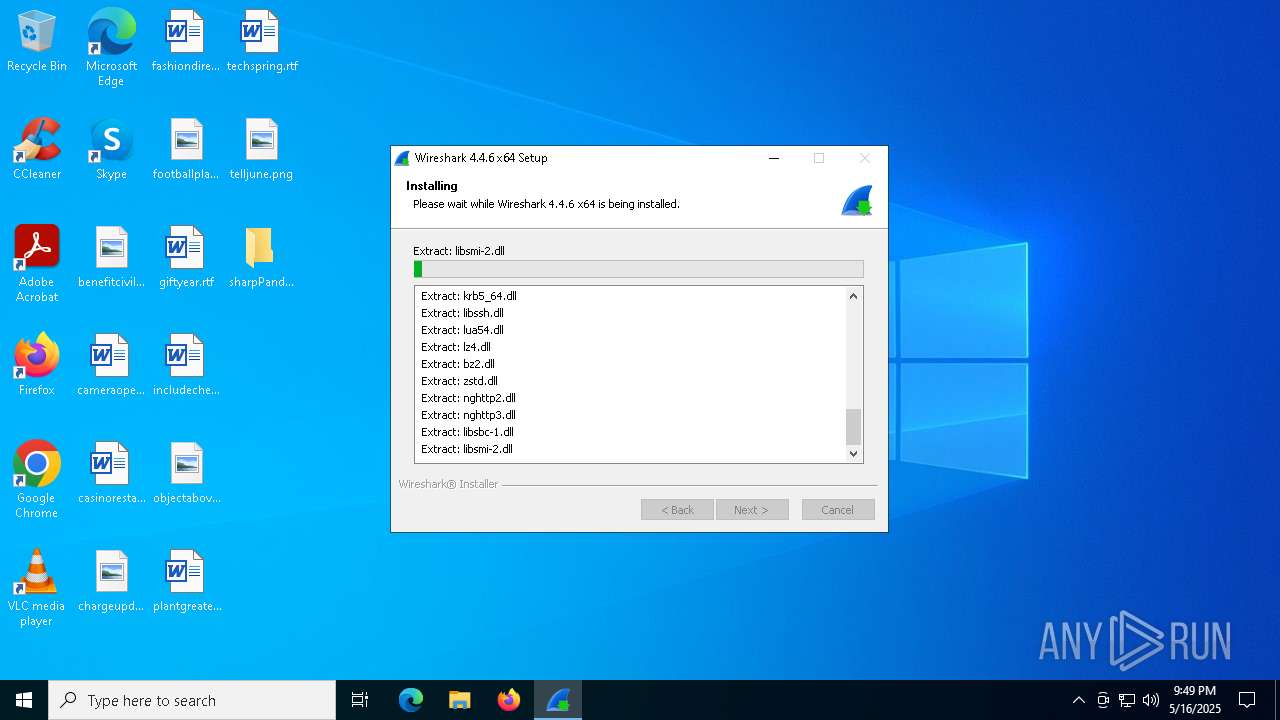
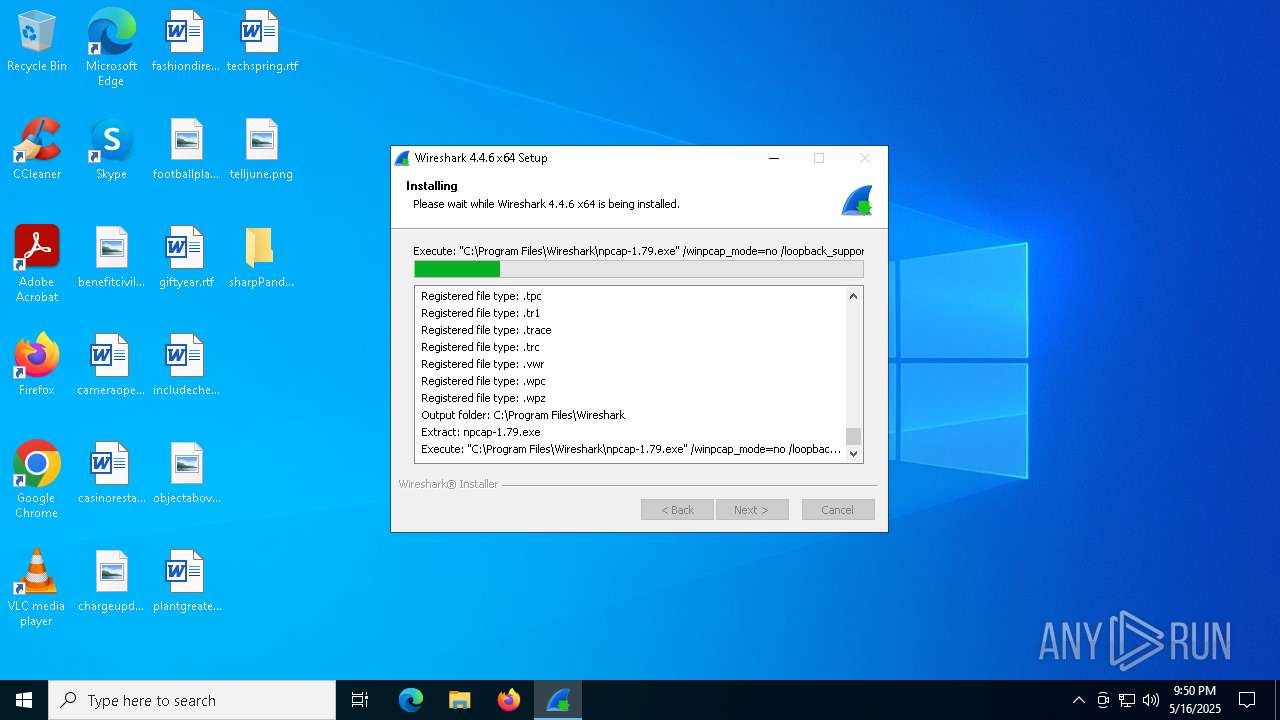
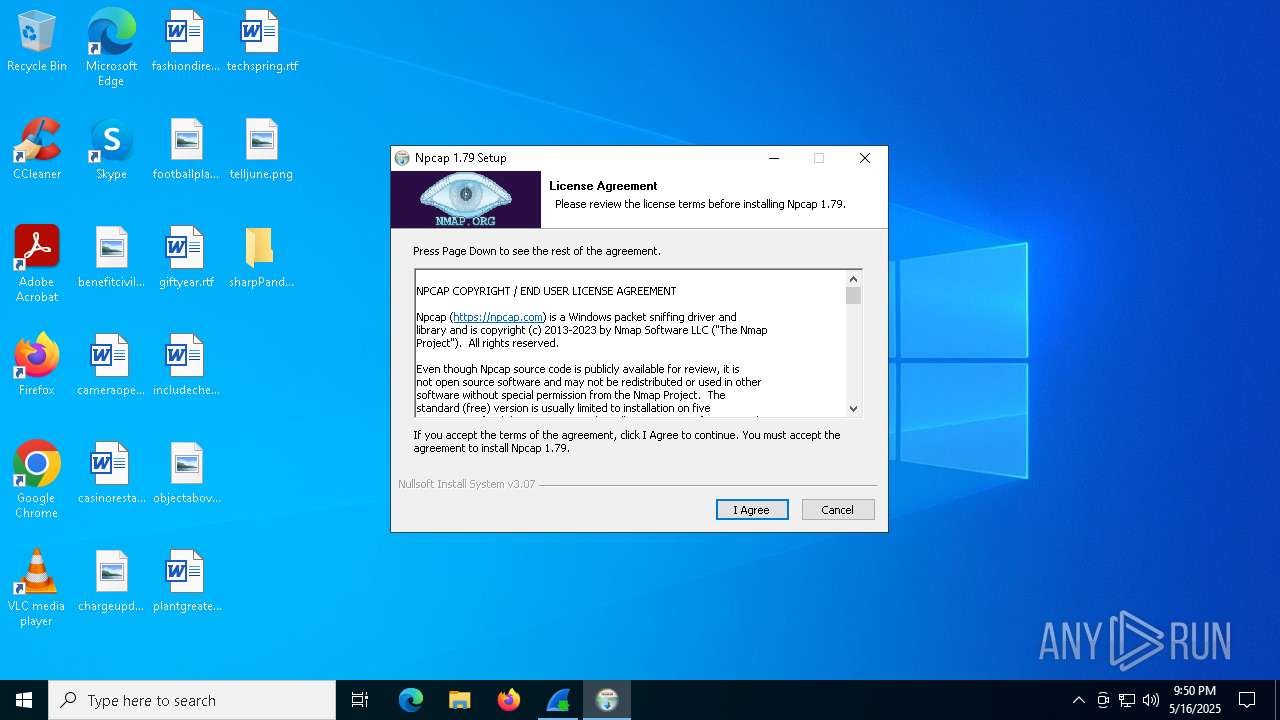
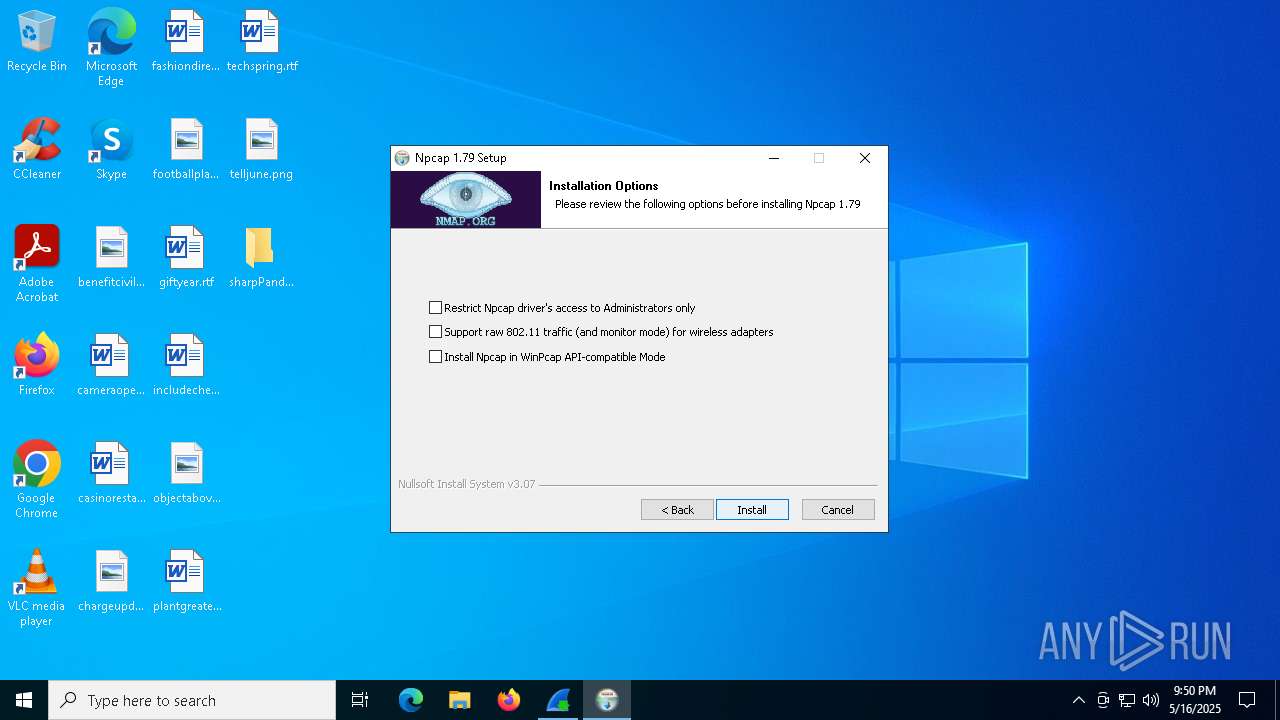
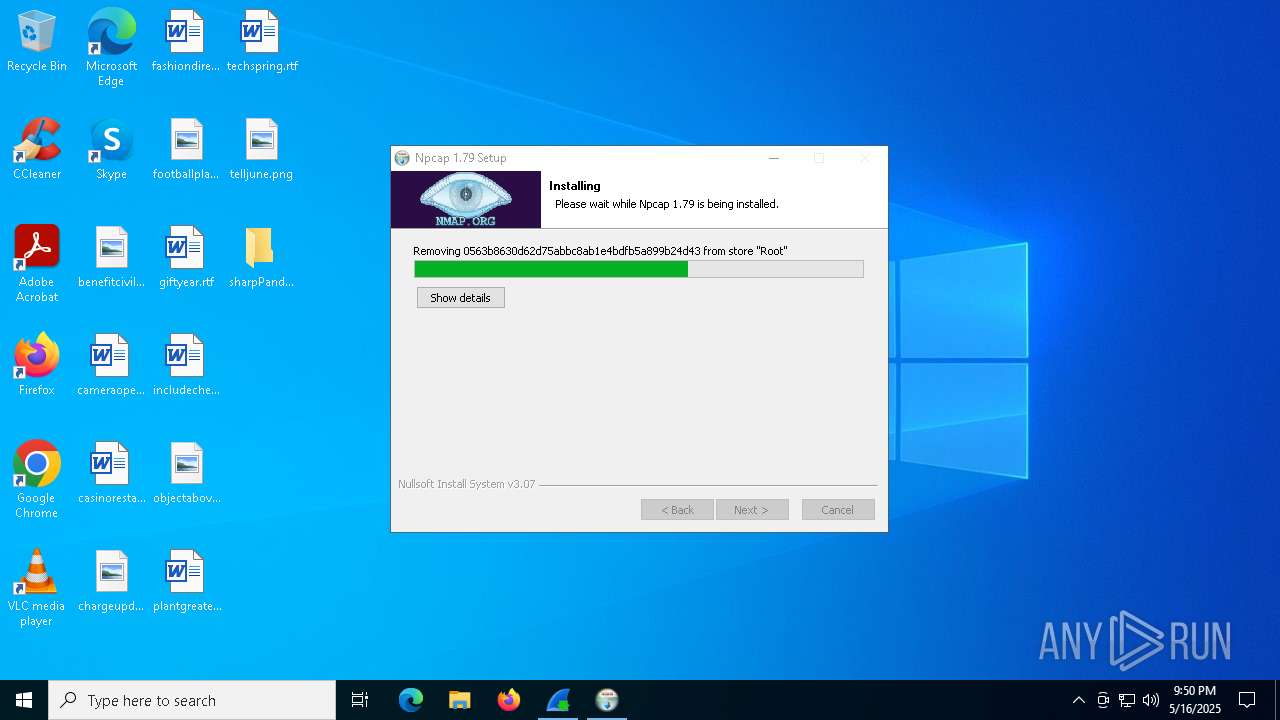
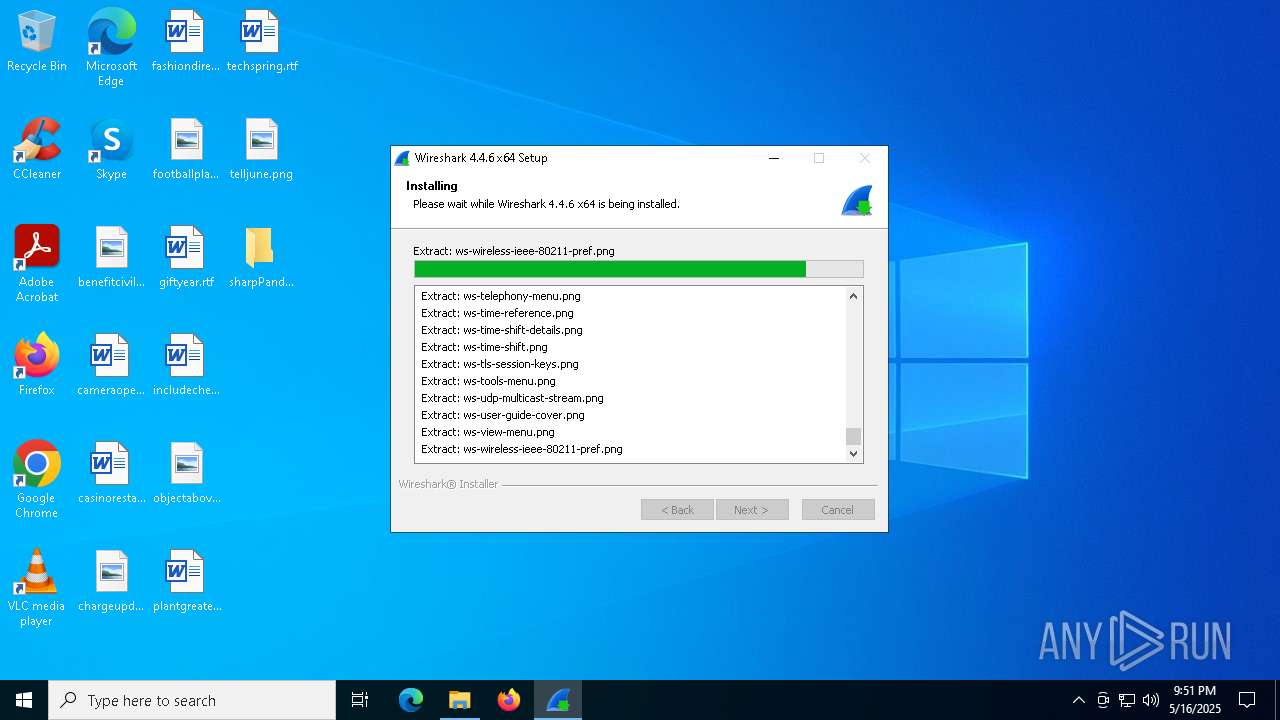
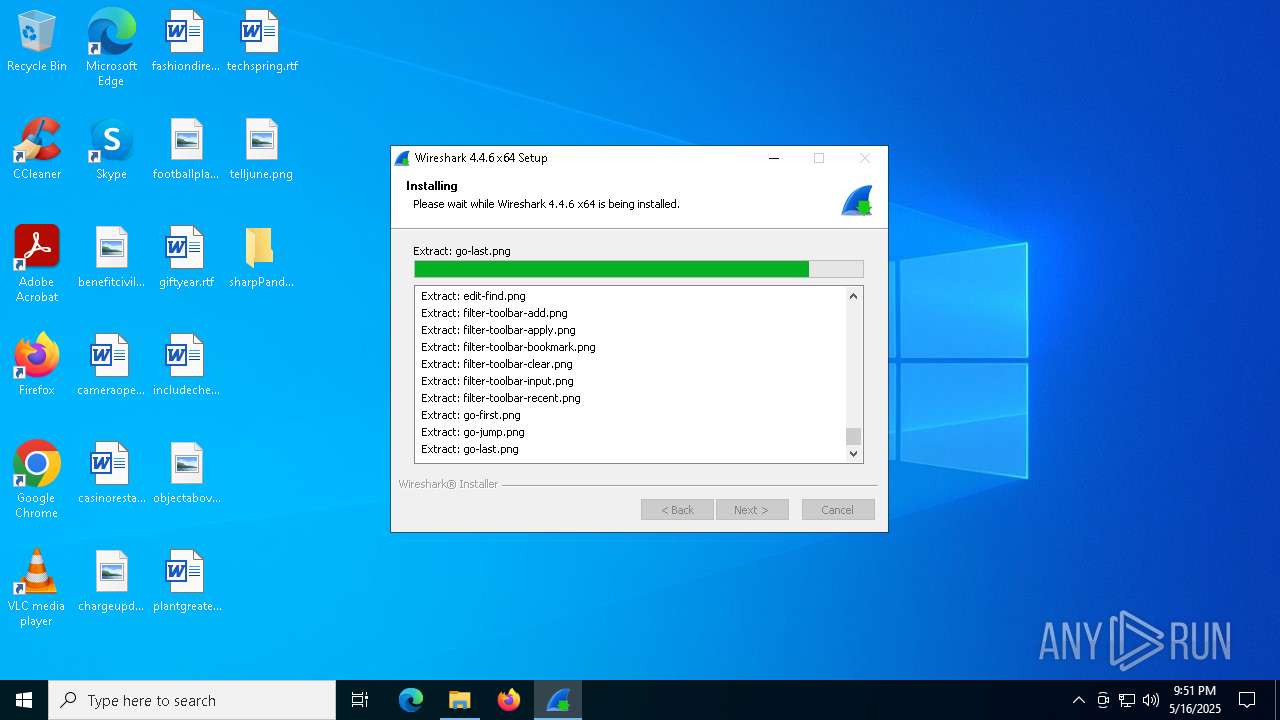
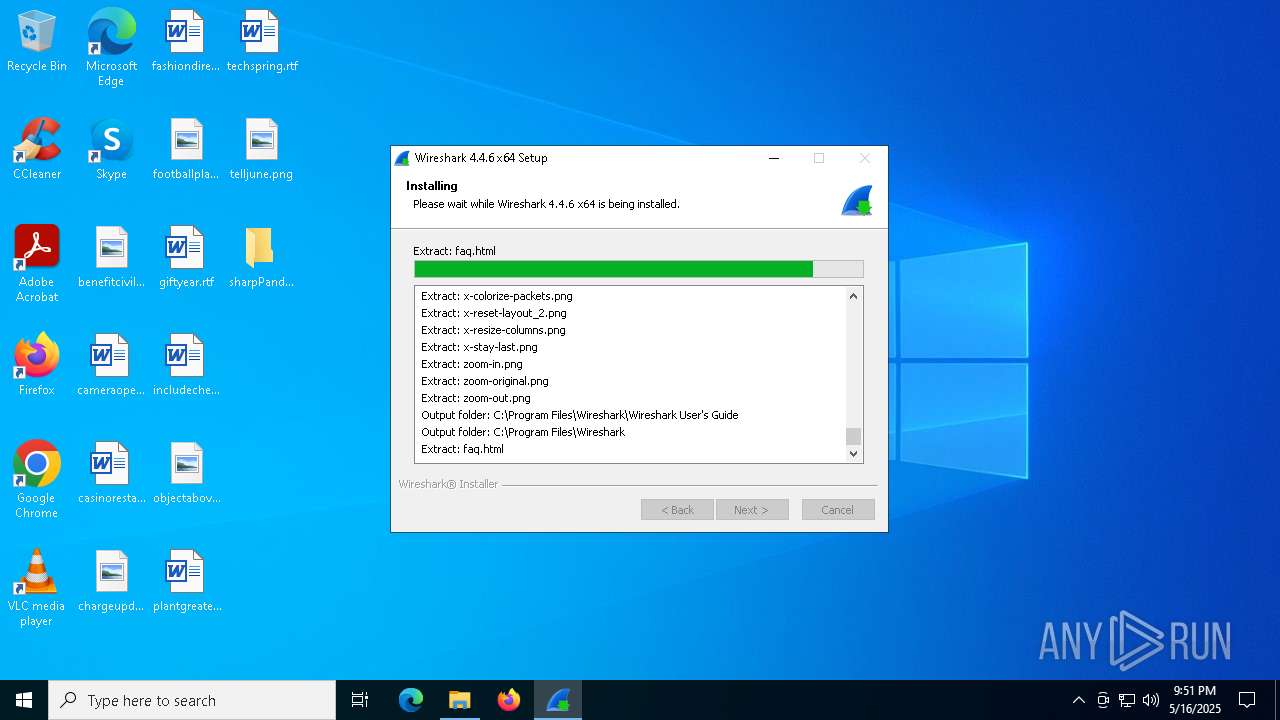
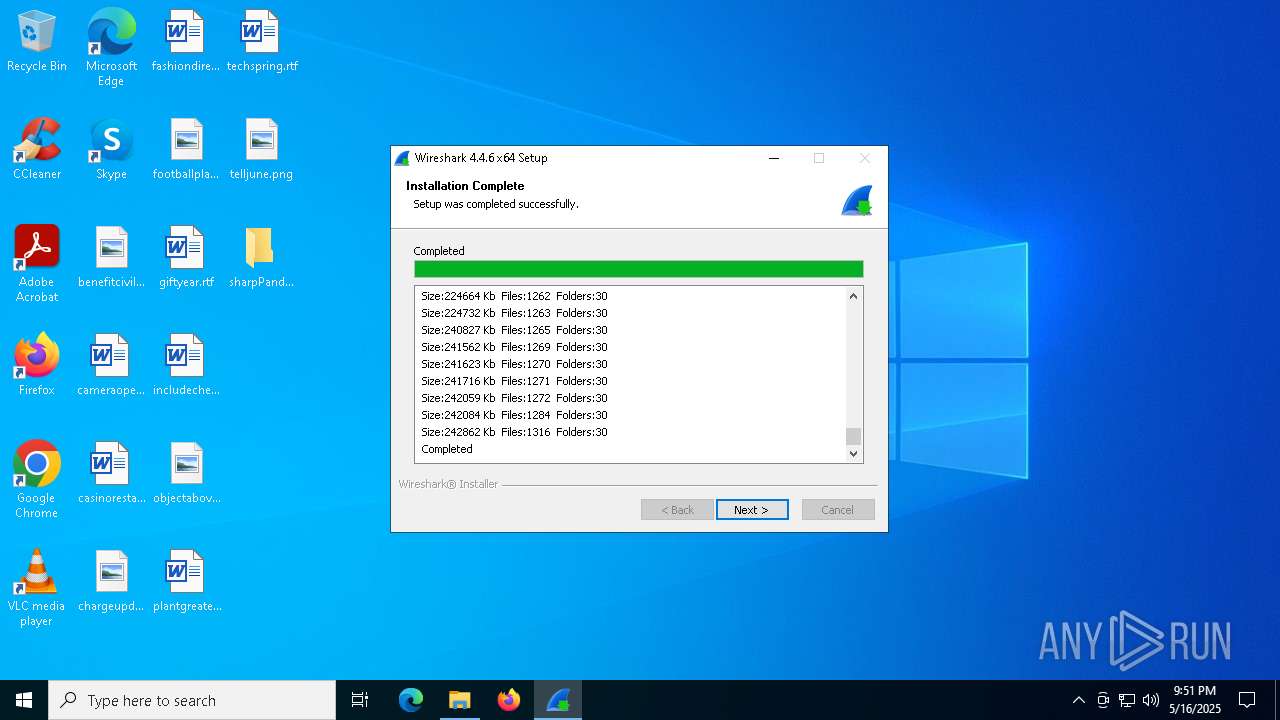
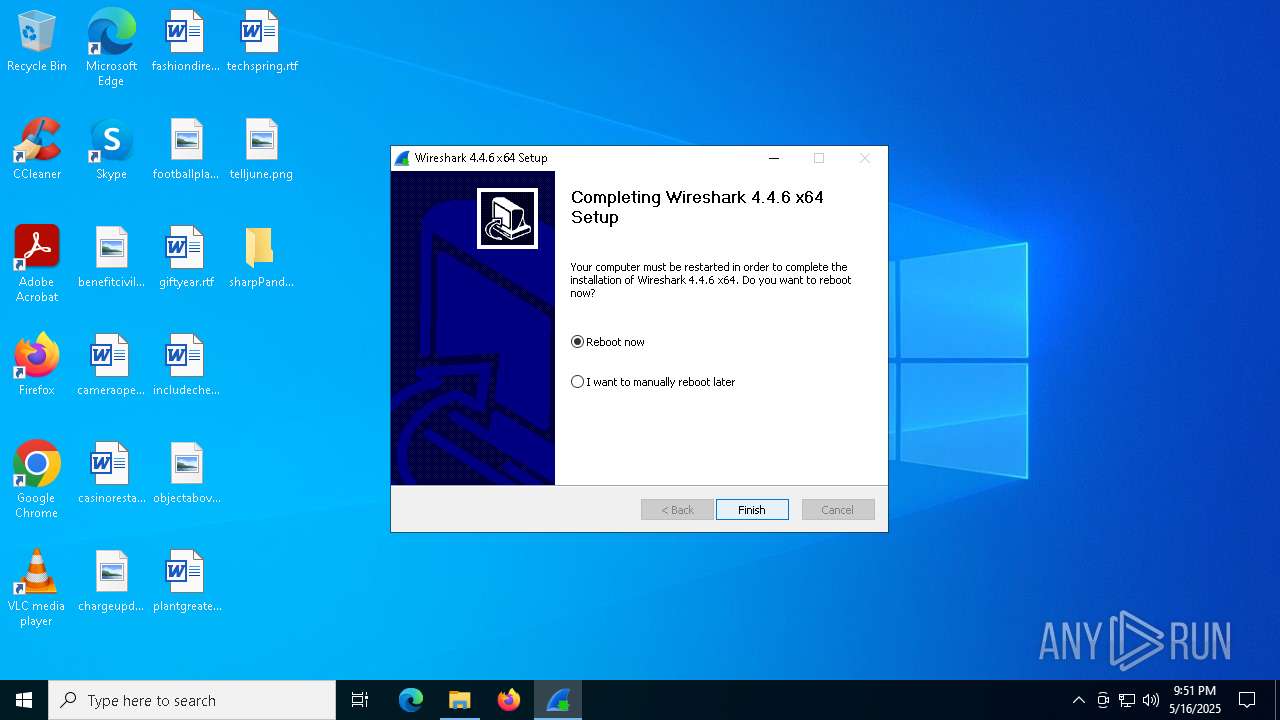
Malware-specific behavior (creating "System.dll" in Temp)
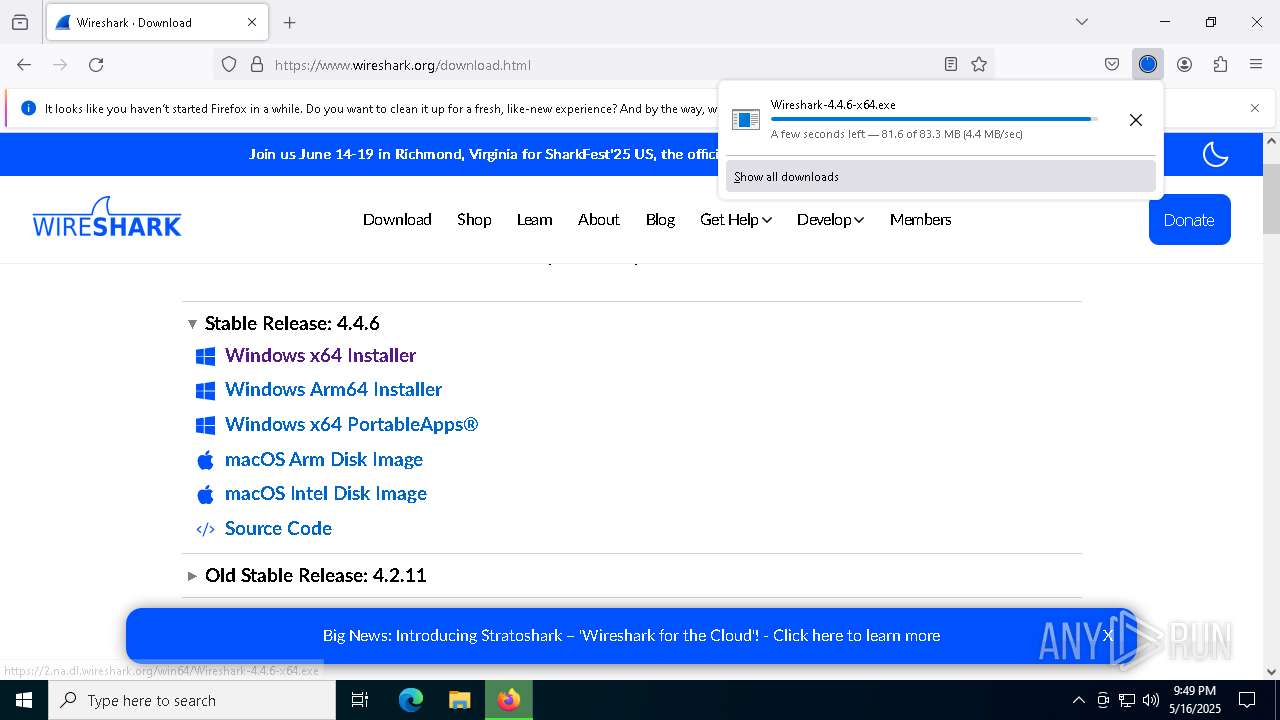
- Wireshark-4.4.6-x64.exe (PID: 4164)
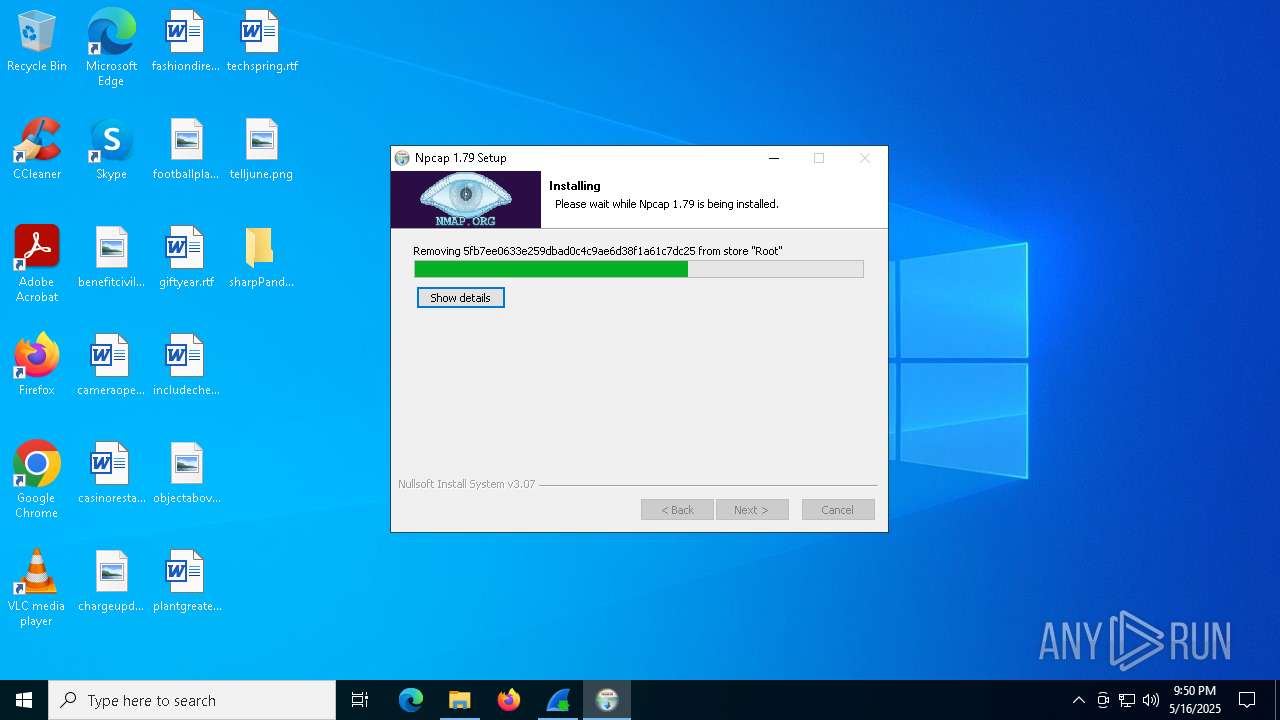
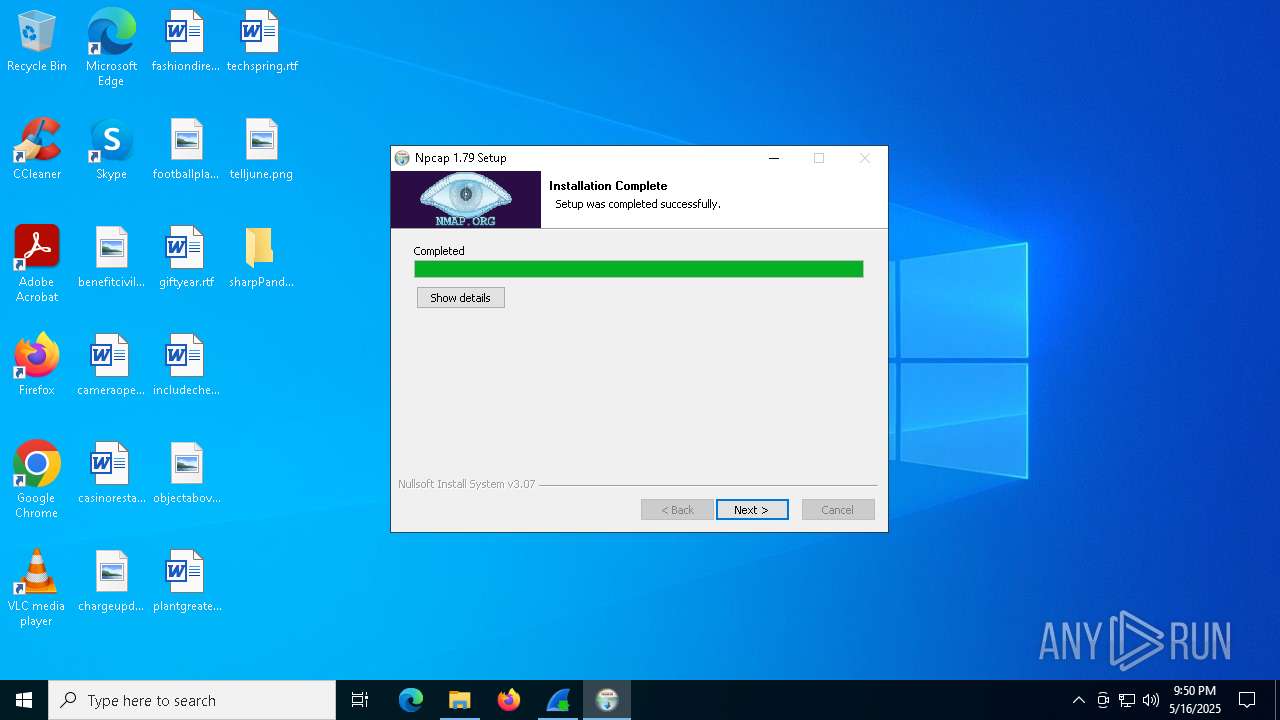
- npcap-1.79.exe (PID: 5416)
The process creates files with name similar to system file names
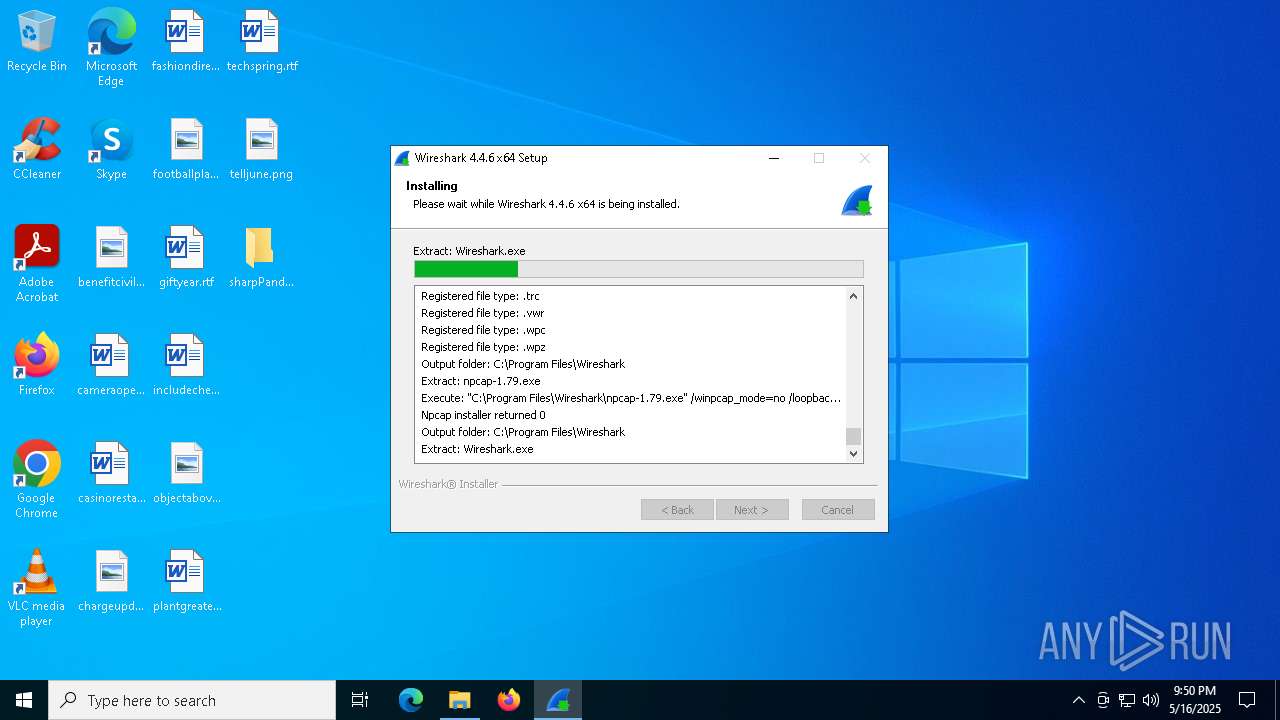
- Wireshark-4.4.6-x64.exe (PID: 4164)
Searches for installed software
- Wireshark-4.4.6-x64.exe (PID: 4164)
Executable content was dropped or overwritten
- Wireshark-4.4.6-x64.exe (PID: 4164)
- vc_redist.x64.exe (PID: 2568)
- vc_redist.x64.exe (PID: 2772)
- VC_redist.x64.exe (PID: 1804)
- VC_redist.x64.exe (PID: 8180)
- VC_redist.x64.exe (PID: 7644)
- npcap-1.79.exe (PID: 5416)
- NPFInstall.exe (PID: 4304)
- drvinst.exe (PID: 2236)
There is functionality for taking screenshot (YARA)
- Wireshark-4.4.6-x64.exe (PID: 4164)
Process drops legitimate windows executable
- Wireshark-4.4.6-x64.exe (PID: 4164)
- vc_redist.x64.exe (PID: 2568)
- vc_redist.x64.exe (PID: 2772)
- msiexec.exe (PID: 5728)
- VC_redist.x64.exe (PID: 1804)
- VC_redist.x64.exe (PID: 8180)
Starts a Microsoft application from unusual location
- vc_redist.x64.exe (PID: 2772)
- VC_redist.x64.exe (PID: 1804)
Starts itself from another location
- vc_redist.x64.exe (PID: 2772)
Executes as Windows Service
- VSSVC.exe (PID: 6256)
The process drops C-runtime libraries
- msiexec.exe (PID: 5728)
Application launched itself
- VC_redist.x64.exe (PID: 3900)
- VC_redist.x64.exe (PID: 7644)
Removes files via Powershell
- powershell.exe (PID: 7224)
- powershell.exe (PID: 5200)
Drops a system driver (possible attempt to evade defenses)
- npcap-1.79.exe (PID: 5416)
- drvinst.exe (PID: 2236)
- NPFInstall.exe (PID: 4304)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 5680)
- powershell.exe (PID: 7224)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 968)
The process hide an interactive prompt from the user
- npcap-1.79.exe (PID: 5416)
Starts POWERSHELL.EXE for commands execution
- npcap-1.79.exe (PID: 5416)
The process bypasses the loading of PowerShell profile settings
- npcap-1.79.exe (PID: 5416)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4880)
- firefox.exe (PID: 7688)
- msiexec.exe (PID: 5728)
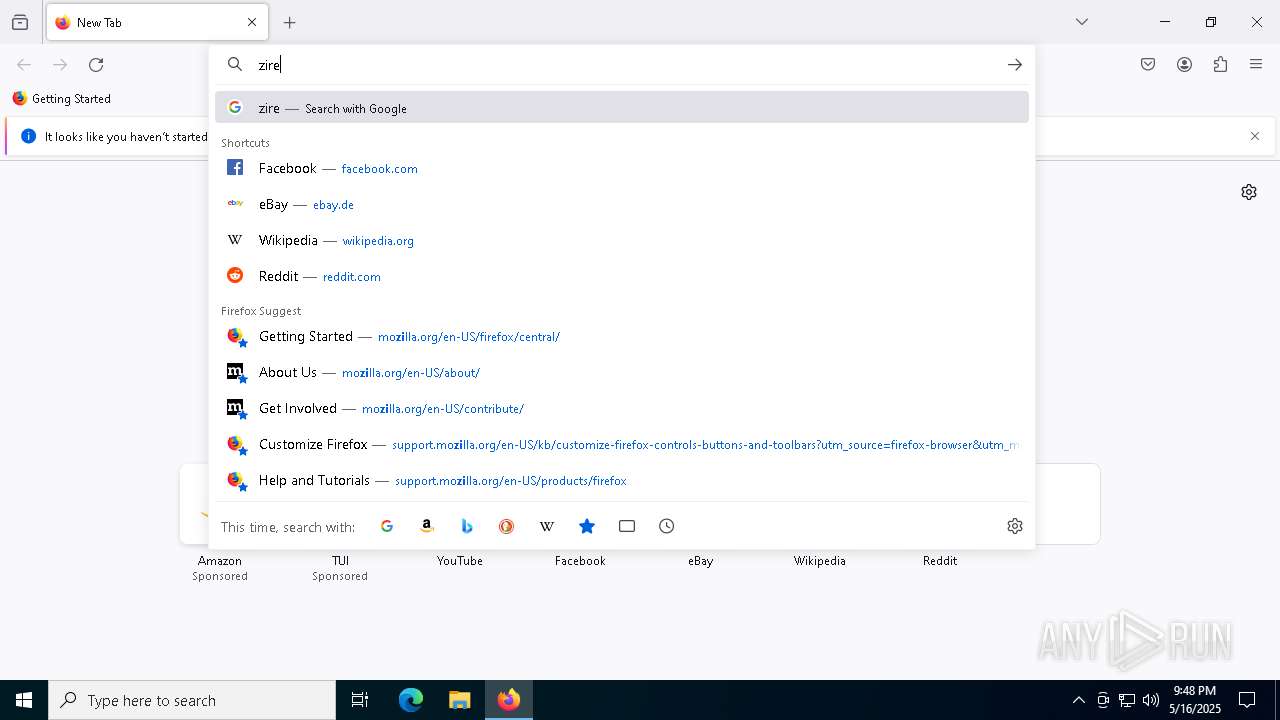
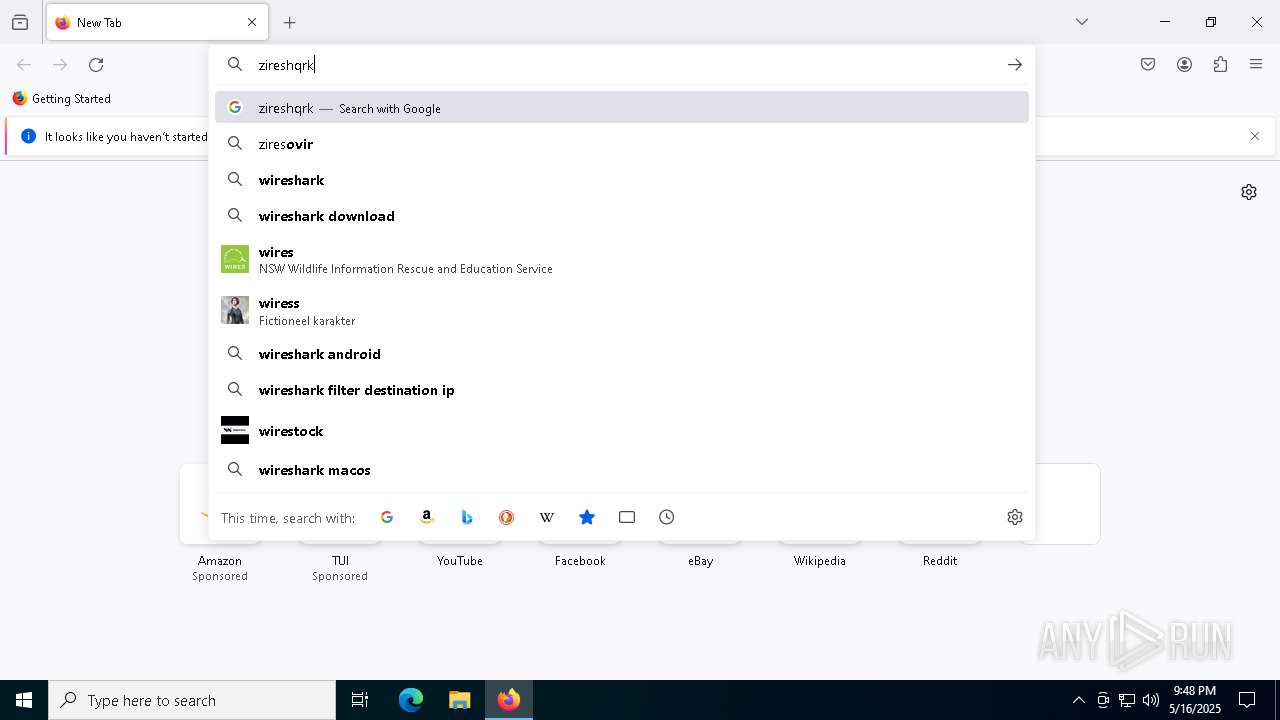
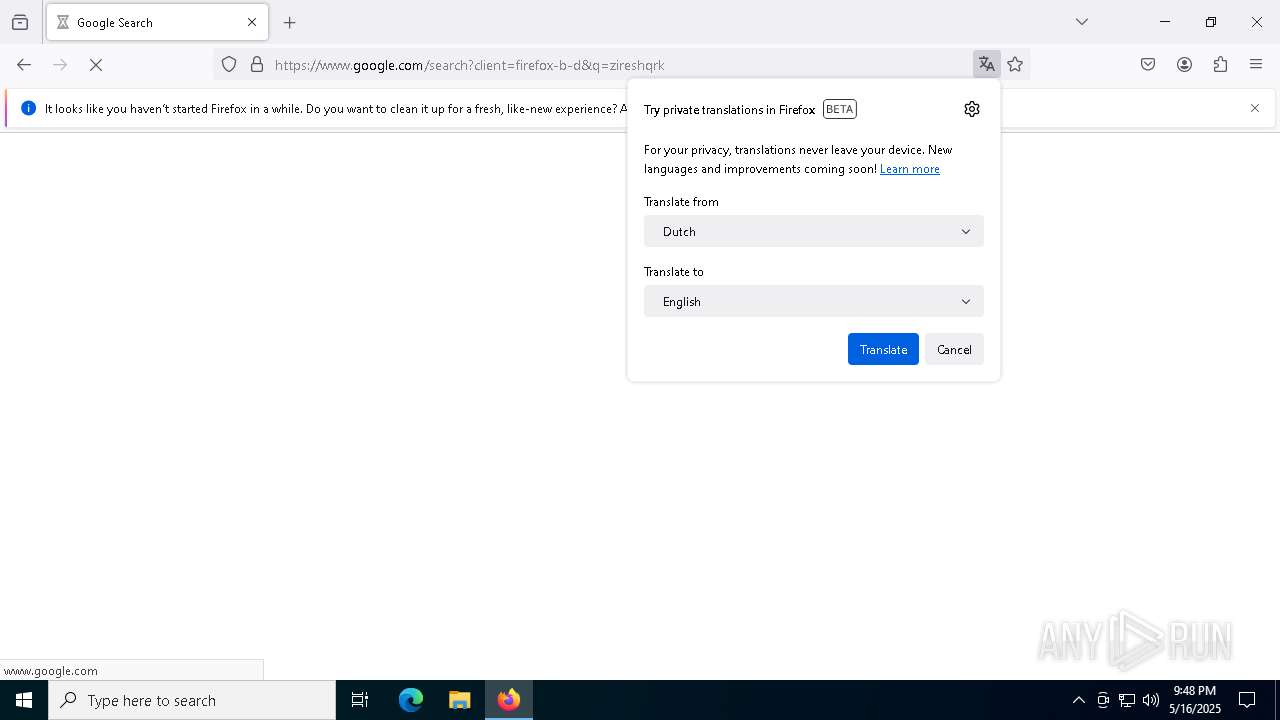
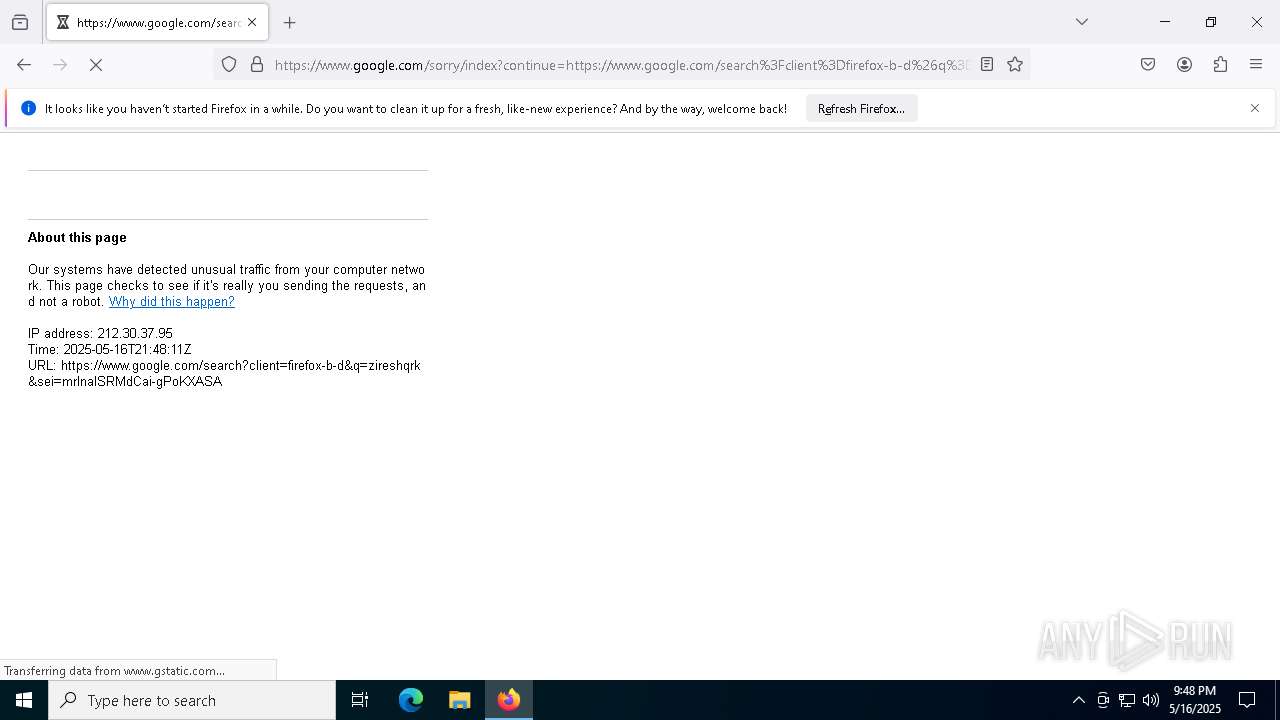
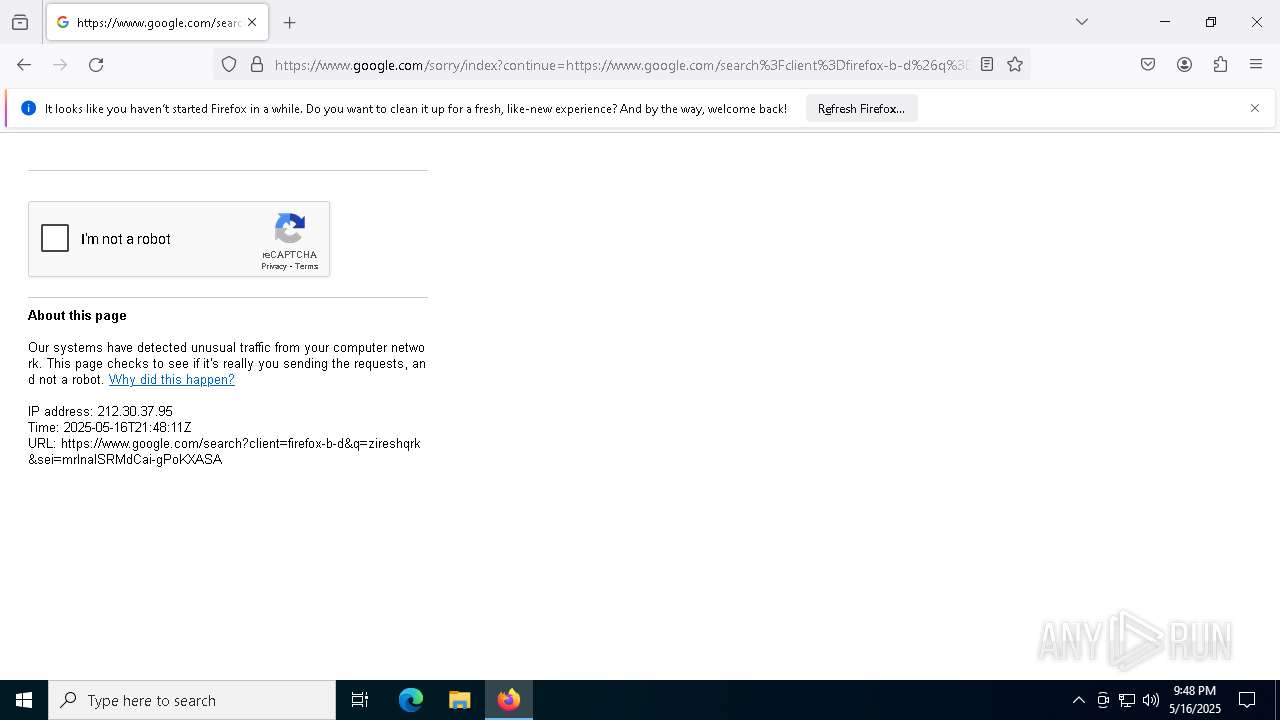
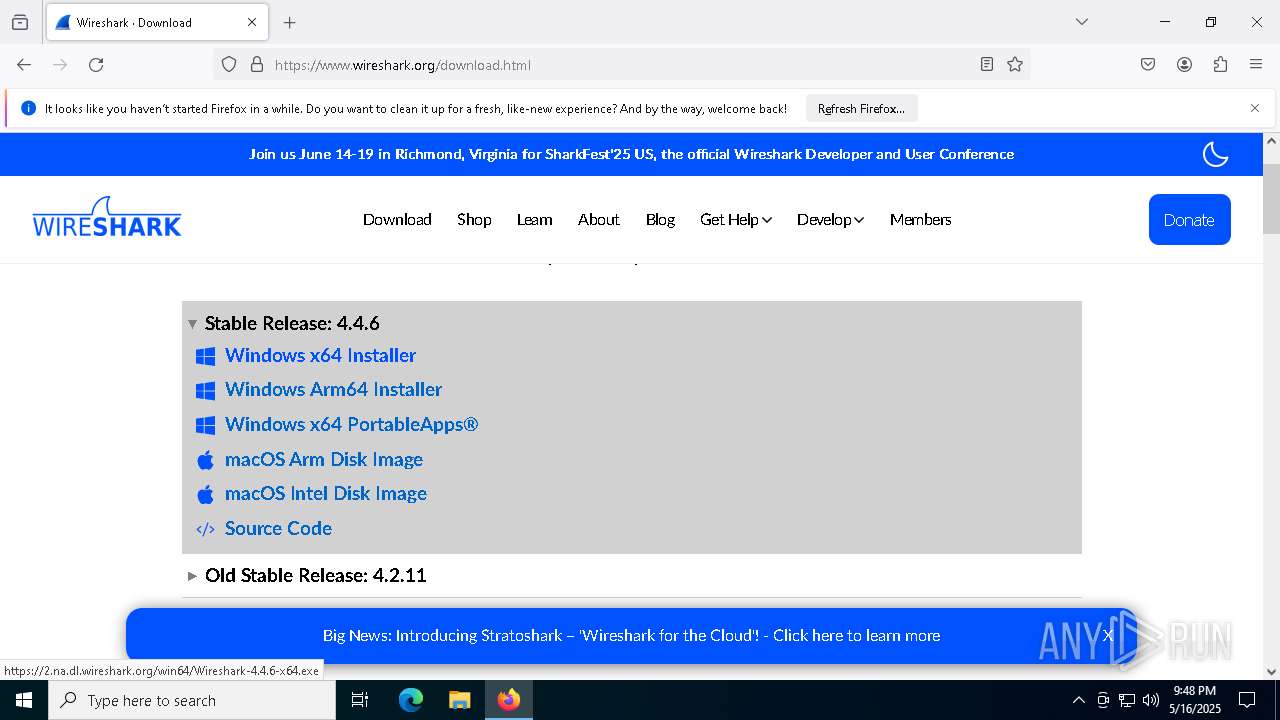
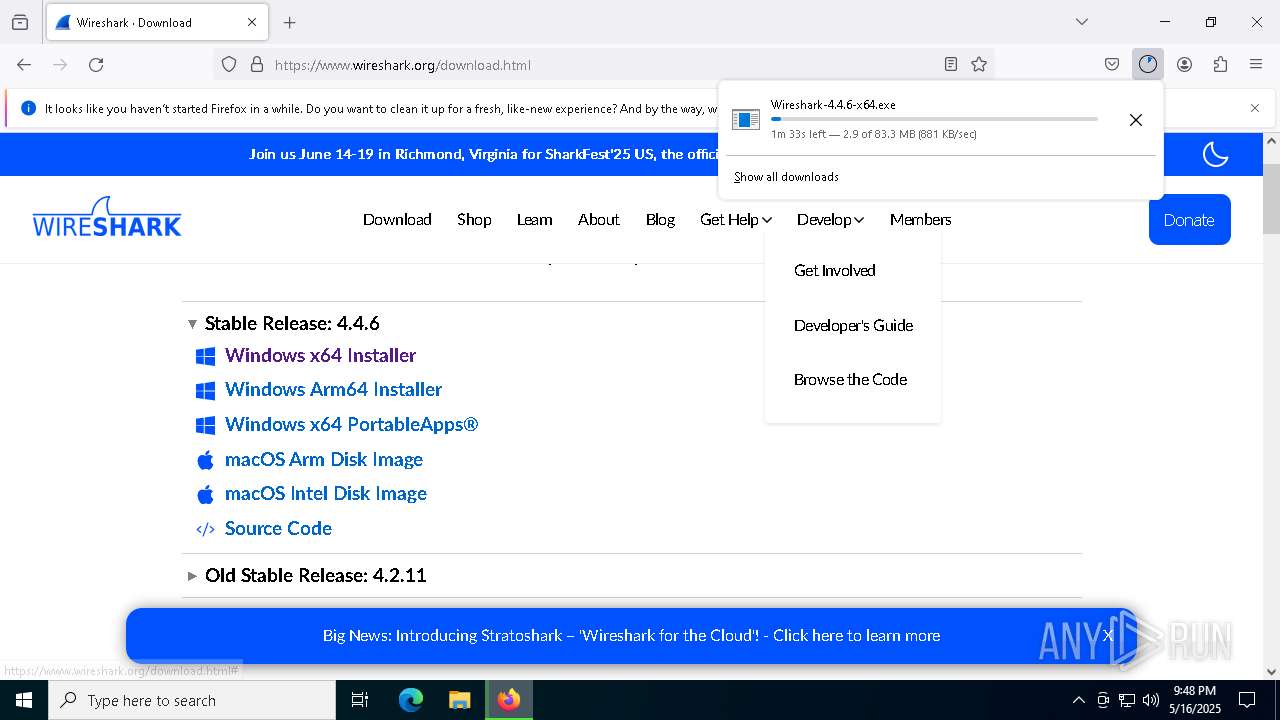
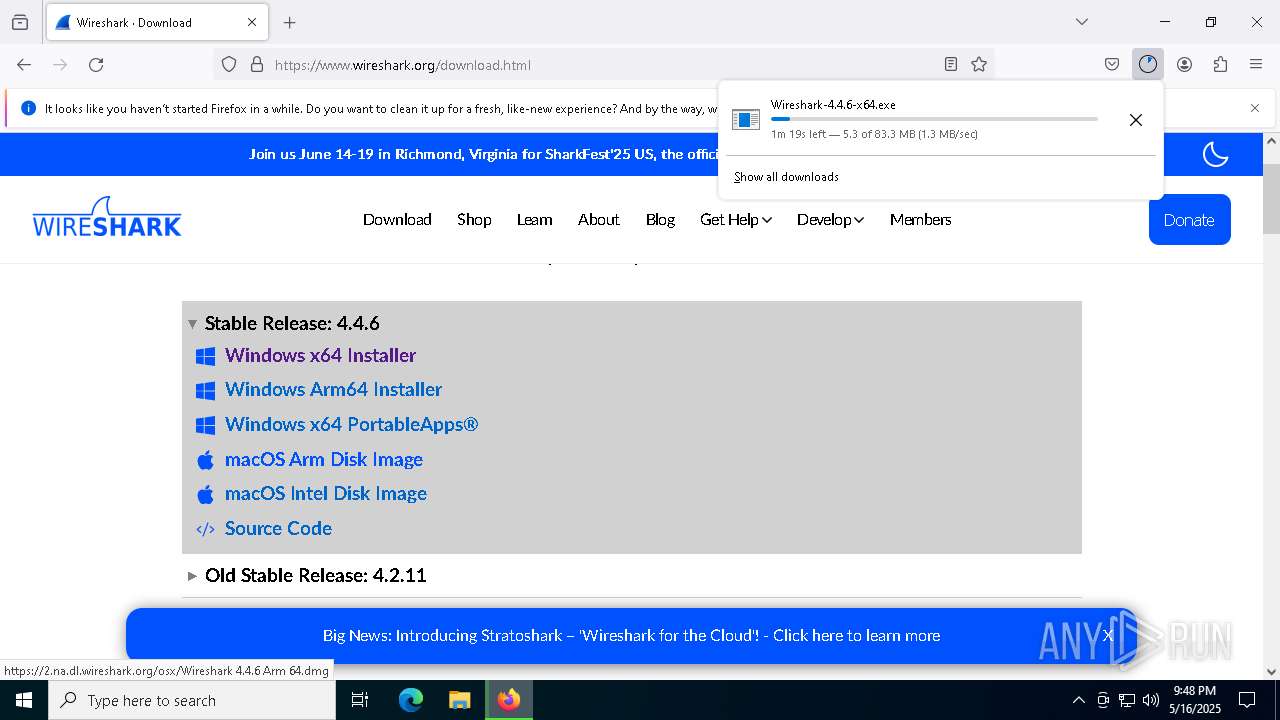
Manual execution by a user
- firefox.exe (PID: 7668)
Application launched itself
- firefox.exe (PID: 7668)
- firefox.exe (PID: 7688)
Reads the software policy settings
- slui.exe (PID: 7288)
Checks supported languages
- Wireshark-4.4.6-x64.exe (PID: 4164)
WIRESHARK mutex has been found
- Wireshark-4.4.6-x64.exe (PID: 4164)
Create files in a temporary directory
- Wireshark-4.4.6-x64.exe (PID: 4164)
Reads the computer name
- Wireshark-4.4.6-x64.exe (PID: 4164)
The sample compiled with english language support
- Wireshark-4.4.6-x64.exe (PID: 4164)
- vc_redist.x64.exe (PID: 2568)
- vc_redist.x64.exe (PID: 2772)
- msiexec.exe (PID: 5728)
- VC_redist.x64.exe (PID: 7644)
- VC_redist.x64.exe (PID: 1804)
- VC_redist.x64.exe (PID: 8180)
- npcap-1.79.exe (PID: 5416)
Manages system restore points
- SrTasks.exe (PID: 7512)
Returns hidden items found within a container (POWERSHELL)
- conhost.exe (PID: 1240)
- conhost.exe (PID: 4008)
- conhost.exe (PID: 7968)
- conhost.exe (PID: 7584)
- conhost.exe (PID: 2152)
- conhost.exe (PID: 4868)
- conhost.exe (PID: 5020)
- conhost.exe (PID: 1244)
- conhost.exe (PID: 7288)
- conhost.exe (PID: 8148)
- conhost.exe (PID: 2288)
- conhost.exe (PID: 2692)
- conhost.exe (PID: 5056)
- conhost.exe (PID: 5548)
- powershell.exe (PID: 1040)
- conhost.exe (PID: 6872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 100656 |
| UncompressedSize: | 311808 |
| OperatingSystem: | Win32 |
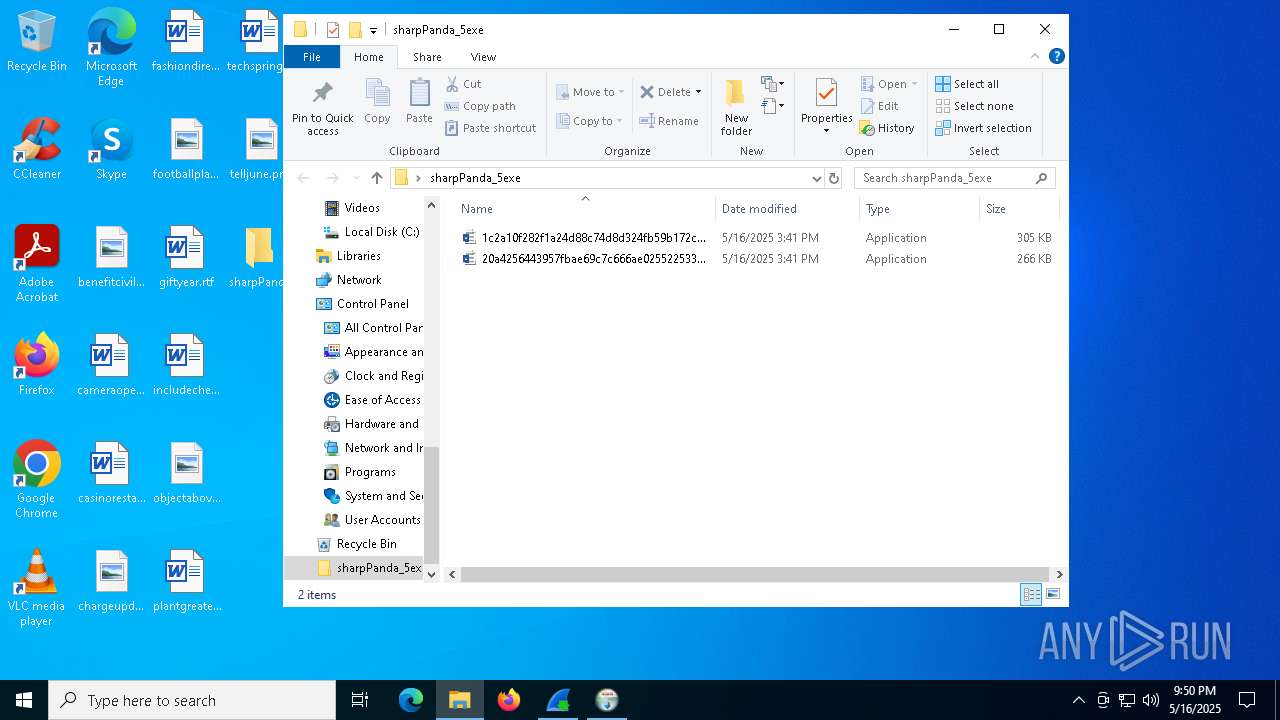
| ArchivedFileName: | sharpPanda_5exe/1c2a10f282f1a24d88c74d8d324fb59b172cee4ee2e3e3996d9a62ba979812a6.exe |
Total processes
212
Monitored processes
71
Malicious processes
4
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2868 -childID 2 -isForBrowser -prefsHandle 2880 -prefMapHandle 2876 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {3fbb6a49-911d-41ad-995d-335295d16aa2} 7688 "\\.\pipe\gecko-crash-server-pipe.7688" 25900d57850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 968 | powershell.exe -NoProfile -WindowStyle Hidden -NonInteractive -Command "Get-ChildItem Cert:\LocalMachine\Root | Where-Object {$_.Thumbprint -eq '5fb7ee0633e259dbad0c4c9ae6d38f1a61c7dc25'} | Sort-Object -Descending -Property FriendlyName | Select-Object -Skip 1 | Remove-Item" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | npcap-1.79.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | powershell.exe -NoProfile -WindowStyle Hidden -NonInteractive -Command "ScheduledTasks\Register-ScheduledTask -Force -TaskName 'npcapwatchdog' -Description 'Ensure Npcap service is configured to start at boot' -Action (ScheduledTasks\New-ScheduledTaskAction -Execute 'C:\Program Files\Npcap\CheckStatus.bat') -Principal (ScheduledTasks\New-ScheduledTaskPrincipal -UserId 'SYSTEM' -LogonType ServiceAccount) -Trigger (ScheduledTasks\New-ScheduledTaskTrigger -AtStartup) -Settings (ScheduledTasks\New-ScheduledTaskSettingsSet -AllowStartIfOnBatteries -Compatibility Win8)" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | npcap-1.79.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2808 -childID 6 -isForBrowser -prefsHandle 4700 -prefMapHandle 4824 -prefsLen 31366 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {f4cccc07-e874-441c-8c8a-40de1c4d1f5c} 7688 "\\.\pipe\gecko-crash-server-pipe.7688" 25901971690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | "C:\WINDOWS\Temp\{C36ED5E3-911A-4CE6-A3DE-95A7060AB40F}\.be\VC_redist.x64.exe" -q -burn.elevated BurnPipe.{19FAED53-6901-4C5D-9C64-34BCA716A741} {1FFE3583-3C1A-4851-BF37-188F0657EF93} 2772 | C:\Windows\Temp\{C36ED5E3-911A-4CE6-A3DE-95A7060AB40F}\.be\VC_redist.x64.exe | vc_redist.x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.40.33816 Exit code: 3010 Version: 14.40.33816.0 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5068 -childID 8 -isForBrowser -prefsHandle 4828 -prefMapHandle 6076 -prefsLen 31687 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {32a0dc22-9137-4d15-8db4-c87306af2437} 7688 "\\.\pipe\gecko-crash-server-pipe.7688" 259034e0d90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2152 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
81 702
Read events
80 572
Write events
730
Delete events
400
Modification events
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sharpPanda_5exe.rar | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7688) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
Executable files
210
Suspicious files
385
Text files
1 270
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7688 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7688 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 7688 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7688 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 7688 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7688 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7688 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7688 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7688 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7688 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:AFE2158CBEF7796834E4A9D61BBCA6DA | SHA256:24710317535D27FB02CFBC738B706CA1E6D18044FECCE60F5FB0B62C1B470C75 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
73
TCP/UDP connections
174
DNS requests
183
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7688 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7688 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7688 | firefox.exe | POST | 200 | 184.24.77.46:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7688 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
7688 | firefox.exe | POST | 200 | 184.24.77.46:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7688 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7688 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7688 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
7688 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
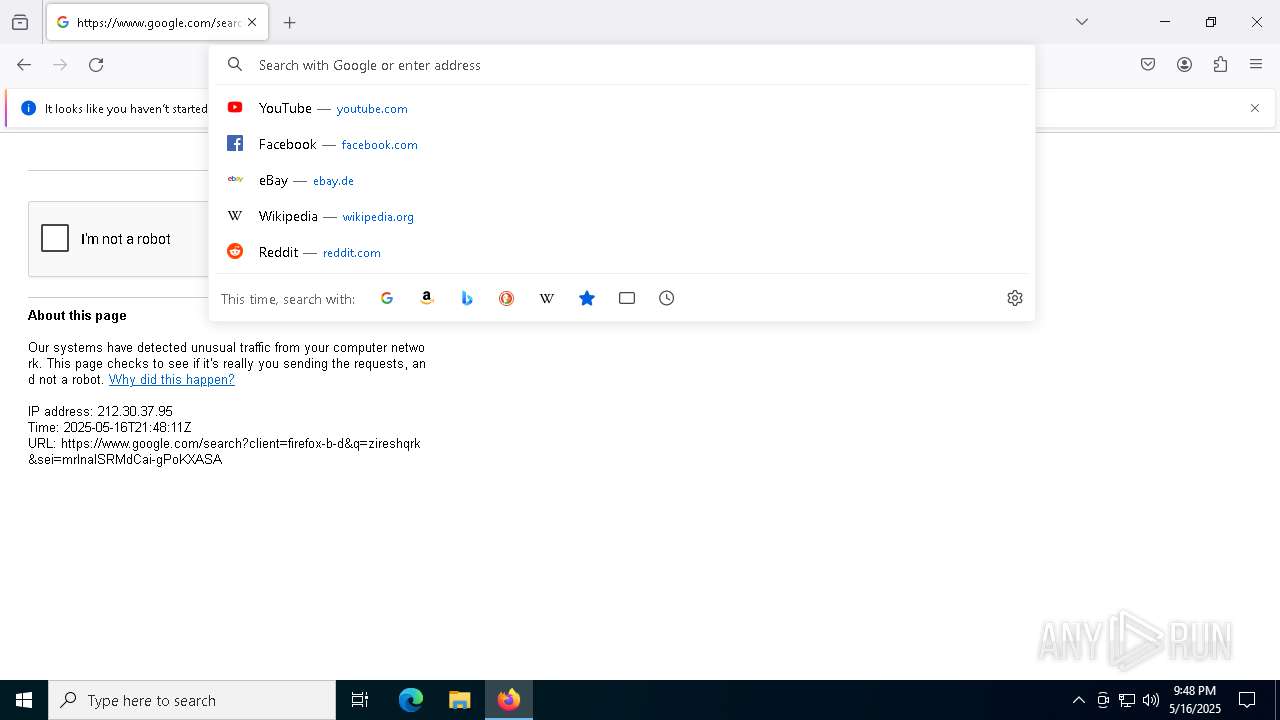
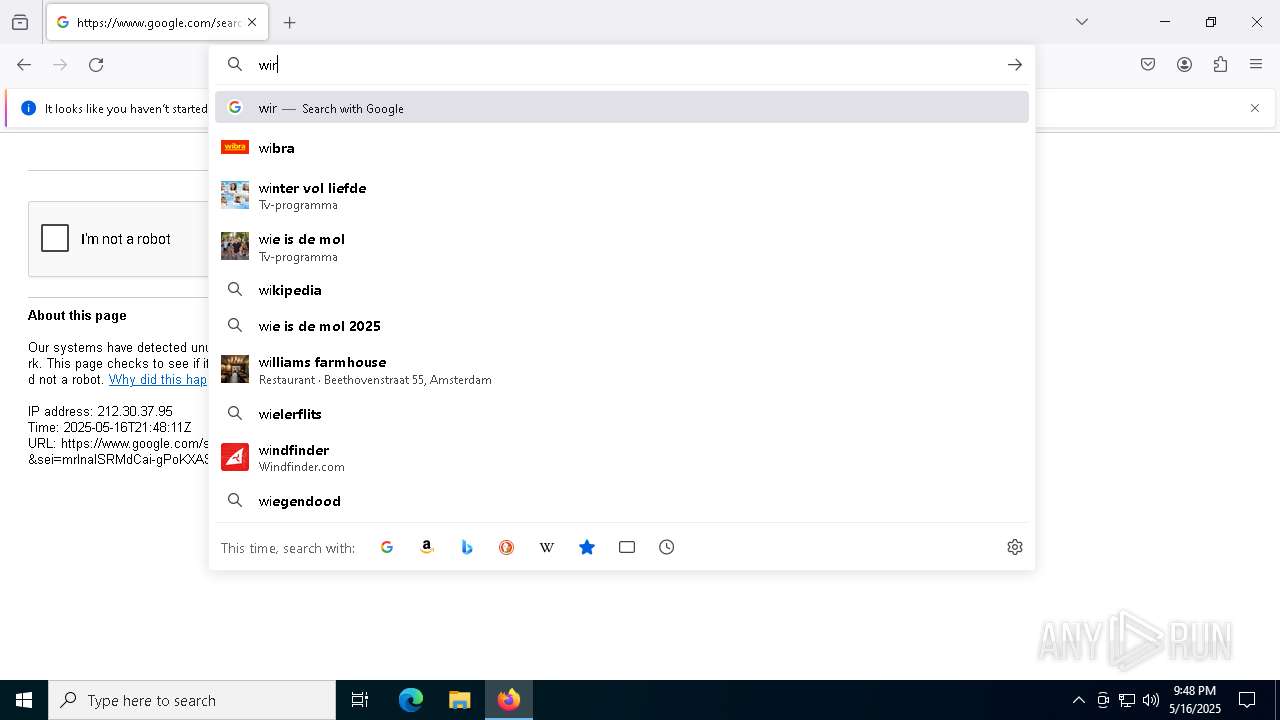
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|