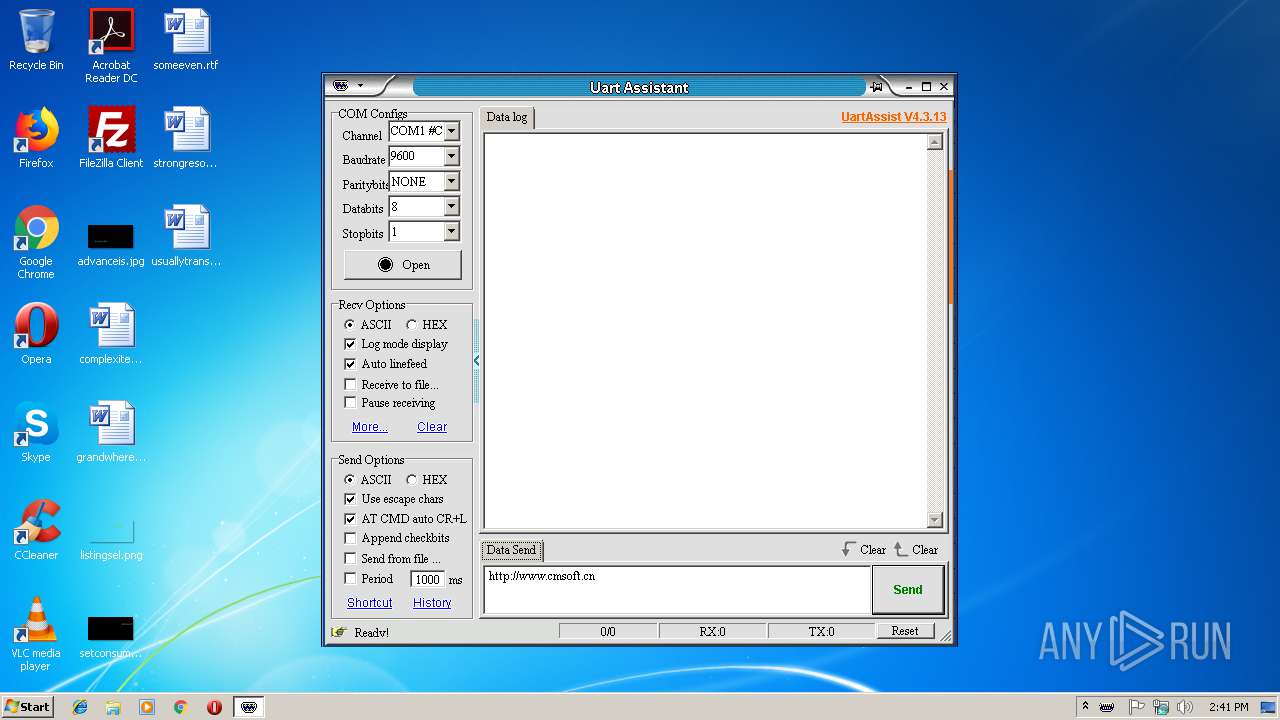
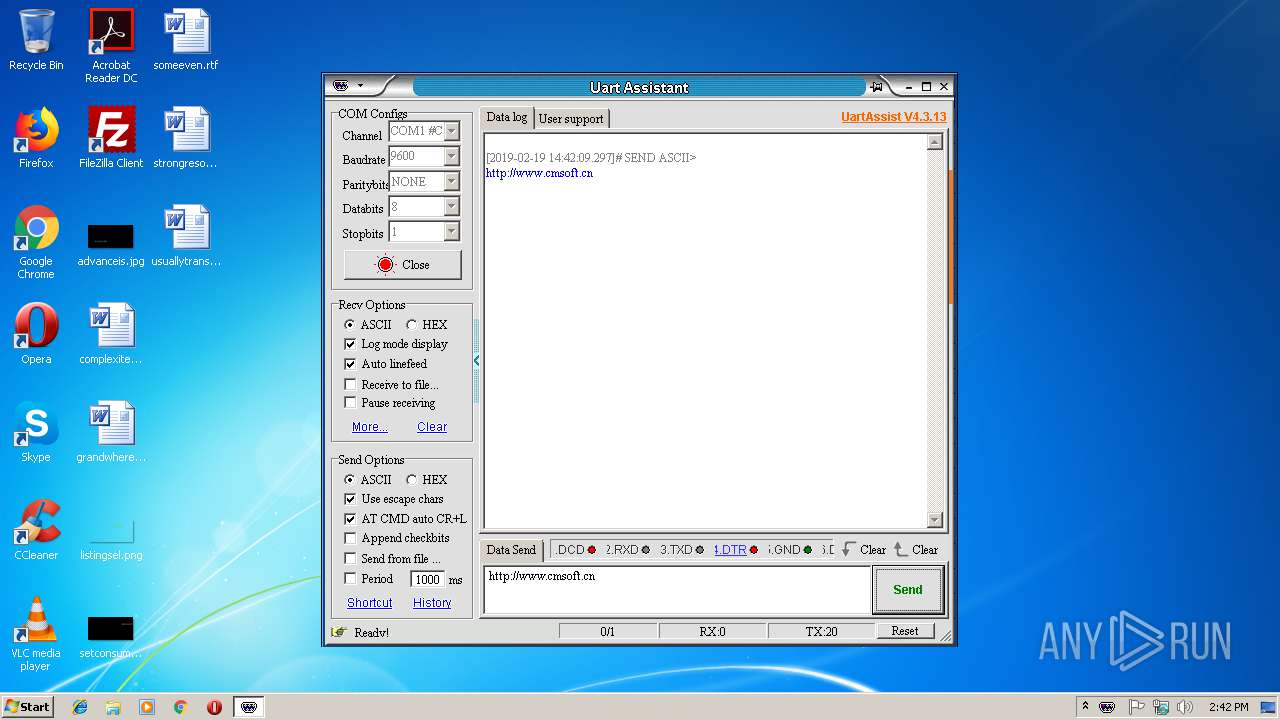
| File name: | UartAssist.exe |
| Full analysis: | https://app.any.run/tasks/68b6c6f7-dff9-4b5d-9b31-8a838dbd13ac |
| Verdict: | No threats detected |
| Analysis date: | February 19, 2019, 14:41:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressed |
| MD5: | 53BB08CE46029083274888C214E6575B |
| SHA1: | 0E4128A1F36E7A854EE4DF9F9475C711D1A929A9 |
| SHA256: | C4460882EB284FE28224693C56AF2C688A6FCABAE22ED06E30A70D839E1C8A23 |
| SSDEEP: | 12288:GwLF3TGjJ2Mx0GsOjW2DADw777cp/vvG8ki:GA3HFVpIXIZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads internet explorer settings
- UartAssist.exe (PID: 3756)
Creates files in the user directory
- UartAssist.exe (PID: 3756)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (48.9) |
|---|---|---|
| .scr | | | Windows screen saver (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.8) |
| .exe | | | Win32 Executable (generic) (8.1) |
| .exe | | | Generic Win/DOS Executable (3.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:29 09:12:15+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 520192 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 1404928 |
| EntryPoint: | 0x1d62b0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.64 |
| ProductVersionNumber: | 1.0.0.64 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | 野人家园 |
| FileDescription: | 串口调试助手 |
| FileVersion: | 1.0.0.64 |
| InternalName: | - |
| LegalCopyright: | 野人家园 CMSOFT.CN |
| LegalTrademarks: | - |
| OriginalFileName: | UartAssist |
| ProductName: | 串口调试助手 |
| ProductVersion: | 1.0.0.0 |
| Comments: | 野人家园出品 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Jan-2019 08:12:15 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 29-Jan-2019 08:12:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00157000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00158000 | 0x0007F000 | 0x0007E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92775 |
.rsrc | 0x001D7000 | 0x00002000 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.65127 |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
COMDLG32.DLL |
GDI32.DLL |
KERNEL32.DLL |
OLE32.DLL |
OLEAUT32.DLL |
SETUPAPI.DLL |
SHELL32.DLL |
USER32.DLL |
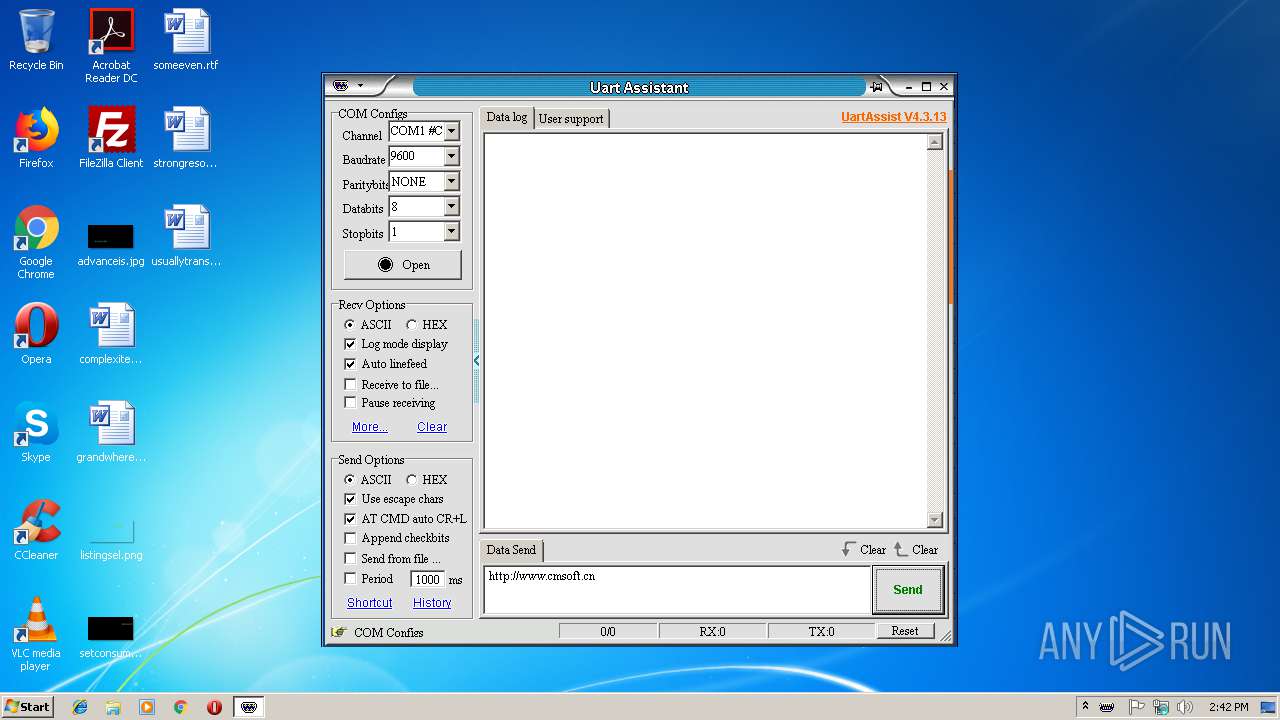
Total processes
31
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3756 | "C:\Users\admin\Downloads\UartAssist.exe" | C:\Users\admin\Downloads\UartAssist.exe | explorer.exe | ||||||||||||
User: admin Company: 野人家园 Integrity Level: MEDIUM Description: 串口调试助手 Exit code: 0 Version: 1.0.0.64 Modules
| |||||||||||||||
Total events
121
Read events
94
Write events
27
Delete events
0
Modification events
| (PID) Process: | (3756) UartAssist.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\UartAssist_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3756) UartAssist.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\UartAssist_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3756) UartAssist.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\UartAssist_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) UartAssist.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\UartAssist_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) UartAssist.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\UartAssist_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3756) UartAssist.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\UartAssist_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3756) UartAssist.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\UartAssist_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3756) UartAssist.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\UartAssist_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3756) UartAssist.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\UartAssist_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3756) UartAssist.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\UartAssist_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
0
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3756 | UartAssist.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\ErrorPageTemplate[1] | text | |
MD5:F4FE1CB77E758E1BA56B8A8EC20417C5 | SHA256:8D018639281B33DA8EB3CE0B21D11E1D414E59024C3689F92BE8904EB5779B5F | |||
| 3756 | UartAssist.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\errorPageStrings[1] | text | |
MD5:1A0563F7FB85A678771450B131ED66FD | SHA256:EB5678DE9D8F29CA6893D4E6CA79BD5AB4F312813820FE4997B009A2B1A1654C | |||
| 3756 | UartAssist.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\down[1] | image | |
MD5:555E83CE7F5D280D7454AF334571FB25 | SHA256:70F316A5492848BB8242D49539468830B353DDAA850964DB4E60A6D2D7DB4880 | |||
| 3756 | UartAssist.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\httpErrorPagesScripts[1] | text | |
MD5:E7CA76A3C9EE0564471671D500E3F0F3 | SHA256:58268CA71A28973B756A48BBD7C9DC2F6B87B62AE343E582CE067C725275B63C | |||
| 3756 | UartAssist.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\http_404_webOC[1] | html | |
MD5:92AB50175C4B03970F264C637C78FEBE | SHA256:3926C545AE82FC264C98D6C229A8A0999E2B59ED2BB736F1BDA9E2F89E0EEAC8 | |||
| 3756 | UartAssist.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\bullet[1] | image | |
MD5:0C4C086DD852704E8EEB8FF83E3B73D1 | SHA256:1CB3B6EA56C5B5DECF5E1D487AD51DBB2F62E6A6C78F23C1C81FDA1B64F8DB16 | |||
| 3756 | UartAssist.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2YPIJ90\background_gradient[1] | image | |
MD5:20F0110ED5E4E0D5384A496E4880139B | SHA256:1471693BE91E53C2640FE7BAEECBC624530B088444222D93F2815DFCE1865D5B | |||
| 3756 | UartAssist.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\info_48[1] | image | |
MD5:49E0EF03E74704089A60C437085DB89E | SHA256:CAA140523BA00994536B33618654E379216261BABAAE726164A0F74157BB11FF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
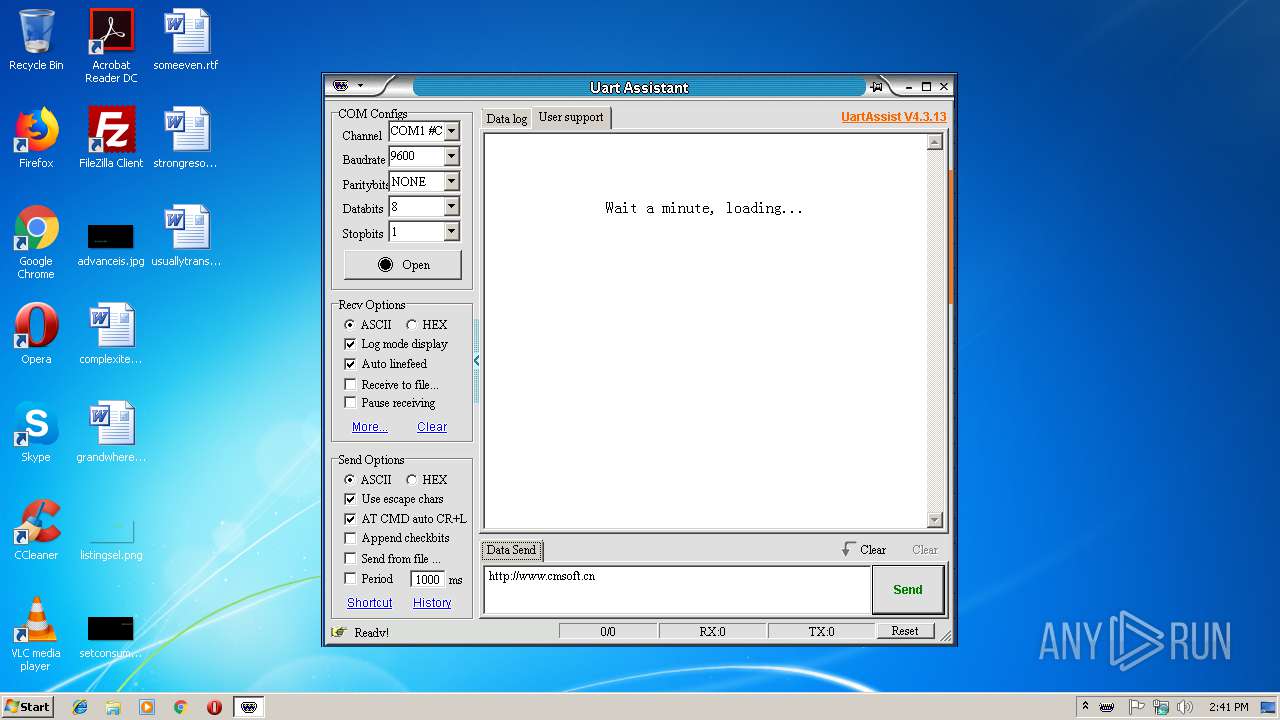
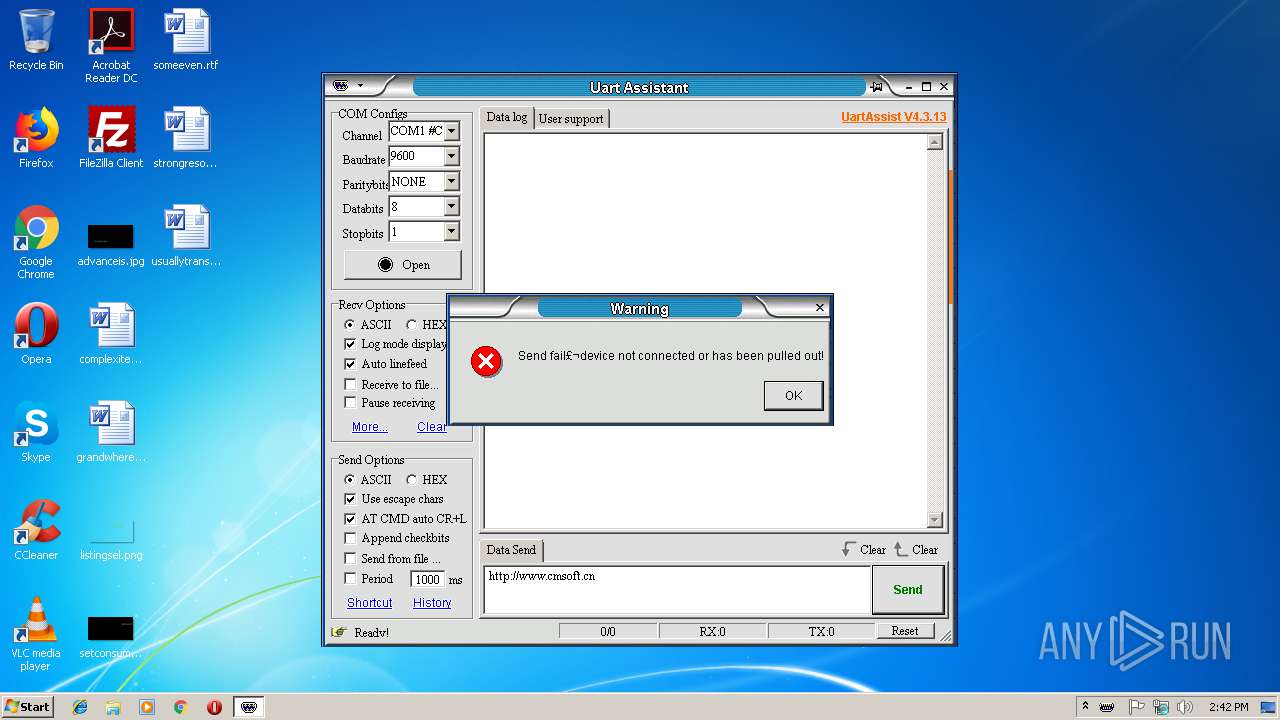
3756 | UartAssist.exe | GET | — | 45.114.11.236:80 | http://www.cmsoft.cn/assistcenter/?target=UartAssist&ver=40313 | HK | — | — | malicious |
3756 | UartAssist.exe | GET | 404 | 45.114.11.236:80 | http://www.cmsoft.cn/assistcenter/uartassist_upgrade/?ver=40313&id=17946 | HK | xml | 345 b | malicious |
3756 | UartAssist.exe | GET | 404 | 45.114.11.236:80 | http://www.cmsoft.cn/assistcenter/?target=UartAssist&ver=40313 | HK | xml | 345 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3756 | UartAssist.exe | 45.114.11.236:80 | www.cmsoft.cn | Cloudie Limited | HK | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cmsoft.cn |
| malicious |