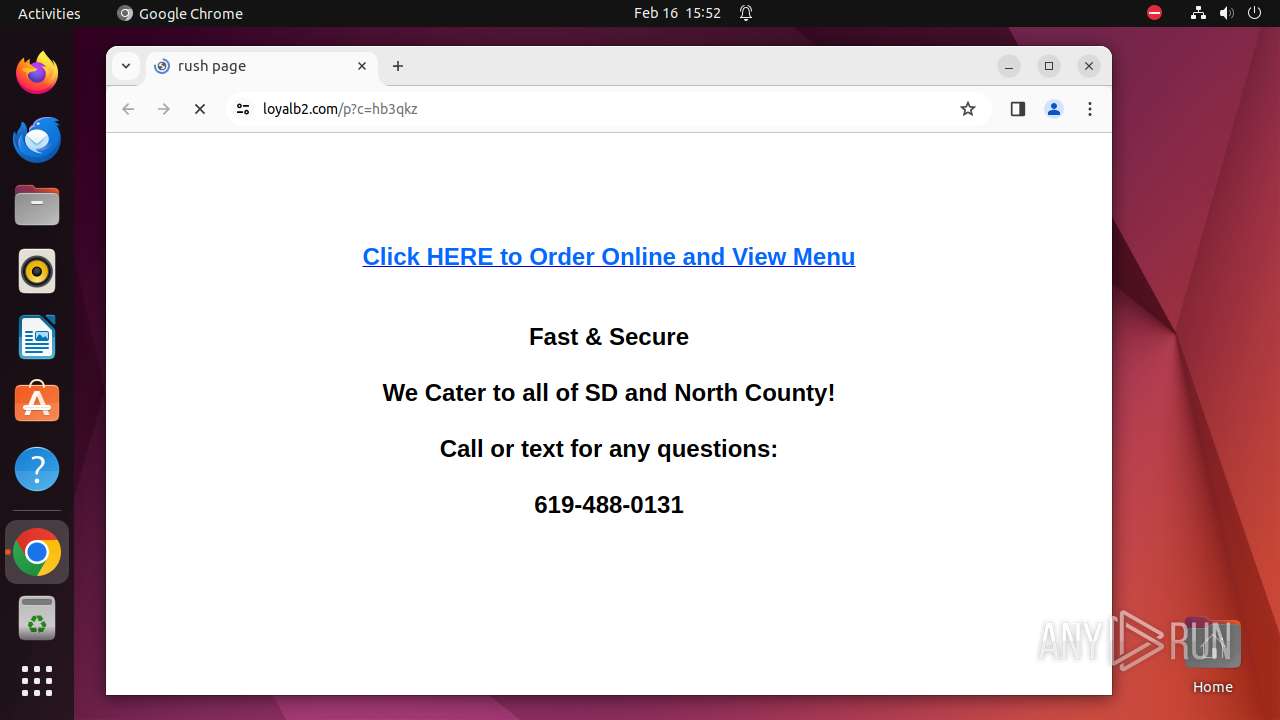
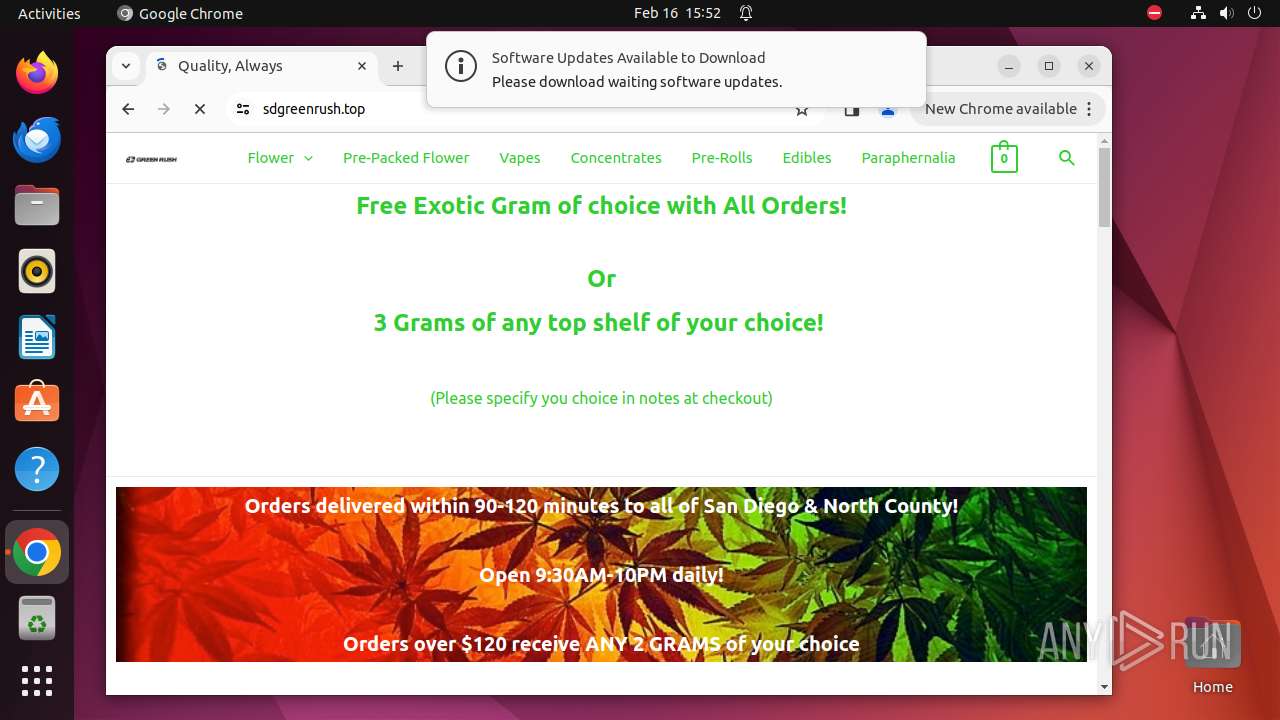
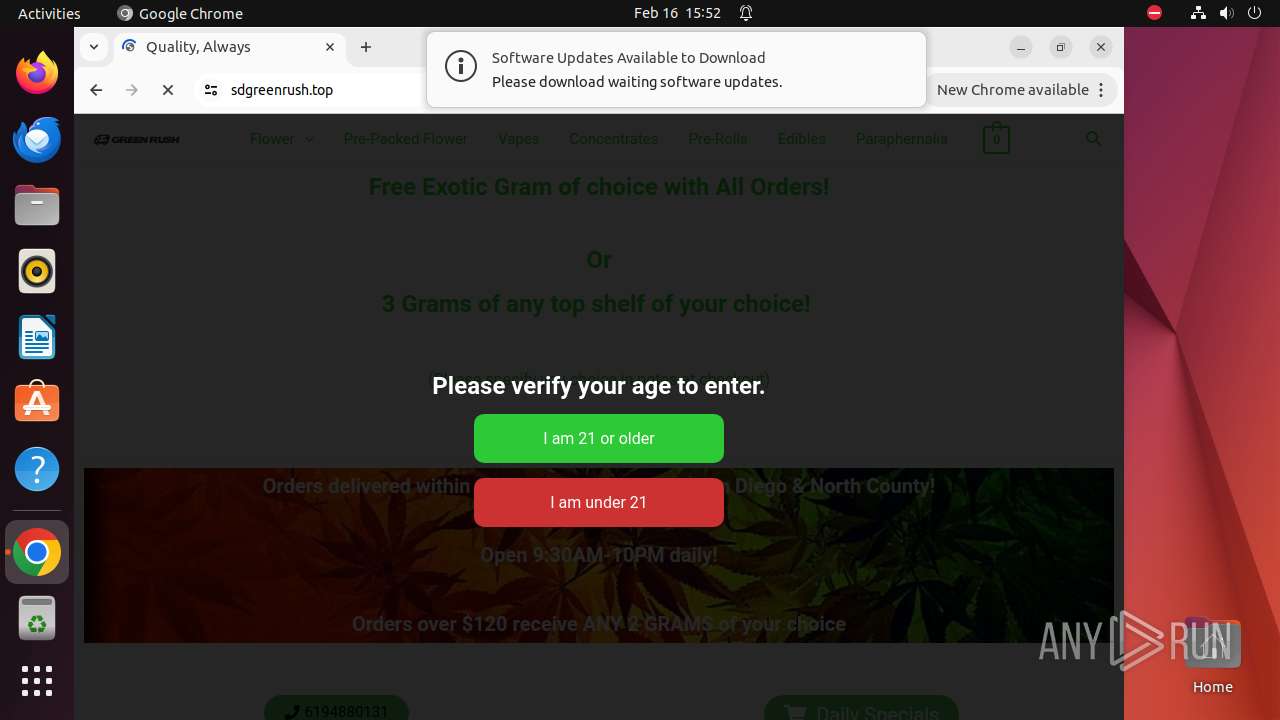
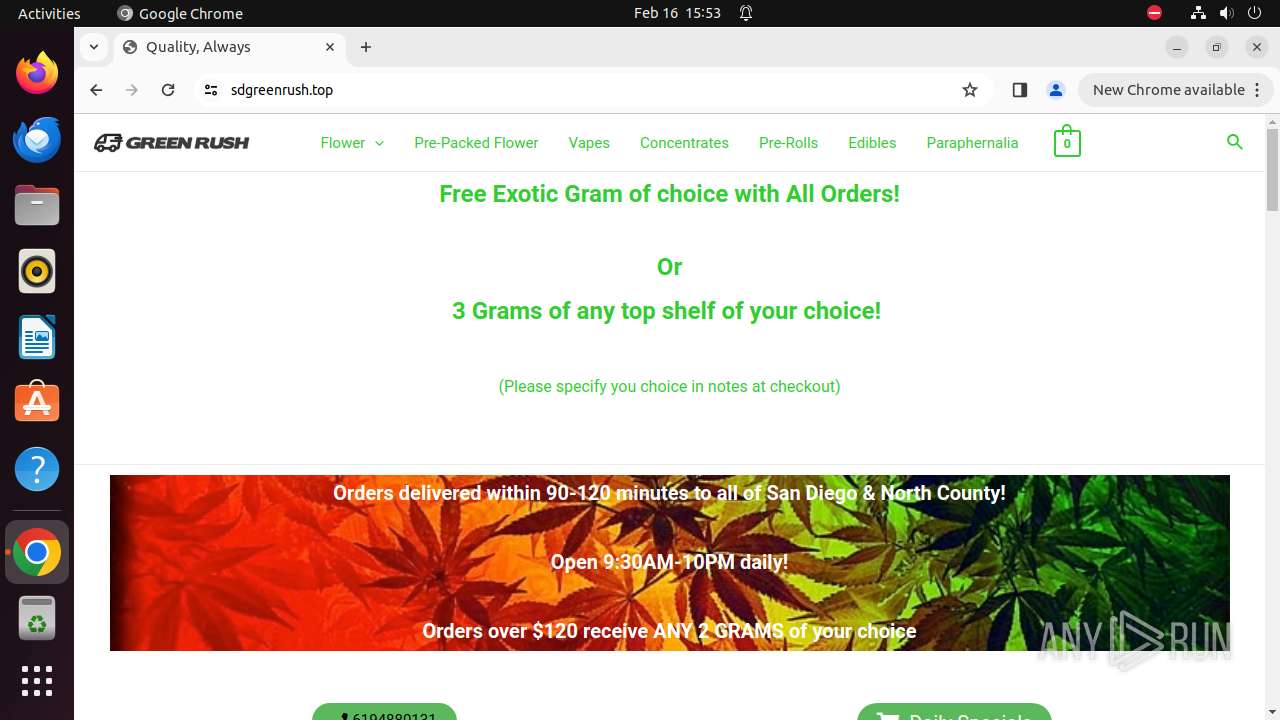
| URL: | https://rebrand.ly/qv4z |
| Full analysis: | https://app.any.run/tasks/ab32e8a4-d50a-4657-a350-dd28e3a505b4 |
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2024, 15:52:35 |
| OS: | Ubuntu 22.04.2 |
| MD5: | DBA5989E5F96604EB3FCF95ADBCB3635 |
| SHA1: | 983CD3E8A96D6FDBFDA0B2A617512ED206CF2B46 |
| SHA256: | C45BCEDB3B4F5EC4811D3AA947A8BAC5275771A8A4FC2228364725D0AA187E60 |
| SSDEEP: | 3:N8vLBLJGf:2vLBLsf |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
295
Monitored processes
77
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 7931 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome \"https://rebrand\.ly/qv4z\" " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7932 | sudo -iu user google-chrome https://rebrand.ly/qv4z | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7935 | /usr/bin/google-chrome https://rebrand.ly/qv4z | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7936 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7937 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7938 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7939 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7940 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7941 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7942 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7935 | chrome | /7935/fd/63 | — | |
MD5:— | SHA256:— | |||
| 7935 | chrome | /home/user/.config/google-chrome/BrowserMetrics/BrowserMetrics-65CF84C9-1EFF.pma | — | |
MD5:— | SHA256:— | |||
| 7935 | chrome | /home/user/.config/google-chrome/Default/parcel_tracking_db/LOG | — | |
MD5:— | SHA256:— | |||
| 7935 | chrome | /home/user/.config/google-chrome/Default/discounts_db/LOG | — | |
MD5:— | SHA256:— | |||
| 7935 | chrome | /home/user/.config/google-chrome/Default/chrome_cart_db/LOG | — | |
MD5:— | SHA256:— | |||
| 7935 | chrome | /home/user/.config/google-chrome/Default/coupon_db/LOG | — | |
MD5:— | SHA256:— | |||
| 7935 | chrome | /home/user/.config/google-chrome/Default/LOG | — | |
MD5:— | SHA256:— | |||
| 7935 | chrome | /home/user/.config/google-chrome/Default/commerce_subscription_db/LOG | — | |
MD5:— | SHA256:— | |||
| 7935 | chrome | /home/user/.config/google-chrome/Default/Local Storage/leveldb/LOG | — | |
MD5:— | SHA256:— | |||
| 7935 | chrome | /home/user/.config/google-chrome/Default/PersistentOriginTrials/LOG | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
29
DNS requests
34
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.96:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.189.91.96:80 | — | Canonical Group Limited | US | unknown |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 156.146.33.141:443 | — | Datacamp Limited | DE | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 142.250.185.99:443 | clientservices.googleapis.com | GOOGLE | US | unknown |
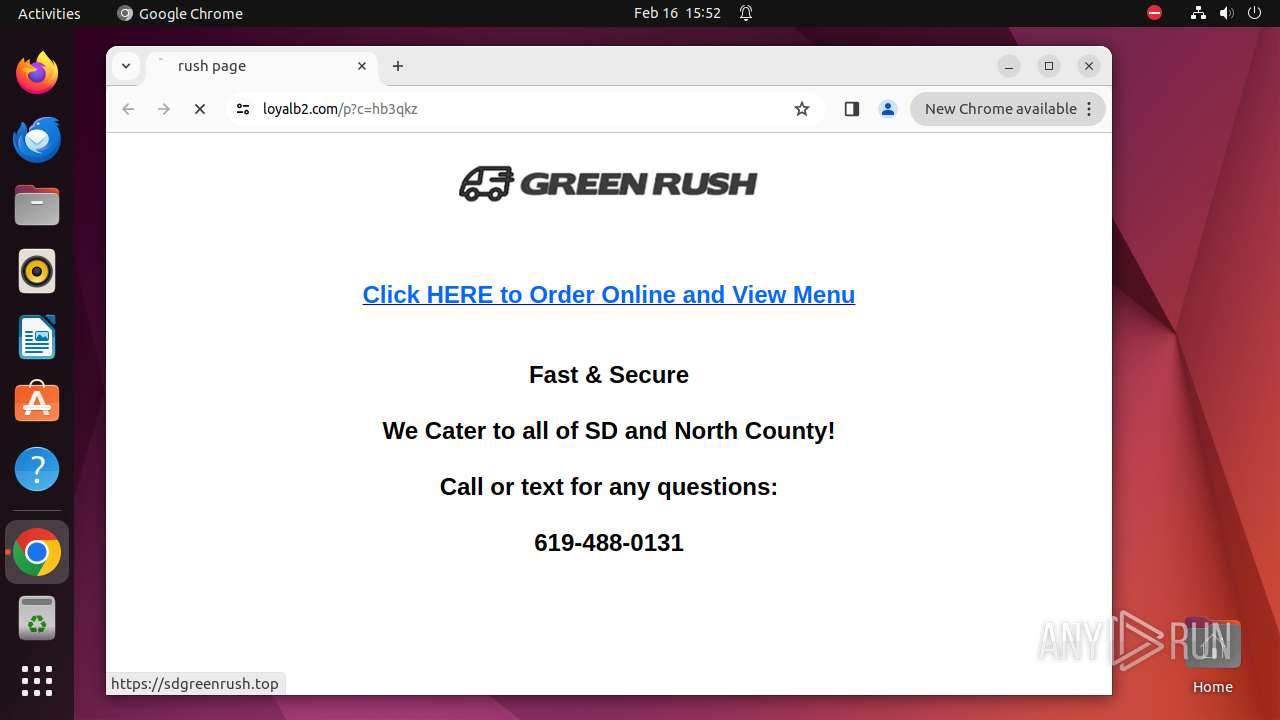
— | — | 3.33.143.57:443 | rebrand.ly | AMAZON-02 | US | unknown |
— | — | 35.238.198.137:443 | loyalb2.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
— | — | 142.250.181.227:443 | update.googleapis.com | GOOGLE | US | unknown |
— | — | 172.217.16.196:443 | www.google.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
rebrand.ly |
| whitelisted |
loyalb2.com |
| unknown |
mcpn.us |
| unknown |
update.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
12.100.168.192.in-addr.arpa |
| unknown |
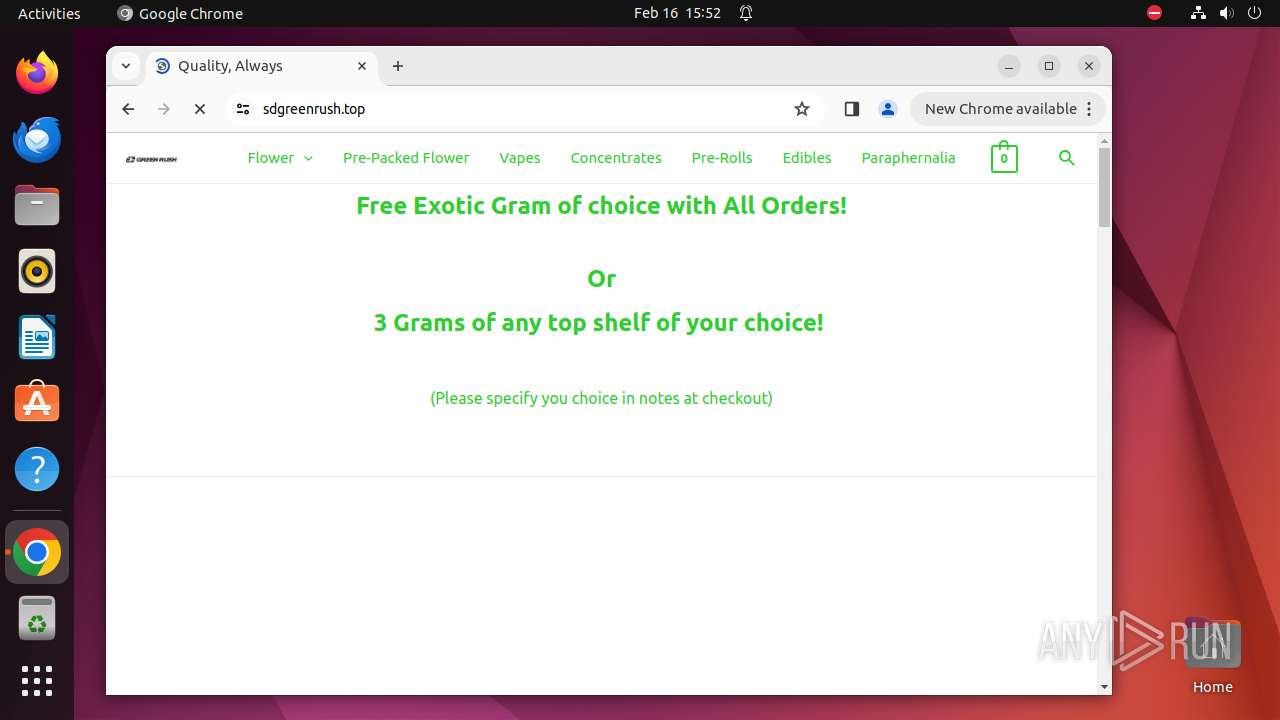
sdgreenrush.top |
| unknown |
stats.wp.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (rebrand .ly) |
— | — | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (rebrand .ly) |
— | — | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |