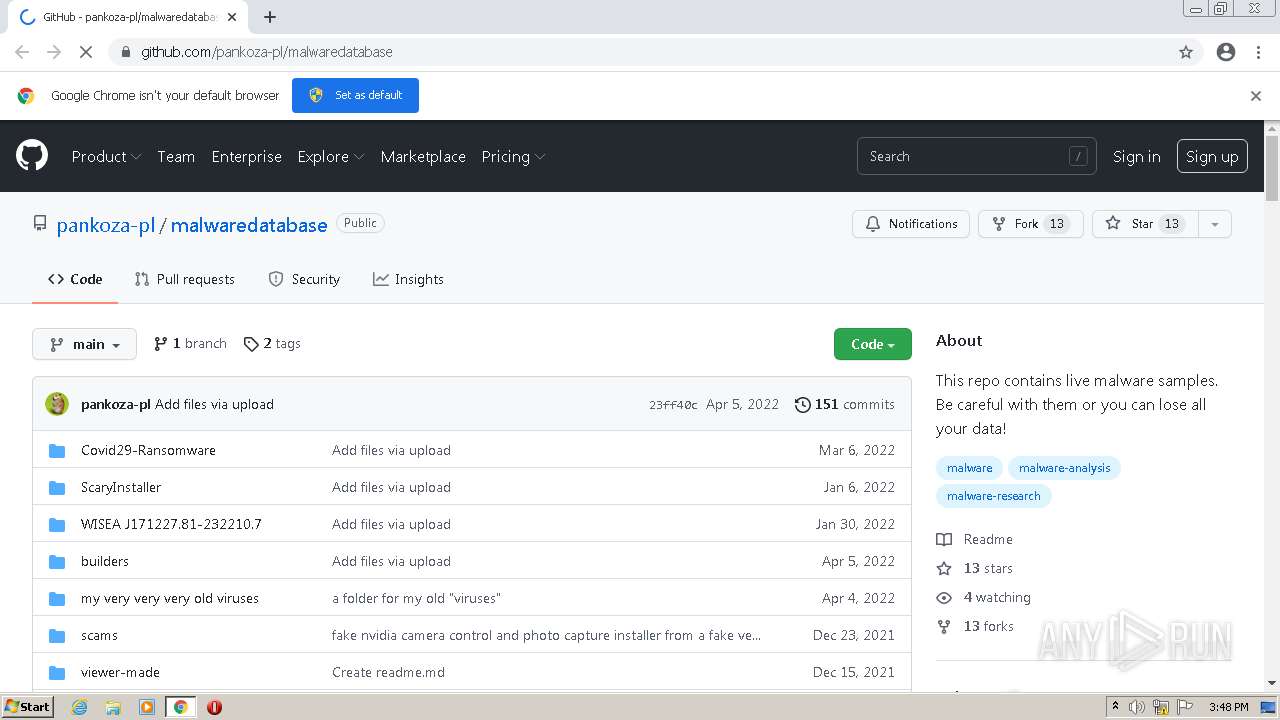
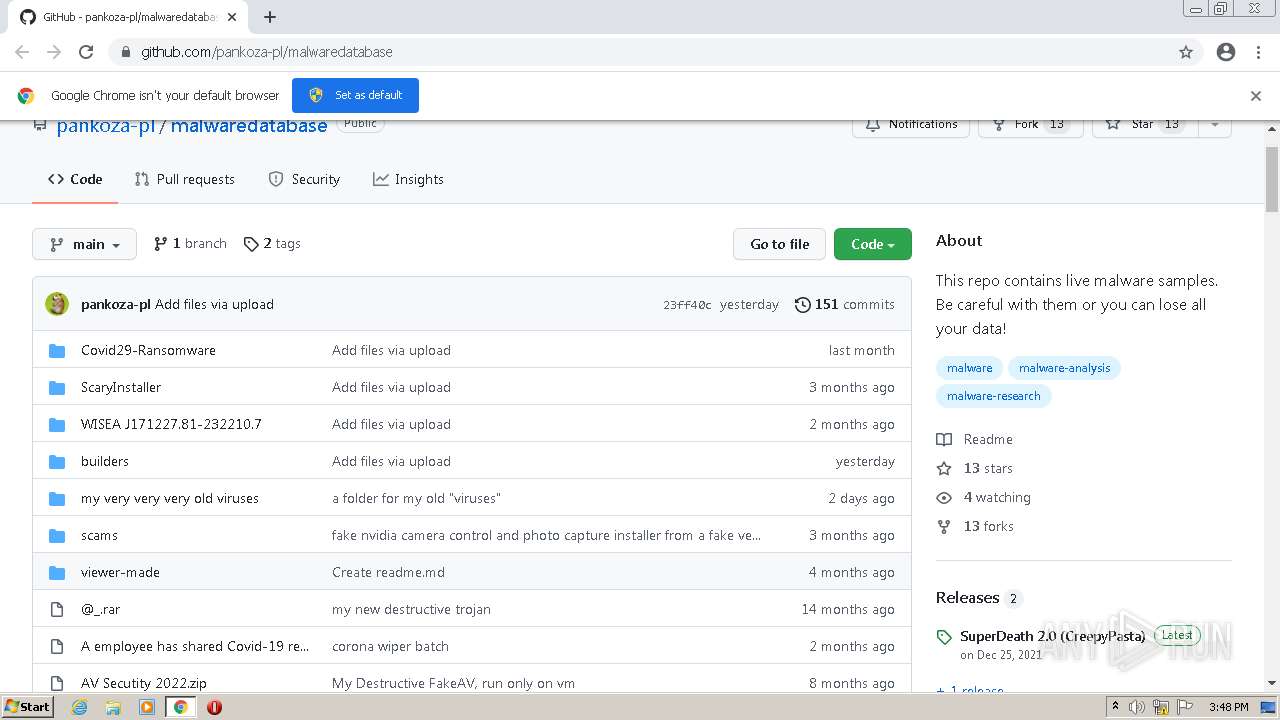
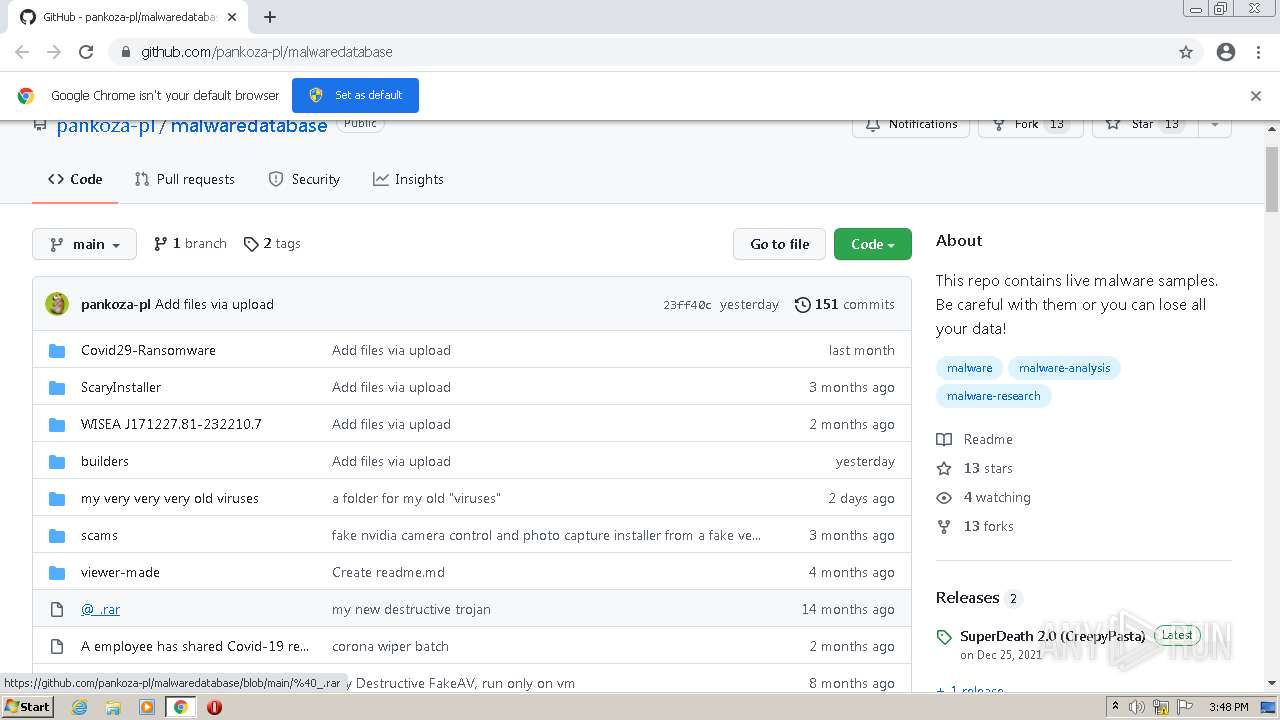
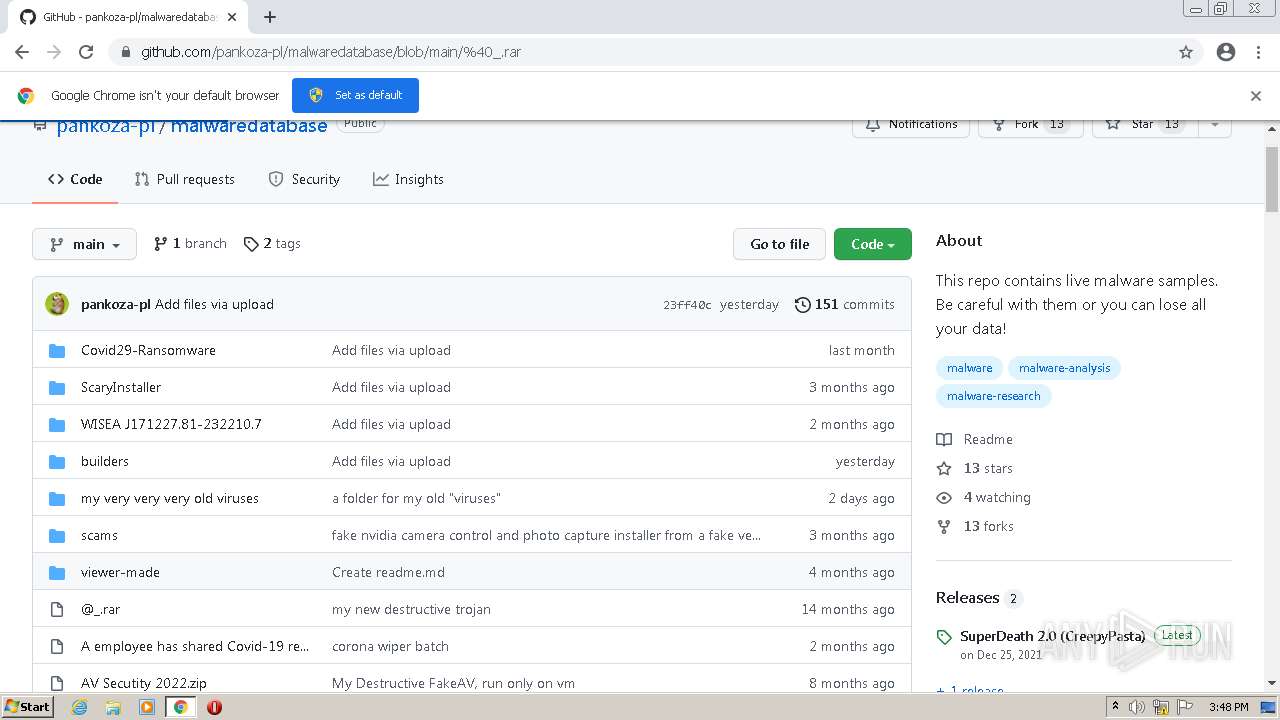
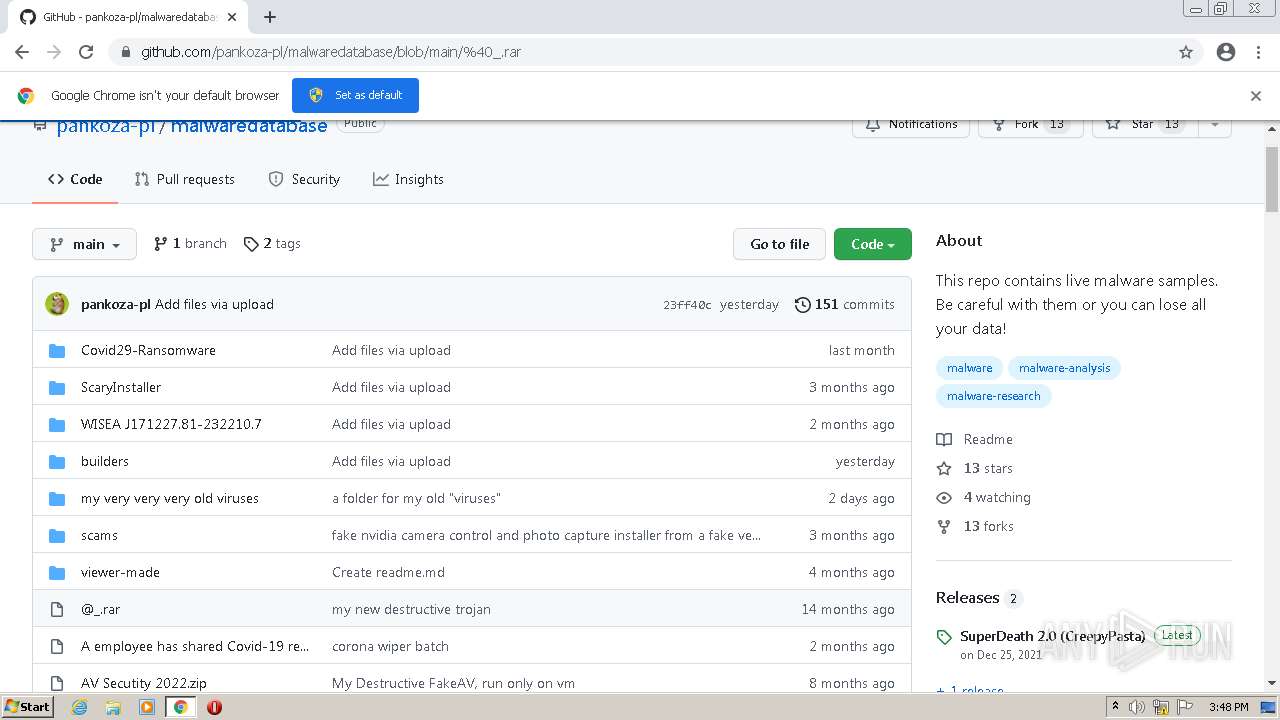
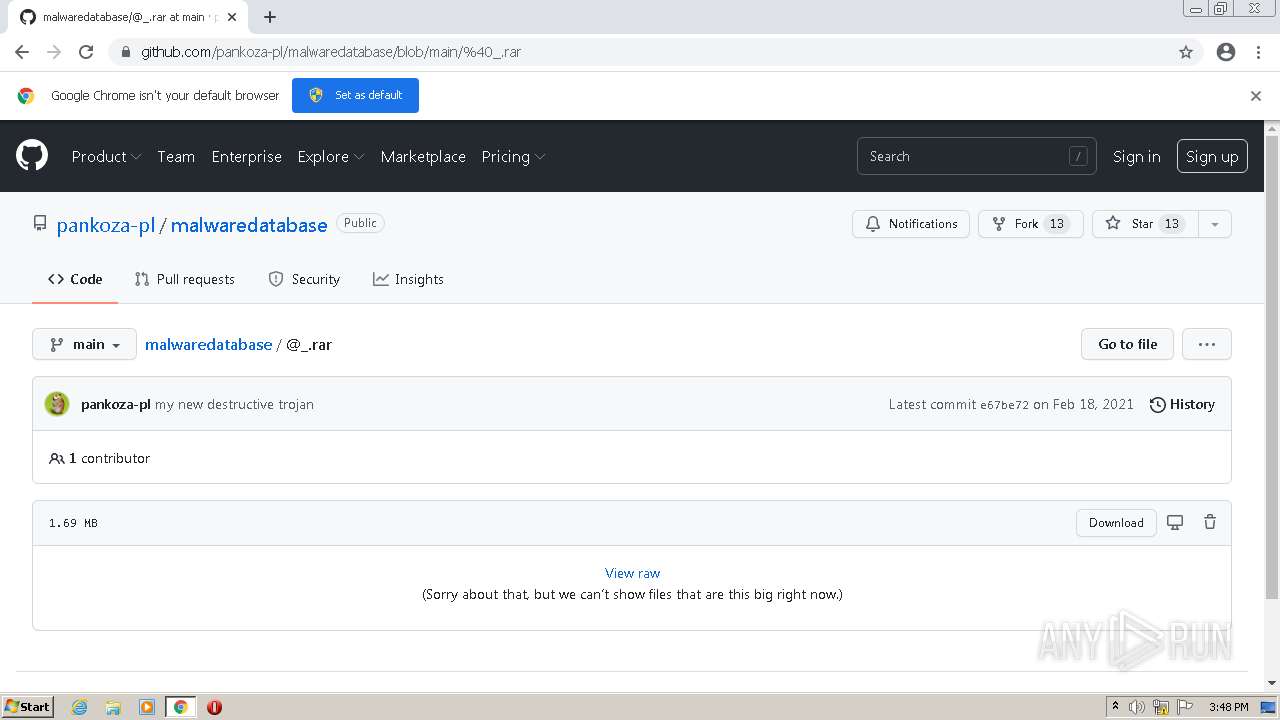
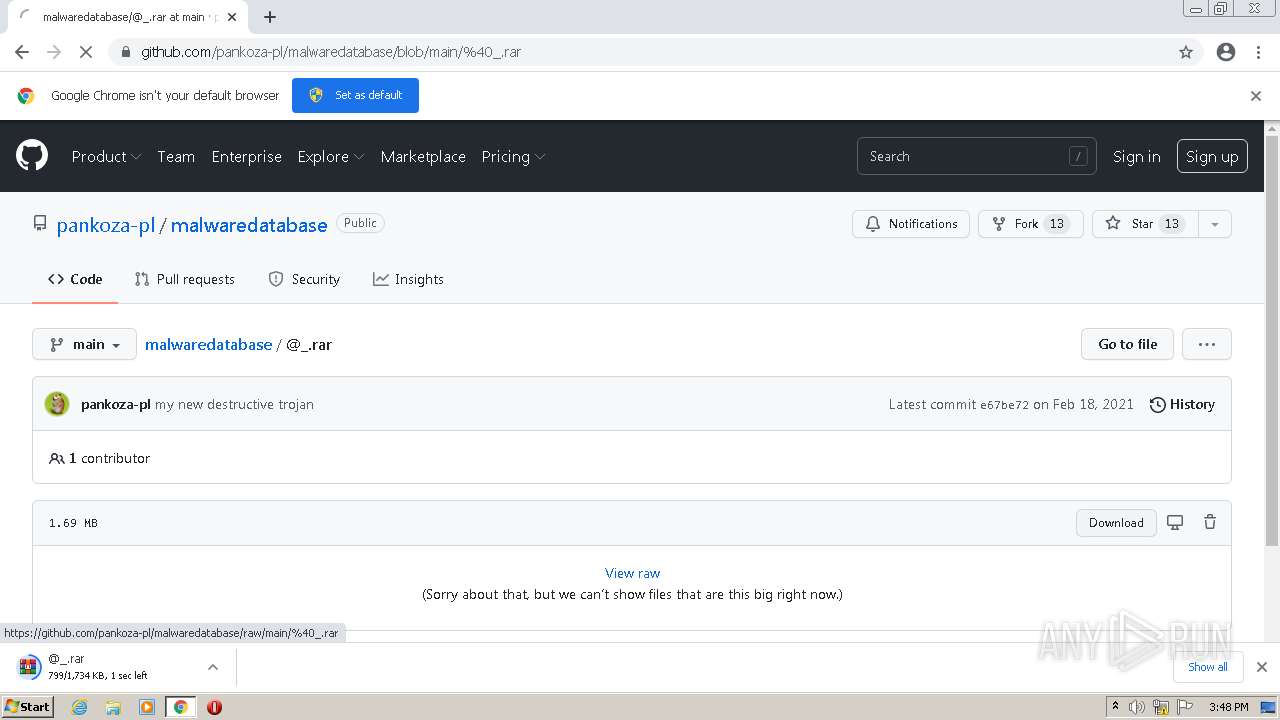
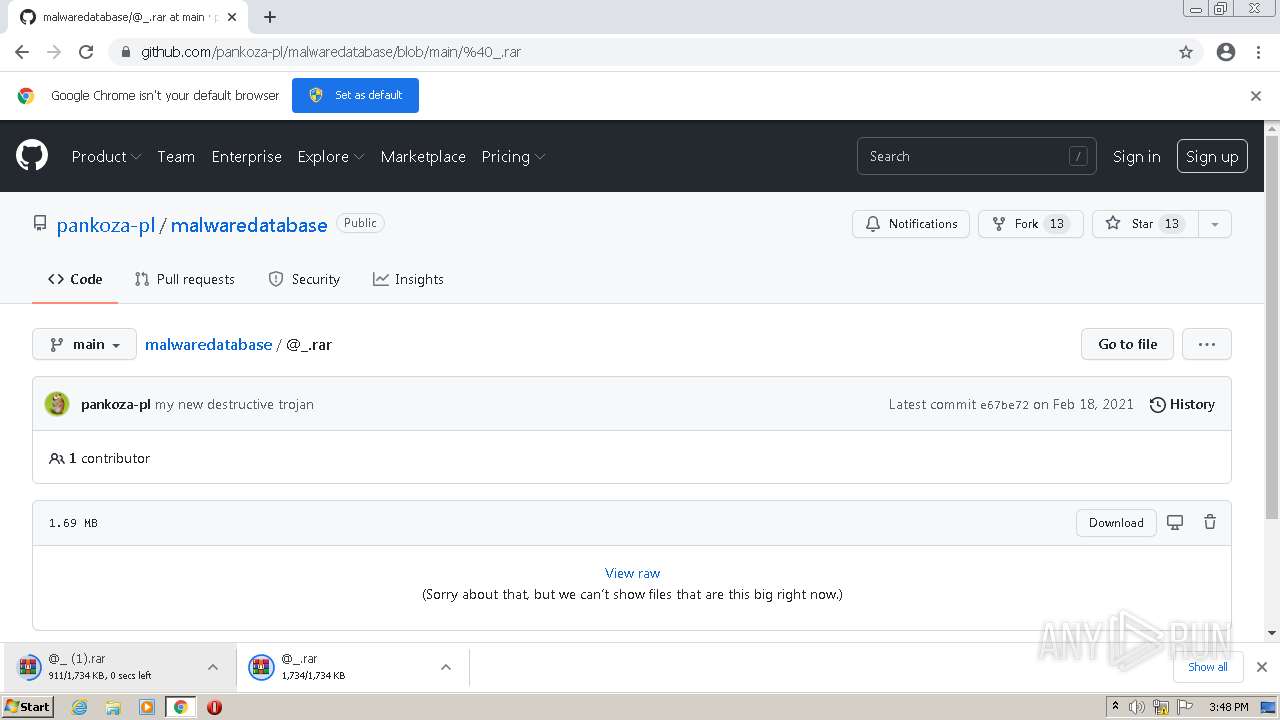
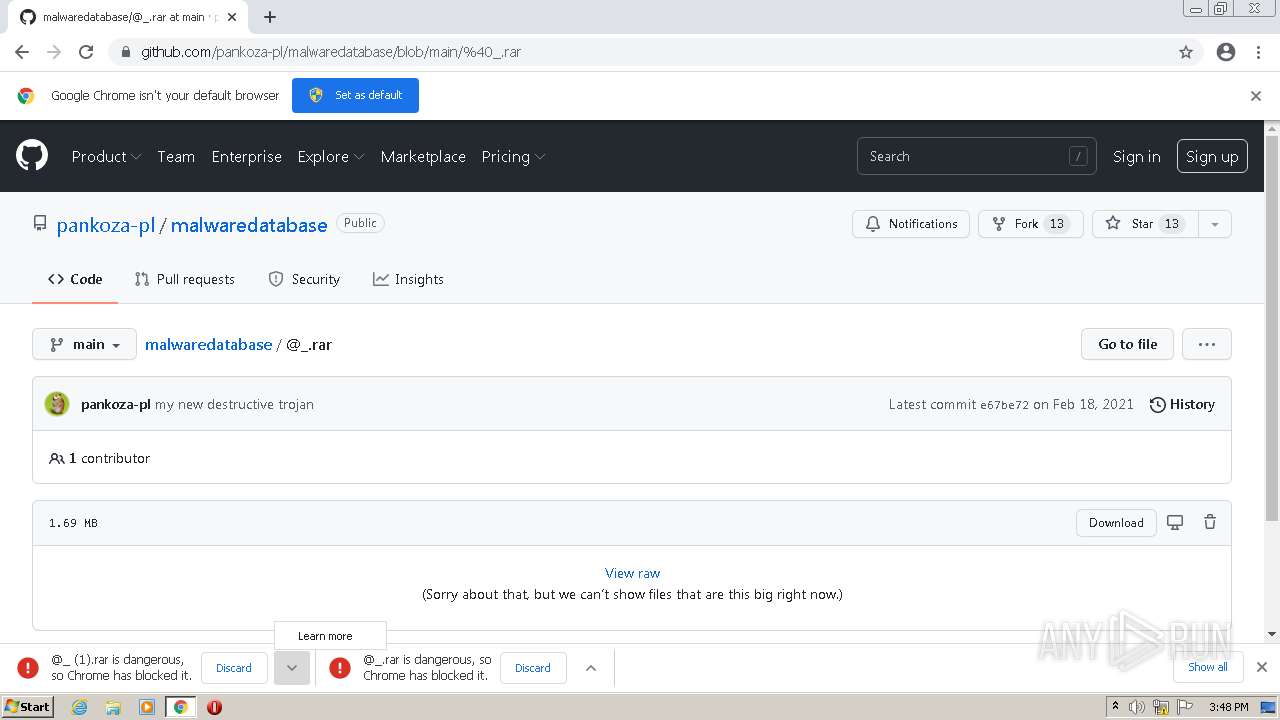
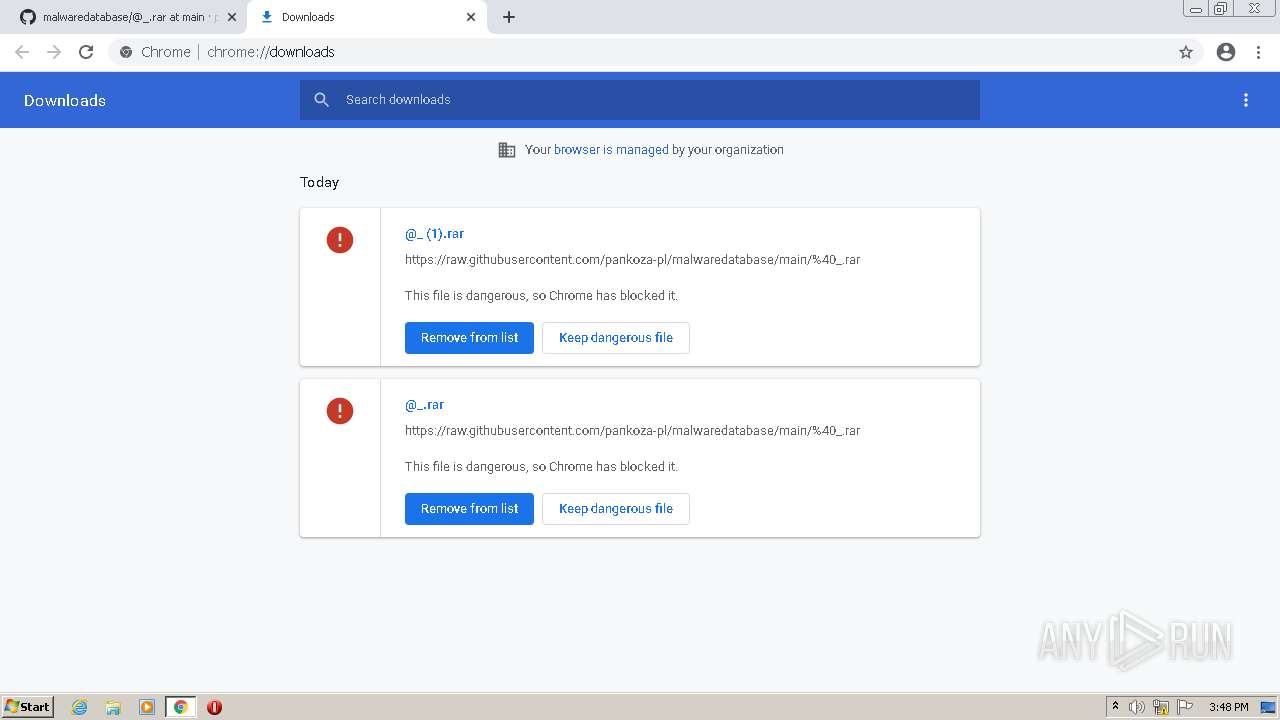
| URL: | https://github.com/pankoza-pl/malwaredatabase |
| Full analysis: | https://app.any.run/tasks/597a89c1-8c56-426a-a66f-c1ea1653a49d |
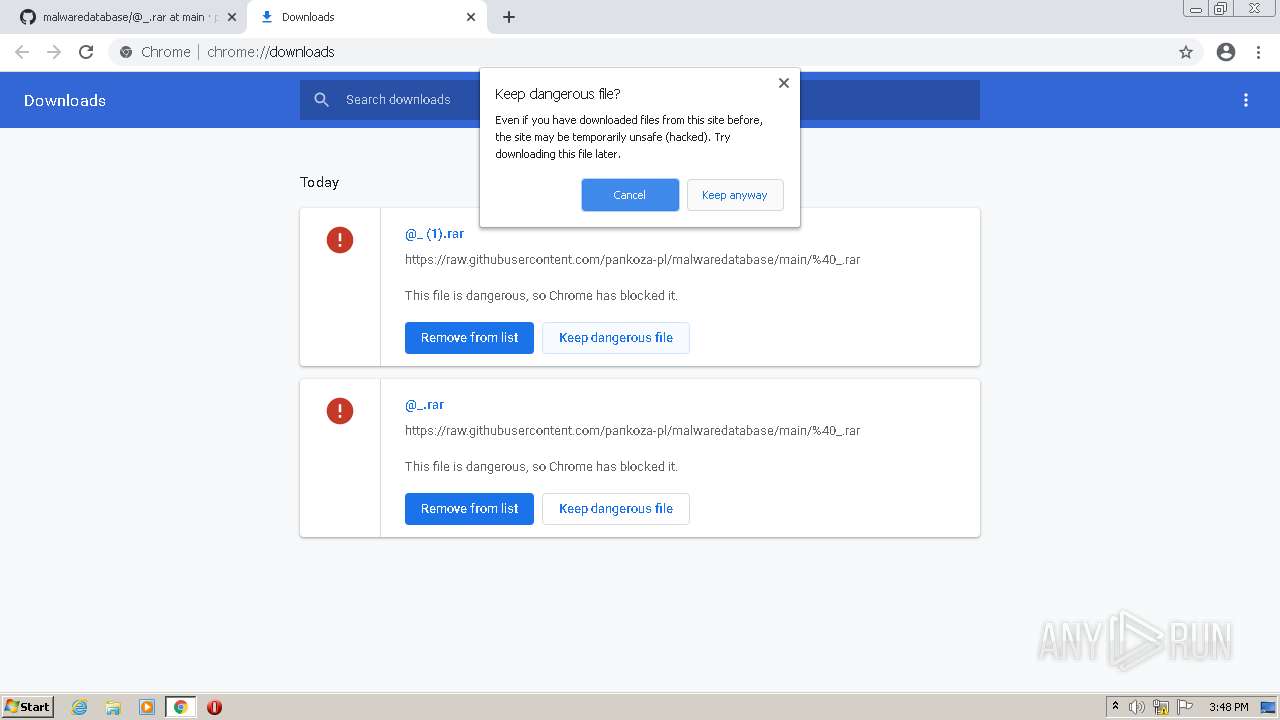
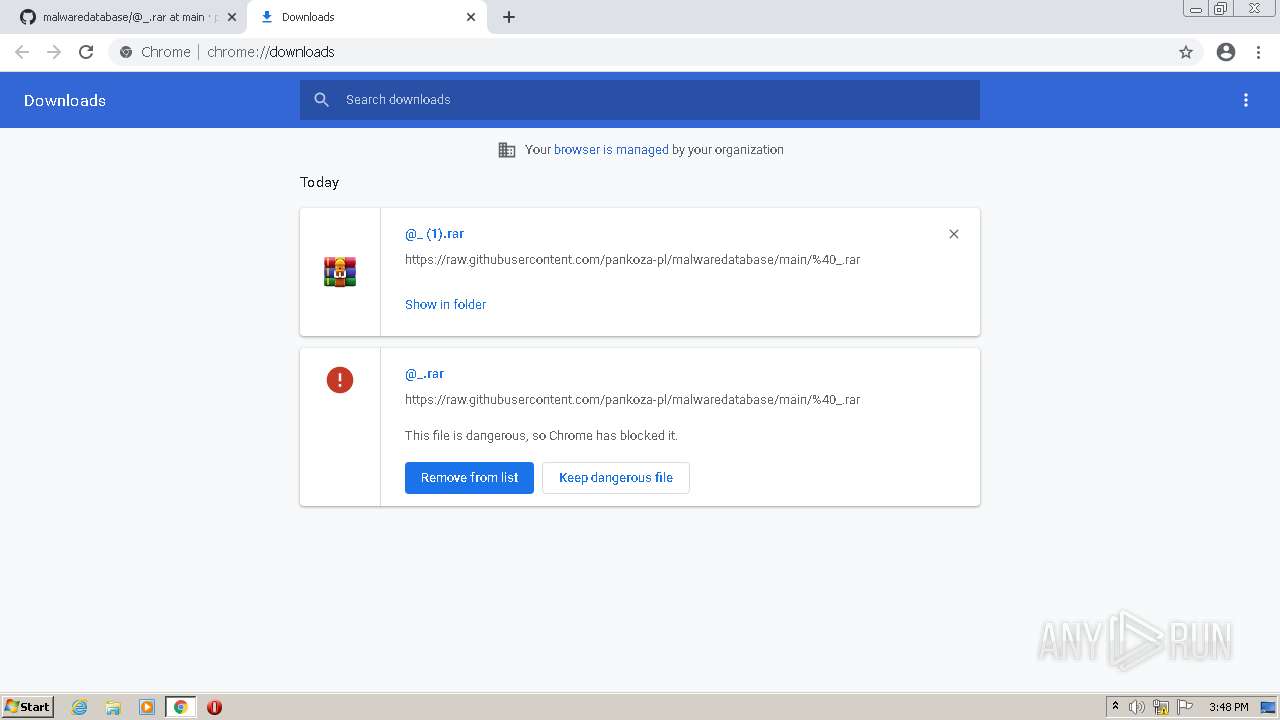
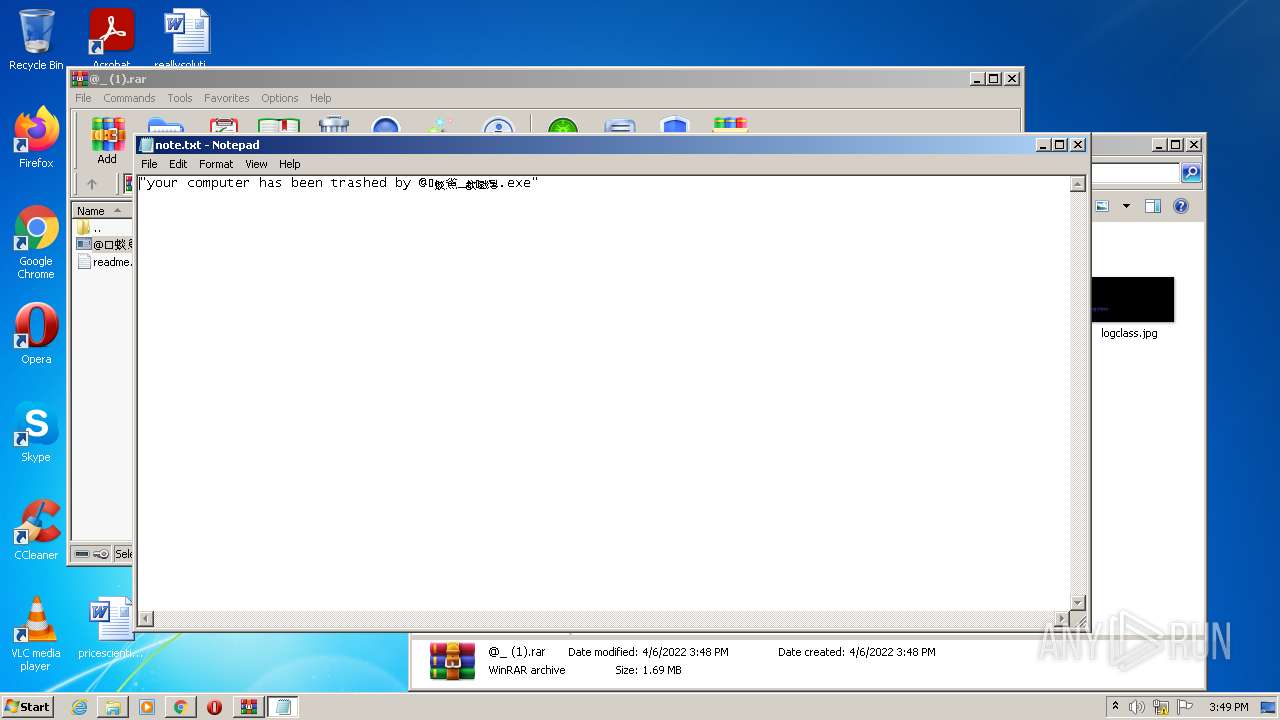
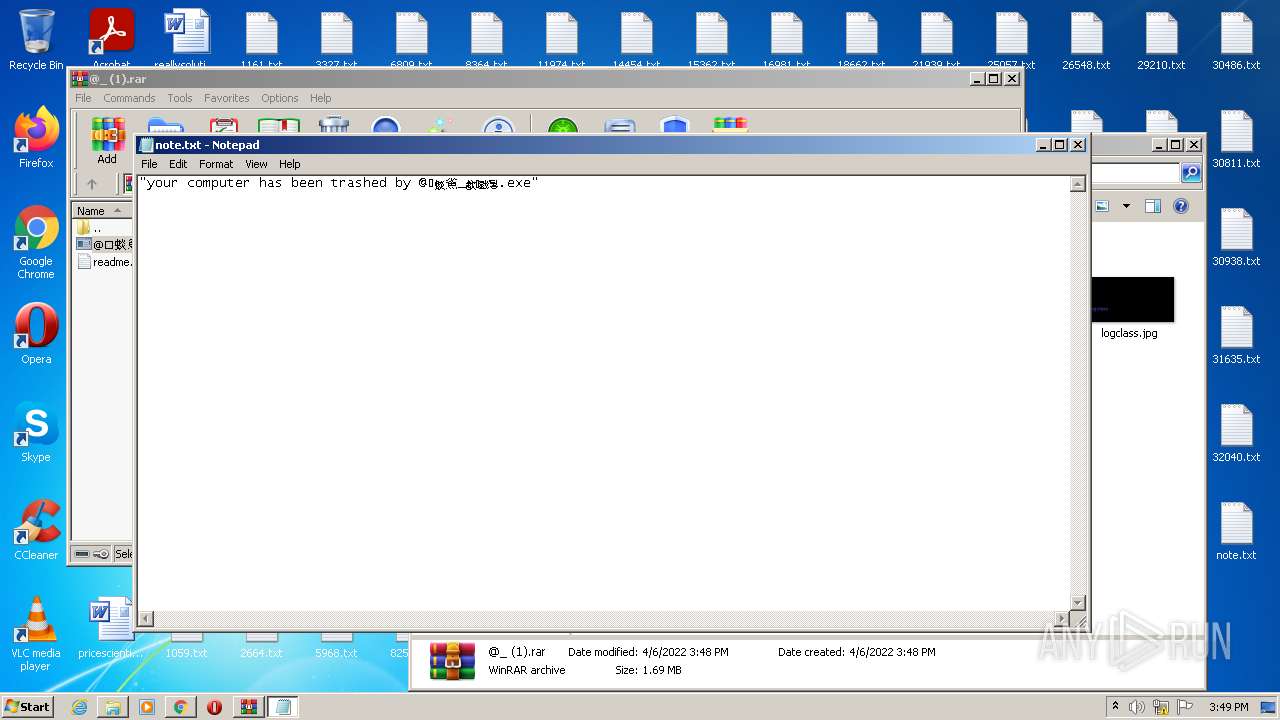
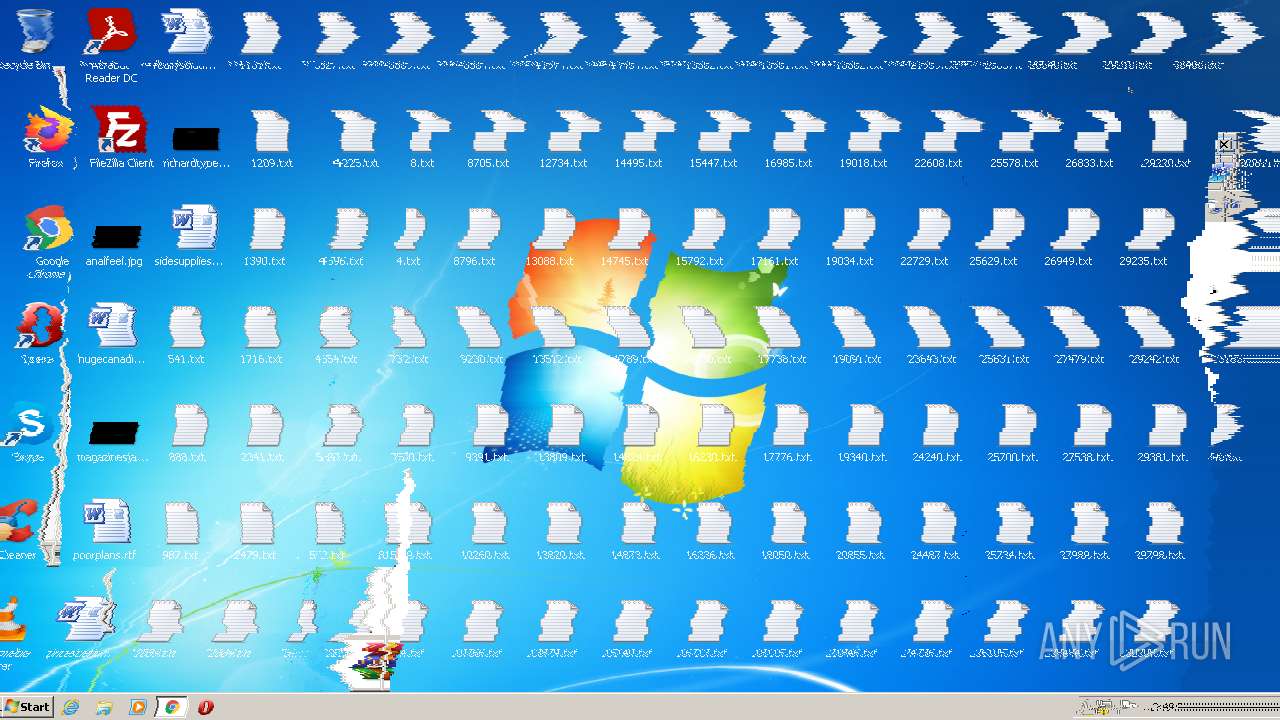
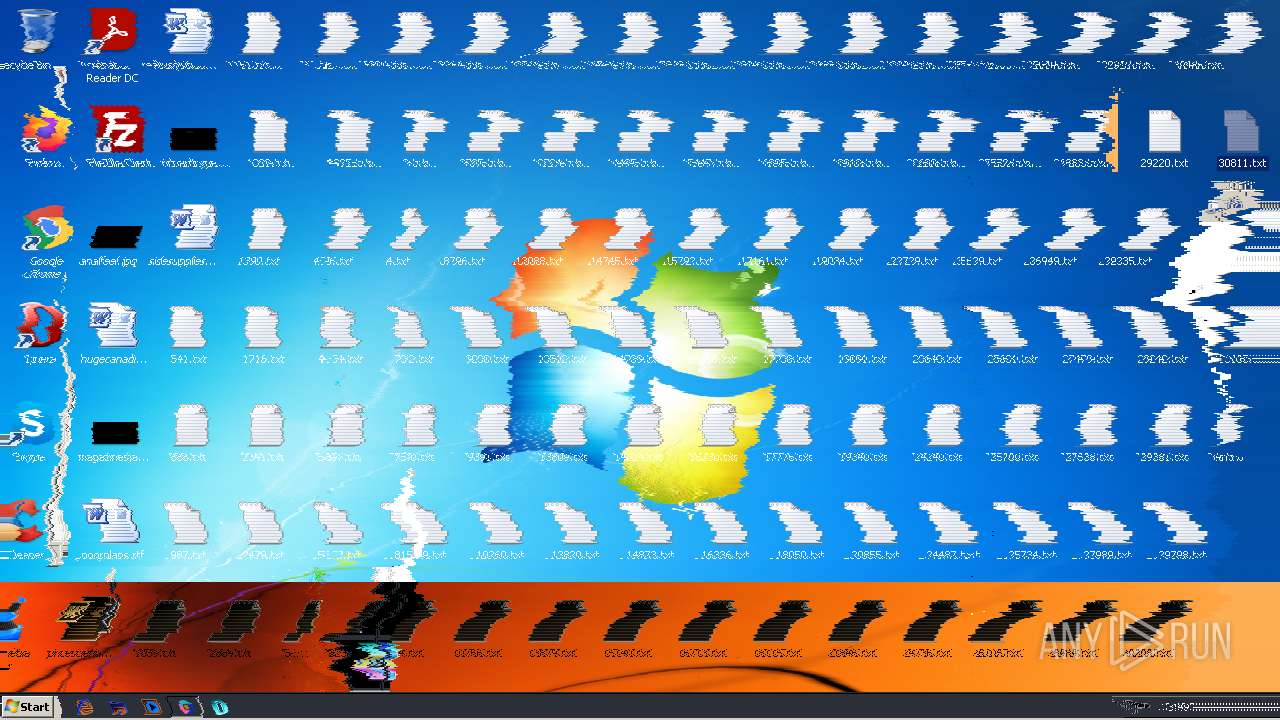
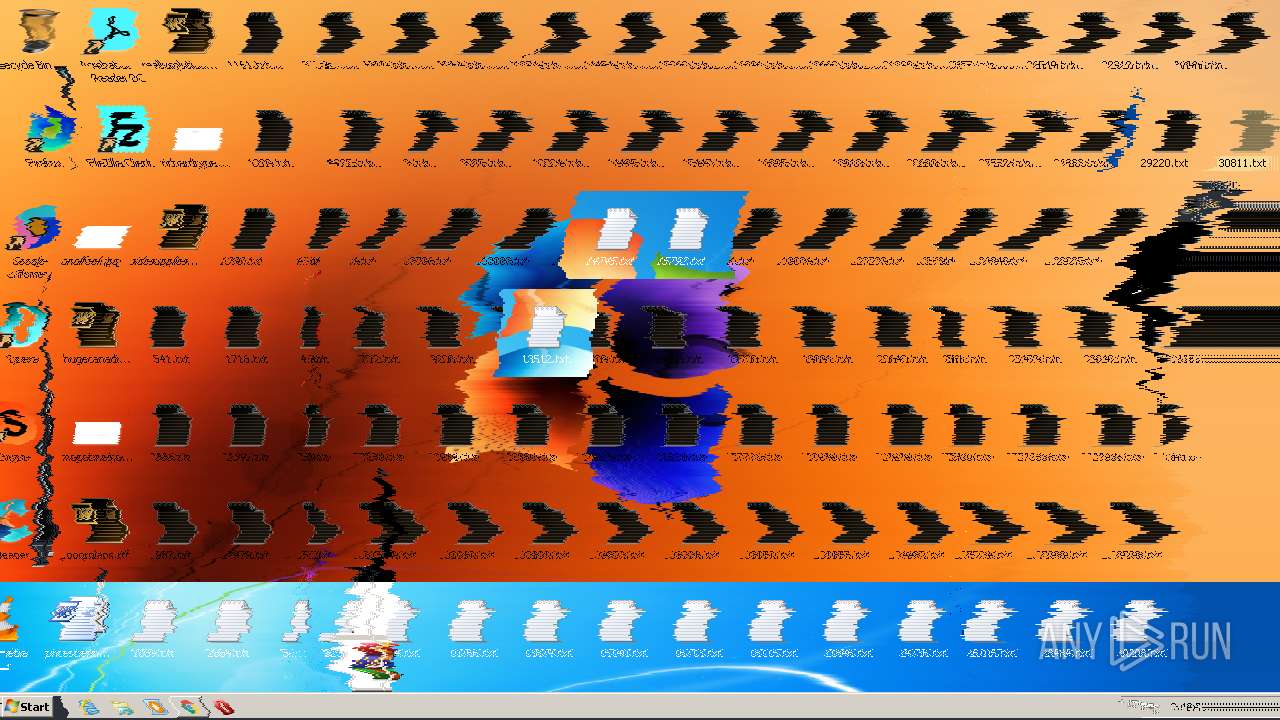
| Verdict: | Malicious activity |
| Analysis date: | April 06, 2022, 14:48:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1CEB493D2EB319B095BE59826131B050 |
| SHA1: | 546E492CF8FF384A8614A0E751CFB8A639DF804B |
| SHA256: | C44486C41CE9FF15A10A1A307FA249F8985C39D30B799B0A8226AD2EE68DBFA7 |
| SSDEEP: | 3:N8tEdlELlfVKIXKRj:2uoLFN6j |
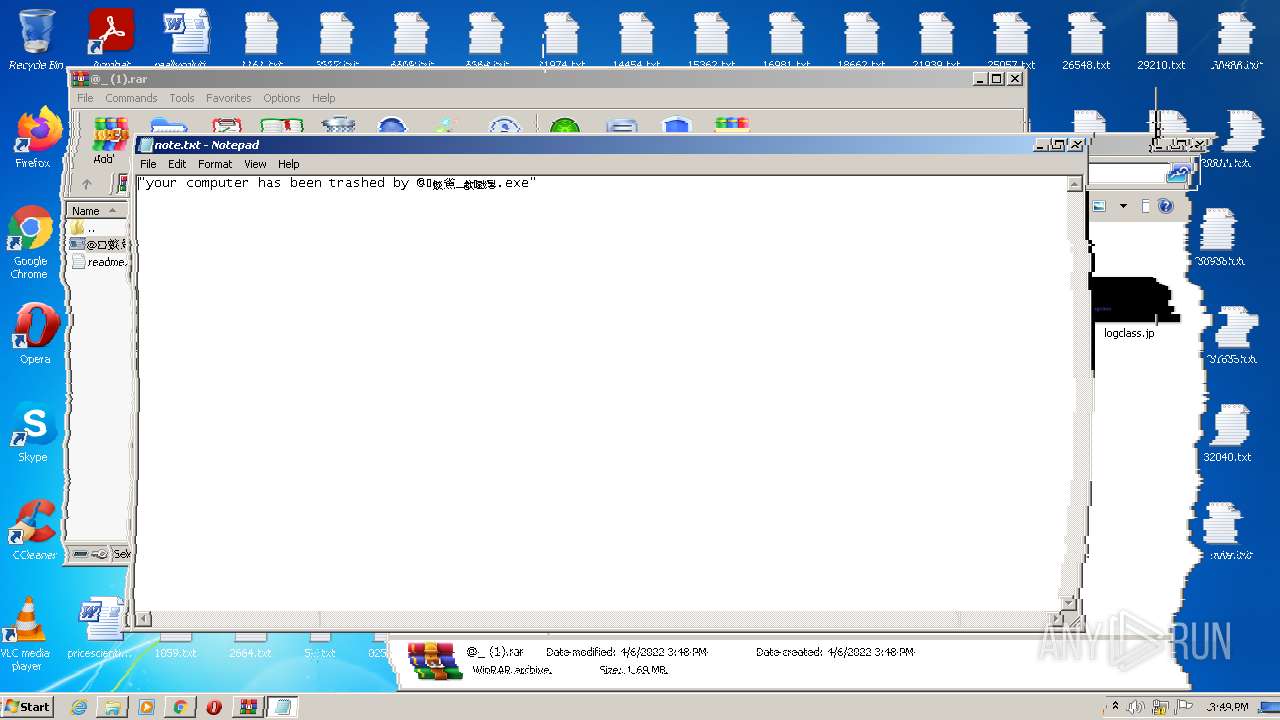
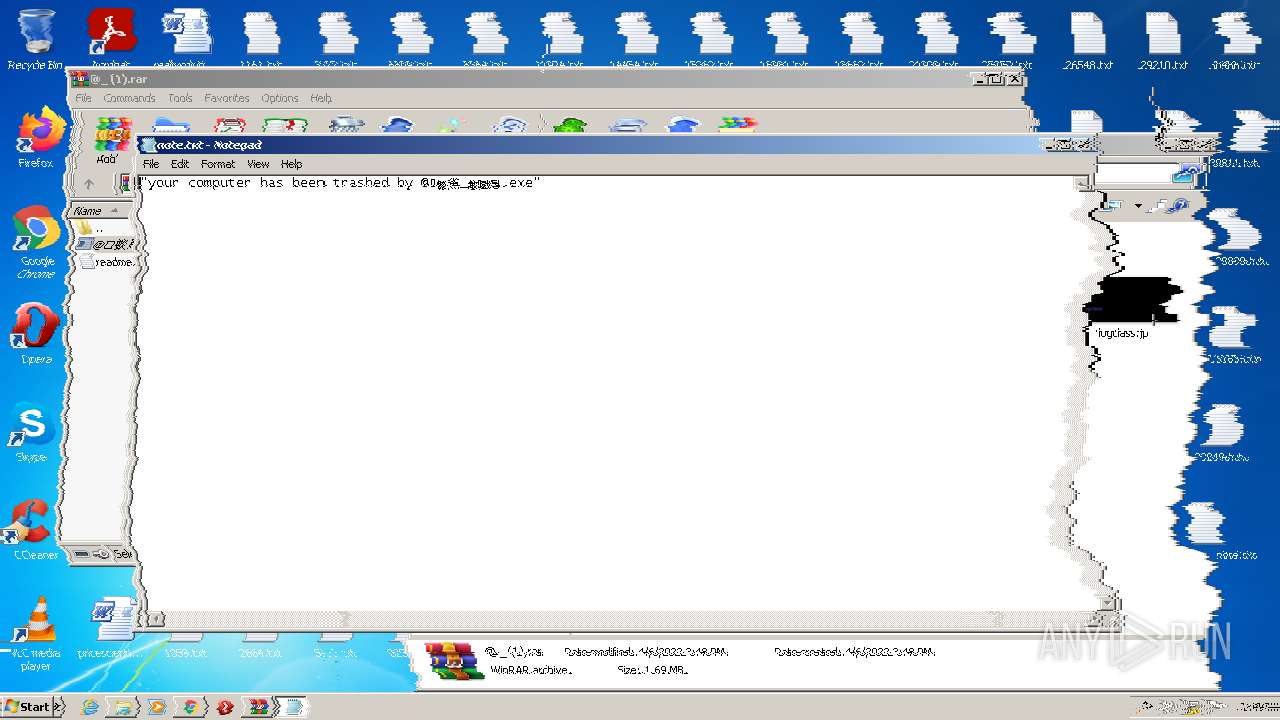
MALICIOUS
Application was dropped or rewritten from another process
- @䗊𤍳_㱃ͷ戥̍뒿.exe (PID: 3008)
- @䗊𤍳_㱃ͷ戥̍뒿.exe (PID: 2944)
- MBRKill.exe (PID: 3640)
- waves.exe (PID: 1868)
- inv.exe (PID: 3324)
Drops executable file immediately after starts
- @䗊𤍳_㱃ͷ戥̍뒿.exe (PID: 2944)
Uses Task Scheduler to run other applications
- MBRKill.exe (PID: 3640)
Changes the autorun value in the registry
- MBRKill.exe (PID: 3640)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3712)
Task Manager has been disabled (taskmgr)
- reg.exe (PID: 2932)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2672)
- @䗊𤍳_㱃ͷ戥̍뒿.exe (PID: 2944)
- MBRKill.exe (PID: 3640)
- vlc.exe (PID: 2324)
- cmd.exe (PID: 3220)
- waves.exe (PID: 1868)
- inv.exe (PID: 3324)
Reads the computer name
- WinRAR.exe (PID: 2672)
- @䗊𤍳_㱃ͷ戥̍뒿.exe (PID: 2944)
- cmd.exe (PID: 3220)
- vlc.exe (PID: 2324)
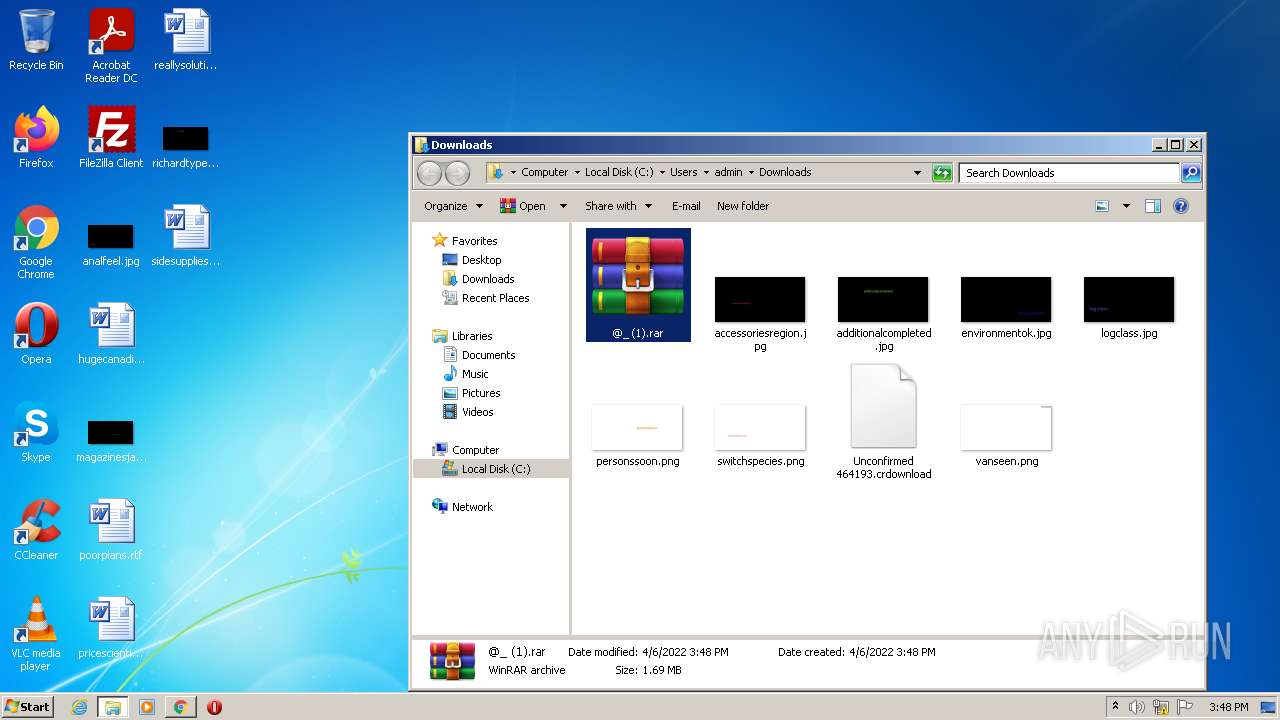
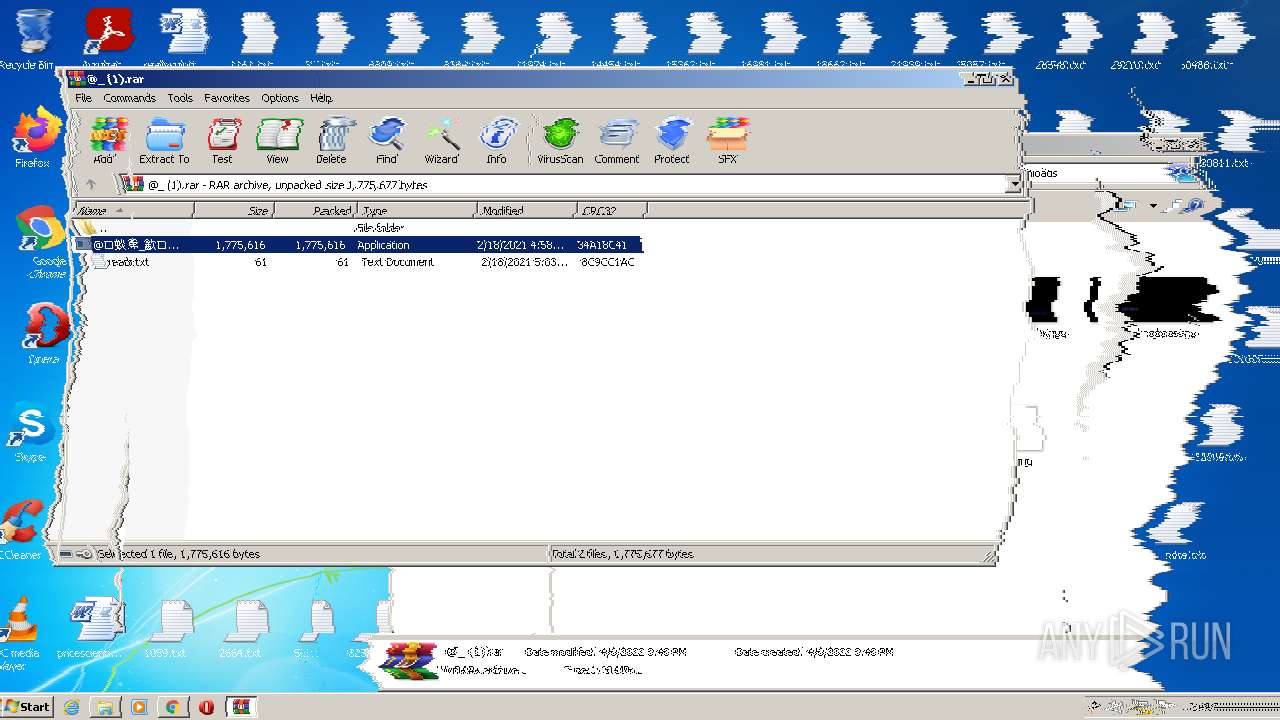
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2672)
- @䗊𤍳_㱃ͷ戥̍뒿.exe (PID: 2944)
Drops a file with too old compile date
- @䗊𤍳_㱃ͷ戥̍뒿.exe (PID: 2944)
Drops a file that was compiled in debug mode
- @䗊𤍳_㱃ͷ戥̍뒿.exe (PID: 2944)
Starts CMD.EXE for commands execution
- @䗊𤍳_㱃ͷ戥̍뒿.exe (PID: 2944)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3220)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 3220)
Creates files in the user directory
- vlc.exe (PID: 2324)
INFO
Checks supported languages
- chrome.exe (PID: 3096)
- chrome.exe (PID: 528)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 1608)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 1320)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 1088)
- chrome.exe (PID: 2416)
- chrome.exe (PID: 3224)
- NOTEPAD.EXE (PID: 3076)
- bcdedit.exe (PID: 984)
- schtasks.exe (PID: 3712)
- reg.exe (PID: 2932)
- reg.exe (PID: 1448)
- timeout.exe (PID: 3744)
- NOTEPAD.EXE (PID: 3024)
- rundll32.exe (PID: 2784)
- chrome.exe (PID: 3232)
- timeout.exe (PID: 808)
- chrome.exe (PID: 368)
- timeout.exe (PID: 2624)
Application launched itself
- chrome.exe (PID: 3096)
Reads the computer name
- chrome.exe (PID: 528)
- chrome.exe (PID: 3096)
- chrome.exe (PID: 1608)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 2416)
- schtasks.exe (PID: 3712)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 368)
Reads the hosts file
- chrome.exe (PID: 3096)
- chrome.exe (PID: 1608)
Reads settings of System Certificates
- chrome.exe (PID: 1608)
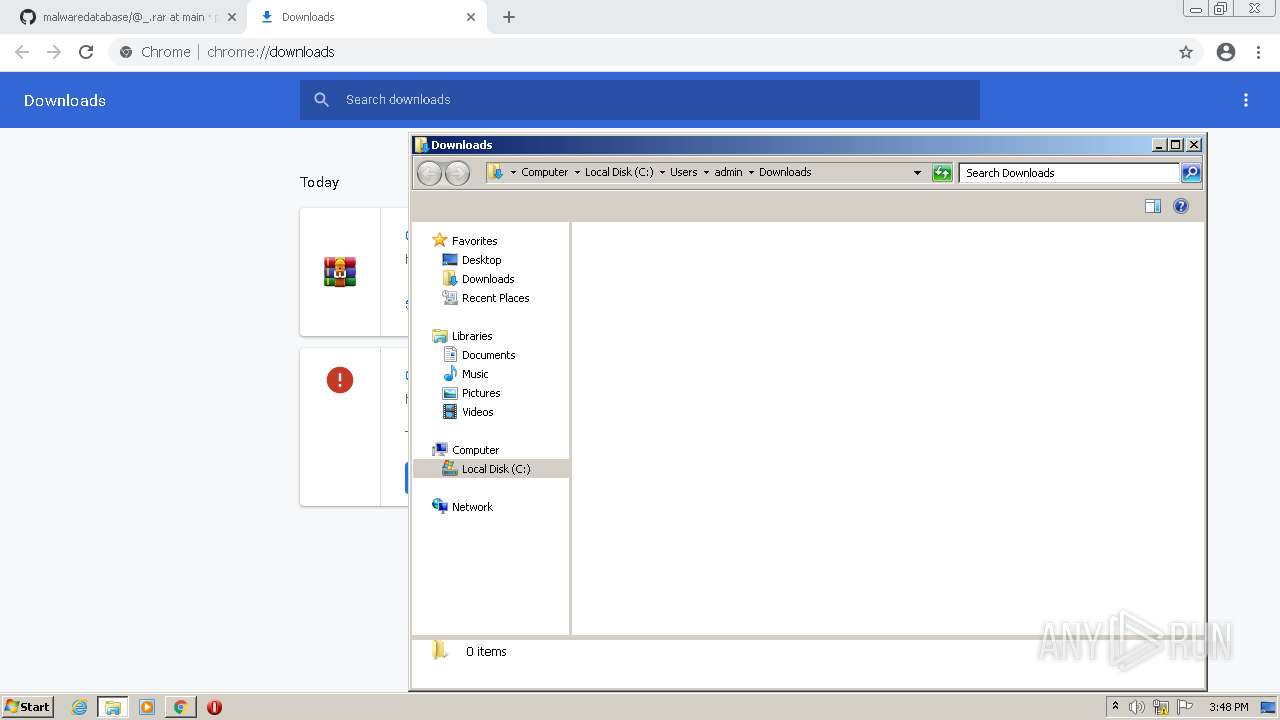
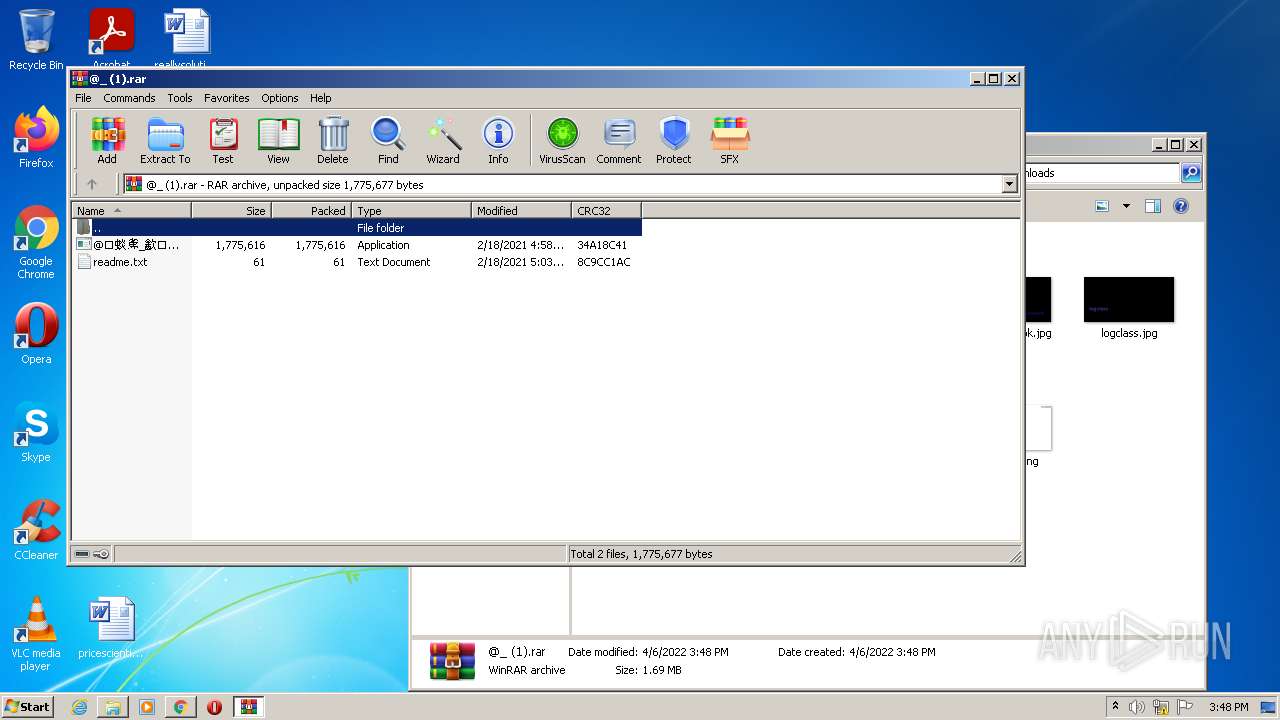
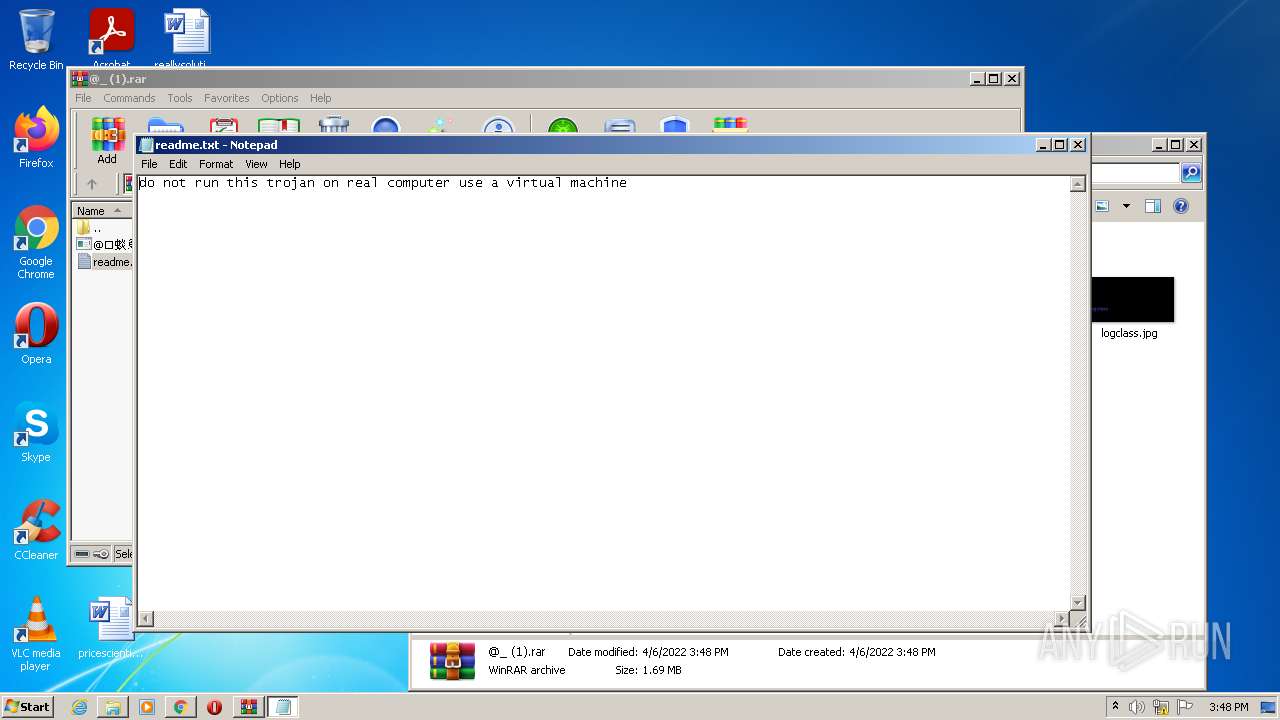
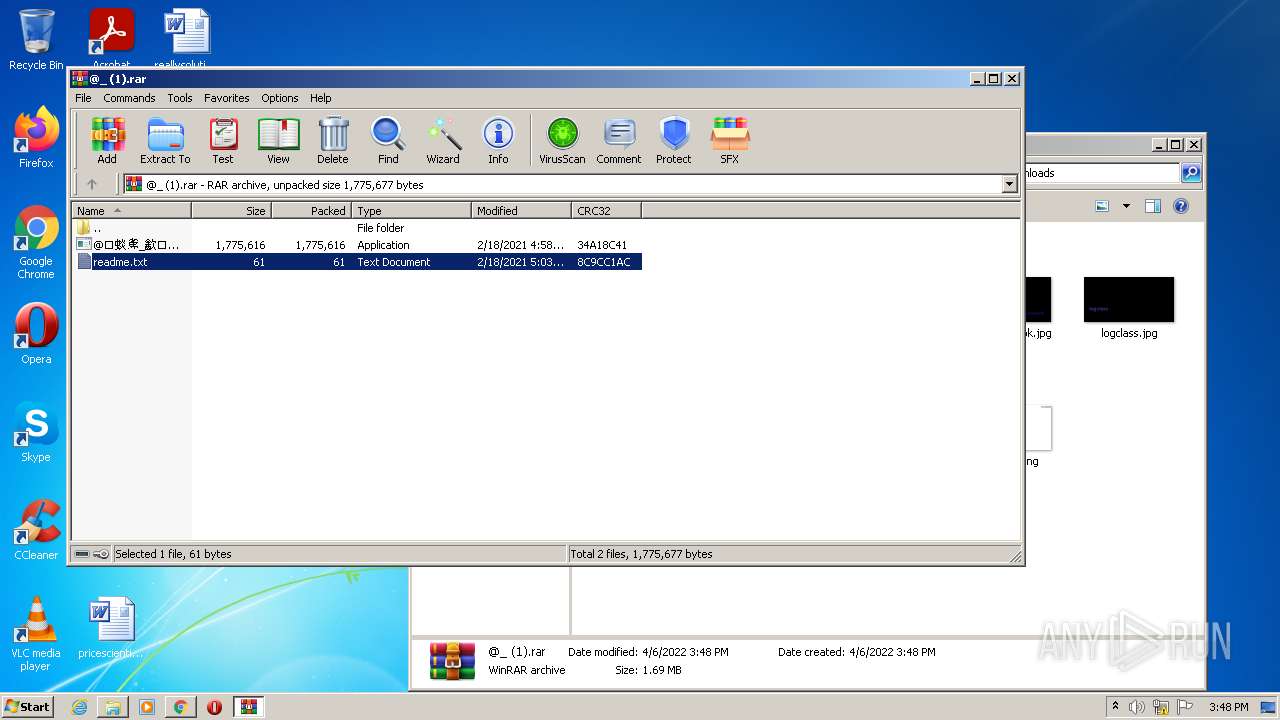
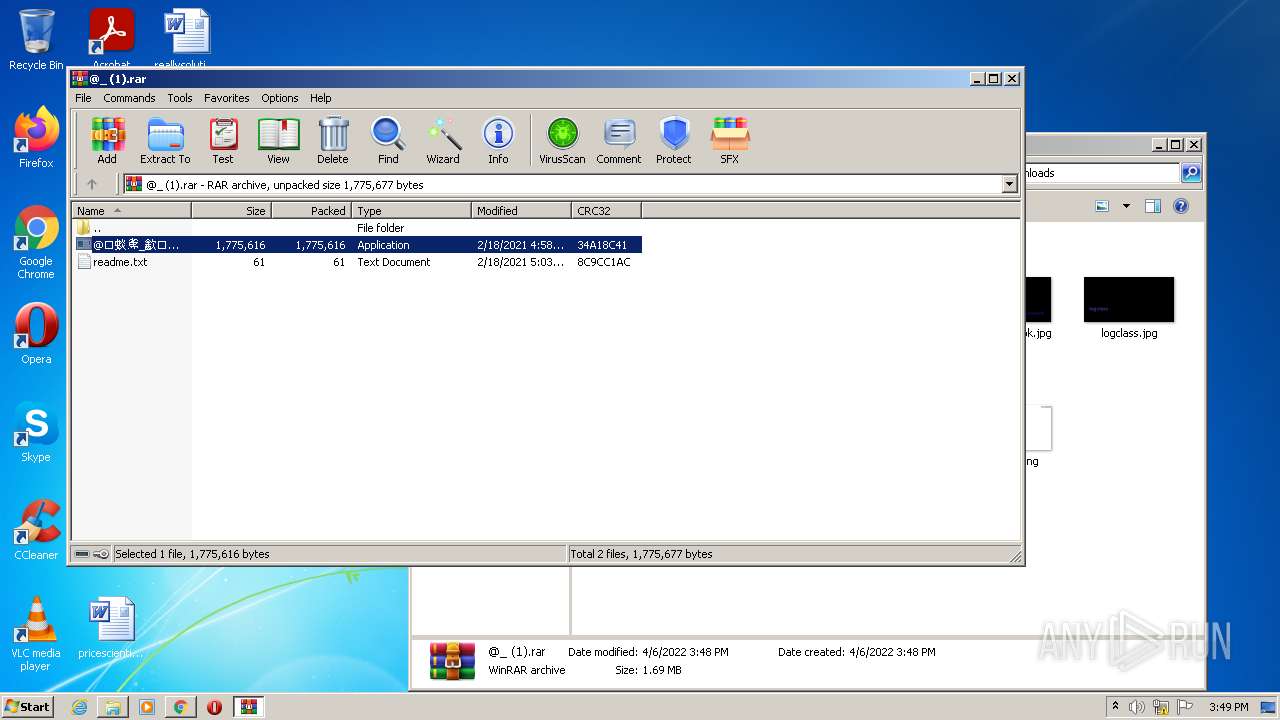
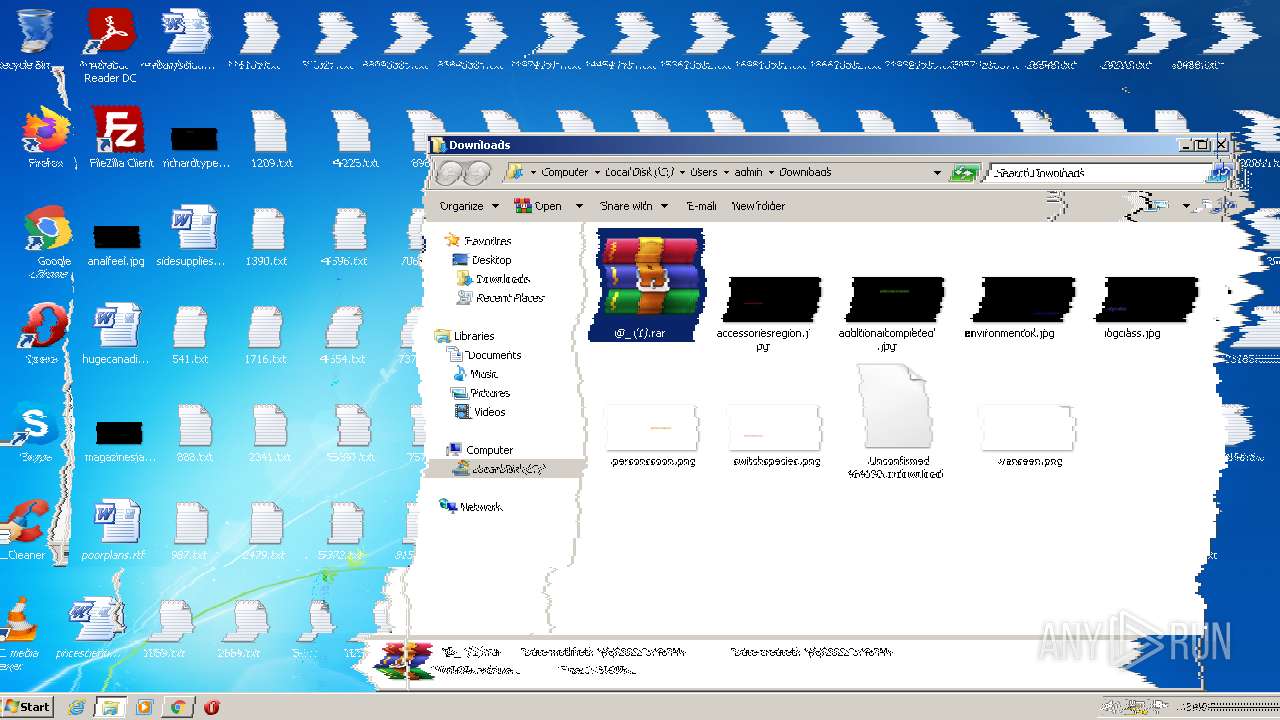
Manual execution by user
- WinRAR.exe (PID: 2672)
Reads the date of Windows installation
- chrome.exe (PID: 368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
34
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,9984270442166682933,11026177734246081250,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=732 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,9984270442166682933,11026177734246081250,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1064 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 808 | timeout 5 /nobreak | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 984 | bcdedit /delete {current} | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,9984270442166682933,11026177734246081250,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,9984270442166682933,11026177734246081250,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1832 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1448 | reg delete "HKCU\Control Panel\Desktop" /v Wallpaper /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1044,9984270442166682933,11026177734246081250,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1316 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1868 | waves.exe | C:\Users\admin\AppData\Local\Temp\D9E8.tmp\waves.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
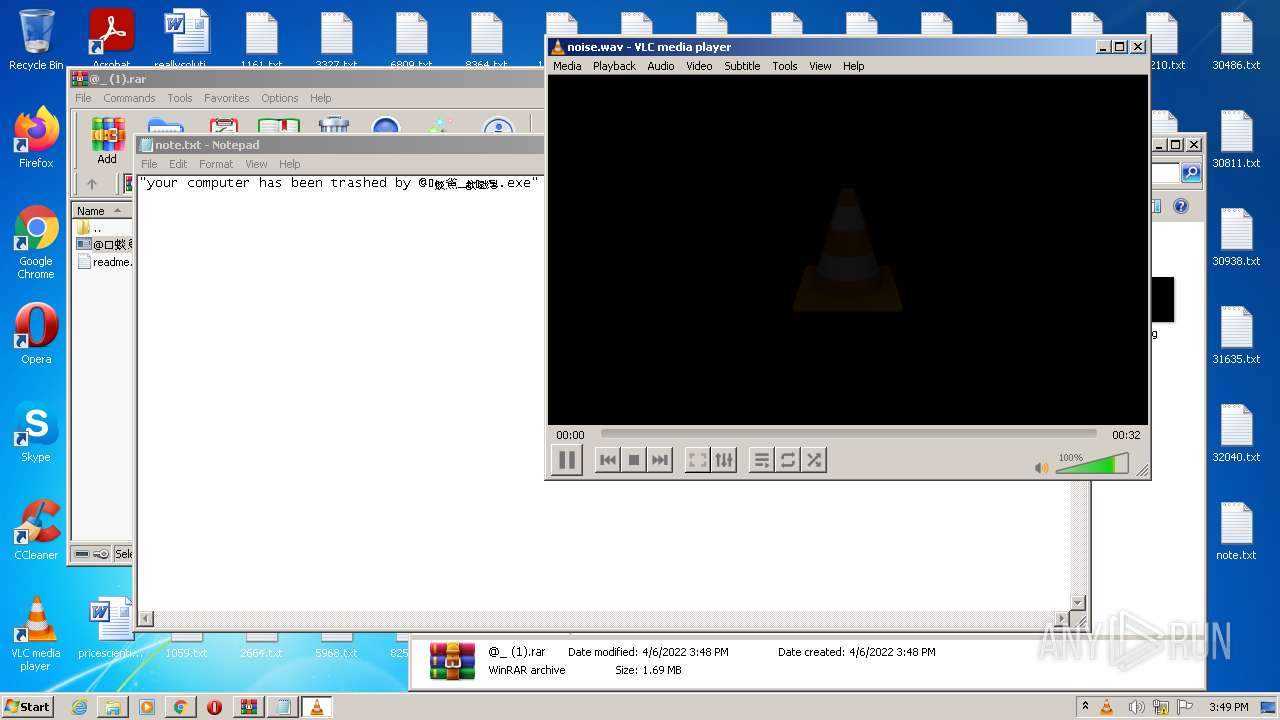
| 2324 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\AppData\Local\Temp\D9E8.tmp\noise.wav" | C:\Program Files\VideoLAN\VLC\vlc.exe | cmd.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: HIGH Description: VLC media player Exit code: 0 Version: 3.0.11 Modules
| |||||||||||||||
Total events
16 476
Read events
16 303
Write events
141
Delete events
32
Modification events
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
8
Suspicious files
21
Text files
179
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-624DA83A-C18.pma | — | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5f7a6629-9bab-4b58-b7dd-5f1e03f0c740.tmp | text | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF135027.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF135036.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1351ec.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF135036.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF1352f5.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
39
DNS requests
15
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1608 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 142.250.186.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
— | — | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
1608 | chrome.exe | 142.250.185.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1608 | chrome.exe | 142.250.185.234:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
1608 | chrome.exe | 142.250.186.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1608 | chrome.exe | 140.82.121.5:443 | api.github.com | — | US | suspicious |
1608 | chrome.exe | 142.250.184.206:443 | safebrowsing.google.com | Google Inc. | US | whitelisted |
1608 | chrome.exe | 142.250.186.46:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1608 | chrome.exe | 140.82.121.4:443 | github.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
github.com |
| malicious |
accounts.google.com |
| shared |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
user-images.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
collector.github.com |
| whitelisted |
Threats
Process | Message |
|---|---|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=i686-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=i686-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x86/contrib/i686-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc error: stale plugins cache: modified C:\Program Files\VideoLAN\VLC\plugins\access\libaccess_concat_plugin.dll
|