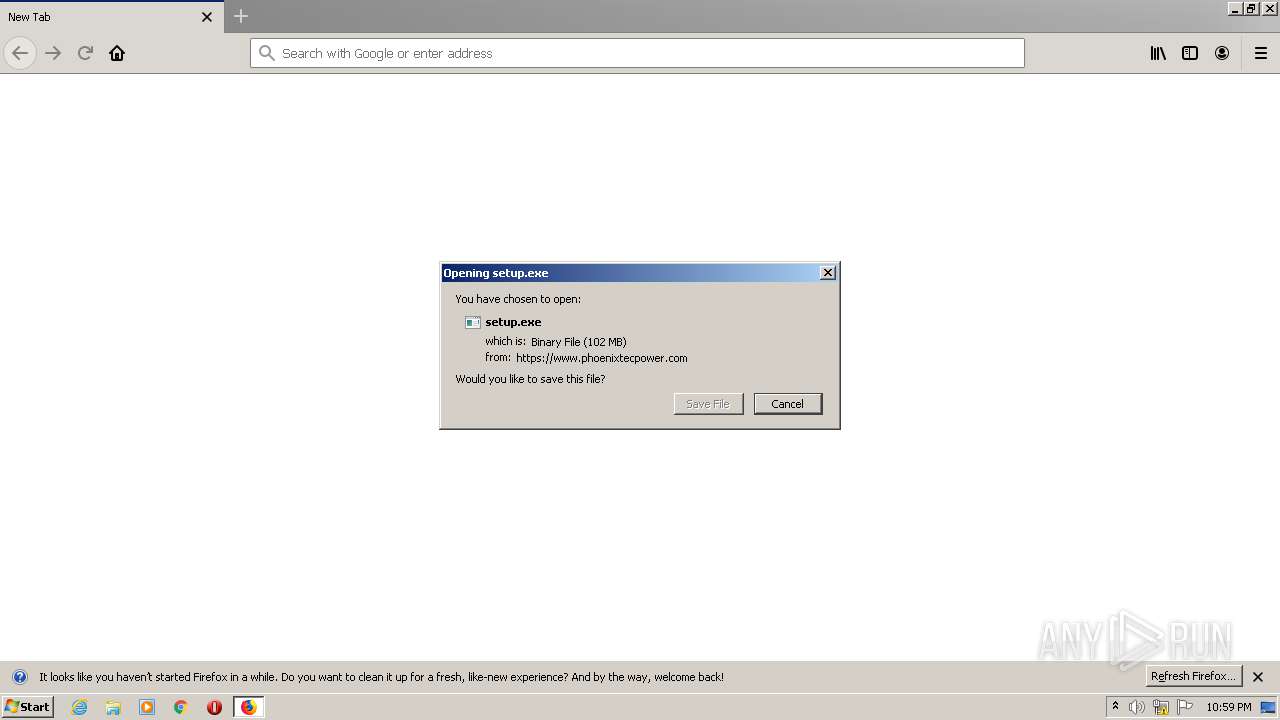
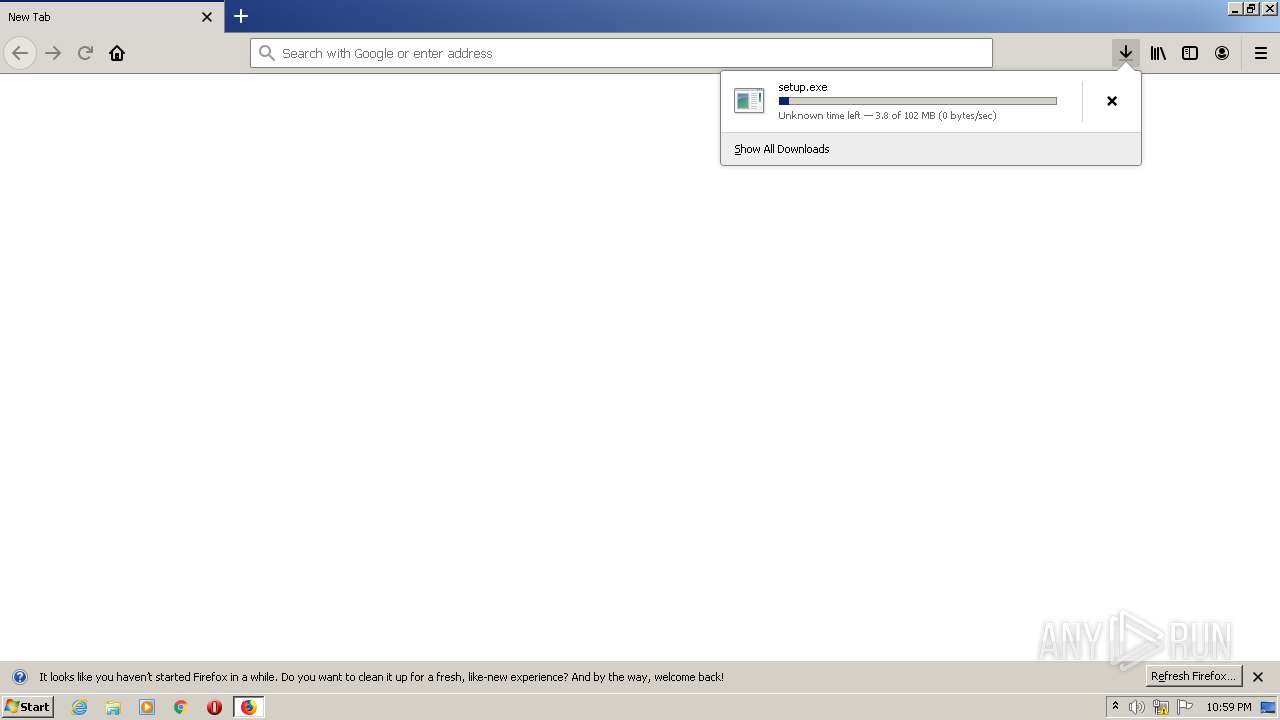
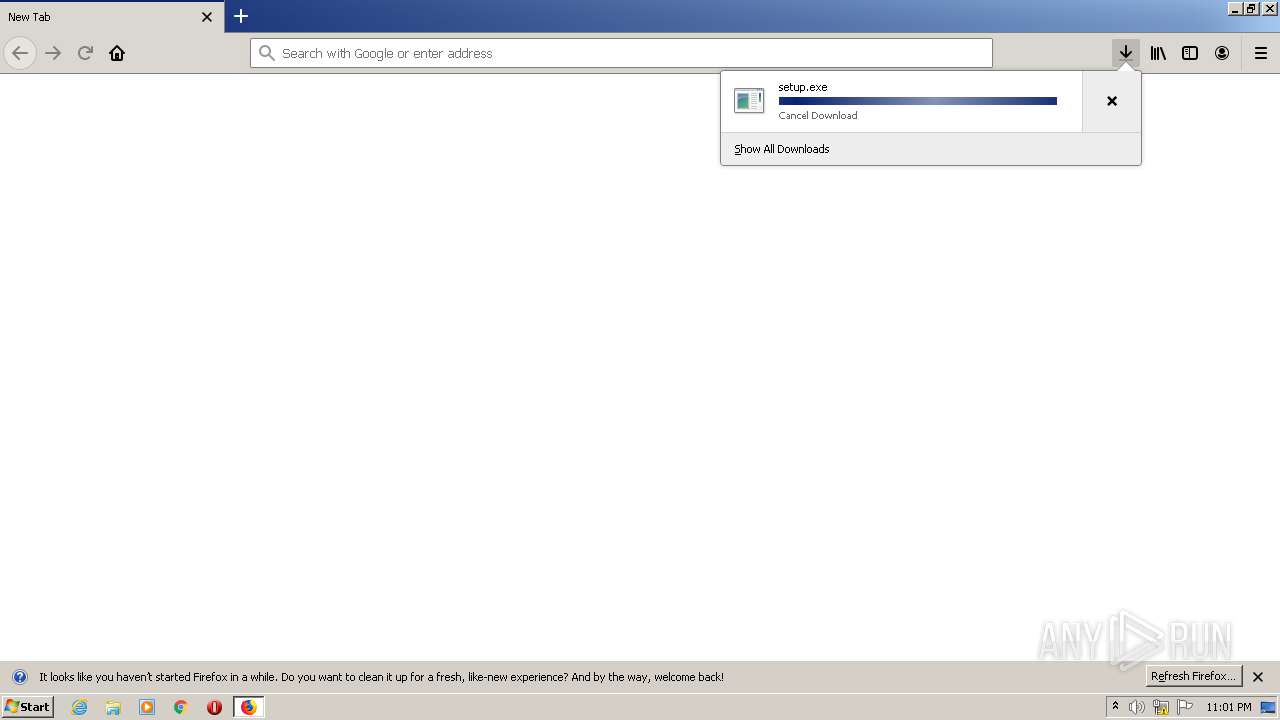
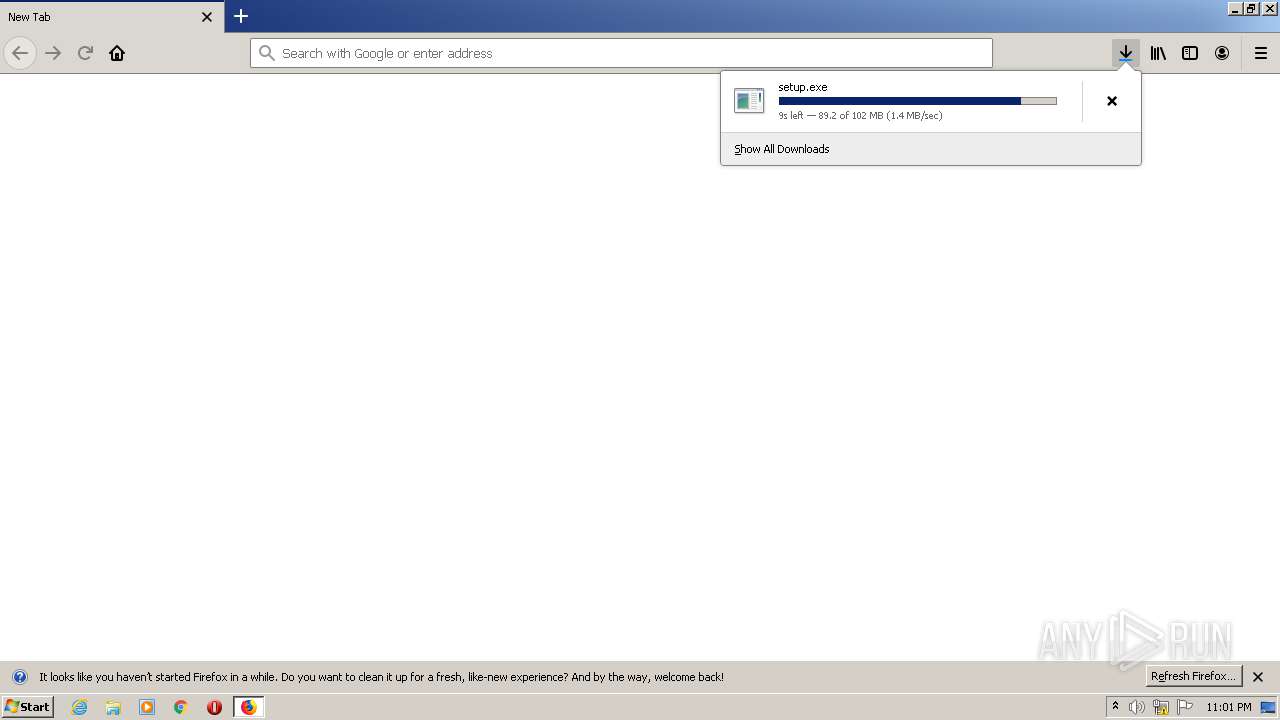
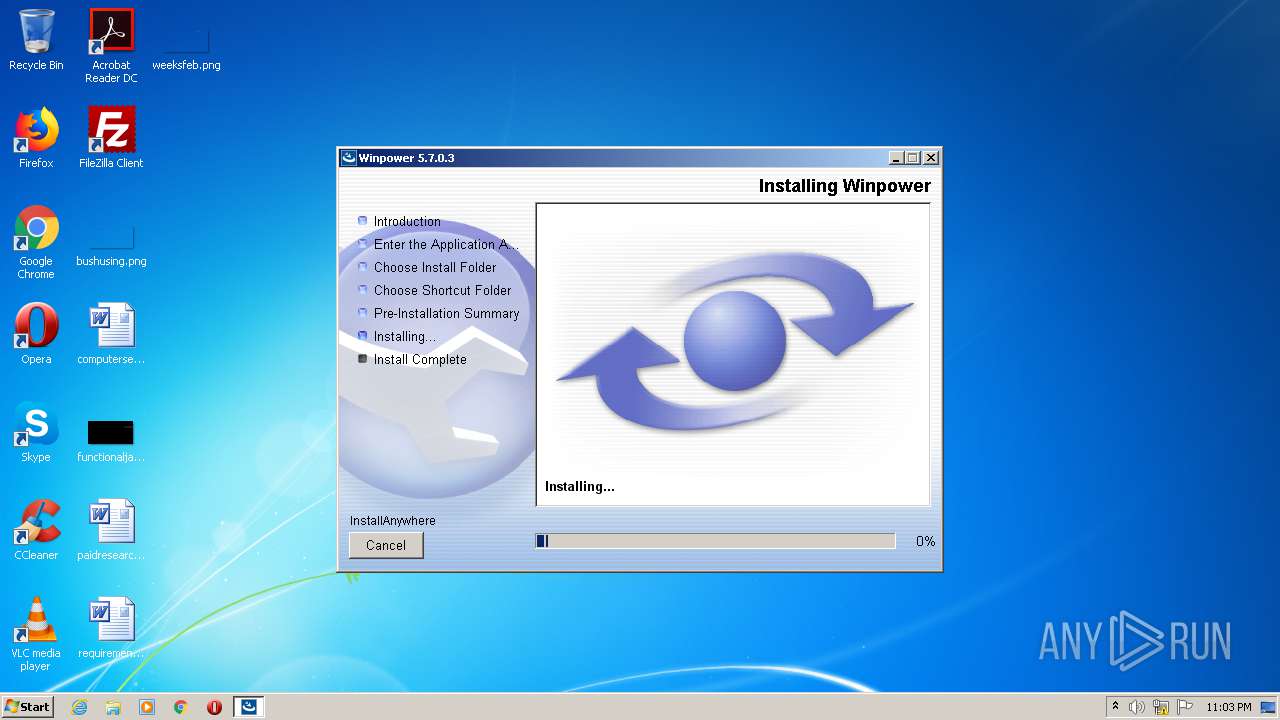
| URL: | https://www.phoenixtecpower.com/content/dam/phoenixtec/sw---fw/winpower_setup_windows/setup.exe |
| Full analysis: | https://app.any.run/tasks/66afcab9-e83f-4df7-b564-adb309262c4e |
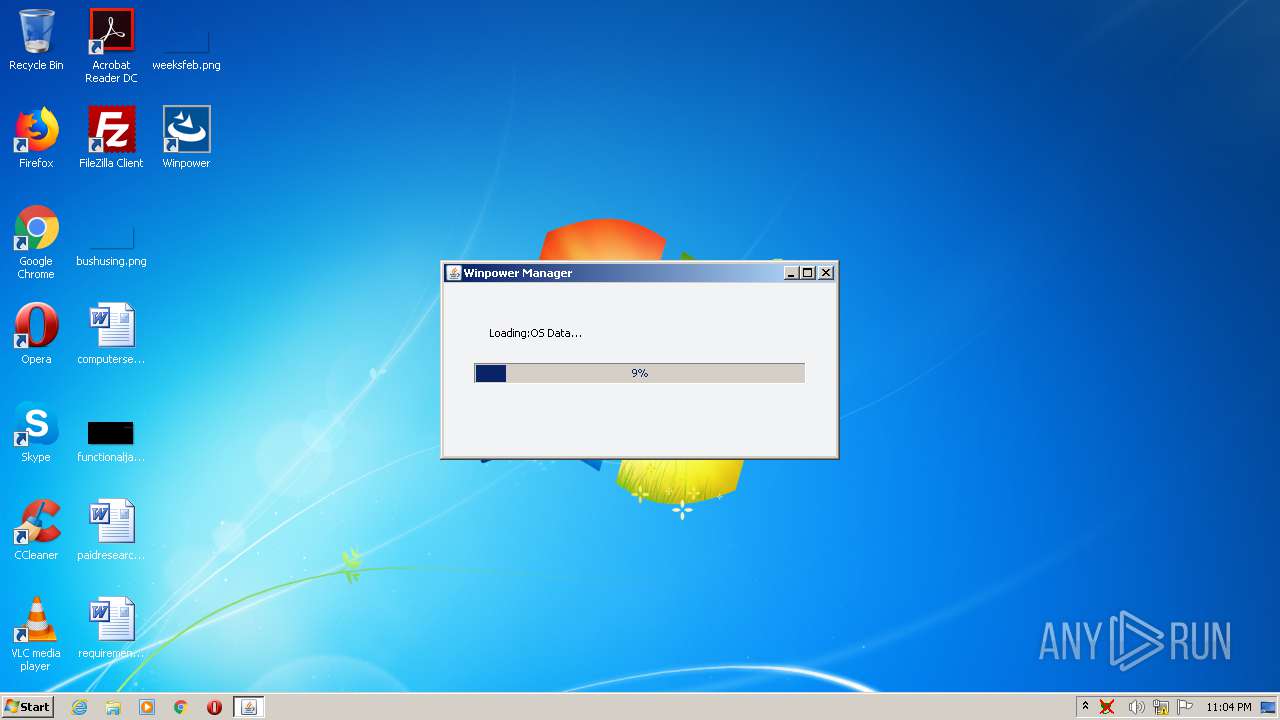
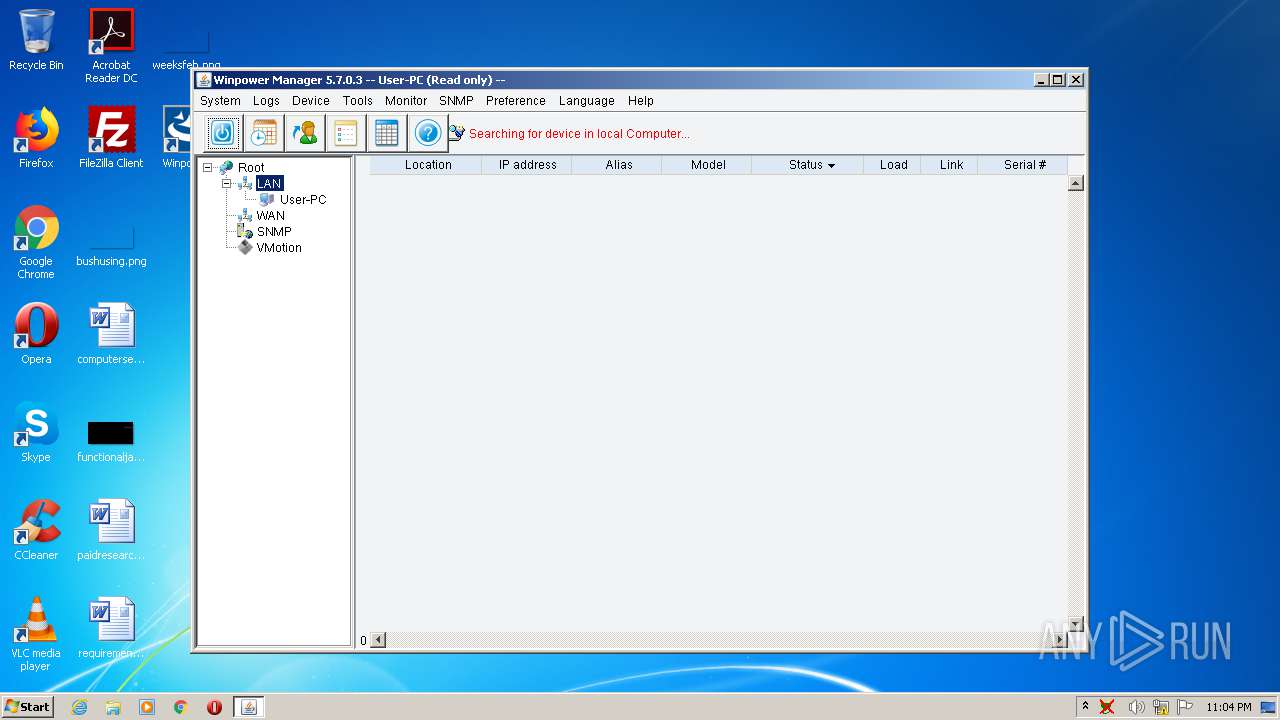
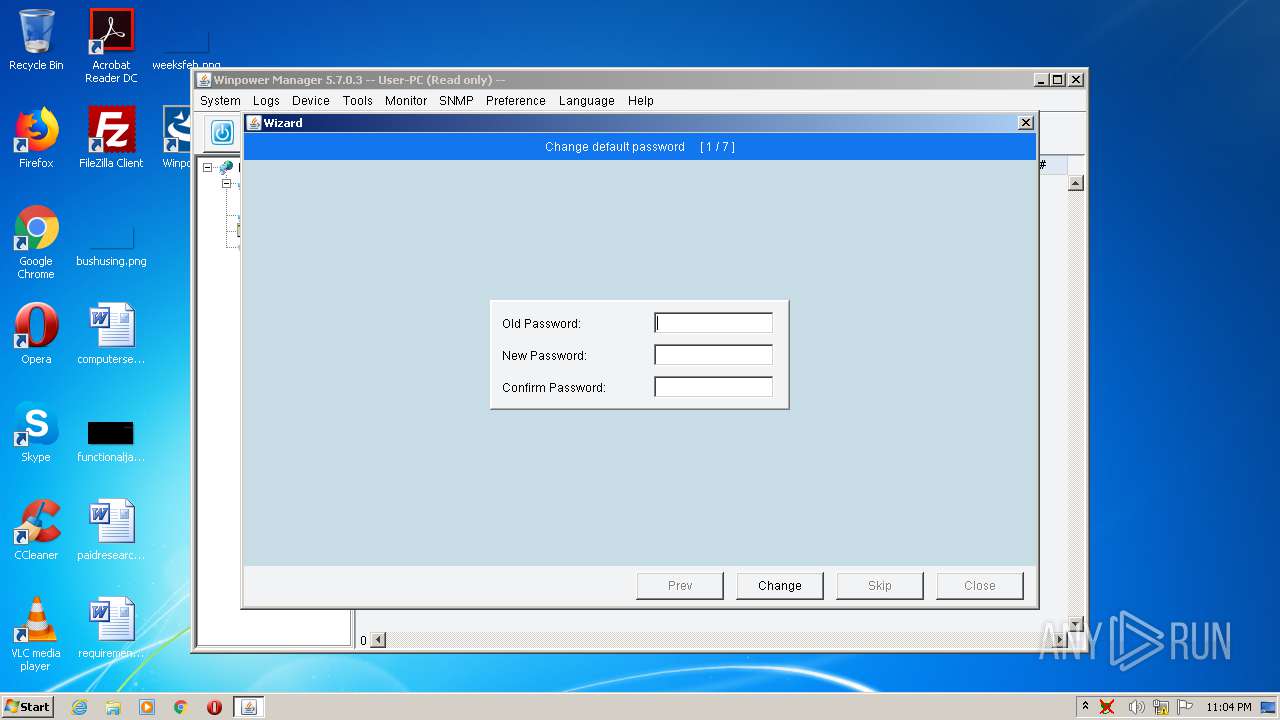
| Verdict: | Malicious activity |
| Analysis date: | October 08, 2020, 21:59:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A9D29C625C4B64F175AFCBD2B6F8C7C3 |
| SHA1: | 54B315A4451ADE4E748B3F7C598F43D256A0DCB2 |
| SHA256: | C45DCEFD4F3754F67476FFD4A6182A6FED9D1148993C4D613B4C3428217D0E03 |
| SSDEEP: | 3:N8DSLbLFxisL8syIivMMdWJlDzf/LwAyL4A:2OLbLFxiqjiNdWPLw7L4A |
MALICIOUS
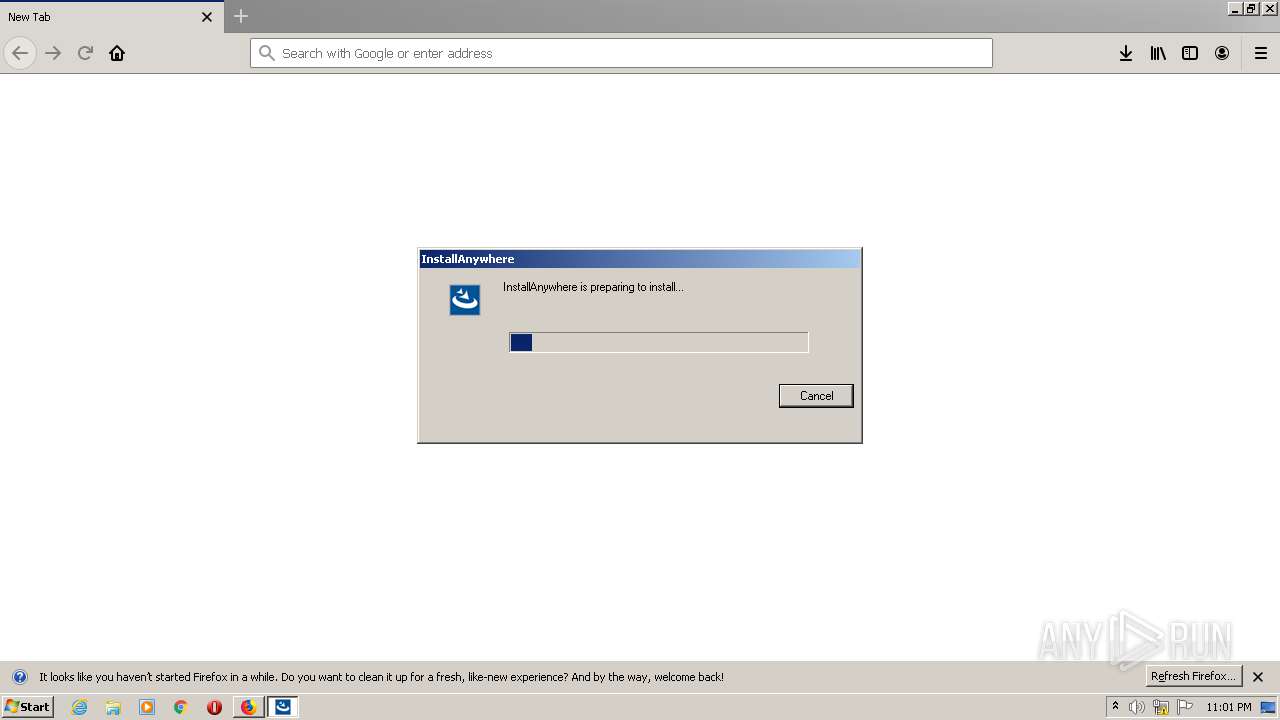
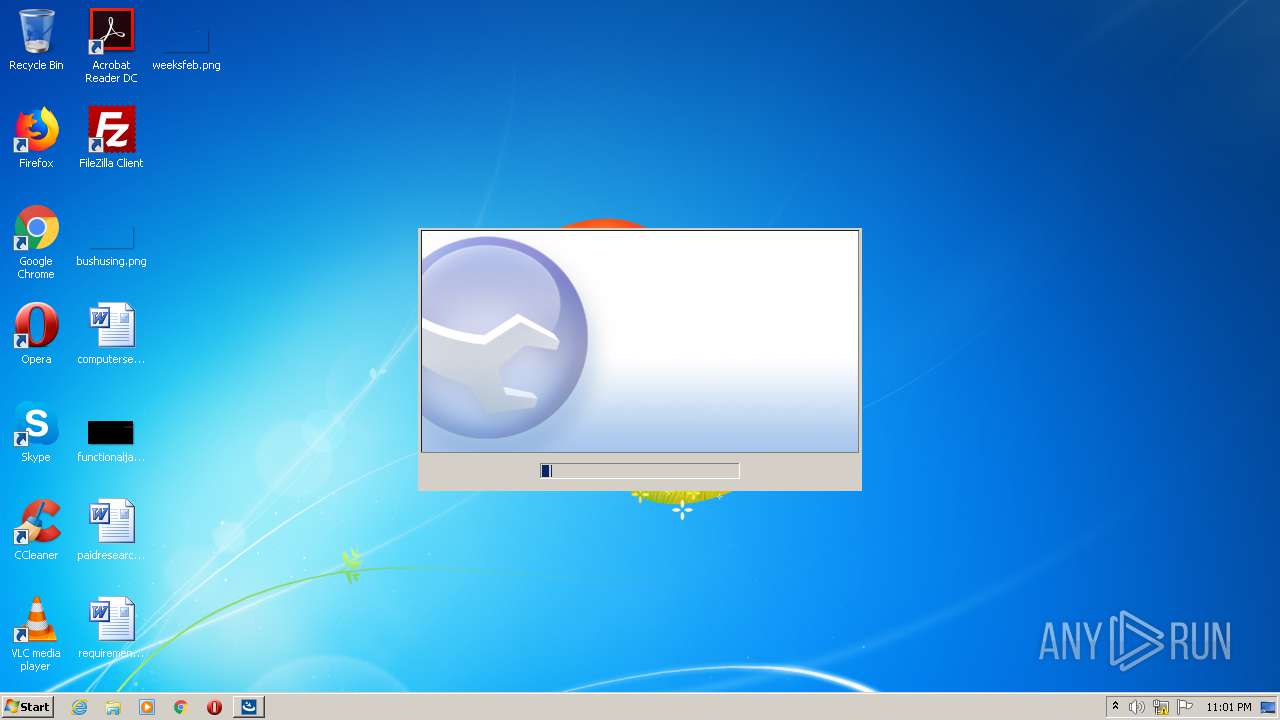
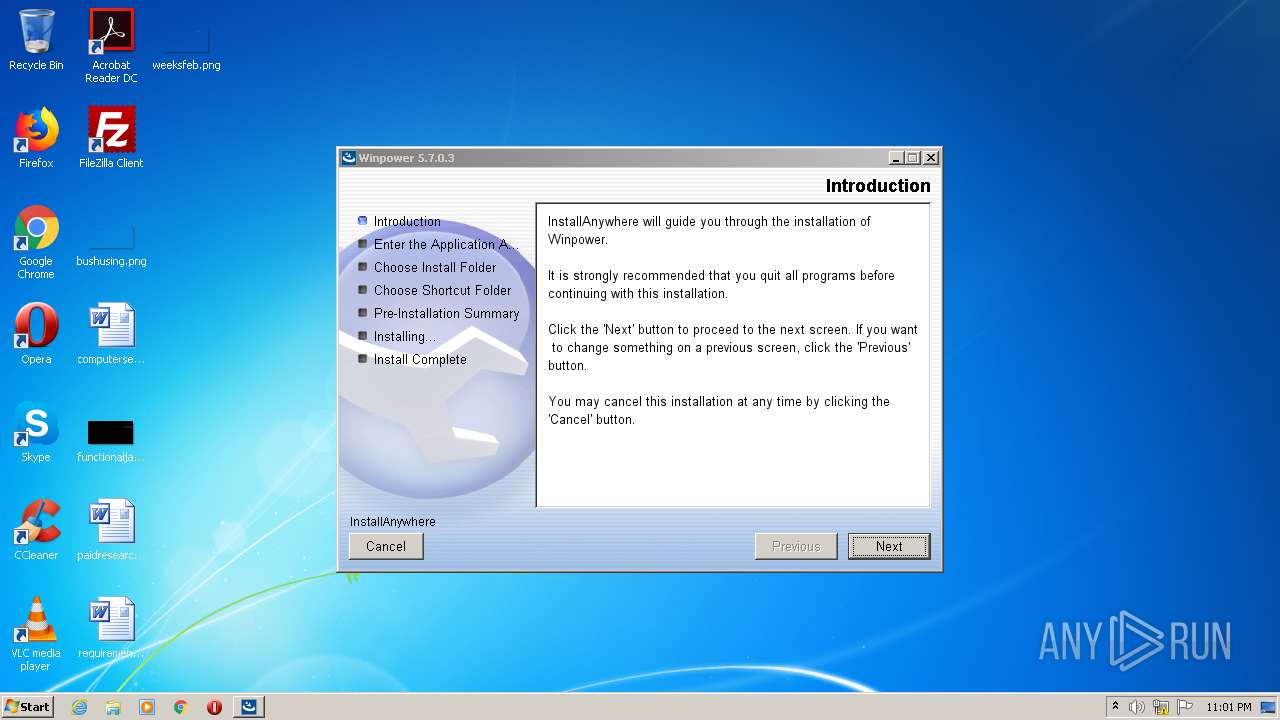
Application was dropped or rewritten from another process
- setup.exe (PID: 3552)
- setup.exe (PID: 1788)
- setup.exe (PID: 3408)
- javaw.exe (PID: 4024)
- ZGWin32LaunchHelper.exe (PID: 1348)
- ZGWin32LaunchHelper.exe (PID: 2964)
- javaw.exe (PID: 2992)
- javaw.exe (PID: 2848)
- remove.exe (PID: 3852)
- javaw.exe (PID: 4072)
- javaw.exe (PID: 2836)
- UPSMS.exe (PID: 2640)
- UPSMS.exe (PID: 1072)
- manager.exe (PID: 3984)
- monitor.exe (PID: 2868)
Actions looks like stealing of personal data
- setup.exe (PID: 3408)
Loads dropped or rewritten executable
- javaw.exe (PID: 4024)
- setup.exe (PID: 1788)
- javaw.exe (PID: 2992)
- UPSMS.exe (PID: 2640)
- javaw.exe (PID: 2848)
- monitor.exe (PID: 2868)
- UPSMS.exe (PID: 1072)
- javaw.exe (PID: 4072)
- javaw.exe (PID: 2836)
- manager.exe (PID: 3984)
Changes the autorun value in the registry
- javaw.exe (PID: 4024)
Starts NET.EXE for service management
- javaw.exe (PID: 4024)
SUSPICIOUS
Executable content was dropped or overwritten
- firefox.exe (PID: 1724)
- setup.exe (PID: 3408)
- javaw.exe (PID: 4024)
Uses ATTRIB.EXE to modify file attributes
- javaw.exe (PID: 4024)
Creates files in the program directory
- firefox.exe (PID: 1724)
- javaw.exe (PID: 4024)
- javaw.exe (PID: 2992)
- javaw.exe (PID: 2848)
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 4024)
Uses WMIC.EXE to obtain a system information
- javaw.exe (PID: 4024)
Creates files in the user directory
- javaw.exe (PID: 4024)
- powershell.exe (PID: 2440)
Executes JAVA applets
- javaw.exe (PID: 4024)
Starts SC.EXE for service management
- ZGWin32LaunchHelper.exe (PID: 1348)
- ZGWin32LaunchHelper.exe (PID: 2964)
- javaw.exe (PID: 4024)
- powershell.exe (PID: 2440)
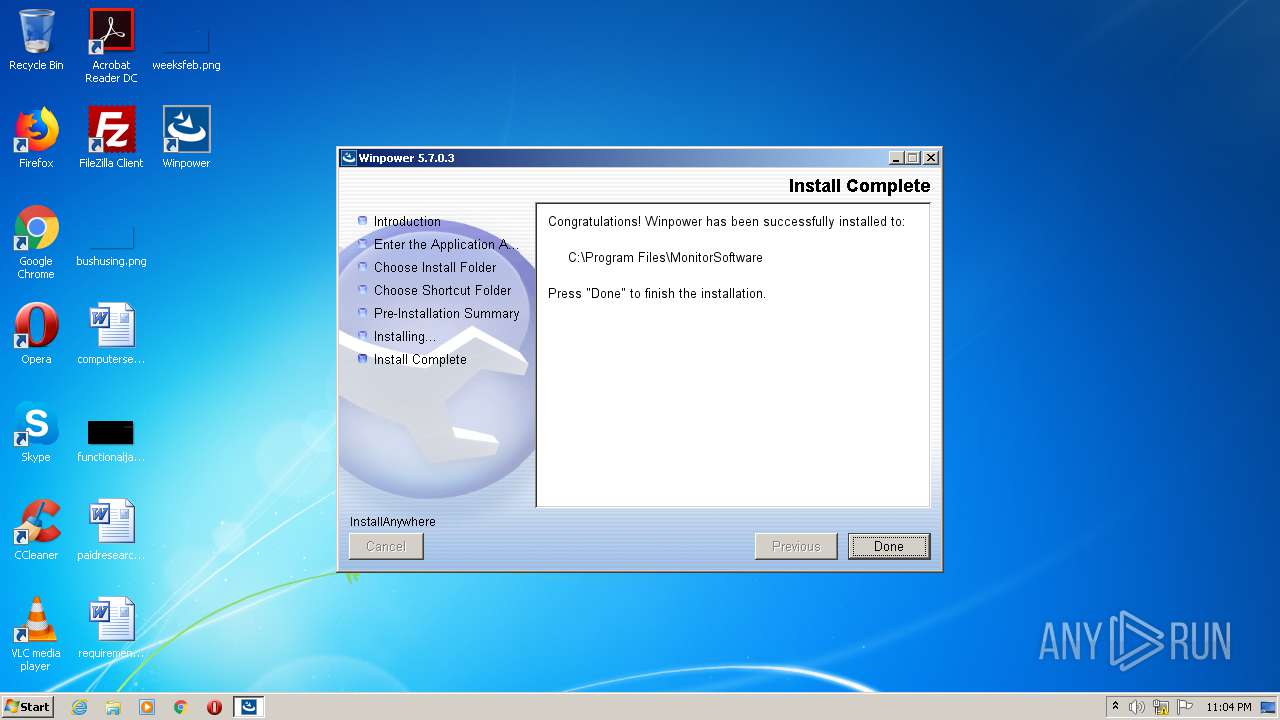
Creates a software uninstall entry
- javaw.exe (PID: 4024)
Creates files in the Windows directory
- javaw.exe (PID: 4024)
- monitor.exe (PID: 2868)
- javaw.exe (PID: 2848)
Executed as Windows Service
- monitor.exe (PID: 2868)
Removes files from Windows directory
- javaw.exe (PID: 2848)
Executes PowerShell scripts
- javaw.exe (PID: 2992)
INFO
Application launched itself
- firefox.exe (PID: 2688)
- firefox.exe (PID: 1724)
Reads CPU info
- firefox.exe (PID: 1724)
Reads Internet Cache Settings
- firefox.exe (PID: 1724)
- pingsender.exe (PID: 3324)
- pingsender.exe (PID: 3204)
Adds / modifies Windows certificates
- pingsender.exe (PID: 3204)
- pingsender.exe (PID: 3324)
Changes settings of System certificates
- pingsender.exe (PID: 3204)
- pingsender.exe (PID: 3324)
Creates files in the user directory
- firefox.exe (PID: 1724)
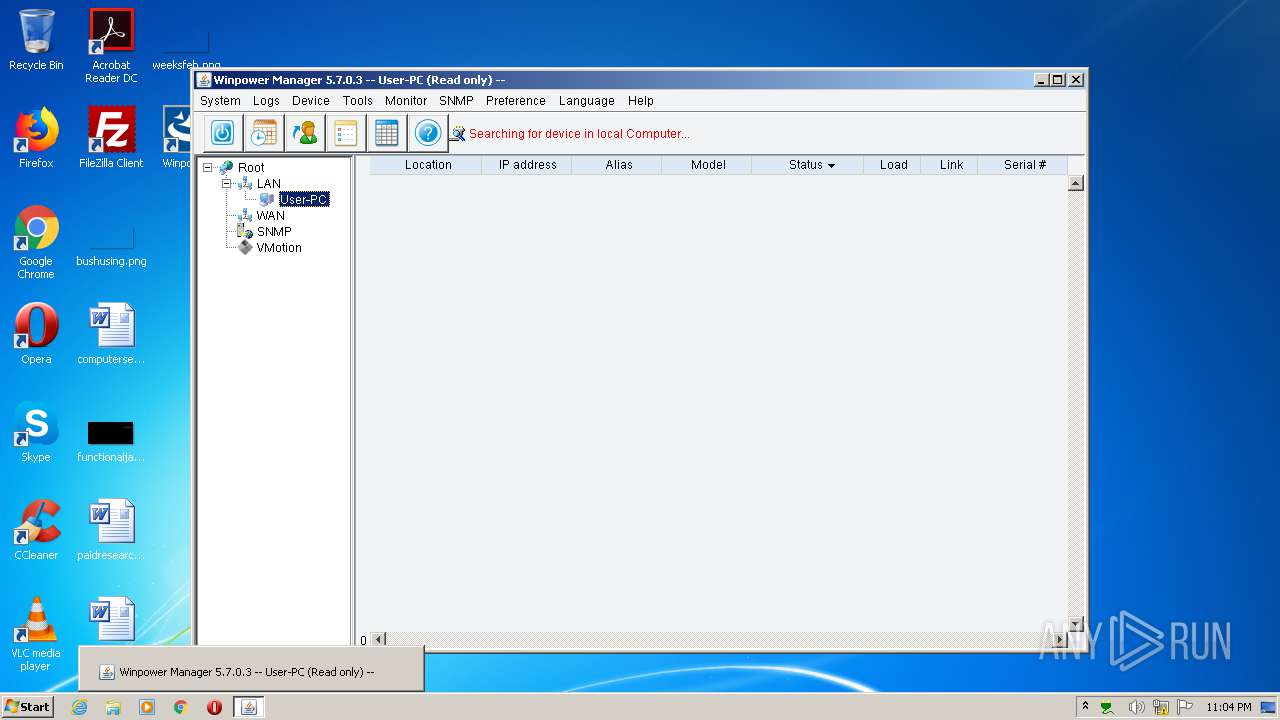
Manual execution by user
- UPSMS.exe (PID: 1072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
43
Malicious processes
12
Suspicious processes
1
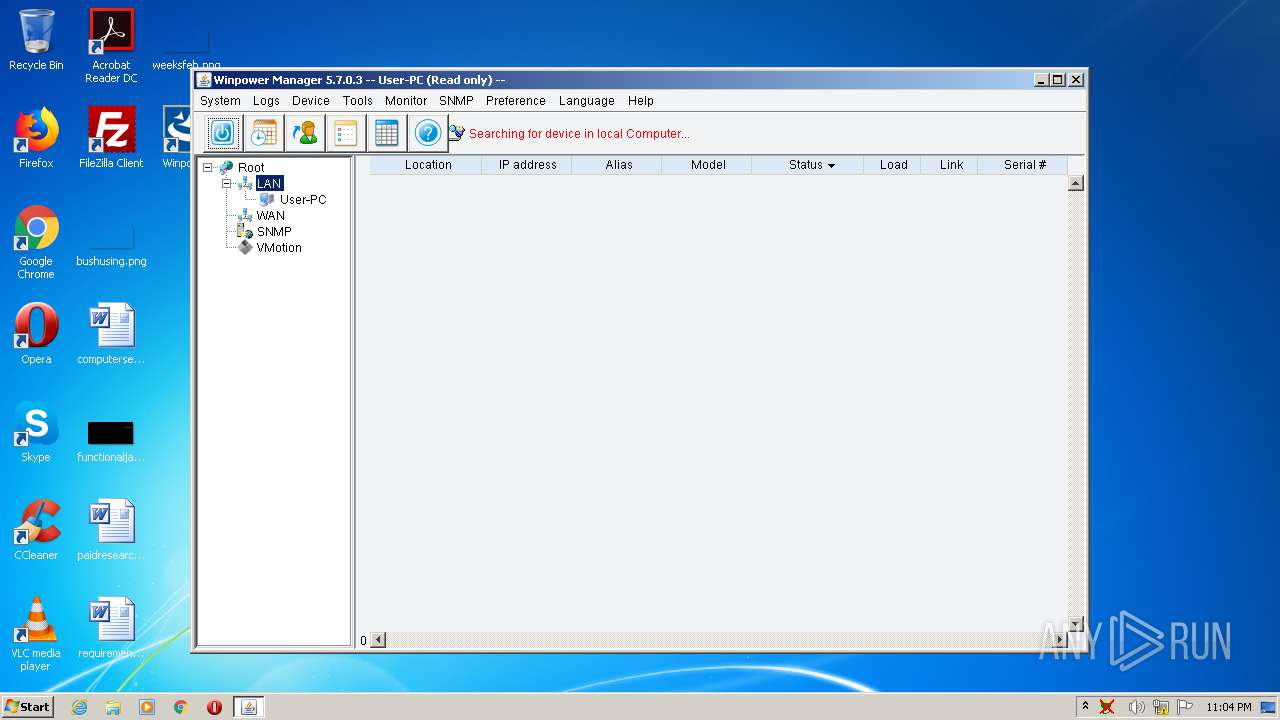
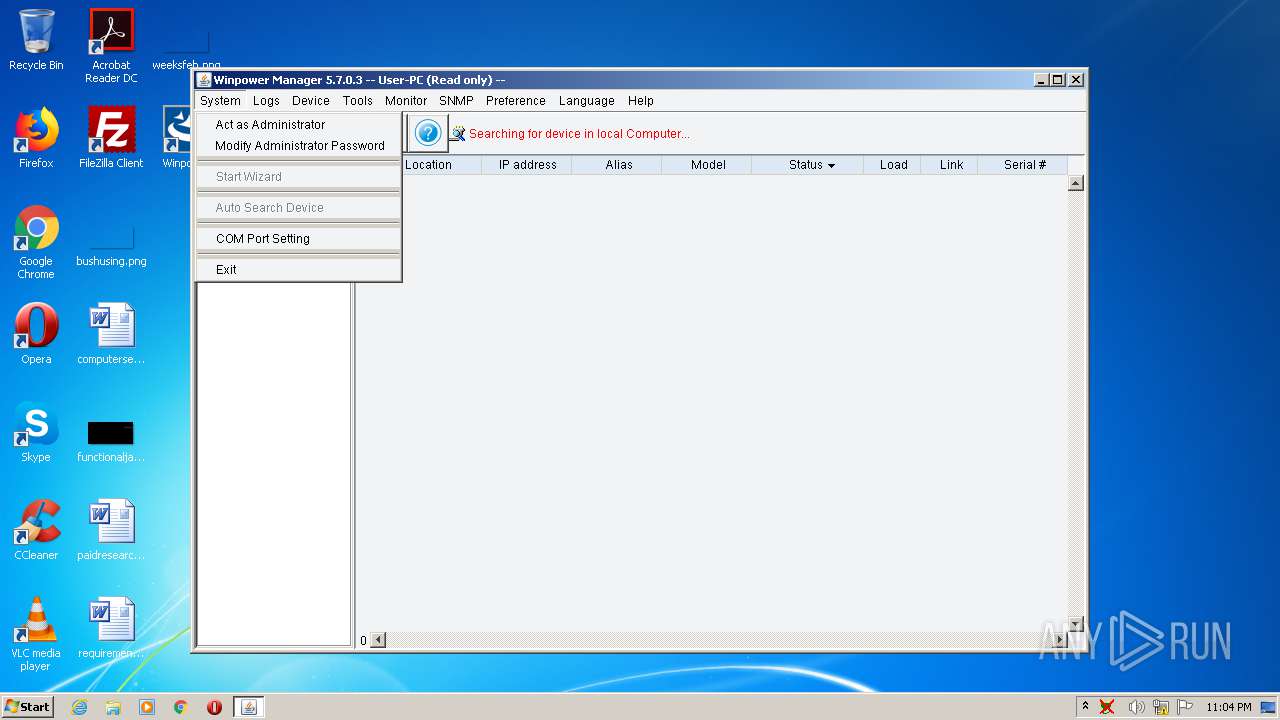
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | sc.exe create UPSmonitor DisplayName= UPSmonitor start= auto type= own binPath= "C:\PROGRA~1\MONITO~1\monitor.exe -zglaxservice UPSmonitor" | C:\Windows\system32\sc.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
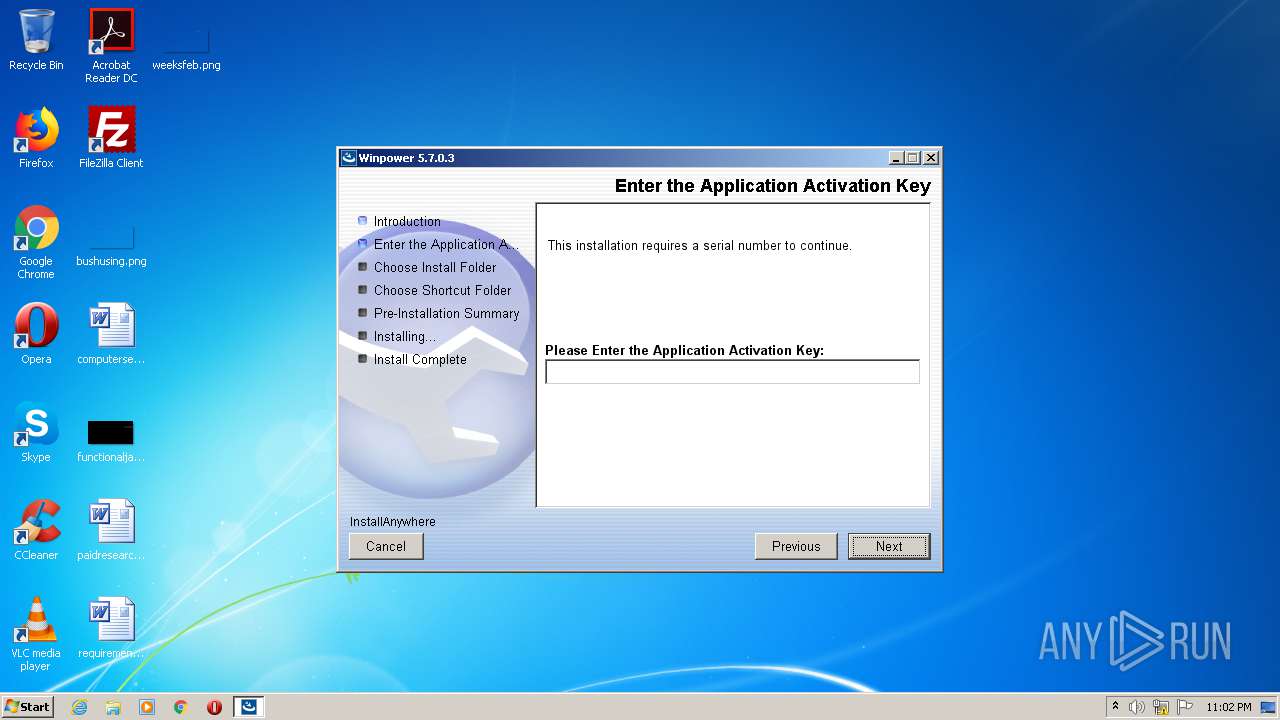
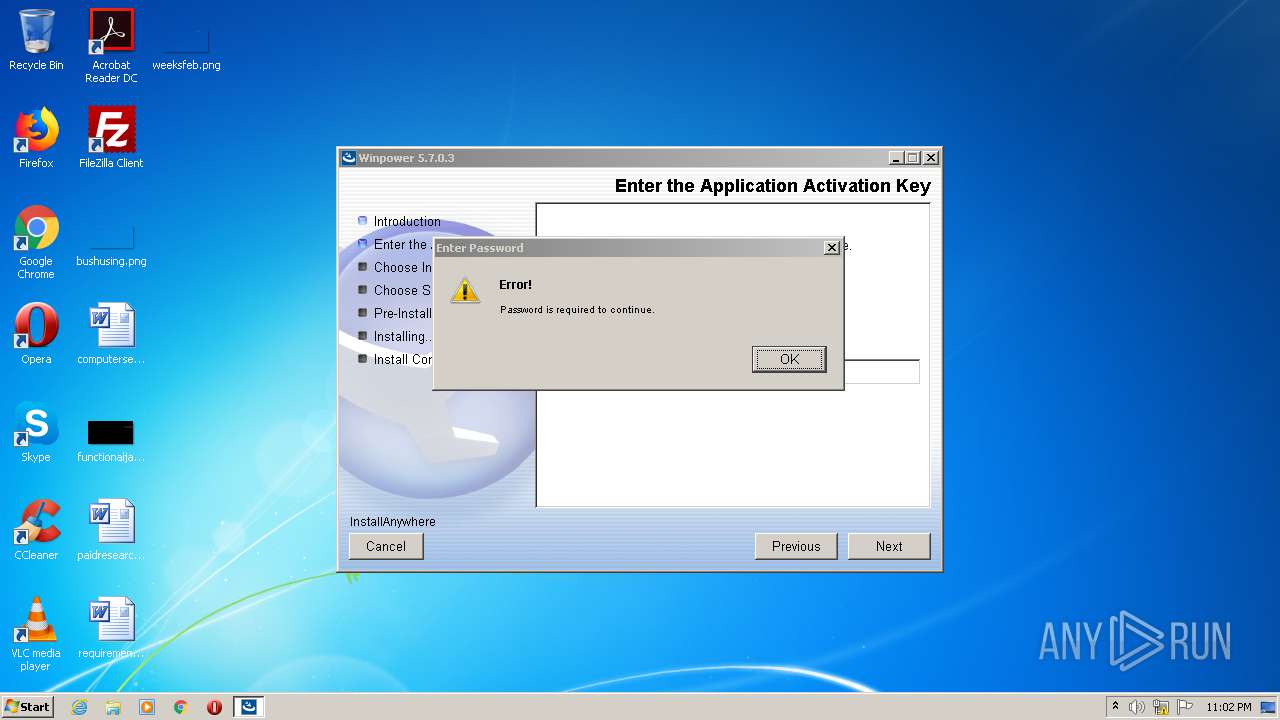
| 1072 | "C:\Program Files\MonitorSoftware\UPSMS.exe" | C:\Program Files\MonitorSoftware\UPSMS.exe | — | explorer.exe | |||||||||||
User: admin Company: Santak Integrity Level: MEDIUM Description: LaunchAnywhere Exit code: 0 Version: 5.7.0.3 Modules
| |||||||||||||||
| 1348 | C:\Users\admin\AppData\Local\Temp\I1602194502\Windows\resource\ZGWin32LaunchHelper.exe sc.exe delete UPSmonitor | C:\Users\admin\AppData\Local\Temp\I1602194502\Windows\resource\ZGWin32LaunchHelper.exe | — | javaw.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1724.13.713112147\1892474117" -childID 2 -isForBrowser -prefsHandle 2948 -prefMapHandle 2952 -prefsLen 5996 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1724 "\\.\pipe\gecko-crash-server-pipe.1724" 2968 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://www.phoenixtecpower.com/content/dam/phoenixtec/sw---fw/winpower_setup_windows/setup.exe | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1748 | ie4uinit.exe -ClearIconCache | C:\Windows\system32\ie4uinit.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1788 | C:\Users\admin\AppData\Local\Temp\I1602194502\Windows\setup.exe | C:\Users\admin\AppData\Local\Temp\I1602194502\Windows\setup.exe | — | setup.exe | |||||||||||
User: admin Company: Flexera Software Integrity Level: HIGH Description: LaunchAnywhere Exit code: 0 Version: 19, 0, 0, 0 Modules
| |||||||||||||||
| 2068 | wmic os get version | C:\Windows\System32\Wbem\wmic.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2148 | sc.exe delete UPSmonitor | C:\Windows\system32\sc.exe | — | ZGWin32LaunchHelper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | wmic os get name | C:\Windows\System32\Wbem\wmic.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 325
Read events
1 062
Write events
191
Delete events
72
Modification events
| (PID) Process: | (1724) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: F9FF124B00000000 | |||
| (PID) Process: | (2688) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: E2FF124B00000000 | |||
| (PID) Process: | (1724) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (1724) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1724) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1724) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1724) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4024) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (3324) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3324) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
362
Suspicious files
182
Text files
557
Unknown types
94
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1724 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1724 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 1724 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 1724 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 1724 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 1724 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 1724 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 1724 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\54B9FDC469C596FE1C5630E45D75CDD46AB42FAD | der | |
MD5:— | SHA256:— | |||
| 1724 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flashallow-digest256.pset | — | |
MD5:— | SHA256:— | |||
| 1724 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\except-flashallow-digest256.sbstore | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
38
DNS requests
82
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3204 | pingsender.exe | GET | — | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAzmtf2PsbB81NVMrv5Nv1c%3D | US | — | — | whitelisted |
3204 | pingsender.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1724 | firefox.exe | POST | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com/ | US | der | 1.74 Kb | whitelisted |
1724 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
1724 | firefox.exe | POST | 200 | 216.58.212.163:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
1724 | firefox.exe | POST | 200 | 192.124.249.22:80 | http://ocsp.godaddy.com/ | US | der | 1.74 Kb | whitelisted |
1052 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTzEBwbi4EtIEVqKGq%2FDeuw3LZDrAQU%2BCXZpjnHw4GHJT4wVJEYIUCbF50CEAGlbicmfJ%2B9cwizLdCwXcY%3D | US | binary | 5 b | whitelisted |
3324 | pingsender.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1724 | firefox.exe | 104.109.86.102:443 | www.phoenixtecpower.com | Akamai International B.V. | NL | unknown |
1724 | firefox.exe | 192.124.249.22:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
1724 | firefox.exe | 35.161.199.137:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1724 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1724 | firefox.exe | 216.58.210.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1724 | firefox.exe | 216.58.212.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1724 | firefox.exe | 54.186.45.50:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
1724 | firefox.exe | 13.225.238.111:443 | tracking-protection.cdn.mozilla.net | — | US | unknown |
1724 | firefox.exe | 13.225.238.52:443 | snippets.cdn.mozilla.net | — | US | unknown |
1724 | firefox.exe | 2.16.177.88:80 | detectportal.firefox.com | Akamai International B.V. | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.phoenixtecpower.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
e14486.dsca.akamaiedge.net |
| unknown |
ocsp.godaddy.com |
| whitelisted |
ocsp.godaddy.com.akadns.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |