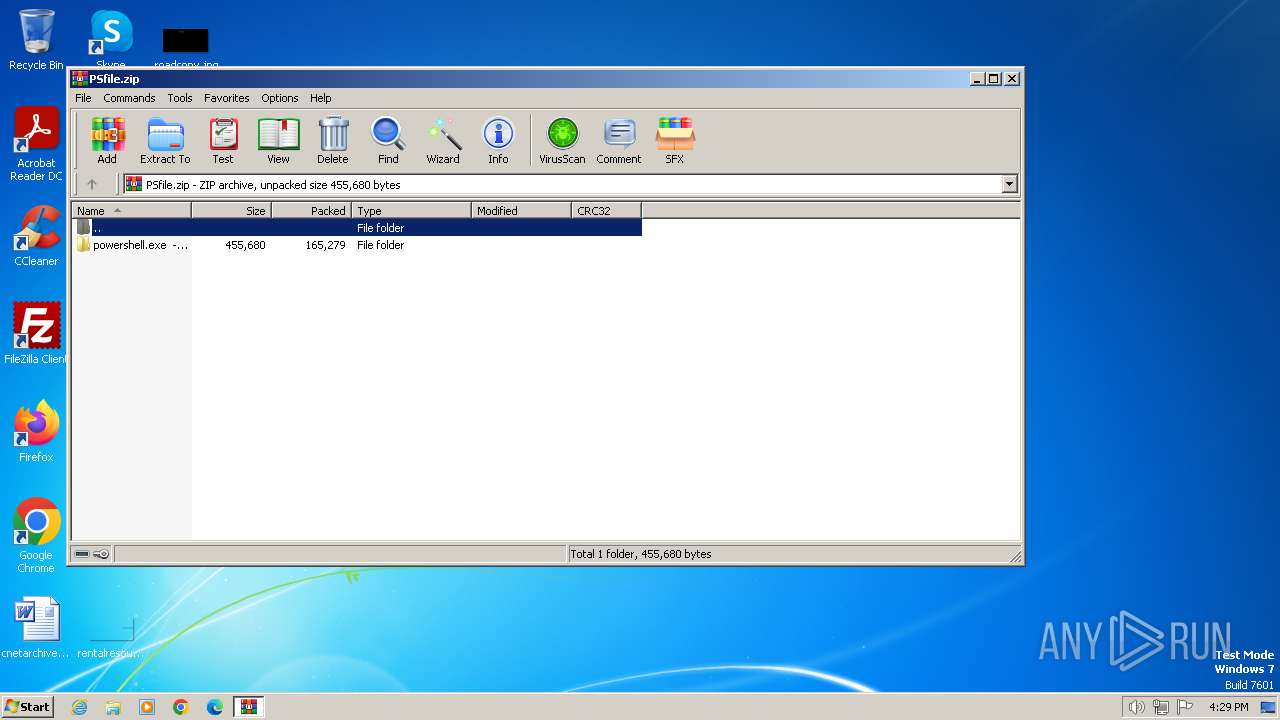
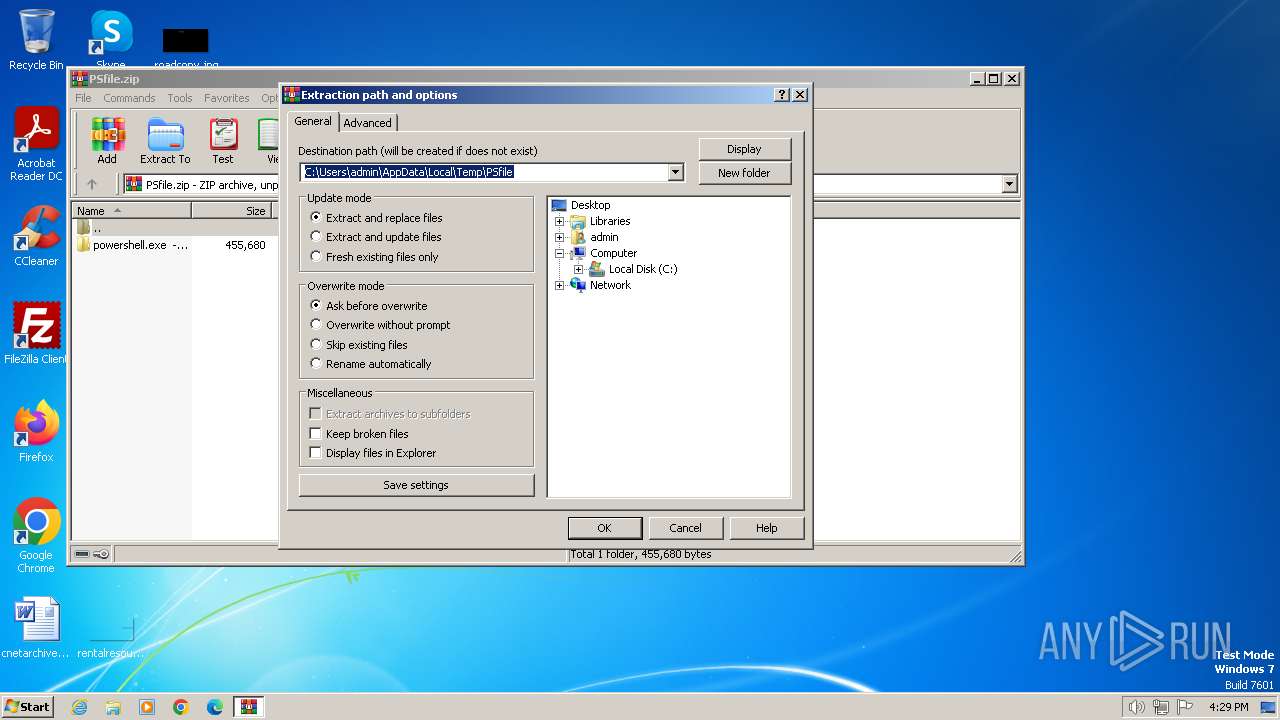
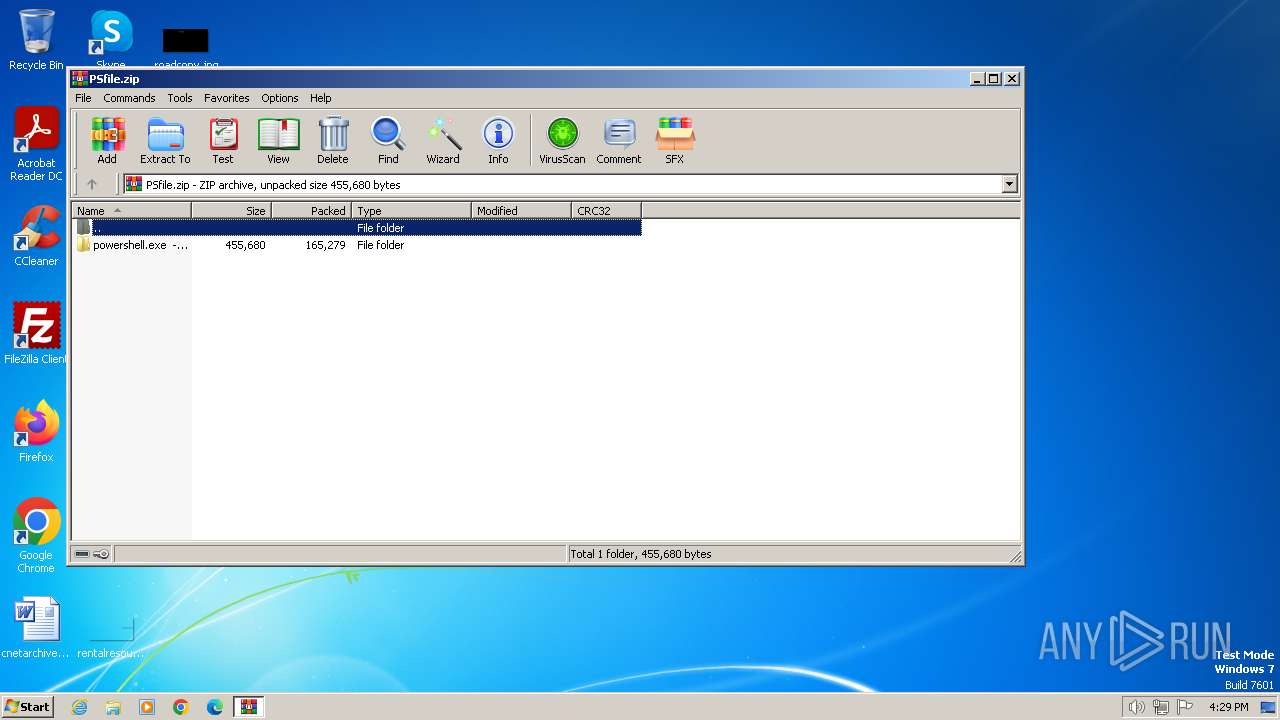
| File name: | PSfile.zip |
| Full analysis: | https://app.any.run/tasks/b2d84683-980a-4266-975b-5af178c29122 |
| Verdict: | Malicious activity |
| Analysis date: | April 24, 2024, 15:29:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 3CA11275FC42FA817DDC8A84054674FD |
| SHA1: | AE4BF6F6EE3B63E2F0CE144AA367417A00B08936 |
| SHA256: | C4DD6551EF549195599BFD8D93B94666D0A9B766EA9CFB753F933ACD09A84B1A |
| SSDEEP: | 6144:/+u4/jeepN/+UbDS0N0o+PkMTPnu/WFeBVw:r4/KCfS0Psjvu/WYvw |
MALICIOUS
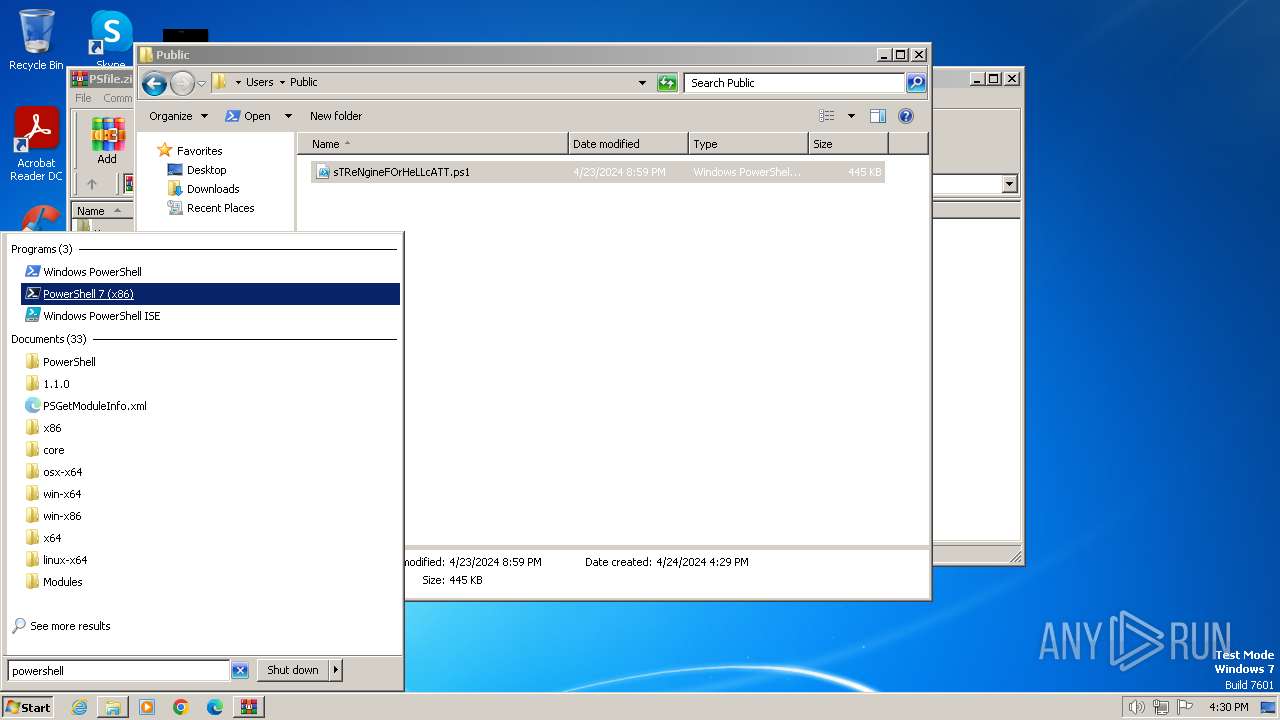
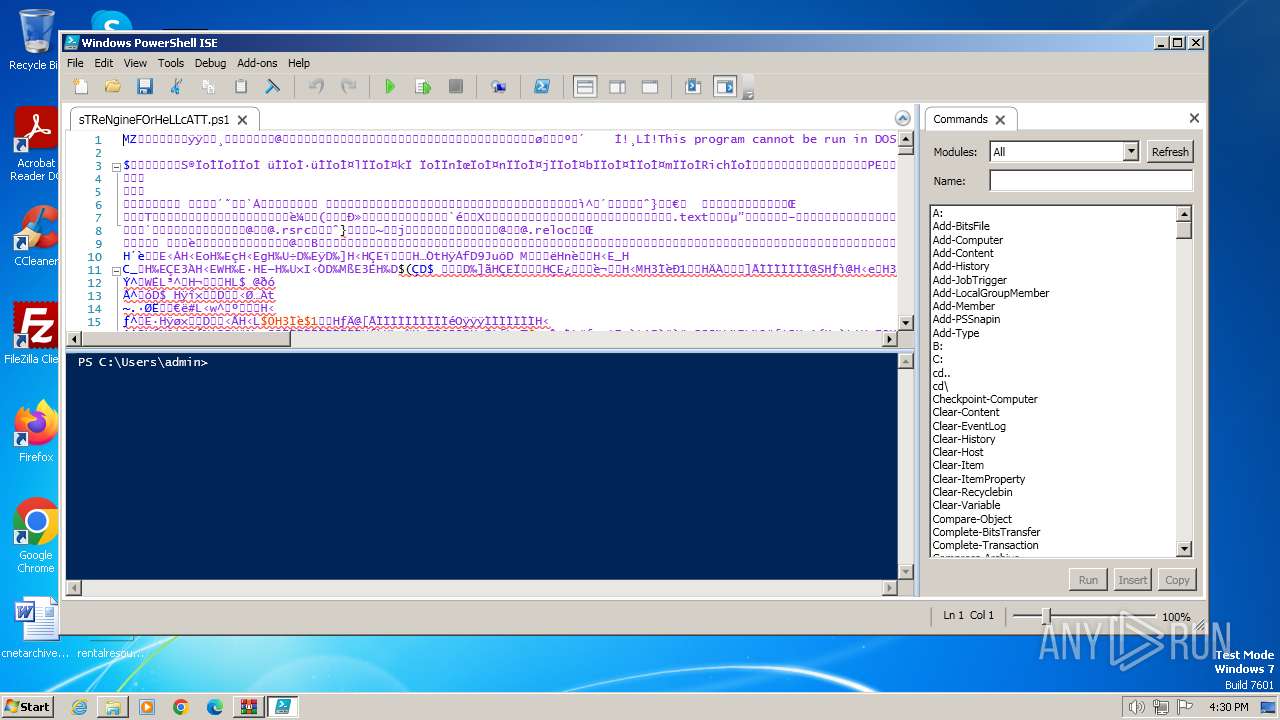
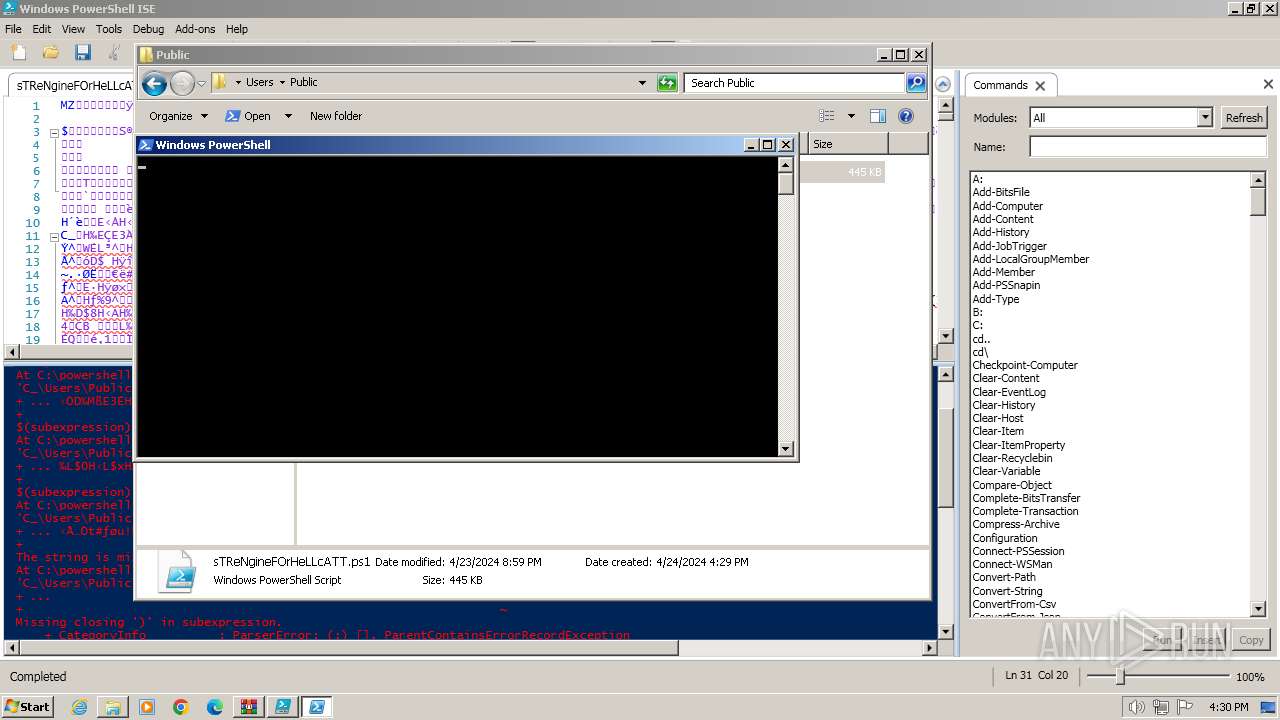
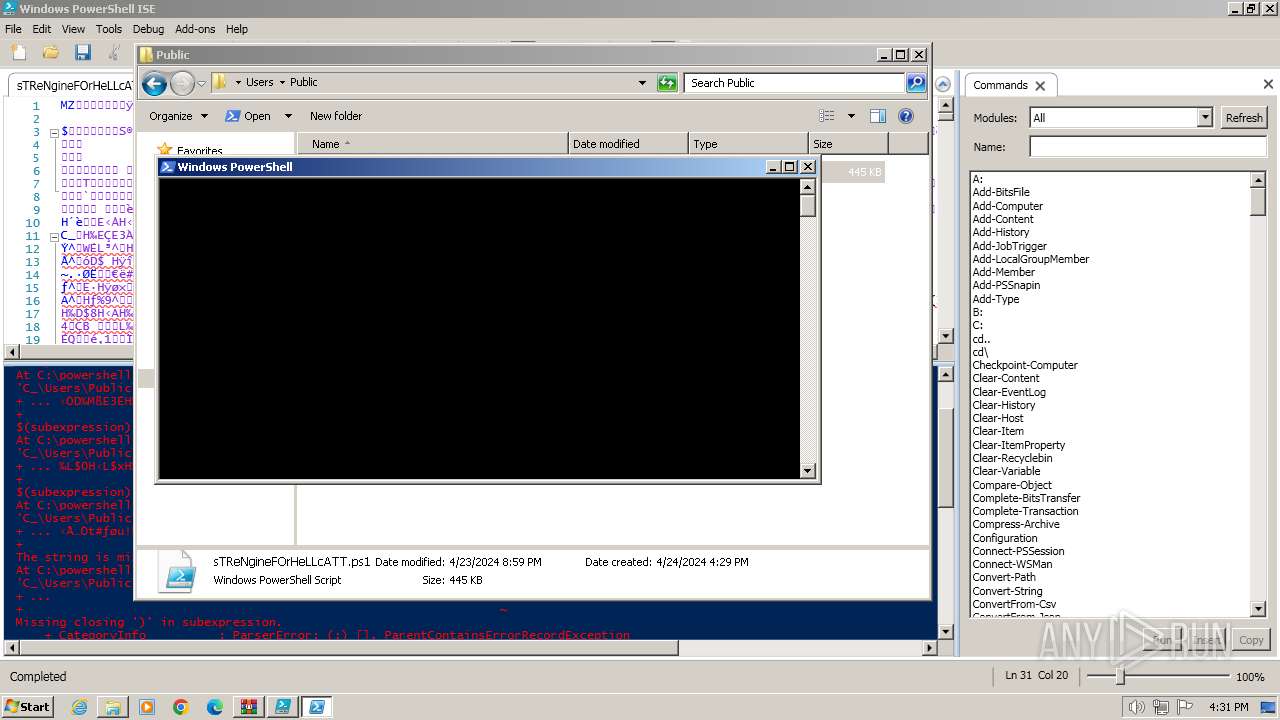
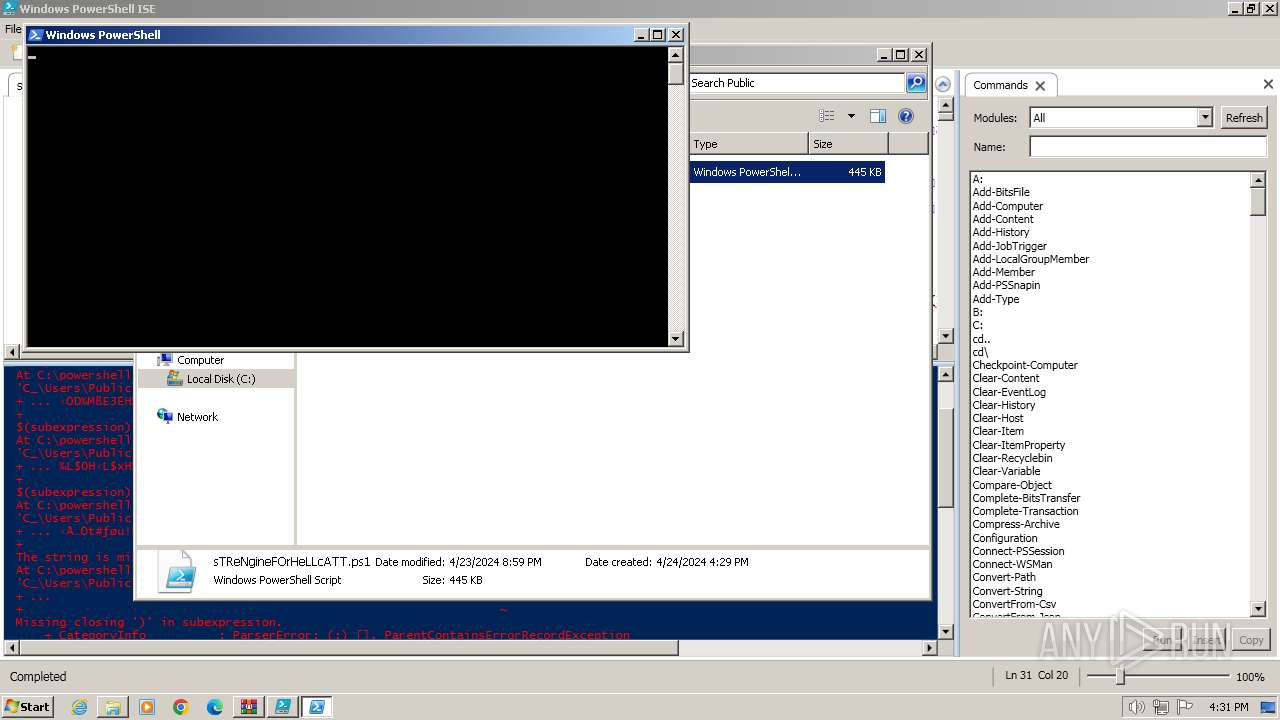
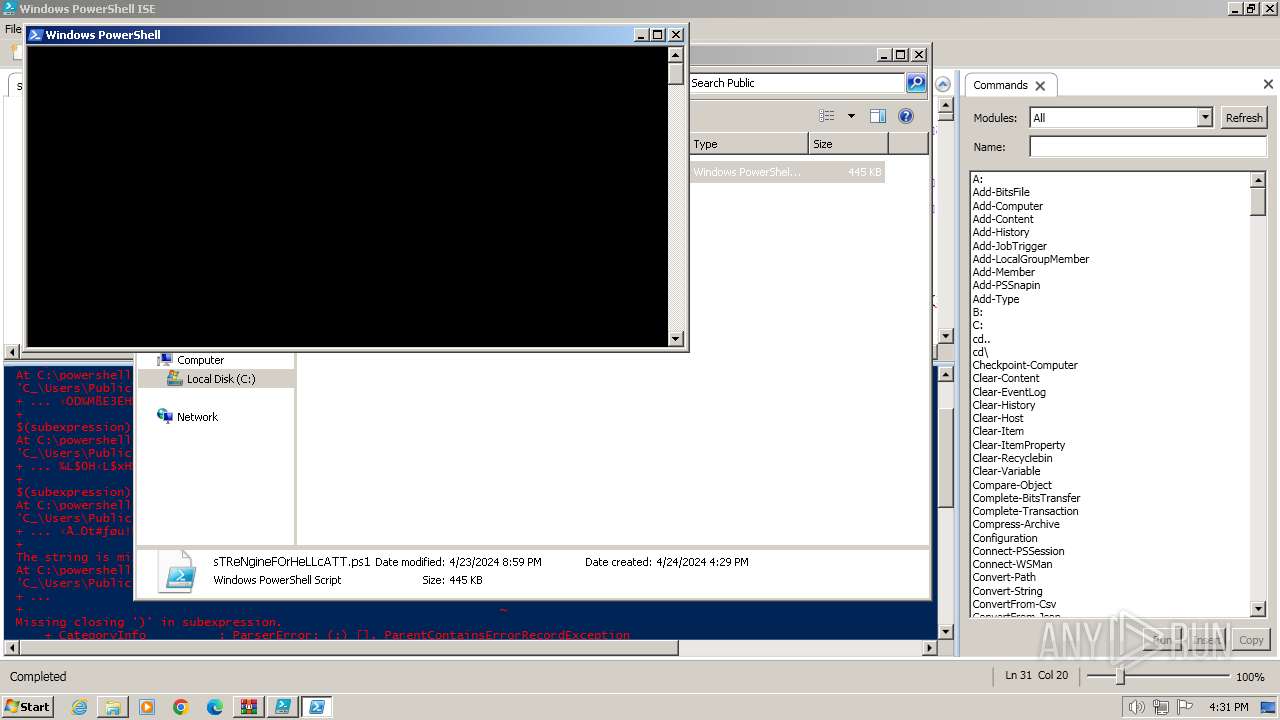
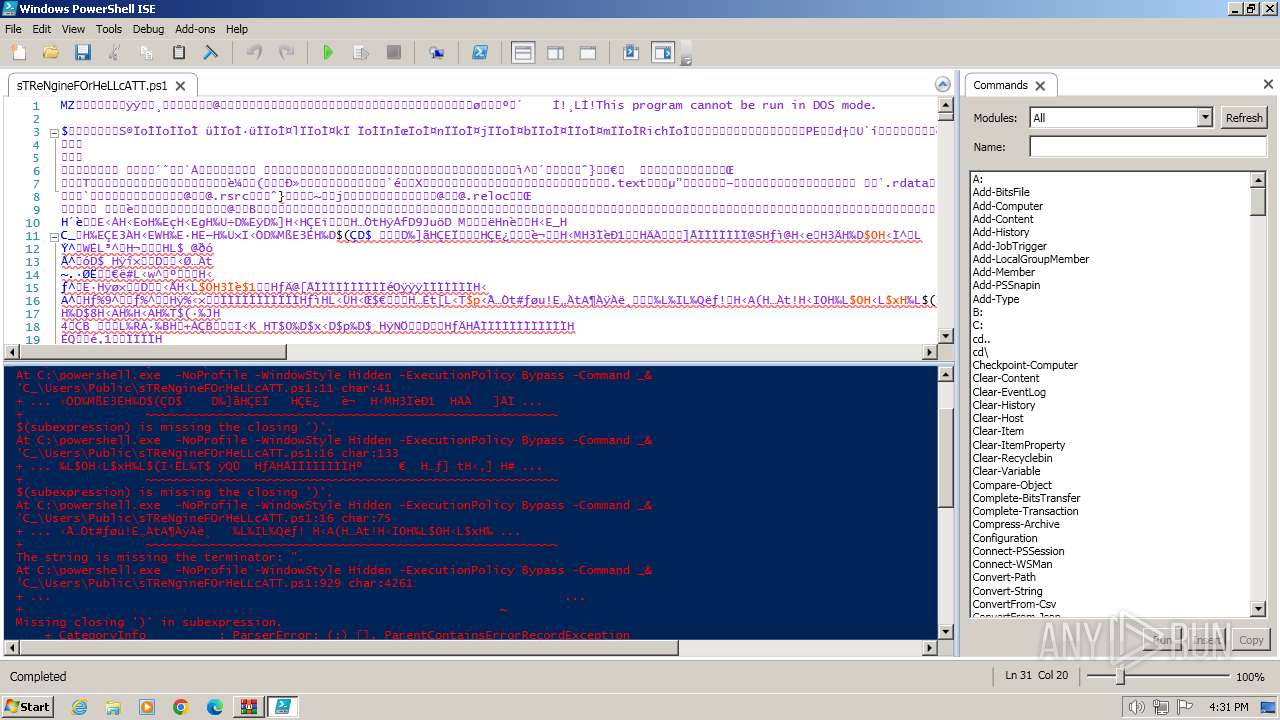
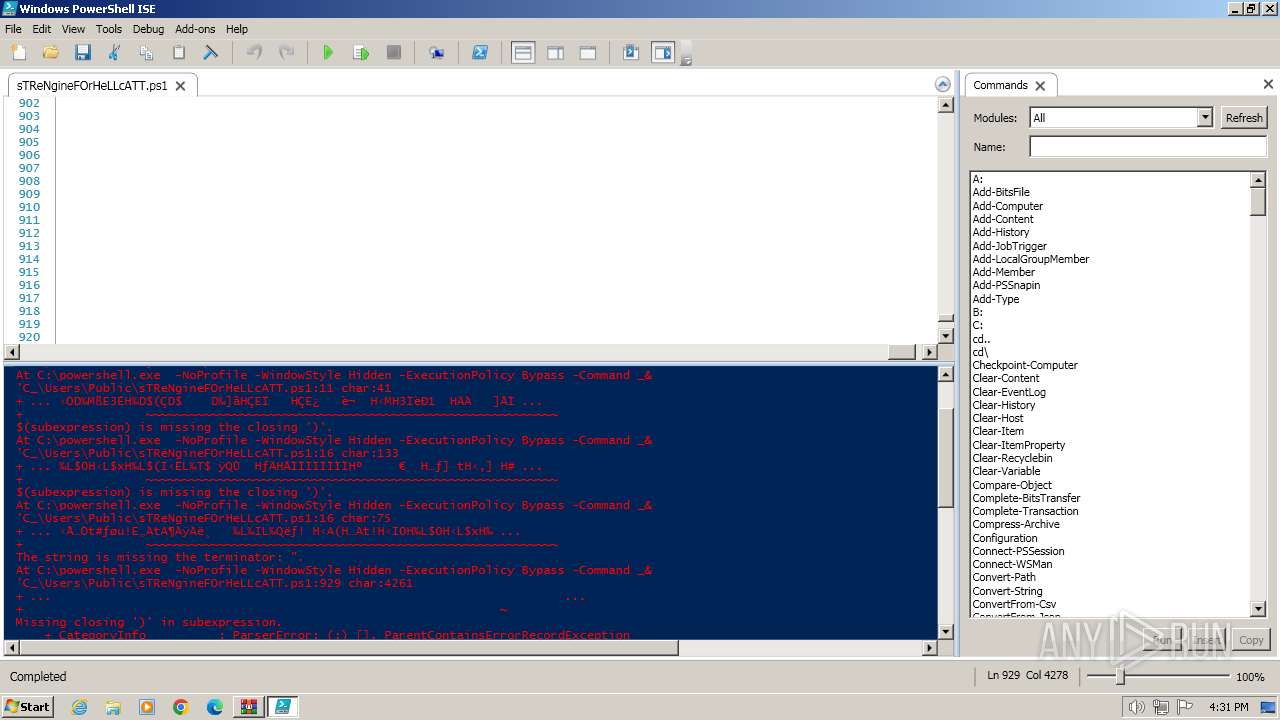
Run PowerShell with an invisible window
- powershell.exe (PID: 3056)
- powershell.exe (PID: 3680)
- powershell.exe (PID: 3776)
- powershell.exe (PID: 4004)
- powershell.exe (PID: 1628)
- powershell.exe (PID: 1496)
Bypass execution policy to execute commands
- powershell.exe (PID: 3056)
- powershell.exe (PID: 3680)
- powershell.exe (PID: 3776)
- powershell.exe (PID: 4004)
- powershell.exe (PID: 1496)
- powershell.exe (PID: 1628)
SUSPICIOUS
Application launched itself
- WinRAR.exe (PID: 668)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 668)
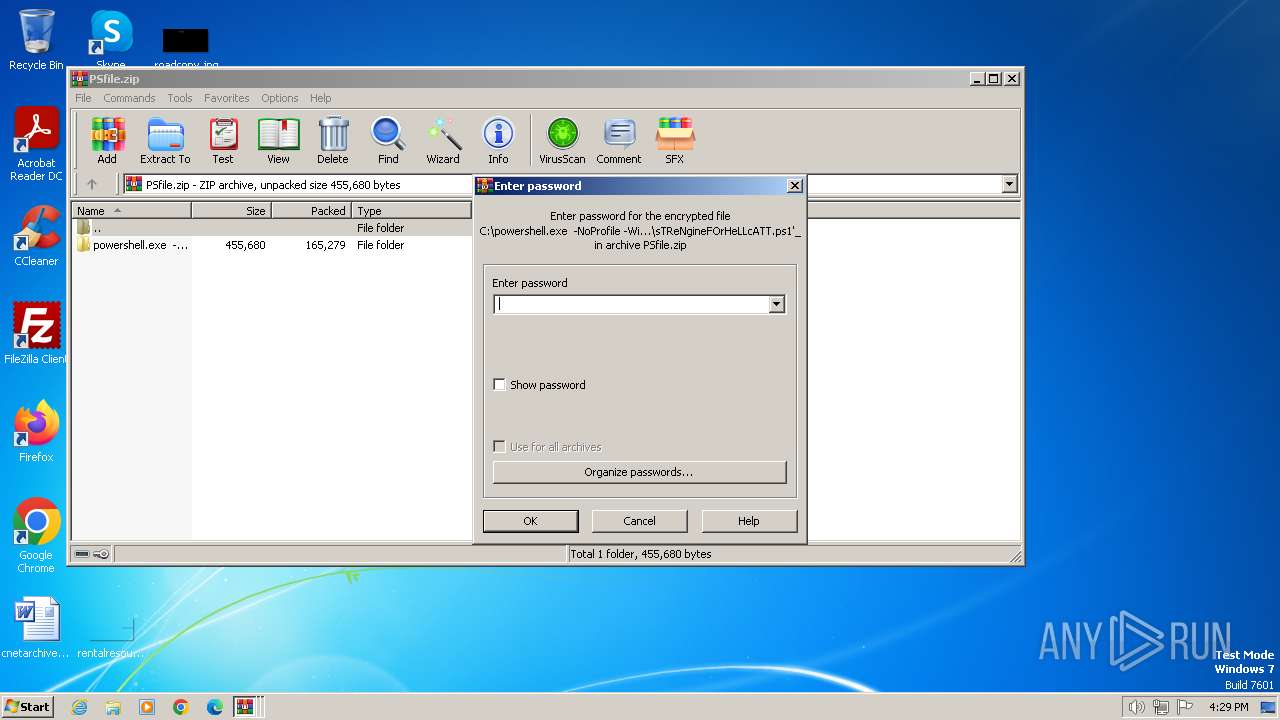
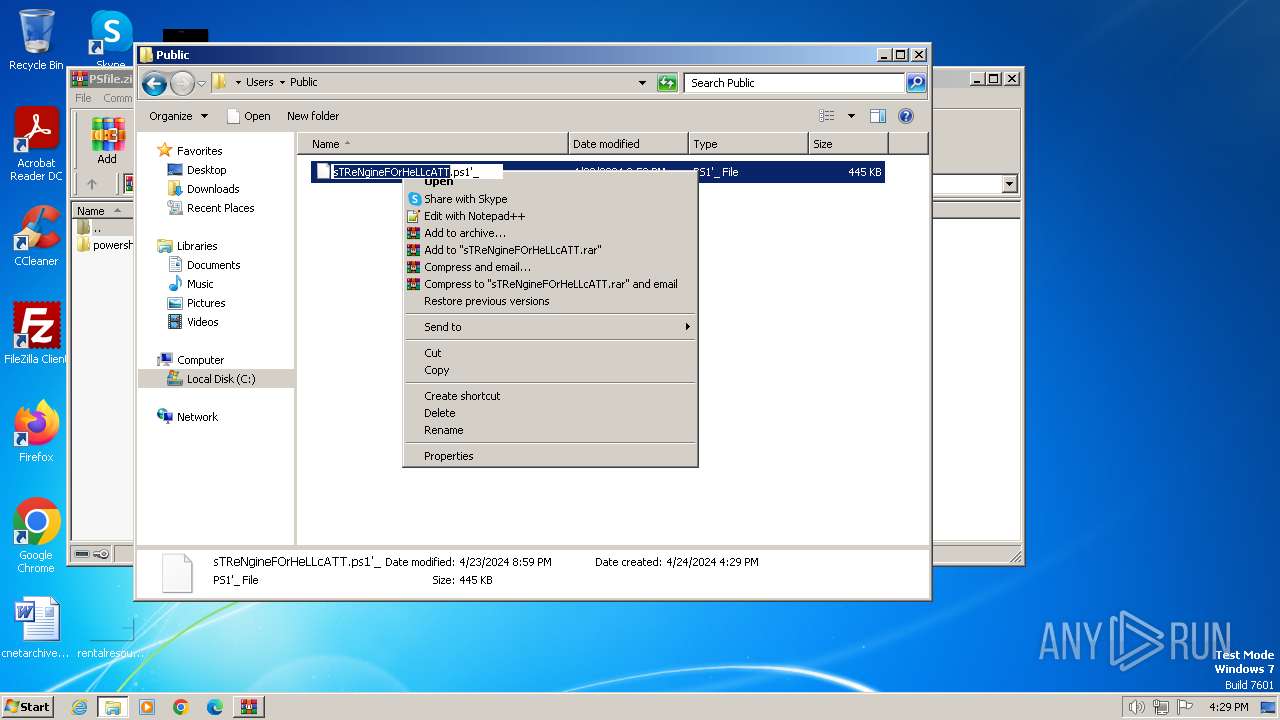
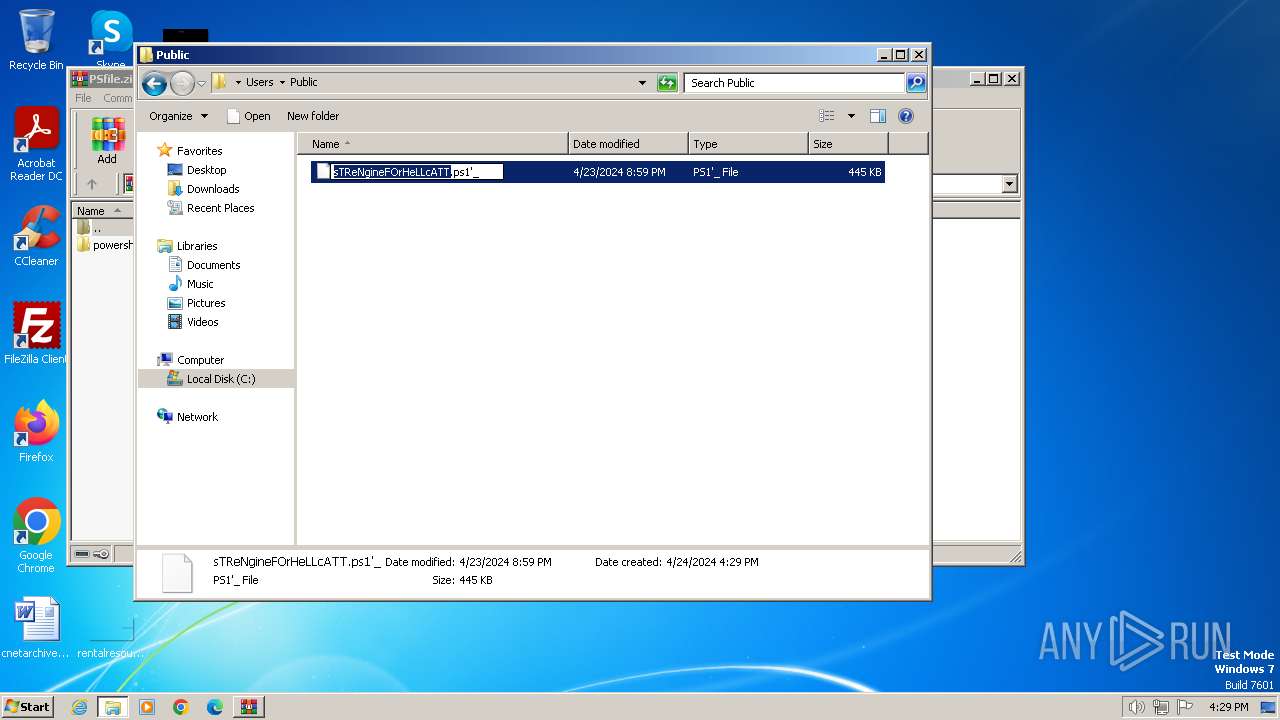
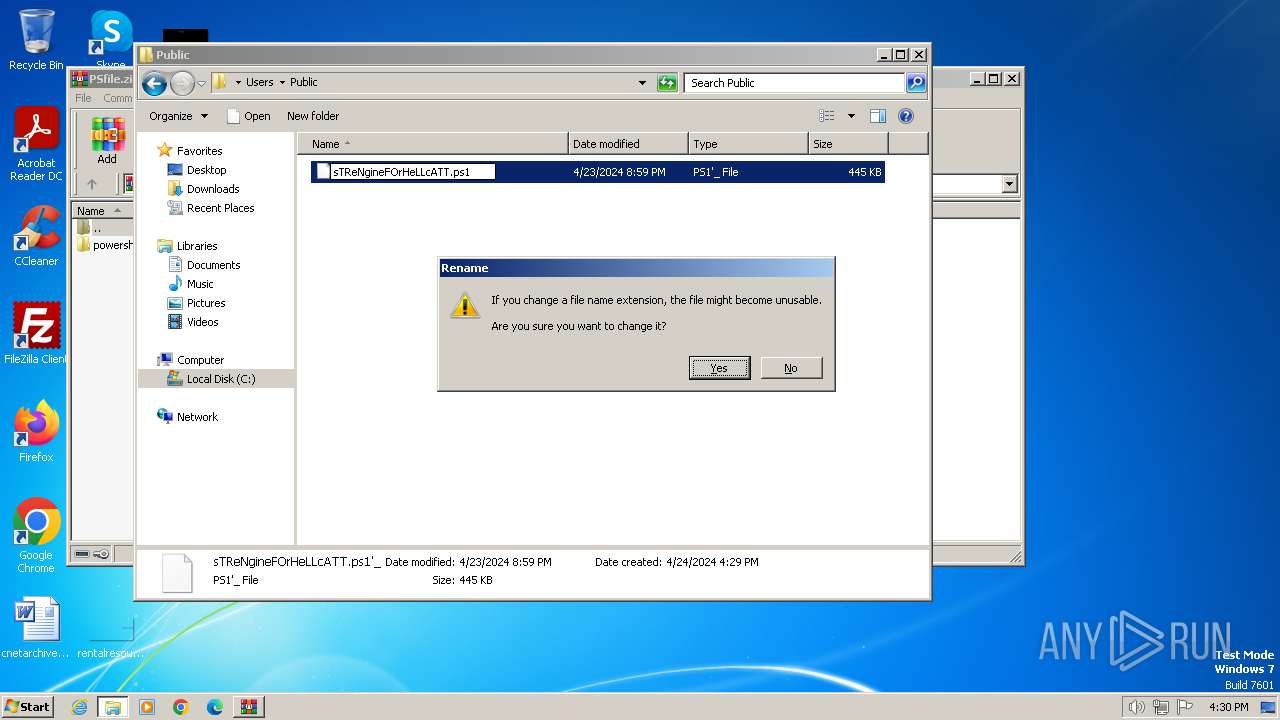
The process creates files with name similar to system file names
- WinRAR.exe (PID: 3988)
Blank space has been found in the path
- WinRAR.exe (PID: 3988)
Process drops legitimate windows executable
- WinRAR.exe (PID: 3988)
Reads the Internet Settings
- PowerShell_ISE.exe (PID: 3916)
- powershell.exe (PID: 3056)
- powershell.exe (PID: 3680)
- powershell.exe (PID: 3776)
- powershell.exe (PID: 1496)
- powershell.exe (PID: 1628)
- powershell.exe (PID: 4004)
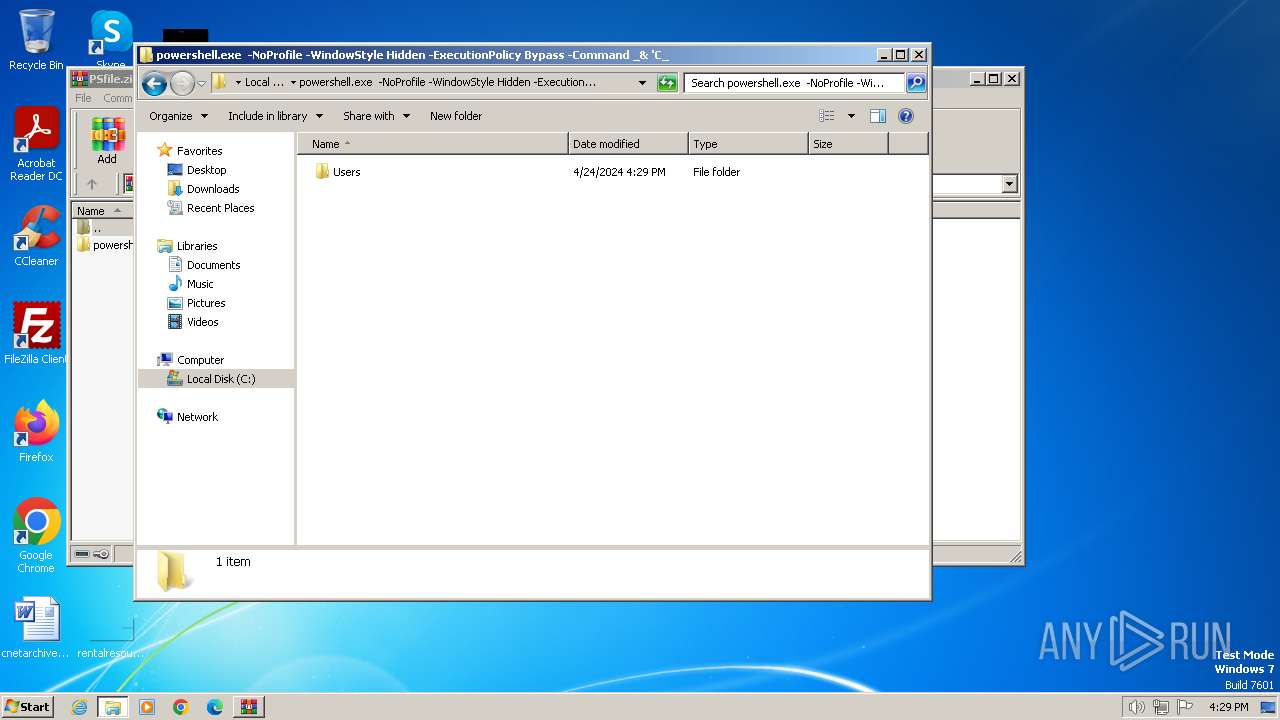
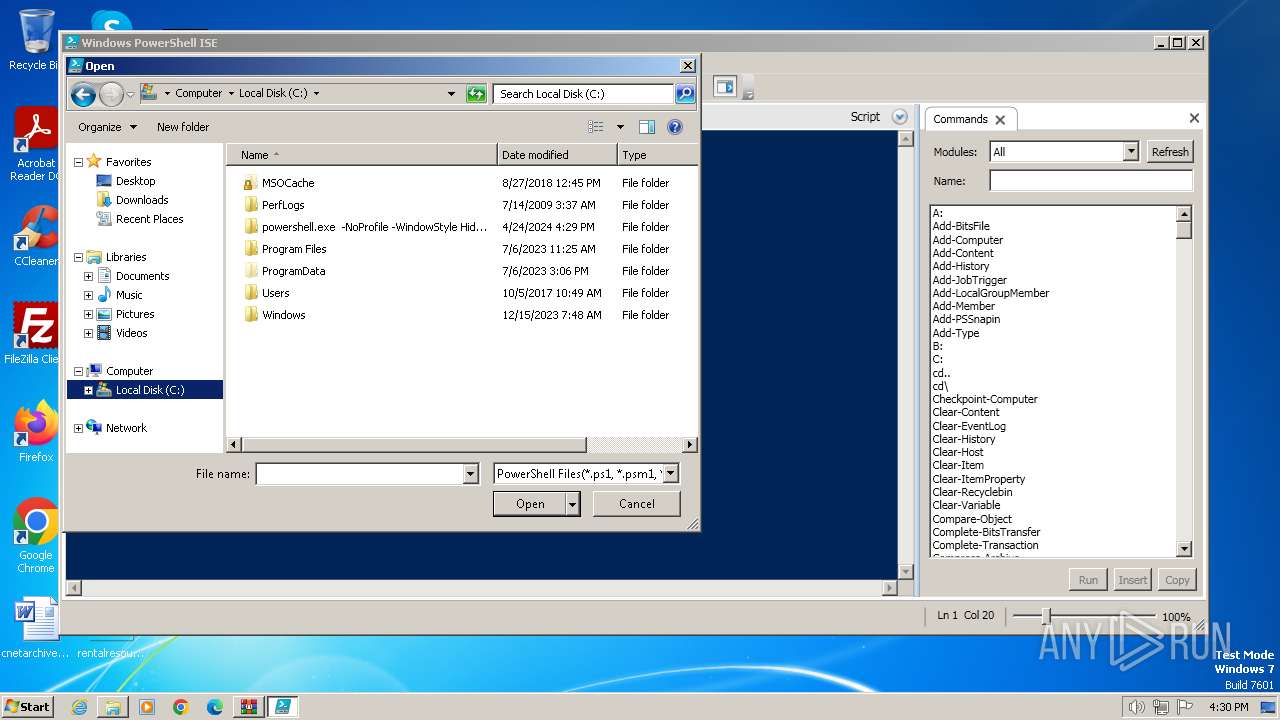
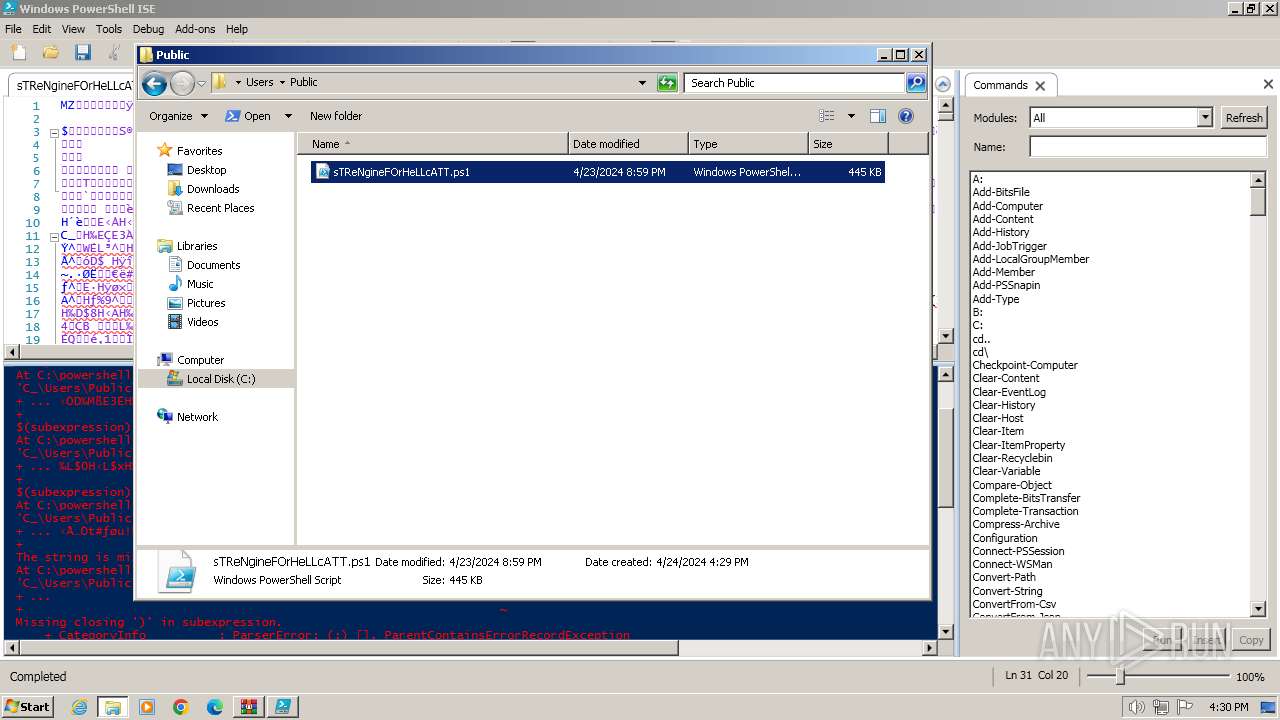
Creates file in the systems drive root
- PowerShell_ISE.exe (PID: 3916)
Reads settings of System Certificates
- PowerShell_ISE.exe (PID: 3916)
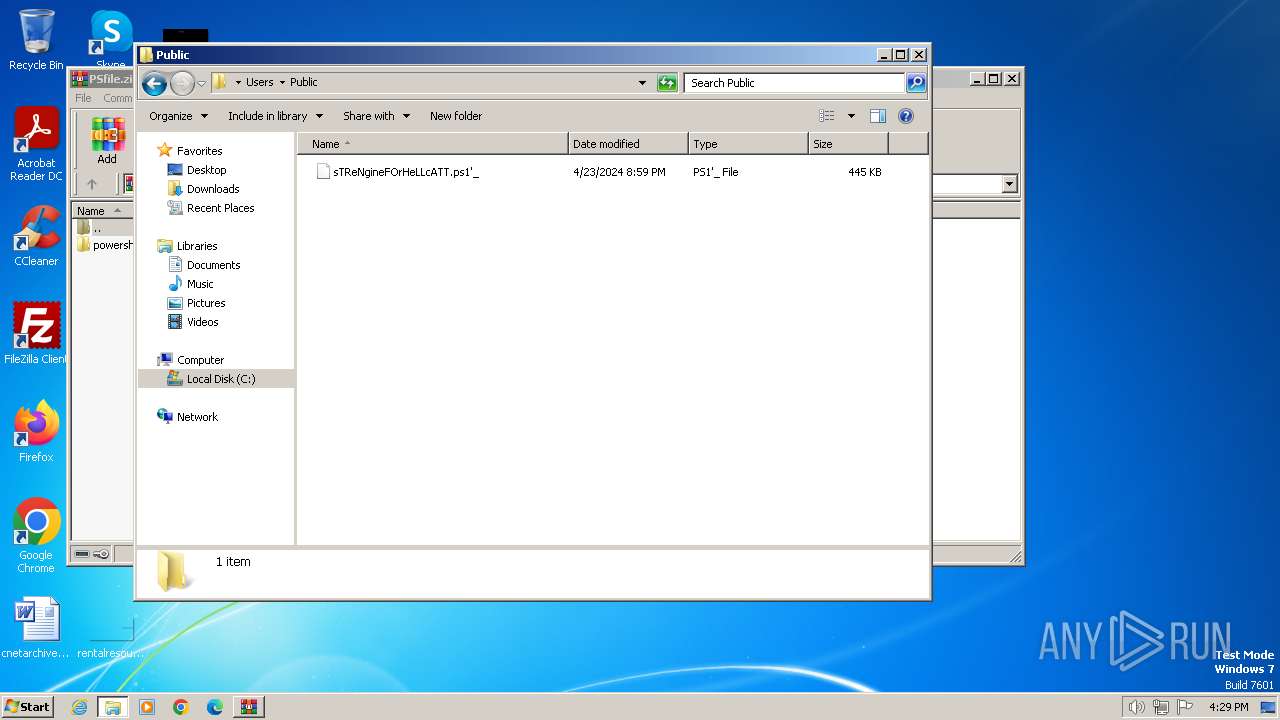
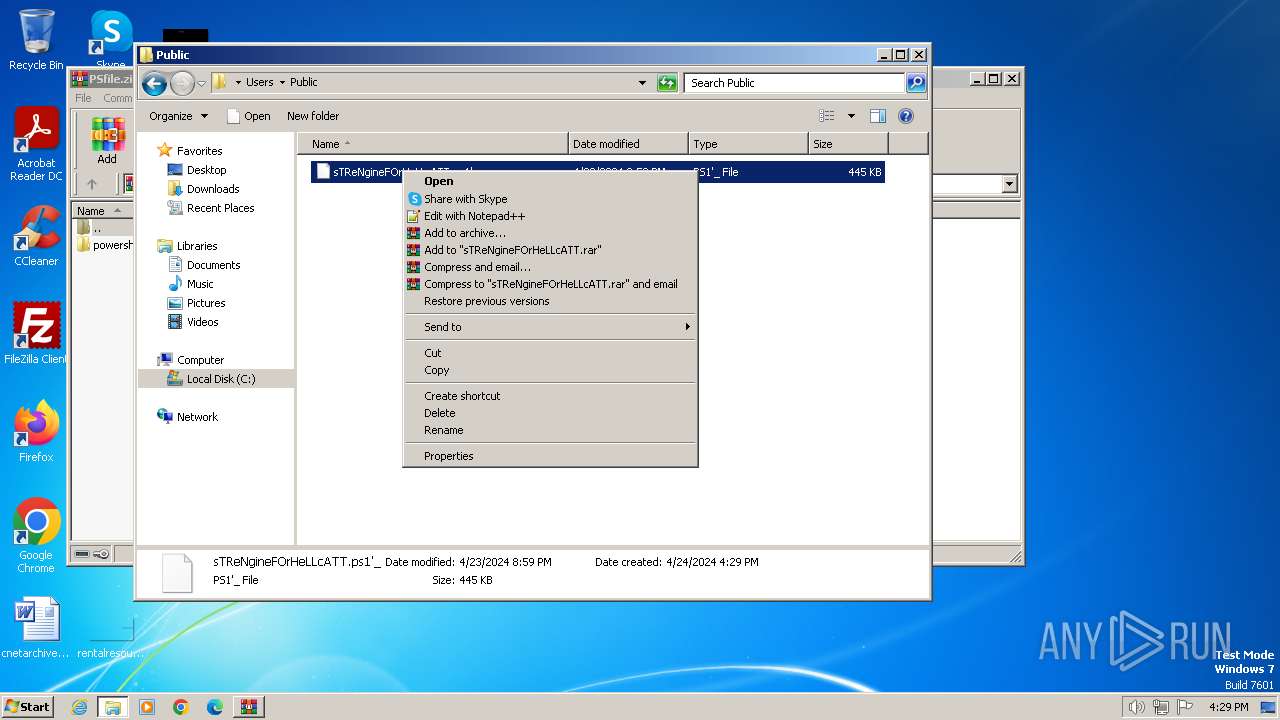
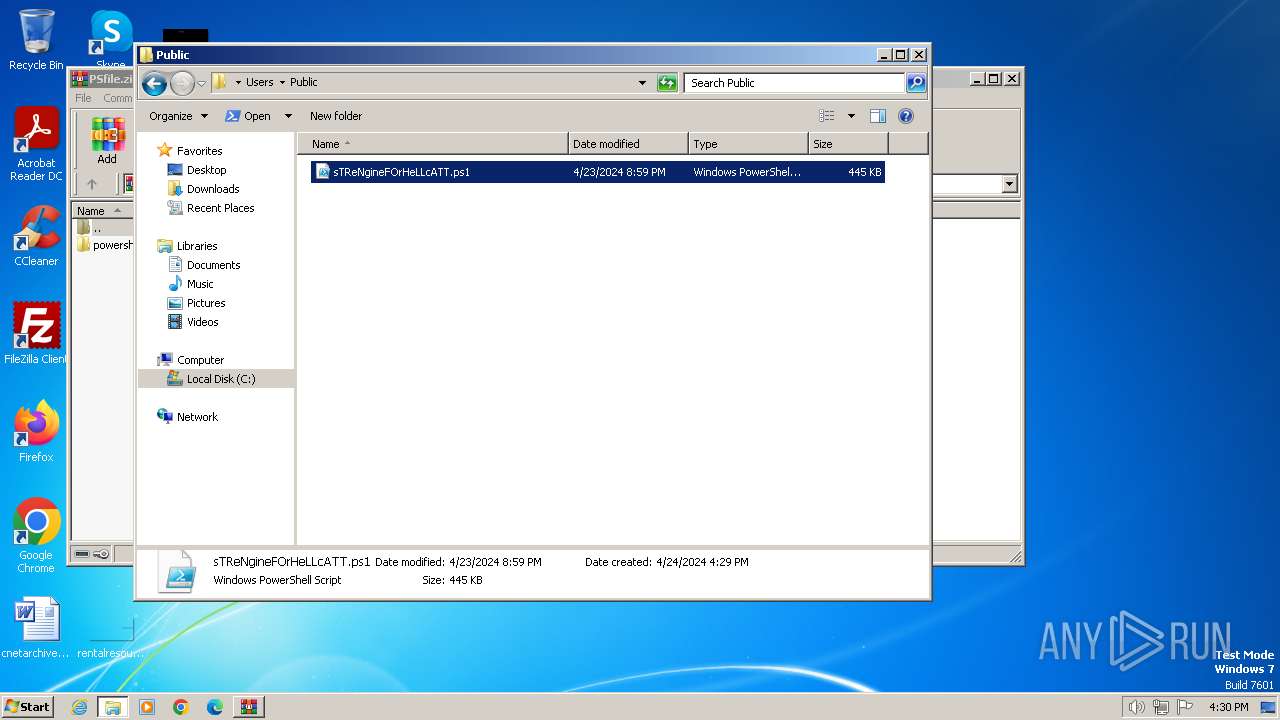
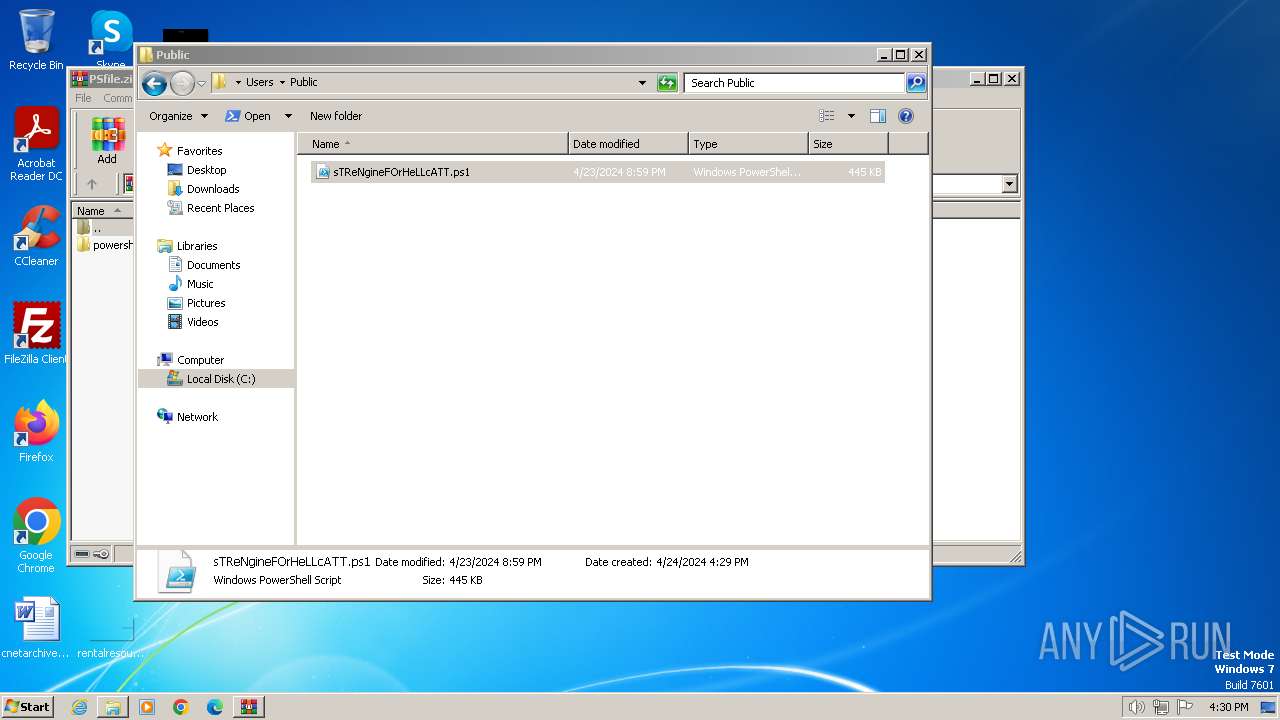
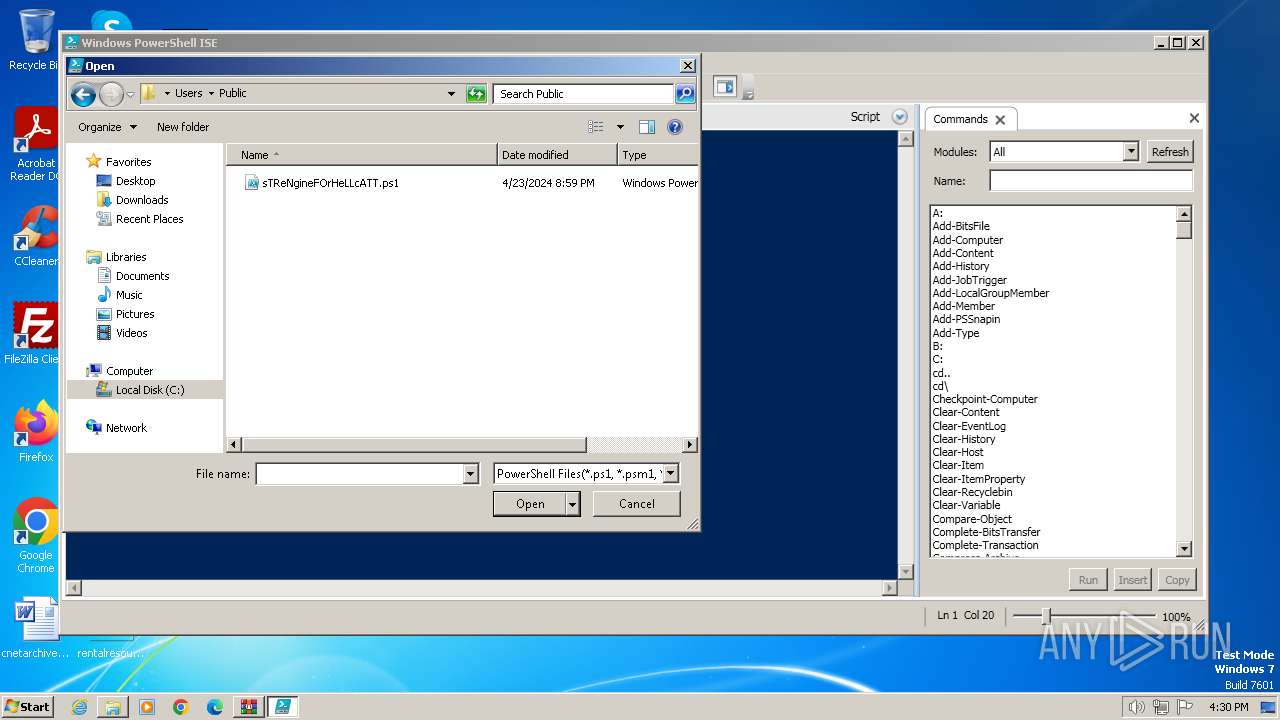
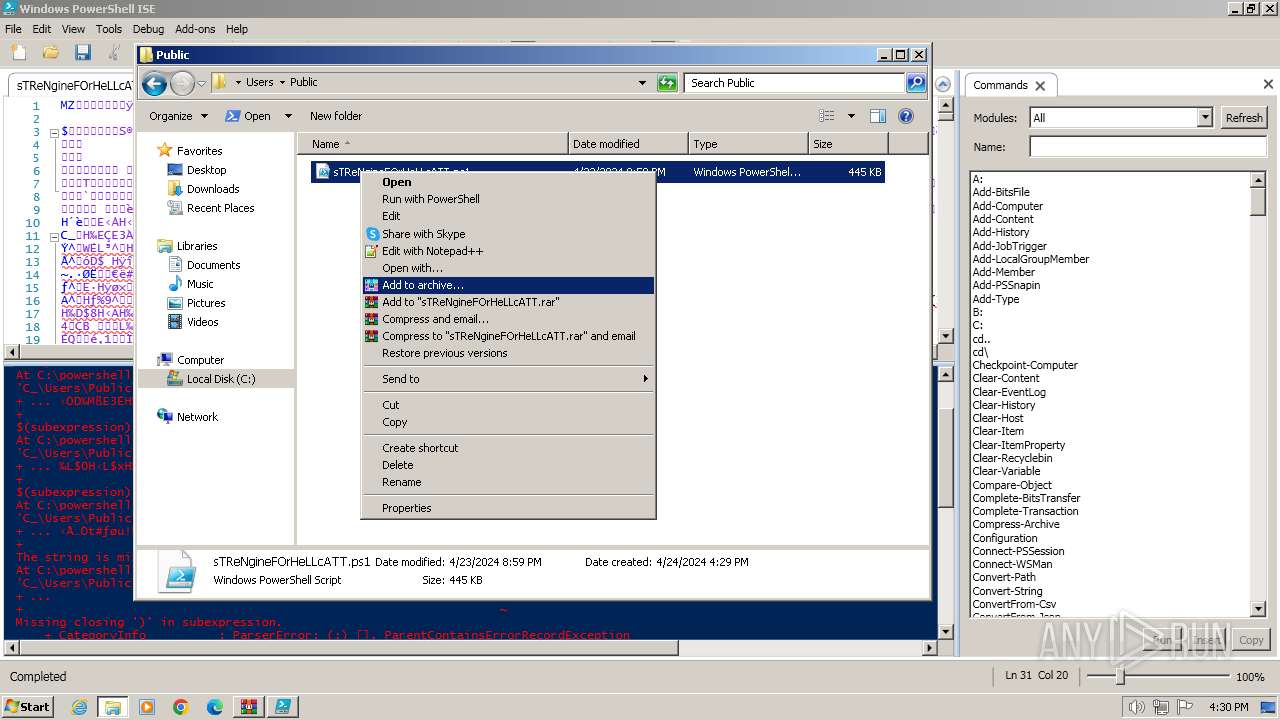
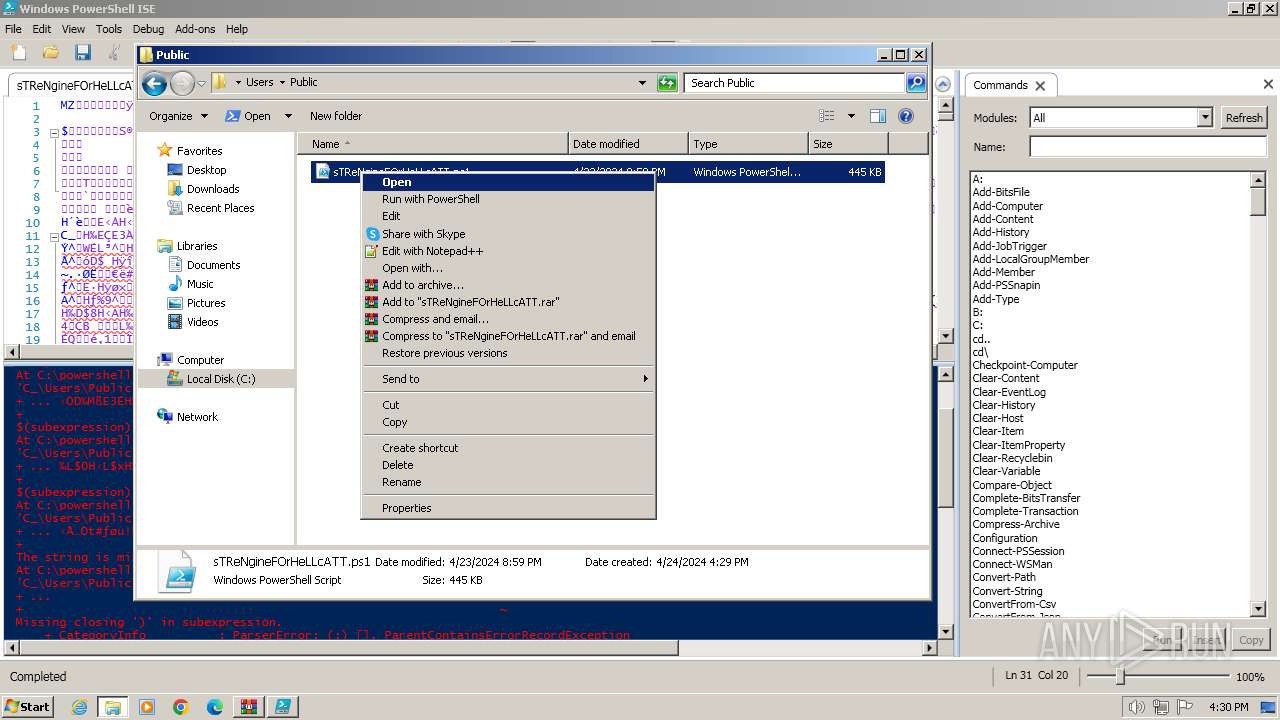
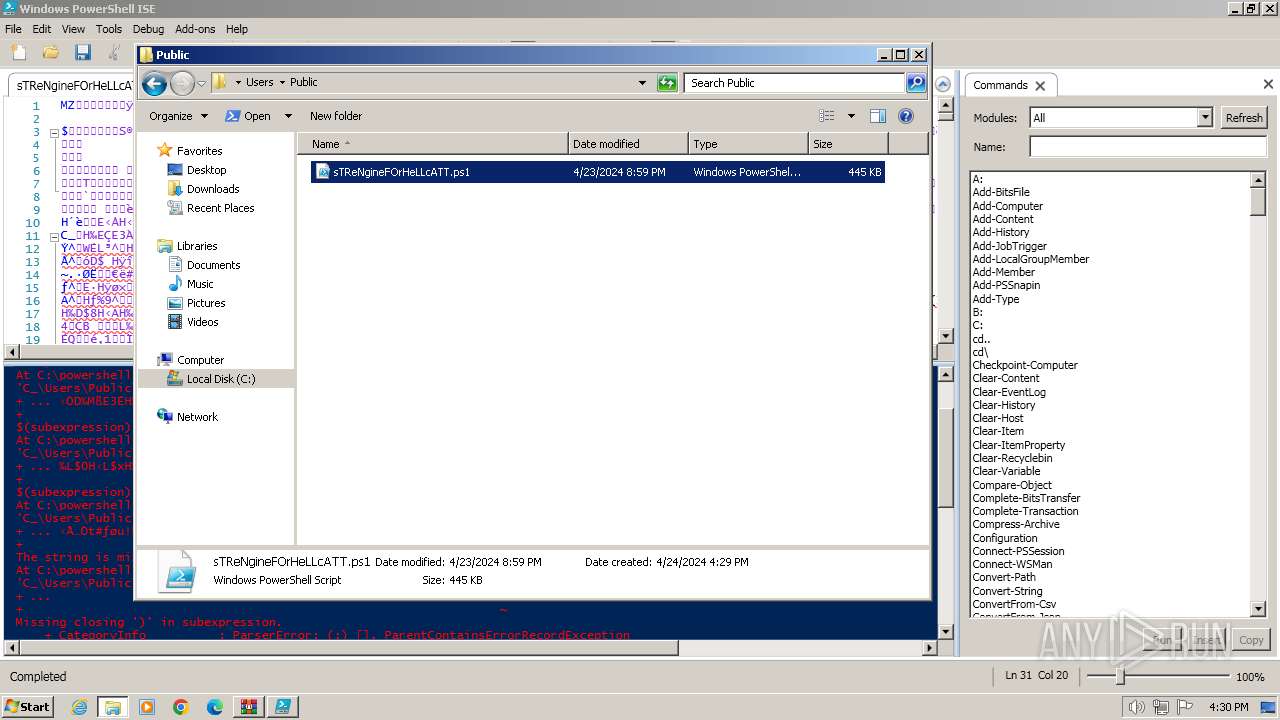
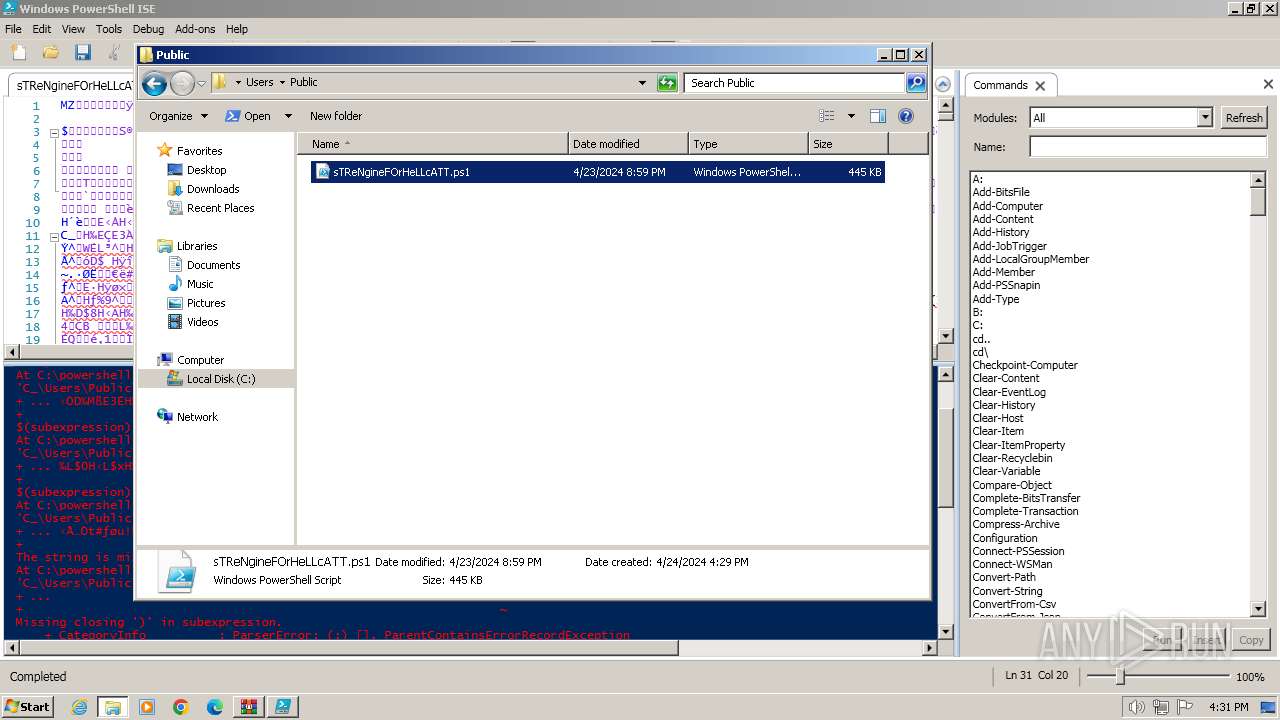
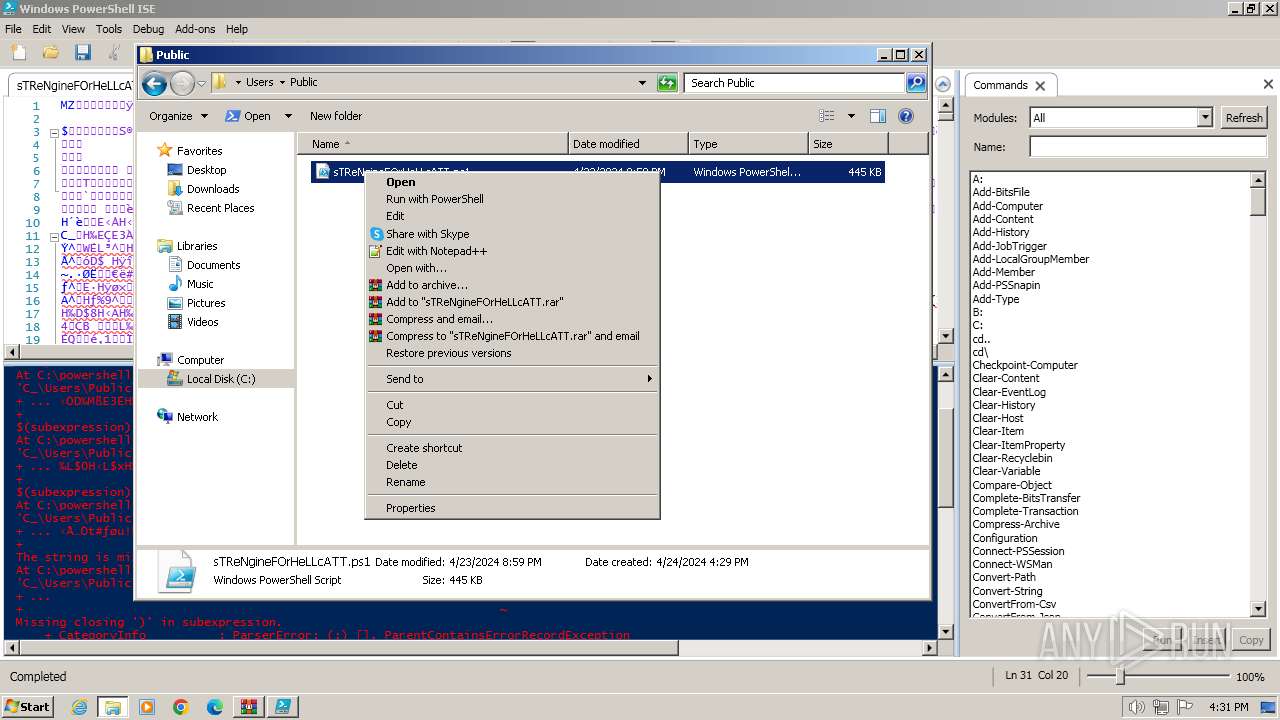
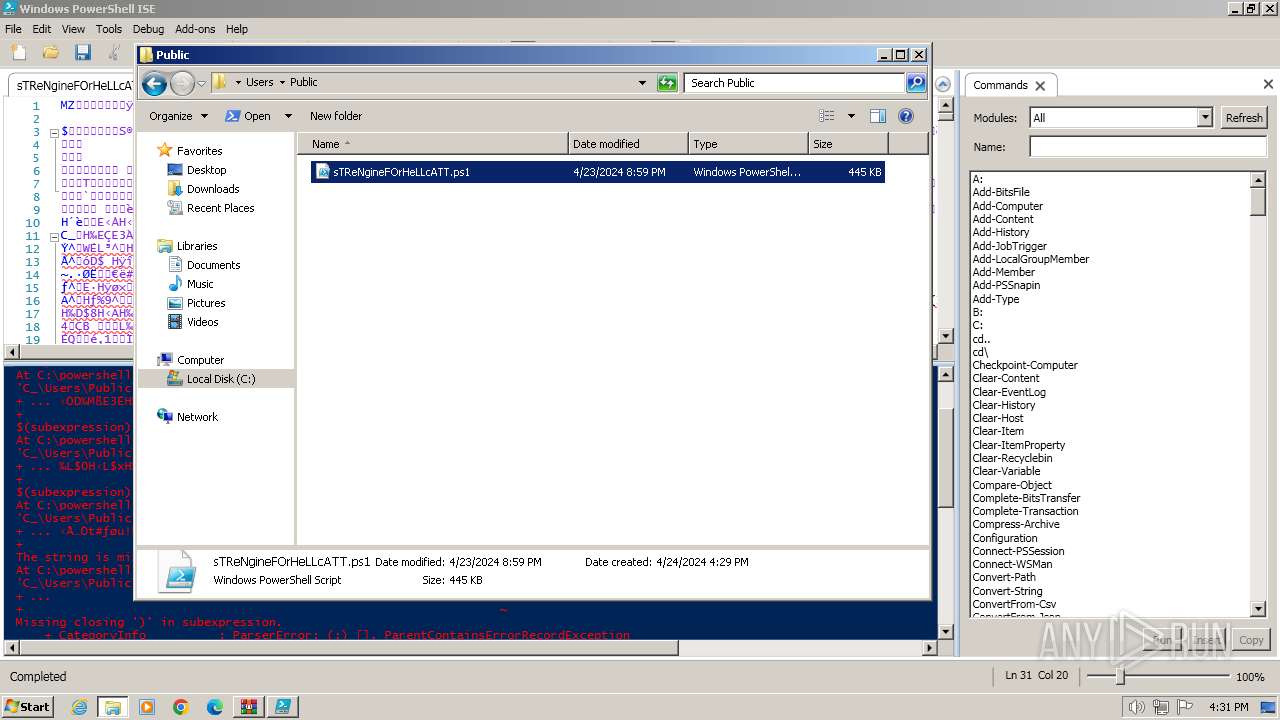
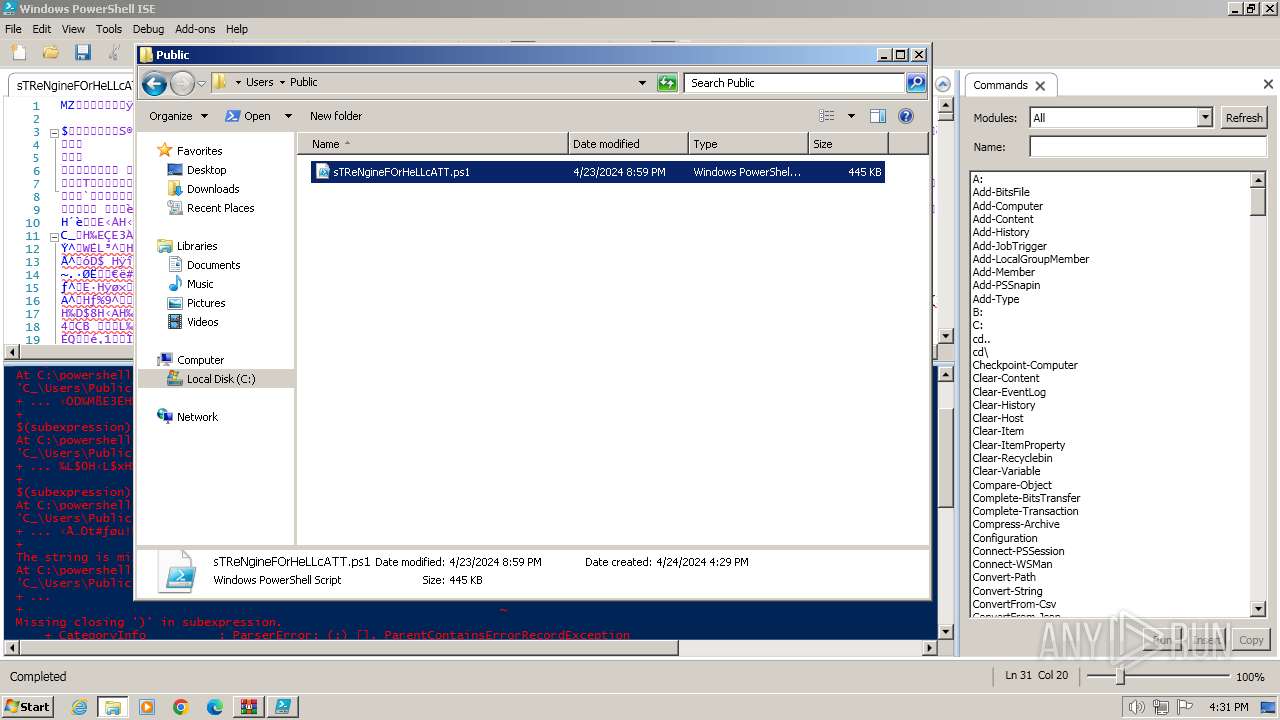
Likely accesses (executes) a file from the Public directory
- powershell.exe (PID: 3776)
- powershell.exe (PID: 3680)
- powershell.exe (PID: 3056)
- powershell.exe (PID: 1496)
- powershell.exe (PID: 4004)
- powershell.exe (PID: 1628)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3988)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3988)
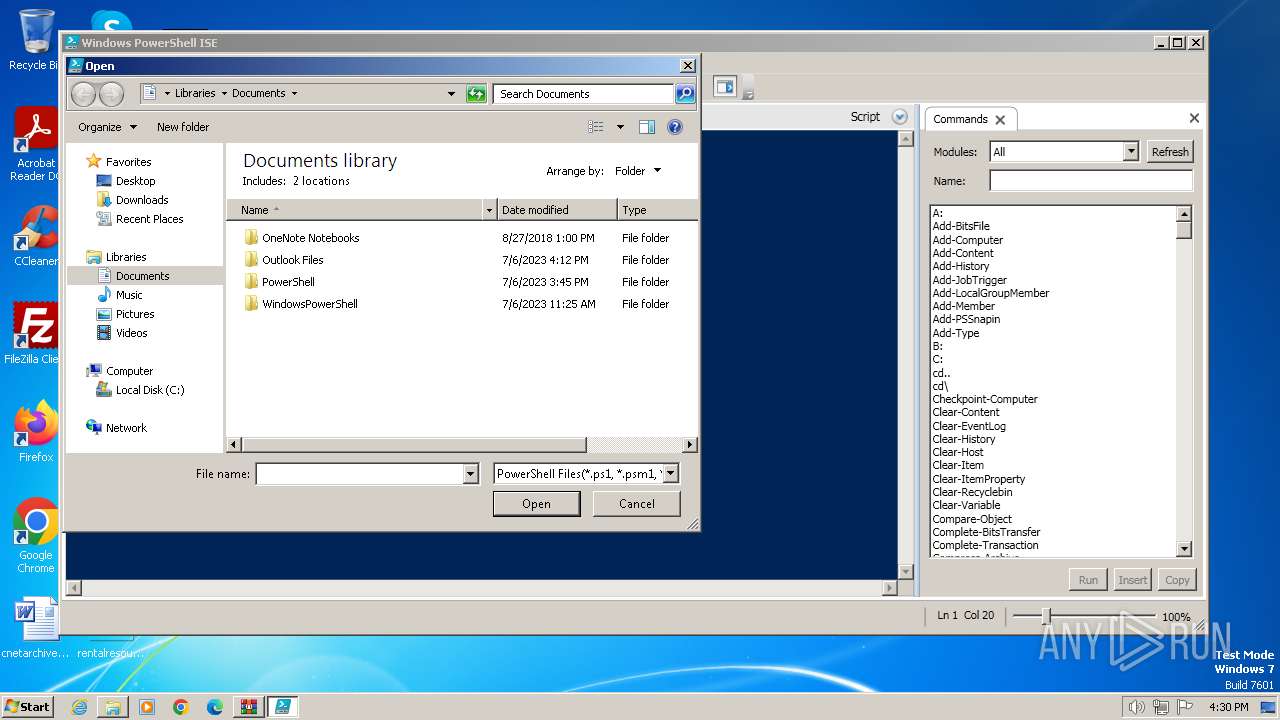
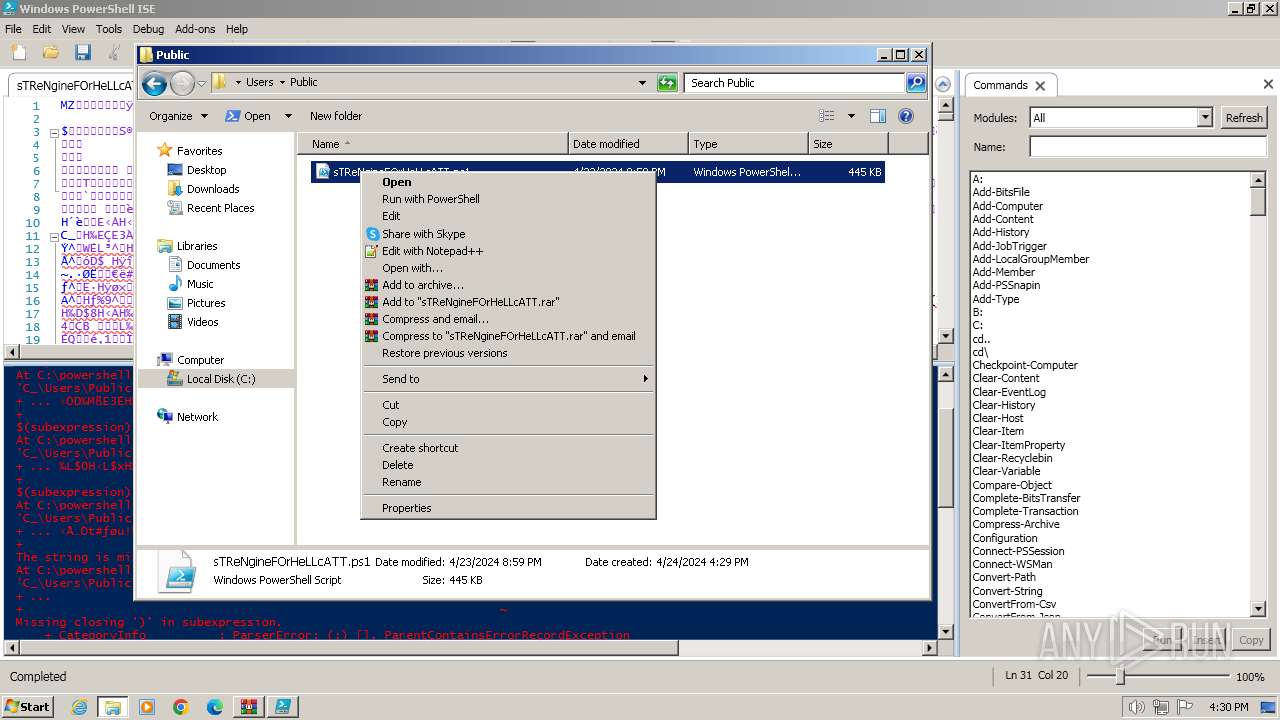
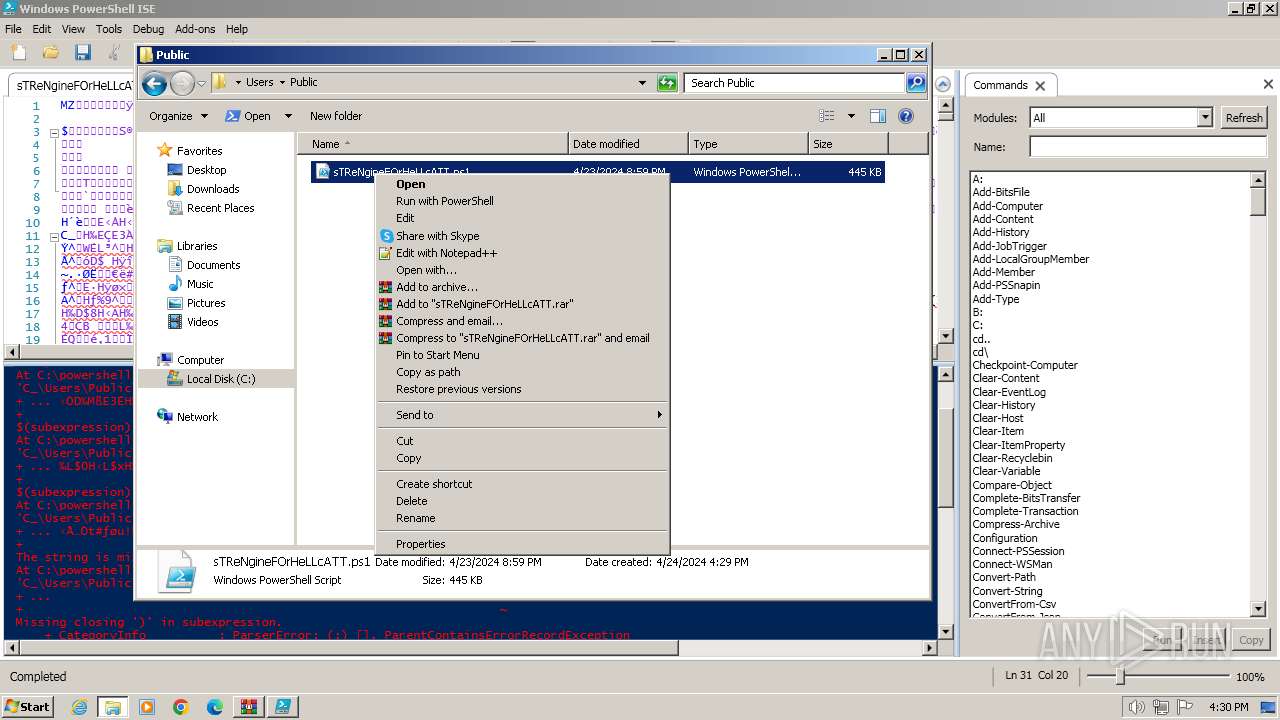
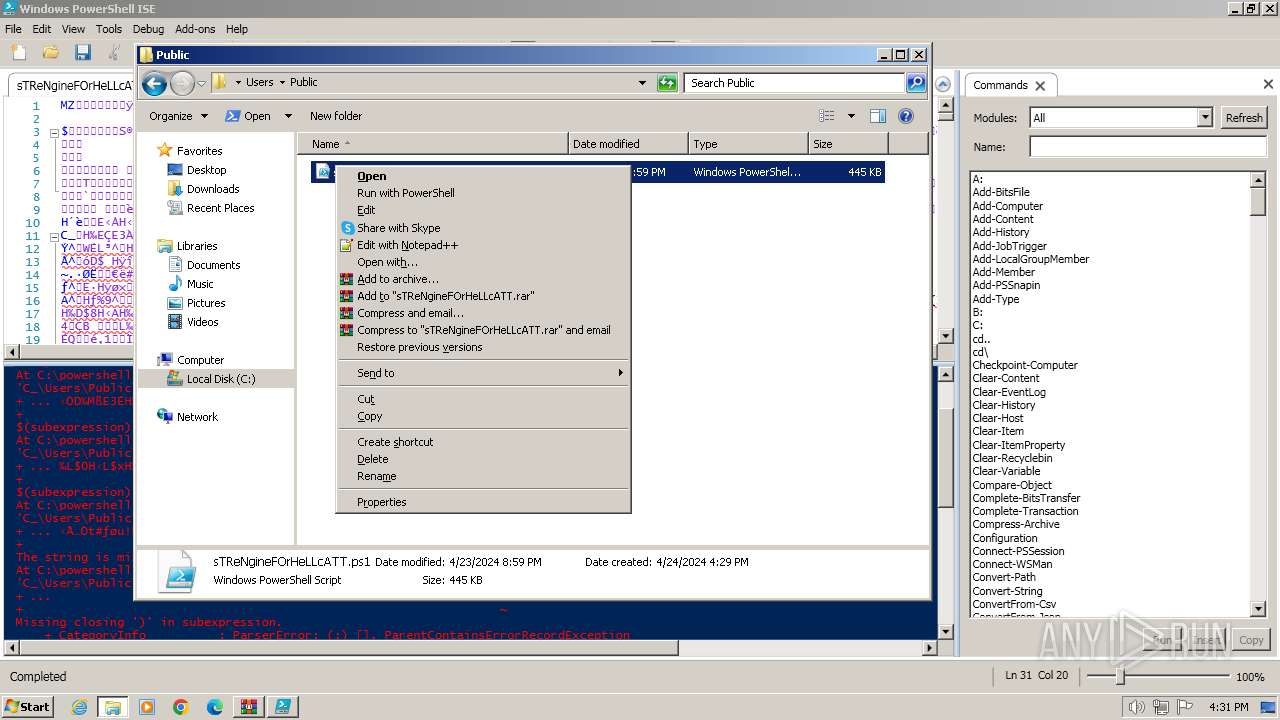
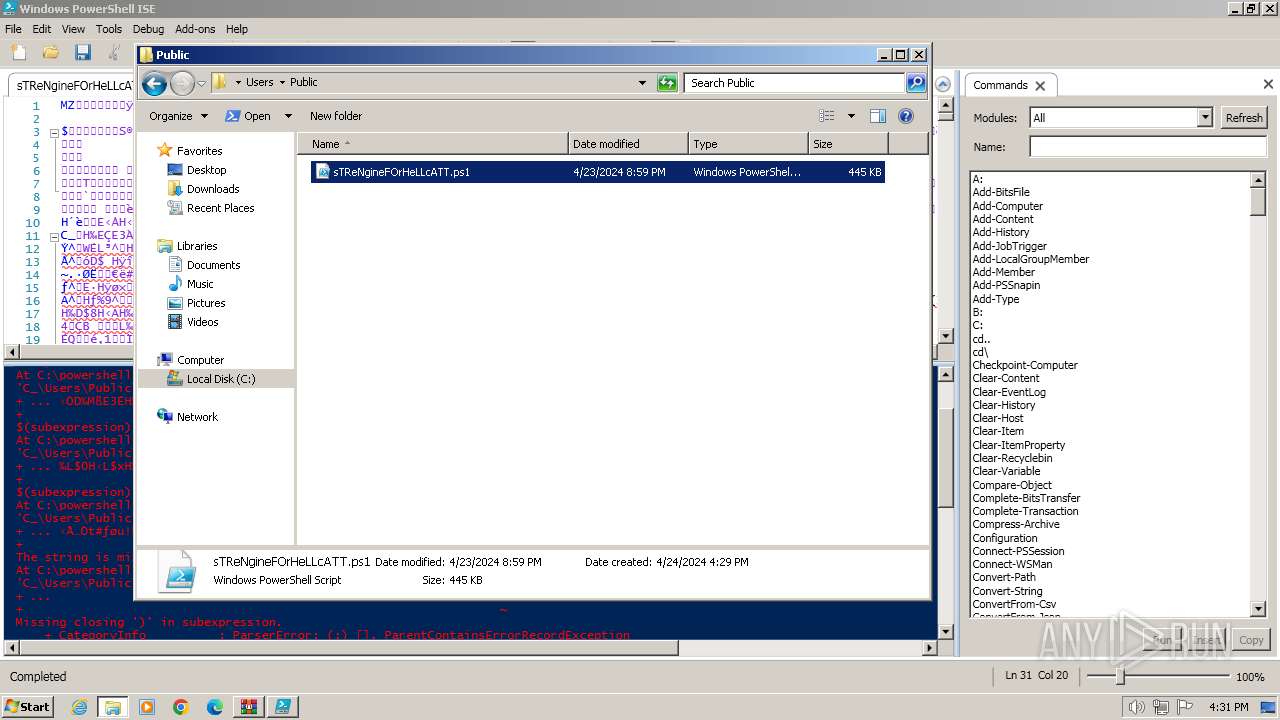
Manual execution by a user
- PowerShell_ISE.exe (PID: 3916)
- powershell.exe (PID: 3056)
- powershell.exe (PID: 3680)
- powershell.exe (PID: 3776)
- powershell.exe (PID: 1496)
- powershell.exe (PID: 4004)
- powershell.exe (PID: 1628)
- wmpnscfg.exe (PID: 3900)
- explorer.exe (PID: 3084)
Creates files or folders in the user directory
- PowerShell_ISE.exe (PID: 3916)
Reads security settings of Internet Explorer
- PowerShell_ISE.exe (PID: 3916)
Create files in a temporary directory
- PowerShell_ISE.exe (PID: 3916)
Reads the software policy settings
- PowerShell_ISE.exe (PID: 3916)
Checks current location (POWERSHELL)
- PowerShell_ISE.exe (PID: 3916)
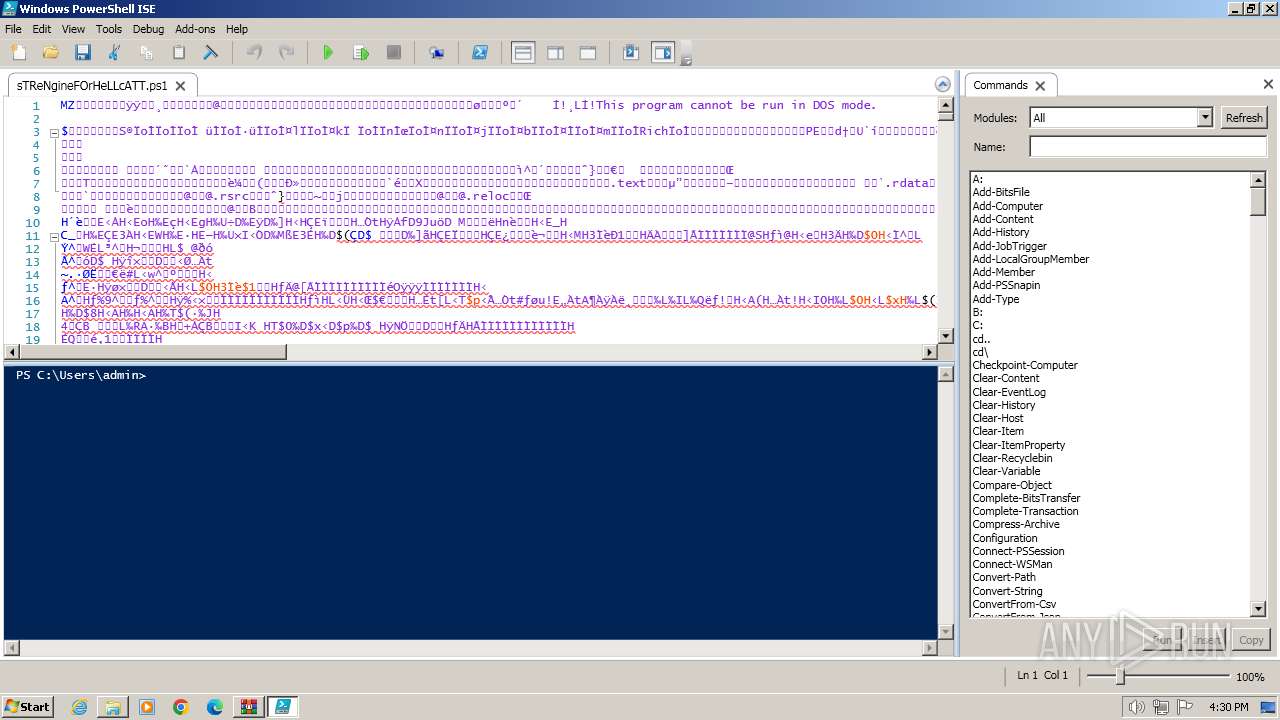
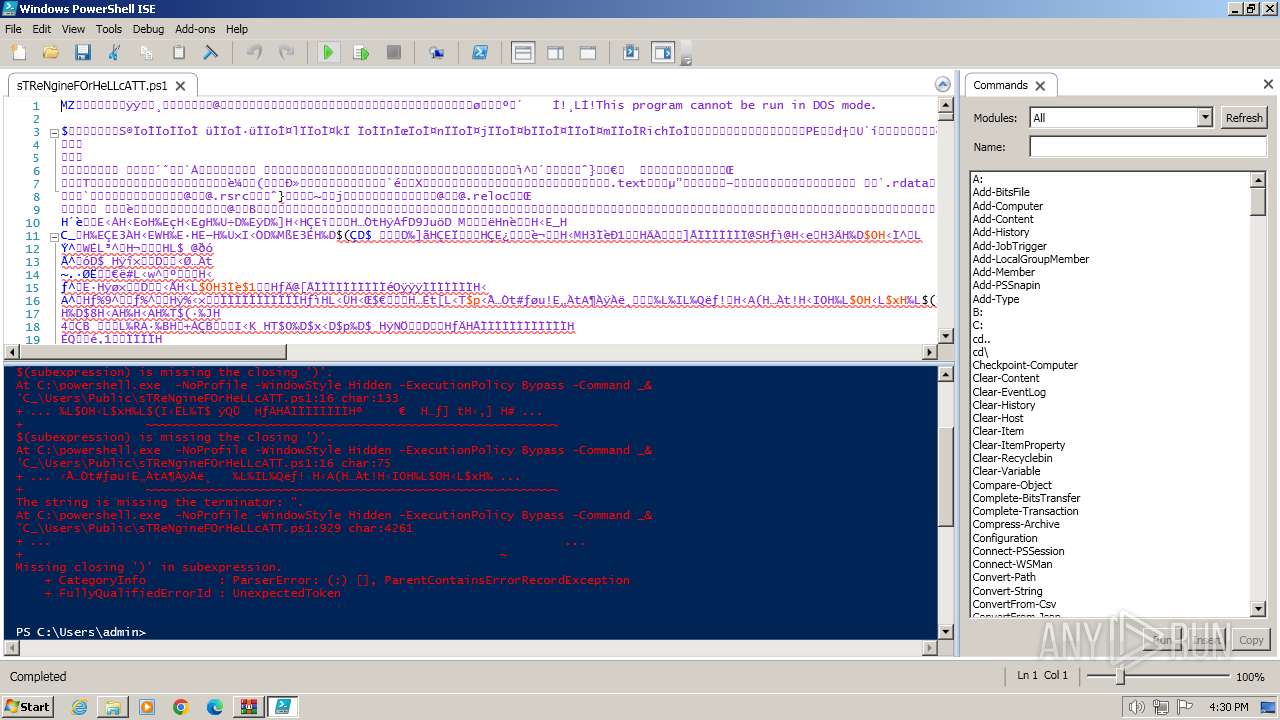
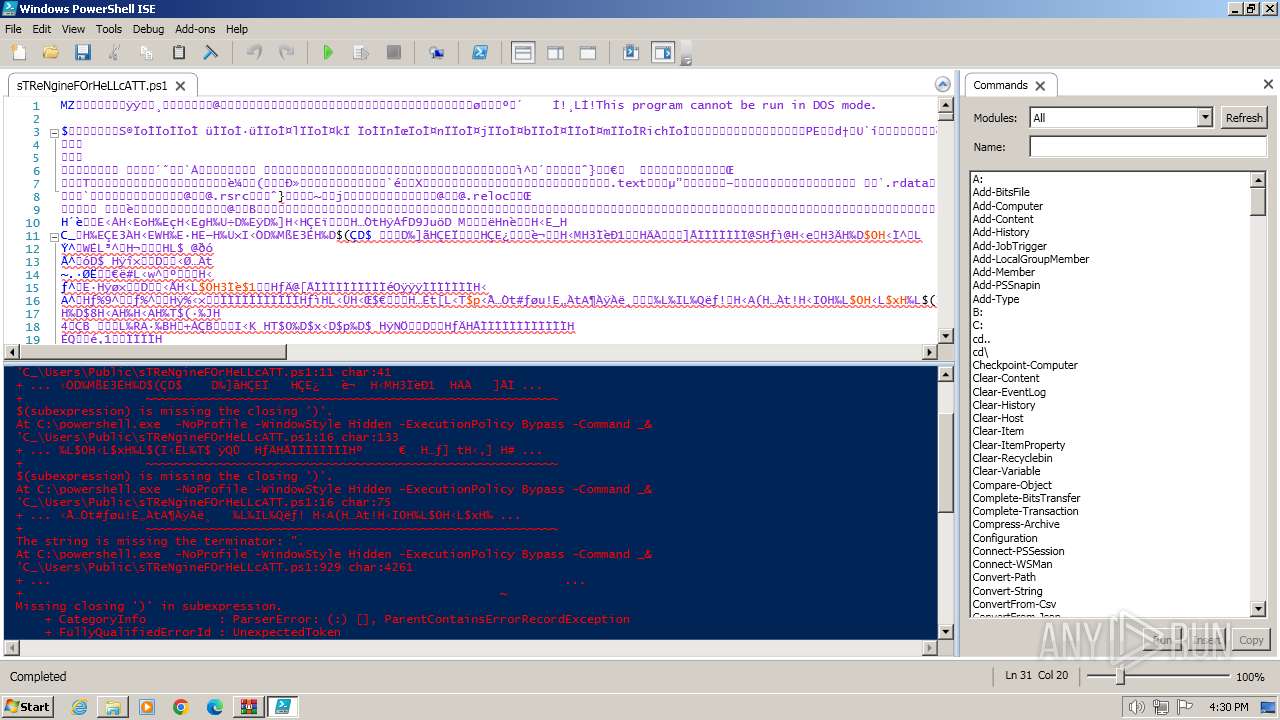
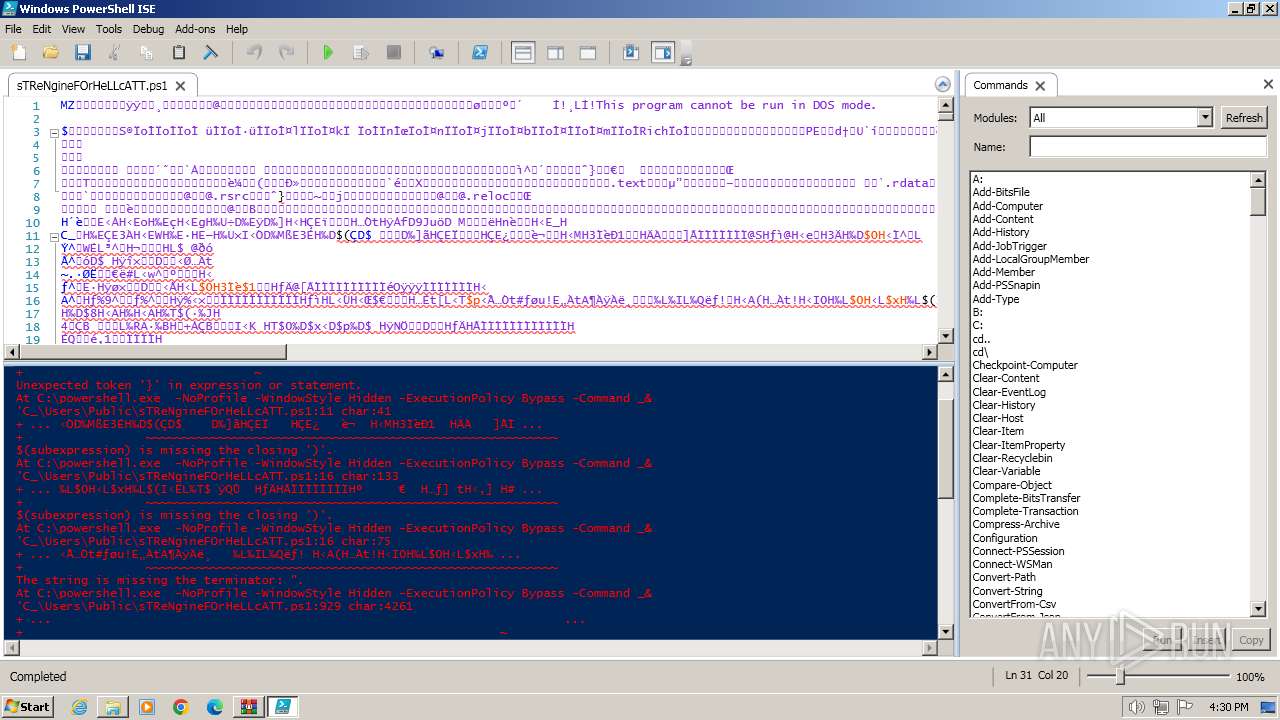
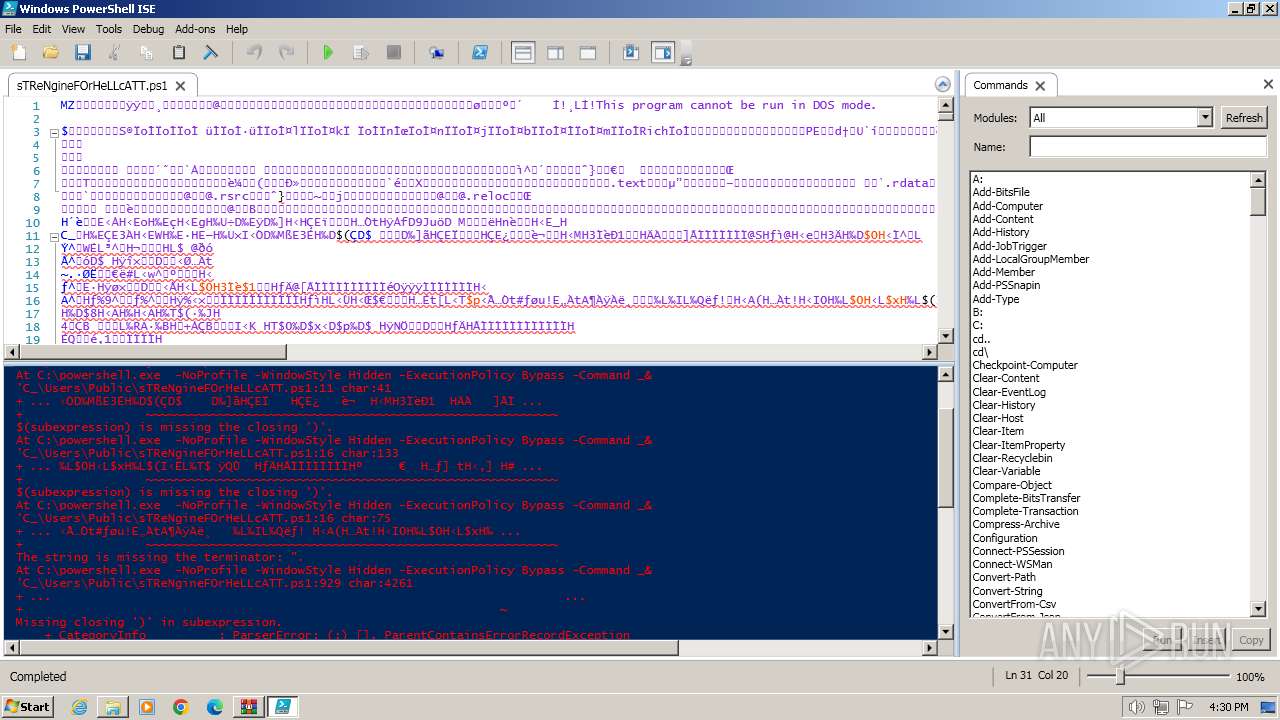
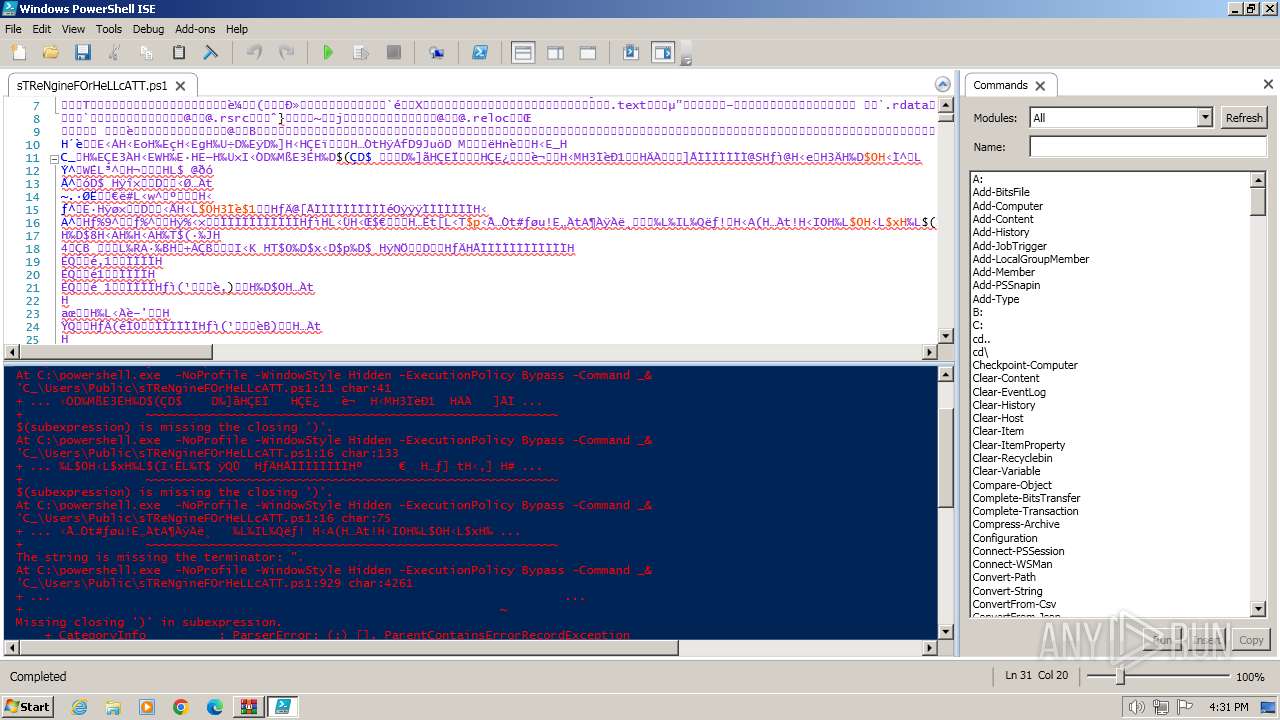
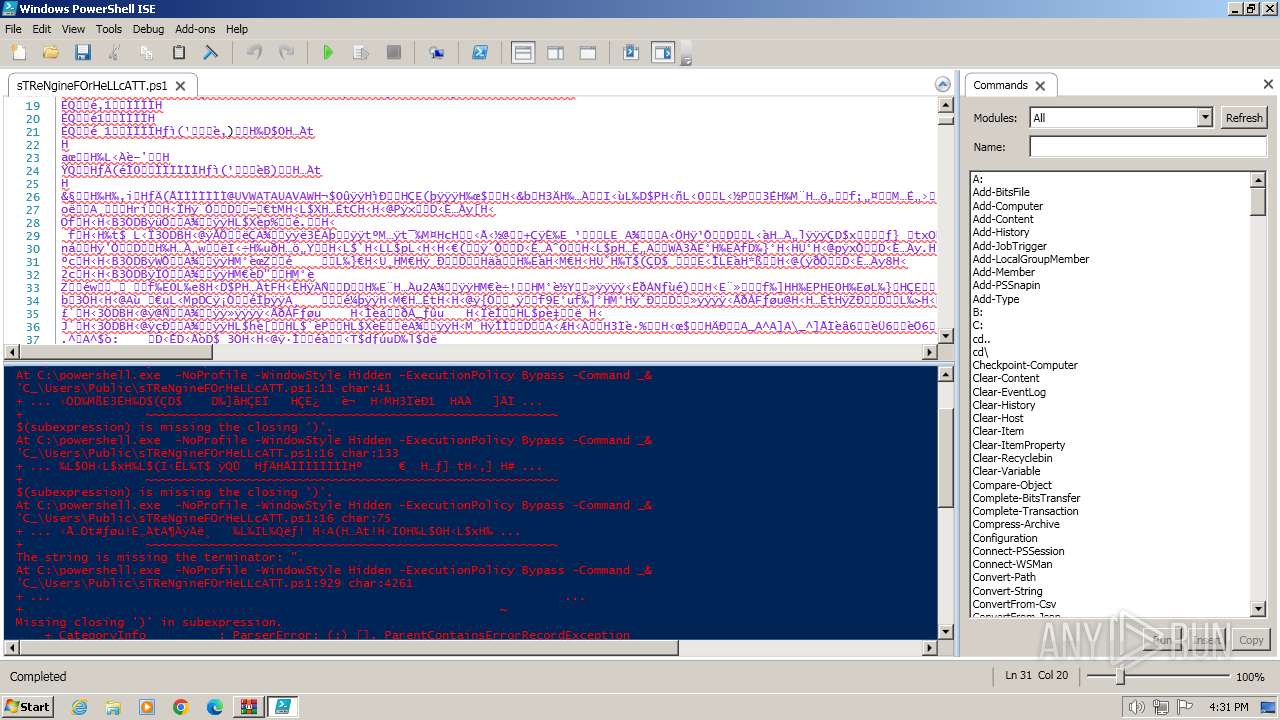
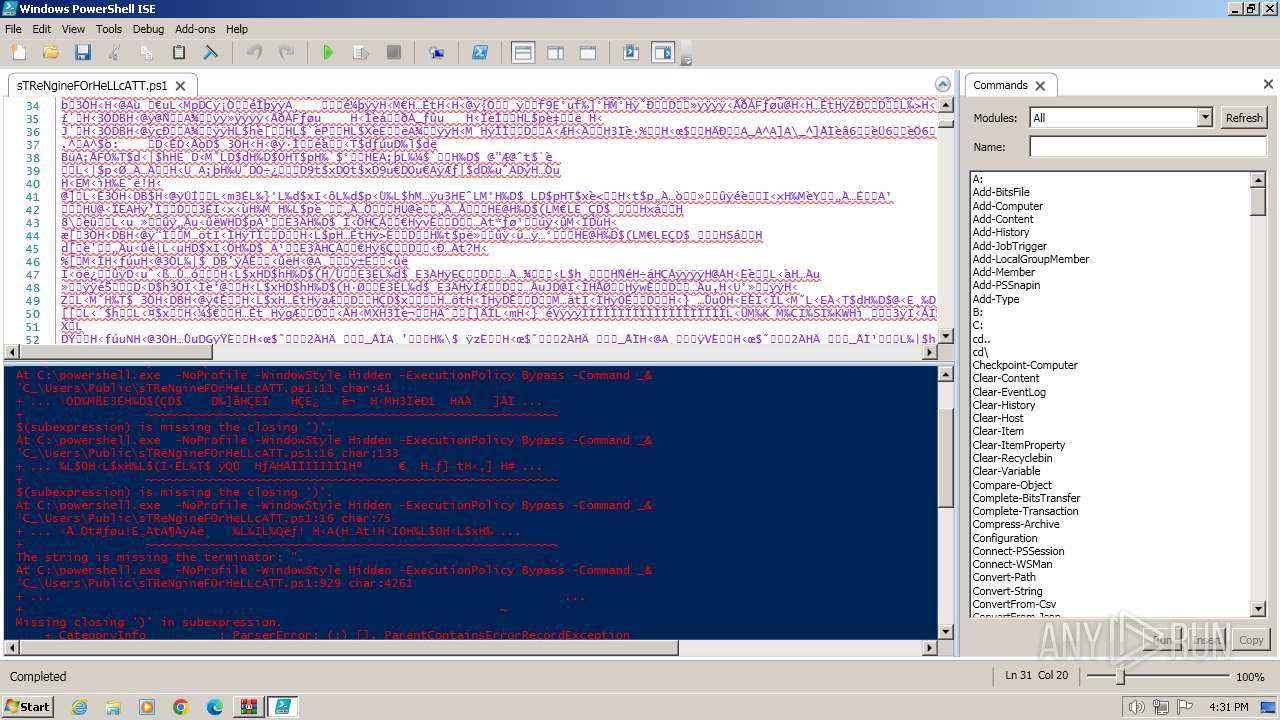
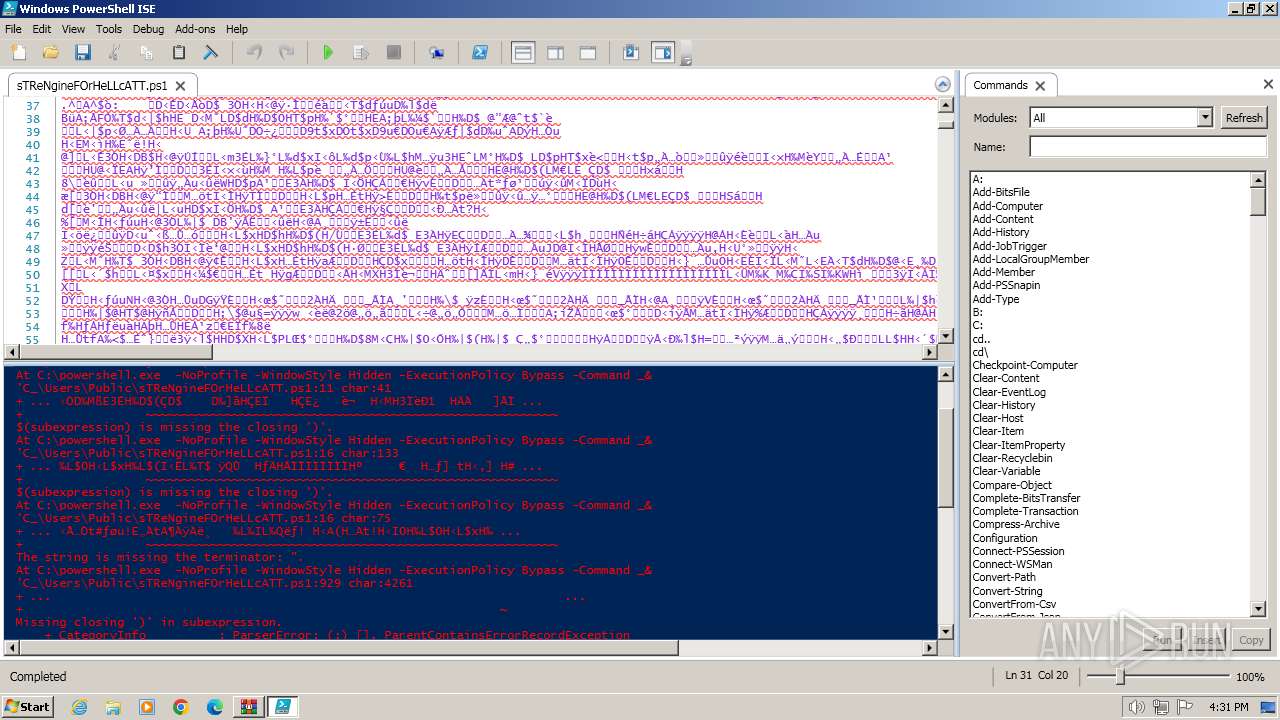
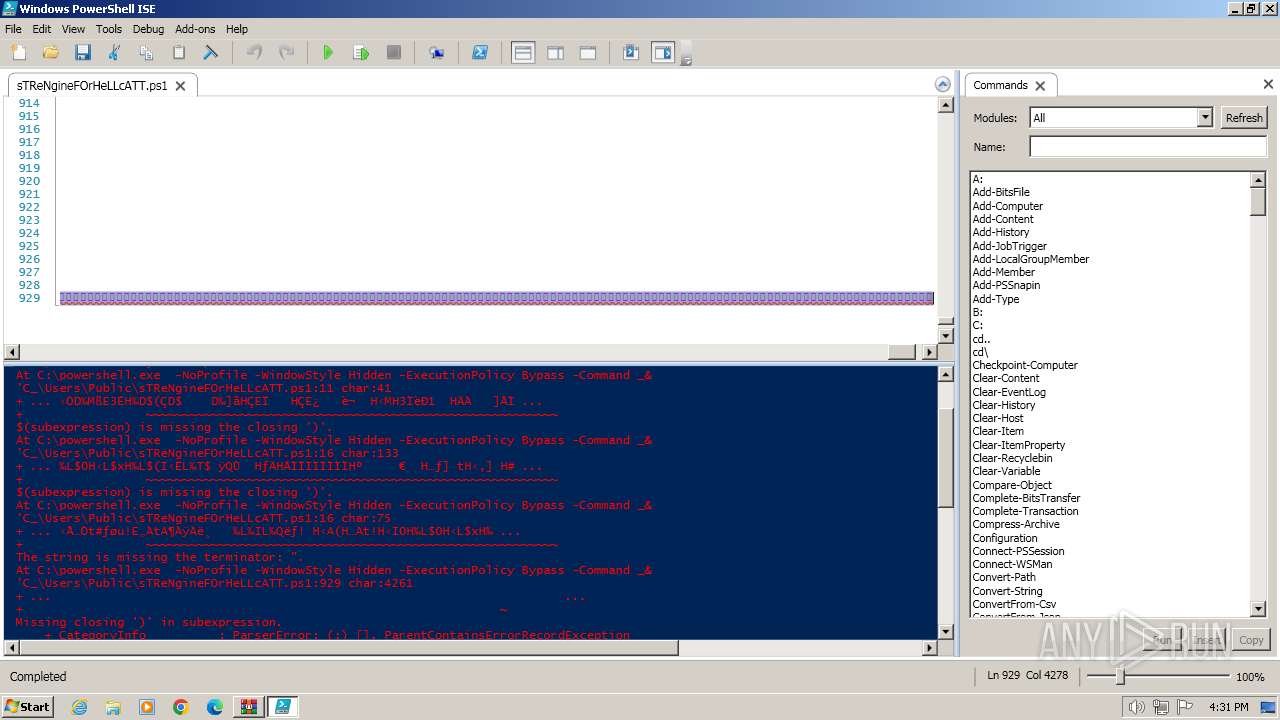
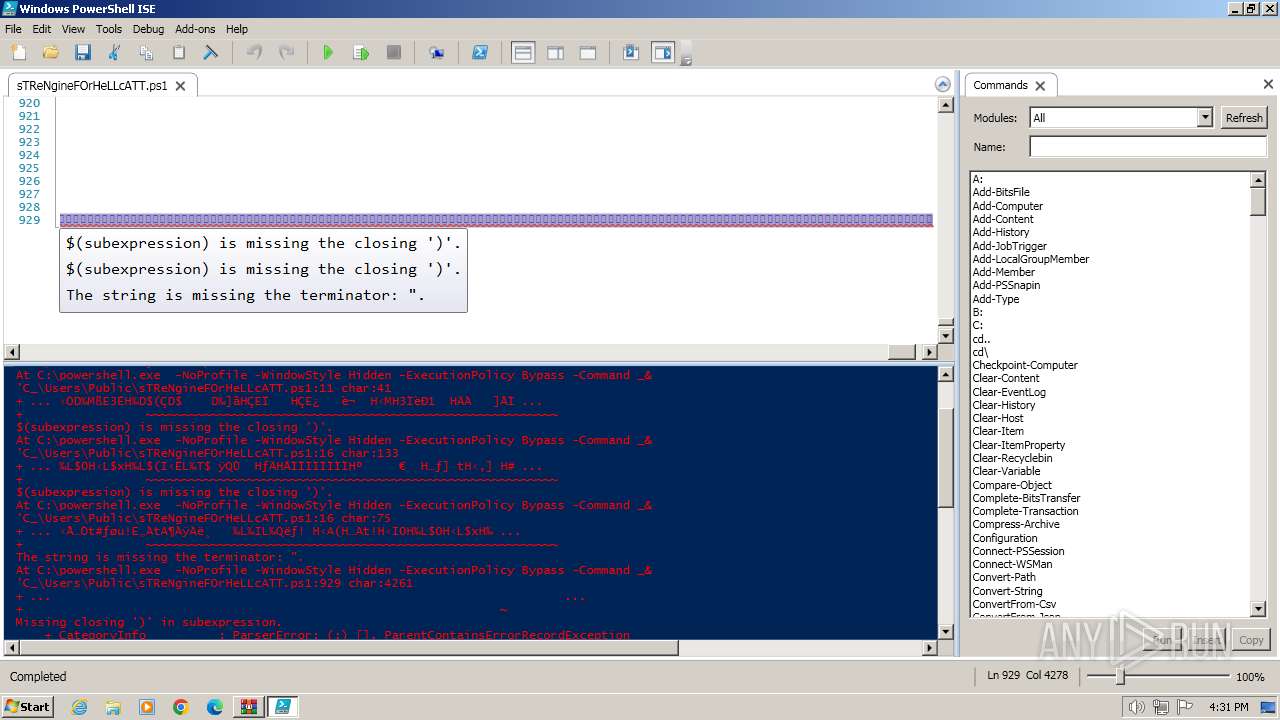
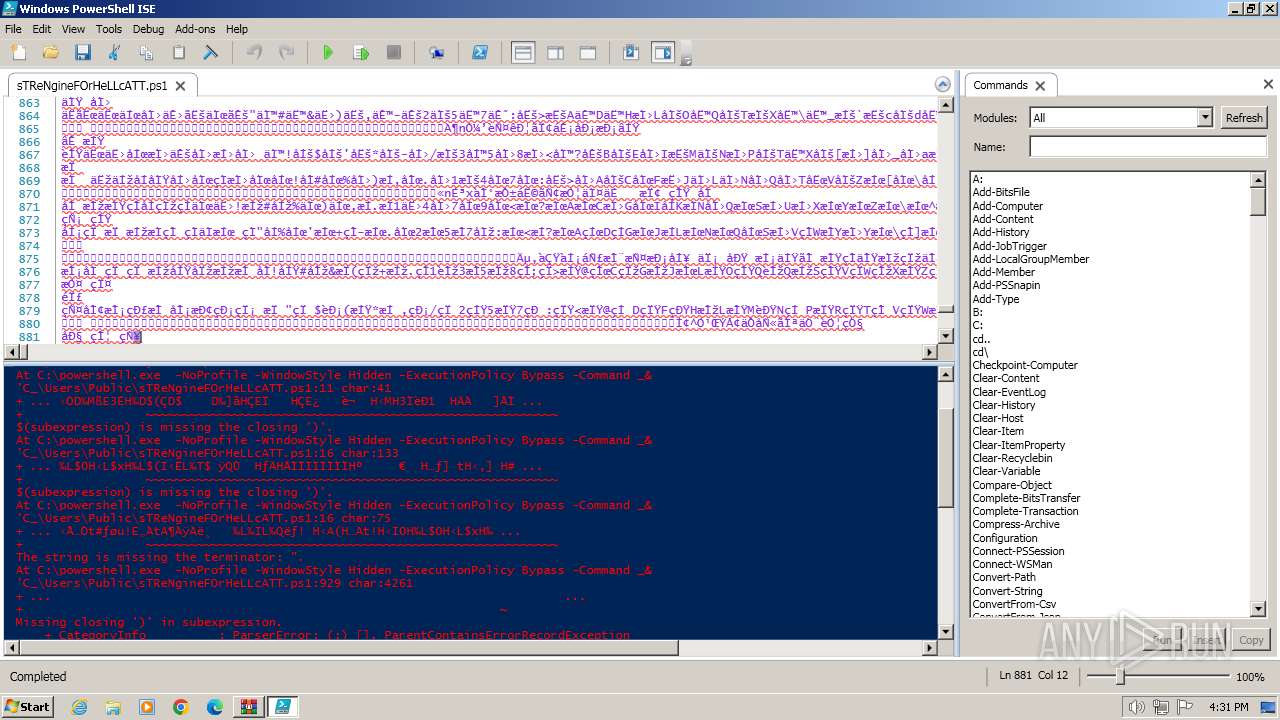
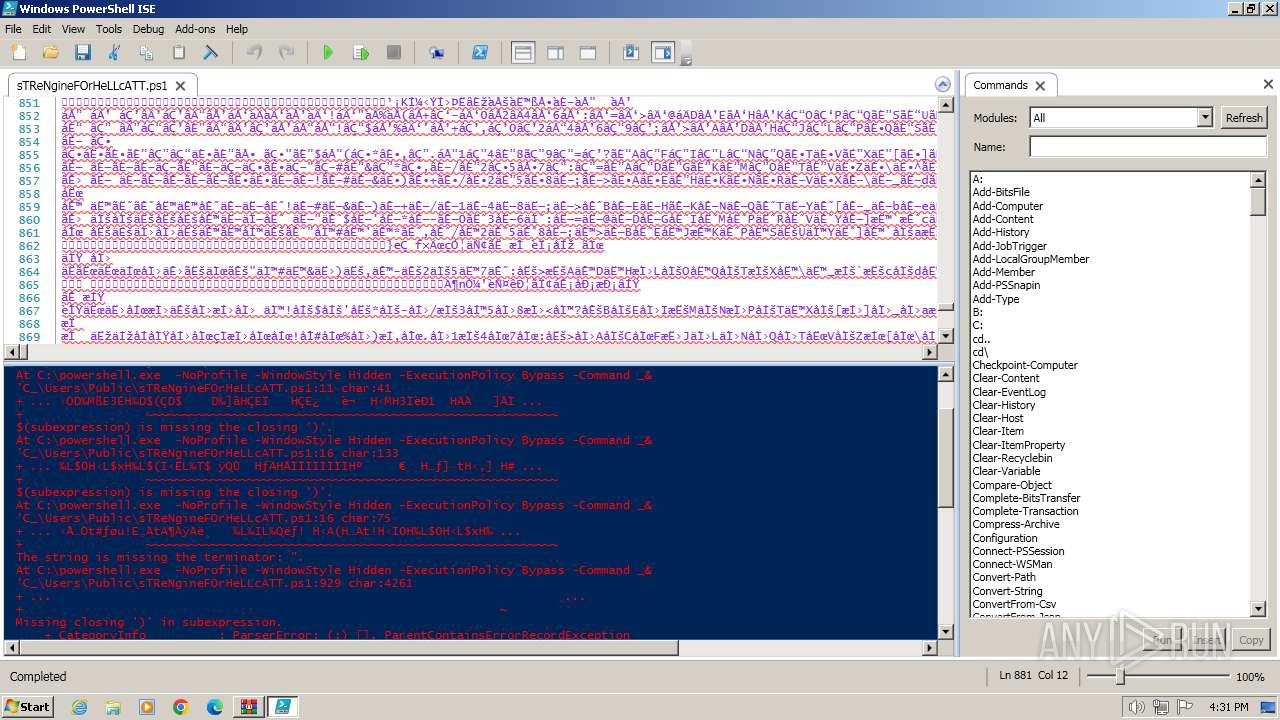
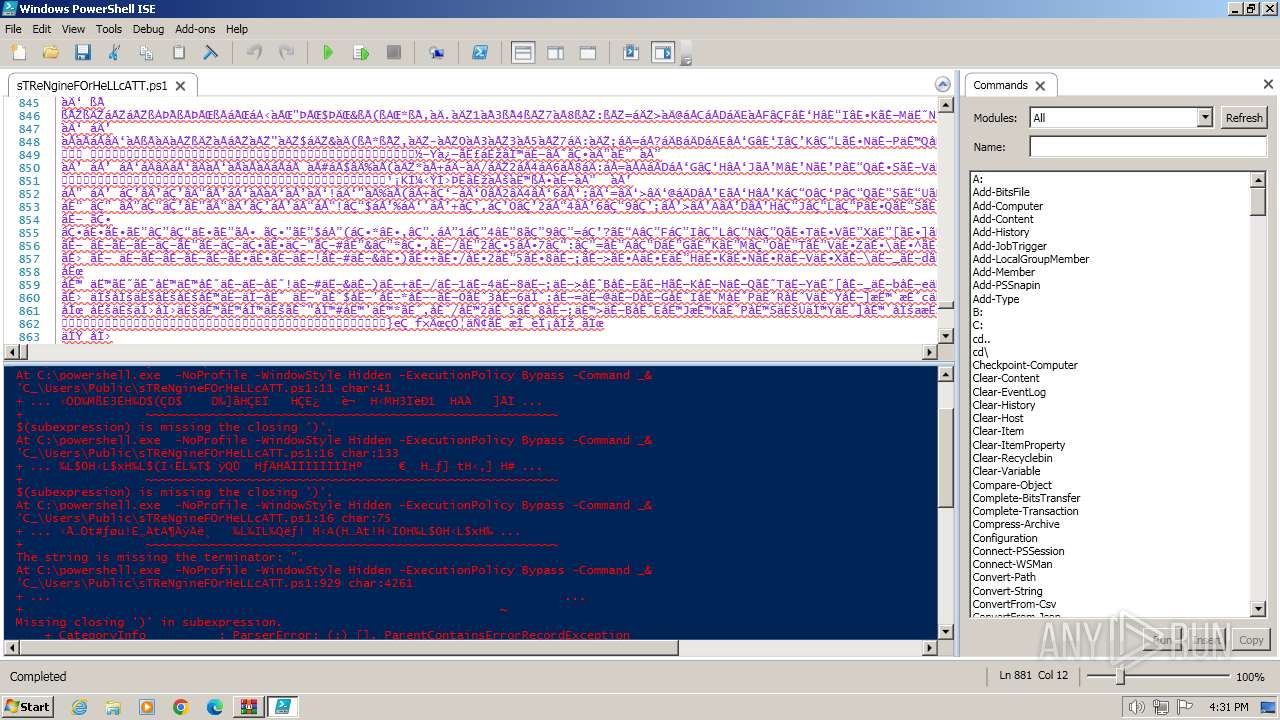
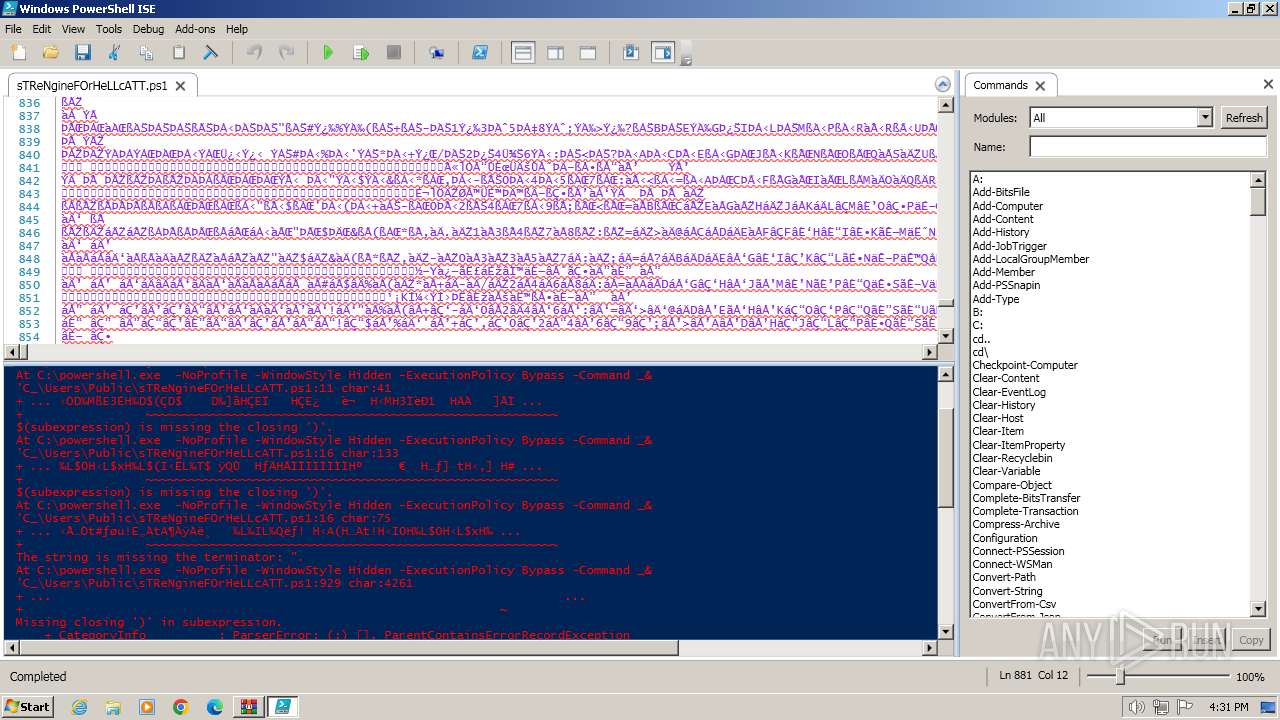
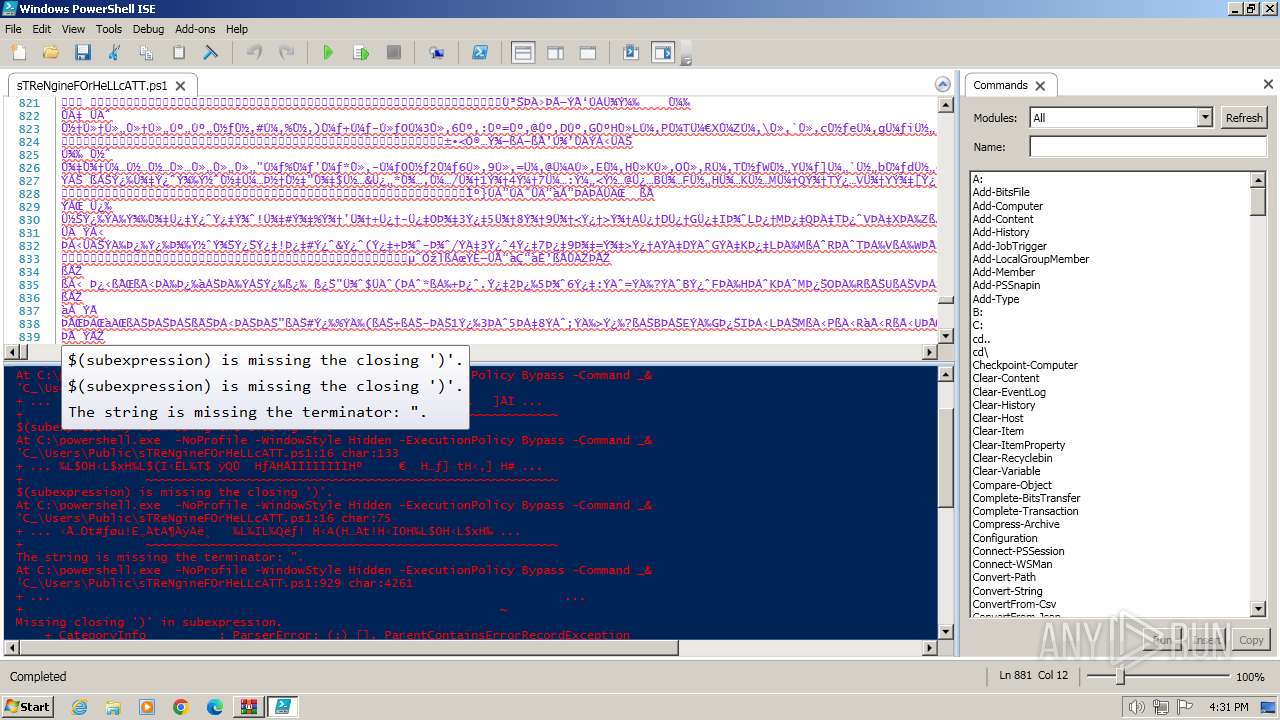
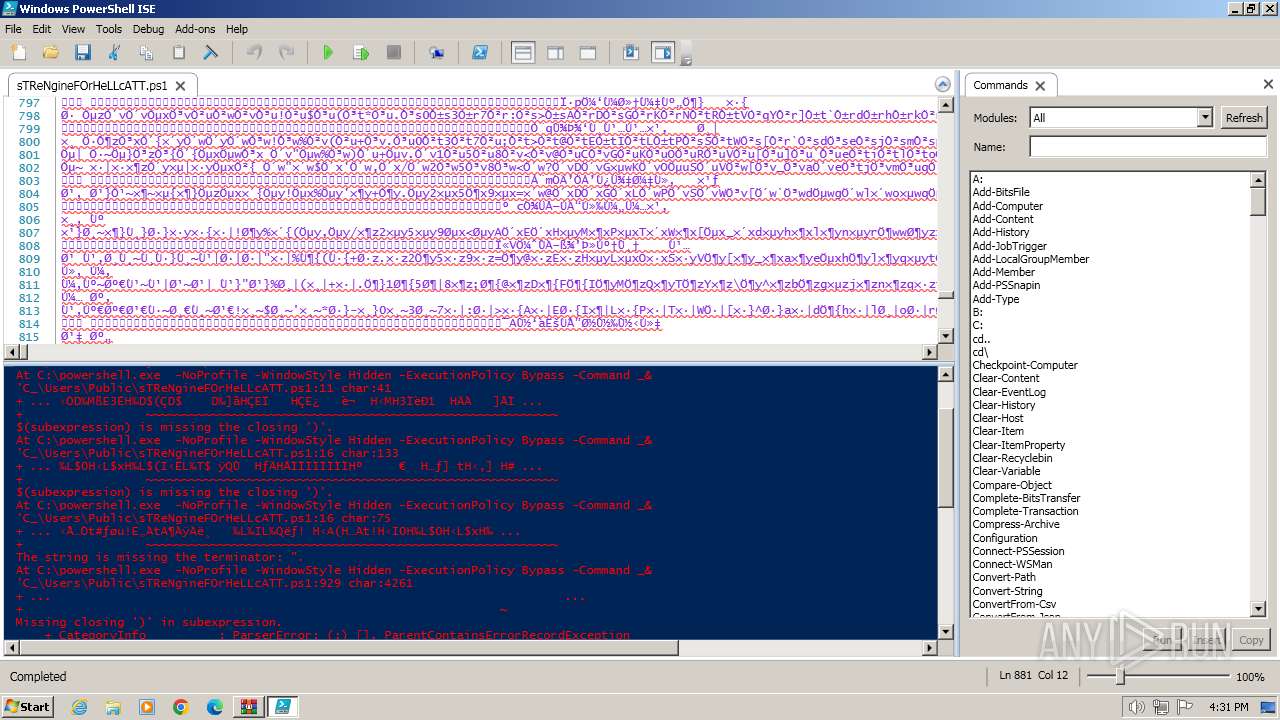
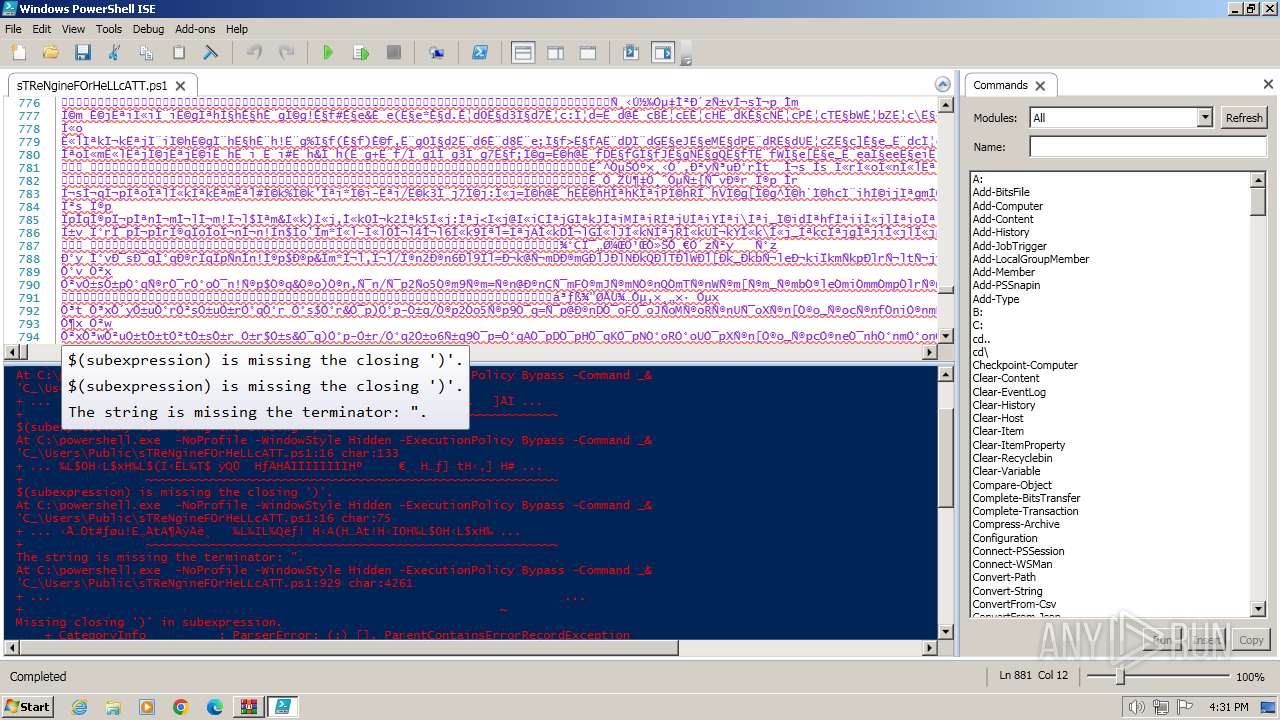
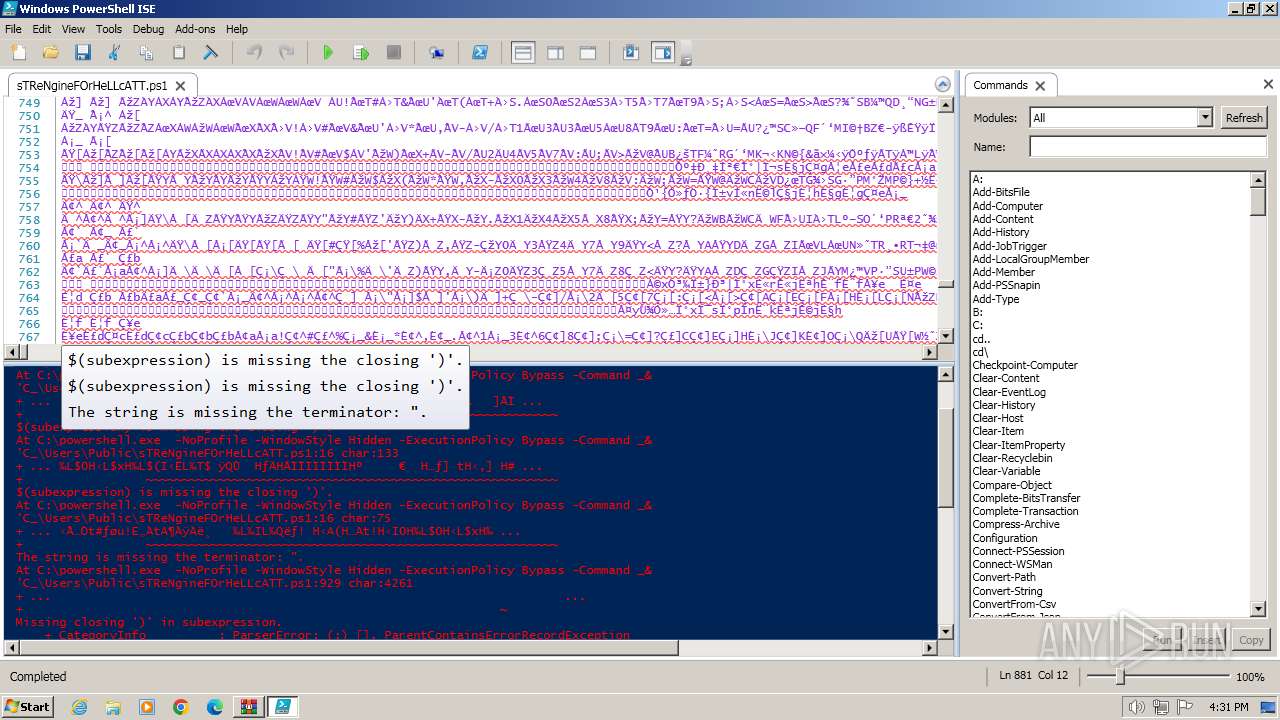
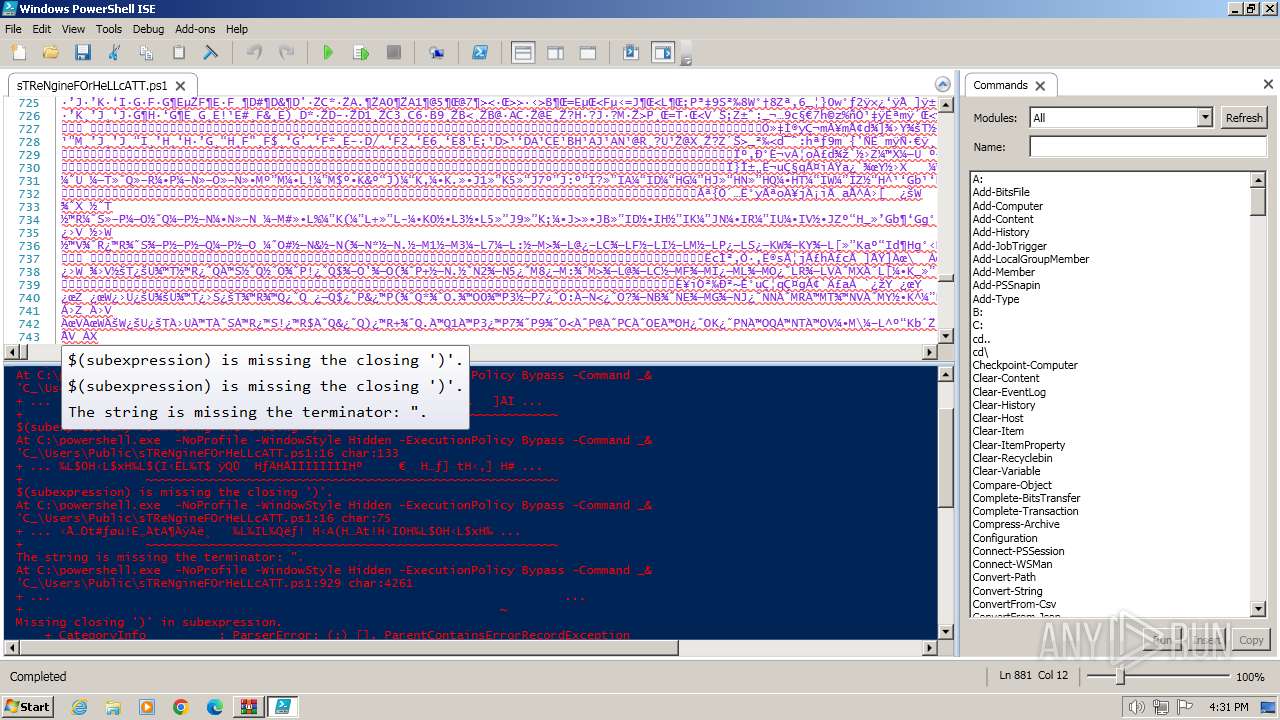
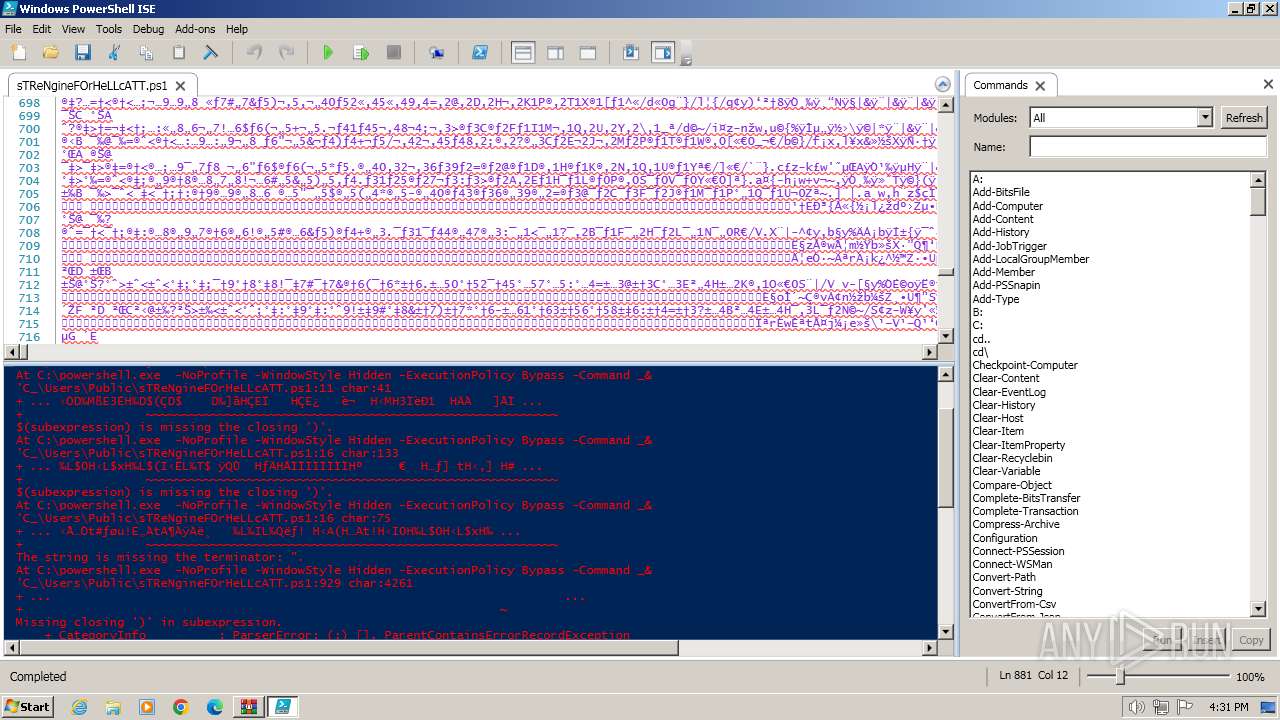
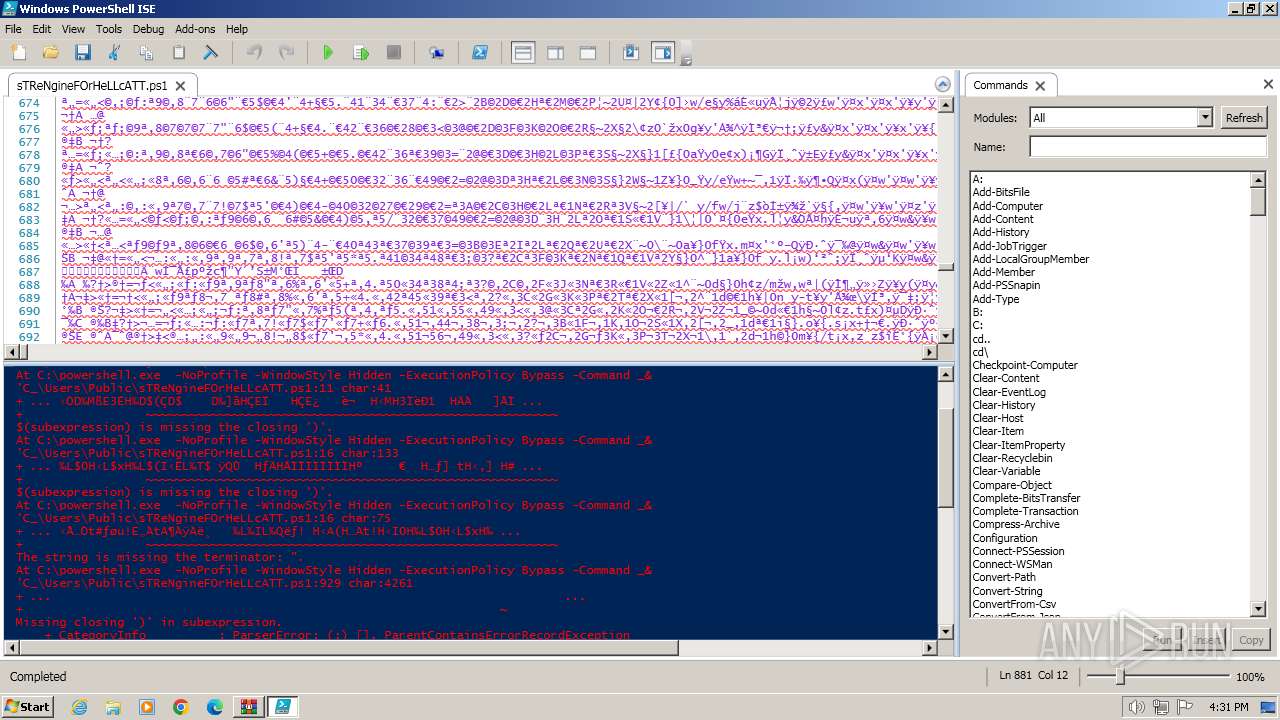
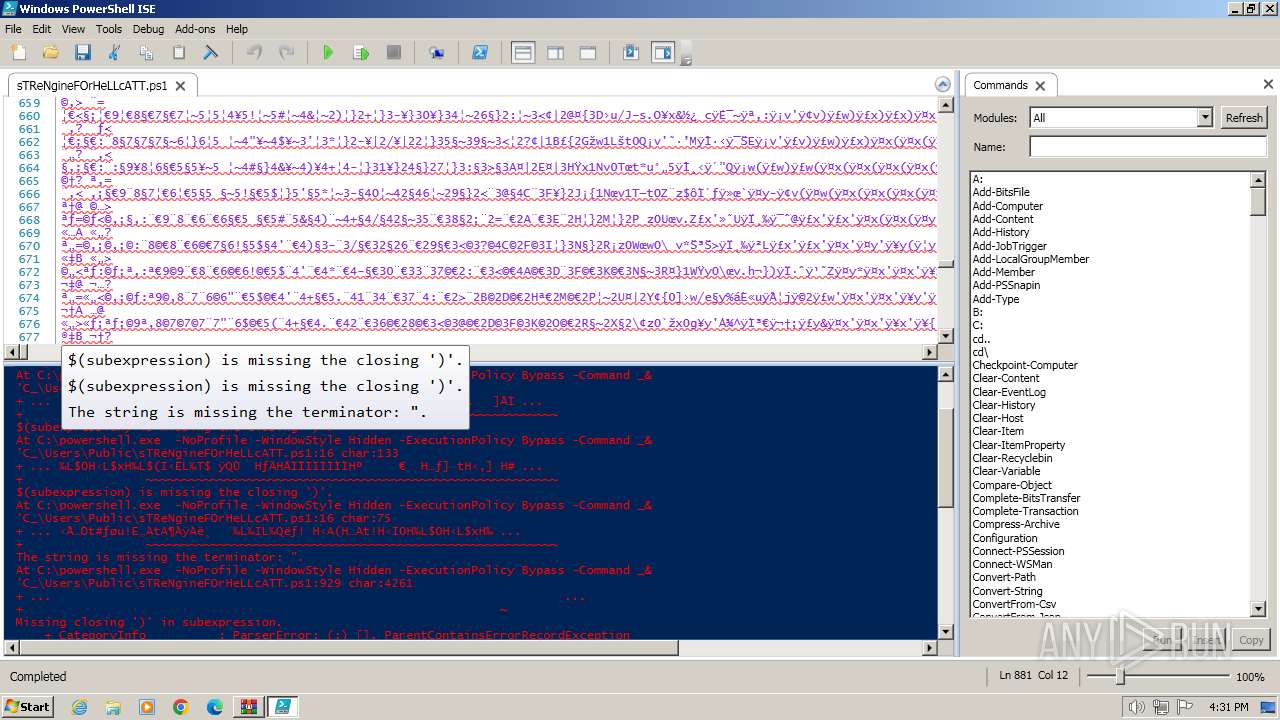
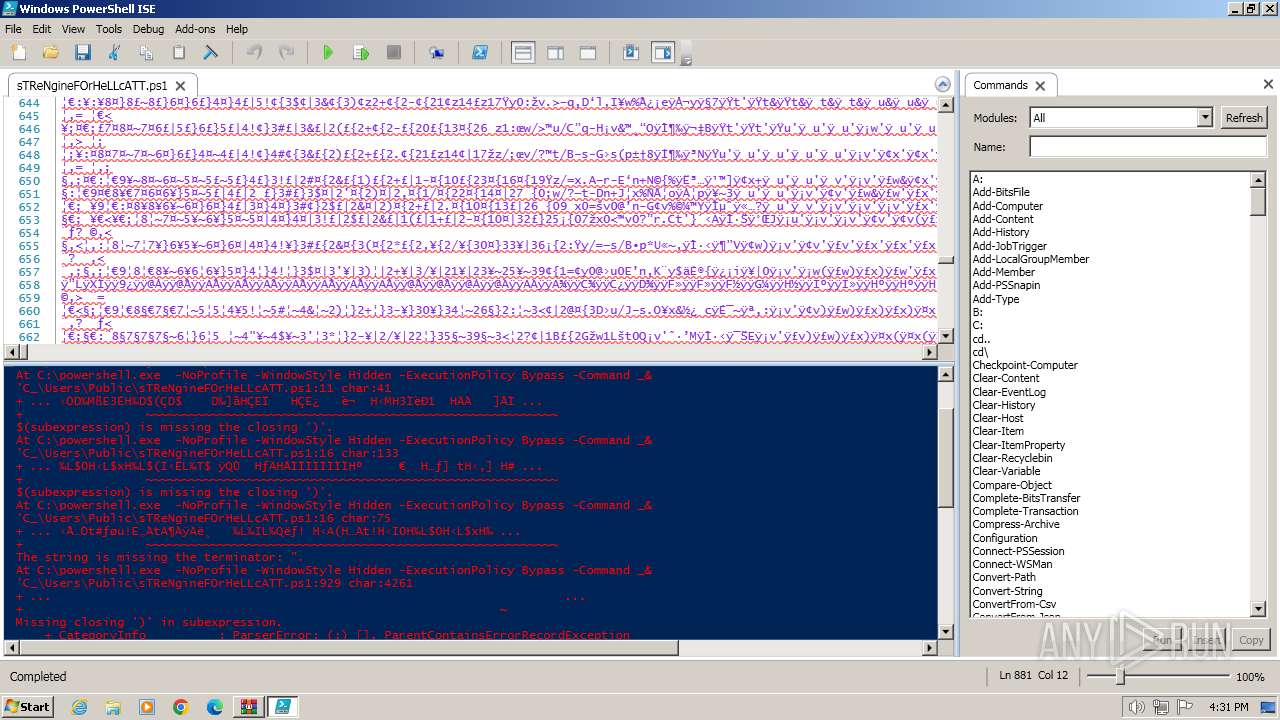
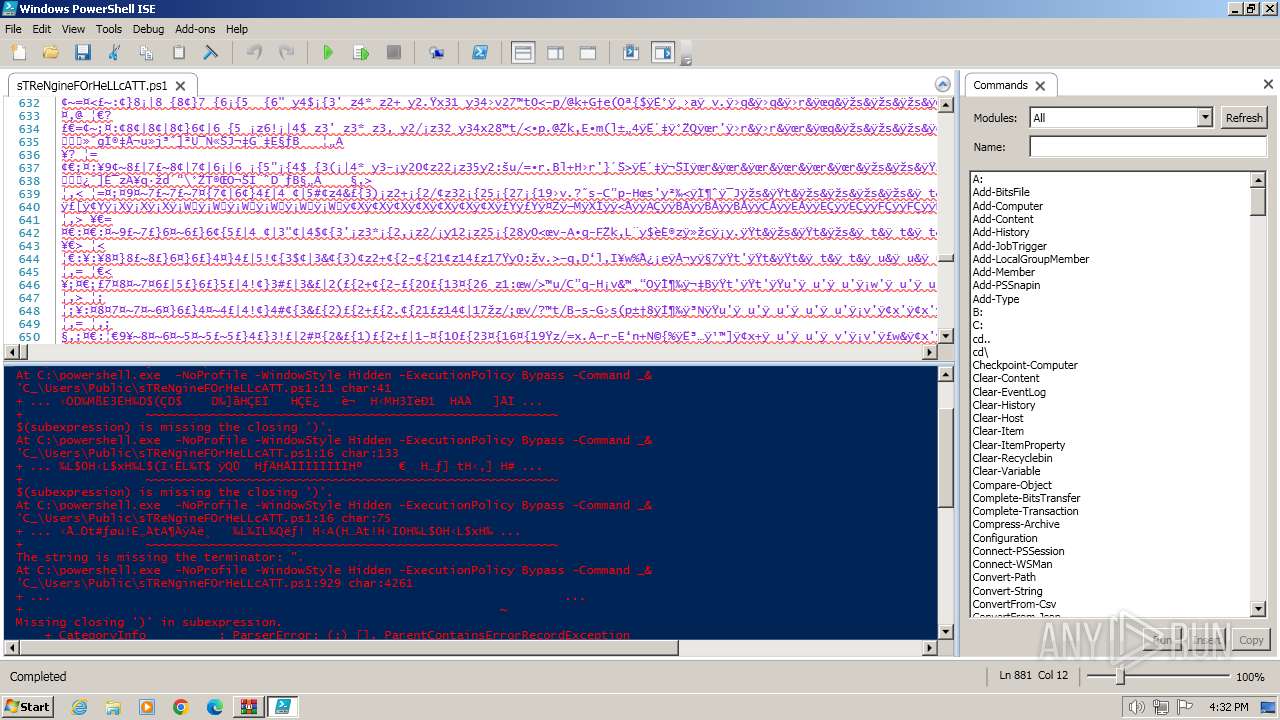
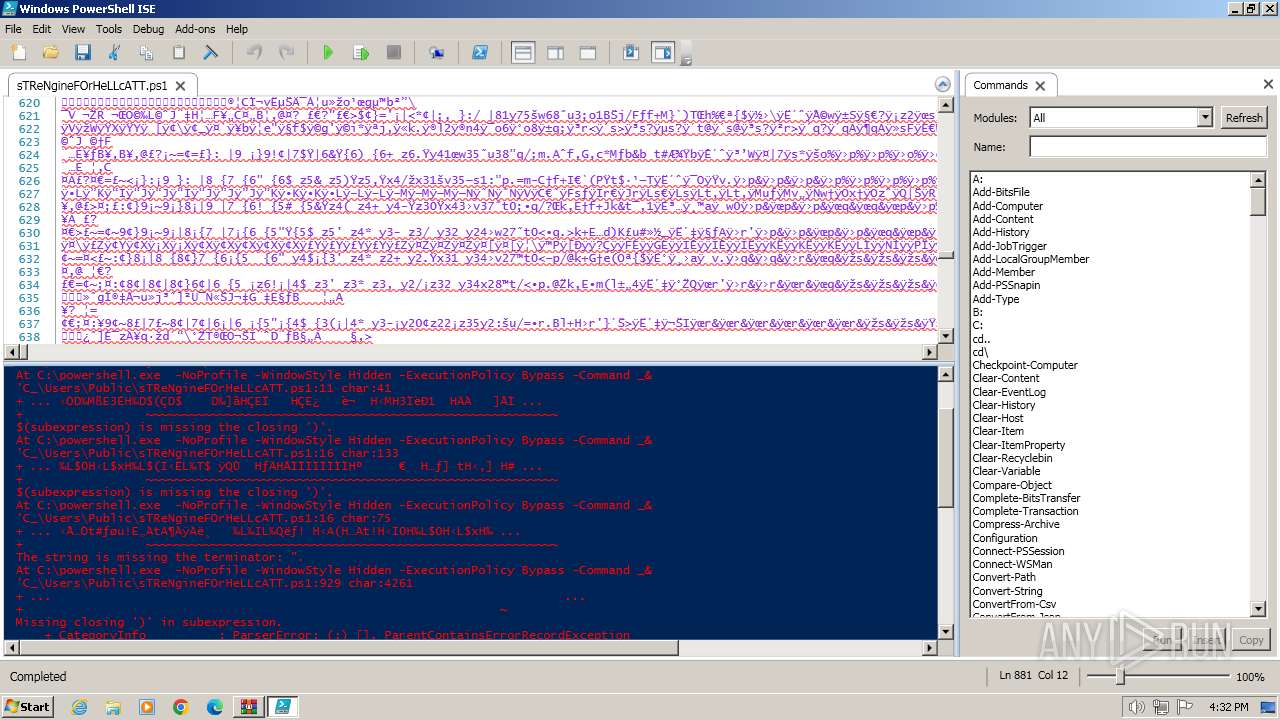
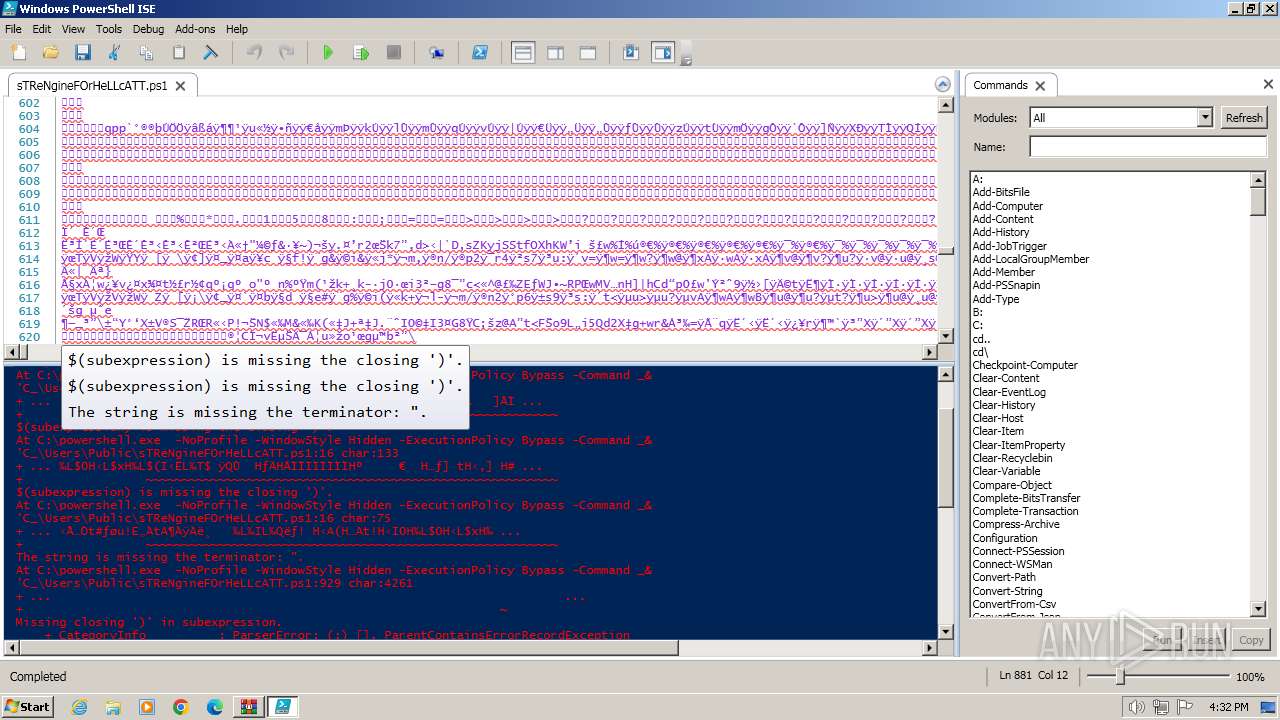
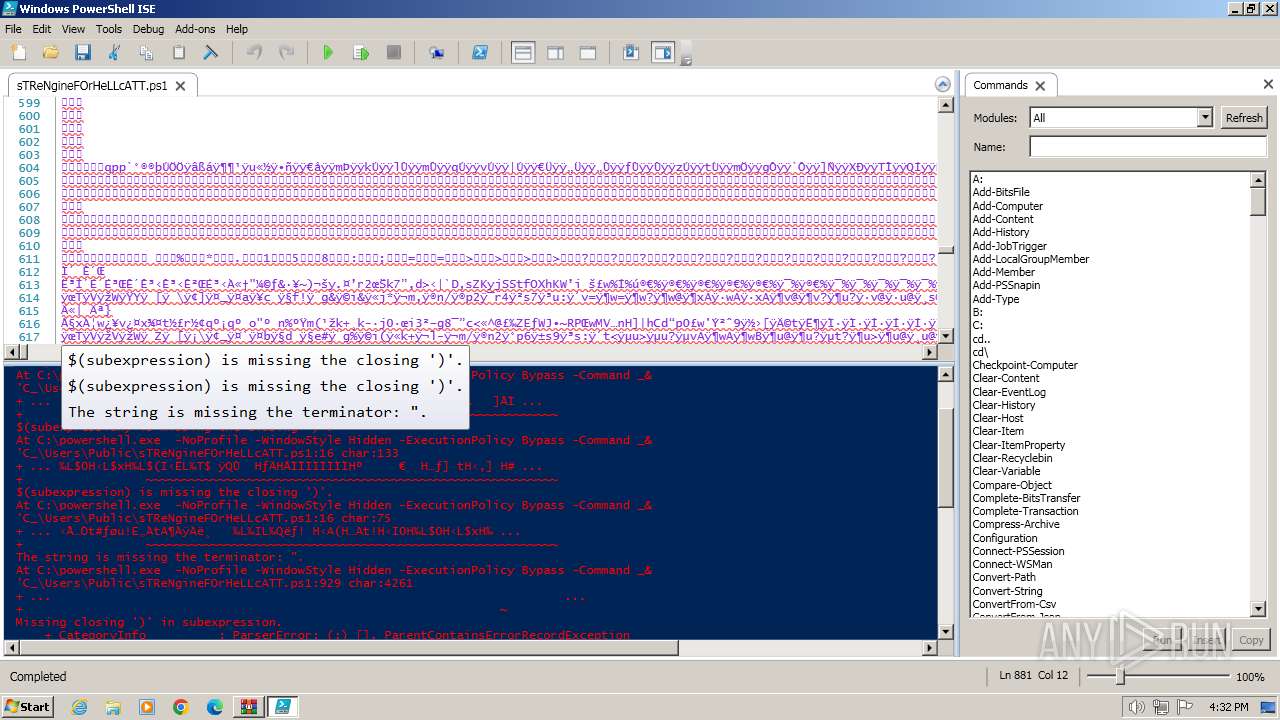
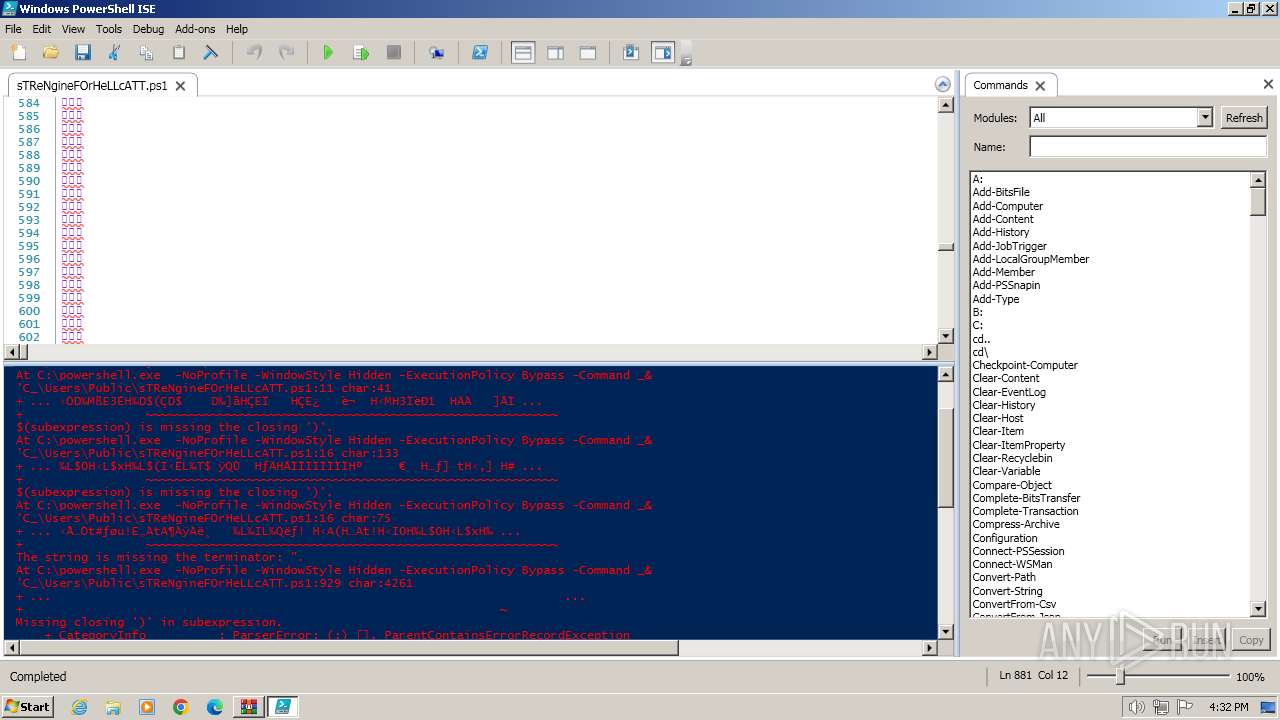
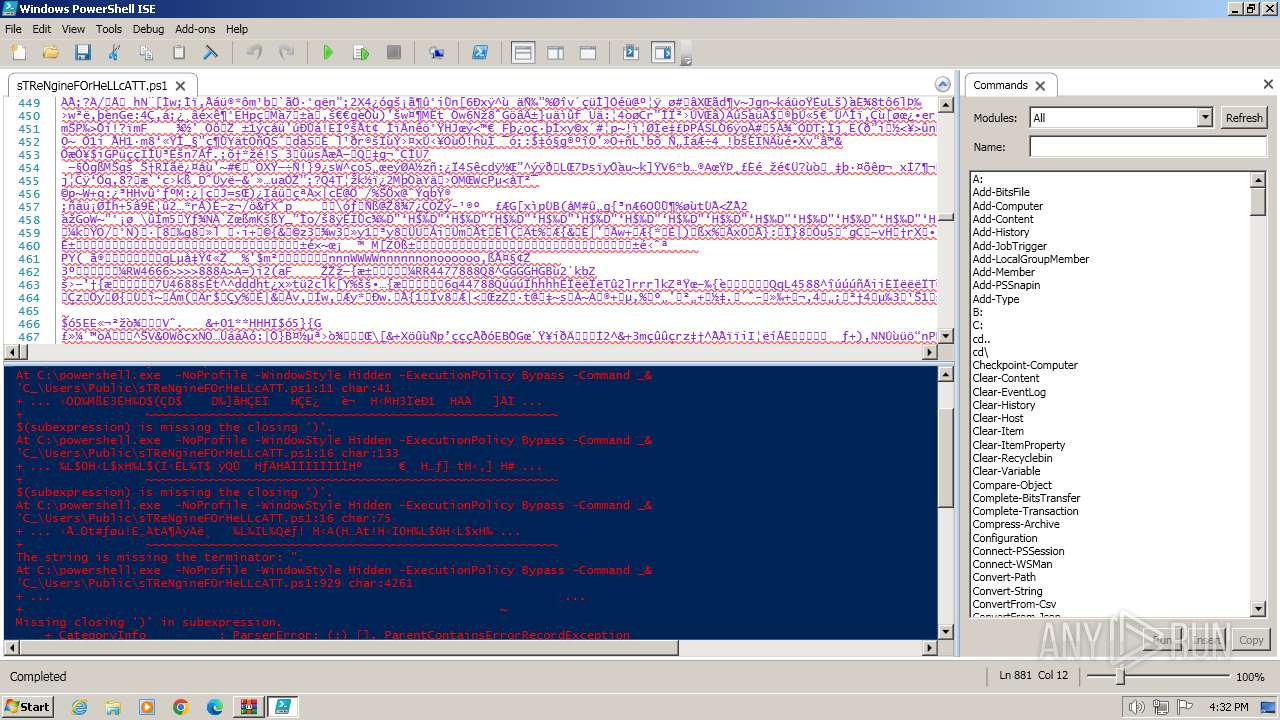
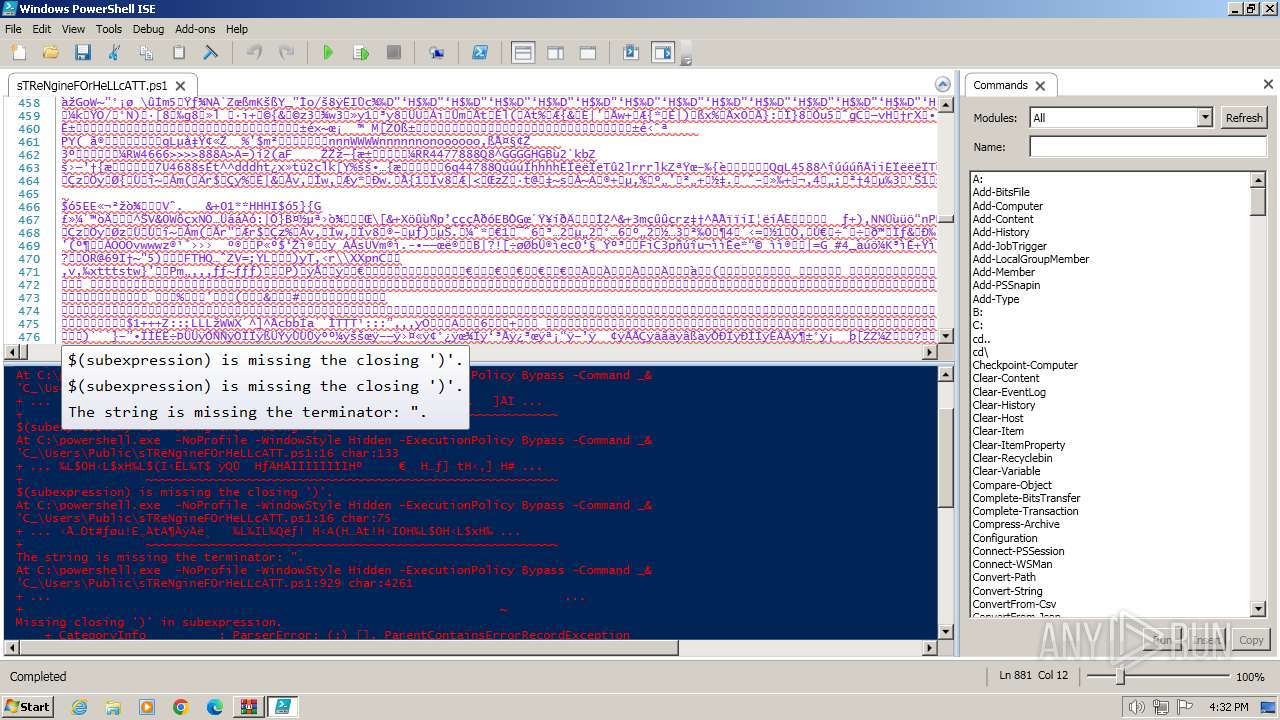
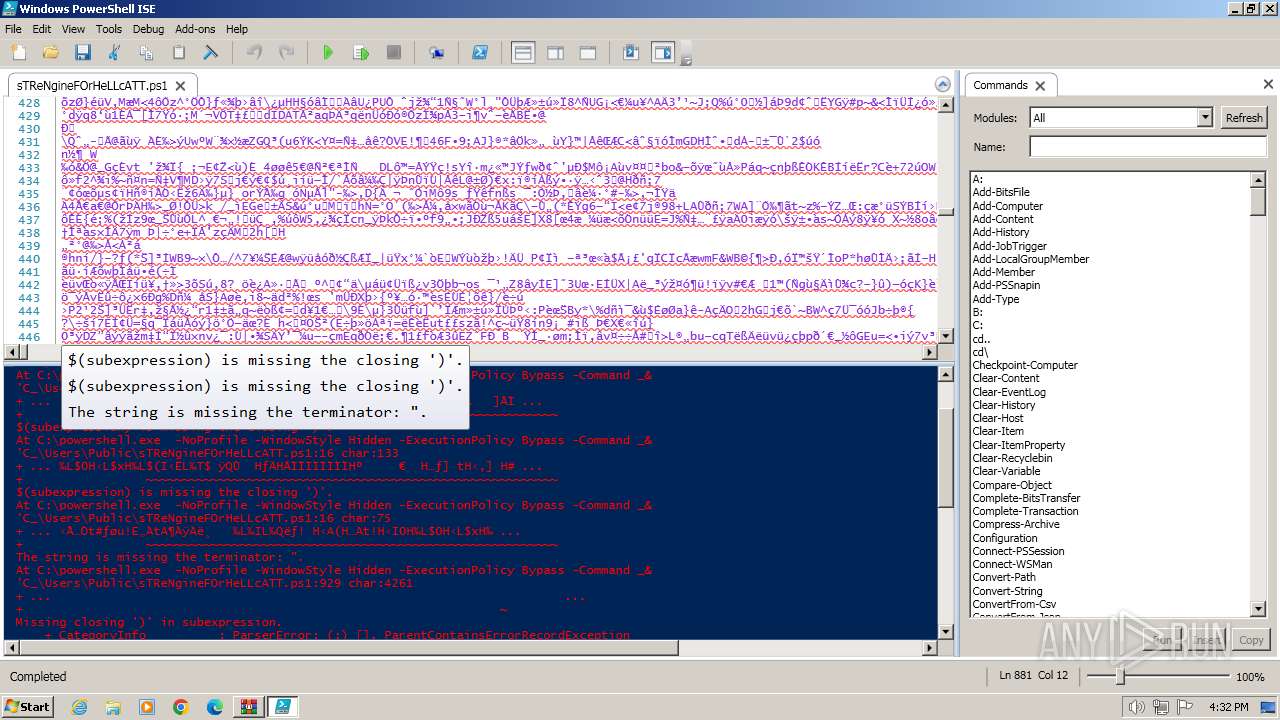
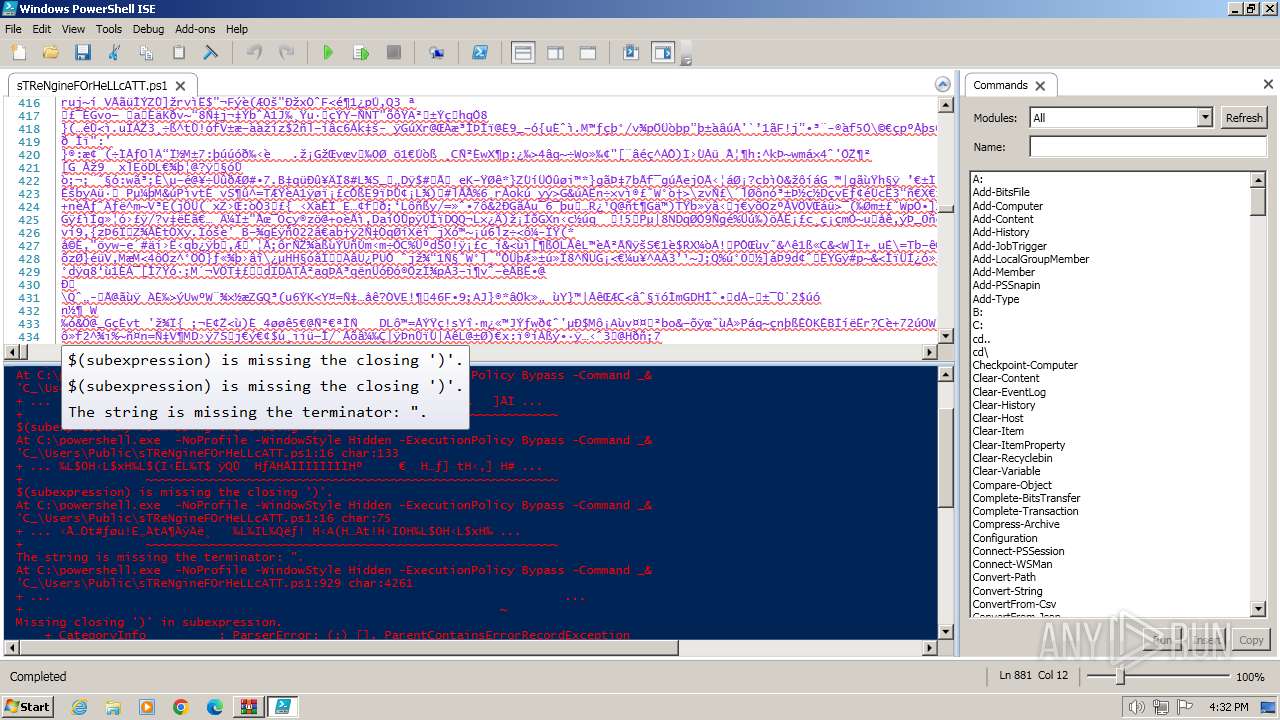
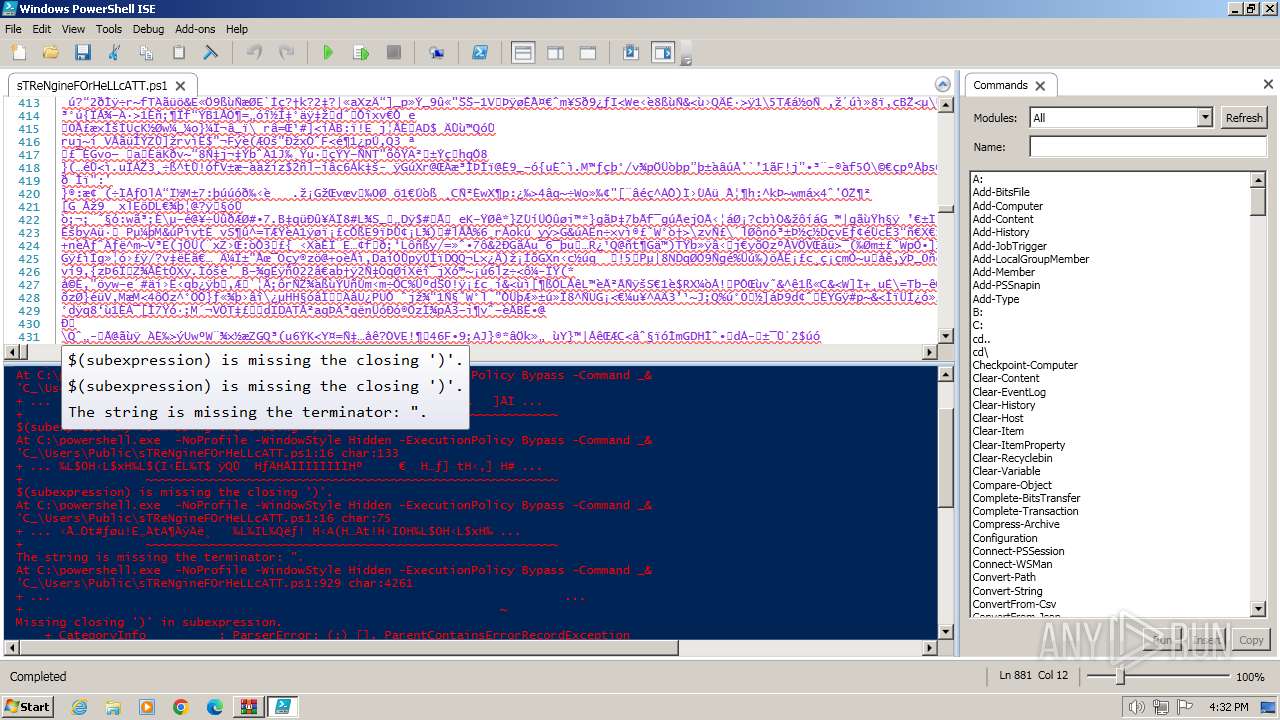
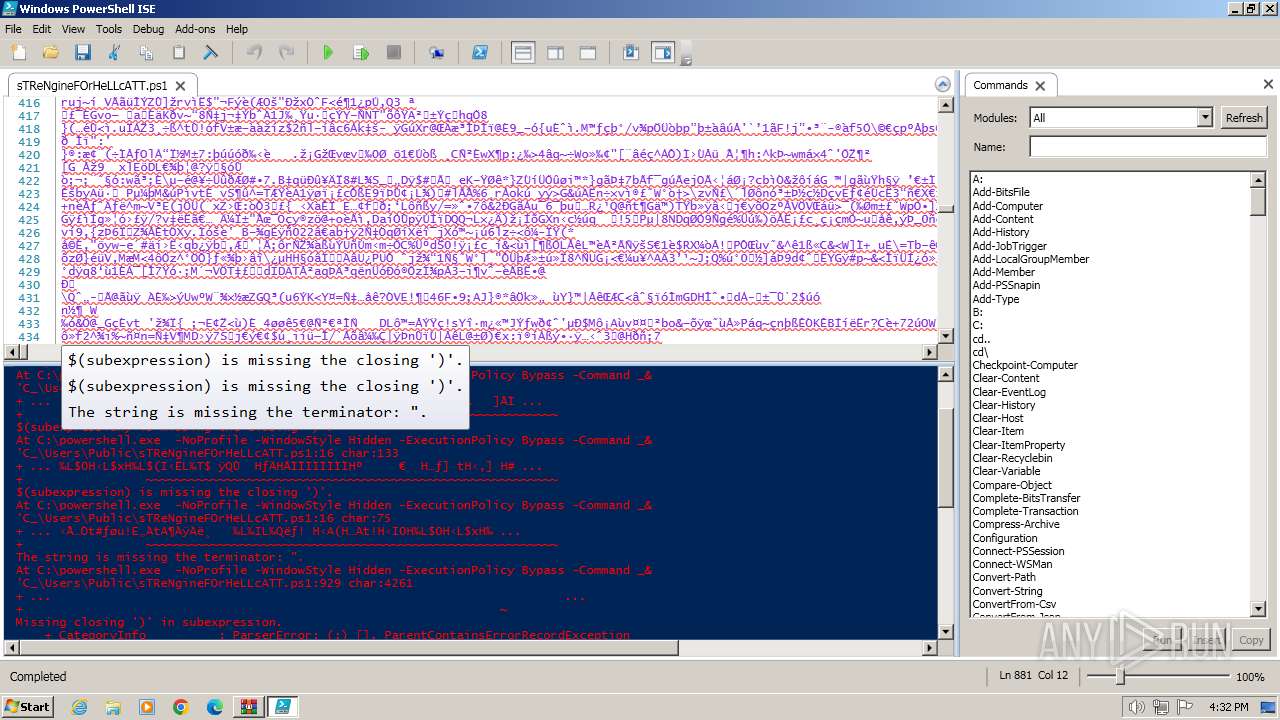
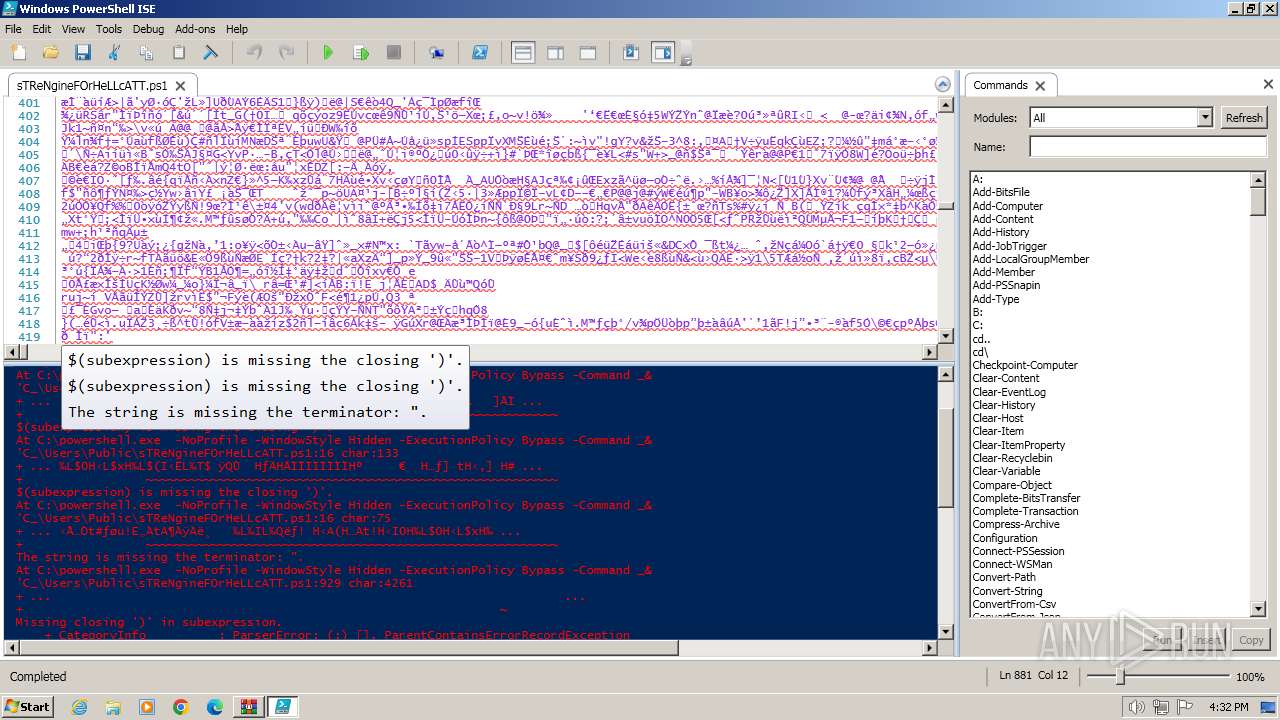
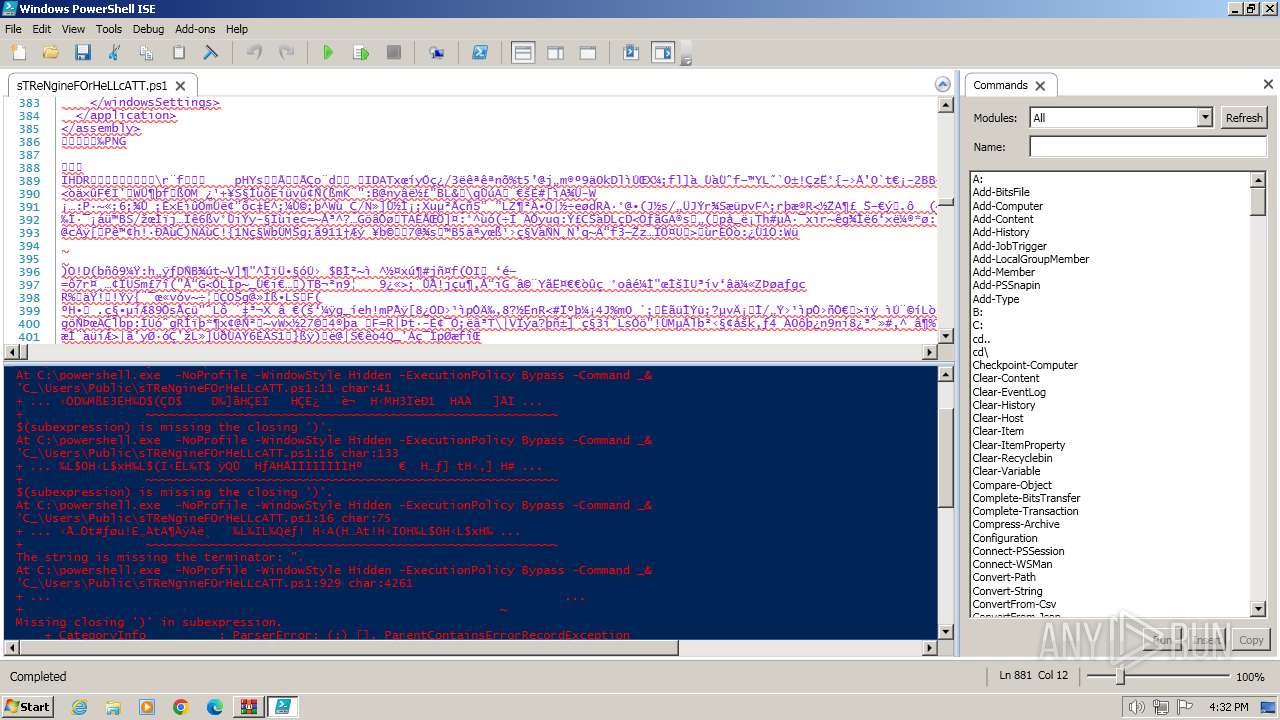
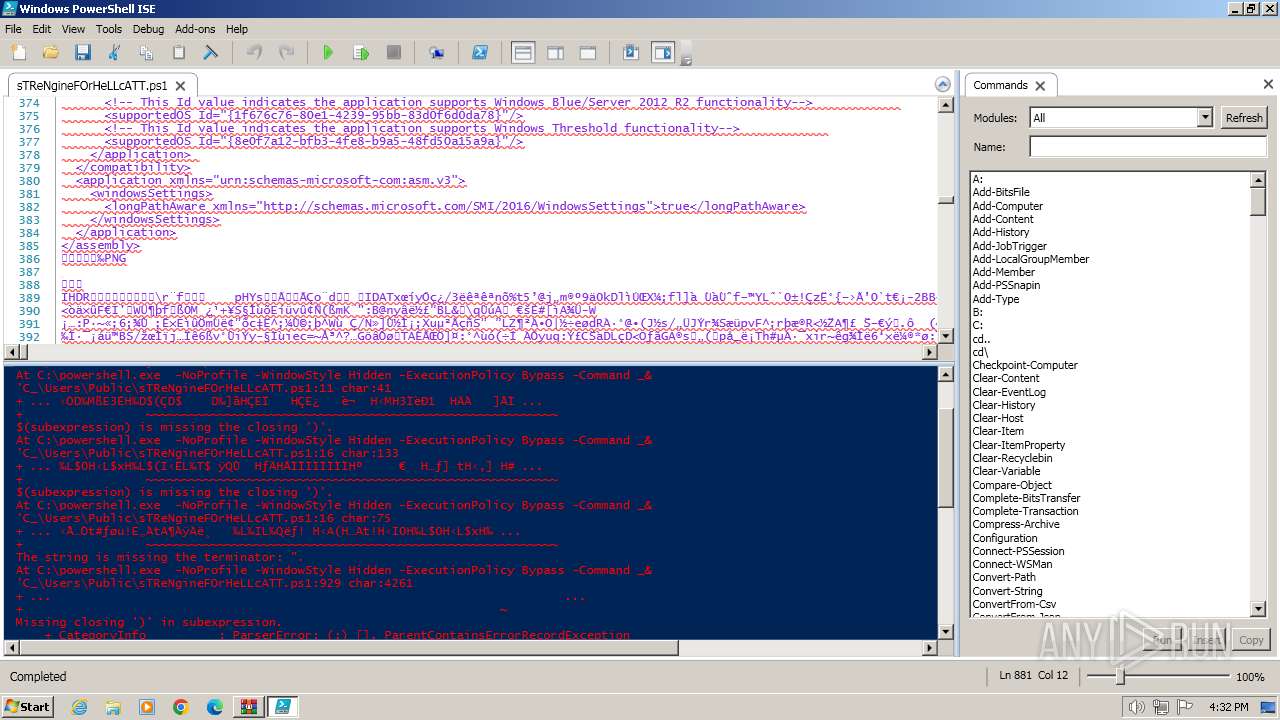
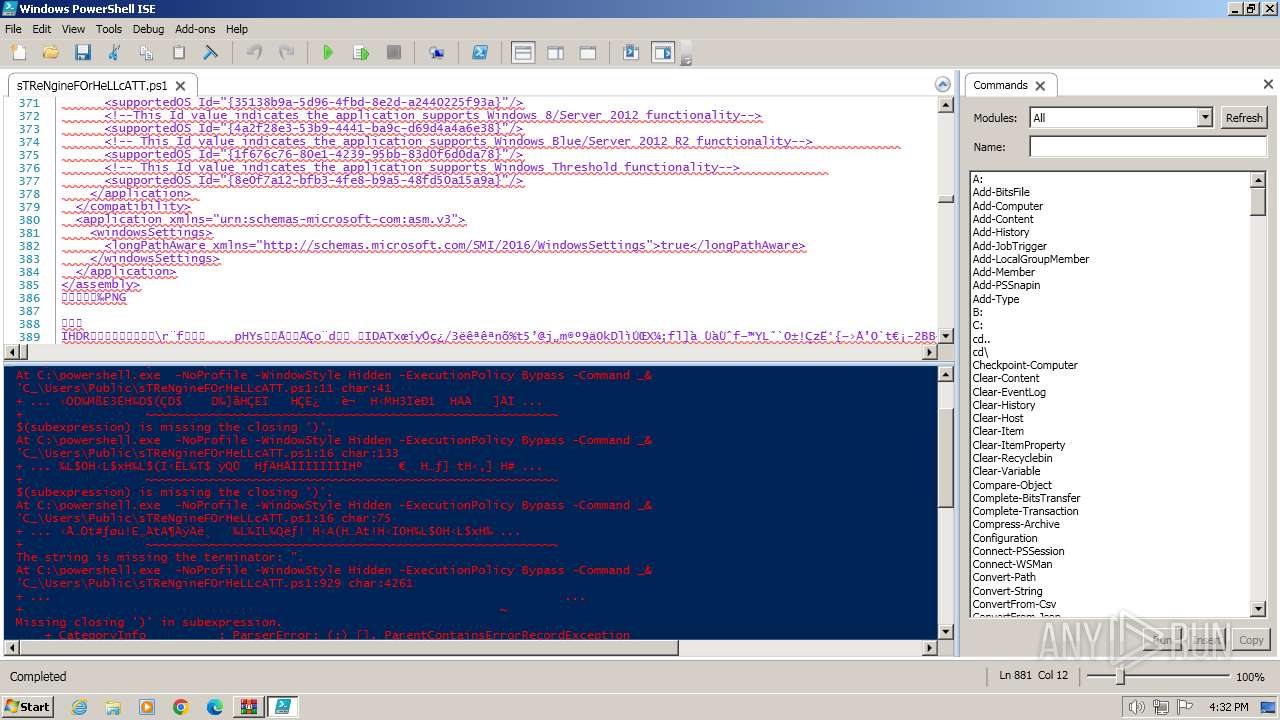
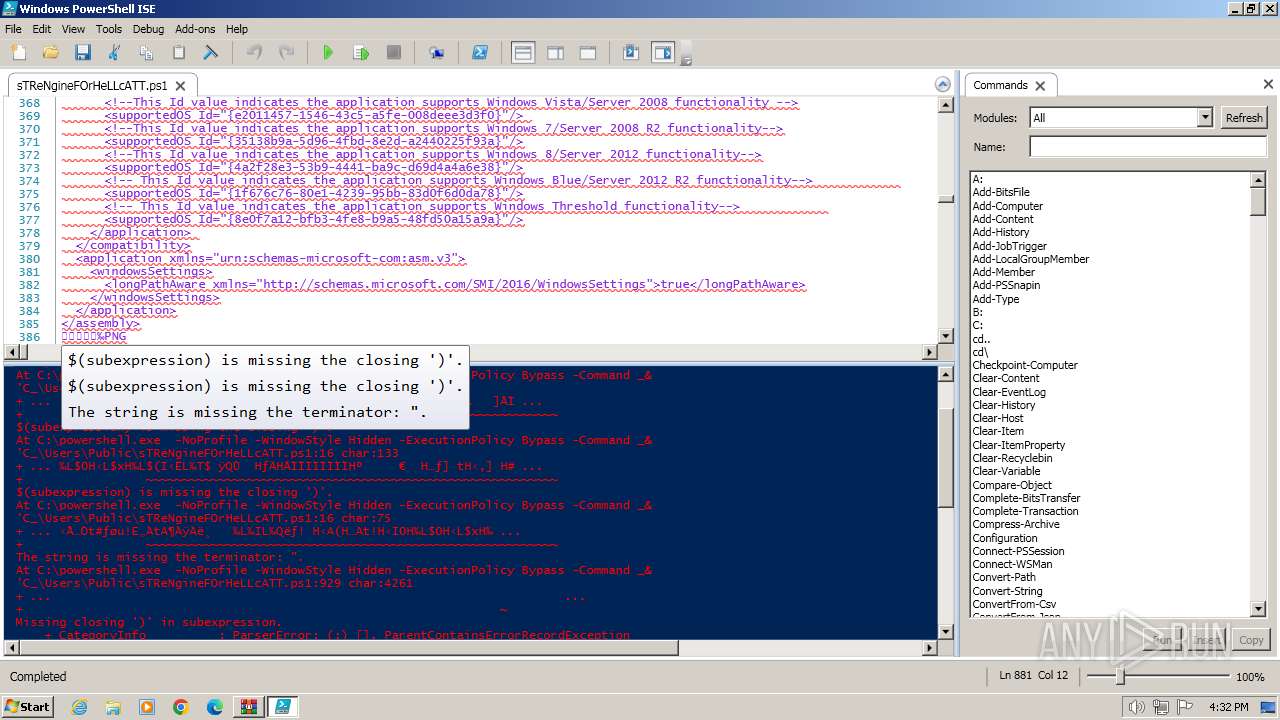
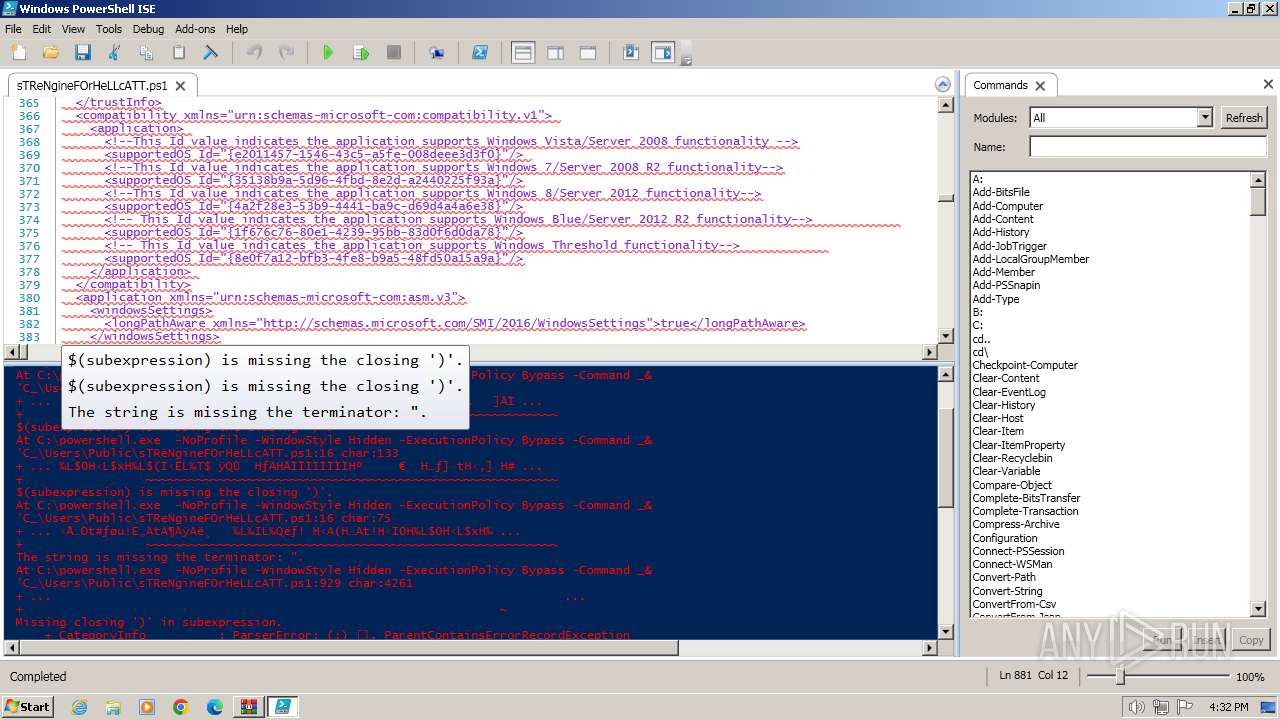
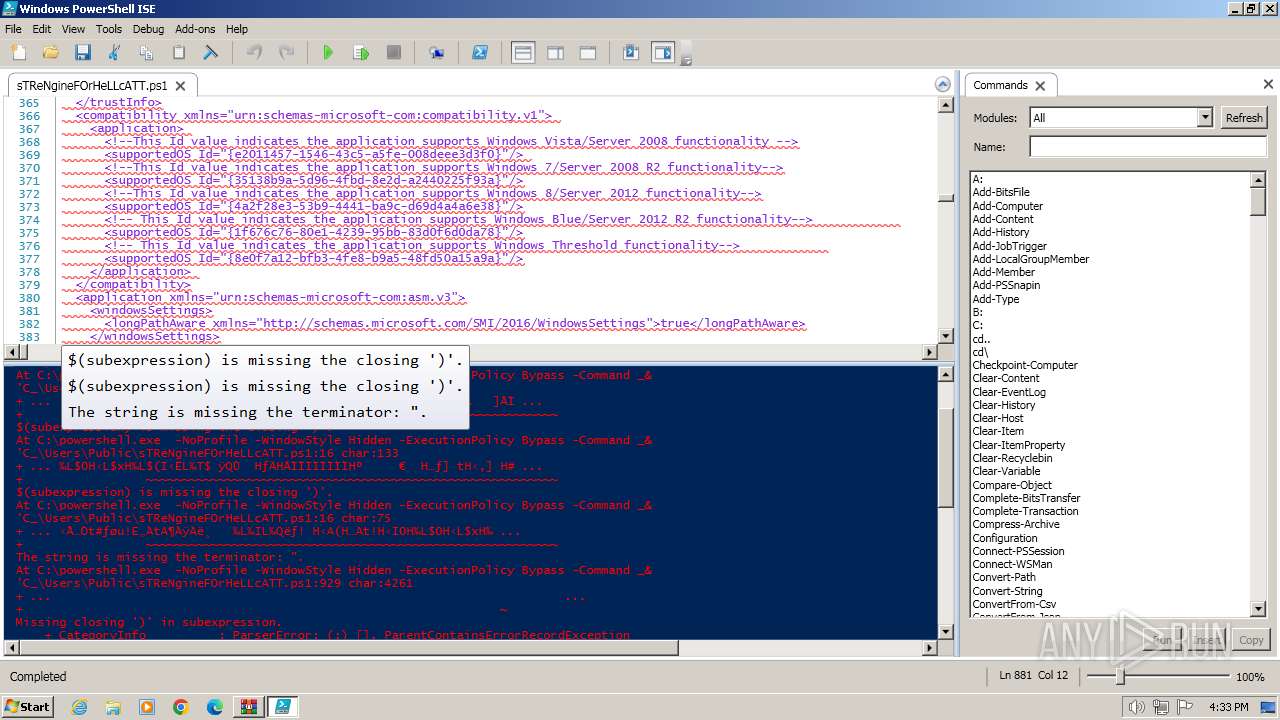
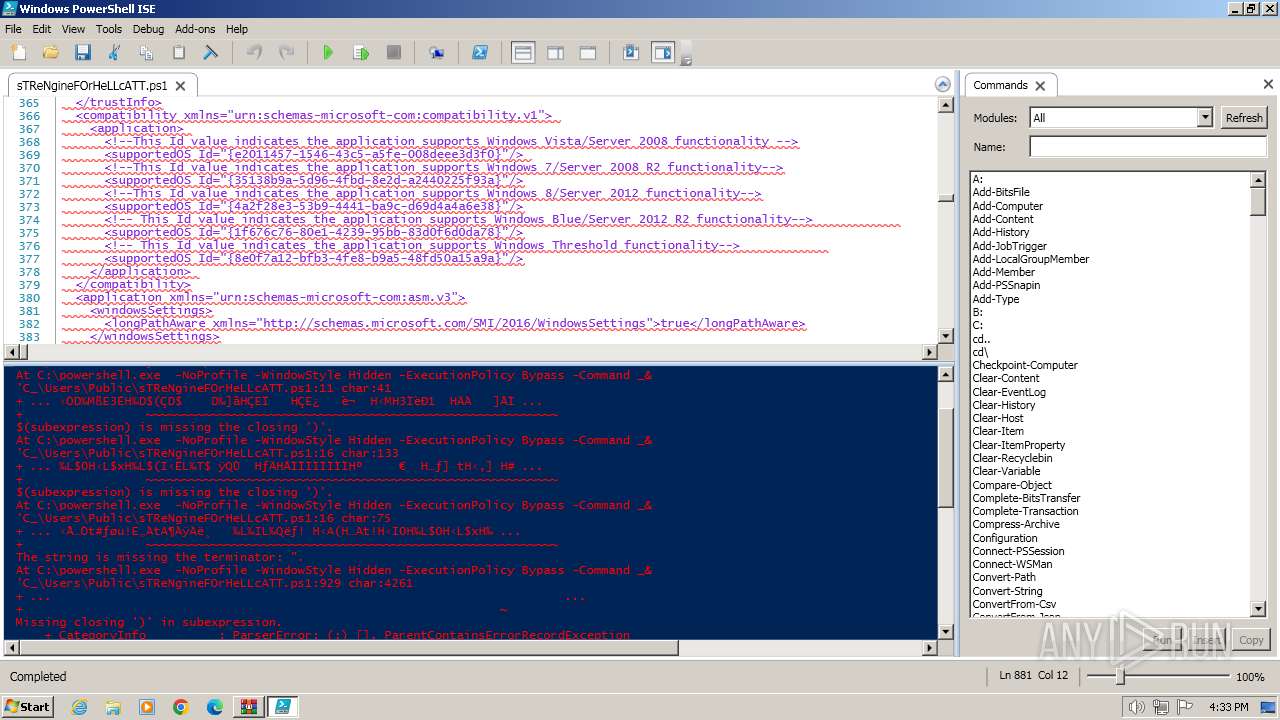
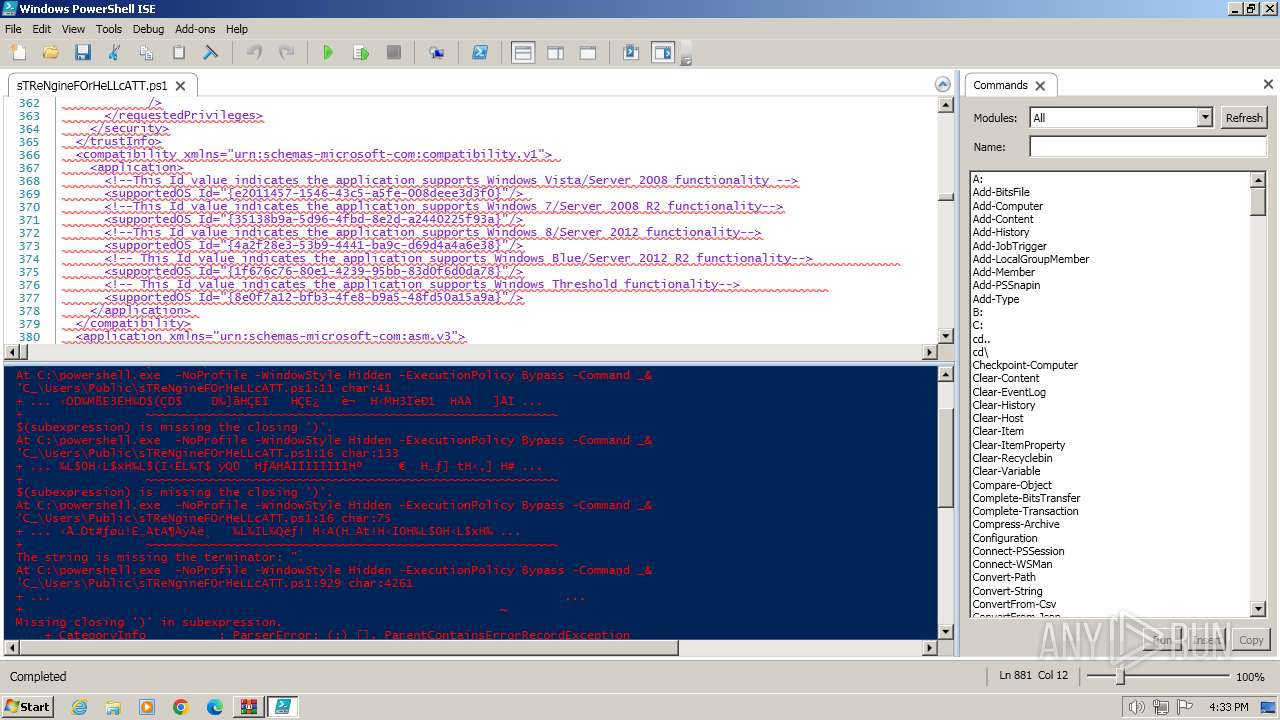
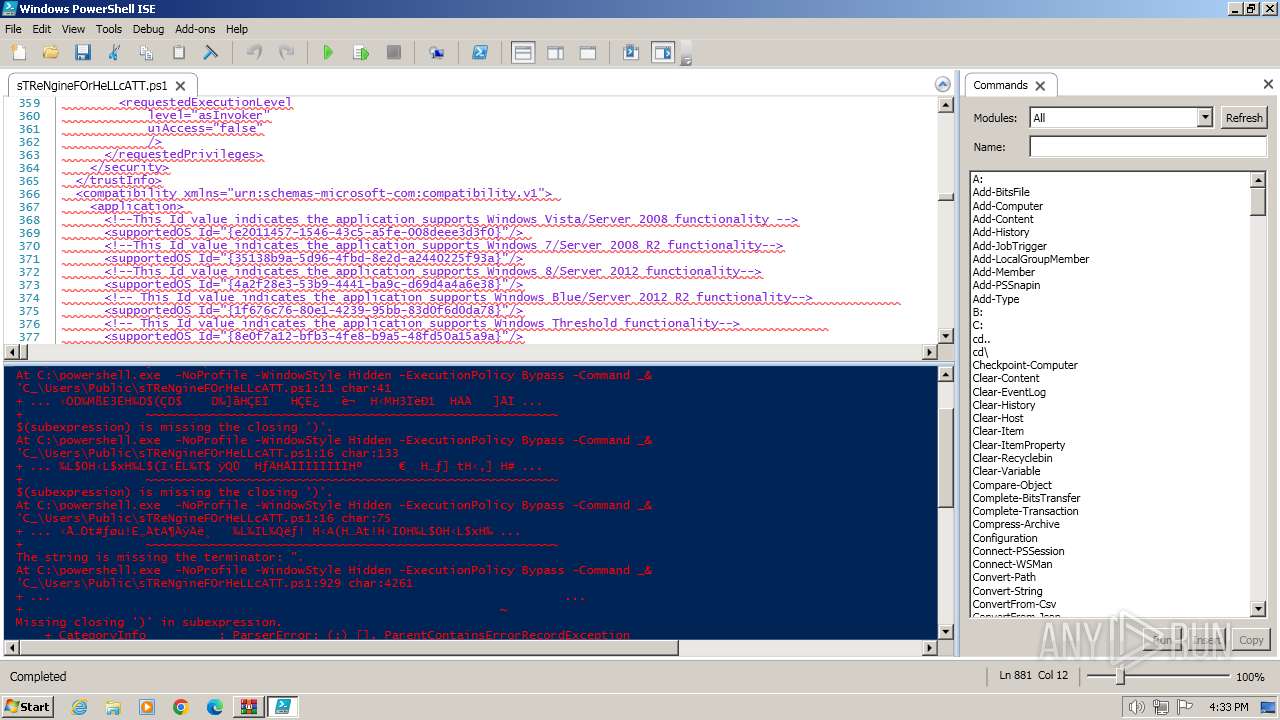
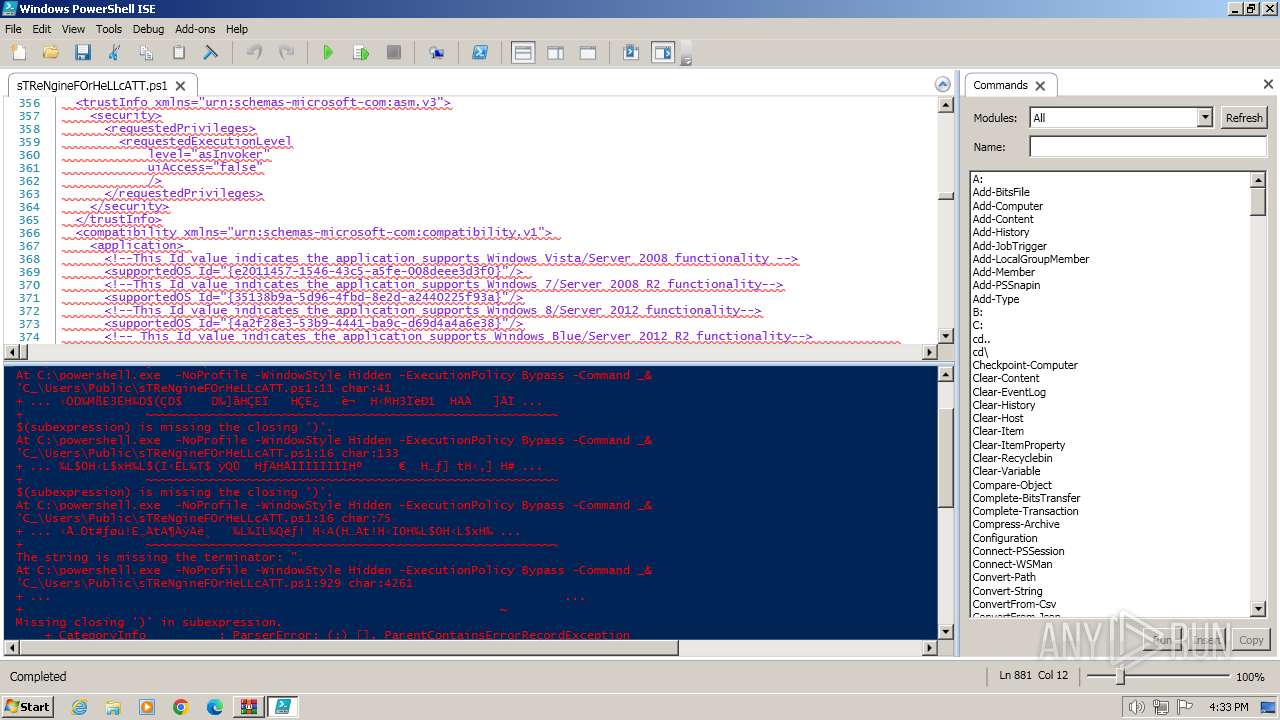
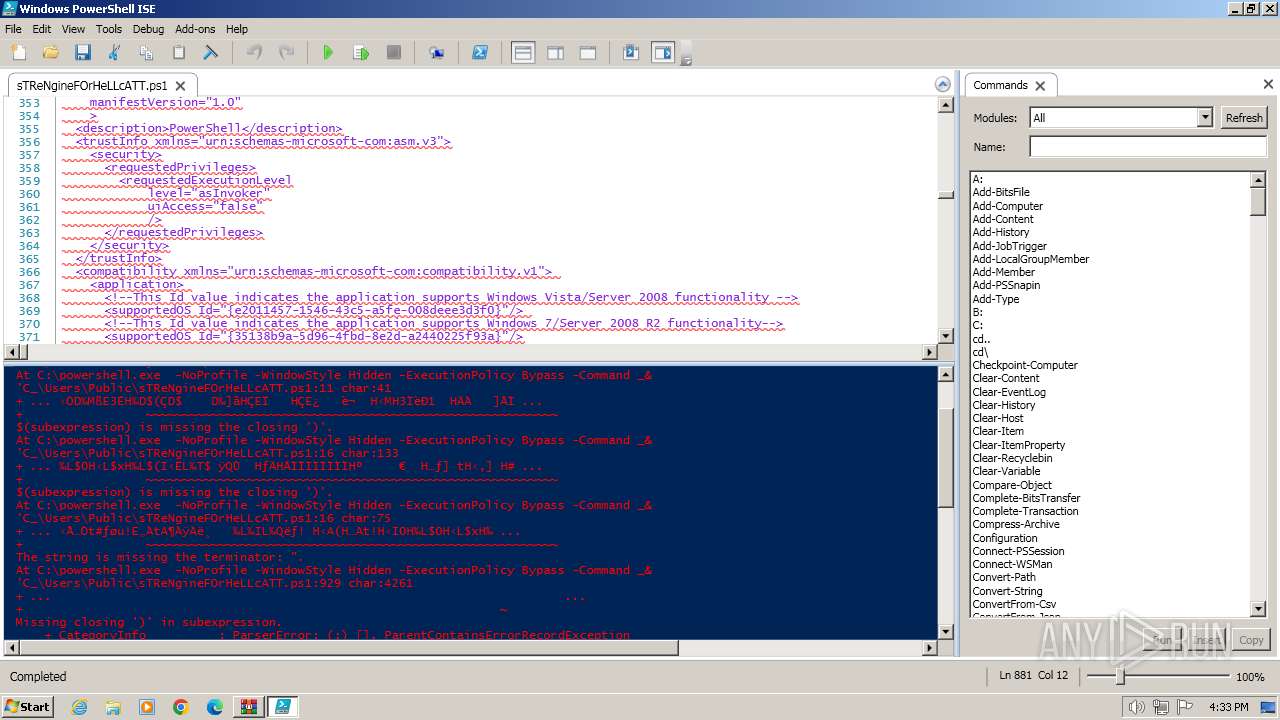
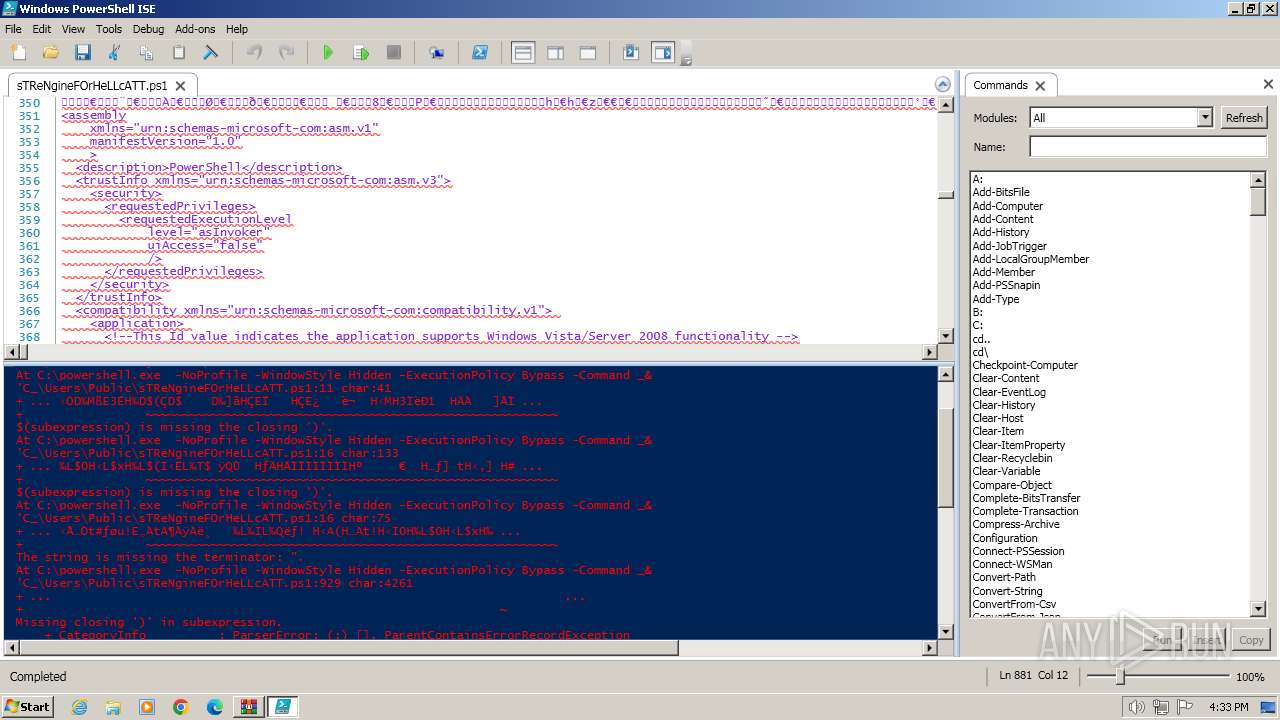
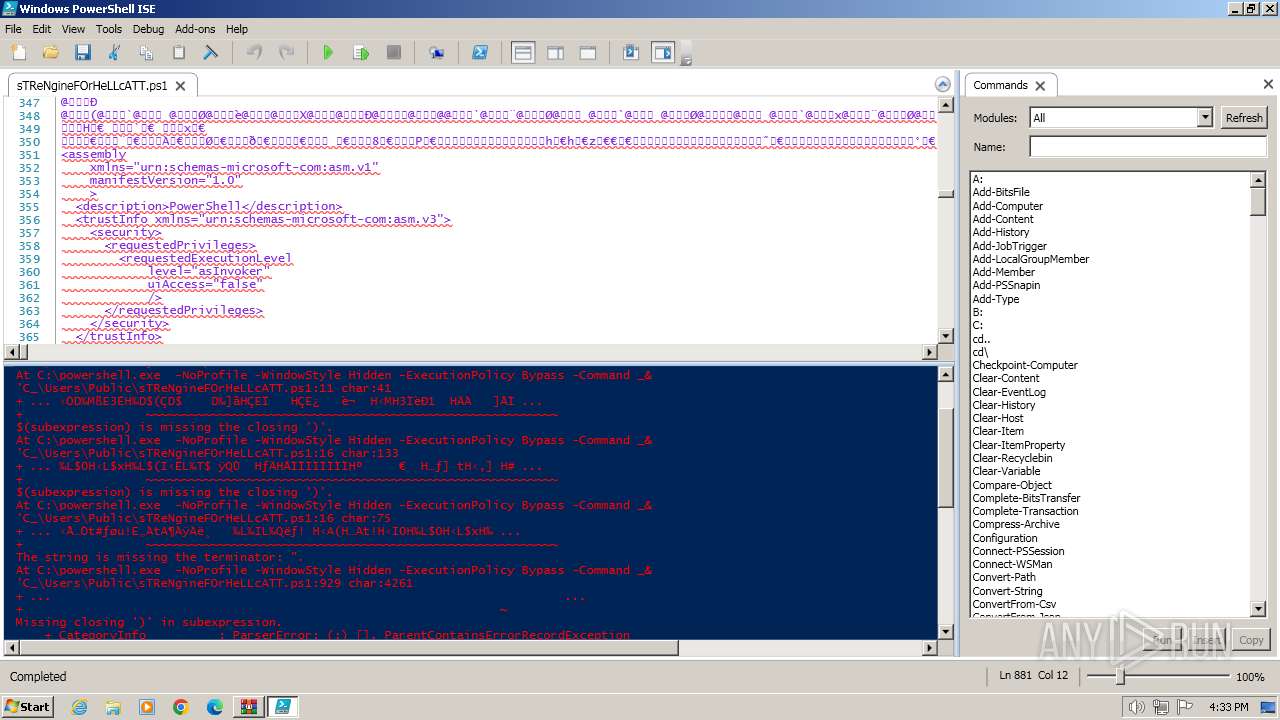
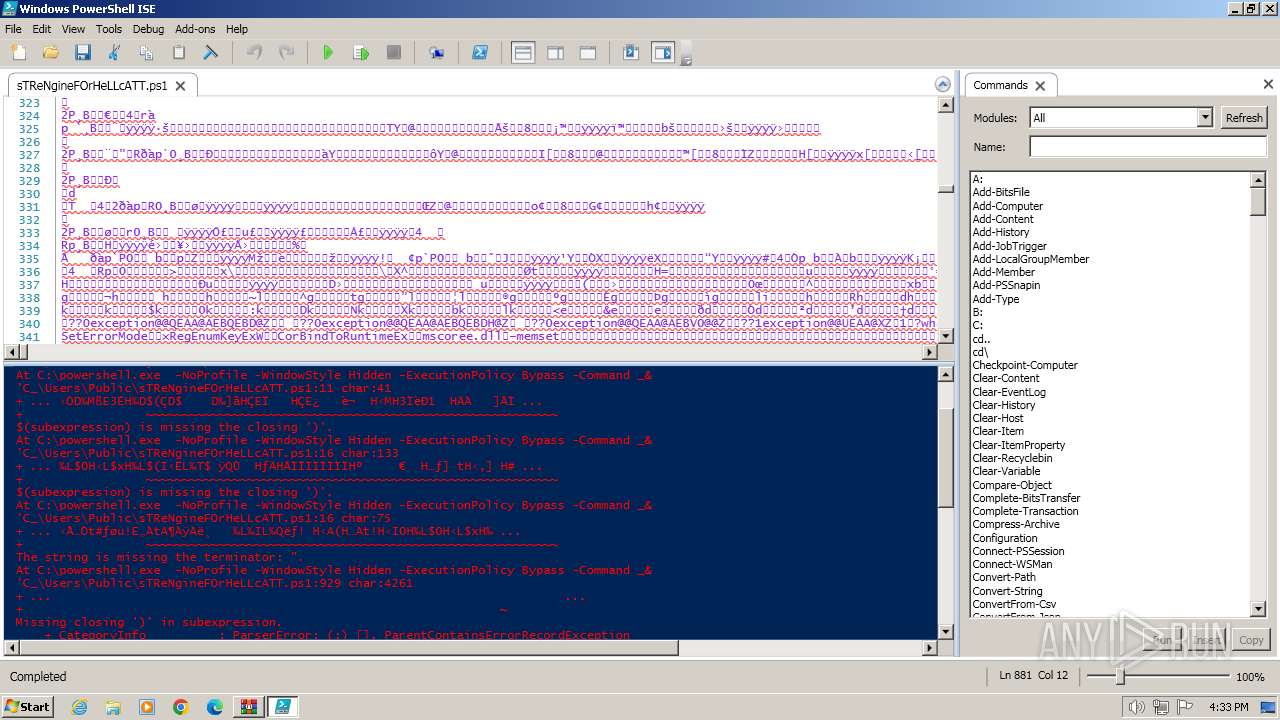
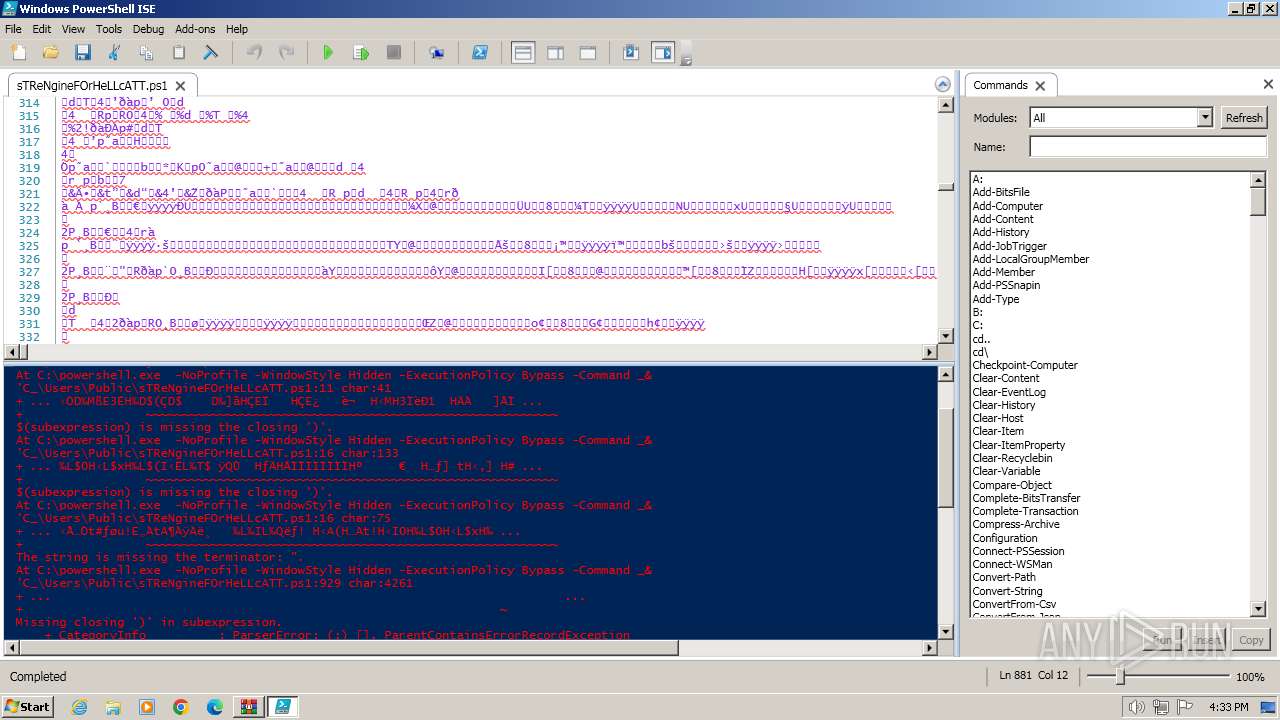
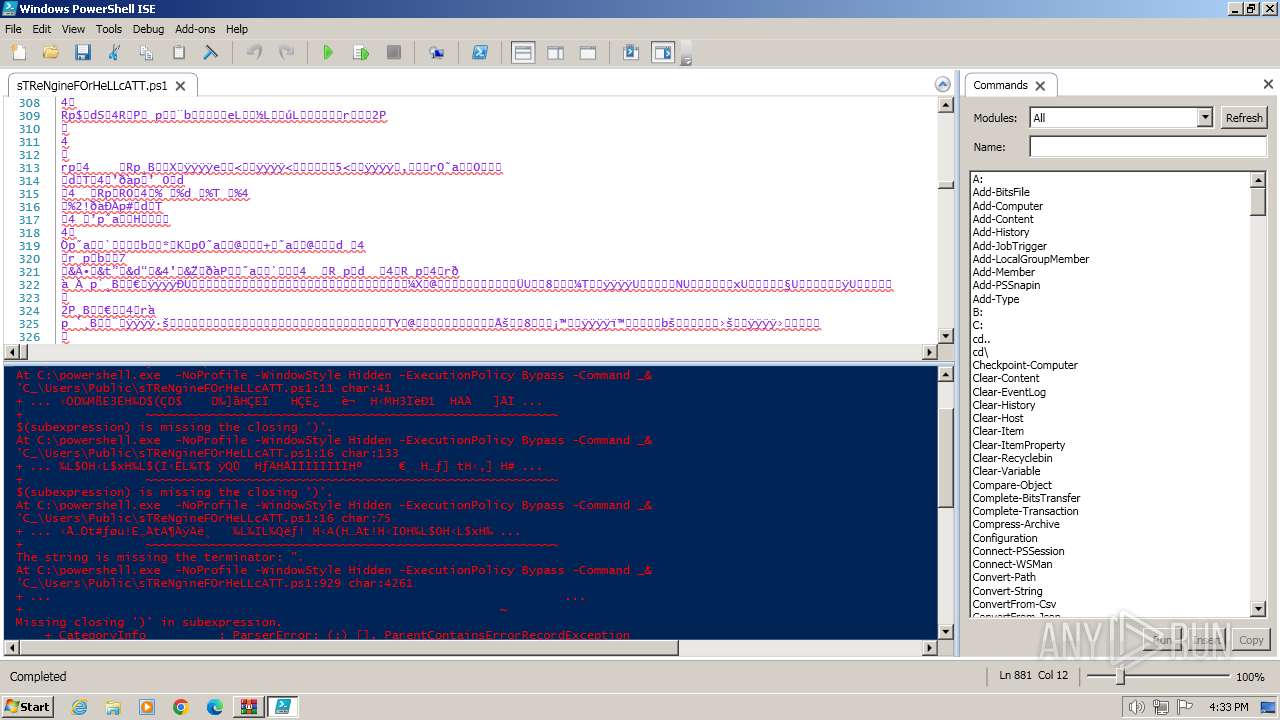
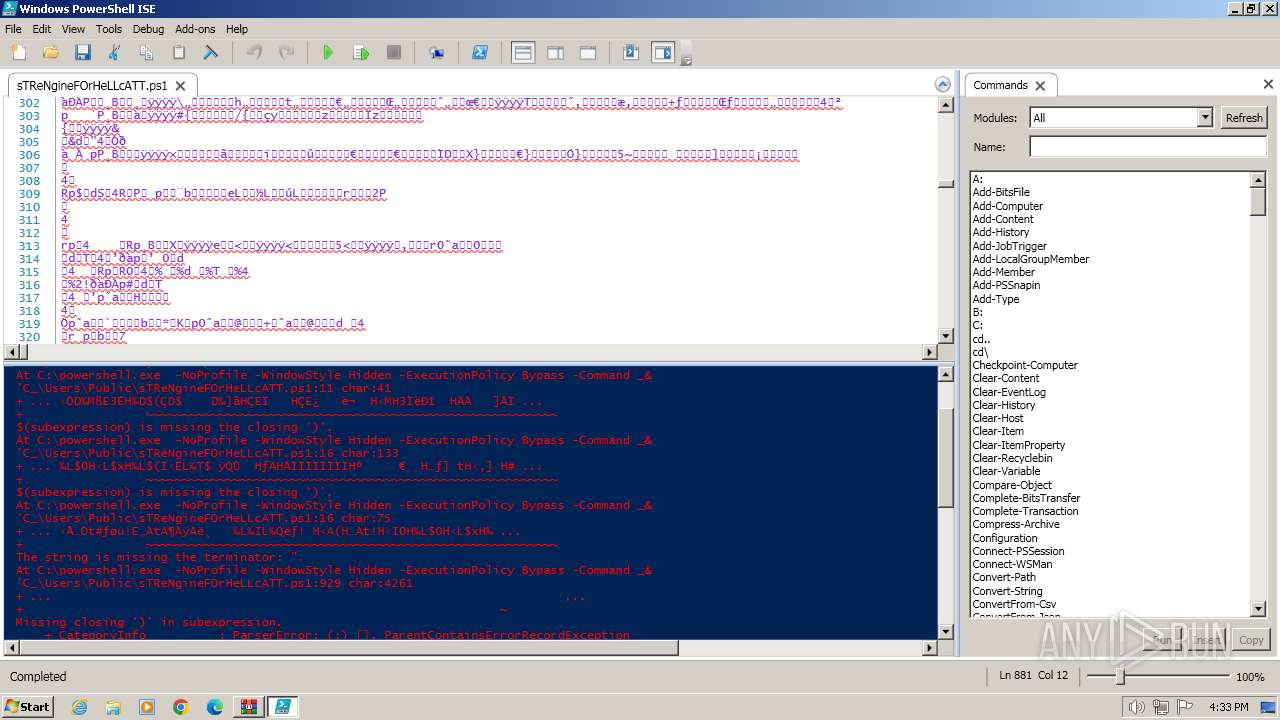
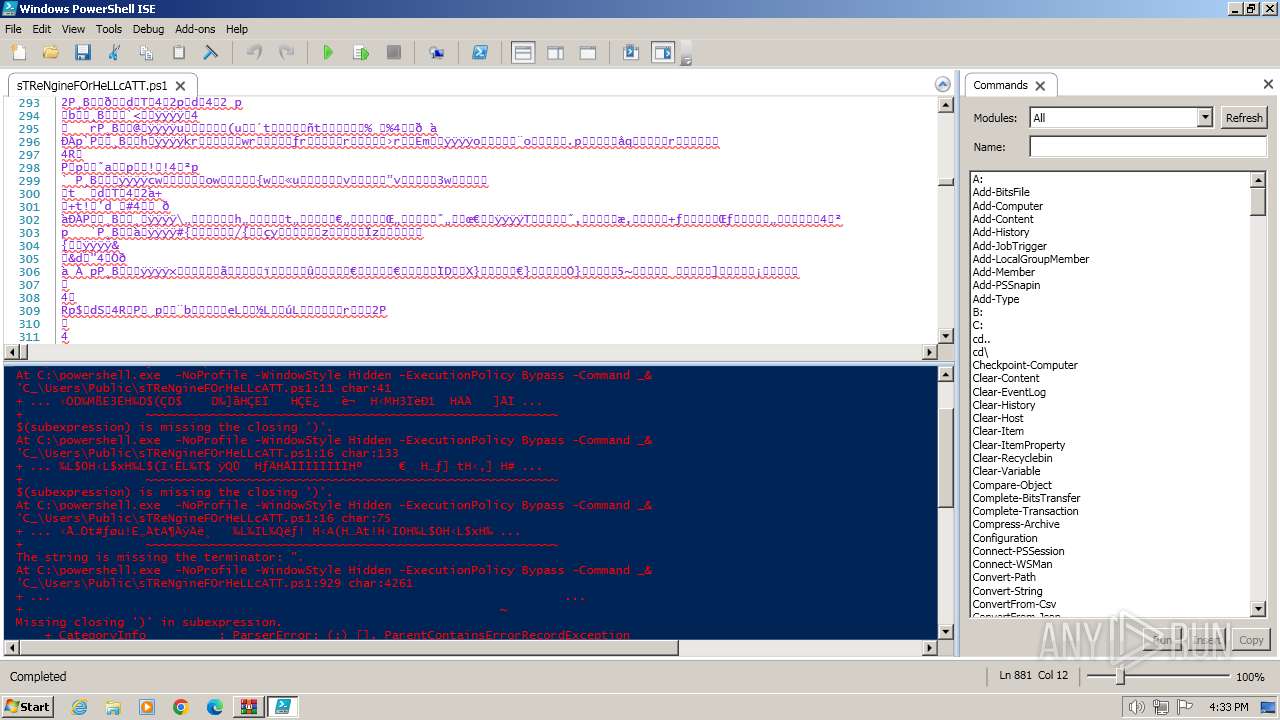
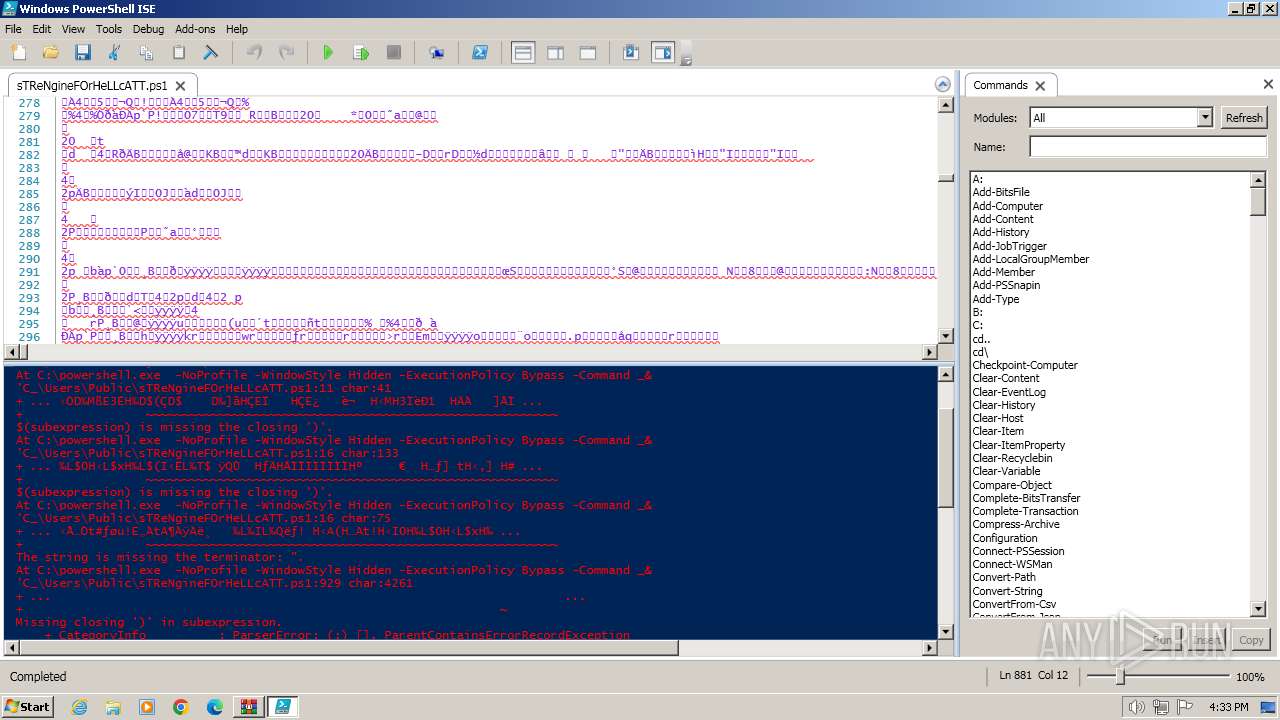
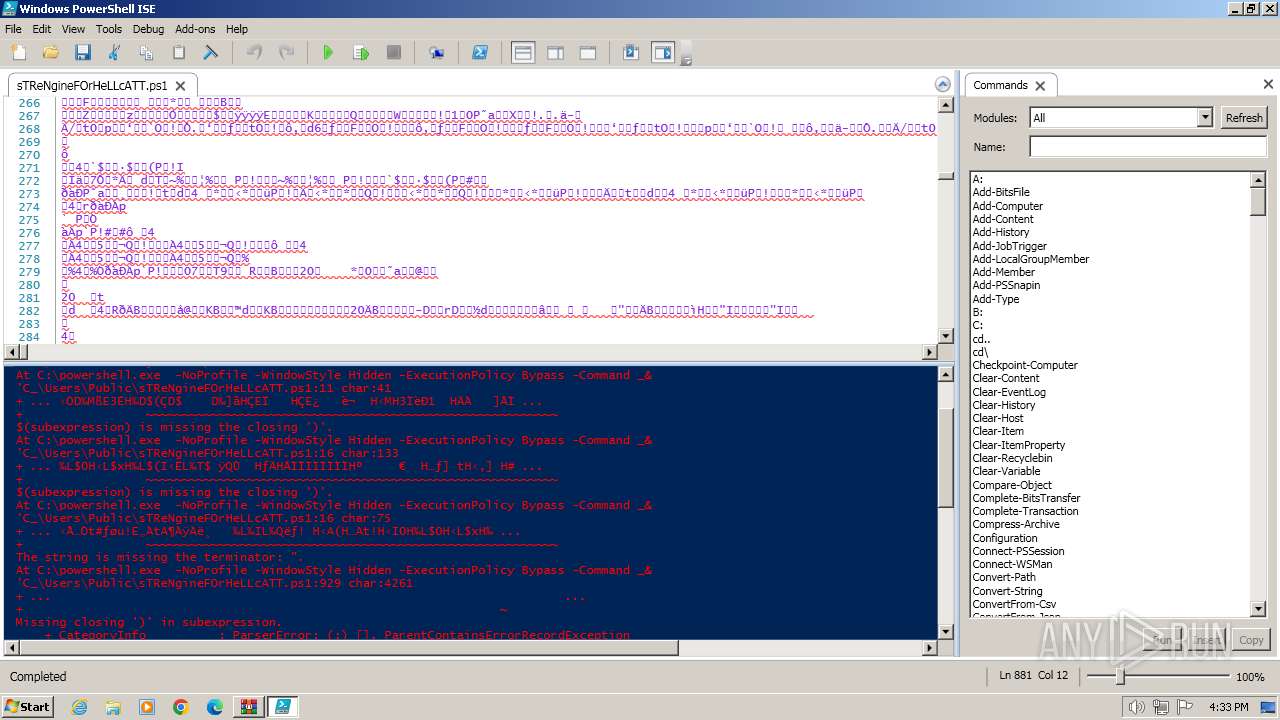
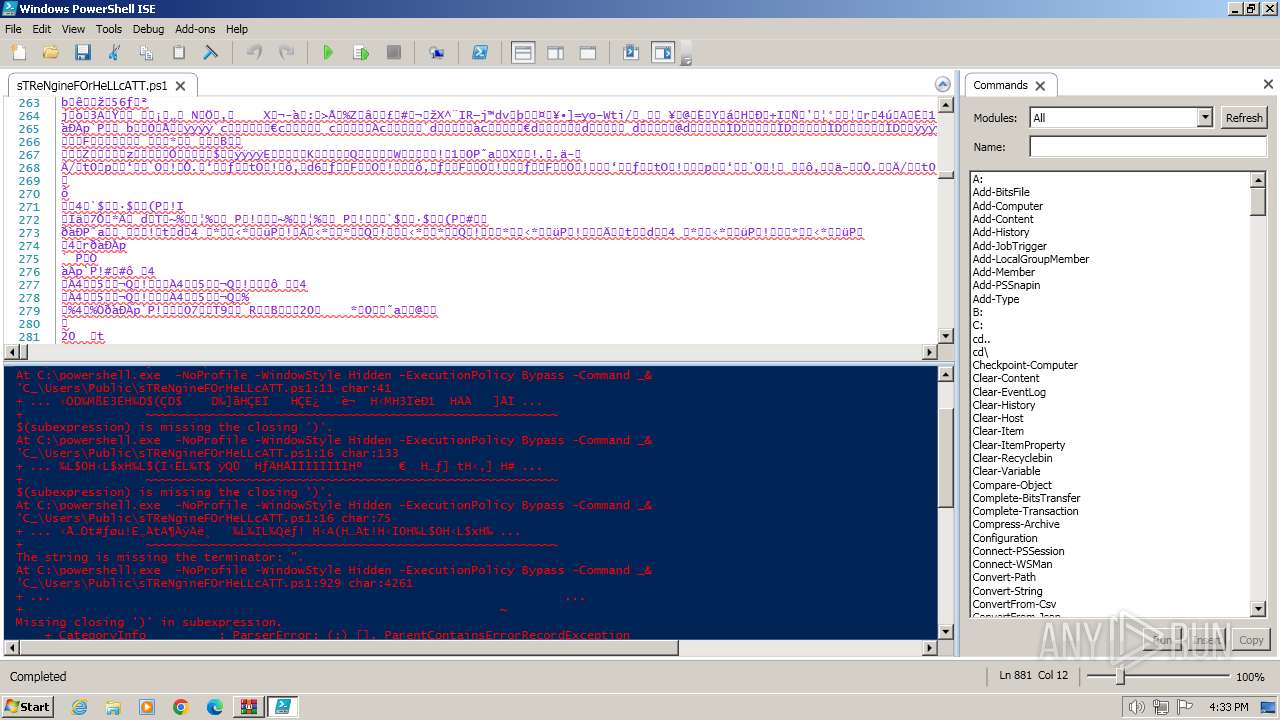
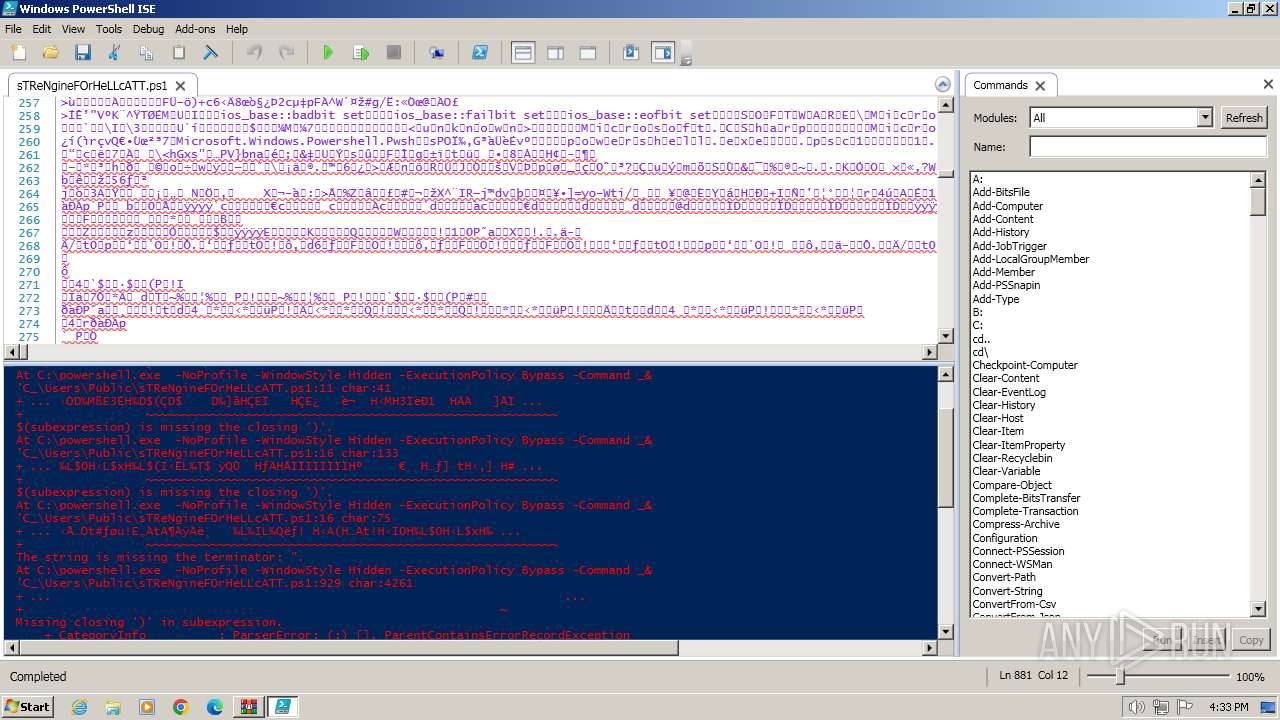
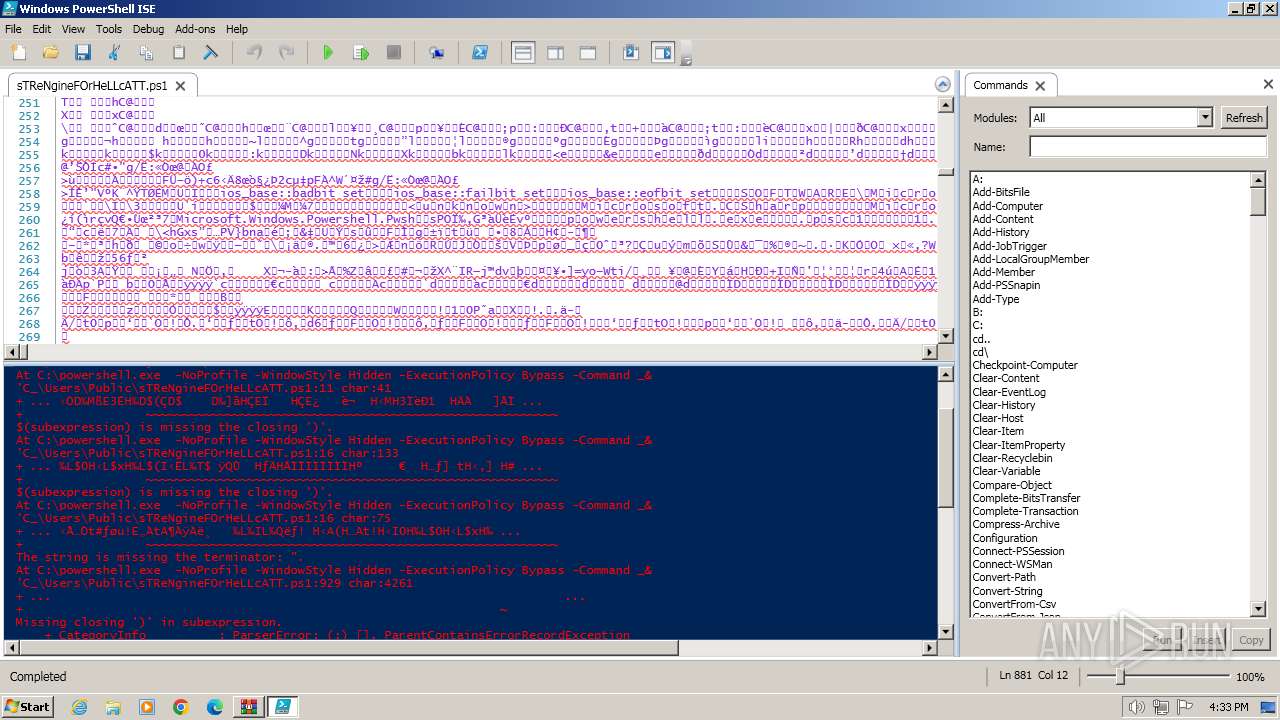
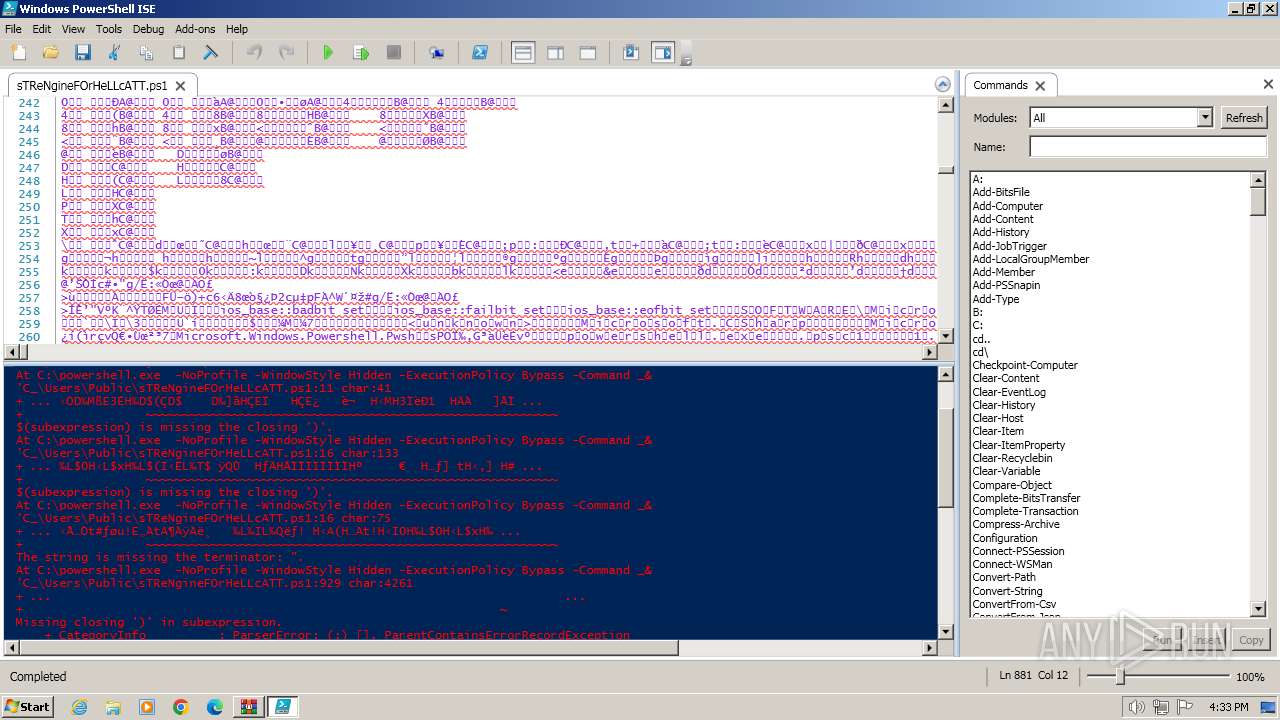
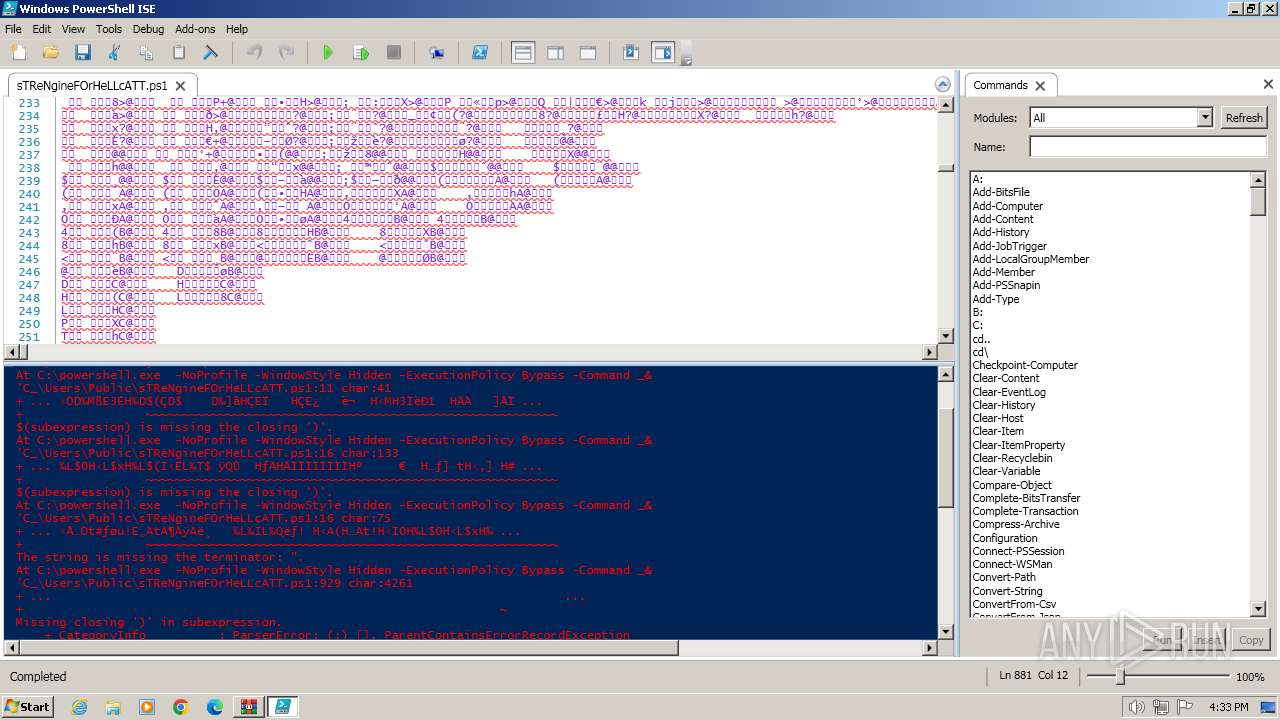
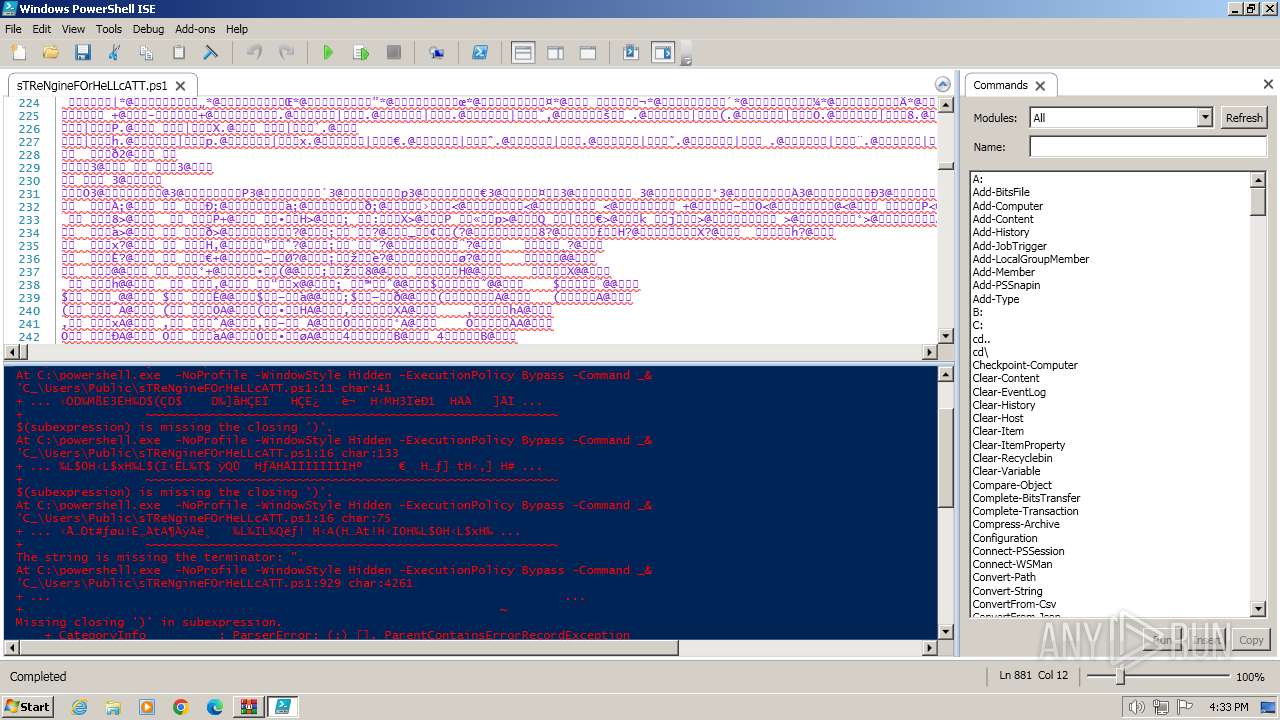
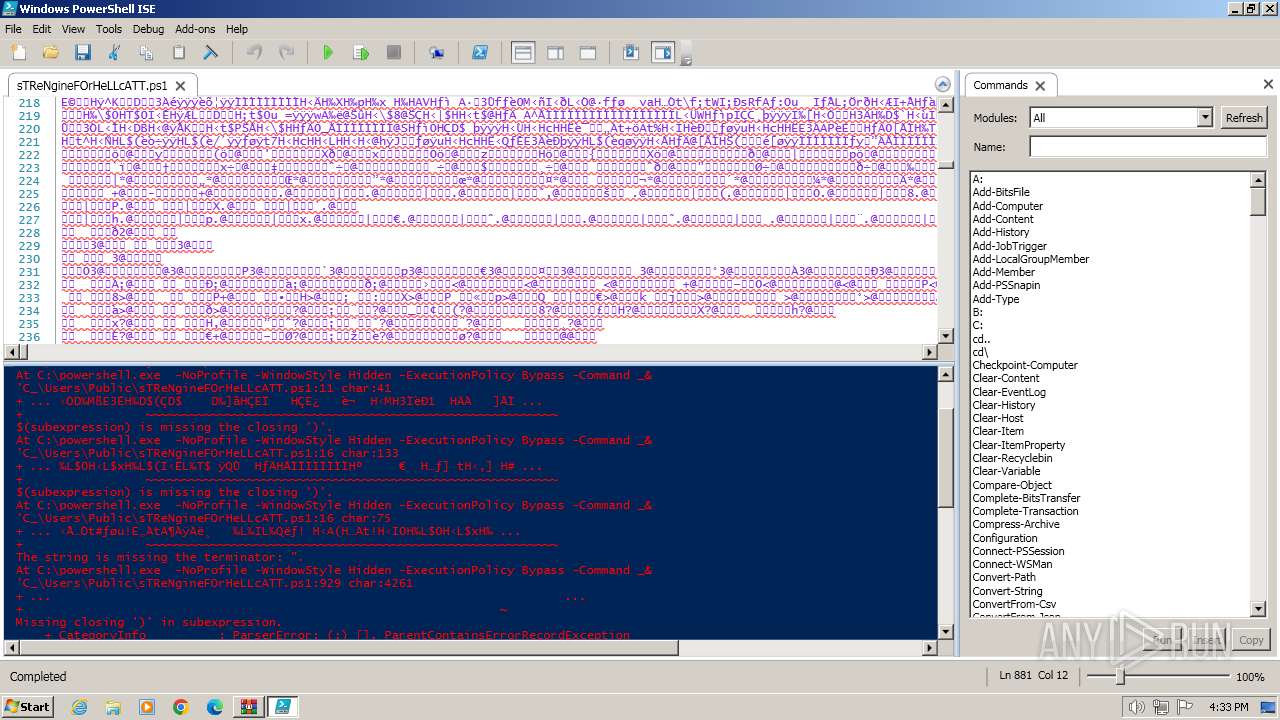
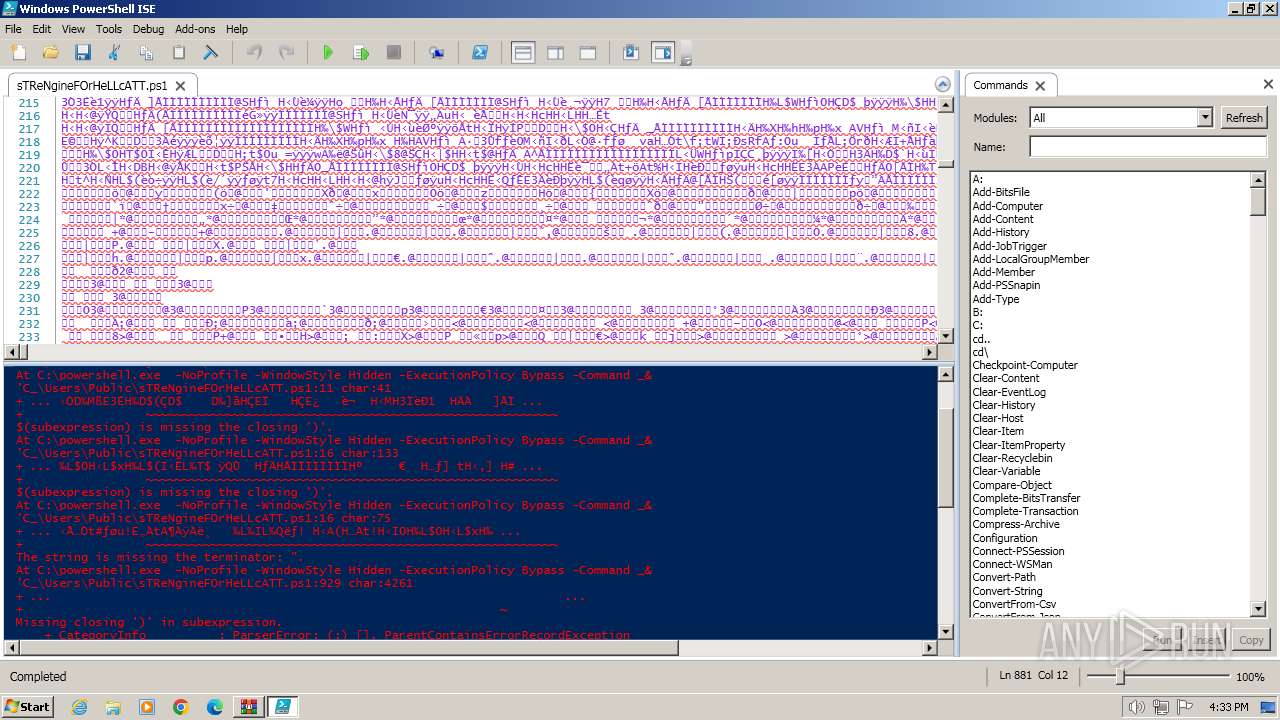
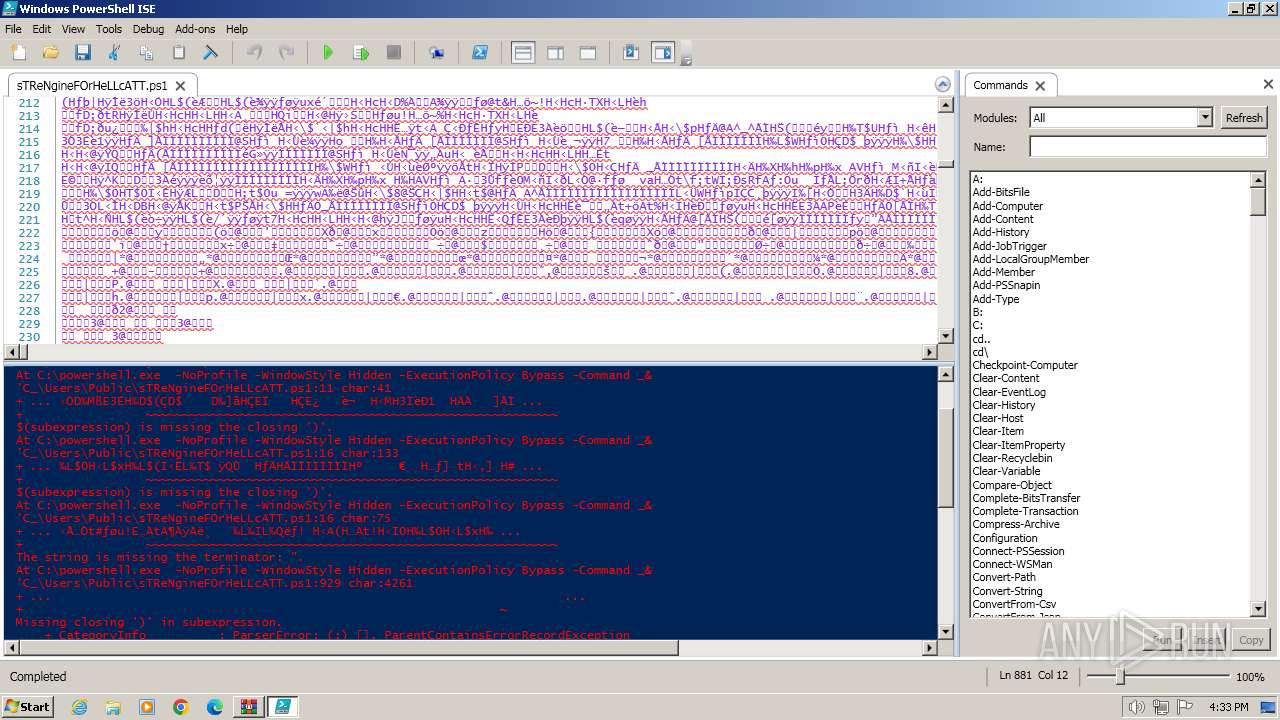
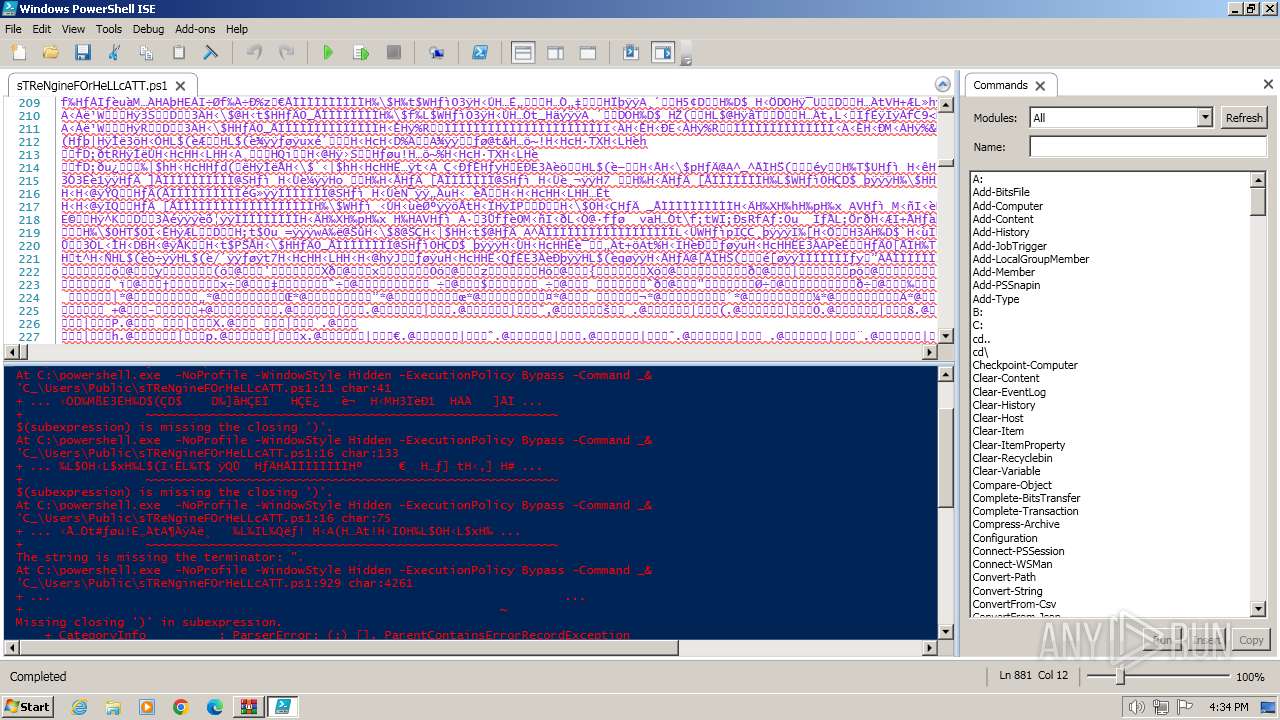
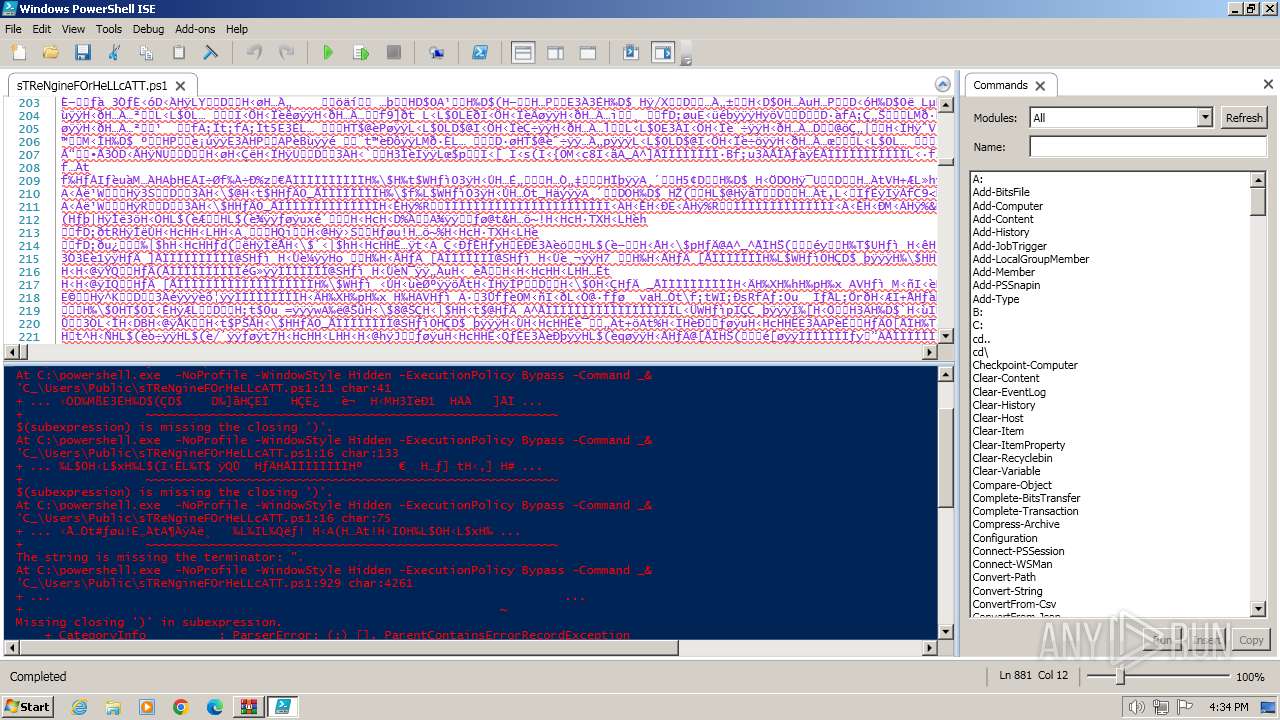
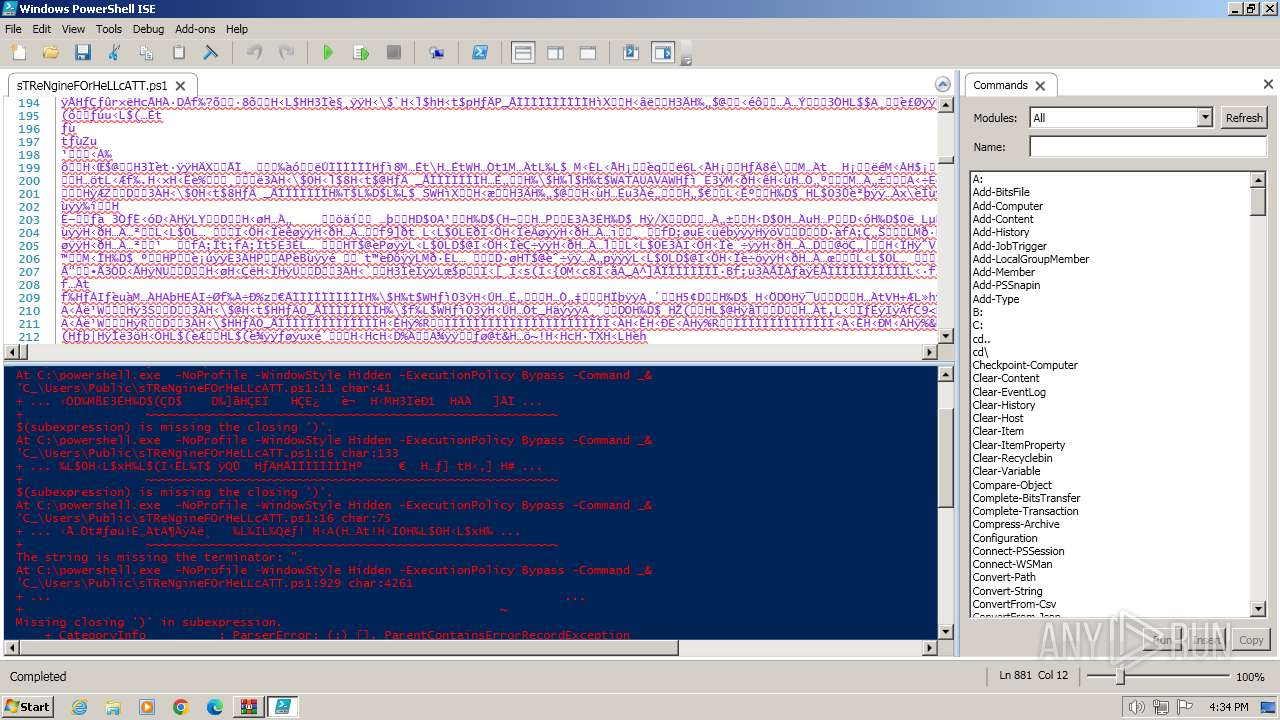
Script raised an exception (POWERSHELL)
- PowerShell_ISE.exe (PID: 3916)
- powershell.exe (PID: 3056)
- powershell.exe (PID: 3680)
- powershell.exe (PID: 3776)
- powershell.exe (PID: 1496)
- powershell.exe (PID: 4004)
- powershell.exe (PID: 1628)
Checks supported languages
- wmpnscfg.exe (PID: 3900)
Reads the computer name
- wmpnscfg.exe (PID: 3900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:04:23 19:59:14 |
| ZipCRC: | 0x47efc081 |
| ZipCompressedSize: | 165279 |
| ZipUncompressedSize: | 455680 |
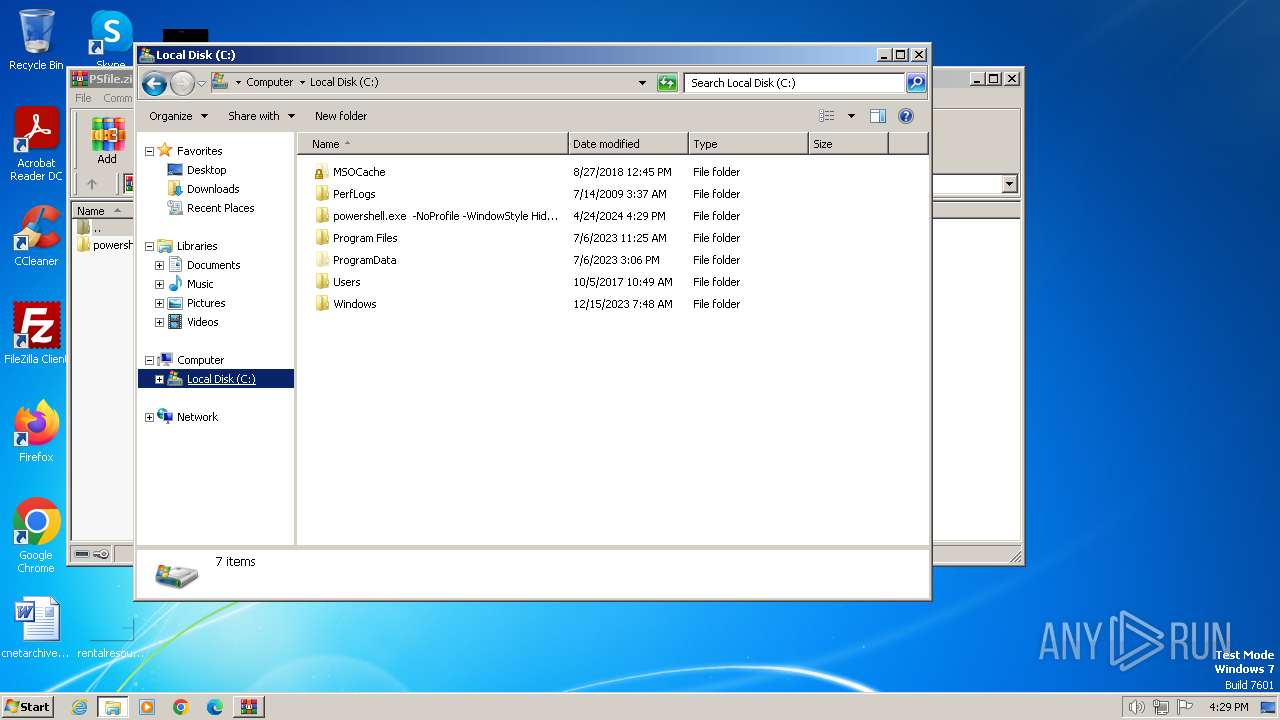
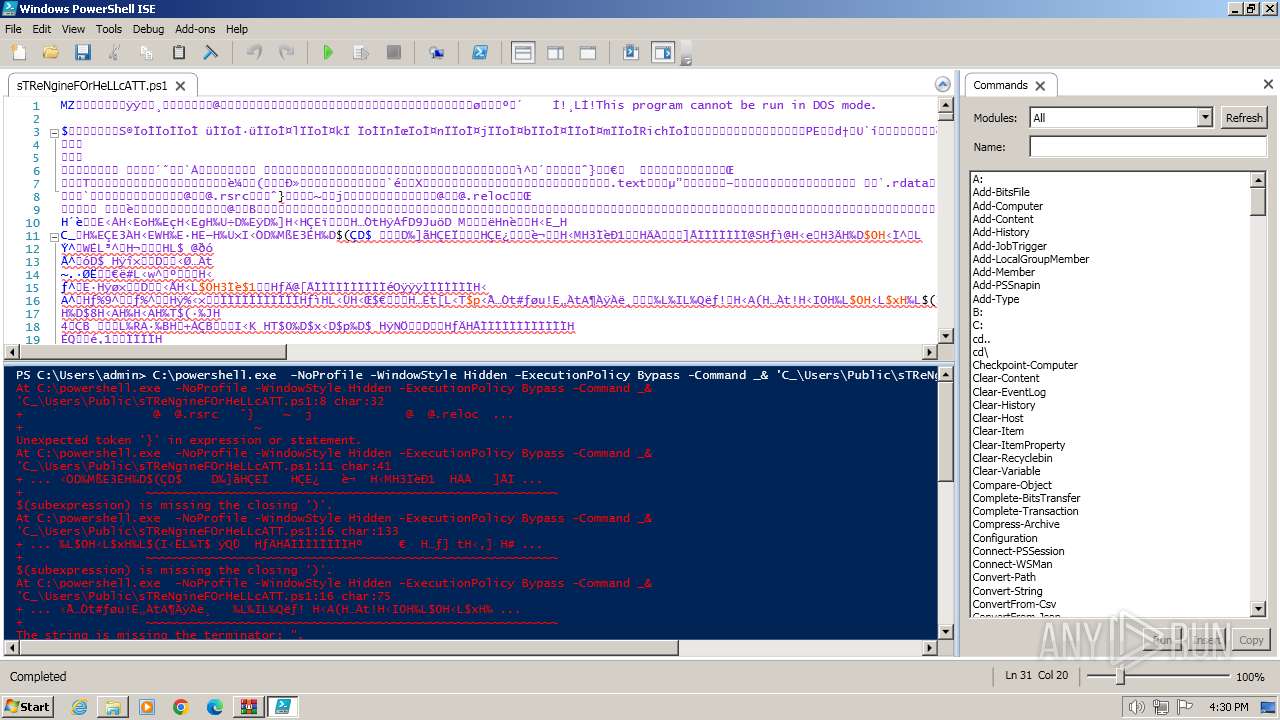
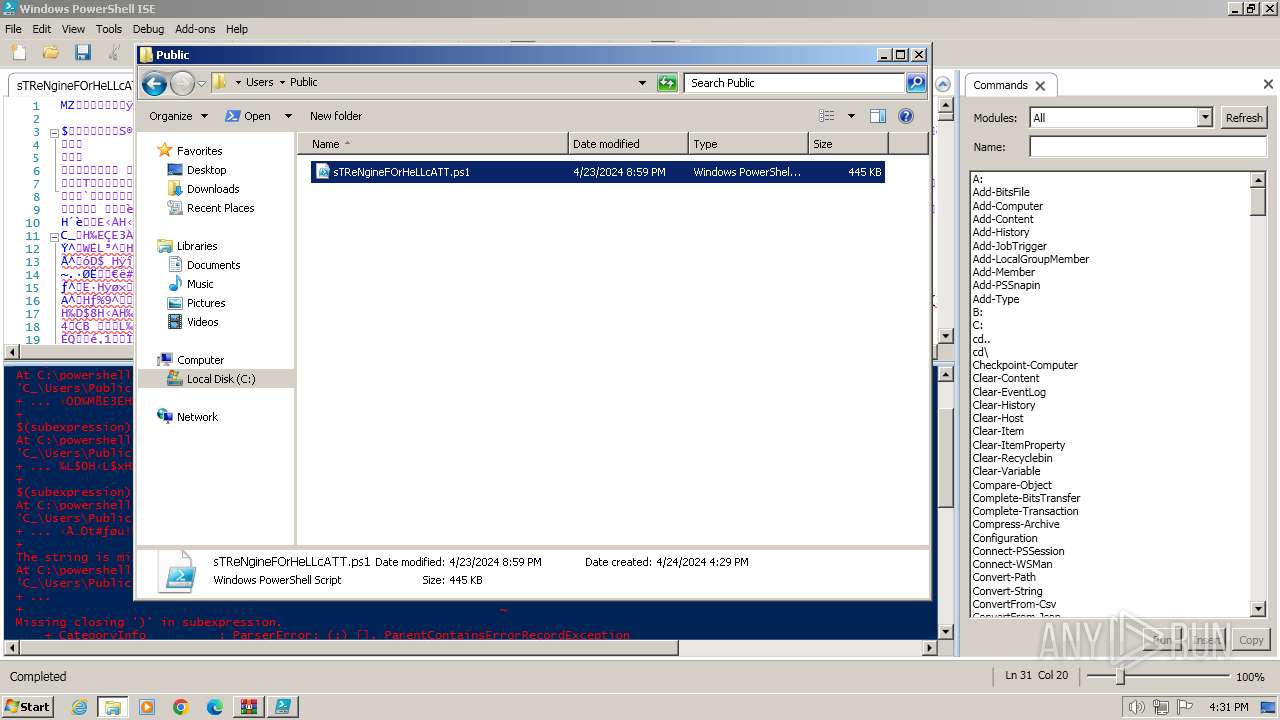
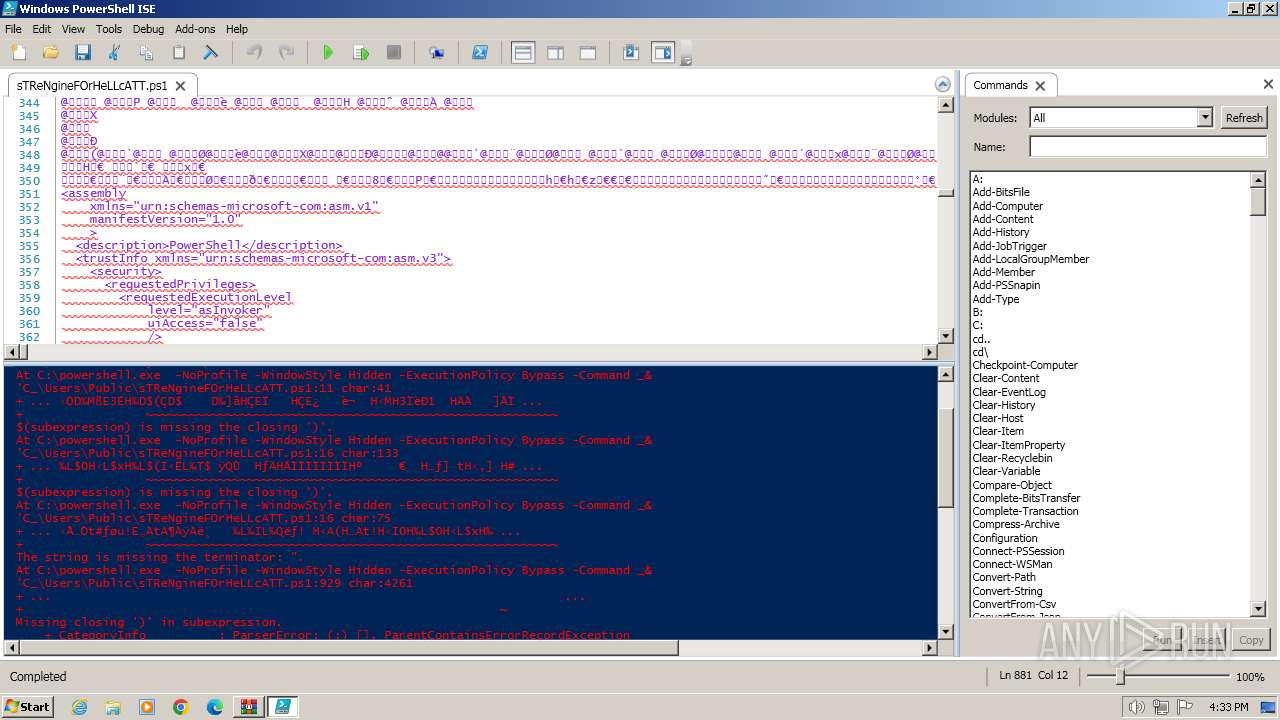
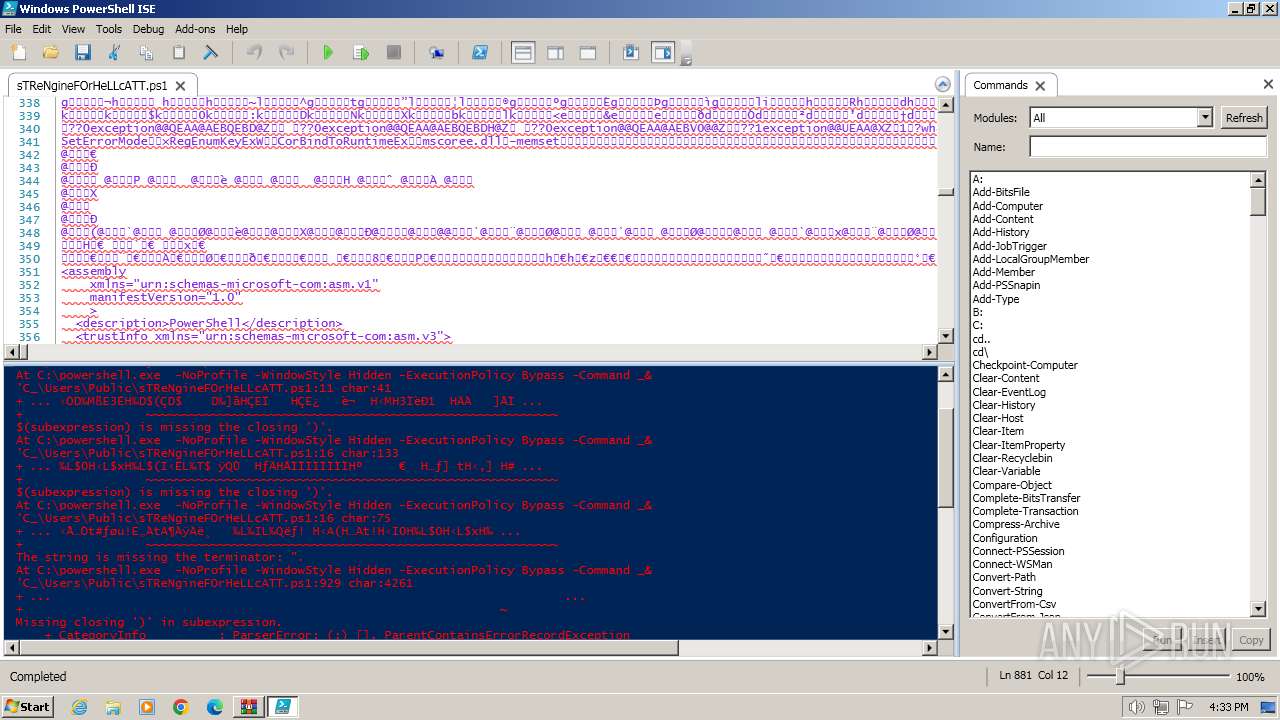
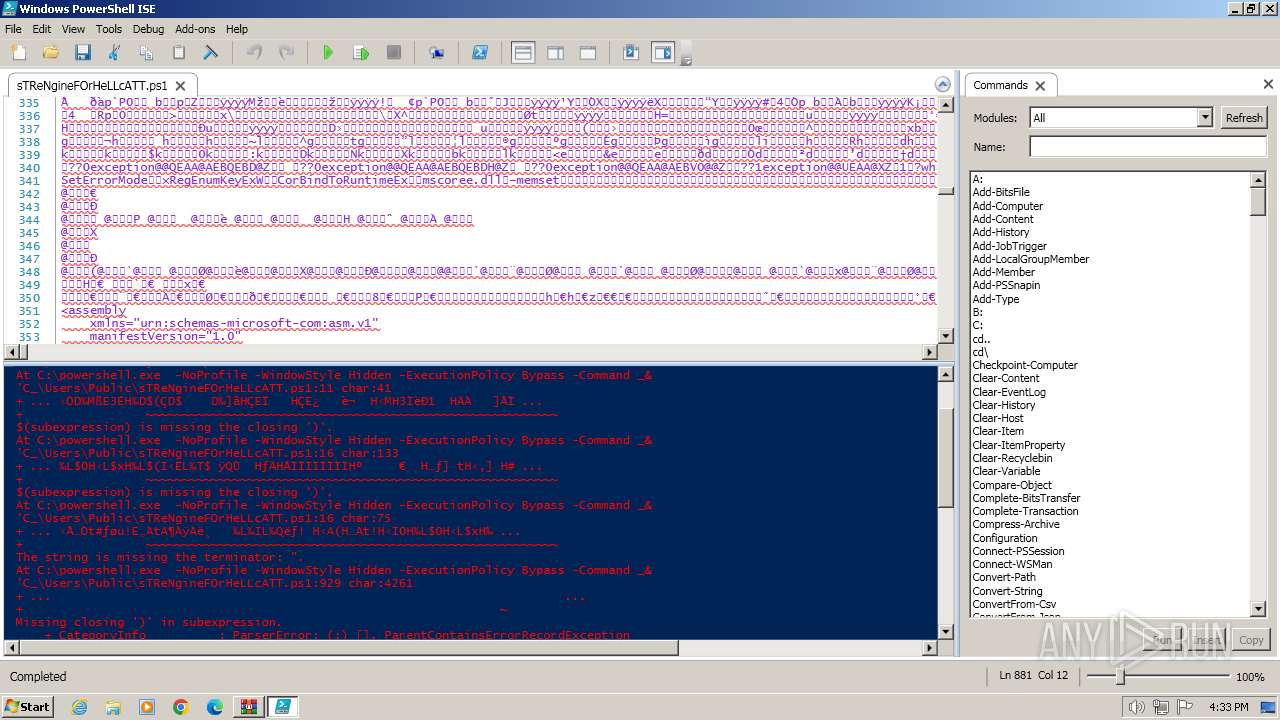
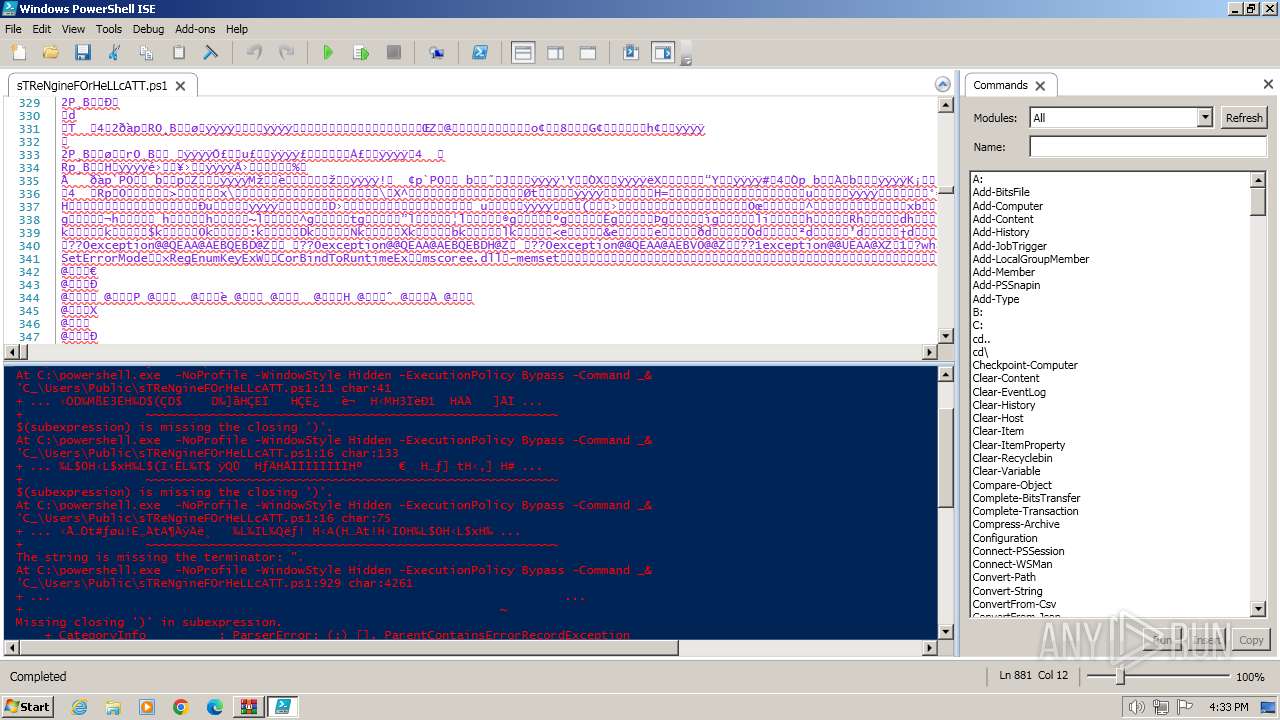
| ZipFileName: | powershell.exe -NoProfile -WindowStyle Hidden -ExecutionPolicy Bypass -Command "& 'C:/Users/Public/sTReNgineFOrHeLLcATT.ps1'" |
Total processes
55
Monitored processes
11
Malicious processes
1
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\PSfile.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1496 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\powershell.exe -NoProfile -WindowStyle Hidden -ExecutionPolicy Bypass -Command _& 'C_\Users\Public\sTReNgineFOrHeLLcATT.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1628 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\powershell.exe -NoProfile -WindowStyle Hidden -ExecutionPolicy Bypass -Command _& 'C_\Users\Public\sTReNgineFOrHeLLcATT.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3056 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\powershell.exe -NoProfile -WindowStyle Hidden -ExecutionPolicy Bypass -Command _& 'C_\Users\Public\sTReNgineFOrHeLLcATT.ps1" "-Command" "if((Get-ExecutionPolicy ) -ne AllSigned) { Set-ExecutionPolicy -Scope Process Bypass }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3084 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3680 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\powershell.exe -NoProfile -WindowStyle Hidden -ExecutionPolicy Bypass -Command _& 'C_\Users\Public\sTReNgineFOrHeLLcATT.ps1" "-Command" "if((Get-ExecutionPolicy ) -ne AllSigned) { Set-ExecutionPolicy -Scope Process Bypass }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3776 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\powershell.exe -NoProfile -WindowStyle Hidden -ExecutionPolicy Bypass -Command _& 'C_\Users\Public\sTReNgineFOrHeLLcATT.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3900 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3916 | "C:\Windows\system32\WindowsPowerShell\v1.0\PowerShell_ISE.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\PowerShell_ISE.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell ISE Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3988 | "C:\Program Files\WinRAR\WinRAR.exe" -elevate668 | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
43 347
Read events
42 764
Write events
577
Delete events
6
Modification events
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\PSfile.zip | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
1
Suspicious files
35
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3680 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1d7ef6.TMP | binary | |
MD5:42E3956892291F5EE35E1B989213EF05 | SHA256:D4E6947871B5FD00AD32F8707479DD6EC92AB65D8C6D157B1C0C3D99D575E468 | |||
| 3916 | PowerShell_ISE.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ISE\S-1-5-5-0-67545\PowerShellISEPipeName_0_90af18f7-2f70-4834-9e62-53025c041ec8 | text | |
MD5:A5EA0AD9260B1550A14CC58D2C39B03D | SHA256:F1B2F662800122BED0FF255693DF89C4487FBDCF453D3524A42D4EC20C3D9C04 | |||
| 3916 | PowerShell_ISE.exe | C:\Users\admin\AppData\Local\Temp\bg0durk1.okh.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3916 | PowerShell_ISE.exe | C:\Users\admin\AppData\Local\Temp\trvik1zh.leg.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3776 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1d9146.TMP | binary | |
MD5:42E3956892291F5EE35E1B989213EF05 | SHA256:D4E6947871B5FD00AD32F8707479DD6EC92AB65D8C6D157B1C0C3D99D575E468 | |||
| 3776 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:42E3956892291F5EE35E1B989213EF05 | SHA256:D4E6947871B5FD00AD32F8707479DD6EC92AB65D8C6D157B1C0C3D99D575E468 | |||
| 3916 | PowerShell_ISE.exe | C:\Users\admin\AppData\Local\Temp\WPF\itfuzysm.hdo | binary | |
MD5:F04A2805F60770668268454EDFC499FA | SHA256:AB3A68D162953659E8C02DBD5C13121DF9DB824D404824450FD38134E32F5ADF | |||
| 3776 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VR4556UY2RAMZWL6SEW5.temp | binary | |
MD5:42E3956892291F5EE35E1B989213EF05 | SHA256:D4E6947871B5FD00AD32F8707479DD6EC92AB65D8C6D157B1C0C3D99D575E468 | |||
| 3056 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1d5de2.TMP | binary | |
MD5:0268C3470C936E6FBAC2945B9E1C2099 | SHA256:DF2AF58E8879B48826D8A418ED3B02CC8D484BCFC231C5B7A11BD153ED3998E9 | |||
| 3680 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Y9Q448FAKZGJWBLPKBQC.temp | binary | |
MD5:42E3956892291F5EE35E1B989213EF05 | SHA256:D4E6947871B5FD00AD32F8707479DD6EC92AB65D8C6D157B1C0C3D99D575E468 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |