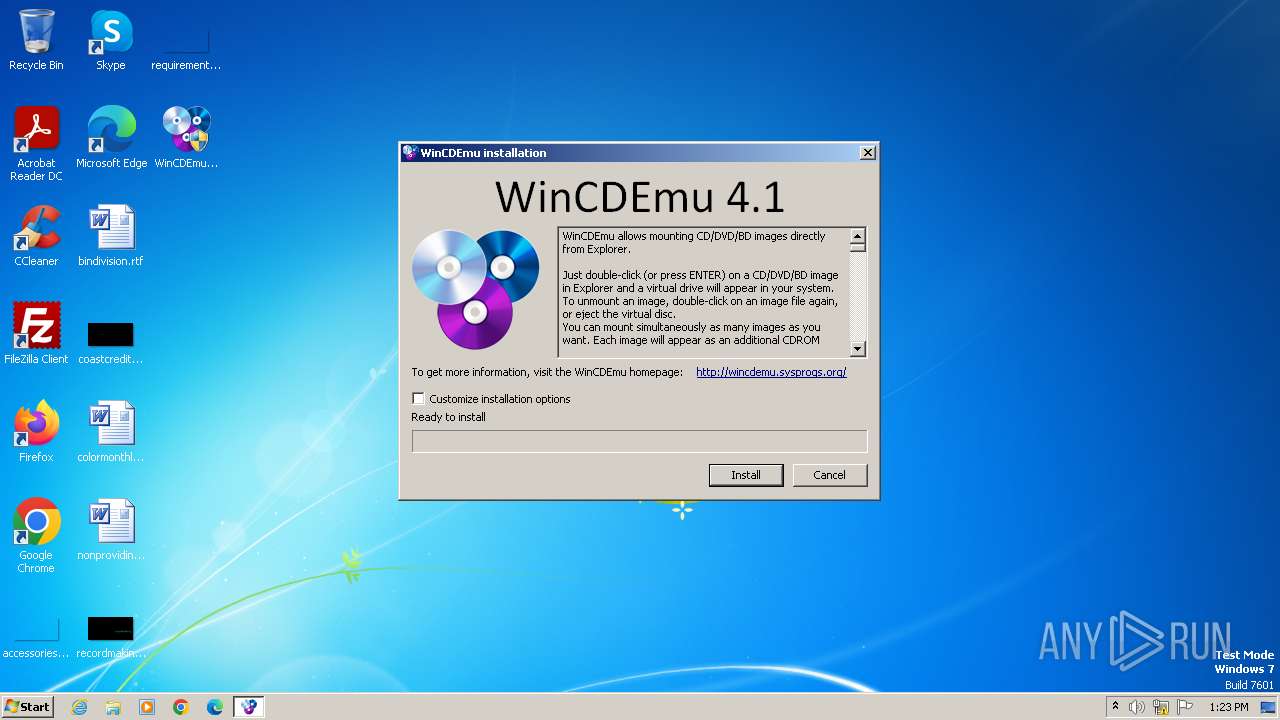
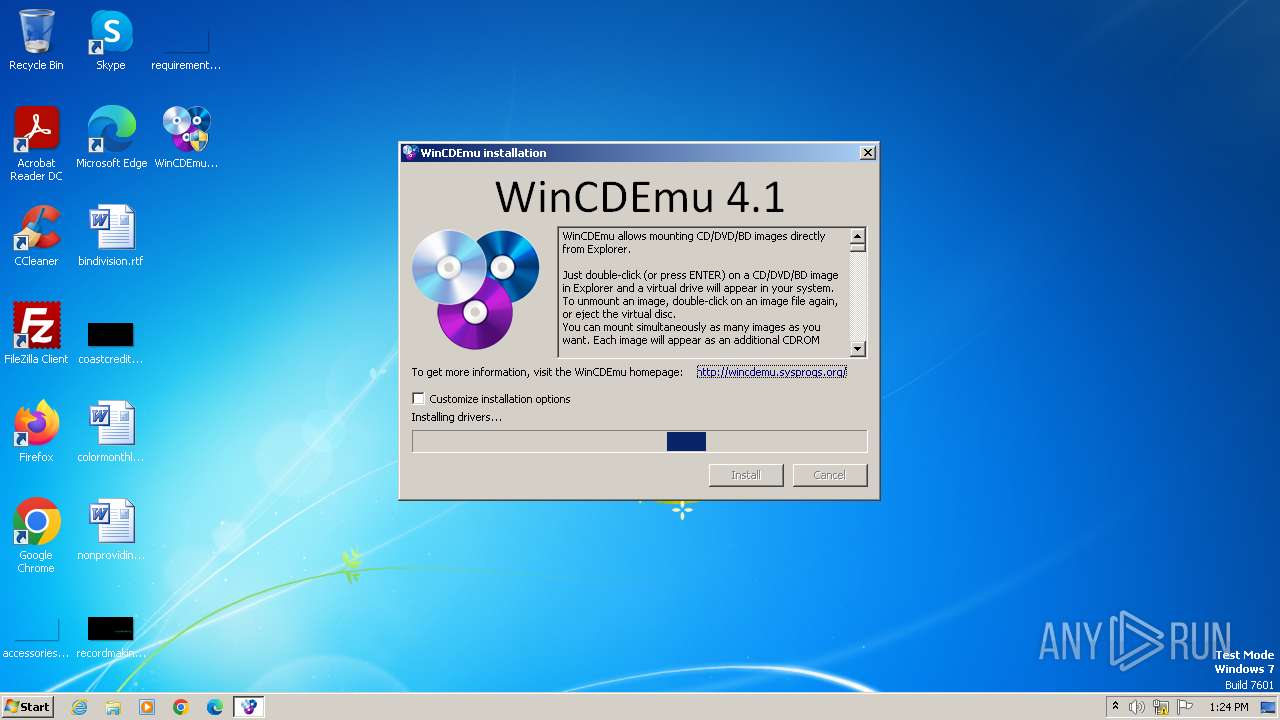
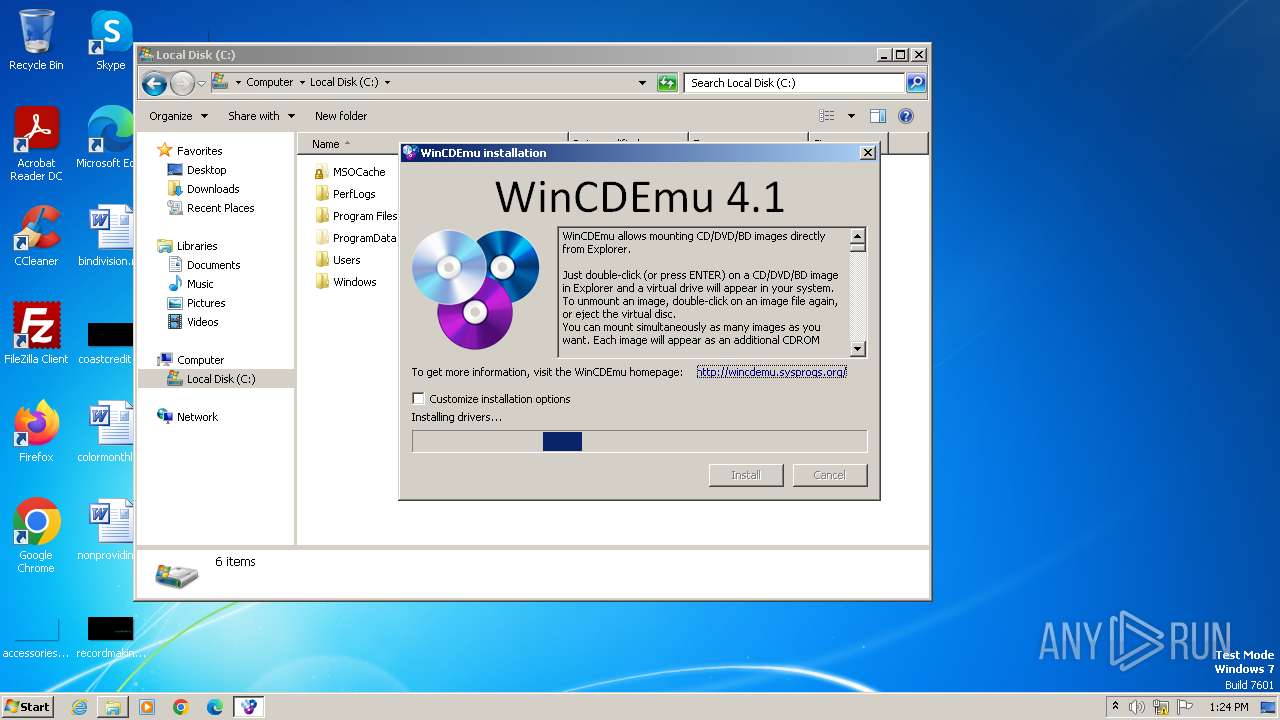
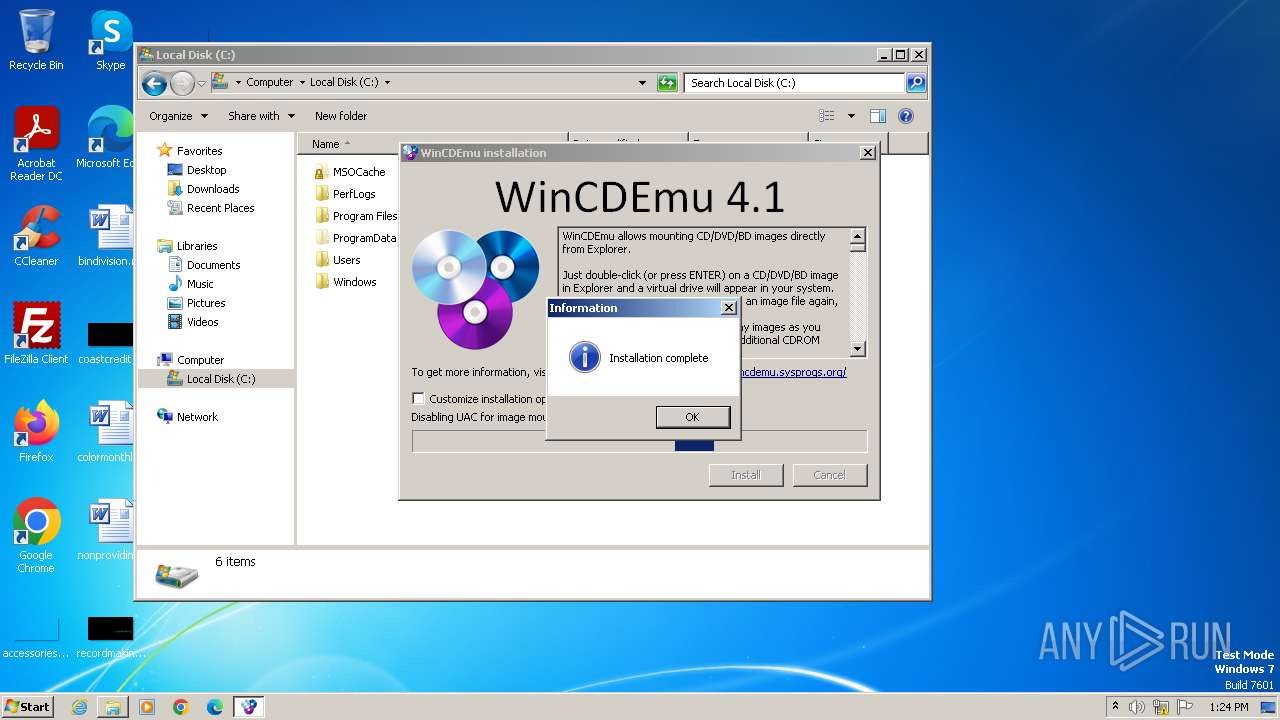
| File name: | WinCDEmu-4.1.exe |
| Full analysis: | https://app.any.run/tasks/a5cb8c04-e506-4138-abbf-ffae398a9c86 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2024, 12:23:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 4E53BEFE779F677B1CCEC54B84F60A8C |
| SHA1: | 9FF4F2ED41D5BD09496D2CFB6E09C4B31659DC19 |
| SHA256: | C47763631D20120057766F2F71F781BF958E22712DA4AC933B21DB0D615DC93C |
| SSDEEP: | 49152:kCFdVNpsRKZdJ0ya6wWfumwumbp/afUD+6EVV4dDD/P:kaVNpsIF0ya6wWf32p/69Z4dDjP |
MALICIOUS
Drops the executable file immediately after the start
- WinCDEmu-4.1.exe (PID: 1120)
- drvinst32.exe (PID: 336)
- drvinst.exe (PID: 2312)
- drvinst.exe (PID: 2476)
Registers / Runs the DLL via REGSVR32.EXE
- uninstall.exe (PID: 112)
Creates a writable file in the system directory
- drvinst.exe (PID: 2312)
- drvinst.exe (PID: 2476)
SUSPICIOUS
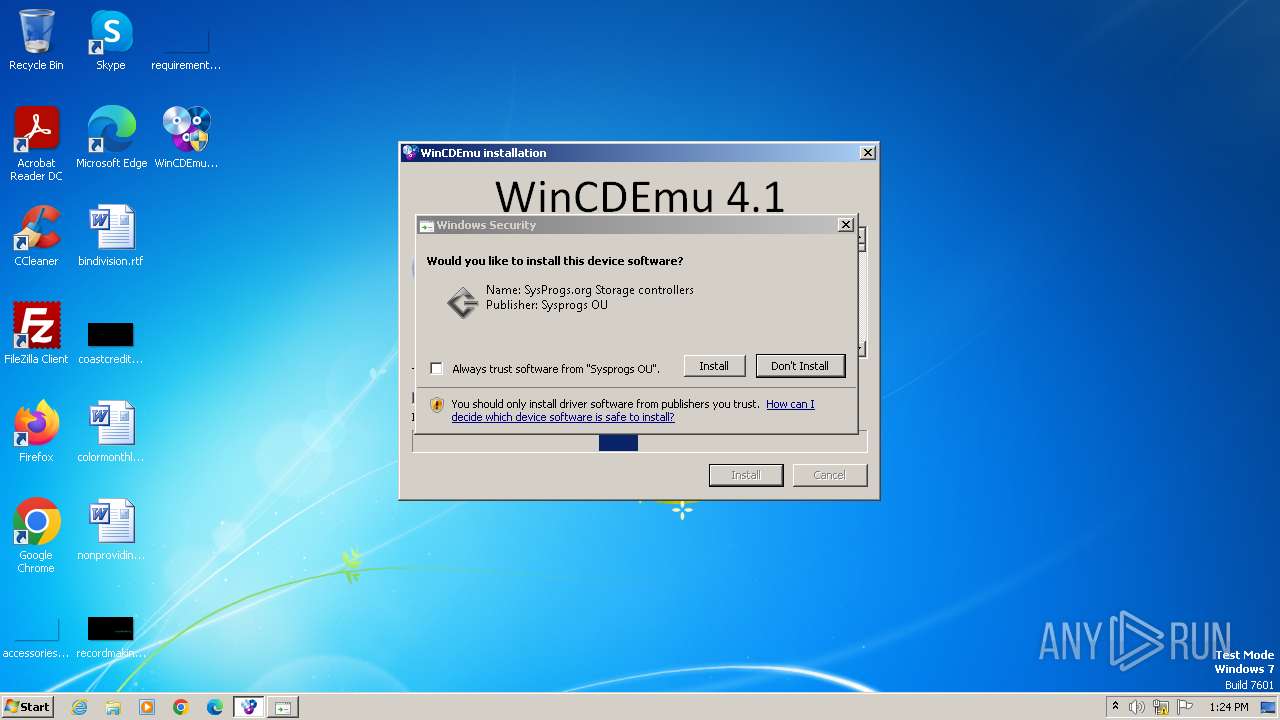
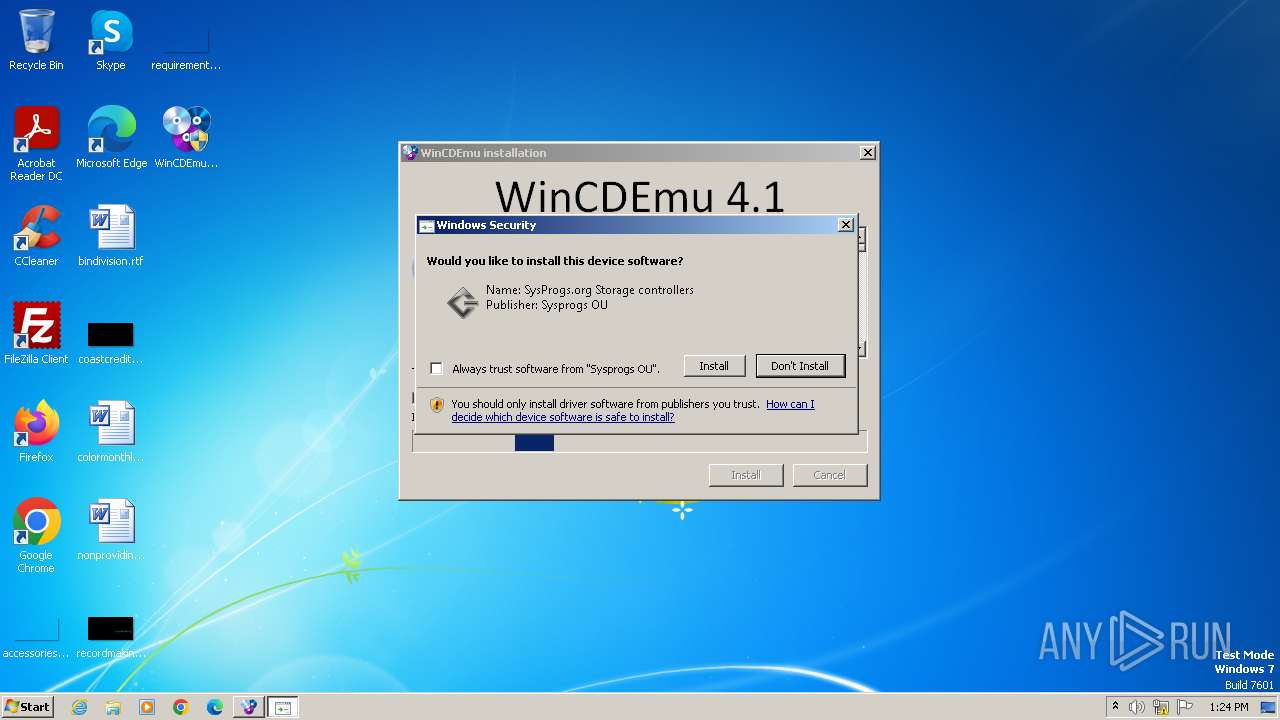
Drops a system driver (possible attempt to evade defenses)
- WinCDEmu-4.1.exe (PID: 1120)
- drvinst.exe (PID: 2312)
- drvinst32.exe (PID: 336)
- drvinst.exe (PID: 2476)
Executable content was dropped or overwritten
- WinCDEmu-4.1.exe (PID: 1120)
- drvinst32.exe (PID: 336)
- drvinst.exe (PID: 2312)
- drvinst.exe (PID: 2476)
Reads the Internet Settings
- uninstall.exe (PID: 112)
- vmnt.exe (PID: 2560)
Reads security settings of Internet Explorer
- uninstall.exe (PID: 112)
- drvinst32.exe (PID: 336)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 116)
- regsvr32.exe (PID: 372)
Checks Windows Trust Settings
- drvinst32.exe (PID: 336)
- drvinst.exe (PID: 2312)
- drvinst.exe (PID: 2476)
Reads settings of System Certificates
- drvinst32.exe (PID: 336)
- rundll32.exe (PID: 1580)
Creates files in the driver directory
- drvinst.exe (PID: 2312)
- drvinst.exe (PID: 2476)
Executes as Windows Service
- VSSVC.exe (PID: 1488)
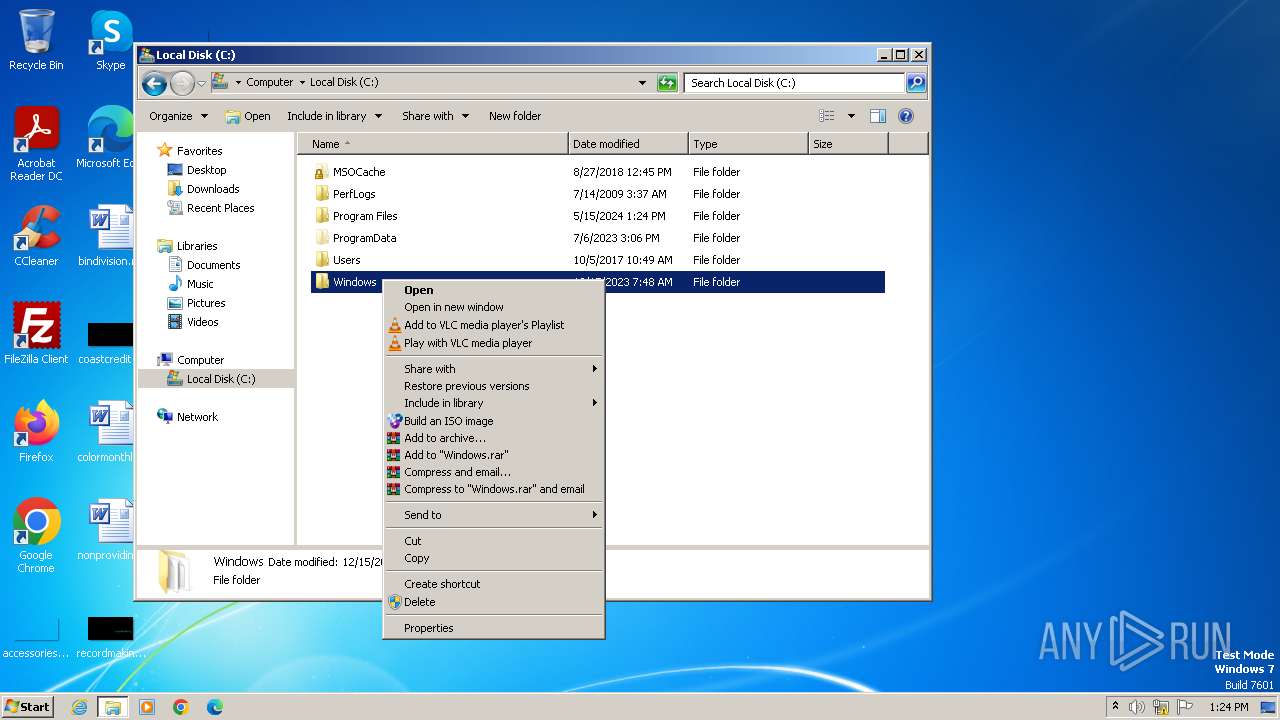
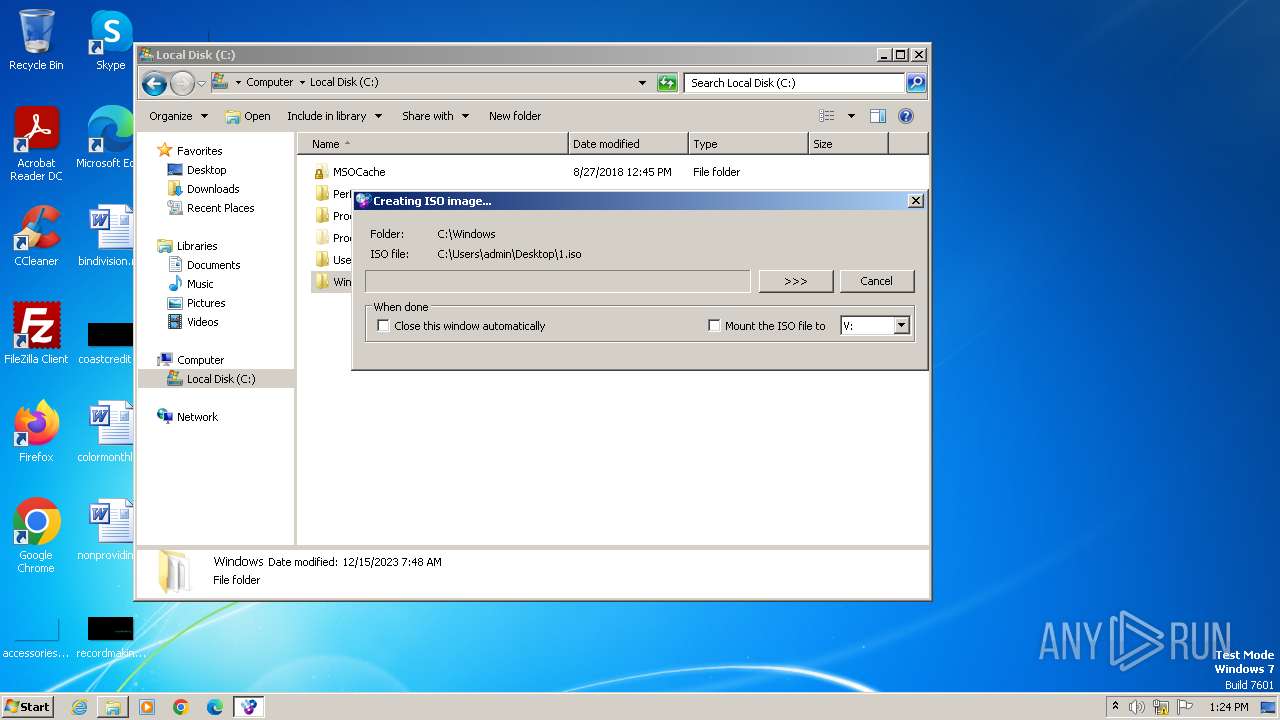
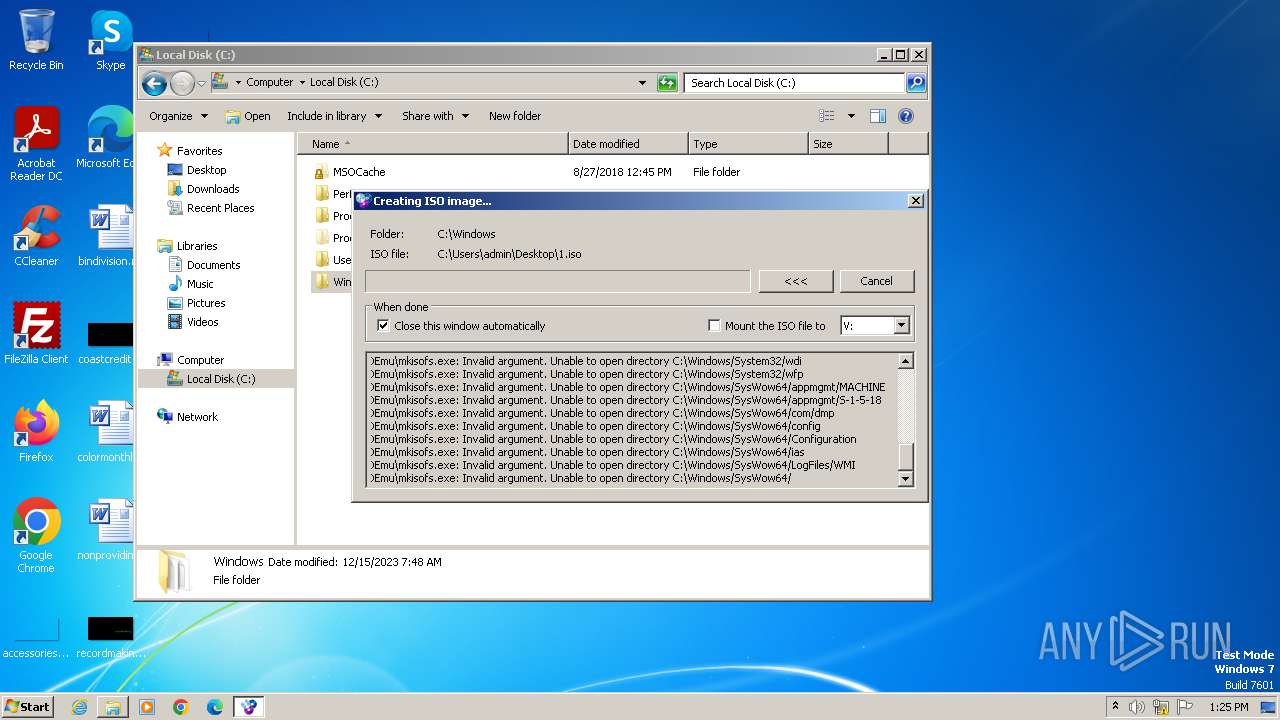
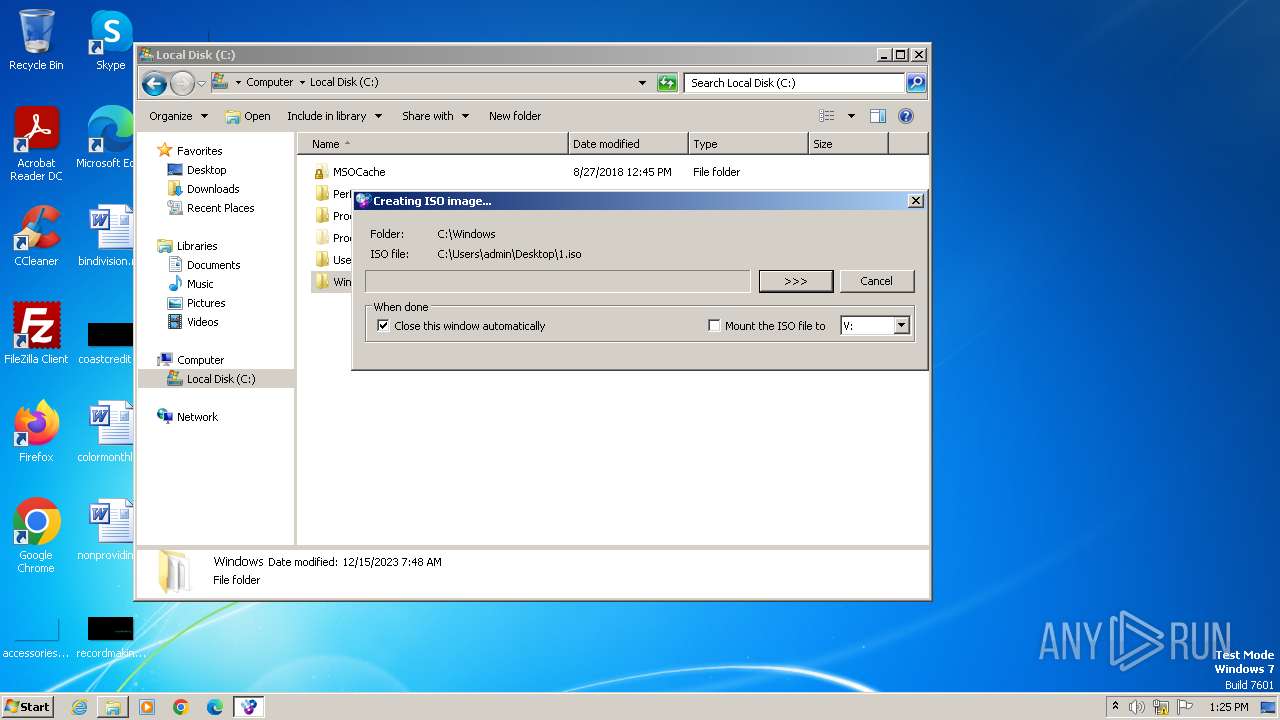
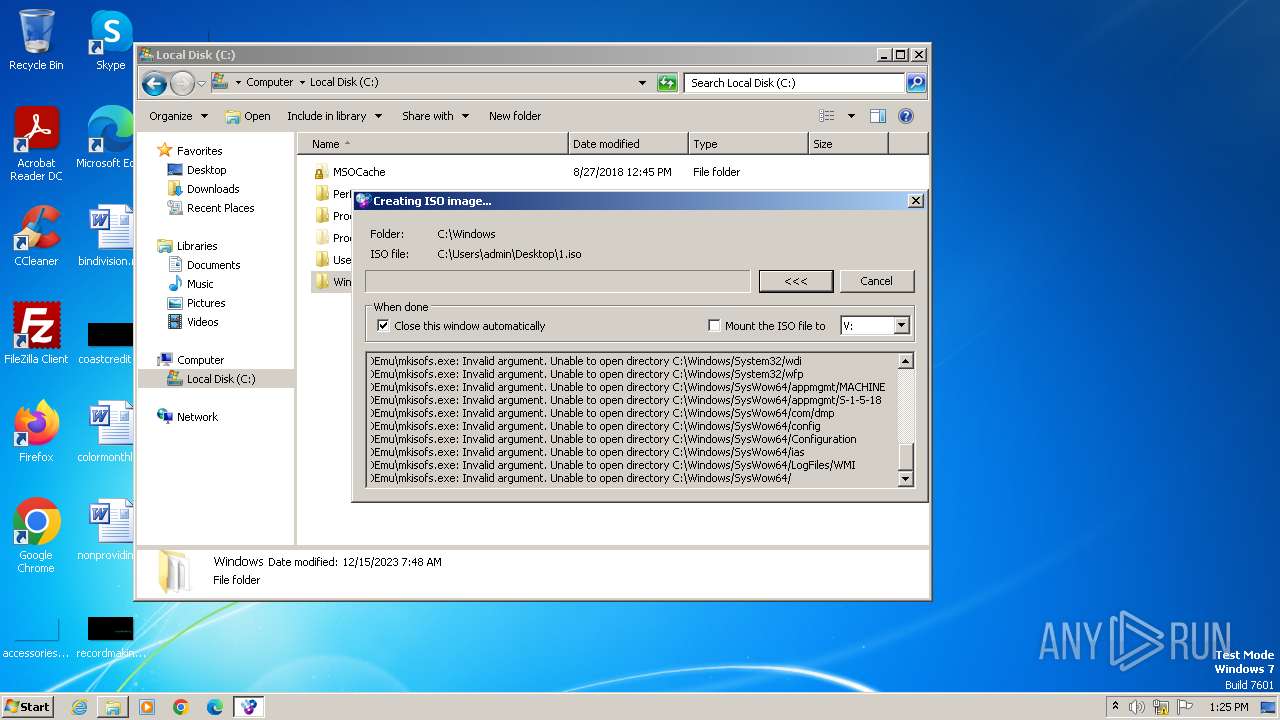
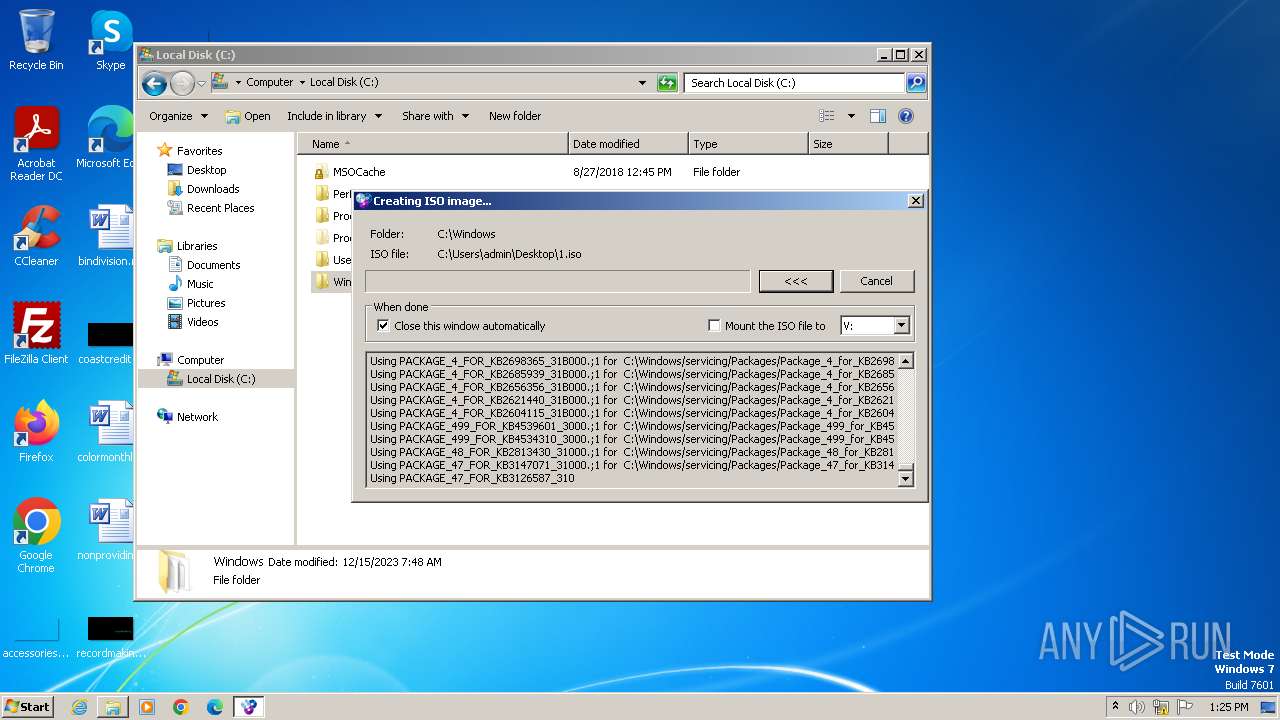
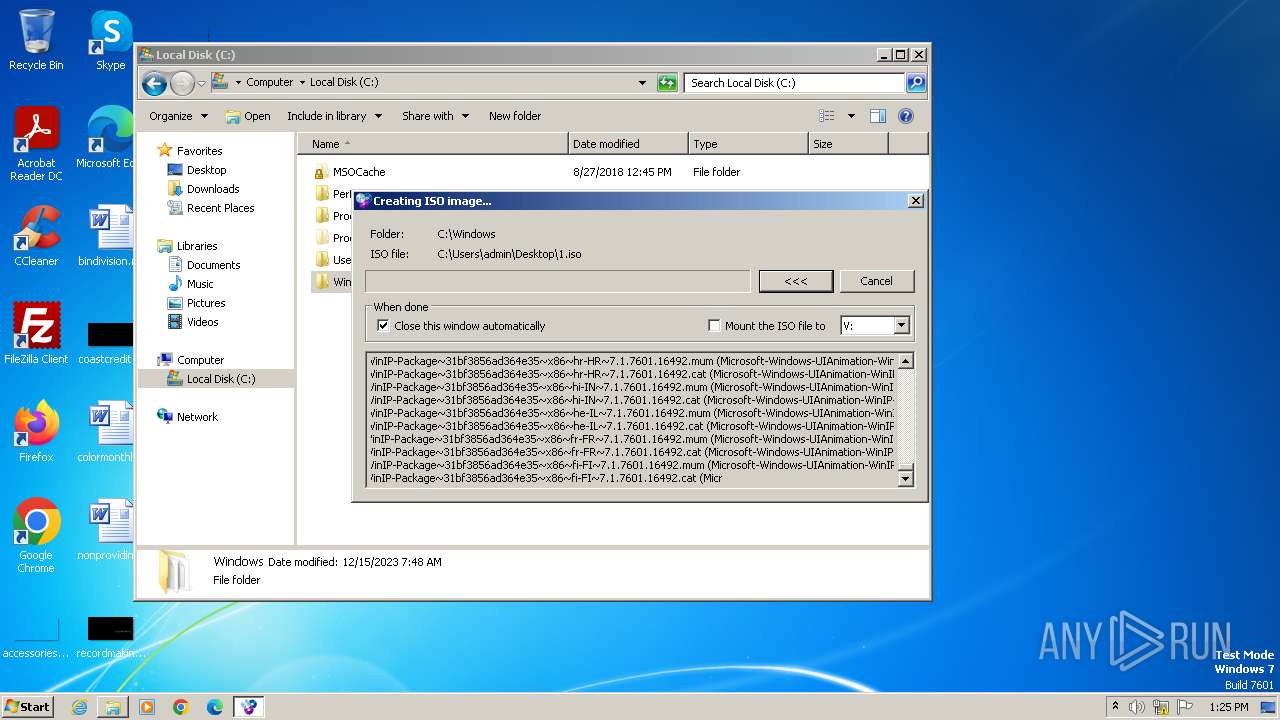
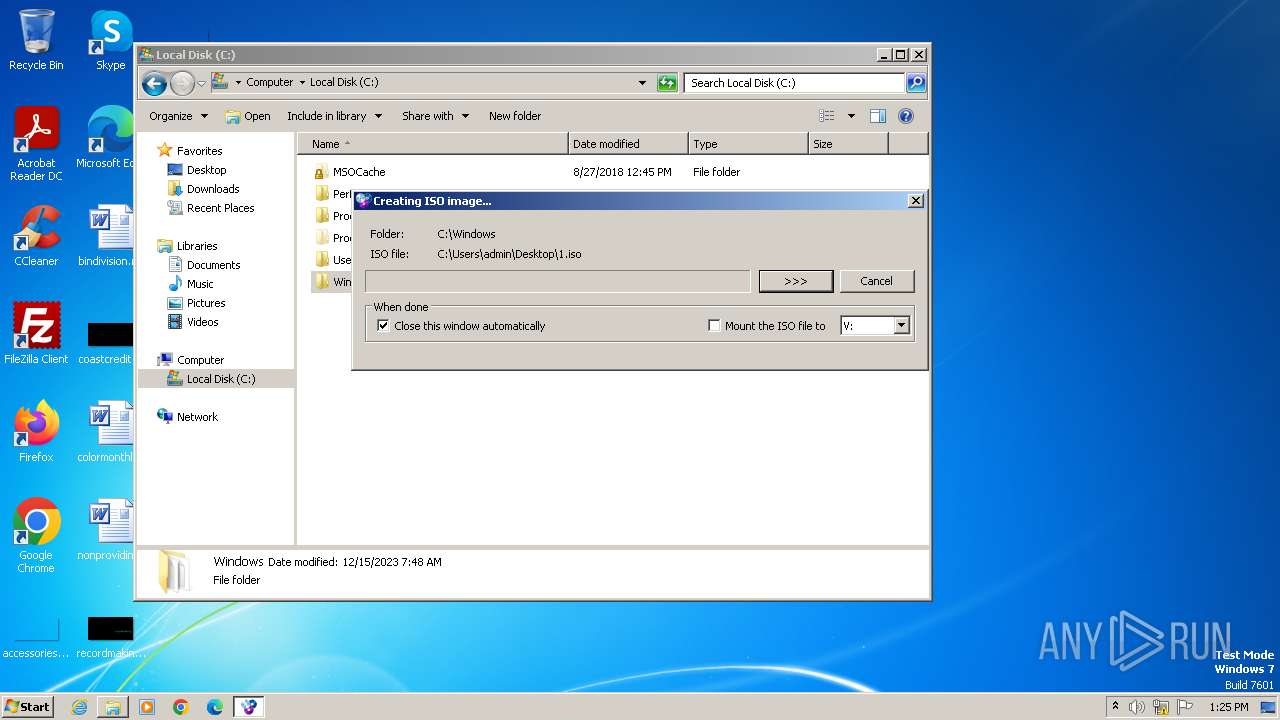
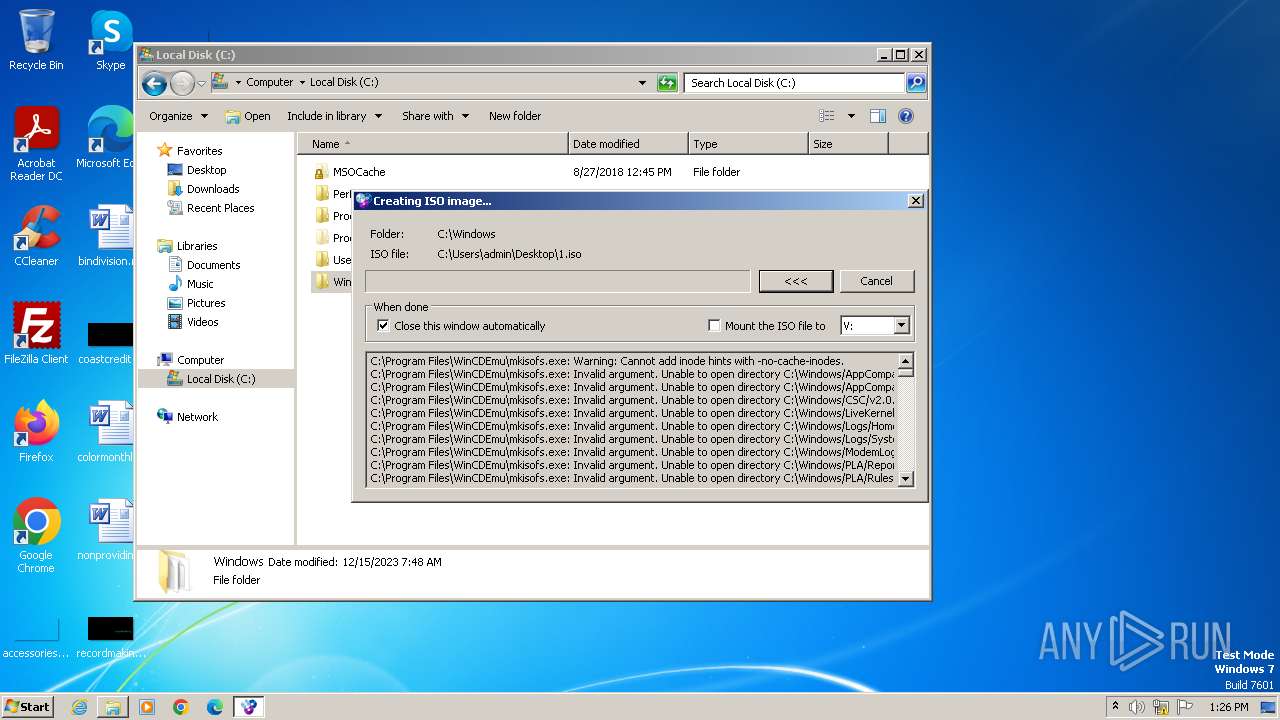
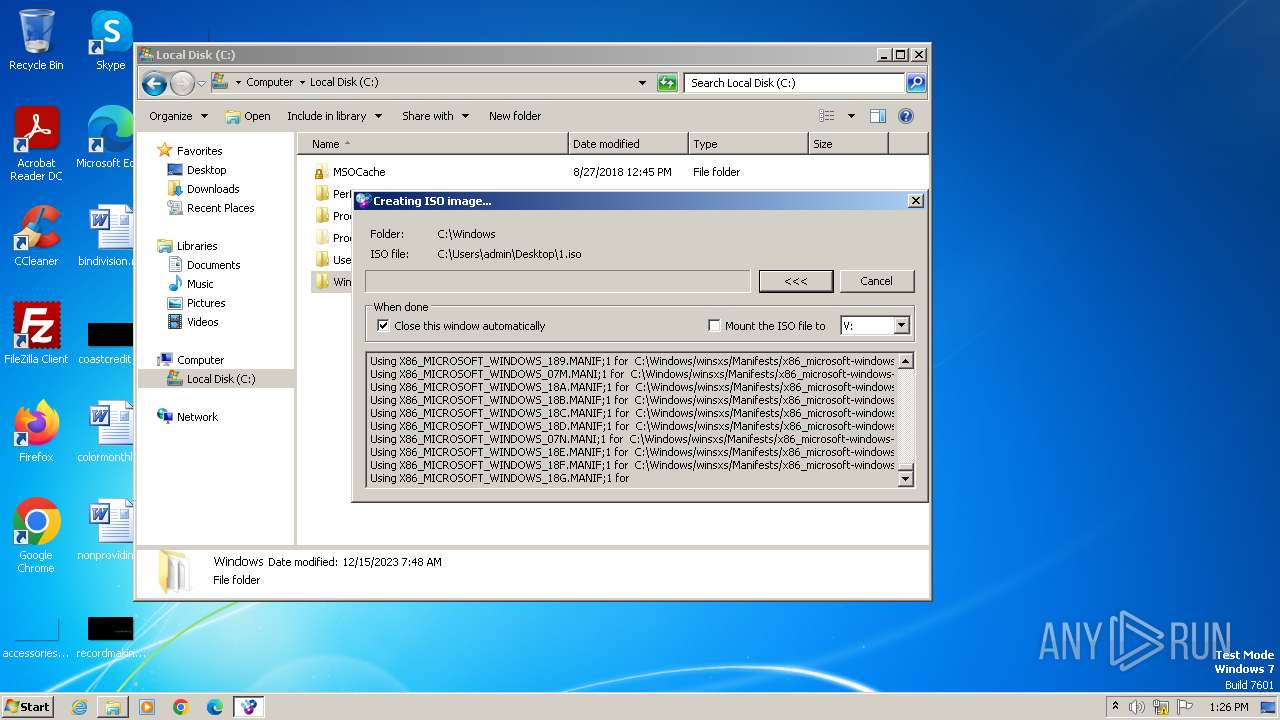
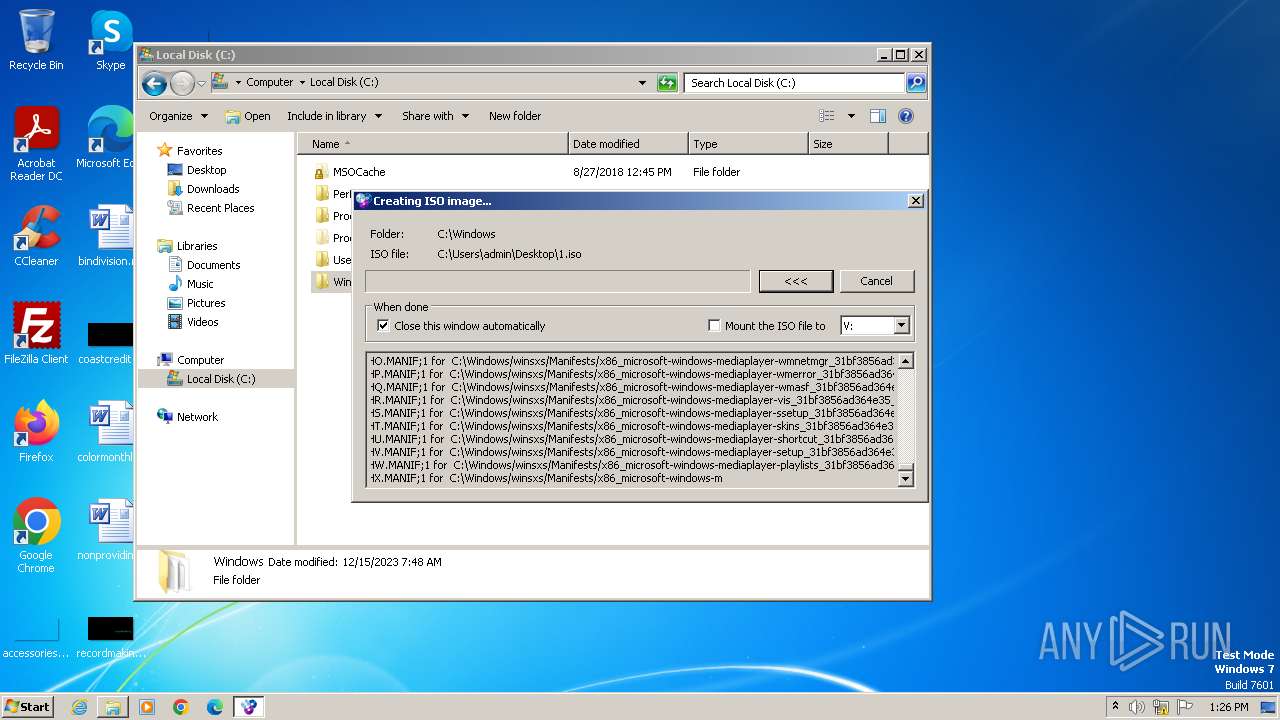
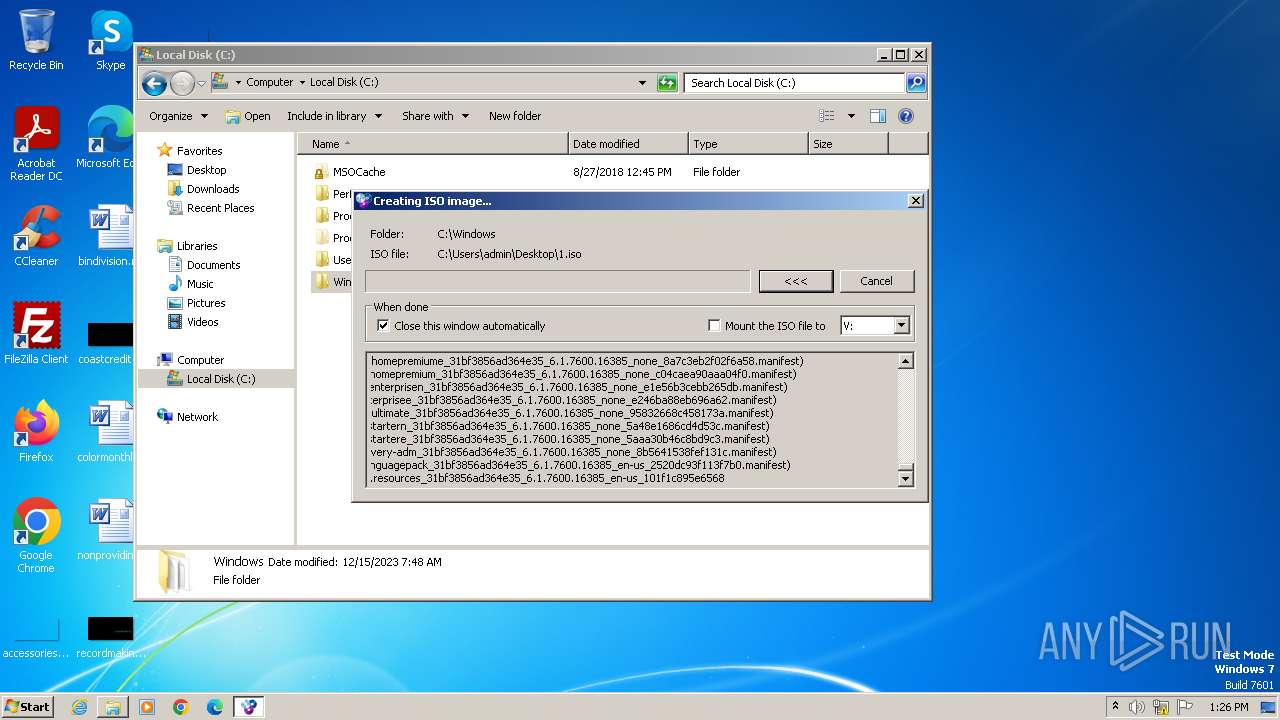
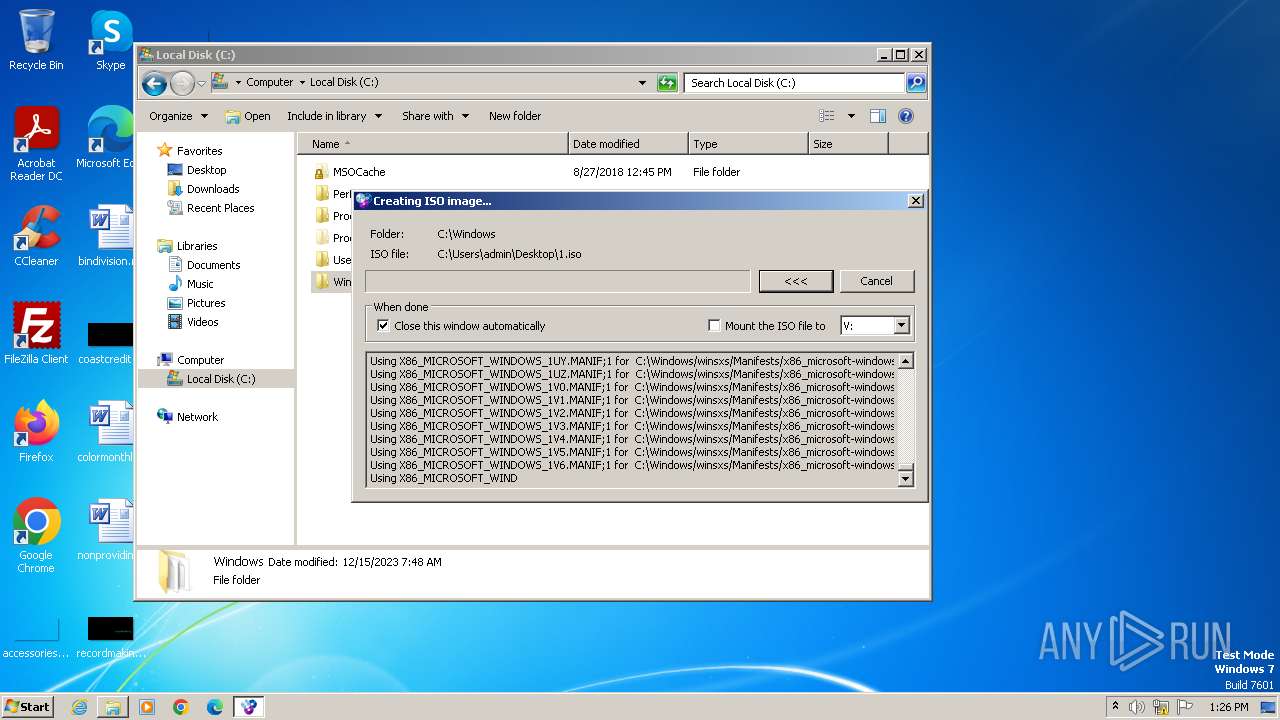
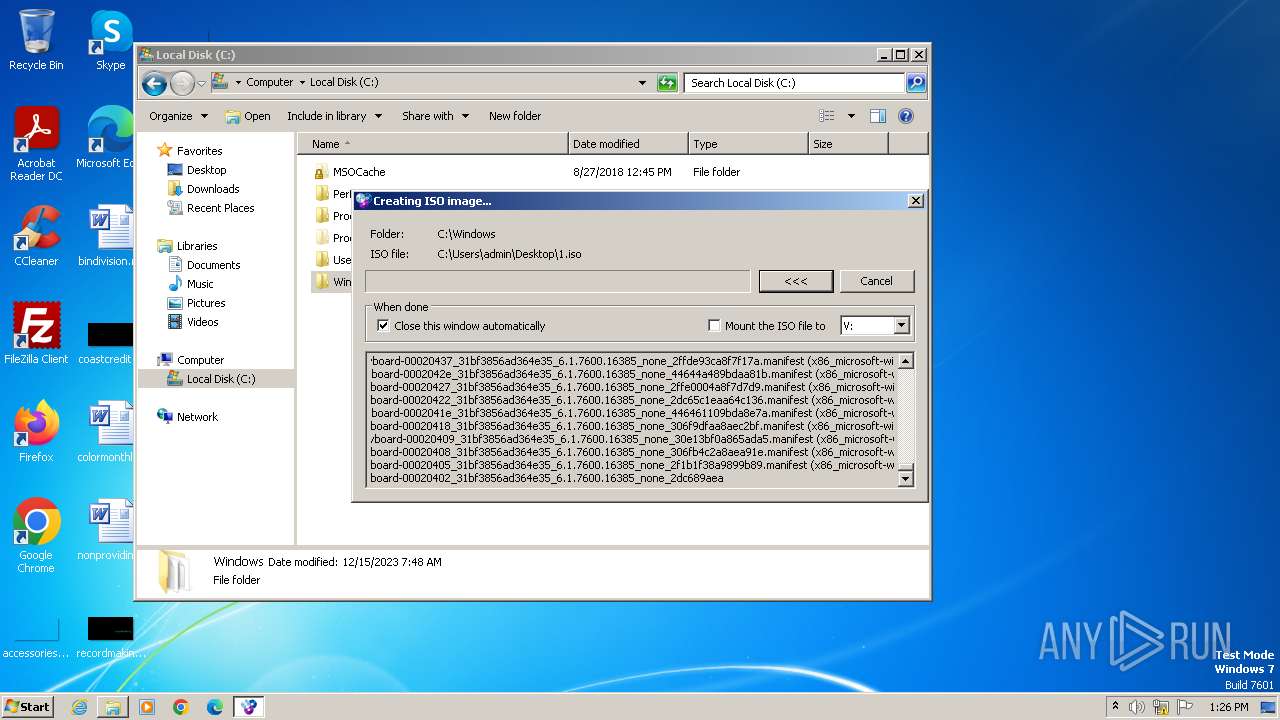
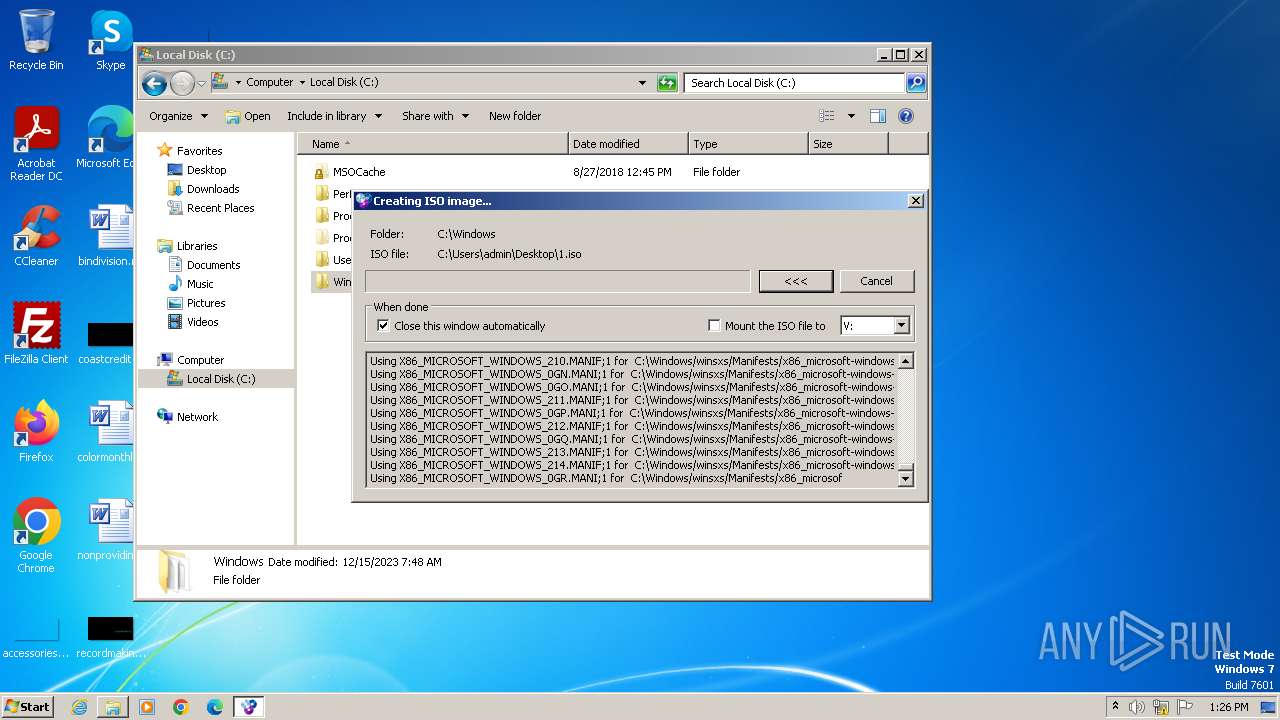
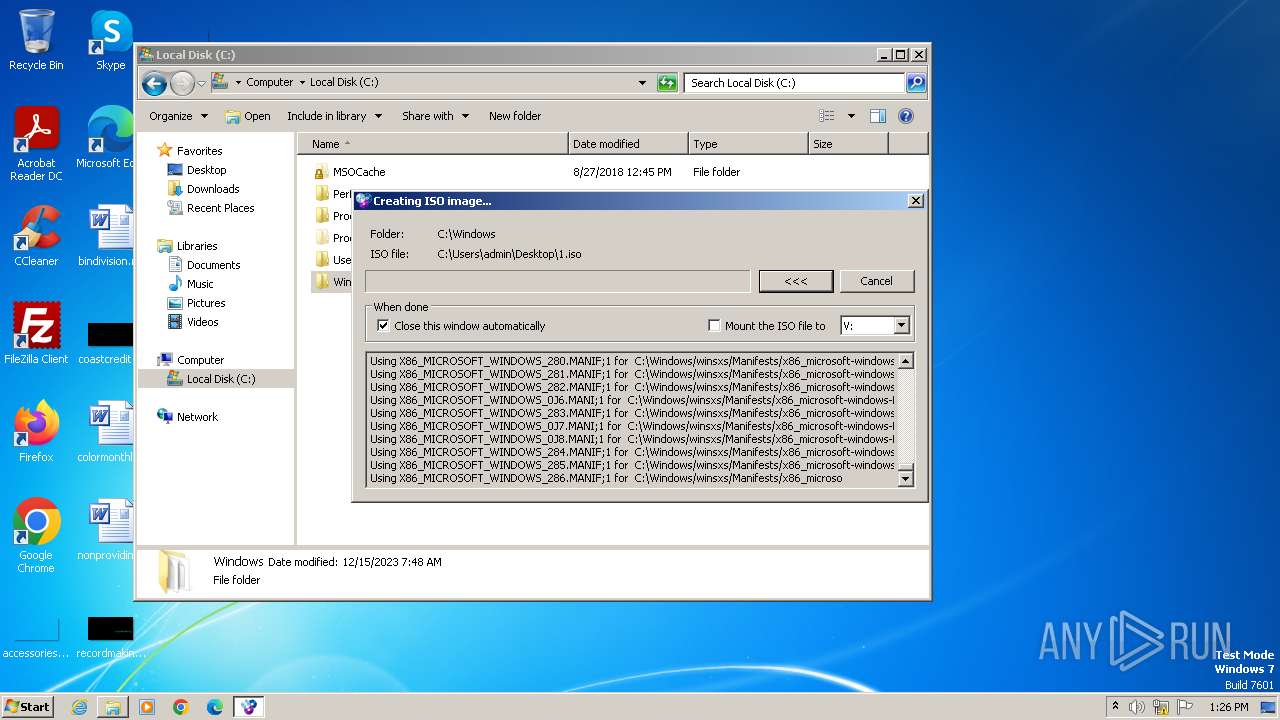
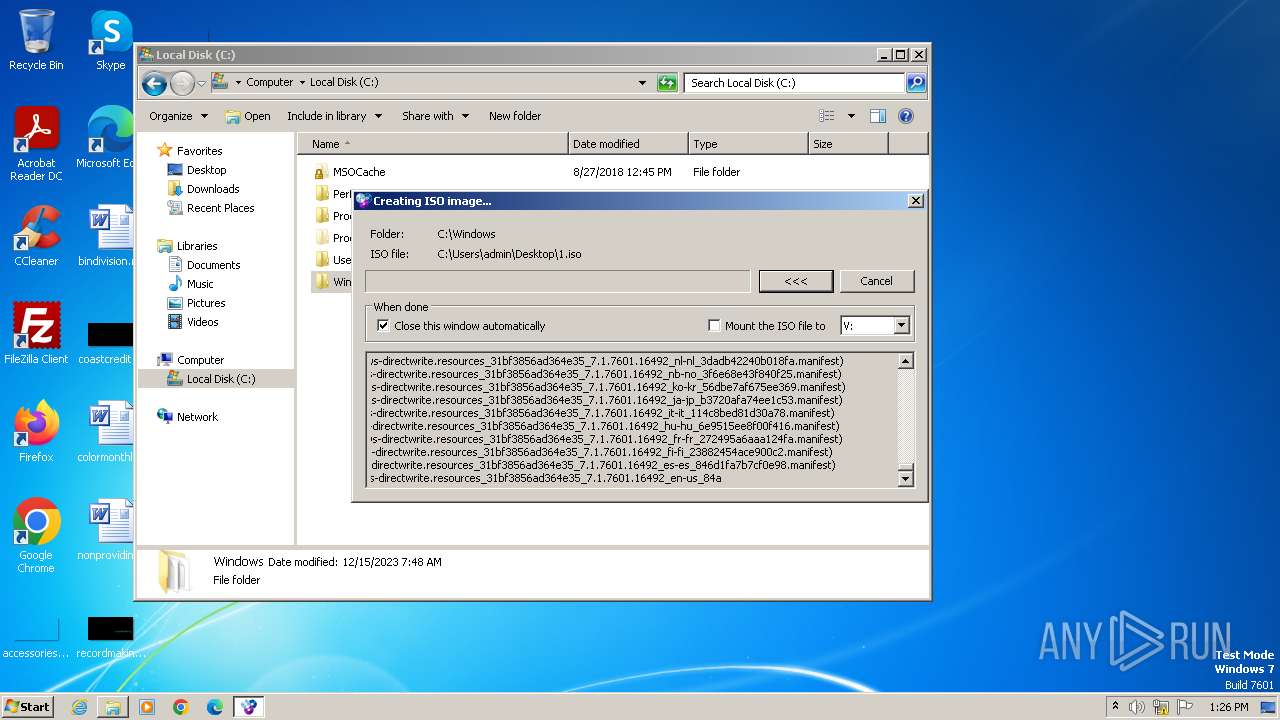
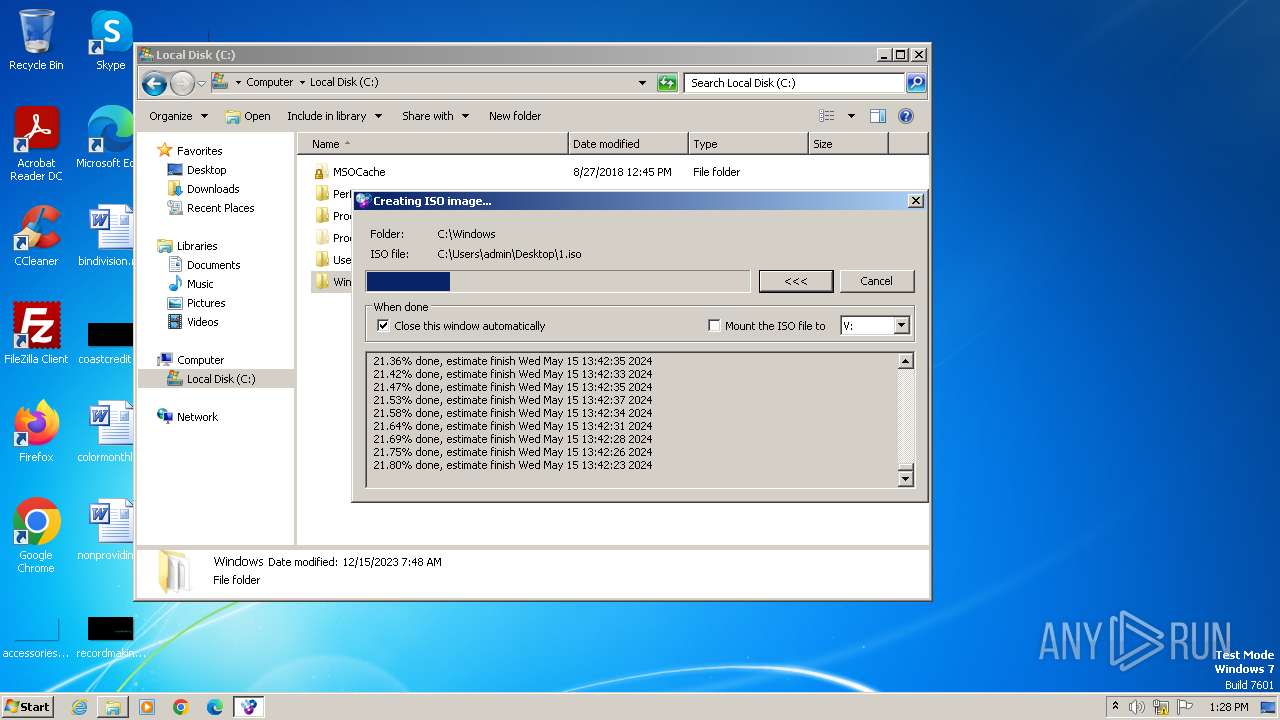
Image mount has been detect
- drvinst.exe (PID: 2476)
Creates a software uninstall entry
- WinCDEmu-4.1.exe (PID: 1120)
INFO
Checks supported languages
- WinCDEmu-4.1.exe (PID: 1120)
- uninstall.exe (PID: 112)
- drvinst32.exe (PID: 336)
- VirtualAutorunDisabler.exe (PID: 2040)
- drvinst.exe (PID: 2312)
- drvinst.exe (PID: 2476)
- vmnt.exe (PID: 2408)
- vmnt.exe (PID: 2560)
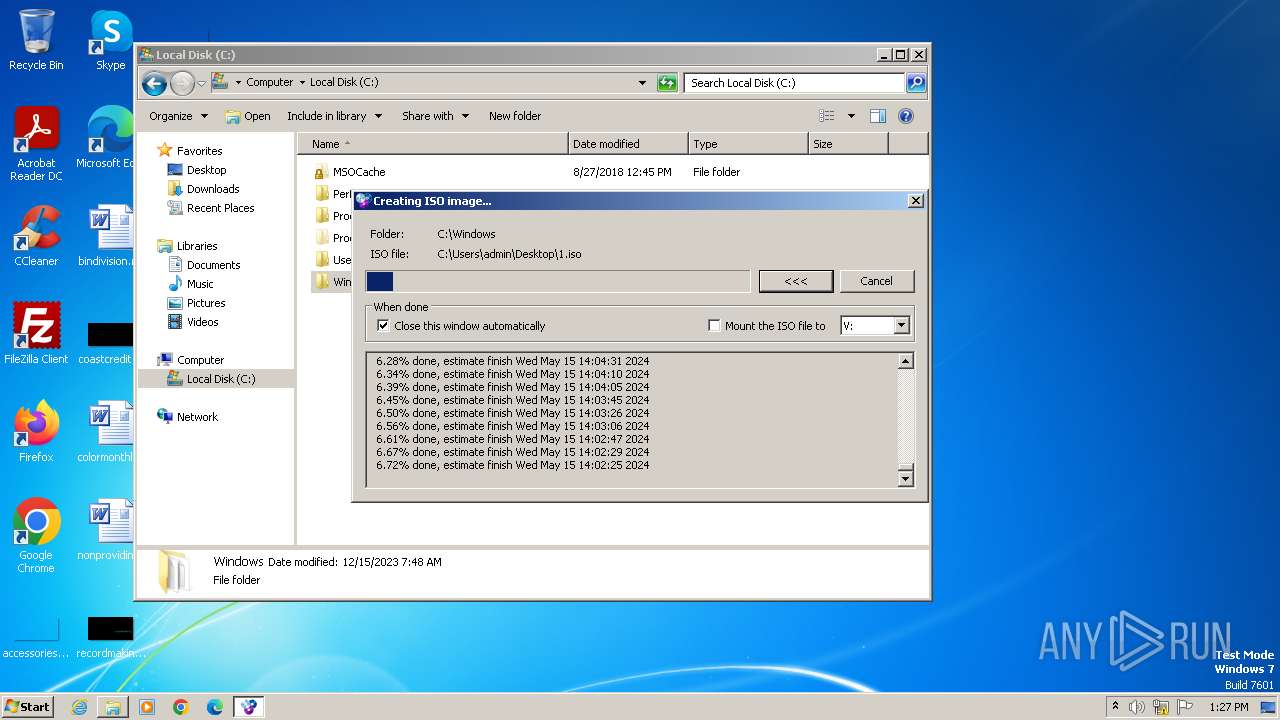
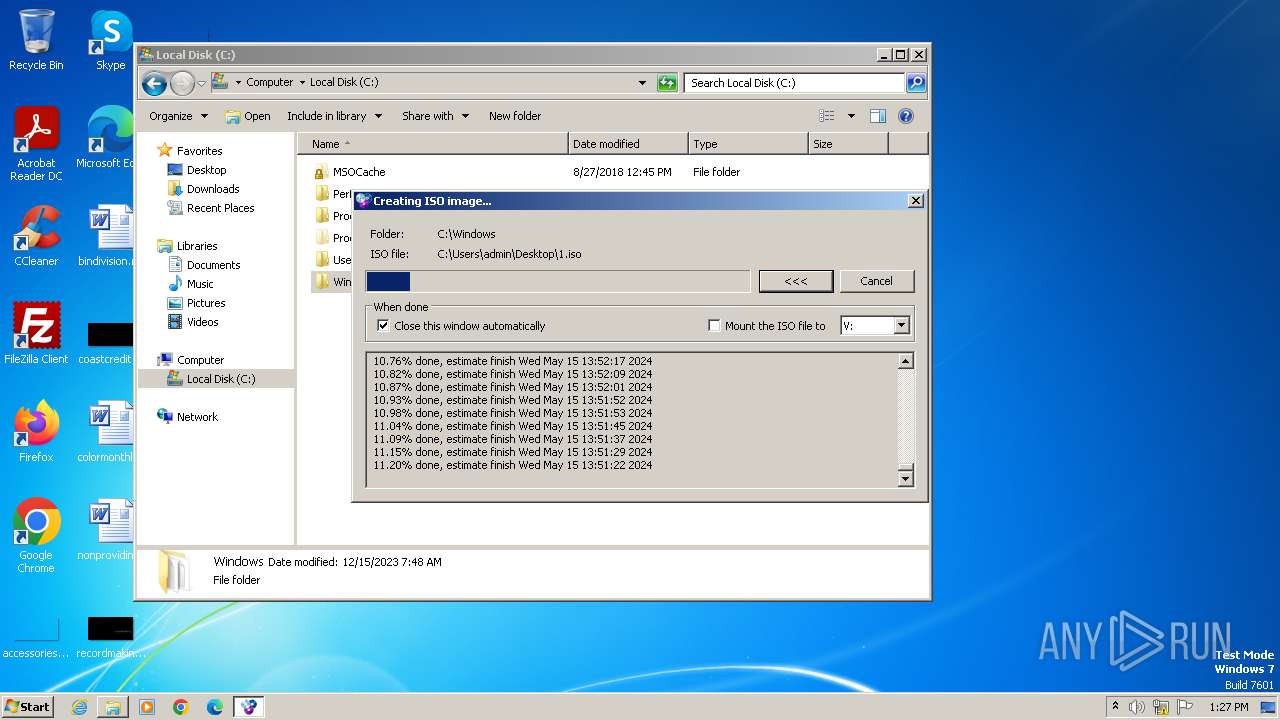
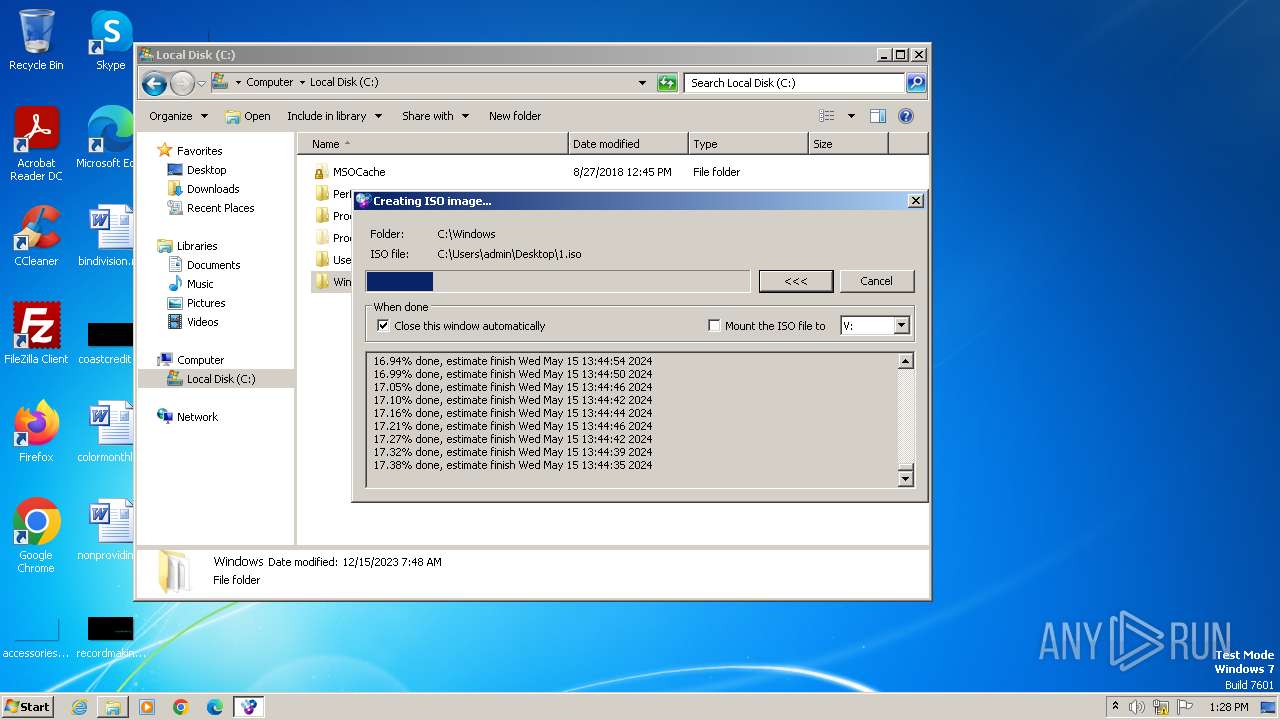
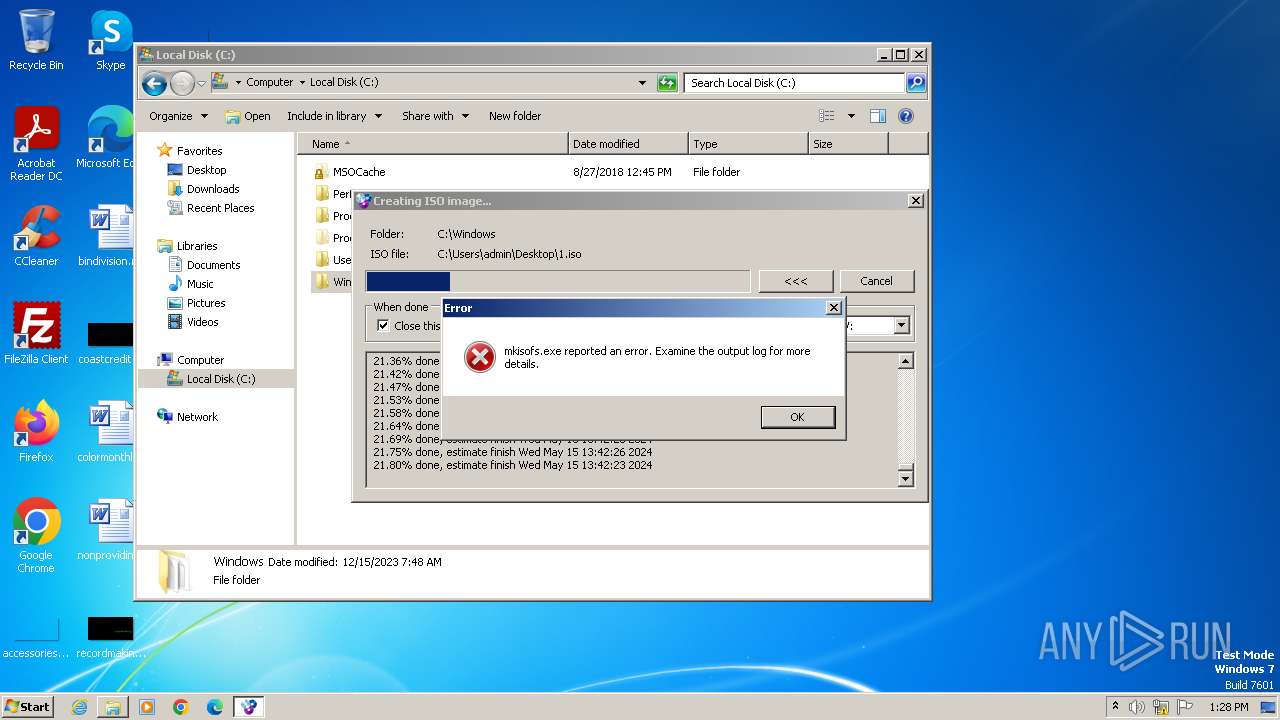
- mkisofs.exe (PID: 2392)
Reads the computer name
- WinCDEmu-4.1.exe (PID: 1120)
- uninstall.exe (PID: 112)
- drvinst32.exe (PID: 336)
- drvinst.exe (PID: 2312)
- drvinst.exe (PID: 2476)
- vmnt.exe (PID: 2408)
- vmnt.exe (PID: 2560)
Create files in a temporary directory
- WinCDEmu-4.1.exe (PID: 1120)
- drvinst32.exe (PID: 336)
Creates files in the program directory
- WinCDEmu-4.1.exe (PID: 1120)
Reads the machine GUID from the registry
- drvinst32.exe (PID: 336)
- drvinst.exe (PID: 2312)
- drvinst.exe (PID: 2476)
- vmnt.exe (PID: 2560)
Reads the software policy settings
- drvinst.exe (PID: 2312)
- rundll32.exe (PID: 1580)
- drvinst32.exe (PID: 336)
- drvinst.exe (PID: 2476)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 1580)
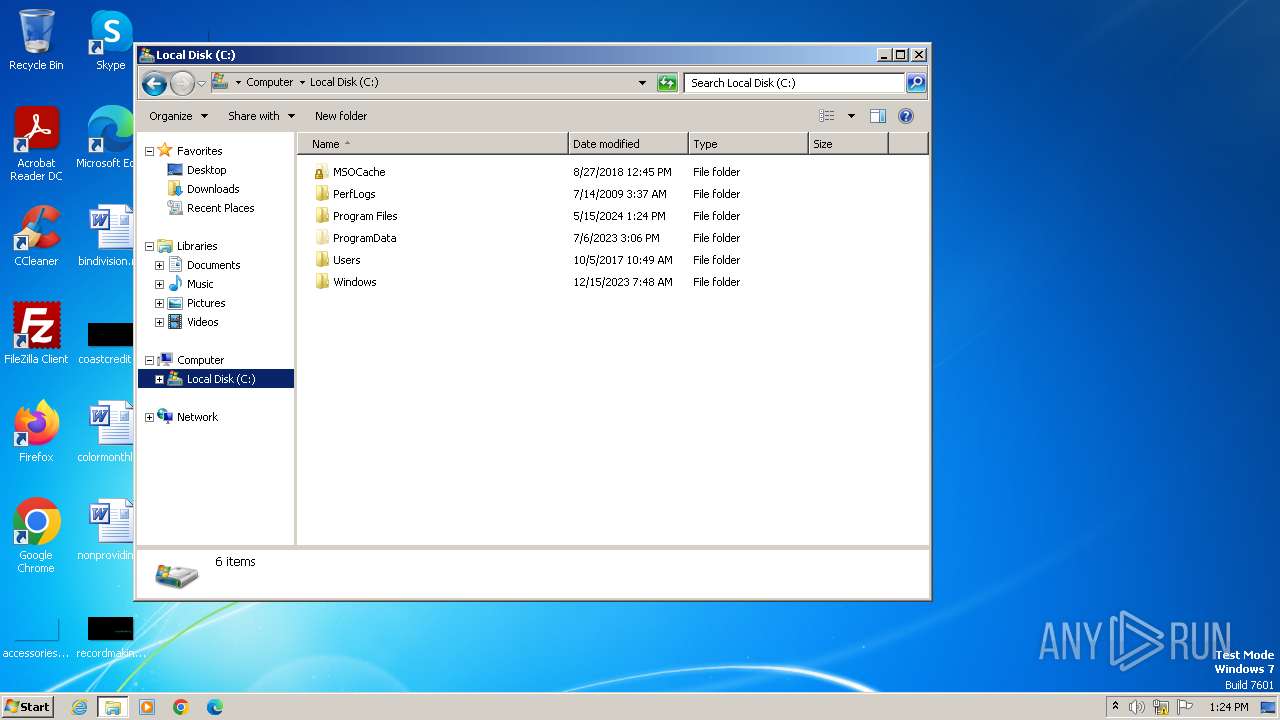
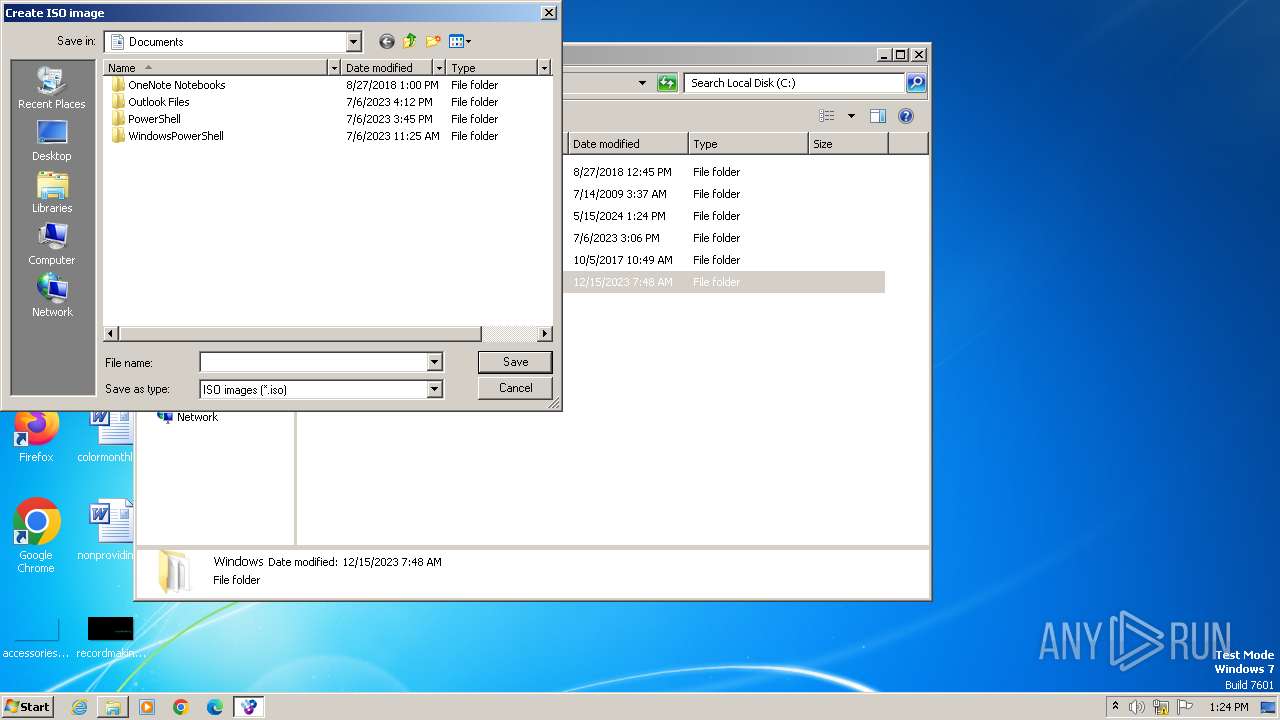
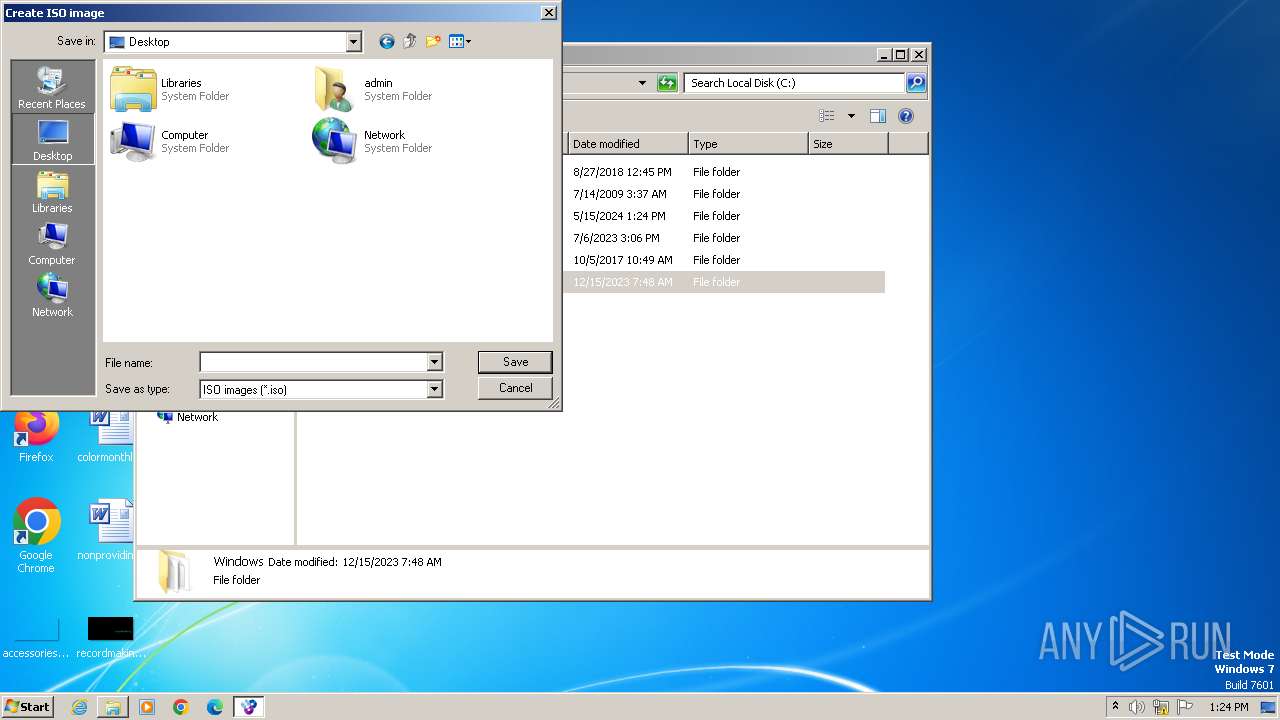
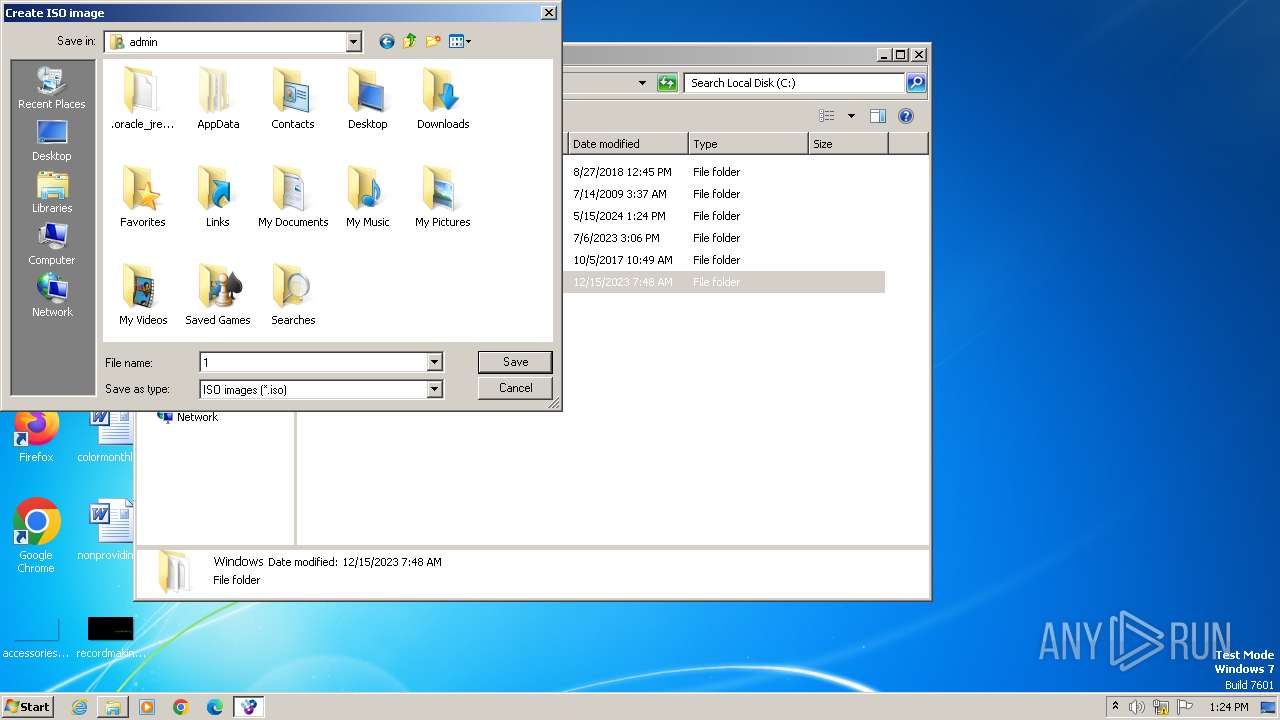
Manual execution by a user
- explorer.exe (PID: 1932)
- vmnt.exe (PID: 2560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:09:30 18:31:31+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 118784 |
| InitializedDataSize: | 40960 |
| UninitializedDataSize: | 249856 |
| EntryPoint: | 0x5a900 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.1.0.0 |
| ProductVersionNumber: | 4.1.0.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | http://wincdemu.sysprogs.org/ |
| CompanyName: | Sysprogs OU |
| FileDescription: | WinCDEmu installer |
| FileVersion: | 4.1 |
| LegalCopyright: | LGPL |
| LegalTrademarks: | Sysprogs |
| OriginalFileName: | WinCDEmu-installer.exe |
| ProductName: | WinCDEmu |
| ProductVersion: | 4.1 |
Total processes
61
Monitored processes
16
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 112 | "C:\Program Files\WinCDEmu\uninstall.exe" /UPDATE | C:\Program Files\WinCDEmu\uninstall.exe | — | WinCDEmu-4.1.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 116 | "C:\Windows\System32\regsvr32.exe" /s "C:\Program Files\WinCDEmu\x86\VirtualAutorunDisablerPS.dll" | C:\Windows\System32\regsvr32.exe | — | uninstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 336 | C:\Users\admin\AppData\Local\Temp\ssi66E9.tmp\drvinst32.exe instroot "root\BazisVirtualCDBus" "C:\Program Files\WinCDEmu\BazisVirtualCDBus.inf" | C:\Users\admin\AppData\Local\Temp\ssi66E9.tmp\drvinst32.exe | WinCDEmu-4.1.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 372 | "C:\Windows\System32\regsvr32.exe" /s "C:\Program Files\WinCDEmu\x86\WinCDEmuContextMenu.dll" | C:\Windows\System32\regsvr32.exe | — | uninstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1120 | "C:\Users\admin\Desktop\WinCDEmu-4.1.exe" | C:\Users\admin\Desktop\WinCDEmu-4.1.exe | explorer.exe | ||||||||||||
User: admin Company: Sysprogs OU Integrity Level: HIGH Description: WinCDEmu installer Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 1488 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1568 | C:\Windows\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {995C996E-D918-4a8c-A302-45719A6F4EA7} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1580 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{18734e92-c61b-7ddd-ca7b-aa75099b1c7e} Global\{7ed7dc9d-e37f-2e0a-2065-ff20e1da7d12} C:\Windows\System32\DriverStore\Temp\{176662a4-e1b9-108a-3979-c514a4626617}\bazisvirtualcdbus.inf C:\Windows\System32\DriverStore\Temp\{176662a4-e1b9-108a-3979-c514a4626617}\BazisVirtualCDBus.cat | C:\Windows\System32\rundll32.exe | — | drvinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1932 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2040 | "C:\Program Files\WinCDEmu\x86\VirtualAutorunDisabler.exe" /RegServer | C:\Program Files\WinCDEmu\x86\VirtualAutorunDisabler.exe | — | uninstall.exe | |||||||||||
User: admin Company: Sysprogs OU Integrity Level: HIGH Description: WinCDEmu autorun disabling module Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
Total events
25 625
Read events
25 164
Write events
438
Delete events
23
Modification events
| (PID) Process: | (1120) WinCDEmu-4.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.iso |
| Operation: | write | Name: | Application |
Value: vmnt.exe | |||
| (PID) Process: | (1120) WinCDEmu-4.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.cue |
| Operation: | write | Name: | Application |
Value: vmnt.exe | |||
| (PID) Process: | (1120) WinCDEmu-4.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.img |
| Operation: | write | Name: | Application |
Value: vmnt.exe | |||
| (PID) Process: | (1120) WinCDEmu-4.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.nrg |
| Operation: | write | Name: | Application |
Value: vmnt.exe | |||
| (PID) Process: | (1120) WinCDEmu-4.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.mds |
| Operation: | write | Name: | Application |
Value: vmnt.exe | |||
| (PID) Process: | (1120) WinCDEmu-4.1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.ccd |
| Operation: | write | Name: | Application |
Value: vmnt.exe | |||
| (PID) Process: | (112) uninstall.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (112) uninstall.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (112) uninstall.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (112) uninstall.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
26
Suspicious files
58
Text files
8
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1120 | WinCDEmu-4.1.exe | C:\Program Files\WinCDEmu\x64\WinCDEmuContextMenu.dll | executable | |
MD5:E3526F364347D94C329A8CA6D8DF17DA | SHA256:0CA454FA57A90A4D899E0797D0AFF5364260F3649B963D21582FA7010E419C2A | |||
| 1120 | WinCDEmu-4.1.exe | C:\Program Files\WinCDEmu\x86\WinCDEmuContextMenu.dll | executable | |
MD5:C36FEE011C683583EC2D7F81DC53C348 | SHA256:51659ADDDEC203EE06BB21BA263E1BFB7EEE990648CDE127628E2C963F53A8C9 | |||
| 1120 | WinCDEmu-4.1.exe | C:\Program Files\WinCDEmu\x64\WinCDEmuContextMenu.bak | executable | |
MD5:03A9955EC55C5C6E00A3281602B30132 | SHA256:24B62E505F0A612FED69A425A9FD0F3459E76941ADD8FB6CCC3F43C64F12A7BE | |||
| 1120 | WinCDEmu-4.1.exe | C:\Program Files\WinCDEmu\x86\VirtualAutorunDisablerPS.dll | executable | |
MD5:E3BD21095F8D0017E2073D53E68F7509 | SHA256:F7DD93BF06C41897D8EA789F7B9B358547576F30F1D93ABCFCC421BA50C89C69 | |||
| 1120 | WinCDEmu-4.1.exe | C:\Program Files\WinCDEmu\x64\VirtualAutorunDisablerPS.dll | executable | |
MD5:7D20F582E32CC6D34E633928C5564F65 | SHA256:B8C08185576D7CD5749C94D792B35F5EDE59885BE89F26F980526B7AB47CB534 | |||
| 1120 | WinCDEmu-4.1.exe | C:\Program Files\WinCDEmu\batchmnt.exe | executable | |
MD5:5E6561921A7722EA025A79172E7B443E | SHA256:C694D42D19DAA784687B9146D19B7797B937E151A8AA7155904F54A1A6FD7A84 | |||
| 1120 | WinCDEmu-4.1.exe | C:\Program Files\WinCDEmu\batchmnt64.exe | executable | |
MD5:EF5F980E1E1DBDF454673206751BF255 | SHA256:4A363E27B849A994250E6F2E4C9B4DD56F70F7CF9FF78375B3EE23244F1F9B6E | |||
| 1120 | WinCDEmu-4.1.exe | C:\Program Files\WinCDEmu\mkisofs.exe | executable | |
MD5:298B00E6DC408F5EA4FAD8FF173028D5 | SHA256:19F7C8771CCE642A15984C73C4BEE2B441D6C47236958D8F5A7EB05738B0DA4B | |||
| 1120 | WinCDEmu-4.1.exe | C:\Program Files\WinCDEmu\uninstall64.exe | executable | |
MD5:2ED433C12CFA75908EB790FC8B23EA9E | SHA256:9590EBD10C8CF1D58CC7FF543923E22DBDFC901EA5643F0E59670EF911694C90 | |||
| 1120 | WinCDEmu-4.1.exe | C:\Program Files\WinCDEmu\uninstall.exe | executable | |
MD5:168CF87105D81FD649C2D49F91C53496 | SHA256:6A8F9819384A46411ACD85297D895D650766271D476EFEB3392134D6784680C5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |