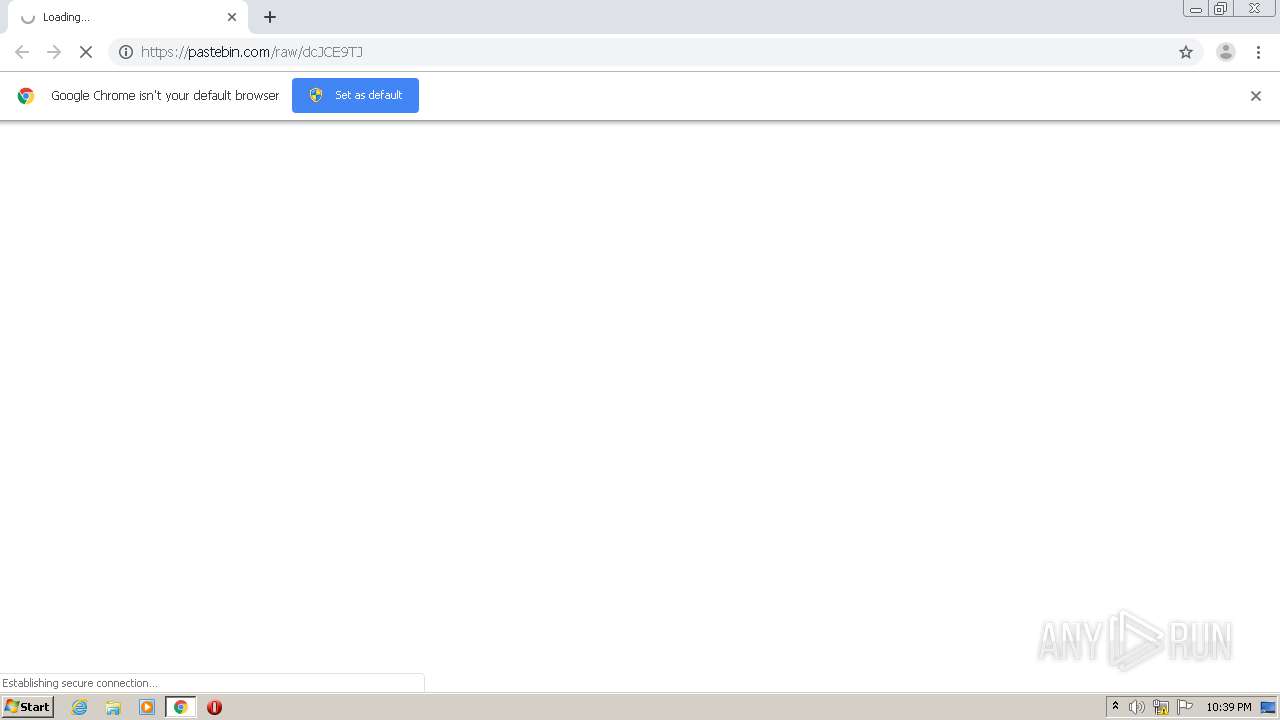
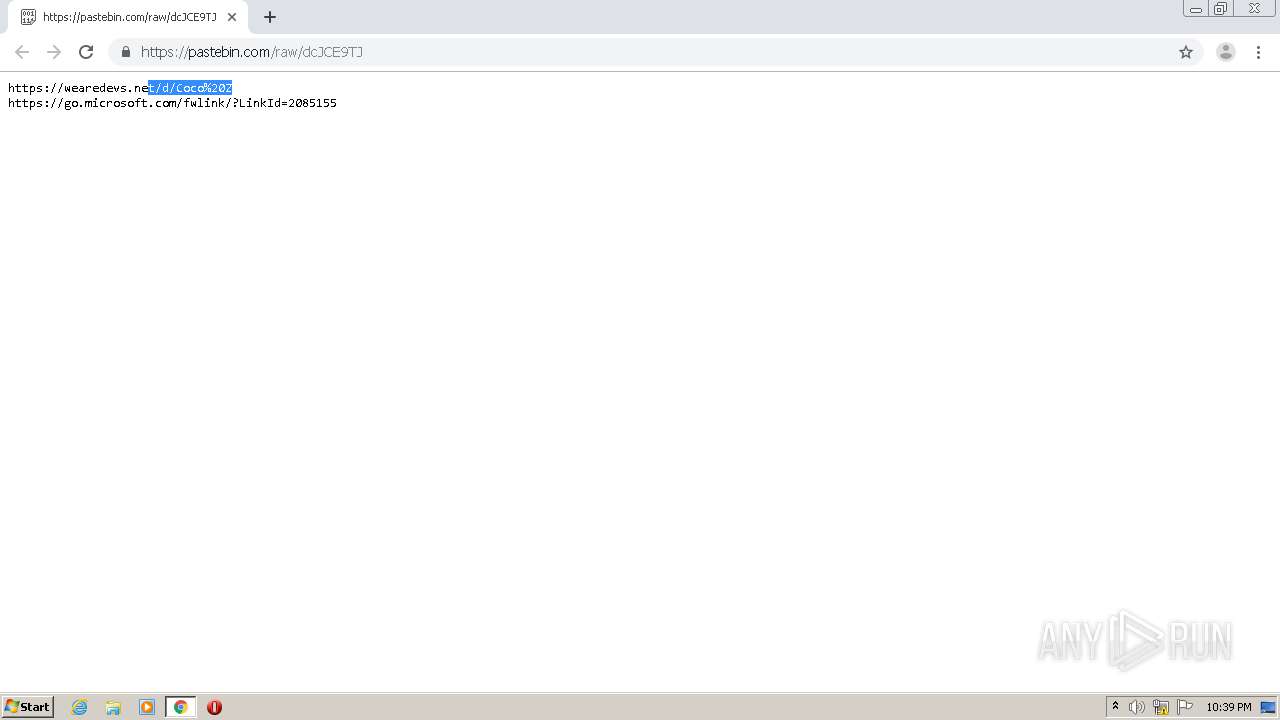
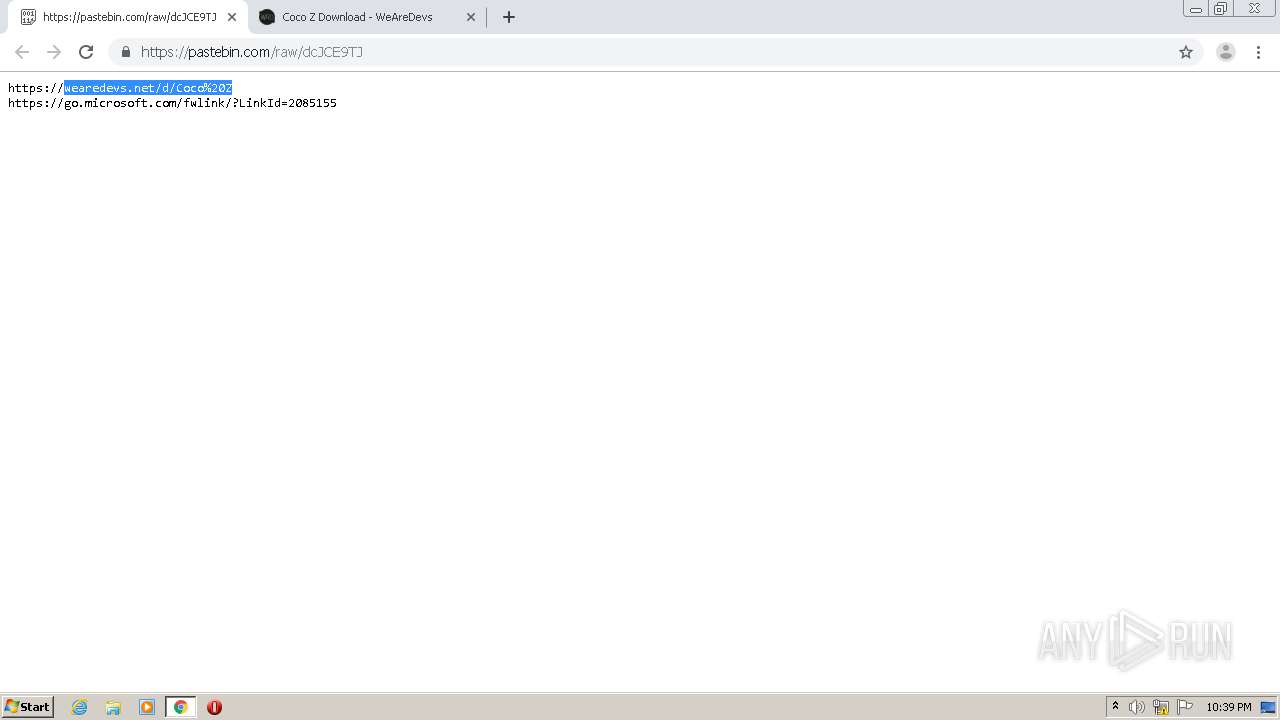
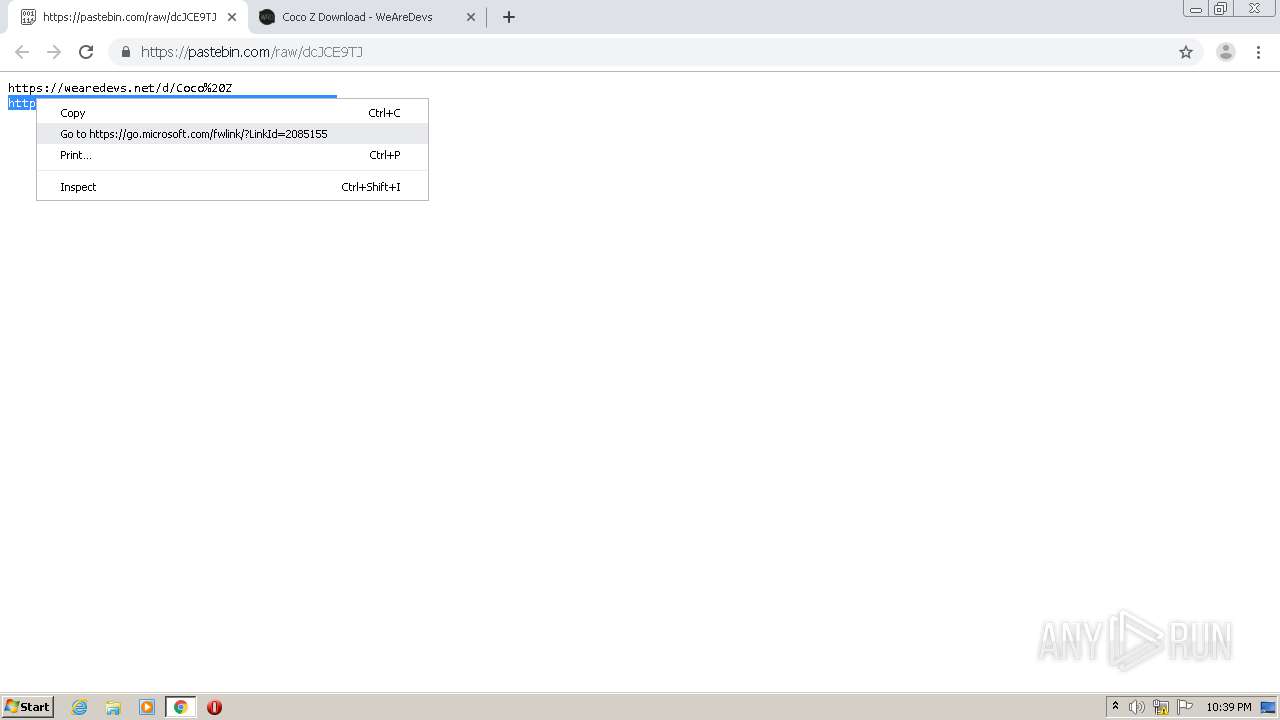
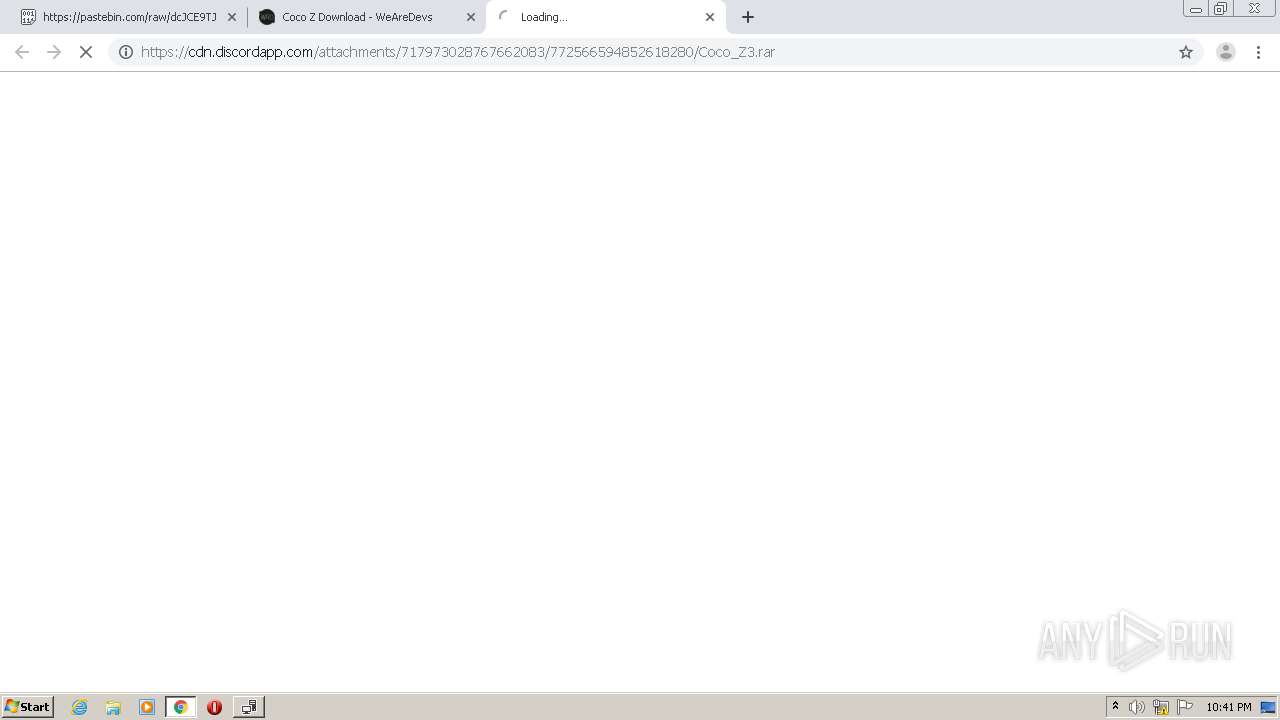
| URL: | https://pastebin.com/raw/dcJCE9TJ |
| Full analysis: | https://app.any.run/tasks/e8872d2e-710c-46e4-9910-3db5d43876dd |
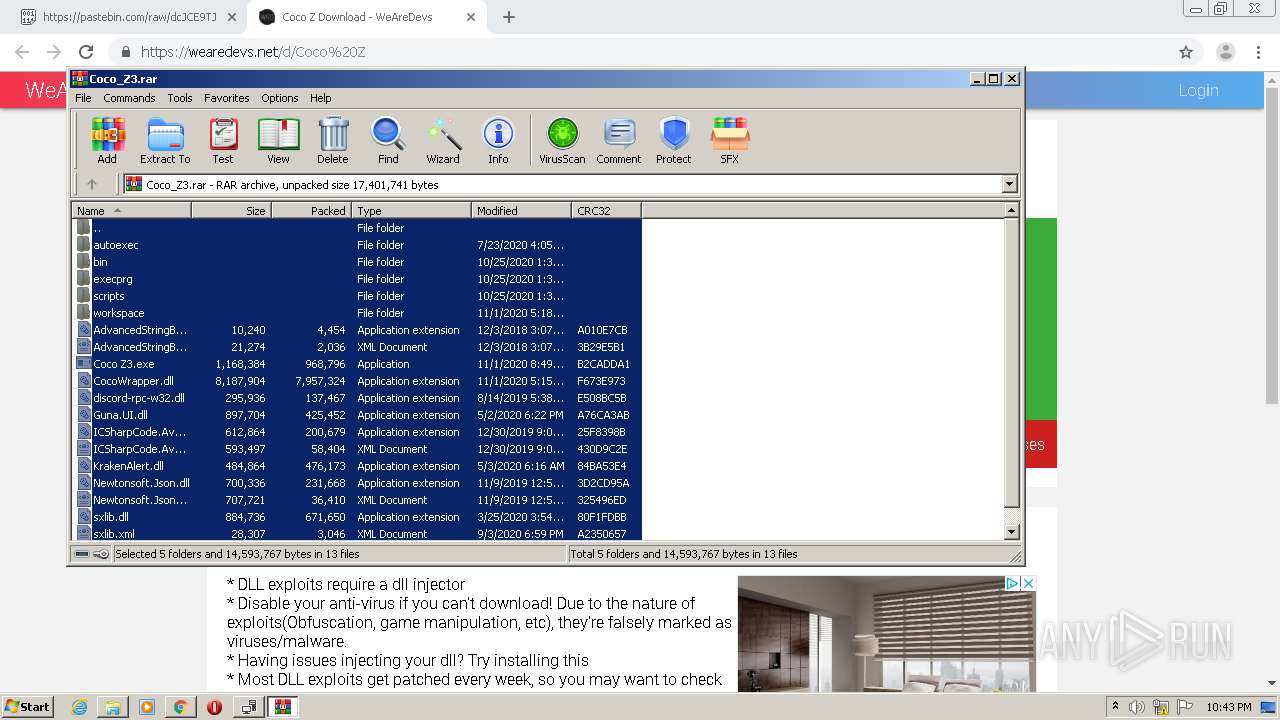
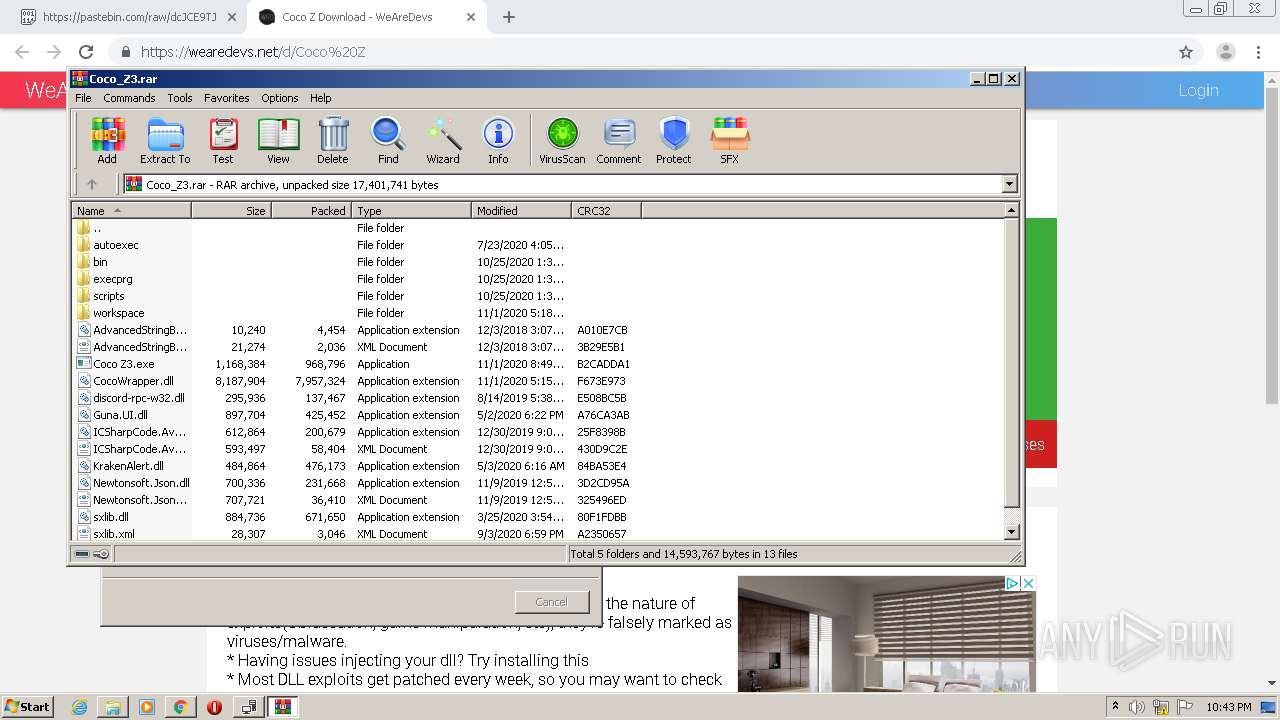
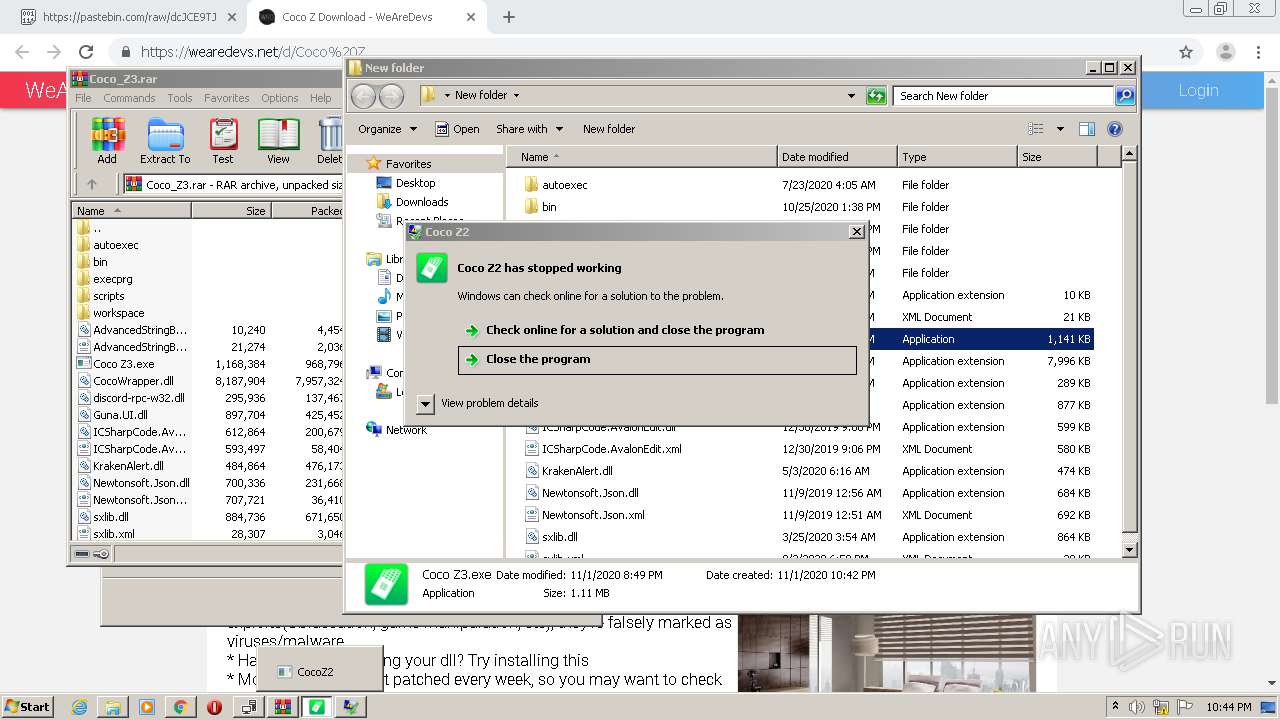
| Verdict: | Malicious activity |
| Analysis date: | November 01, 2020, 22:38:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 373B3E0F117B035C2E7C7C187A168511 |
| SHA1: | 7AD90AFC1AEEF0E5FE3FEAB7697864E5D0731A38 |
| SHA256: | C4432FE4E88FCE0EEEF07A08823E2DFF034229C88FB5AB4D2CF0AC103C238709 |
| SSDEEP: | 3:N8AWiMLZnJvXK:2AKva |
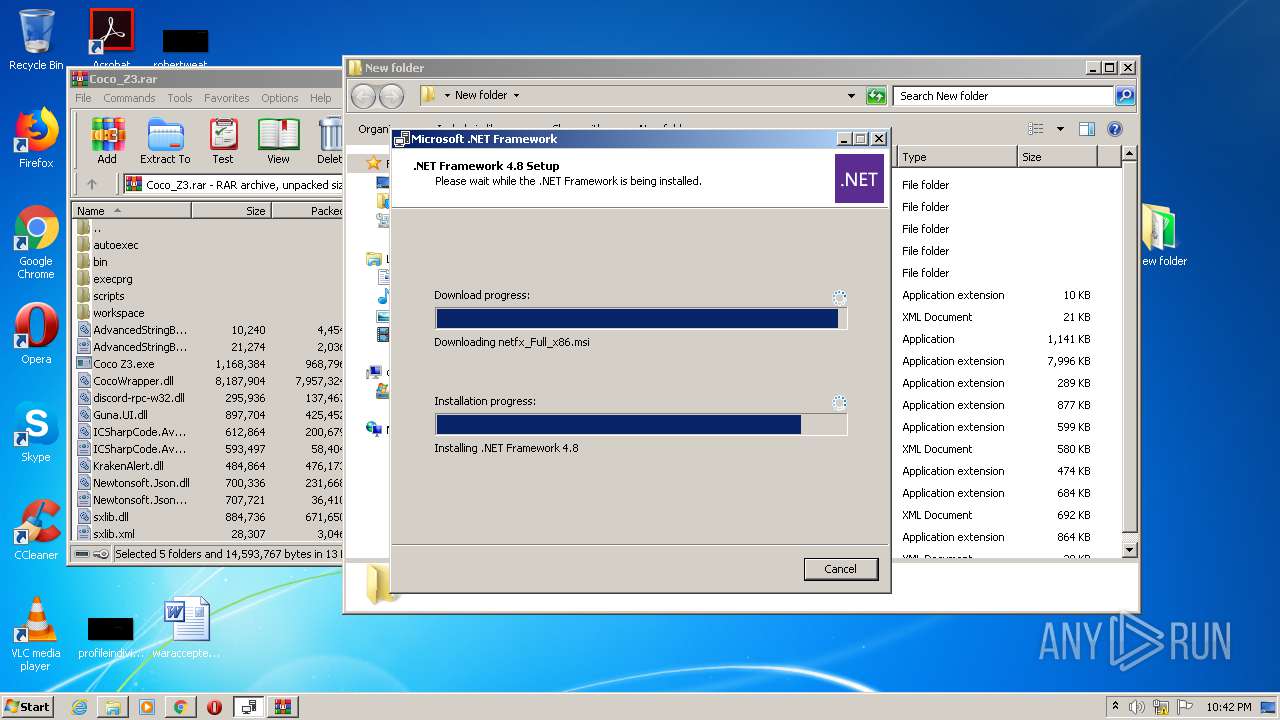
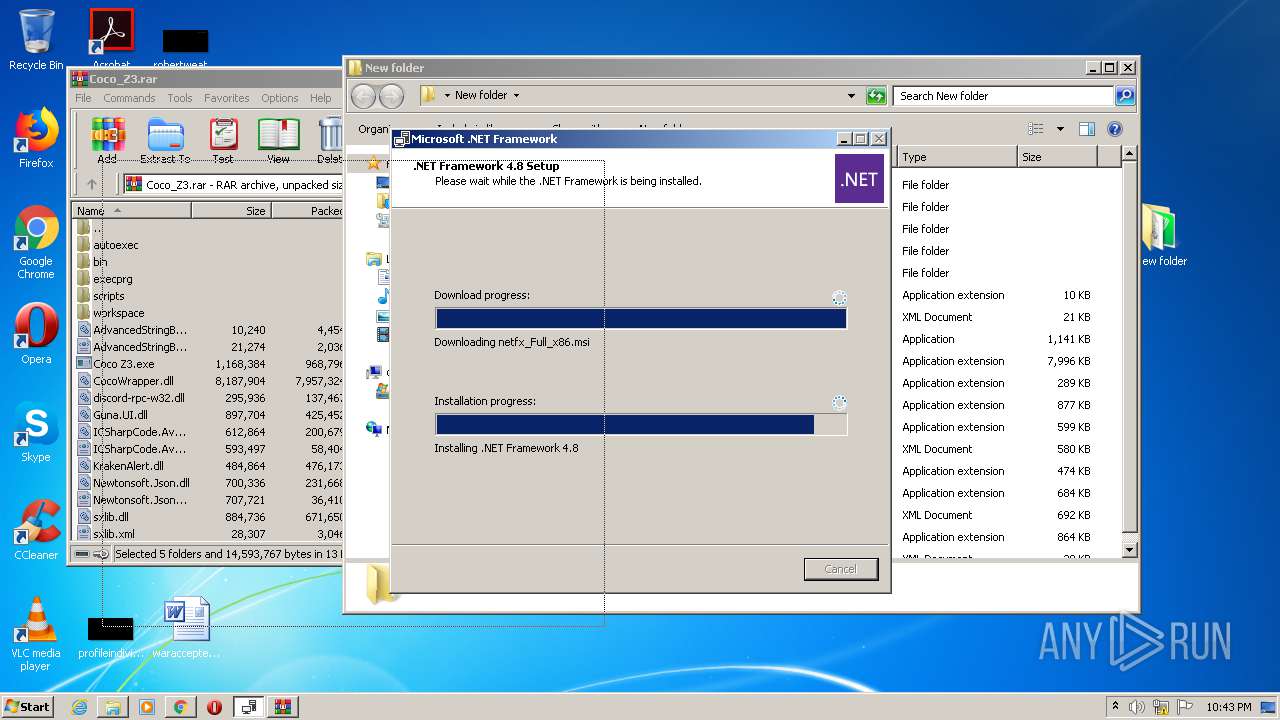
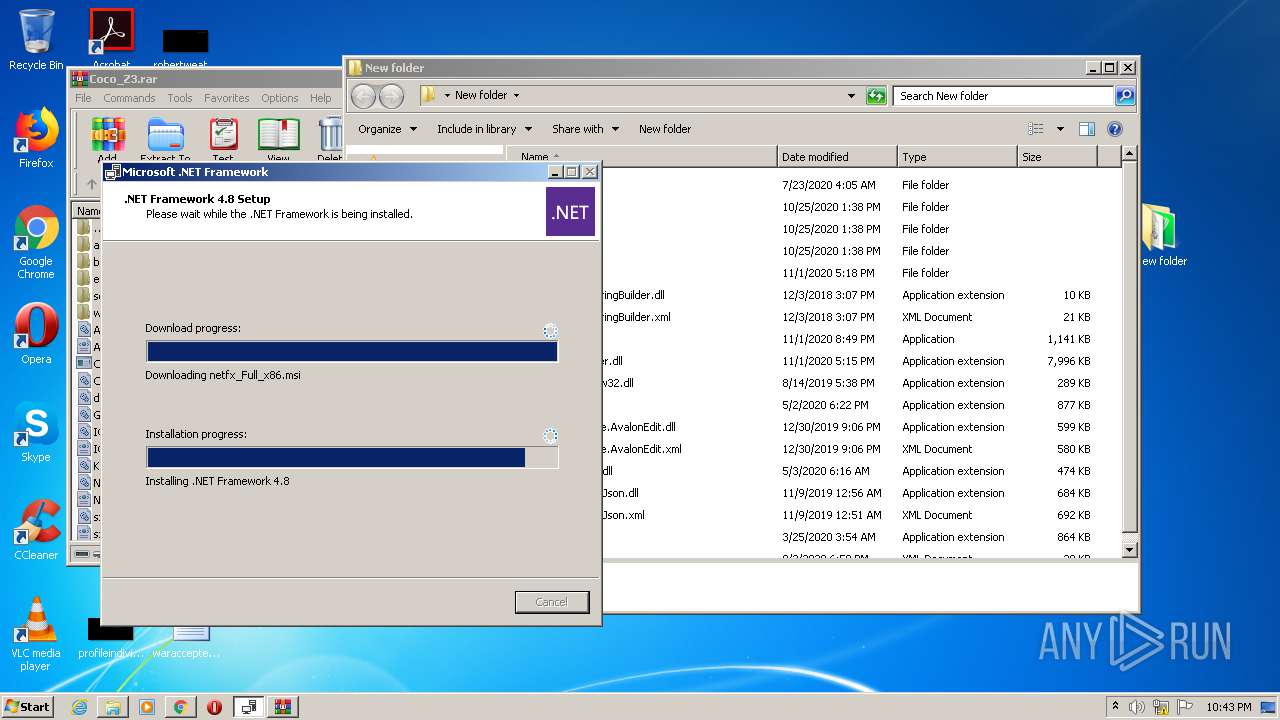
MALICIOUS
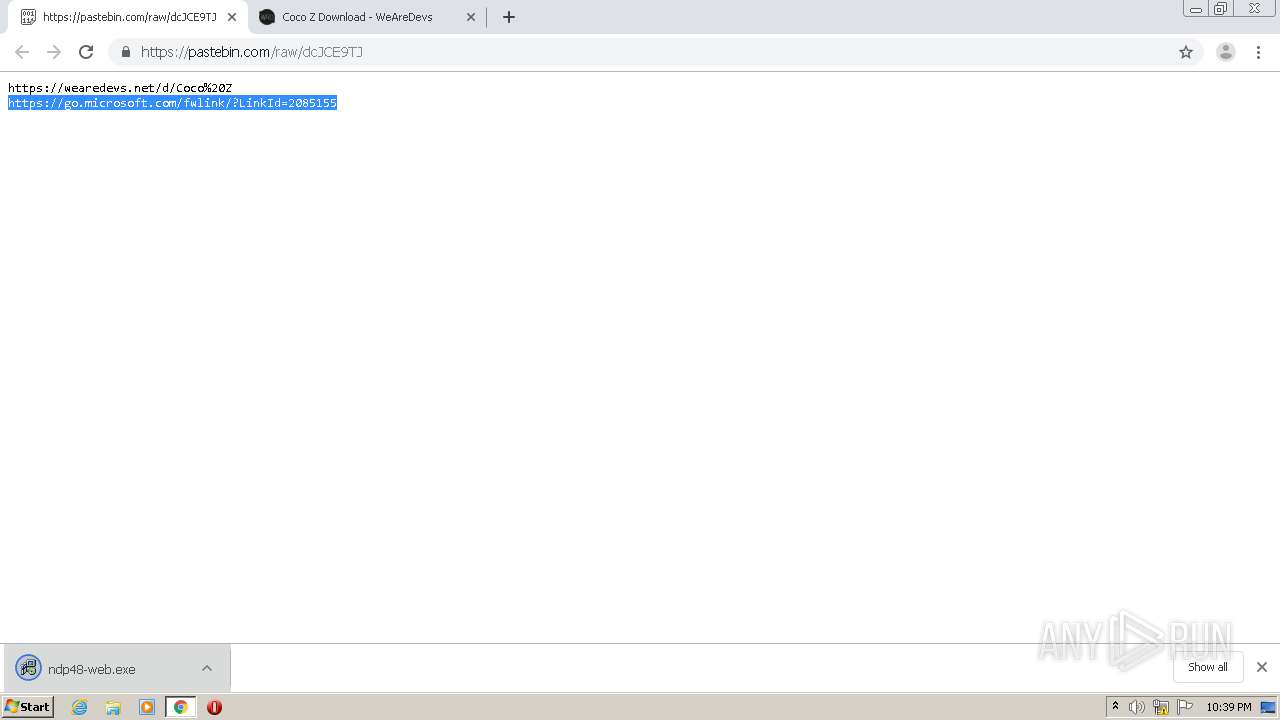
Actions looks like stealing of personal data
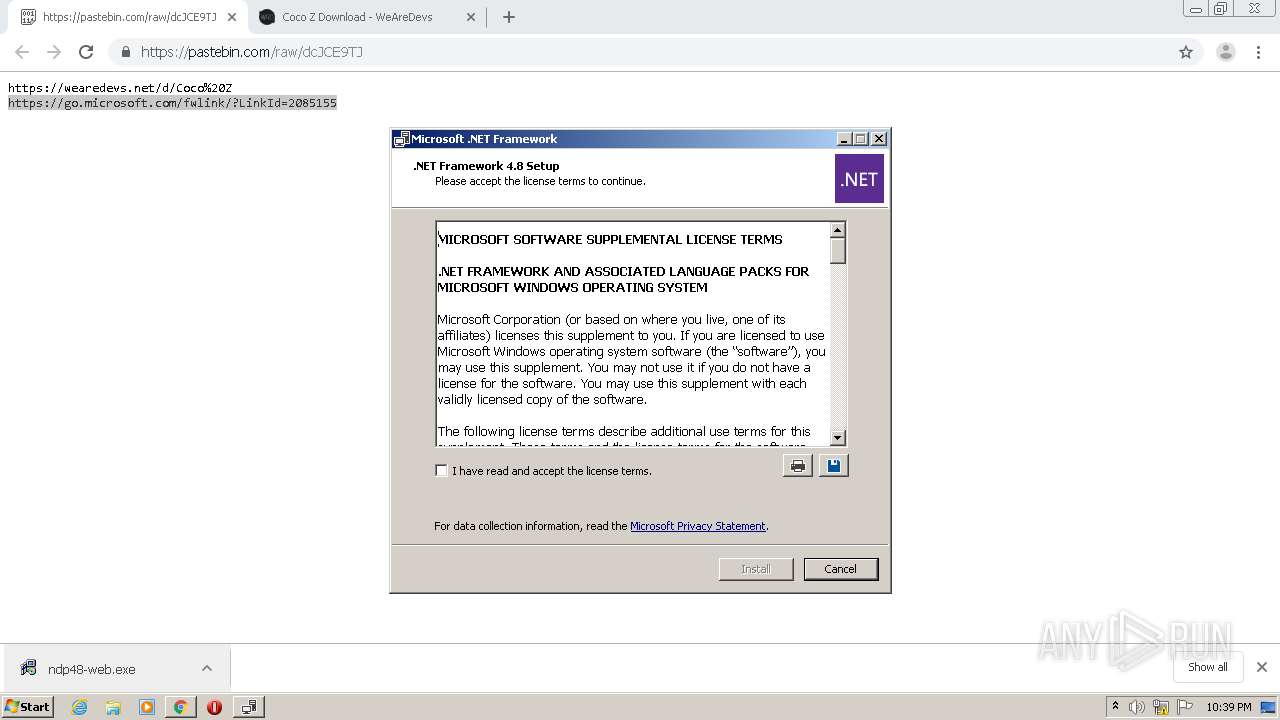
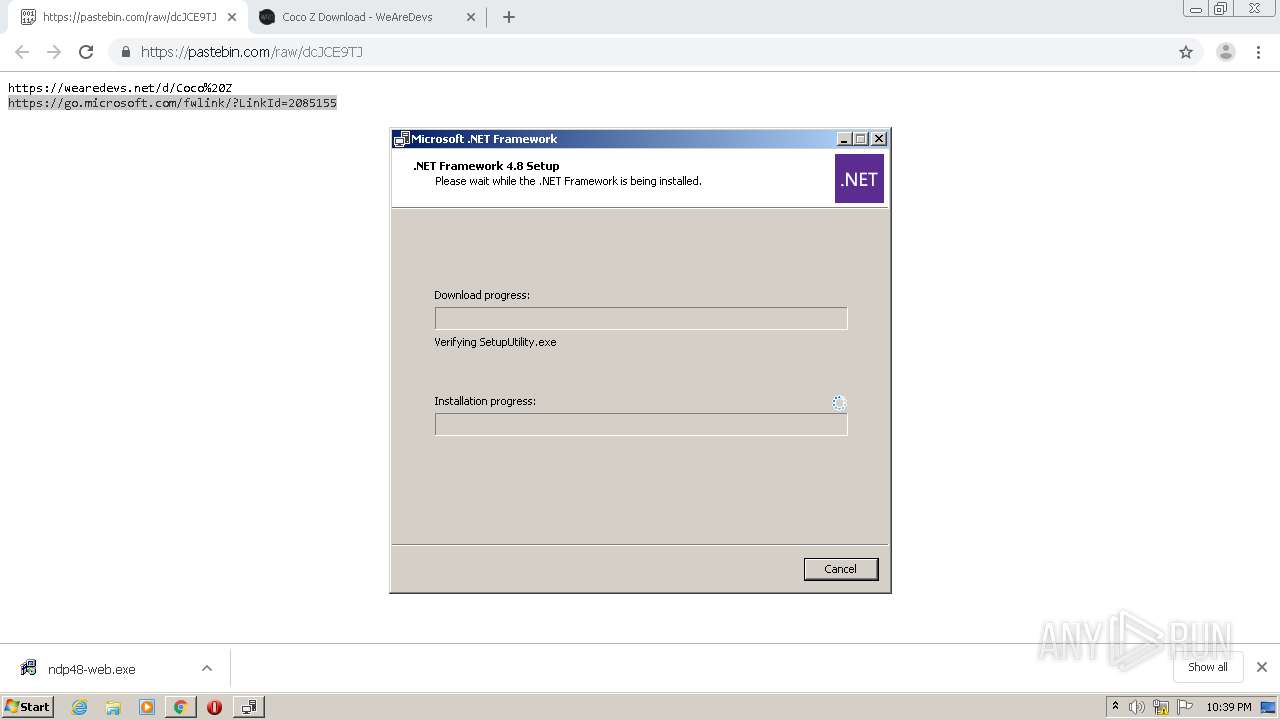
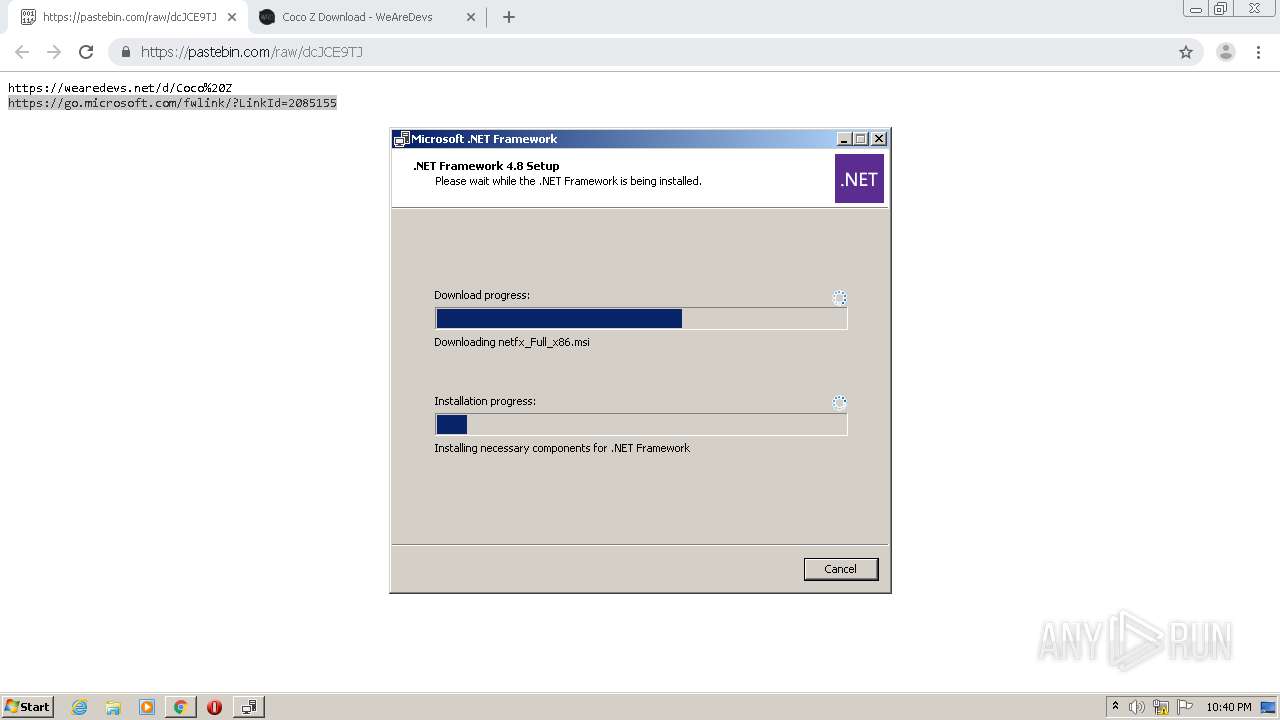
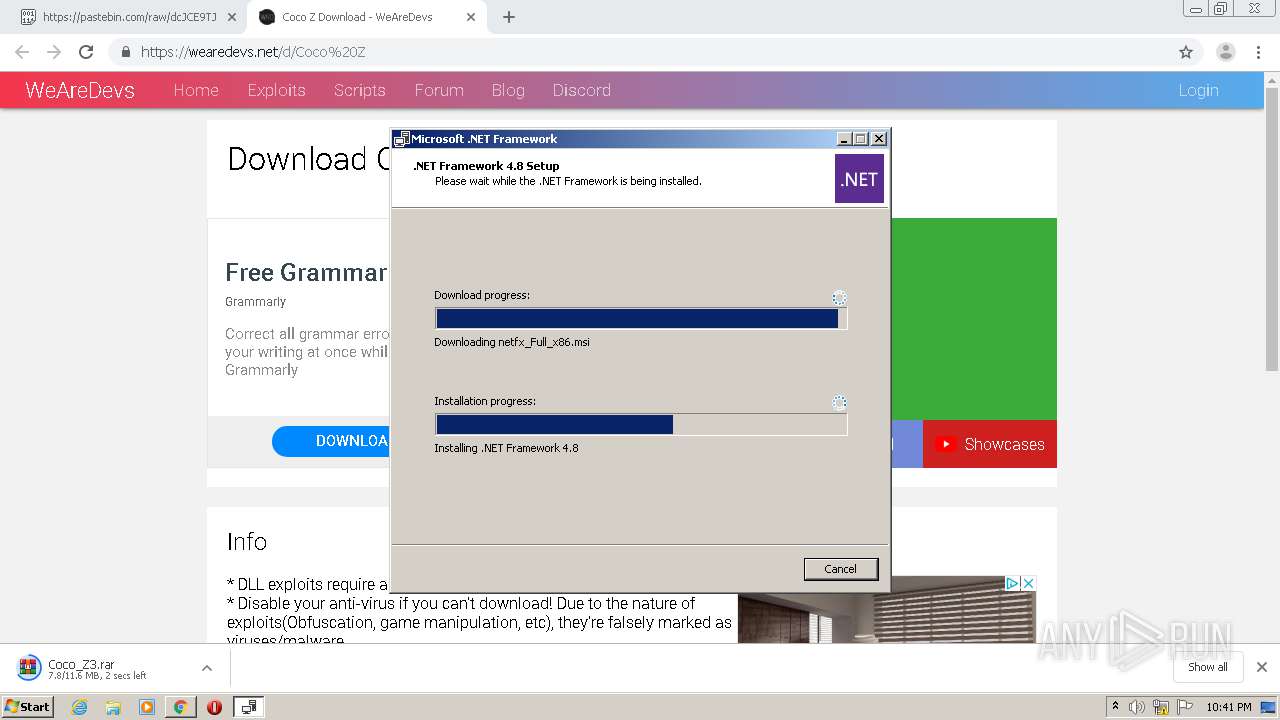
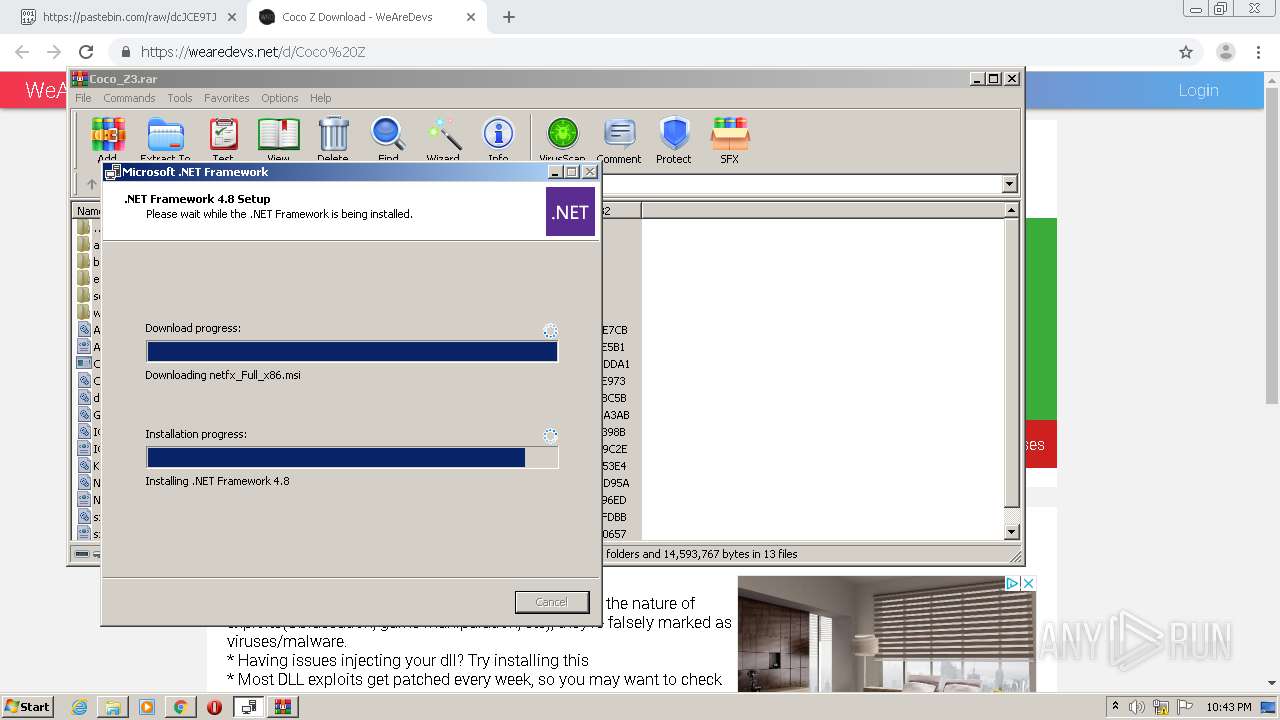
- ndp48-web.exe (PID: 3424)
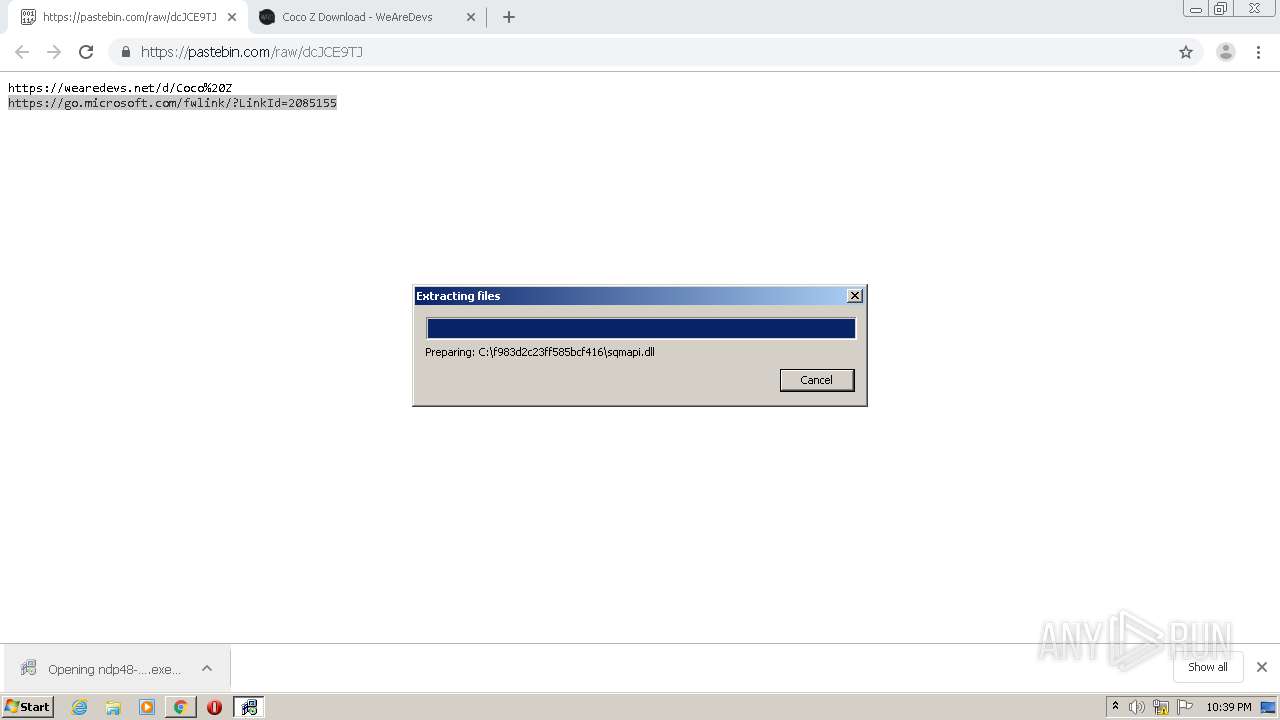
Application was dropped or rewritten from another process
- ndp48-web.exe (PID: 3452)
- ndp48-web.exe (PID: 3424)
- Setup.exe (PID: 2552)
- SetupUtility.exe (PID: 2968)
- SetupUtility.exe (PID: 3824)
- regtlibv12.exe (PID: 2228)
- ServiceModelReg.exe (PID: 2628)
- regtlibv12.exe (PID: 704)
- regtlibv12.exe (PID: 2824)
- regtlibv12.exe (PID: 3920)
- regtlibv12.exe (PID: 4088)
- regtlibv12.exe (PID: 2992)
- aspnet_regiis.exe (PID: 1304)
- ngen.exe (PID: 1732)
- mscorsvw.exe (PID: 2588)
- ngen.exe (PID: 2836)
- mscorsvw.exe (PID: 3948)
- mscorsvw.exe (PID: 3852)
- mscorsvw.exe (PID: 120)
- mscorsvw.exe (PID: 3272)
- ngen.exe (PID: 3440)
- mscorsvw.exe (PID: 2948)
- mscorsvw.exe (PID: 2344)
- mscorsvw.exe (PID: 960)
- mscorsvw.exe (PID: 2764)
- mscorsvw.exe (PID: 2612)
- mscorsvw.exe (PID: 3632)
- mscorsvw.exe (PID: 3708)
- mscorsvw.exe (PID: 3144)
- mscorsvw.exe (PID: 2100)
- mscorsvw.exe (PID: 2576)
- mscorsvw.exe (PID: 2580)
- mscorsvw.exe (PID: 444)
- mscorsvw.exe (PID: 3964)
- mscorsvw.exe (PID: 3024)
- mscorsvw.exe (PID: 3612)
- mscorsvw.exe (PID: 932)
- mscorsvw.exe (PID: 3484)
- mscorsvw.exe (PID: 3832)
- mscorsvw.exe (PID: 2644)
- mscorsvw.exe (PID: 1768)
- mscorsvw.exe (PID: 2140)
- regtlibv12.exe (PID: 2900)
- mscorsvw.exe (PID: 2536)
- mscorsvw.exe (PID: 3428)
- mscorsvw.exe (PID: 2352)
- mscorsvw.exe (PID: 2312)
- mscorsvw.exe (PID: 2248)
- mscorsvw.exe (PID: 912)
- mscorsvw.exe (PID: 3784)
- mscorsvw.exe (PID: 1808)
- mscorsvw.exe (PID: 1208)
- mscorsvw.exe (PID: 1468)
- mscorsvw.exe (PID: 3312)
- mscorsvw.exe (PID: 3492)
- mscorsvw.exe (PID: 3696)
- mscorsvw.exe (PID: 3112)
- mscorsvw.exe (PID: 3760)
- mscorsvw.exe (PID: 568)
- mscorsvw.exe (PID: 2648)
- mscorsvw.exe (PID: 2652)
- mscorsvw.exe (PID: 1792)
- mscorsvw.exe (PID: 3812)
- mscorsvw.exe (PID: 3644)
- mscorsvw.exe (PID: 336)
- mscorsvw.exe (PID: 1352)
- mscorsvw.exe (PID: 3364)
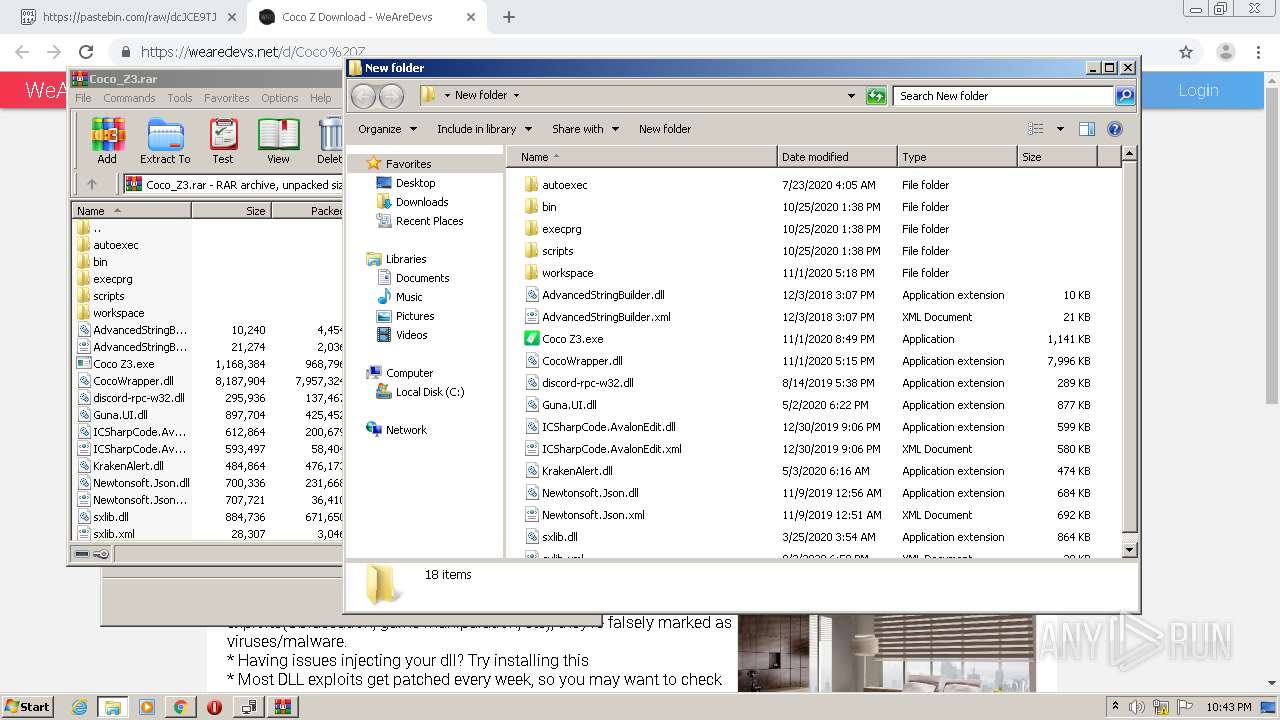
- Coco Z3.exe (PID: 1544)
- mscorsvw.exe (PID: 928)
- mscorsvw.exe (PID: 2188)
- mscorsvw.exe (PID: 908)
- mscorsvw.exe (PID: 4008)
- mscorsvw.exe (PID: 3336)
- mscorsvw.exe (PID: 1508)
- mscorsvw.exe (PID: 3252)
- mscorsvw.exe (PID: 2684)
- mscorsvw.exe (PID: 3176)
- mscorsvw.exe (PID: 2488)
- mscorsvw.exe (PID: 628)
- mscorsvw.exe (PID: 2180)
- mscorsvw.exe (PID: 3560)
- mscorsvw.exe (PID: 2764)
- mscorsvw.exe (PID: 3400)
- mscorsvw.exe (PID: 2236)
- mscorsvw.exe (PID: 1472)
- mscorsvw.exe (PID: 2880)
- mscorsvw.exe (PID: 1864)
Changes settings of System certificates
- Setup.exe (PID: 2552)
Loads dropped or rewritten executable
- Setup.exe (PID: 2552)
- svchost.exe (PID: 776)
- wmiprvse.exe (PID: 2720)
- SearchFilterHost.exe (PID: 888)
- SearchProtocolHost.exe (PID: 1632)
- aspnet_regiis.exe (PID: 1304)
- ngen.exe (PID: 1732)
- mscorsvw.exe (PID: 2588)
- ngen.exe (PID: 2836)
- ngen.exe (PID: 3440)
- mscorsvw.exe (PID: 3948)
- mscorsvw.exe (PID: 2948)
- mscorsvw.exe (PID: 3852)
- mscorsvw.exe (PID: 120)
- mscorsvw.exe (PID: 3272)
- mscorsvw.exe (PID: 2344)
- mscorsvw.exe (PID: 2764)
- mscorsvw.exe (PID: 960)
- mscorsvw.exe (PID: 2612)
- mscorsvw.exe (PID: 3632)
- mscorsvw.exe (PID: 2100)
- mscorsvw.exe (PID: 3144)
- mscorsvw.exe (PID: 2576)
- mscorsvw.exe (PID: 2580)
- mscorsvw.exe (PID: 3708)
- mscorsvw.exe (PID: 3024)
- mscorsvw.exe (PID: 932)
- mscorsvw.exe (PID: 3612)
- mscorsvw.exe (PID: 444)
- mscorsvw.exe (PID: 3964)
- mscorsvw.exe (PID: 3484)
- mscorsvw.exe (PID: 2140)
- mscorsvw.exe (PID: 1768)
- mscorsvw.exe (PID: 3832)
- mscorsvw.exe (PID: 2644)
- mscorsvw.exe (PID: 3428)
- mscorsvw.exe (PID: 2536)
- mscorsvw.exe (PID: 2312)
- mscorsvw.exe (PID: 2352)
- mscorsvw.exe (PID: 1808)
- mscorsvw.exe (PID: 3784)
- mscorsvw.exe (PID: 1208)
- mscorsvw.exe (PID: 2248)
- mscorsvw.exe (PID: 1468)
- mscorsvw.exe (PID: 912)
- mscorsvw.exe (PID: 3696)
- mscorsvw.exe (PID: 3312)
- mscorsvw.exe (PID: 3492)
- mscorsvw.exe (PID: 3112)
- mscorsvw.exe (PID: 2648)
- mscorsvw.exe (PID: 568)
- mscorsvw.exe (PID: 3364)
- mscorsvw.exe (PID: 336)
- mscorsvw.exe (PID: 2652)
- mscorsvw.exe (PID: 1792)
- mscorsvw.exe (PID: 3812)
- mscorsvw.exe (PID: 3644)
- mscorsvw.exe (PID: 3760)
- Coco Z3.exe (PID: 1544)
- mscorsvw.exe (PID: 2188)
- mscorsvw.exe (PID: 928)
- mscorsvw.exe (PID: 3336)
- mscorsvw.exe (PID: 908)
- mscorsvw.exe (PID: 4008)
- mscorsvw.exe (PID: 1352)
- mscorsvw.exe (PID: 3252)
- mscorsvw.exe (PID: 3176)
- mscorsvw.exe (PID: 2684)
- mscorsvw.exe (PID: 2180)
- mscorsvw.exe (PID: 2488)
- mscorsvw.exe (PID: 2764)
- mscorsvw.exe (PID: 3560)
- mscorsvw.exe (PID: 1508)
- mscorsvw.exe (PID: 628)
- mscorsvw.exe (PID: 1472)
- mscorsvw.exe (PID: 3400)
- mscorsvw.exe (PID: 2880)
- mscorsvw.exe (PID: 1864)
Loads the Task Scheduler COM API
- ngen.exe (PID: 1732)
- mscorsvw.exe (PID: 2588)
- ngen.exe (PID: 2836)
- ngen.exe (PID: 3440)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2096)
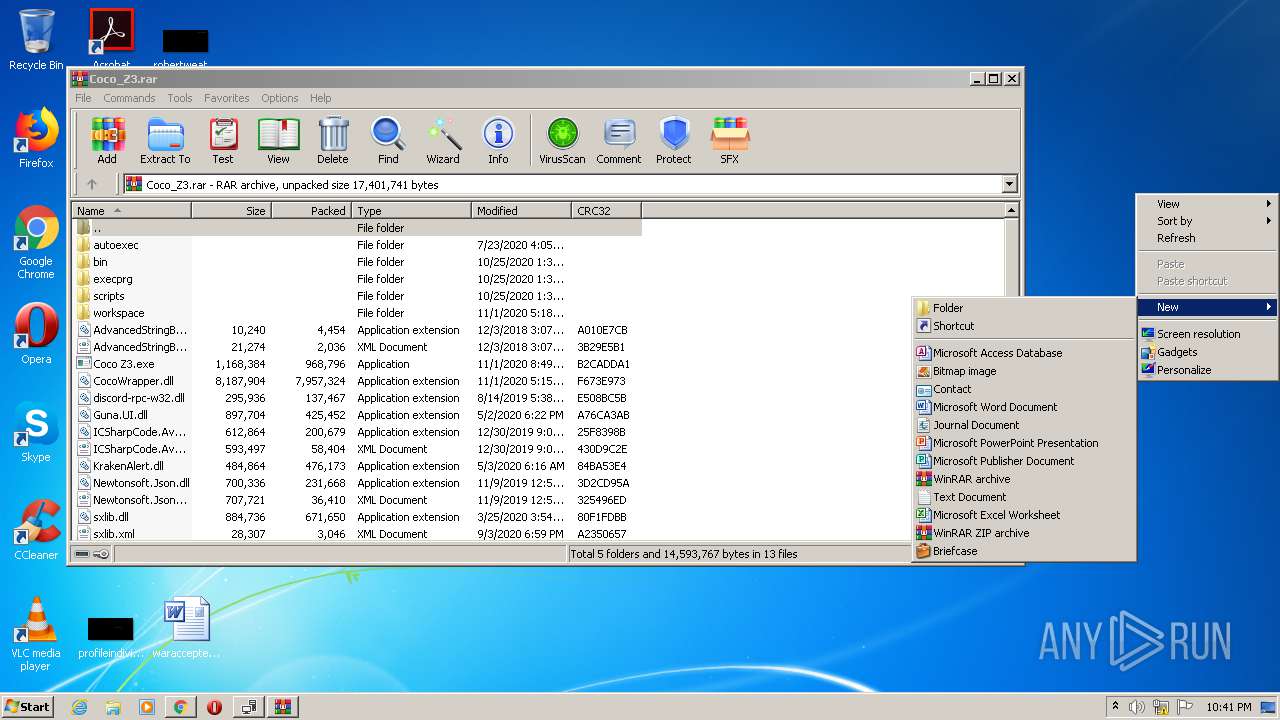
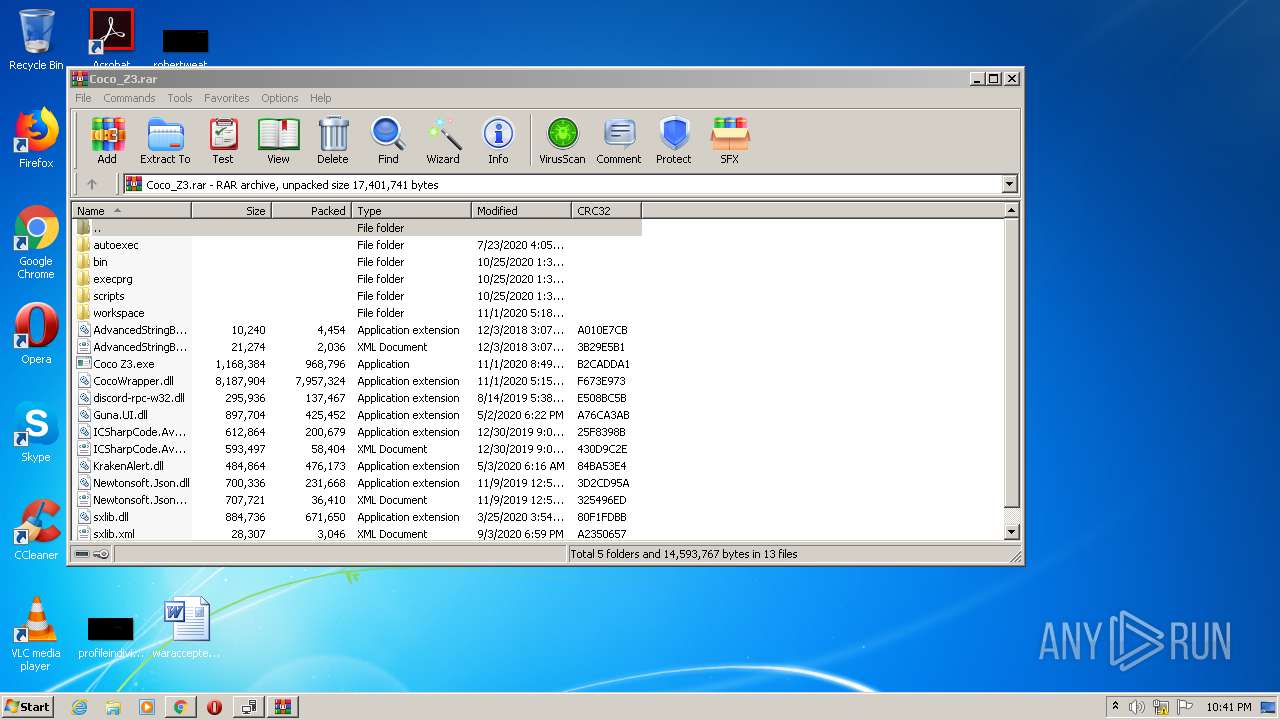
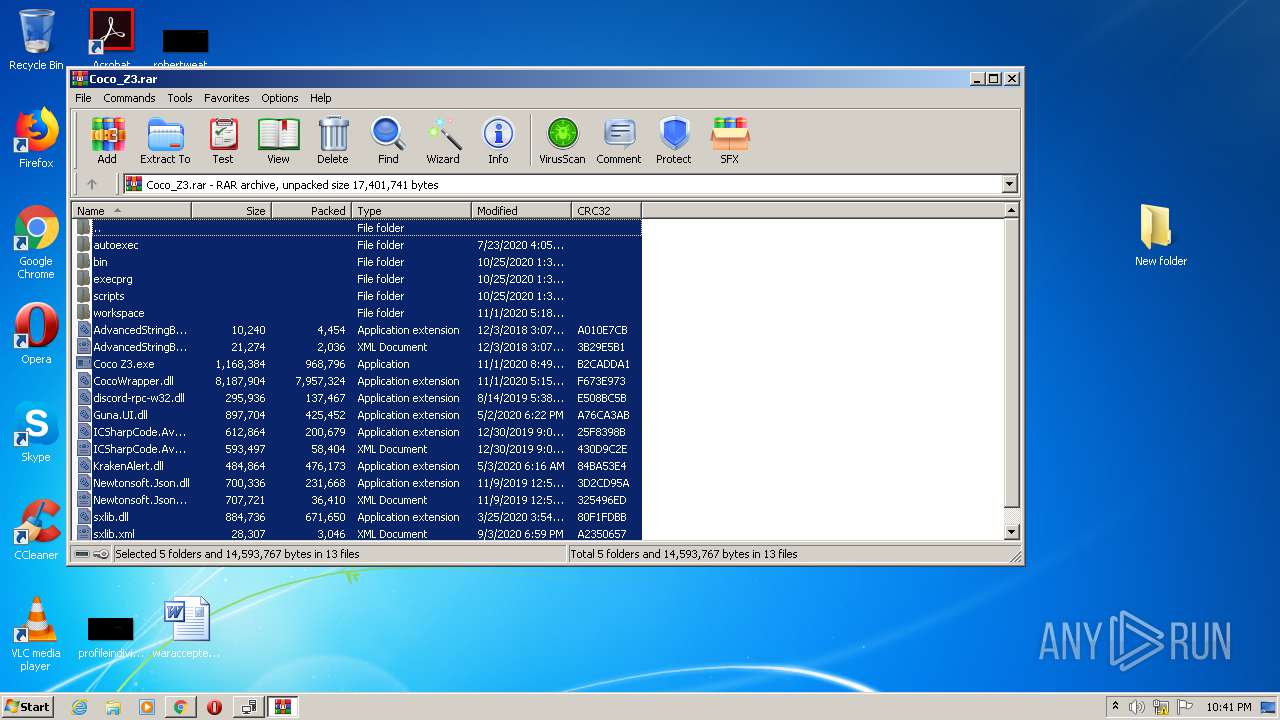
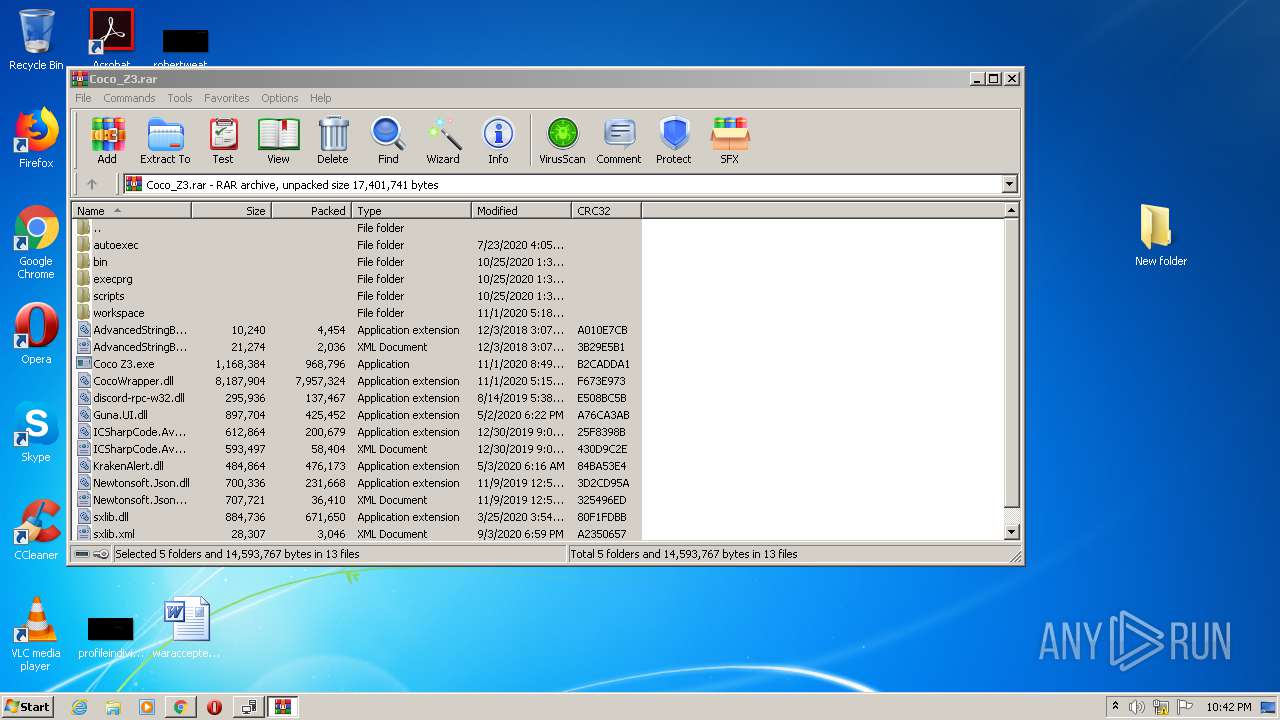
Executable content was dropped or overwritten
- chrome.exe (PID: 1248)
- chrome.exe (PID: 2096)
- ndp48-web.exe (PID: 3424)
- TMPFD1D.tmp.exe (PID: 1972)
- Setup.exe (PID: 2552)
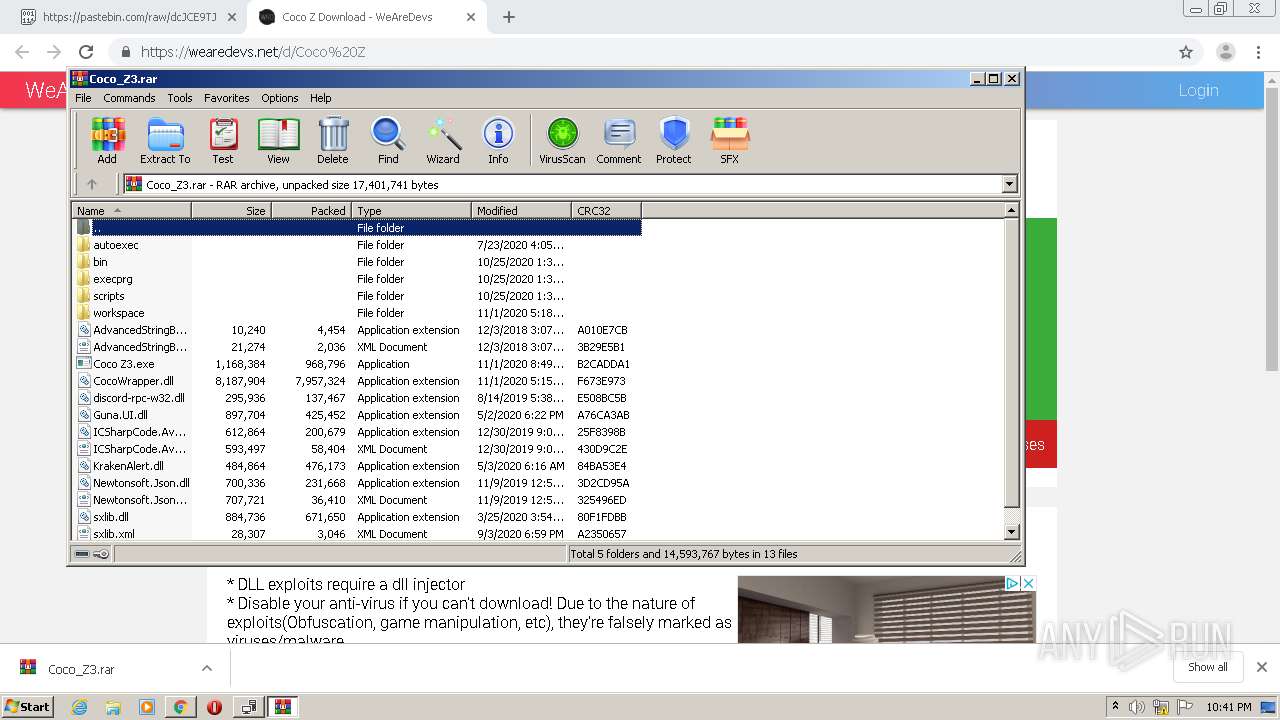
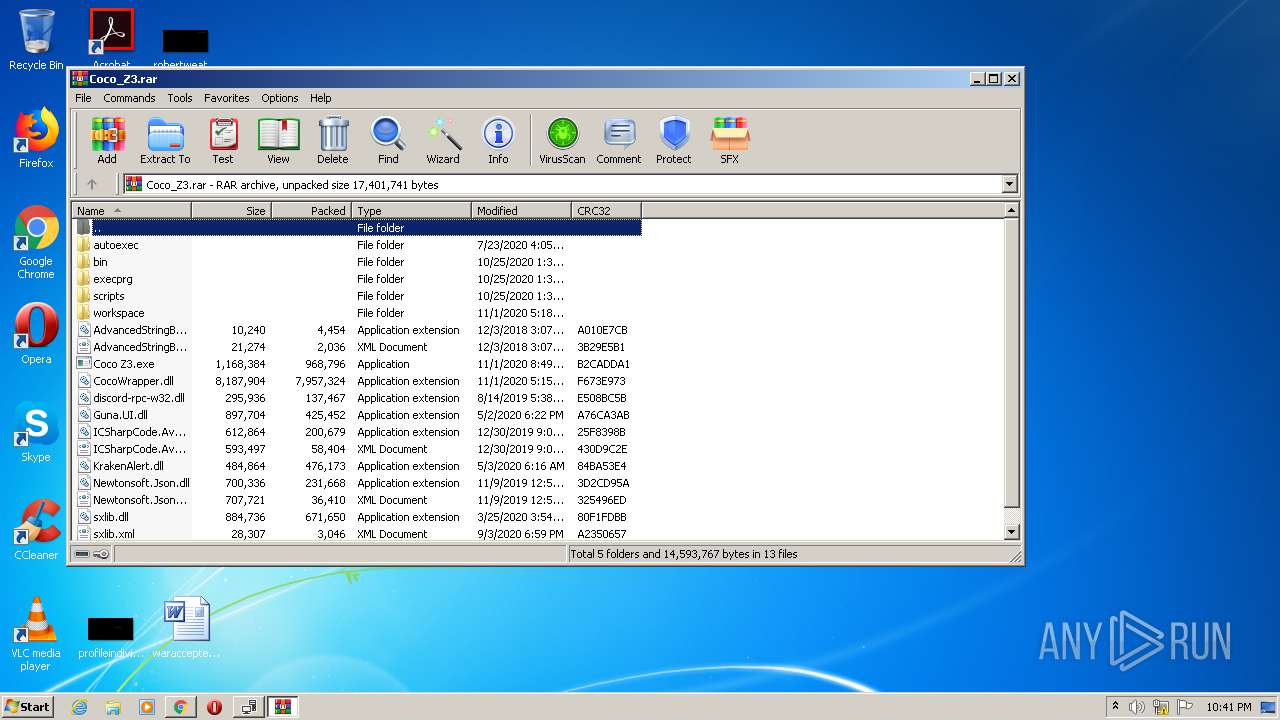
- WinRAR.exe (PID: 1340)
- msiexec.exe (PID: 3276)
- mscorsvw.exe (PID: 3852)
- mscorsvw.exe (PID: 912)
- mscorsvw.exe (PID: 2352)
- mscorsvw.exe (PID: 3336)
- mscorsvw.exe (PID: 2764)
Adds / modifies Windows certificates
- Setup.exe (PID: 2552)
Creates files in the Windows directory
- lodctr.exe (PID: 3308)
- msiexec.exe (PID: 3276)
- aspnet_regiis.exe (PID: 1304)
- ngen.exe (PID: 1732)
- lodctr.exe (PID: 4032)
- lodctr.exe (PID: 1388)
- mscorsvw.exe (PID: 2588)
- lodctr.exe (PID: 3764)
- lodctr.exe (PID: 3152)
- ngen.exe (PID: 2836)
- ngen.exe (PID: 3440)
- mscorsvw.exe (PID: 3852)
- mscorsvw.exe (PID: 912)
- mscorsvw.exe (PID: 2352)
- mscorsvw.exe (PID: 3784)
- mscorsvw.exe (PID: 3336)
- mscorsvw.exe (PID: 2764)
Changes the autorun value in the registry
- msiexec.exe (PID: 3276)
Removes files from Windows directory
- lodctr.exe (PID: 3308)
- msiexec.exe (PID: 3276)
- lodctr.exe (PID: 1388)
- aspnet_regiis.exe (PID: 1304)
- lodctr.exe (PID: 3152)
- lodctr.exe (PID: 4032)
- lodctr.exe (PID: 3764)
- mscorsvw.exe (PID: 3852)
- mscorsvw.exe (PID: 2352)
- mscorsvw.exe (PID: 912)
- mscorsvw.exe (PID: 3784)
- mscorsvw.exe (PID: 3336)
- mscorsvw.exe (PID: 2764)
Creates COM task schedule object
- msiexec.exe (PID: 3276)
- aspnet_regiis.exe (PID: 1304)
Reads Internet Cache Settings
- Setup.exe (PID: 2552)
Application launched itself
- mscorsvw.exe (PID: 2588)
Reads Environment values
- Coco Z3.exe (PID: 1544)
INFO
Reads the hosts file
- chrome.exe (PID: 2096)
- chrome.exe (PID: 1248)
Application launched itself
- chrome.exe (PID: 2096)
- msiexec.exe (PID: 3276)
Reads settings of System Certificates
- chrome.exe (PID: 1248)
- Setup.exe (PID: 2552)
Reads Internet Cache Settings
- chrome.exe (PID: 2096)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3972)
- MsiExec.exe (PID: 4068)
- msiexec.exe (PID: 3276)
Creates a software uninstall entry
- msiexec.exe (PID: 3276)
Creates or modifies windows services
- msiexec.exe (PID: 3276)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3276)
- WinRAR.exe (PID: 1340)
- mscorsvw.exe (PID: 2588)
Manual execution by user
- Coco Z3.exe (PID: 1544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
204
Monitored processes
143
Malicious processes
85
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 134 -InterruptEvent 0 -NGENProcess ec -Pipe f8 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 336 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 2b0 -InterruptEvent 0 -NGENProcess 2ac -Pipe 29c -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 444 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 1f0 -InterruptEvent 0 -NGENProcess 1e8 -Pipe 1e4 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 568 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 294 -InterruptEvent 0 -NGENProcess 288 -Pipe 274 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 628 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 2ec -InterruptEvent 0 -NGENProcess 2c4 -Pipe 2f0 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 704 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\regtlibv12.exe" "C:\Windows\Microsoft.NET\Framework\v4.0.30319\System.Drawing.tlb" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\regtlibv12.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: RegTLib Exit code: 0 Version: 14.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 776 | C:\Windows\System32\svchost.exe -k LocalServiceNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,6309067512836936163,8394113737305724559,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5484195595289905671 --mojo-platform-channel-handle=4204 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 888 | "C:\Windows\system32\SearchFilterHost.exe" 0 516 520 528 65536 524 | C:\Windows\system32\SearchFilterHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Filter Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 2c0 -InterruptEvent 0 -NGENProcess 2cc -Pipe 268 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
Total events
33 871
Read events
17 240
Write events
14 245
Delete events
2 386
Modification events
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2224) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2096-13248743944687875 |
Value: 259 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2096-13248743944687875 |
Value: 259 | |||
Executable files
2 407
Suspicious files
101
Text files
813
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F9F3909-830.pma | — | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\74271f52-5580-4758-b83a-cc04802aada2.tmp | — | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1240ca.TMP | text | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF12435a.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
58
DNS requests
44
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
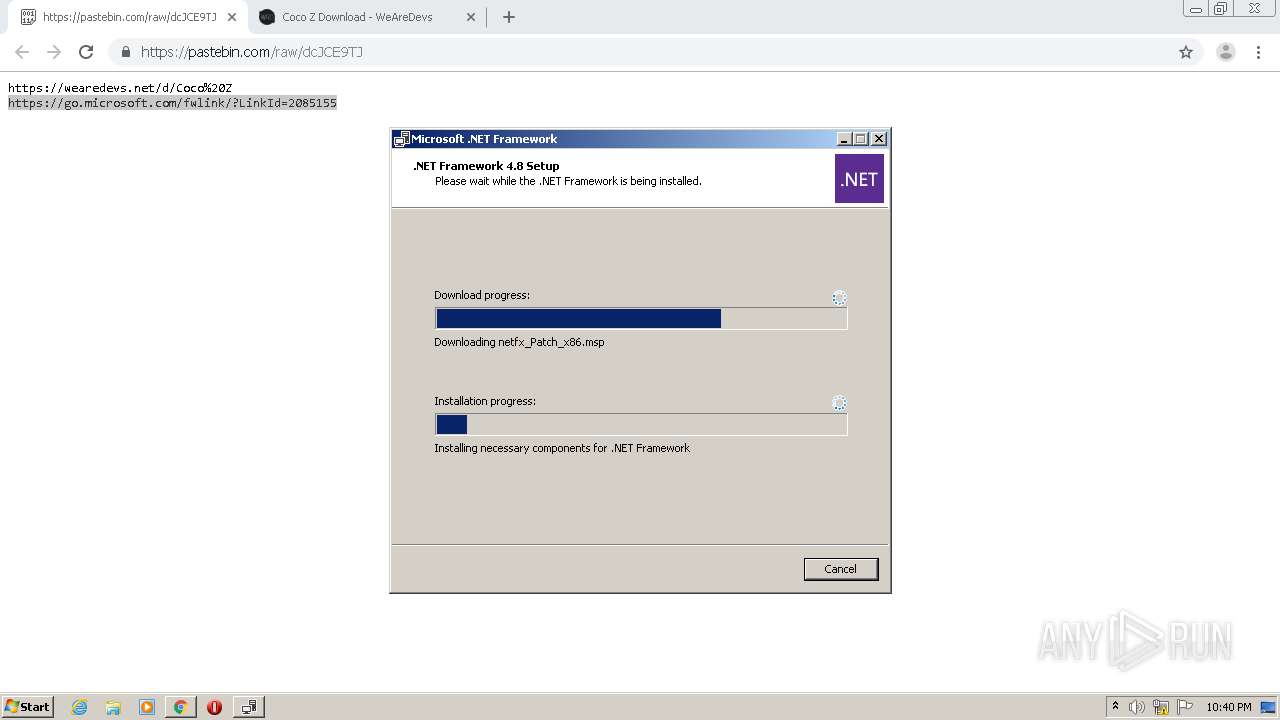
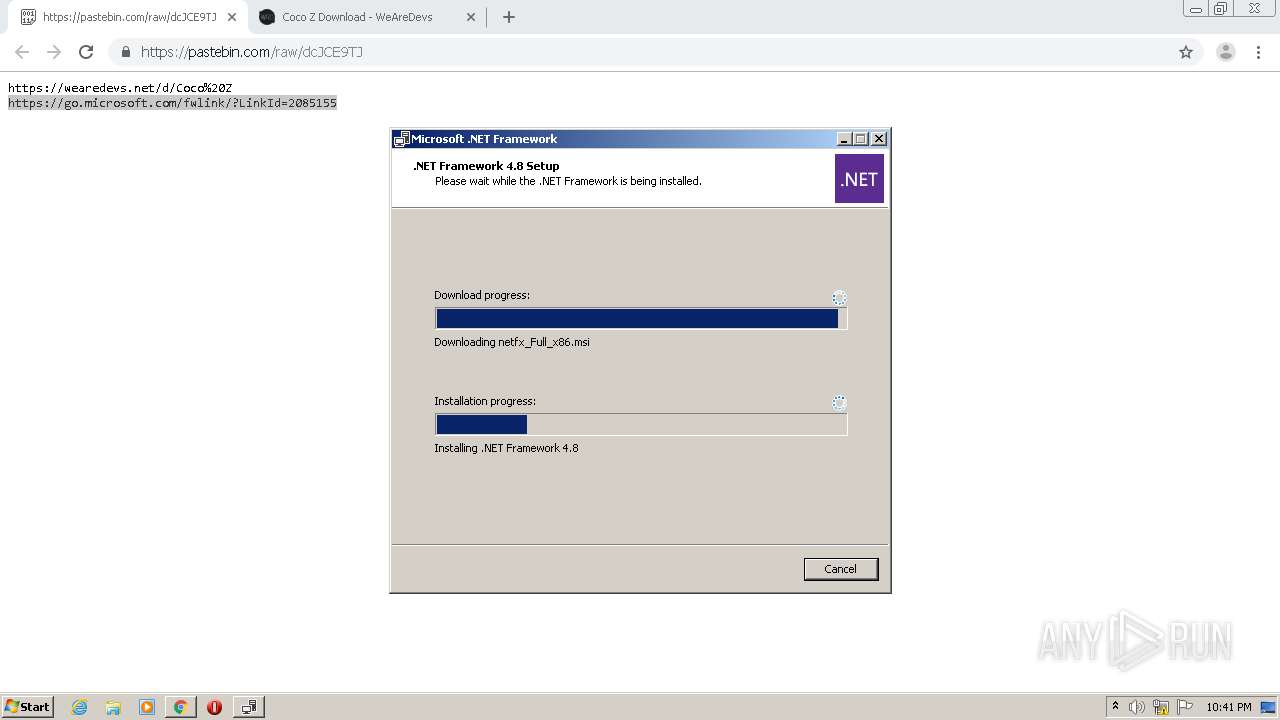
— | — | GET | 302 | 23.43.214.226:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03761.00&sar=x86&o1=netfx_Full.mzz | US | — | — | whitelisted |
— | — | HEAD | 302 | 23.43.214.226:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03761.00&sar=x86&o1=netfx_Full.mzz | US | — | — | whitelisted |
— | — | HEAD | 302 | 23.43.214.226:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03761.00&sar=amd64&o1=netfx_Full_x86.msi | US | — | — | whitelisted |
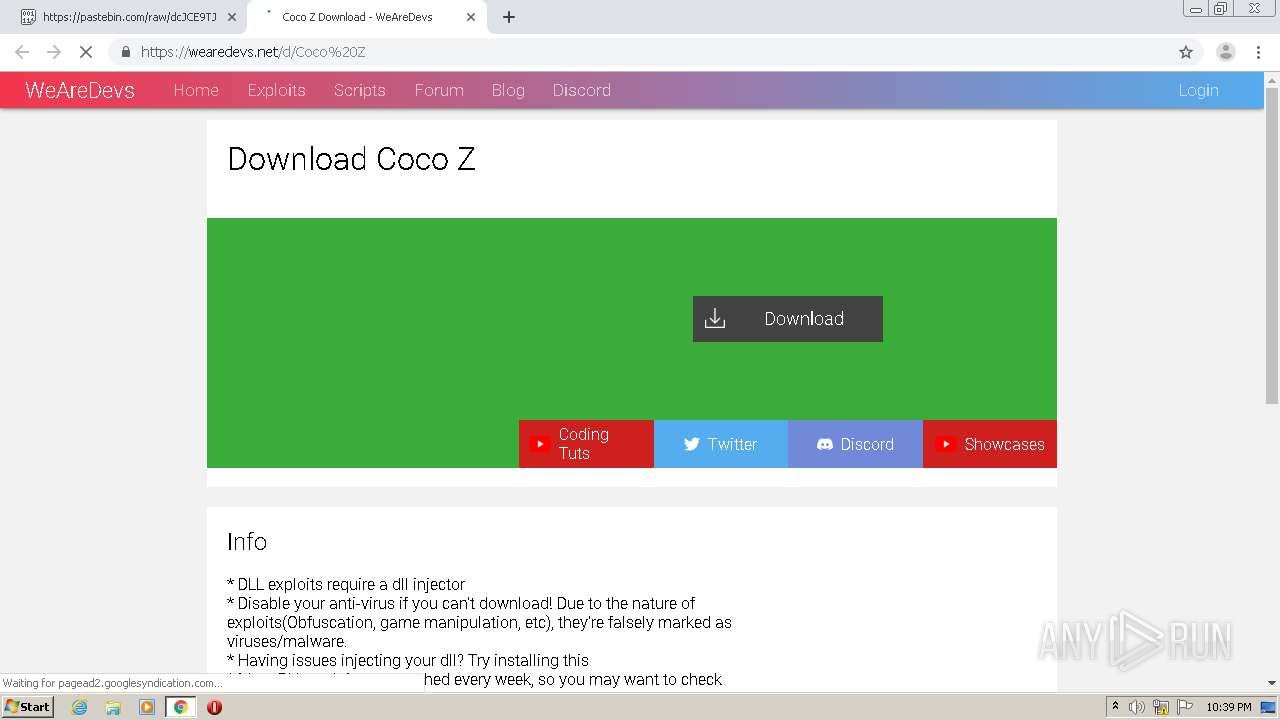
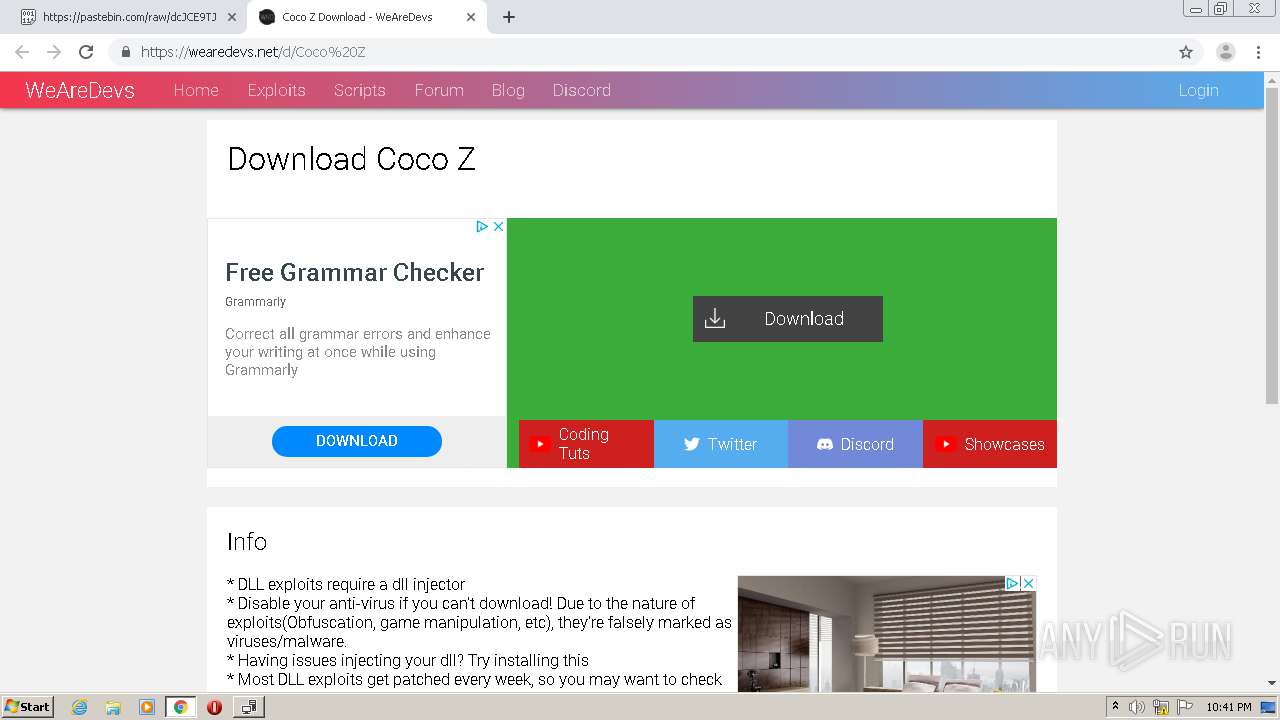
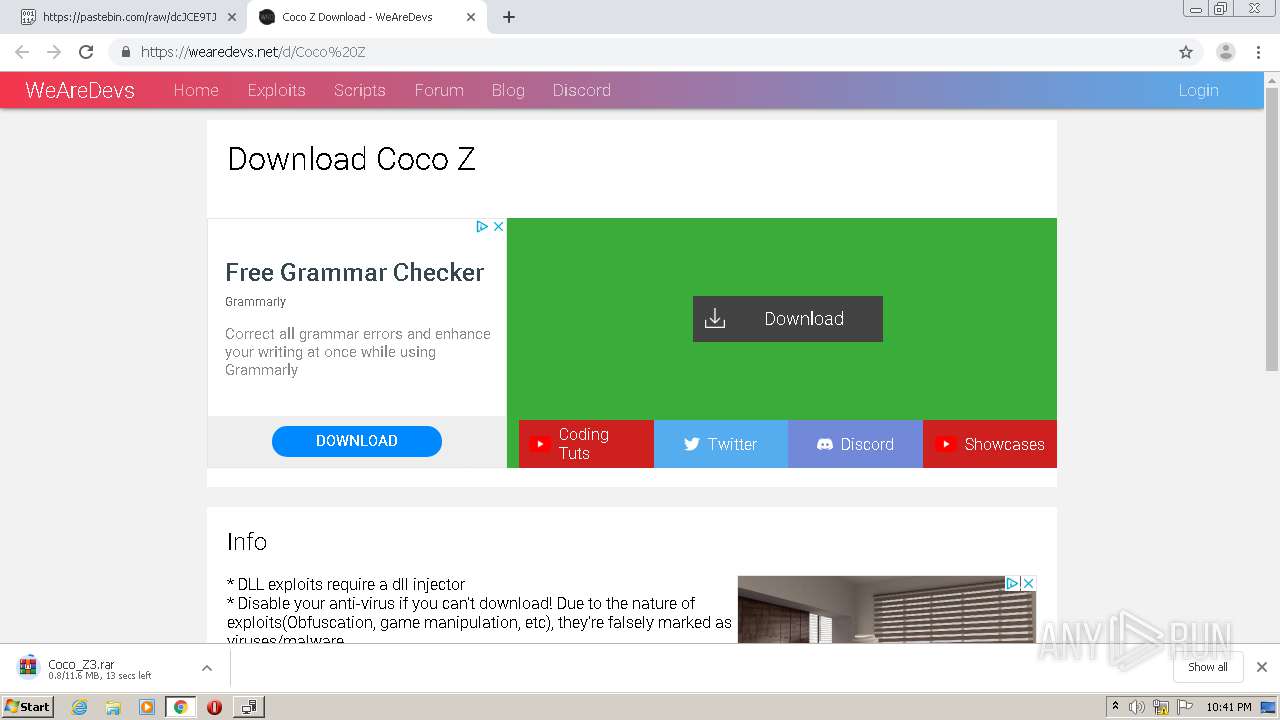
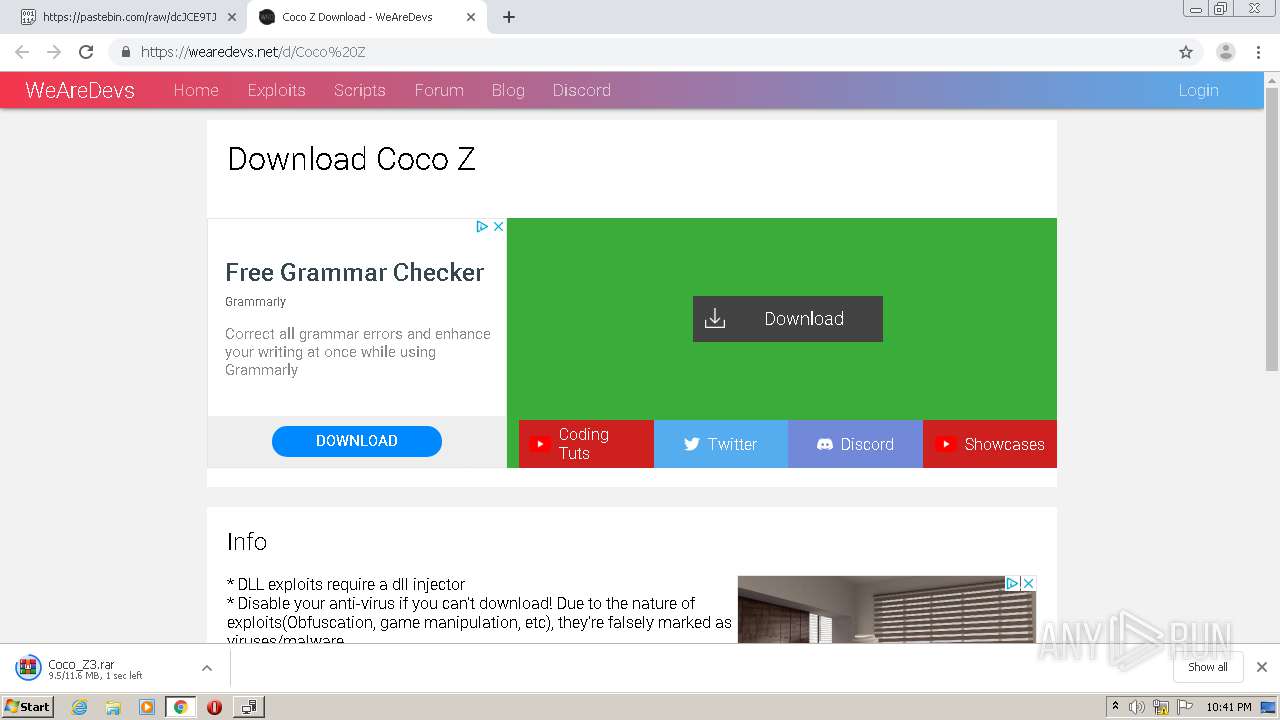
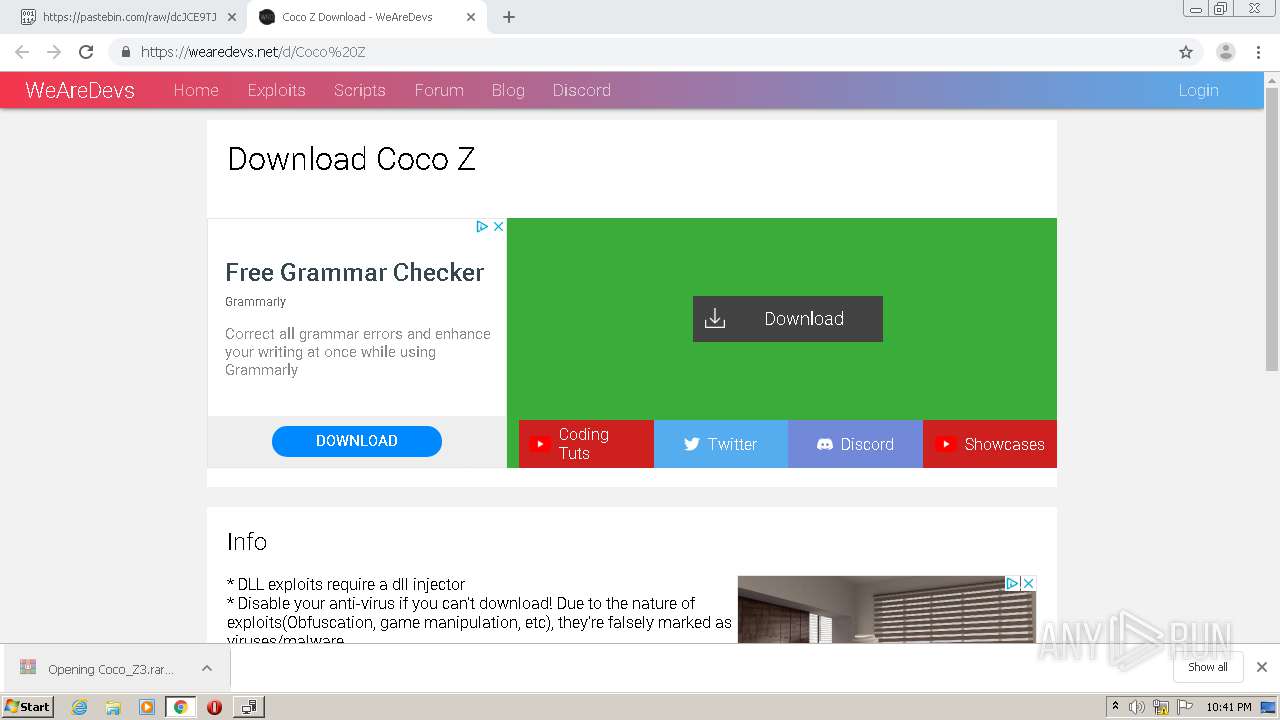
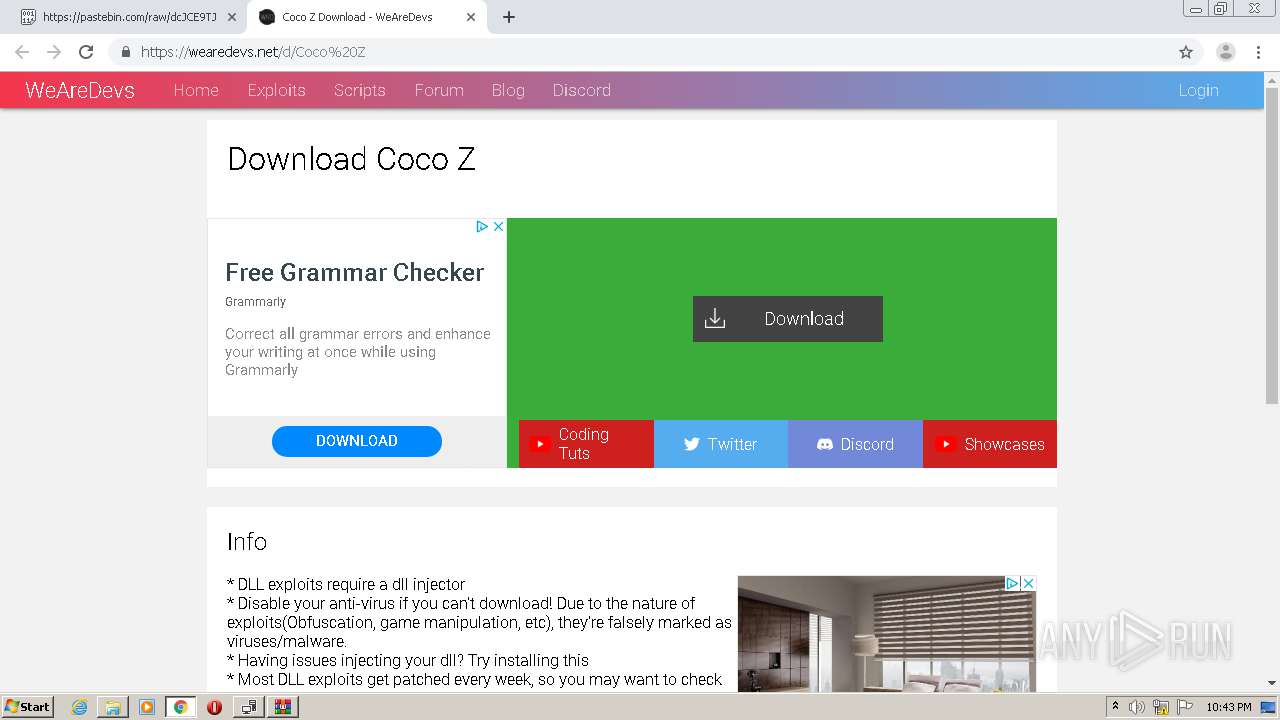
1248 | chrome.exe | GET | 301 | 104.26.7.147:80 | http://wearedevs.net/d/Coco%20Z | US | — | — | whitelisted |
— | — | HEAD | 302 | 23.43.214.226:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03928.00&sar=amd64&o1=netfx_Patch_x86.msp | US | — | — | whitelisted |
— | — | HEAD | 302 | 23.43.214.226:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03928.00&sar=amd64&o1=NetFx472\netfx_Full_x86.msi | US | — | — | whitelisted |
2552 | Setup.exe | GET | 302 | 23.43.214.226:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03928.00&sar=amd64&o1=NetFx472%5Cnetfx_Full_x86.msi | US | — | — | whitelisted |
2552 | Setup.exe | GET | 302 | 23.43.214.226:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03928.00&sar=amd64&o1=NetFx472\netfx_Full_x86.msi | US | — | — | whitelisted |
— | — | GET | 302 | 23.43.214.226:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=netfx&sbp=Net48Rel1&plcid=0x409&clcid=0x409&ar=03928.00&sar=amd64&o1=netfx_Patch_x86.msp | US | — | — | whitelisted |
2552 | Setup.exe | GET | 200 | 2.18.233.62:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | der | 813 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1248 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1248 | chrome.exe | 216.58.210.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1248 | chrome.exe | 84.15.64.14:80 | r3---sn-cpux-8ovs.gvt1.com | UAB Bite Lietuva | LT | whitelisted |
1248 | chrome.exe | 172.217.20.4:443 | www.google.com | Google Inc. | US | whitelisted |
1248 | chrome.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1248 | chrome.exe | 104.26.7.147:80 | wearedevs.net | Cloudflare Inc | US | suspicious |
1248 | chrome.exe | 104.26.7.147:443 | wearedevs.net | Cloudflare Inc | US | suspicious |
1248 | chrome.exe | 172.217.23.162:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
1248 | chrome.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-cpux-8ovs.gvt1.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
wearedevs.net |
| whitelisted |