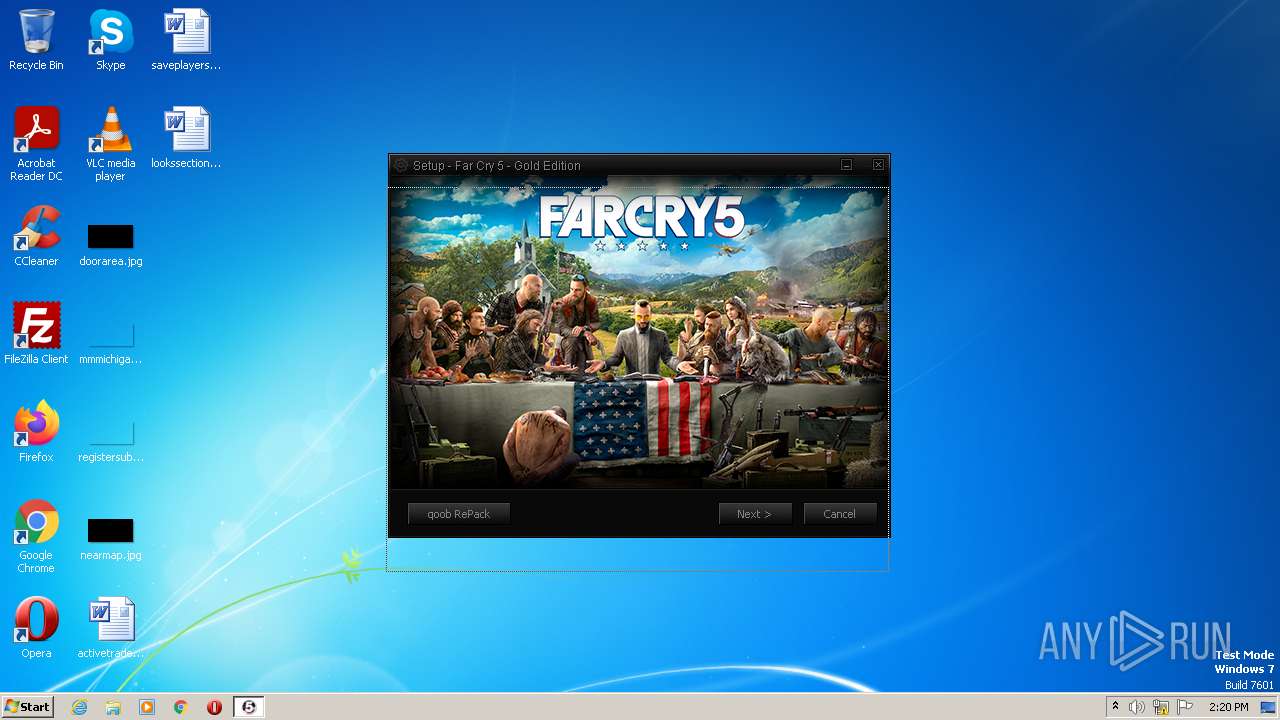
| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/309663a0-bda0-455c-bd30-99a207731504 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 13:20:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E3FDADEA59208735A4B1C4AE0A873646 |
| SHA1: | 38FFC128C3C5CC05543B4C244B385DB71CF87242 |
| SHA256: | C49D7E3611BC6F8621688530543D49838E72F6FD0D5DF481E0C04DDF27720FAF |
| SSDEEP: | 24576:zyNXlADcofn6Vhpf80c8bqzlpYI5vNtPJnLKrVi0KgPfFz3TNRMzWPXmh0EqBY:mNVAlnGhpf80c8CF3PJnxrgJ3xCWw0ER |
MALICIOUS
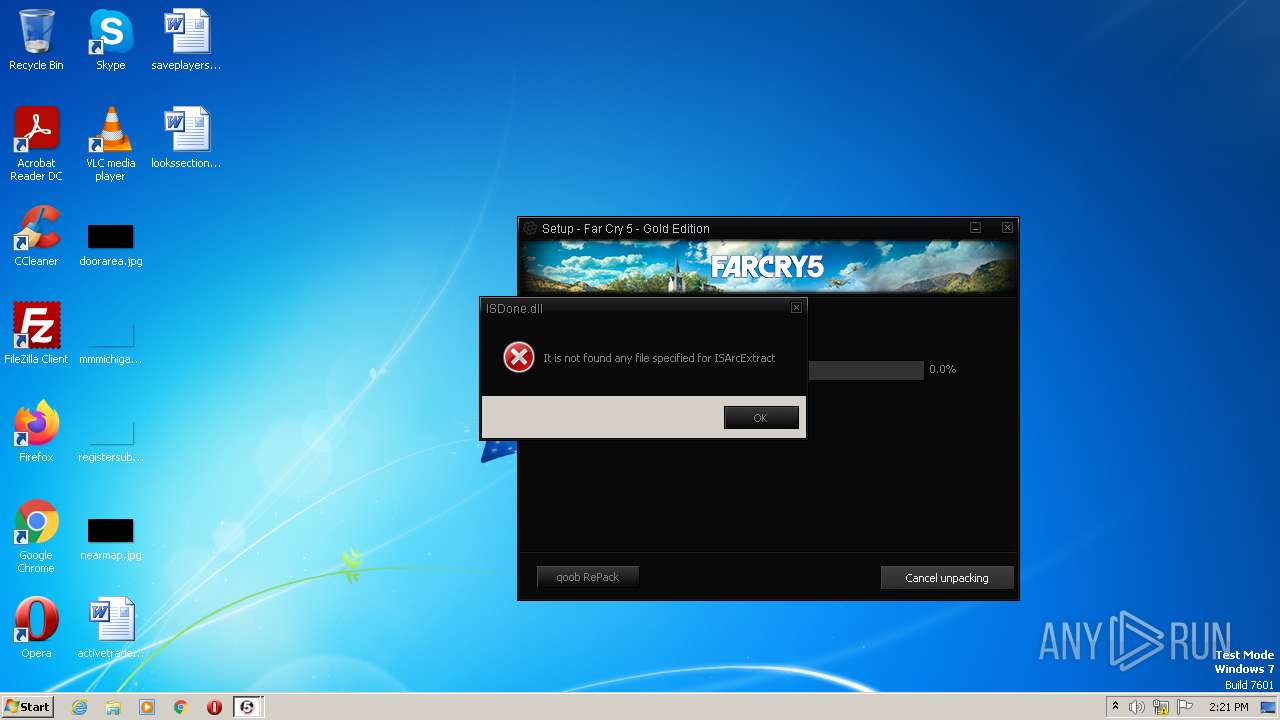
Loads dropped or rewritten executable
- Setup.tmp (PID: 3536)
- _iu14D2N.tmp (PID: 3556)
Application was dropped or rewritten from another process
- _iu14D2N.tmp (PID: 3556)
- unins000.exe (PID: 3456)
SUSPICIOUS
Executable content was dropped or overwritten
- Setup.tmp (PID: 3536)
- Setup.exe (PID: 3324)
- unins000.exe (PID: 3456)
- _iu14D2N.tmp (PID: 3556)
Reads the Internet Settings
- Setup.tmp (PID: 3536)
Reads the Windows owner or organization settings
- Setup.tmp (PID: 3536)
- _iu14D2N.tmp (PID: 3556)
Starts itself from another location
- unins000.exe (PID: 3456)
Starts application with an unusual extension
- unins000.exe (PID: 3456)
INFO
Create files in a temporary directory
- Setup.tmp (PID: 3536)
- Setup.exe (PID: 3324)
- unins000.exe (PID: 3456)
- iexplore.exe (PID: 2924)
- _iu14D2N.tmp (PID: 3556)
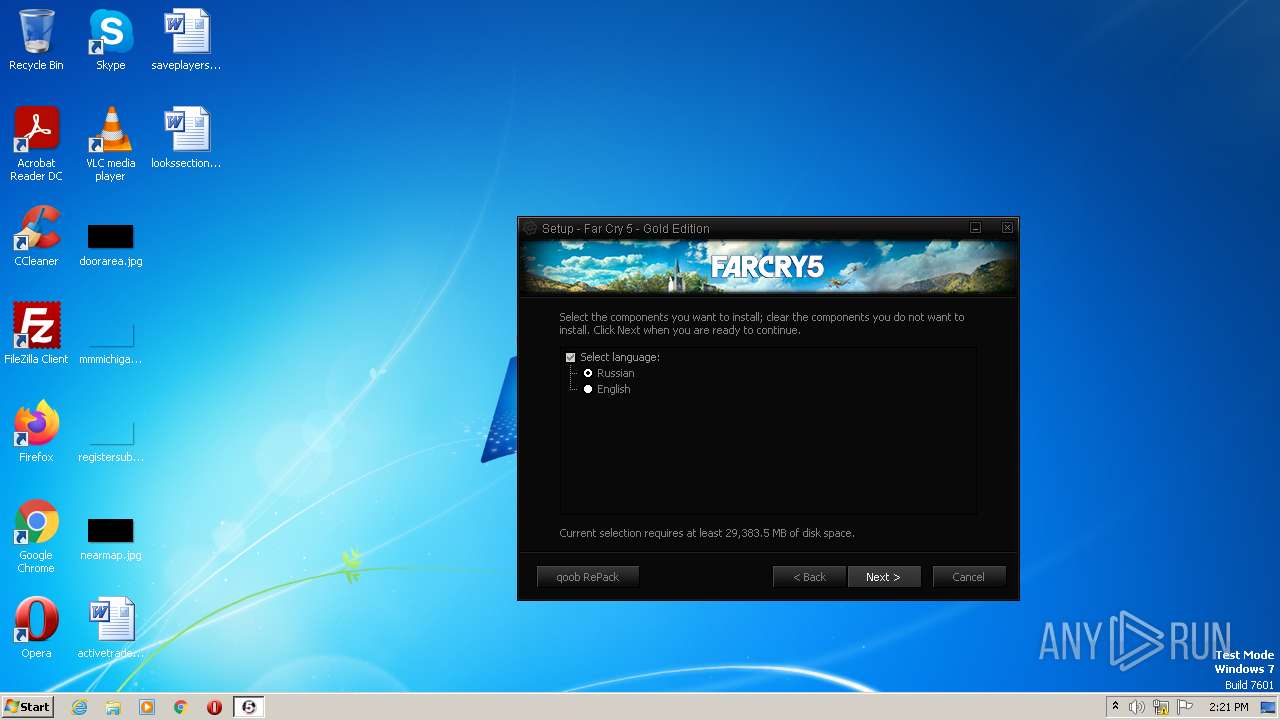
Checks supported languages
- Setup.exe (PID: 3324)
- Setup.tmp (PID: 3536)
- unins000.exe (PID: 3456)
- _iu14D2N.tmp (PID: 3556)
The process checks LSA protection
- Setup.tmp (PID: 3536)
- _iu14D2N.tmp (PID: 3556)
Reads the computer name
- Setup.tmp (PID: 3536)
- _iu14D2N.tmp (PID: 3556)
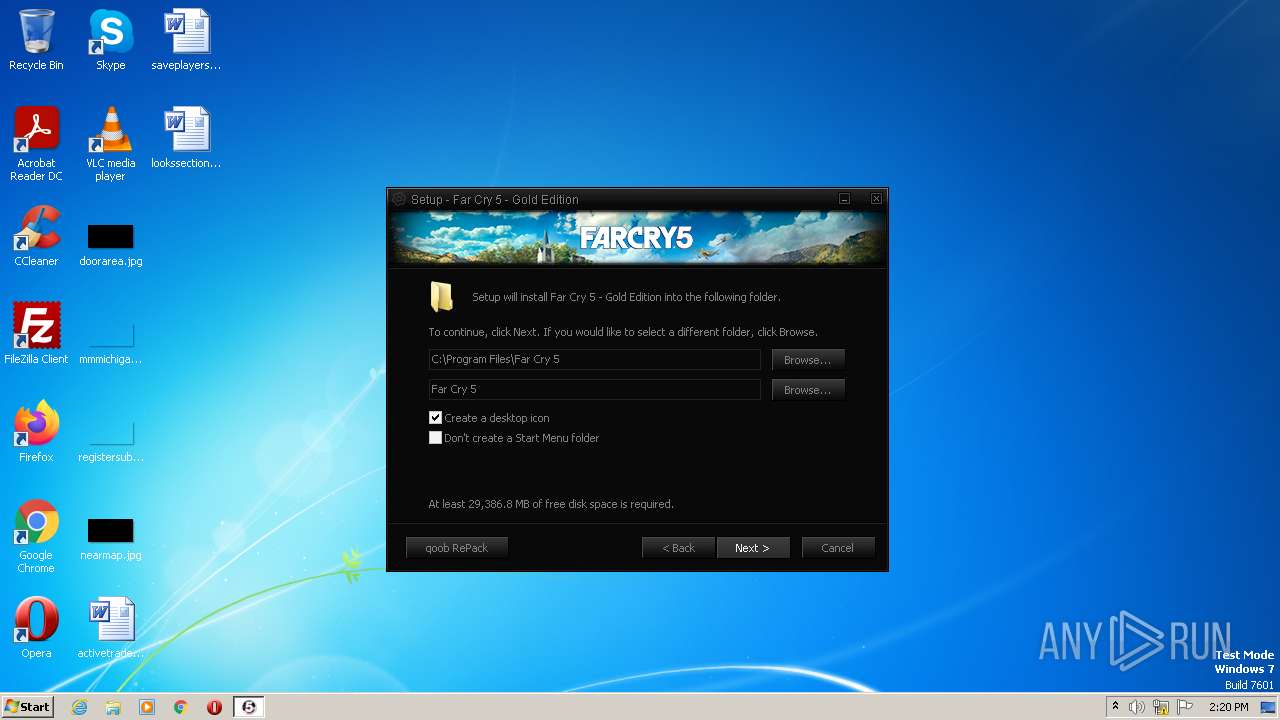
Creates files in the program directory
- Setup.tmp (PID: 3536)
Application launched itself
- iexplore.exe (PID: 2924)
Application was dropped or rewritten from another process
- Setup.tmp (PID: 3536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
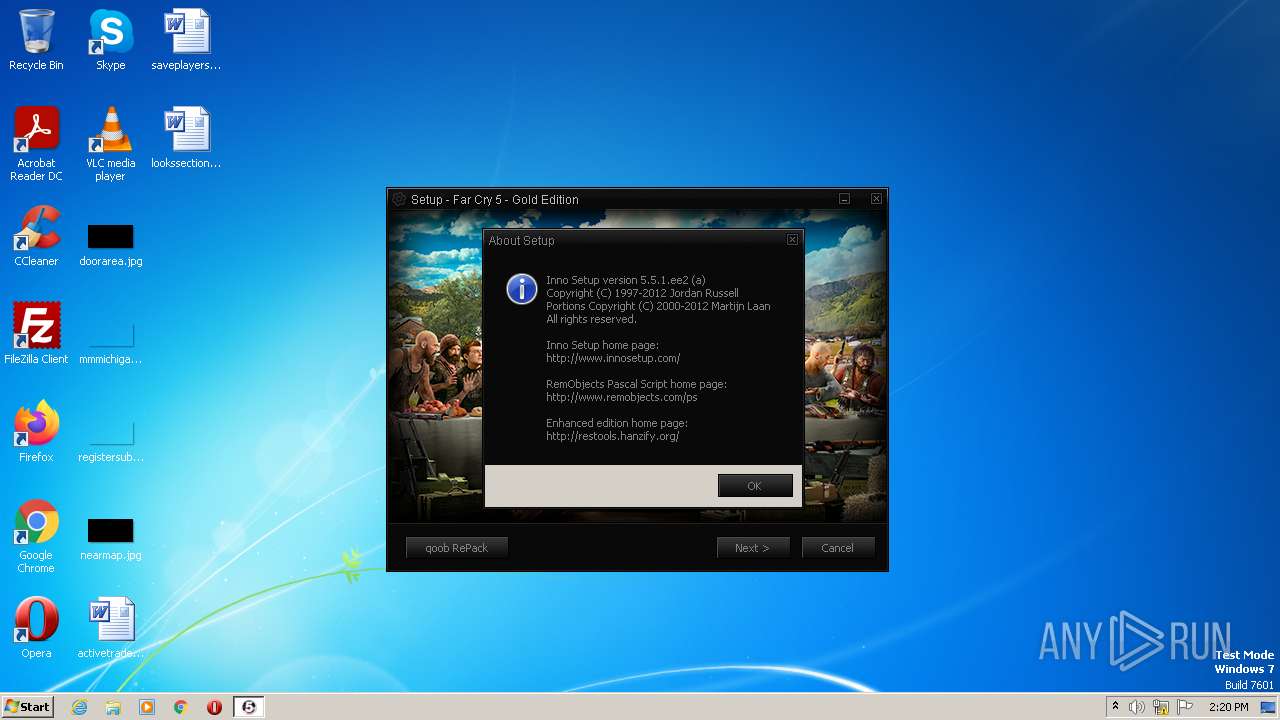
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| ProductVersion: | 1.0 |
|---|---|
| ProductName: | Setup |
| LegalCopyright: | Setup |
| FileVersion: | 1.0 |
| FileDescription: | Setup |
| CompanyName: | |
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 1 |
| EntryPoint: | 0x9c14 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 89088 |
| CodeSize: | 37888 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Setup |
| FileVersion: | 1.0 |
| LegalCopyright: | Setup |
| ProductName: | Setup |
| ProductVersion: | 1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009338 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55605 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.73918 |
BSS | 0x0000C000 | 0x00000E8C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B0 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00014B38 | 0x00014C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.79318 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.15342 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.23388 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.5532 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | Latin 1 / Western European | UNKNOWN | RT_STRING |
11111 | 4.61354 | 44 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
45
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
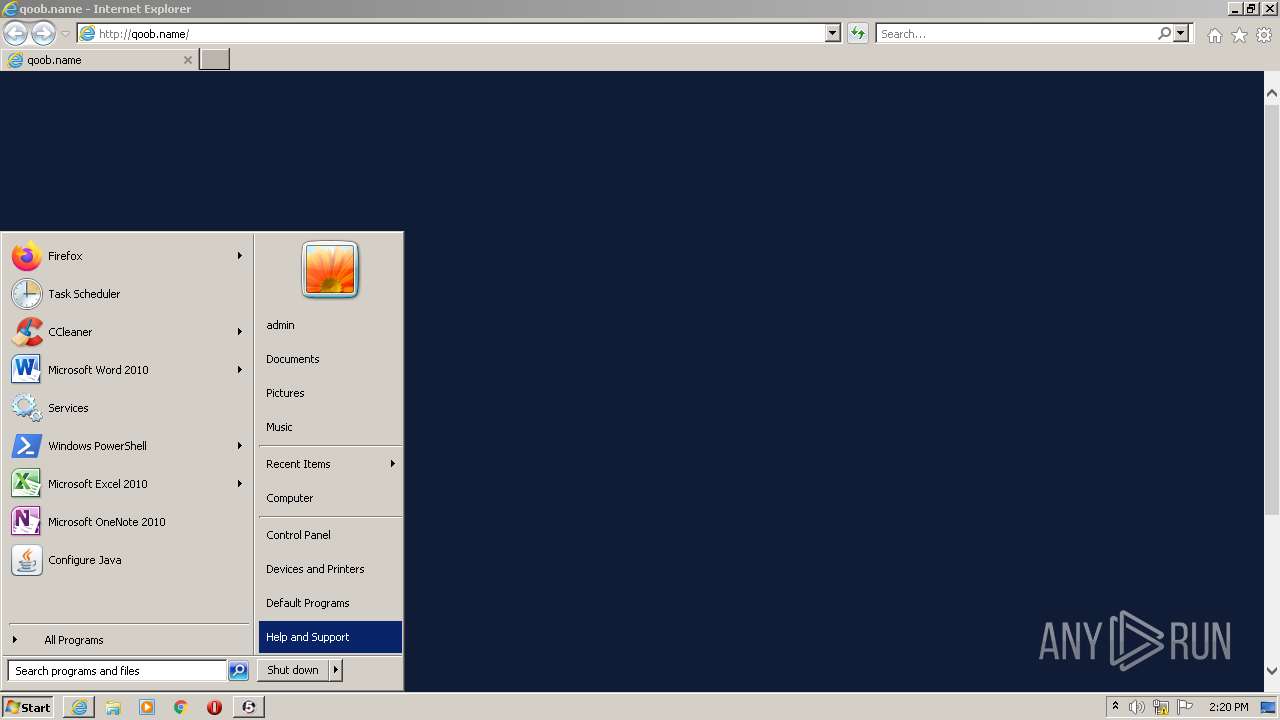
| 2672 | "C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Users\admin\AppData\Local\Temp\Setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup Exit code: 3221226540 Version: 1.0 Modules
| |||||||||||||||
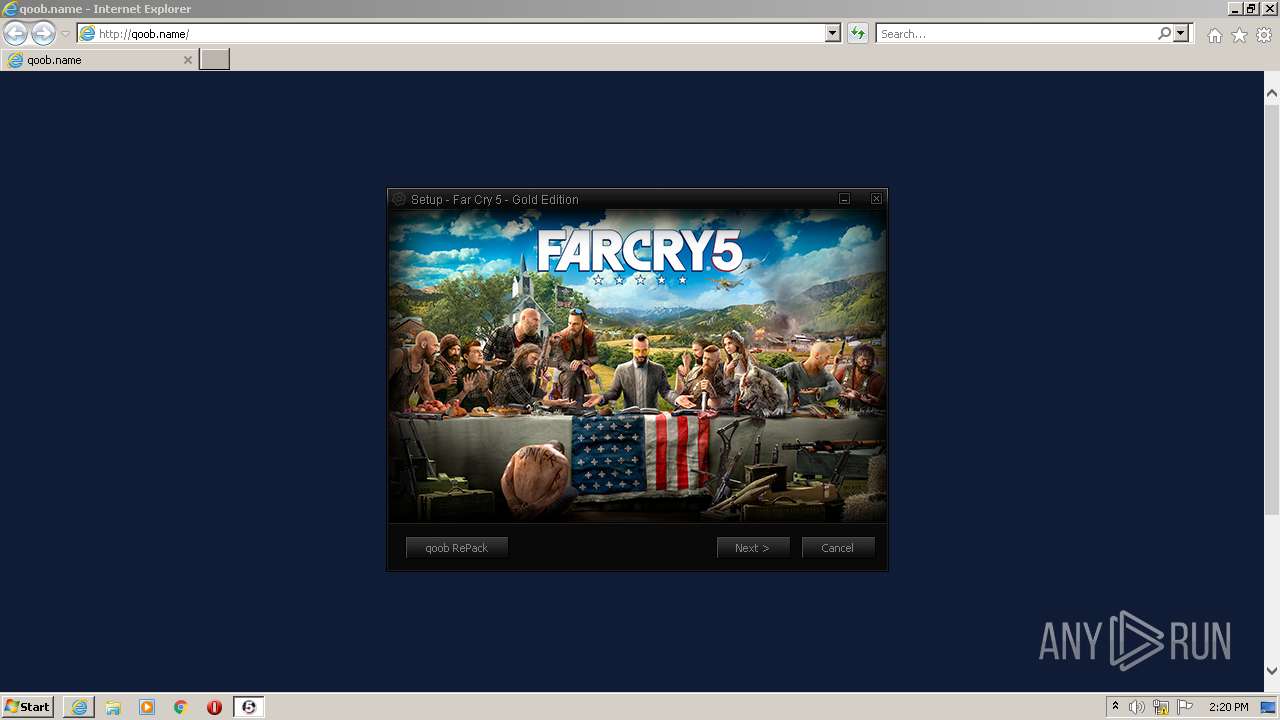
| 2924 | "C:\Program Files\Internet Explorer\iexplore.exe" http://qoob.name/ | C:\Program Files\Internet Explorer\iexplore.exe | Setup.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3056 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2924 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3324 | "C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Users\admin\AppData\Local\Temp\Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup Exit code: 0 Version: 1.0 Modules
| |||||||||||||||
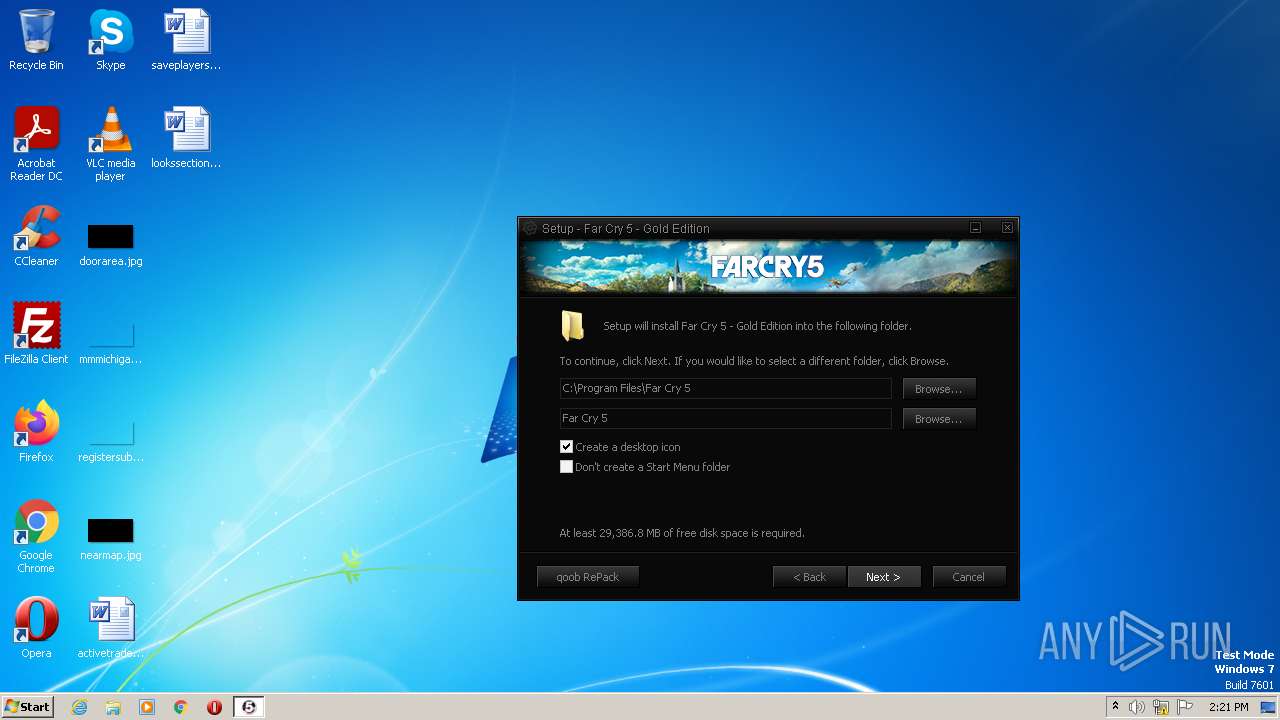
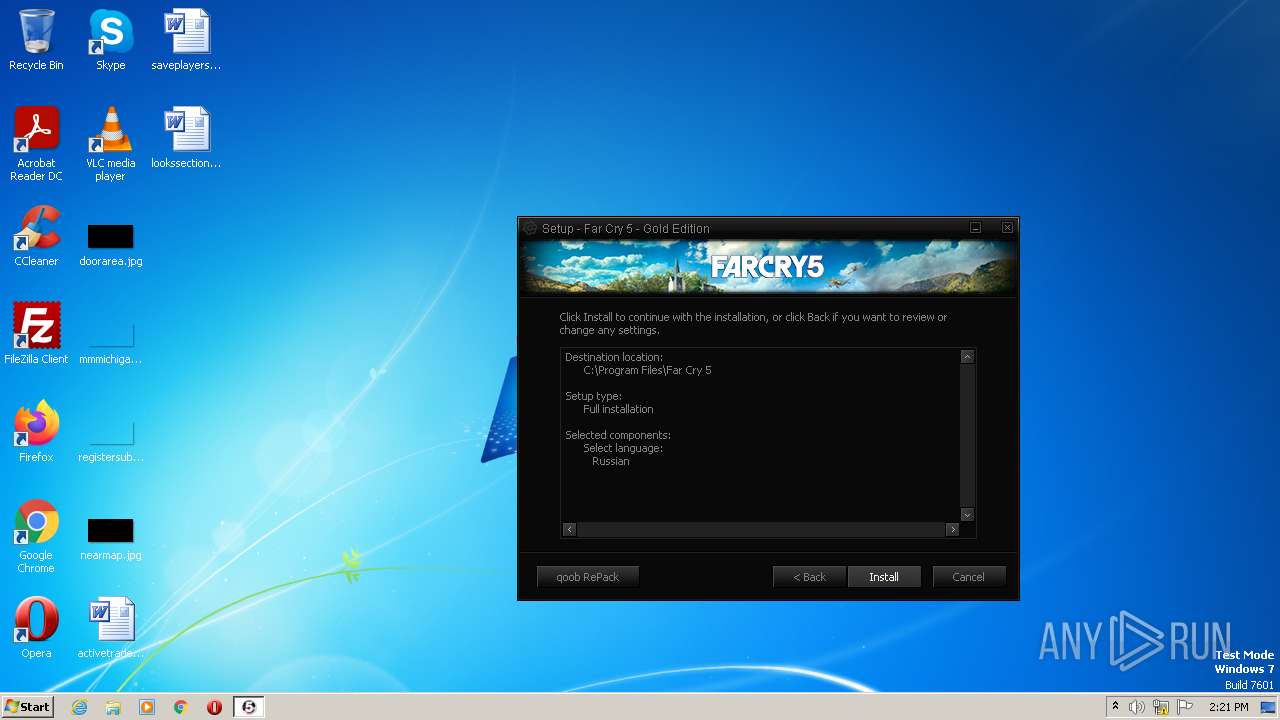
| 3456 | "C:\Program Files\Far Cry 5\unins000.exe" /VERYSILENT | C:\Program Files\Far Cry 5\unins000.exe | Setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3536 | "C:\Users\admin\AppData\Local\Temp\is-QK8I6.tmp\Setup.tmp" /SL5="$6012A,1459701,128000,C:\Users\admin\AppData\Local\Temp\Setup.exe" | C:\Users\admin\AppData\Local\Temp\is-QK8I6.tmp\Setup.tmp | Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 3556 | "C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp" /SECONDPHASE="C:\Program Files\Far Cry 5\unins000.exe" /FIRSTPHASEWND=$301F6 /VERYSILENT | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | unins000.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
33 332
Read events
33 068
Write events
262
Delete events
2
Modification events
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2924) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
30
Suspicious files
28
Text files
64
Unknown types
30
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 3056 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\PC5CKRSG.txt | text | |
MD5:— | SHA256:— | |||
| 3056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\W76DM60S.htm | html | |
MD5:— | SHA256:— | |||
| 3056 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\V4P2C7U1.txt | text | |
MD5:— | SHA256:— | |||
| 3056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\caf[1].js | text | |
MD5:— | SHA256:— | |||
| 3056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3056 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 3536 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-P0OPP.tmp\end.bmp | image | |
MD5:07602DAC85E2E9E807A0BECD07F5D3A1 | SHA256:A31BDA32BE2FD73C76B968CD57FE3BACE0E0048237B9694ECD26A20EEE363512 | |||
| 3056 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\sale_form[1].js | text | |
MD5:64F809E06446647E192FCE8D1EC34E09 | SHA256:F52CBD664986AD7ED6E71C448E2D31D1A16463E4D9B7BCA0C6BE278649CCC4F3 | |||
| 3536 | Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-P0OPP.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:0EE914C6F0BB93996C75941E1AD629C6 | SHA256:4DC09BAC0613590F1FAC8771D18AF5BE25A1E1CB8FDBF4031AA364F3057E74A2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
30
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3056 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3056 | iexplore.exe | GET | 200 | 75.2.81.221:80 | http://qoob.name/ | US | html | 5.64 Kb | malicious |
3056 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCXh%2B17FzWzVgrisikgAGpW | US | der | 472 b | whitelisted |
3056 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEMhbiGFxLZ5EgQHgSI51DM%3D | US | der | 471 b | whitelisted |
3056 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGuOw5S%2FgZeuCs2W38ctSDs%3D | US | der | 471 b | whitelisted |
3056 | iexplore.exe | GET | 200 | 142.250.185.196:80 | http://www.google.com/adsense/domains/caf.js?abp=1 | US | text | 52.6 Kb | malicious |
2924 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3056 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8195da0f924e6a30 | US | compressed | 4.70 Kb | whitelisted |
3056 | iexplore.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2924 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3056 | iexplore.exe | 75.2.81.221:80 | qoob.name | AMAZON-02 | US | malicious |
3056 | iexplore.exe | 142.250.185.196:80 | www.google.com | GOOGLE | US | whitelisted |
3056 | iexplore.exe | 185.53.178.30:80 | c.parkingcrew.net | Team Internet AG | DE | suspicious |
3056 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3056 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3056 | iexplore.exe | 142.250.185.163:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3056 | iexplore.exe | 142.250.185.163:443 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2924 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2924 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2924 | iexplore.exe | 13.107.21.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
qoob.name |
| malicious |
www.google.com |
| malicious |
c.parkingcrew.net |
| whitelisted |
partner.googleadservices.com |
| whitelisted |
d38psrni17bvxu.cloudfront.net |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |