| File name: | Purchase_Order_003263_Karl_Crowell_Insurance.eml |
| Full analysis: | https://app.any.run/tasks/7cf73caa-a736-4b03-86d5-2f6d62892773 |
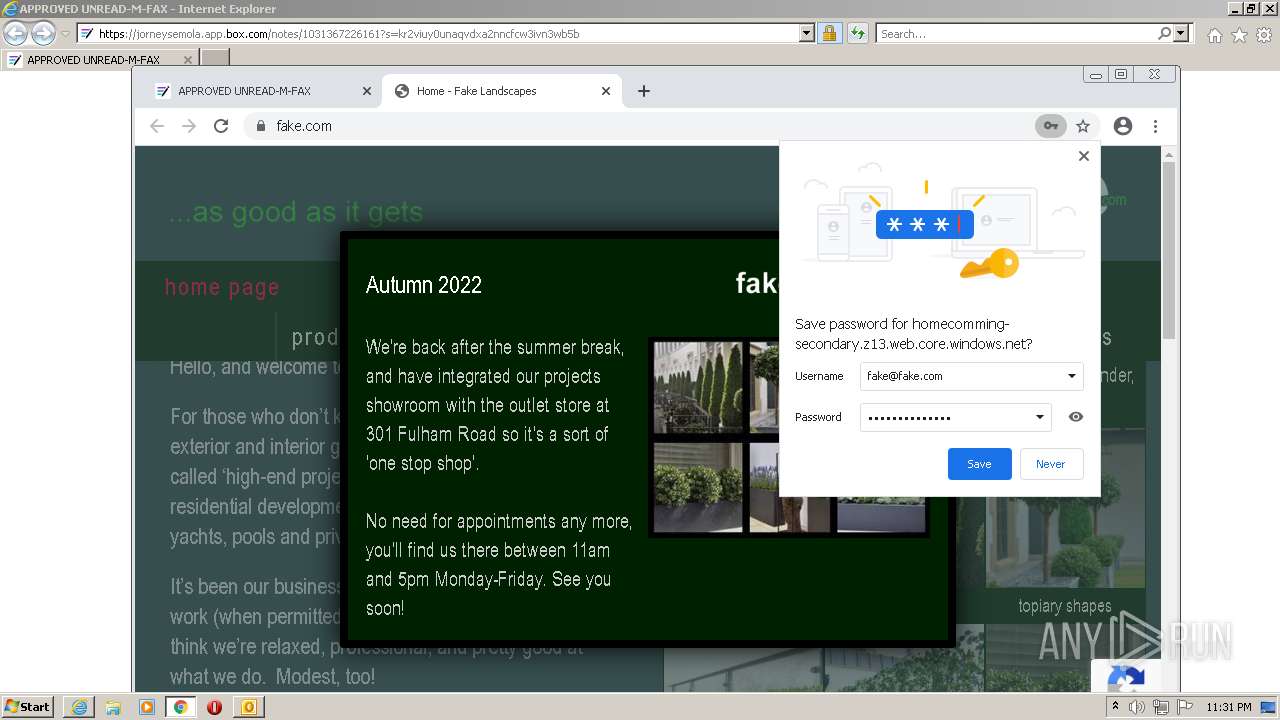
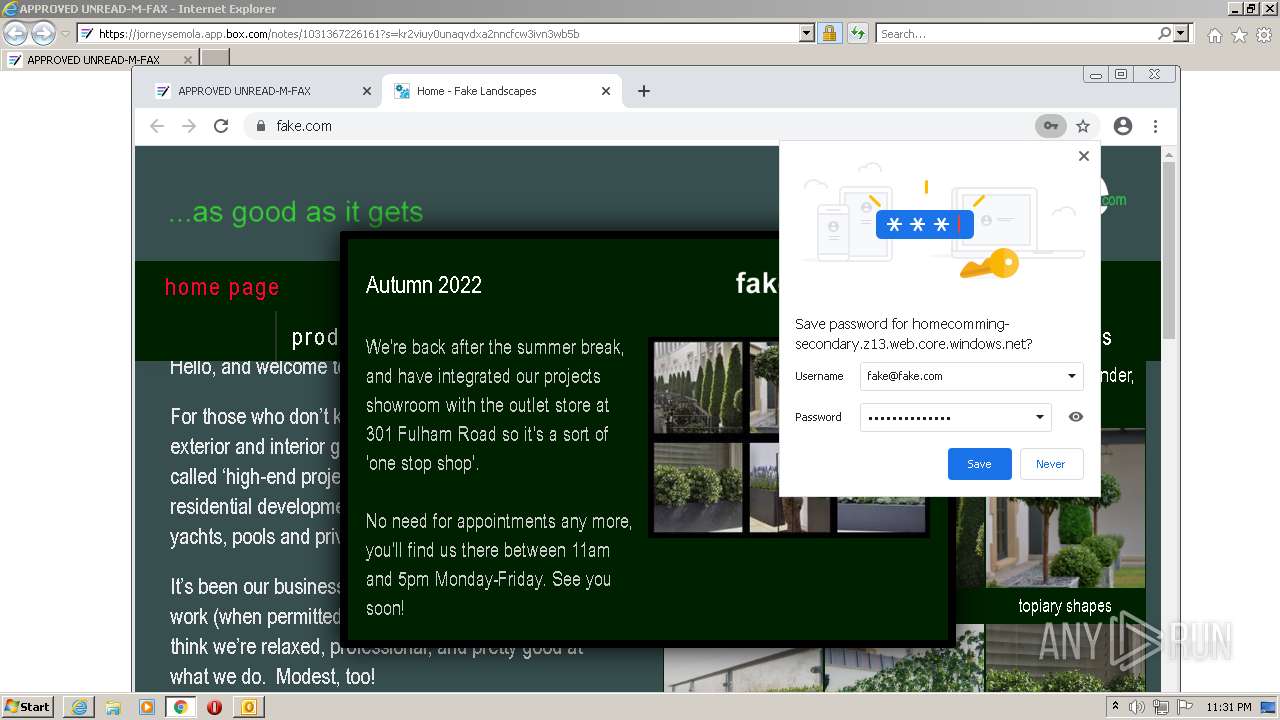
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 22:28:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | news or mail, ASCII text, with CRLF, LF line terminators |
| MD5: | 857C13A08DBE163E0B979A54BE3830A9 |
| SHA1: | 1E4B8DC621D998F664F01C268BCA809355D06B12 |
| SHA256: | C450005CBD2FFFC7F04B6756E22FD0C521C1477E32046A9F6DFA046374596D98 |
| SSDEEP: | 3072:JrxMA2CgPb1zDHz2NOOHftzbCZ3DHvcx7ZLu:u3Pdf2NO8fBCxV |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 3356)
SUSPICIOUS
Checks supported languages
- OUTLOOK.EXE (PID: 3176)
Reads the computer name
- OUTLOOK.EXE (PID: 3176)
Searches for installed software
- OUTLOOK.EXE (PID: 3176)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3176)
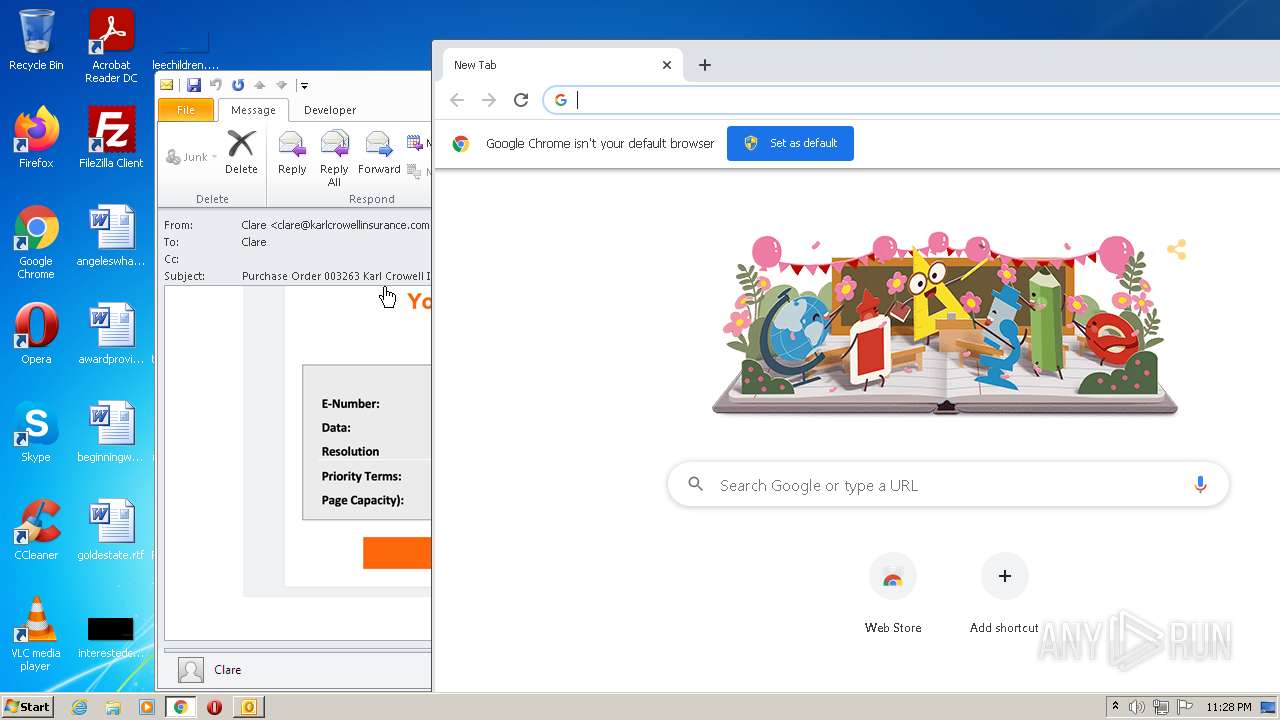
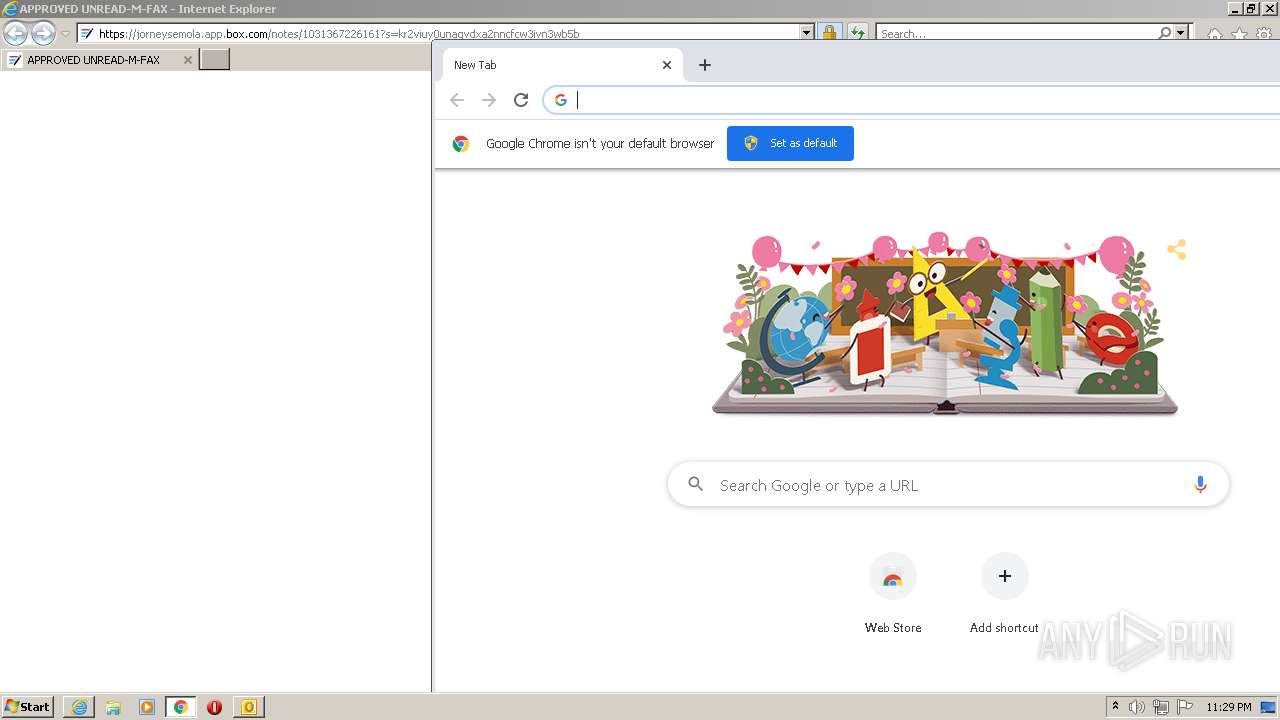
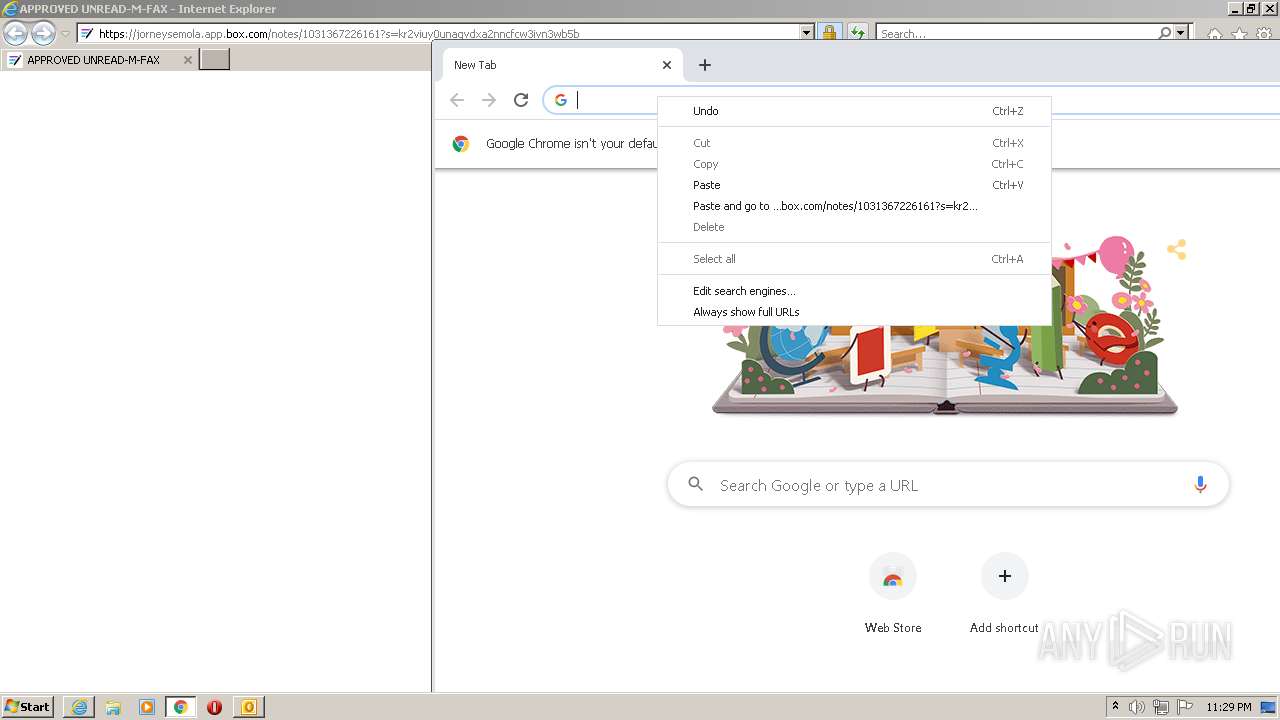
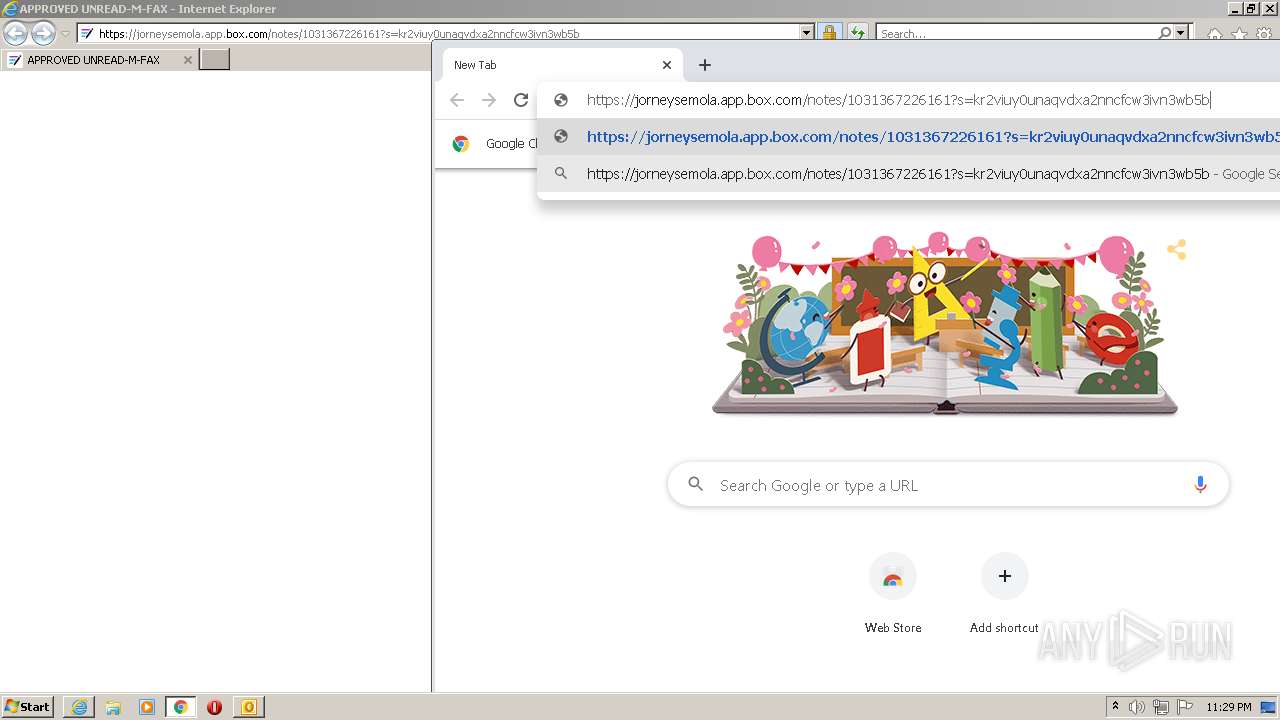
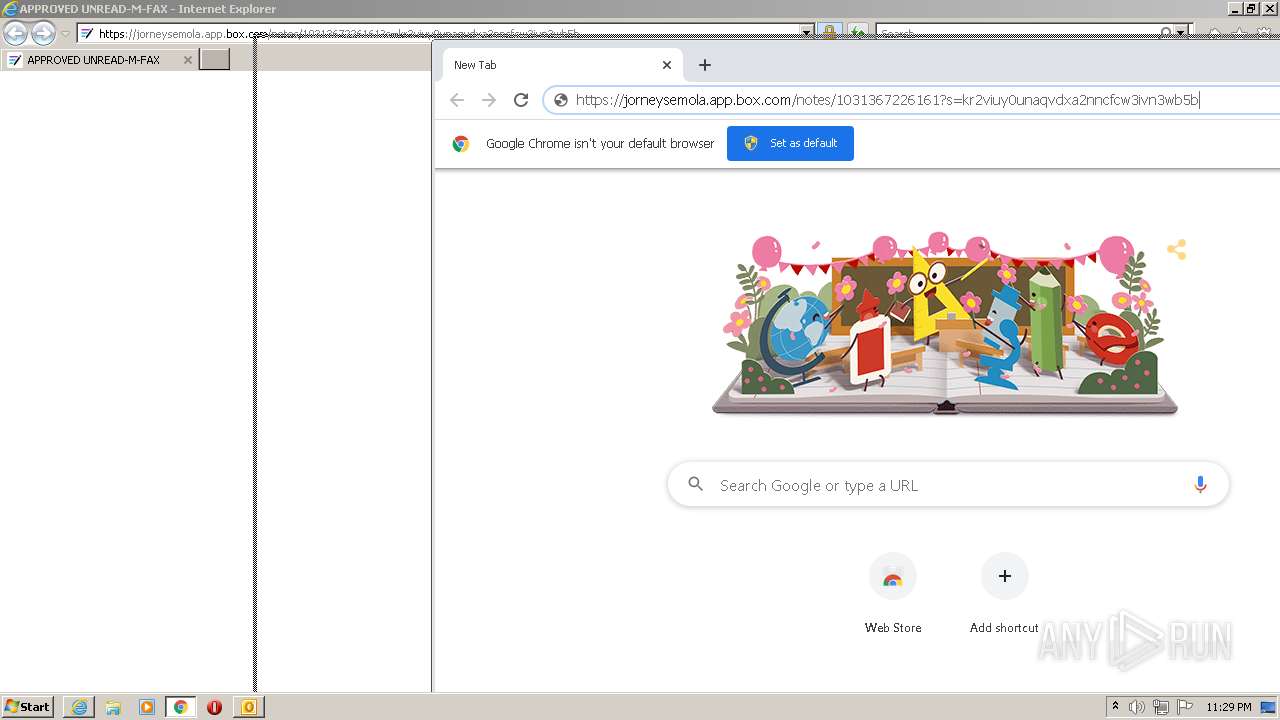
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3176)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2224)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3144)
Drops a file with a compile date too recent
- chrome.exe (PID: 3356)
Executable content was dropped or overwritten
- chrome.exe (PID: 3356)
INFO
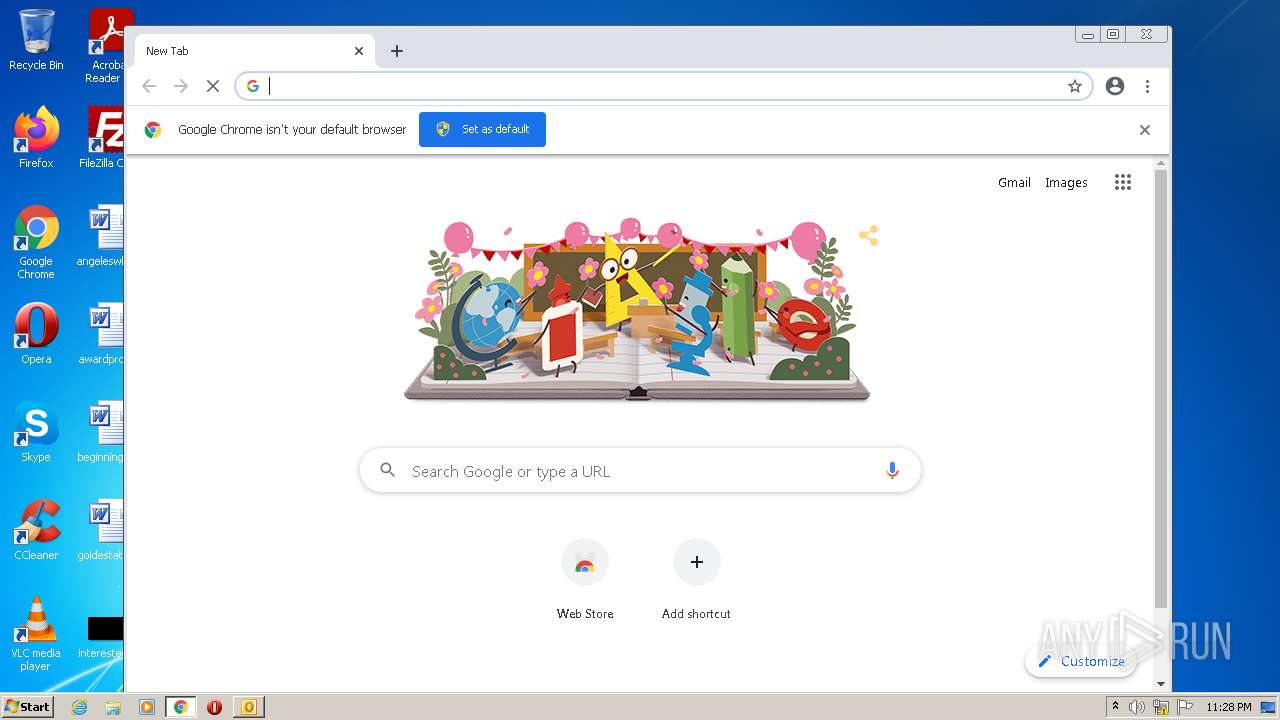
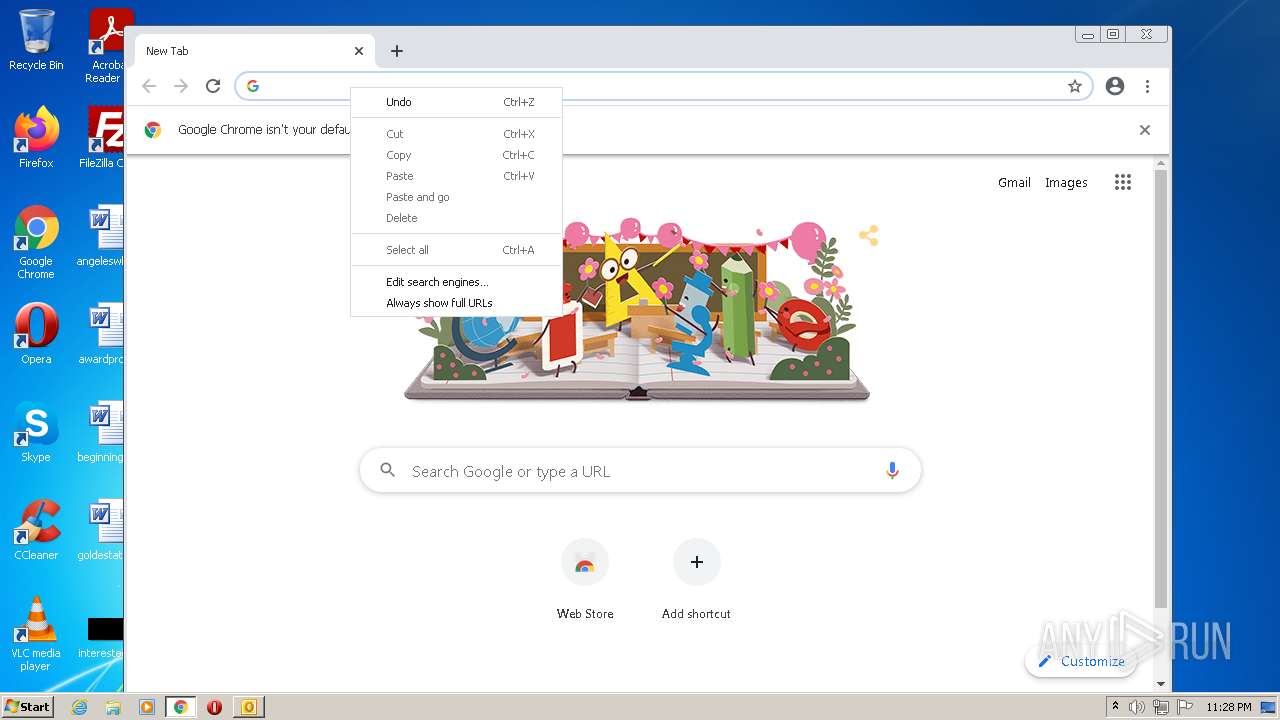
Manual execution by user
- chrome.exe (PID: 2224)
Checks supported languages
- chrome.exe (PID: 2416)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 2912)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 2348)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3848)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 3824)
- chrome.exe (PID: 3292)
- chrome.exe (PID: 3552)
- chrome.exe (PID: 3348)
- chrome.exe (PID: 1780)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 2604)
- iexplore.exe (PID: 3144)
- iexplore.exe (PID: 1384)
- chrome.exe (PID: 1692)
- chrome.exe (PID: 1724)
- chrome.exe (PID: 3528)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 2836)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 1080)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 2860)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 2356)
- chrome.exe (PID: 3856)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 3356)
- chrome.exe (PID: 4000)
- chrome.exe (PID: 3128)
- chrome.exe (PID: 764)
- chrome.exe (PID: 936)
Reads the hosts file
- chrome.exe (PID: 2224)
- chrome.exe (PID: 2348)
Reads the computer name
- chrome.exe (PID: 2348)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 2912)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 1780)
- iexplore.exe (PID: 1384)
- iexplore.exe (PID: 3144)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 1692)
Application launched itself
- chrome.exe (PID: 2224)
- iexplore.exe (PID: 1384)
Reads settings of System Certificates
- chrome.exe (PID: 2348)
- iexplore.exe (PID: 3144)
- iexplore.exe (PID: 1384)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3176)
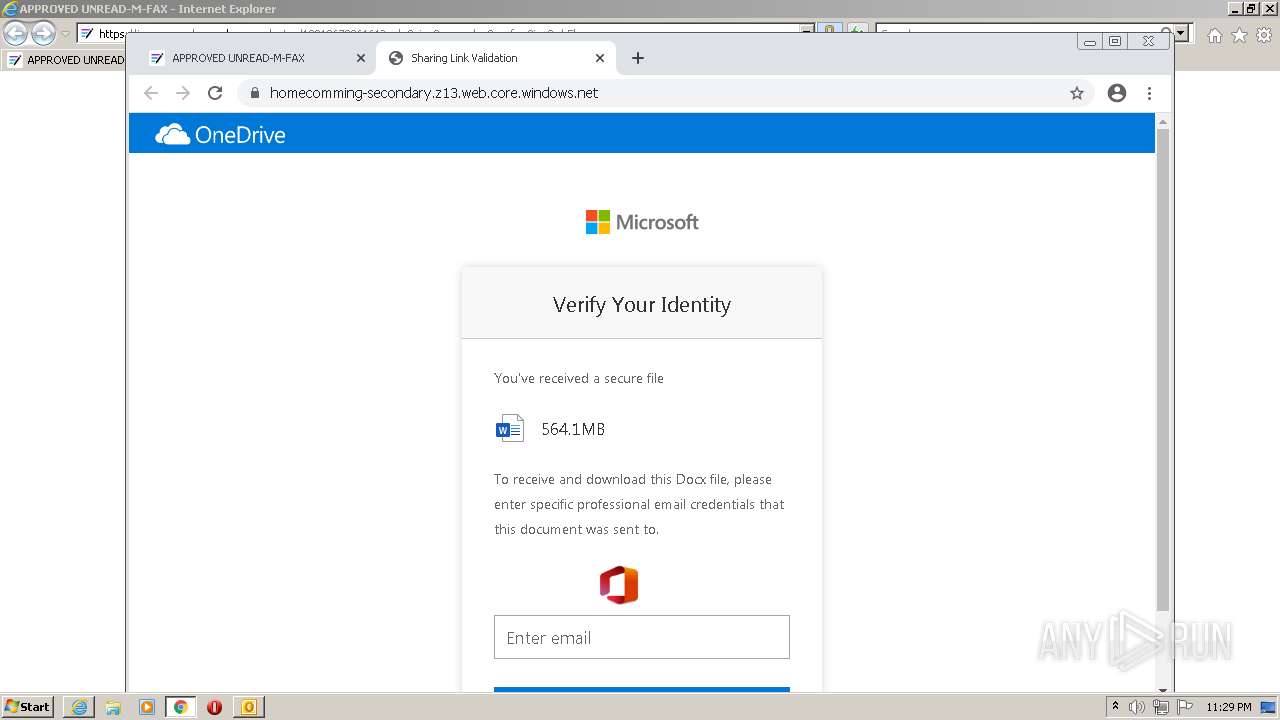
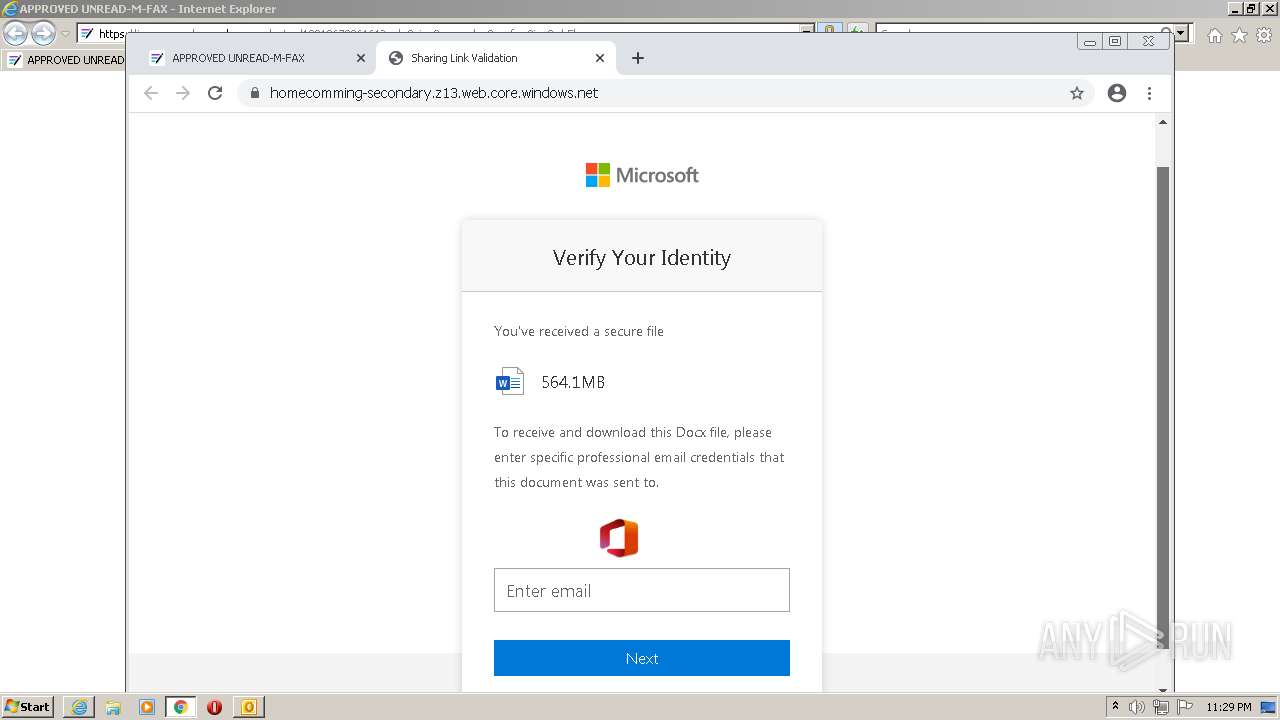
Changes internet zones settings
- iexplore.exe (PID: 1384)
Checks Windows Trust Settings
- iexplore.exe (PID: 3144)
- iexplore.exe (PID: 1384)
Reads internet explorer settings
- iexplore.exe (PID: 3144)
Creates files in the user directory
- iexplore.exe (PID: 3144)
- iexplore.exe (PID: 1384)
Changes settings of System certificates
- iexplore.exe (PID: 1384)
Reads the date of Windows installation
- chrome.exe (PID: 1692)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 2) (100) |
|---|
Total processes
79
Monitored processes
39
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3168672682609655102,4353735666349604753,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1028,3168672682609655102,4353735666349604753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3204 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1028,3168672682609655102,4353735666349604753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3580 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
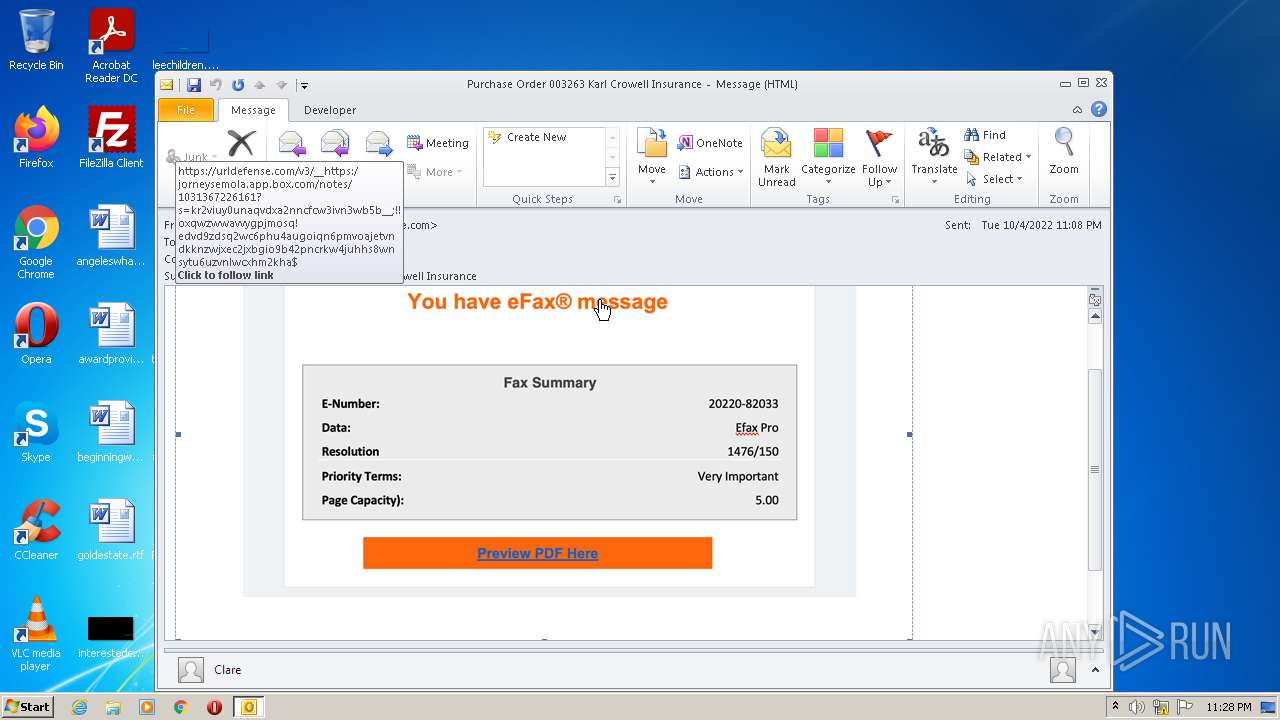
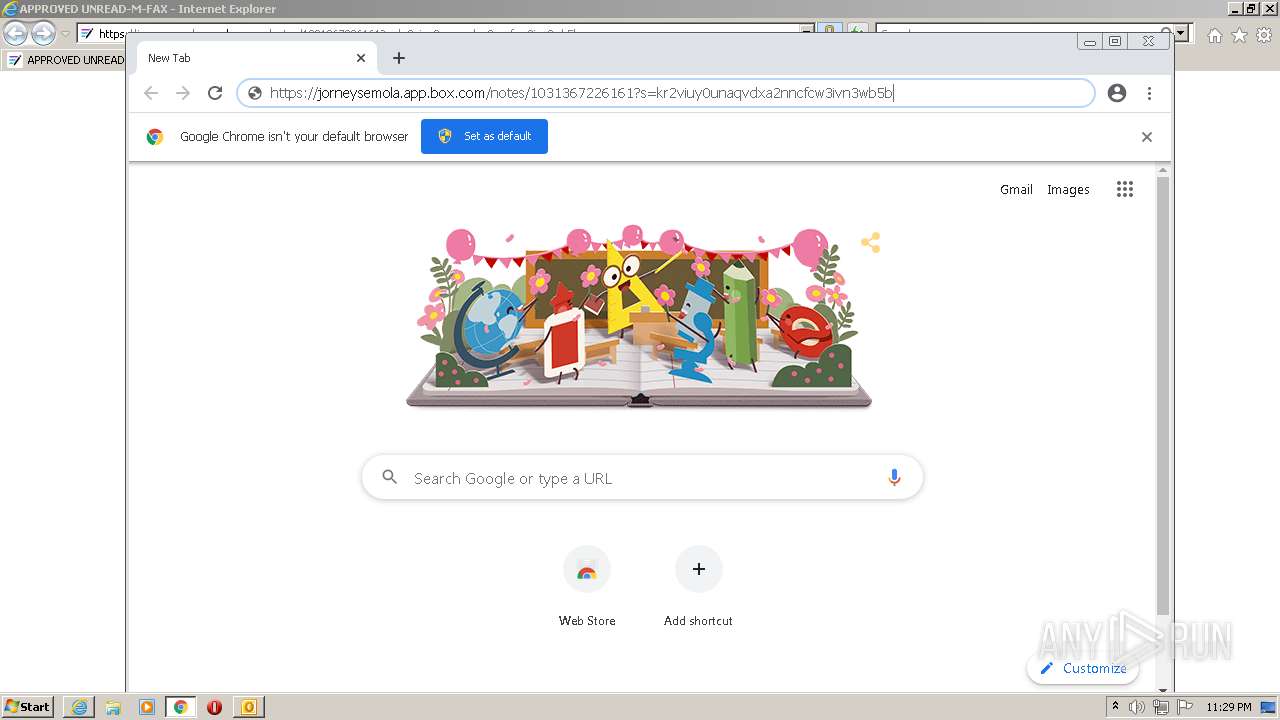
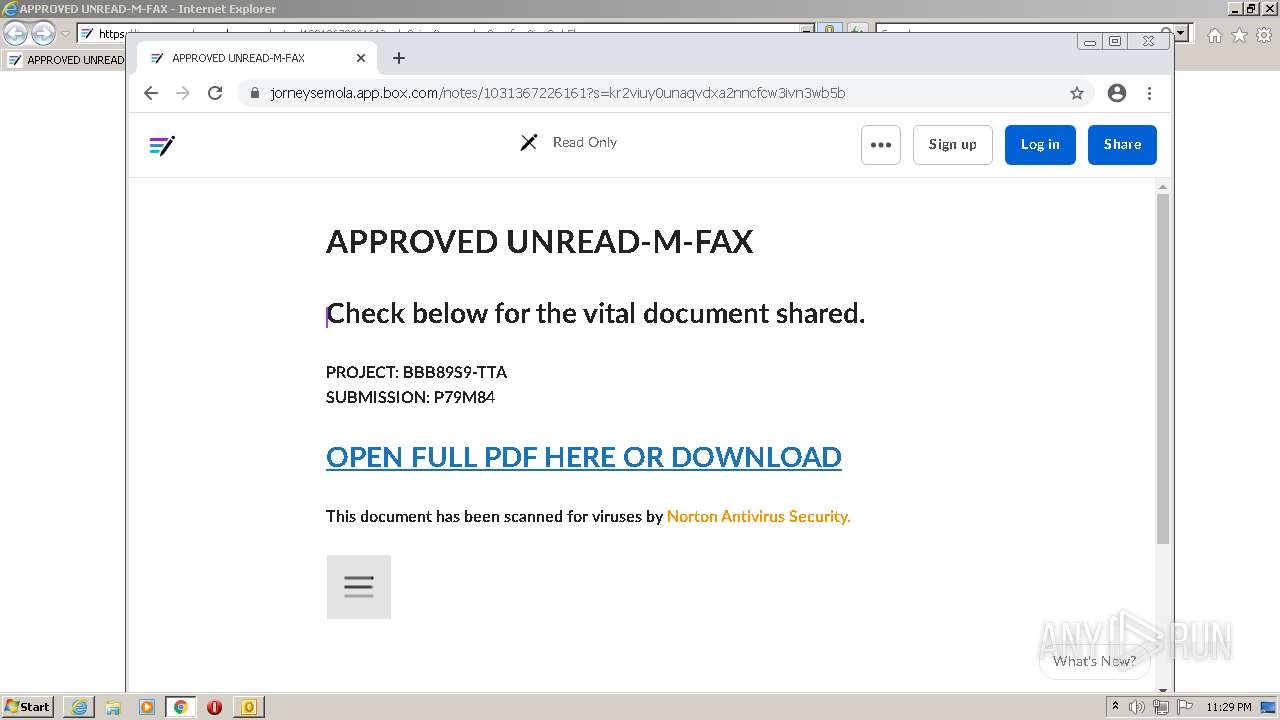
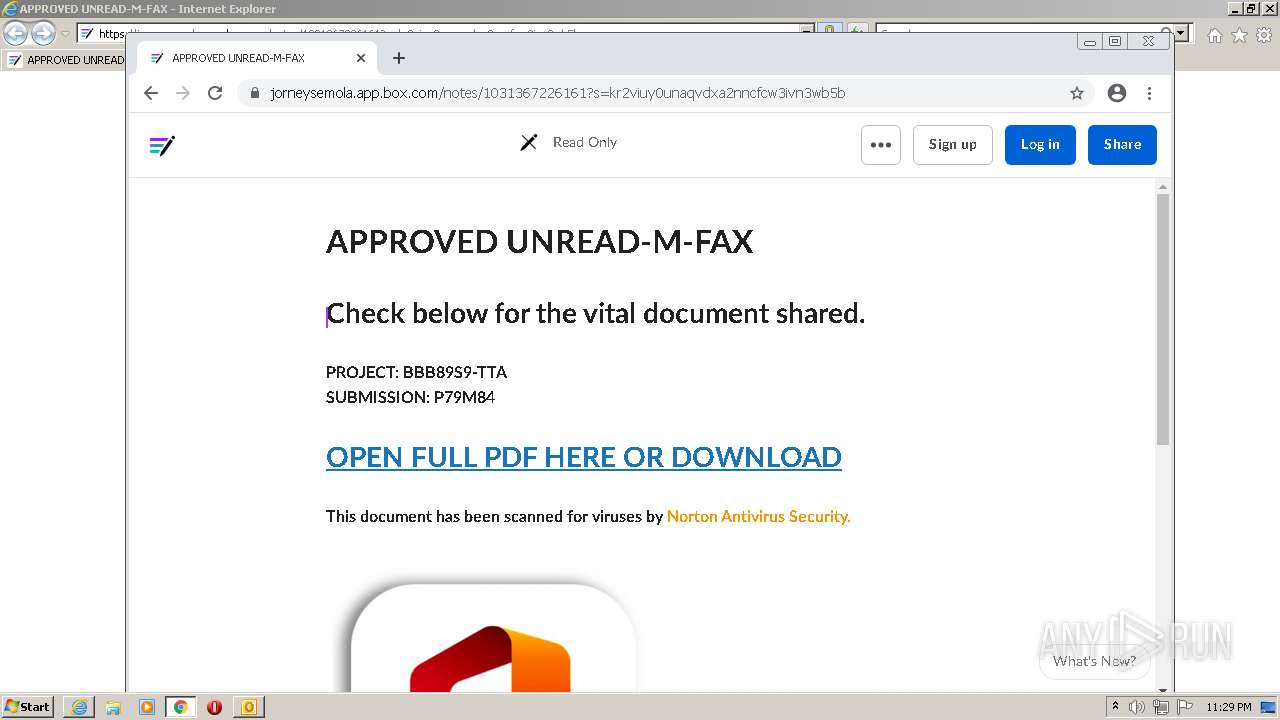
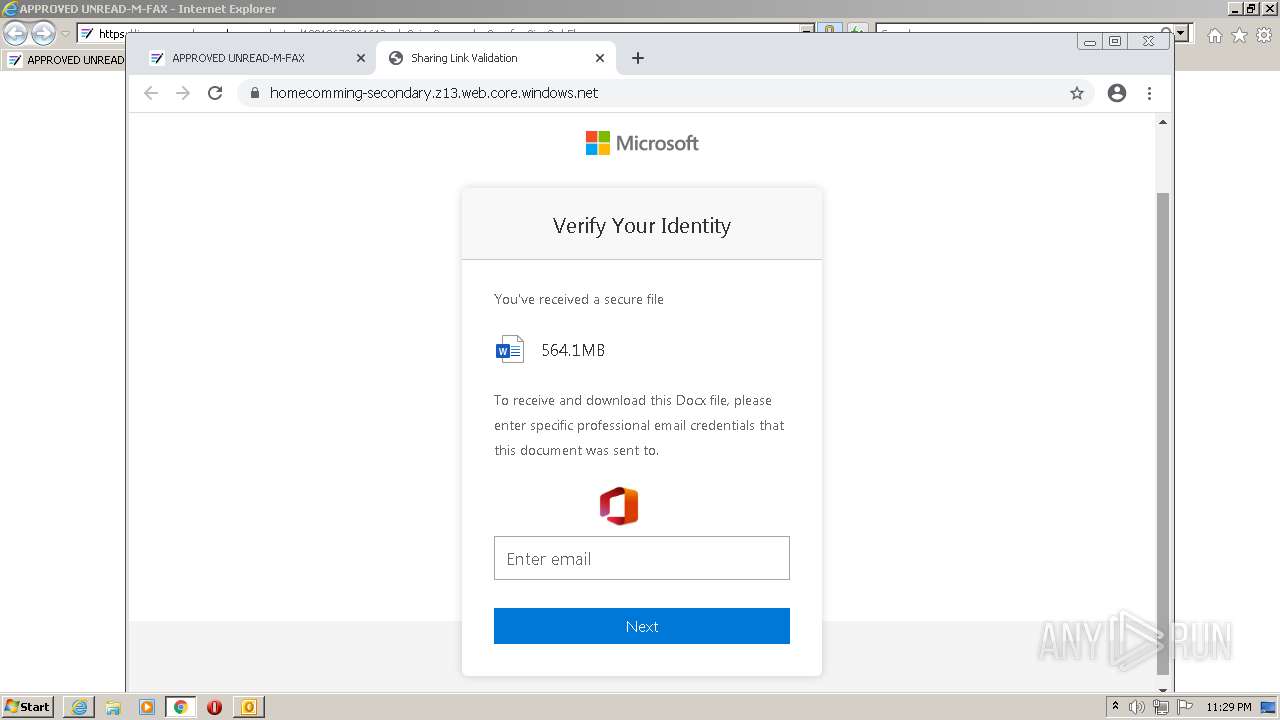
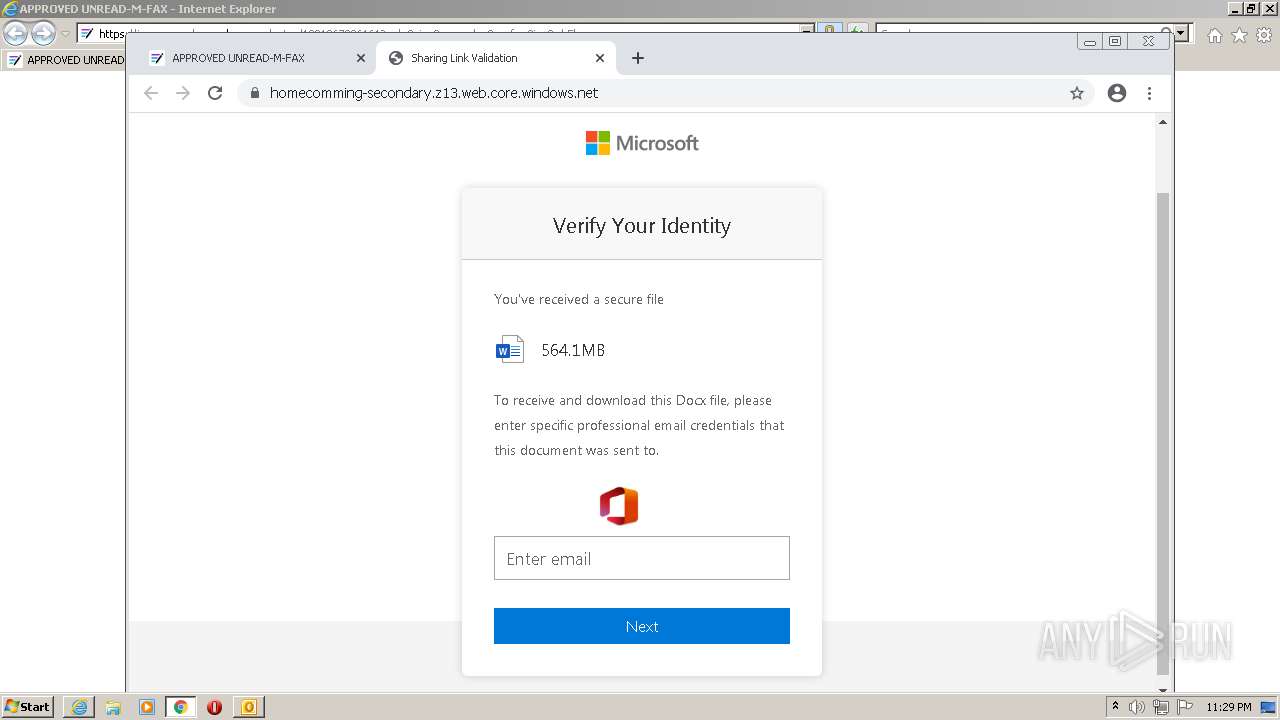
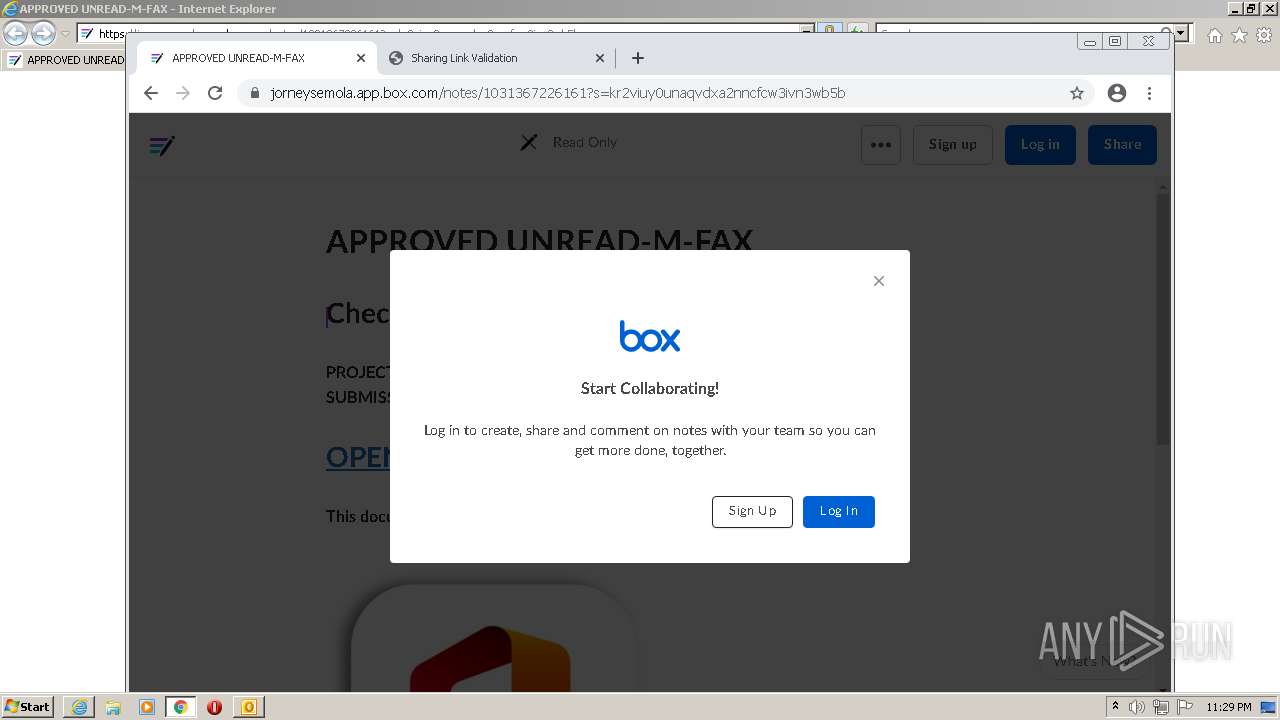
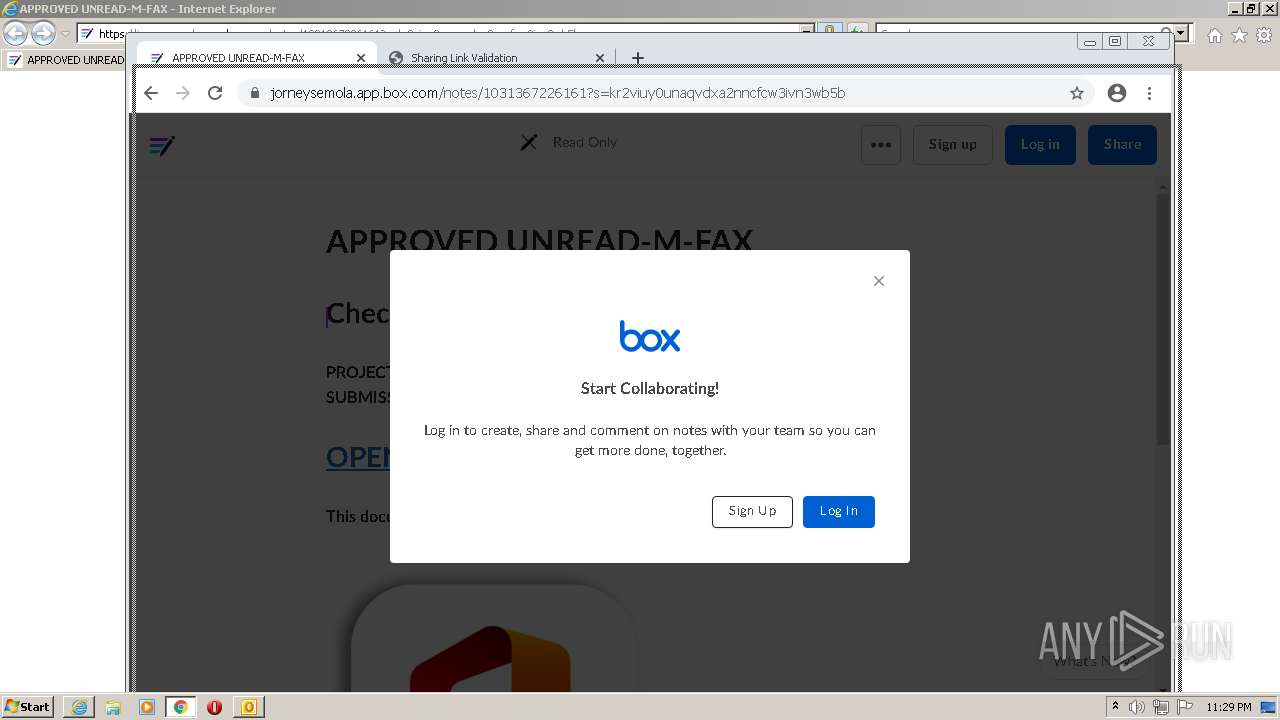
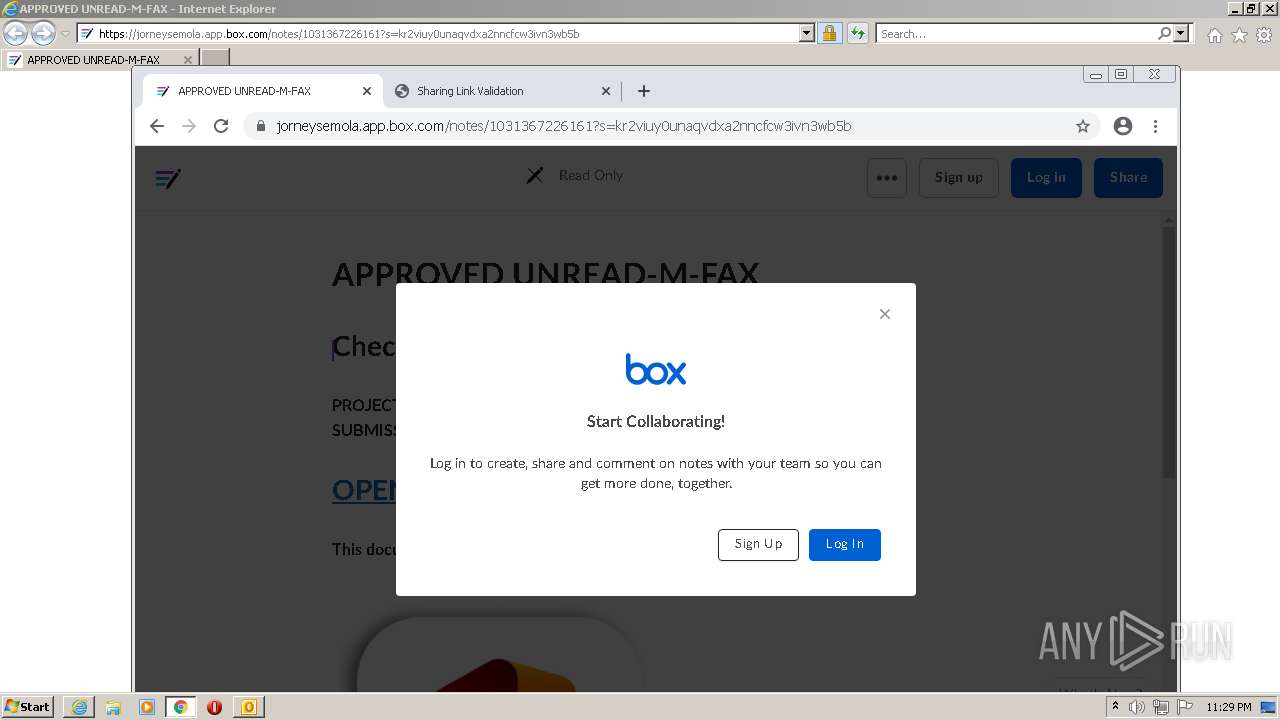
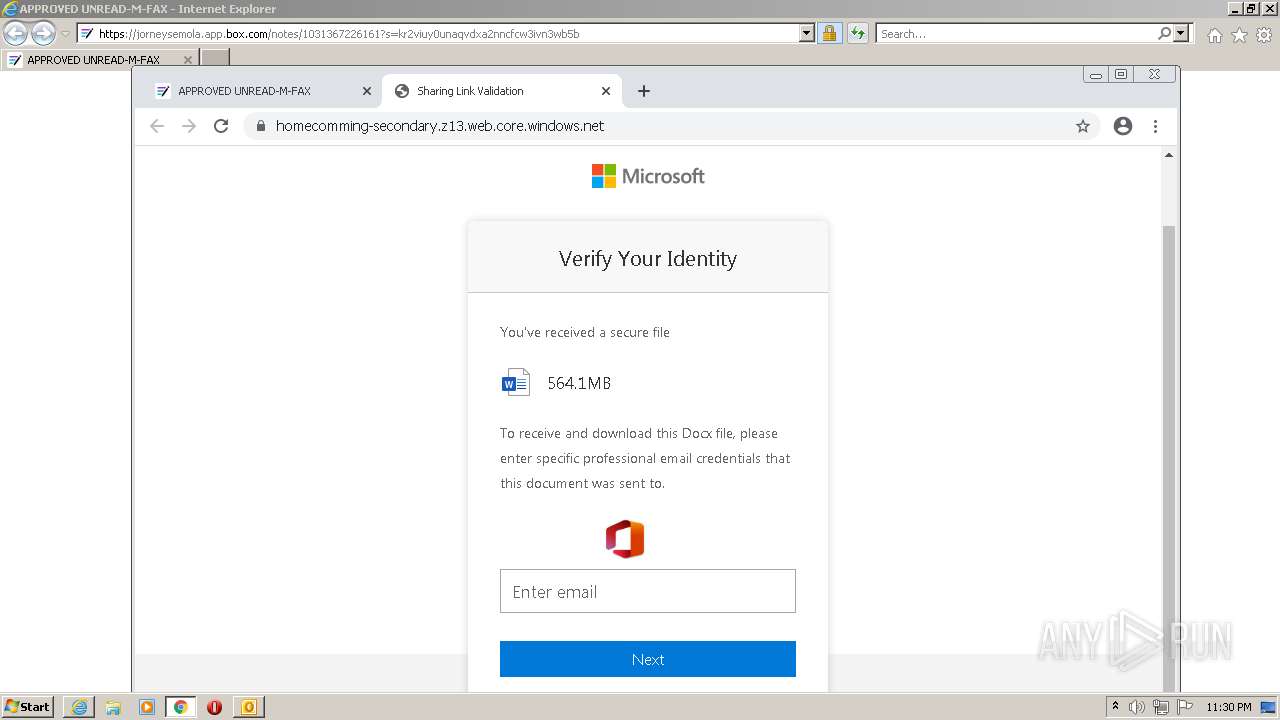
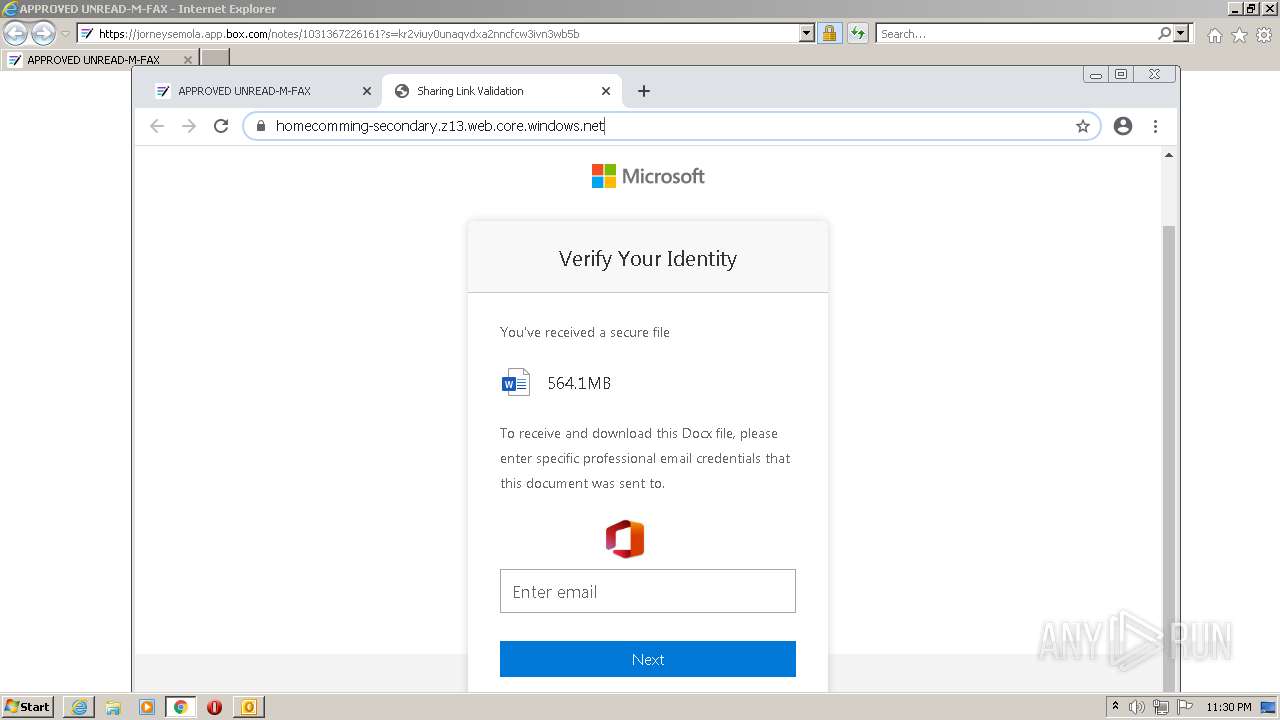
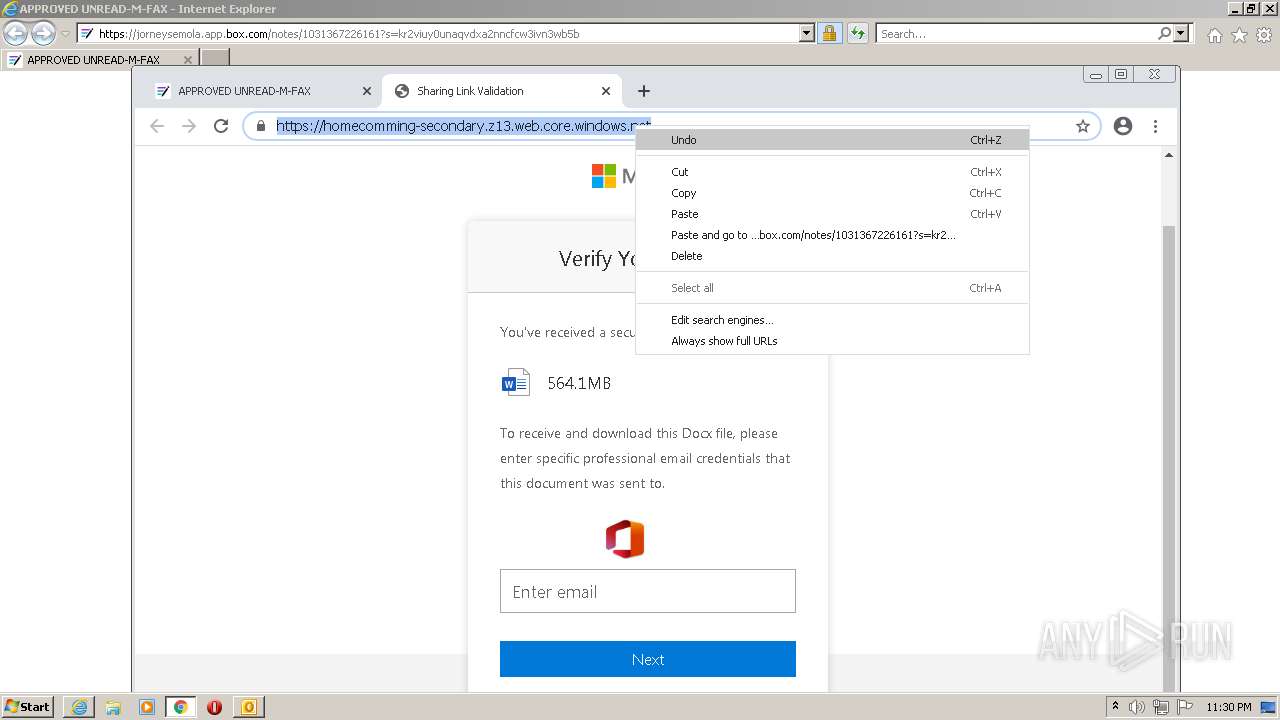
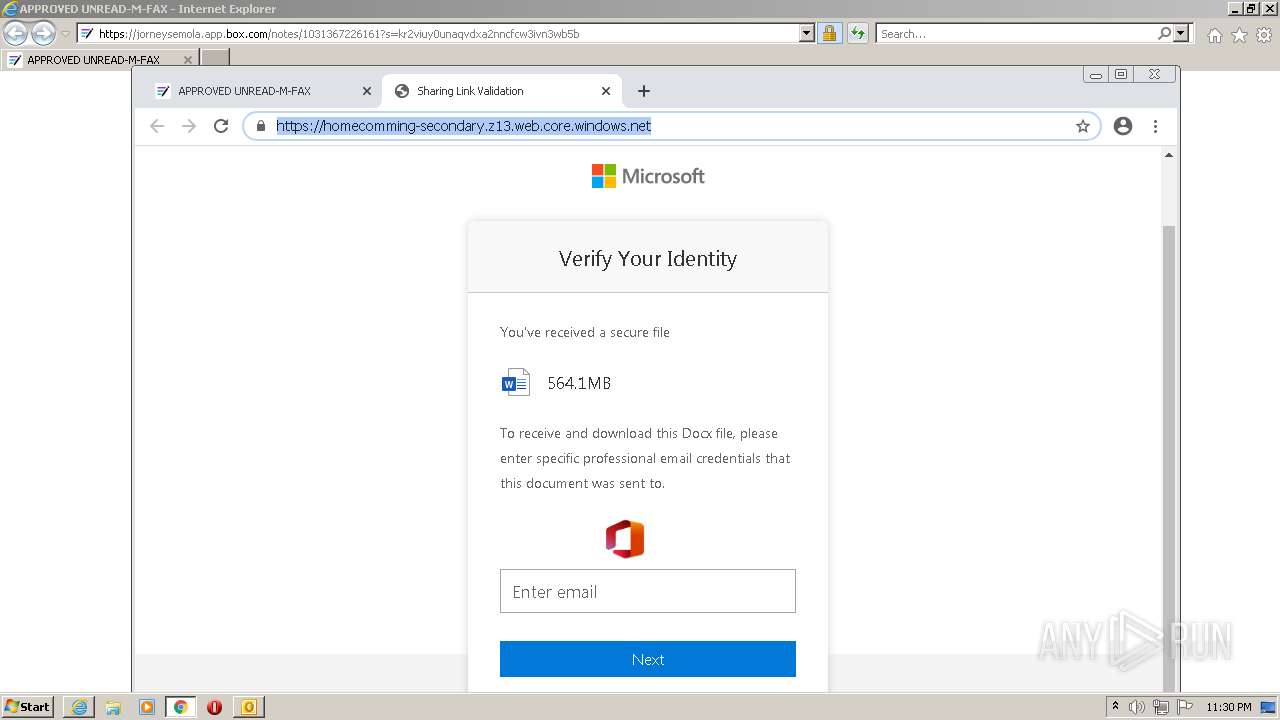
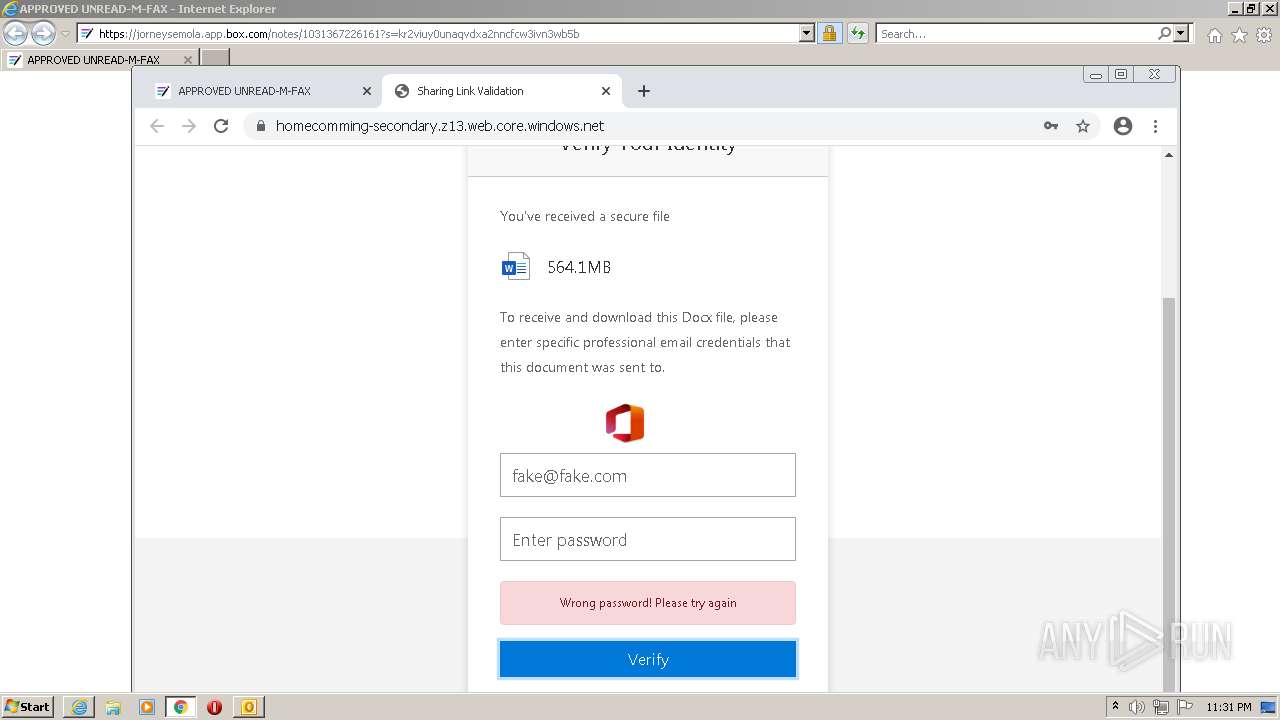
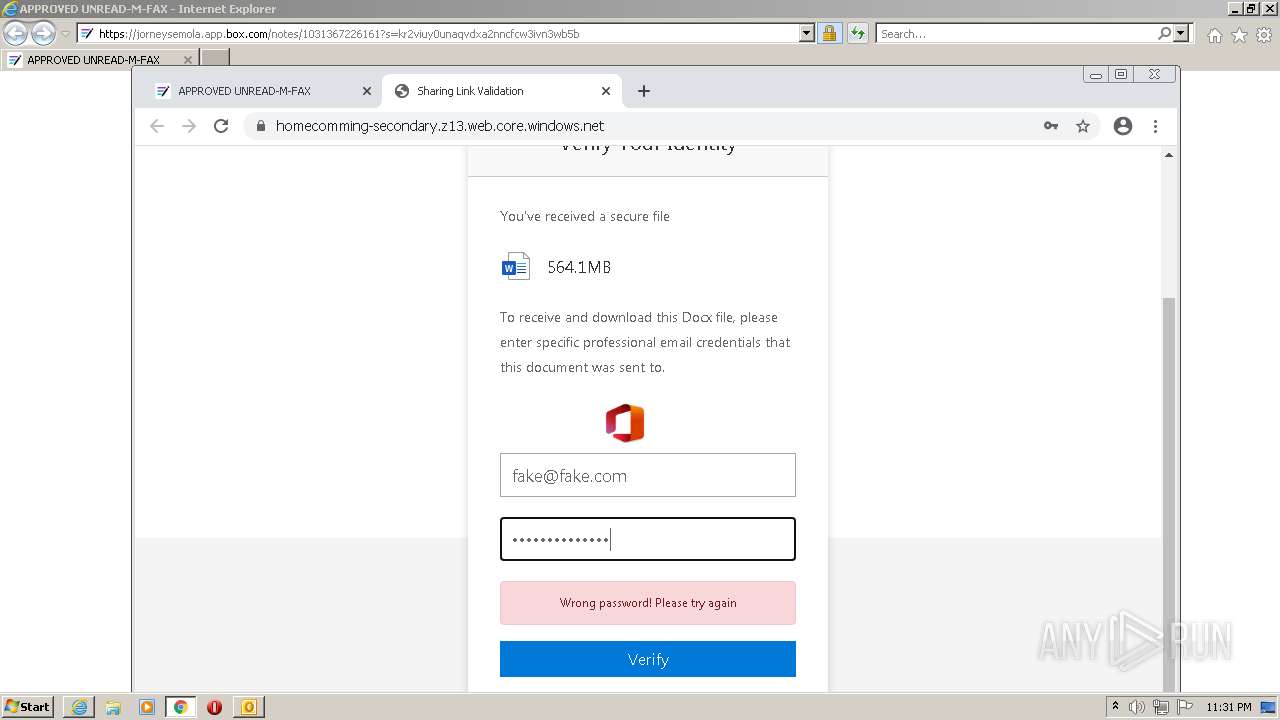
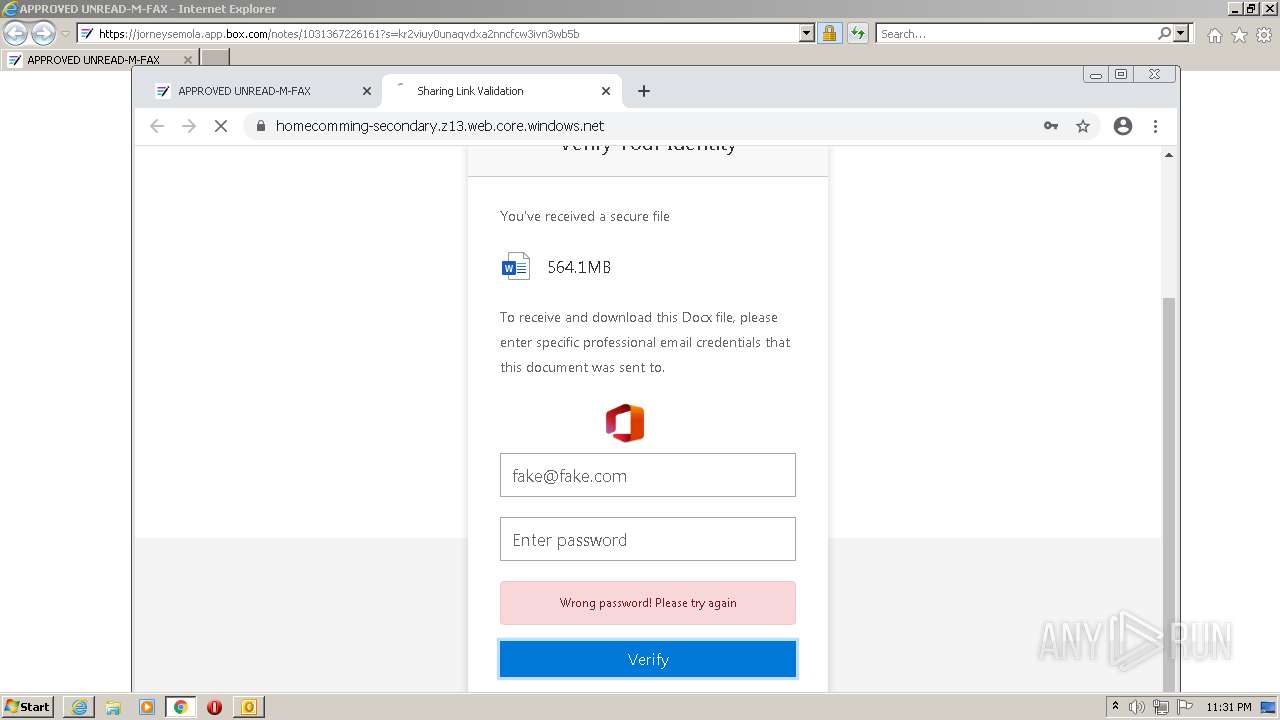
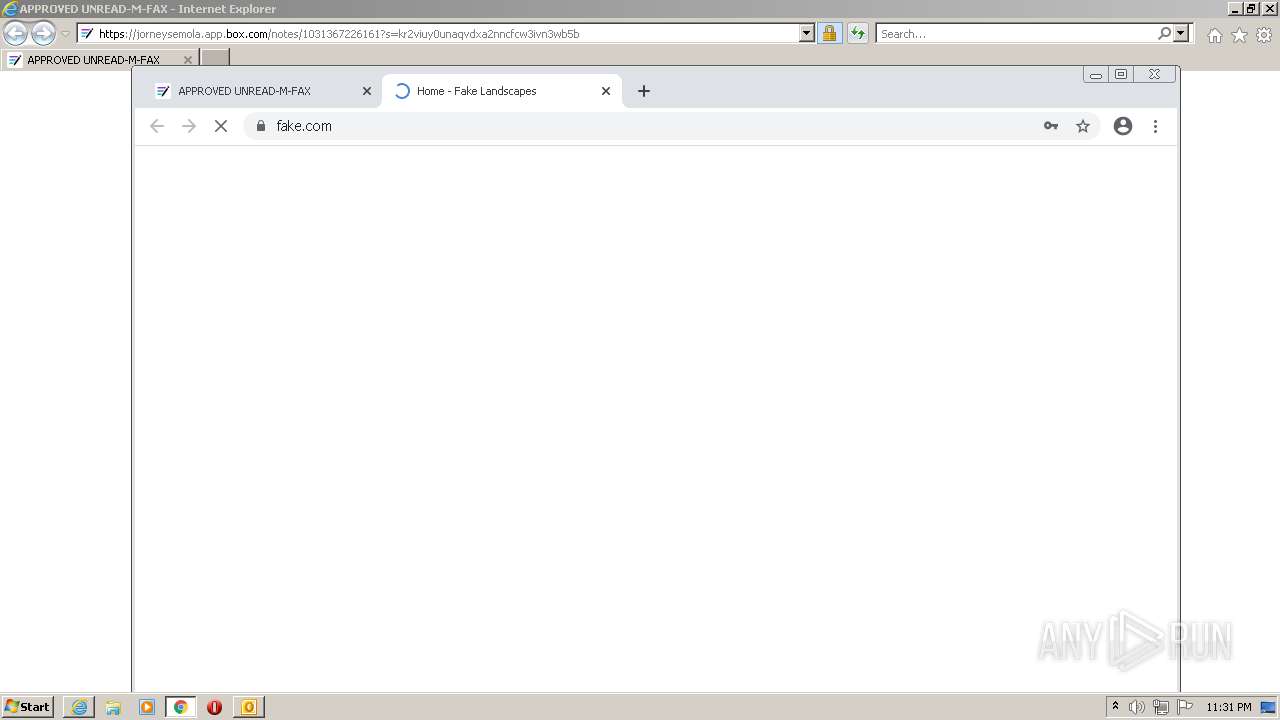
| 1384 | "C:\Program Files\Internet Explorer\iexplore.exe" https://urldefense.com/v3/__https:/jorneysemola.app.box.com/notes/1031367226161?s=kr2viuy0unaqvdxa2nncfcw3ivn3wb5b__;!!OxqwZwwAVvYGpJMosQ!eDVd9ZdSq2wC6Phu4aUgOIQn6PMvOajetvnDKkNZWJxEc2jXbGIo9B42pncRKW4juHhS8wnSytu6UZVnlWcxhm2KhA$ | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,3168672682609655102,4353735666349604753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1548 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3168672682609655102,4353735666349604753,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=592 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,3168672682609655102,4353735666349604753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3628 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,3168672682609655102,4353735666349604753,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3380 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3168672682609655102,4353735666349604753,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
34 968
Read events
34 113
Write events
825
Delete events
30
Modification events
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3176) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
1
Suspicious files
253
Text files
246
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3176 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR4D29.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3176 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-633CB394-8B0.pma | — | |
MD5:— | SHA256:— | |||
| 3176 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3176 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3176 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_RssRule_2_7B55903753F35043B40C9C42BB127DD9.dat | xml | |
MD5:D8B37ED0410FB241C283F72B76987F18 | SHA256:31E68049F6B7F21511E70CD7F2D95B9CF1354CF54603E8F47C1FC40F40B7A114 | |||
| 2416 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3176 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ContactPrefs_2_FD789EC7D68C2945B4CA390F84822F02.dat | xml | |
MD5:BBCF400BD7AE536EB03054021D6A6398 | SHA256:383020065C1F31F4FB09F448599A6D5E532C390AF4E5B8AF0771FE17A23222AD | |||
| 2224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2224 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF139a7e.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
70
DNS requests
56
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
3144 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCEA2KFitLH9n0LY9WTWFSpcE%3D | US | der | 471 b | whitelisted |
3144 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 1.42 Kb | whitelisted |
3144 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 10.5 Kb | whitelisted |
3144 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEA7ze%2BiSFHmYKH4I97FkjrU%3D | US | der | 471 b | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 22.6 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 10.5 Kb | whitelisted |
3144 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | der | 2.18 Kb | whitelisted |
3144 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3176 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2348 | chrome.exe | 172.217.169.163:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2348 | chrome.exe | 172.217.20.78:443 | clients2.google.com | GOOGLE | US | whitelisted |
2348 | chrome.exe | 142.250.187.164:443 | www.google.com | GOOGLE | US | whitelisted |
2348 | chrome.exe | 142.250.184.141:443 | accounts.google.com | GOOGLE | US | unknown |
2348 | chrome.exe | 172.217.17.193:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
2348 | chrome.exe | 142.250.187.138:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2348 | chrome.exe | 172.217.20.67:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
2348 | chrome.exe | 142.250.184.131:443 | update.googleapis.com | GOOGLE | US | whitelisted |
2348 | chrome.exe | 172.217.17.142:443 | apis.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |
2348 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.ga) in TLS SNI |