| File name: | fcdfg.exe |
| Full analysis: | https://app.any.run/tasks/00c11764-bc81-46e7-a5d0-6138a1b70340 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 01:44:14 |
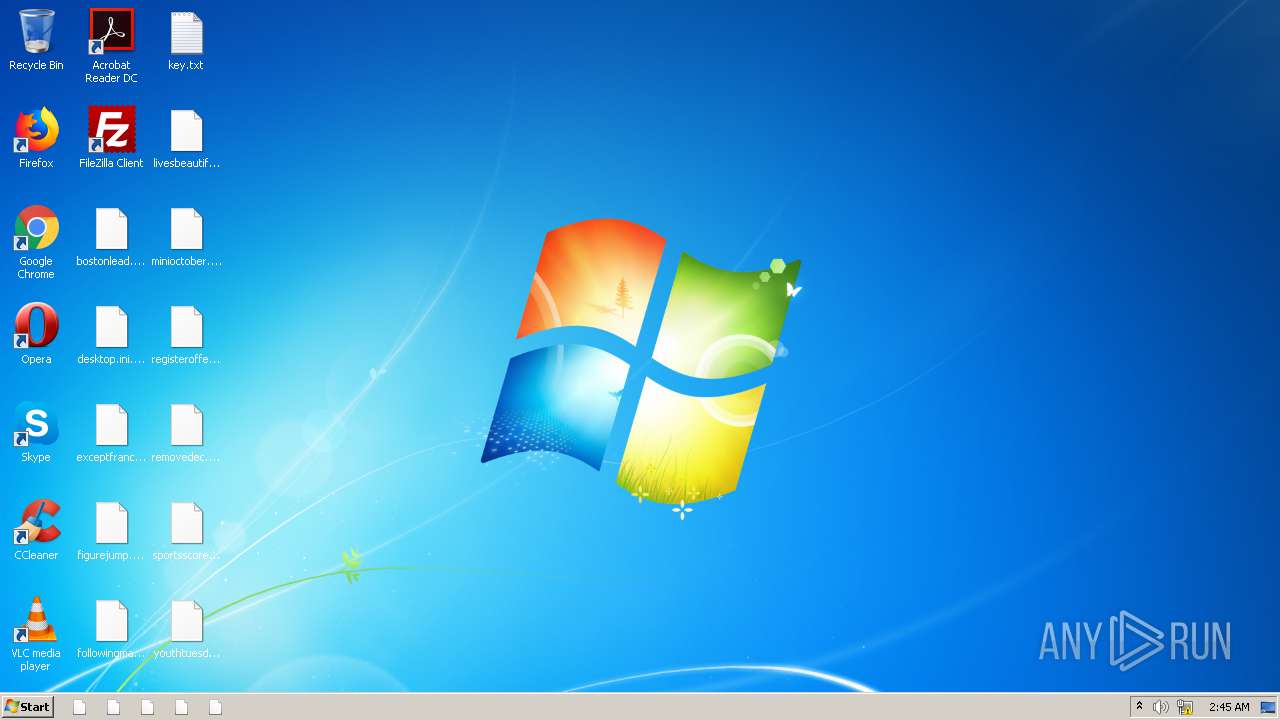
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C243C0A3E2B6079B9AE736DD954ADAB2 |
| SHA1: | F45085742D3762829152C82A6ED05A3AA868B985 |
| SHA256: | C4BD0BAEC275A7F967ADF3DF4D30FF38BAB699B87C2106CF652EEA8311D26C0D |
| SSDEEP: | 24576:NeLH4AlFanAsf8so7JJnHfjthf/dTYCjQ2au6YFLTnY36nGp0MR5:YjGAHP/ZlUCjDau6YF/nY3CGeM |
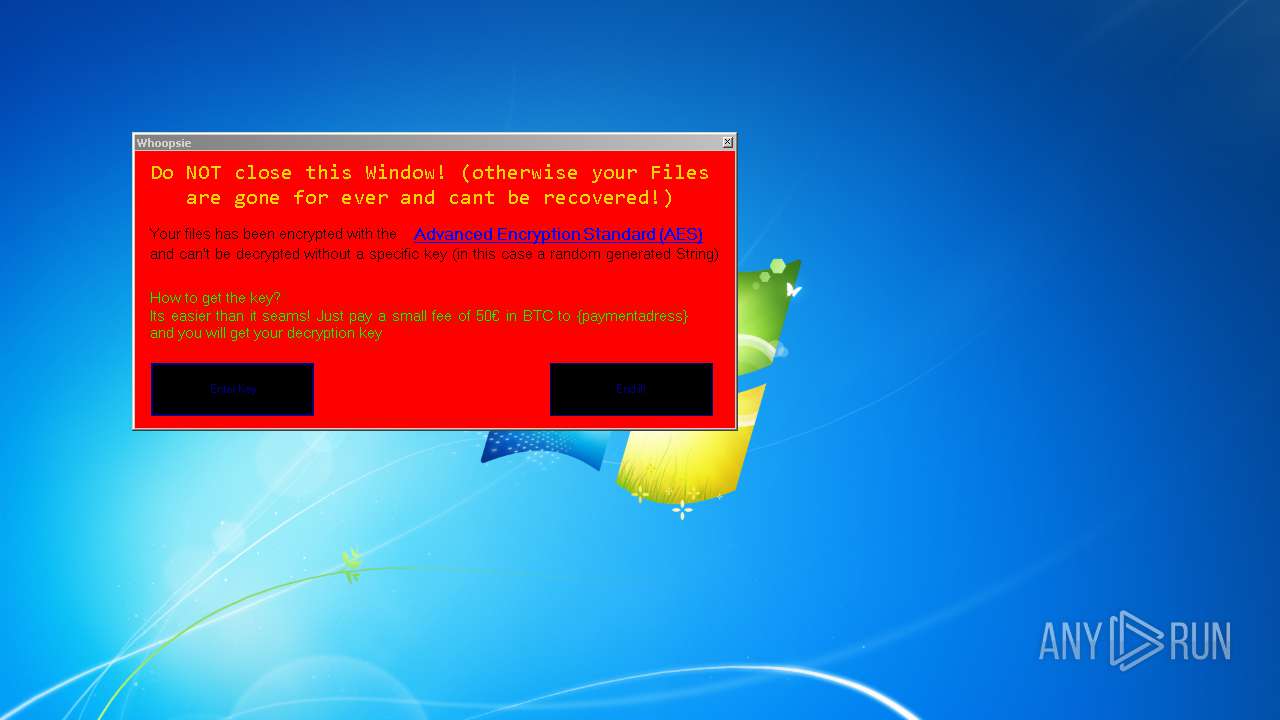
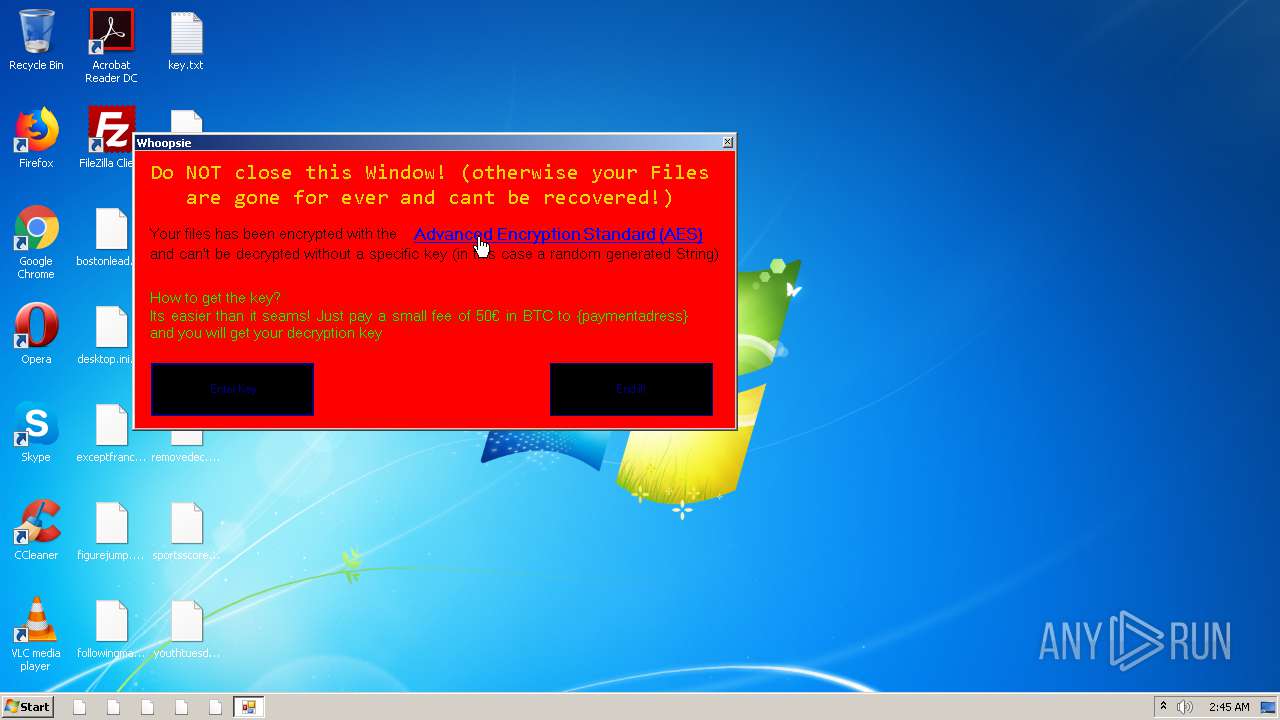
MALICIOUS
Writes to a start menu file
- fcdfg.exe (PID: 2820)
Modifies files in Chrome extension folder
- fcdfg.exe (PID: 2820)
Actions looks like stealing of personal data
- fcdfg.exe (PID: 2820)
SUSPICIOUS
Reads the cookies of Google Chrome
- fcdfg.exe (PID: 2820)
Reads the cookies of Mozilla Firefox
- fcdfg.exe (PID: 2820)
Creates files in the program directory
- fcdfg.exe (PID: 2820)
Creates files in the user directory
- fcdfg.exe (PID: 2820)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:25 17:13:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 19456 |
| InitializedDataSize: | 5120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2b40 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | rw |
| CompanyName: | - |
| FileDescription: | rw |
| FileVersion: | 0.0.0.0 |
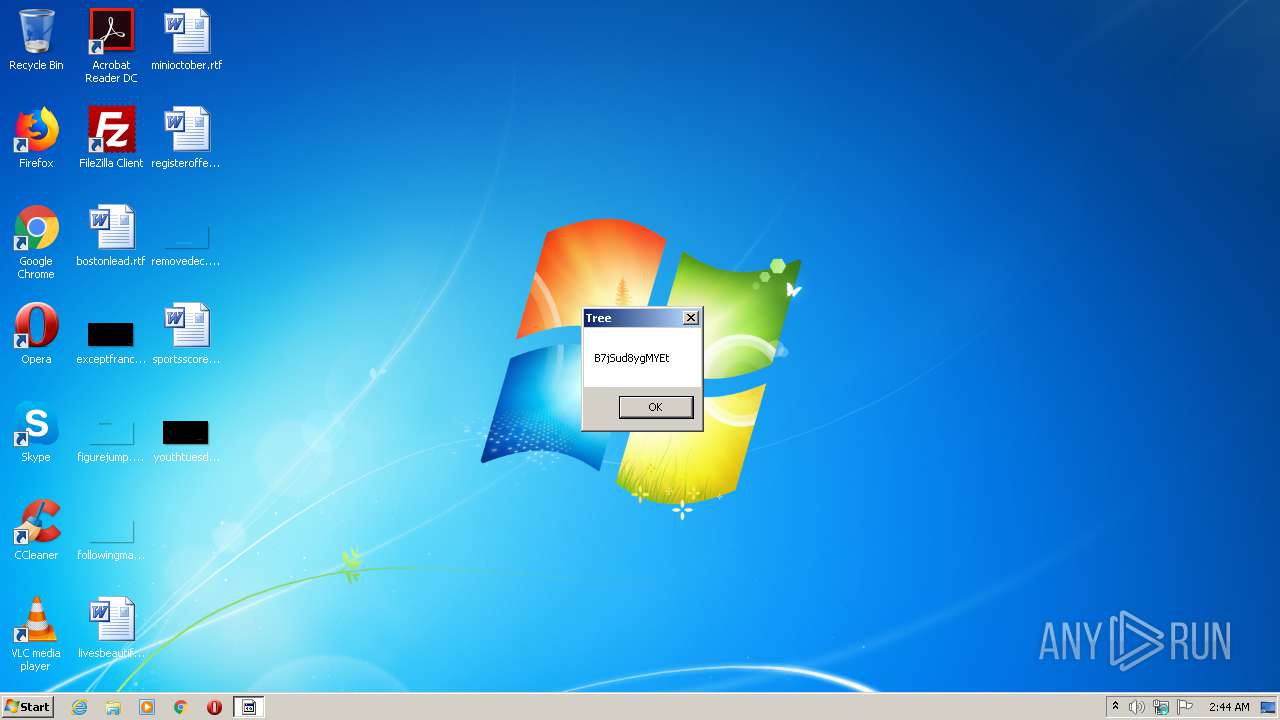
| InternalName: | Tree.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | Tree.exe |
| ProductName: | - |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jun-2018 15:13:43 |
| Comments: | rw |
| CompanyName: | - |
| FileDescription: | rw |
| FileVersion: | 0.0.0.0 |
| InternalName: | Tree.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | Tree.exe |
| ProductName: | - |
| ProductVersion: | 0.0.0.0 |
| Assembly Version: | 0.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 25-Jun-2018 15:13:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x0000E000 | 0x00280000 | 0x0002BA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99834 | |
.rsrc | 0x0000C000 | 0x00002000 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.90396 |
.data | 0x0028E000 | 0x000E4000 | 0x000E2A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9786 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06644 | 3362 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
advapi32.dll |
gdi32.dll |
kernel32.dll |
mscoree.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
39
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2820 | "C:\Users\admin\AppData\Local\Temp\fcdfg.exe" | C:\Users\admin\AppData\Local\Temp\fcdfg.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: rw Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
22
Read events
22
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
1 741
Text files
104
Unknown types
31
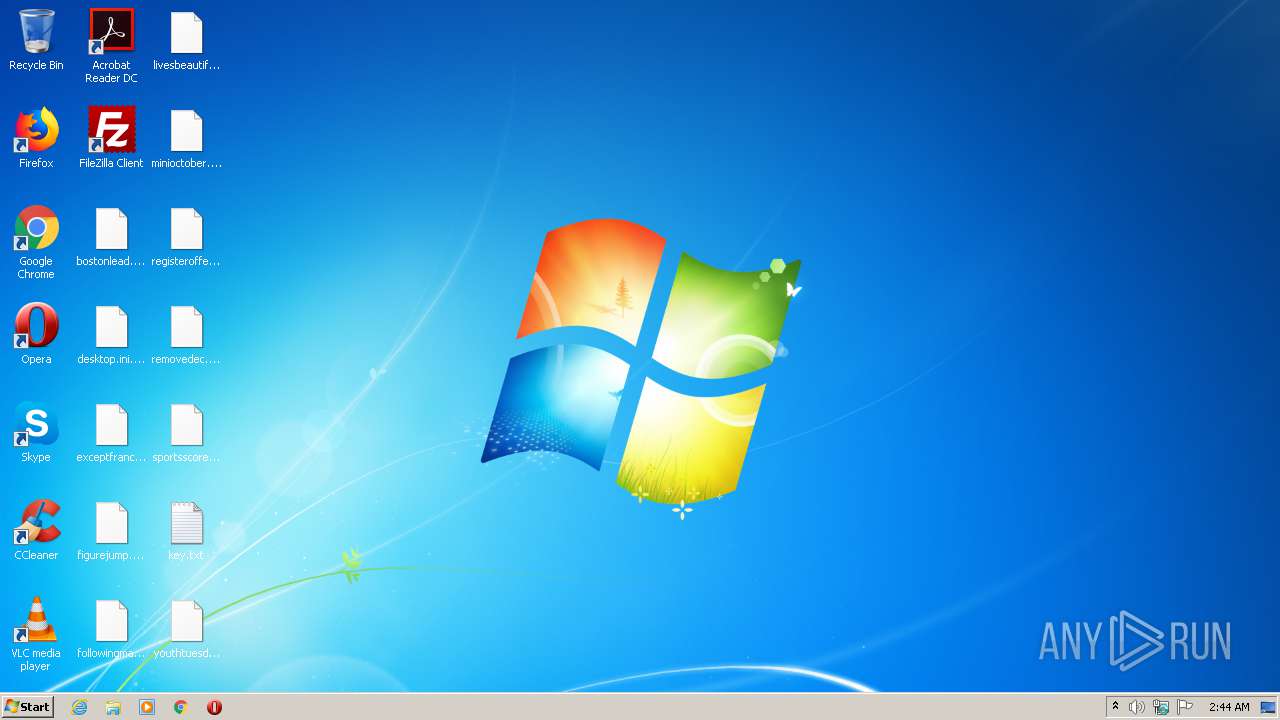
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2820 | fcdfg.exe | C:\Users\admin\Desktop\key.txt | text | |
MD5:— | SHA256:— | |||
| 2820 | fcdfg.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SharedDataEvents.enc | binary | |
MD5:— | SHA256:— | |||
| 2820 | fcdfg.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp.enc | binary | |
MD5:— | SHA256:— | |||
| 2820 | fcdfg.exe | C:\Users\admin\AppData\Local\IconCache.db.enc | binary | |
MD5:— | SHA256:— | |||
| 2820 | fcdfg.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\IconCacheRdr.dat.enc | binary | |
MD5:— | SHA256:— | |||
| 2820 | fcdfg.exe | C:\Users\admin\ntuser.ini.enc | binary | |
MD5:— | SHA256:— | |||
| 2820 | fcdfg.exe | C:\Users\admin\AppData\Local\Adobe\AcroCef\DC\Acrobat\Cache\data_0.enc | binary | |
MD5:— | SHA256:— | |||
| 2820 | fcdfg.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\UserCache.bin.enc | binary | |
MD5:— | SHA256:— | |||
| 2820 | fcdfg.exe | C:\Users\admin\AppData\Local\GDIPFONTCACHEV1.DAT.enc | binary | |
MD5:— | SHA256:— | |||
| 2820 | fcdfg.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\IconCacheRdr65536.dat.enc | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report