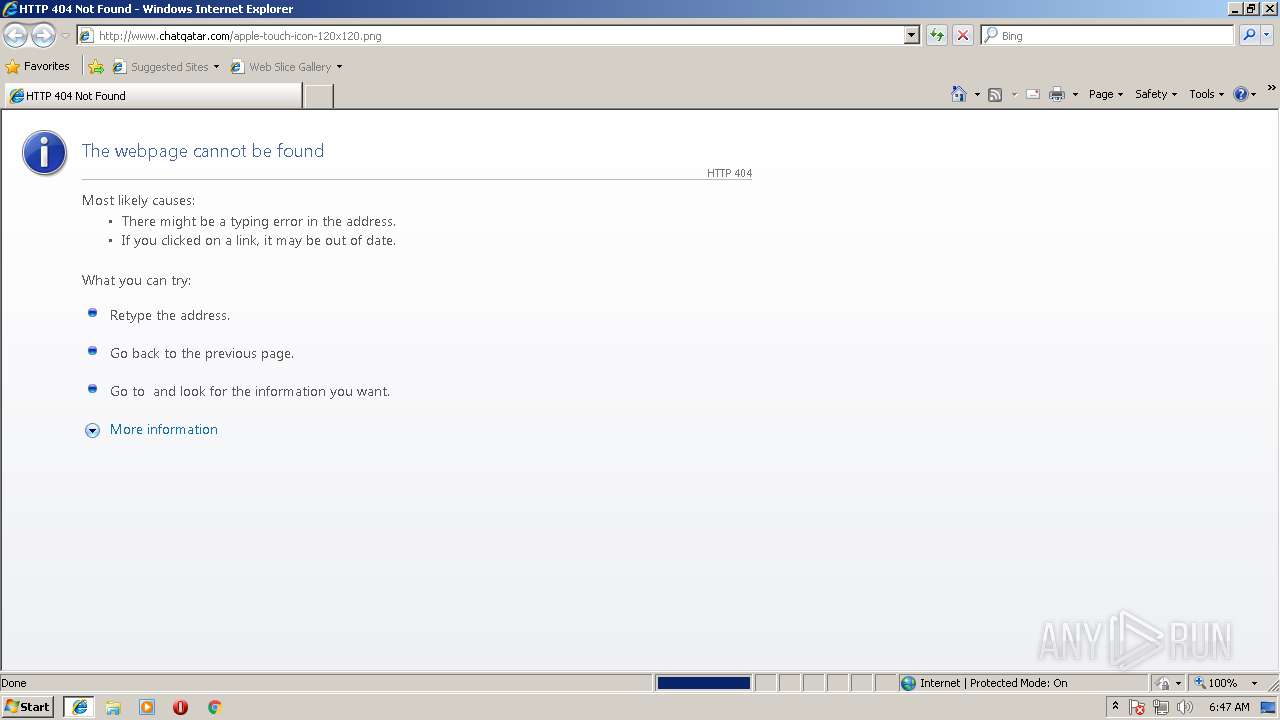
| URL: | http://www.chatqatar.com/apple-touch-icon-120x120.png |
| Full analysis: | https://app.any.run/tasks/43351bf3-5eca-4acf-89bb-9c2159e55840 |
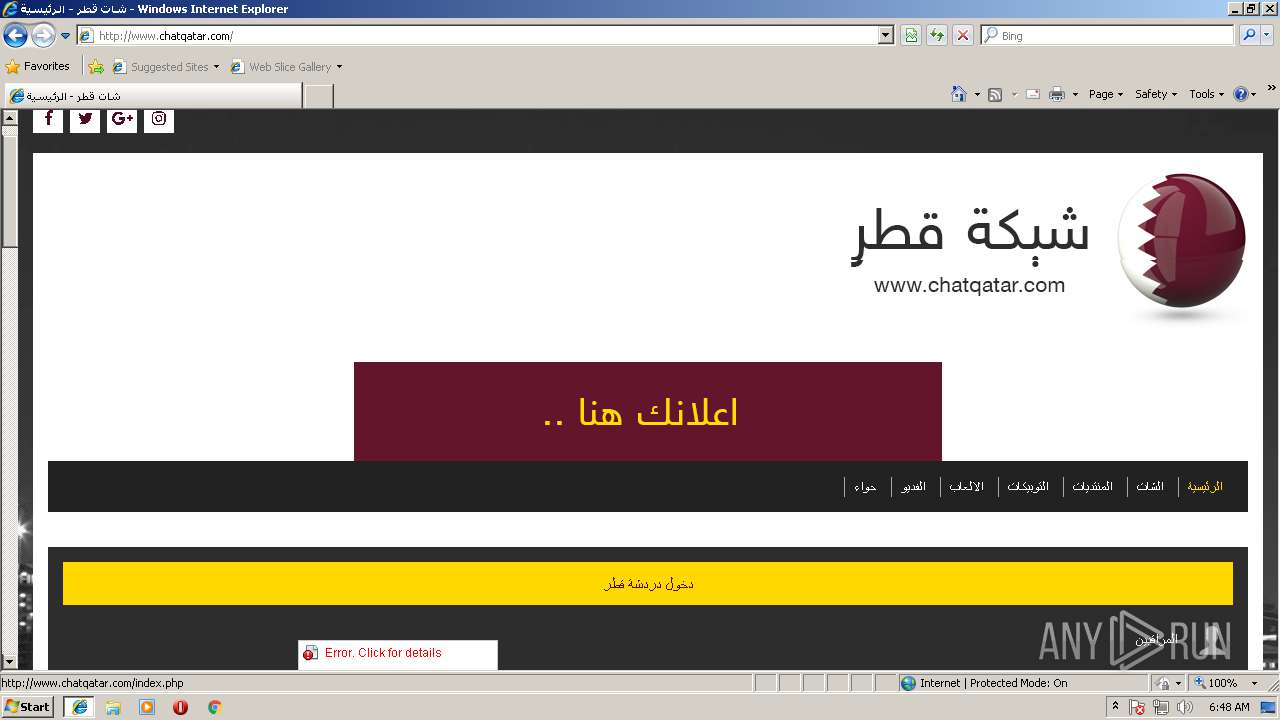
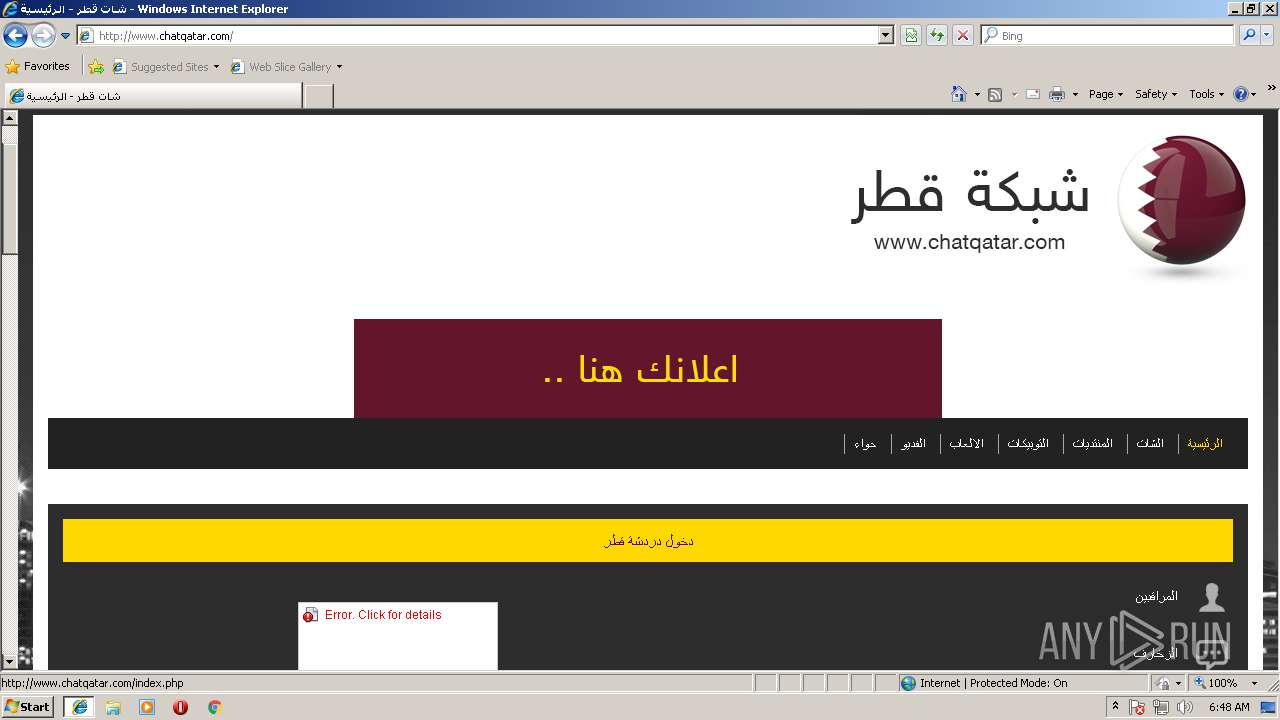
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2018, 05:47:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EF5C1FD01804F423225EA2F39DDC2AD0 |
| SHA1: | 846EDF600F8B5A08BCDD2FD1B00CFFD6D8C70B9D |
| SHA256: | C4B99FF783C6D94AB64909040C06AAB3BDB5C881F08D5A13E460B4003DA24433 |
| SSDEEP: | 3:N1KJS4vR+LdOGa2FuhC:Cc4J0IGchC |
MALICIOUS
No malicious indicators.SUSPICIOUS
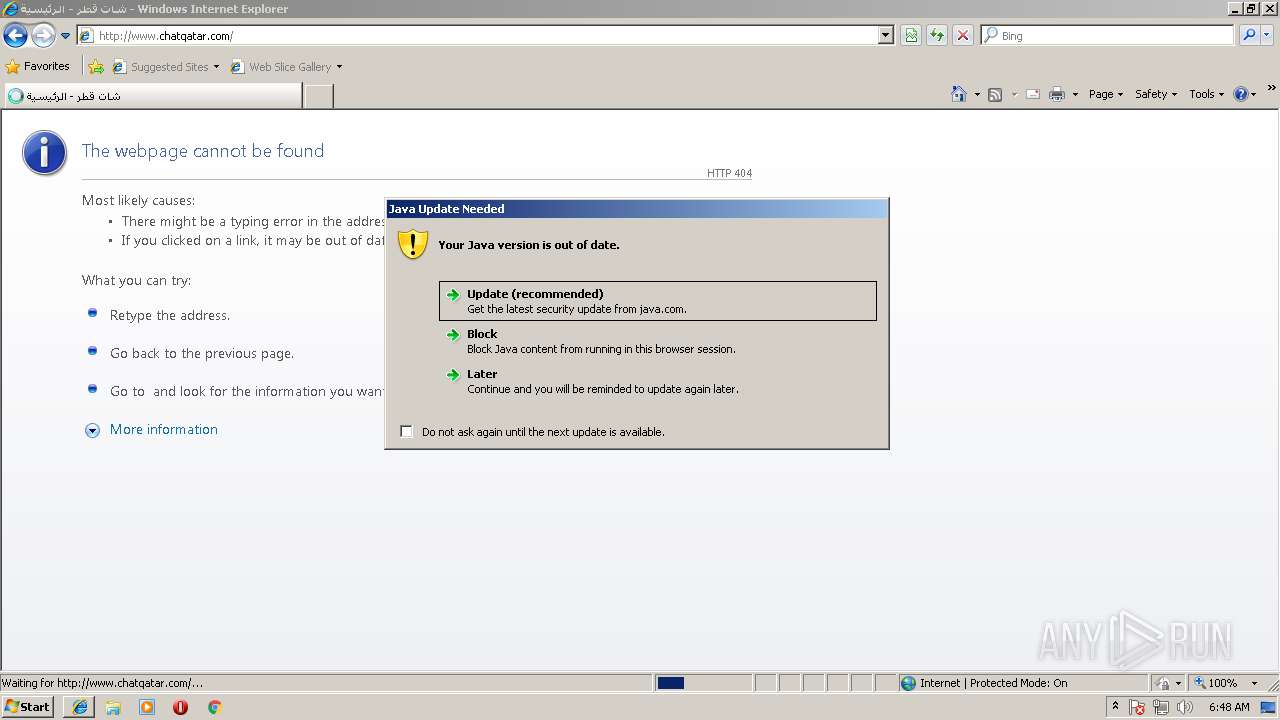
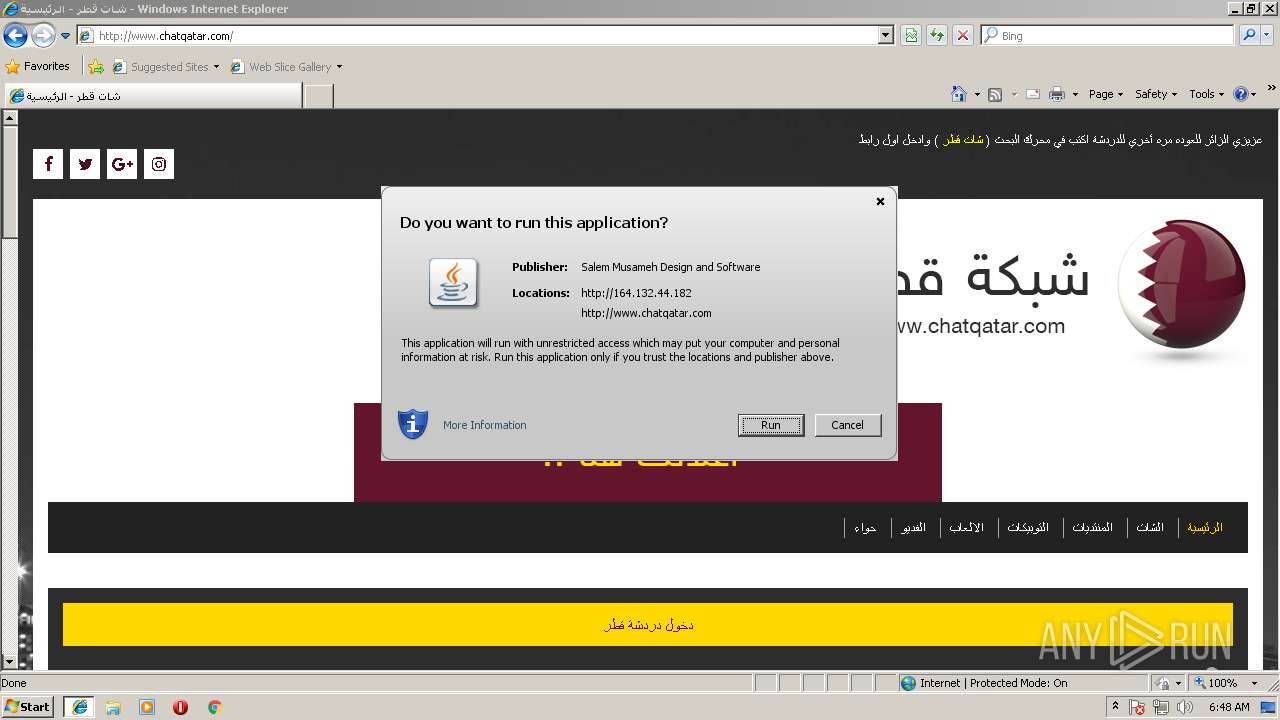
Executes JAVA applets
- iexplore.exe (PID: 2300)
Reads Internet Cache Settings
- jp2launcher.exe (PID: 3540)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2240)
Dropped object may contain URL's
- iexplore.exe (PID: 2300)
- iexplore.exe (PID: 2240)
- jp2launcher.exe (PID: 3540)
Reads Internet Cache Settings
- iexplore.exe (PID: 2300)
Reads internet explorer settings
- iexplore.exe (PID: 2300)
Application launched itself
- iexplore.exe (PID: 2240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
7
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 712 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_9\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.timestamp.11.92.2" "1533620895" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: LOW Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Java\jre1.8.0_92\bin\jp2launcher.exe" -secure -plugin -jre "C:\Program Files\Java\jre1.8.0_92" -vma LURfX2p2bV9sYXVuY2hlZD00NTIxNDk3MTY0AC1EX19hcHBsZXRfbGF1bmNoZWQ9NDUyMTQ4MjYwMwAtRHN1bi5hd3Qud2FybXVwPXRydWUALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIA -ma cmVhZF9waXBlX25hbWU9anBpMl9waWQyMzAwX3BpcGUyLHdyaXRlX3BpcGVfbmFtZT1qcGkyX3BpZDIzMDBfcGlwZTMA | C:\Program Files\Java\jre1.8.0_92\bin\jp2launcher.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: LOW Description: Java(TM) Web Launcher Exit code: 0 Version: 11.92.2.14 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_9\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.11.92.2" "later" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: LOW Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.chatqatar.com/apple-touch-icon-120x120.png | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2240 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3444 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_9\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.suppression.11.92.2" "false" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | — | iexplore.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: LOW Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 3540 | "C:\Program Files\Java\jre1.8.0_92\bin\jp2launcher.exe" -secure -plugin -jre "C:\Program Files\Java\jre1.8.0_92" -vma LURfX2p2bV9sYXVuY2hlZD00NTIxNDk3MTY0AC1EX19hcHBsZXRfbGF1bmNoZWQ9NDUyMTQ4MjYwMwAtRHN1bi5hd3Qud2FybXVwPXRydWUALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIA -ma cmVhZF9waXBlX25hbWU9anBpMl9waWQyMzAwX3BpcGUyLHdyaXRlX3BpcGVfbmFtZT1qcGkyX3BpZDIzMDBfcGlwZTMA | C:\Program Files\Java\jre1.8.0_92\bin\jp2launcher.exe | iexplore.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.92.2.14 Modules
| |||||||||||||||
Total events
583
Read events
442
Write events
131
Delete events
10
Modification events
| (PID) Process: | (2240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000048000000010000000000000000000000000000000000000000000000B096B68868EBD301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000D8BFD602040000000000000000000000000000000000000000000000F4BFD602040000000000000000000000000000000000000000000000D8372A0000000000FFFFFFFF000000000000000000000000010000002E00000000000000000000000000000002000000C0A801640000000000000000D84ED505AC02000005000000010000000000000000000000010000000000000000000000BF060000000000000000000000000000000000001000000088C0D60204000000000000000000000000000000000000000000000000000000C8E40C00000000000C0000000000000000000000 | |||
| (PID) Process: | (2240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {6F7DD395-9A05-11E8-ACE5-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (2240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 10 | |||
| (PID) Process: | (2240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E20708000200070005002F003A004D01 | |||
Executable files
1
Suspicious files
4
Text files
42
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2240 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2240 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2300 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5A31W00O\chatqatar_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 2300 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 2240 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 2300 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5A31W00O\chatqatar_com[1].htm | html | |
MD5:— | SHA256:— | |||
| 2300 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5A31W00O\hint.min[1].css | text | |
MD5:— | SHA256:— | |||
| 2300 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5A31W00O\info_48[1] | image | |
MD5:49E0EF03E74704089A60C437085DB89E | SHA256:CAA140523BA00994536B33618654E379216261BABAAE726164A0F74157BB11FF | |||
| 2300 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5A31W00O\bootstrap.min-arabic[1].css | text | |
MD5:— | SHA256:— | |||
| 2300 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DSILEDM7\bullet[1] | image | |
MD5:0C4C086DD852704E8EEB8FF83E3B73D1 | SHA256:1CB3B6EA56C5B5DECF5E1D487AD51DBB2F62E6A6C78F23C1C81FDA1B64F8DB16 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
23
DNS requests
11
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2300 | iexplore.exe | GET | 200 | 94.130.150.147:80 | http://www.chatqatar.com/ | DE | html | 13.6 Kb | unknown |
2300 | iexplore.exe | GET | 200 | 94.130.150.147:80 | http://www.chatqatar.com/assest/g.css | DE | text | 428 b | unknown |
2300 | iexplore.exe | GET | 404 | 94.130.150.147:80 | http://www.chatqatar.com/apple-touch-icon-120x120.png | DE | html | 345 b | unknown |
2300 | iexplore.exe | GET | 200 | 94.130.150.147:80 | http://www.chatqatar.com/assest/css/bootstrap.min-arabic.css | DE | text | 113 Kb | unknown |
2300 | iexplore.exe | GET | 200 | 164.132.44.182:80 | http://164.132.44.182/DigiChat/jsf/chatqatar.js | FR | text | 271 b | suspicious |
2300 | iexplore.exe | GET | 200 | 94.130.150.147:80 | http://www.chatqatar.com/assest/imgs/bg.jpg | DE | image | 711 Kb | unknown |
2300 | iexplore.exe | GET | 200 | 94.130.150.147:80 | http://www.chatqatar.com/assest/imgs/ic2.jpg | DE | image | 2.10 Kb | unknown |
2300 | iexplore.exe | GET | 200 | 94.130.150.147:80 | http://www.chatqatar.com/assest/fonts/glyphicons-halflings-regular.eot? | DE | eot | 19.6 Kb | unknown |
2300 | iexplore.exe | GET | 200 | 212.47.239.38:80 | http://c1.al-yasser.info/mtajr/style/assest/jquery.js | FR | text | 93.6 Kb | unknown |
2240 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2300 | iexplore.exe | 94.130.150.147:80 | www.chatqatar.com | Hetzner Online GmbH | DE | unknown |
2240 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2300 | iexplore.exe | 164.132.44.182:80 | — | OVH SAS | FR | suspicious |
2300 | iexplore.exe | 216.58.215.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2300 | iexplore.exe | 212.47.239.38:80 | c1.al-yasser.info | Online S.a.s. | FR | unknown |
3540 | jp2launcher.exe | 164.132.44.182:80 | — | OVH SAS | FR | suspicious |
2240 | iexplore.exe | 94.130.150.147:80 | www.chatqatar.com | Hetzner Online GmbH | DE | unknown |
3540 | jp2launcher.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3540 | jp2launcher.exe | 23.37.43.27:80 | s2.symcb.com | Akamai Technologies, Inc. | NL | whitelisted |
3540 | jp2launcher.exe | 104.111.238.56:443 | javadl-esd-secure.oracle.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.chatqatar.com |
| unknown |
www.bing.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
c1.al-yasser.info |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
javadl-esd-secure.oracle.com |
| whitelisted |
status.geotrust.com |
| whitelisted |
s2.symcb.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3540 | jp2launcher.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
3540 | jp2launcher.exe | Potentially Bad Traffic | ET INFO Java .jar request to dotted-quad domain |
3540 | jp2launcher.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download By Vulnerable Client |
3540 | jp2launcher.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |