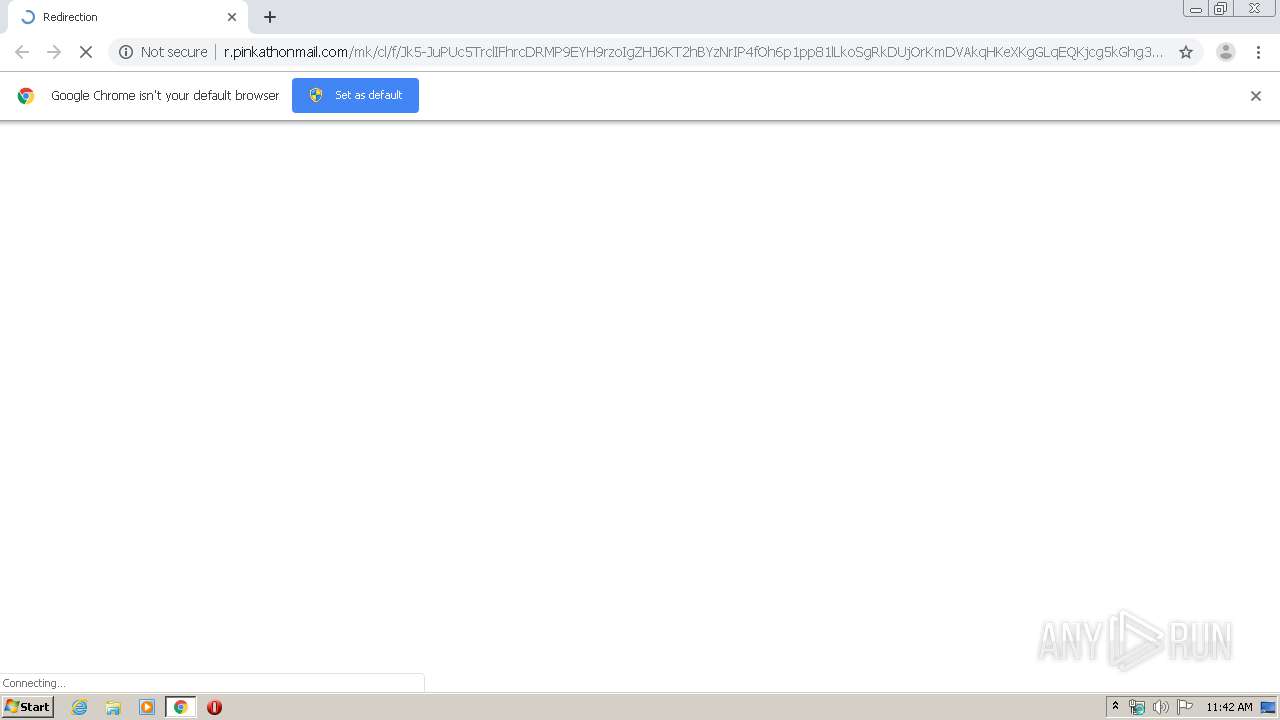
| URL: | http://r.pinkathonmail.com/mk/cl/f/Jk5-JuPUc5TrclIFhrcDRMP9EYH9rzoIgZHJ6KT2hBYzNrIP4fOh6p1pp81lLkoSgRkDUjOrKmDVAkqHKeXKgGLqEQKjcg5kGhg3HpkJZrkg7NTWxpf83AXflI89GP4ad-U2Tp2g6LUxNSEg-X_BaXaD_BZdsNJo7kJReAP0wmeIIlEtxw |
| Full analysis: | https://app.any.run/tasks/f965d480-295e-4975-b22d-f8d26d4b4631 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 10:42:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 917CA98DA63405638D3EF33123BBC0F2 |
| SHA1: | 7AA6A531BCC47185566AB10185A181143506D77B |
| SHA256: | C46F97A3B48060E3D9B467FFC73EFF8F1DA7B355E150496BA1E0B80FDB7EBBB4 |
| SSDEEP: | 6:CMLf22KI4Y9gg8m6ZQOD+qAU6+OuFfCYGDvi2Lrah6dYBQSn:Zr221jyQOBA1+OuFqYsL+tBQS |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2784)
INFO
Reads the hosts file
- chrome.exe (PID: 2784)
- chrome.exe (PID: 3880)
Application launched itself
- chrome.exe (PID: 2784)
Reads settings of System Certificates
- chrome.exe (PID: 3880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
28
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,17520006566804599063,14212101678021356474,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9829528296900080855 --mojo-platform-channel-handle=3140 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,17520006566804599063,14212101678021356474,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12387323925272525812 --mojo-platform-channel-handle=3784 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,17520006566804599063,14212101678021356474,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14951041694016943795 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3560 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,17520006566804599063,14212101678021356474,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1274924732245934638 --mojo-platform-channel-handle=2676 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,17520006566804599063,14212101678021356474,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4847863903209838669 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,17520006566804599063,14212101678021356474,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3831353489382544519 --mojo-platform-channel-handle=2284 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,17520006566804599063,14212101678021356474,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8454695492285760490 --mojo-platform-channel-handle=4236 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,17520006566804599063,14212101678021356474,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1850490659179737053 --mojo-platform-channel-handle=1308 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,17520006566804599063,14212101678021356474,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7247475647148529709 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
651
Read events
566
Write events
80
Delete events
5
Modification events
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2876) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2784-13230124970473500 |
Value: 259 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
113
Text files
251
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E831EAA-AE0.pma | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\49e7477d-8f54-4802-a8e6-6c8b8d1e1ed4.tmp | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66ba3.TMP | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66dc6.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
202
TCP/UDP connections
50
DNS requests
26
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
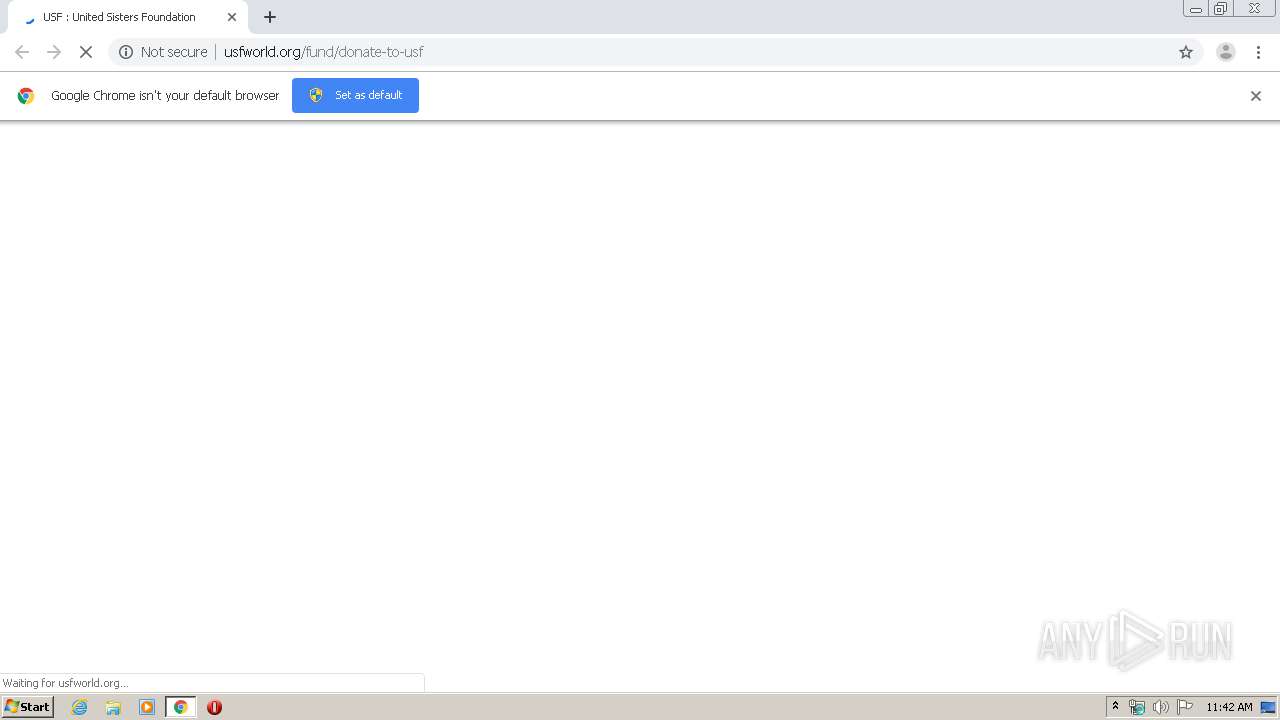
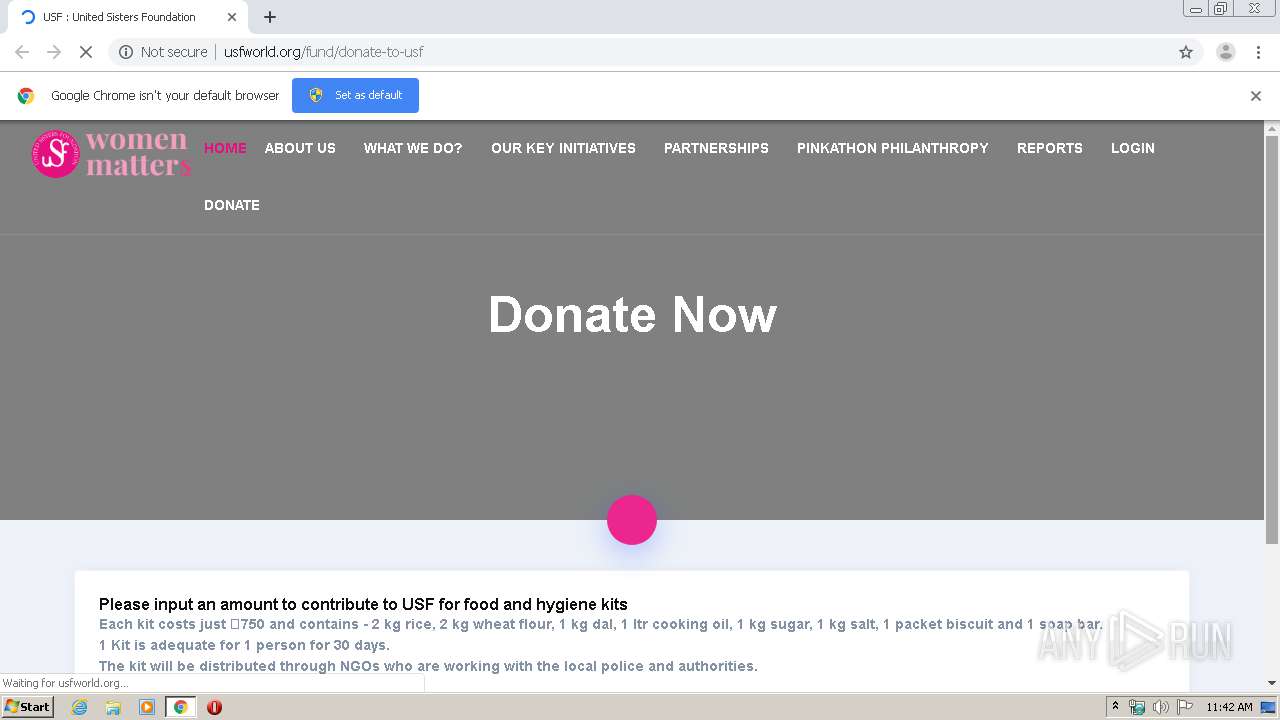
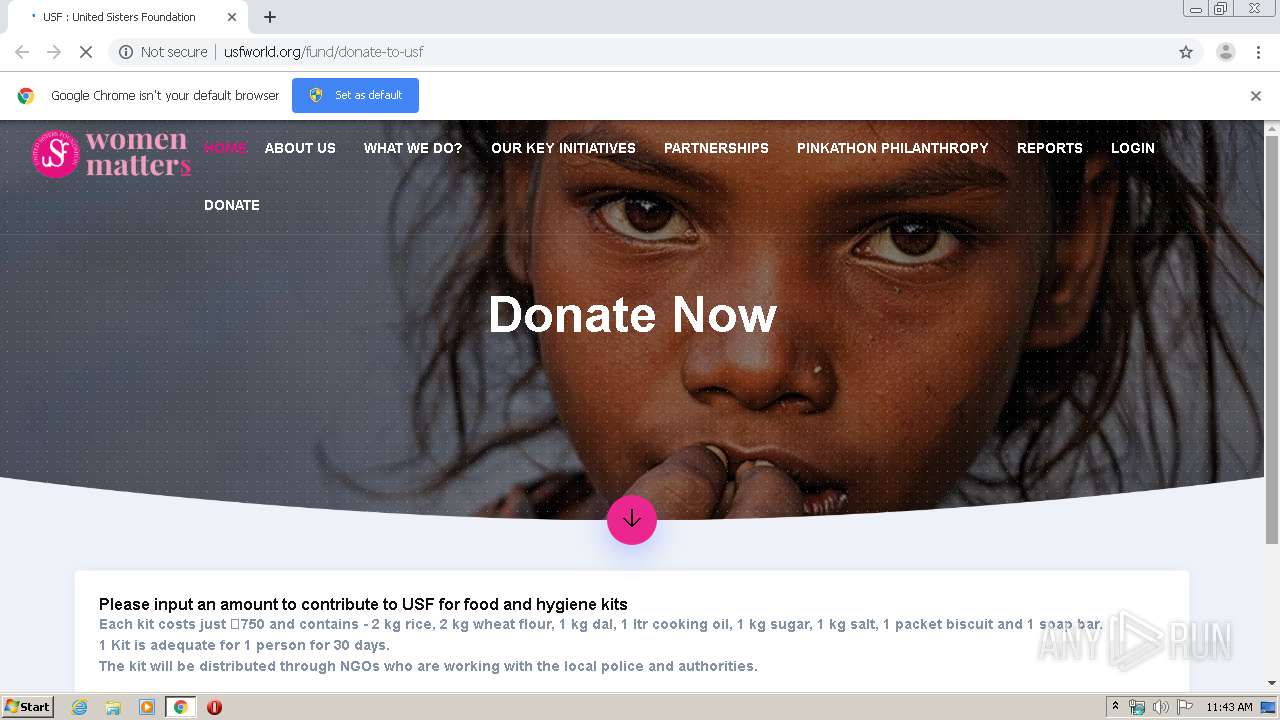
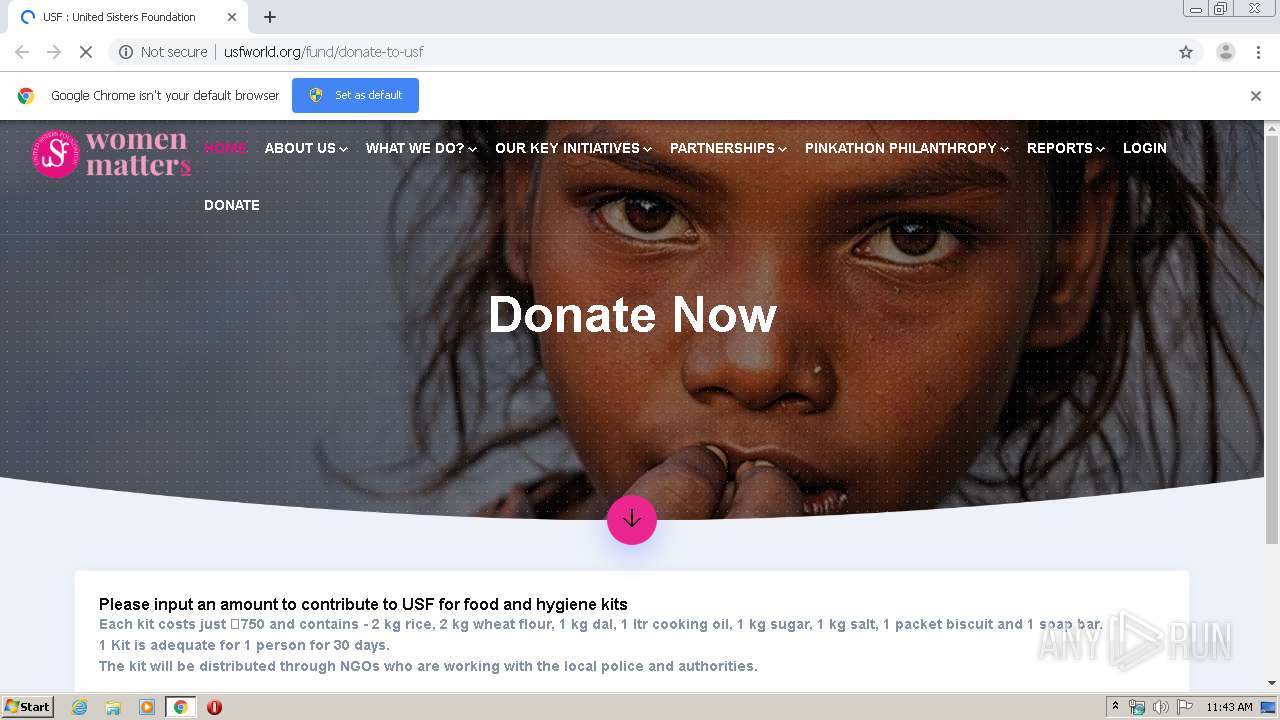
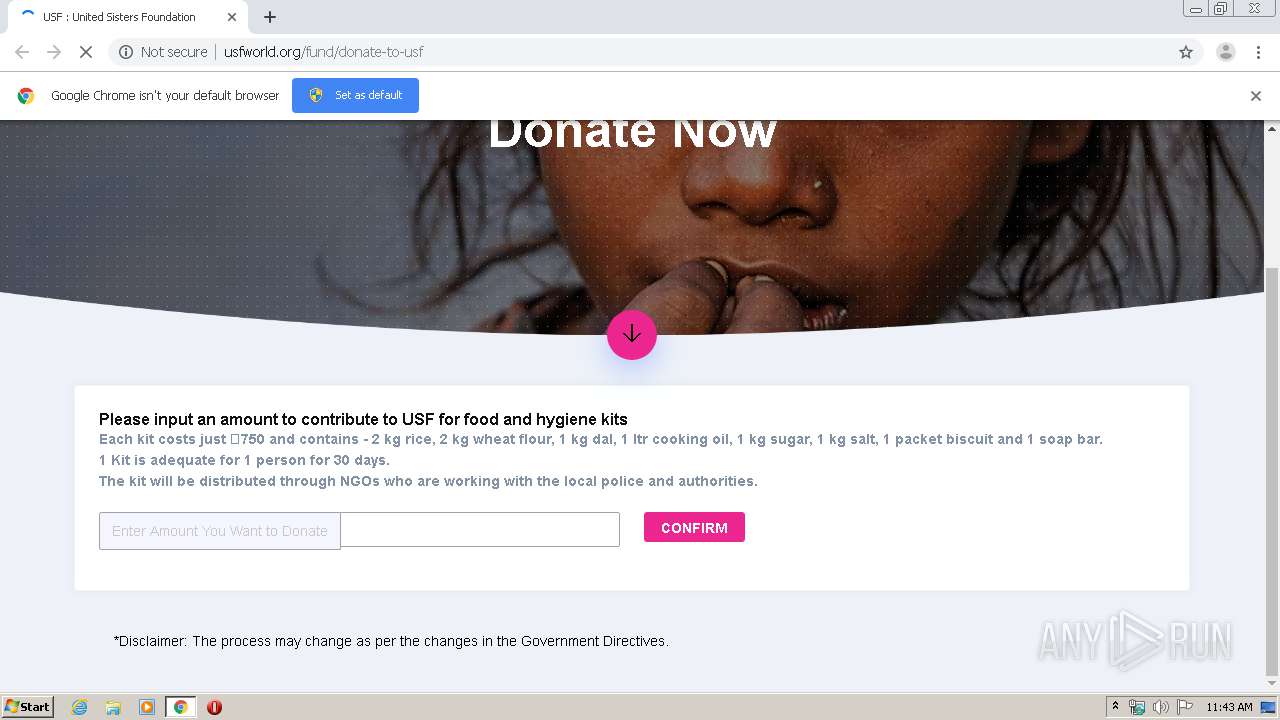
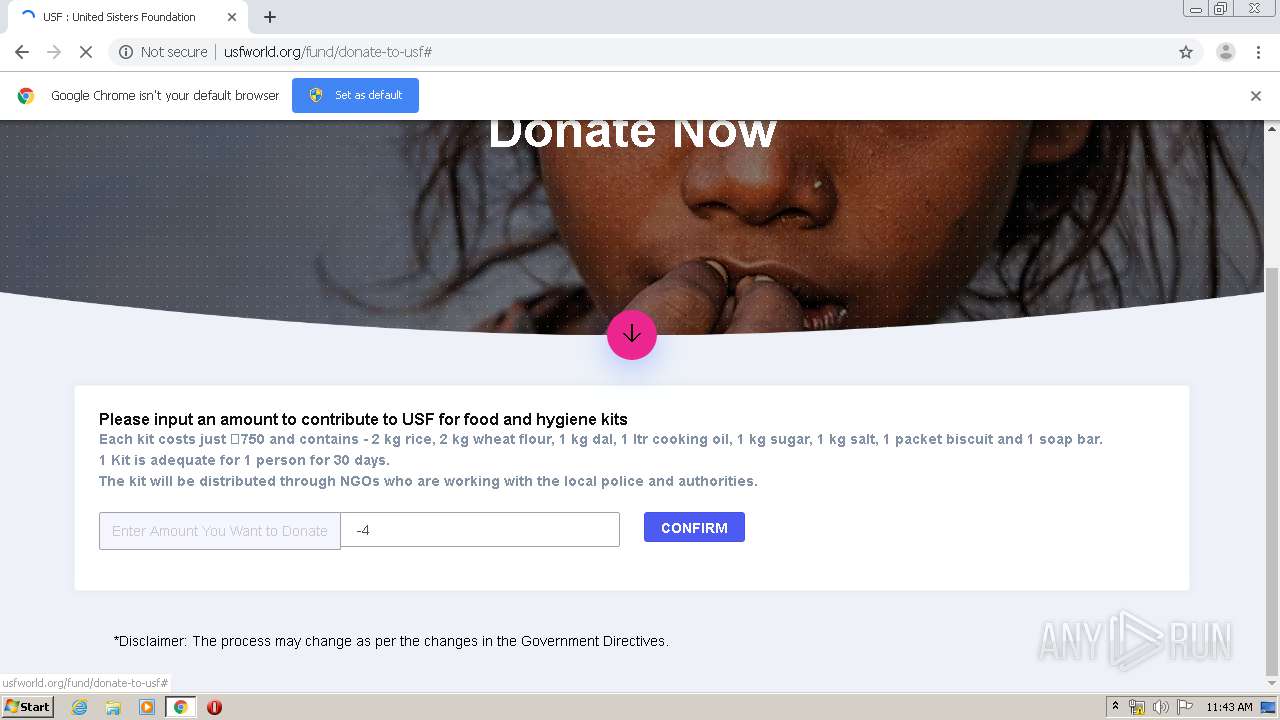
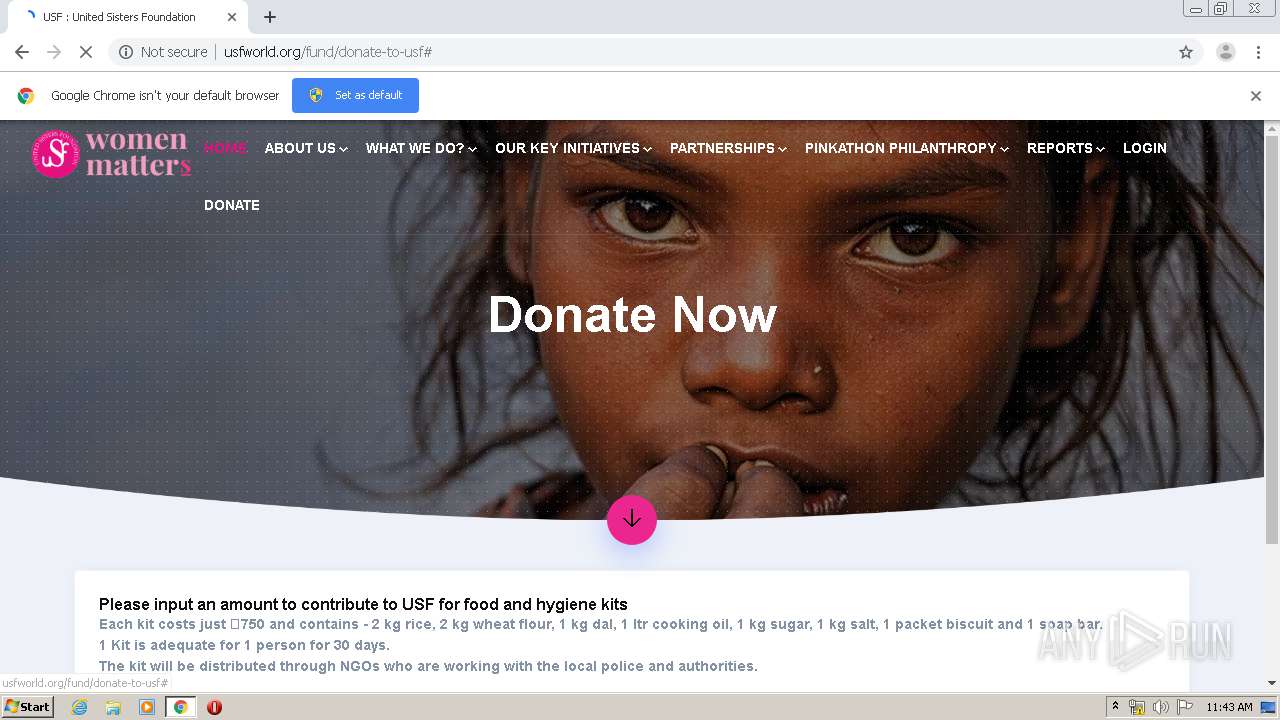
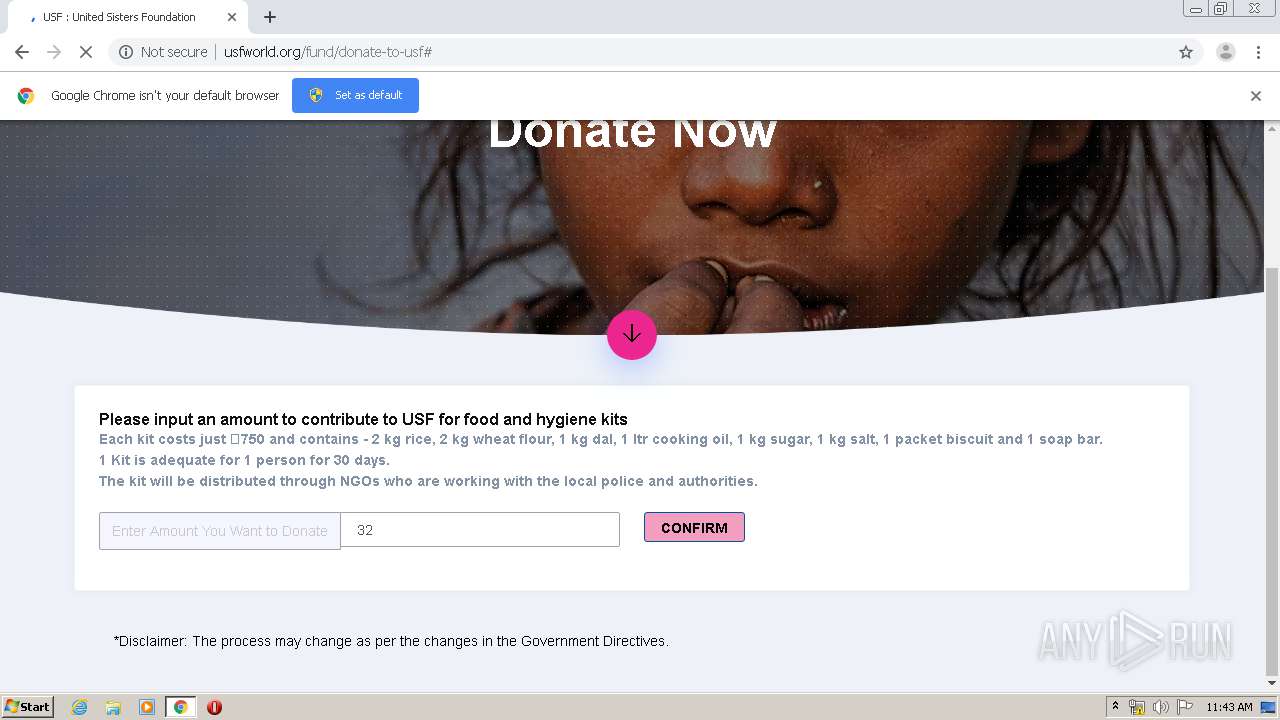
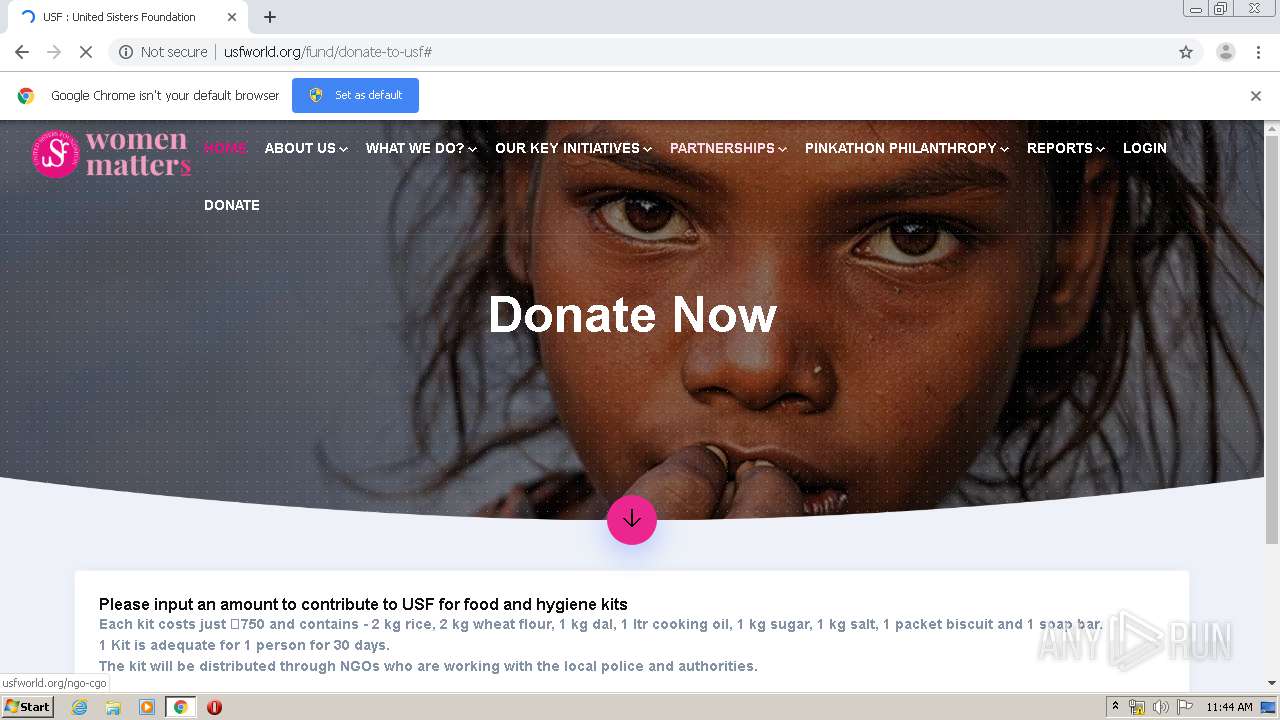
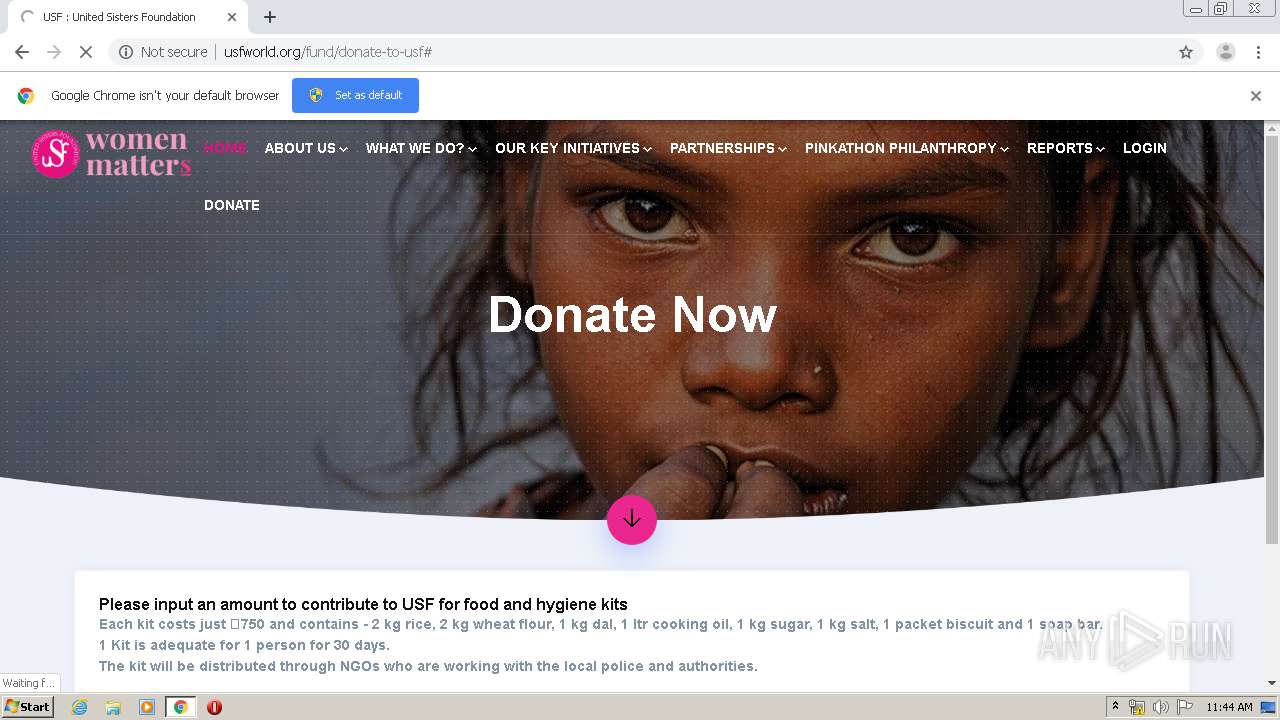
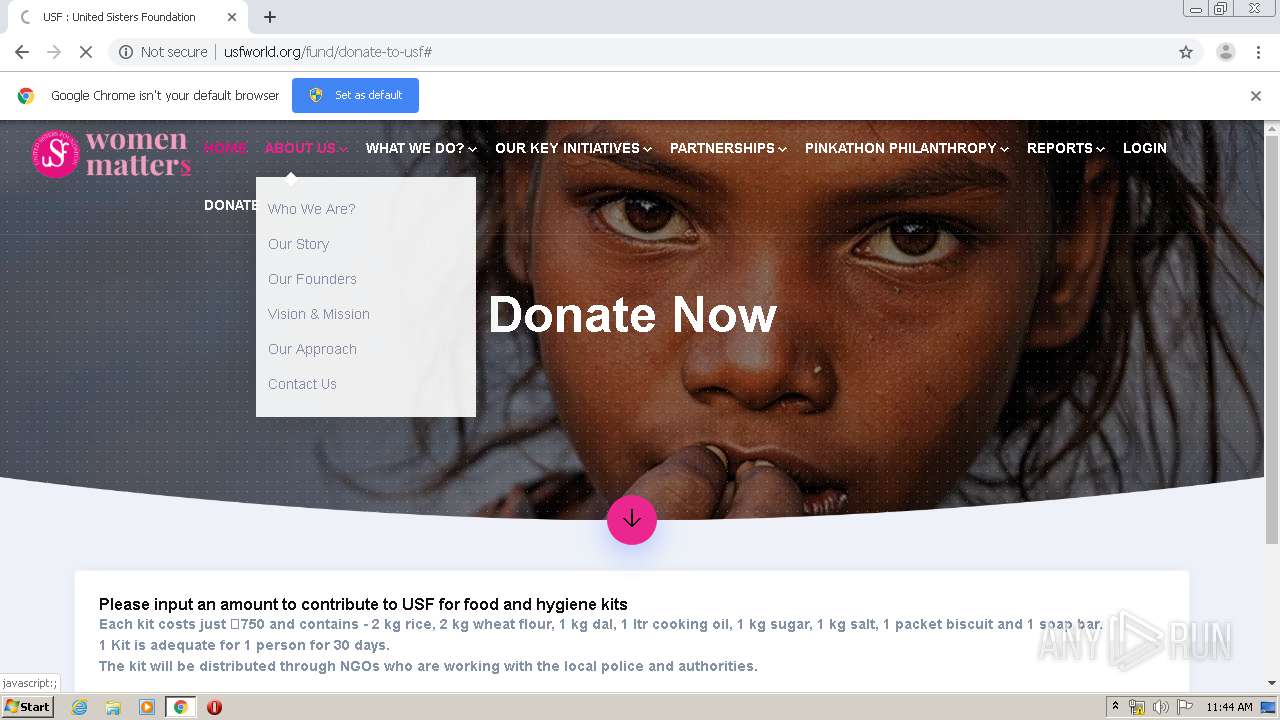
3880 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/donate-to-usf | US | html | 5.41 Kb | suspicious |
3880 | chrome.exe | GET | 200 | 104.16.230.163:80 | http://r.pinkathonmail.com/mk/cl/f/Jk5-JuPUc5TrclIFhrcDRMP9EYH9rzoIgZHJ6KT2hBYzNrIP4fOh6p1pp81lLkoSgRkDUjOrKmDVAkqHKeXKgGLqEQKjcg5kGhg3HpkJZrkg7NTWxpf83AXflI89GP4ad-U2Tp2g6LUxNSEg-X_BaXaD_BZdsNJo7kJReAP0wmeIIlEtxw | US | html | 391 b | suspicious |
3880 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/css/typography.css | US | text | 3.84 Kb | suspicious |
3880 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/css/color/color-1.css | US | text | 1.18 Kb | suspicious |
3880 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/vendors/jquery-steps/jquery.steps.css | US | text | 1.23 Kb | suspicious |
3880 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/css/assets.css | US | text | 200 b | suspicious |
3880 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/css/style.css | US | text | 28.2 Kb | suspicious |
3880 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/vendors/dropify/dist/dropify.min.css | US | text | 1.98 Kb | suspicious |
3880 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/vendors/core/core.css | US | text | 655 b | suspicious |
3880 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/vendors/revolution/css/layers.css | US | text | 10.4 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3880 | chrome.exe | 172.217.23.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 173.194.151.74:80 | r4---sn-4g5e6nes.gvt1.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 104.16.230.163:80 | r.pinkathonmail.com | Cloudflare Inc | US | shared |
3880 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 185.107.232.249:443 | in-automate.sendinblue.com | Sendinblue SAS | FR | unknown |
3880 | chrome.exe | 104.28.5.90:443 | sibautomation.com | Cloudflare Inc | US | unknown |
3880 | chrome.exe | 148.72.201.193:80 | usfworld.org | — | US | suspicious |
3880 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 216.58.207.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3880 | chrome.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
r.pinkathonmail.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sibautomation.com |
| whitelisted |
in-automate.sendinblue.com |
| whitelisted |
usfworld.org |
| suspicious |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
twitter.com |
| whitelisted |
www.facebook.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3880 | chrome.exe | Potentially Bad Traffic | ET HUNTING Suspicious GET Request with Possible COVID-19 URI M1 |