| File name: | C:\Users\admin\AppData\Roaming\MSUpdate\ImportantUpdate.exe |
| Full analysis: | https://app.any.run/tasks/fd537698-409a-4d55-a741-bac270a3aad8 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 17:43:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 651F0F2B99D6F9D8A474D042F141B2ED |
| SHA1: | A82E341F42C7E291AE85ED99843BA567AC35011E |
| SHA256: | C4C83313F96E8D8C50F02249289DE652A2F757BD3012153DD26086463187C194 |
| SSDEEP: | 6144:rCOpa+yknfqWqKnx4EUOarCyvQeFDhiX2Yx:vpa+XHqKZ79yzFDM9 |
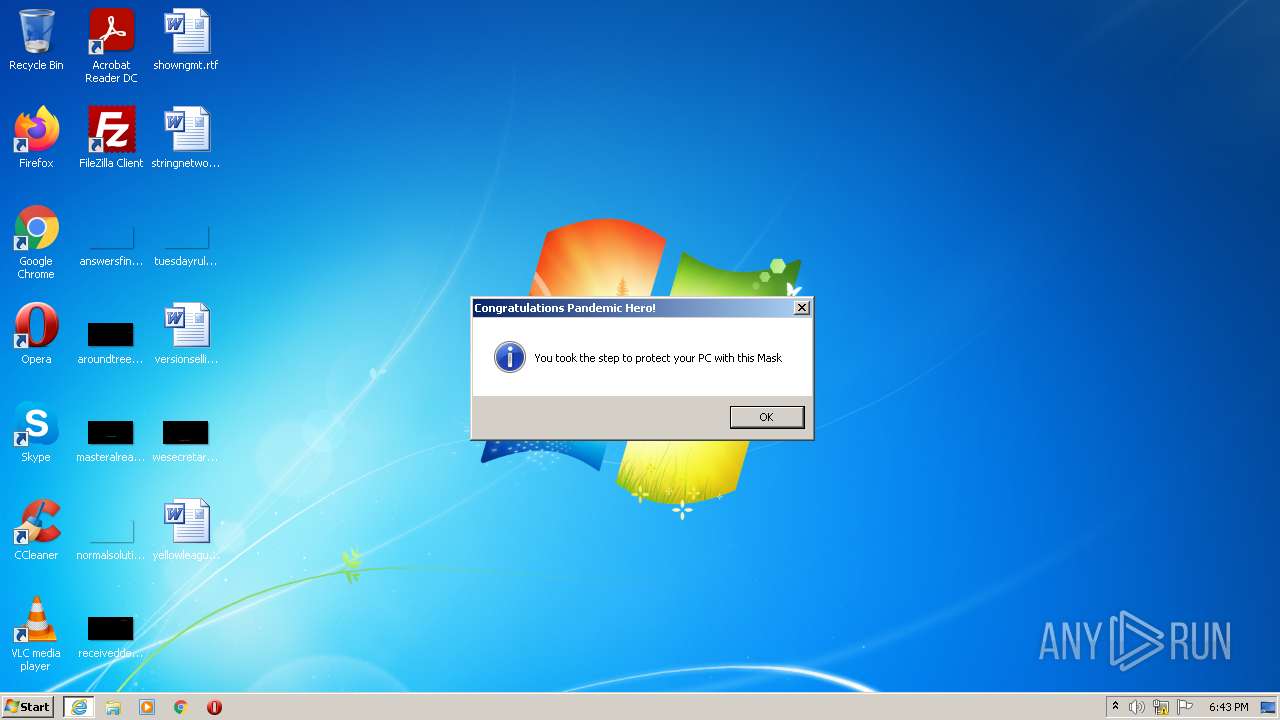
MALICIOUS
Application was injected by another process
- csrss.exe (PID: 344)
- csrss.exe (PID: 388)
- smss.exe (PID: 260)
- wininit.exe (PID: 380)
Runs injected code in another process
- ImportantUpdate.exe (PID: 2480)
SUSPICIOUS
Checks supported languages
- ImportantUpdate.exe (PID: 2480)
Reads the computer name
- ImportantUpdate.exe (PID: 2480)
Starts Internet Explorer
- ImportantUpdate.exe (PID: 2480)
INFO
Checks supported languages
- iexplore.exe (PID: 2780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (42.1) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (41.3) |
| .exe | | | Win32 Executable (generic) (7) |
| .exe | | | Win16/32 Executable Delphi generic (3.2) |
| .exe | | | Generic Win/DOS Executable (3.1) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x4a5f0 |
| UninitializedDataSize: | 139264 |
| InitializedDataSize: | 77824 |
| CodeSize: | 163840 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00022000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00023000 | 0x00028000 | 0x00027800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.81034 |
.rsrc | 0x0004B000 | 0x00013000 | 0x00012800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.61196 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.58582 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
50 | 7.59119 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
51 | 7.66291 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
52 | 7.72789 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
53 | 7.81658 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
54 | 7.69107 | 56368 | Latin 1 / Western European | UNKNOWN | RT_ICON |
55 | 6.19042 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
56 | 6.0626 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
57 | 5.92014 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
58 | 5.47513 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
KERNEL32.DLL |
advapi32.dll |
oleaut32.dll |
user32.dll |
Total processes
40
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 260 | \SystemRoot\System32\smss.exe | \SystemRoot\System32\smss.exe | System | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 344 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\system32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 380 | wininit.exe | C:\Windows\system32\wininit.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Start-Up Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 388 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\system32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
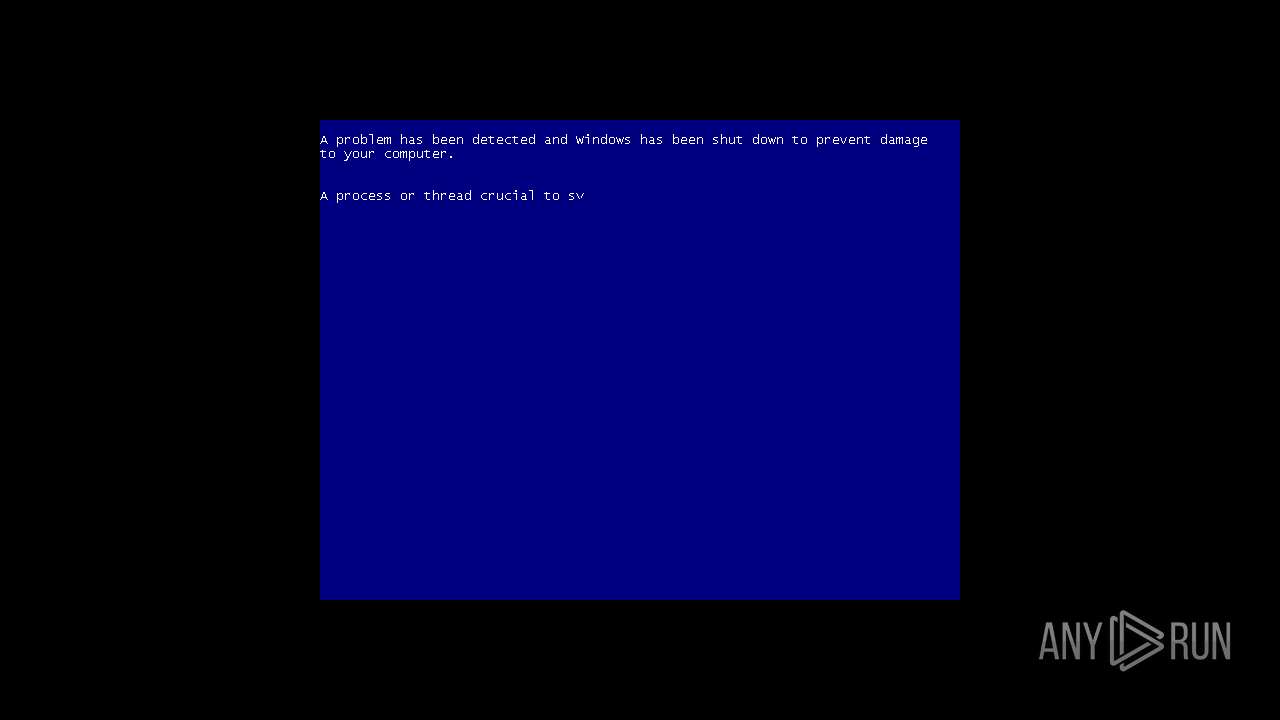
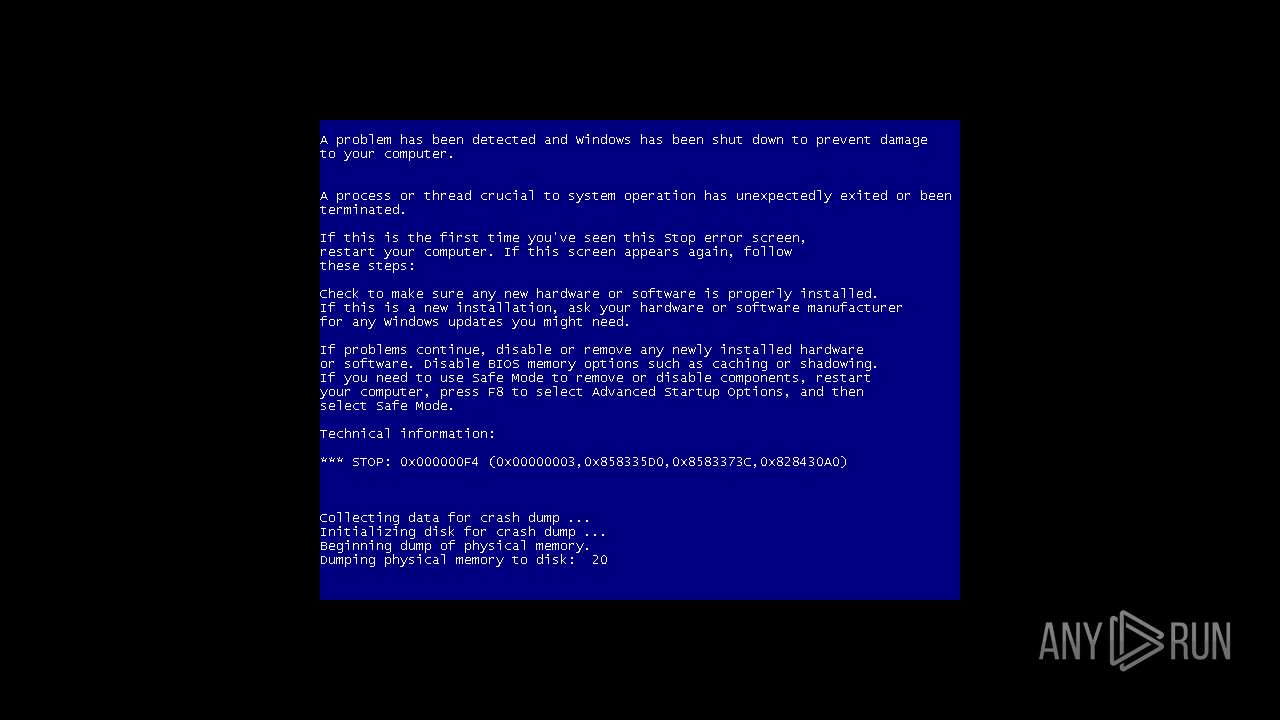
| 1000 | "C:\Users\admin\AppData\Local\Temp\ImportantUpdate.exe" | C:\Users\admin\AppData\Local\Temp\ImportantUpdate.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2480 | "C:\Users\admin\AppData\Local\Temp\ImportantUpdate.exe" | C:\Users\admin\AppData\Local\Temp\ImportantUpdate.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | ImportantUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
189
Read events
187
Write events
2
Delete events
0
Modification events
| (PID) Process: | (2480) ImportantUpdate.exe | Key: | HKEY_CURRENT_USER\Software\CovidUpdater |
| Operation: | write | Name: | FileNameAtual |
Value: C:\Users\admin\AppData\Local\Temp\ImportantUpdate.exe | |||
| (PID) Process: | (2780) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\CovidUpdater |
| Operation: | write | Name: | FirstExecution |
Value: 05/20/2022 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report