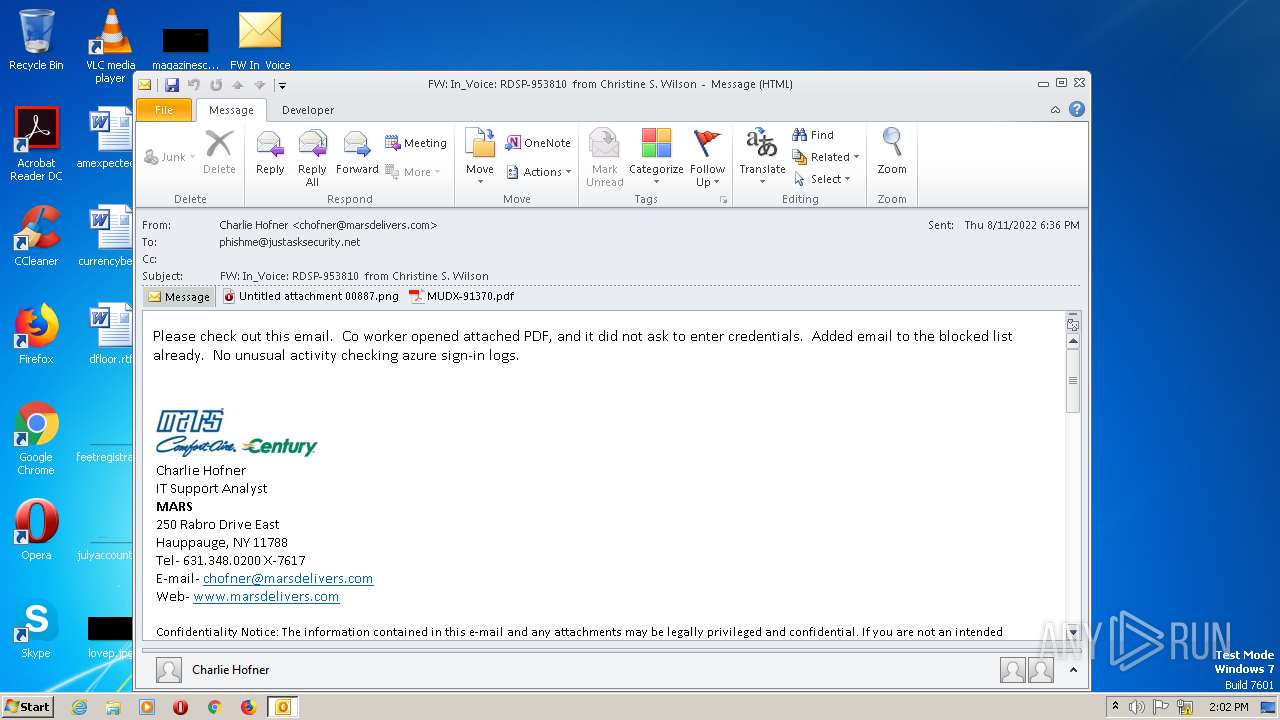
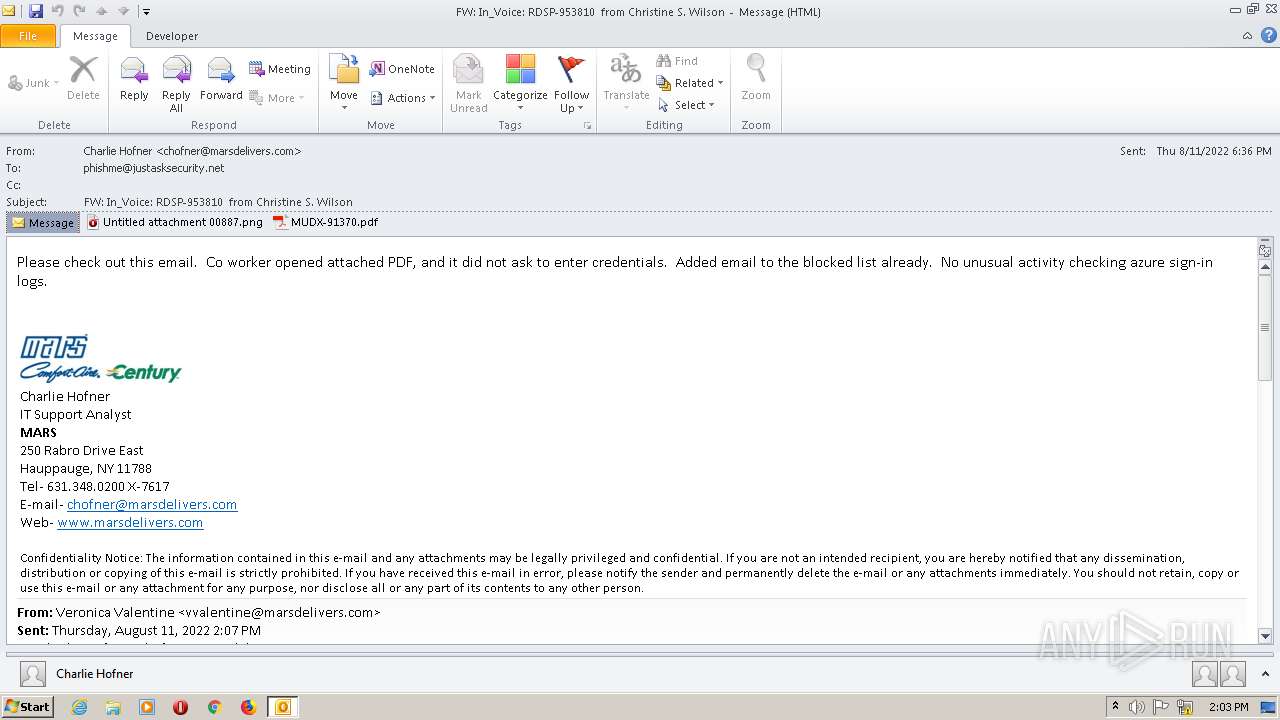
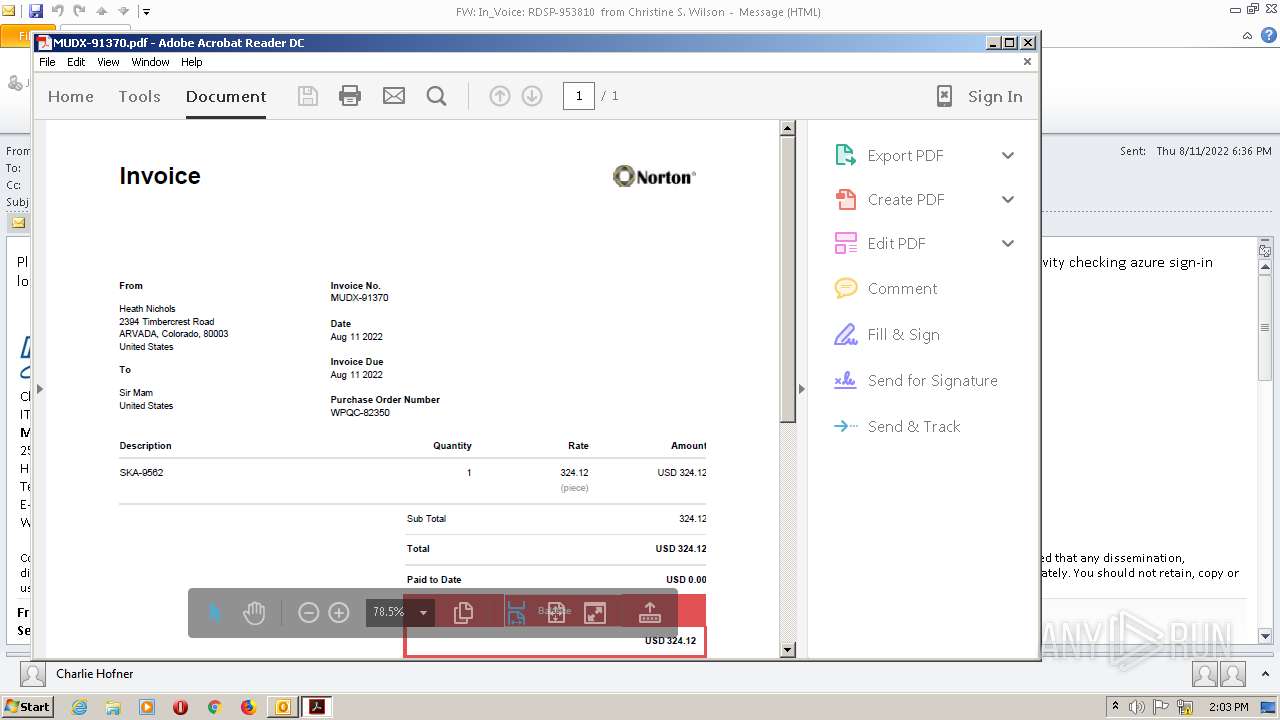
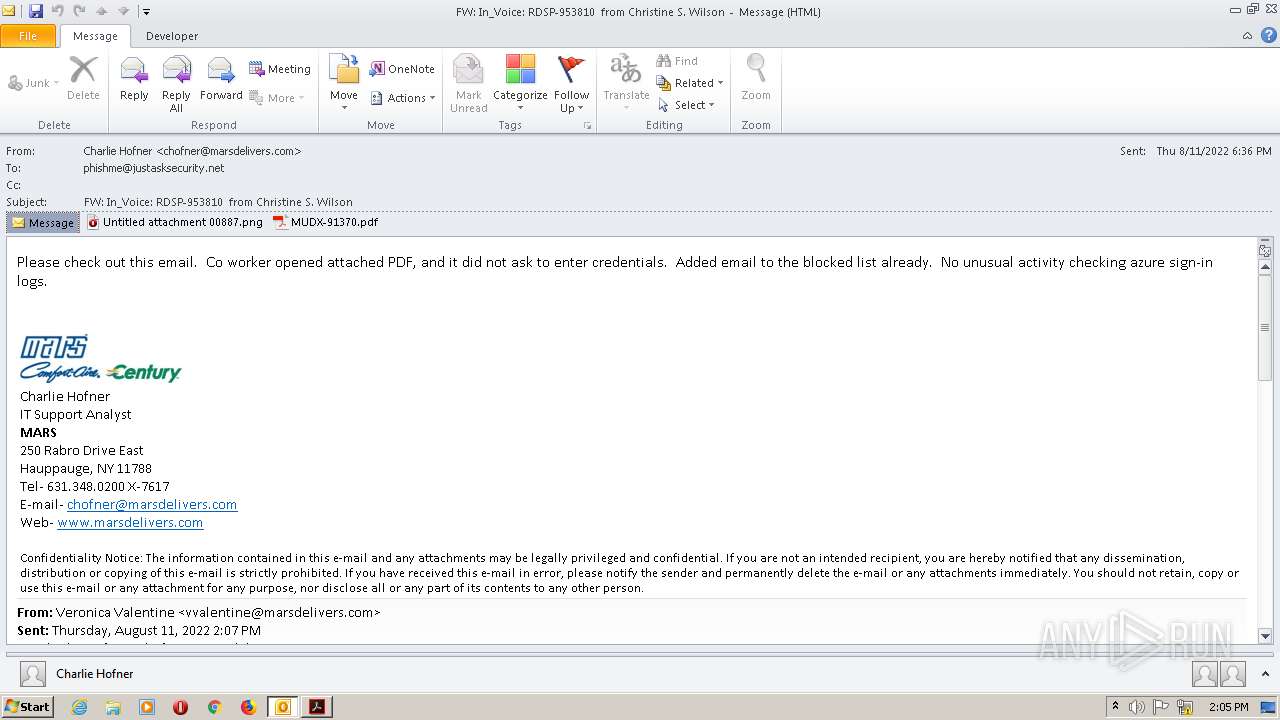
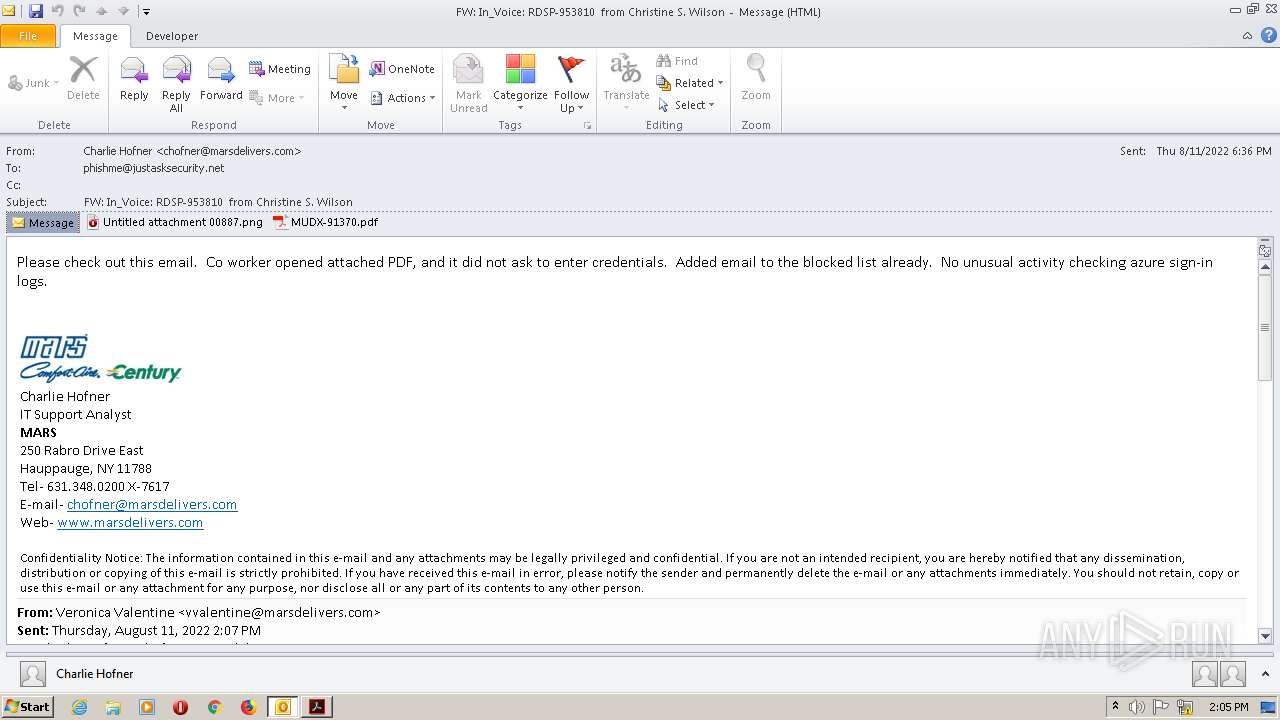
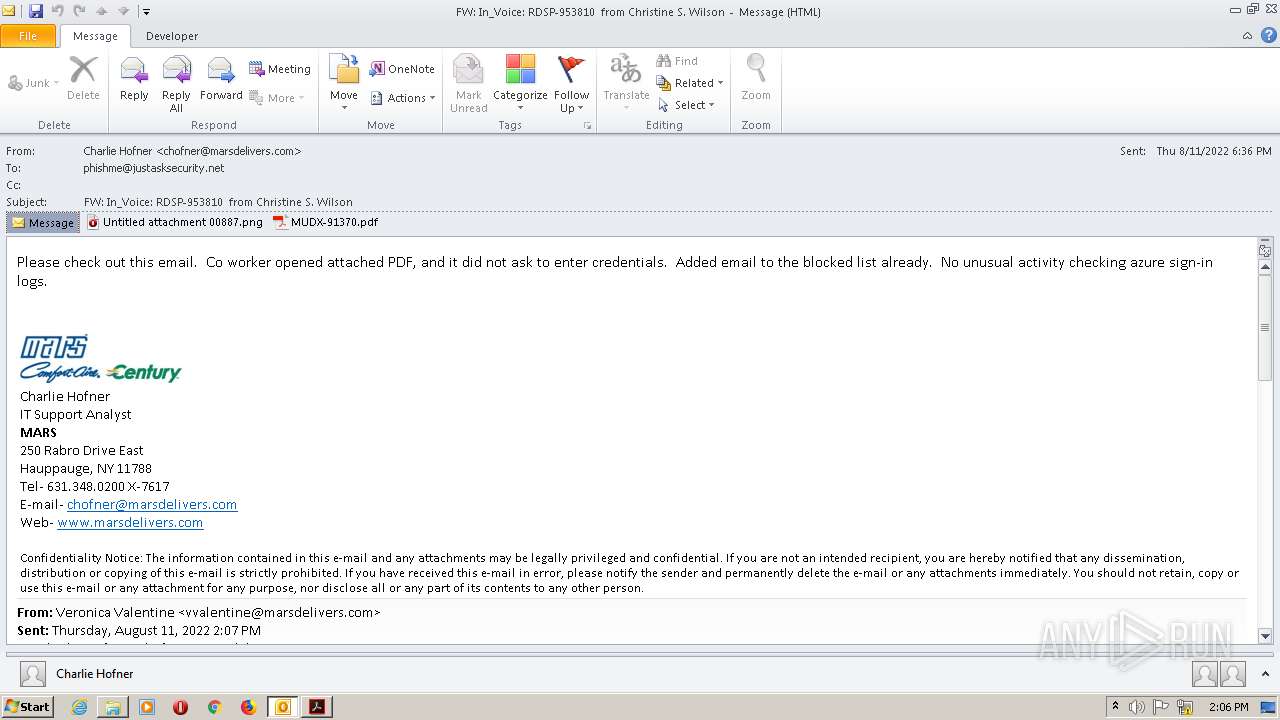
| File name: | FW In_Voice RDSP-953810 from Christine S. Wilson.msg |
| Full analysis: | https://app.any.run/tasks/4256dee2-a6df-466a-b799-a26e103f8579 |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 14:02:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | EF3052FAB2AE98CDE1C0123C5F1CA7B0 |
| SHA1: | B38CDD1AC1AA0BF63648F7583FFA310B93A9A5D1 |
| SHA256: | C4B6B303CA4EB913AE1B2CA7966CDED13A5AD0A0F177EF9144D430925803EC12 |
| SSDEEP: | 6144:QFXXcEisufS0zRjQWeerw/6X5pdmRBR7csV2iUgUadiCj6G8dKsbhBGZXS:uQX+zeM6X5pxE0RamdKihIBS |
MALICIOUS
Drops executable file immediately after starts
- AdobeARM.exe (PID: 2912)
- firefox.exe (PID: 1952)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 2624)
Checks supported languages
- opera_plugin_wrapper_32.exe (PID: 384)
- AdobeARM.exe (PID: 2912)
- Reader_sl.exe (PID: 2688)
- gup.exe (PID: 676)
- notepad++.exe (PID: 1432)
Creates files in the program directory
- AdobeARM.exe (PID: 2912)
Reads the computer name
- AdobeARM.exe (PID: 2912)
- gup.exe (PID: 676)
- notepad++.exe (PID: 1432)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 2912)
- firefox.exe (PID: 1952)
Drops a file with a compile date too recent
- AdobeARM.exe (PID: 2912)
- firefox.exe (PID: 1952)
Reads default file associations for system extensions
- chrome.exe (PID: 4604)
INFO
Searches for installed software
- OUTLOOK.EXE (PID: 2732)
- AcroRd32.exe (PID: 3040)
- AcroRd32.exe (PID: 2356)
Checks supported languages
- OUTLOOK.EXE (PID: 2732)
- Opera.exe (PID: 3016)
- DllHost.exe (PID: 2624)
- opera_plugin_wrapper.exe (PID: 2900)
- AcroRd32.exe (PID: 3040)
- AcroRd32.exe (PID: 2356)
- RdrCEF.exe (PID: 1740)
- RdrCEF.exe (PID: 1660)
- RdrCEF.exe (PID: 472)
- explorer.exe (PID: 2932)
- firefox.exe (PID: 1952)
- firefox.exe (PID: 3044)
- firefox.exe (PID: 2124)
- firefox.exe (PID: 2080)
- firefox.exe (PID: 3664)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 3288)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 3720)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 3192)
- chrome.exe (PID: 4064)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 4204)
- chrome.exe (PID: 3800)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 984)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 4500)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 4524)
- chrome.exe (PID: 4832)
- chrome.exe (PID: 4324)
- chrome.exe (PID: 964)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 4480)
- chrome.exe (PID: 4656)
- chrome.exe (PID: 4292)
- chrome.exe (PID: 4688)
- chrome.exe (PID: 5060)
- pingsender.exe (PID: 4800)
- pingsender.exe (PID: 4252)
- chrome.exe (PID: 4584)
- chrome.exe (PID: 4636)
- chrome.exe (PID: 4604)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 4384)
Reads the computer name
- OUTLOOK.EXE (PID: 2732)
- DllHost.exe (PID: 2624)
- Opera.exe (PID: 3016)
- AcroRd32.exe (PID: 3040)
- AcroRd32.exe (PID: 2356)
- RdrCEF.exe (PID: 1740)
- explorer.exe (PID: 2932)
- firefox.exe (PID: 1952)
- firefox.exe (PID: 3044)
- firefox.exe (PID: 2124)
- firefox.exe (PID: 2080)
- firefox.exe (PID: 3664)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 4092)
- pingsender.exe (PID: 4252)
- chrome.exe (PID: 4584)
- chrome.exe (PID: 4604)
- pingsender.exe (PID: 4800)
Check for Java to be installed
- Opera.exe (PID: 3016)
Dropped object may contain Bitcoin addresses
- Opera.exe (PID: 3016)
- firefox.exe (PID: 1952)
- chrome.exe (PID: 3184)
Reads the date of Windows installation
- Opera.exe (PID: 3016)
- firefox.exe (PID: 1952)
- chrome.exe (PID: 4584)
Application launched itself
- AcroRd32.exe (PID: 3040)
- RdrCEF.exe (PID: 1740)
- firefox.exe (PID: 1952)
- chrome.exe (PID: 3184)
Reads CPU info
- AcroRd32.exe (PID: 2356)
- RdrCEF.exe (PID: 1740)
- RdrCEF.exe (PID: 1660)
- RdrCEF.exe (PID: 472)
- firefox.exe (PID: 1952)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2732)
- AcroRd32.exe (PID: 2356)
Reads settings of System Certificates
- AcroRd32.exe (PID: 3040)
- RdrCEF.exe (PID: 1740)
- AdobeARM.exe (PID: 2912)
- chrome.exe (PID: 4092)
- pingsender.exe (PID: 4800)
- pingsender.exe (PID: 4252)
Checks Windows Trust Settings
- AdobeARM.exe (PID: 2912)
- pingsender.exe (PID: 4252)
- pingsender.exe (PID: 4800)
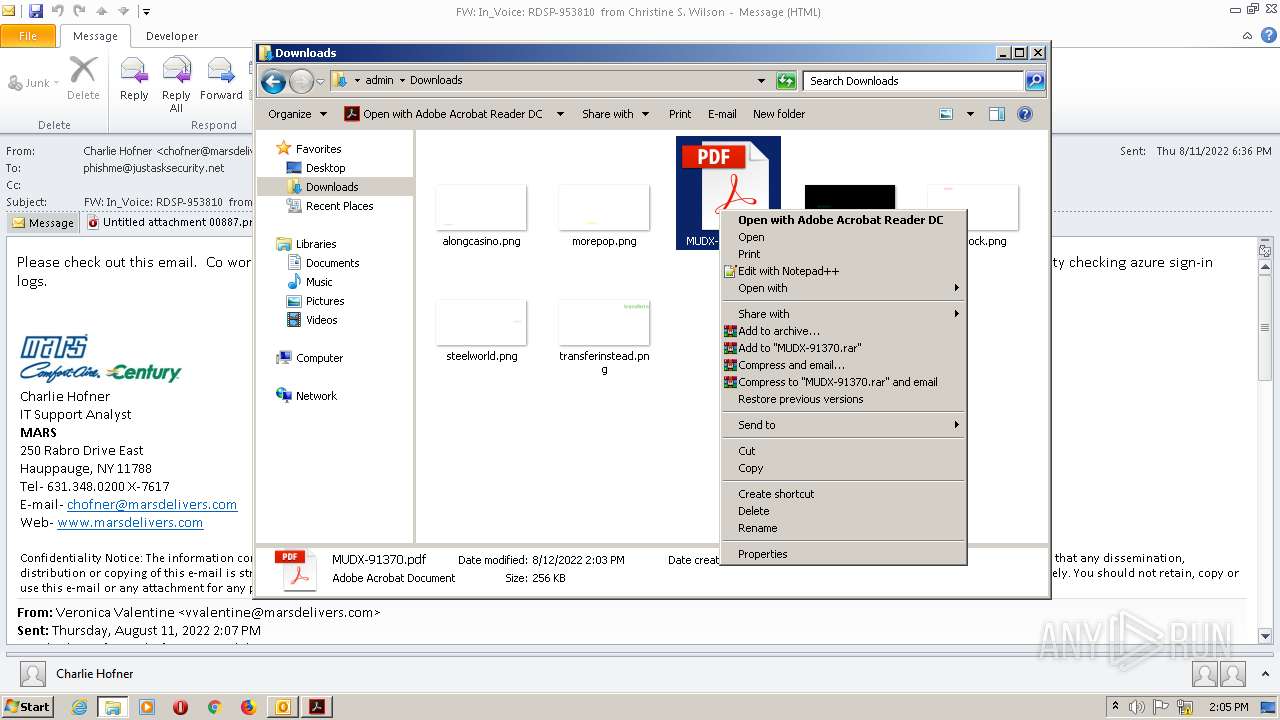
Manual execution by user
- explorer.exe (PID: 2932)
- notepad++.exe (PID: 1432)
- firefox.exe (PID: 1952)
- chrome.exe (PID: 3184)
Creates files in the program directory
- firefox.exe (PID: 1952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
100
Monitored processes
55
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 384 | "C:\Program Files\Opera x64\pluginwrapper\opera_plugin_wrapper_32.exe" -newprocess "3016 5 0 1 3" -logfolder "C:\Users\admin\AppData\Local\Opera\Opera x64\logs" | C:\Program Files\Opera x64\pluginwrapper\opera_plugin_wrapper_32.exe | — | Opera.exe | |||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser plugin wrapper Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 472 | "C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-delegated-renderer --disable-desktop-notifications --disable-file-system --disable-shared-workers --disable-speech-input --disable-threaded-compositing --disable-webaudio --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.7.20033 Chrome/35.0.1916.138" --disable-accelerated-compositing --disable-accelerated-video-decode --enable-software-compositing --disable-gpu-compositing --channel="1740.1.1584375898\1655501671" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.7.20033.133275 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 -px64 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 964 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1072,13838505169457364123,9974732059070511620,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3686057688005931521 --mojo-platform-channel-handle=4288 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 984 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1072,13838505169457364123,9974732059070511620,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2338013638056239526 --mojo-platform-channel-handle=4000 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
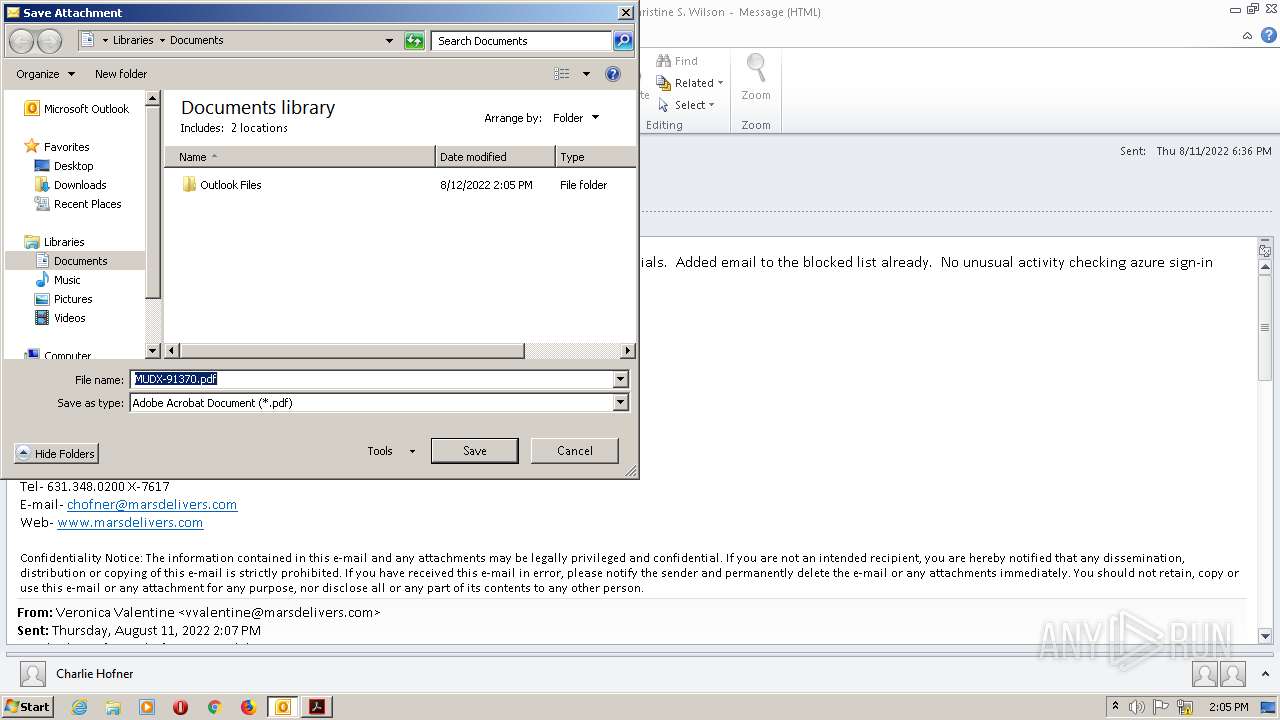
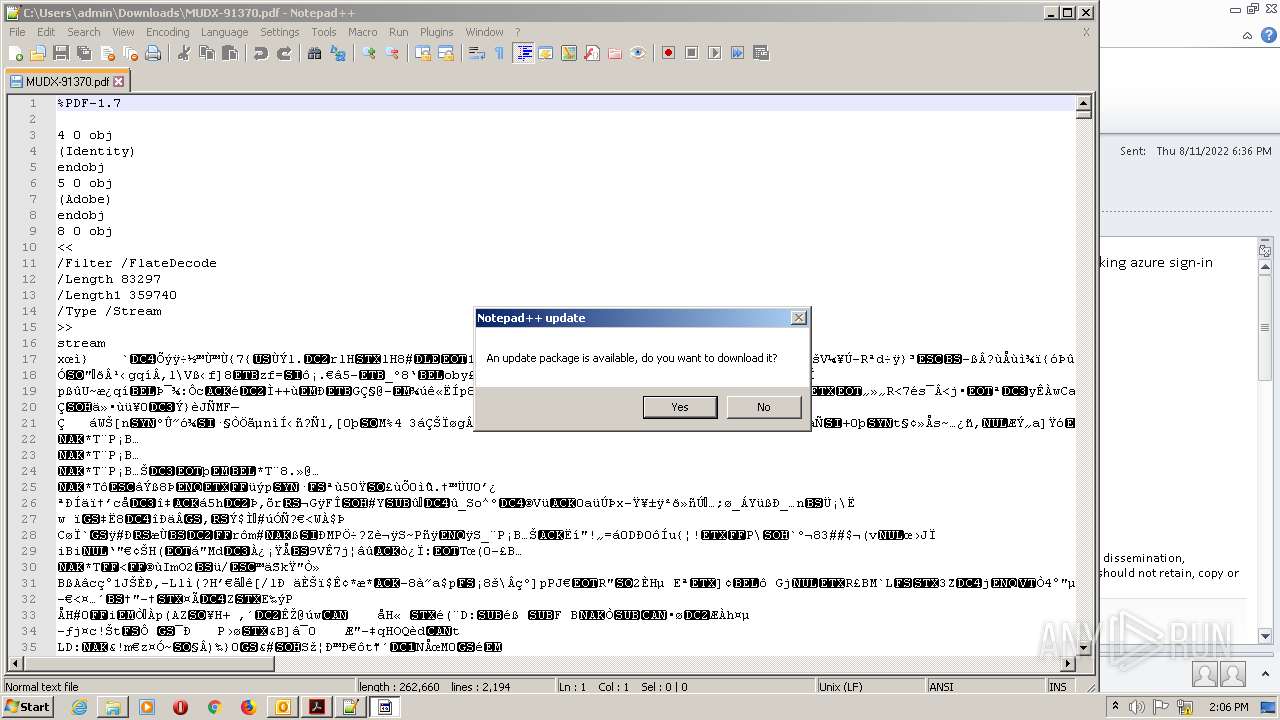
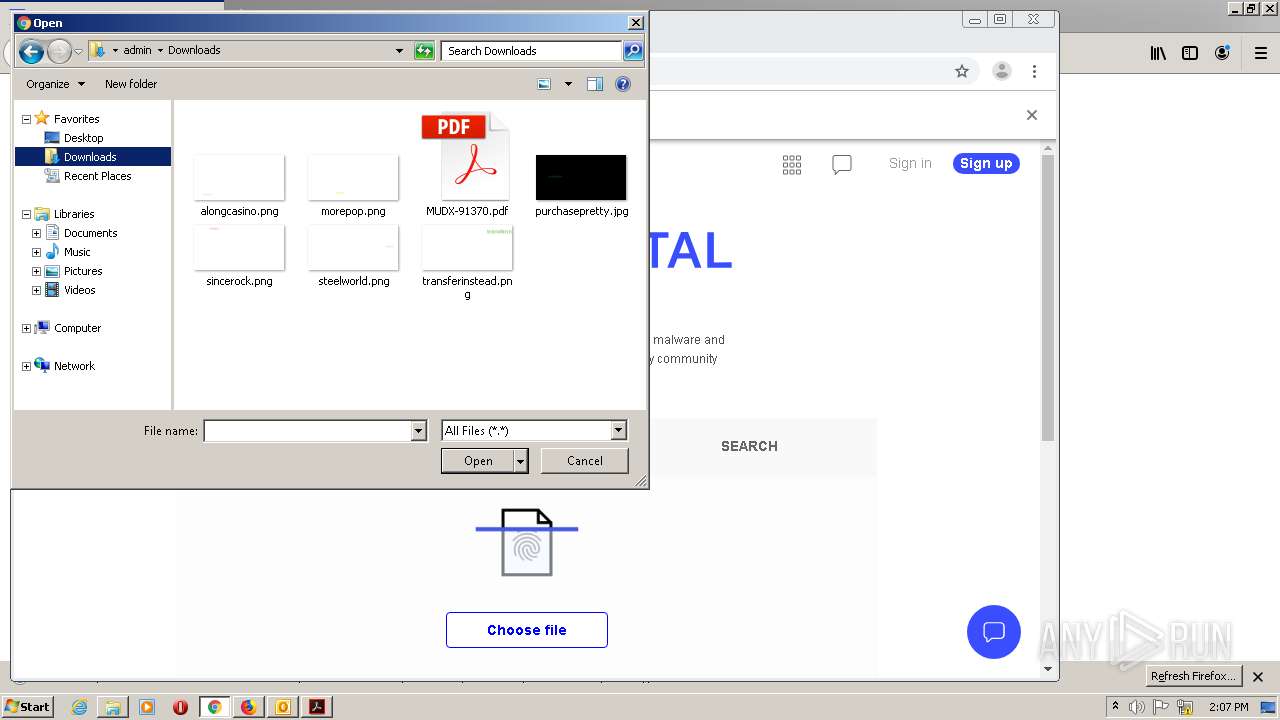
| 1432 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Downloads\MUDX-91370.pdf" | C:\Program Files\Notepad++\notepad++.exe | Explorer.EXE | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 1660 | "C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-delegated-renderer --disable-desktop-notifications --disable-file-system --disable-shared-workers --disable-speech-input --disable-threaded-compositing --disable-webaudio --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.7.20033 Chrome/35.0.1916.138" --disable-accelerated-compositing --disable-accelerated-video-decode --enable-software-compositing --disable-gpu-compositing --channel="1740.0.816148788\1355740763" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.7.20033.133275 Modules
| |||||||||||||||
| 1740 | "C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" | C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.7.20033.133275 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | Explorer.EXE | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1952.13.1587912698\362212307" -childID 2 -isForBrowser -prefsHandle 2900 -prefMapHandle 2916 -prefsLen 5823 -prefMapSize 189239 -parentBuildID 20190619235627 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1952 "\\.\pipe\gecko-crash-server-pipe.1952" 2928 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 67.0.4 Modules
| |||||||||||||||
Total events
33 579
Read events
32 450
Write events
1 099
Delete events
30
Modification events
| (PID) Process: | (2732) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2732) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2732) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2732) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2732) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2732) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2732) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2732) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2732) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2732) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
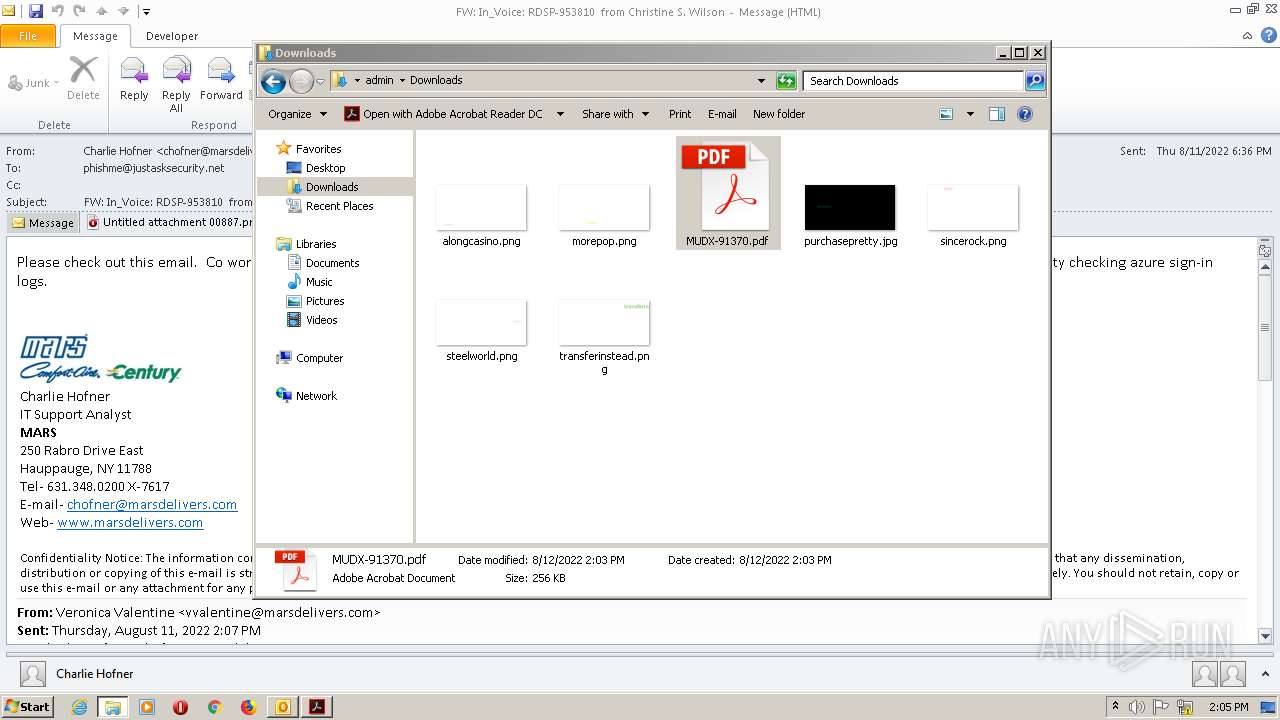
Executable files
6
Suspicious files
634
Text files
262
Unknown types
123
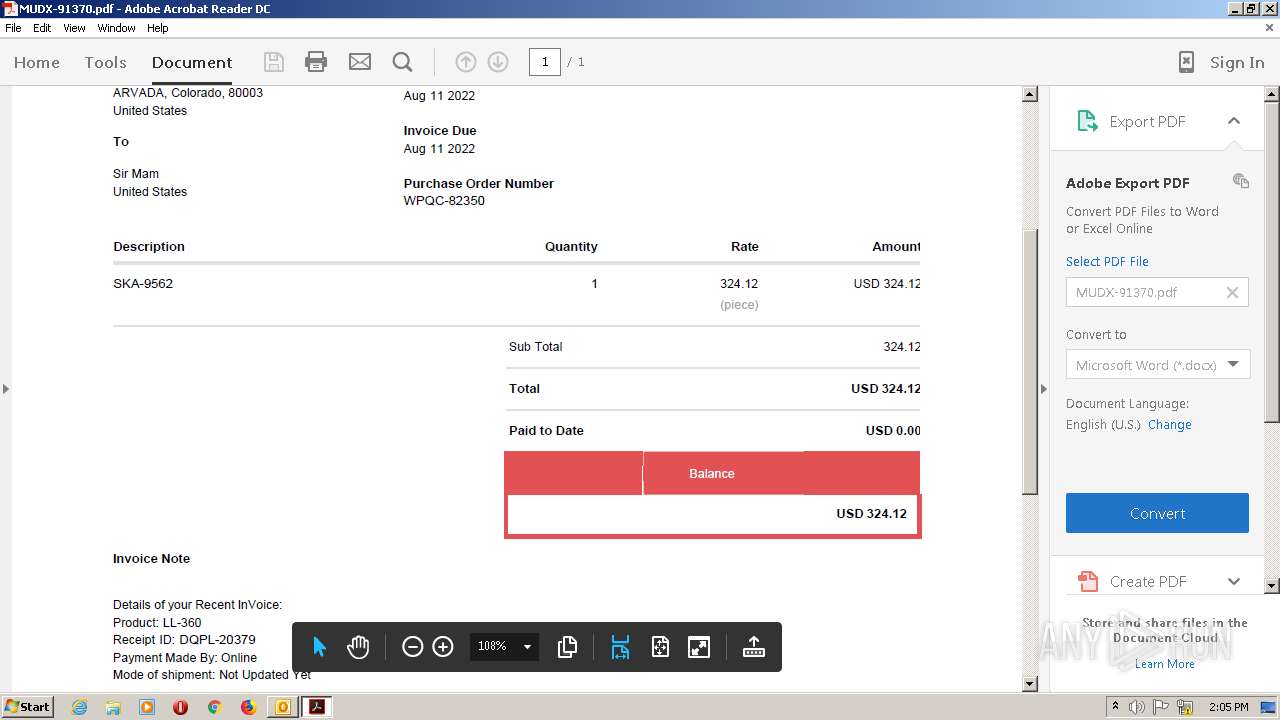
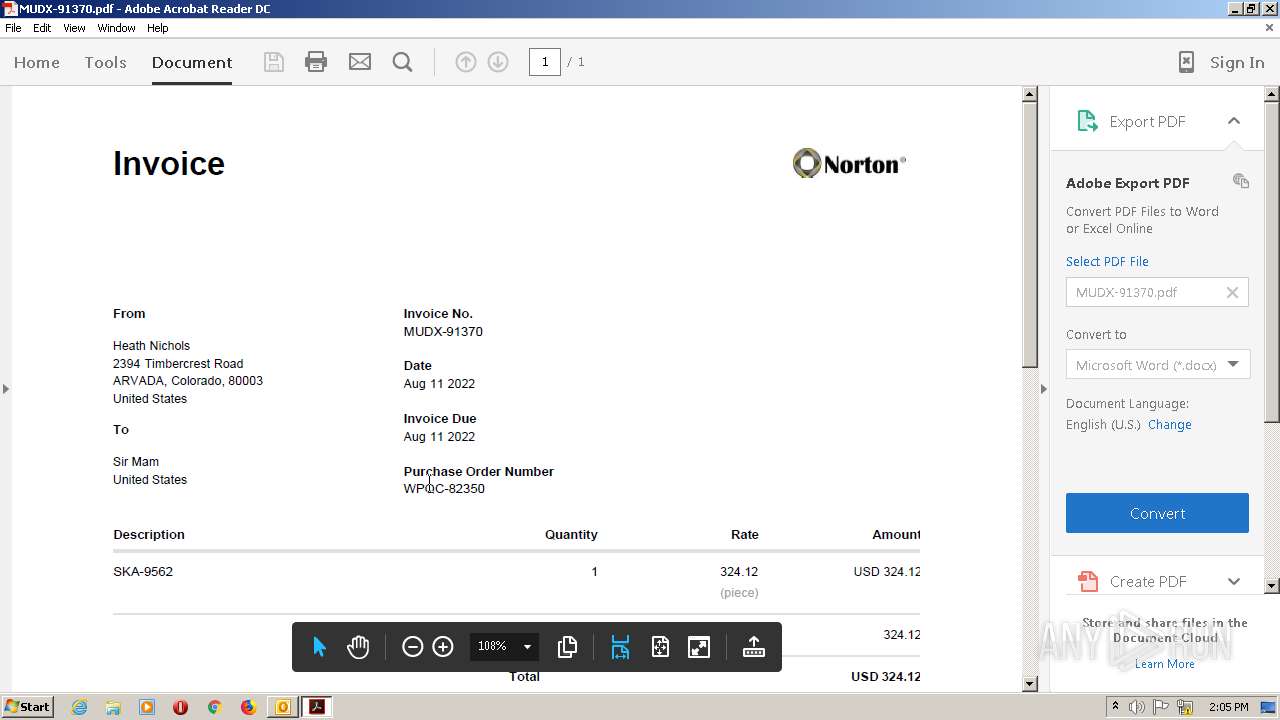
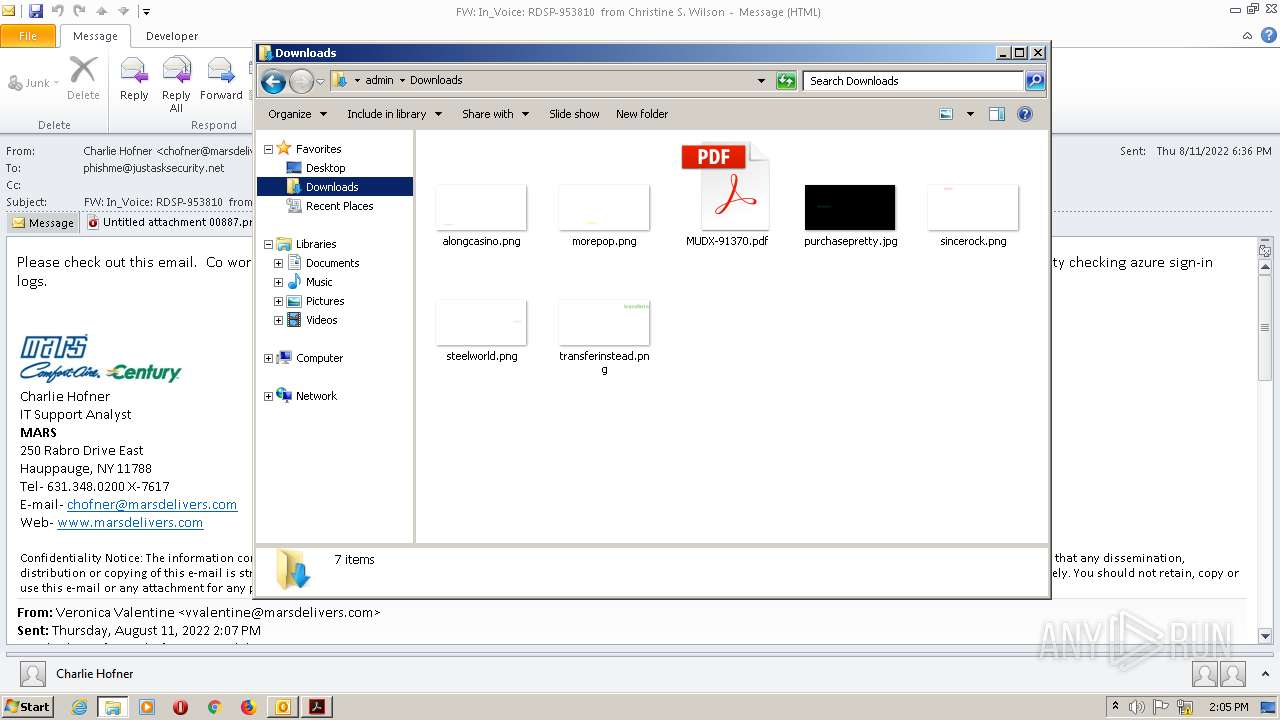
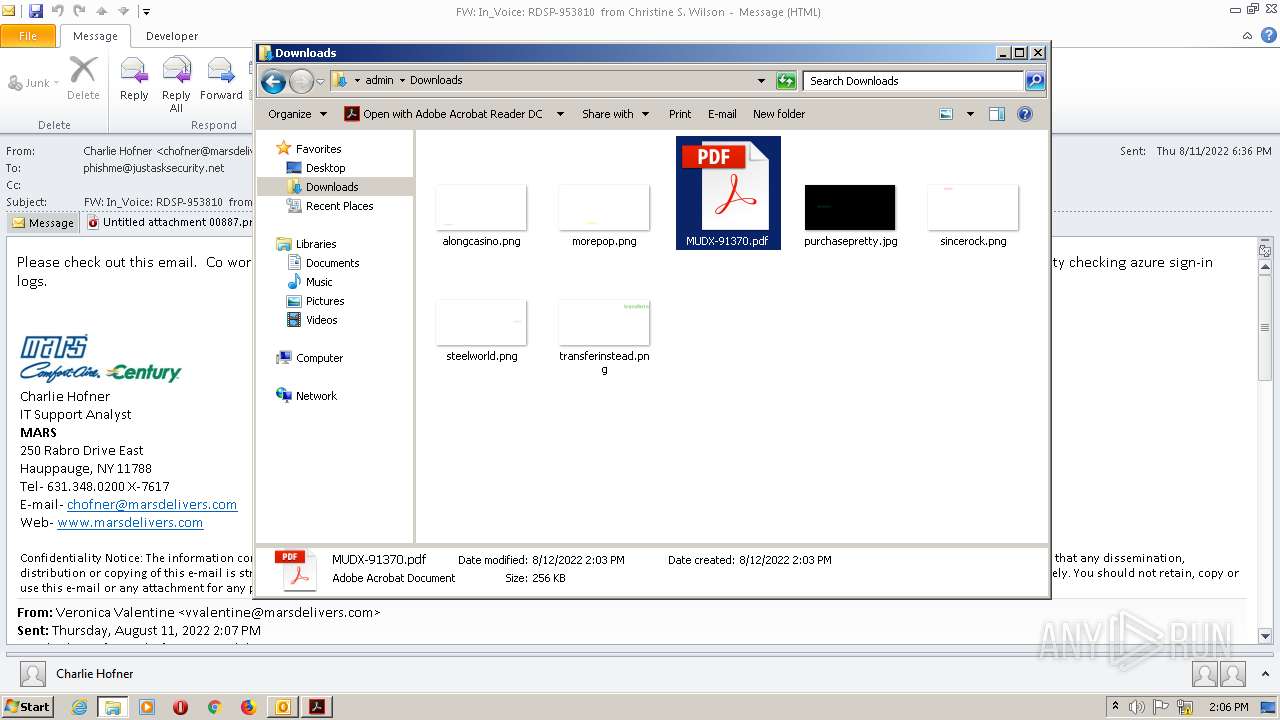
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2732 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA60F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2732 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2624 | DllHost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\WebCacheV01.dat | — | |
MD5:— | SHA256:— | |||
| 2624 | DllHost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\V01.log | binary | |
MD5:— | SHA256:— | |||
| 2732 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2732 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2624 | DllHost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WebCache\V01.chk | binary | |
MD5:— | SHA256:— | |||
| 2732 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\EDE4D17F.tmp | image | |
MD5:BBD13EBCFCB693DE7E7D2577152644F0 | SHA256:F75852BC676534EFC42275793AE286CF633D620E6C4DC090B2B00271412FBB4B | |||
| 2732 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\FORMS\FRMDATA64.DAT | binary | |
MD5:C4643157E488AC6D771054CAD7D50D84 | SHA256:D4FF48EB72AA94E3BA215C87B198733048E75105D024CCA42960EF96A8E04EA6 | |||
| 2732 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{618A5148-5995-4875-809A-2812E16BB9AF}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
108
DNS requests
174
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2732 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3040 | AcroRd32.exe | GET | 304 | 23.48.23.54:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277.zip | US | — | — | whitelisted |
3040 | AcroRd32.exe | GET | 304 | 23.48.23.54:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278.zip | US | — | — | whitelisted |
3040 | AcroRd32.exe | GET | 304 | 23.48.23.54:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281.zip | US | — | — | whitelisted |
— | — | HEAD | 200 | 23.48.23.41:80 | http://ardownload.adobe.com/pub/adobe/reader/win/AcrobatDC/1502320070/AcroRdrDCUpd1502320070_MUI.msp | US | — | — | whitelisted |
3040 | AcroRd32.exe | GET | 304 | 23.48.23.54:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280.zip | US | — | — | whitelisted |
3016 | Opera.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEBp9LmS70lPuCr4VsgvV1T0%3D | US | der | 471 b | whitelisted |
3016 | Opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
3016 | Opera.exe | GET | 200 | 172.217.16.131:80 | http://crl.pki.goog/gtsr1/gtsr1.crl | US | der | 760 b | whitelisted |
3016 | Opera.exe | GET | 200 | 172.217.16.131:80 | http://crl.pki.goog/gsr1/gsr1.crl | US | der | 1.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2732 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3016 | Opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3016 | Opera.exe | 142.250.186.100:443 | www.google.com | Google Inc. | US | whitelisted |
3016 | Opera.exe | 142.250.185.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3016 | Opera.exe | 172.217.16.131:80 | crl.pki.goog | Google Inc. | US | whitelisted |
1740 | RdrCEF.exe | 34.199.101.34:443 | cloud.acrobat.com | Amazon.com, Inc. | US | suspicious |
3016 | Opera.exe | 93.184.220.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3040 | AcroRd32.exe | 23.48.23.54:80 | acroipm2.adobe.com | TRUE INTERNET Co.,Ltd. | US | suspicious |
— | — | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
— | — | 23.48.23.41:80 | ardownload.adobe.com | TRUE INTERNET Co.,Ltd. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
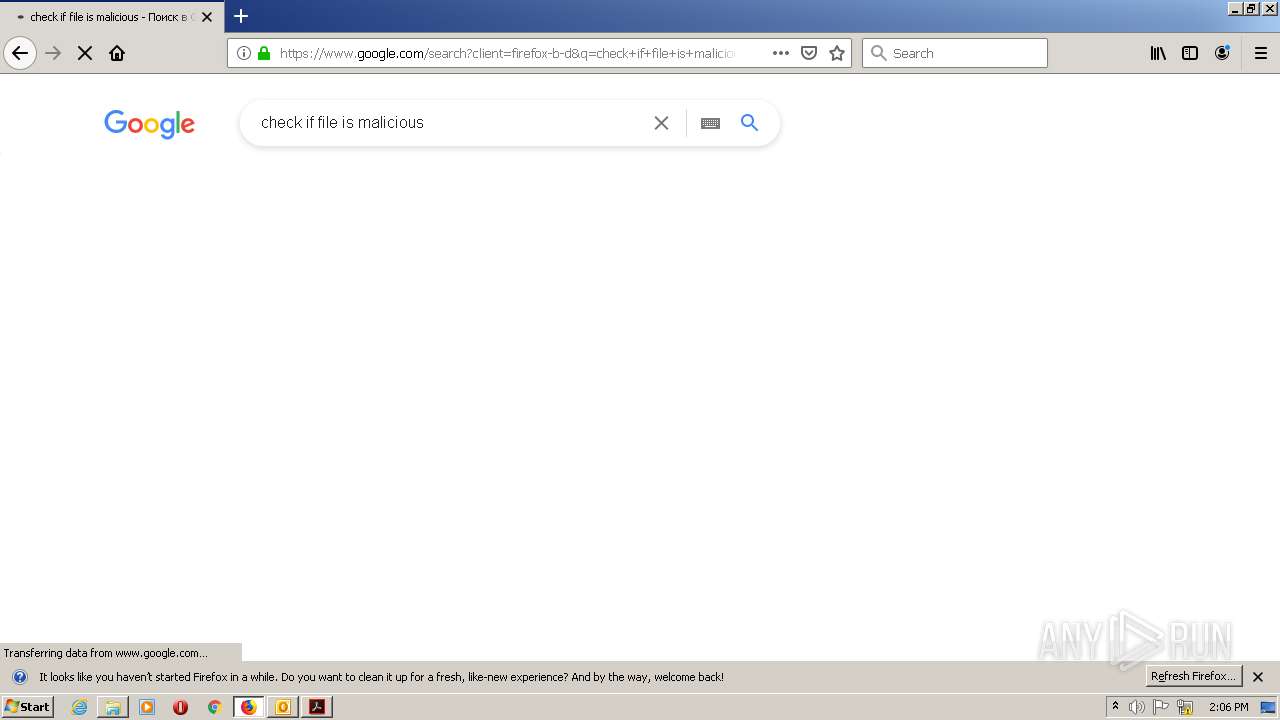
www.google.com |
| malicious |
certs.opera.com |
| whitelisted |
crl.pki.goog |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
crl3.digicert.com |
| whitelisted |
cloud.acrobat.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ardownload.adobe.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
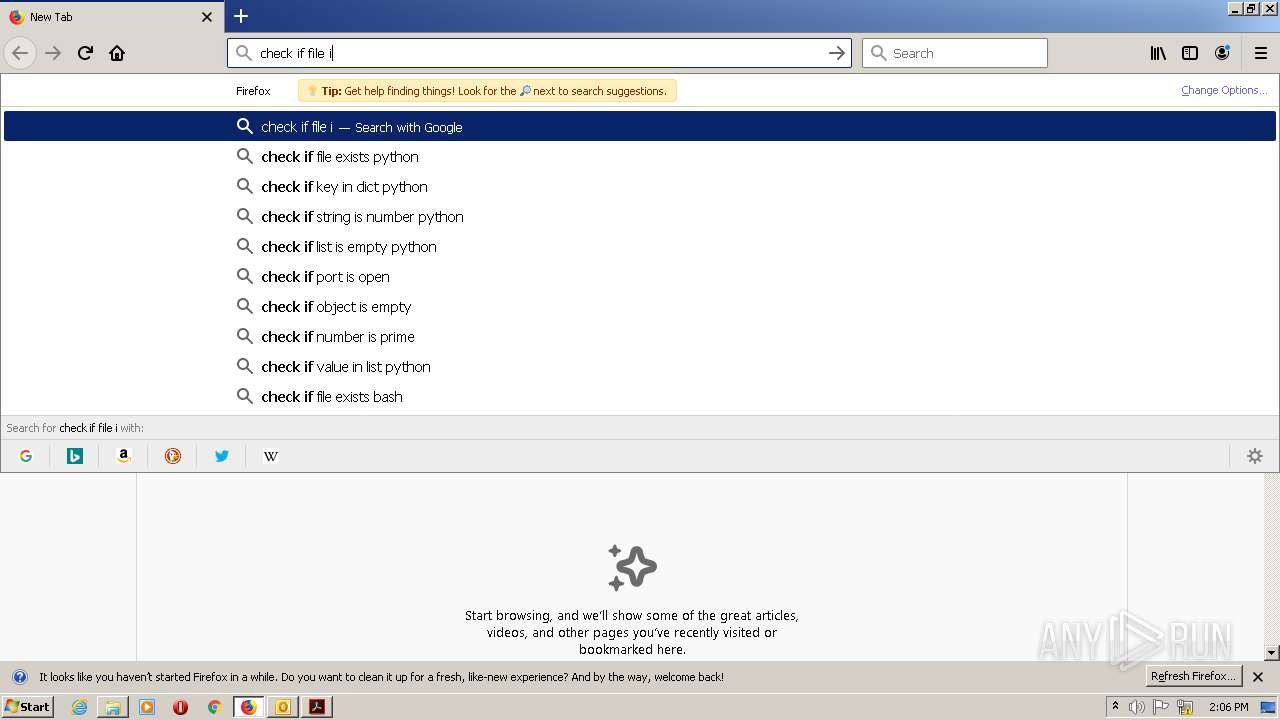
1952 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
1952 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|