| download: | /download/2.349/Setup.exe |
| Full analysis: | https://app.any.run/tasks/faab2ec6-68c9-42d7-8e53-aed864a18980 |
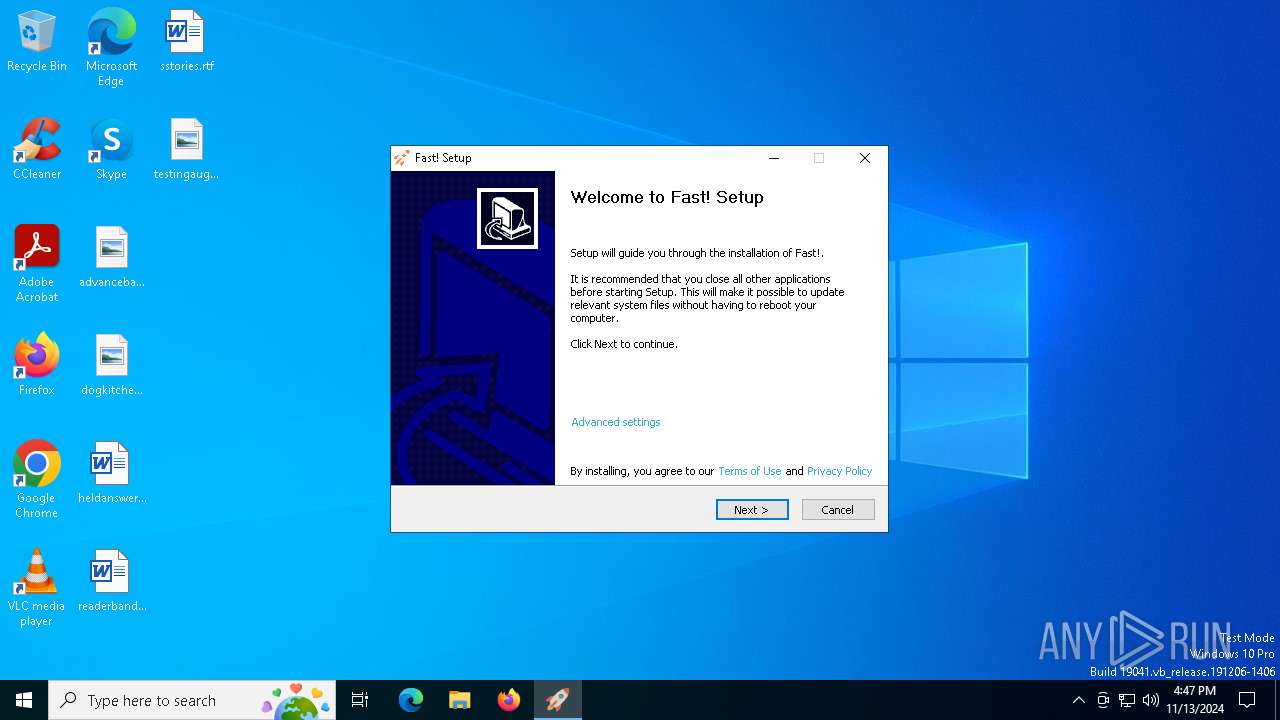
| Verdict: | Malicious activity |
| Analysis date: | November 13, 2024, 16:47:41 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 85F2849F25944FC15E58521A52B800FF |
| SHA1: | 718D11673DE4743835523983AB5E06F88785A03D |
| SHA256: | C4942BAD2EAACA0BB5ED7E6900D6C85F12F0DB6DE790072838CE3F854B9AD677 |
| SSDEEP: | 3072:uefw3Auu/ysEL5f3WBo9A/BwdKIkM3WXgtqr44:u0ww/FEN4o9AWxrWwtW |
MALICIOUS
No malicious indicators.SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- Setup.exe (PID: 6488)
The process creates files with name similar to system file names
- Setup.exe (PID: 6488)
Searches for installed software
- Setup.exe (PID: 6488)
Checks Windows Trust Settings
- Setup.exe (PID: 6488)
Reads security settings of Internet Explorer
- Setup.exe (PID: 6488)
Executable content was dropped or overwritten
- Setup.exe (PID: 6488)
INFO
Create files in a temporary directory
- Setup.exe (PID: 6488)
Checks supported languages
- Setup.exe (PID: 6488)
Checks proxy server information
- Setup.exe (PID: 6488)
Reads the computer name
- Setup.exe (PID: 6488)
Reads the machine GUID from the registry
- Setup.exe (PID: 6488)
Creates files or folders in the user directory
- Setup.exe (PID: 6488)
Reads the software policy settings
- Setup.exe (PID: 6488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:57:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 186880 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x352d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.3.4.9 |
| ProductVersionNumber: | 2.3.4.9 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Fast Corporation LTD |
| FileDescription: | Fast! Setup |
| FileVersion: | 2.3.4.9 |
| LegalCopyright: | Fast Corporation LTD |
| ProductName: | Get Fast! |
| ProductVersion: | 2.3.4.9 |
Total processes
138
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4032 | "C:\Users\admin\Downloads\Setup.exe" | C:\Users\admin\Downloads\Setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Fast Corporation LTD Integrity Level: MEDIUM Description: Fast! Setup Exit code: 3221226540 Version: 2.3.4.9 Modules
| |||||||||||||||
| 4676 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6488 | "C:\Users\admin\Downloads\Setup.exe" | C:\Users\admin\Downloads\Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Fast Corporation LTD Integrity Level: HIGH Description: Fast! Setup Version: 2.3.4.9 Modules
| |||||||||||||||
| 6960 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 081
Read events
1 078
Write events
3
Delete events
0
Modification events
| (PID) Process: | (6488) Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6488) Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6488) Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
5
Suspicious files
4
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6488 | Setup.exe | C:\Users\admin\AppData\Local\Temp\nsuB9A5.tmp\Banner.dll | executable | |
MD5:A1B9BDEE9FC87D11676605BD79037646 | SHA256:39E3108E0A4CCFB9FE4D8CAF4FB40BAA39BDD797F3A4C1FA886086226E00F465 | |||
| 6488 | Setup.exe | C:\Users\admin\AppData\Local\Temp\nsuB9A5.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 6488 | Setup.exe | C:\Users\admin\AppData\Local\Temp\nsuB9A5.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 6488 | Setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_C39E9DBC666D19C07EEE7CD1E11AF8BE | der | |
MD5:B6DE3928D507B44D107971489204EBA4 | SHA256:0D4A97322F5EF313A0B2EC8B657929C0419B987D65BD2A57C6F7B3D74C419608 | |||
| 6488 | Setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_C39E9DBC666D19C07EEE7CD1E11AF8BE | binary | |
MD5:91D9503F61130FBB9C81DF9AB64B90C1 | SHA256:D8660CA4C247DC0EC5925DC56CB3363BCEBC26C39210EEFCF4B6931FF6C6A375 | |||
| 6488 | Setup.exe | C:\Users\admin\AppData\Local\Temp\nsuB9A5.tmp\nsDialogs.dll | executable | |
MD5:6C3F8C94D0727894D706940A8A980543 | SHA256:56B96ADD1978B1ABBA286F7F8982B0EFBE007D4A48B3DED6A4D408E01D753FE2 | |||
| 6488 | Setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\773CFF2C7835D48C4E76FE153DBA9F81_B7B1925BDA9E33CE0A92ECF660593288 | der | |
MD5:70902C2967ADA4E44F355DA7449EB4AC | SHA256:A3E15520089A6014628A4404062A3D86580B98153D0C853C584937867181FDBF | |||
| 6488 | Setup.exe | C:\Users\admin\AppData\Local\Temp\nsuB9A5.tmp\nsJSON.dll | executable | |
MD5:F4D89D9A2A3E2F164AEA3E93864905C9 | SHA256:64B3EFDF3DE54E338D4DB96B549A7BDB7237BB88A82A0A63AEF570327A78A6FB | |||
| 6488 | Setup.exe | C:\Users\admin\AppData\Local\Temp\nsuB9A5.tmp\inetc.dll | executable | |
MD5:A35CDC9CF1D17216C0AB8C5282488EAD | SHA256:A793929232AFB78B1C5B2F45D82094098BCF01523159FAD1032147D8D5F9C4DF | |||
| 6488 | Setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\773CFF2C7835D48C4E76FE153DBA9F81_B7B1925BDA9E33CE0A92ECF660593288 | binary | |
MD5:7E3C366BFF6A48C99D455F549CB7A2F0 | SHA256:8A51EDAF9B8B50EB18D706EA4F2A856D32B26484BBDCA17737927499AADF4E19 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
42
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6488 | Setup.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAsllCLO2YEqFaBOmVKKDvo%3D | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 23.48.23.145:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
944 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6488 | Setup.exe | GET | 200 | 192.229.221.95:80 | http://status.rapidssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJiUKgT2m88fZ4nxc1Lu6M%2FjvkagQUDNtsgkkPSmcKuBTuesRIUojrVjgCEAECyHKLsbZHFMkaaaqQRe8%3D | unknown | — | — | whitelisted |
3852 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6220 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6220 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4292 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6488 | Setup.exe | 64.227.17.224:443 | veryfast.io | DIGITALOCEAN-ASN | US | unknown |
6488 | Setup.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6944 | svchost.exe | 23.48.23.145:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 104.126.37.123:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
veryfast.io |
| unknown |
ocsp.digicert.com |
| whitelisted |
status.rapidssl.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |