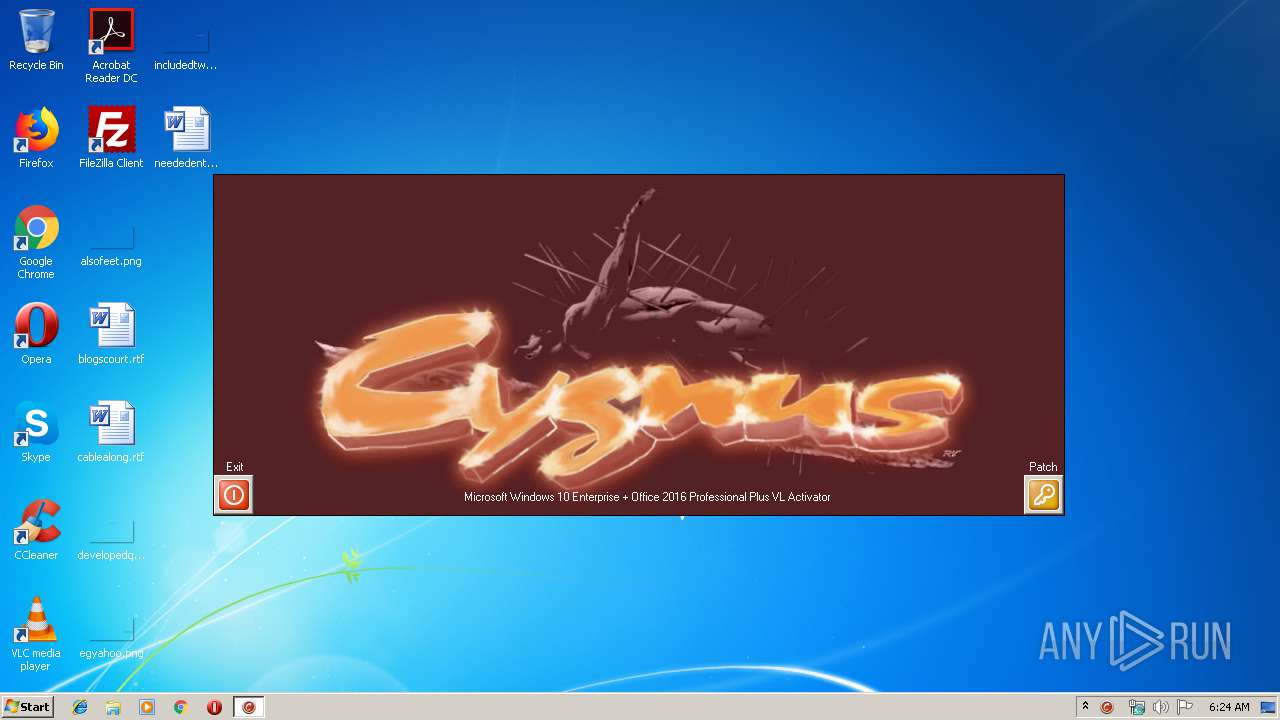
| File name: | win10_activator.exe |
| Full analysis: | https://app.any.run/tasks/e264e398-0017-4135-8181-d72edebdd843 |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2019, 06:24:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D85169218CE7E6CC97D340620AB8BB98 |
| SHA1: | 63DE42A381F599CF9FD806A02CFD437D45010E6A |
| SHA256: | C4A0CF2420FA1FEE9EA1B0BAAD61F34F457E2FB76C7E527E0C4AA7FCE1523243 |
| SSDEEP: | 24576:iCdxte/80jYLT3U1jfsWapHRFtKgB9onh3Q:zw80cTsjkWajnKg8n+ |
MALICIOUS
Application was dropped or rewritten from another process
- win10_acti_x86.exe (PID: 1520)
- win10_acti_x86.exe (PID: 4084)
- win10_acti_x86.exe (PID: 2992)
- SppExtComObjPatcher.exe (PID: 392)
Loads dropped or rewritten executable
- win10_acti_x86.exe (PID: 4084)
- sppsvc.exe (PID: 2104)
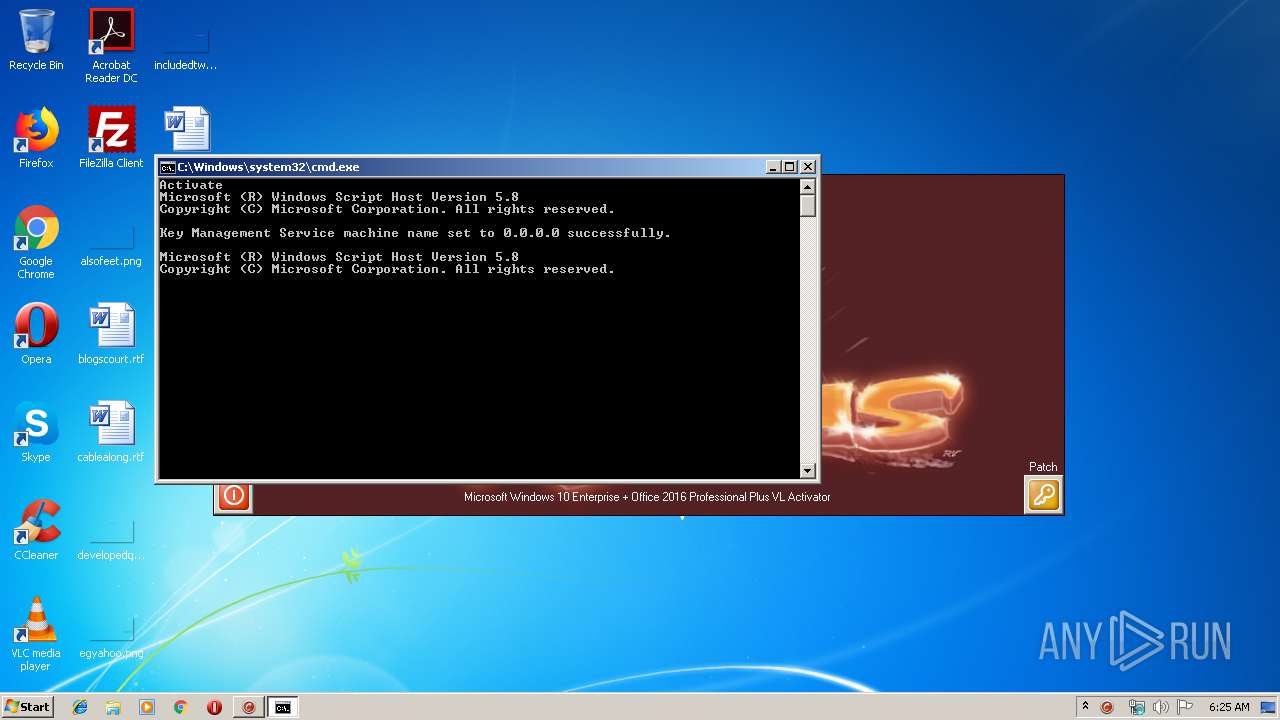
Starts NET.EXE for service management
- cmd.exe (PID: 616)
Changes Image File Execution Options
- reg.exe (PID: 3096)
- reg.exe (PID: 3752)
Loads the Task Scheduler COM API
- sppsvc.exe (PID: 2104)
SUSPICIOUS
Starts CMD.EXE for commands execution
- win10_activator.exe (PID: 2524)
- win10_acti_x86.exe (PID: 4084)
- cmd.exe (PID: 616)
Executable content was dropped or overwritten
- win10_activator.exe (PID: 2524)
- win10_acti_x86.exe (PID: 4084)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 616)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 616)
Starts SC.EXE for service management
- cmd.exe (PID: 616)
Creates files in the Windows directory
- sppsvc.exe (PID: 2104)
- win10_acti_x86.exe (PID: 4084)
Executes scripts
- cmd.exe (PID: 1912)
Executed as Windows Service
- SppExtComObjPatcher.exe (PID: 392)
Removes files from Windows directory
- sppsvc.exe (PID: 2104)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:05 14:50:04+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581120 |
| InitializedDataSize: | 624640 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27f4a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2015 13:50:04 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2015 13:50:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DD2E | 0x0008DE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67588 |
.rdata | 0x0008F000 | 0x0002E10E | 0x0002E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76073 |
.data | 0x000BE000 | 0x00008F74 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.19881 |
.rsrc | 0x000C7000 | 0x0005E164 | 0x0005E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.85496 |
.reloc | 0x00126000 | 0x00007130 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78238 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.40026 | 1007 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 2.05883 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 7.95295 | 26224 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
5 | 3.90227 | 1640 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
6 | 4.04927 | 744 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
64
Monitored processes
25
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | find /i "STOPPED" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | SppExtComObjPatcher.exe C:\Windows\system32\sppsvc.exe | C:\Windows\system32\SppExtComObjPatcher.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 616 | cmd /c "C:\Users\admin\AppData\Local\Temp\crack.cmd" | C:\Windows\system32\cmd.exe | — | win10_acti_x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 776 | cscript slmgr.vbs /skms 0.0.0.0 | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 960 | find /i "amd64" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1520 | C:\Users\admin\AppData\Local\Temp\win10_acti_x86.exe /silent | C:\Users\admin\AppData\Local\Temp\win10_acti_x86.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1532 | sc query sppsvc | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1912 | cmd /c "C:\Users\admin\AppData\Local\Temp\actiw10.cmd" | C:\Windows\system32\cmd.exe | — | win10_acti_x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221536791 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2104 | C:\Windows\system32\sppsvc.exe | C:\Windows\system32\sppsvc.exe | — | SppExtComObjPatcher.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Software Protection Platform Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2116 | wmic path OfficeSoftwareProtectionService get version | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
470
Read events
463
Write events
7
Delete events
0
Modification events
| (PID) Process: | (4004) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4004) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3096) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sppsvc.exe |
| Operation: | write | Name: | Debugger |
Value: SppExtComObjPatcher.exe | |||
| (PID) Process: | (3752) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe |
| Operation: | write | Name: | Debugger |
Value: SppExtComObjPatcher.exe | |||
| (PID) Process: | (2104) sppsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform |
| Operation: | write | Name: | ServiceSessionId |
Value: 9A3D3D2098C5CC42AD22458D8E667F0F | |||
Executable files
6
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2524 | win10_activator.exe | C:\Users\admin\AppData\Local\Temp\autAA63.tmp | — | |
MD5:— | SHA256:— | |||
| 2524 | win10_activator.exe | C:\Users\admin\AppData\Local\Temp\autB32.tmp | — | |
MD5:— | SHA256:— | |||
| 2104 | sppsvc.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Roaming\Microsoft\SoftwareProtectionPlatform\tokens.dat.bak | — | |
MD5:— | SHA256:— | |||
| 2104 | sppsvc.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Roaming\Microsoft\SoftwareProtectionPlatform\tokens.dat | — | |
MD5:— | SHA256:— | |||
| 2524 | win10_activator.exe | C:\Users\admin\AppData\Local\Temp\cyg.jpg | image | |
MD5:5D6BC8DD792D50F87852147F82C64C25 | SHA256:DDE234CAB3FD58C8D6D1CE6C41B6ADB6C8489F1109CCE6801E844D859C280B7E | |||
| 4084 | win10_acti_x86.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:8D6A74C15F9B8D2CFCF13CC54B9C45FD | SHA256:1970FF3C9A124821F5FA1FE4FAFFE309CAD1BF6A5FB6F6E3D7648A6BA41E3548 | |||
| 4084 | win10_acti_x86.exe | C:\Users\admin\AppData\Local\Temp\actiw10.cmd | text | |
MD5:F03256583EA095FEA042208B043E356F | SHA256:C16EF54FED387CC9617EC004DA2327A6069073E8C863C199E68063BA7D02A8D7 | |||
| 4084 | win10_acti_x86.exe | C:\Users\admin\AppData\Local\Temp\crack.cmd | text | |
MD5:4DC7A9FCF9D77A80C896D42EF96E1A1C | SHA256:C8C0A808E4E2A4B190C1D443B0B02274AB35F25E96B566E35CB664917B94033B | |||
| 4084 | win10_acti_x86.exe | C:\Windows\system32\SppExtComObjPatcher.exe | executable | |
MD5:86B83B8700C5E5C25FD7CB4B59962FD5 | SHA256:DAECFCDDCE56274F2B8A813D6E1600B5252EE04AD1CDA452A2D20F63914F72B4 | |||
| 2524 | win10_activator.exe | C:\Users\admin\AppData\Local\Temp\win10_acti_x86.exe | executable | |
MD5:1845C9ADE00A9337DDA2A2766395617B | SHA256:FF6FBF10BF1CA2446E604F958D4257BBEDE3E43D2DCA4D9E1FB9DEA165E656E0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3896 | wmiprvse.exe | POST | 302 | 23.8.11.188:80 | http://go.microsoft.com/fwlink/?LinkID=88341 | NL | — | — | whitelisted |
3896 | wmiprvse.exe | POST | 302 | 23.8.11.188:80 | http://go.microsoft.com/fwlink/?LinkID=88340 | NL | — | — | whitelisted |
3896 | wmiprvse.exe | POST | 302 | 23.8.11.188:80 | http://go.microsoft.com/fwlink/?LinkID=88339 | NL | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3896 | wmiprvse.exe | 23.8.11.188:80 | go.microsoft.com | Akamai International B.V. | NL | malicious |
3896 | wmiprvse.exe | 40.91.122.234:443 | activation.sls.microsoft.com | Microsoft Corporation | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
activation.sls.microsoft.com |
| whitelisted |